| File name: | Request for Quotation-RFQ20250324.exe |
| Full analysis: | https://app.any.run/tasks/a30edd5a-9547-4e8a-b9f1-811254293467 |
| Verdict: | Malicious activity |
| Threats: | GuLoader is an advanced downloader written in shellcode. It’s used by criminals to distribute other malware, notably trojans, on a large scale. It’s infamous for using anti-detection and anti-analysis capabilities. |
| Analysis date: | March 25, 2025, 07:15:50 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive, 5 sections |
| MD5: | 2A8FBE2D50908C07A7CD4CDCE653BAD3 |
| SHA1: | F8B7F96A3D2D44E57129741690899DB4B4E21CD8 |
| SHA256: | 7BF0A9004804816099998527AFEED9128F2AC1AE7431F851FD60CF014B141104 |
| SSDEEP: | 24576:pvCj8j3RsWh9B7gDeZJuFWoPJDKpRhR/k9vE+JqtPSJ+b34HAc/QWf2PI:pvCj8j3RDh9B7gDeZJuFZPJDKpRhR8y8 |
MALICIOUS
GULOADER SHELLCODE has been detected (YARA)
- powershell.exe (PID: 6040)
GULOADER has been detected (YARA)
- powershell.exe (PID: 6040)
SNAKE has been detected (YARA)
- msiexec.exe (PID: 4040)
SUSPICIOUS
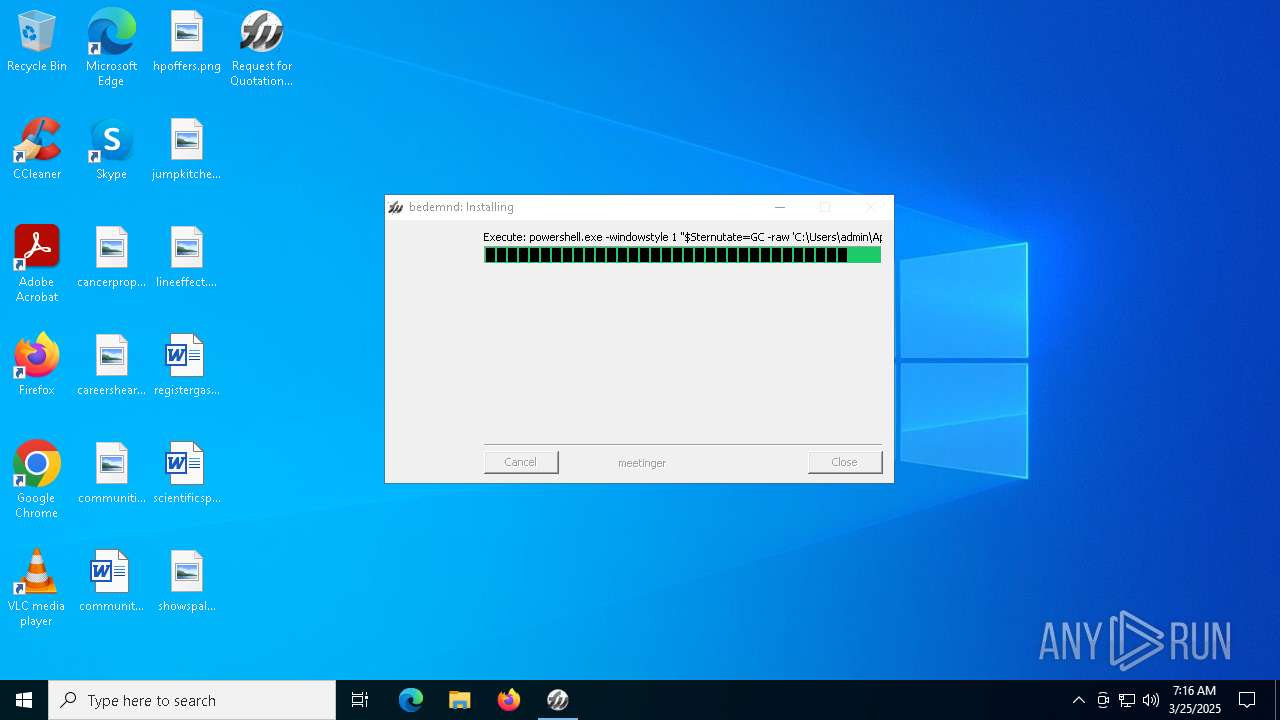
Starts POWERSHELL.EXE for commands execution
- Request for Quotation-RFQ20250324.exe (PID: 6964)
Converts a specified value to a byte (POWERSHELL)
- powershell.exe (PID: 6040)
Executable content was dropped or overwritten
- powershell.exe (PID: 6040)
Executes application which crashes
- msiexec.exe (PID: 4040)
INFO
Create files in a temporary directory
- Request for Quotation-RFQ20250324.exe (PID: 6964)
Reads the computer name
- Request for Quotation-RFQ20250324.exe (PID: 6964)
Checks supported languages
- Request for Quotation-RFQ20250324.exe (PID: 6964)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 6040)
Gets data length (POWERSHELL)
- powershell.exe (PID: 6040)
Converts byte array into ASCII string (POWERSHELL)
- powershell.exe (PID: 6040)
Checks whether the specified file exists (POWERSHELL)
- powershell.exe (PID: 6040)
Uses string split method (POWERSHELL)
- powershell.exe (PID: 6040)
Reads security settings of Internet Explorer
- msiexec.exe (PID: 4040)
Checks proxy server information
- msiexec.exe (PID: 4040)
- slui.exe (PID: 5400)
Reads the software policy settings
- msiexec.exe (PID: 4040)
- slui.exe (PID: 616)
- slui.exe (PID: 5400)
Creates files or folders in the user directory
- WerFault.exe (PID: 5244)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (67.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.2) |
| .exe | | | Win32 Executable (generic) (9.7) |
| .exe | | | Generic Win/DOS Executable (4.3) |
| .exe | | | DOS Executable Generic (4.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2020:07:31 23:27:21+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 26112 |
| InitializedDataSize: | 3805696 |
| UninitializedDataSize: | 2048 |
| EntryPoint: | 0x34a2 |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Total processes
163
Monitored processes
12
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 536 | "C:\WINDOWS\system32\UCPDMgr.exe" | C:\Windows\System32\UCPDMgr.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: User Choice Protection Manager Exit code: 0 Version: 1.0.0.414301 Modules
| |||||||||||||||
| 616 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | SppExtComObj.Exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1660 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4040 | "C:\WINDOWS\SysWOW64\msiexec.exe" | C:\Windows\SysWOW64\msiexec.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 3762504530 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5244 | C:\WINDOWS\SysWOW64\WerFault.exe -u -p 4040 -s 2332 | C:\Windows\SysWOW64\WerFault.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Problem Reporting Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5400 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5528 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5964 | "C:\WINDOWS\system32\UCPDMgr.exe" | C:\Windows\System32\UCPDMgr.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: User Choice Protection Manager Exit code: 0 Version: 1.0.0.414301 Modules
| |||||||||||||||
| 6040 | powershell.exe -windowstyle 1 "$Sternutate=GC -raw 'C:\Users\admin\AppData\Local\Temp\bremseraket\brother\Sakalava.Cor';$Giringernes=$Sternutate.SubString(53052,3);.$Giringernes($Sternutate)" | C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe | Request for Quotation-RFQ20250324.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6780 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | UCPDMgr.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
19 460
Read events
19 459
Write events
1
Delete events
0
Modification events
| (PID) Process: | (6964) Request for Quotation-RFQ20250324.exe | Key: | HKEY_CURRENT_USER\Cinnoberrdes\Uninstall\Hjrdt |
| Operation: | write | Name: | modularizing |
Value: 0 | |||
Executable files
1
Suspicious files
7
Text files
15
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6964 | Request for Quotation-RFQ20250324.exe | C:\Users\admin\AppData\Local\Temp\bremseraket\brother\Produktkontroller.Uin | binary | |
MD5:91F0A51E649E051B647DA63957ACC97E | SHA256:3124420CE18771F1AE5038C88091E1F2596FF76B9756A046F13079C7F47AA11E | |||
| 6964 | Request for Quotation-RFQ20250324.exe | C:\Users\admin\AppData\Local\Temp\bremseraket\brother\monstrosity.jpg | image | |
MD5:82E92251110D9EF915AA0139BAA18AE3 | SHA256:EBAD3EF4674AFAAF3AE1C962E7BE6A23C8C8664455AEB18E07AF15B84D8F4950 | |||
| 6964 | Request for Quotation-RFQ20250324.exe | C:\Users\admin\AppData\Local\Temp\bremseraket\brother\Brneforsorgen57.kor | binary | |
MD5:08D117BA4A9C832CC30E032C7BCF7474 | SHA256:6207CAB20D6E437934816344BCC024D6DE625AD0AF4139A32EB9476A3A5E98DE | |||
| 6964 | Request for Quotation-RFQ20250324.exe | C:\Users\admin\AppData\Local\Temp\bremseraket\brother\maadehold.jpg | image | |
MD5:24231B987AFE80EE9FAC1E7A88974ED7 | SHA256:48A34680FAB2D112DAE48D9BE43730131646AD3EEC352C0686CADD34062FF13B | |||
| 5244 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\ReportQueue\AppCrash_msiexec.exe_f94532dbcfb749ffa7a61da790f4e296f08a4_e3234a03_d90e0530-2921-4380-9a3c-f9696f34244a\Report.wer | — | |
MD5:— | SHA256:— | |||
| 5244 | WerFault.exe | C:\Users\admin\AppData\Local\CrashDumps\msiexec.exe.4040.dmp | — | |
MD5:— | SHA256:— | |||
| 6964 | Request for Quotation-RFQ20250324.exe | C:\Users\admin\AppData\Local\Temp\bremseraket\brother\Tejns.ini | text | |
MD5:BB68691C101EBA2B784C6C6D2E278C64 | SHA256:41F7E84A177337F60EBF11D0B52FF9DDD3031C519243074EEBF4425BDB6803F4 | |||
| 6964 | Request for Quotation-RFQ20250324.exe | C:\Users\admin\AppData\Local\Temp\bremseraket\brother\saltworker.lov | binary | |
MD5:02066795962478538949DDAAA39AD8E2 | SHA256:622FED9C730729C6840EB073EDA1C5A41F374B034D2ECF894A6EBFFECC9D8B6D | |||
| 6964 | Request for Quotation-RFQ20250324.exe | C:\Users\admin\AppData\Local\Temp\bremseraket\brother\maskulinitetens.str | binary | |
MD5:752AFECA31E0B3748C0345DA7761865C | SHA256:D8944C09A73AE4B6C67F185DDA3CF0876813183D863AB25F6142A0E896650091 | |||
| 6964 | Request for Quotation-RFQ20250324.exe | C:\Users\admin\AppData\Local\Temp\bremseraket\brother\Boyos\workfile.txt | text | |
MD5:EC854A5D93F10747B372EC3CC25D2162 | SHA256:A1BDC83CE5564EC49911451277BF889233E581001DD4E045D7D3704019C33CFD | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
54
TCP/UDP connections
89
DNS requests
20
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 303 | 142.250.185.142:443 | https://drive.google.com/uc?export=download&id=1dbFlp4N3At5mAJWqSUIar9v5CFq8UhOk | unknown | — | — | unknown |
— | — | GET | 200 | 40.69.42.241:443 | https://fe3cr.delivery.mp.microsoft.com/clientwebservice/ping | unknown | — | — | unknown |
2560 | SIHClient.exe | GET | 200 | 2.16.164.120:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut_2010-06-23.crl | unknown | — | — | whitelisted |
2560 | SIHClient.exe | GET | 200 | 92.123.22.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Update%20Signing%20CA%202.1.crl | unknown | — | — | whitelisted |
2560 | SIHClient.exe | GET | 200 | 2.16.164.120:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
2560 | SIHClient.exe | GET | 200 | 92.123.22.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Signing%20CA%202.1.crl | unknown | — | — | whitelisted |
2560 | SIHClient.exe | GET | 200 | 2.16.164.120:80 | http://crl.microsoft.com/pki/crl/products/MicTimStaPCA_2010-07-01.crl | unknown | — | — | whitelisted |
2560 | SIHClient.exe | GET | 200 | 92.123.22.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
2560 | SIHClient.exe | GET | 200 | 92.123.22.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Update%20Signing%20CA%202.2.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 20.12.23.50:443 | https://slscr.update.microsoft.com/sls/ping | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2104 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2112 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2104 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4040 | msiexec.exe | 142.250.186.174:443 | drive.google.com | GOOGLE | US | whitelisted |
4040 | msiexec.exe | 142.250.185.193:443 | drive.usercontent.google.com | GOOGLE | US | whitelisted |
616 | slui.exe | 20.83.72.98:443 | activation-v2.sls.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5400 | slui.exe | 20.83.72.98:443 | activation-v2.sls.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
drive.google.com |
| whitelisted |
drive.usercontent.google.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |