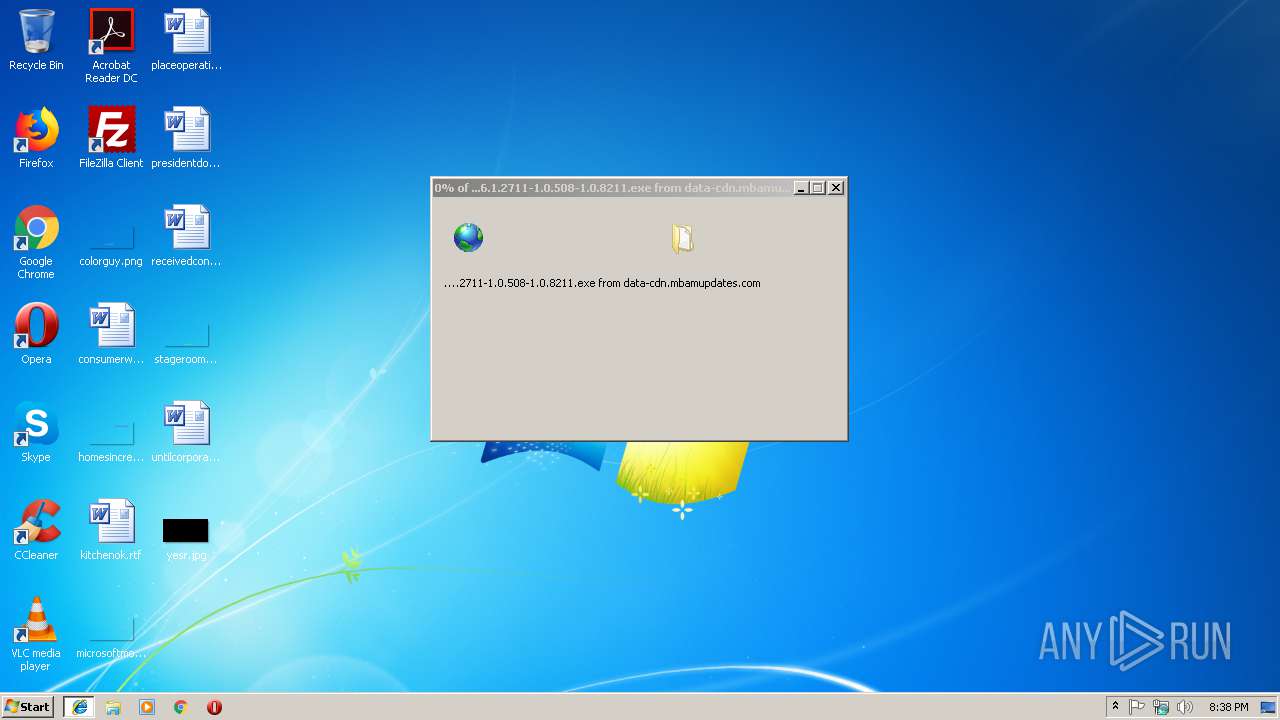
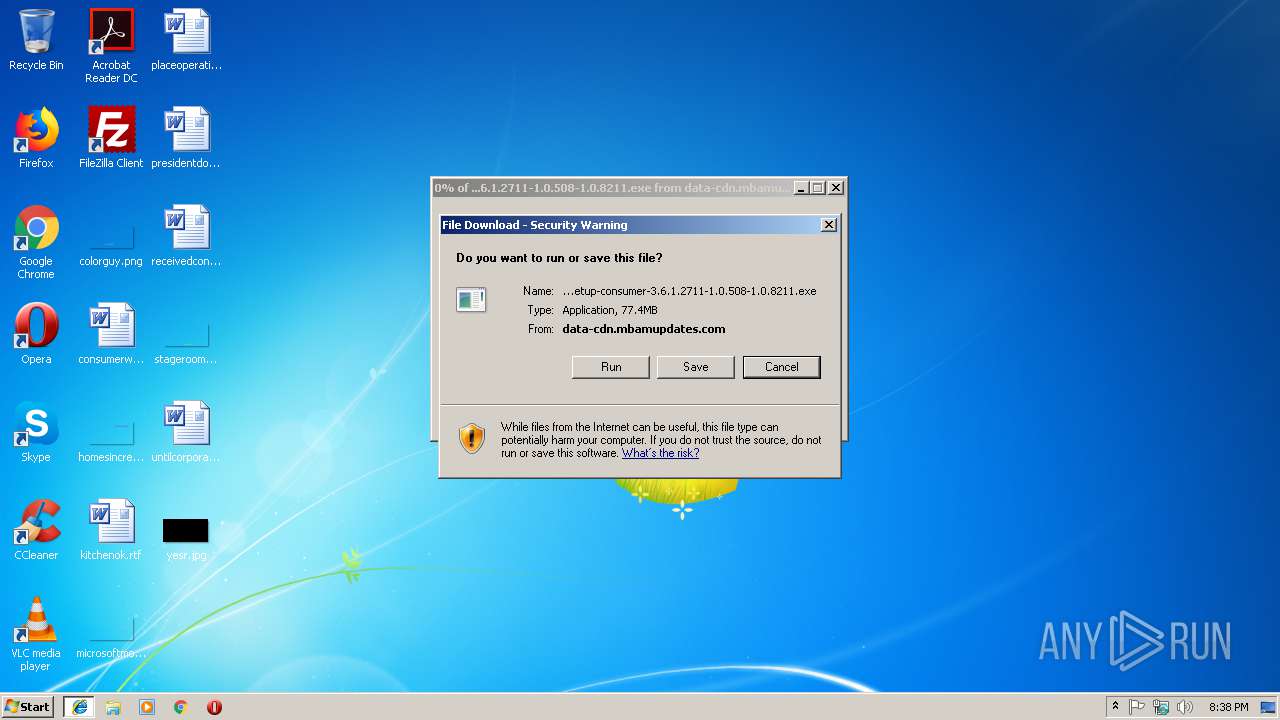
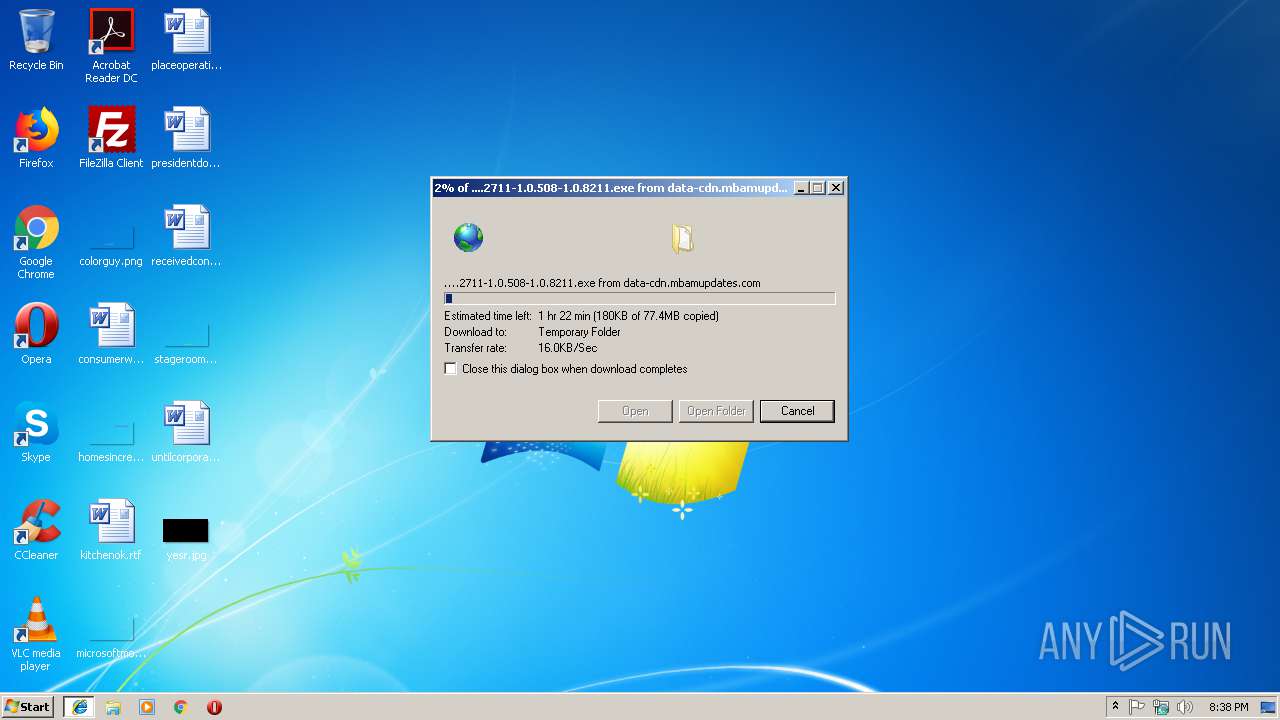
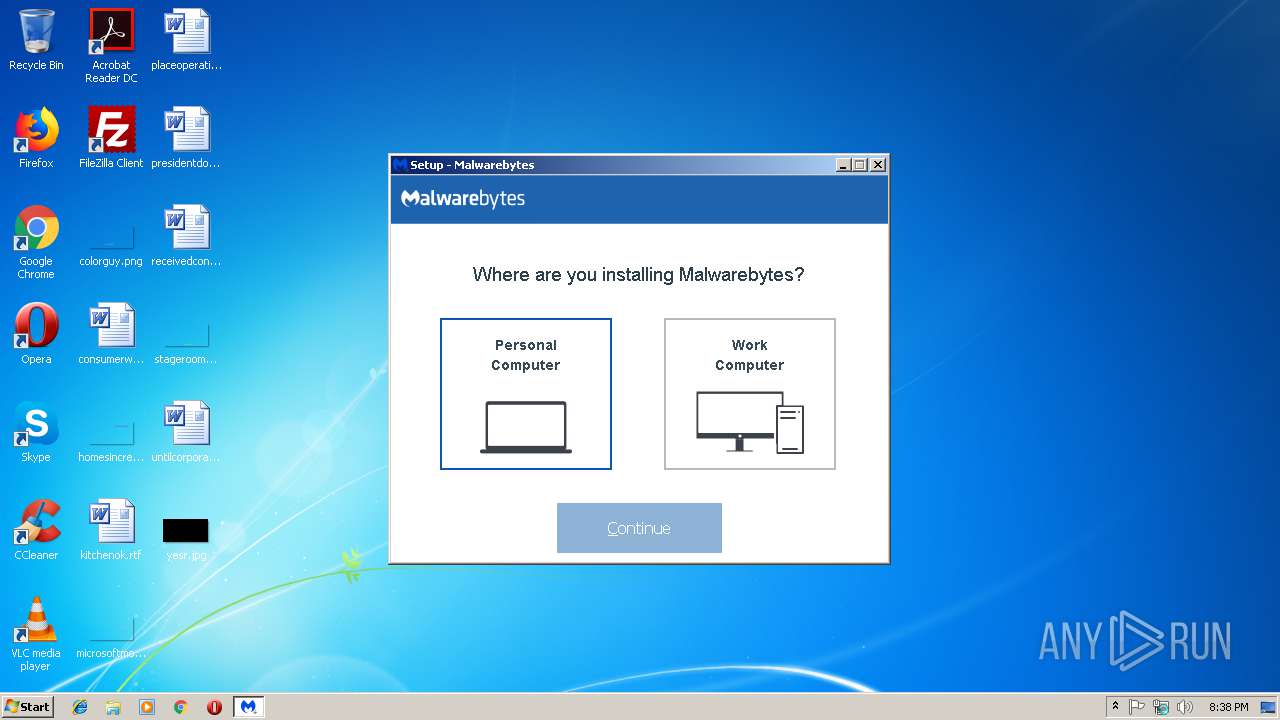
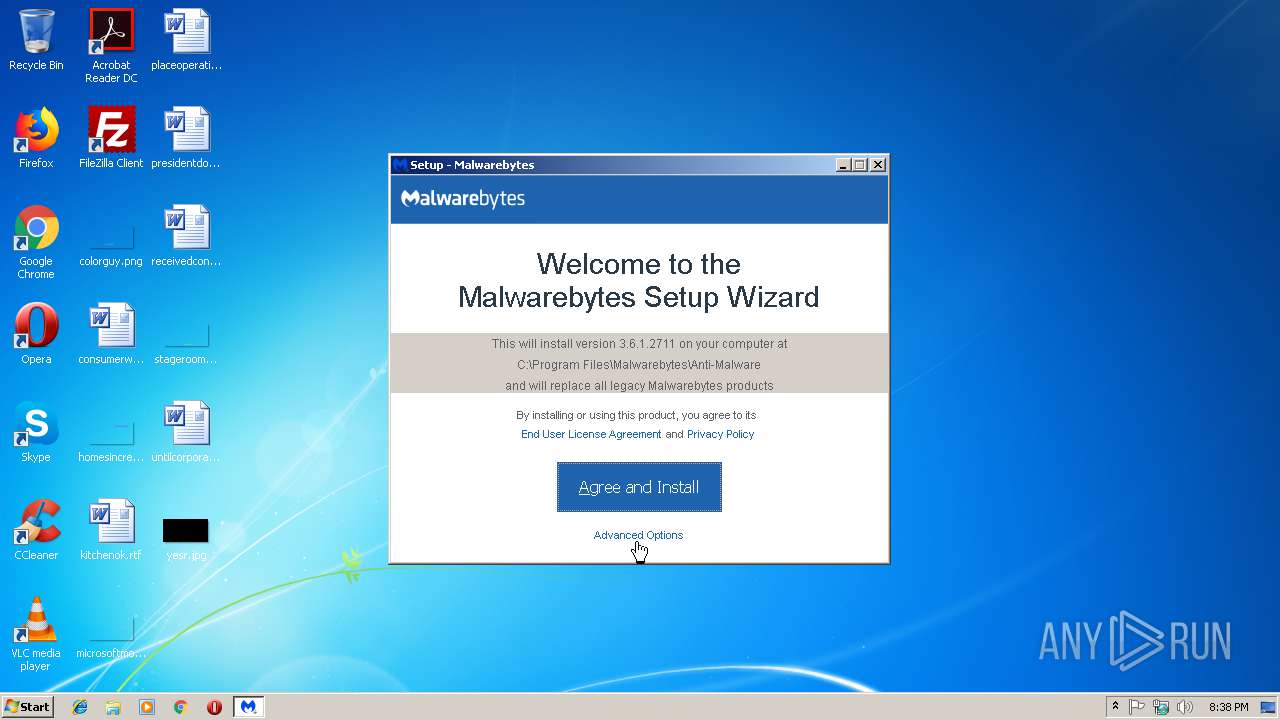
| URL: | https://data-cdn.mbamupdates.com/web/mb3-setup-consumer/mb3-setup-consumer-3.6.1.2711-1.0.508-1.0.8211.exe |
| Full analysis: | https://app.any.run/tasks/3c05bfda-4c82-4d90-99c3-25e4c985b1a6 |
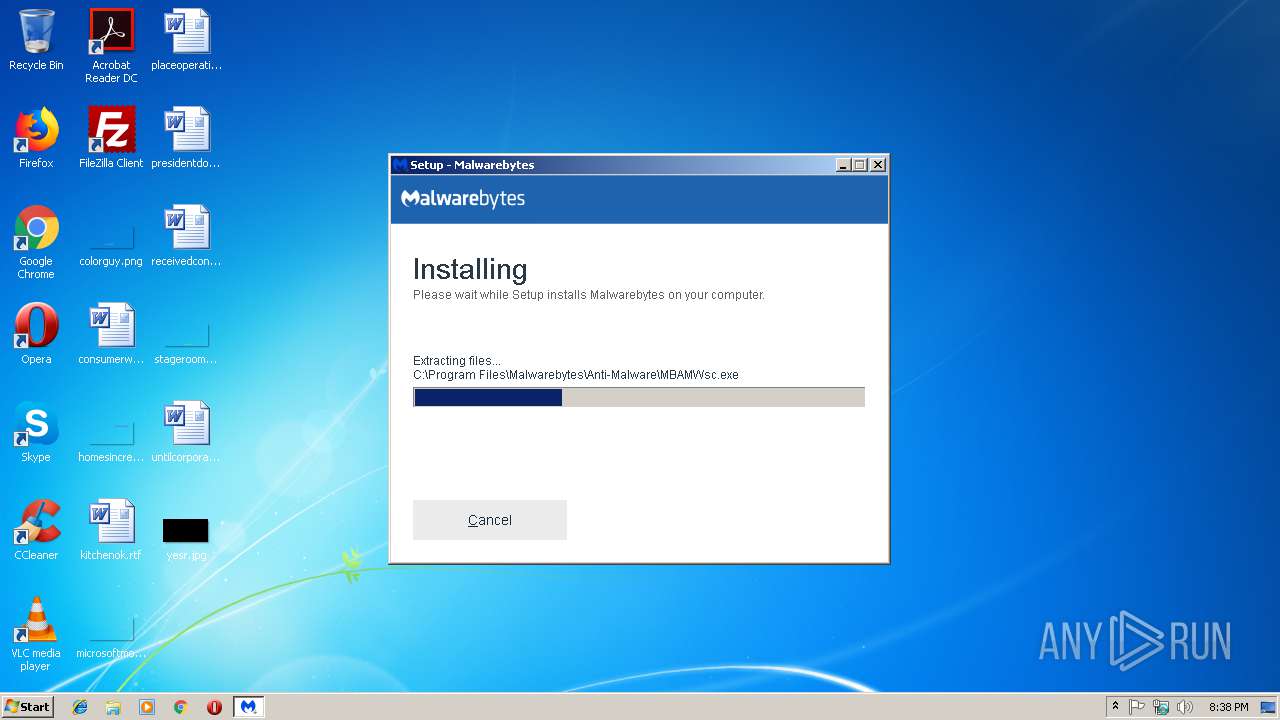
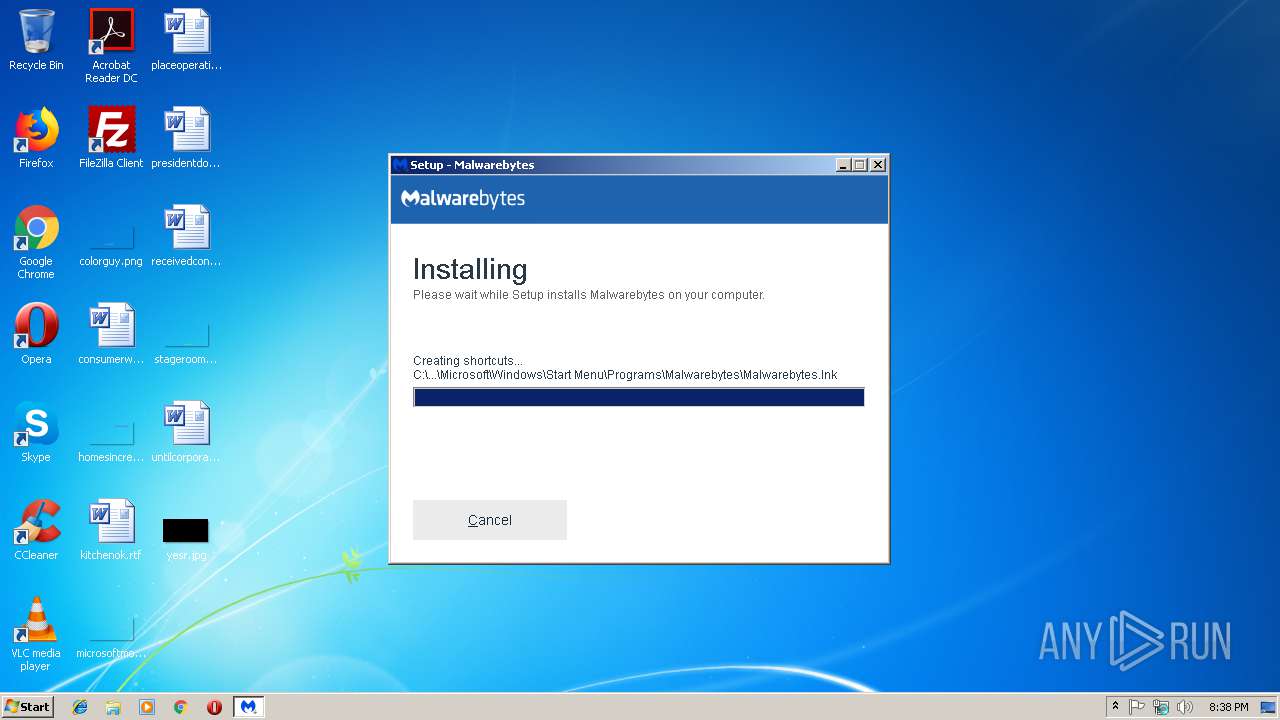
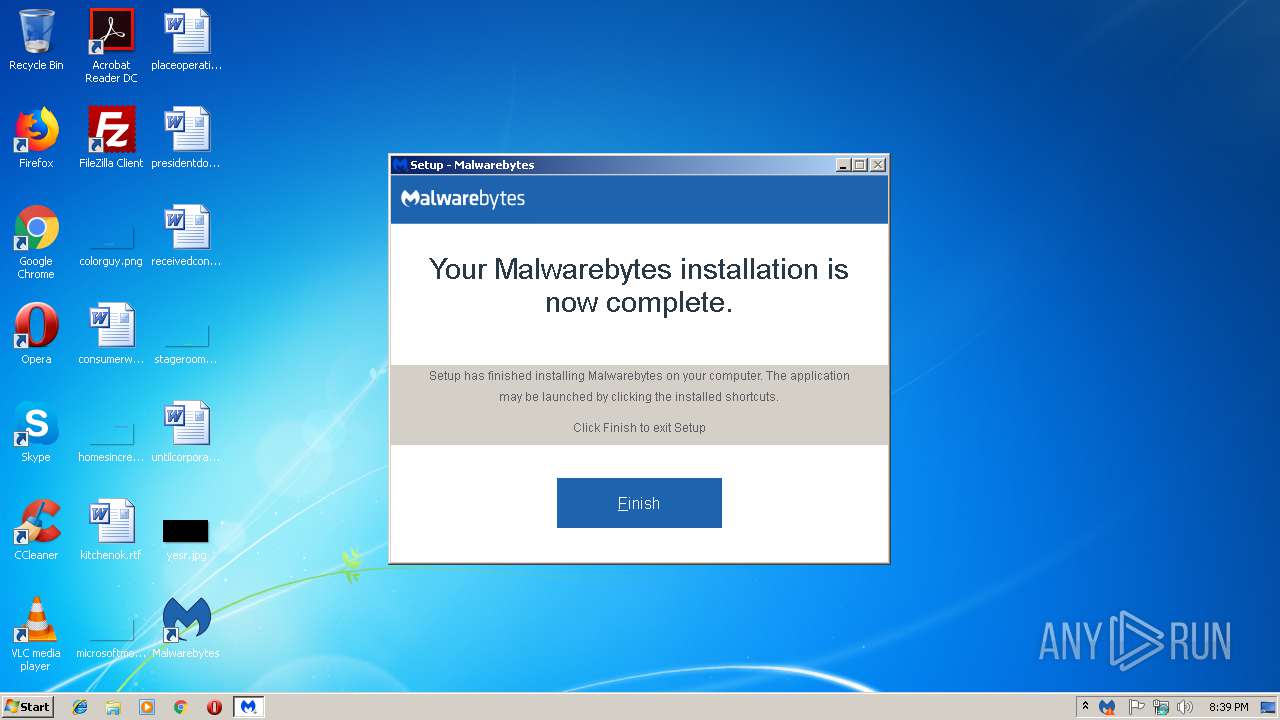
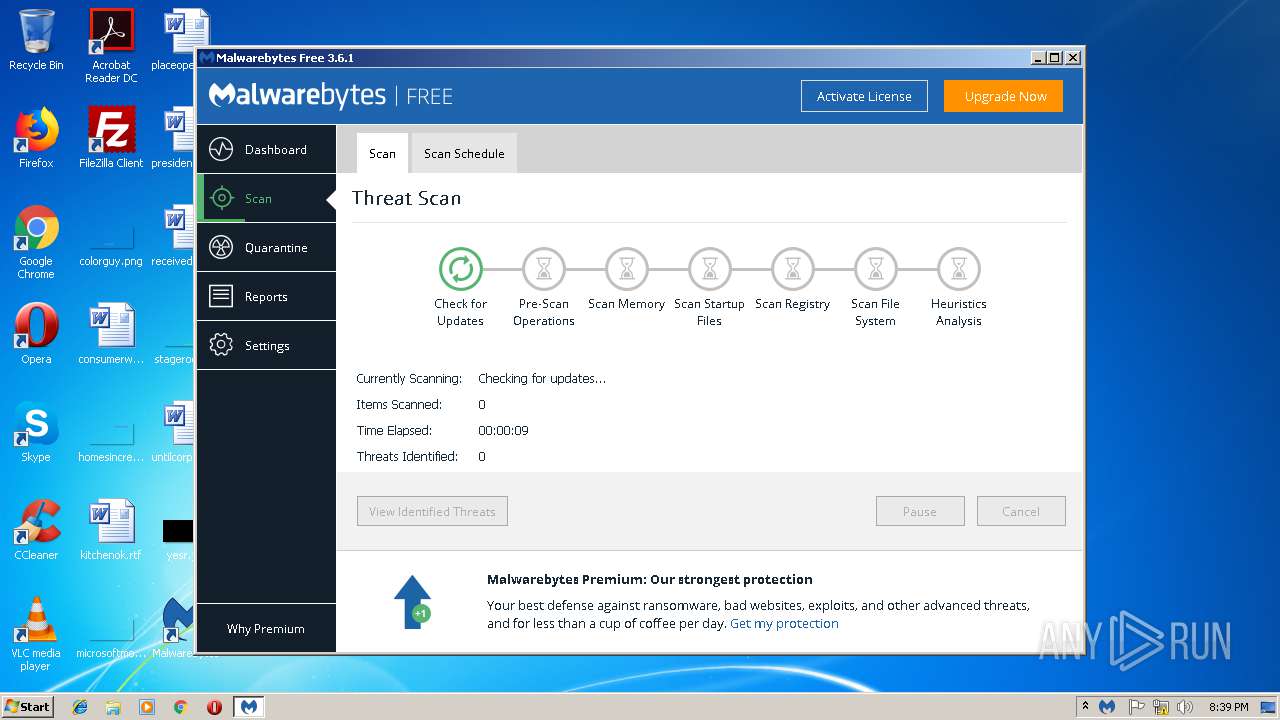
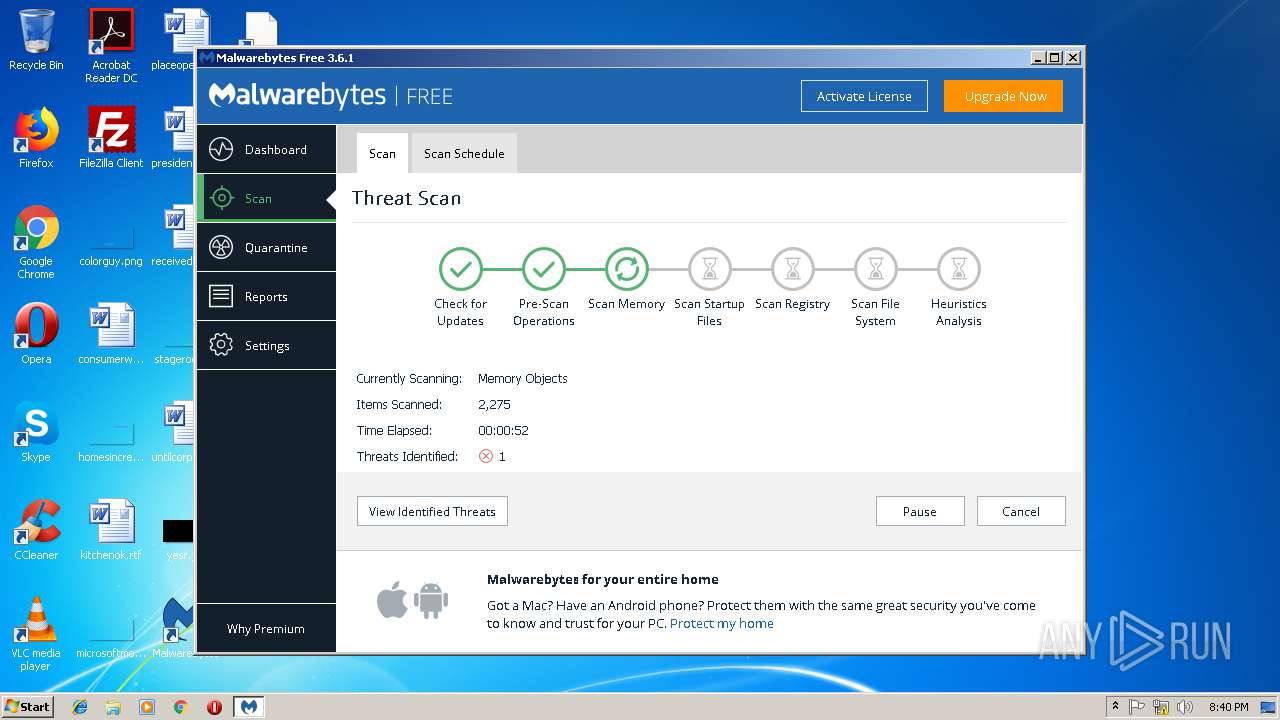
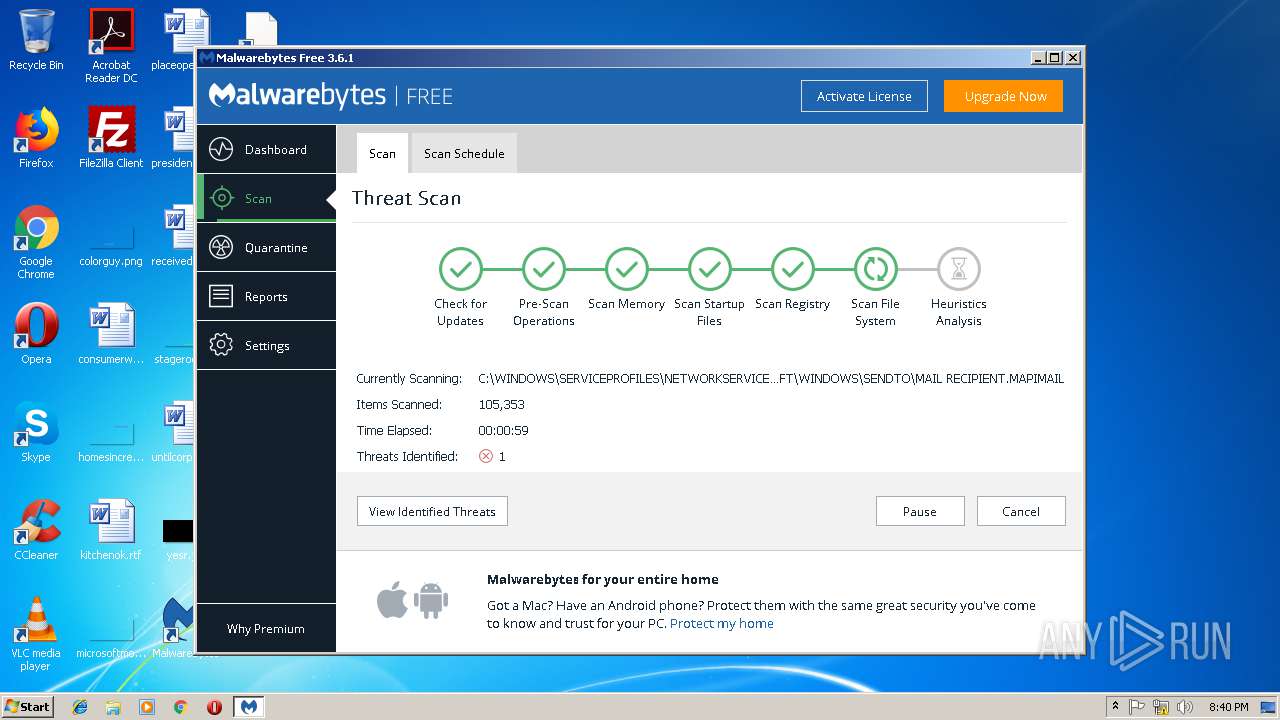
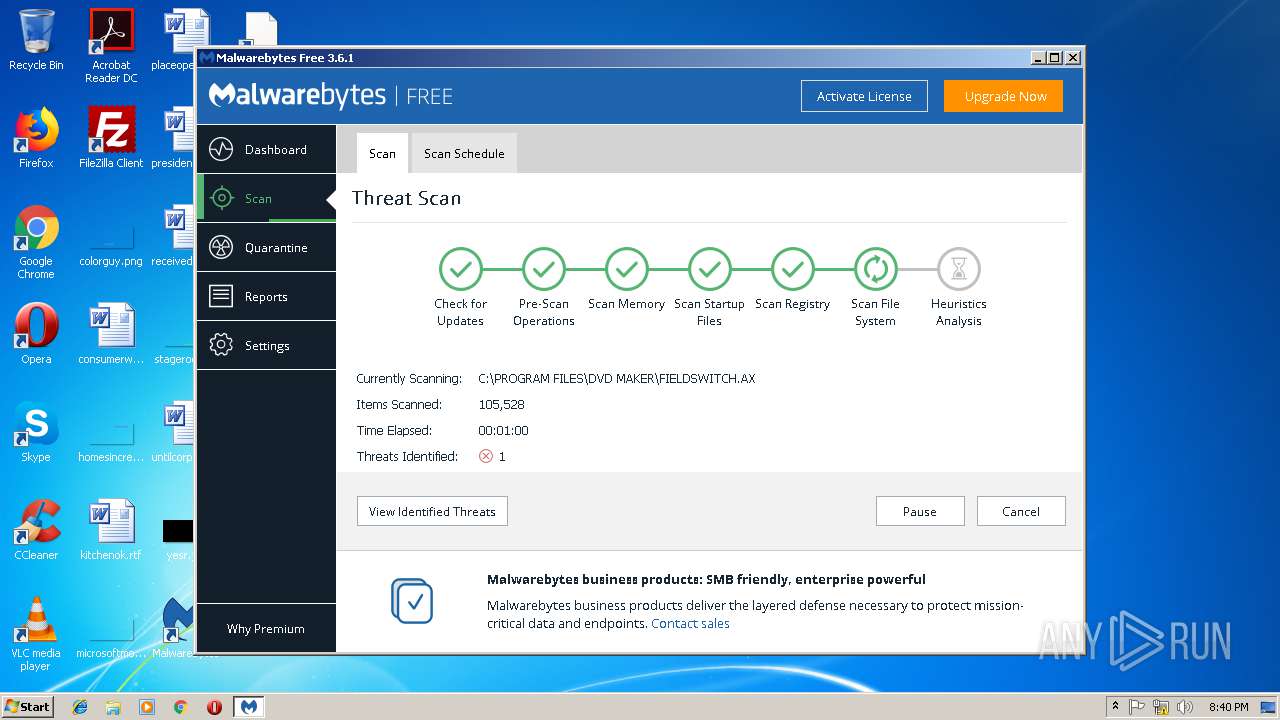
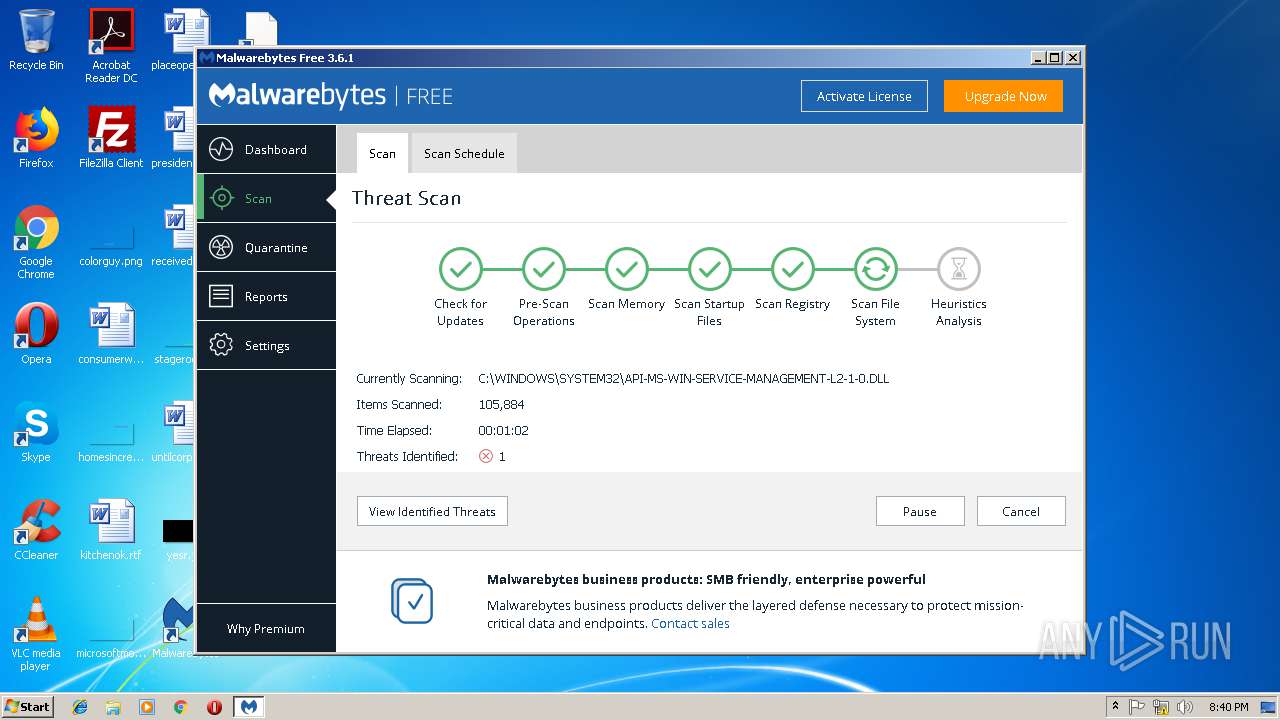
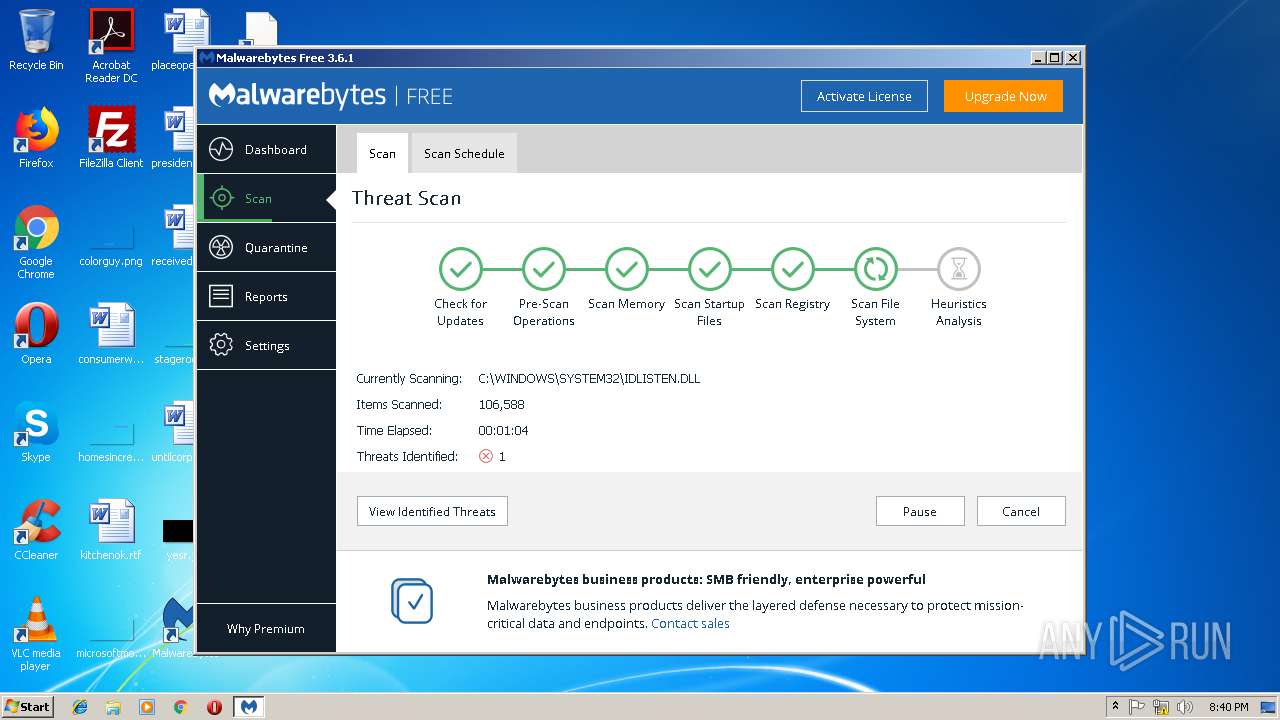
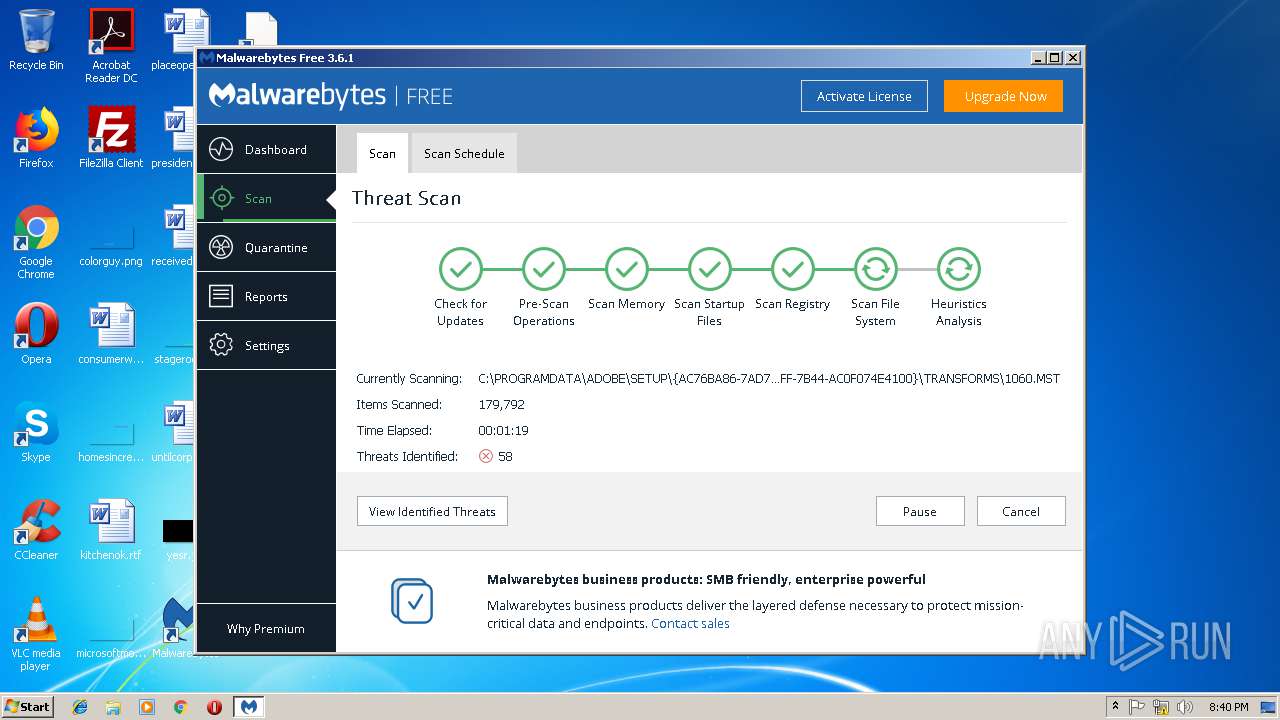
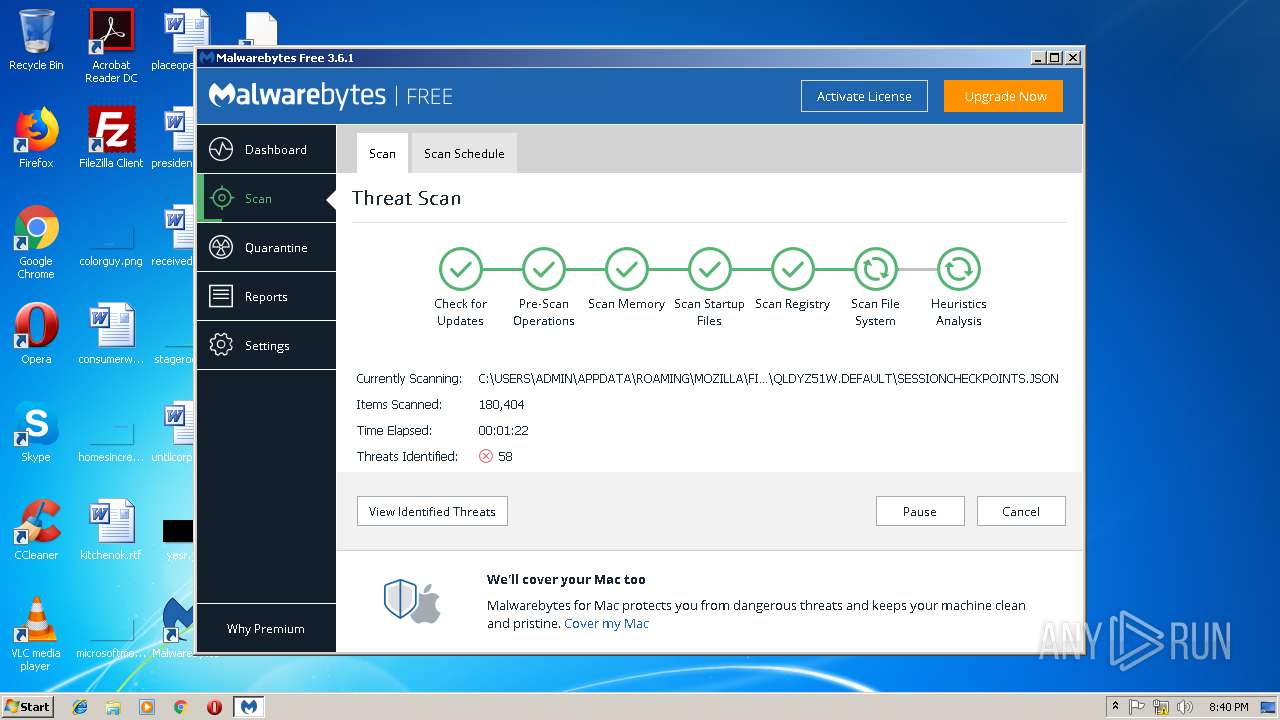
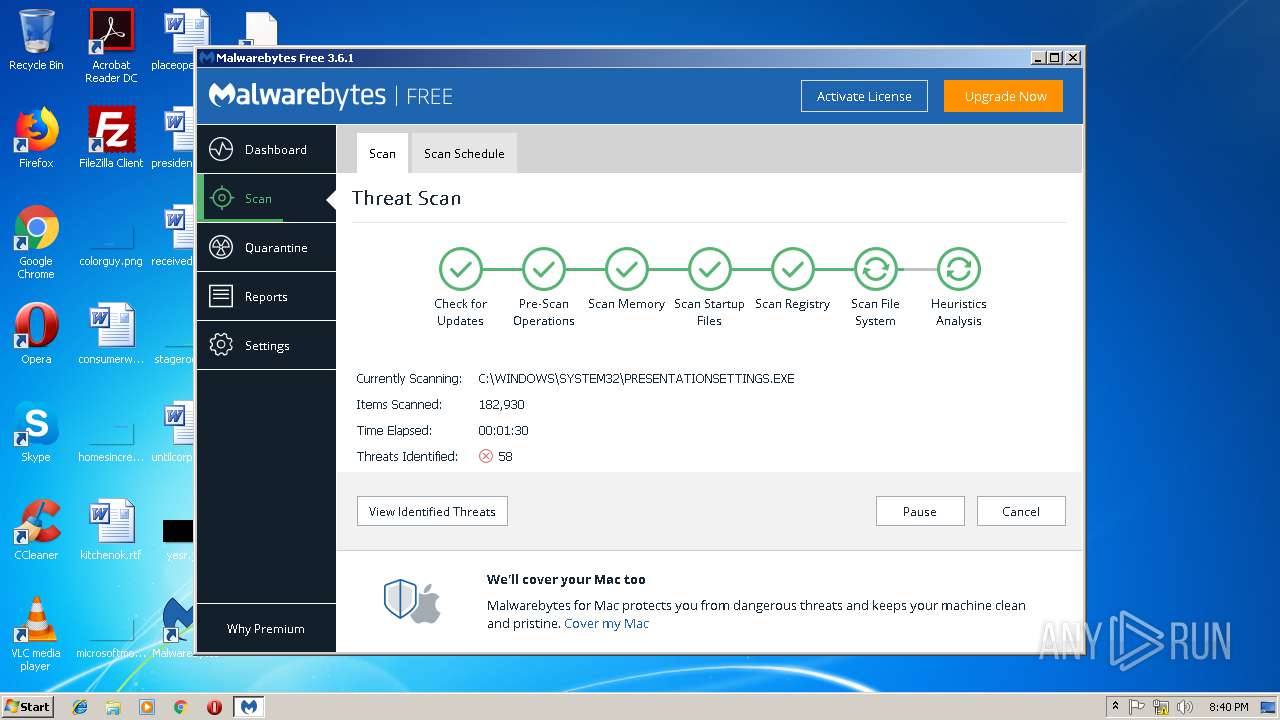
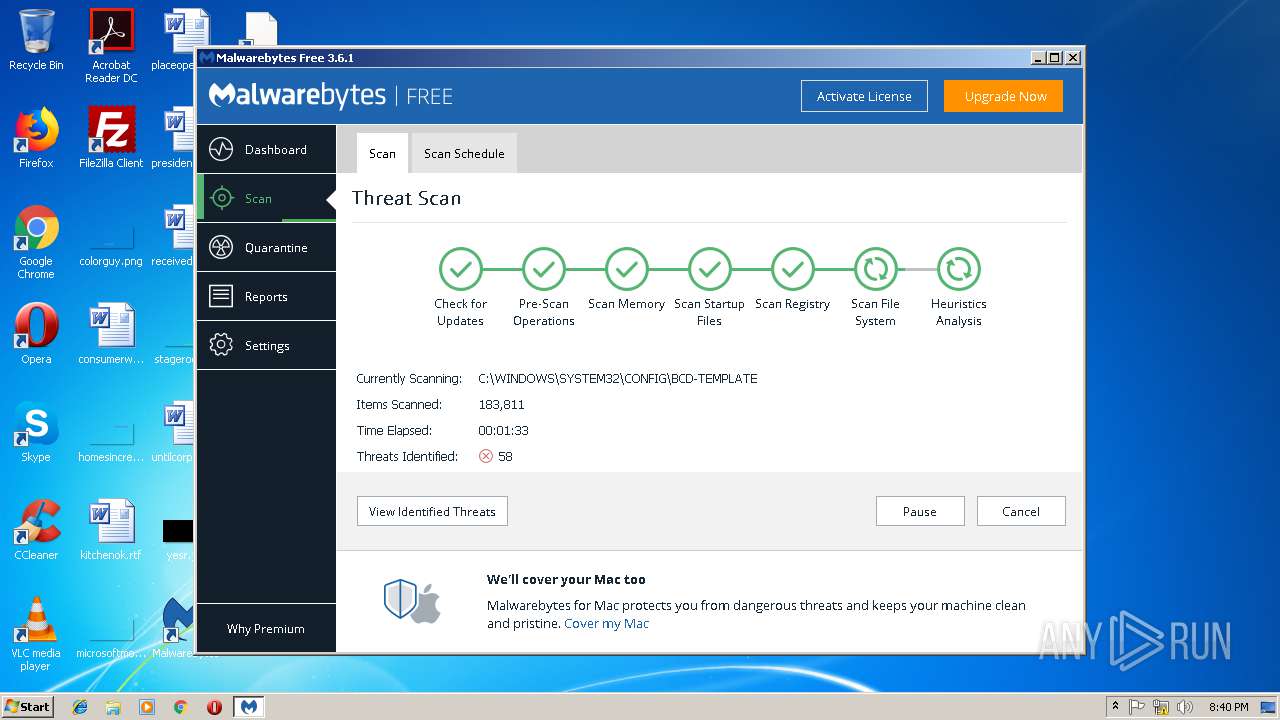
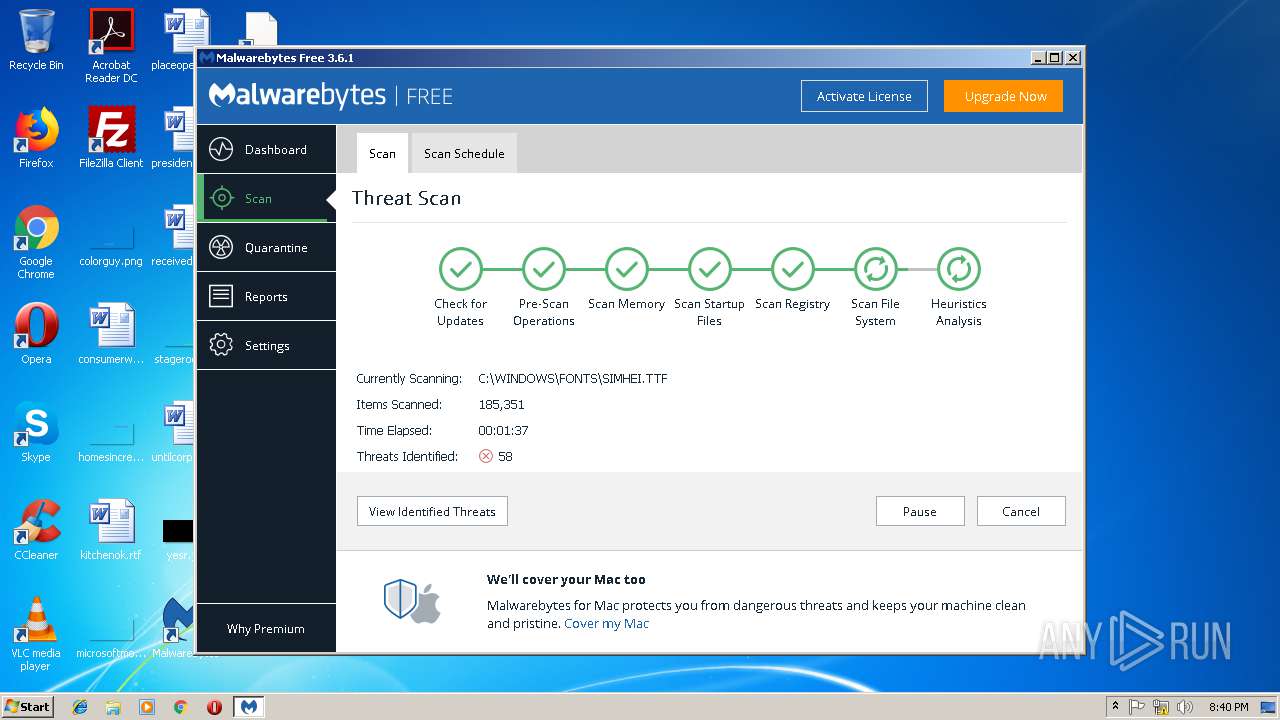
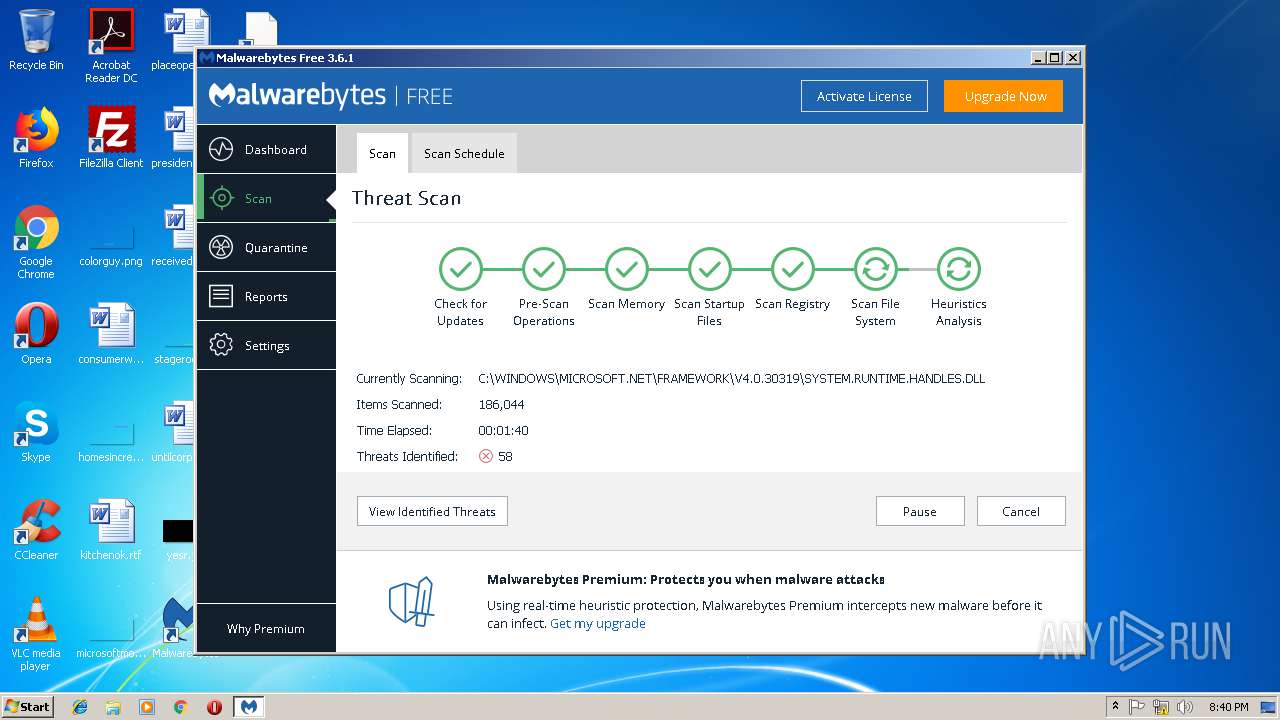
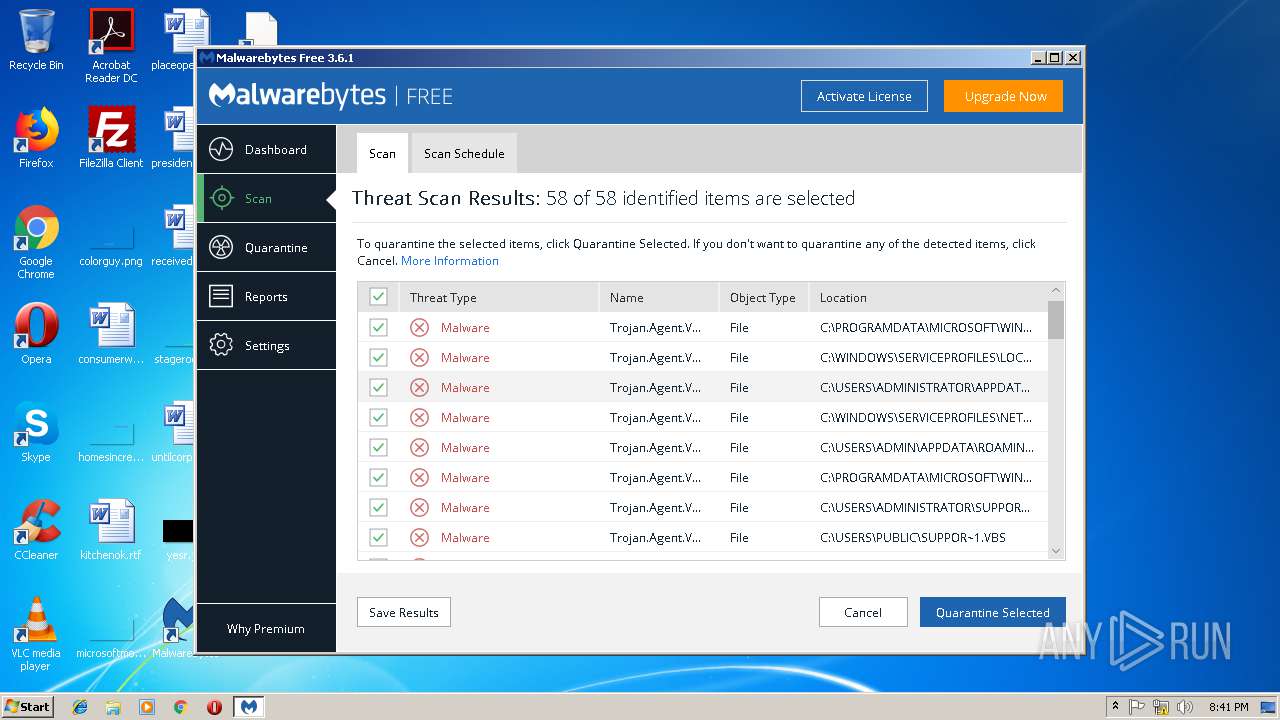
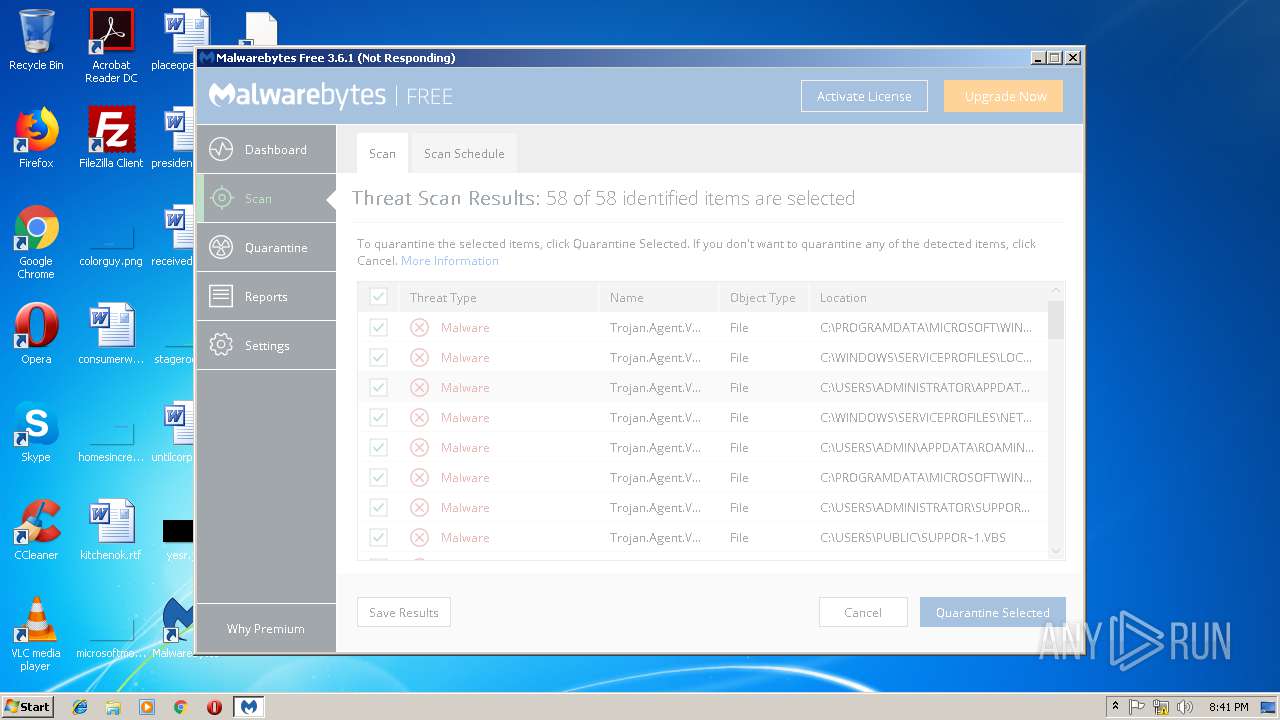
| Verdict: | Malicious activity |
| Threats: | Agent Tesla is spyware that collects information about the actions of its victims by recording keystrokes and user interactions. It is falsely marketed as a legitimate software on the dedicated website where this malware is sold. |
| Analysis date: | January 09, 2019, 20:38:13 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | E7BEAAE7A80D4ABCDD97FBB79D3EFF07 |
| SHA1: | 269E457301B288C383251BE94B4E03B6E19C44C9 |
| SHA256: | 7BE6A84514282CAF46ACF17CCEA74335528BBFC7E32FF2F3258F959302C8D2CC |
| SSDEEP: | 3:N8ciFiEnDMGFAt0MIZI2IW00MIbM+mcPhR:2cynnQGFhZ9IWpbrdR |
MALICIOUS
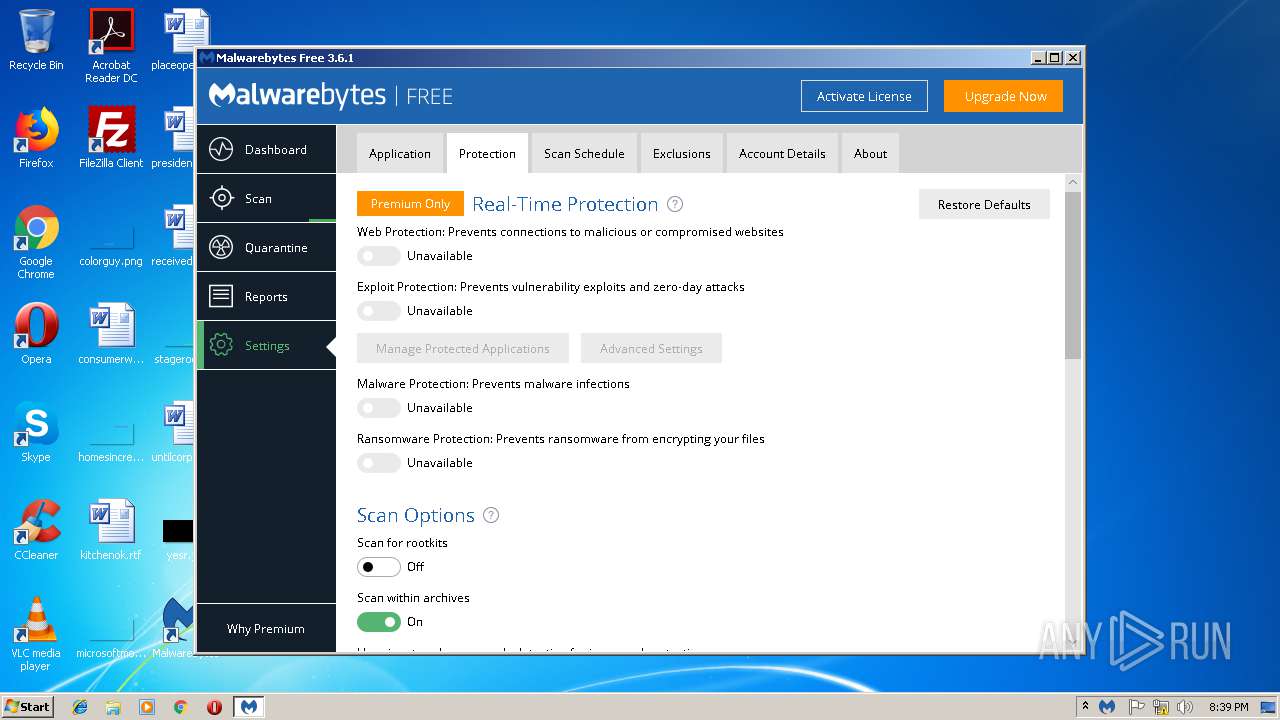
Changes settings of System certificates
- certutil.exe (PID: 2740)
- certutil.exe (PID: 3644)
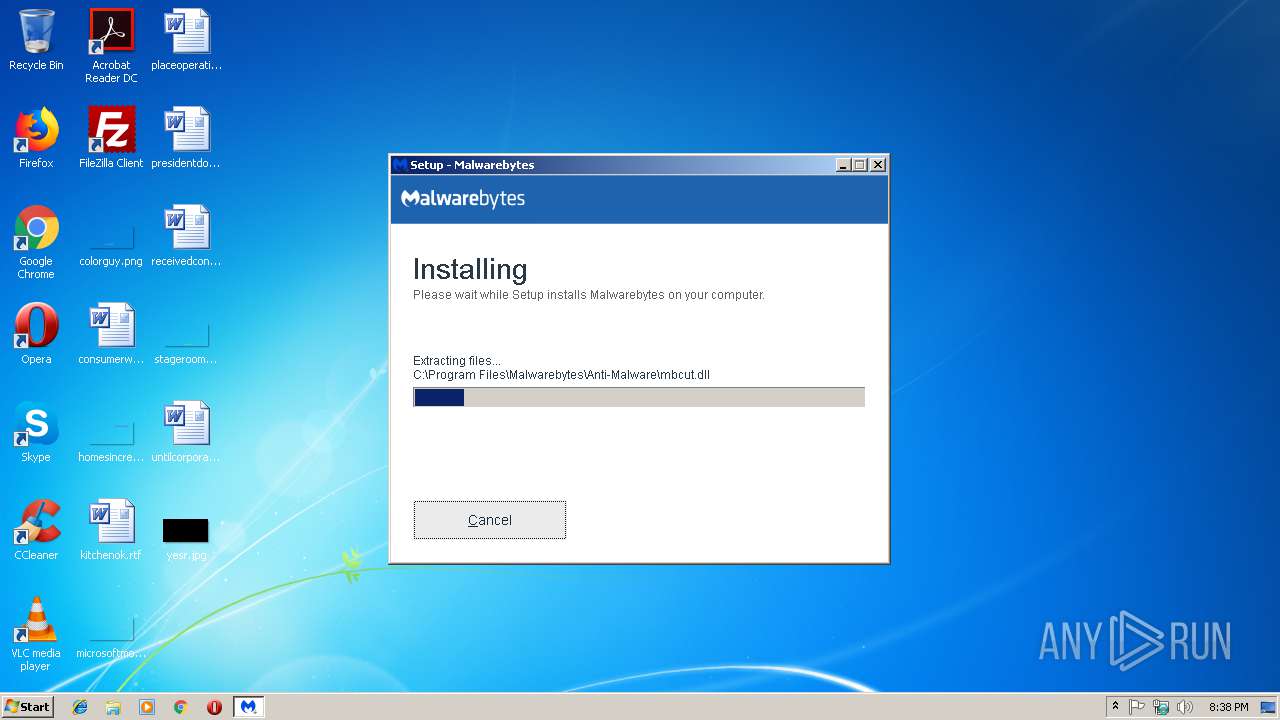
Application was dropped or rewritten from another process
- mbam.exe (PID: 2040)
- mbamtray.exe (PID: 2664)
- mbamservice.exe (PID: 3104)
- mbamservice.exe (PID: 3692)
Loads dropped or rewritten executable
- mbam.exe (PID: 2040)
- mbamservice.exe (PID: 3692)
- mbamtray.exe (PID: 2664)
Detected AgentTesla Keylogger
- mbamservice.exe (PID: 3692)
SUSPICIOUS
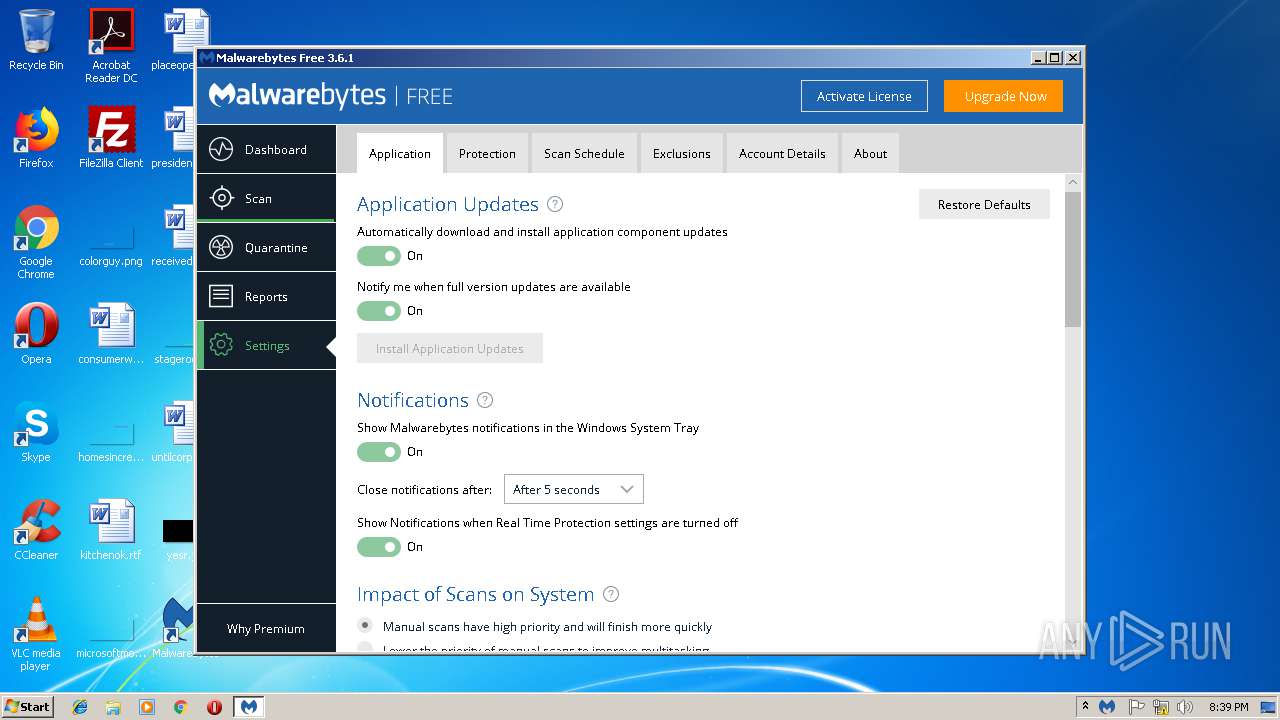
Reads the Windows organization settings
- mb3-setup-consumer-3.6.1.2711-1.0.508-1.0.8211[1].tmp (PID: 2892)
Reads Windows owner or organization settings
- mb3-setup-consumer-3.6.1.2711-1.0.508-1.0.8211[1].tmp (PID: 2892)
Executable content was dropped or overwritten
- mb3-setup-consumer-3.6.1.2711-1.0.508-1.0.8211[1].exe (PID: 3480)
- mb3-setup-consumer-3.6.1.2711-1.0.508-1.0.8211[1].exe (PID: 2508)
- mb3-setup-consumer-3.6.1.2711-1.0.508-1.0.8211[1].tmp (PID: 2892)
- mbamservice.exe (PID: 3692)
Creates files in the Windows directory
- mb3-setup-consumer-3.6.1.2711-1.0.508-1.0.8211[1].tmp (PID: 2892)
- certutil.exe (PID: 2740)
- certutil.exe (PID: 3644)
- mbamservice.exe (PID: 3692)
Creates files in the driver directory
- mb3-setup-consumer-3.6.1.2711-1.0.508-1.0.8211[1].tmp (PID: 2892)
- mbamservice.exe (PID: 3692)
Changes IE settings (feature browser emulation)
- mb3-setup-consumer-3.6.1.2711-1.0.508-1.0.8211[1].tmp (PID: 2892)
Modifies the open verb of a shell class
- mb3-setup-consumer-3.6.1.2711-1.0.508-1.0.8211[1].tmp (PID: 2892)
Creates COM task schedule object
- mbamservice.exe (PID: 3692)
Removes files from Windows directory
- certutil.exe (PID: 3644)
- certutil.exe (PID: 2740)
- mbamservice.exe (PID: 3692)
Searches for installed software
- mb3-setup-consumer-3.6.1.2711-1.0.508-1.0.8211[1].tmp (PID: 2892)
- mbamservice.exe (PID: 3692)
Creates files in the user directory
- mbam.exe (PID: 2040)
Creates or modifies windows services
- mbamservice.exe (PID: 3692)
Creates files in the program directory
- mbamservice.exe (PID: 3692)
INFO
Application launched itself
- iexplore.exe (PID: 3000)
Application was dropped or rewritten from another process
- mb3-setup-consumer-3.6.1.2711-1.0.508-1.0.8211[1].tmp (PID: 2892)
- mb3-setup-consumer-3.6.1.2711-1.0.508-1.0.8211[1].tmp (PID: 2596)
Reads Internet Cache Settings
- iexplore.exe (PID: 3000)
- iexplore.exe (PID: 3400)
Changes internet zones settings
- iexplore.exe (PID: 3000)
Loads dropped or rewritten executable
- mb3-setup-consumer-3.6.1.2711-1.0.508-1.0.8211[1].tmp (PID: 2892)
Dropped object may contain Bitcoin addresses
- mb3-setup-consumer-3.6.1.2711-1.0.508-1.0.8211[1].tmp (PID: 2892)
- mbamservice.exe (PID: 3692)
Creates a software uninstall entry
- mb3-setup-consumer-3.6.1.2711-1.0.508-1.0.8211[1].tmp (PID: 2892)
Reads settings of System Certificates
- mbamservice.exe (PID: 3692)
Creates files in the program directory
- mb3-setup-consumer-3.6.1.2711-1.0.508-1.0.8211[1].tmp (PID: 2892)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
51
Monitored processes
12
Malicious processes
7
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2040 | "C:\Program Files\Malwarebytes\Anti-Malware\mbam.exe" | C:\Program Files\Malwarebytes\Anti-Malware\mbam.exe | mb3-setup-consumer-3.6.1.2711-1.0.508-1.0.8211[1].tmp | ||||||||||||
User: admin Company: Malwarebytes Integrity Level: MEDIUM Description: Malwarebytes Exit code: 0 Version: 3.1.0.1662 Modules
| |||||||||||||||
| 2508 | "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\0UU90R59\mb3-setup-consumer-3.6.1.2711-1.0.508-1.0.8211[1].exe" /SPAWNWND=$40164 /NOTIFYWND=$50214 | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\0UU90R59\mb3-setup-consumer-3.6.1.2711-1.0.508-1.0.8211[1].exe | mb3-setup-consumer-3.6.1.2711-1.0.508-1.0.8211[1].tmp | ||||||||||||
User: admin Company: Malwarebytes Integrity Level: HIGH Description: Malwarebytes Exit code: 0 Version: 3.6.1.2711 Modules
| |||||||||||||||
| 2596 | "C:\Users\admin\AppData\Local\Temp\is-Q6ATG.tmp\mb3-setup-consumer-3.6.1.2711-1.0.508-1.0.8211[1].tmp" /SL5="$50214,80647131,239616,C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\0UU90R59\mb3-setup-consumer-3.6.1.2711-1.0.508-1.0.8211[1].exe" | C:\Users\admin\AppData\Local\Temp\is-Q6ATG.tmp\mb3-setup-consumer-3.6.1.2711-1.0.508-1.0.8211[1].tmp | — | mb3-setup-consumer-3.6.1.2711-1.0.508-1.0.8211[1].exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 2664 | "C:\Program Files\Malwarebytes\Anti-Malware\mbamtray.exe" | C:\Program Files\Malwarebytes\Anti-Malware\mbamtray.exe | mbamservice.exe | ||||||||||||
User: admin Company: Malwarebytes Integrity Level: MEDIUM Description: Malwarebytes Tray Application Exit code: 0 Version: 3.1.0.1662 Modules
| |||||||||||||||
| 2740 | "certutil.exe" -f -addStore root "C:\Users\admin\AppData\Local\Temp\is-TIBAM.tmp\BaltimoreCyberTrustRoot.crt" | C:\Windows\system32\certutil.exe | — | mb3-setup-consumer-3.6.1.2711-1.0.508-1.0.8211[1].tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: CertUtil.exe Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2892 | "C:\Users\admin\AppData\Local\Temp\is-0RFL6.tmp\mb3-setup-consumer-3.6.1.2711-1.0.508-1.0.8211[1].tmp" /SL5="$50130,80647131,239616,C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\0UU90R59\mb3-setup-consumer-3.6.1.2711-1.0.508-1.0.8211[1].exe" /SPAWNWND=$40164 /NOTIFYWND=$50214 | C:\Users\admin\AppData\Local\Temp\is-0RFL6.tmp\mb3-setup-consumer-3.6.1.2711-1.0.508-1.0.8211[1].tmp | mb3-setup-consumer-3.6.1.2711-1.0.508-1.0.8211[1].exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 3000 | "C:\Program Files\Internet Explorer\iexplore.exe" https://data-cdn.mbamupdates.com/web/mb3-setup-consumer/mb3-setup-consumer-3.6.1.2711-1.0.508-1.0.8211.exe | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3104 | "C:\Program Files\Malwarebytes\Anti-Malware\mbamservice.exe" /service | C:\Program Files\Malwarebytes\Anti-Malware\mbamservice.exe | — | mb3-setup-consumer-3.6.1.2711-1.0.508-1.0.8211[1].tmp | |||||||||||
User: admin Company: Malwarebytes Integrity Level: HIGH Description: Malwarebytes Service Exit code: 0 Version: 3.2.0.704 Modules
| |||||||||||||||
| 3400 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3000 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3480 | "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\0UU90R59\mb3-setup-consumer-3.6.1.2711-1.0.508-1.0.8211[1].exe" | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\0UU90R59\mb3-setup-consumer-3.6.1.2711-1.0.508-1.0.8211[1].exe | iexplore.exe | ||||||||||||
User: admin Company: Malwarebytes Integrity Level: MEDIUM Description: Malwarebytes Exit code: 0 Version: 3.6.1.2711 Modules
| |||||||||||||||
Total events
2 632
Read events
1 460
Write events
1 161
Delete events
11
Modification events
| (PID) Process: | (3000) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3000) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3000) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3000) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (3000) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3000) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000069000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3000) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Recovery\Active |
| Operation: | write | Name: | {85337F23-144E-11E9-91D7-5254004A04AF} |
Value: 0 | |||
| (PID) Process: | (3000) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Type |
Value: 4 | |||
| (PID) Process: | (3000) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Count |
Value: 3 | |||
| (PID) Process: | (3000) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Time |
Value: E307010003000900140026001D008B03 | |||
Executable files
129
Suspicious files
144
Text files
272
Unknown types
43
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3000 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\R9ZEWH8D\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 3000 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 3000 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DFB4341703B672BFA6.TMP | — | |
MD5:— | SHA256:— | |||
| 3400 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\OCDM6JB6\mb3-setup-consumer-3.6.1.2711-1.0.508-1.0.8211[1].exe | — | |
MD5:— | SHA256:— | |||
| 3000 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\0UU90R59\mb3-setup-consumer-3.6.1.2711-1.0.508-1.0.8211[1].exe | — | |
MD5:— | SHA256:— | |||
| 3000 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DFA0F754E79B2ECF93.TMP | — | |
MD5:— | SHA256:— | |||
| 3000 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\RecoveryStore.{85337F23-144E-11E9-91D7-5254004A04AF}.dat | — | |
MD5:— | SHA256:— | |||
| 2892 | mb3-setup-consumer-3.6.1.2711-1.0.508-1.0.8211[1].tmp | C:\Users\admin\AppData\Local\Temp\is-TIBAM.tmp\mb-header100.bmp | — | |
MD5:— | SHA256:— | |||
| 2892 | mb3-setup-consumer-3.6.1.2711-1.0.508-1.0.8211[1].tmp | C:\Users\admin\AppData\Local\Temp\is-TIBAM.tmp\mb-personal-image100.bmp | — | |
MD5:— | SHA256:— | |||
| 2892 | mb3-setup-consumer-3.6.1.2711-1.0.508-1.0.8211[1].tmp | C:\Users\admin\AppData\Local\Temp\is-TIBAM.tmp\mb-work-image100.bmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
2
DNS requests
2
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3000 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3000 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3400 | iexplore.exe | 23.54.113.43:443 | data-cdn.mbamupdates.com | Akamai International B.V. | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
data-cdn.mbamupdates.com |
| whitelisted |
www.bing.com |
| whitelisted |
Threats
Process | Message |
|---|---|
mbamtray.exe | QAxBase::setControl: requested control {F36AD0D0-B5F0-4C69-AF08-603D177FEF0E} could not be instantiated
|
mbamtray.exe | QAxBase: Error calling IDispatch member GetLastActiveScanner: Exception thrown by server
|
mbamtray.exe | Code : -2147467259
|
mbamtray.exe | Source :
|
mbamtray.exe | Description:
|
mbamtray.exe | Help :
|
mbamtray.exe | Connect to the exception(int,QString,QString,QString) signal to catch this exception
|
mbamtray.exe | void __thiscall PageStatusMonitor::OnRequestFinished(class QNetworkReply *) "Page: https://links.malwarebytes.com/link/3x_cart?affiliate=&uuid=&x-source=h_15million&x-action=comparison_chart&x-prodcode=MBAM-C&lang=en received code: 307"
|
mbamtray.exe | class QUrl __thiscall PageStatusMonitor::processRedirectUrl(const class QUrl &,const class QUrl &) const Potential Redirect is: "https://cleo.mb-internal.com/?x-source=h_15million&ADDITIONAL_x-source=inproduct&x-action=comparison_chart&x-prodcode=MBAM-C" Last Redirect is: ""
|
mbamtray.exe | void __thiscall PageStatusMonitor::OnRequestFinished(class QNetworkReply *) " Attempting redirect to: https://cleo.mb-internal.com/?x-source=h_15million&ADDITIONAL_x-source=inproduct&x-action=comparison_chart&x-prodcode=MBAM-C"
|