| File name: | ntoskrnl.exe |
| Full analysis: | https://app.any.run/tasks/9d6edad3-ebcd-400e-866e-f73b79ade43c |
| Verdict: | Malicious activity |
| Threats: | AsyncRAT is a RAT that can monitor and remotely control infected systems. This malware was introduced on Github as a legitimate open-source remote administration software, but hackers use it for its many powerful malicious functions. |
| Analysis date: | April 21, 2025, 17:52:58 |
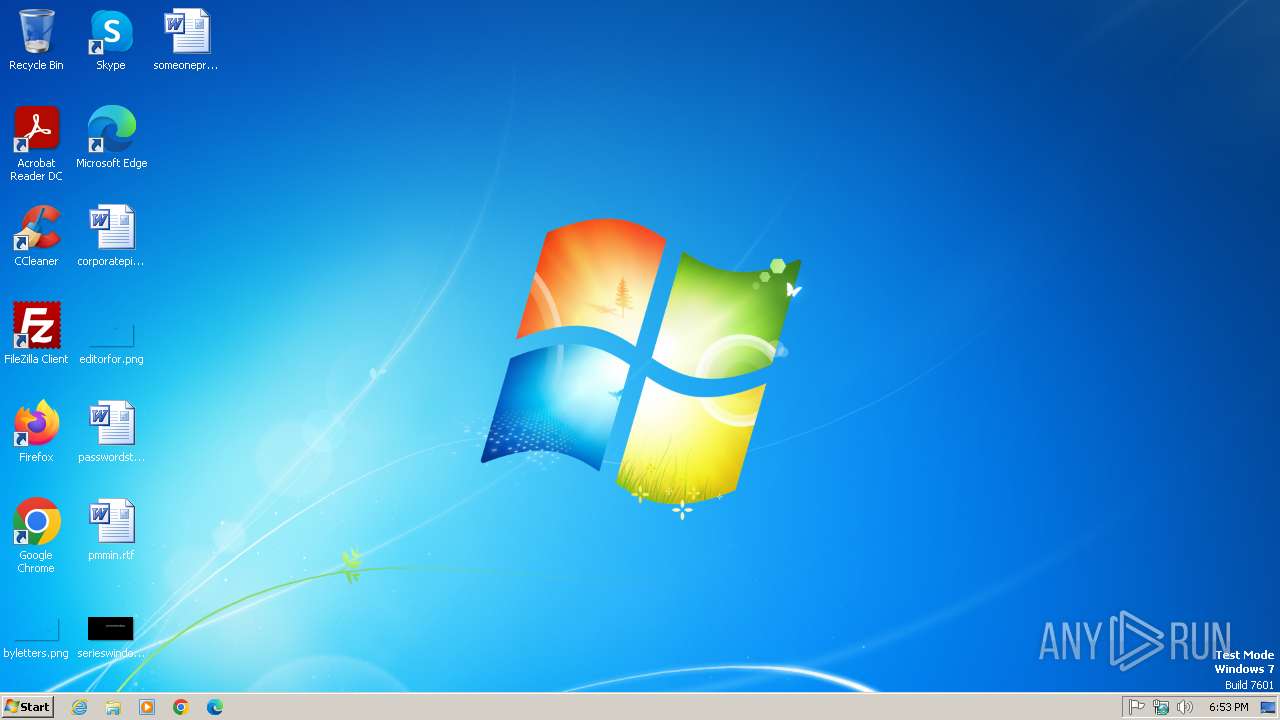
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows, 3 sections |
| MD5: | 5618B6BA6E74AC356D403022B24ABDEA |
| SHA1: | D385CF7A0A8FEBE06F9ADFCDD4BF22EBD50C7348 |
| SHA256: | 7BCB6827F59FE8C33BF687901C2C2C7486D2E8C570ECE4A88F1AB4CDDB2C5165 |
| SSDEEP: | 1536:ybWwowH89DsJkRaKpcD15b/iJKvvgsmww:ybWwowH89DsicD15b/DZw |
MALICIOUS
Changes the autorun value in the registry
- ntoskrnl.exe (PID: 2060)
ASYNCRAT has been detected (YARA)
- ntoskrnl.exe (PID: 2360)
SUSPICIOUS
Process drops legitimate windows executable
- ntoskrnl.exe (PID: 2060)
Starts a Microsoft application from unusual location
- ntoskrnl.exe (PID: 2060)
Executable content was dropped or overwritten
- ntoskrnl.exe (PID: 2060)
Uses TIMEOUT.EXE to delay execution
- cmd.exe (PID: 2692)
Executing commands from a ".bat" file
- ntoskrnl.exe (PID: 2060)
The executable file from the user directory is run by the CMD process
- ntoskrnl.exe (PID: 2360)
Starts CMD.EXE for commands execution
- ntoskrnl.exe (PID: 2060)
Connects to unusual port
- ntoskrnl.exe (PID: 2360)
INFO
Reads the computer name
- ntoskrnl.exe (PID: 2060)
- ntoskrnl.exe (PID: 2360)
Checks supported languages
- ntoskrnl.exe (PID: 2060)
- ntoskrnl.exe (PID: 2360)
Reads the machine GUID from the registry
- ntoskrnl.exe (PID: 2060)
- ntoskrnl.exe (PID: 2360)
Create files in a temporary directory
- ntoskrnl.exe (PID: 2060)
Creates files or folders in the user directory
- ntoskrnl.exe (PID: 2060)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
AsyncRat
(PID) Process(2360) ntoskrnl.exe
C2 (1)0.tcp.ngrok.io
Ports (1)14530
Version0.5.8
BotnetDefault
Options
AutoRuntrue
Mutexh0kJRa5OShSV
InstallFolder%AppData%
BSoDtrue
AntiVMfalse
Certificates
Cert1MIIE8jCCAtqgAwIBAgIQAIHcyTEvA3IWzzXtjL1ZITANBgkqhkiG9w0BAQ0FADAaMRgwFgYDVQQDDA9Bc3luY1JBVCBTZXJ2ZXIwIBcNMjUwNDE5MTczNTUzWhgPOTk5OTEyMzEyMzU5NTlaMBoxGDAWBgNVBAMMD0FzeW5jUkFUIFNlcnZlcjCCAiIwDQYJKoZIhvcNAQEBBQADggIPADCCAgoCggIBAKYX1eNqln8zSK0PB2rbgtUR8EPgzv7kqvgKPaNGNvAIWCDLZSZcuZgB4oPq3Byc38EuAVspw0AZ...
Server_SignatureCzcBNJbNLpByMzMxTmigxzzUnmx3jm6rby5Dk5VNCzFeCGItfBrU6yMJ/8m+NOUyIPce0zsd12luCmdXxBfpufm0bpJ/bVVhgLVmUSj5qHpadcS8+GhOHm3XtiBLe+2qsgTuovc0ZDUjUTWabRs2J6qf7kgbEnJ2oaHf+eqsyx0HbyNbs1hPzPbgyda+grLttDRG3fkVkwM8nxB1Ye7Had3Rc/5zMOFTJZPz6SwiwsTHr84UCgAG7nIuLBv6wsTm2CO7sjn1XxckNzl/sd6QxJaVR5I5iiBy9wMgh+X39Egv...
Keys
AESc505d14b05966609cc777ded8a26e16238b786bb2f6e56900e72bc7a30c973e7
Saltbfeb1e56fbcd973bb219022430a57843003d5644d21e62b9d4f180e7e6c33941
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (82.9) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (7.4) |
| .exe | | | Win32 Executable (generic) (5.1) |
| .exe | | | Generic Win/DOS Executable (2.2) |
| .exe | | | DOS Executable Generic (2.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2023:10:16 21:40:53+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 8 |
| CodeSize: | 45568 |
| InitializedDataSize: | 3072 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xd03e |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 6.2.26100.3775 |
| ProductVersionNumber: | 6.2.26100.3775 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | - |
| CompanyName: | Microsoft Corporation |
| FileDescription: | NT Kernel & System |
| FileVersion: | 6.2.26100.3775 |
| InternalName: | ntkrnlmp.exe |
| LegalCopyright: | © Microsoft Corporation. All rights reserved. |
| LegalTrademarks: | - |
| OriginalFileName: | ntkrnlmp.exe |
| ProductName: | Microsoft® Windows® Operating System |
| ProductVersion: | 6.2.26100.3775 |
| AssemblyVersion: | 6.2.26100.3775 |
Total processes
37
Monitored processes
4
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2060 | "C:\Users\admin\AppData\Local\Temp\ntoskrnl.exe" | C:\Users\admin\AppData\Local\Temp\ntoskrnl.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: NT Kernel & System Exit code: 0 Version: 6.2.26100.3775 Modules
| |||||||||||||||
| 2360 | "C:\Users\admin\AppData\Roaming\ntoskrnl.exe" | C:\Users\admin\AppData\Roaming\ntoskrnl.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: NT Kernel & System Version: 6.2.26100.3775 Modules
AsyncRat(PID) Process(2360) ntoskrnl.exe C2 (1)0.tcp.ngrok.io Ports (1)14530 Version0.5.8 BotnetDefault Options AutoRuntrue Mutexh0kJRa5OShSV InstallFolder%AppData% BSoDtrue AntiVMfalse Certificates Cert1MIIE8jCCAtqgAwIBAgIQAIHcyTEvA3IWzzXtjL1ZITANBgkqhkiG9w0BAQ0FADAaMRgwFgYDVQQDDA9Bc3luY1JBVCBTZXJ2ZXIwIBcNMjUwNDE5MTczNTUzWhgPOTk5OTEyMzEyMzU5NTlaMBoxGDAWBgNVBAMMD0FzeW5jUkFUIFNlcnZlcjCCAiIwDQYJKoZIhvcNAQEBBQADggIPADCCAgoCggIBAKYX1eNqln8zSK0PB2rbgtUR8EPgzv7kqvgKPaNGNvAIWCDLZSZcuZgB4oPq3Byc38EuAVspw0AZ... Server_SignatureCzcBNJbNLpByMzMxTmigxzzUnmx3jm6rby5Dk5VNCzFeCGItfBrU6yMJ/8m+NOUyIPce0zsd12luCmdXxBfpufm0bpJ/bVVhgLVmUSj5qHpadcS8+GhOHm3XtiBLe+2qsgTuovc0ZDUjUTWabRs2J6qf7kgbEnJ2oaHf+eqsyx0HbyNbs1hPzPbgyda+grLttDRG3fkVkwM8nxB1Ye7Had3Rc/5zMOFTJZPz6SwiwsTHr84UCgAG7nIuLBv6wsTm2CO7sjn1XxckNzl/sd6QxJaVR5I5iiBy9wMgh+X39Egv... Keys AESc505d14b05966609cc777ded8a26e16238b786bb2f6e56900e72bc7a30c973e7 Saltbfeb1e56fbcd973bb219022430a57843003d5644d21e62b9d4f180e7e6c33941 | |||||||||||||||
| 2364 | timeout 3 | C:\Windows\System32\timeout.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: timeout - pauses command processing Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2692 | C:\Windows\system32\cmd.exe /c ""C:\Users\admin\AppData\Local\Temp\tmp23EE.tmp.bat"" | C:\Windows\System32\cmd.exe | — | ntoskrnl.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
670
Read events
641
Write events
29
Delete events
0
Modification events
| (PID) Process: | (2060) ntoskrnl.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\182\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2060) ntoskrnl.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | ntoskrnl |
Value: "C:\Users\admin\AppData\Roaming\ntoskrnl.exe" | |||
| (PID) Process: | (2360) ntoskrnl.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\182\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
Executable files
1
Suspicious files
0
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2060 | ntoskrnl.exe | C:\Users\admin\AppData\Roaming\ntoskrnl.exe | executable | |
MD5:5618B6BA6E74AC356D403022B24ABDEA | SHA256:7BCB6827F59FE8C33BF687901C2C2C7486D2E8C570ECE4A88F1AB4CDDB2C5165 | |||
| 2060 | ntoskrnl.exe | C:\Users\admin\AppData\Local\Temp\tmp23EE.tmp.bat | text | |
MD5:A1CF3F56A706AA7D48BAD250B03EB5BA | SHA256:04CA67913277608E906356FCAFF7D4952F50818B6C849F6E3A570448632974F3 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
30
DNS requests
2
Threats
1
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2360 | ntoskrnl.exe | 18.190.63.84:14530 | 0.tcp.ngrok.io | AMAZON-02 | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
0.tcp.ngrok.io |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1080 | svchost.exe | Misc activity | ET INFO DNS Query to a *.ngrok domain (ngrok.io) |