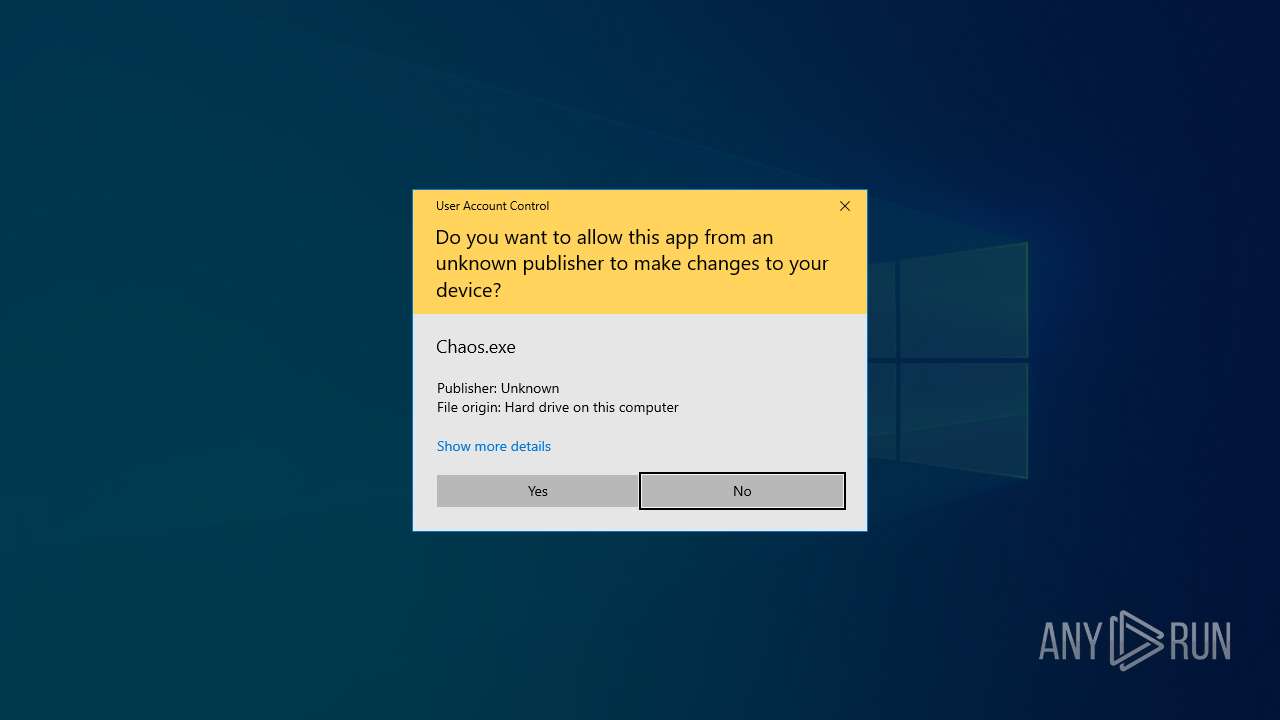
| File name: | Chaos.exe |
| Full analysis: | https://app.any.run/tasks/32645268-cf44-4a28-9912-6f7499755799 |
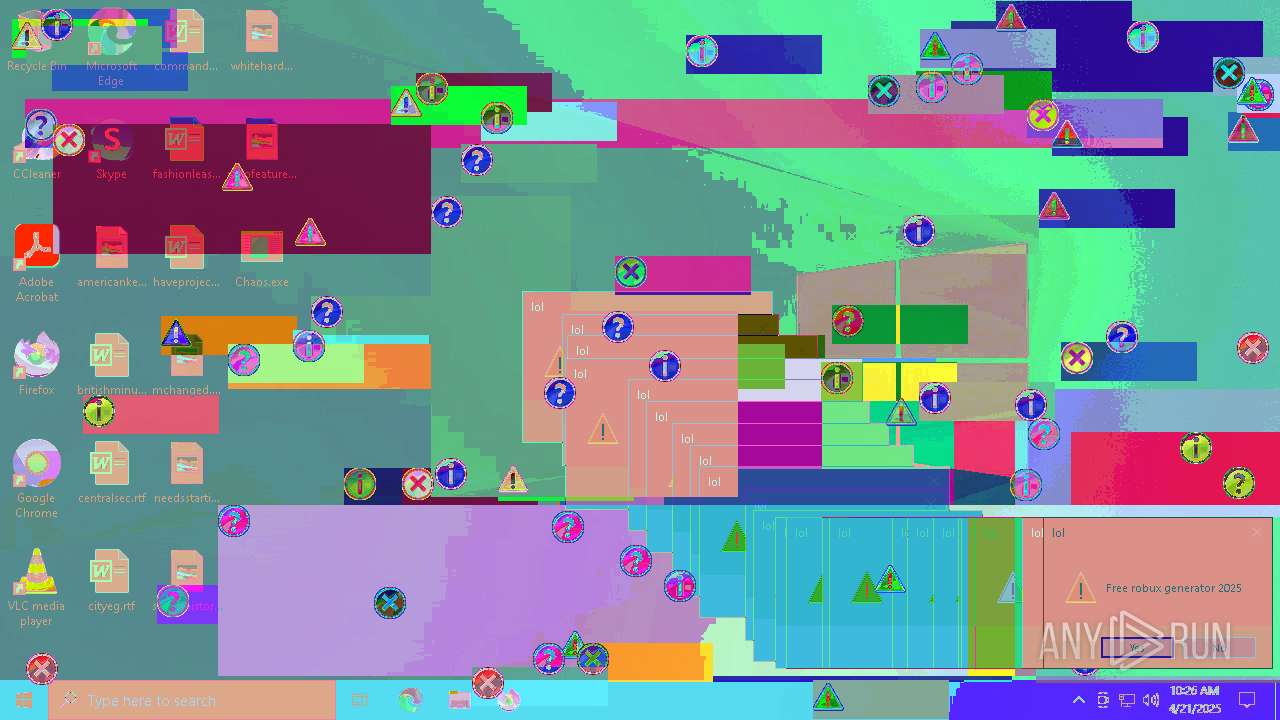
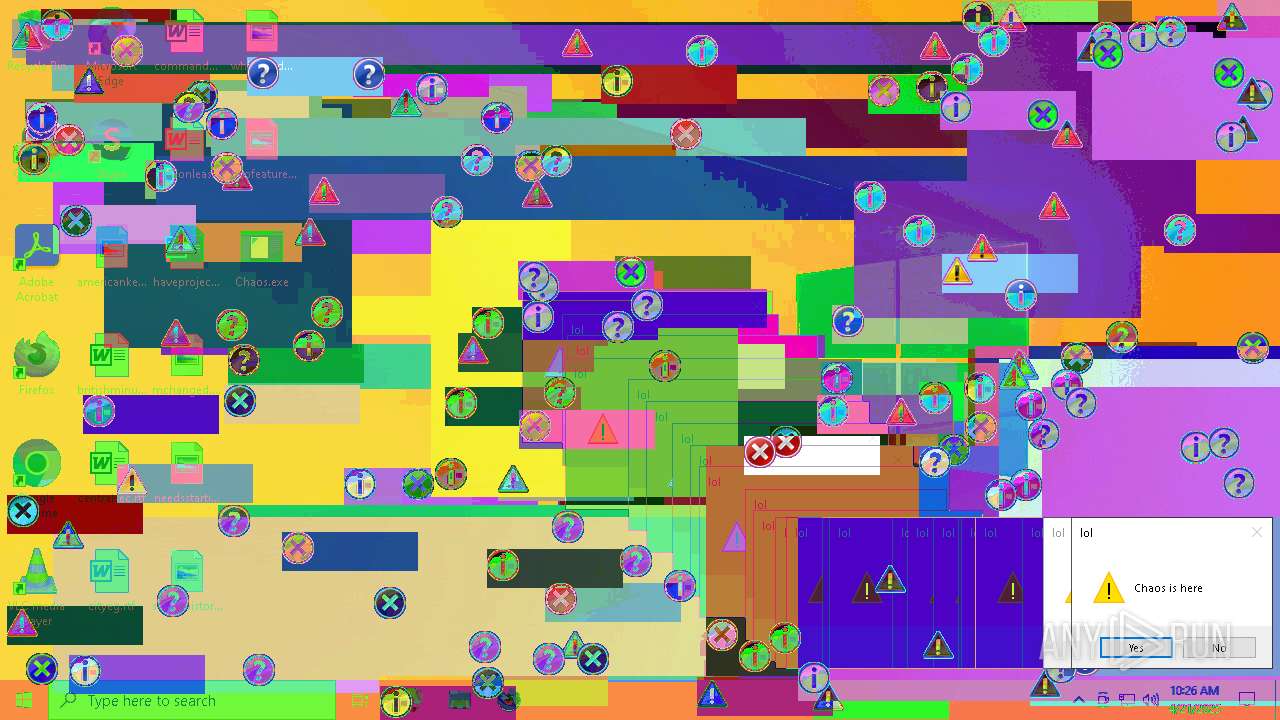
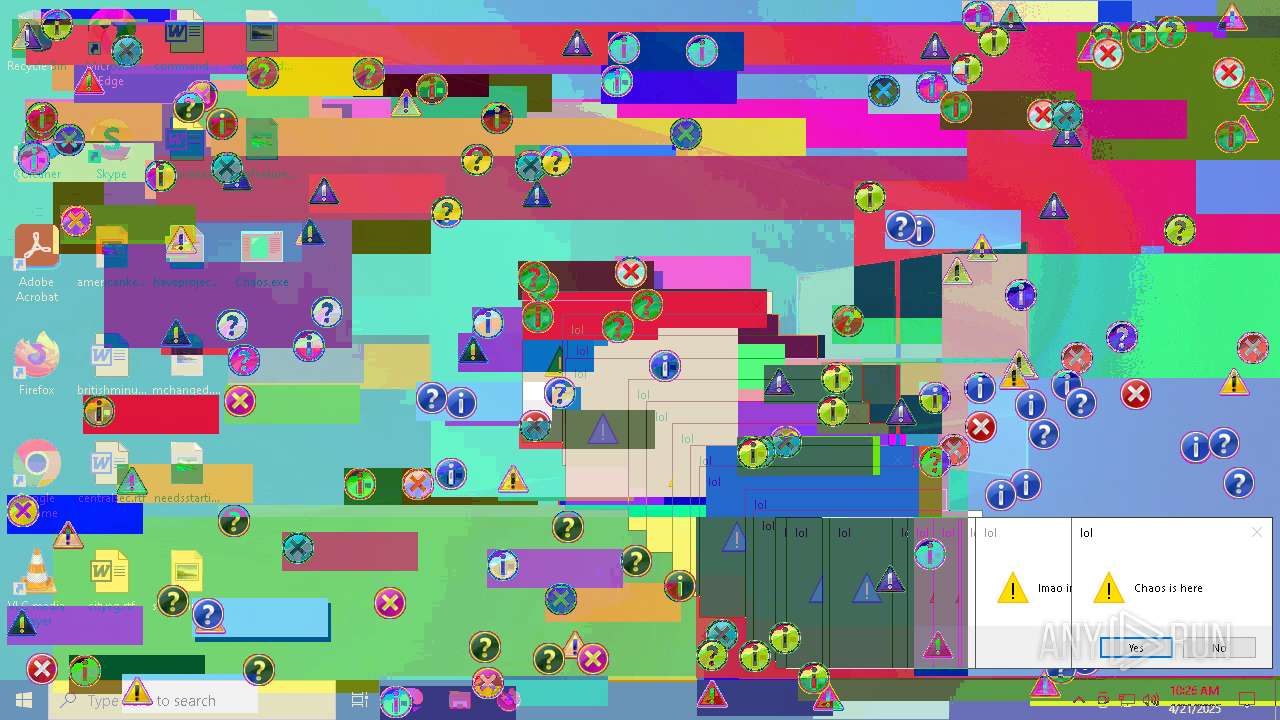
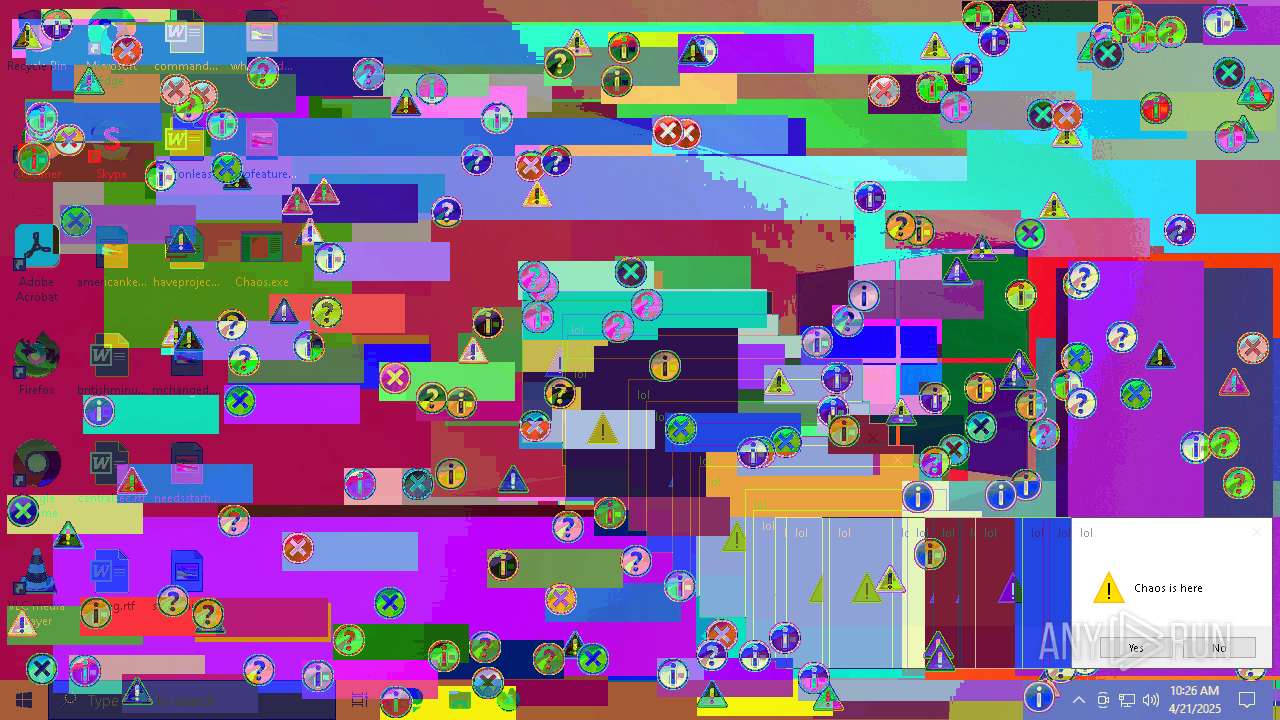
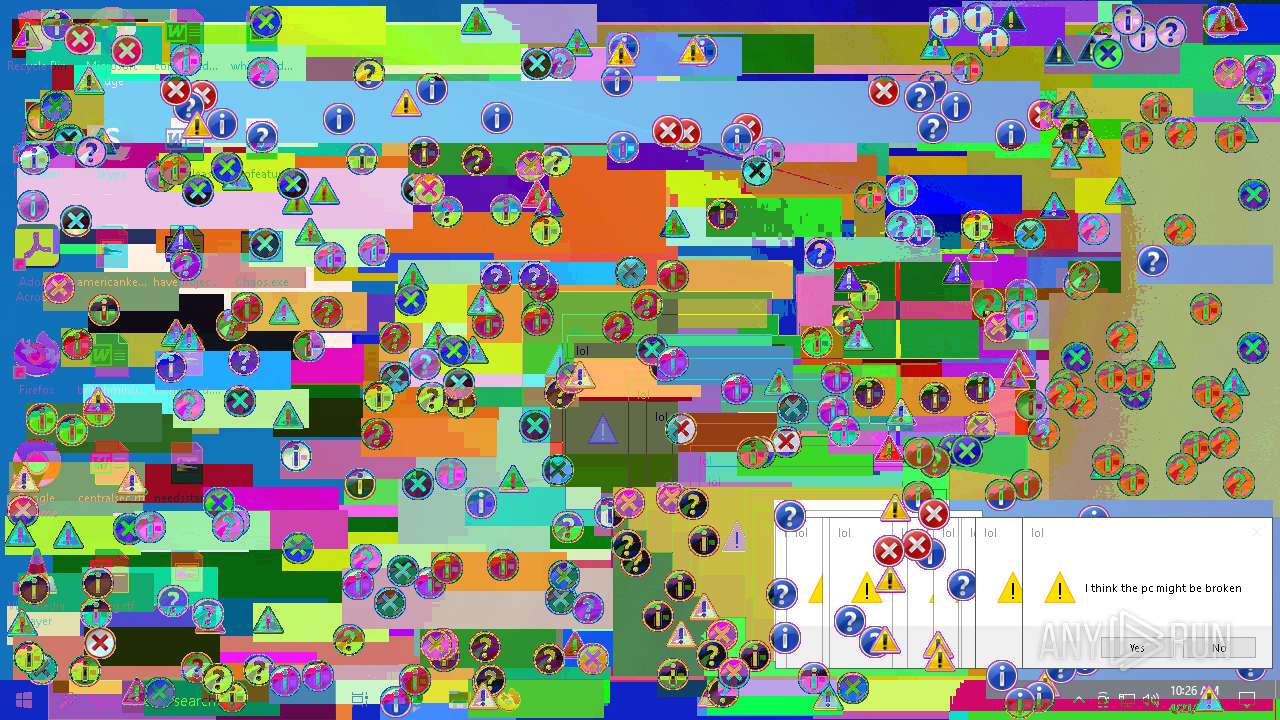
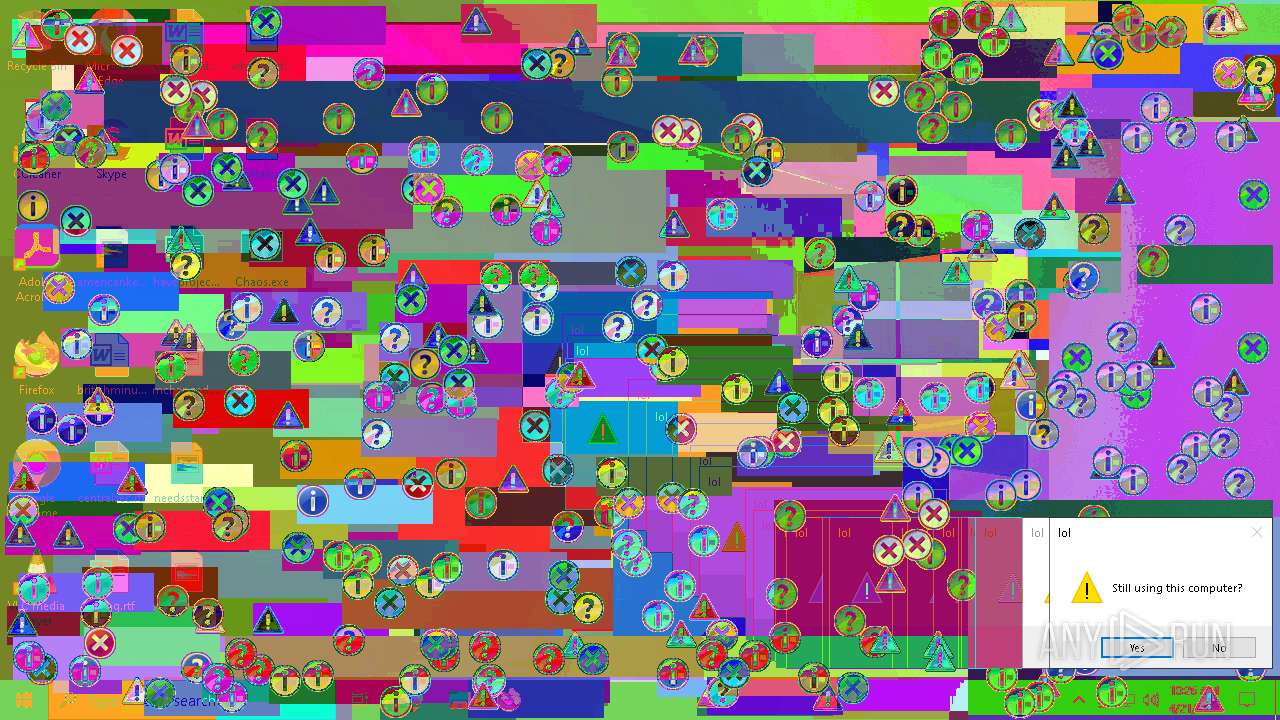
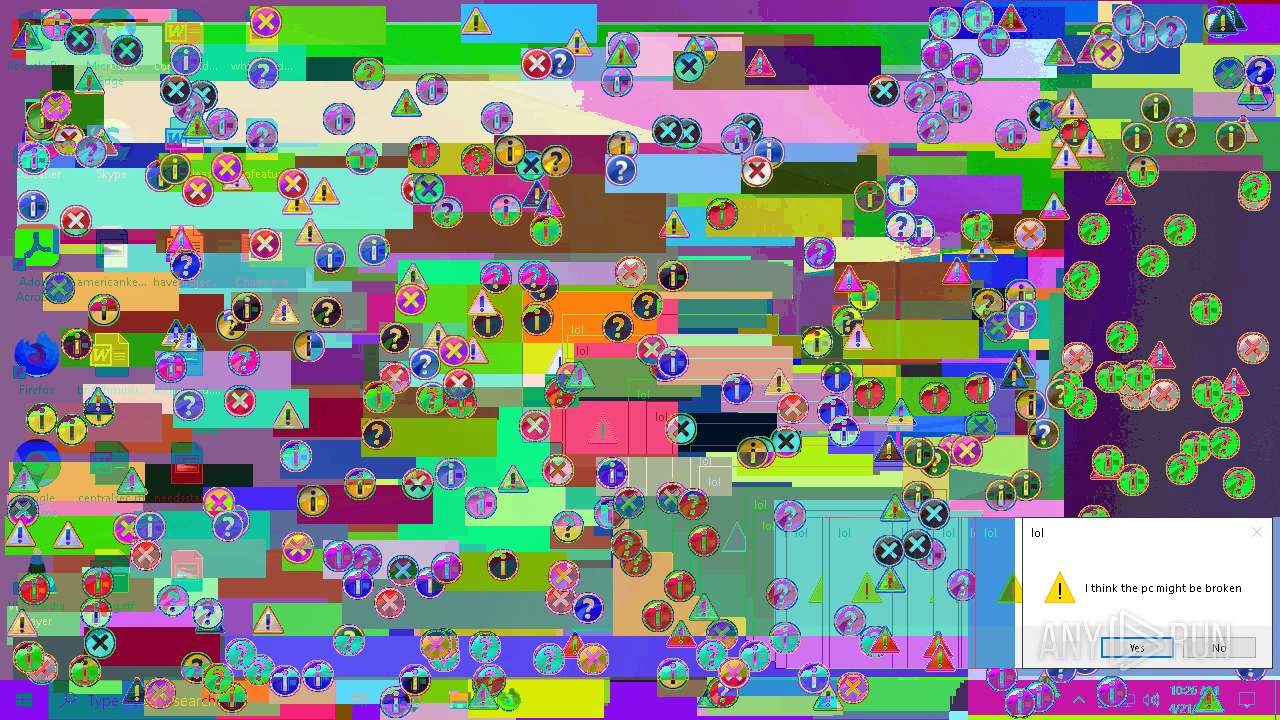
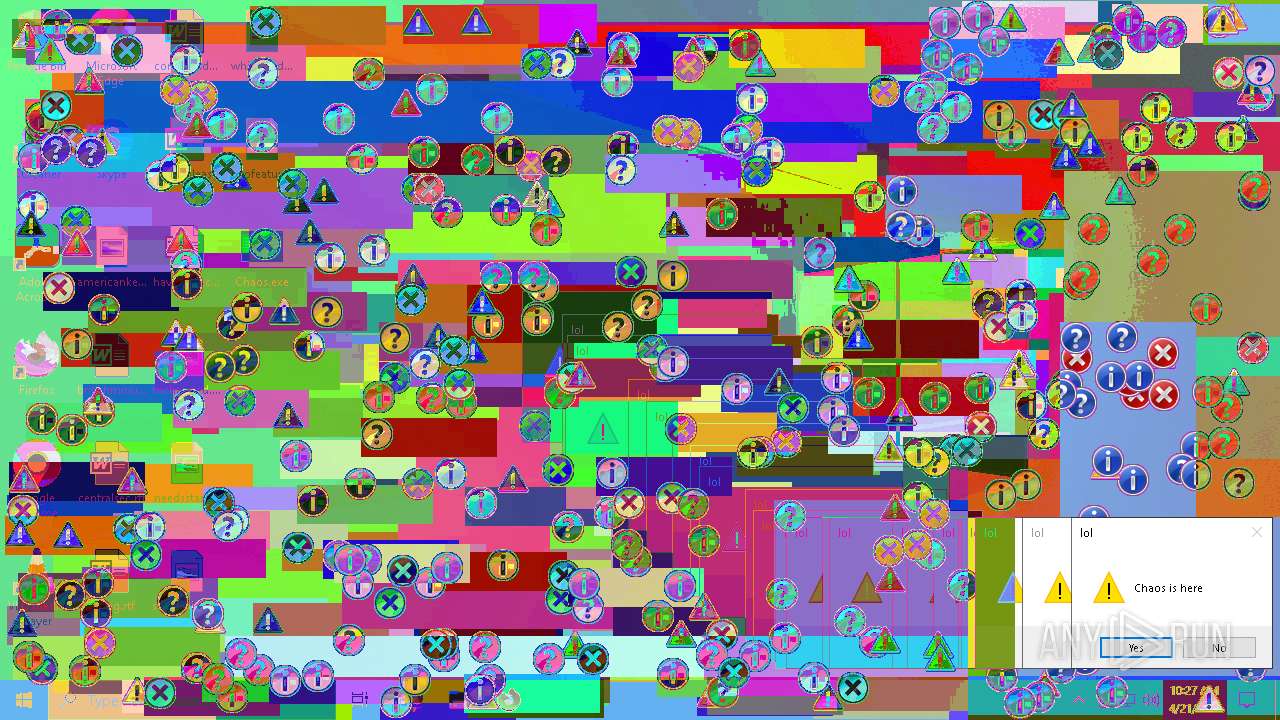
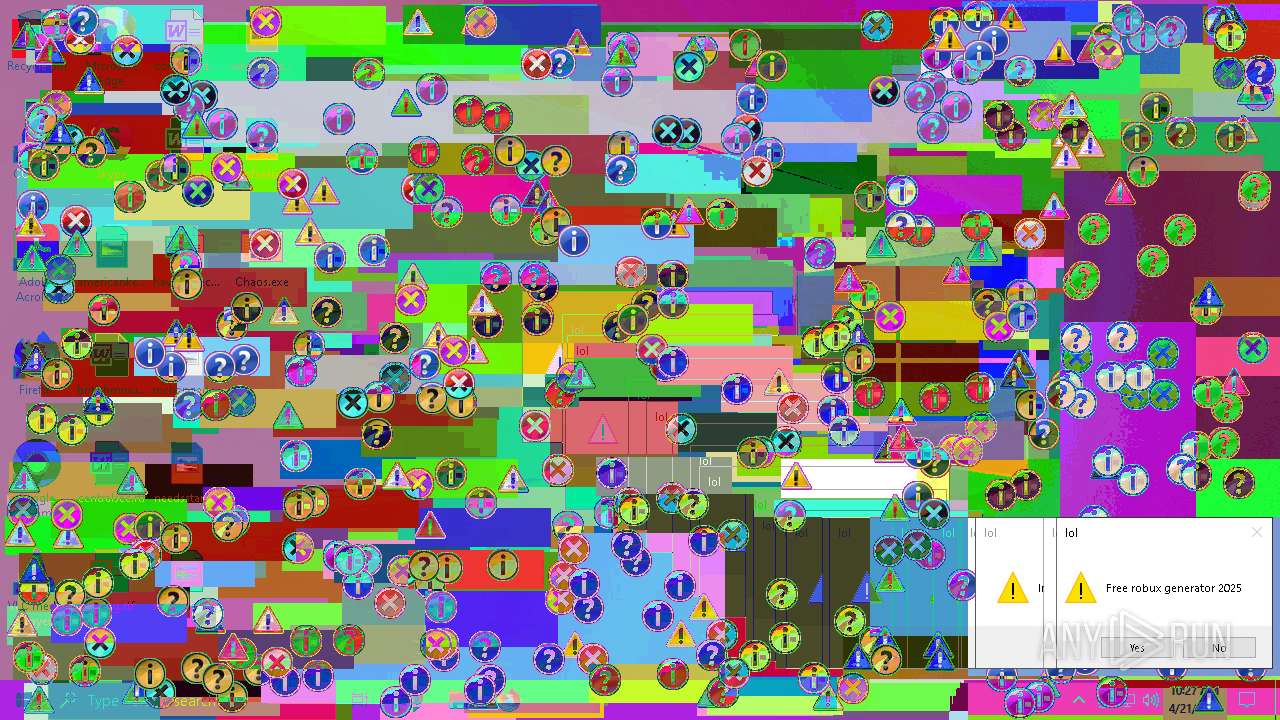
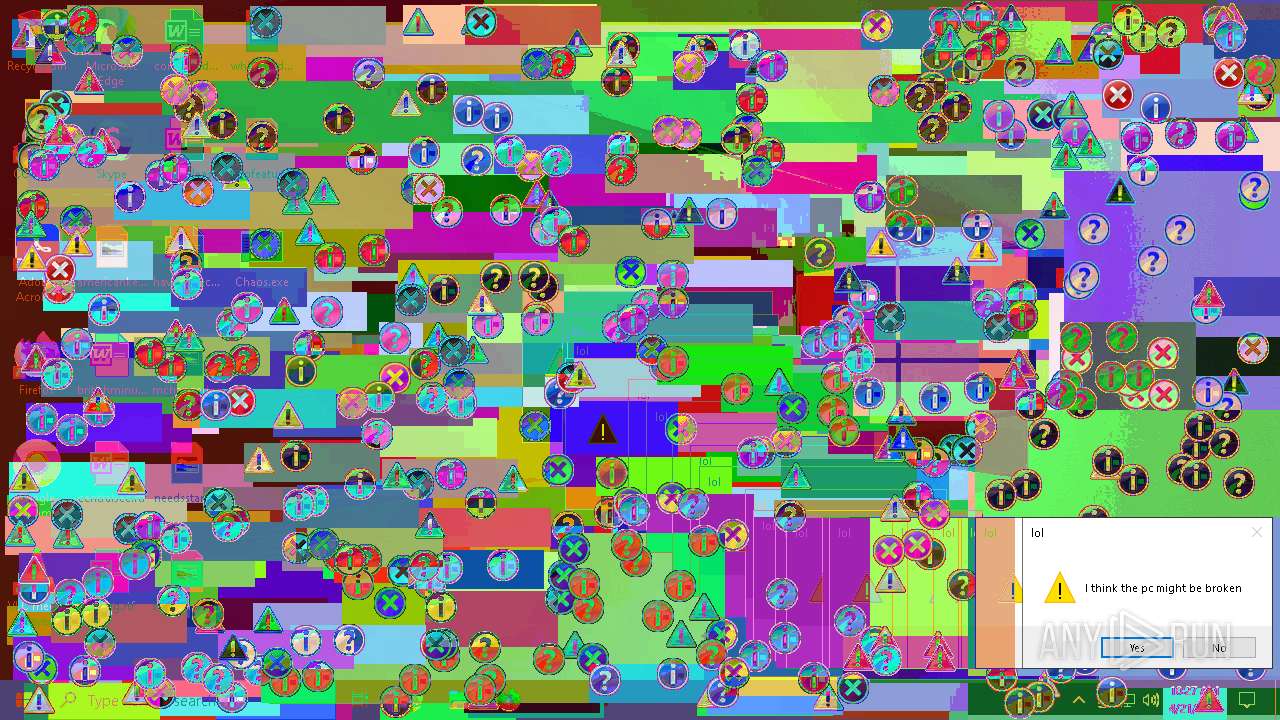
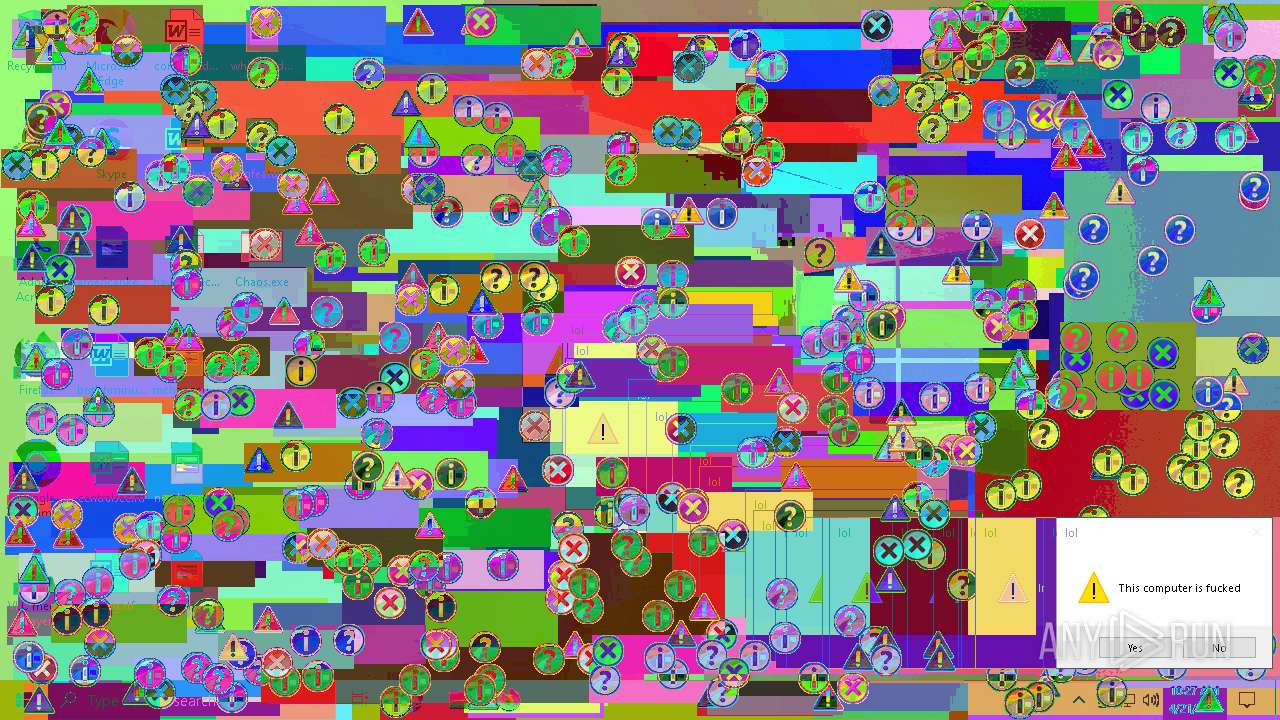
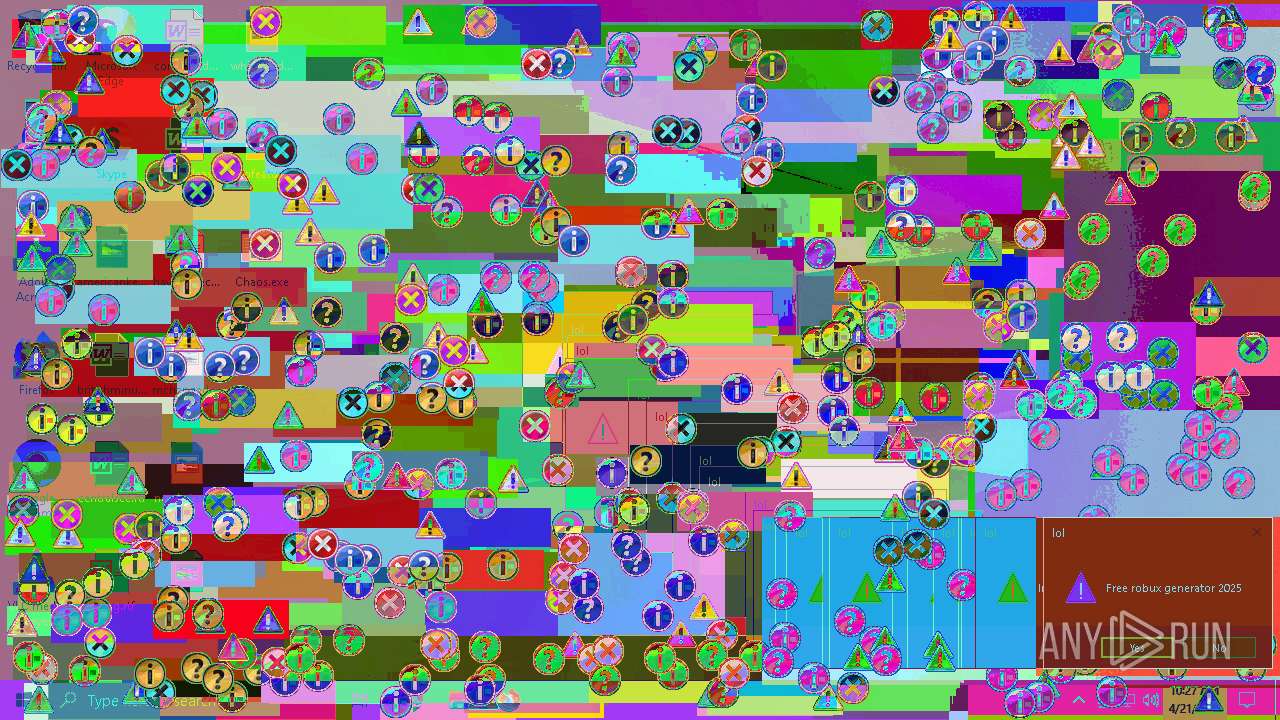
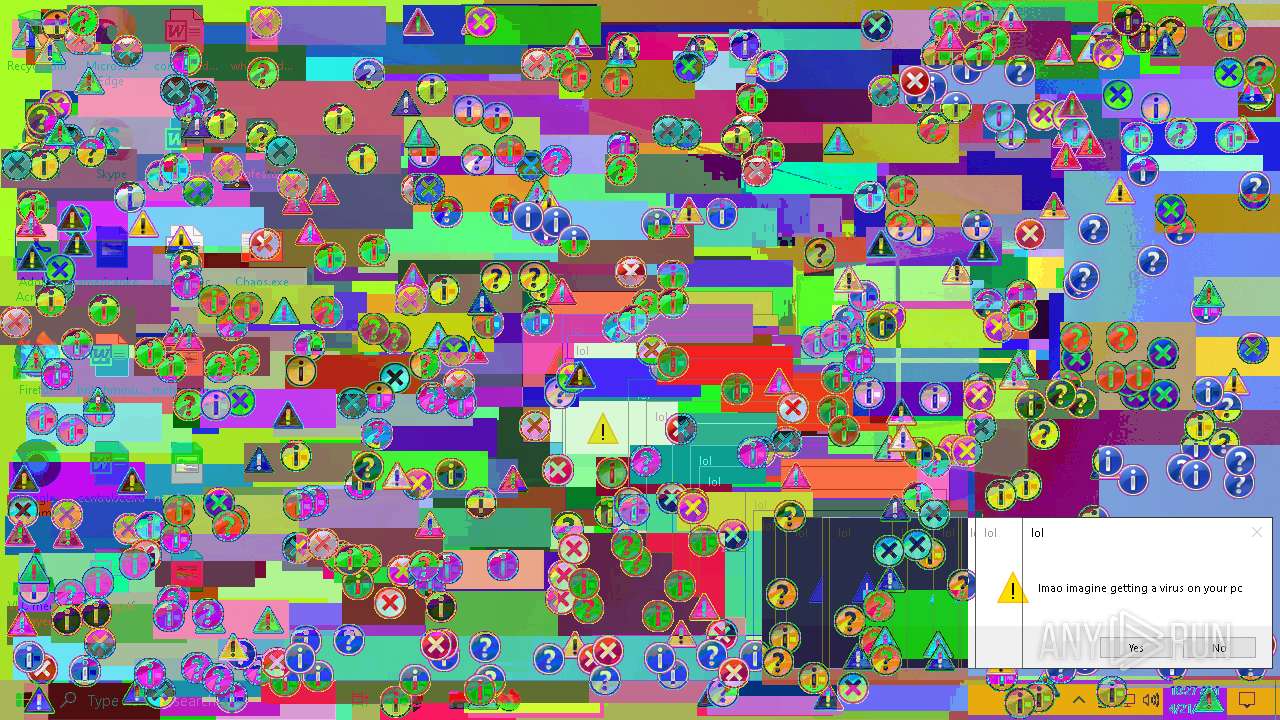
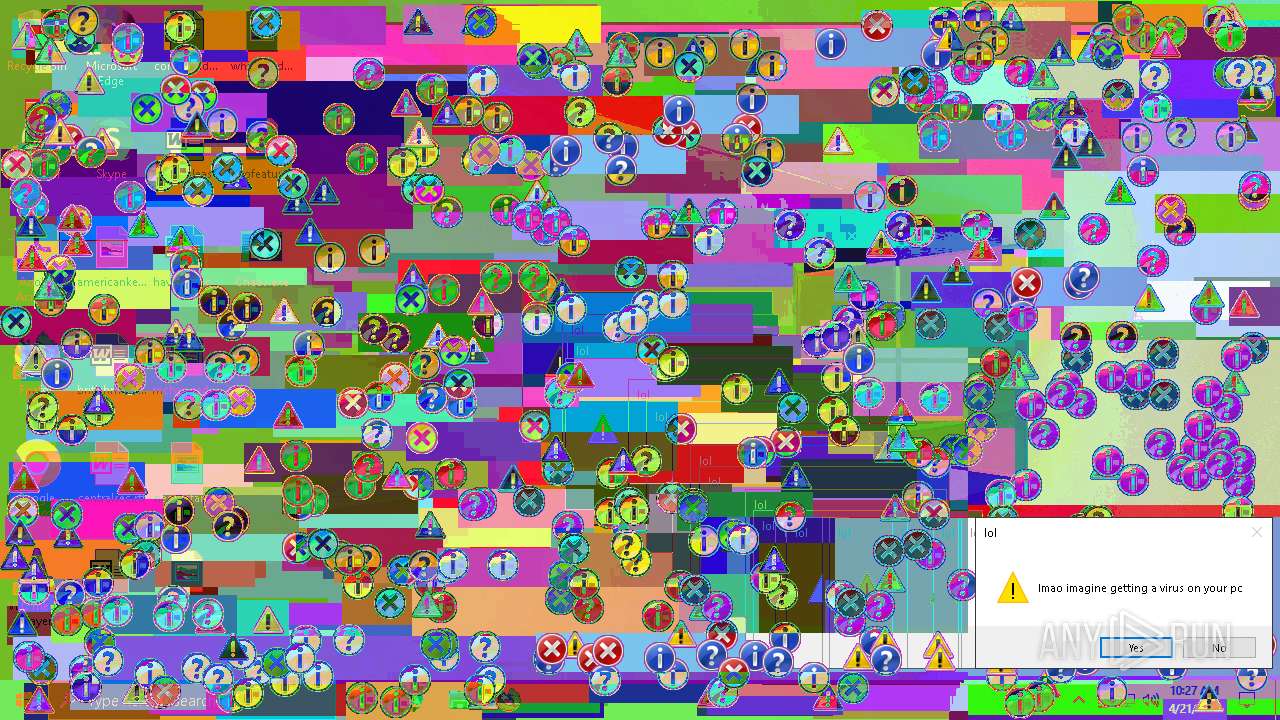
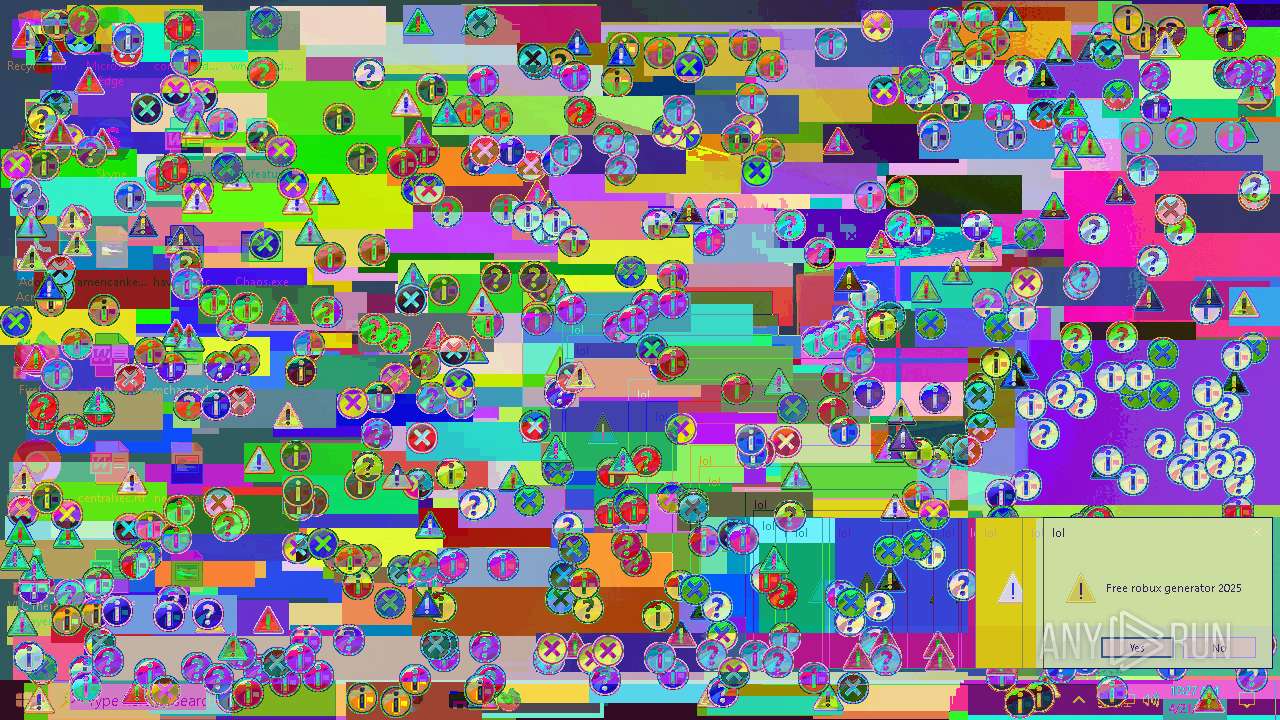
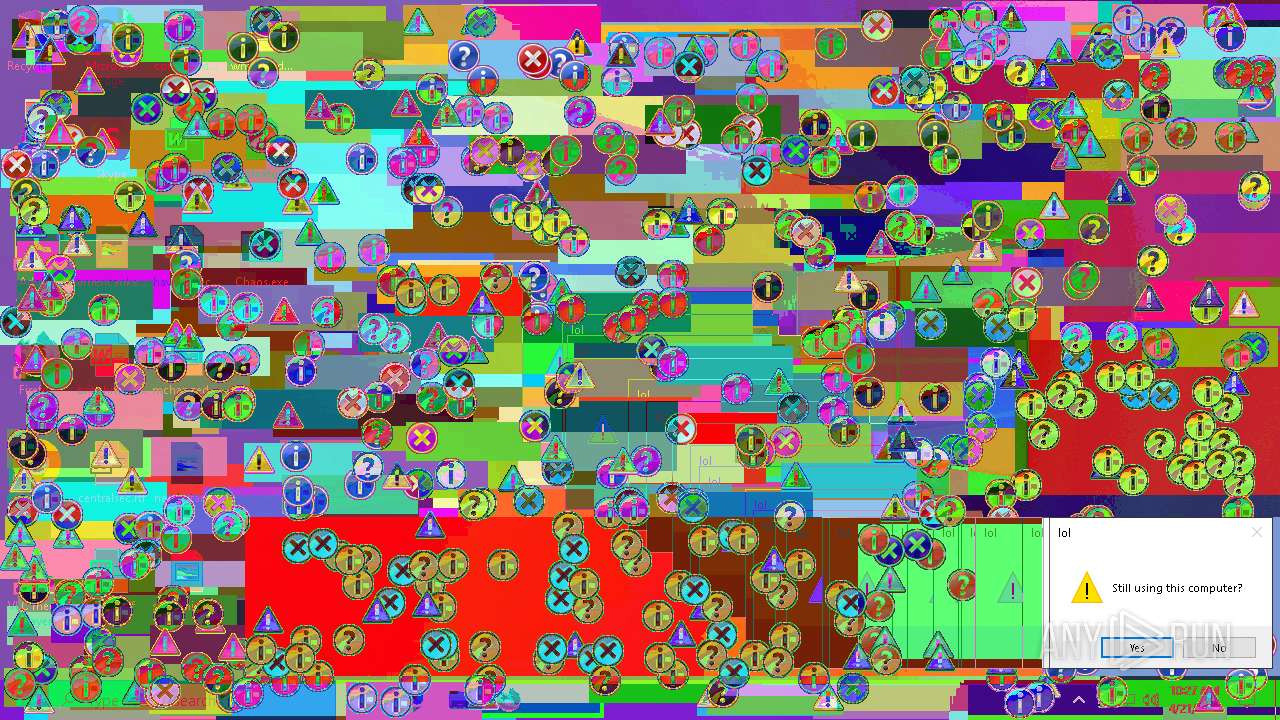
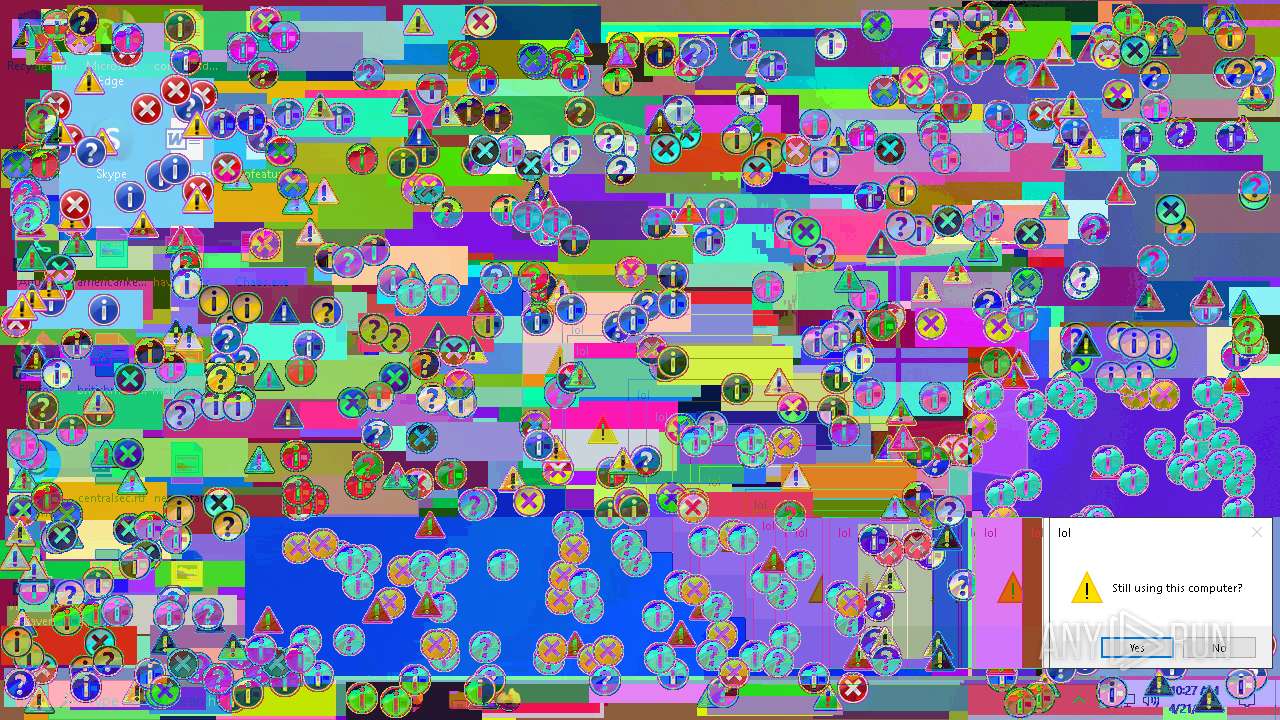
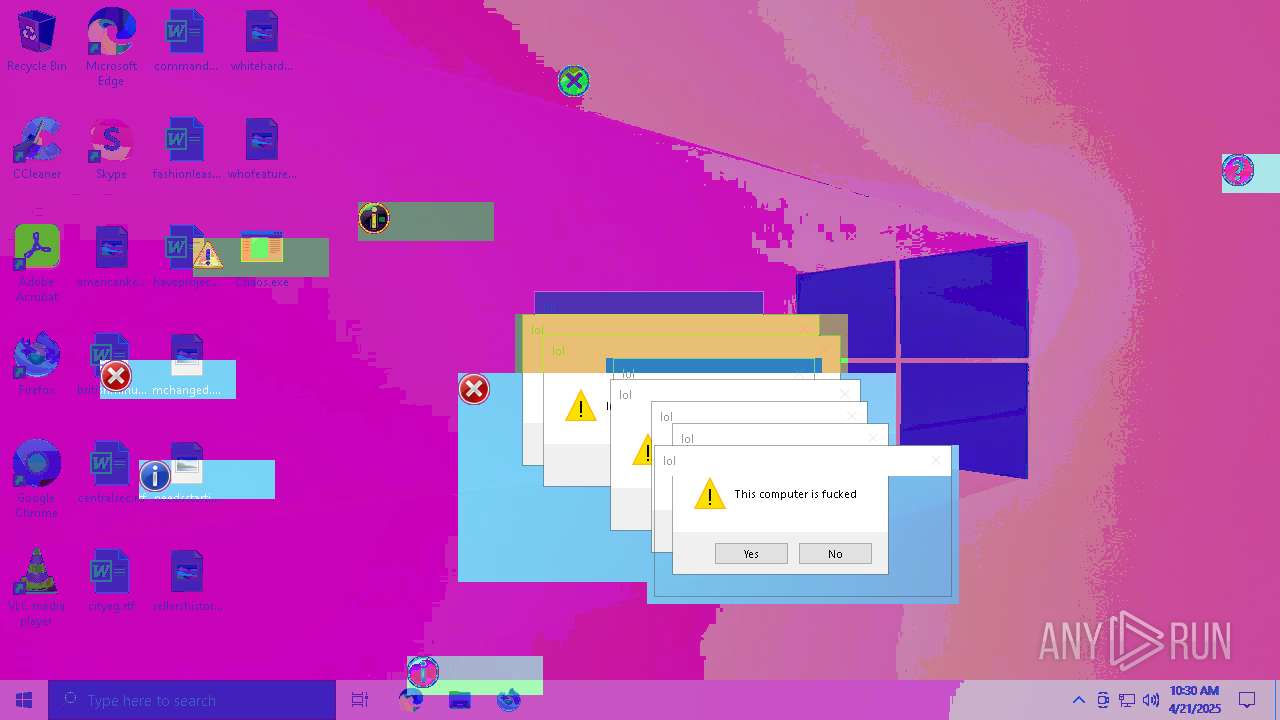
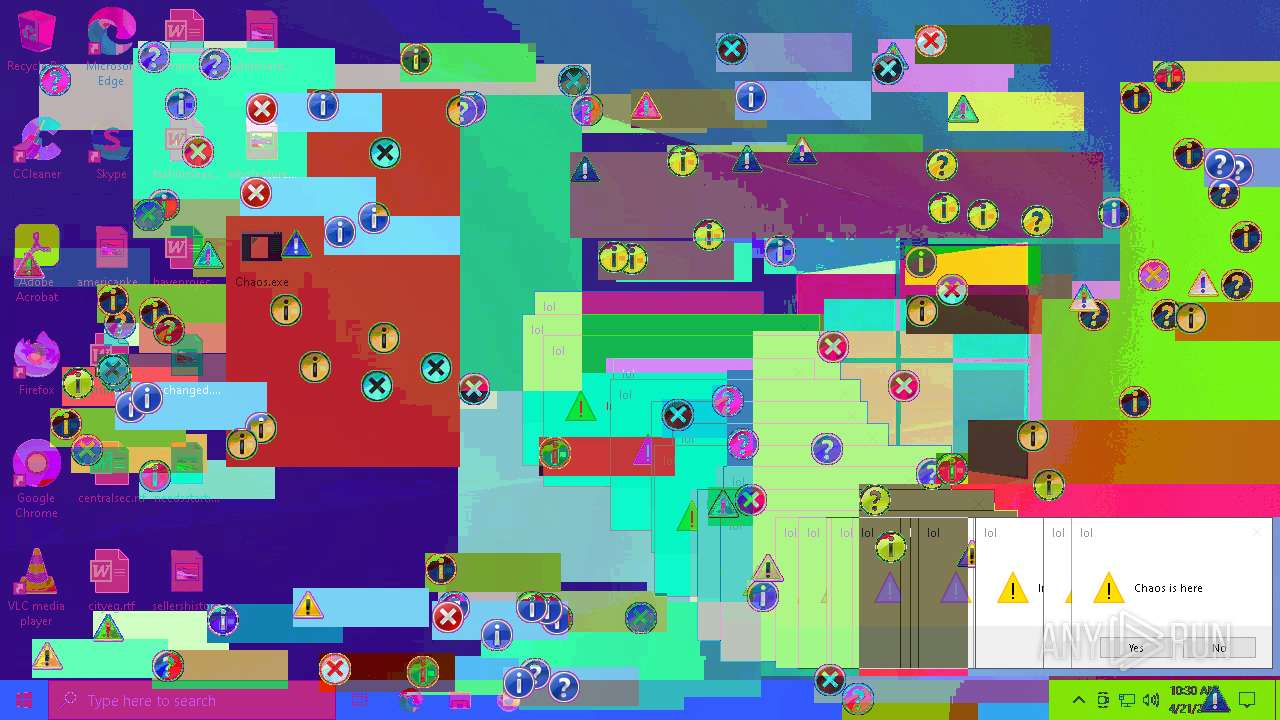
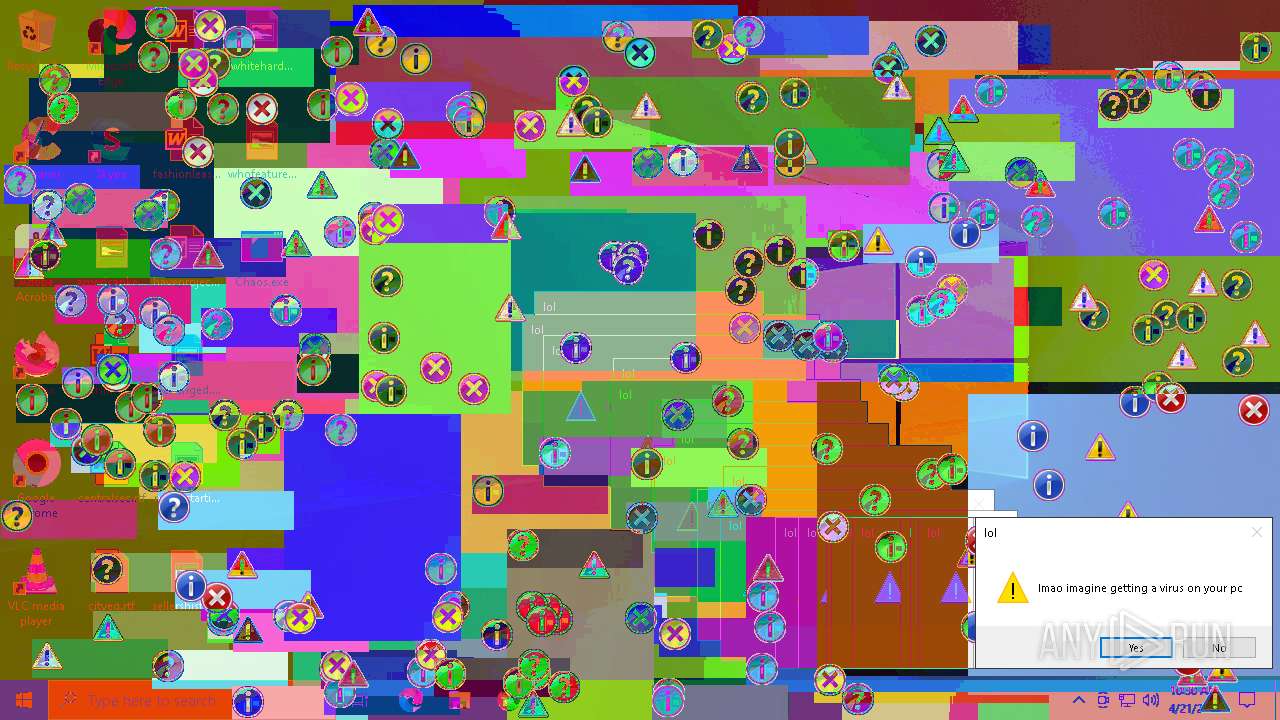
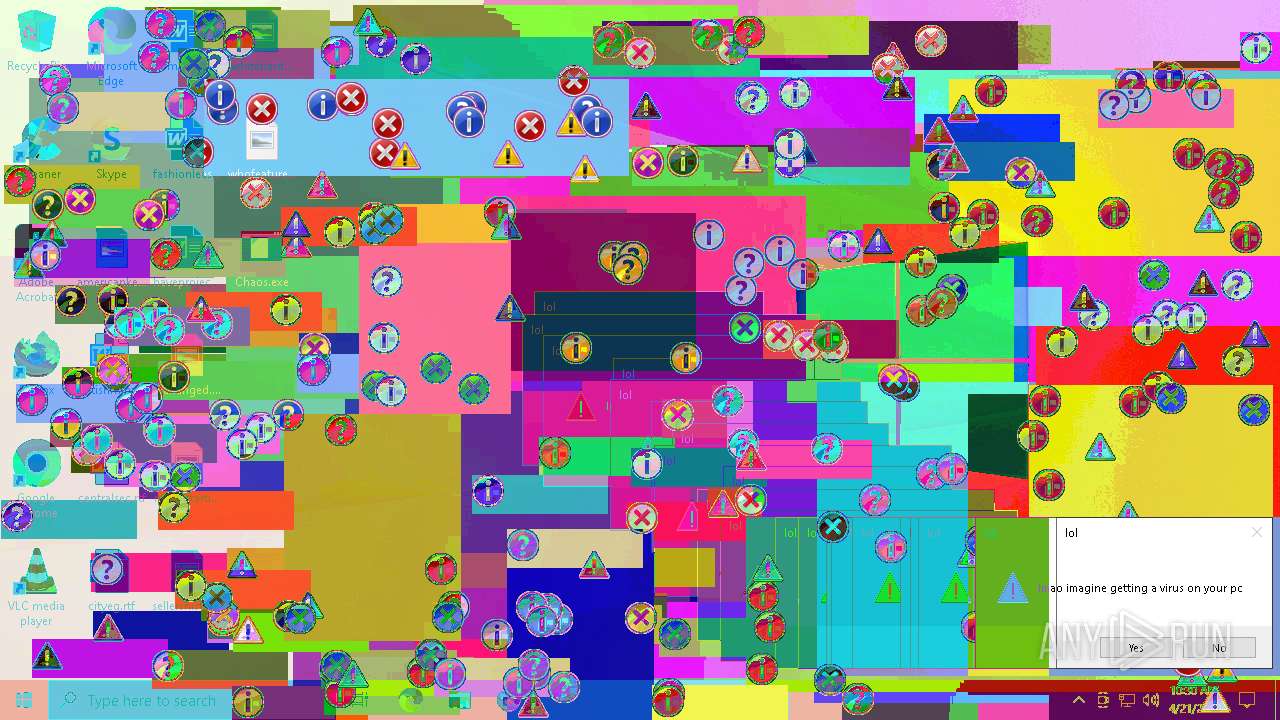
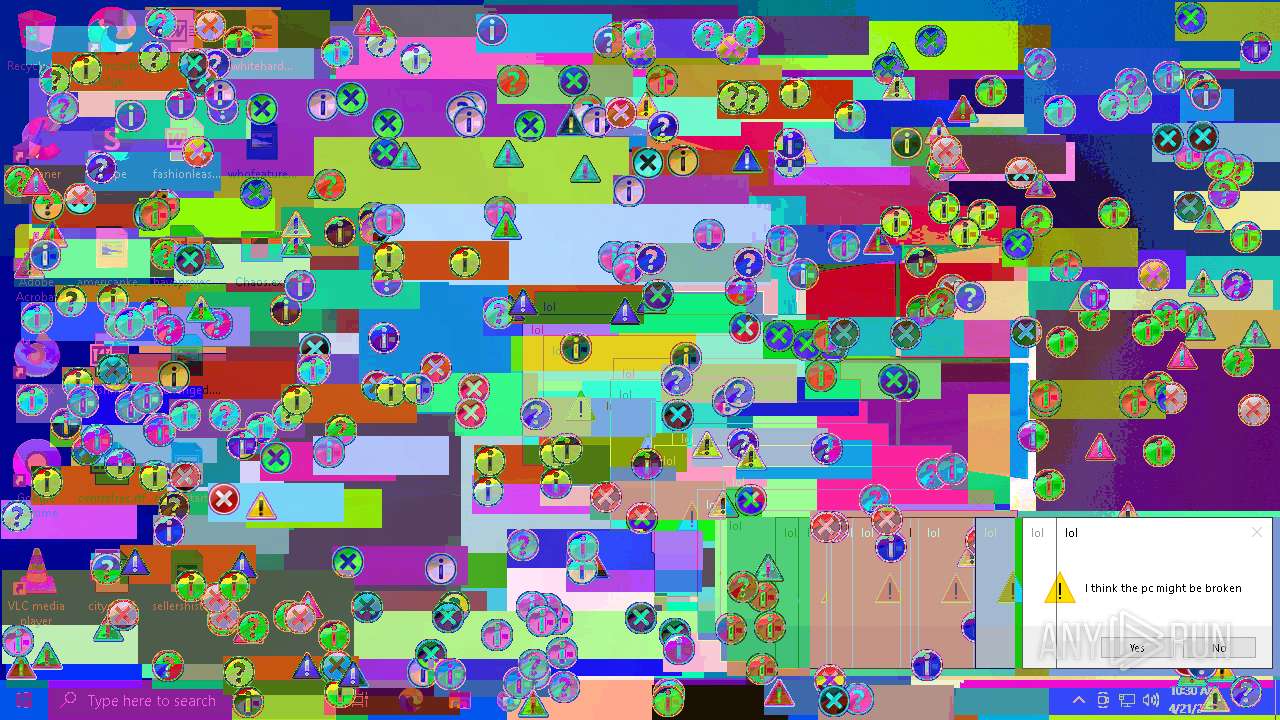
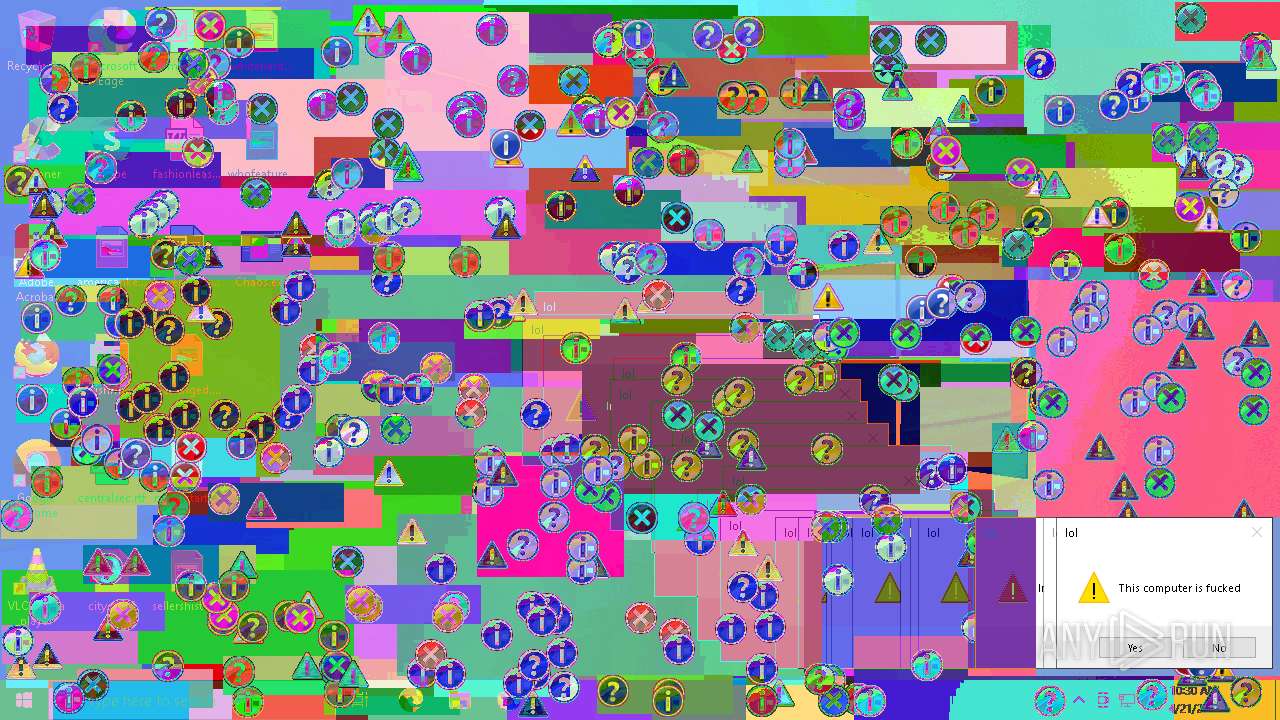
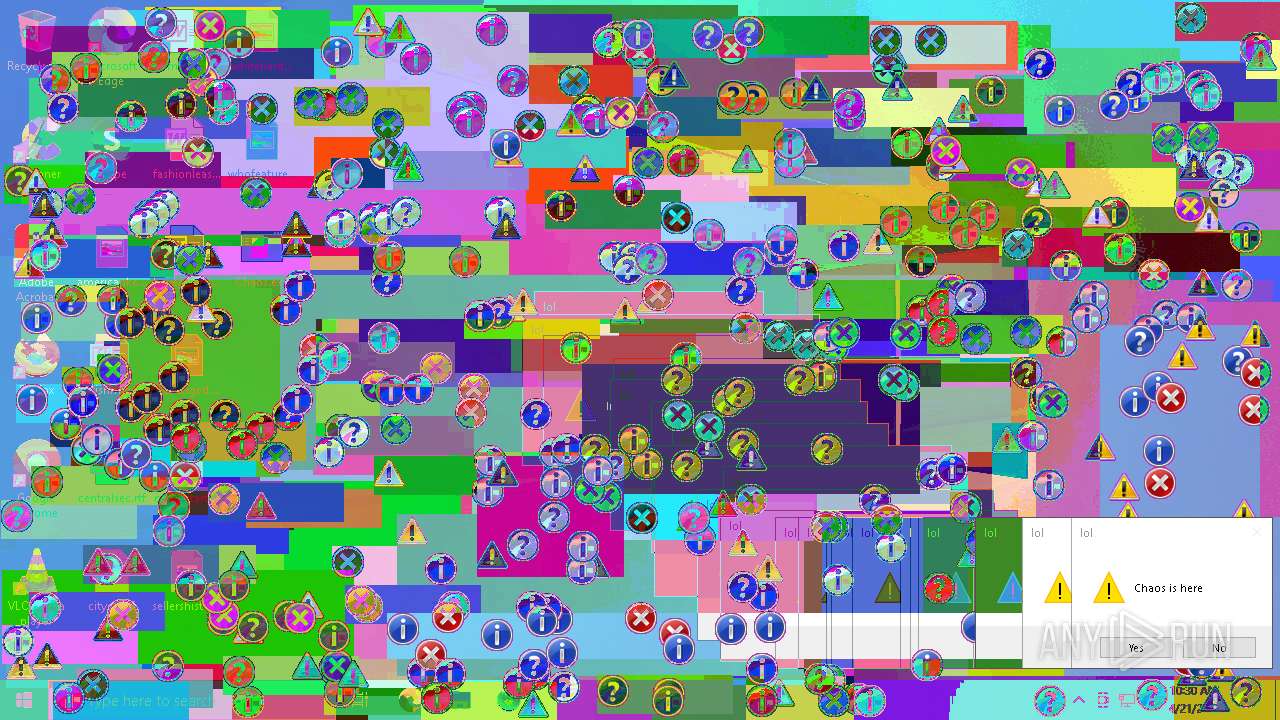
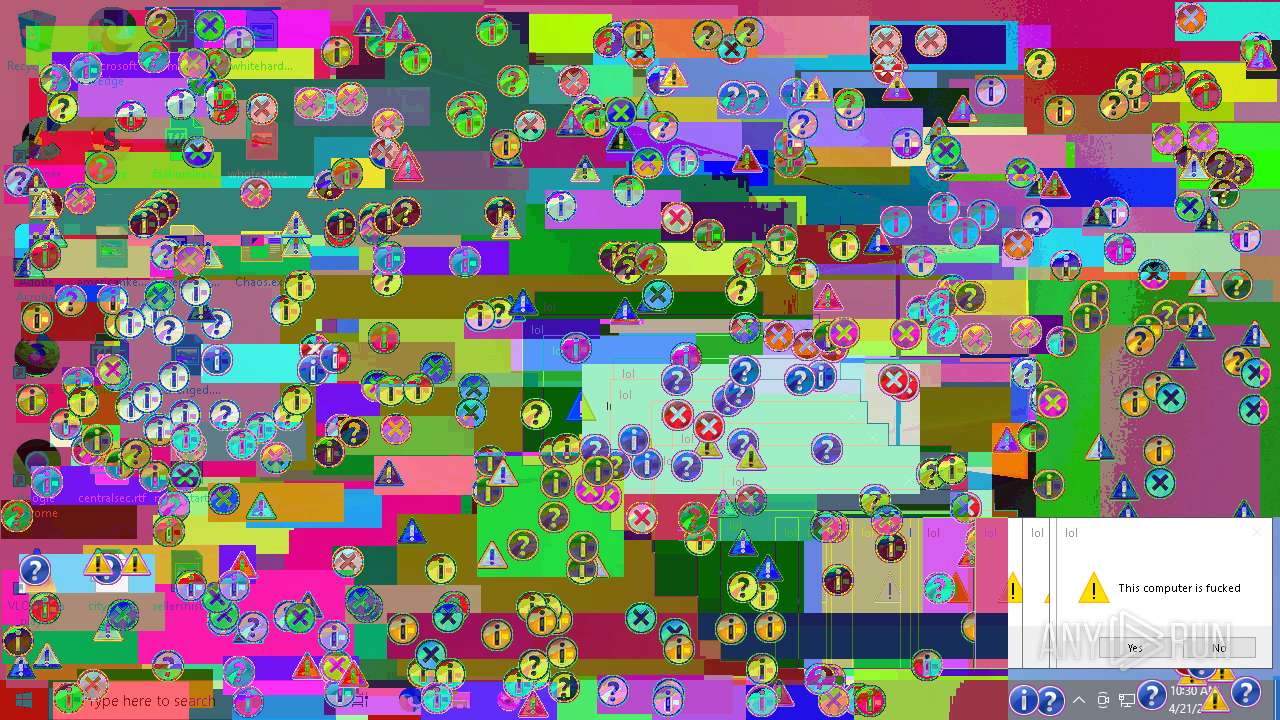
| Verdict: | Malicious activity |
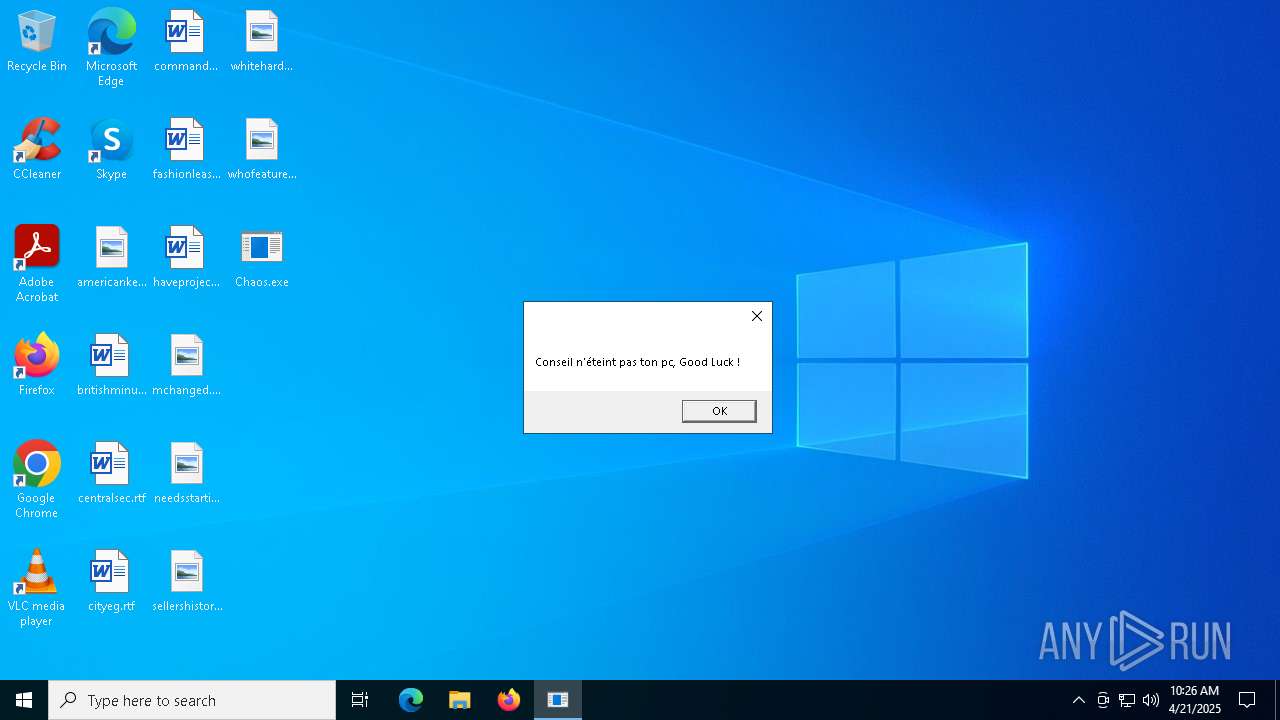
| Threats: | Chaos ransomware is a malware family known for its destructive capabilities and diverse variants. It first appeared in 2021 as a ransomware builder and later acted as a wiper. Unlike most ransomware strains that encrypt data to extort payment, early Chaos variants permanently corrupted files, while later versions adopted more conventional encryption techniques. |
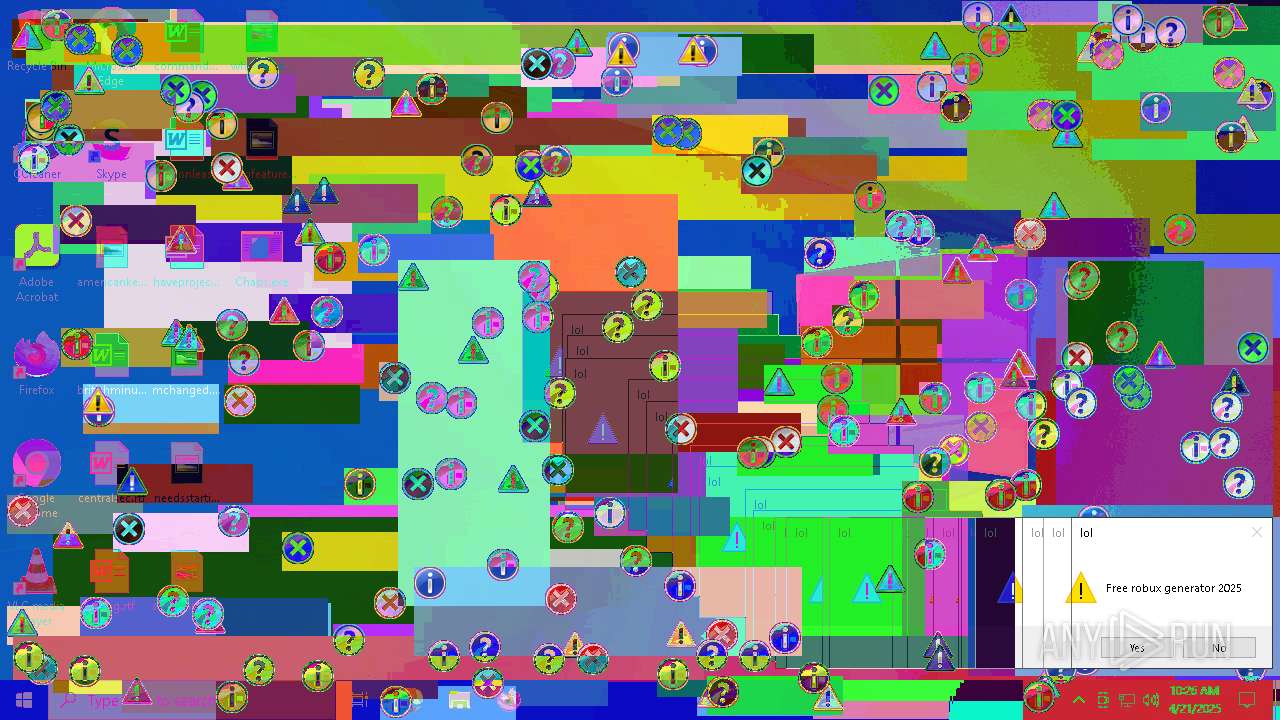
| Analysis date: | April 21, 2025, 10:25:51 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows, 3 sections |
| MD5: | 4A19EF0BAB9B9934811B9020D47B78CB |
| SHA1: | A184E1ADB0C8EDF218FDA1FFB94FDB48441C5DCC |
| SHA256: | 7B6867087DC41B42AFDEC95394CF1EAE09DB158FE916D61536BE80462E6F1038 |
| SSDEEP: | 768:3MwjhNo/xJMERvIy/kOL+nYDjdYW9+zoDjAT7+8HT9294Ic2skS:3MwjhNlDOLlDjrEzoDW7bHTvIc3j |
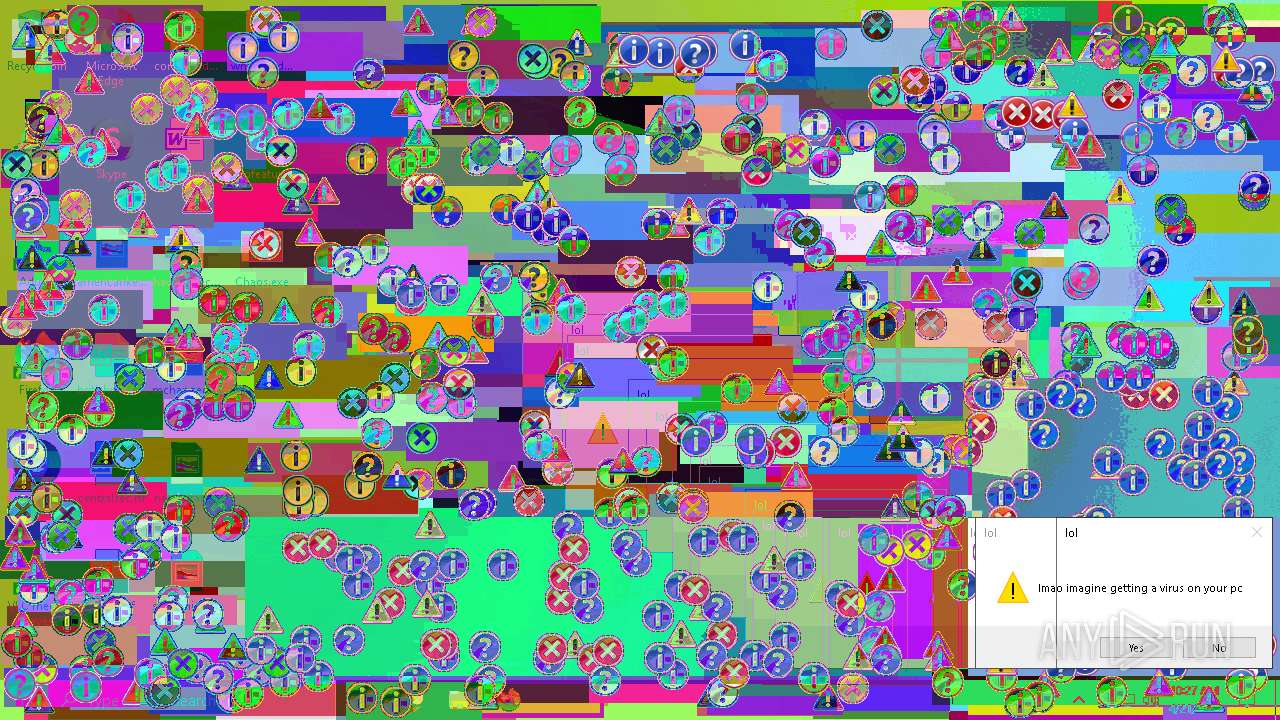
MALICIOUS
CHAOS has been detected (YARA)
- Chaos.exe (PID: 7472)
- Chaos.exe (PID: 6300)
- Chaos.exe (PID: 5892)
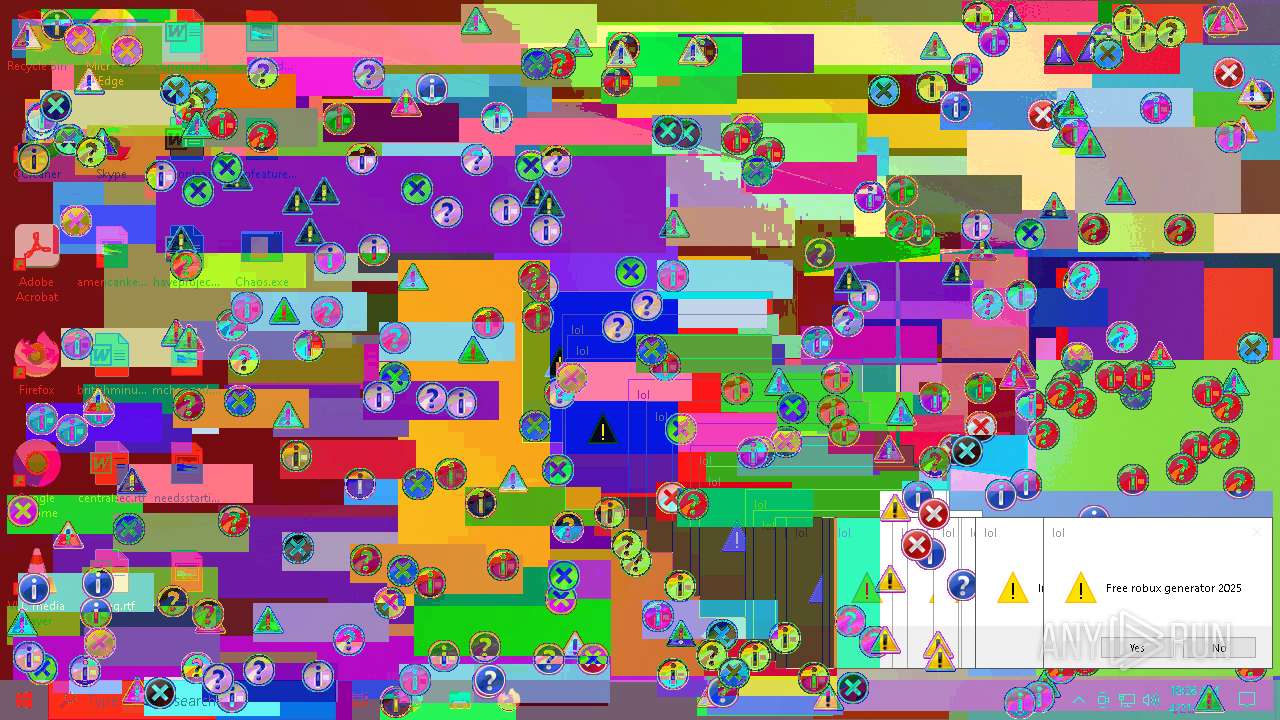
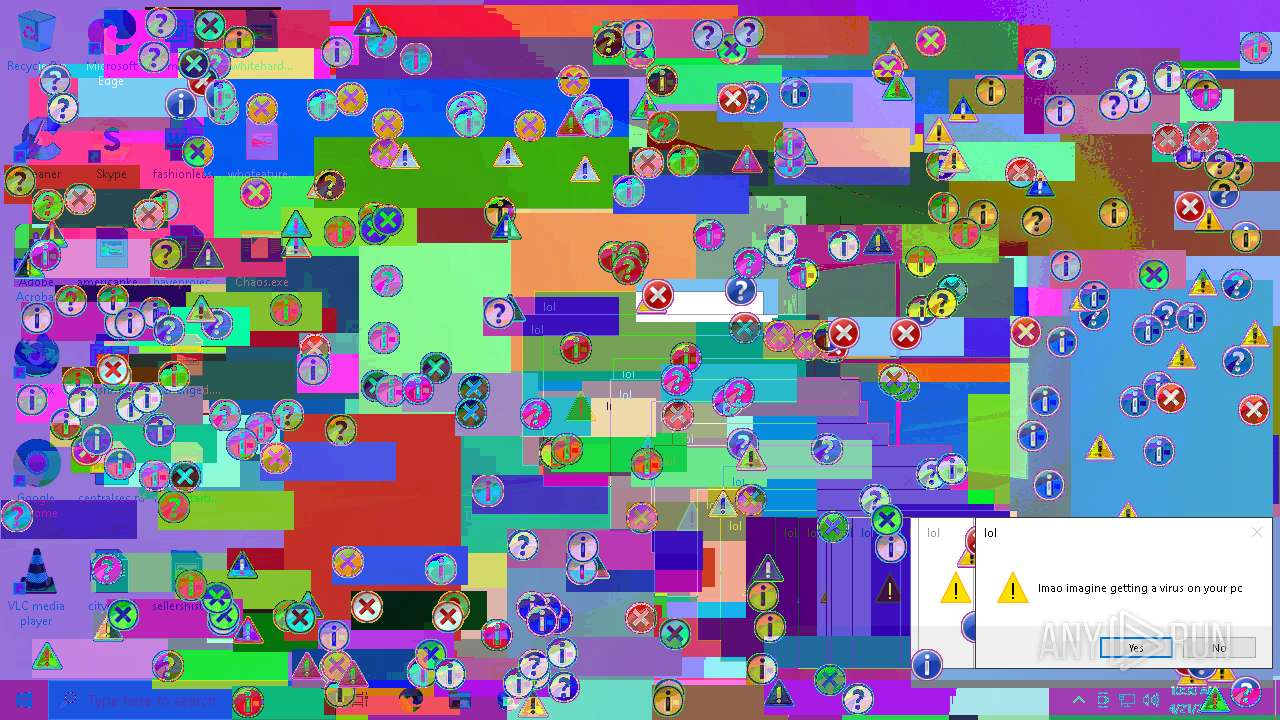
Stealers network behavior
- Chaos.exe (PID: 7472)
Attempting to use instant messaging service
- Chaos.exe (PID: 7472)
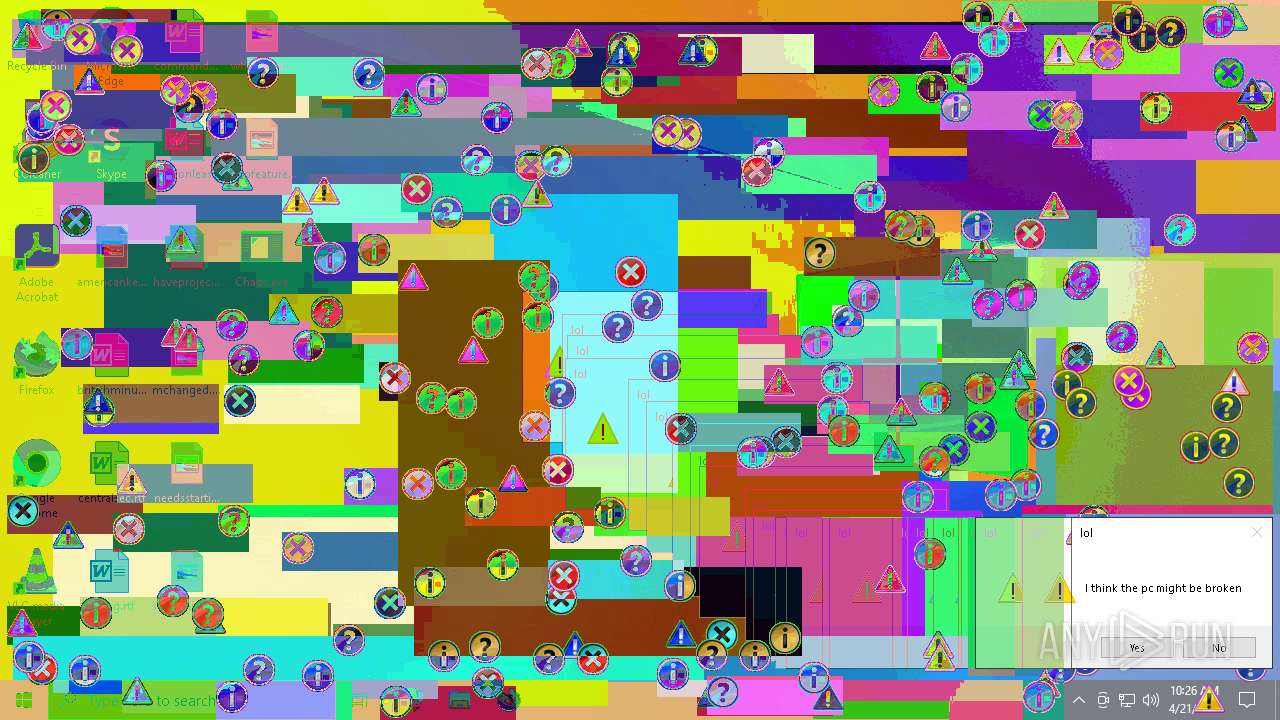
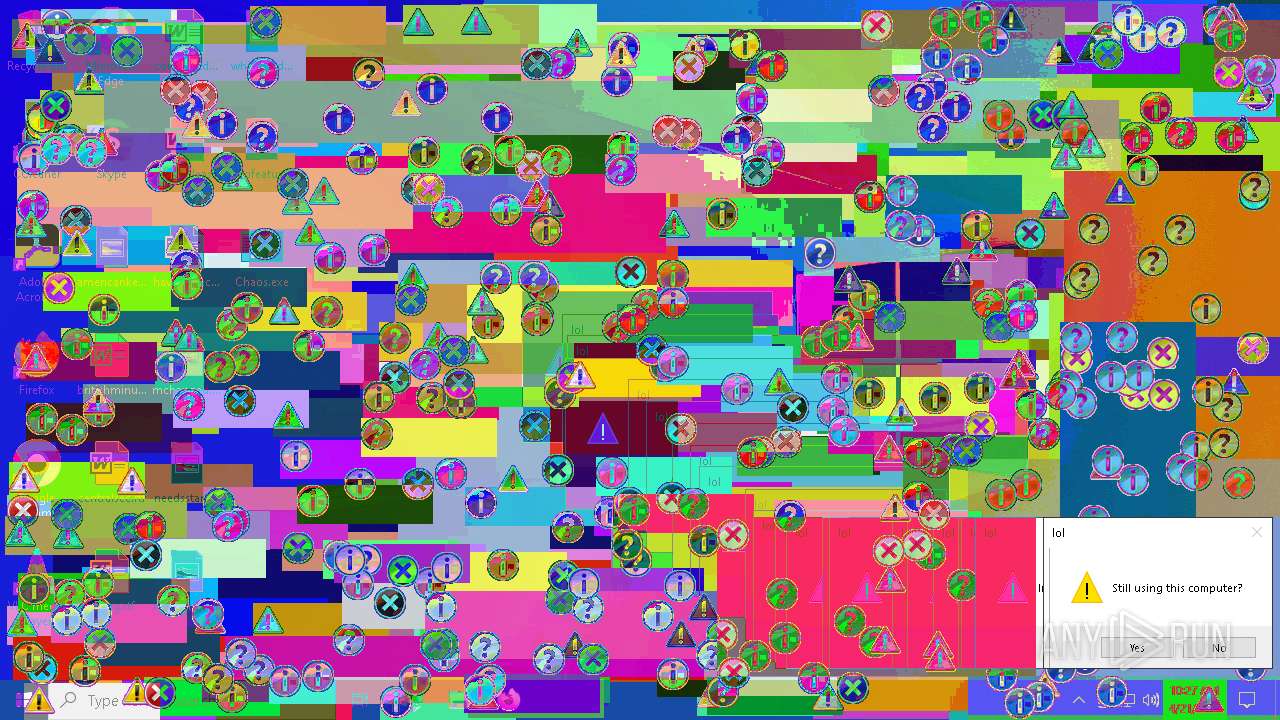
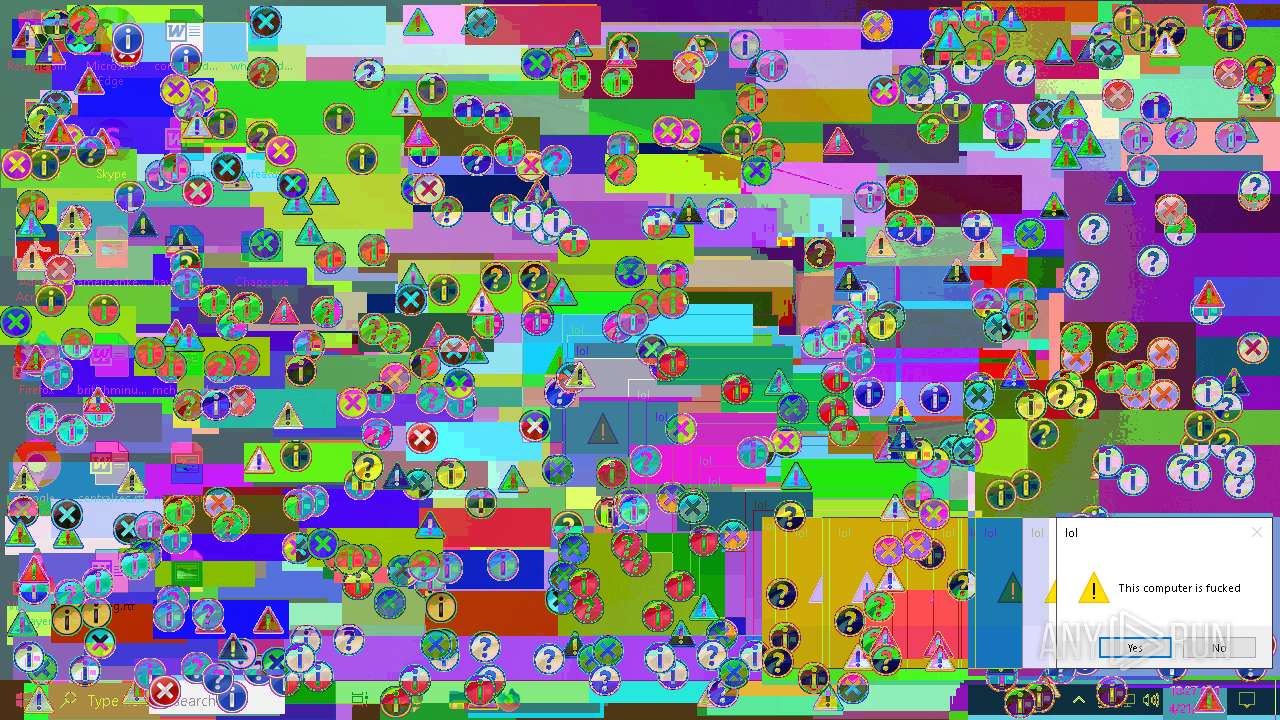
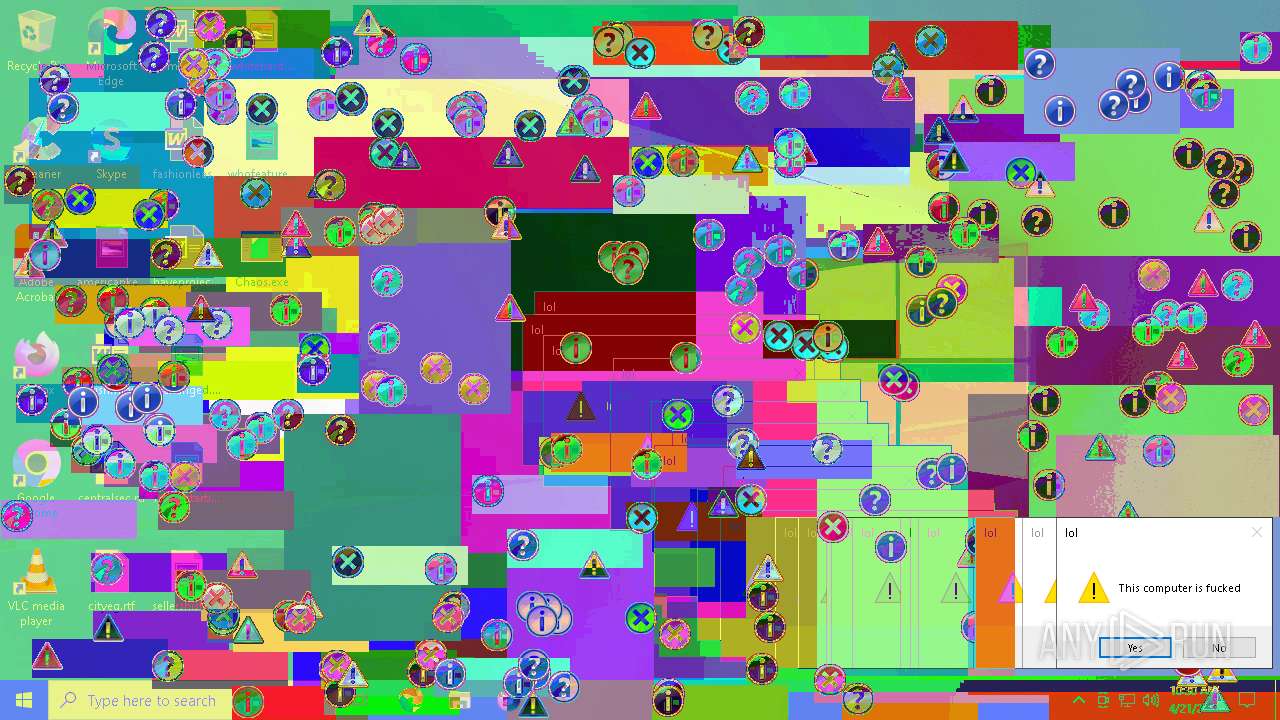
Disables the Run the Start menu
- Chaos.exe (PID: 6300)
- Chaos.exe (PID: 5892)
Disables task manager
- Chaos.exe (PID: 6300)
- Chaos.exe (PID: 5892)
Disables the Command Prompt (cmd)
- Chaos.exe (PID: 6300)
- Chaos.exe (PID: 5892)
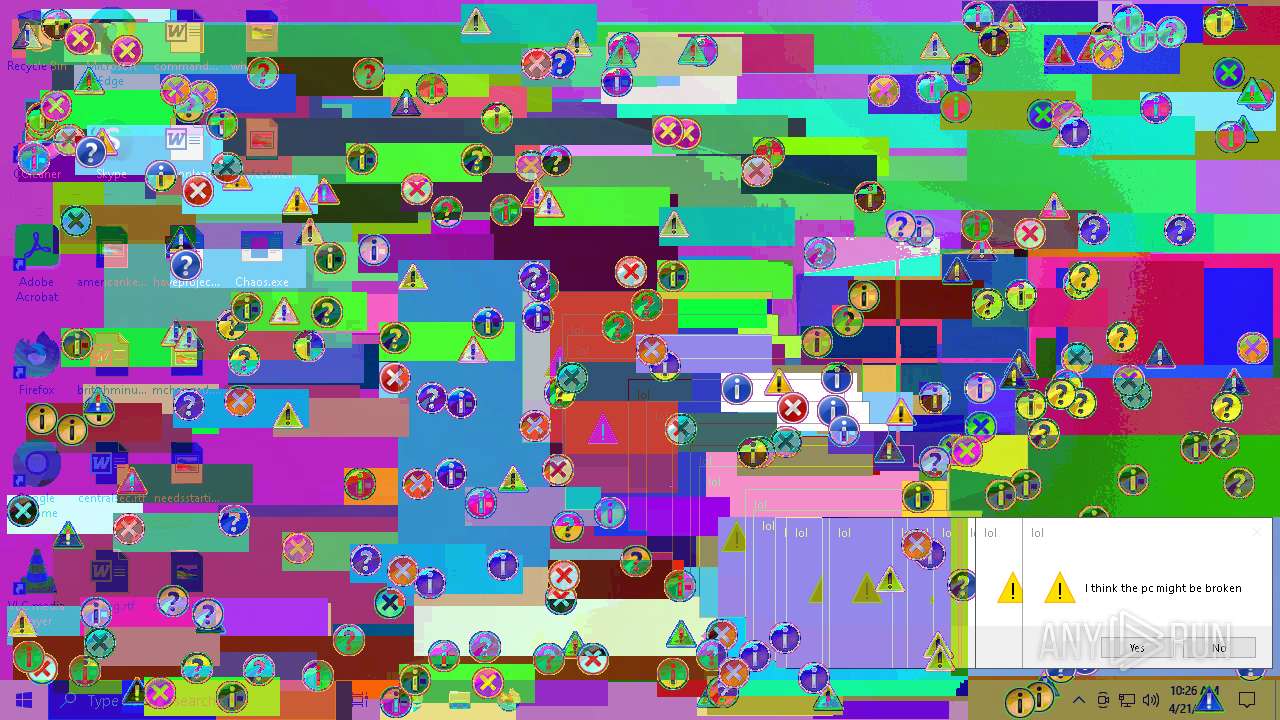
Task Manager has been disabled (taskmgr)
- Chaos.exe (PID: 5892)
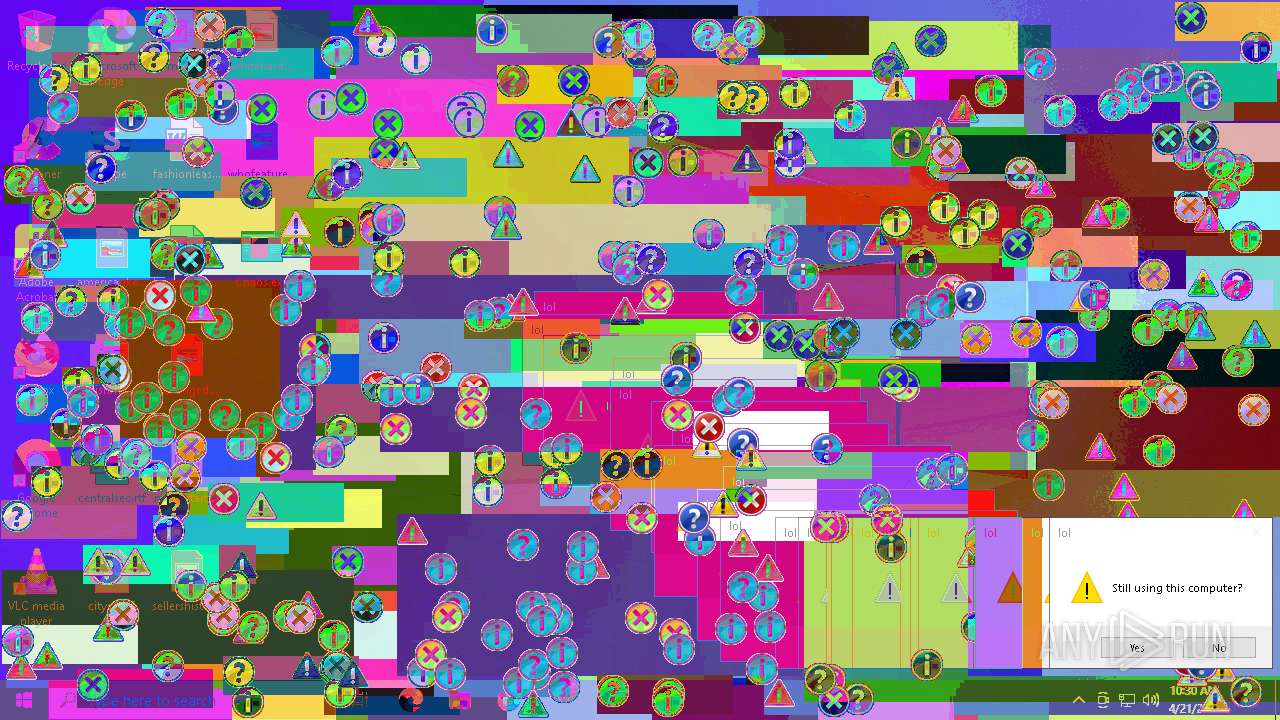
SUSPICIOUS
There is functionality for taking screenshot (YARA)
- Chaos.exe (PID: 7472)
- Chaos.exe (PID: 6300)
- Chaos.exe (PID: 5892)
Possible usage of Discord/Telegram API has been detected (YARA)
- Chaos.exe (PID: 7472)
- Chaos.exe (PID: 6300)
- Chaos.exe (PID: 5892)
The process connected to a server suspected of theft
- Chaos.exe (PID: 7472)
- Chaos.exe (PID: 6300)
- Chaos.exe (PID: 7488)
- Chaos.exe (PID: 5892)
Reads security settings of Internet Explorer
- Chaos.exe (PID: 7472)
- Chaos.exe (PID: 7488)
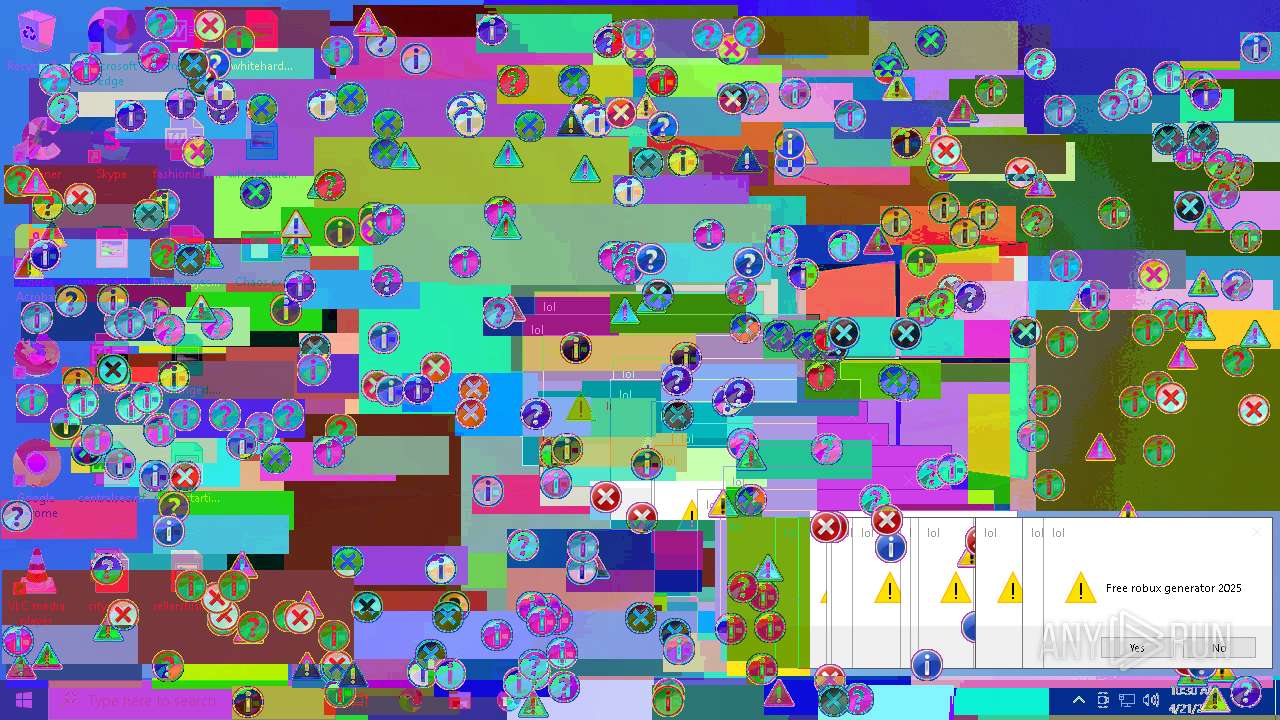
Application launched itself
- Chaos.exe (PID: 7472)
- Chaos.exe (PID: 7488)
Uses WMIC.EXE to obtain Windows Installer data
- Chaos.exe (PID: 6300)
- Chaos.exe (PID: 5892)
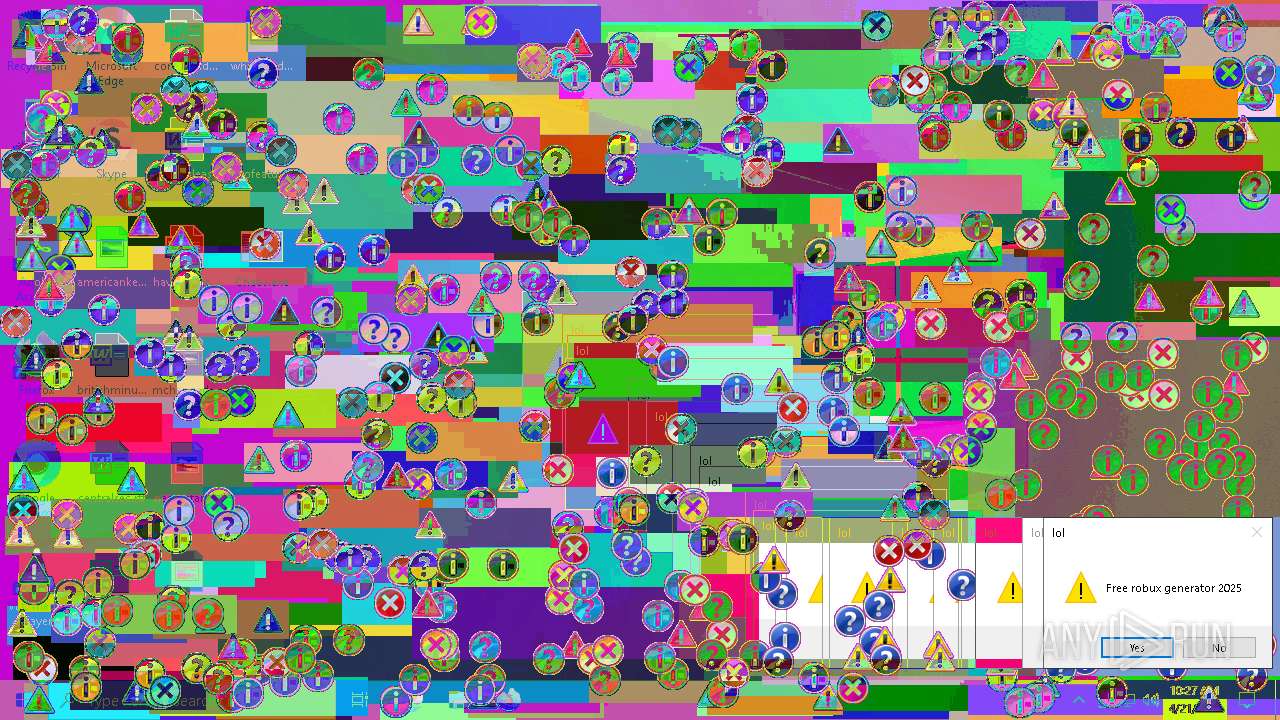
Checks for external IP
- Chaos.exe (PID: 6300)
- Chaos.exe (PID: 5892)
Accesses product unique identifier via WMI (SCRIPT)
- WMIC.exe (PID: 7644)
- WMIC.exe (PID: 6632)
Executes application which crashes
- Chaos.exe (PID: 6300)
INFO
Disables trace logs
- Chaos.exe (PID: 7472)
- Chaos.exe (PID: 6300)
- Chaos.exe (PID: 7488)
- Chaos.exe (PID: 5892)
Reads the software policy settings
- Chaos.exe (PID: 7472)
- Chaos.exe (PID: 6300)
- slui.exe (PID: 7972)
- slui.exe (PID: 8124)
- Chaos.exe (PID: 7488)
- Chaos.exe (PID: 5892)
Reads the computer name
- Chaos.exe (PID: 7472)
- Chaos.exe (PID: 6300)
- Chaos.exe (PID: 7488)
- Chaos.exe (PID: 5892)
Checks proxy server information
- Chaos.exe (PID: 7472)
- Chaos.exe (PID: 6300)
- slui.exe (PID: 8124)
- Chaos.exe (PID: 7488)
- Chaos.exe (PID: 5892)
Checks supported languages
- Chaos.exe (PID: 7472)
- Chaos.exe (PID: 6300)
- Chaos.exe (PID: 7488)
- Chaos.exe (PID: 5892)
Attempting to use instant messaging service
- Chaos.exe (PID: 7472)
- Chaos.exe (PID: 6300)
- Chaos.exe (PID: 5892)
Reads the machine GUID from the registry
- Chaos.exe (PID: 7472)
- Chaos.exe (PID: 6300)
- Chaos.exe (PID: 7488)
- Chaos.exe (PID: 5892)
Process checks computer location settings
- Chaos.exe (PID: 7472)
- Chaos.exe (PID: 7488)
Reads security settings of Internet Explorer
- WMIC.exe (PID: 7644)
- WMIC.exe (PID: 6632)
Creates files or folders in the user directory
- WerFault.exe (PID: 632)
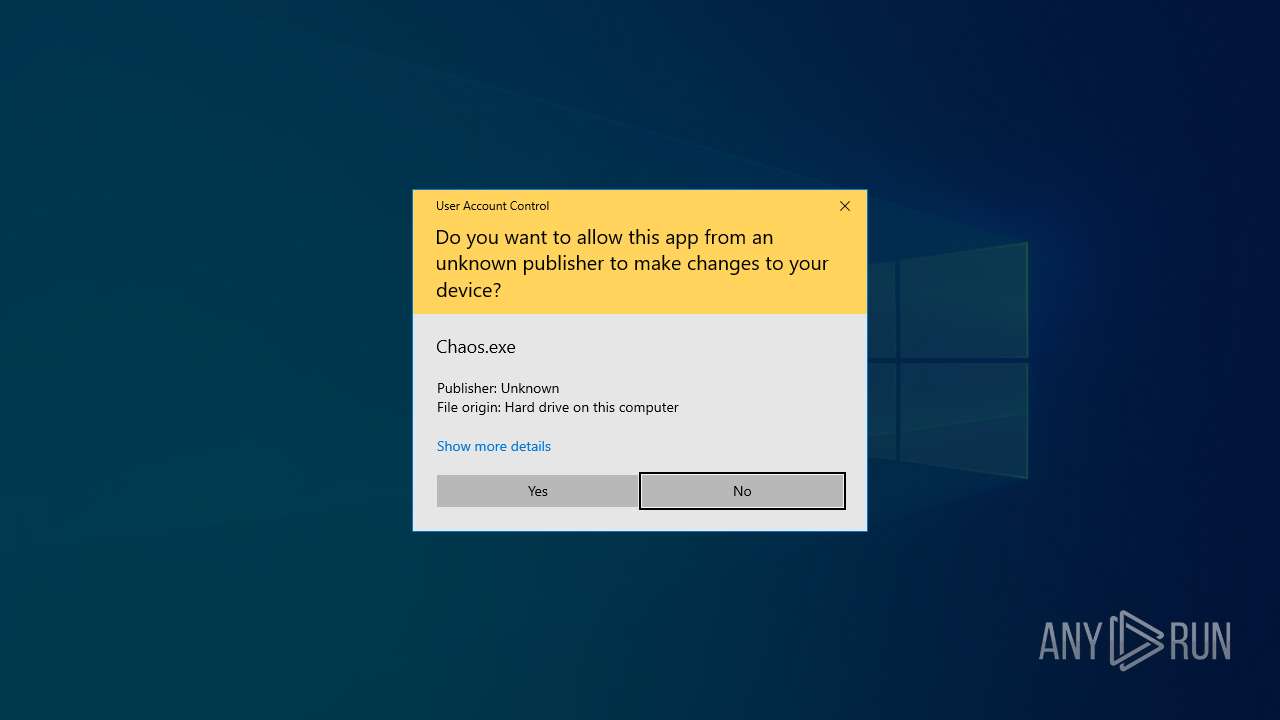
Manual execution by a user
- Chaos.exe (PID: 7488)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
ims-api
(PID) Process(7472) Chaos.exe
Discord-Webhook-Tokens (3)1363668358976770108/tT5Uge87qLsPbs491T2HnYXQckYNYU4jg9TEDuRTEiQkGSS0WxtyepC3qIxJCU8G-X_7
1363683168758268104/K9YaamjIs5dgF6o4yIsc92V0uJrspIBmISMjdOI1j_-7JD3oRuwbcuRRJIPIZDJ3iknd
1363670828759257270/rW8K5FhWMpKgXZ5AbsWc8bvx5Pzei5a41zCybrffmJNwhXwJCJZ6lp2E0kyOupHfk10W
Discord-Info-Links
1363668358976770108/tT5Uge87qLsPbs491T2HnYXQckYNYU4jg9TEDuRTEiQkGSS0WxtyepC3qIxJCU8G-X_7
Get Webhook Infohttps://discord.com/api/webhooks/1363668358976770108/tT5Uge87qLsPbs491T2HnYXQckYNYU4jg9TEDuRTEiQkGSS0WxtyepC3qIxJCU8G-X_7
1363683168758268104/K9YaamjIs5dgF6o4yIsc92V0uJrspIBmISMjdOI1j_-7JD3oRuwbcuRRJIPIZDJ3iknd
Get Webhook Infohttps://discord.com/api/webhooks/1363683168758268104/K9YaamjIs5dgF6o4yIsc92V0uJrspIBmISMjdOI1j_-7JD3oRuwbcuRRJIPIZDJ3iknd
1363670828759257270/rW8K5FhWMpKgXZ5AbsWc8bvx5Pzei5a41zCybrffmJNwhXwJCJZ6lp2E0kyOupHfk10W
Get Webhook Infohttps://discord.com/api/webhooks/1363670828759257270/rW8K5FhWMpKgXZ5AbsWc8bvx5Pzei5a41zCybrffmJNwhXwJCJZ6lp2E0kyOupHfk10W
Discord-Webhook-Tokens (2)1363683168758268104/K9YaamjIs5dgF6o4yIsc92V0uJrspIBmISMjdOI1j_-7JD3oRuwbcuRRJIPIZDJ3iknd
1363670828759257270/rW8K5FhWMpKgXZ5AbsWc8bvx5Pzei5a41zCybrffmJNwhXwJCJZ6lp2E0kyOupHfk10W
Discord-Info-Links
1363683168758268104/K9YaamjIs5dgF6o4yIsc92V0uJrspIBmISMjdOI1j_-7JD3oRuwbcuRRJIPIZDJ3iknd
Get Webhook Infohttps://discord.com/api/webhooks/1363683168758268104/K9YaamjIs5dgF6o4yIsc92V0uJrspIBmISMjdOI1j_-7JD3oRuwbcuRRJIPIZDJ3iknd
1363670828759257270/rW8K5FhWMpKgXZ5AbsWc8bvx5Pzei5a41zCybrffmJNwhXwJCJZ6lp2E0kyOupHfk10W
Get Webhook Infohttps://discord.com/api/webhooks/1363670828759257270/rW8K5FhWMpKgXZ5AbsWc8bvx5Pzei5a41zCybrffmJNwhXwJCJZ6lp2E0kyOupHfk10W
(PID) Process(6300) Chaos.exe
Discord-Webhook-Tokens (3)1363668358976770108/tT5Uge87qLsPbs491T2HnYXQckYNYU4jg9TEDuRTEiQkGSS0WxtyepC3qIxJCU8G-X_7
1363683168758268104/K9YaamjIs5dgF6o4yIsc92V0uJrspIBmISMjdOI1j_-7JD3oRuwbcuRRJIPIZDJ3iknd
1363670828759257270/rW8K5FhWMpKgXZ5AbsWc8bvx5Pzei5a41zCybrffmJNwhXwJCJZ6lp2E0kyOupHfk10W
Discord-Info-Links
1363668358976770108/tT5Uge87qLsPbs491T2HnYXQckYNYU4jg9TEDuRTEiQkGSS0WxtyepC3qIxJCU8G-X_7
Get Webhook Infohttps://discord.com/api/webhooks/1363668358976770108/tT5Uge87qLsPbs491T2HnYXQckYNYU4jg9TEDuRTEiQkGSS0WxtyepC3qIxJCU8G-X_7
1363683168758268104/K9YaamjIs5dgF6o4yIsc92V0uJrspIBmISMjdOI1j_-7JD3oRuwbcuRRJIPIZDJ3iknd
Get Webhook Infohttps://discord.com/api/webhooks/1363683168758268104/K9YaamjIs5dgF6o4yIsc92V0uJrspIBmISMjdOI1j_-7JD3oRuwbcuRRJIPIZDJ3iknd
1363670828759257270/rW8K5FhWMpKgXZ5AbsWc8bvx5Pzei5a41zCybrffmJNwhXwJCJZ6lp2E0kyOupHfk10W
Get Webhook Infohttps://discord.com/api/webhooks/1363670828759257270/rW8K5FhWMpKgXZ5AbsWc8bvx5Pzei5a41zCybrffmJNwhXwJCJZ6lp2E0kyOupHfk10W
(PID) Process(5892) Chaos.exe
Discord-Webhook-Tokens (3)1363668358976770108/tT5Uge87qLsPbs491T2HnYXQckYNYU4jg9TEDuRTEiQkGSS0WxtyepC3qIxJCU8G-X_7
1363683168758268104/K9YaamjIs5dgF6o4yIsc92V0uJrspIBmISMjdOI1j_-7JD3oRuwbcuRRJIPIZDJ3iknd
1363670828759257270/rW8K5FhWMpKgXZ5AbsWc8bvx5Pzei5a41zCybrffmJNwhXwJCJZ6lp2E0kyOupHfk10W
Discord-Info-Links
1363668358976770108/tT5Uge87qLsPbs491T2HnYXQckYNYU4jg9TEDuRTEiQkGSS0WxtyepC3qIxJCU8G-X_7
Get Webhook Infohttps://discord.com/api/webhooks/1363668358976770108/tT5Uge87qLsPbs491T2HnYXQckYNYU4jg9TEDuRTEiQkGSS0WxtyepC3qIxJCU8G-X_7
1363683168758268104/K9YaamjIs5dgF6o4yIsc92V0uJrspIBmISMjdOI1j_-7JD3oRuwbcuRRJIPIZDJ3iknd
Get Webhook Infohttps://discord.com/api/webhooks/1363683168758268104/K9YaamjIs5dgF6o4yIsc92V0uJrspIBmISMjdOI1j_-7JD3oRuwbcuRRJIPIZDJ3iknd
1363670828759257270/rW8K5FhWMpKgXZ5AbsWc8bvx5Pzei5a41zCybrffmJNwhXwJCJZ6lp2E0kyOupHfk10W
Get Webhook Infohttps://discord.com/api/webhooks/1363670828759257270/rW8K5FhWMpKgXZ5AbsWc8bvx5Pzei5a41zCybrffmJNwhXwJCJZ6lp2E0kyOupHfk10W
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (63.1) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (23.8) |
| .dll | | | Win32 Dynamic Link Library (generic) (5.6) |
| .exe | | | Win32 Executable (generic) (3.8) |
| .exe | | | Generic Win/DOS Executable (1.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2105:09:20 11:22:31+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32 |
| LinkerVersion: | 48 |
| CodeSize: | 52224 |
| InitializedDataSize: | 2048 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xea2e |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | - |
| CompanyName: | - |
| FileDescription: | Chaos |
| FileVersion: | 1.0.0.0 |
| InternalName: | Chaos.exe |
| LegalCopyright: | Copyright © 2025 |
| LegalTrademarks: | - |
| OriginalFileName: | Chaos.exe |
| ProductName: | Chaos |
| ProductVersion: | 1.0.0.0 |
| AssemblyVersion: | 1.0.0.0 |
Total processes
155
Monitored processes
12
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 632 | C:\WINDOWS\SysWOW64\WerFault.exe -u -p 6300 -s 2244 | C:\Windows\SysWOW64\WerFault.exe | — | Chaos.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Problem Reporting Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5892 | "C:\Users\admin\Desktop\Chaos.exe" | C:\Users\admin\Desktop\Chaos.exe | Chaos.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Chaos Version: 1.0.0.0 Modules
ims-api(PID) Process(5892) Chaos.exe Discord-Webhook-Tokens (3)1363668358976770108/tT5Uge87qLsPbs491T2HnYXQckYNYU4jg9TEDuRTEiQkGSS0WxtyepC3qIxJCU8G-X_7 1363683168758268104/K9YaamjIs5dgF6o4yIsc92V0uJrspIBmISMjdOI1j_-7JD3oRuwbcuRRJIPIZDJ3iknd 1363670828759257270/rW8K5FhWMpKgXZ5AbsWc8bvx5Pzei5a41zCybrffmJNwhXwJCJZ6lp2E0kyOupHfk10W Discord-Info-Links 1363668358976770108/tT5Uge87qLsPbs491T2HnYXQckYNYU4jg9TEDuRTEiQkGSS0WxtyepC3qIxJCU8G-X_7 Get Webhook Infohttps://discord.com/api/webhooks/1363668358976770108/tT5Uge87qLsPbs491T2HnYXQckYNYU4jg9TEDuRTEiQkGSS0WxtyepC3qIxJCU8G-X_7 1363683168758268104/K9YaamjIs5dgF6o4yIsc92V0uJrspIBmISMjdOI1j_-7JD3oRuwbcuRRJIPIZDJ3iknd Get Webhook Infohttps://discord.com/api/webhooks/1363683168758268104/K9YaamjIs5dgF6o4yIsc92V0uJrspIBmISMjdOI1j_-7JD3oRuwbcuRRJIPIZDJ3iknd 1363670828759257270/rW8K5FhWMpKgXZ5AbsWc8bvx5Pzei5a41zCybrffmJNwhXwJCJZ6lp2E0kyOupHfk10W Get Webhook Infohttps://discord.com/api/webhooks/1363670828759257270/rW8K5FhWMpKgXZ5AbsWc8bvx5Pzei5a41zCybrffmJNwhXwJCJZ6lp2E0kyOupHfk10W | |||||||||||||||
| 6300 | "C:\Users\admin\Desktop\Chaos.exe" | C:\Users\admin\Desktop\Chaos.exe | Chaos.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Chaos Exit code: 3221225725 Version: 1.0.0.0 Modules
ims-api(PID) Process(6300) Chaos.exe Discord-Webhook-Tokens (3)1363668358976770108/tT5Uge87qLsPbs491T2HnYXQckYNYU4jg9TEDuRTEiQkGSS0WxtyepC3qIxJCU8G-X_7 1363683168758268104/K9YaamjIs5dgF6o4yIsc92V0uJrspIBmISMjdOI1j_-7JD3oRuwbcuRRJIPIZDJ3iknd 1363670828759257270/rW8K5FhWMpKgXZ5AbsWc8bvx5Pzei5a41zCybrffmJNwhXwJCJZ6lp2E0kyOupHfk10W Discord-Info-Links 1363668358976770108/tT5Uge87qLsPbs491T2HnYXQckYNYU4jg9TEDuRTEiQkGSS0WxtyepC3qIxJCU8G-X_7 Get Webhook Infohttps://discord.com/api/webhooks/1363668358976770108/tT5Uge87qLsPbs491T2HnYXQckYNYU4jg9TEDuRTEiQkGSS0WxtyepC3qIxJCU8G-X_7 1363683168758268104/K9YaamjIs5dgF6o4yIsc92V0uJrspIBmISMjdOI1j_-7JD3oRuwbcuRRJIPIZDJ3iknd Get Webhook Infohttps://discord.com/api/webhooks/1363683168758268104/K9YaamjIs5dgF6o4yIsc92V0uJrspIBmISMjdOI1j_-7JD3oRuwbcuRRJIPIZDJ3iknd 1363670828759257270/rW8K5FhWMpKgXZ5AbsWc8bvx5Pzei5a41zCybrffmJNwhXwJCJZ6lp2E0kyOupHfk10W Get Webhook Infohttps://discord.com/api/webhooks/1363670828759257270/rW8K5FhWMpKgXZ5AbsWc8bvx5Pzei5a41zCybrffmJNwhXwJCJZ6lp2E0kyOupHfk10W | |||||||||||||||
| 6632 | "wmic" csproduct get UUID | C:\Windows\SysWOW64\wbem\WMIC.exe | — | Chaos.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: WMI Commandline Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7340 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | WMIC.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7472 | "C:\Users\admin\Desktop\Chaos.exe" | C:\Users\admin\Desktop\Chaos.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Chaos Exit code: 0 Version: 1.0.0.0 Modules
ims-api(PID) Process(7472) Chaos.exe Discord-Webhook-Tokens (3)1363668358976770108/tT5Uge87qLsPbs491T2HnYXQckYNYU4jg9TEDuRTEiQkGSS0WxtyepC3qIxJCU8G-X_7 1363683168758268104/K9YaamjIs5dgF6o4yIsc92V0uJrspIBmISMjdOI1j_-7JD3oRuwbcuRRJIPIZDJ3iknd 1363670828759257270/rW8K5FhWMpKgXZ5AbsWc8bvx5Pzei5a41zCybrffmJNwhXwJCJZ6lp2E0kyOupHfk10W Discord-Info-Links 1363668358976770108/tT5Uge87qLsPbs491T2HnYXQckYNYU4jg9TEDuRTEiQkGSS0WxtyepC3qIxJCU8G-X_7 Get Webhook Infohttps://discord.com/api/webhooks/1363668358976770108/tT5Uge87qLsPbs491T2HnYXQckYNYU4jg9TEDuRTEiQkGSS0WxtyepC3qIxJCU8G-X_7 1363683168758268104/K9YaamjIs5dgF6o4yIsc92V0uJrspIBmISMjdOI1j_-7JD3oRuwbcuRRJIPIZDJ3iknd Get Webhook Infohttps://discord.com/api/webhooks/1363683168758268104/K9YaamjIs5dgF6o4yIsc92V0uJrspIBmISMjdOI1j_-7JD3oRuwbcuRRJIPIZDJ3iknd 1363670828759257270/rW8K5FhWMpKgXZ5AbsWc8bvx5Pzei5a41zCybrffmJNwhXwJCJZ6lp2E0kyOupHfk10W Get Webhook Infohttps://discord.com/api/webhooks/1363670828759257270/rW8K5FhWMpKgXZ5AbsWc8bvx5Pzei5a41zCybrffmJNwhXwJCJZ6lp2E0kyOupHfk10W (PID) Process(7472) Chaos.exe Discord-Webhook-Tokens (2)1363683168758268104/K9YaamjIs5dgF6o4yIsc92V0uJrspIBmISMjdOI1j_-7JD3oRuwbcuRRJIPIZDJ3iknd 1363670828759257270/rW8K5FhWMpKgXZ5AbsWc8bvx5Pzei5a41zCybrffmJNwhXwJCJZ6lp2E0kyOupHfk10W Discord-Info-Links 1363683168758268104/K9YaamjIs5dgF6o4yIsc92V0uJrspIBmISMjdOI1j_-7JD3oRuwbcuRRJIPIZDJ3iknd Get Webhook Infohttps://discord.com/api/webhooks/1363683168758268104/K9YaamjIs5dgF6o4yIsc92V0uJrspIBmISMjdOI1j_-7JD3oRuwbcuRRJIPIZDJ3iknd 1363670828759257270/rW8K5FhWMpKgXZ5AbsWc8bvx5Pzei5a41zCybrffmJNwhXwJCJZ6lp2E0kyOupHfk10W Get Webhook Infohttps://discord.com/api/webhooks/1363670828759257270/rW8K5FhWMpKgXZ5AbsWc8bvx5Pzei5a41zCybrffmJNwhXwJCJZ6lp2E0kyOupHfk10W | |||||||||||||||
| 7488 | "C:\Users\admin\Desktop\Chaos.exe" | C:\Users\admin\Desktop\Chaos.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Chaos Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 7644 | "wmic" csproduct get UUID | C:\Windows\SysWOW64\wbem\WMIC.exe | — | Chaos.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: WMI Commandline Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7648 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | WMIC.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7940 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
6 481
Read events
6 449
Write events
29
Delete events
3
Modification events
| (PID) Process: | (7472) Chaos.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\Chaos_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (7472) Chaos.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\Chaos_RASAPI32 |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (7472) Chaos.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\Chaos_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (7472) Chaos.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\Chaos_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: | |||
| (PID) Process: | (7472) Chaos.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\Chaos_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: | |||
| (PID) Process: | (7472) Chaos.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\Chaos_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (7472) Chaos.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\Chaos_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (7472) Chaos.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\Chaos_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (7472) Chaos.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\Chaos_RASMANCS |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (7472) Chaos.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\Chaos_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
Executable files
0
Suspicious files
2
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 632 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\ReportQueue\AppCrash_Chaos.exe_8f1ff056cc3acb7bd4e5243c467e2522bc2f088_7b098860_e6d273a5-dd39-4e06-b099-ec3f0ceca9d9\Report.wer | — | |
MD5:— | SHA256:— | |||
| 632 | WerFault.exe | C:\Users\admin\AppData\Local\CrashDumps\Chaos.exe.6300.dmp | — | |
MD5:— | SHA256:— | |||
| 632 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\Temp\WER8046.tmp.xml | xml | |
MD5:0BEB130CAA98B382B8B7B32598E760D7 | SHA256:910CCB2B4E165655AAADD27FF007C94E3B55CEEB5929A663E9934E7A349526AC | |||
| 632 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\Temp\WER798D.tmp.dmp | binary | |
MD5:FDF5393F867CA3A1316C4D2872A36360 | SHA256:C341206DA140C87CA81C3295119F4AA9246EA8BD488EF92BC7C0448E3F2CA593 | |||
| 632 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\Temp\WER8006.tmp.WERInternalMetadata.xml | binary | |
MD5:7AE55B887E2467C38E7E749708B160F2 | SHA256:D41B70BED83B9540E7EA040E157FF7148D1E5FE40533418747B57DE5B1527CD1 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
71
DNS requests
22
Threats
98
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.48.23.143:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7828 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
7828 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2104 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.48.23.143:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5496 | MoUsoCoreWorker.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
7472 | Chaos.exe | 162.159.128.233:443 | discord.com | CLOUDFLARENET | — | whitelisted |
3216 | svchost.exe | 172.211.123.248:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
6544 | svchost.exe | 40.126.32.134:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
discord.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
api.ipify.org |
| shared |
slscr.update.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | Misc activity | ET INFO Observed Discord Domain in DNS Lookup (discord .com) |
7472 | Chaos.exe | Misc activity | ET INFO Observed Discord Domain (discord .com in TLS SNI) |
7472 | Chaos.exe | Misc activity | ET INFO Observed Discord Service Domain (discord .com) in TLS SNI |
2196 | svchost.exe | Misc activity | ET INFO Discord Chat Service Domain in DNS Lookup (discord .com) |
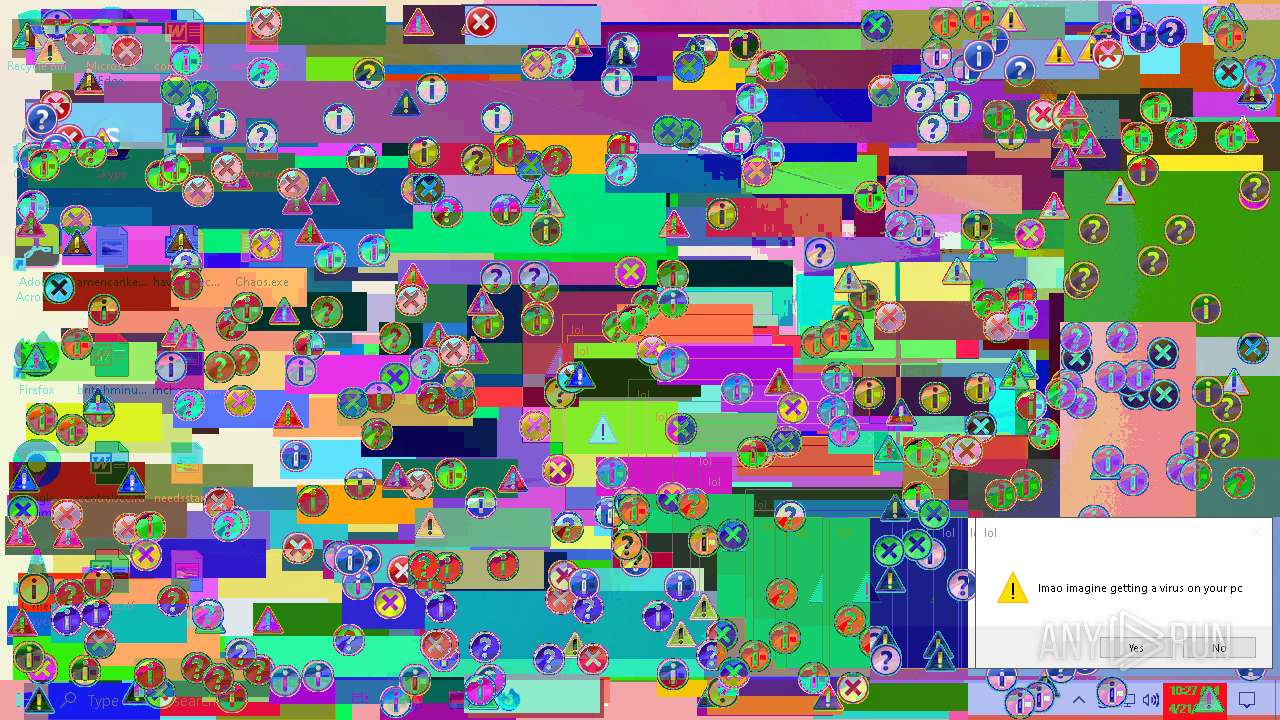
7472 | Chaos.exe | Successful Credential Theft Detected | STEALER [ANY.RUN] Attempt to exfiltrate via Discord |
6300 | Chaos.exe | Misc activity | ET INFO Observed Discord Domain (discord .com in TLS SNI) |
6300 | Chaos.exe | Misc activity | ET INFO Observed Discord Service Domain (discord .com) in TLS SNI |
6300 | Chaos.exe | Successful Credential Theft Detected | STEALER [ANY.RUN] Attempt to exfiltrate via Discord |
6300 | Chaos.exe | Misc activity | ET INFO Observed Discord Domain (discord .com in TLS SNI) |
6300 | Chaos.exe | Misc activity | ET INFO Observed Discord Service Domain (discord .com) in TLS SNI |