| File name: | webex.exe |
| Full analysis: | https://app.any.run/tasks/7ee839ab-cae1-4d57-8f6a-438c703d8faa |
| Verdict: | Malicious activity |
| Threats: | WarZone RAT is a remote access trojan, which is written in C++ and offered as a malware-as-a-service. It packs a wide range of capabilities, from stealing victims’ files and passwords to capturing desktop activities. WarZone RAT is primarily distributed via phishing emails and receives regular updates from its C2. |
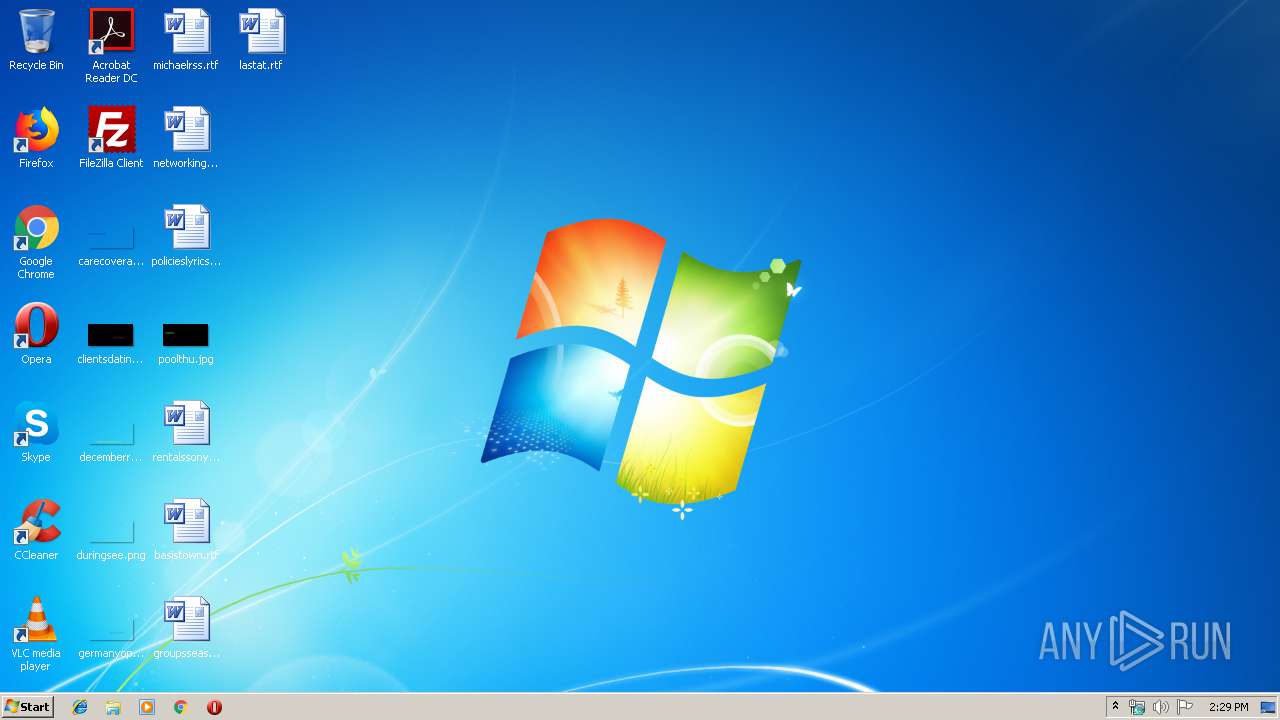
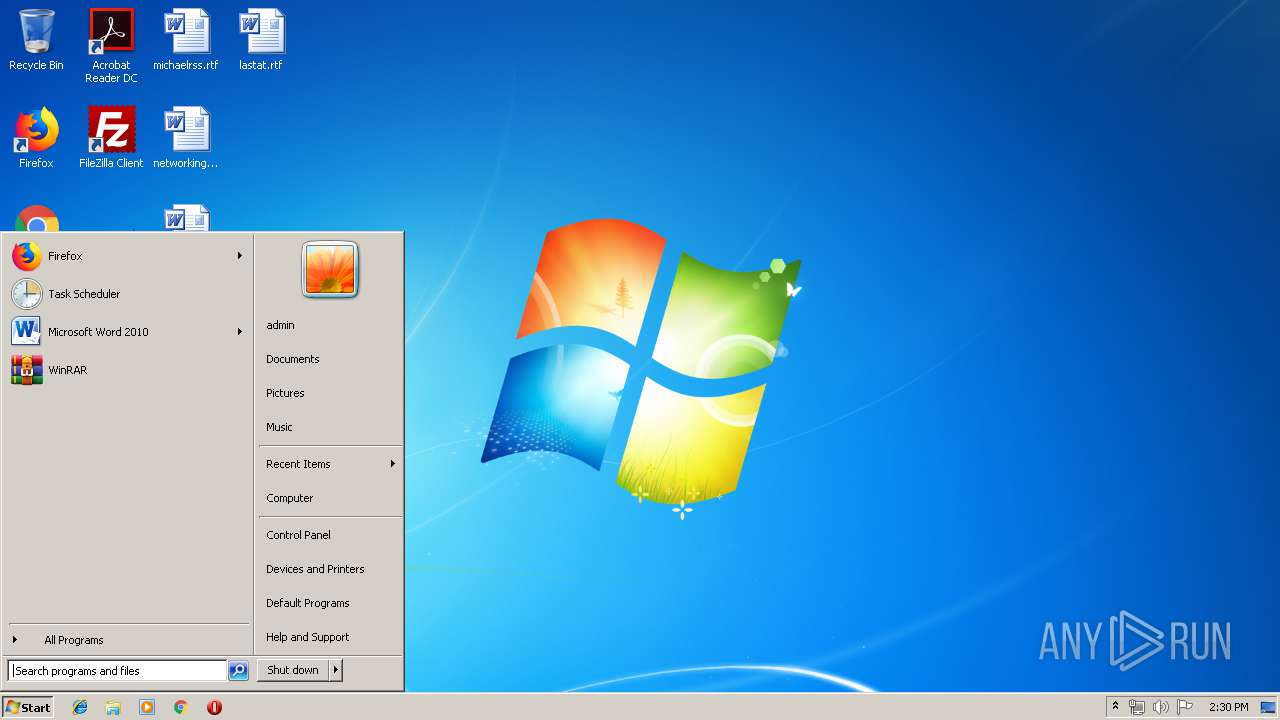
| Analysis date: | November 08, 2019, 14:29:31 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 073B85C6A9F95A409CF2D7C694E2BCF1 |
| SHA1: | 5EA2C8C485F002863E6128646D1283313FECDB35 |
| SHA256: | 79873E1AD7AE8D612134AF50C654E34364B1249F86FA13FB4813D7BC63B774E2 |
| SSDEEP: | 24576:bu6J33O0c+JY5UZ+XC0kGso6FaSazta3odl28UWY:Vu0c++OCvkGs9FaISY |
MALICIOUS
Writes to a start menu file
- webex.exe (PID: 2768)
Changes the autorun value in the registry
- webex.exe (PID: 3764)
AVEMARIA was detected
- webex.exe (PID: 3736)
- services.exe (PID: 1796)
SUSPICIOUS
Executable content was dropped or overwritten
- webex.exe (PID: 2768)
- webex.exe (PID: 3764)
Creates executable files which already exist in Windows
- webex.exe (PID: 3764)
Creates files in the user directory
- webex.exe (PID: 2768)
- webex.exe (PID: 3764)
Application launched itself
- webex.exe (PID: 2768)
- services.exe (PID: 1600)
Starts itself from another location
- webex.exe (PID: 3764)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:11:05 11:32:29+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 12 |
| CodeSize: | 581120 |
| InitializedDataSize: | 620032 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x27dcd |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 0.0.0.0 |
| ProductVersionNumber: | 0.0.0.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (British) |
| CharacterSet: | Unicode |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 05-Nov-2019 10:32:29 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000110 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 05-Nov-2019 10:32:29 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0008DCC4 | 0x0008DE00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.67612 |
.rdata | 0x0008F000 | 0x0002E10E | 0x0002E200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.76011 |
.data | 0x000BE000 | 0x00008F74 | 0x00005200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 1.19875 |
.rsrc | 0x000C7000 | 0x0005CE18 | 0x0005D000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.843 |
.reloc | 0x00124000 | 0x0000711C | 0x00007200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.77903 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.40026 | 1007 | Latin 1 / Western European | English - United Kingdom | RT_MANIFEST |
2 | 2.05883 | 296 | Latin 1 / Western European | English - United Kingdom | RT_ICON |
3 | 2.25499 | 296 | Latin 1 / Western European | English - United Kingdom | RT_ICON |
4 | 3.07937 | 1128 | Latin 1 / Western European | English - United Kingdom | RT_ICON |
5 | 7.87682 | 6922 | Latin 1 / Western European | English - United Kingdom | RT_ICON |
6 | 2.24641 | 9640 | Latin 1 / Western European | English - United Kingdom | RT_ICON |
7 | 3.34702 | 1428 | Latin 1 / Western European | English - United Kingdom | RT_STRING |
8 | 3.2817 | 1674 | Latin 1 / Western European | English - United Kingdom | RT_STRING |
9 | 3.28849 | 1168 | Latin 1 / Western European | English - United Kingdom | RT_STRING |
10 | 3.28373 | 1532 | Latin 1 / Western European | English - United Kingdom | RT_STRING |
Imports
ADVAPI32.dll |
COMCTL32.dll |
COMDLG32.dll |
GDI32.dll |
IPHLPAPI.DLL |
KERNEL32.dll |
MPR.dll |
OLEAUT32.dll |
PSAPI.DLL |
SHELL32.dll |
Total processes
38
Monitored processes
5
Malicious processes
4
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1600 | "C:\Users\admin\AppData\Roaming\services.exe" | C:\Users\admin\AppData\Roaming\services.exe | — | webex.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1796 | "C:\Users\admin\AppData\Roaming\services.exe" | C:\Users\admin\AppData\Roaming\services.exe | services.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2768 | "C:\Users\admin\AppData\Local\Temp\webex.exe" | C:\Users\admin\AppData\Local\Temp\webex.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3736 | "C:\Users\admin\AppData\Local\Temp\webex.exe" | C:\Users\admin\AppData\Local\Temp\webex.exe | webex.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3764 | "C:\Users\admin\AppData\Local\Temp\webex.exe" | C:\Users\admin\AppData\Local\Temp\webex.exe | webex.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
43
Read events
35
Write events
8
Delete events
0
Modification events
| (PID) Process: | (3764) webex.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | MaxConnectionsPer1_0Server |
Value: 10 | |||
| (PID) Process: | (3764) webex.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | MaxConnectionsPerServer |
Value: 10 | |||
| (PID) Process: | (3764) webex.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\WJSRE4FOW2 |
| Operation: | write | Name: | inst |
Value: 3B7518BCACC7D5CFF4F480E4BD9F96F02E3959C83AD61FB9FB56D6EE8196A97897F0C0B042028569836CE9DD869AFEE5946D1836C0FF6011DB54B87CD61B26BC294051F55349515D3B76573F7D02FDE046DAD6FC5E2E0A1C | |||
| (PID) Process: | (3764) webex.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | Google App Update |
Value: C:\Users\admin\AppData\Roaming\services.exe | |||
| (PID) Process: | (3736) webex.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | MaxConnectionsPer1_0Server |
Value: 10 | |||
| (PID) Process: | (3736) webex.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | MaxConnectionsPerServer |
Value: 10 | |||
| (PID) Process: | (1796) services.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | MaxConnectionsPer1_0Server |
Value: 10 | |||
| (PID) Process: | (1796) services.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | MaxConnectionsPerServer |
Value: 10 | |||
Executable files
2
Suspicious files
0
Text files
2
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2768 | webex.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\MusNotificationUx.url | text | |
MD5:— | SHA256:— | |||
| 2768 | webex.exe | C:\Users\admin\MusNotificationUx\avifil32.exe | executable | |
MD5:— | SHA256:— | |||
| 3764 | webex.exe | C:\Users\admin\AppData\Roaming\services.exe | executable | |
MD5:— | SHA256:— | |||
| 2768 | webex.exe | C:\Users\admin\MusNotificationUx\MusNotificationUx.vbs | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
2
DNS requests
1
Threats
12
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3736 | webex.exe | 194.5.97.14:4758 | deaphnote.ddns.net | — | FR | malicious |
1796 | services.exe | 194.5.97.14:4758 | deaphnote.ddns.net | — | FR | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
deaphnote.ddns.net |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1080 | svchost.exe | Potentially Bad Traffic | ET POLICY DNS Query to DynDNS Domain *.ddns .net |
3736 | webex.exe | A Network Trojan was detected | MALWARE [PTsecurity] RAT.Win32.AveMaria |
1796 | services.exe | A Network Trojan was detected | MALWARE [PTsecurity] RAT.Win32.AveMaria |
3736 | webex.exe | A Network Trojan was detected | MALWARE [PTsecurity] AveMaria.RAT Connection |
1796 | services.exe | A Network Trojan was detected | MALWARE [PTsecurity] AveMaria.RAT Connection |
7 ETPRO signatures available at the full report