| File name: | Attachment.1524849.InvoiceNumber-.exe |
| Full analysis: | https://app.any.run/tasks/66262229-0cf5-461e-9d80-c1e5fe293722 |
| Verdict: | Malicious activity |
| Threats: | A keylogger is a type of spyware that infects a system and has the ability to record every keystroke made on the device. This lets attackers collect personal information of victims, which may include their online banking credentials, as well as personal conversations. The most widespread vector of attack leading to a keylogger infection begins with a phishing email or link. Keylogging is also often present in remote access trojans as part of an extended set of malicious tools. |
| Analysis date: | August 21, 2024, 13:54:42 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | 65885A964C90402671DA9671C4904D7B |
| SHA1: | 9F9425C730549B91F6EA011A925AF660C1DE9F87 |
| SHA256: | 788799AE5A044C5F06E5CB0BC746FAEC185DE1B92D7AD641490DD99811699D9C |
| SSDEEP: | 98304:MEFR6mIaJ92A/X+ujTKg6tm8X8GC+JD/I13NH3OLtu+oIgxz2SqNc1Cc+2O:Khzf |
MALICIOUS
Antivirus name has been found in the command line (generic signature)
- findstr.exe (PID: 6748)
- findstr.exe (PID: 6868)
Create files in the Startup directory
- cmd.exe (PID: 7024)
REMCOS has been detected
- Bacteria.pif (PID: 6980)
- Bacteria.pif (PID: 6980)
- Bacteria.pif (PID: 6980)
SUSPICIOUS
Drops the executable file immediately after the start
- Attachment.1524849.InvoiceNumber-.exe (PID: 6640)
- cmd.exe (PID: 6680)
- Bacteria.pif (PID: 6980)
Executing commands from ".cmd" file
- Attachment.1524849.InvoiceNumber-.exe (PID: 6640)
Get information on the list of running processes
- cmd.exe (PID: 6680)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 6680)
Application launched itself
- cmd.exe (PID: 6680)
Starts CMD.EXE for commands execution
- cmd.exe (PID: 6680)
- Attachment.1524849.InvoiceNumber-.exe (PID: 6640)
Drops a file with a rarely used extension (PIF)
- cmd.exe (PID: 6680)
- Bacteria.pif (PID: 6980)
Executable content was dropped or overwritten
- cmd.exe (PID: 6680)
- Bacteria.pif (PID: 6980)
Starts application with an unusual extension
- cmd.exe (PID: 6680)
The executable file from the user directory is run by the CMD process
- Bacteria.pif (PID: 6980)
Reads security settings of Internet Explorer
- Attachment.1524849.InvoiceNumber-.exe (PID: 6640)
Reads the date of Windows installation
- Attachment.1524849.InvoiceNumber-.exe (PID: 6640)
Writes files like Keylogger logs
- Bacteria.pif (PID: 6980)
Connects to unusual port
- Bacteria.pif (PID: 6980)
INFO
Checks supported languages
- Attachment.1524849.InvoiceNumber-.exe (PID: 6640)
- Bacteria.pif (PID: 6980)
Process checks computer location settings
- Attachment.1524849.InvoiceNumber-.exe (PID: 6640)
Reads the computer name
- Attachment.1524849.InvoiceNumber-.exe (PID: 6640)
- Bacteria.pif (PID: 6980)
Create files in a temporary directory
- Attachment.1524849.InvoiceNumber-.exe (PID: 6640)
Reads mouse settings
- Bacteria.pif (PID: 6980)
Creates files or folders in the user directory
- Bacteria.pif (PID: 6980)
Manual execution by a user
- cmd.exe (PID: 7024)
Creates files in the program directory
- Bacteria.pif (PID: 6980)
Reads Environment values
- Bacteria.pif (PID: 6980)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2010:04:10 12:19:38+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 9 |
| CodeSize: | 26624 |
| InitializedDataSize: | 475136 |
| UninitializedDataSize: | 16896 |
| EntryPoint: | 0x3415 |
| OSVersion: | 5 |
| ImageVersion: | 6 |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 4.5253.6.8989 |
| ProductVersionNumber: | 4.5253.6.8989 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| Comments: | Facilitates virtual learning experiences through immersive educational content. |
| CompanyName: | EduVirtu Dynamics |
| FileDescription: | Facilitates virtual learning experiences through immersive educational content. |
| FileVersion: | 4.5253.6.8989 |
| LegalCopyright: | Copyright © EduVirtu Dynamics 2015 All rights reserved. |
| LegalTrademarks: | VirtuLearn is a trademark of EduVirtu Dynamics |
| ProductName: | VirtuLearn |
Total processes
146
Monitored processes
14
Malicious processes
3
Suspicious processes
0
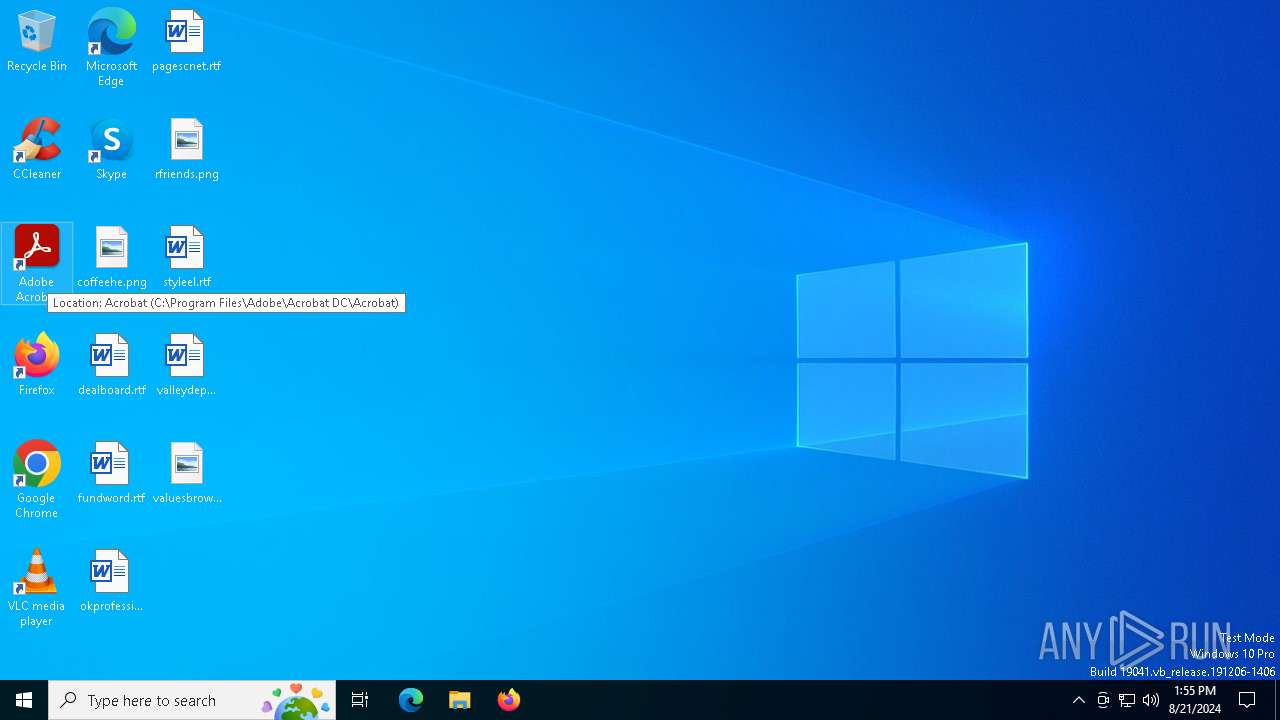
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 6640 | "C:\Users\admin\AppData\Local\Temp\Attachment.1524849.InvoiceNumber-.exe" | C:\Users\admin\AppData\Local\Temp\Attachment.1524849.InvoiceNumber-.exe | explorer.exe | ||||||||||||
User: admin Company: EduVirtu Dynamics Integrity Level: MEDIUM Description: Facilitates virtual learning experiences through immersive educational content. Exit code: 0 Version: 4.5253.6.8989 Modules
| |||||||||||||||
| 6680 | "C:\Windows\System32\cmd.exe" /k move Elvis Elvis.cmd & Elvis.cmd & exit | C:\Windows\SysWOW64\cmd.exe | Attachment.1524849.InvoiceNumber-.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 9009 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6688 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6740 | tasklist | C:\Windows\SysWOW64\tasklist.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Lists the current running tasks Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6748 | findstr /I "wrsa.exe opssvc.exe" | C:\Windows\SysWOW64\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Find String (QGREP) Utility Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6860 | tasklist | C:\Windows\SysWOW64\tasklist.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Lists the current running tasks Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6868 | findstr /I "avastui.exe avgui.exe bdservicehost.exe ekrn.exe nswscsvc.exe sophoshealth.exe" | C:\Windows\SysWOW64\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Find String (QGREP) Utility Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6916 | cmd /c md 526248 | C:\Windows\SysWOW64\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6936 | findstr /V "STYLISHSCHOLARSHIPSOOOLESSONS" Products | C:\Windows\SysWOW64\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Find String (QGREP) Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6960 | cmd /c copy /b ..\Perfume + ..\Detector + ..\Zen + ..\Lessons + ..\Payroll + ..\Biology + ..\Eternal + ..\Neck + ..\Today + ..\Welsh + ..\Spell + ..\Pf g | C:\Windows\SysWOW64\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
4 691
Read events
4 677
Write events
11
Delete events
3
Modification events
| (PID) Process: | (6640) Attachment.1524849.InvoiceNumber-.exe | Key: | HKEY_CURRENT_USER |
| Operation: | delete value | Name: | NurseBudgets |
Value: | |||
| (PID) Process: | (6640) Attachment.1524849.InvoiceNumber-.exe | Key: | HKEY_CURRENT_USER |
| Operation: | delete value | Name: | LibrarianMagical |
Value: | |||
| (PID) Process: | (6640) Attachment.1524849.InvoiceNumber-.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (6640) Attachment.1524849.InvoiceNumber-.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (6640) Attachment.1524849.InvoiceNumber-.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (6640) Attachment.1524849.InvoiceNumber-.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (6640) Attachment.1524849.InvoiceNumber-.exe | Key: | HKEY_CURRENT_USER |
| Operation: | delete value | Name: | AssetsOxford |
Value: | |||
| (PID) Process: | (6980) Bacteria.pif | Key: | HKEY_CURRENT_USER\SOFTWARE\Rmc-66PYM3 |
| Operation: | write | Name: | exepath |
Value: 4A0D8585E74B407CE44AF746F86540BEA6E55A192674B56FBE44EB5913C7E528CA321EEF09B8720B69B6285962D95DB31BC971A4E33F5ACB88147528C03398CC2B6703608D13E82ABF0583BD95FB9EFC0EFBD4089CF2B3A62CA8A8CD61FCE07E8AAF7C124388478DEC992B61 | |||
| (PID) Process: | (6980) Bacteria.pif | Key: | HKEY_CURRENT_USER\SOFTWARE\Rmc-66PYM3 |
| Operation: | write | Name: | licence |
Value: B13C867AD4FAB14114C2C2EACFC86653 | |||
| (PID) Process: | (6980) Bacteria.pif | Key: | HKEY_CURRENT_USER\SOFTWARE\Rmc-66PYM3 |
| Operation: | write | Name: | time |
Value: | |||
Executable files
2
Suspicious files
17
Text files
4
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6640 | Attachment.1524849.InvoiceNumber-.exe | C:\Users\admin\AppData\Local\Temp\Eternal | binary | |
MD5:03EEB504DAA231A37BAE5135BA5F64E8 | SHA256:C44DF8ECA6F19F9C0A7AE49E0AF7D3181F5025AE21BFF9B7A61A7499EF16ED1D | |||
| 6640 | Attachment.1524849.InvoiceNumber-.exe | C:\Users\admin\AppData\Local\Temp\Pci | binary | |
MD5:DEF061969B254BC9A916950A86192BEB | SHA256:A1C4AB767E4B0DD2E88A67A2117B1F0A533852992E50CA6281711182FB342112 | |||
| 6640 | Attachment.1524849.InvoiceNumber-.exe | C:\Users\admin\AppData\Local\Temp\Products | binary | |
MD5:770E6F2DB6B742F019EBCA81A3CBD8C9 | SHA256:852820A106FC80331235CDD60323AE3300D46802A35B0570E79179EDAF67596F | |||
| 6640 | Attachment.1524849.InvoiceNumber-.exe | C:\Users\admin\AppData\Local\Temp\Perfume | binary | |
MD5:2BAB6E1AB209E65D4C817B599E9CB4AA | SHA256:01F3F02DD03603EEA3DDFE6172B1FBC03FC50C1877A249991772B02C679F4837 | |||
| 6640 | Attachment.1524849.InvoiceNumber-.exe | C:\Users\admin\AppData\Local\Temp\Pf | binary | |
MD5:73F37FE7AF6191B73508BD025E9D7FCF | SHA256:F6A85925C40088016422CD91F51672FC34C6A0E450FE6FF5C9F0C6B683E18771 | |||
| 6640 | Attachment.1524849.InvoiceNumber-.exe | C:\Users\admin\AppData\Local\Temp\Detector | binary | |
MD5:8EAAA60C54D73BB04181737D2C517A7C | SHA256:2E3550744B331CD692F248618B3B82CCE25DB16B4CC971C57ACF574E6353C0BB | |||
| 6640 | Attachment.1524849.InvoiceNumber-.exe | C:\Users\admin\AppData\Local\Temp\Zen | binary | |
MD5:D7915329FFD1A9B487BFF139E71F2567 | SHA256:31DE4EF46B161F22F680B3714EDE320AFE56E1210A3D7CBE6D2B6807759AA185 | |||
| 6640 | Attachment.1524849.InvoiceNumber-.exe | C:\Users\admin\AppData\Local\Temp\Lessons | binary | |
MD5:E42028258413CABEAD613E445B13058F | SHA256:FDB699EDFB224C1205108421AA03039419E2FC6F1052AD865B702D1FAF5CB6F2 | |||
| 6640 | Attachment.1524849.InvoiceNumber-.exe | C:\Users\admin\AppData\Local\Temp\Biology | binary | |
MD5:858FC00B8A7BF18962CB57F6DE74EFAD | SHA256:A64CF4F1E7336C0877F4EC13D6F42F70F94975AD305D8842D305727AFC0E27C1 | |||
| 6640 | Attachment.1524849.InvoiceNumber-.exe | C:\Users\admin\AppData\Local\Temp\Payroll | binary | |
MD5:77CC286B6728FFB4C876BBD2A9FAEFC5 | SHA256:72C1C7535FA22AA7A0E46411F7EDC004C3ED15AFF2F748346F88DF165E1193E0 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
72
DNS requests
15
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4592 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6504 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
6936 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3992 | RUXIMICS.exe | 20.73.194.208:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2120 | MoUsoCoreWorker.exe | 20.73.194.208:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
3176 | svchost.exe | 20.73.194.208:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
3176 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3260 | svchost.exe | 40.115.3.253:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4592 | svchost.exe | 20.190.160.14:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | unknown |
4592 | svchost.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
2120 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
6504 | backgroundTaskHost.exe | 20.223.35.26:443 | arc.msn.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
fgTXqomqtXKWm.fgTXqomqtXKWm |
| unknown |
settings-win.data.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
arc.msn.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6980 | Bacteria.pif | Misc Attack | ET DROP Spamhaus DROP Listed Traffic Inbound group 4 |
6980 | Bacteria.pif | Misc Attack | ET DROP Spamhaus DROP Listed Traffic Inbound group 13 |