| File name: | 8af2031c4745713568d61010c97583fed974129f613ff5f2285ea5e294fa5311.zip |
| Full analysis: | https://app.any.run/tasks/3c3daf05-67af-4ac9-8968-9311431572a9 |
| Verdict: | Malicious activity |
| Threats: | Agent Tesla is spyware that collects information about the actions of its victims by recording keystrokes and user interactions. It is falsely marketed as a legitimate software on the dedicated website where this malware is sold. |
| Analysis date: | May 15, 2025, 18:59:32 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
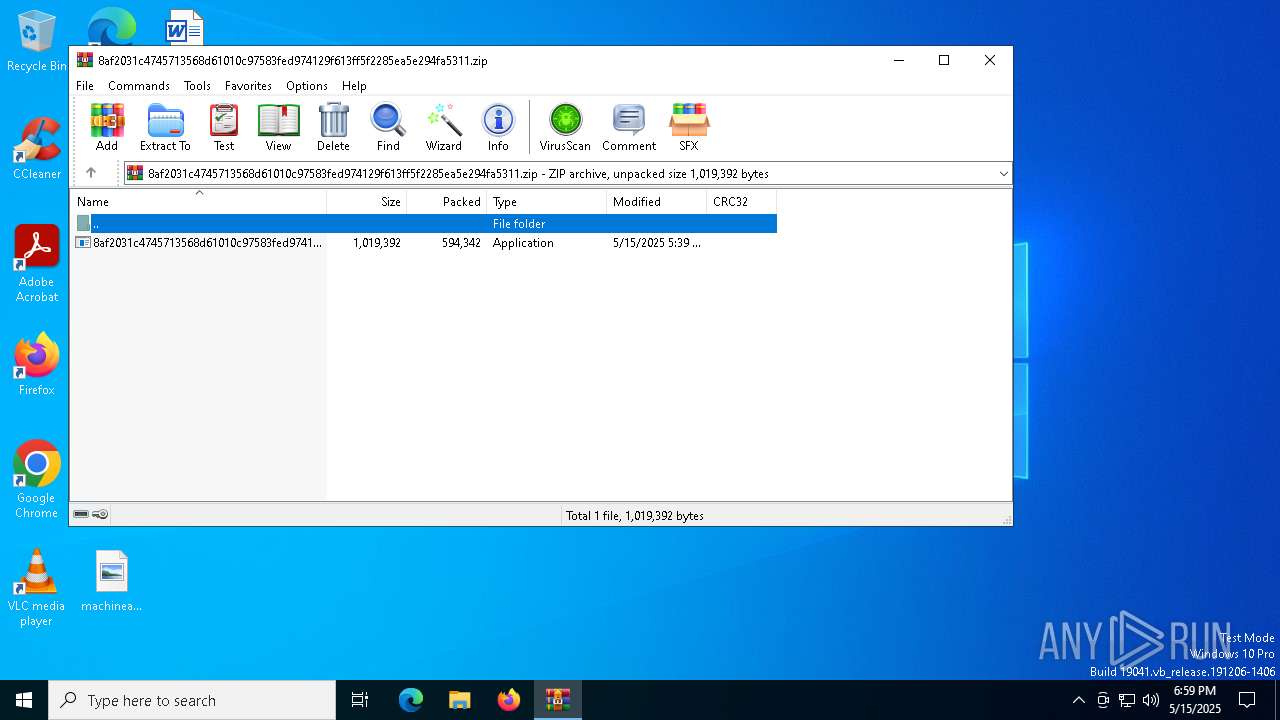
| MIME: | application/zip |
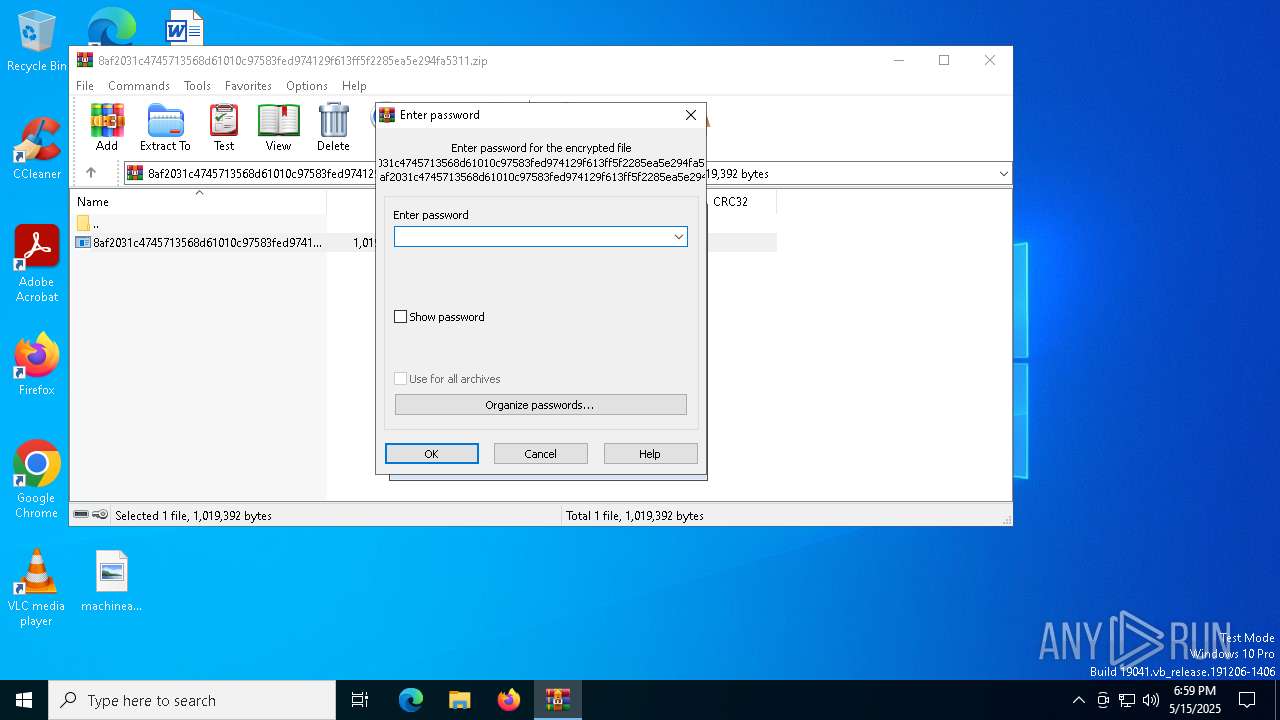
| File info: | Zip archive data, at least v5.1 to extract, compression method=AES Encrypted |
| MD5: | 13E825F14B2BCE3327CAD9208C56E2B7 |
| SHA1: | 17F0BD3F964BBEEC78959C99497560EF15096969 |
| SHA256: | 77CC3B33C791A968514041FCE5D38D84F0DDA9045BFAA401B91F2A2474763965 |
| SSDEEP: | 24576:drvdnpR/t1DwRYMSK9XOyWXcnqVu9pHxY2xVapua9rfl0GAsN:drvdnpR/t1DwRYMSK9XOyWXcnqVu9pHK |
MALICIOUS
Generic archive extractor
- WinRAR.exe (PID: 3676)
AGENTTESLA has been found (auto)
- WinRAR.exe (PID: 3676)
Actions looks like stealing of personal data
- RegSvcs.exe (PID: 4756)
Steals credentials from Web Browsers
- RegSvcs.exe (PID: 4756)
AGENTTESLA has been detected (YARA)
- RegSvcs.exe (PID: 4756)
SUSPICIOUS
Checks for external IP
- RegSvcs.exe (PID: 4756)
The process connected to a server suspected of theft
- RegSvcs.exe (PID: 4756)
Process communicates with Telegram (possibly using it as an attacker's C2 server)
- RegSvcs.exe (PID: 4756)
Possible usage of Discord/Telegram API has been detected (YARA)
- RegSvcs.exe (PID: 4756)
INFO
Reads mouse settings
- 8af2031c4745713568d61010c97583fed974129f613ff5f2285ea5e294fa5311.exe (PID: 4740)
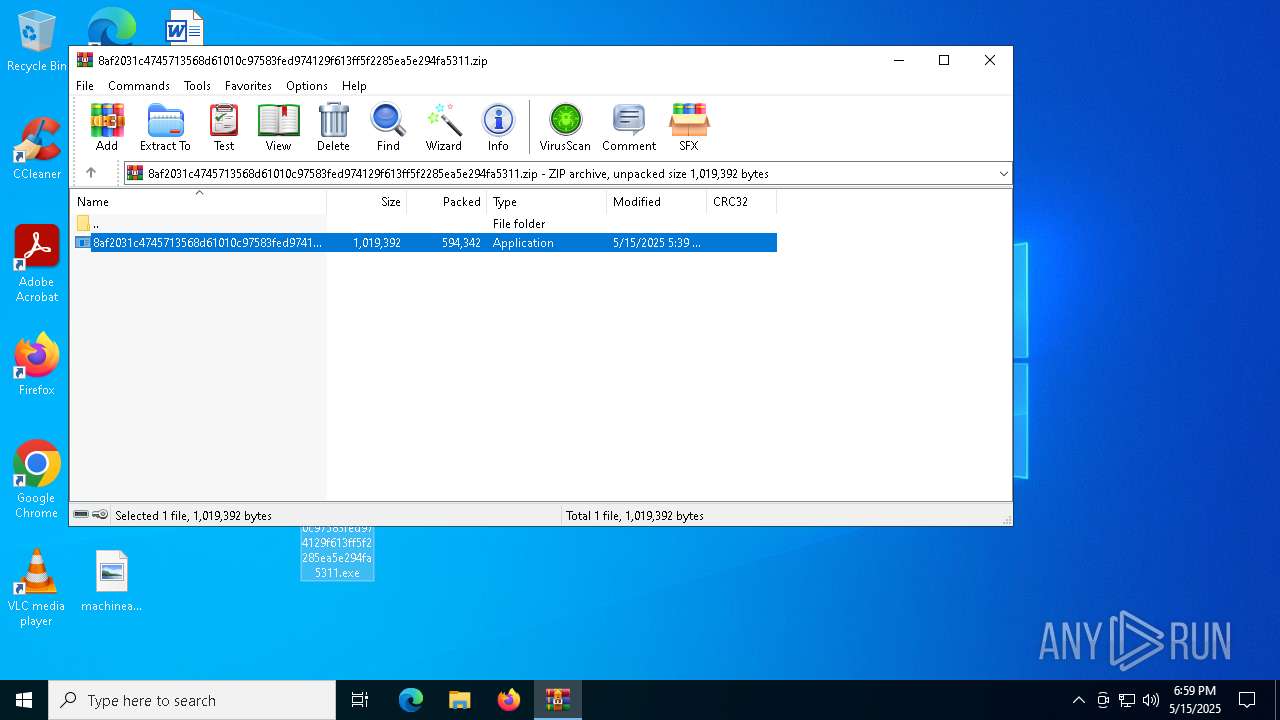
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3676)
Manual execution by a user
- 8af2031c4745713568d61010c97583fed974129f613ff5f2285ea5e294fa5311.exe (PID: 4740)
Reads the computer name
- RegSvcs.exe (PID: 4756)
Create files in a temporary directory
- 8af2031c4745713568d61010c97583fed974129f613ff5f2285ea5e294fa5311.exe (PID: 4740)
Checks supported languages
- 8af2031c4745713568d61010c97583fed974129f613ff5f2285ea5e294fa5311.exe (PID: 4740)
- RegSvcs.exe (PID: 4756)
Disables trace logs
- RegSvcs.exe (PID: 4756)
Checks proxy server information
- RegSvcs.exe (PID: 4756)
Reads the software policy settings
- RegSvcs.exe (PID: 4756)
Reads the machine GUID from the registry
- RegSvcs.exe (PID: 4756)
ULTRAVNC has been detected
- RegSvcs.exe (PID: 4756)
The sample compiled with english language support
- WinRAR.exe (PID: 3676)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
AgentTesla
(PID) Process(4756) RegSvcs.exe
C2https://api.telegram.org/bot5656780330:AAHZyLIE6okSCdG1d9lg5RtZ3MsApsmed3U/
ims-api
(PID) Process(4756) RegSvcs.exe
Telegram-Tokens (1)5656780330:AAHZyLIE6okSCdG1d9lg5RtZ3MsApsmed3U
Telegram-Info-Links
5656780330:AAHZyLIE6okSCdG1d9lg5RtZ3MsApsmed3U
Get info about bothttps://api.telegram.org/bot5656780330:AAHZyLIE6okSCdG1d9lg5RtZ3MsApsmed3U/getMe
Get incoming updateshttps://api.telegram.org/bot5656780330:AAHZyLIE6okSCdG1d9lg5RtZ3MsApsmed3U/getUpdates
Get webhookhttps://api.telegram.org/bot5656780330:AAHZyLIE6okSCdG1d9lg5RtZ3MsApsmed3U/getWebhookInfo
Delete webhookhttps://api.telegram.org/bot5656780330:AAHZyLIE6okSCdG1d9lg5RtZ3MsApsmed3U/deleteWebhook
Drop incoming updateshttps://api.telegram.org/bot5656780330:AAHZyLIE6okSCdG1d9lg5RtZ3MsApsmed3U/deleteWebhook?drop_pending_updates=true
Telegram-Requests
Token5656780330:AAHZyLIE6okSCdG1d9lg5RtZ3MsApsmed3U
End-PointsendDocument
Args
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 51 |
|---|---|
| ZipBitFlag: | 0x0003 |
| ZipCompression: | Unknown (99) |
| ZipModifyDate: | 2025:05:15 17:39:20 |
| ZipCRC: | 0x4f6b25d1 |
| ZipCompressedSize: | 594342 |
| ZipUncompressedSize: | 1019392 |
| ZipFileName: | 8af2031c4745713568d61010c97583fed974129f613ff5f2285ea5e294fa5311.exe |
Total processes
133
Monitored processes
5
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 896 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | — | SppExtComObj.Exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3676 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\AppData\Local\Temp\8af2031c4745713568d61010c97583fed974129f613ff5f2285ea5e294fa5311.zip | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
| 4740 | "C:\Users\admin\Desktop\8af2031c4745713568d61010c97583fed974129f613ff5f2285ea5e294fa5311.exe" | C:\Users\admin\Desktop\8af2031c4745713568d61010c97583fed974129f613ff5f2285ea5e294fa5311.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 4756 | "C:\Users\admin\Desktop\8af2031c4745713568d61010c97583fed974129f613ff5f2285ea5e294fa5311.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\RegSvcs.exe | 8af2031c4745713568d61010c97583fed974129f613ff5f2285ea5e294fa5311.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft .NET Services Installation Utility Version: 4.8.9037.0 built by: NET481REL1 Modules
AgentTesla(PID) Process(4756) RegSvcs.exe C2https://api.telegram.org/bot5656780330:AAHZyLIE6okSCdG1d9lg5RtZ3MsApsmed3U/ ims-api(PID) Process(4756) RegSvcs.exe Telegram-Tokens (1)5656780330:AAHZyLIE6okSCdG1d9lg5RtZ3MsApsmed3U Telegram-Info-Links 5656780330:AAHZyLIE6okSCdG1d9lg5RtZ3MsApsmed3U Get info about bothttps://api.telegram.org/bot5656780330:AAHZyLIE6okSCdG1d9lg5RtZ3MsApsmed3U/getMe Get incoming updateshttps://api.telegram.org/bot5656780330:AAHZyLIE6okSCdG1d9lg5RtZ3MsApsmed3U/getUpdates Get webhookhttps://api.telegram.org/bot5656780330:AAHZyLIE6okSCdG1d9lg5RtZ3MsApsmed3U/getWebhookInfo Delete webhookhttps://api.telegram.org/bot5656780330:AAHZyLIE6okSCdG1d9lg5RtZ3MsApsmed3U/deleteWebhook Drop incoming updateshttps://api.telegram.org/bot5656780330:AAHZyLIE6okSCdG1d9lg5RtZ3MsApsmed3U/deleteWebhook?drop_pending_updates=true Telegram-Requests Token5656780330:AAHZyLIE6okSCdG1d9lg5RtZ3MsApsmed3U End-PointsendDocument Args | |||||||||||||||
| 4812 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
2 686
Read events
2 663
Write events
23
Delete events
0
Modification events
| (PID) Process: | (3676) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (3676) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (3676) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (3676) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\8af2031c4745713568d61010c97583fed974129f613ff5f2285ea5e294fa5311.zip | |||
| (PID) Process: | (3676) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3676) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3676) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3676) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (3676) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
| (PID) Process: | (4756) RegSvcs.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\RegSvcs_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
Executable files
1
Suspicious files
3
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3676 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb3676.39242\8af2031c4745713568d61010c97583fed974129f613ff5f2285ea5e294fa5311.exe | executable | |
MD5:645D95E1354A66C2F19DF6AFBF0E710C | SHA256:8AF2031C4745713568D61010C97583FED974129F613FF5F2285EA5E294FA5311 | |||
| 4740 | 8af2031c4745713568d61010c97583fed974129f613ff5f2285ea5e294fa5311.exe | C:\Users\admin\AppData\Local\Temp\autEEA7.tmp | binary | |
MD5:7DEC24821D169028C975E88D5EF5CB11 | SHA256:F30D87142ABB61954C82765A3972EBC0357946E9C54CEDC8F13AFB93ABCBC39F | |||
| 4740 | 8af2031c4745713568d61010c97583fed974129f613ff5f2285ea5e294fa5311.exe | C:\Users\admin\AppData\Local\Temp\unrosined | binary | |
MD5:95033B396CA2B1EE7909AD22B447805F | SHA256:613D0AE73195C5BCBEC4767D1F7F8BFDF0EF98DFCD9AA188CB91FC0EFE8BCFF3 | |||
| 4740 | 8af2031c4745713568d61010c97583fed974129f613ff5f2285ea5e294fa5311.exe | C:\Users\admin\AppData\Local\Temp\autEEC8.tmp | binary | |
MD5:4700903CC215F0C4557D17EFC6CFA37A | SHA256:D35F69B3A71EC5AB962917C4744D84154A94141F5424E2F32123F65A6ECAEB77 | |||
| 4740 | 8af2031c4745713568d61010c97583fed974129f613ff5f2285ea5e294fa5311.exe | C:\Users\admin\AppData\Local\Temp\Gehman | text | |
MD5:8C5062AA14672989F1501D0CEC531754 | SHA256:28D71B44BEDB9666F17BB2BEB463DF690DCE590E5D0365450A00DD546397330D | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
21
DNS requests
17
Threats
7
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.48.23.156:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
1672 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
1672 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.48.23.156:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
— | — | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
3216 | svchost.exe | 172.211.123.248:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
6544 | svchost.exe | 40.126.31.0:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6544 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
2104 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
api.ipify.org |
| shared |
api.telegram.org |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | Misc activity | ET INFO External IP Lookup Domain (ipify .org) in DNS Lookup |
4756 | RegSvcs.exe | Misc activity | ET INFO External IP Address Lookup Domain (ipify .org) in TLS SNI |
2196 | svchost.exe | Misc activity | SUSPICIOUS [ANY.RUN] Possible sending an external IP address to Telegram |
2196 | svchost.exe | Misc activity | ET HUNTING Telegram API Domain in DNS Lookup |
4756 | RegSvcs.exe | Misc activity | ET HUNTING Observed Telegram API Domain (api .telegram .org in TLS SNI) |
4756 | RegSvcs.exe | Misc activity | ET HUNTING Telegram API Certificate Observed |
4756 | RegSvcs.exe | Successful Credential Theft Detected | STEALER [ANY.RUN] Attempt to exfiltrate via Telegram |