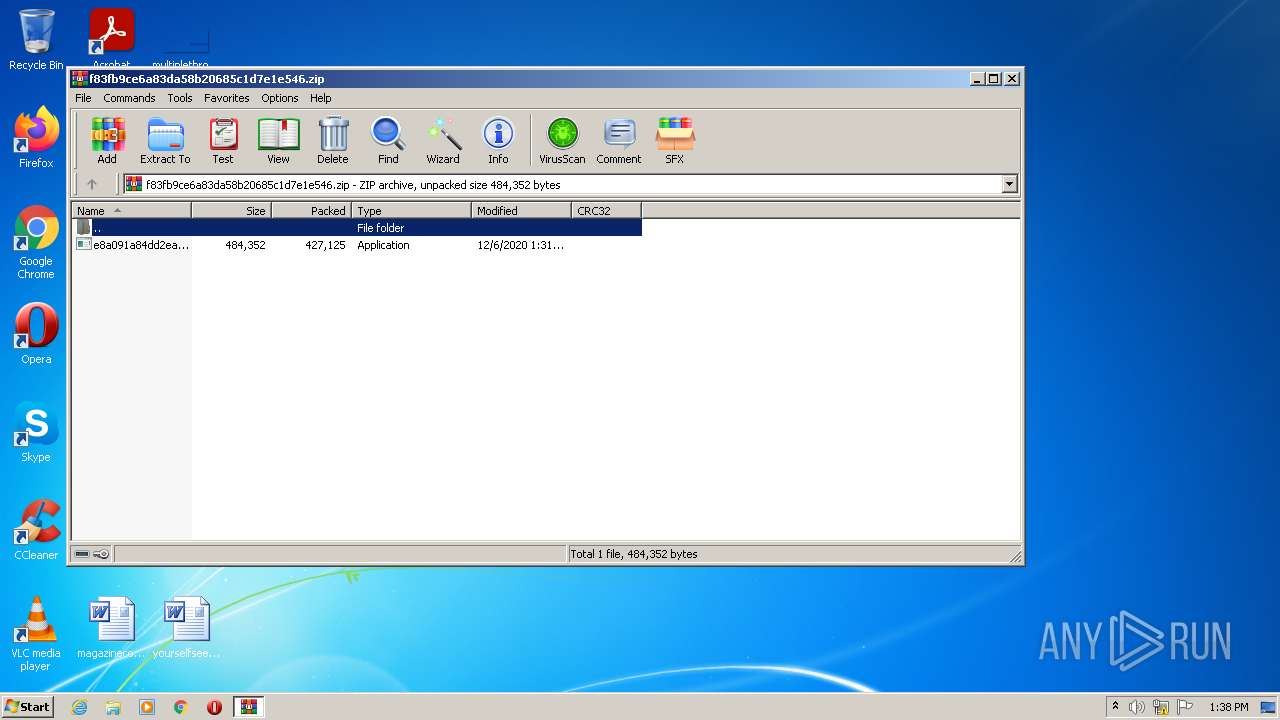
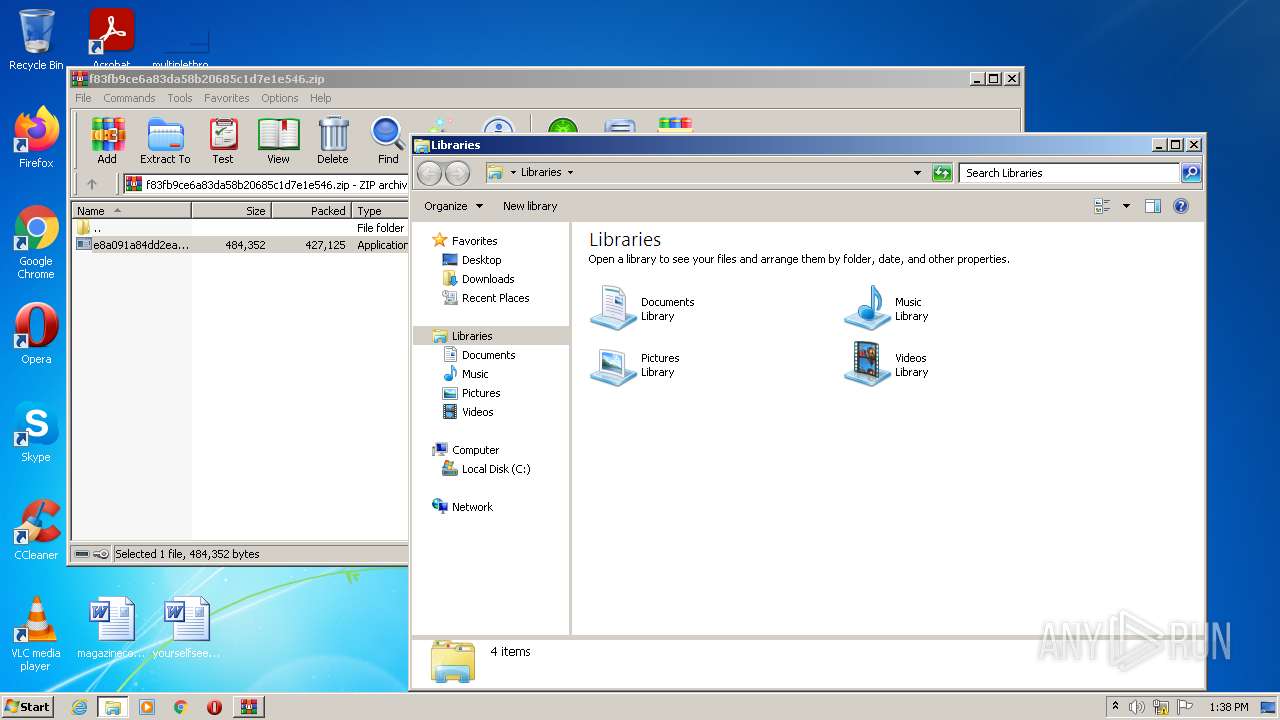
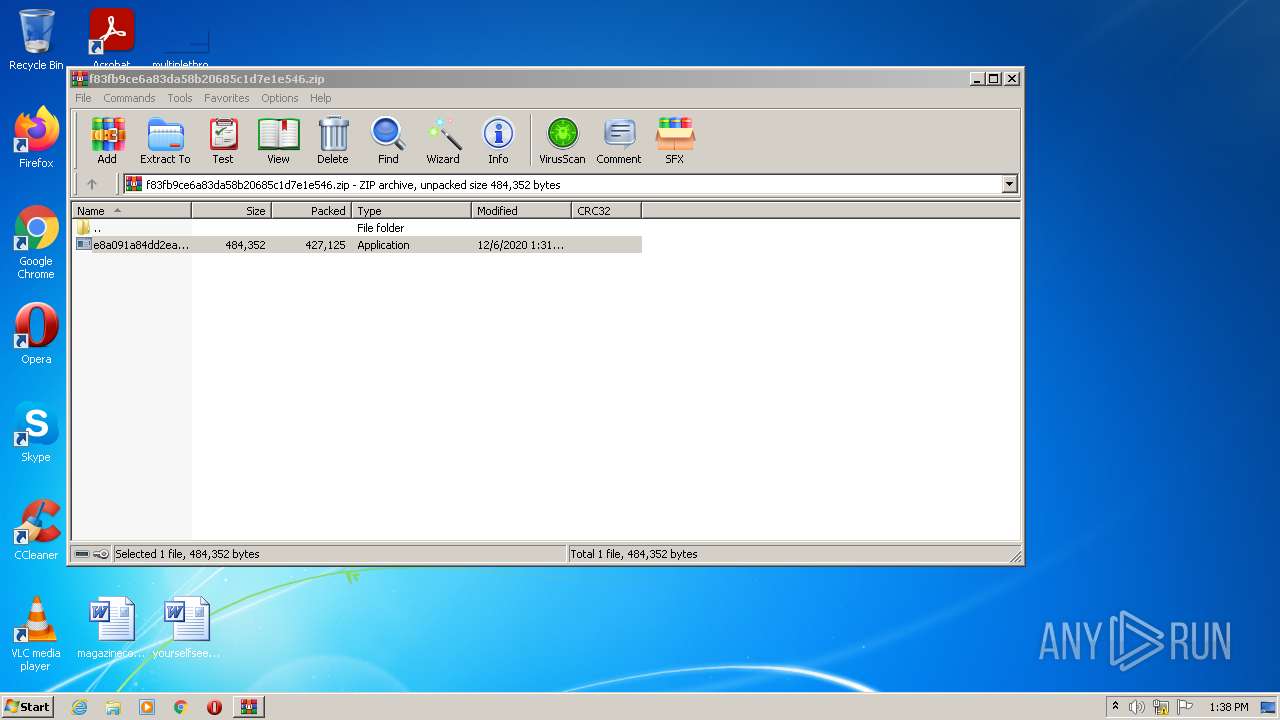
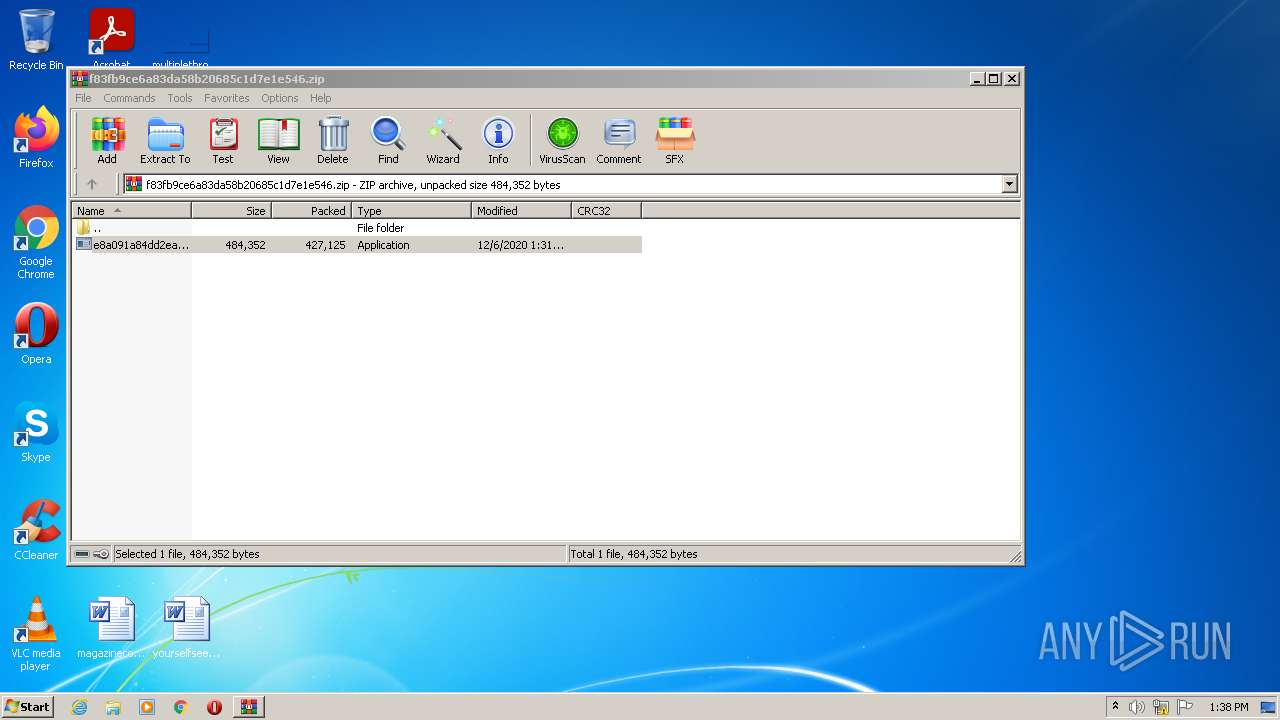
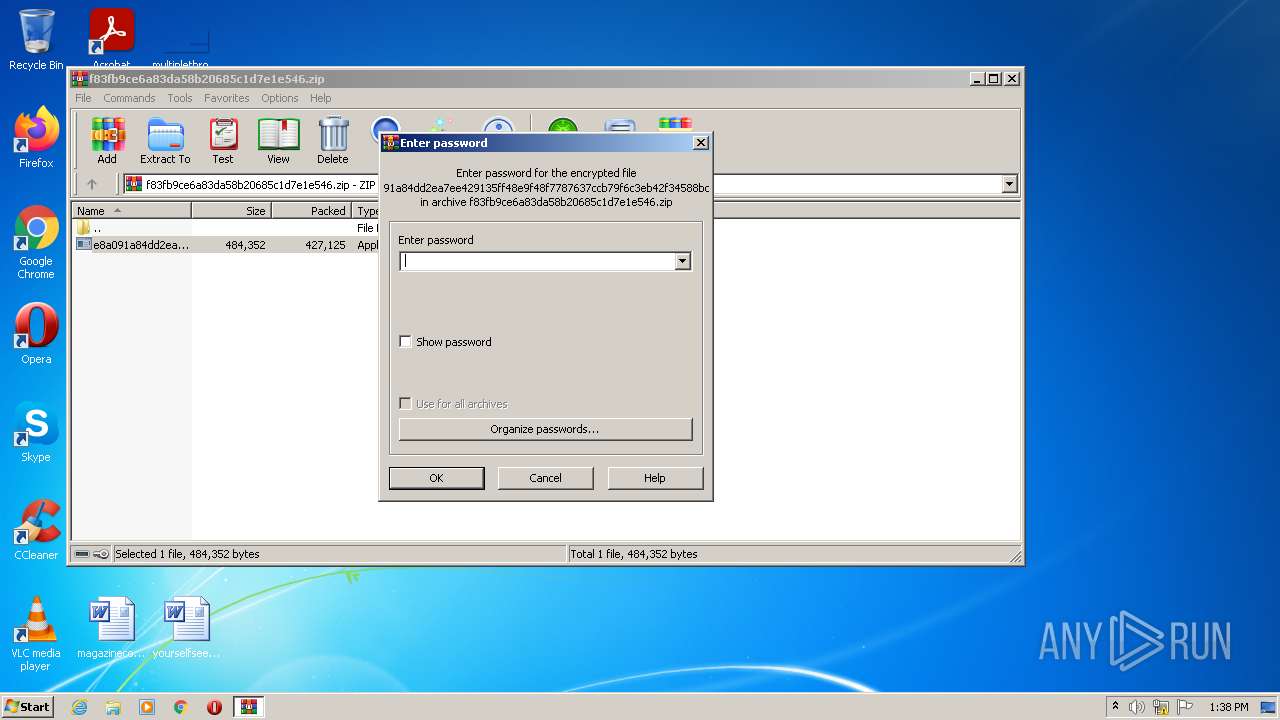
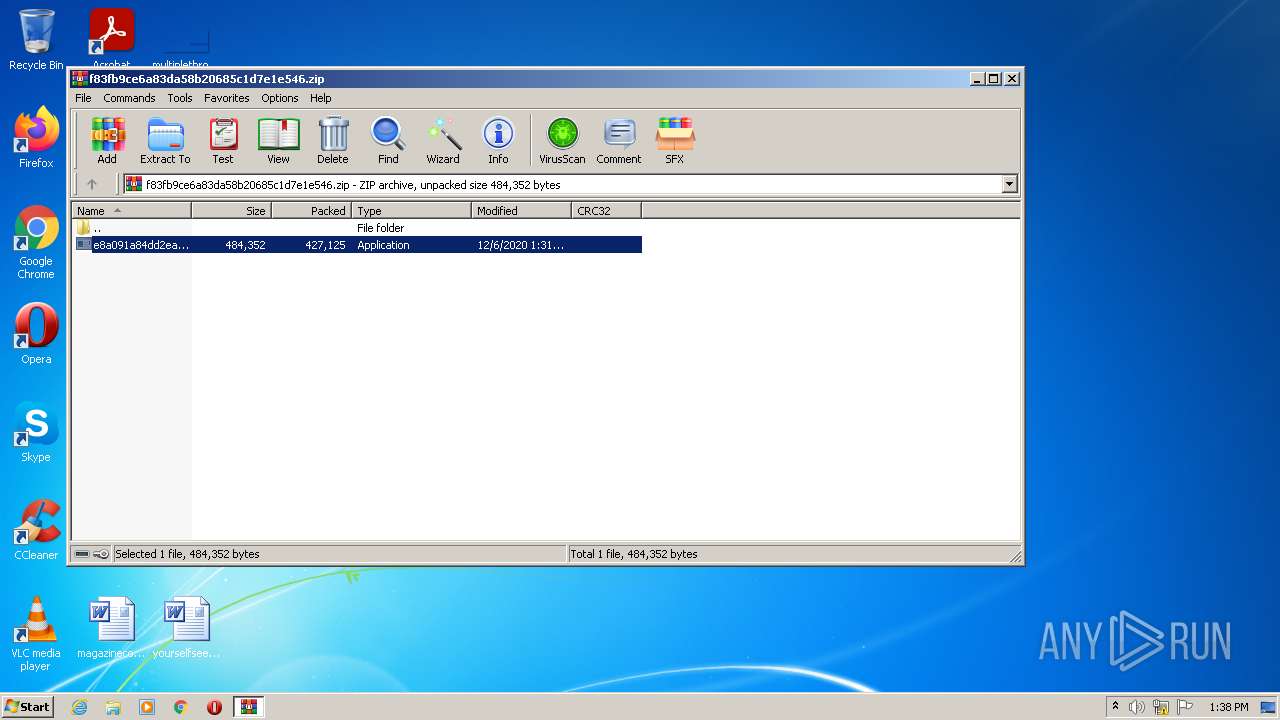
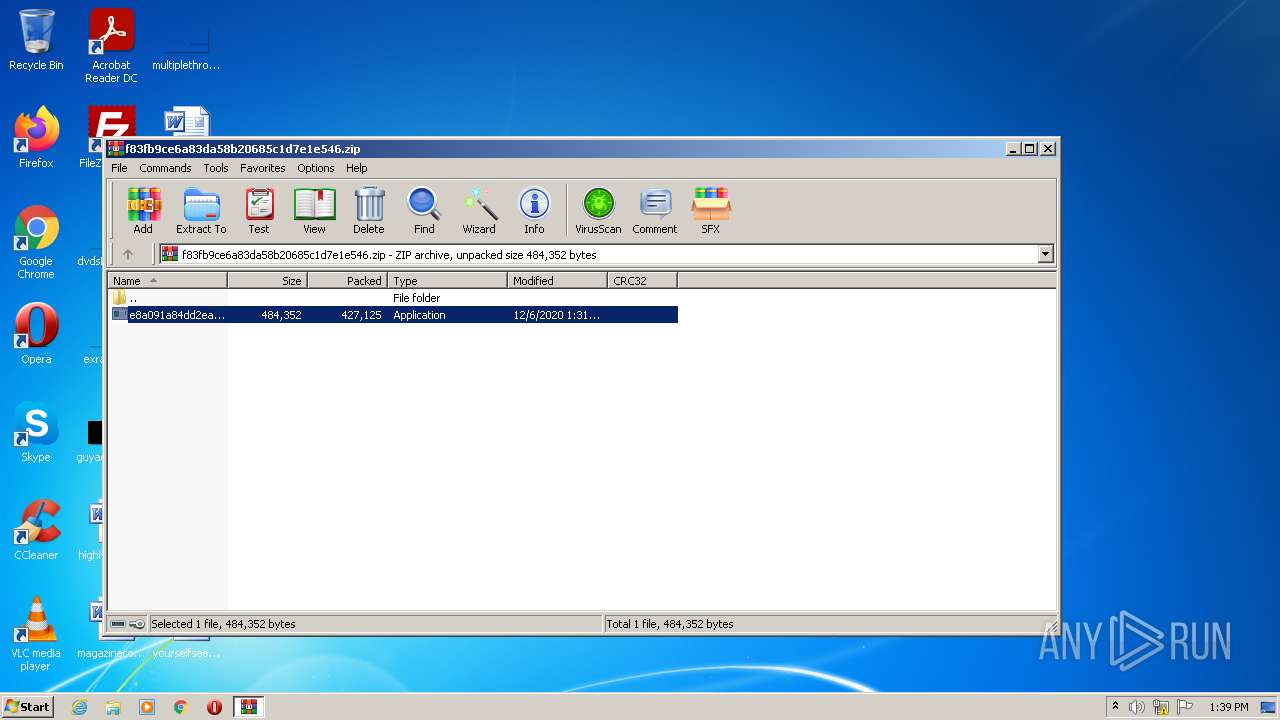
| File name: | f83fb9ce6a83da58b20685c1d7e1e546.zip |
| Full analysis: | https://app.any.run/tasks/0c0e891c-5d33-48cc-8a26-e8082f55e38c |
| Verdict: | Malicious activity |
| Threats: | Maze is ransomware — a malware type that encrypts the victim’s files and restores the data in exchange for a ransom payment. One of the most distinguishable features of Maze is that it is one of the first malware of the kind to publicly release stolen data. |
| Analysis date: | June 27, 2022, 12:38:08 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v5.1 to extract |
| MD5: | A024E1D53D75EAEFC4AA74131FF16FD8 |
| SHA1: | CFD053A7E793EC84EC78679F224B417C760E0A5E |
| SHA256: | 77B2731FF3C7A14B8B962EA387C41293415B3478E73973888851991105777560 |
| SSDEEP: | 12288:6Zr2Dvm+2LDF+jgcz5jCDiIuexi3FBUzvASSB7d:6ZCDvmRLDwjPrIuekUz4SS5 |
MALICIOUS
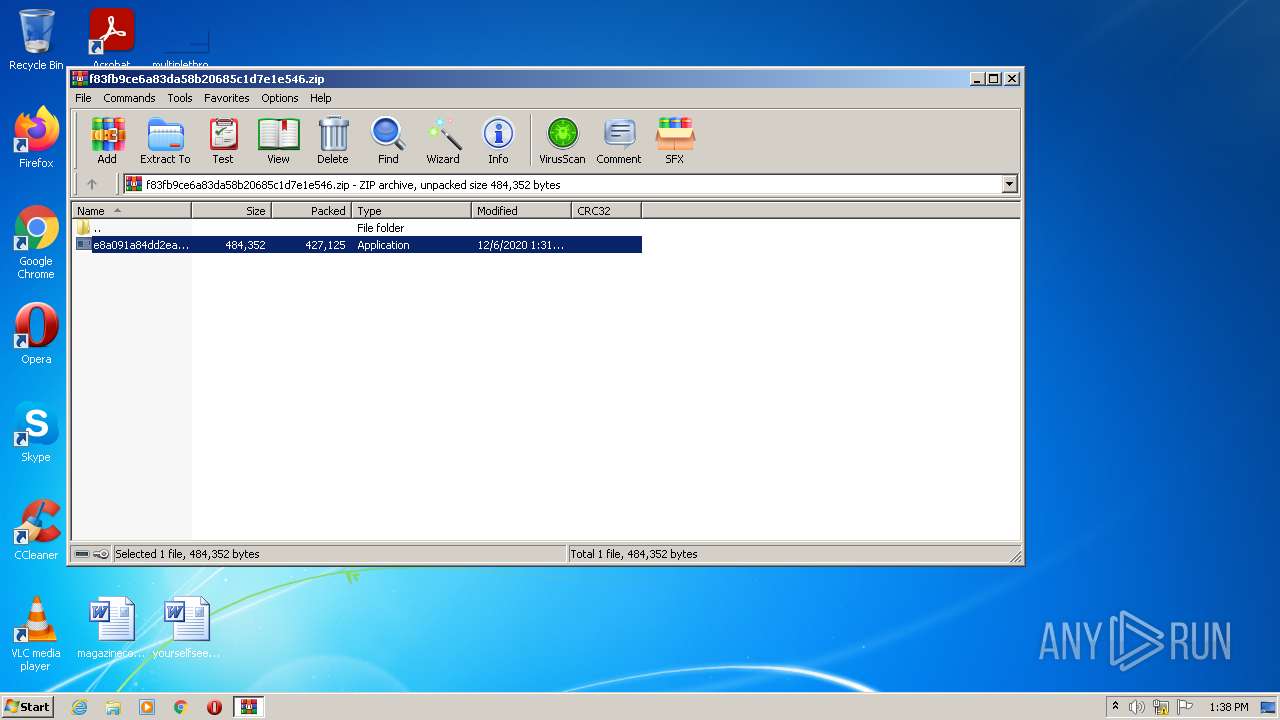
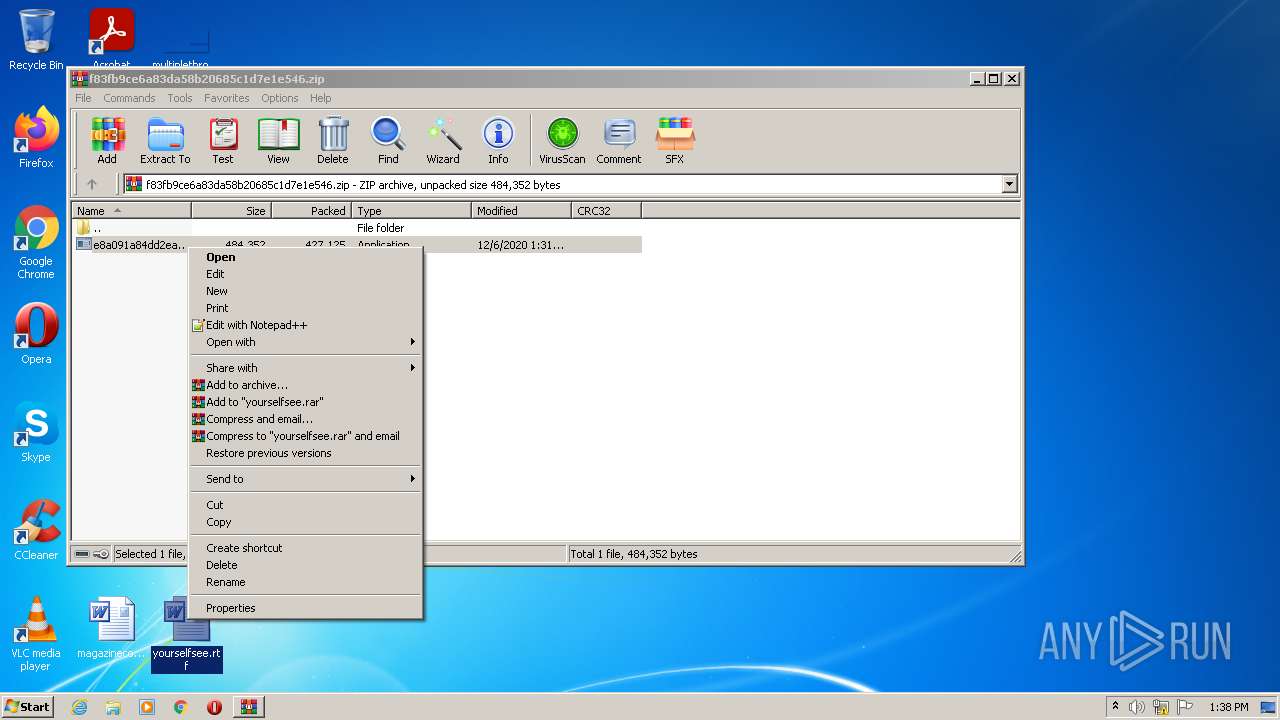
Application was dropped or rewritten from another process
- e8a091a84dd2ea7ee429135ff48e9f48f7787637ccb79f6c3eb42f34588bc684.exe (PID: 1244)
- e8a091a84dd2ea7ee429135ff48e9f48f7787637ccb79f6c3eb42f34588bc684.exe (PID: 4008)
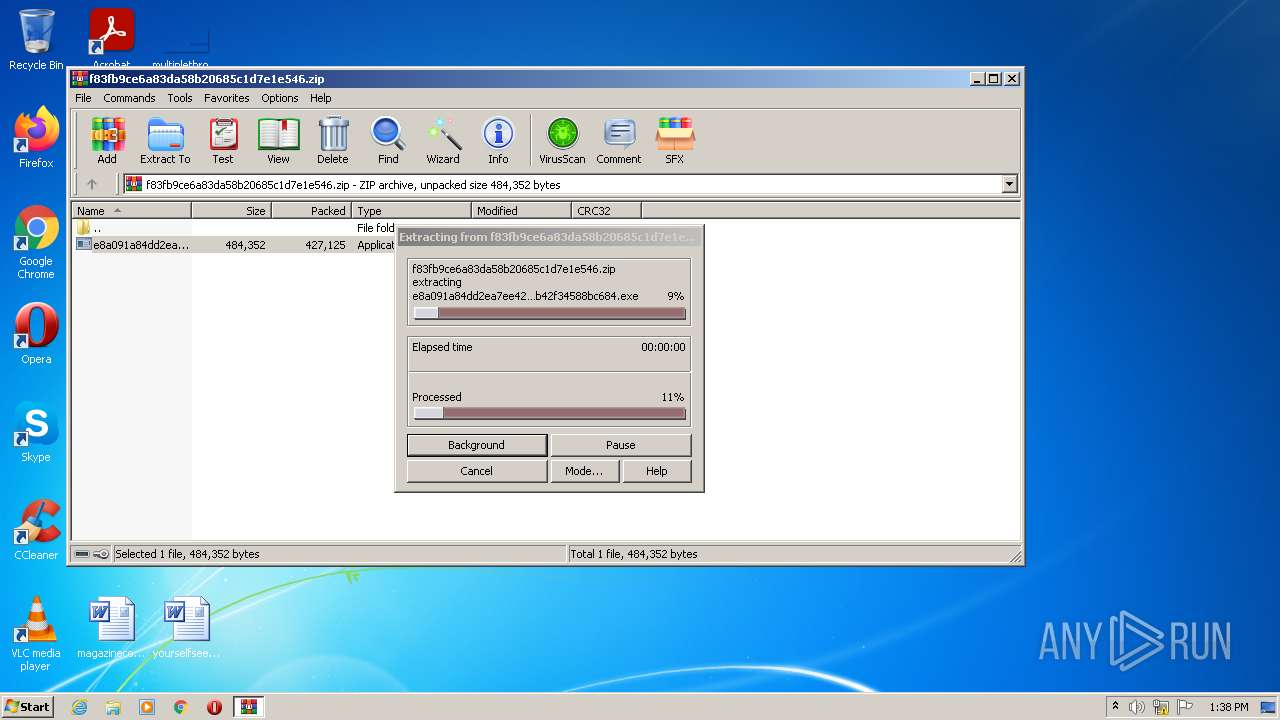
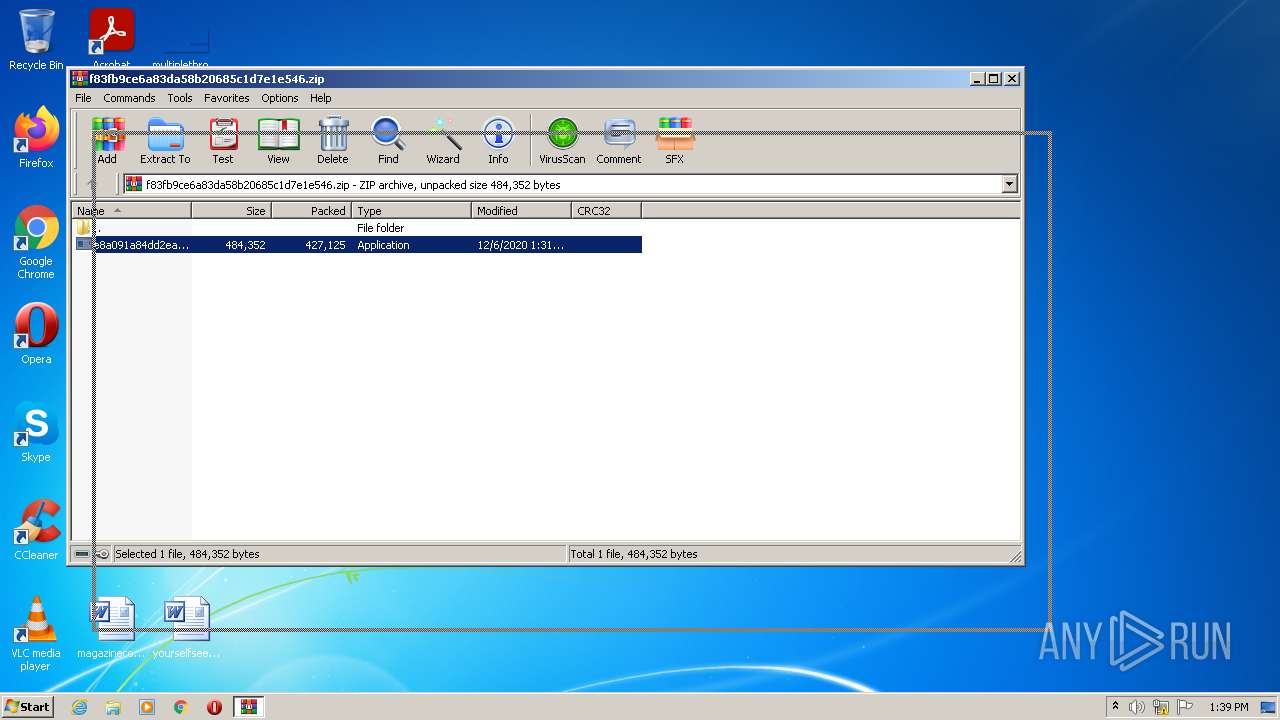
Drops executable file immediately after starts
- WinRAR.exe (PID: 2508)
- e8a091a84dd2ea7ee429135ff48e9f48f7787637ccb79f6c3eb42f34588bc684.exe (PID: 1244)
MAZE was detected
- e8a091a84dd2ea7ee429135ff48e9f48f7787637ccb79f6c3eb42f34588bc684.exe (PID: 1244)
Deletes shadow copies
- e8a091a84dd2ea7ee429135ff48e9f48f7787637ccb79f6c3eb42f34588bc684.exe (PID: 1244)
Maze ransom note found
- e8a091a84dd2ea7ee429135ff48e9f48f7787637ccb79f6c3eb42f34588bc684.exe (PID: 1244)
Modifies files in Chrome extension folder
- e8a091a84dd2ea7ee429135ff48e9f48f7787637ccb79f6c3eb42f34588bc684.exe (PID: 1244)
SUSPICIOUS
Checks supported languages
- e8a091a84dd2ea7ee429135ff48e9f48f7787637ccb79f6c3eb42f34588bc684.exe (PID: 1244)
- WinRAR.exe (PID: 2508)
- wmic.exe (PID: 3512)
- e8a091a84dd2ea7ee429135ff48e9f48f7787637ccb79f6c3eb42f34588bc684.exe (PID: 4008)
Reads the computer name
- WinRAR.exe (PID: 2508)
- e8a091a84dd2ea7ee429135ff48e9f48f7787637ccb79f6c3eb42f34588bc684.exe (PID: 1244)
- e8a091a84dd2ea7ee429135ff48e9f48f7787637ccb79f6c3eb42f34588bc684.exe (PID: 4008)
- wmic.exe (PID: 3512)
Drops a file with a compile date too recent
- WinRAR.exe (PID: 2508)
- e8a091a84dd2ea7ee429135ff48e9f48f7787637ccb79f6c3eb42f34588bc684.exe (PID: 1244)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2508)
Reads Environment values
- e8a091a84dd2ea7ee429135ff48e9f48f7787637ccb79f6c3eb42f34588bc684.exe (PID: 1244)
- e8a091a84dd2ea7ee429135ff48e9f48f7787637ccb79f6c3eb42f34588bc684.exe (PID: 4008)
Creates files in the program directory
- e8a091a84dd2ea7ee429135ff48e9f48f7787637ccb79f6c3eb42f34588bc684.exe (PID: 1244)
INFO
Checks supported languages
- explorer.exe (PID: 1276)
- WINWORD.EXE (PID: 1940)
Reads the computer name
- explorer.exe (PID: 1276)
- WINWORD.EXE (PID: 1940)
Manual execution by user
- explorer.exe (PID: 1276)
- WINWORD.EXE (PID: 1940)
Creates files in the user directory
- WINWORD.EXE (PID: 1940)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 1940)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
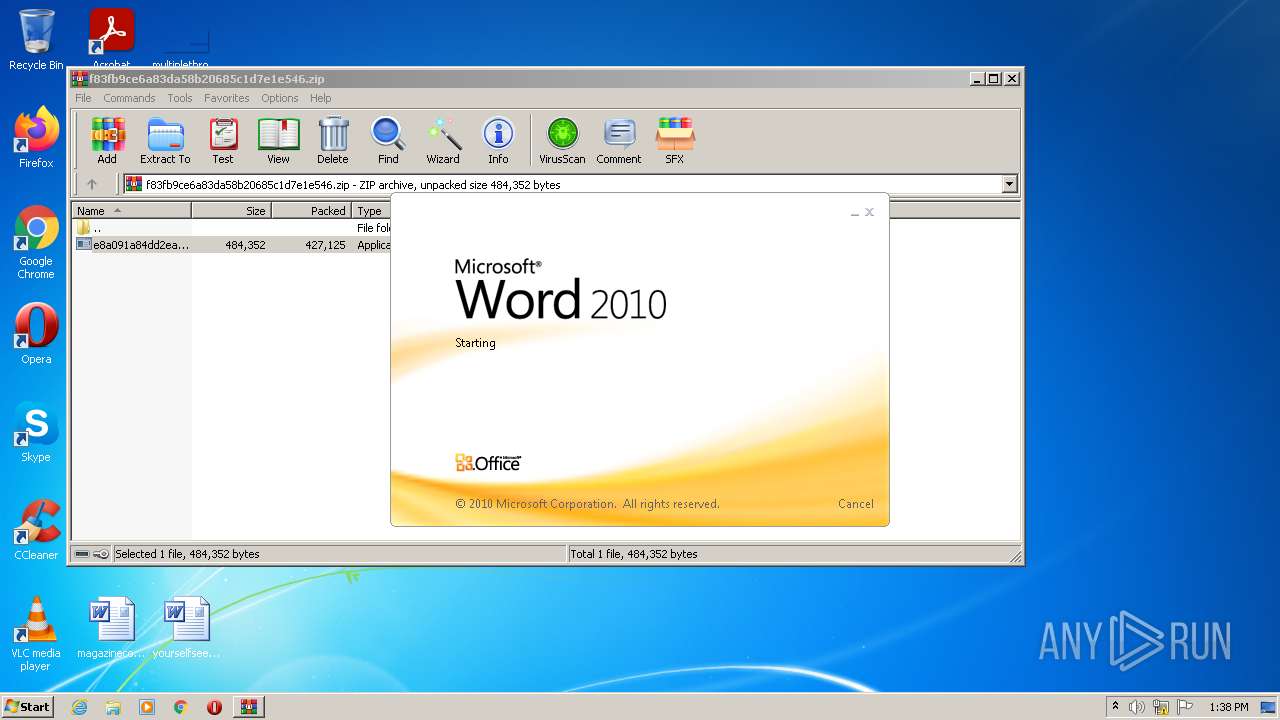
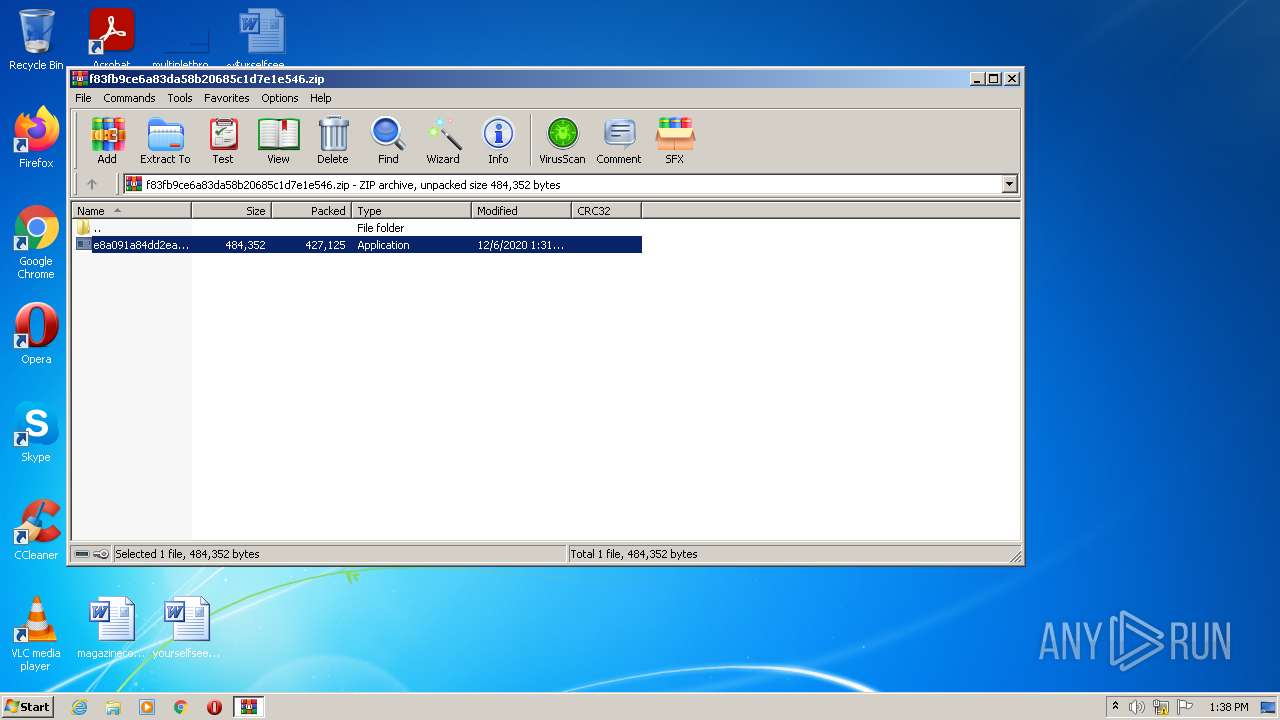
| ZipFileName: | e8a091a84dd2ea7ee429135ff48e9f48f7787637ccb79f6c3eb42f34588bc684.exe |
|---|---|
| ZipUncompressedSize: | 484352 |
| ZipCompressedSize: | 427125 |
| ZipCRC: | 0x3e6fd65f |
| ZipModifyDate: | 2020:12:06 13:31:04 |
| ZipCompression: | Unknown (99) |
| ZipBitFlag: | 0x0003 |
| ZipRequiredVersion: | 51 |
Total processes
43
Monitored processes
6
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1244 | "C:\Users\admin\AppData\Local\Temp\Rar$EXb2508.15318\e8a091a84dd2ea7ee429135ff48e9f48f7787637ccb79f6c3eb42f34588bc684.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXb2508.15318\e8a091a84dd2ea7ee429135ff48e9f48f7787637ccb79f6c3eb42f34588bc684.exe | WinRAR.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1276 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
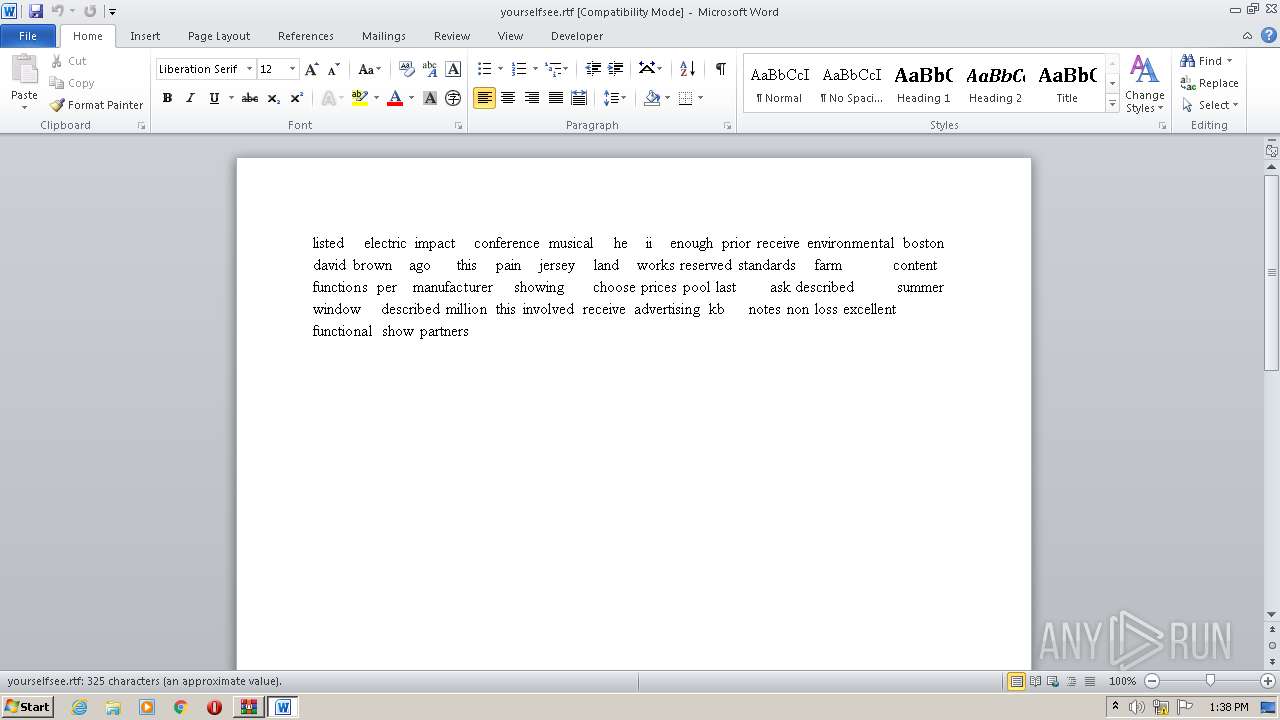
| 1940 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\yourselfsee.rtf" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
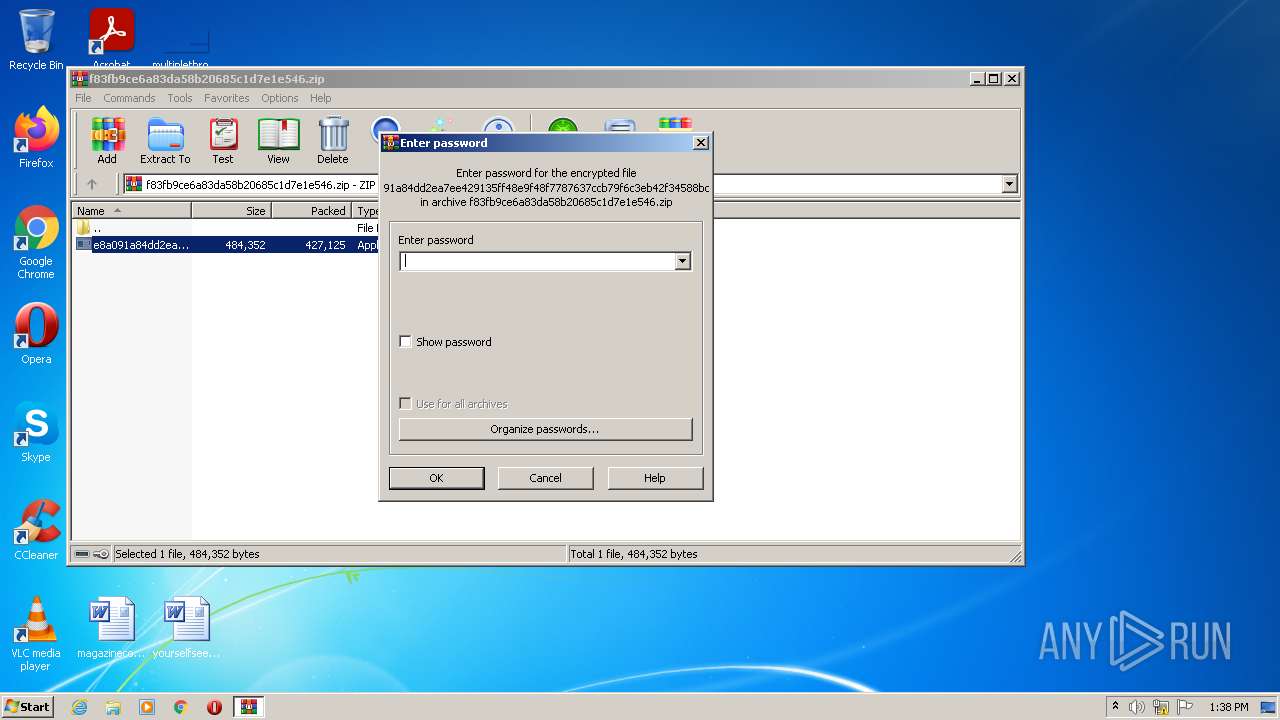
| 2508 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\f83fb9ce6a83da58b20685c1d7e1e546.zip" | C:\Program Files\WinRAR\WinRAR.exe | Explorer.EXE | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 3512 | "C:\pqvl\..\Windows\yof\qb\pjxa\..\..\..\system32\met\..\wbem\n\job\liwtb\..\..\..\wmic.exe" shadowcopy delete | C:\Windows\system32\wbem\wmic.exe | — | e8a091a84dd2ea7ee429135ff48e9f48f7787637ccb79f6c3eb42f34588bc684.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: WMI Commandline Utility Exit code: 2147749908 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 4008 | "C:\Users\admin\AppData\Local\Temp\Rar$EXb2508.18931\e8a091a84dd2ea7ee429135ff48e9f48f7787637ccb79f6c3eb42f34588bc684.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXb2508.18931\e8a091a84dd2ea7ee429135ff48e9f48f7787637ccb79f6c3eb42f34588bc684.exe | — | WinRAR.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
3 134
Read events
2 845
Write events
146
Delete events
143
Modification events
| (PID) Process: | (2508) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2508) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2508) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16C\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2508) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\virtio_ivshmem_master_build.zip | |||
| (PID) Process: | (2508) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\Win7-KB3191566-x86.zip | |||
| (PID) Process: | (2508) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\f83fb9ce6a83da58b20685c1d7e1e546.zip | |||
| (PID) Process: | (2508) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2508) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2508) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2508) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
Executable files
2
Suspicious files
543
Text files
146
Unknown types
19
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1940 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRE44C.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 1940 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\index.dat | ini | |
MD5:— | SHA256:— | |||
| 1940 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\yourselfsee.rtf.LNK | lnk | |
MD5:— | SHA256:— | |||
| 1940 | WINWORD.EXE | C:\Users\admin\Desktop\~$urselfsee.rtf | pgc | |
MD5:— | SHA256:— | |||
| 1940 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{64ECF616-2D11-4879-9A10-FF795599775C}.tmp | dbf | |
MD5:— | SHA256:— | |||
| 1940 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRF{B174A8E0-38B5-4B31-98E7-68A95C1AE2C7}.tmp | binary | |
MD5:— | SHA256:— | |||
| 1244 | e8a091a84dd2ea7ee429135ff48e9f48f7787637ccb79f6c3eb42f34588bc684.exe | C:\$Recycle.Bin\S-1-5-21-1302019708-1500728564-335382590-1000\DECRYPT-FILES.html | html | |
MD5:— | SHA256:— | |||
| 1244 | e8a091a84dd2ea7ee429135ff48e9f48f7787637ccb79f6c3eb42f34588bc684.exe | C:\Users\admin\.oracle_jre_usage\90737d32e3abaa4.timestamp | binary | |
MD5:— | SHA256:— | |||
| 1244 | e8a091a84dd2ea7ee429135ff48e9f48f7787637ccb79f6c3eb42f34588bc684.exe | C:\Users\admin\AppData\Local\VirtualStore\DECRYPT-FILES.html | html | |
MD5:— | SHA256:— | |||
| 1244 | e8a091a84dd2ea7ee429135ff48e9f48f7787637ccb79f6c3eb42f34588bc684.exe | C:\MSOCache\DECRYPT-FILES.html | html | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
2
DNS requests
0
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1244 | e8a091a84dd2ea7ee429135ff48e9f48f7787637ccb79f6c3eb42f34588bc684.exe | POST | — | 92.63.8.47:80 | http://92.63.8.47/news/archive/fwoylb.cgi?s=062pde0 | TR | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1244 | e8a091a84dd2ea7ee429135ff48e9f48f7787637ccb79f6c3eb42f34588bc684.exe | 92.63.8.47:80 | — | Nethouse Bilgi Islem Merkezi Ltd | TR | malicious |