| File name: | 77ad47e07c6bb16f068a013c2330002464a96672fcd6b99c0fd643d257f92261 |
| Full analysis: | https://app.any.run/tasks/271554ce-8281-4162-9d37-8bfd41de74d4 |
| Verdict: | Malicious activity |
| Threats: | A keylogger is a type of spyware that infects a system and has the ability to record every keystroke made on the device. This lets attackers collect personal information of victims, which may include their online banking credentials, as well as personal conversations. The most widespread vector of attack leading to a keylogger infection begins with a phishing email or link. Keylogging is also often present in remote access trojans as part of an extended set of malicious tools. |
| Analysis date: | March 25, 2025, 05:33:55 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
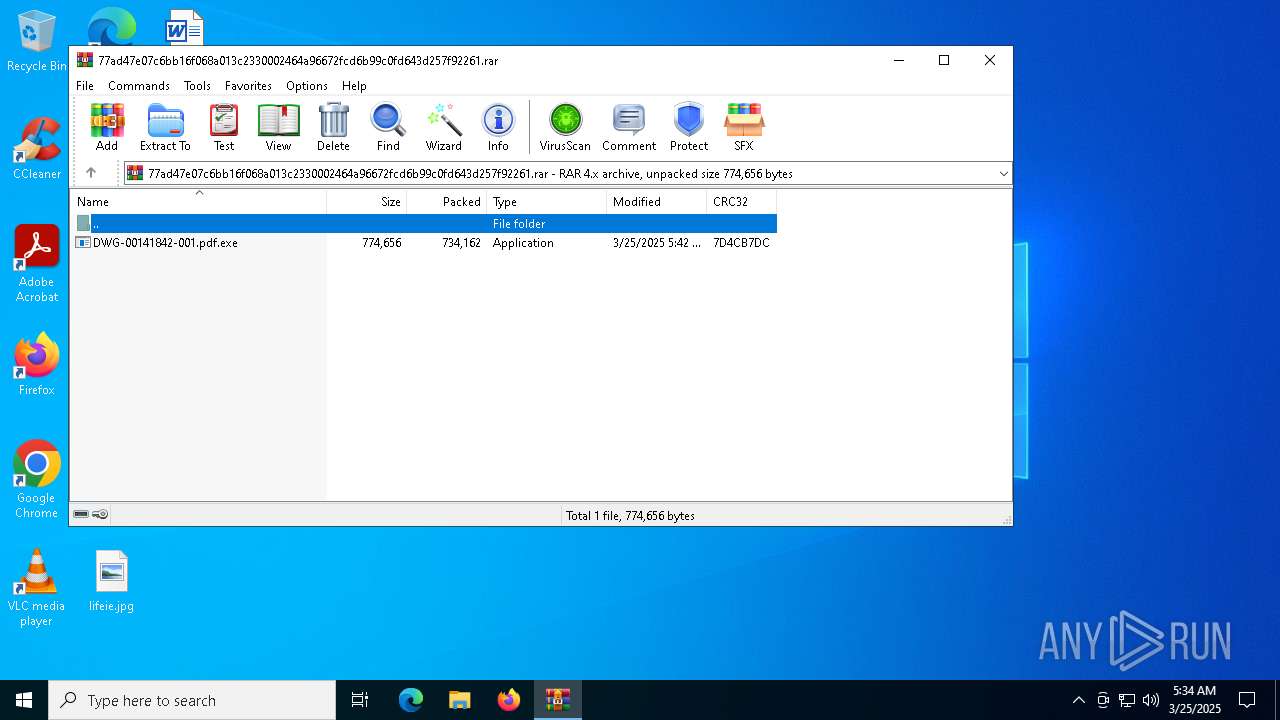
| MIME: | application/x-rar |
| File info: | RAR archive data, v4, os: Win32 |
| MD5: | 8F3B8E1A8224A9E90F2DADD11F4BD404 |
| SHA1: | F5A0E62365B465BB83407EC550E3635FFE9B59E5 |
| SHA256: | 77AD47E07C6BB16F068A013C2330002464A96672FCD6B99C0FD643D257F92261 |
| SSDEEP: | 24576:FOgkNV0nCjEu0hOFslh9NB4Sxl/yLGtGOLrQfkwVoeT3m+mK0wycthMSP3/KD+9Y:FOgkz0nCjEu0hOFslh9NmSxl/yLGtGO5 |
MALICIOUS
Generic archive extractor
- WinRAR.exe (PID: 5156)
SNAKEKEYLOGGER has been detected (SURICATA)
- DWG-00141842-001.pdf.exe (PID: 4880)
SNAKE has been detected (YARA)
- DWG-00141842-001.pdf.exe (PID: 4880)
Steals credentials from Web Browsers
- DWG-00141842-001.pdf.exe (PID: 4880)
Actions looks like stealing of personal data
- DWG-00141842-001.pdf.exe (PID: 4880)
SUSPICIOUS
Checks for external IP
- svchost.exe (PID: 2196)
- DWG-00141842-001.pdf.exe (PID: 4880)
Application launched itself
- DWG-00141842-001.pdf.exe (PID: 6744)
Process communicates with Telegram (possibly using it as an attacker's C2 server)
- DWG-00141842-001.pdf.exe (PID: 4880)
Possible usage of Discord/Telegram API has been detected (YARA)
- DWG-00141842-001.pdf.exe (PID: 4880)
The process verifies whether the antivirus software is installed
- DWG-00141842-001.pdf.exe (PID: 4880)
INFO
Manual execution by a user
- DWG-00141842-001.pdf.exe (PID: 6744)
Checks supported languages
- DWG-00141842-001.pdf.exe (PID: 6744)
- DWG-00141842-001.pdf.exe (PID: 4880)
Reads the computer name
- DWG-00141842-001.pdf.exe (PID: 6744)
- DWG-00141842-001.pdf.exe (PID: 4880)
Reads the machine GUID from the registry
- DWG-00141842-001.pdf.exe (PID: 6744)
- DWG-00141842-001.pdf.exe (PID: 4880)
Disables trace logs
- DWG-00141842-001.pdf.exe (PID: 4880)
Checks proxy server information
- DWG-00141842-001.pdf.exe (PID: 4880)
- slui.exe (PID: 4812)
Reads the software policy settings
- DWG-00141842-001.pdf.exe (PID: 4880)
- slui.exe (PID: 4812)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
SnakeKeylogger
(PID) Process(4880) DWG-00141842-001.pdf.exe
Keys
DES6fc98cd68a1aab8b
Options
Telegram Bot Token7950066405:AAE5kUvk04Df6LzJFoe-yZt3F12hJhmZIQg
Telegram Chat ID-4703613545
ims-api
(PID) Process(4880) DWG-00141842-001.pdf.exe
Telegram-Tokens (1)7950066405:AAE5kUvk04Df6LzJFoe-yZt3F12hJhmZIQg
Telegram-Info-Links
7950066405:AAE5kUvk04Df6LzJFoe-yZt3F12hJhmZIQg
Get info about bothttps://api.telegram.org/bot7950066405:AAE5kUvk04Df6LzJFoe-yZt3F12hJhmZIQg/getMe
Get incoming updateshttps://api.telegram.org/bot7950066405:AAE5kUvk04Df6LzJFoe-yZt3F12hJhmZIQg/getUpdates
Get webhookhttps://api.telegram.org/bot7950066405:AAE5kUvk04Df6LzJFoe-yZt3F12hJhmZIQg/getWebhookInfo
Delete webhookhttps://api.telegram.org/bot7950066405:AAE5kUvk04Df6LzJFoe-yZt3F12hJhmZIQg/deleteWebhook
Drop incoming updateshttps://api.telegram.org/bot7950066405:AAE5kUvk04Df6LzJFoe-yZt3F12hJhmZIQg/deleteWebhook?drop_pending_updates=true
TRiD
| .rar | | | RAR compressed archive (v-4.x) (58.3) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (41.6) |
EXIF
ZIP
| FileVersion: | RAR v4 |
|---|---|
| CompressedSize: | 734207 |
| UncompressedSize: | 774656 |
| OperatingSystem: | Win32 |
| ModifyDate: | 2025:03:25 05:42:36 |
| PackingMethod: | Normal |
| ArchivedFileName: | DWG-00141842-001.pdf.exe |
Total processes
122
Monitored processes
5
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2196 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4812 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4880 | "C:\Users\admin\Desktop\DWG-00141842-001.pdf.exe" | C:\Users\admin\Desktop\DWG-00141842-001.pdf.exe | DWG-00141842-001.pdf.exe | ||||||||||||
User: admin Company: Microsoft Integrity Level: MEDIUM Description: Version: 0.4 Modules
SnakeKeylogger(PID) Process(4880) DWG-00141842-001.pdf.exe Keys DES6fc98cd68a1aab8b Options Telegram Bot Token7950066405:AAE5kUvk04Df6LzJFoe-yZt3F12hJhmZIQg Telegram Chat ID-4703613545 ims-api(PID) Process(4880) DWG-00141842-001.pdf.exe Telegram-Tokens (1)7950066405:AAE5kUvk04Df6LzJFoe-yZt3F12hJhmZIQg Telegram-Info-Links 7950066405:AAE5kUvk04Df6LzJFoe-yZt3F12hJhmZIQg Get info about bothttps://api.telegram.org/bot7950066405:AAE5kUvk04Df6LzJFoe-yZt3F12hJhmZIQg/getMe Get incoming updateshttps://api.telegram.org/bot7950066405:AAE5kUvk04Df6LzJFoe-yZt3F12hJhmZIQg/getUpdates Get webhookhttps://api.telegram.org/bot7950066405:AAE5kUvk04Df6LzJFoe-yZt3F12hJhmZIQg/getWebhookInfo Delete webhookhttps://api.telegram.org/bot7950066405:AAE5kUvk04Df6LzJFoe-yZt3F12hJhmZIQg/deleteWebhook Drop incoming updateshttps://api.telegram.org/bot7950066405:AAE5kUvk04Df6LzJFoe-yZt3F12hJhmZIQg/deleteWebhook?drop_pending_updates=true | |||||||||||||||
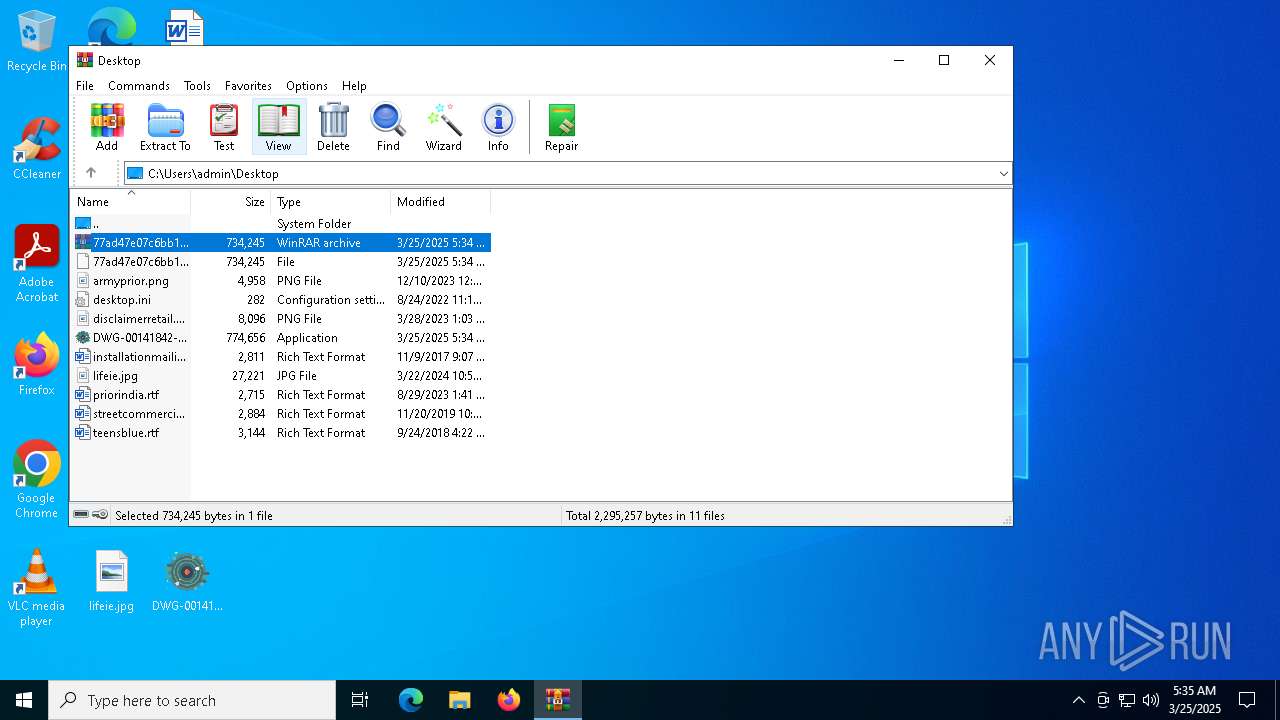
| 5156 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\Desktop\77ad47e07c6bb16f068a013c2330002464a96672fcd6b99c0fd643d257f92261.rar | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
| 6744 | "C:\Users\admin\Desktop\DWG-00141842-001.pdf.exe" | C:\Users\admin\Desktop\DWG-00141842-001.pdf.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Integrity Level: MEDIUM Description: Exit code: 0 Version: 0.4 Modules
| |||||||||||||||
Total events
9 133
Read events
9 102
Write events
31
Delete events
0
Modification events
| (PID) Process: | (5156) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (5156) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (5156) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (5156) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\77ad47e07c6bb16f068a013c2330002464a96672fcd6b99c0fd643d257f92261.rar | |||
| (PID) Process: | (5156) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (5156) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (5156) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (5156) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (4880) DWG-00141842-001.pdf.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\DWG-00141842-001_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (4880) DWG-00141842-001.pdf.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\DWG-00141842-001_RASAPI32 |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
Executable files
0
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
22
TCP/UDP connections
22
DNS requests
6
Threats
20
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4880 | DWG-00141842-001.pdf.exe | GET | 200 | 193.122.6.168:80 | http://checkip.dyndns.org/ | unknown | — | — | whitelisted |
4880 | DWG-00141842-001.pdf.exe | GET | 200 | 193.122.6.168:80 | http://checkip.dyndns.org/ | unknown | — | — | whitelisted |
— | — | GET | 200 | 104.21.112.1:443 | https://reallyfreegeoip.org/xml/180.74.219.139 | unknown | — | — | unknown |
4880 | DWG-00141842-001.pdf.exe | GET | 200 | 193.122.6.168:80 | http://checkip.dyndns.org/ | unknown | — | — | whitelisted |
— | — | GET | 200 | 104.21.96.1:443 | https://reallyfreegeoip.org/xml/180.74.219.139 | unknown | — | — | unknown |
— | — | GET | 200 | 104.21.64.1:443 | https://reallyfreegeoip.org/xml/180.74.219.139 | unknown | — | — | unknown |
4880 | DWG-00141842-001.pdf.exe | GET | 200 | 193.122.6.168:80 | http://checkip.dyndns.org/ | unknown | — | — | whitelisted |
4880 | DWG-00141842-001.pdf.exe | GET | 200 | 193.122.6.168:80 | http://checkip.dyndns.org/ | unknown | — | — | whitelisted |
4880 | DWG-00141842-001.pdf.exe | GET | 200 | 193.122.6.168:80 | http://checkip.dyndns.org/ | unknown | — | — | whitelisted |
— | — | GET | 200 | 104.21.16.1:443 | https://reallyfreegeoip.org/xml/180.74.219.139 | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4880 | DWG-00141842-001.pdf.exe | 193.122.6.168:80 | checkip.dyndns.org | ORACLE-BMC-31898 | DE | whitelisted |
4880 | DWG-00141842-001.pdf.exe | 104.21.16.1:443 | reallyfreegeoip.org | CLOUDFLARENET | — | malicious |
4880 | DWG-00141842-001.pdf.exe | 149.154.167.220:443 | api.telegram.org | Telegram Messenger Inc | GB | whitelisted |
4996 | slui.exe | 20.83.72.98:443 | activation-v2.sls.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4812 | slui.exe | 20.83.72.98:443 | activation-v2.sls.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
checkip.dyndns.org |
| whitelisted |
reallyfreegeoip.org |
| malicious |
api.telegram.org |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | Device Retrieving External IP Address Detected | ET DYN_DNS External IP Lookup Domain in DNS Query (checkip .dyndns .org) |
4880 | DWG-00141842-001.pdf.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup - checkip.dyndns.org |
4880 | DWG-00141842-001.pdf.exe | Device Retrieving External IP Address Detected | ET INFO 404/Snake/Matiex Keylogger Style External IP Check |
4880 | DWG-00141842-001.pdf.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup - checkip.dyndns.org |
2196 | svchost.exe | Device Retrieving External IP Address Detected | INFO [ANY.RUN] External IP Address Lookup Domain (reallyfreegeoip .org) |
2196 | svchost.exe | Misc activity | ET INFO External IP Address Lookup Domain in DNS Lookup (reallyfreegeoip .org) |
4880 | DWG-00141842-001.pdf.exe | Misc activity | ET INFO External IP Lookup Service Domain (reallyfreegeoip .org) in TLS SNI |
4880 | DWG-00141842-001.pdf.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup - checkip.dyndns.org |
4880 | DWG-00141842-001.pdf.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup - checkip.dyndns.org |
4880 | DWG-00141842-001.pdf.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup - checkip.dyndns.org |