| File name: | Loader.exe |
| Full analysis: | https://app.any.run/tasks/013eacaf-734b-4726-847b-00ad3fdf3955 |
| Verdict: | Malicious activity |
| Threats: | Lumma is an information stealer, developed using the C programming language. It is offered for sale as a malware-as-a-service, with several plans available. It usually targets cryptocurrency wallets, login credentials, and other sensitive information on a compromised system. The malicious software regularly gets updates that improve and expand its functionality, making it a serious stealer threat. |
| Analysis date: | May 19, 2025, 19:53:15 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32+ executable (console) x86-64, for MS Windows, 15 sections |
| MD5: | 1C791F7A8249199461E8CBD1307304FC |
| SHA1: | 806F3C1BC62BEAF53C540F30B1F82746D98079FB |
| SHA256: | 775D25D0BC3125AE6DF9A2E84CD448E2108AE7EDF6D66916E39F97E9B5CB86E2 |
| SSDEEP: | 98304:kNwv1yaHSj4ELpbG00DaGZhhz2YaOhXysrJJ6NU+Mu0McPoXNfEVZSCdMIt/py0u:3dOvcP5YHZ |
MALICIOUS
Steals credentials from Web Browsers
- MSBuild.exe (PID: 6372)
LUMMA mutex has been found
- MSBuild.exe (PID: 6372)
Actions looks like stealing of personal data
- MSBuild.exe (PID: 6372)
LUMMA has been detected (YARA)
- MSBuild.exe (PID: 6372)
SUSPICIOUS
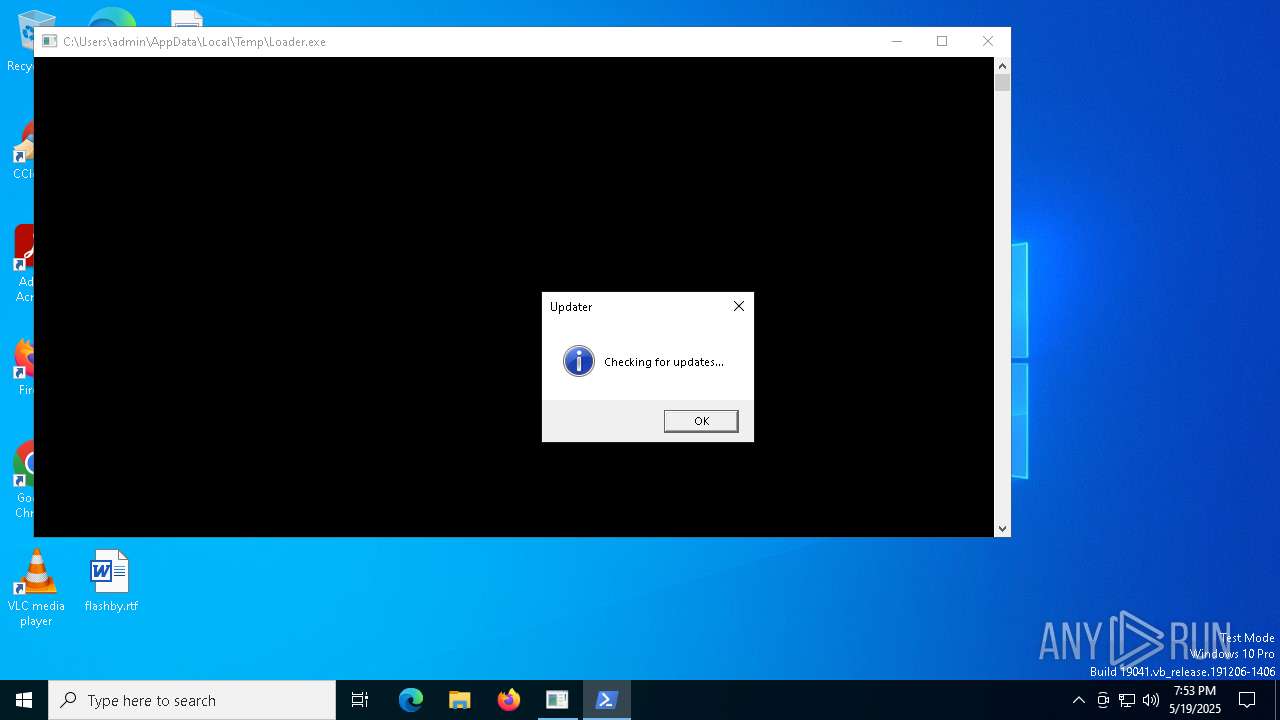
Starts POWERSHELL.EXE for commands execution
- Loader.exe (PID: 6808)
Executable content was dropped or overwritten
- Loader.exe (PID: 6808)
Process communicates with Telegram (possibly using it as an attacker's C2 server)
- MSBuild.exe (PID: 6372)
Searches for installed software
- MSBuild.exe (PID: 6372)
There is functionality for taking screenshot (YARA)
- MSBuild.exe (PID: 6372)
INFO
Drops encrypted JS script (Microsoft Script Encoder)
- Loader.exe (PID: 6808)
Checks supported languages
- Loader.exe (PID: 6808)
- MSBuild.exe (PID: 6372)
Reads the computer name
- Loader.exe (PID: 6808)
- MSBuild.exe (PID: 6372)
Reads the software policy settings
- Loader.exe (PID: 6808)
- MSBuild.exe (PID: 6372)
- slui.exe (PID: 4892)
Reads the machine GUID from the registry
- Loader.exe (PID: 6808)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Lumma
(PID) Process(6372) MSBuild.exe
C2 (10)onehunqpom.life/zpxd
featurlyin.top/pdal
overcovtcg.top/juhd
blackswmxc.top/bgry
laminaflbx.shop/twoq
https://t.me/kz_prokla2
posseswsnc.top/akds
jackthyfuc.run/xpas
narrathfpt.top/tekq
shoresolfe.live/ysbt
TRiD
| .exe | | | Win64 Executable (generic) (87.3) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (6.3) |
| .exe | | | DOS Executable Generic (6.3) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 0000:00:00 00:00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 3 |
| CodeSize: | 2626048 |
| InitializedDataSize: | 305152 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x775e0 |
| OSVersion: | 6.1 |
| ImageVersion: | 1 |
| SubsystemVersion: | 6.1 |
| Subsystem: | Windows command line |
Total processes
137
Monitored processes
9
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 616 | C:\Users\admin\AppData\Roaming\5f6fcf2901404b150.exe | C:\Users\admin\AppData\Roaming\5f6fcf2901404b150.exe | — | Loader.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 960 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2196 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2908 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | Loader.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3888 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Version: 10.0.19041.3996 (WinBuild.160101.0800) | |||||||||||||||
| 4880 | powershell -Command "Add-Type -AssemblyName System.Windows.Forms; [System.Windows.Forms.MessageBox]::Show('Checking for updates...', 'Updater', 'OK', 'Information')" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | Loader.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4892 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | SppExtComObj.Exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6372 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\MSBuild.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\MSBuild.exe | 5f6fcf2901404b150.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: MSBuild.exe Version: 4.8.9037.0 built by: NET481REL1 Modules
Lumma(PID) Process(6372) MSBuild.exe C2 (10)onehunqpom.life/zpxd featurlyin.top/pdal overcovtcg.top/juhd blackswmxc.top/bgry laminaflbx.shop/twoq https://t.me/kz_prokla2 posseswsnc.top/akds jackthyfuc.run/xpas narrathfpt.top/tekq shoresolfe.live/ysbt | |||||||||||||||
| 6808 | "C:\Users\admin\AppData\Local\Temp\Loader.exe" | C:\Users\admin\AppData\Local\Temp\Loader.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Modules
| |||||||||||||||
Total events
3 416
Read events
3 416
Write events
0
Delete events
0
Modification events
Executable files
1
Suspicious files
1
Text files
2
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6808 | Loader.exe | C:\Users\admin\AppData\Roaming\5f6fcf2901404b150.exe | executable | |
MD5:AF36569A200F106248A889D08F590379 | SHA256:078705BB3A75A7DD8930CE7772945DD7EA9D02618C3A4BEC97AADA543D4B97D5 | |||
| 4880 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_4kfjawkt.isd.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 4880 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_1cusmfor.n2q.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 4880 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:23DA19B7DDE4304B76EA2E2AD70D0881 | SHA256:8D4EF00314204717FB6D05F9200DF41B09B4A796CB2623F7911EFF8875A54D82 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
32
DNS requests
22
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.48.23.147:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.52.120.96:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
4740 | SIHClient.exe | GET | 200 | 23.52.120.96:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
4740 | SIHClient.exe | GET | 200 | 23.52.120.96:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2104 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 23.48.23.147:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 23.52.120.96:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6808 | Loader.exe | 172.67.25.94:443 | pastebin.com | CLOUDFLARENET | US | whitelisted |
— | — | 140.82.121.4:443 | github.com | GITHUB | US | whitelisted |
— | — | 185.199.108.133:443 | raw.githubusercontent.com | FASTLY | US | whitelisted |
3216 | svchost.exe | 172.211.123.248:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
pastebin.com |
| whitelisted |
github.com |
| whitelisted |
raw.githubusercontent.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
t.me |
| whitelisted |
shoresolfe.live |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Online Pastebin Text Storage |
2196 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |
6372 | MSBuild.exe | Misc activity | ET INFO Observed Telegram Domain (t .me in TLS SNI) |
2196 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a *.top domain - Likely Hostile |