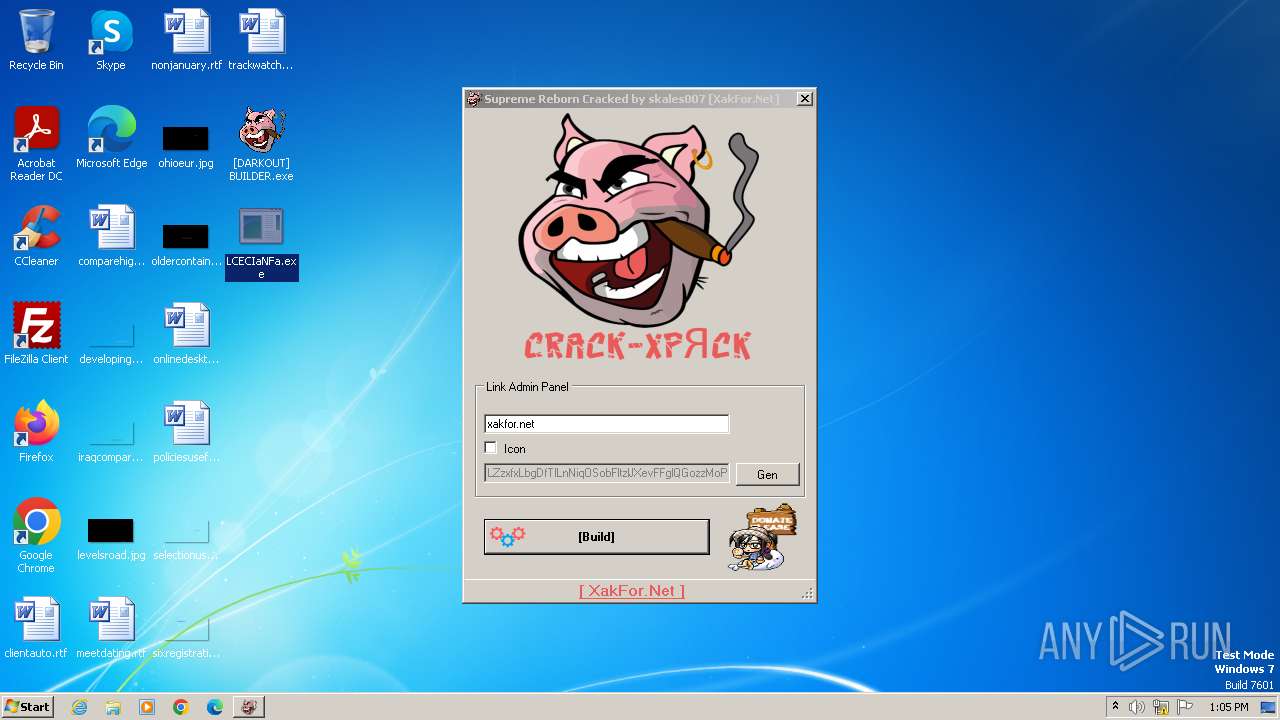
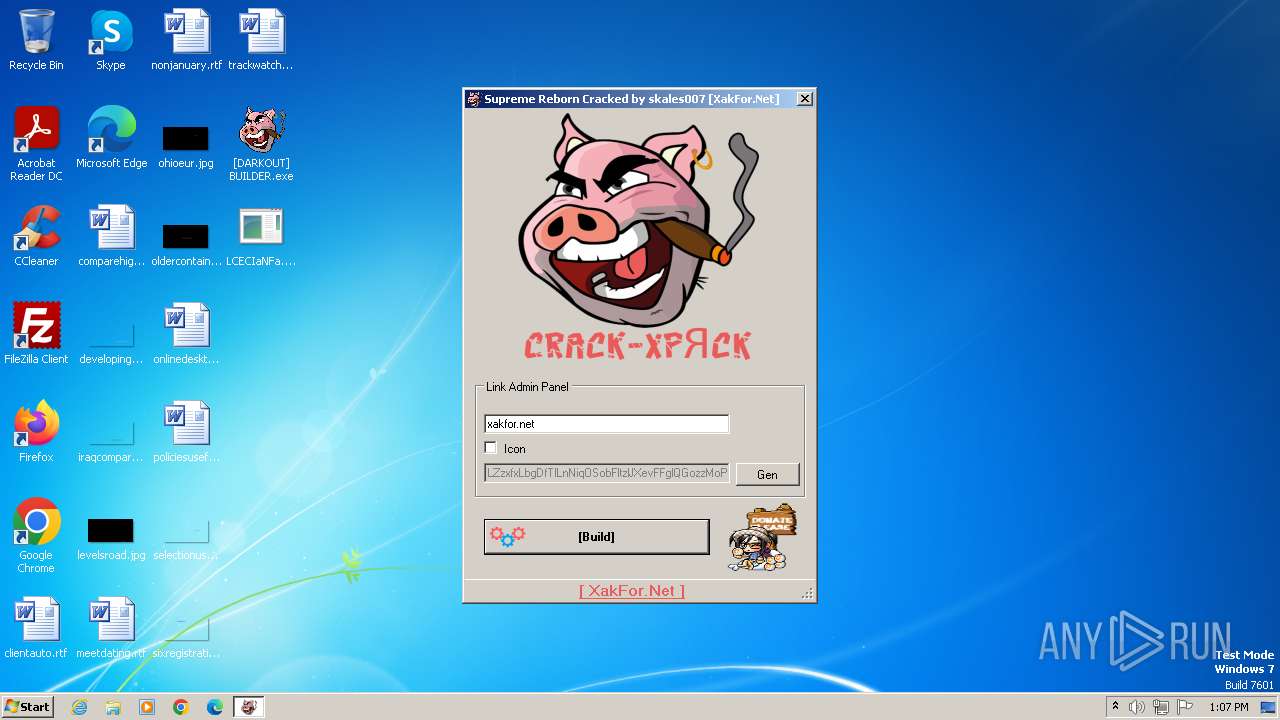
| File name: | [DARKOUT] BUILDER.exe |
| Full analysis: | https://app.any.run/tasks/1f25f857-9fc6-4799-8a3a-a5304911d2ac |
| Verdict: | Malicious activity |
| Threats: | Crypto mining malware is a resource-intensive threat that infiltrates computers with the purpose of mining cryptocurrencies. This type of threat can be deployed either on an infected machine or a compromised website. In both cases the miner will utilize the computing power of the device and its network bandwidth. |
| Analysis date: | June 09, 2024, 12:05:26 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | 638A083025C7A9924AF1F8D045B98E3F |
| SHA1: | 19D1B9FC1FAEA0186A1AE6CFDF6172028C42D744 |
| SHA256: | 772F38FBB48D9B01F9F564D38D8C545BB82D2AFF8F84C1511CF9D7FEC3426504 |
| SSDEEP: | 24576:N93X86sdcQzdiT4YH9KzOzDTz3IOPQUlkBj2tIF8vlgAPsdTfbtMP:NpXbwksmoyTz42QU2Mw8vl/0dv2P |
MALICIOUS
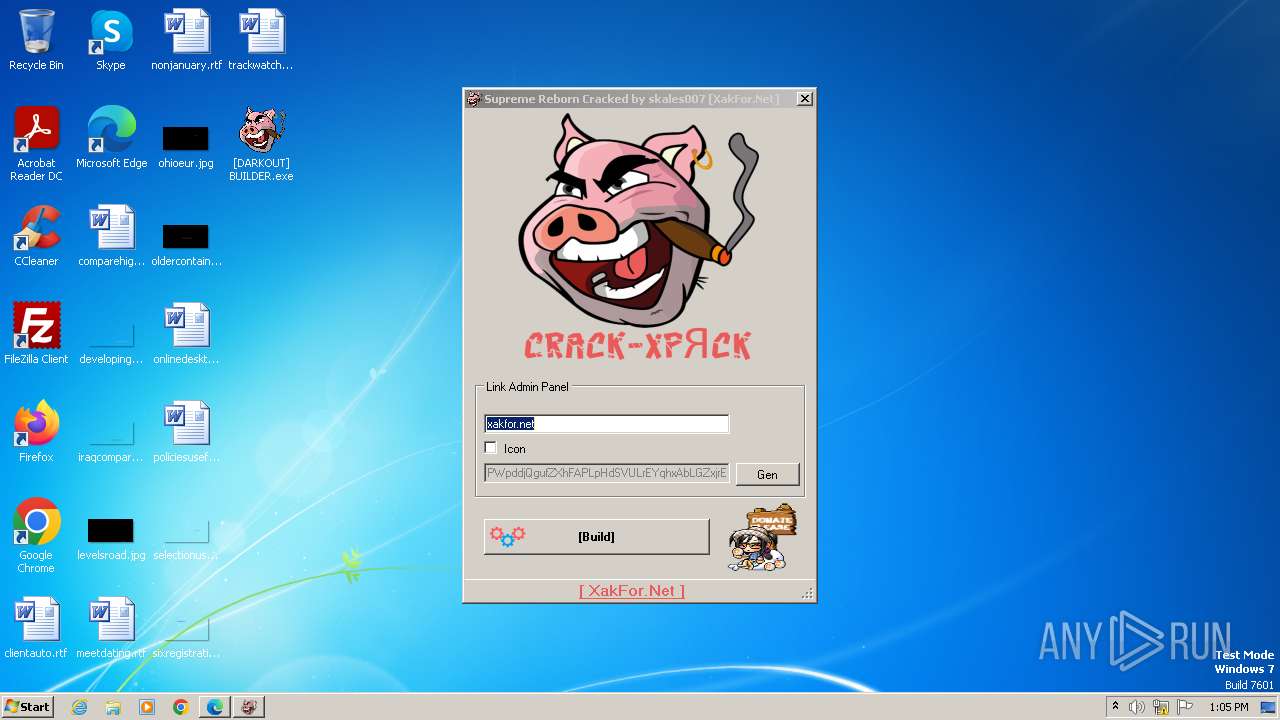
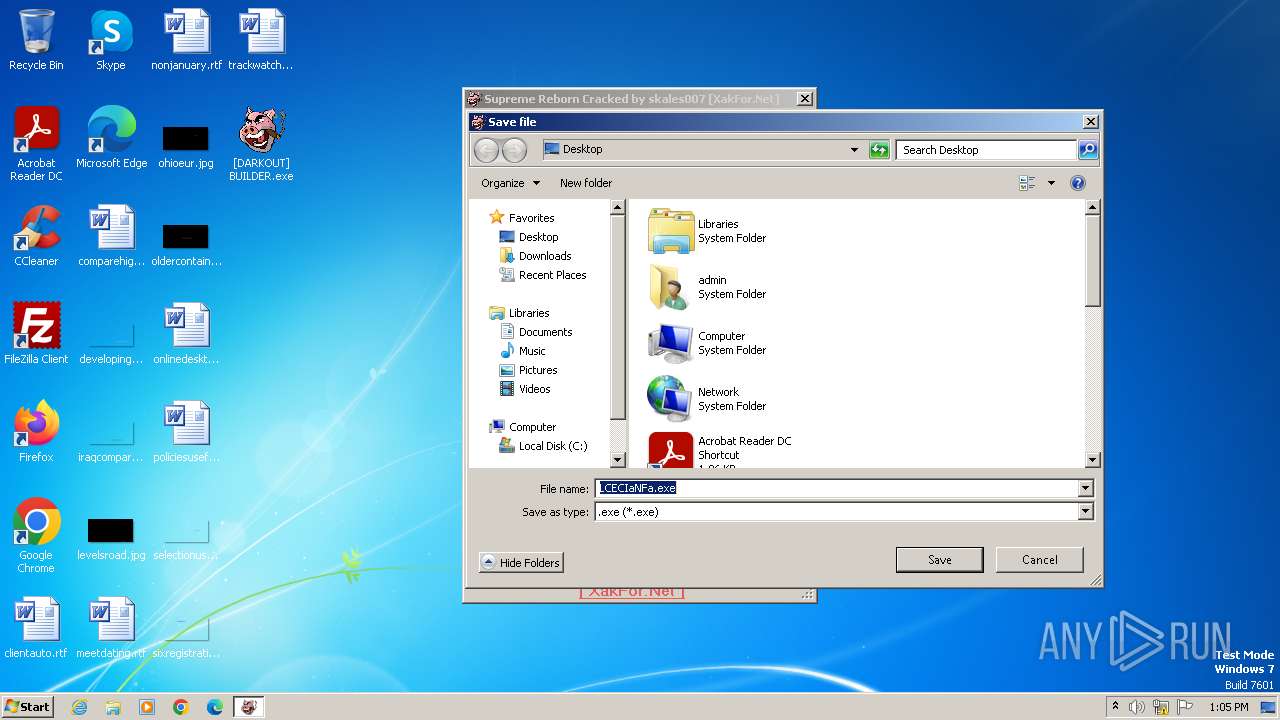
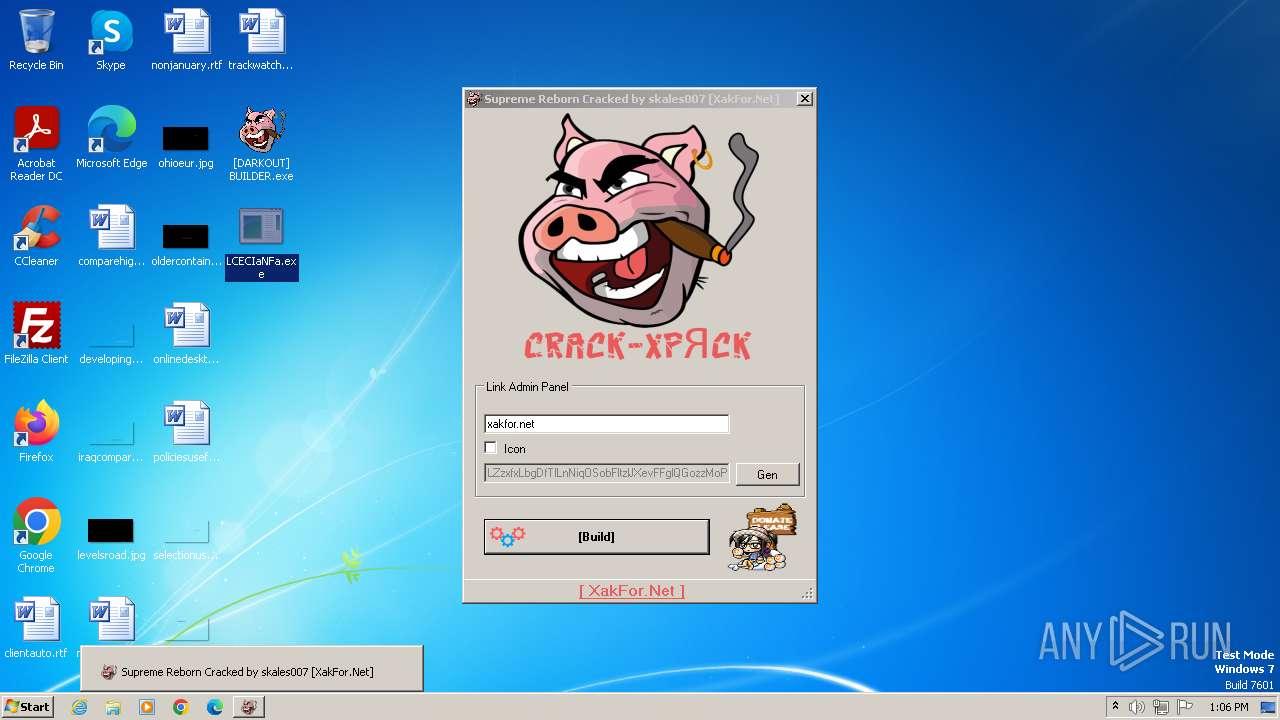
Drops the executable file immediately after the start
- [DARKOUT] BUILDER.exe (PID: 3980)
- LCECIaNFa.exe (PID: 1136)
Connects to the CnC server
- taskhost.exe (PID: 2036)
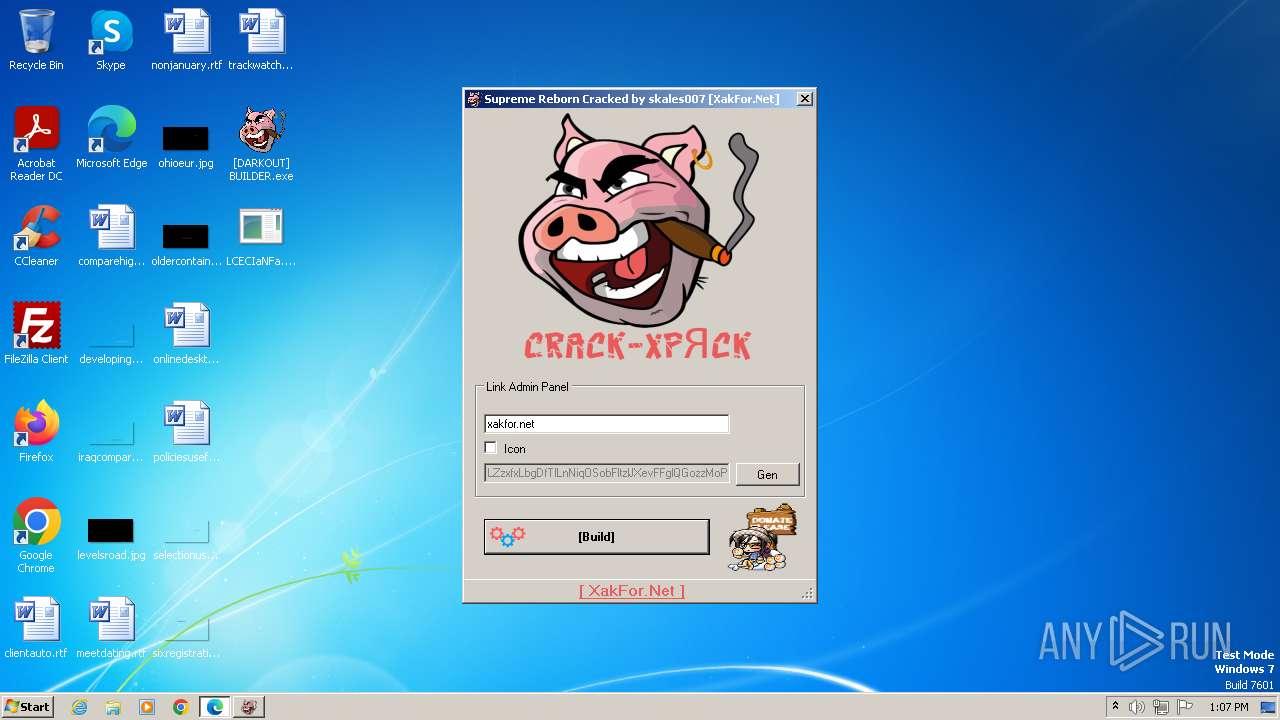
Uses Task Scheduler to run other applications
- LCECIaNFa.exe (PID: 1136)
Starts CMD.EXE for self-deleting
- LCECIaNFa.exe (PID: 1136)
SUPREME has been detected (SURICATA)
- taskhost.exe (PID: 2036)
SUSPICIOUS
Executable content was dropped or overwritten
- [DARKOUT] BUILDER.exe (PID: 3980)
- LCECIaNFa.exe (PID: 1136)
Reads the Internet Settings
- [DARKOUT] BUILDER.exe (PID: 3980)
- LCECIaNFa.exe (PID: 1136)
The process creates files with name similar to system file names
- LCECIaNFa.exe (PID: 1136)
Starts itself from another location
- LCECIaNFa.exe (PID: 1136)
Reads security settings of Internet Explorer
- LCECIaNFa.exe (PID: 1136)
Starts CMD.EXE for commands execution
- LCECIaNFa.exe (PID: 1136)
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 372)
Contacting a server suspected of hosting an CnC
- taskhost.exe (PID: 2036)
INFO
Reads the computer name
- [DARKOUT] BUILDER.exe (PID: 3980)
- LCECIaNFa.exe (PID: 1136)
- wmpnscfg.exe (PID: 1620)
- taskhost.exe (PID: 2036)
Checks supported languages
- [DARKOUT] BUILDER.exe (PID: 3980)
- LCECIaNFa.exe (PID: 1136)
- wmpnscfg.exe (PID: 1620)
- taskhost.exe (PID: 2036)
Reads the machine GUID from the registry
- [DARKOUT] BUILDER.exe (PID: 3980)
- taskhost.exe (PID: 2036)
Manual execution by a user
- LCECIaNFa.exe (PID: 1136)
- wmpnscfg.exe (PID: 1620)
Reads Environment values
- LCECIaNFa.exe (PID: 1136)
- taskhost.exe (PID: 2036)
Reads product name
- LCECIaNFa.exe (PID: 1136)
- taskhost.exe (PID: 2036)
The process uses the downloaded file
- LCECIaNFa.exe (PID: 1136)
Reads CPU info
- LCECIaNFa.exe (PID: 1136)
- taskhost.exe (PID: 2036)
Creates files in the program directory
- LCECIaNFa.exe (PID: 1136)
Application launched itself
- msedge.exe (PID: 1132)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .dll | | | Win32 Dynamic Link Library (generic) (38.3) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (26.2) |
| .exe | | | Win16/32 Executable Delphi generic (12) |
| .exe | | | Generic Win/DOS Executable (11.6) |
| .exe | | | DOS Executable Generic (11.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:01:11 11:00:14+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 48 |
| CodeSize: | 430592 |
| InitializedDataSize: | 1559552 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1ec00a |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | - |
| CompanyName: | Microsoft |
| FileDescription: | Supreme Reborn Cracked by skales007 |
| FileVersion: | 1.0.0.0 |
| InternalName: | Supreme Reborn Cracked by skales007.exe |
| LegalCopyright: | Copyright © Microsoft 2019 |
| LegalTrademarks: | - |
| OriginalFileName: | Supreme Reborn Cracked by skales007.exe |
| ProductName: | Supreme Reborn Cracked by skales007 |
| ProductVersion: | 1.0.0.0 |
| AssemblyVersion: | 1.0.0.0 |
Total processes
56
Monitored processes
20
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 372 | "C:\Windows\System32\cmd.exe" /c taskkill /im LCECIaNFa.exe /f & erase p+ & exit | C:\Windows\System32\cmd.exe | — | LCECIaNFa.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
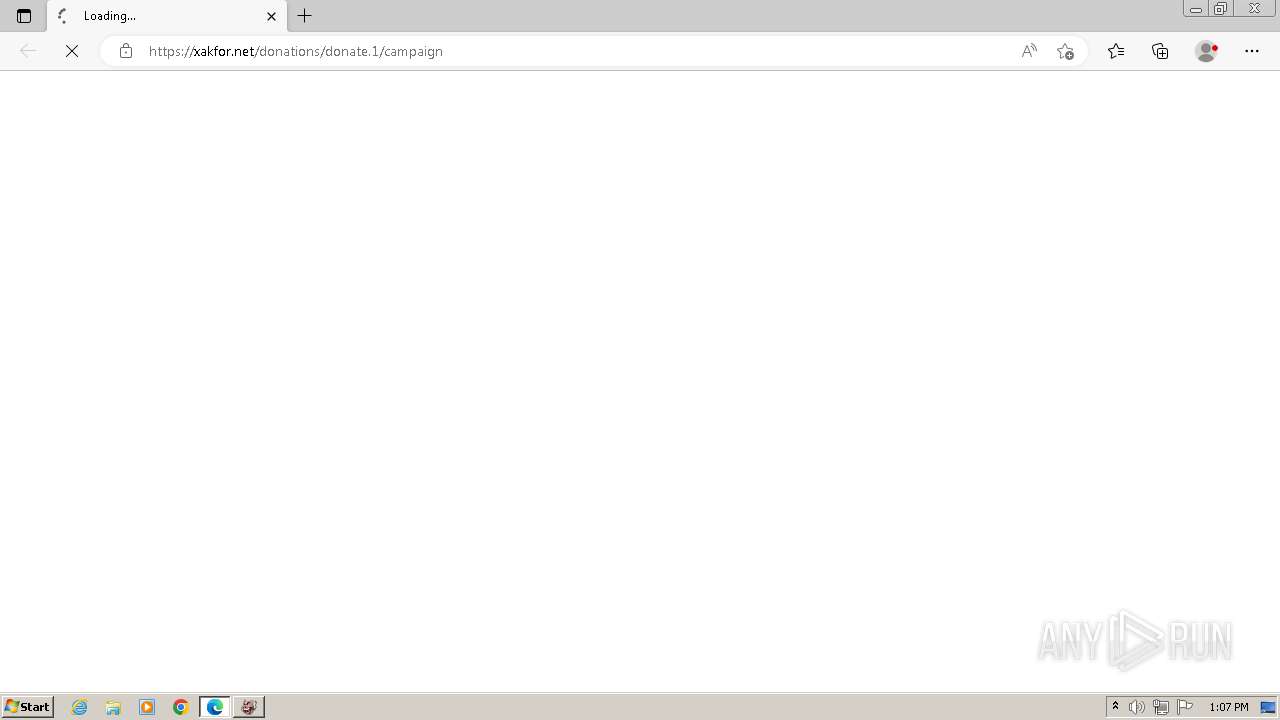
| 1132 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --single-argument https://xakfor.net/donations/donate.1/campaign | C:\Program Files\Microsoft\Edge\Application\msedge.exe | [DARKOUT] BUILDER.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 1136 | "C:\Users\admin\Desktop\LCECIaNFa.exe" | C:\Users\admin\Desktop\LCECIaNFa.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1312 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --mojo-platform-channel-handle=3732 --field-trial-handle=1320,i,1742158213999427764,5578473956964287071,131072 /prefetch:8 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 1620 | "C:\Program Files\Windows Media Player\wmpnscfg.exe" | C:\Program Files\Windows Media Player\wmpnscfg.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Media Player Network Sharing Service Configuration Application Exit code: 0 Version: 12.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1676 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --mojo-platform-channel-handle=1640 --field-trial-handle=1320,i,1742158213999427764,5578473956964287071,131072 /prefetch:8 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 1800 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data" --annotation=IsOfficialBuild=1 --annotation=channel= --annotation=chromium-version=109.0.5414.149 "--annotation=exe=C:\Program Files\Microsoft\Edge\Application\msedge.exe" --annotation=plat=Win32 "--annotation=prod=Microsoft Edge" --annotation=ver=109.0.1518.115 --initial-client-data=0xc8,0xcc,0xd0,0x9c,0xd8,0x6da3f598,0x6da3f5a8,0x6da3f5b4 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 1876 | "C:\Windows\System32\schtasks.exe" /Create /SC MINUTE /MO 15 /TN "7FVK2OFJNUGPN0IVG6" /TR "C:\ProgramData\{5GLV7879-AXJL-X3CZ-E56IHHGSTQCX}\taskhost.exe" /F | C:\Windows\System32\schtasks.exe | — | LCECIaNFa.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Manages scheduled tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1928 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=1452 --field-trial-handle=1320,i,1742158213999427764,5578473956964287071,131072 /prefetch:3 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | msedge.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 2036 | "C:\ProgramData\{5GLV7879-AXJL-X3CZ-E56IHHGSTQCX}\taskhost.exe" | C:\ProgramData\{5GLV7879-AXJL-X3CZ-E56IHHGSTQCX}\taskhost.exe | LCECIaNFa.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Modules
| |||||||||||||||
Total events
8 399
Read events
8 321
Write events
69
Delete events
9
Modification events
| (PID) Process: | (3980) [DARKOUT] BUILDER.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\ComDlg32\CIDSizeMRU |
| Operation: | write | Name: | 4 |
Value: 5B004400410052004B004F00550054005D0020004200550049004C004400450052002E0065007800650000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000100000000000000 | |||
| (PID) Process: | (3980) [DARKOUT] BUILDER.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | NodeSlots |
Value: 0202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202 | |||
| (PID) Process: | (3980) [DARKOUT] BUILDER.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | MRUListEx |
Value: 01000000070000000200000006000000000000000B0000000C0000000D0000000A0000000900000008000000030000000500000004000000FFFFFFFF | |||
| (PID) Process: | (3980) [DARKOUT] BUILDER.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\182\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3980) [DARKOUT] BUILDER.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\ComDlg32\LastVisitedPidlMRU |
| Operation: | write | Name: | 3 |
Value: 5B004400410052004B004F00550054005D0020004200550049004C004400450052002E0065007800650000000000 | |||
| (PID) Process: | (3980) [DARKOUT] BUILDER.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\ComDlg32\LastVisitedPidlMRU |
| Operation: | write | Name: | MRUListEx |
Value: 03000000000000000200000001000000FFFFFFFF | |||
| (PID) Process: | (3980) [DARKOUT] BUILDER.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\ComDlg32\OpenSavePidlMRU\exe |
| Operation: | delete value | Name: | MRUList |
Value: | |||
| (PID) Process: | (3980) [DARKOUT] BUILDER.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\ComDlg32\OpenSavePidlMRU\exe |
| Operation: | write | Name: | 0 |
Value: 64003200000000000000000080004C43454349614E46612E65786500480008000400EFBE00000000000000002A000000000000000000000000000000000000000000000000004C00430045004300490061004E00460061002E0065007800650000001C000000 | |||
| (PID) Process: | (3980) [DARKOUT] BUILDER.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\ComDlg32\OpenSavePidlMRU\exe |
| Operation: | write | Name: | MRUListEx |
Value: 00000000FFFFFFFF | |||
| (PID) Process: | (3980) [DARKOUT] BUILDER.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\ComDlg32\OpenSavePidlMRU\* |
| Operation: | write | Name: | 13 |
Value: 64003200000000000000000080004C43454349614E46612E65786500480008000400EFBE00000000000000002A000000000000000000000000000000000000000000000000004C00430045004300490061004E00460061002E0065007800650000001C000000 | |||
Executable files
3
Suspicious files
54
Text files
37
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1132 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF11d435.TMP | — | |
MD5:— | SHA256:— | |||
| 1132 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1132 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF11d445.TMP | — | |
MD5:— | SHA256:— | |||
| 1132 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1132 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old~RF11d4c2.TMP | — | |
MD5:— | SHA256:— | |||
| 1132 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1136 | LCECIaNFa.exe | C:\ProgramData\{5GLV7879-AXJL-X3CZ-E56IHHGSTQCX}\taskhost.exe | executable | |
MD5:738454050C06E2E9037D2443348B68F7 | SHA256:32B8079AE32A43D38303BD39C88976B2C3B209DFE85474449393E0D9B7170BEC | |||
| 1132 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgeCoupons\coupons_data.db\LOG.old~RF11d445.TMP | text | |
MD5:B1E05B031BC39D74E7AC1CA69AC72F82 | SHA256:899DE7900989F710A925E38FA5AE4EA2C3B0EF47A1FEEFBF9EB57C21FA513A8E | |||
| 1132 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Last Version | text | |
MD5:61FE7896F9494DCDF53480A325F4FB85 | SHA256:ACFD3CD36E0DFCF1DCB67C7F31F2A5B9BA0815528A0C604D4330DFAA9E683E51 | |||
| 1136 | LCECIaNFa.exe | C:\ProgramData\{5GLV7879-AXJL-X3CZ-E56IHHGSTQCX}\taskhost.exe:Zone.Identifier | text | |
MD5:9F22B5D78B010677142FFE4A66E02CB2 | SHA256:F0E0B1154B82AD66F9D3B1AA8CA4EAE94A138A55E17538392315EBF63D2C36FE | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
11
TCP/UDP connections
25
DNS requests
24
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2036 | taskhost.exe | POST | 302 | 162.210.199.65:80 | http://xakfor.net/gate/connection.php | unknown | — | — | unknown |
2036 | taskhost.exe | POST | 302 | 162.210.199.65:80 | http://xakfor.net/gate/create.php | unknown | — | — | unknown |
2036 | taskhost.exe | GET | 200 | 199.59.243.225:80 | http://survey-smiles.com/ | unknown | — | — | unknown |
2036 | taskhost.exe | GET | 200 | 199.59.243.225:80 | http://survey-smiles.com/ | unknown | — | — | unknown |
2036 | taskhost.exe | POST | 302 | 162.210.199.65:80 | http://xakfor.net/gate/config.php | unknown | — | — | unknown |
2036 | taskhost.exe | GET | 200 | 199.59.243.225:80 | http://survey-smiles.com/ | unknown | — | — | unknown |
2036 | taskhost.exe | POST | 302 | 162.210.199.65:80 | http://xakfor.net/gate/update.php | unknown | — | — | unknown |
2036 | taskhost.exe | GET | 200 | 199.59.243.225:80 | http://survey-smiles.com/ | unknown | — | — | unknown |
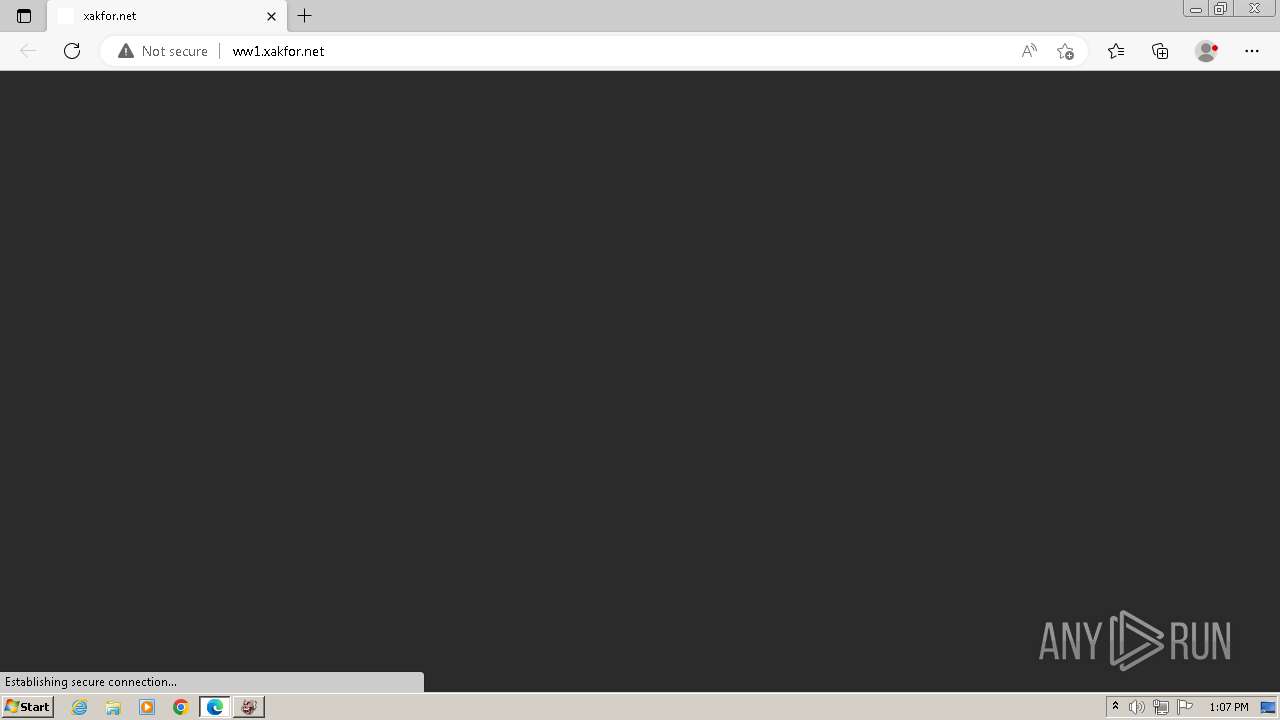
1928 | msedge.exe | GET | 200 | 199.59.243.225:80 | http://ww1.xakfor.net/ | unknown | — | — | unknown |
1928 | msedge.exe | GET | 200 | 199.59.243.225:80 | http://ww1.xakfor.net/bhllInRGg.js | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | unknown |
— | — | 224.0.0.252:5355 | — | — | — | unknown |
2036 | taskhost.exe | 162.210.199.65:80 | xakfor.net | LEASEWEB-USA-WDC | US | unknown |
2036 | taskhost.exe | 199.59.243.225:80 | survey-smiles.com | AMAZON-02 | US | unknown |
1132 | msedge.exe | 239.255.255.250:1900 | — | — | — | unknown |
1928 | msedge.exe | 162.210.199.65:443 | xakfor.net | LEASEWEB-USA-WDC | US | unknown |
1928 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
1928 | msedge.exe | 13.107.21.239:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
1928 | msedge.exe | 199.59.243.225:80 | survey-smiles.com | AMAZON-02 | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
xakfor.net |
| unknown |
survey-smiles.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
ww1.xakfor.net |
| unknown |
www.google.com |
| whitelisted |
www.adsensecustomsearchads.com |
| whitelisted |
partner.googleadservices.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
www.bing.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2036 | taskhost.exe | A Network Trojan was detected | ET MALWARE SupremeLogger CnC Checkin |
2036 | taskhost.exe | A Network Trojan was detected | ET MALWARE Win32/SupremeBot CnC Checkin (POST) M1 |
2036 | taskhost.exe | A Network Trojan was detected | ET MALWARE Win32/SupremeBot CnC Checkin (POST) M2 |
1 ETPRO signatures available at the full report