| File name: | terminal.ps1 |
| Full analysis: | https://app.any.run/tasks/bdf42032-fc82-4fa9-80c3-2df937cba426 |
| Verdict: | Malicious activity |
| Threats: | Lumma is an information stealer, developed using the C programming language. It is offered for sale as a malware-as-a-service, with several plans available. It usually targets cryptocurrency wallets, login credentials, and other sensitive information on a compromised system. The malicious software regularly gets updates that improve and expand its functionality, making it a serious stealer threat. |
| Analysis date: | July 17, 2025, 21:54:35 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | text/plain |
| File info: | ASCII text, with no line terminators |
| MD5: | 37D1401CFB2D1B0F82E514DB829929AA |
| SHA1: | 886977C13A034B5D1686DF0431E7D81D02660F69 |
| SHA256: | 76F3B6B45C6832030D25323144948952FCD7A11237D12D4315E81C0A106F0ACD |
| SSDEEP: | 3:TiI+dTZr:m1Zr |
MALICIOUS
Bypass execution policy to execute commands
- powershell.exe (PID: 2292)
Create files in the Startup directory
- powershell.exe (PID: 2292)
Actions looks like stealing of personal data
- explorer.exe (PID: 4836)
Steals credentials from Web Browsers
- explorer.exe (PID: 4836)
LUMMA mutex has been found
- explorer.exe (PID: 4836)
Dynamically loads an assembly (POWERSHELL)
- powershell.exe (PID: 2292)
SUSPICIOUS
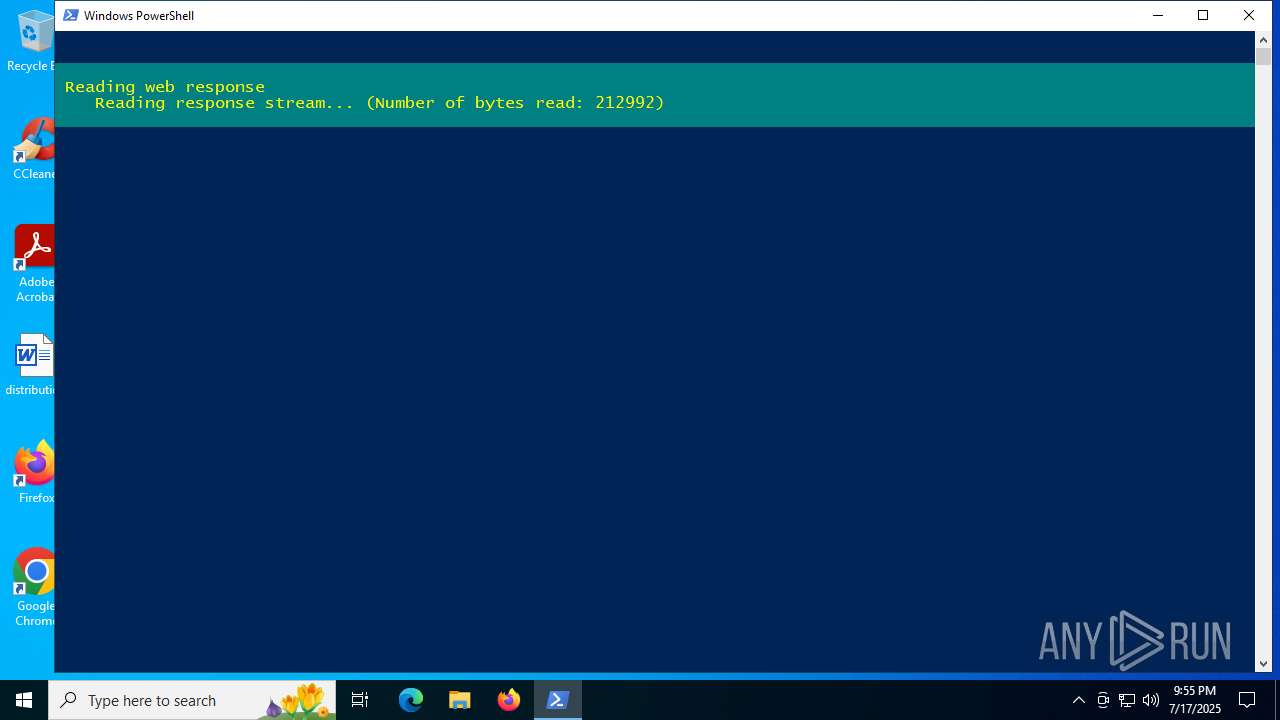
Executable content was dropped or overwritten
- powershell.exe (PID: 2292)
- csc.exe (PID: 6004)
- csc.exe (PID: 3768)
CSC.EXE is used to compile C# code
- csc.exe (PID: 6004)
- csc.exe (PID: 3768)
Uses base64 encoding (POWERSHELL)
- powershell.exe (PID: 2292)
Process drops legitimate windows executable
- powershell.exe (PID: 2292)
Process communicates with Telegram (possibly using it as an attacker's C2 server)
- explorer.exe (PID: 4836)
INFO
Checks proxy server information
- powershell.exe (PID: 2292)
- slui.exe (PID: 2276)
Disables trace logs
- powershell.exe (PID: 2292)
Checks supported languages
- cvtres.exe (PID: 1212)
- csc.exe (PID: 3768)
- cvtres.exe (PID: 1496)
- identity_helper.exe (PID: 2692)
- csc.exe (PID: 6004)
Create files in a temporary directory
- csc.exe (PID: 3768)
- cvtres.exe (PID: 1496)
- csc.exe (PID: 6004)
- cvtres.exe (PID: 1212)
Reads the machine GUID from the registry
- csc.exe (PID: 3768)
- csc.exe (PID: 6004)
Gets data length (POWERSHELL)
- powershell.exe (PID: 2292)
The sample compiled with english language support
- powershell.exe (PID: 2292)
Reads the software policy settings
- explorer.exe (PID: 4836)
- slui.exe (PID: 2276)
Application launched itself
- chrome.exe (PID: 6876)
- msedge.exe (PID: 4100)
- chrome.exe (PID: 6936)
- chrome.exe (PID: 4984)
- chrome.exe (PID: 1520)
- msedge.exe (PID: 6620)
- msedge.exe (PID: 3392)
Reads the computer name
- identity_helper.exe (PID: 2692)
Reads Environment values
- identity_helper.exe (PID: 2692)
Launching a file from the Startup directory
- powershell.exe (PID: 2292)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
221
Monitored processes
84
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 320 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --field-trial-handle=2392,i,8995223758100555080,16862579538810722883,262144 --variations-seed-version=20250221-144540.991000 --mojo-platform-channel-handle=2224 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 480 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --disable-quic --message-loop-type-ui --string-annotations --always-read-main-dll --field-trial-handle=1676,i,8455765173125141182,15606188957135119362,262144 --variations-seed-version --mojo-platform-channel-handle=5864 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 888 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --string-annotations --gpu-preferences=UAAAAAAAAADgAAAEAAAAAAAAAAAAAAAAAABgAAEAAAAAAAAAAAAAAAAAAAACAAAAAAAAAAAAAAAAAAAAAAAAABAAAAAAAAAAEAAAAAAAAAAIAAAAAAAAAAgAAAAAAAAA --field-trial-handle=2024,i,17038602023111771017,9580951582669419249,262144 --variations-seed-version=20250221-144540.991000 --mojo-platform-channel-handle=2008 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 888 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=entity_extraction_service.mojom.Extractor --lang=en-US --service-sandbox-type=entity_extraction --disable-quic --onnx-enabled-for-ee --string-annotations --always-read-main-dll --field-trial-handle=5796,i,1050497738006436231,1821724205066412180,262144 --variations-seed-version --mojo-platform-channel-handle=5584 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 892 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --string-annotations --extension-process --enable-dinosaur-easter-egg-alt-images --video-capture-use-gpu-memory-buffer --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=7 --field-trial-handle=3660,i,1495704470579151534,6402301300846187543,262144 --variations-seed-version=20250221-144540.991000 --mojo-platform-channel-handle=3712 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 1212 | C:\Windows\Microsoft.NET\Framework64\v4.0.30319\cvtres.exe /NOLOGO /READONLY /MACHINE:IX86 "/OUT:C:\Users\admin\AppData\Local\Temp\RES5D49.tmp" "c:\Users\admin\AppData\Local\Temp\CSC24147D377234681AF315D71A9CC2F1B.TMP" | C:\Windows\Microsoft.NET\Framework64\v4.0.30319\cvtres.exe | — | csc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft® Resource File To COFF Object Conversion Utility Exit code: 0 Version: 14.32.31326.0 Modules
| |||||||||||||||
| 1244 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --string-annotations --enable-dinosaur-easter-egg-alt-images --video-capture-use-gpu-memory-buffer --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --field-trial-handle=3168,i,1495704470579151534,6402301300846187543,262144 --variations-seed-version=20250221-144540.991000 --mojo-platform-channel-handle=3404 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 1268 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --always-read-main-dll --field-trial-handle=3564,i,1050497738006436231,1821724205066412180,262144 --variations-seed-version --mojo-platform-channel-handle=3608 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1332 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win64 --annotation=prod=Chrome --annotation=ver=133.0.6943.127 --initial-client-data=0x21c,0x220,0x224,0x1f8,0x228,0x7ffc44dcfff8,0x7ffc44dd0004,0x7ffc44dd0010 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 1336 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win64 --annotation=prod=Chrome --annotation=ver=133.0.6943.127 --initial-client-data=0x21c,0x220,0x224,0x1f8,0x228,0x7ffc44dcfff8,0x7ffc44dd0004,0x7ffc44dd0010 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
Total events
33 341
Read events
33 284
Write events
57
Delete events
0
Modification events
| (PID) Process: | (4984) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (4984) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (4984) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (4984) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (4984) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (6876) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (6876) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (6876) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (6876) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (6876) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
3
Suspicious files
395
Text files
300
Unknown types
37
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2292 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_jpbzngy2.uel.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 2292 | powershell.exe | C:\Users\admin\AppData\Local\Temp\ler0kwb0.0.cs | text | |
MD5:C60E620197B3AA5E9306B58B2DC53407 | SHA256:FCEE29FE956FBAFE9AD6576A9CFAC5C601C3E219A1DE5B3170EE355F880A298E | |||
| 2292 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\4KNAQDQ9GFSGE7FP9O87.temp | binary | |
MD5:AA73FFEF46754EAB4A21722D7F90EA9F | SHA256:7D42A75A19A847A5F39C63BD5210C5CB7340922B076CB2E681845EF9ED38CFFF | |||
| 1212 | cvtres.exe | C:\Users\admin\AppData\Local\Temp\RES5D49.tmp | o | |
MD5:B203184333DE2E5AAC88CFD6FF3B247C | SHA256:19C7309EA183DD8AA2CF11170DC791B16247685CDB9B9117F5A206DE702938FC | |||
| 2292 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\590aee7bdd69b59b.customDestinations-ms~RF18d83a.TMP | binary | |
MD5:00A03B286E6E0EBFF8D9C492365D5EC2 | SHA256:4DBFC417D053BA6867308671F1C61F4DCAFC61F058D4044DB532DA6D3BDE3615 | |||
| 4984 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\ClientCertificates\LOG.old~RF19764f.TMP | — | |
MD5:— | SHA256:— | |||
| 4984 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\ClientCertificates\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2292 | powershell.exe | C:\Users\admin\AppData\Local\Temp\ler0kwb0.cmdline | text | |
MD5:B8A2689562BAD755B463A890D7454958 | SHA256:9E747C726F8DC571BE4D4E8FD63B81925343AD404421996AB734149115BDCB79 | |||
| 2292 | powershell.exe | C:\Users\admin\AppData\Local\Temp\qlymfzza.0.cs | text | |
MD5:ABC13746D876AEE62EB608FC12A8E453 | SHA256:5EBDDCF764BF14282539F137897F863E4BEF0E78C59786DC5892D774990A8523 | |||
| 3768 | csc.exe | C:\Users\admin\AppData\Local\Temp\ler0kwb0.out | text | |
MD5:0778D824933D9A623E4B5419600538C0 | SHA256:FD30037ECEAFD1E5BF625176467474250C2B73B595EA1F287589D27B2B6F253C | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
523
TCP/UDP connections
325
DNS requests
192
Threats
7
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1268 | svchost.exe | GET | 200 | 23.55.110.211:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
3460 | RUXIMICS.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
3460 | RUXIMICS.exe | GET | 200 | 23.55.110.211:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
2292 | powershell.exe | GET | 301 | 146.70.100.103:80 | http://cf-humancheck.info/ | unknown | — | — | unknown |
— | — | GET | 304 | 172.202.163.200:443 | https://slscr.update.microsoft.com/SLS/%7B522D76A4-93E1-47F8-B8CE-07C937AD1A1E%7D/x64/10.0.19045.4046/0?CH=686&L=en-US&P=&PT=0x30&WUA=10.0.19041.3996&MK=DELL&MD=DELL | unknown | — | — | unknown |
5944 | MoUsoCoreWorker.exe | GET | 200 | 23.55.110.211:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6948 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Update%20Signing%20CA%202.1.crl | unknown | — | — | whitelisted |
6948 | SIHClient.exe | GET | 200 | 23.55.110.193:80 | http://crl.microsoft.com/pki/crl/products/MicTimStaPCA_2010-07-01.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1268 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3460 | RUXIMICS.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | 23.55.110.211:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
1268 | svchost.exe | 23.55.110.211:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
3460 | RUXIMICS.exe | 23.55.110.211:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5944 | MoUsoCoreWorker.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
1268 | svchost.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
cf-humancheck.info |
| unknown |
login.live.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
t.me |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2292 | powershell.exe | Not Suspicious Traffic | ET INFO Windows Powershell User-Agent Usage |
— | — | Not Suspicious Traffic | ET INFO Windows Powershell User-Agent Usage |
4836 | explorer.exe | Misc activity | ET INFO Observed Telegram Domain (t .me in TLS SNI) |
— | — | Potentially Bad Traffic | ET INFO HTTP Request to a *.top domain |
2200 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a *.top domain - Likely Hostile |
— | — | Malware Command and Control Activity Detected | MALWARE [ANY.RUN] Win32/Lumma CnC HTTP Activity observed |
— | — | Potentially Bad Traffic | ET INFO HTTP Request to a *.top domain |