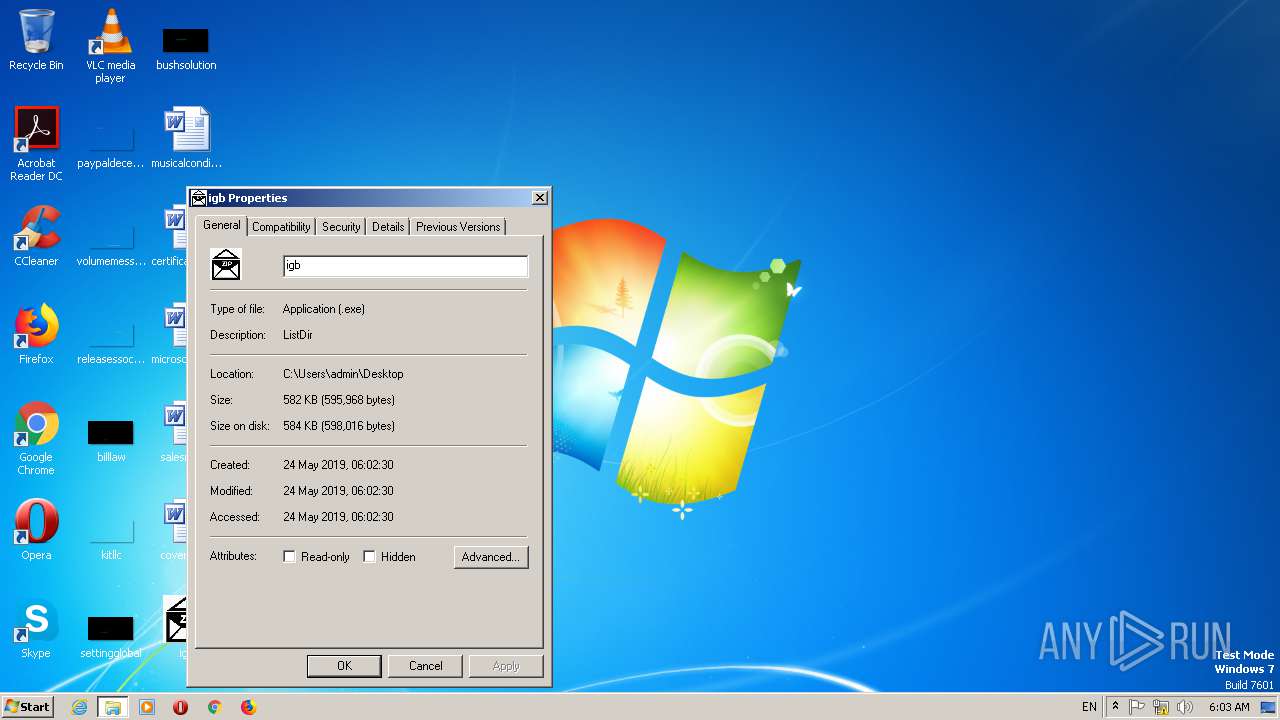
| File name: | igb.exe |
| Full analysis: | https://app.any.run/tasks/dba1266b-db07-41d5-a3dc-7f80853b81f4 |
| Verdict: | Malicious activity |
| Threats: | Agent Tesla is spyware that collects information about the actions of its victims by recording keystrokes and user interactions. It is falsely marketed as a legitimate software on the dedicated website where this malware is sold. |
| Analysis date: | May 24, 2019, 05:02:02 |
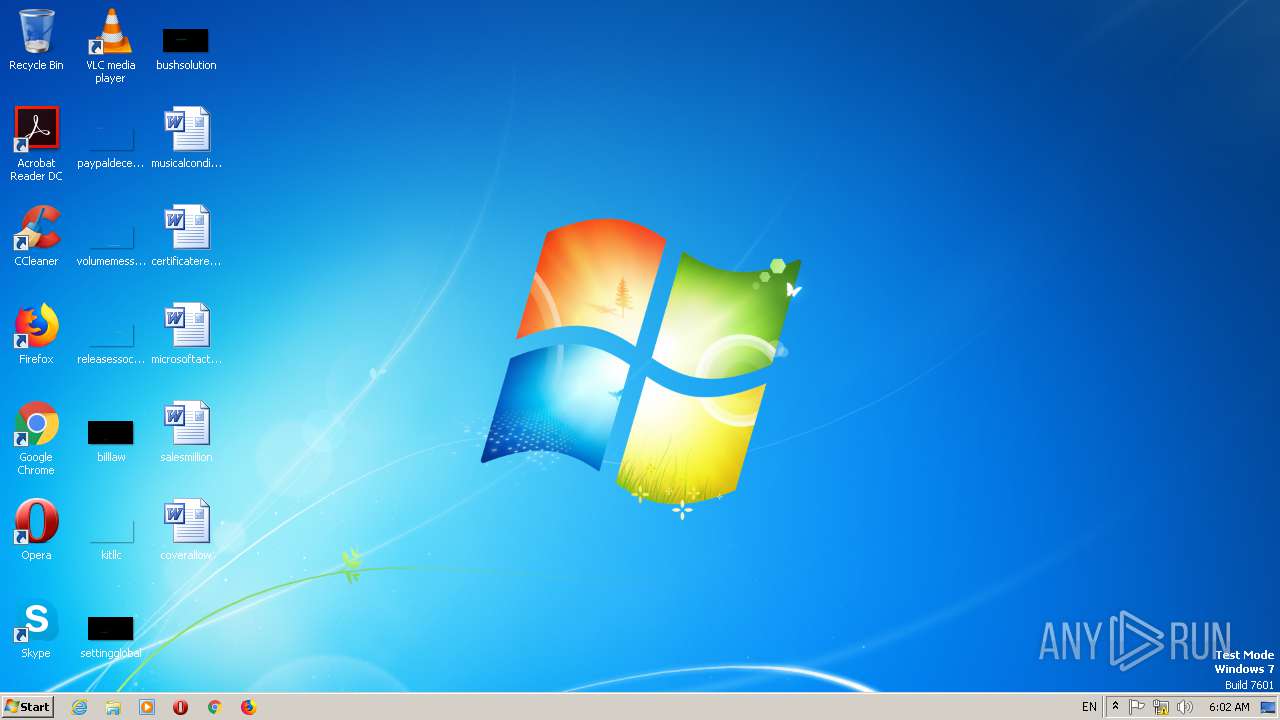
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | BB9793A2ECB16066C9929561A832A3C6 |
| SHA1: | E061258D66C37F178F97DEC906FC61F4CF847CB4 |
| SHA256: | 76DBD2799701596511E00531A851ACBD25AF23CCD2A901A934BE8B8E28CC0A56 |
| SSDEEP: | 6144:EaBqhNoR4sM1O/q9AKa5FnhGyuV77hR8mNOD5aEY3i7O+E4ml2nbhVfGcnB1yJ:EaBWmuZO/ONeFS7dR5OYEAi7O+E1stz |
MALICIOUS
AGENTTESLA was detected
- igb.exe (PID: 2552)
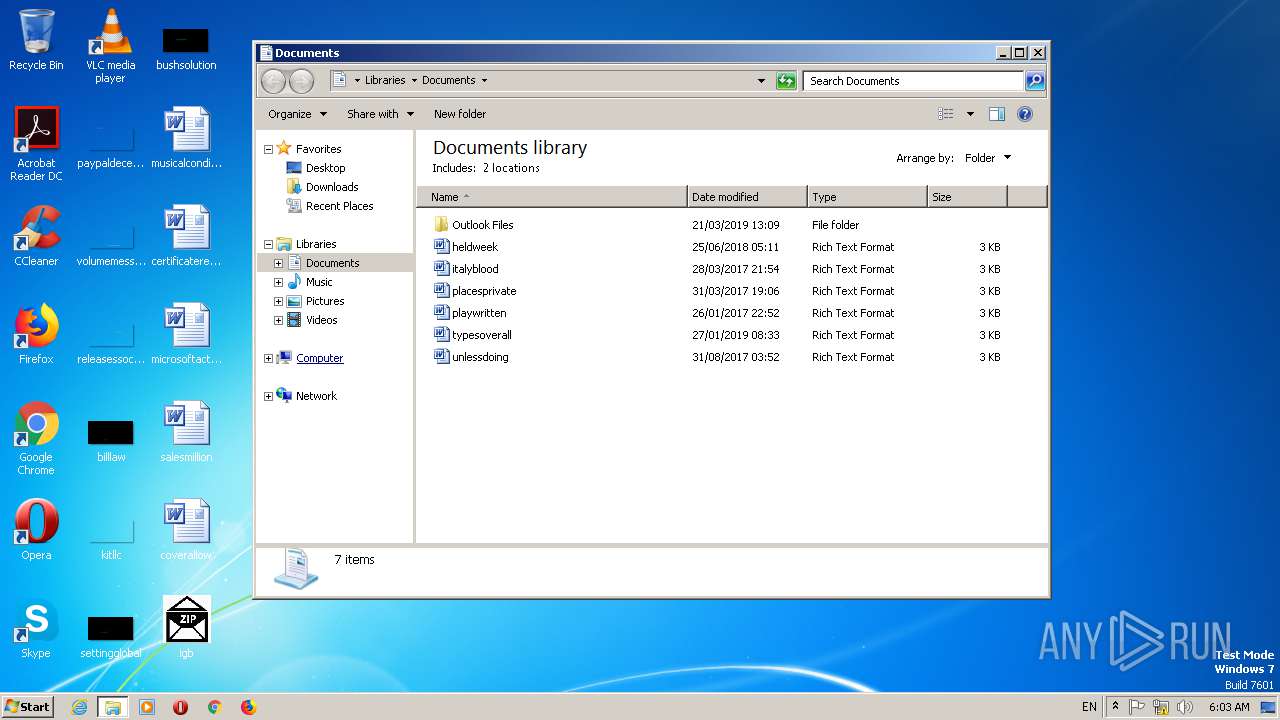
Actions looks like stealing of personal data
- igb.exe (PID: 2552)
SUSPICIOUS
Application launched itself
- igb.exe (PID: 1044)
Executable content was dropped or overwritten
- igb.exe (PID: 2552)
Checks for external IP
- igb.exe (PID: 2552)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (63.1) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (23.8) |
| .dll | | | Win32 Dynamic Link Library (generic) (5.6) |
| .exe | | | Win32 Executable (generic) (3.8) |
| .exe | | | Generic Win/DOS Executable (1.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:05:23 23:46:07+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 8 |
| CodeSize: | 383488 |
| InitializedDataSize: | 211968 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x5f88e |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
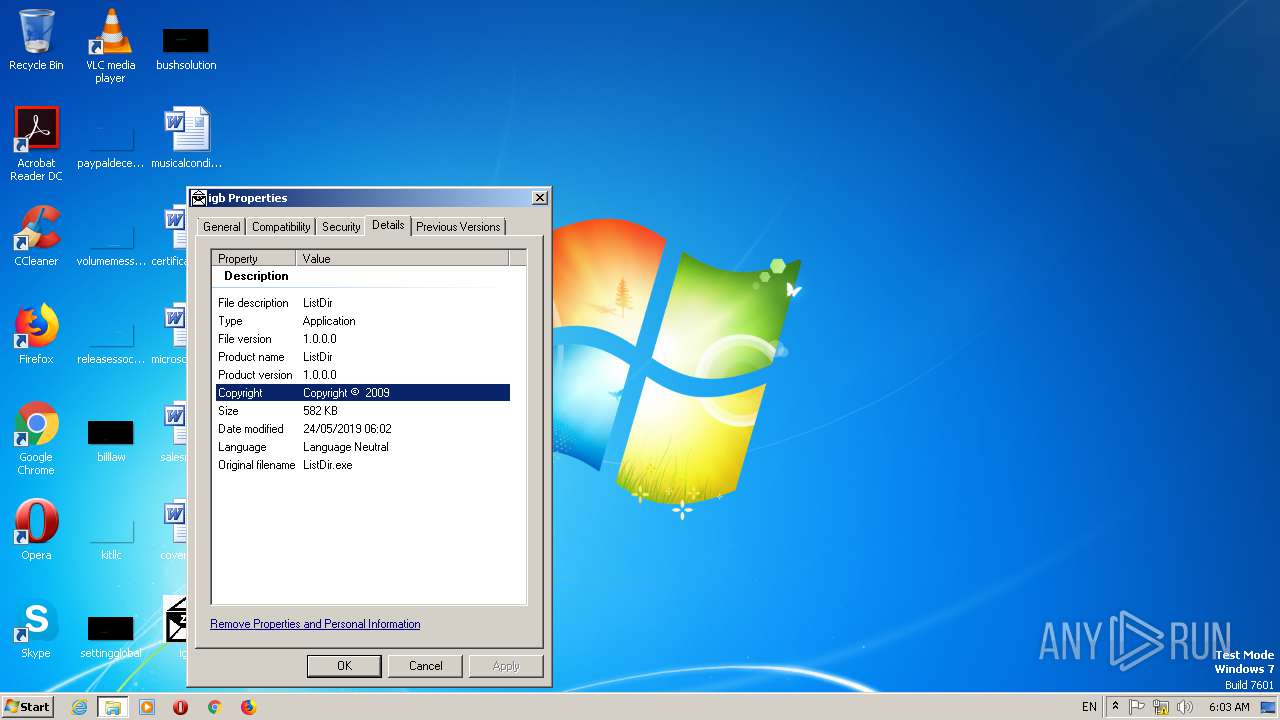
| Comments: | ListDir |
| CompanyName: | - |
| FileDescription: | ListDir |
| FileVersion: | 1.0.0.0 |
| InternalName: | ListDir.exe |
| LegalCopyright: | Copyright © 2009 |
| LegalTrademarks: | - |
| OriginalFileName: | ListDir.exe |
| ProductName: | ListDir |
| ProductVersion: | 1.0.0.0 |
| AssemblyVersion: | 1.0.0.0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 23-May-2019 21:46:07 |
| Comments: | ListDir |
| CompanyName: | - |
| FileDescription: | ListDir |
| FileVersion: | 1.0.0.0 |
| InternalName: | ListDir.exe |
| LegalCopyright: | Copyright © 2009 |
| LegalTrademarks: | - |
| OriginalFilename: | ListDir.exe |
| ProductName: | ListDir |
| ProductVersion: | 1.0.0.0 |
| Assembly Version: | 1.0.0.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 23-May-2019 21:46:07 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00002000 | 0x0005D894 | 0x0005DA00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 7.96812 |
.rsrc | 0x00060000 | 0x00033994 | 0x00033A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 3.7196 |
.reloc | 0x00094000 | 0x0000000C | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 0.10191 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.00112 | 490 | Latin 1 / Western European | UNKNOWN | RT_MANIFEST |
Imports
mscoree.dll |
Total processes
33
Monitored processes
2
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
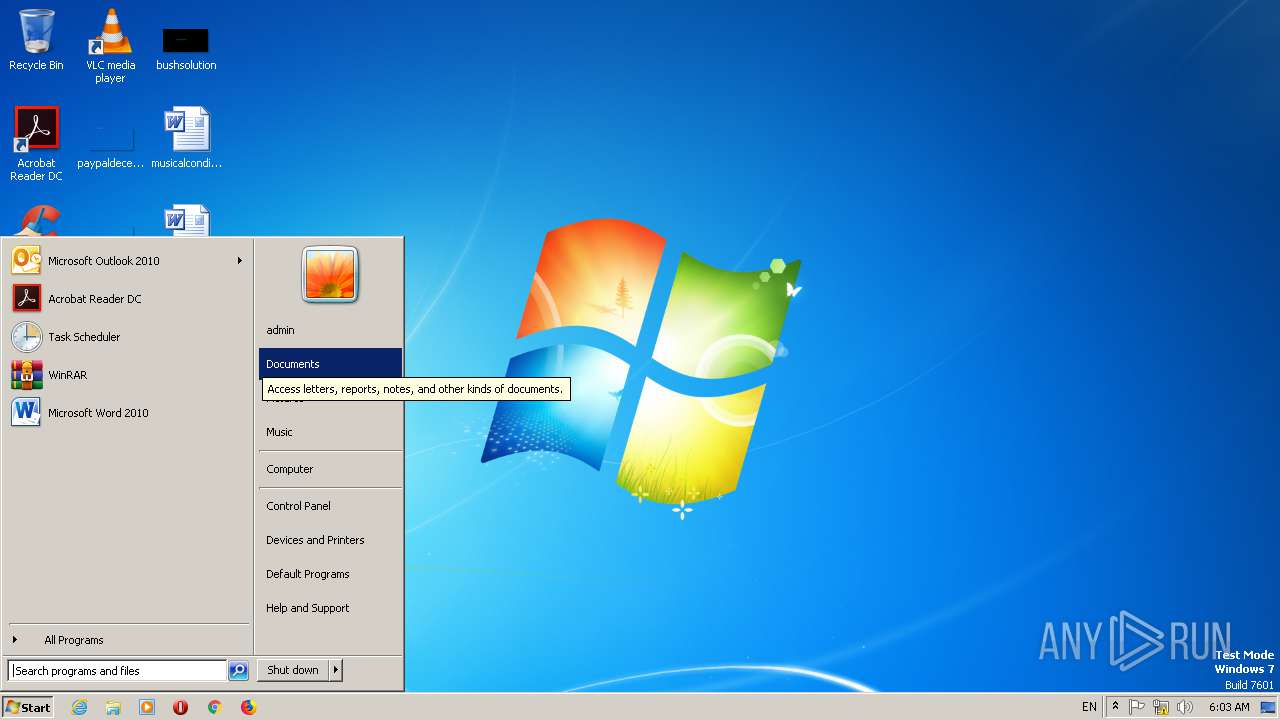
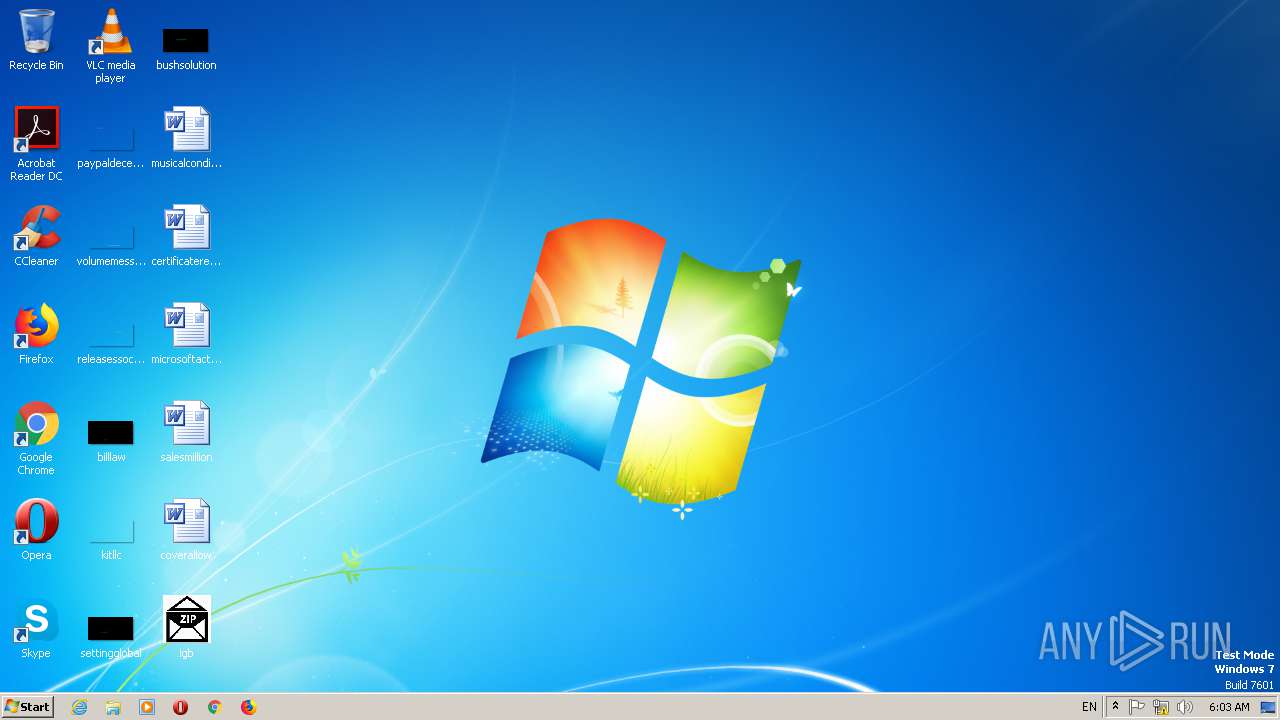
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
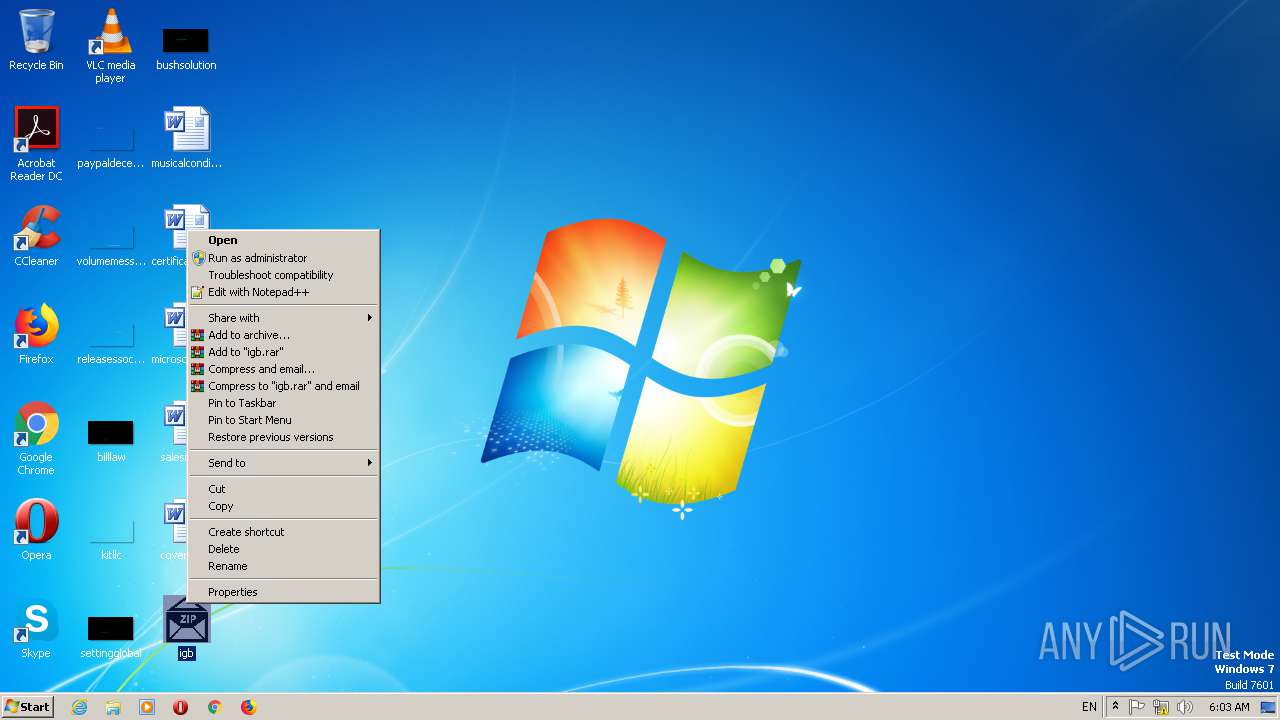
| 1044 | "C:\Users\admin\Desktop\igb.exe" | C:\Users\admin\Desktop\igb.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: ListDir Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 2552 | "C:\Users\admin\Desktop\igb.exe" | C:\Users\admin\Desktop\igb.exe | igb.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: ListDir Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
Total events
69
Read events
48
Write events
21
Delete events
0
Modification events
| (PID) Process: | (2552) igb.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2552) igb.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2552) igb.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2552) igb.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\65\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2552) igb.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Wow6432Node\Microsoft\Tracing |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (2552) igb.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Wow6432Node\Microsoft\Tracing\igb_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (2552) igb.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Wow6432Node\Microsoft\Tracing\igb_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (2552) igb.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Wow6432Node\Microsoft\Tracing\igb_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (2552) igb.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Wow6432Node\Microsoft\Tracing\igb_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (2552) igb.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Wow6432Node\Microsoft\Tracing\igb_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
Executable files
1
Suspicious files
3
Text files
0
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2552 | igb.exe | C:\Users\admin\AppData\Local\Temp\Cab89AA.tmp | — | |
MD5:— | SHA256:— | |||
| 2552 | igb.exe | C:\Users\admin\AppData\Local\Temp\Tar89AB.tmp | — | |
MD5:— | SHA256:— | |||
| 2552 | igb.exe | C:\Users\admin\AppData\Local\Temp\tmpG467.tmp | executable | |
MD5:— | SHA256:— | |||
| 2552 | igb.exe | C:\Users\admin\AppData\Local\Temp\636942746217173750_e61d4c42-1501-4853-9fac-eec99ebaa98d.db | sqlite | |
MD5:— | SHA256:— | |||
| 2552 | igb.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\77EC63BDA74BD0D0E0426DC8F8008506 | compressed | |
MD5:— | SHA256:— | |||
| 2552 | igb.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\E0F5C59F9FA661F6F4C50B87FEF3A15A | binary | |
MD5:— | SHA256:— | |||
| 2552 | igb.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\77EC63BDA74BD0D0E0426DC8F8008506 | binary | |
MD5:— | SHA256:— | |||
| 2552 | igb.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\E0F5C59F9FA661F6F4C50B87FEF3A15A | cat | |
MD5:D4AE187B4574036C2D76B6DF8A8C1A30 | SHA256:A2CE3A0FA7D2A833D1801E01EC48E35B70D84F3467CC9F8FAB370386E13879C7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
4
DNS requests
4
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2552 | igb.exe | GET | 200 | 52.202.139.131:80 | http://checkip.amazonaws.com/ | US | text | 14 b | malicious |
2552 | igb.exe | GET | 200 | 192.35.177.64:80 | http://apps.identrust.com/roots/dstrootcax3.p7c | US | cat | 893 b | shared |
2552 | igb.exe | GET | 200 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?6a35576a372bb611 | US | compressed | 56.1 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2552 | igb.exe | 192.35.177.64:80 | apps.identrust.com | IdenTrust | US | malicious |
2552 | igb.exe | 83.149.71.57:587 | mail.khashcement.com | LeaseWeb Netherlands B.V. | NL | malicious |
2552 | igb.exe | 52.202.139.131:80 | checkip.amazonaws.com | Amazon.com, Inc. | US | shared |
2552 | igb.exe | 93.184.221.240:80 | ctldl.windowsupdate.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
mail.khashcement.com |
| unknown |
apps.identrust.com |
| shared |
ctldl.windowsupdate.com |
| whitelisted |
checkip.amazonaws.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2552 | igb.exe | A Network Trojan was detected | MALWARE [PTsecurity] AgentTesla IP Check |
2 ETPRO signatures available at the full report