| File name: | f_001565 |
| Full analysis: | https://app.any.run/tasks/2a2035fe-5805-4b45-bef7-3ef1f0d4852a |
| Verdict: | Malicious activity |
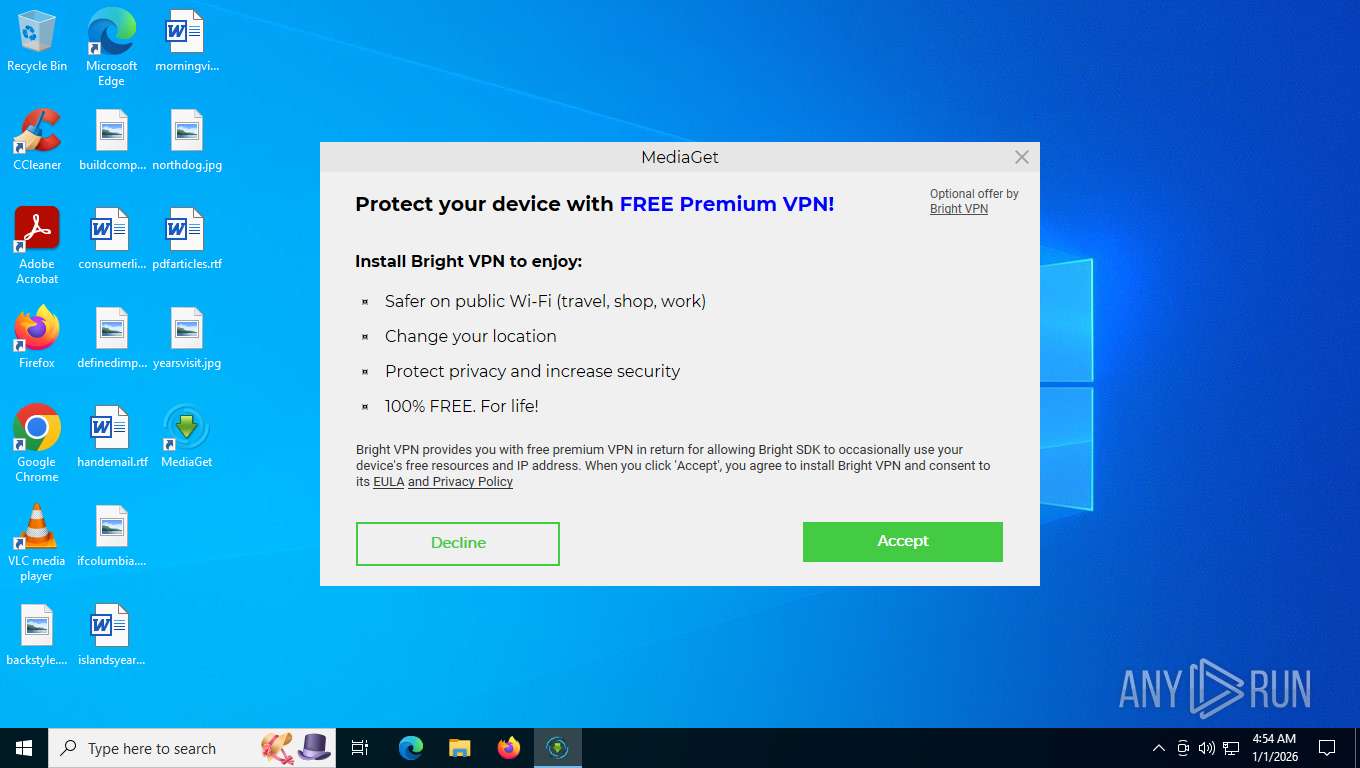
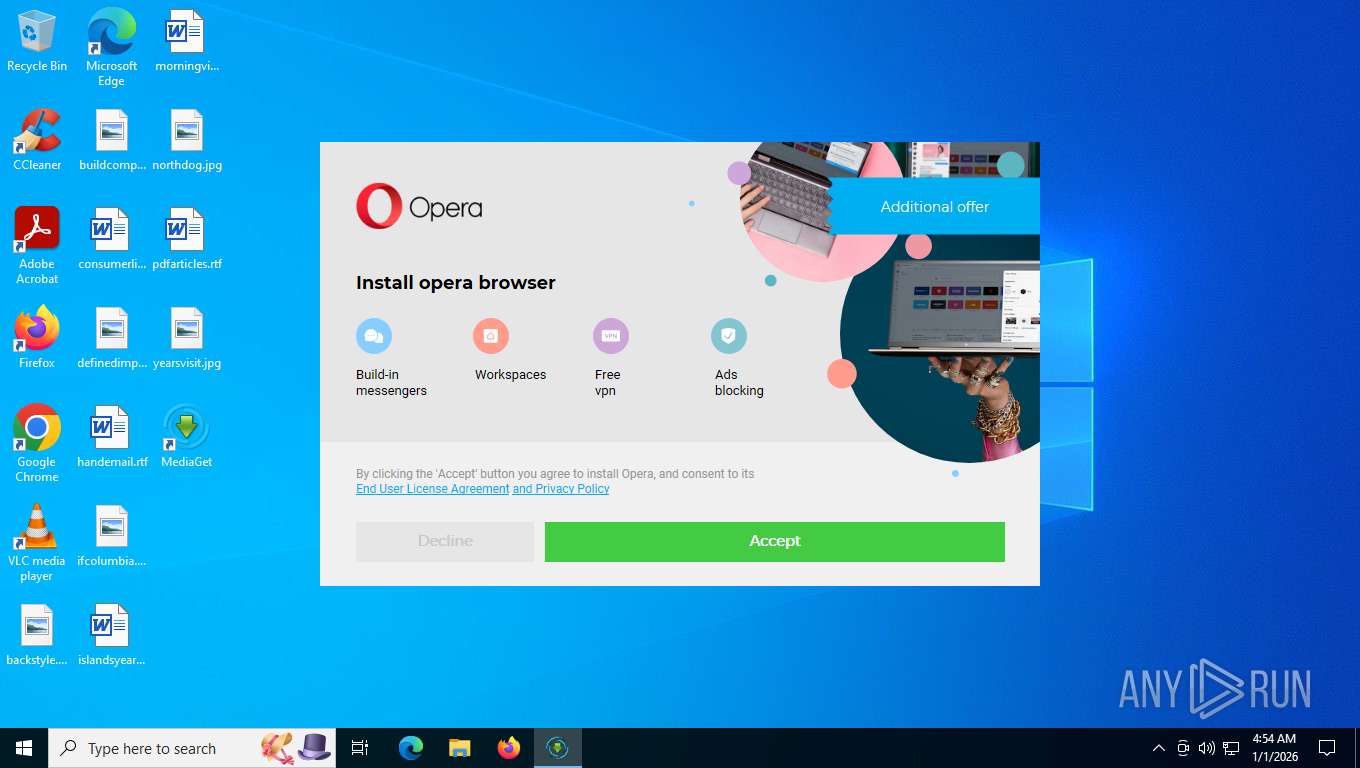
| Threats: | Adware is a form of malware that targets users with unwanted advertisements, often disrupting their browsing experience. It typically infiltrates systems through software bundling, malicious websites, or deceptive downloads. Once installed, it may track user activity, collect sensitive data, and display intrusive ads, including pop-ups or banners. Some advanced adware variants can bypass security measures and establish persistence on devices, making removal challenging. Additionally, adware can create vulnerabilities that other malware can exploit, posing a significant risk to user privacy and system security. |
| Analysis date: | January 01, 2026, 09:54:10 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 5 sections |
| MD5: | 478646169B3F002498C8670BDF09D22A |
| SHA1: | 0CA95914E8ECFD928EC59265B8FEA5D045974573 |
| SHA256: | 76B3193F4B5D620E96C834452143F8C50238A8153A32BF179A8DAA07BAFC3813 |
| SSDEEP: | 98304:us0t9a+UihPpHtPwjE/rwYexVwdfKjNJUks/OoIY5sCL8e6rbLVUpVRdzy5zJwkt:XxJwXy |
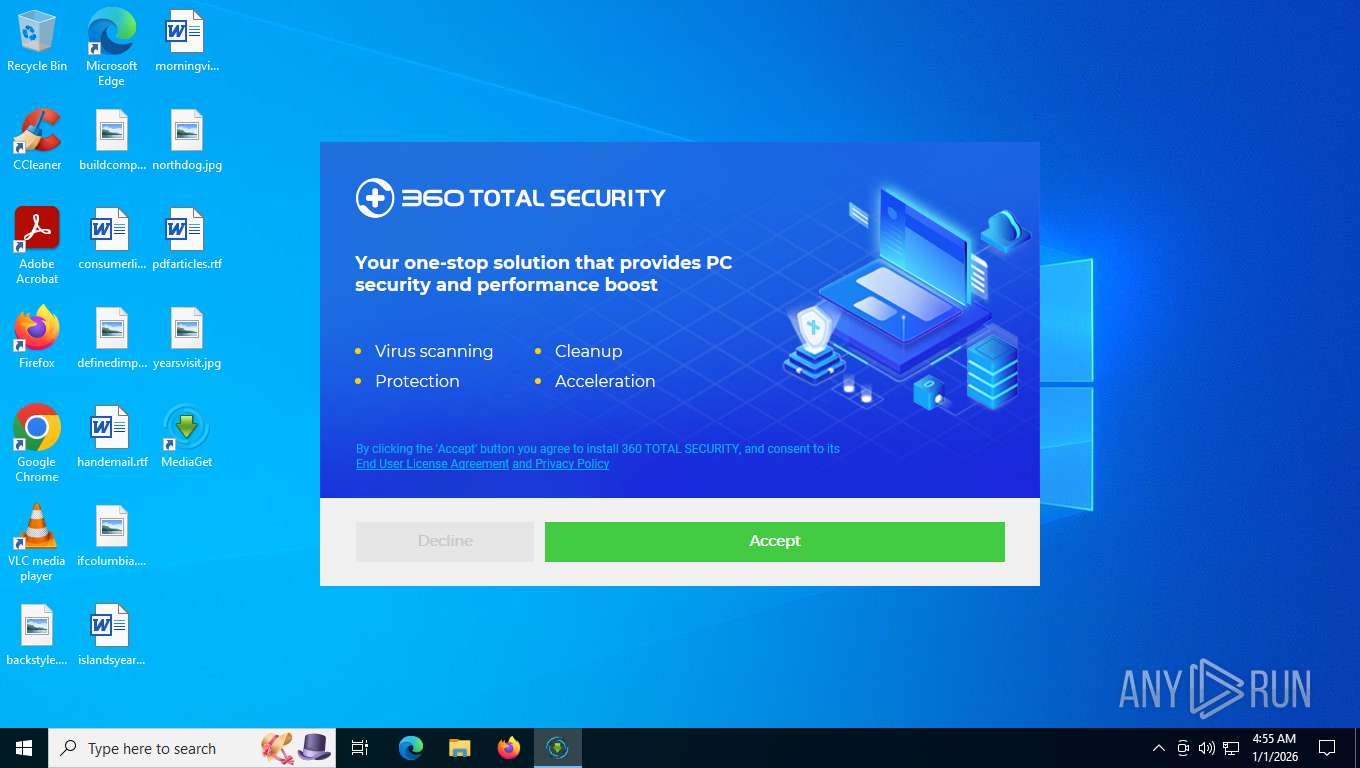
MALICIOUS
Changes the autorun value in the registry
- mediaget.exe (PID: 7276)
- inf_inst.tmp (PID: 5040)
- bdvpn_setup.exe (PID: 7980)
- 360TS_Setup.exe (PID: 4336)
- QHActiveDefense.exe (PID: 8144)
Actions looks like stealing of personal data
- f_001565.exe (PID: 7752)
- mediaget.exe (PID: 7276)
- 360TS_Setup.exe (PID: 4336)
- csrss.exe (PID: 652)
- regsvr32.exe (PID: 8720)
- PowerSaver.exe (PID: 7716)
- WscReg.exe (PID: 3236)
- WscReg.exe (PID: 5480)
- EaInstHelper64.exe (PID: 7984)
- QHActiveDefense.exe (PID: 2448)
- QHActiveDefense.exe (PID: 8144)
- QHSafeTray.exe (PID: 5636)
- QHSafeTray.exe (PID: 8980)
- PopWndLog.exe (PID: 5284)
- regsvr32.exe (PID: 8756)
- PopWndLog.exe (PID: 4288)
- csrss.exe (PID: 564)
- QHSafeTray.exe (PID: 8924)
- KB931125-rootsupd.exe (PID: 9300)
- regsvr32.exe (PID: 9404)
- regsvr32.exe (PID: 9412)
- WscReg.exe (PID: 9540)
- WscReg.exe (PID: 9644)
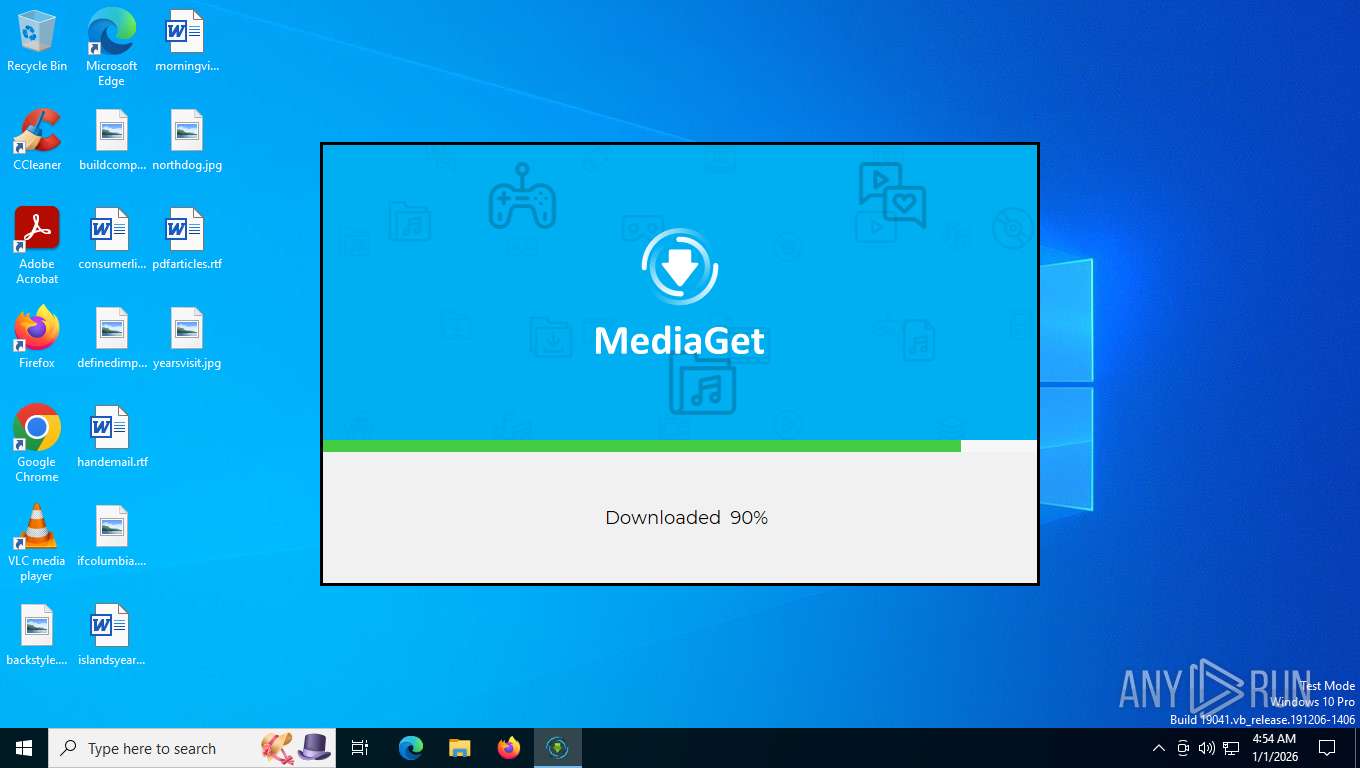
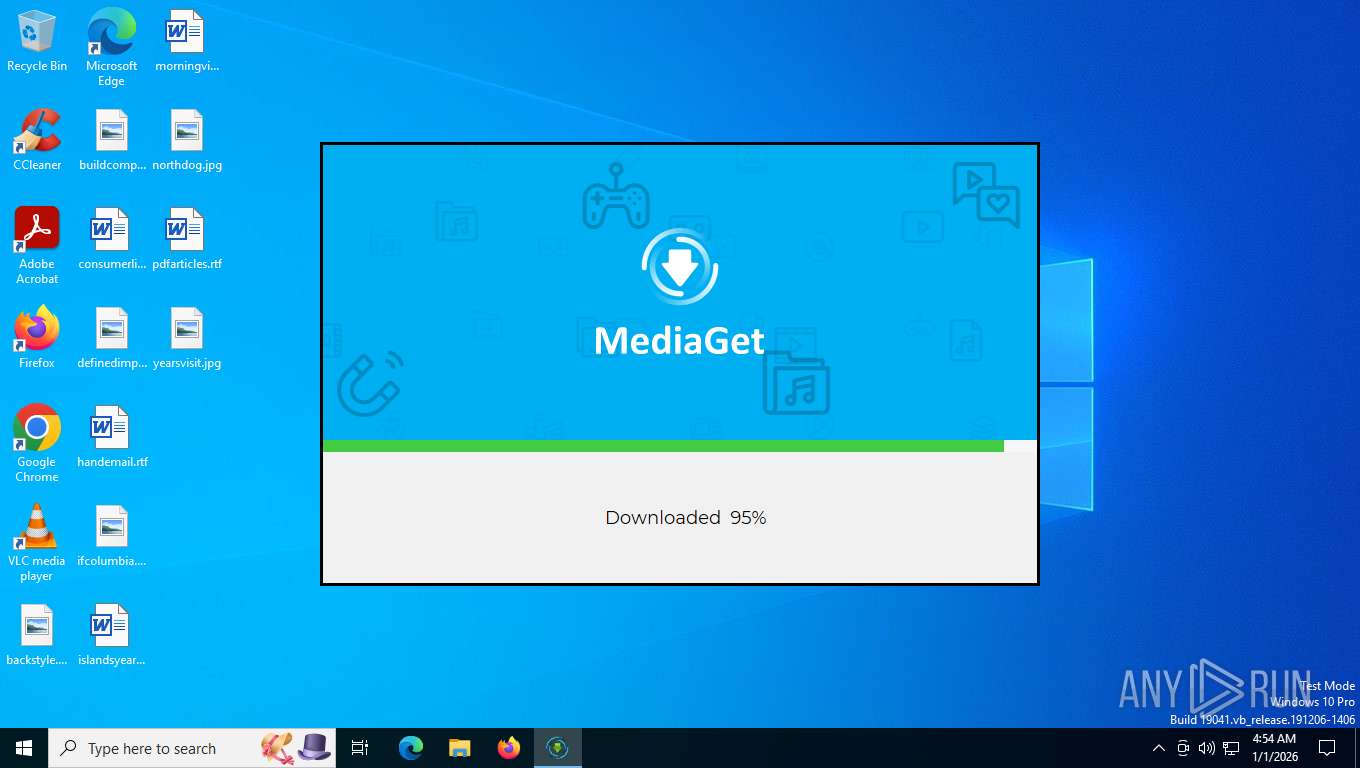
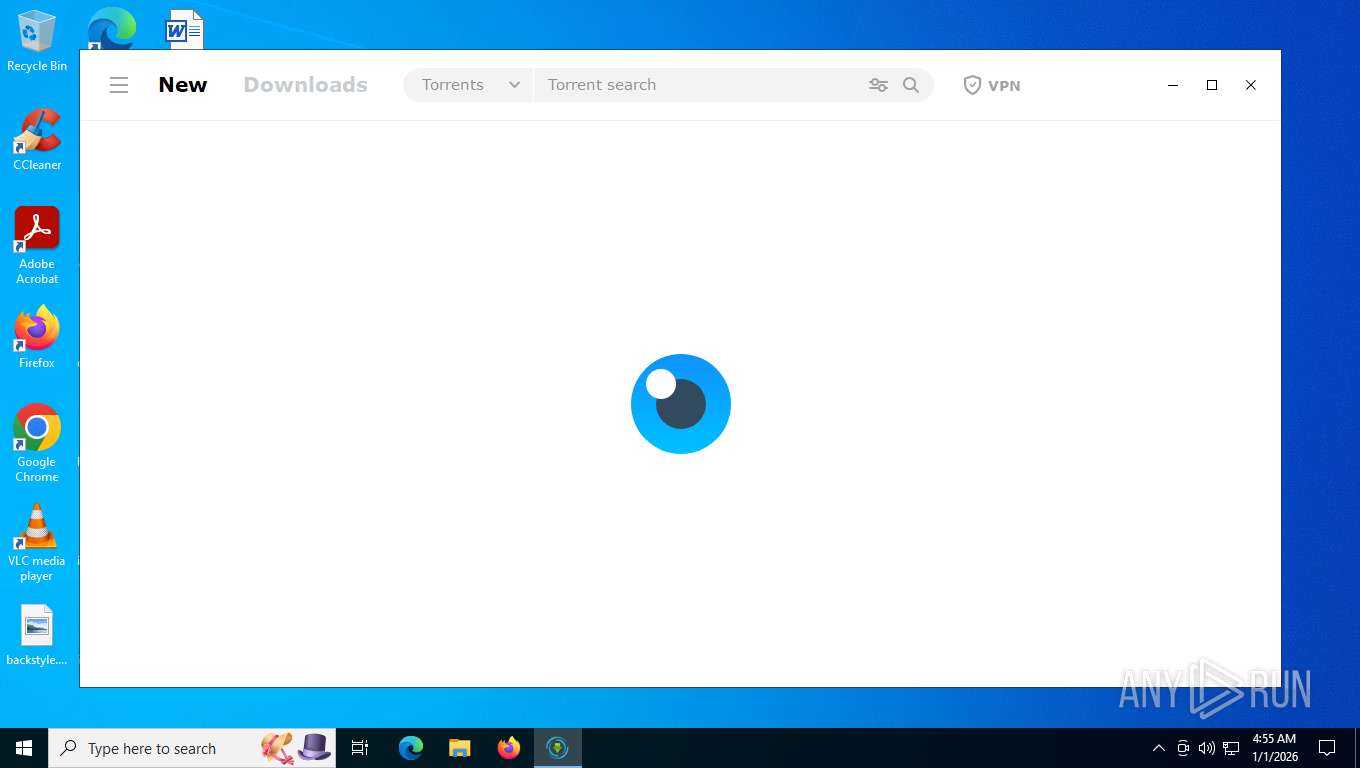
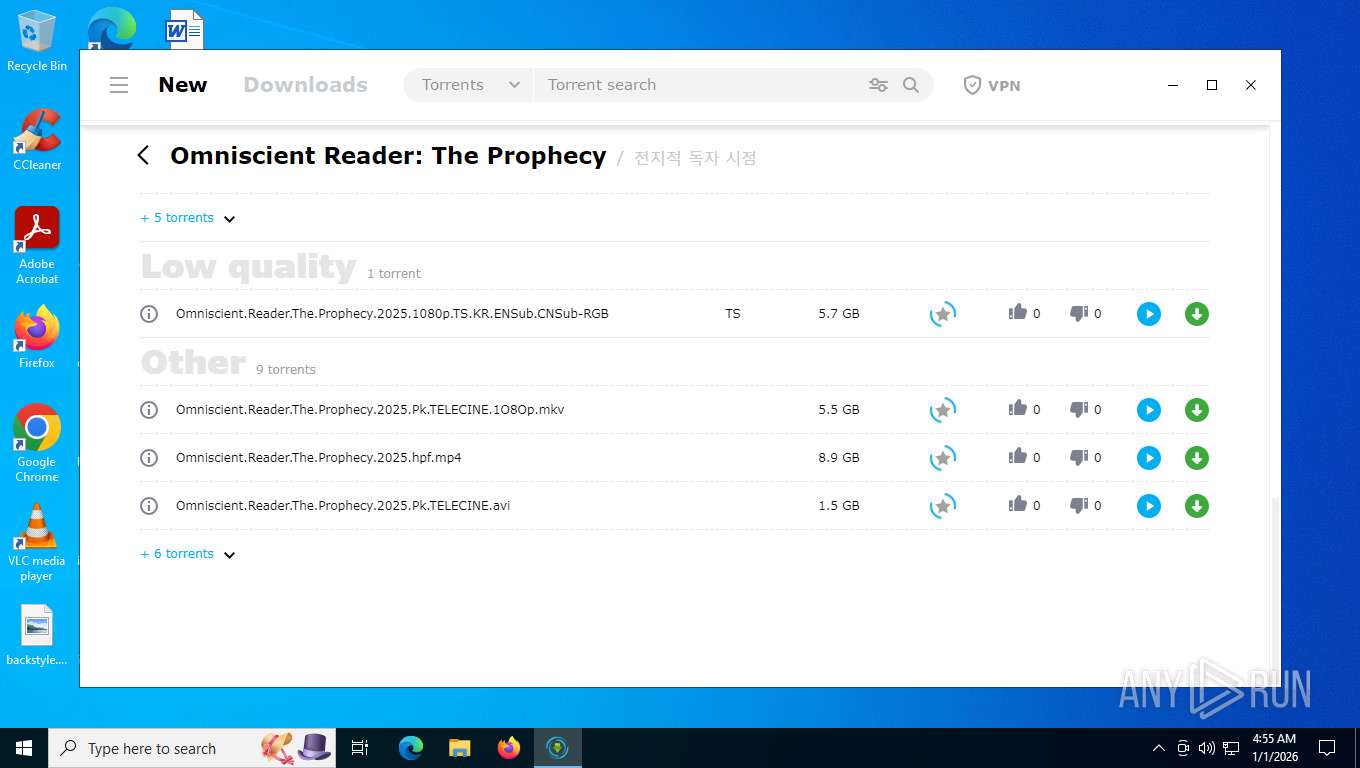
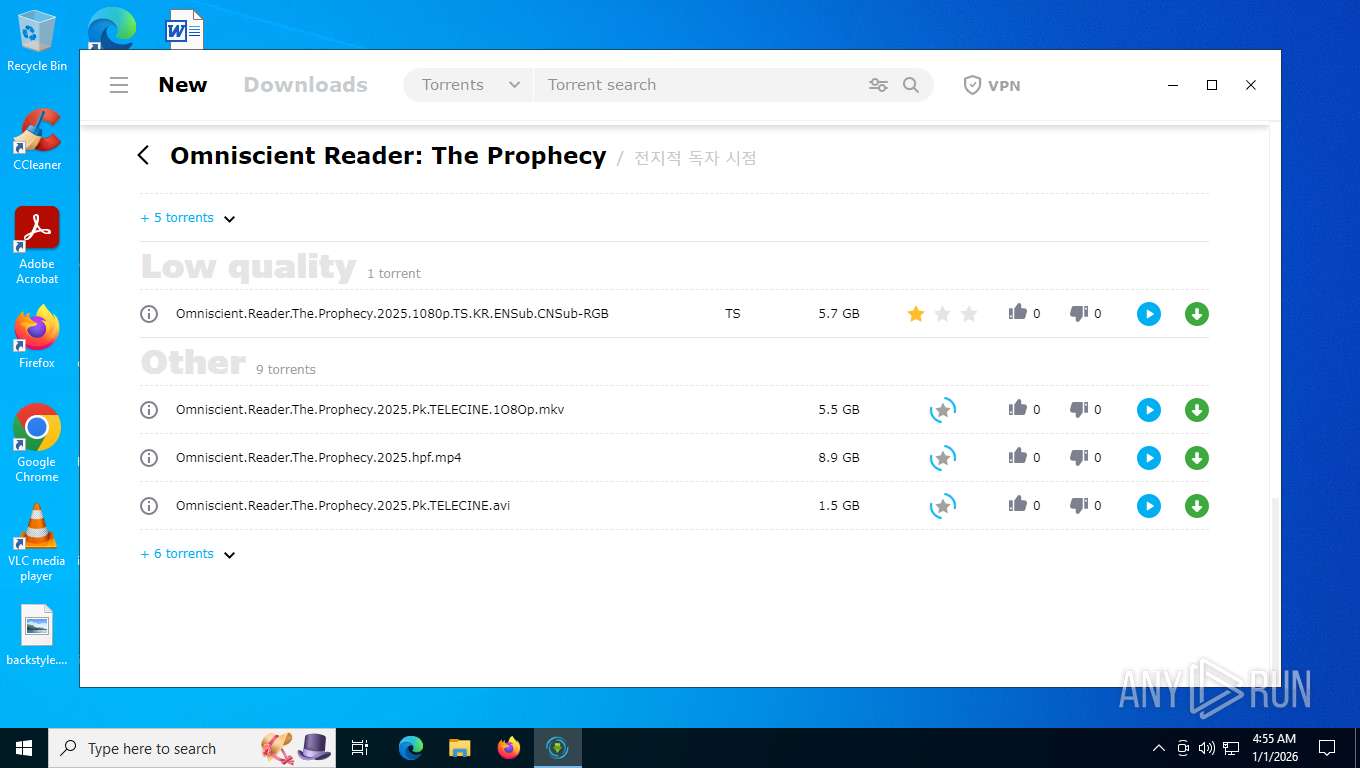
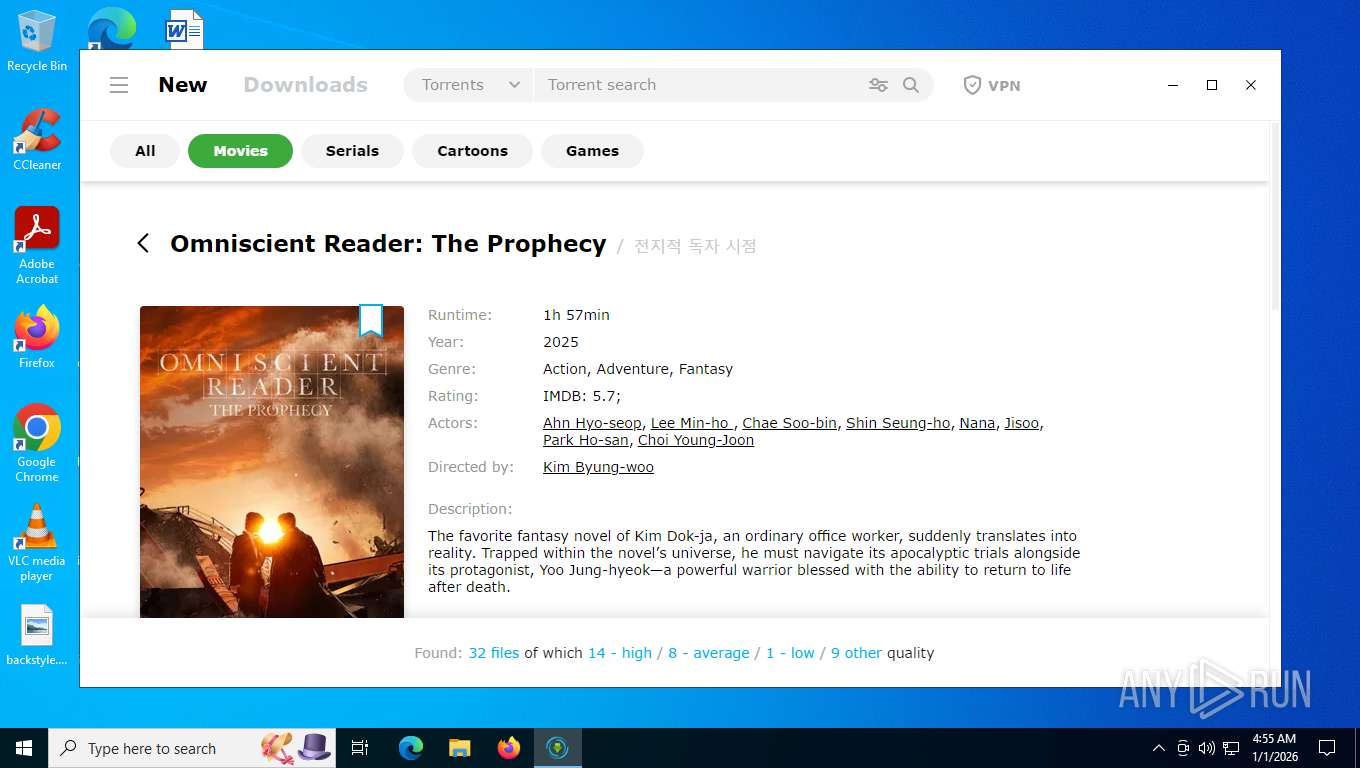
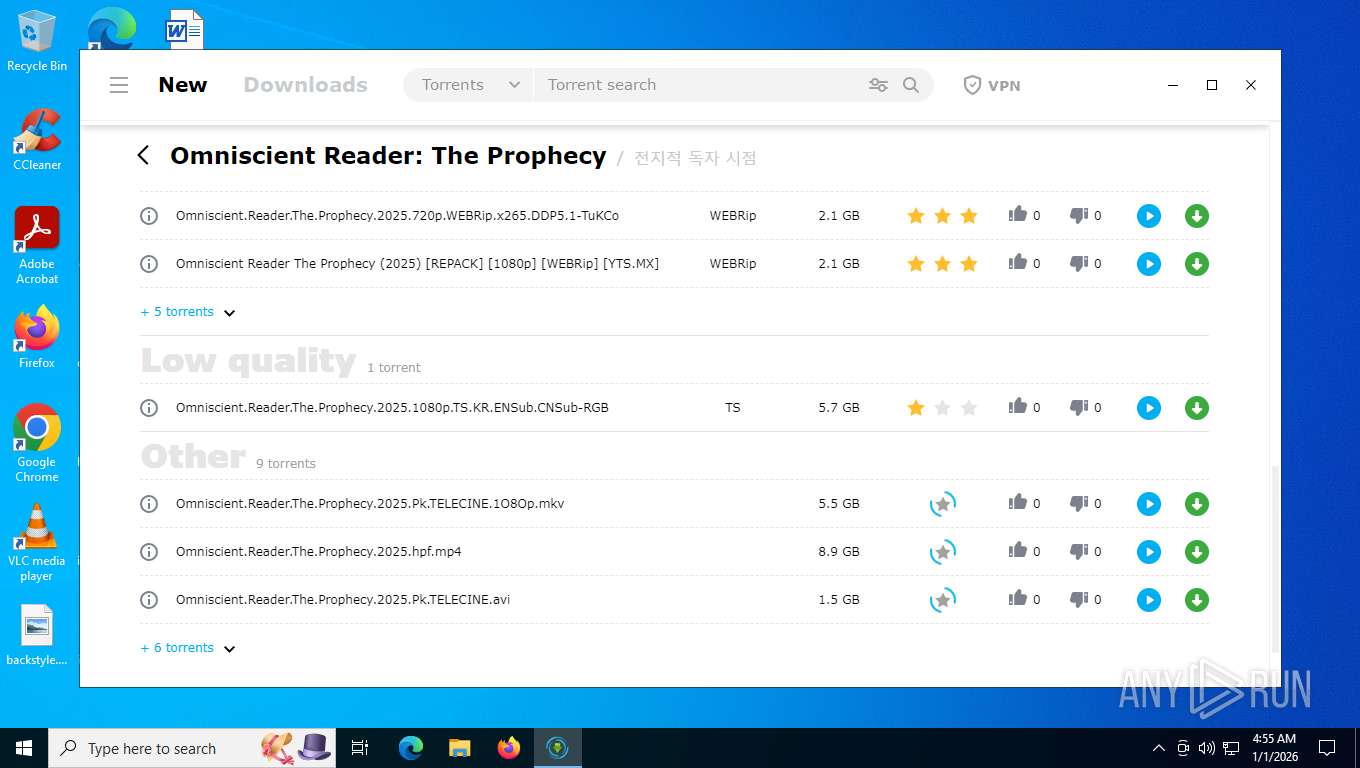
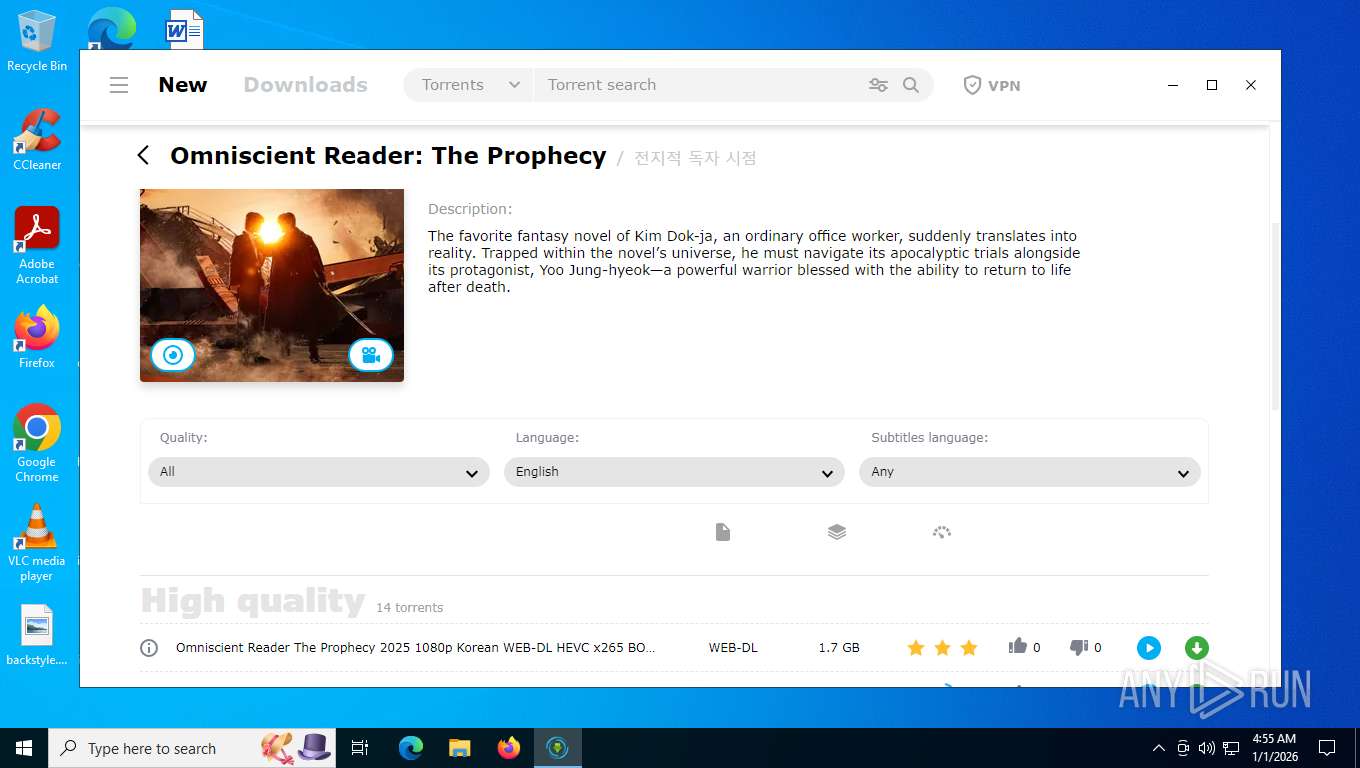
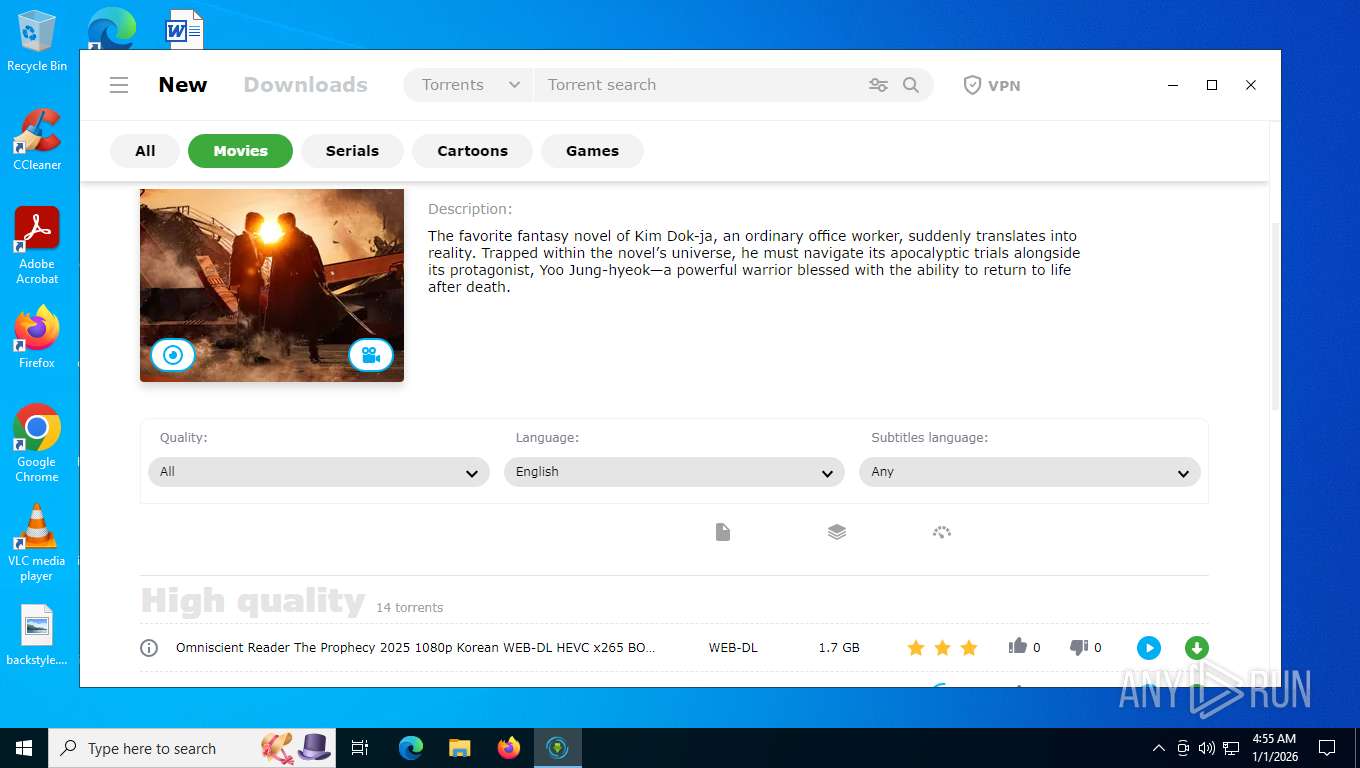
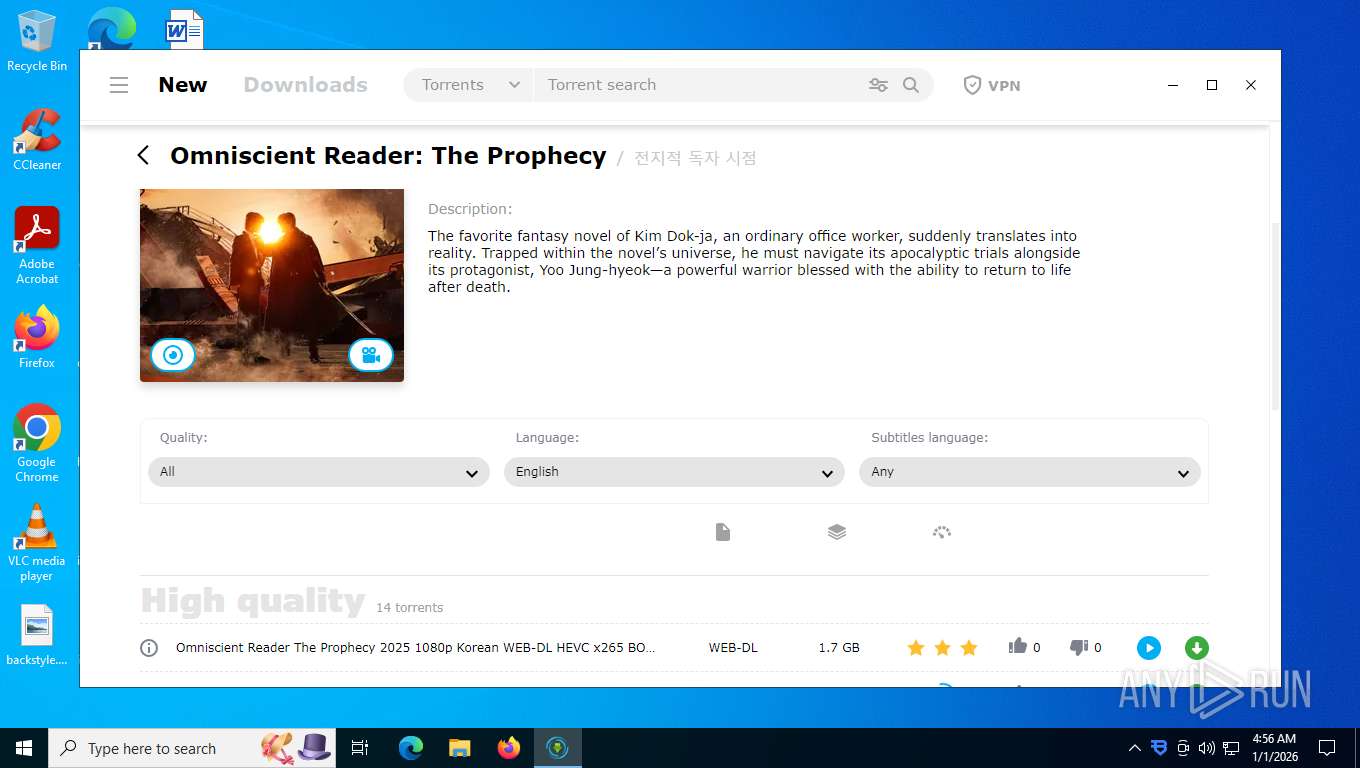
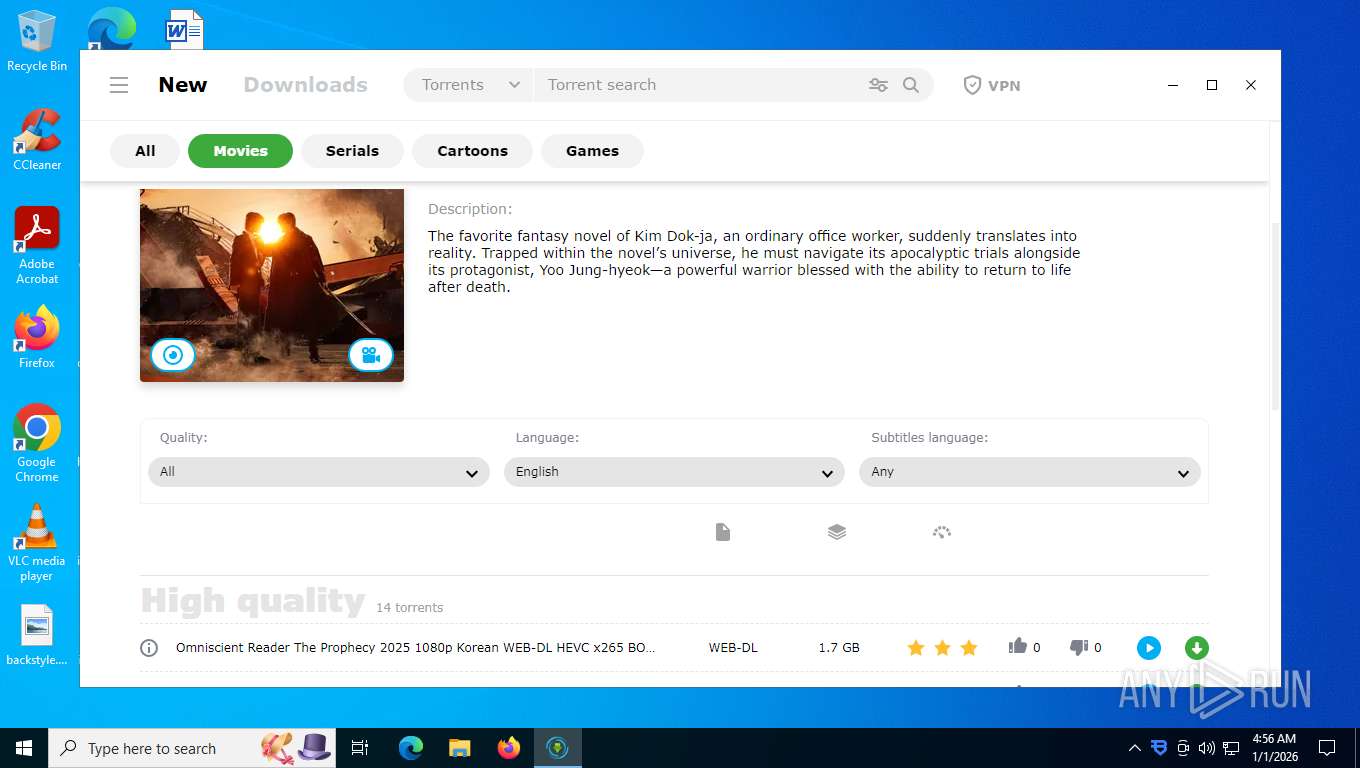
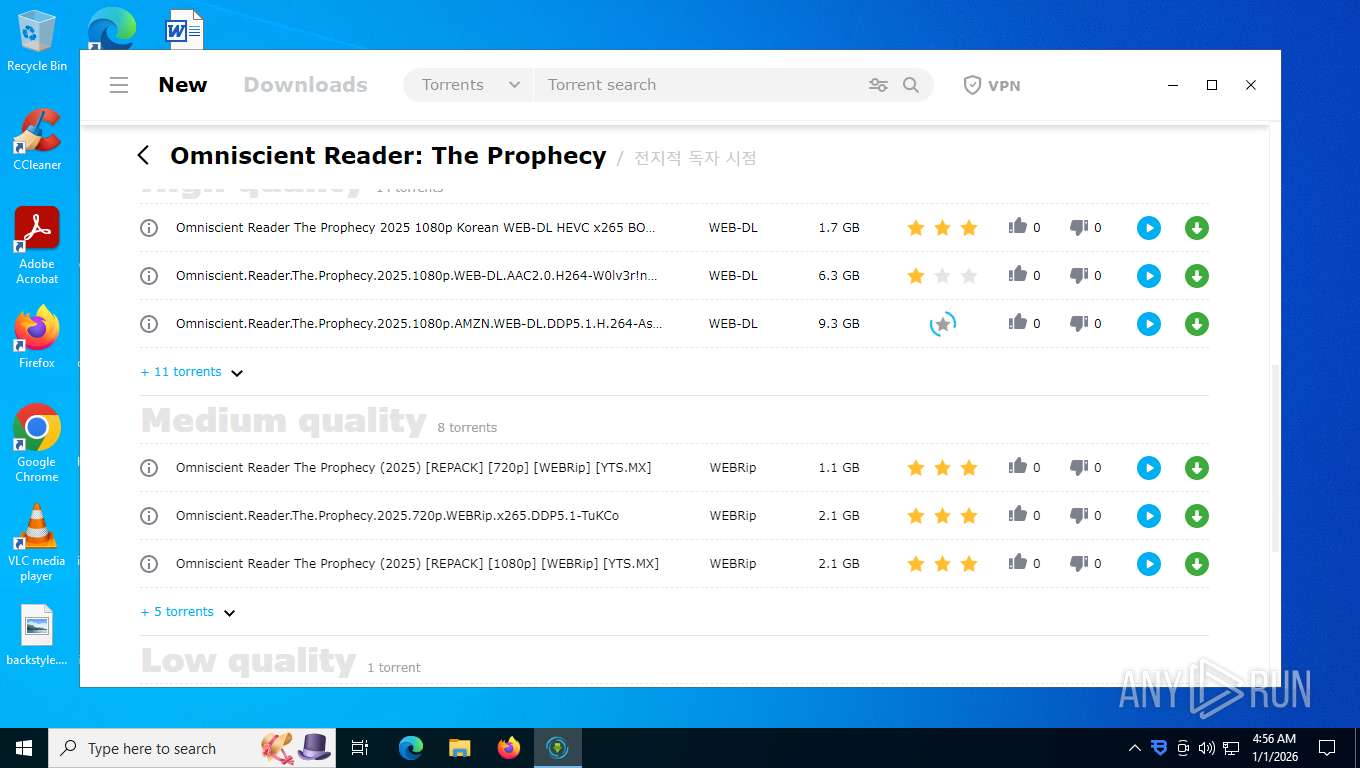
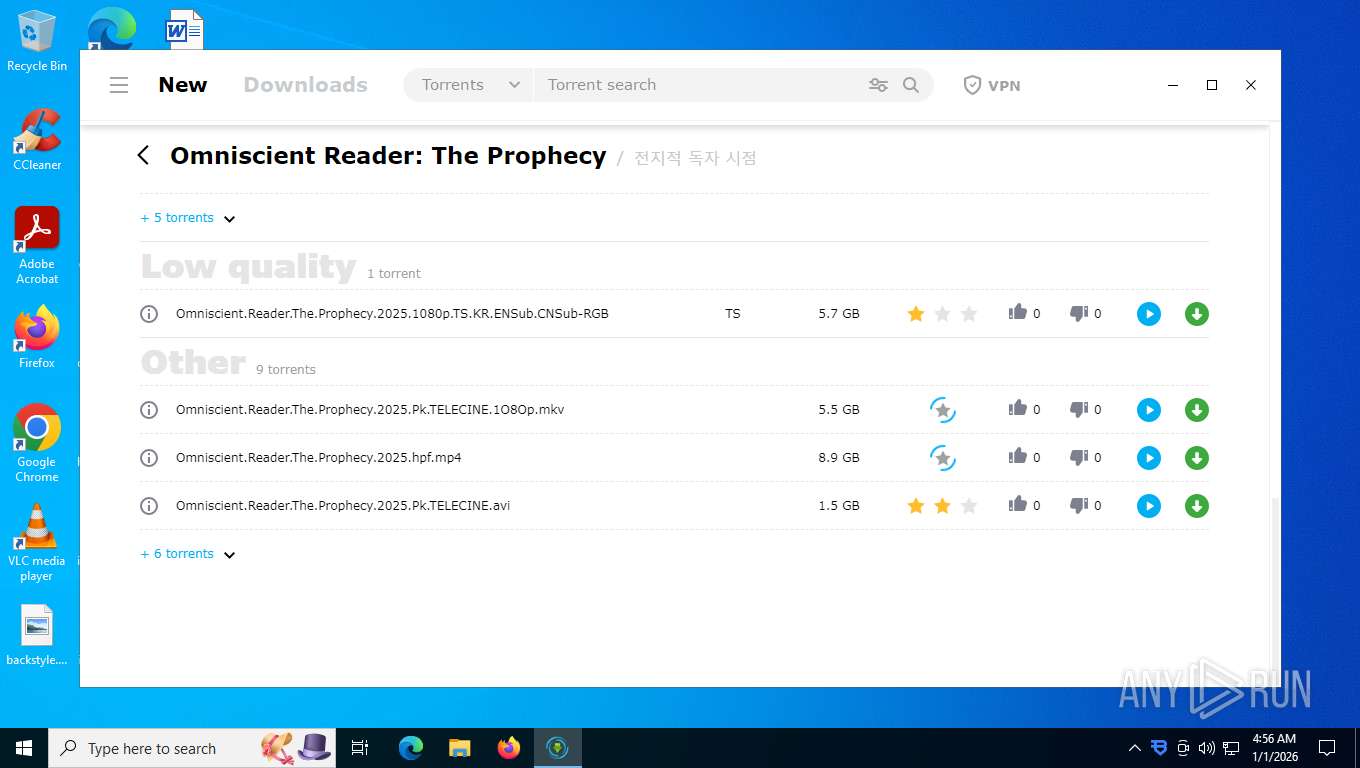
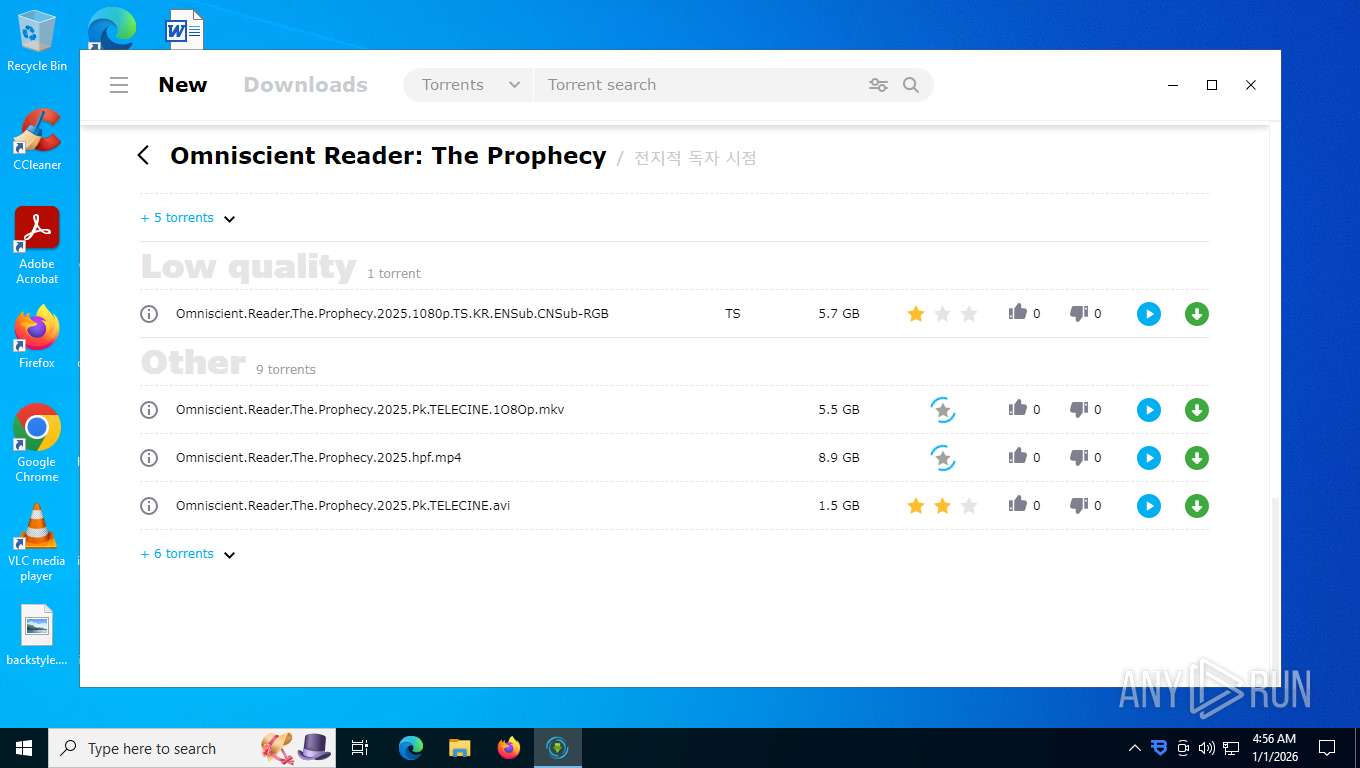
BITTORRENT has been detected (SURICATA)
- mediaget.exe (PID: 7276)
Starts NET.EXE for service management
- bdvpn_setup.exe (PID: 7980)
- net.exe (PID: 7832)
Registers / Runs the DLL via REGSVR32.EXE
- 360TS_Setup.exe (PID: 4336)
- QHSafeTray.exe (PID: 5636)
- QHActiveDefense.exe (PID: 8144)
Executing a file with an untrusted certificate
- PowerSaver.exe (PID: 7716)
- EaInstHelper64.exe (PID: 7984)
- QHWatchdog.exe (PID: 8628)
- QHWatchdog.exe (PID: 7716)
- KB931125-rootsupd.exe (PID: 9300)
Changes settings of System certificates
- PowerSaver.exe (PID: 7716)
- WscReg.exe (PID: 5480)
- updroots.exe (PID: 9444)
- updroots.exe (PID: 9324)
- updroots.exe (PID: 9352)
- 360TS_Setup.exe (PID: 4336)
SUSPICIOUS
Reads security settings of Internet Explorer
- f_001565.exe (PID: 7752)
- bdvpn_setup.exe (PID: 7980)
- brightvpn_installer.exe (PID: 1520)
- net_updater32.exe (PID: 4632)
- net_updater32.exe (PID: 3444)
- antivirus360.exe (PID: 5180)
- net_updater32.exe (PID: 5592)
- net_updater32.exe (PID: 1232)
- net_updater32.exe (PID: 7220)
- Bright VPN.exe (PID: 7780)
- net_updater32.exe (PID: 2864)
- 360TS_Setup.exe (PID: 4336)
- QHSafeTray.exe (PID: 5636)
- PopWndLog.exe (PID: 5284)
- PopWndLog.exe (PID: 4288)
Reads Internet Explorer settings
- f_001565.exe (PID: 7752)
Executable content was dropped or overwritten
- f_001565.exe (PID: 7752)
- bdvpn_setup.exe (PID: 7980)
- mediaget.exe (PID: 7276)
- net_updater32.exe (PID: 4632)
- antivirus360.exe (PID: 5180)
- net_updater32.exe (PID: 5592)
- inf_inst.tmp (PID: 5040)
- inf_inst.exe (PID: 1908)
- net_updater32.exe (PID: 1232)
- Bright VPN.exe (PID: 7780)
- net_updater32.exe (PID: 2864)
- net_updater32.exe (PID: 1344)
- 360TS_Setup.exe (PID: 7888)
- 360TS_Setup.exe (PID: 4336)
- EaInstHelper64.exe (PID: 7984)
- QHActiveDefense.exe (PID: 2448)
- KB931125-rootsupd.exe (PID: 9300)
- QHActiveDefense.exe (PID: 8144)
The process drops C-runtime libraries
- f_001565.exe (PID: 7752)
- net_updater32.exe (PID: 4632)
- mediaget.exe (PID: 7276)
Process drops legitimate windows executable
- f_001565.exe (PID: 7752)
- net_updater32.exe (PID: 4632)
- bdvpn_setup.exe (PID: 7980)
- mediaget.exe (PID: 7276)
- 360TS_Setup.exe (PID: 4336)
- KB931125-rootsupd.exe (PID: 9300)
Reads Microsoft Outlook installation path
- f_001565.exe (PID: 7752)
Malware-specific behavior (creating "System.dll" in Temp)
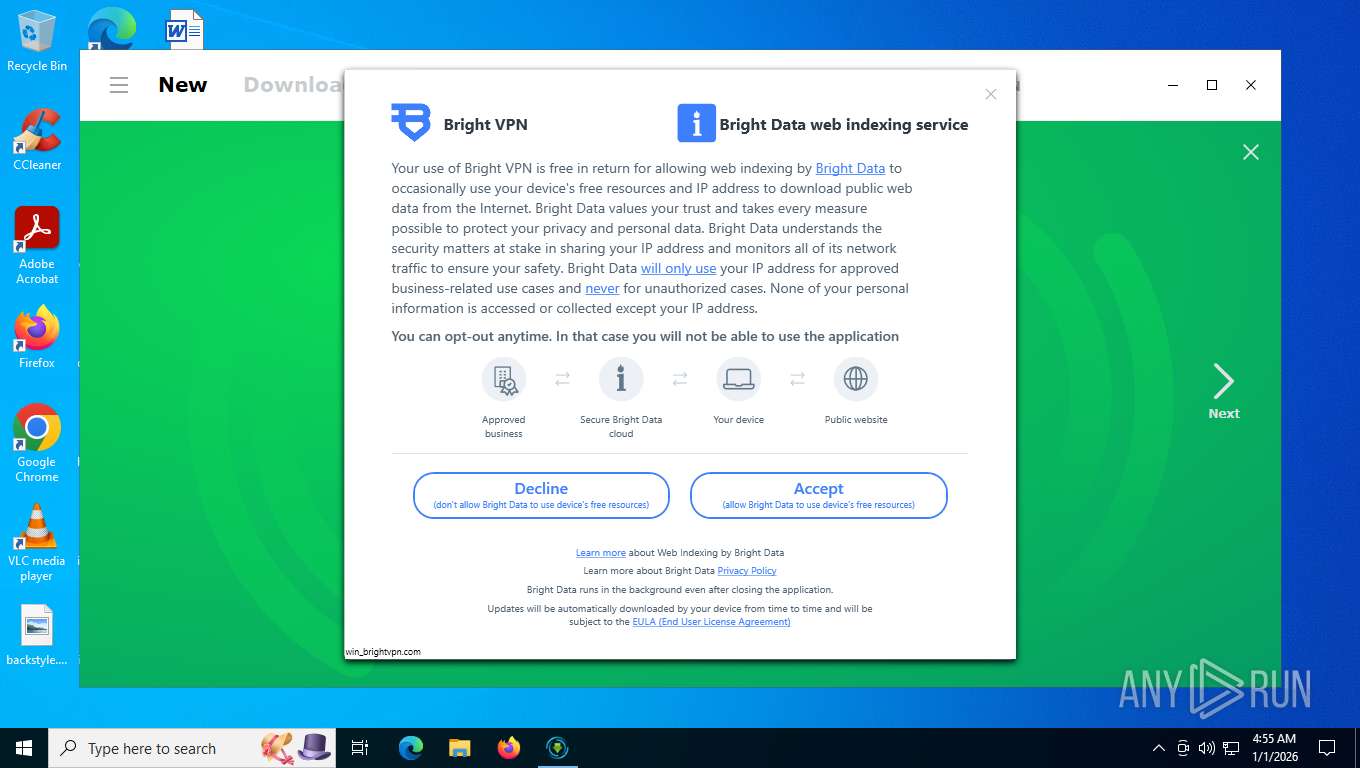
- bdvpn_setup.exe (PID: 7980)
The process creates files with name similar to system file names
- bdvpn_setup.exe (PID: 7980)
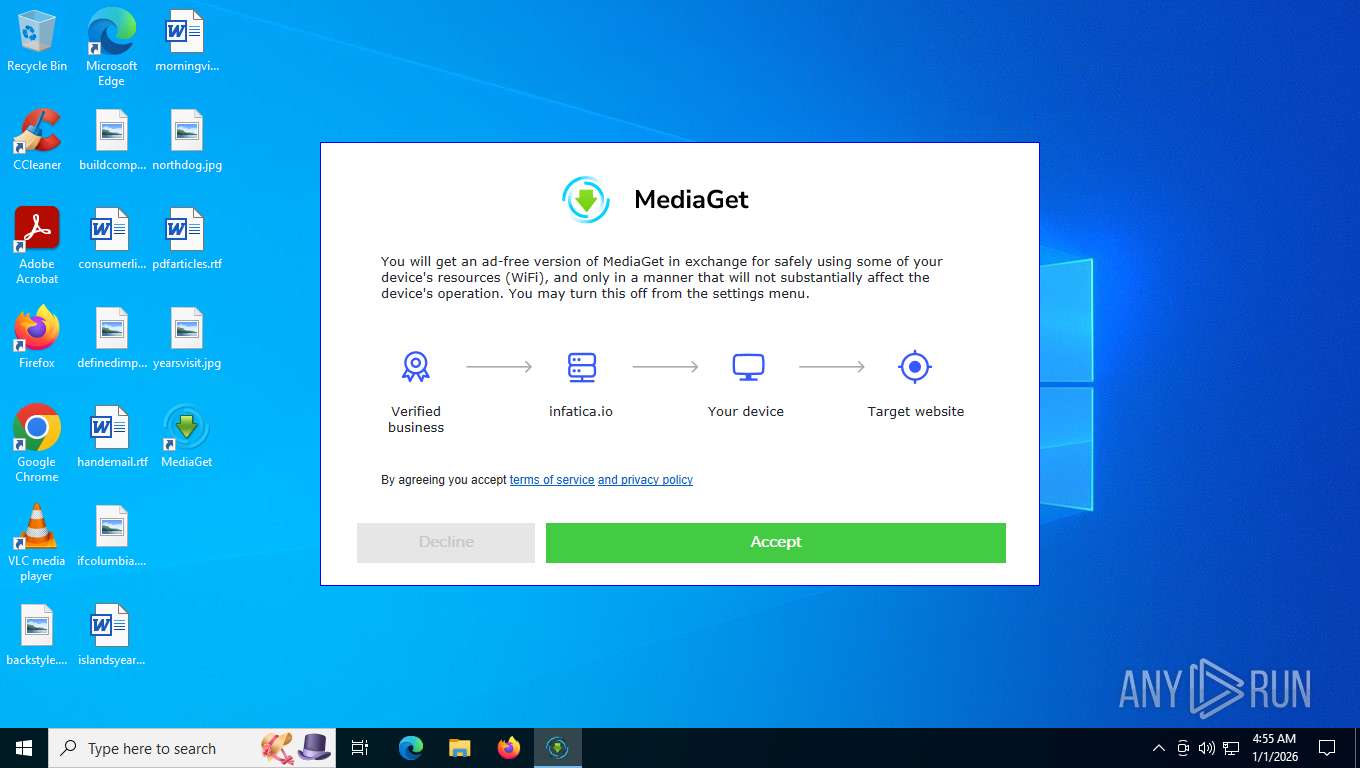
Potential Corporate Privacy Violation
- mediaget.exe (PID: 7276)
Application launched itself
- net_updater32.exe (PID: 4632)
- net_updater32.exe (PID: 3444)
- net_updater32.exe (PID: 1232)
- Bright VPN.exe (PID: 7780)
- QHSafeTray.exe (PID: 5636)
- PopWndLog.exe (PID: 5284)
- WscReg.exe (PID: 9540)
Found regular expressions for crypto-addresses (YARA)
- mediaget.exe (PID: 7276)
Reads the Windows owner or organization settings
- inf_inst.tmp (PID: 5040)
Uses TASKKILL.EXE to kill process
- inf_inst.tmp (PID: 5040)
Starts POWERSHELL.EXE for commands execution
- bdvpn_setup.exe (PID: 7980)
Reads binary file using Get-Content
- powershell.exe (PID: 7360)
- powershell.exe (PID: 7852)
Connects to unusual port
- mediaget.exe (PID: 7276)
Probably obfuscated PowerShell command line is found
- bdvpn_setup.exe (PID: 7980)
Drops 7-zip archiver for unpacking
- bdvpn_setup.exe (PID: 7980)
- 360TS_Setup.exe (PID: 4336)
There is functionality for taking screenshot (YARA)
- mediaget.exe (PID: 7276)
- QtWebEngineProcess.exe (PID: 7912)
- QtWebEngineProcess.exe (PID: 8016)
- QtWebEngineProcess.exe (PID: 3192)
- QtWebEngineProcess.exe (PID: 6244)
- Bright VPN.exe (PID: 7436)
Process drops python dynamic module
- mediaget.exe (PID: 7276)
Starts CMD.EXE for commands execution
- Bright VPN.exe (PID: 7780)
Uses WMIC.EXE to obtain Windows Installer data
- cmd.exe (PID: 5148)
Executes as Windows Service
- net_updater32.exe (PID: 1344)
- WmiApSrv.exe (PID: 7028)
- WscReg.exe (PID: 5480)
- QHActiveDefense.exe (PID: 8144)
- WscReg.exe (PID: 9540)
Starts itself from another location
- 360TS_Setup.exe (PID: 7888)
The process checks if it is being run in the virtual environment
- net_updater32.exe (PID: 1344)
Creates file in the systems drive root
- 360TS_Setup.exe (PID: 4336)
The process verifies whether the antivirus software is installed
- 360TS_Setup.exe (PID: 4336)
- csrss.exe (PID: 652)
- regsvr32.exe (PID: 8720)
- PowerSaver.exe (PID: 7716)
- WscReg.exe (PID: 3236)
- WscReg.exe (PID: 5480)
- EaInstHelper64.exe (PID: 7984)
- QHActiveDefense.exe (PID: 2448)
- QHActiveDefense.exe (PID: 8144)
- QHSafeTray.exe (PID: 5636)
- QHWatchdog.exe (PID: 8628)
- QHSafeTray.exe (PID: 8980)
- PopWndLog.exe (PID: 5284)
- regsvr32.exe (PID: 8756)
- csrss.exe (PID: 564)
- QHSafeTray.exe (PID: 8924)
- PopWndLog.exe (PID: 4288)
- KB931125-rootsupd.exe (PID: 9300)
- regsvr32.exe (PID: 9412)
- regsvr32.exe (PID: 9404)
- WscReg.exe (PID: 9540)
- WscReg.exe (PID: 9644)
Checks for external IP
- net_updater32.exe (PID: 1344)
Drops a system driver (possible attempt to evade defenses)
- 360TS_Setup.exe (PID: 4336)
- EaInstHelper64.exe (PID: 7984)
- QHActiveDefense.exe (PID: 2448)
- QHActiveDefense.exe (PID: 8144)
Creates files in the driver directory
- 360TS_Setup.exe (PID: 4336)
- EaInstHelper64.exe (PID: 7984)
- QHActiveDefense.exe (PID: 2448)
- QHActiveDefense.exe (PID: 8144)
Creates or modifies Windows services
- 360TS_Setup.exe (PID: 4336)
- EaInstHelper64.exe (PID: 7984)
- QHActiveDefense.exe (PID: 2448)
- QHActiveDefense.exe (PID: 8144)
- QHSafeTray.exe (PID: 5636)
Creates/Modifies COM task schedule object
- regsvr32.exe (PID: 8720)
Adds/modifies Windows certificates
- PowerSaver.exe (PID: 7716)
- WscReg.exe (PID: 5480)
- updroots.exe (PID: 9324)
- updroots.exe (PID: 9352)
- updroots.exe (PID: 9444)
- 360TS_Setup.exe (PID: 4336)
Zapya greyware has been detected
- QHActiveDefense.exe (PID: 8144)
Searches for installed software
- QHSafeTray.exe (PID: 5636)
Starts a Microsoft application from unusual location
- updroots.exe (PID: 9324)
- updroots.exe (PID: 9352)
- updroots.exe (PID: 9444)
- updroots.exe (PID: 9492)
INFO
The sample compiled with english language support
- f_001565.exe (PID: 7752)
- bdvpn_setup.exe (PID: 7980)
- net_updater32.exe (PID: 4632)
- antivirus360.exe (PID: 5180)
- mediaget.exe (PID: 7276)
- 360TS_Setup.exe (PID: 4336)
- QHActiveDefense.exe (PID: 2448)
- KB931125-rootsupd.exe (PID: 9300)
Checks supported languages
- f_001565.exe (PID: 7752)
- mediaget.exe (PID: 7276)
- mediaget_crashpad_handler.exe (PID: 7736)
- QtWebEngineProcess.exe (PID: 7912)
- bdvpn_setup.exe (PID: 7980)
- QtWebEngineProcess.exe (PID: 8016)
- QtWebEngineProcess.exe (PID: 3192)
- brightvpn_installer.exe (PID: 1520)
- infatica-service-app.exe (PID: 6636)
- QtWebEngineProcess.exe (PID: 6244)
- net_updater32.exe (PID: 4632)
- test_wpf.exe (PID: 496)
- net_updater32.exe (PID: 3444)
- antivirus360.exe (PID: 5180)
- inf_inst.exe (PID: 1908)
- inf_inst.tmp (PID: 5040)
- infatica-service-app.exe (PID: 5728)
- test_wpf.exe (PID: 7852)
- net_updater32.exe (PID: 1232)
- test_wpf.exe (PID: 7860)
- net_updater32.exe (PID: 7220)
- Bright VPN.exe (PID: 7780)
- test_wpf.exe (PID: 412)
- net_updater32.exe (PID: 5592)
- Bright VPN.exe (PID: 7436)
- Bright VPN.exe (PID: 6592)
- net_updater32.exe (PID: 2864)
- test_wpf.exe (PID: 7852)
- test_wpf.exe (PID: 8020)
- net_updater32.exe (PID: 1344)
- idle_report.exe (PID: 5828)
- brightdata.exe (PID: 356)
- 360TS_Setup.exe (PID: 7888)
- 360TS_Setup.exe (PID: 4336)
- identity_helper.exe (PID: 8848)
- idle_report.exe (PID: 8908)
- Bright VPN.exe (PID: 7344)
- idle_report.exe (PID: 7272)
- WscReg.exe (PID: 3236)
- PowerSaver.exe (PID: 7716)
- WscReg.exe (PID: 5480)
- EaInstHelper64.exe (PID: 7984)
- QHActiveDefense.exe (PID: 2448)
- QHActiveDefense.exe (PID: 8144)
- QHSafeTray.exe (PID: 5636)
- QHWatchdog.exe (PID: 8628)
- PopWndLog.exe (PID: 5284)
- QHSafeTray.exe (PID: 8980)
- PopWndLog.exe (PID: 4288)
- QHWatchdog.exe (PID: 7716)
- QHSafeTray.exe (PID: 8924)
- KB931125-rootsupd.exe (PID: 9300)
- updroots.exe (PID: 9324)
- updroots.exe (PID: 9352)
- updroots.exe (PID: 9444)
- updroots.exe (PID: 9492)
- WscReg.exe (PID: 9540)
- WscReg.exe (PID: 9644)
Creates a software uninstall entry
- f_001565.exe (PID: 7752)
- bdvpn_setup.exe (PID: 7980)
- 360TS_Setup.exe (PID: 4336)
Process checks computer location settings
- f_001565.exe (PID: 7752)
- QtWebEngineProcess.exe (PID: 8016)
- QtWebEngineProcess.exe (PID: 6244)
- QtWebEngineProcess.exe (PID: 3192)
- net_updater32.exe (PID: 4632)
- net_updater32.exe (PID: 3444)
- net_updater32.exe (PID: 1232)
- net_updater32.exe (PID: 7220)
- Bright VPN.exe (PID: 7780)
- net_updater32.exe (PID: 2864)
- net_updater32.exe (PID: 1344)
- antivirus360.exe (PID: 5180)
- 360TS_Setup.exe (PID: 4336)
- QHSafeTray.exe (PID: 5636)
Reads the computer name
- mediaget.exe (PID: 7276)
- QtWebEngineProcess.exe (PID: 7912)
- f_001565.exe (PID: 7752)
- bdvpn_setup.exe (PID: 7980)
- QtWebEngineProcess.exe (PID: 3192)
- QtWebEngineProcess.exe (PID: 8016)
- brightvpn_installer.exe (PID: 1520)
- QtWebEngineProcess.exe (PID: 6244)
- net_updater32.exe (PID: 4632)
- test_wpf.exe (PID: 496)
- net_updater32.exe (PID: 3444)
- antivirus360.exe (PID: 5180)
- inf_inst.tmp (PID: 5040)
- net_updater32.exe (PID: 5592)
- test_wpf.exe (PID: 7852)
- net_updater32.exe (PID: 1232)
- test_wpf.exe (PID: 7860)
- net_updater32.exe (PID: 7220)
- Bright VPN.exe (PID: 7780)
- test_wpf.exe (PID: 412)
- Bright VPN.exe (PID: 7436)
- Bright VPN.exe (PID: 6592)
- net_updater32.exe (PID: 2864)
- test_wpf.exe (PID: 7852)
- net_updater32.exe (PID: 1344)
- test_wpf.exe (PID: 8020)
- idle_report.exe (PID: 5828)
- brightdata.exe (PID: 356)
- 360TS_Setup.exe (PID: 7888)
- 360TS_Setup.exe (PID: 4336)
- identity_helper.exe (PID: 8848)
- idle_report.exe (PID: 8908)
- Bright VPN.exe (PID: 7344)
- idle_report.exe (PID: 7272)
- WscReg.exe (PID: 3236)
- WscReg.exe (PID: 5480)
- EaInstHelper64.exe (PID: 7984)
- QHActiveDefense.exe (PID: 2448)
- QHActiveDefense.exe (PID: 8144)
- QHSafeTray.exe (PID: 5636)
- PopWndLog.exe (PID: 5284)
- QHSafeTray.exe (PID: 8980)
- QHSafeTray.exe (PID: 8924)
- PopWndLog.exe (PID: 4288)
- WscReg.exe (PID: 9540)
- WscReg.exe (PID: 9644)
Reads the machine GUID from the registry
- mediaget.exe (PID: 7276)
- bdvpn_setup.exe (PID: 7980)
- QtWebEngineProcess.exe (PID: 7912)
- brightvpn_installer.exe (PID: 1520)
- net_updater32.exe (PID: 4632)
- test_wpf.exe (PID: 496)
- net_updater32.exe (PID: 3444)
- antivirus360.exe (PID: 5180)
- test_wpf.exe (PID: 7852)
- net_updater32.exe (PID: 5592)
- net_updater32.exe (PID: 1232)
- test_wpf.exe (PID: 7860)
- net_updater32.exe (PID: 7220)
- Bright VPN.exe (PID: 7780)
- test_wpf.exe (PID: 412)
- net_updater32.exe (PID: 2864)
- test_wpf.exe (PID: 7852)
- net_updater32.exe (PID: 1344)
- test_wpf.exe (PID: 8020)
- idle_report.exe (PID: 5828)
- brightdata.exe (PID: 356)
- 360TS_Setup.exe (PID: 4336)
- idle_report.exe (PID: 8908)
- Bright VPN.exe (PID: 7344)
- idle_report.exe (PID: 7272)
- QHActiveDefense.exe (PID: 8144)
- QHSafeTray.exe (PID: 5636)
Creates files or folders in the user directory
- f_001565.exe (PID: 7752)
- mediaget.exe (PID: 7276)
- QtWebEngineProcess.exe (PID: 7912)
- bdvpn_setup.exe (PID: 7980)
- net_updater32.exe (PID: 3444)
- antivirus360.exe (PID: 5180)
- net_updater32.exe (PID: 4632)
- inf_inst.tmp (PID: 5040)
- brightvpn_installer.exe (PID: 1520)
- Bright VPN.exe (PID: 7780)
- Bright VPN.exe (PID: 6592)
- 360TS_Setup.exe (PID: 4336)
- Bright VPN.exe (PID: 7344)
- QHSafeTray.exe (PID: 5636)
Launching a file from a Registry key
- mediaget.exe (PID: 7276)
- inf_inst.tmp (PID: 5040)
- bdvpn_setup.exe (PID: 7980)
- 360TS_Setup.exe (PID: 4336)
- QHActiveDefense.exe (PID: 8144)
Checks proxy server information
- mediaget.exe (PID: 7276)
- f_001565.exe (PID: 7752)
- QtWebEngineProcess.exe (PID: 7912)
- brightvpn_installer.exe (PID: 1520)
- bdvpn_setup.exe (PID: 7980)
- net_updater32.exe (PID: 4632)
- net_updater32.exe (PID: 3444)
- antivirus360.exe (PID: 5180)
- net_updater32.exe (PID: 7220)
- Bright VPN.exe (PID: 7780)
- slui.exe (PID: 2416)
- 360TS_Setup.exe (PID: 4336)
- QHSafeTray.exe (PID: 5636)
Create files in a temporary directory
- f_001565.exe (PID: 7752)
- bdvpn_setup.exe (PID: 7980)
- antivirus360.exe (PID: 5180)
- inf_inst.exe (PID: 1908)
- inf_inst.tmp (PID: 5040)
- Bright VPN.exe (PID: 7780)
- mediaget.exe (PID: 7276)
- 360TS_Setup.exe (PID: 7888)
- 360TS_Setup.exe (PID: 4336)
- KB931125-rootsupd.exe (PID: 9300)
Disables trace logs
- brightvpn_installer.exe (PID: 1520)
- net_updater32.exe (PID: 3444)
- antivirus360.exe (PID: 5180)
- net_updater32.exe (PID: 7220)
- rasdial.exe (PID: 3444)
- Bright VPN.exe (PID: 7780)
- net_updater32.exe (PID: 1344)
- 360TS_Setup.exe (PID: 4336)
- QHActiveDefense.exe (PID: 8144)
- QHSafeTray.exe (PID: 5636)
- QHSafeTray.exe (PID: 8980)
- QHSafeTray.exe (PID: 8924)
Creates files in the program directory
- brightvpn_installer.exe (PID: 1520)
- bdvpn_setup.exe (PID: 7980)
- net_updater32.exe (PID: 4632)
- net_updater32.exe (PID: 3444)
- net_updater32.exe (PID: 5592)
- powershell.exe (PID: 7360)
- powershell.exe (PID: 7852)
- net_updater32.exe (PID: 1232)
- net_updater32.exe (PID: 7220)
- Bright VPN.exe (PID: 7780)
- net_updater32.exe (PID: 2864)
- net_updater32.exe (PID: 1344)
- brightdata.exe (PID: 356)
- 360TS_Setup.exe (PID: 7888)
- 360TS_Setup.exe (PID: 4336)
- QHActiveDefense.exe (PID: 8144)
- PopWndLog.exe (PID: 5284)
- QHSafeTray.exe (PID: 5636)
- PopWndLog.exe (PID: 4288)
- WscReg.exe (PID: 9644)
Manual execution by a user
- Bright VPN.exe (PID: 7780)
- msedge.exe (PID: 2140)
- notepad.exe (PID: 8668)
- msedge.exe (PID: 9100)
- msedge.exe (PID: 8632)
- msedge.exe (PID: 8844)
Reads security settings of Internet Explorer
- WMIC.exe (PID: 6208)
- notepad.exe (PID: 8668)
Reads CPU info
- Bright VPN.exe (PID: 7780)
- net_updater32.exe (PID: 1344)
- 360TS_Setup.exe (PID: 4336)
- QHActiveDefense.exe (PID: 8144)
Reads the time zone
- net_updater32.exe (PID: 1344)
The sample compiled with chinese language support
- 360TS_Setup.exe (PID: 7888)
- 360TS_Setup.exe (PID: 4336)
- EaInstHelper64.exe (PID: 7984)
- QHActiveDefense.exe (PID: 8144)
The sample compiled with turkish language support
- 360TS_Setup.exe (PID: 4336)
Application launched itself
- msedge.exe (PID: 2140)
Reads Environment values
- identity_helper.exe (PID: 8848)
- QHSafeTray.exe (PID: 5636)
- QHActiveDefense.exe (PID: 8144)
The sample compiled with russian language support
- 360TS_Setup.exe (PID: 4336)
Detects GO elliptic curve encryption (YARA)
- infatica-service-app.exe (PID: 5728)
Application based on Golang
- infatica-service-app.exe (PID: 5728)
Node.js compiler has been detected
- Bright VPN.exe (PID: 7780)
- Bright VPN.exe (PID: 7436)
- Bright VPN.exe (PID: 6592)
Process checks whether UAC notifications are on
- 360TS_Setup.exe (PID: 4336)
- QHActiveDefense.exe (PID: 8144)
- QHSafeTray.exe (PID: 5636)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (76.4) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (12.4) |
| .exe | | | Generic Win/DOS Executable (5.5) |
| .exe | | | DOS Executable Generic (5.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2025:12:15 12:38:59+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 14.29 |
| CodeSize: | 2479616 |
| InitializedDataSize: | 2401280 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x2298d8 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.1 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| Comments: | - |
| CompanyName: | - |
| FileDescription: | - |
| FileVersion: | 1 |
| InternalName: | - |
| LegalCopyright: | - |
| OriginalFileName: | - |
| ProductName: | - |
| ProductVersion: | 1 |
Total processes
280
Monitored processes
127
Malicious processes
28
Suspicious processes
6
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 356 | C:\ProgramData\BrightData\6cca5f7f15056f66a3211bbbd92076486a2361bb\brightdata.exe --appid win_brightvpn.com | C:\ProgramData\BrightData\6cca5f7f15056f66a3211bbbd92076486a2361bb\brightdata.exe | — | net_updater32.exe | |||||||||||
User: admin Company: BrightData Ltd. (certified) Integrity Level: MEDIUM Description: BrightData service allows free use of certain features in an app you installed Version: 1.572.298 Modules
| |||||||||||||||
| 412 | C:\ProgramData\BrightData\6cca5f7f15056f66a3211bbbd92076486a2361bb\test_wpf.exe | C:\ProgramData\BrightData\6cca5f7f15056f66a3211bbbd92076486a2361bb\test_wpf.exe | — | Bright VPN.exe | |||||||||||
User: admin Company: BrightData Ltd. (certified) Integrity Level: MEDIUM Description: test_wpf Exit code: 0 Version: 1.572.298 Modules
| |||||||||||||||
| 496 | C:\ProgramData\BrightData\6cca5f7f15056f66a3211bbbd92076486a2361bb\test_wpf.exe | C:\ProgramData\BrightData\6cca5f7f15056f66a3211bbbd92076486a2361bb\test_wpf.exe | — | net_updater32.exe | |||||||||||
User: admin Company: BrightData Ltd. (certified) Integrity Level: HIGH Description: test_wpf Exit code: 0 Version: 1.572.298 Modules
| |||||||||||||||
| 564 | %SystemRoot%\system32\csrss.exe ObjectDirectory=\Windows SharedSection=1024,20480,768 Windows=On SubSystemType=Windows ServerDll=basesrv,1 ServerDll=winsrv:UserServerDllInitialization,3 ServerDll=sxssrv,4 ProfileControl=Off MaxRequestThreads=16 | C:\Windows\System32\csrss.exe | — | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Client Server Runtime Process Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 652 | %SystemRoot%\system32\csrss.exe ObjectDirectory=\Windows SharedSection=1024,20480,768 Windows=On SubSystemType=Windows ServerDll=basesrv,1 ServerDll=winsrv:UserServerDllInitialization,3 ServerDll=sxssrv,4 ProfileControl=Off MaxRequestThreads=16 | C:\Windows\System32\csrss.exe | — | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Client Server Runtime Process Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1092 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1232 | "C:\Program Files (x86)\Bright VPN\net_updater32.exe" --install-ui win_brightvpn.com | C:\Program Files (x86)\Bright VPN\net_updater32.exe | bdvpn_setup.exe | ||||||||||||
User: admin Company: BrightData Ltd. (certified) Integrity Level: HIGH Description: BrightData service allows free use of certain features in an app you installed Exit code: 1 Version: 1.572.298 Modules
| |||||||||||||||
| 1344 | "C:/Program Files (x86)/Bright VPN/net_updater32.exe" --updater win_brightvpn.com | C:\Program Files (x86)\Bright VPN\net_updater32.exe | services.exe | ||||||||||||
User: SYSTEM Company: BrightData Ltd. (certified) Integrity Level: SYSTEM Description: BrightData service allows free use of certain features in an app you installed Version: 1.572.298 Modules
| |||||||||||||||
| 1368 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --disable-quic --message-loop-type-ui --string-annotations --always-read-main-dll --field-trial-handle=6436,i,6076539726963160036,14593318980868985323,262144 --variations-seed-version --mojo-platform-channel-handle=6728 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1492 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
100 020
Read events
96 670
Write events
1 943
Delete events
1 407
Modification events
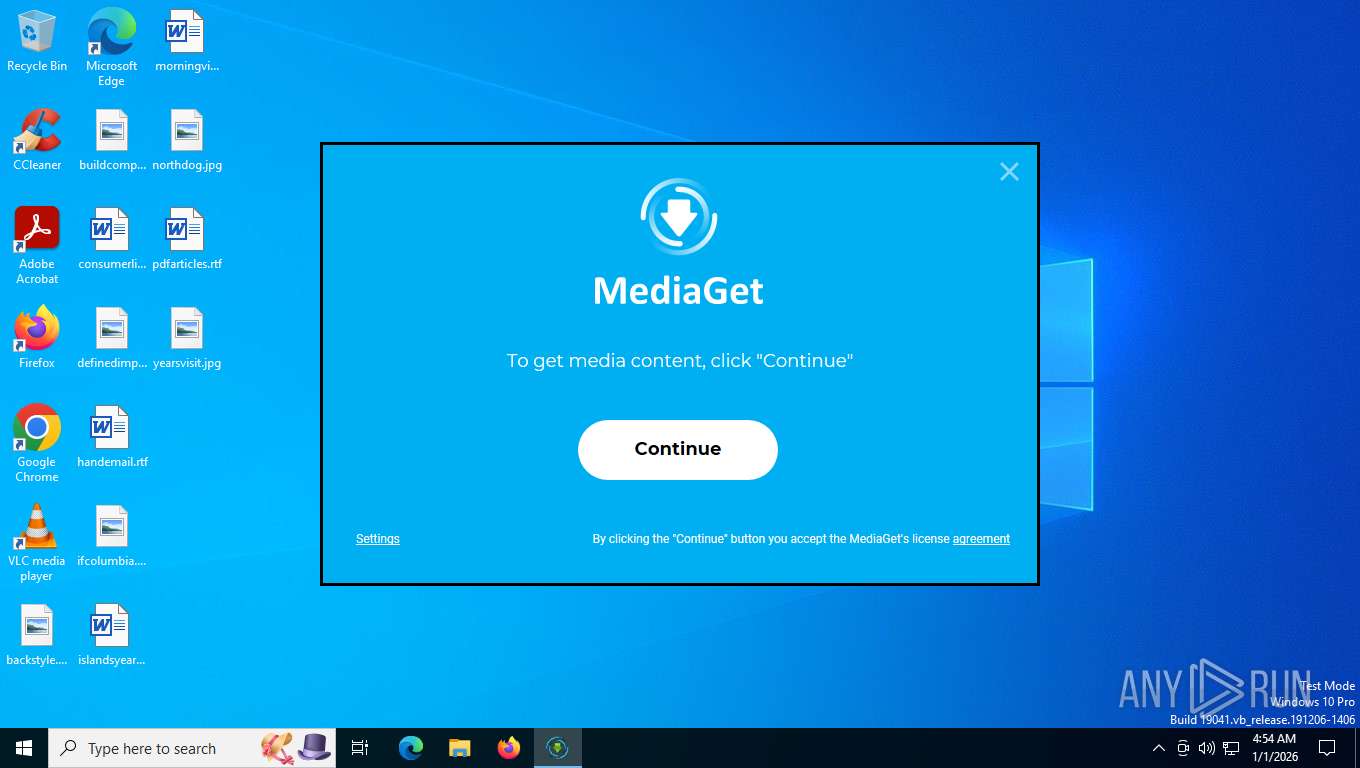
| (PID) Process: | (7752) f_001565.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (7752) f_001565.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | DisableFirstRunCustomize |
Value: 1 | |||
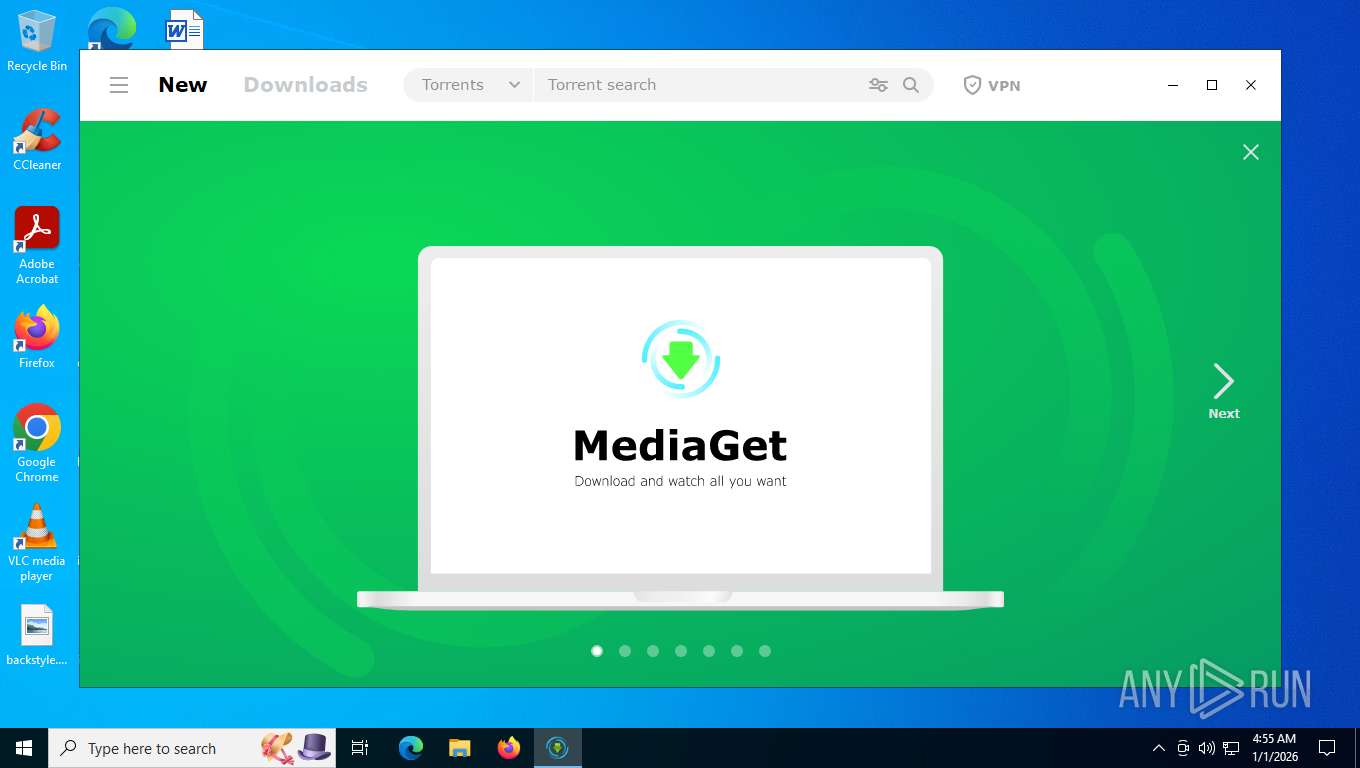
| (PID) Process: | (7752) f_001565.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Media Get LLC\MediaGet2-systemScope\mediaget_info |
| Operation: | write | Name: | hasDownloadedUpdate |
Value: false | |||
| (PID) Process: | (7752) f_001565.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (7752) f_001565.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (7752) f_001565.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\Main\WindowsSearch |
| Operation: | write | Name: | Version |
Value: WS not running | |||
| (PID) Process: | (7752) f_001565.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\MediaGet |
| Operation: | write | Name: | InstallLocation |
Value: C:\Users\admin\MediaGet2\ | |||
| (PID) Process: | (7752) f_001565.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\MediaGet |
| Operation: | write | Name: | DisplayName |
Value: MediaGet | |||
| (PID) Process: | (7752) f_001565.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\MediaGet |
| Operation: | write | Name: | DisplayIcon |
Value: C:\Users\admin\MediaGet2\mediaget.exe | |||
| (PID) Process: | (7752) f_001565.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\MediaGet |
| Operation: | write | Name: | UninstallString |
Value: C:\Users\admin\MediaGet2\mediaget-uninstaller.exe | |||
Executable files
1 844
Suspicious files
1 321
Text files
1 023
Unknown types
7
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7752 | f_001565.exe | C:\Users\admin\AppData\Local\Temp\mediaget-installer-tmp\curl-ca-bundle.crt | text | |
MD5:BE2B0736EA029FFF398559FA7DF4E646 | SHA256:C05A79296D61E3B2A2EBAF5AF476839B976D69A5ACB6F581A667E60E681049A2 | |||
| 7752 | f_001565.exe | C:\Users\admin\AppData\Local\Temp\mediaget-installer-tmp\archive.7z | compressed | |
MD5:D25F096B399598C283BD317D3D7ACF6F | SHA256:C72BB363A7E24B48375F391D0534B64D812C59F3F2FC11564195A5487EAA057E | |||
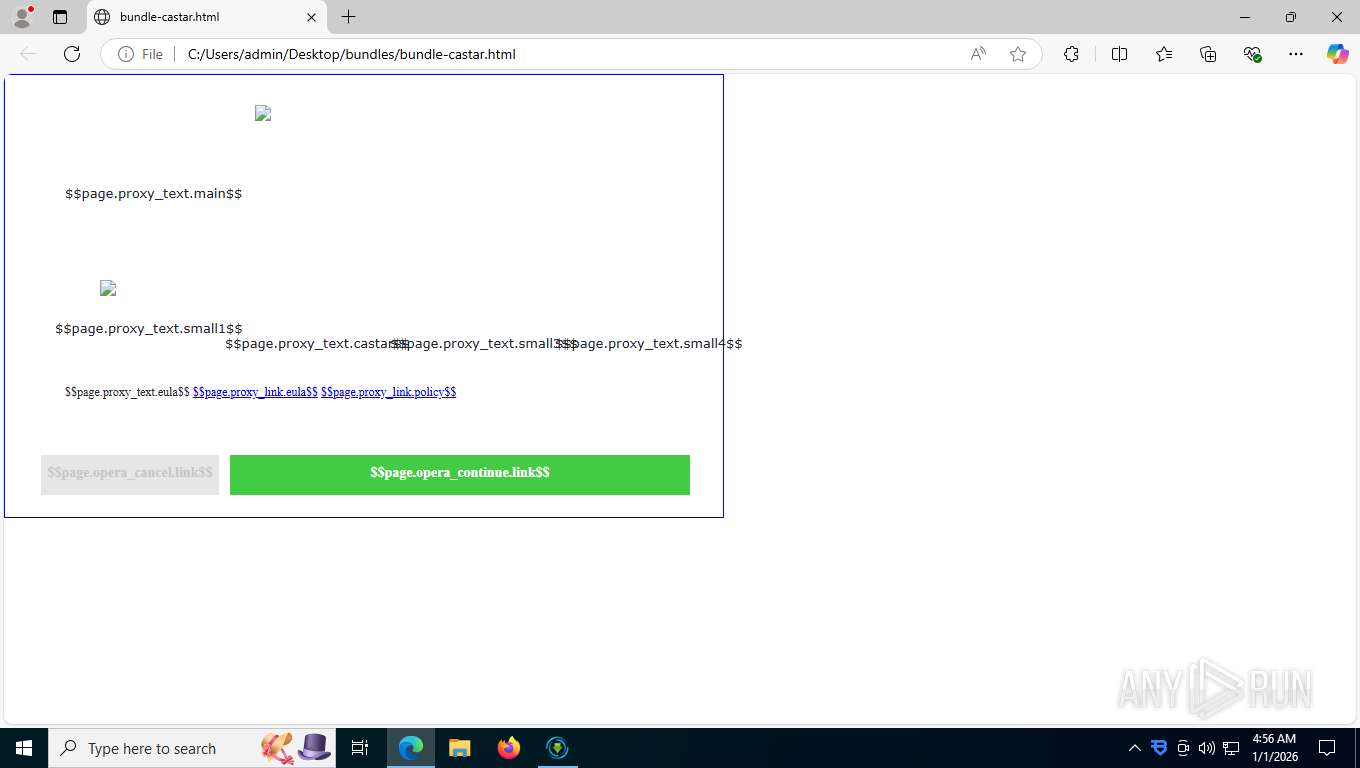
| 7752 | f_001565.exe | C:\Users\admin\AppData\Local\Temp\mediaget-installer-tmp\bundles\bundle-av360.html | html | |
MD5:A57927C1723EA25FD20FE82369F0A000 | SHA256:D07C58DC6C503AAEA6F0169531FEBEE0FAC6FCEBA60E67E144D7C4F16732A878 | |||
| 7752 | f_001565.exe | C:\Users\admin\AppData\Local\Temp\mediaget-installer-tmp\bundles\bundle-bdvpn.html | html | |
MD5:238C957C20B8EBBA156801E120A5C581 | SHA256:EA46E2B35A23321A5CF8B2479806C6812D643A6C0EBD6D81C528C0018BC3BC97 | |||
| 7752 | f_001565.exe | C:\Users\admin\AppData\Local\Temp\mediaget-installer-tmp\bundles\bundle-luminati-wait.html | text | |
MD5:CA89D8AF17EB0E569B5B879878826613 | SHA256:EB7C7D46283A38684362ACA9FEA151035545EC4279EAAE626F8EE0C8DDD17F4E | |||
| 7752 | f_001565.exe | C:\Users\admin\AppData\Local\Temp\mediaget-installer-tmp\bundles\bundle-ipgate.html | html | |
MD5:6B10D1E2BAF9336C582B5F0A865C33D8 | SHA256:A992C8023C8EB36DC7238DB6DD08A346B75B1783B537B4235B0EFA898708225C | |||
| 7752 | f_001565.exe | C:\Users\admin\AppData\Local\Temp\mediaget-installer-tmp\page-wait.png | image | |
MD5:A8210694C45753A7A027296EF745E316 | SHA256:14DE6662062ADC45202E2021AA4D60E98637DC892A22ACB2C7CC16DA3344C14D | |||
| 7752 | f_001565.exe | C:\Users\admin\AppData\Local\Temp\mediaget-installer-tmp\bundles\bundle-castar.html | html | |
MD5:8D4B46D9DA248FD319A1360CD8378225 | SHA256:20327ACB96F1D95F1D2475B22DA874E051112547DD13A79AB8E10497A0DEDA93 | |||
| 7752 | f_001565.exe | C:\Users\admin\AppData\Local\Temp\mediaget-installer-tmp\bundles\bundle-coc.html | html | |
MD5:9C040C5F4DB773934730C0471363B4A4 | SHA256:794AA2B7DCC14CF1A7017A9568AB47A81DA2F2D81CE6DE5BB777EDAE21AEF189 | |||
| 7752 | f_001565.exe | C:\Users\admin\AppData\Local\Temp\mediaget-installer-tmp\bundles\bundle-anyip.html | html | |
MD5:C64F49DE1105689FA739B0F91DCF7698 | SHA256:78757B4119DCD12113C6EC136CF3A1C5E850FAFB063A0C26331405B081344C44 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
260
TCP/UDP connections
11 798
DNS requests
134
Threats
76
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6768 | MoUsoCoreWorker.exe | GET | 304 | 40.127.240.158:443 | https://settings-win.data.microsoft.com/settings/v3.0/OneSettings/Client?OSVersionFull=10.0.19045.4046.amd64fre.vb_release.191206-1406&LocalDeviceID=s%3ABAD99146-31D3-4EC6-A1A4-BE76F32BA5D4&FlightRing=Retail&AttrDataVer=186&OSUILocale=en-US&OSSkuId=48&App=WOSC&AppVer=&IsFlightingEnabled=0&TelemetryLevel=1&DeviceFamily=Windows.Desktop | US | — | — | whitelisted |
6768 | MoUsoCoreWorker.exe | GET | 304 | 40.127.240.158:443 | https://settings-win.data.microsoft.com/settings/v3.0/wsd/muse?ProcessorClockSpeed=3094&FlightIds=&UpdateOfferedDays=4294967295&BranchReadinessLevel=CB&OEMManufacturerName=DELL&IsCloudDomainJoined=0&ProcessorIdentifier=AMD64%20Family%2023%20Model%201%20Stepping%202&sku=48&ActivationChannel=Retail&AttrDataVer=186&IsMDMEnrolled=0&ProcessorCores=6&ProcessorModel=AMD%20Ryzen%205%203500%206-Core%20Processor&TotalPhysicalRAM=6144&PrimaryDiskType=4294967295&FlightingBranchName=&ChassisTypeId=1&OEMModelNumber=DELL&SystemVolumeTotalCapacity=260281&sampleId=95271487&deviceClass=Windows.Desktop&App=muse&DisableDualScan=0&AppVer=10.0&OEMSubModel=J5CR&locale=en-US&IsAlwaysOnAlwaysConnectedCapable=0&ms=0&DefaultUserRegion=244&UpdateServiceUrl=http%3A%2F%2Fneverupdatewindows10.com&osVer=10.0.19045.4046.amd64fre.vb_release.191206-1406&os=windows&deviceId=s%3ABAD99146-31D3-4EC6-A1A4-BE76F32BA5D4&DeferQualityUpdatePeriodInDays=0&ring=Retail&DeferFeatureUpdatePeriodInDays=30 | US | — | — | whitelisted |
7432 | SIHClient.exe | GET | 200 | 20.3.187.198:443 | https://fe3cr.delivery.mp.microsoft.com/clientwebservice/ping | US | — | — | whitelisted |
7432 | SIHClient.exe | GET | 304 | 74.178.76.128:443 | https://slscr.update.microsoft.com/SLS/%7BE7A50285-D08D-499D-9FF8-180FDC2332BC%7D/x64/10.0.19045.4046/0?CH=686&L=en-US&P=&PT=0x30&WUA=10.0.19041.3996&MK=DELL&MD=DELL | US | — | — | whitelisted |
7432 | SIHClient.exe | GET | 200 | 74.178.76.128:443 | https://slscr.update.microsoft.com/sls/ping | US | — | — | whitelisted |
1792 | svchost.exe | GET | 200 | 2.16.164.72:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | NL | binary | 825 b | whitelisted |
1792 | svchost.exe | GET | 200 | 51.104.136.2:443 | https://settings-win.data.microsoft.com/settings/v3.0/WSD/WaaSAssessment?os=Windows&osVer=10.0.19041.1.amd64fre.vb_release.191206-&ring=Retail&sku=48&deviceClass=Windows.Desktop&locale=en-US&deviceId=BAD99146-31D3-4EC6-A1A4-BE76F32BA5D4&FlightRing=Retail&TelemetryLevel=1&HidOverGattReg=C%3A%5CWINDOWS%5CSystem32%5CDriverStore%5CFileRepository%5Chidbthle.inf_amd64_9610b4821fdf82a5%5CMicrosoft.Bluetooth.Profiles.HidOverGatt.dll&AppVer=10.0&ProcessorIdentifier=AMD64%20Family%2023%20Model%201%20Stepping%202&OEMModel=DELL&UpdateOfferedDays=562&ProcessorManufacturer=AuthenticAMD&InstallDate=1661339444&OEMModelBaseBoard=&BranchReadinessLevel=CB&OEMSubModel=J5CR&IsCloudDomainJoined=0&DeferFeatureUpdatePeriodInDays=30&IsDeviceRetailDemo=0&FlightingBranchName=&OSUILocale=en-US&DeviceFamily=Windows.Desktop&WuClientVer=10.0.19041.3996&UninstallActive=1&IsFlightingEnabled=0&OSSkuId=48&ProcessorClockSpeed=3094&TotalPhysicalRAM=6144&SecureBootCapable=0&App=WaaSAssessment&ProcessorCores=6&CurrentBranch=vb_release&InstallLanguage=en-US&DeferQualityUpdatePeriodInDays=0&ServicingBranch=CB&OEMName_Uncleaned=DELL&TPMVersion=0&PrimaryDiskTotalCapacity=262144&InstallationType=Client&AttrDataVer=186&ProcessorModel=AMD%20Ryzen%205%203500%206-Core%20Processor&IsEdgeWithChromiumInstalled=1&OSVersion=10.0.19045.4046&IsMDMEnrolled=0&ActivationChannel=Retail&HonorWUfBDeferrals=1&FirmwareVersion=A.40&TrendInstalledKey=1&OSArchitecture=AMD64&DefaultUserRegion=244&UpdateManagementGroup=2 | US | text | 5.48 Kb | whitelisted |
1792 | svchost.exe | GET | 200 | 51.104.136.2:443 | https://settings-win.data.microsoft.com/settings/v3.0/WSD/UpdateHealthTools?os=Windows&osVer=10.0.19041.1.amd64fre.vb_release.191206-&sku=48&deviceClass=Windows.Desktop&locale=en-US&deviceId=s:BAD99146-31D3-4EC6-A1A4-BE76F32BA5D4&sampleId=s:95271487&appVer=10.0.19041.3626&FlightRing=Retail&TelemetryLevel=1&HidOverGattReg=C%3A%5CWINDOWS%5CSystem32%5CDriverStore%5CFileRepository%5Chidbthle.inf_amd64_9610b4821fdf82a5%5CMicrosoft.Bluetooth.Profiles.HidOverGatt.dll&AppVer=&ProcessorIdentifier=AMD64%20Family%2023%20Model%201%20Stepping%202&OEMModel=DELL&UpdateOfferedDays=562&ProcessorManufacturer=AuthenticAMD&InstallDate=1661339444&OEMModelBaseBoard=&BranchReadinessLevel=CB&OEMSubModel=J5CR&IsCloudDomainJoined=0&DeferFeatureUpdatePeriodInDays=30&IsDeviceRetailDemo=0&FlightingBranchName=&OSUILocale=en-US&DeviceFamily=Windows.Desktop&WuClientVer=10.0.19041.3996&UninstallActive=1&IsFlightingEnabled=0&OSSkuId=48&ProcessorClockSpeed=3094&TotalPhysicalRAM=6144&SecureBootCapable=0&App=SedimentPack&ProcessorCores=6&CurrentBranch=vb_release&InstallLanguage=en-US&DeferQualityUpdatePeriodInDays=0&OEMName_Uncleaned=DELL&TPMVersion=0&PrimaryDiskTotalCapacity=262144&InstallationType=Client&AttrDataVer=186&ProcessorModel=AMD%20Ryzen%205%203500%206-Core%20Processor&IsEdgeWithChromiumInstalled=1&OSVersion=10.0.19045.4046&IsMDMEnrolled=0&ActivationChannel=Retail&FirmwareVersion=A.40&TrendInstalledKey=1&OSArchitecture=AMD64&DefaultUserRegion=244&UpdateManagementGroup=2 | US | text | 1.43 Kb | whitelisted |
1792 | svchost.exe | GET | 200 | 23.59.18.102:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | US | binary | 814 b | whitelisted |
4256 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | binary | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1792 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
6768 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5876 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:138 | — | Not routed | — | whitelisted |
7752 | f_001565.exe | 51.158.227.48:443 | mediaget.com | Online SAS | FR | unknown |
1792 | svchost.exe | 2.16.164.72:80 | crl.microsoft.com | AKAMAI-ASN1 | NL | whitelisted |
1792 | svchost.exe | 23.59.18.102:80 | www.microsoft.com | AKAMAI-AS | US | whitelisted |
3412 | svchost.exe | 172.211.123.250:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6768 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
mediaget.com |
| unknown |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |
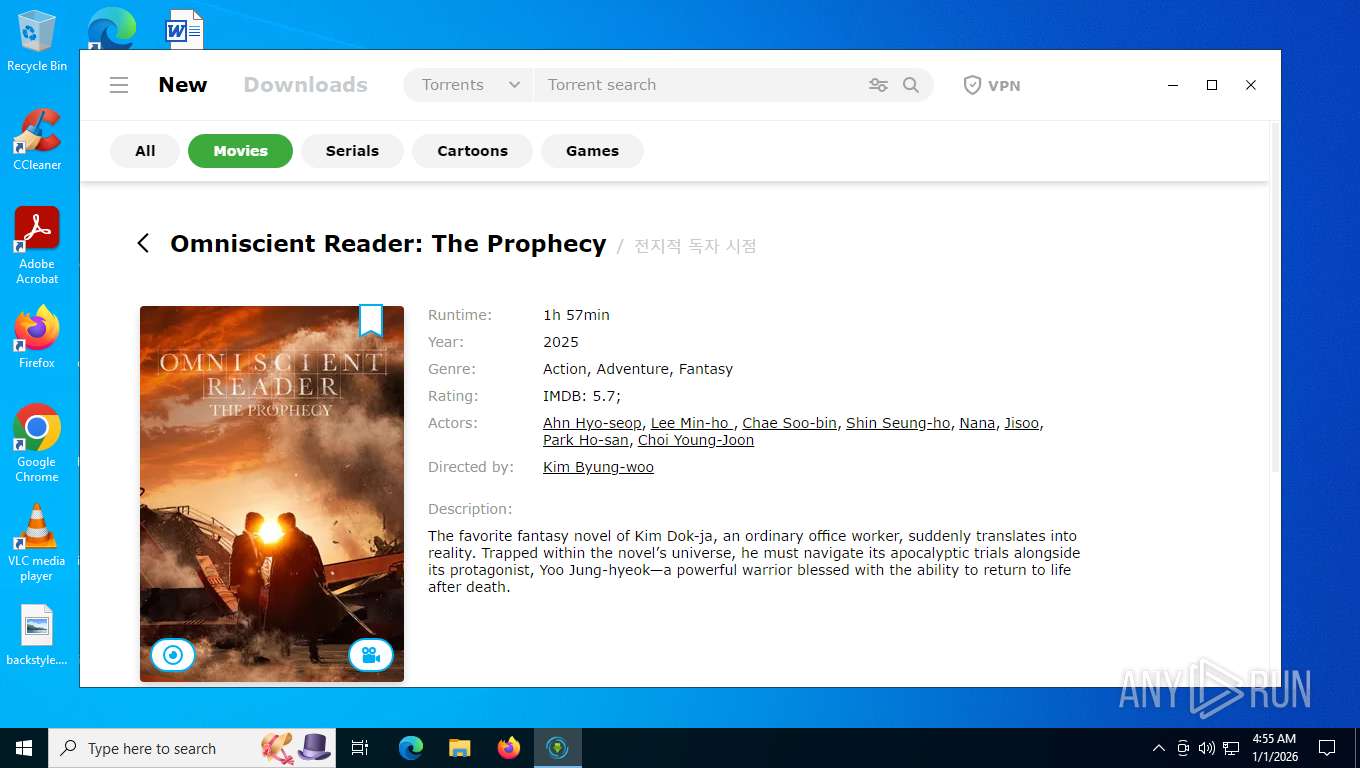
7276 | mediaget.exe | Misc activity | INFO [ANY.RUN] P2P BitTorrent Protocol |
7276 | mediaget.exe | Potential Corporate Privacy Violation | ET P2P Vuze BT UDP Connection (5) |
2292 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
— | — | Potentially Bad Traffic | SUSPICIOUS [ANY.RUN] NSIS INetC plugin User-Agent observed in HTTP request |
7752 | f_001565.exe | Potentially Bad Traffic | ET INFO PE EXE or DLL Windows file download HTTP |
7752 | f_001565.exe | Misc activity | ET INFO Packed Executable Download |
— | — | Misc activity | ADWARE [ANY.RUN] Bright Data SDK User-Agent in HTTP request |
— | — | Misc activity | ADWARE [ANY.RUN] Bright Data SDK User-Agent in HTTP request |
— | — | Misc activity | ADWARE [ANY.RUN] Bright Data SDK User-Agent in HTTP request |
Process | Message |
|---|---|
mediaget.exe | AUTOSELECT OGL
|
mediaget.exe | > __thiscall Application::Application(int &,char *[])
|
mediaget.exe | os version: "10.0.19045v" __ os name: "Windows 10 Version 2009"
|
mediaget.exe | > int __thiscall Application::exec(void)
|
mediaget.exe | > __thiscall MediagetServerSettings::MediagetServerSettings(void)
|
mediaget.exe | INSTALL ID: "" _ OLD ID: ""
|
mediaget.exe | reseller - "" installId ""
|
mediaget.exe | > void __thiscall MediagetServerSettings::flushSettings(void)
|
mediaget.exe | main libvlc debug: VLC media player - 3.0.17.4 Vetinari
|
mediaget.exe | main libvlc debug: Copyright © 1996-2022 the VideoLAN team
|