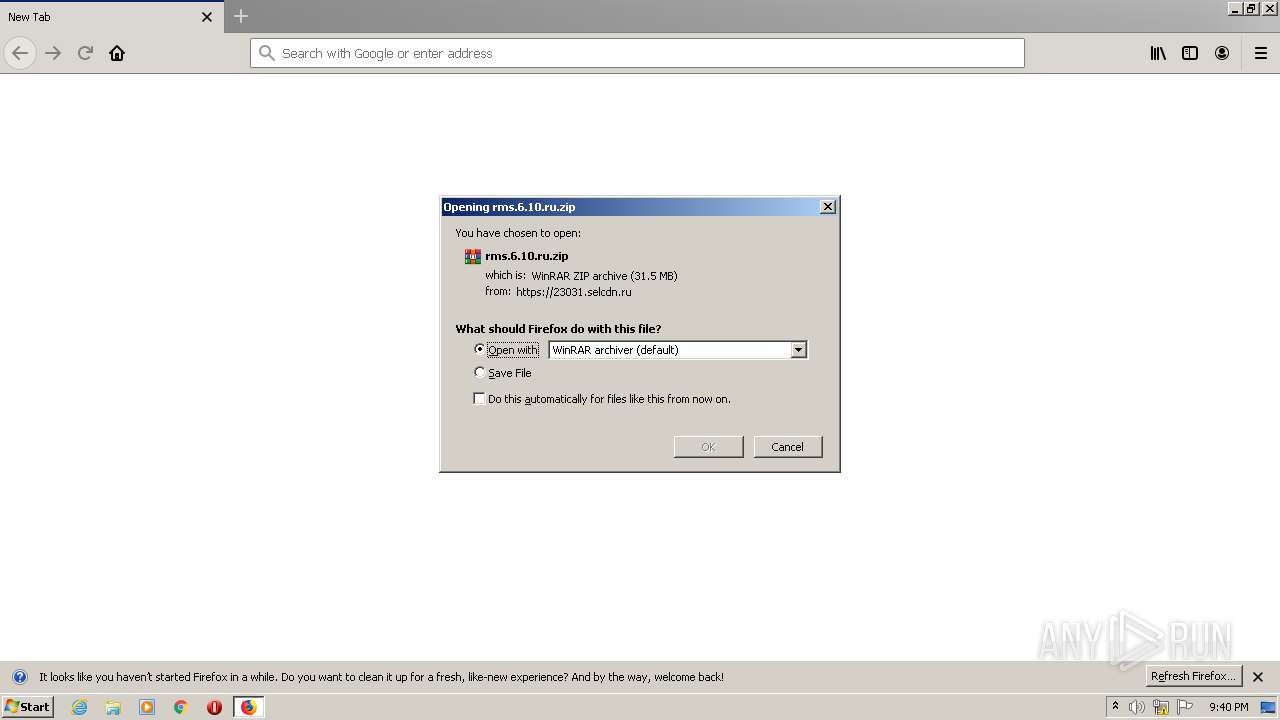
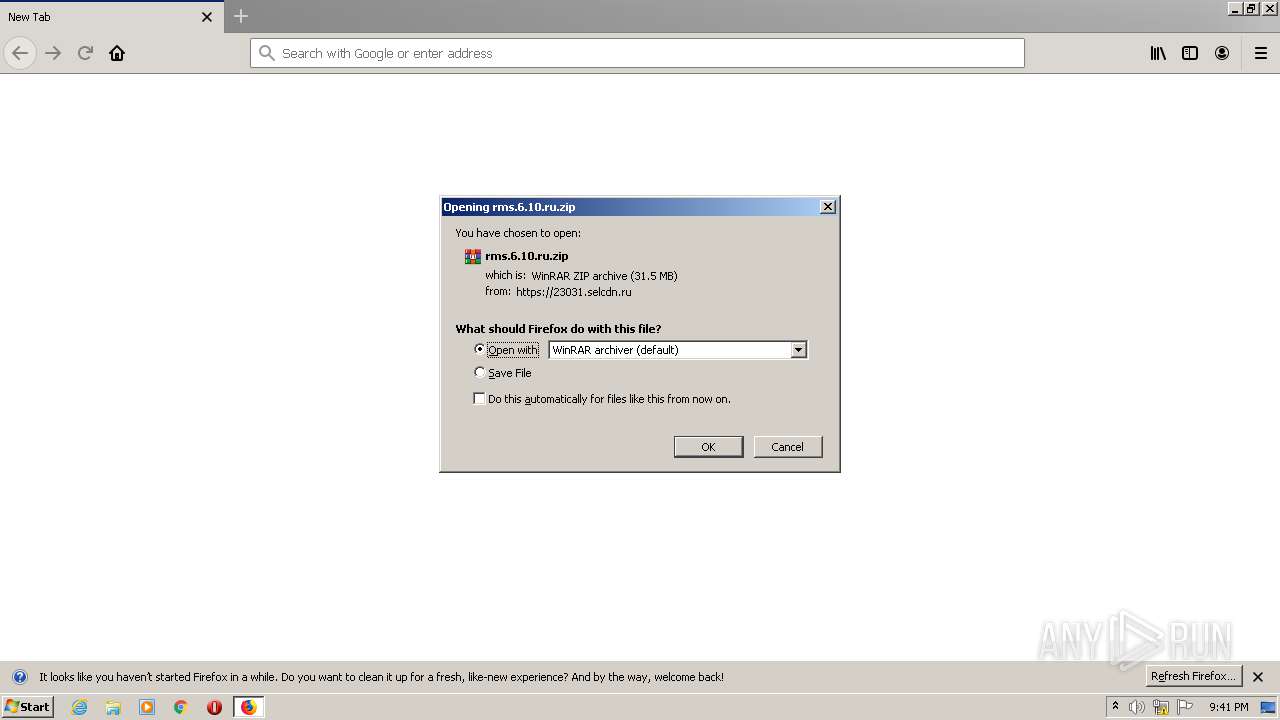
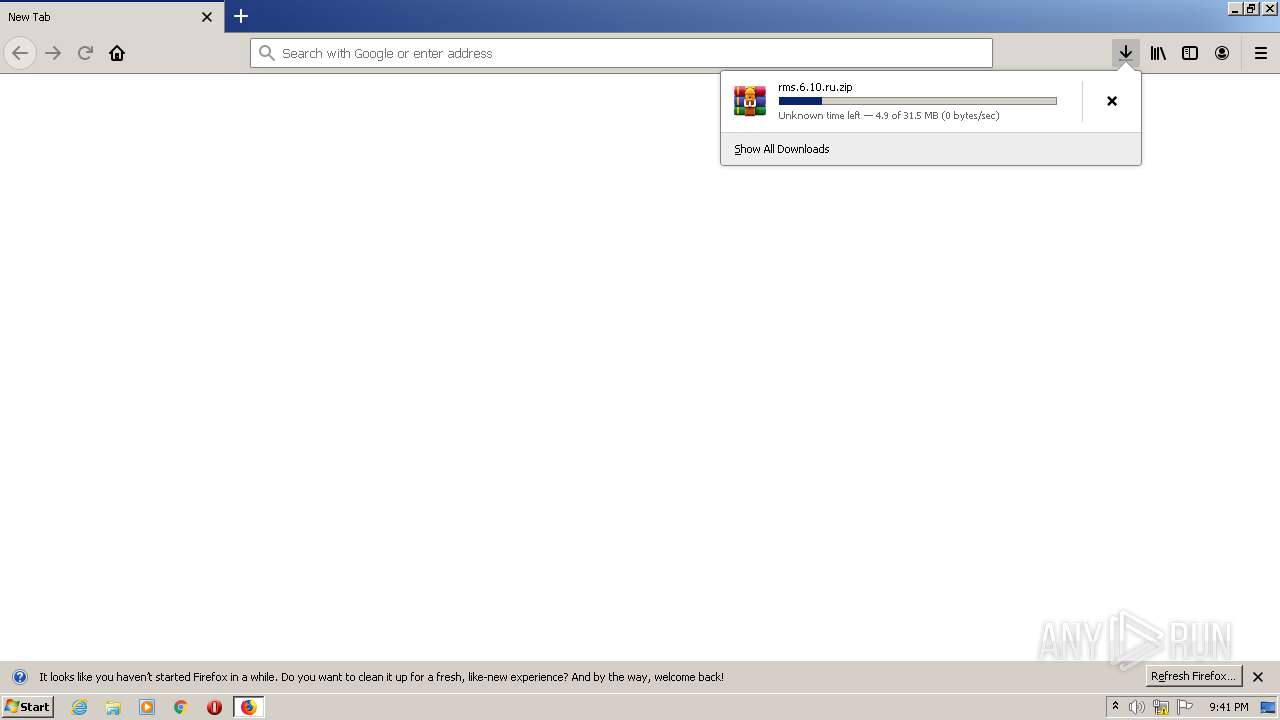
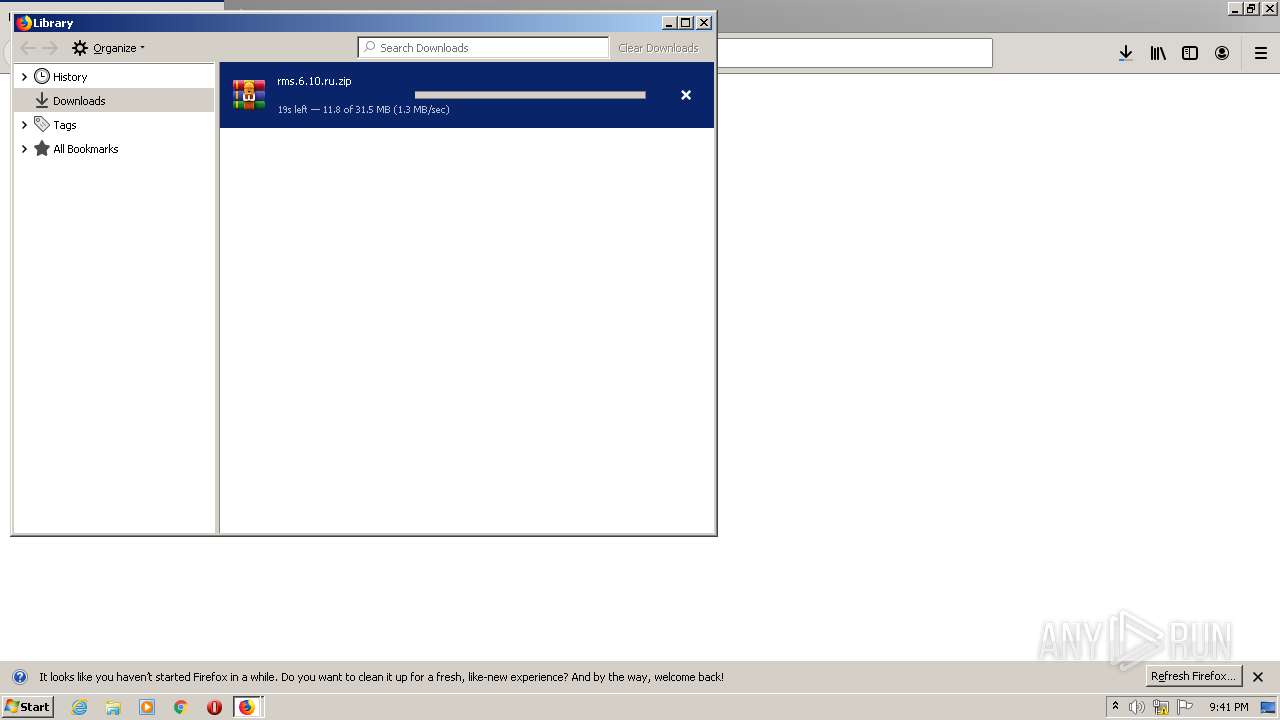
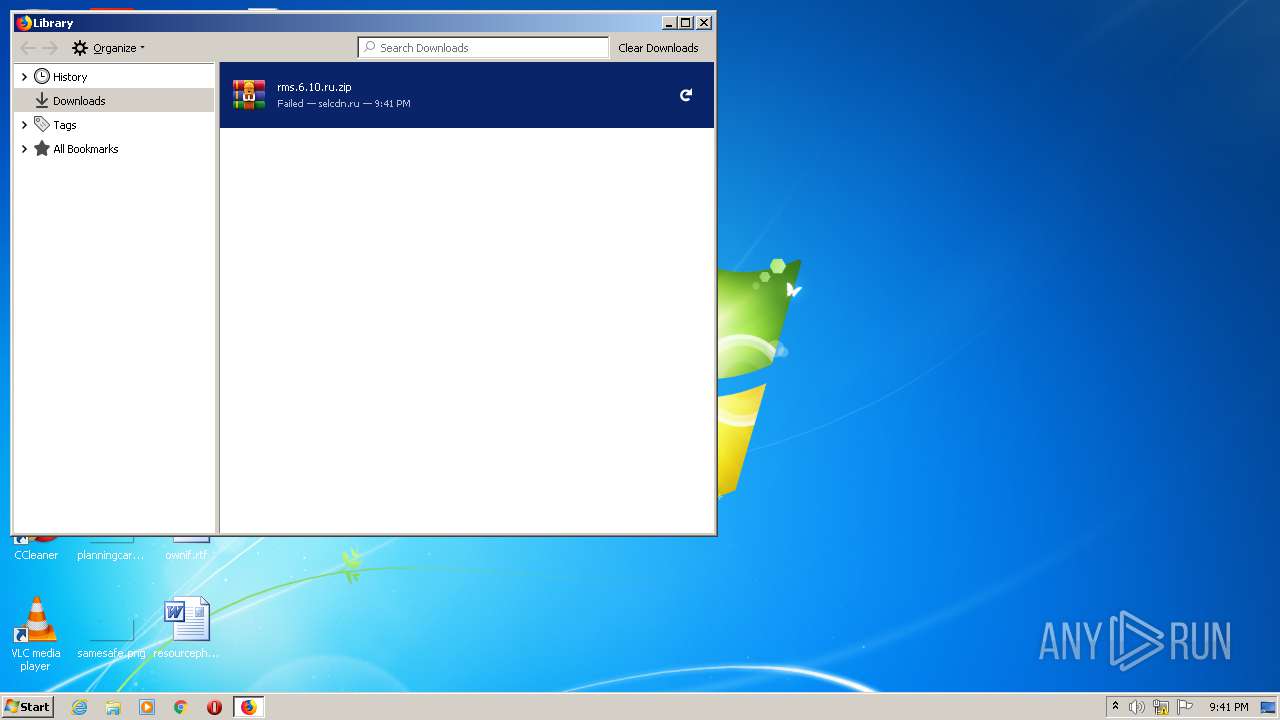
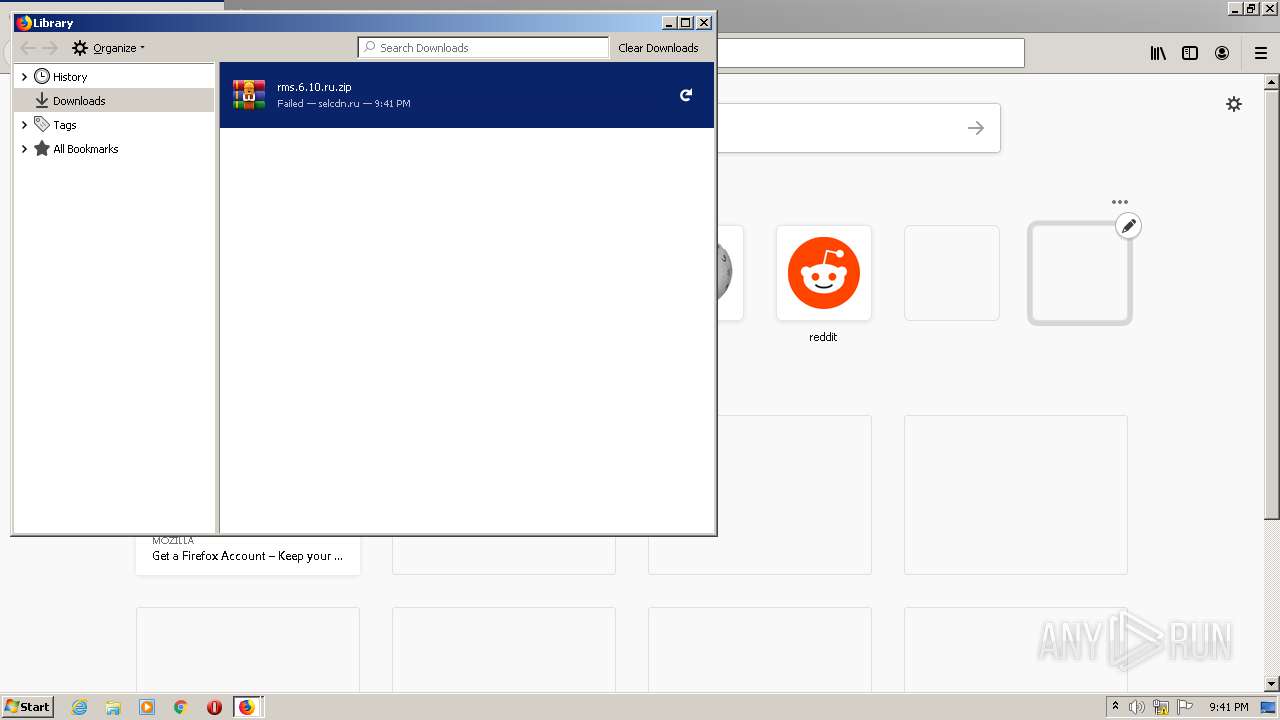
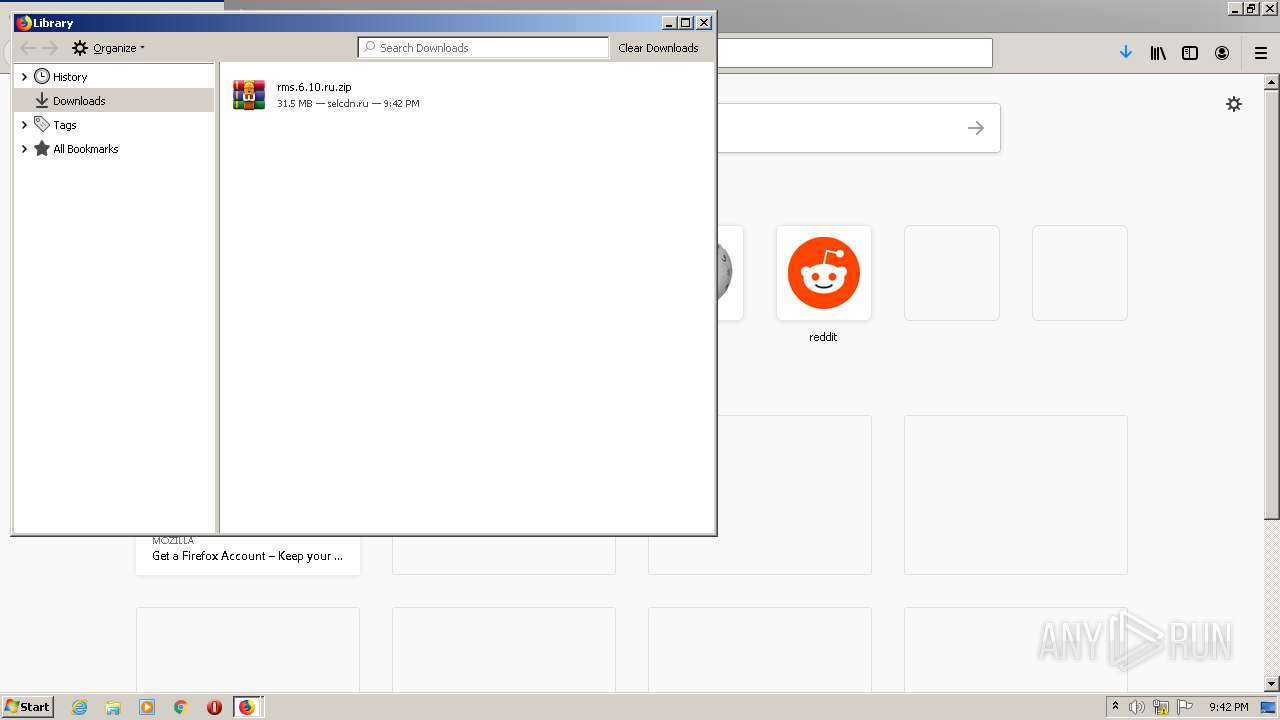
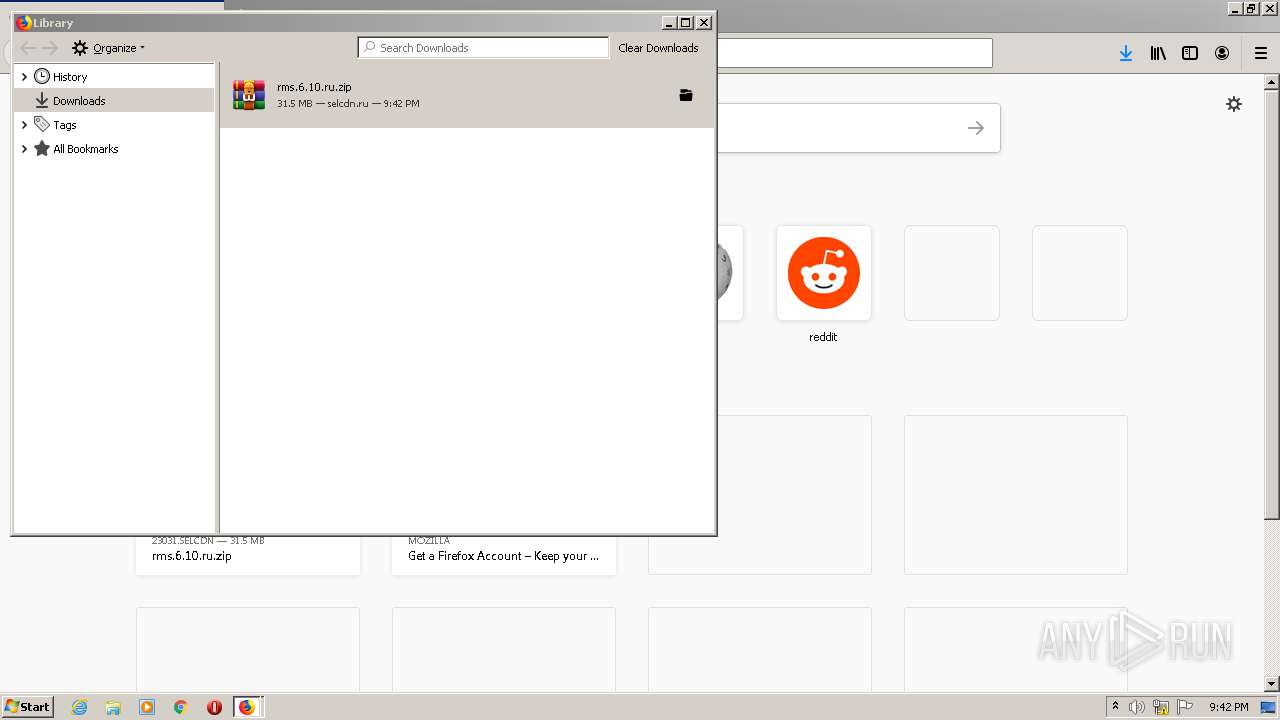
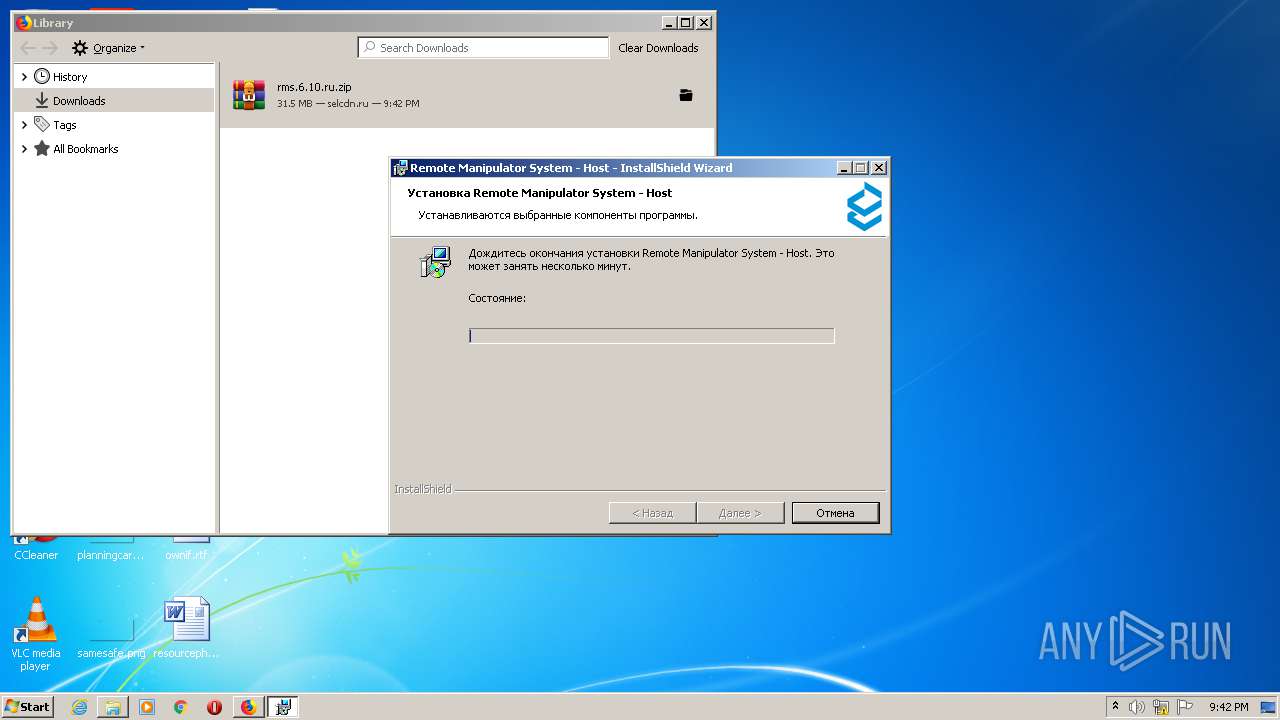
| URL: | https://23031.selcdn.ru/rms-distr-01/rms.6.10.ru.zip |
| Full analysis: | https://app.any.run/tasks/c0fc8427-4721-4bf9-96c8-830dd2e679bb |
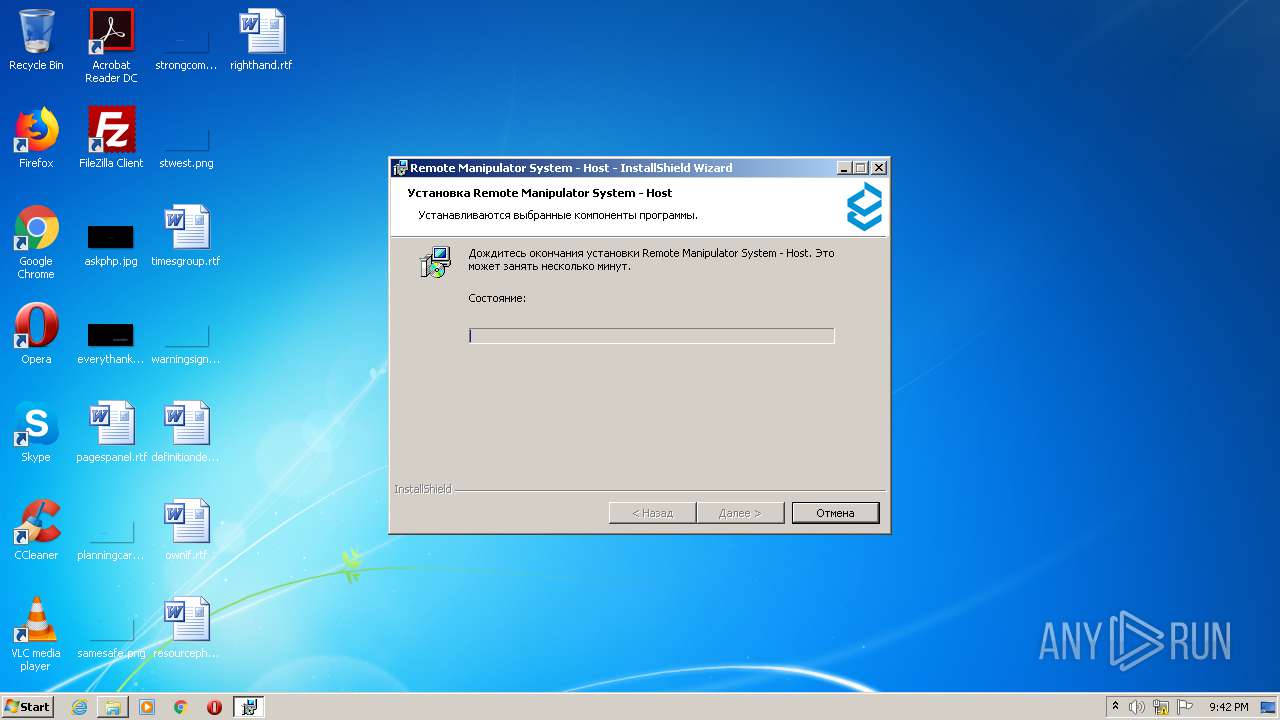
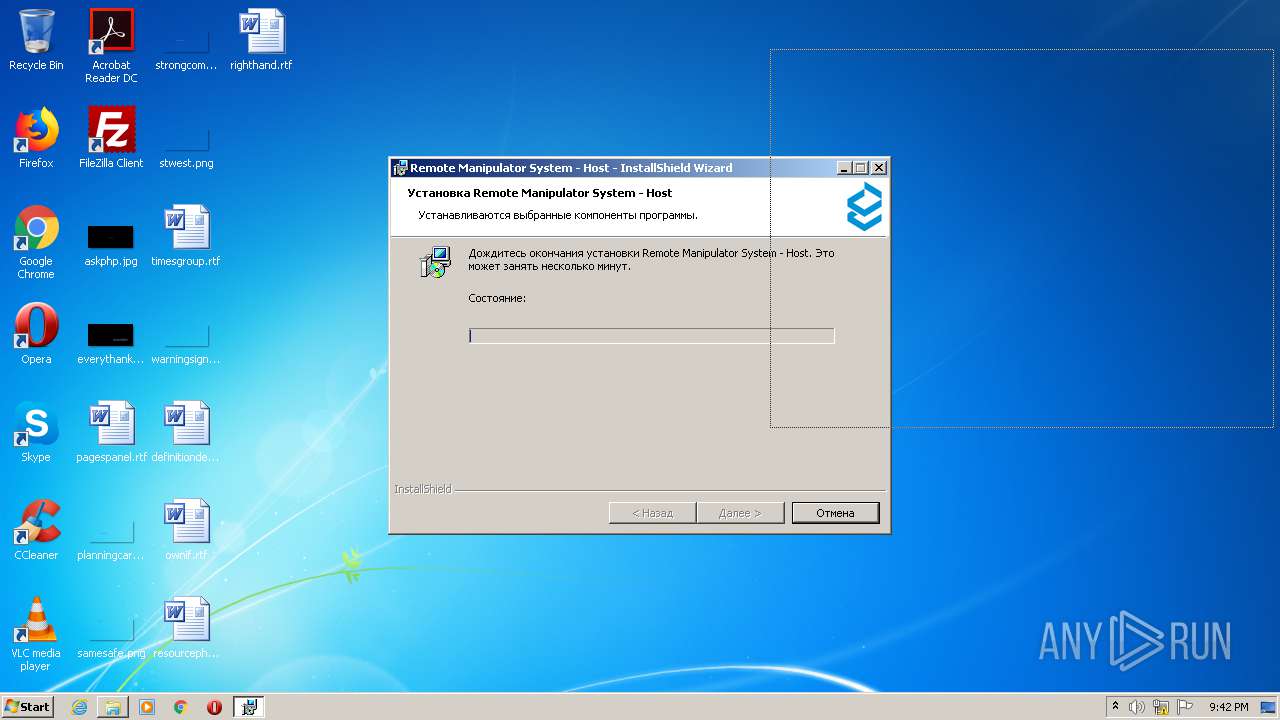
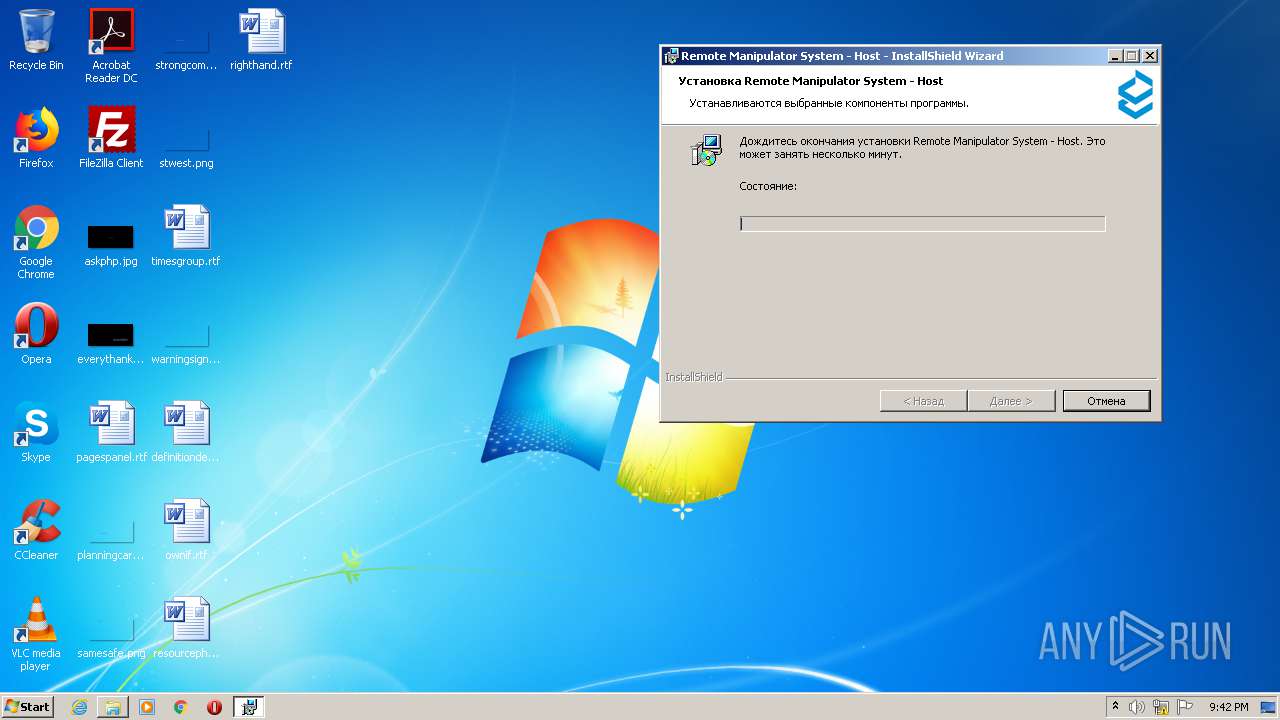
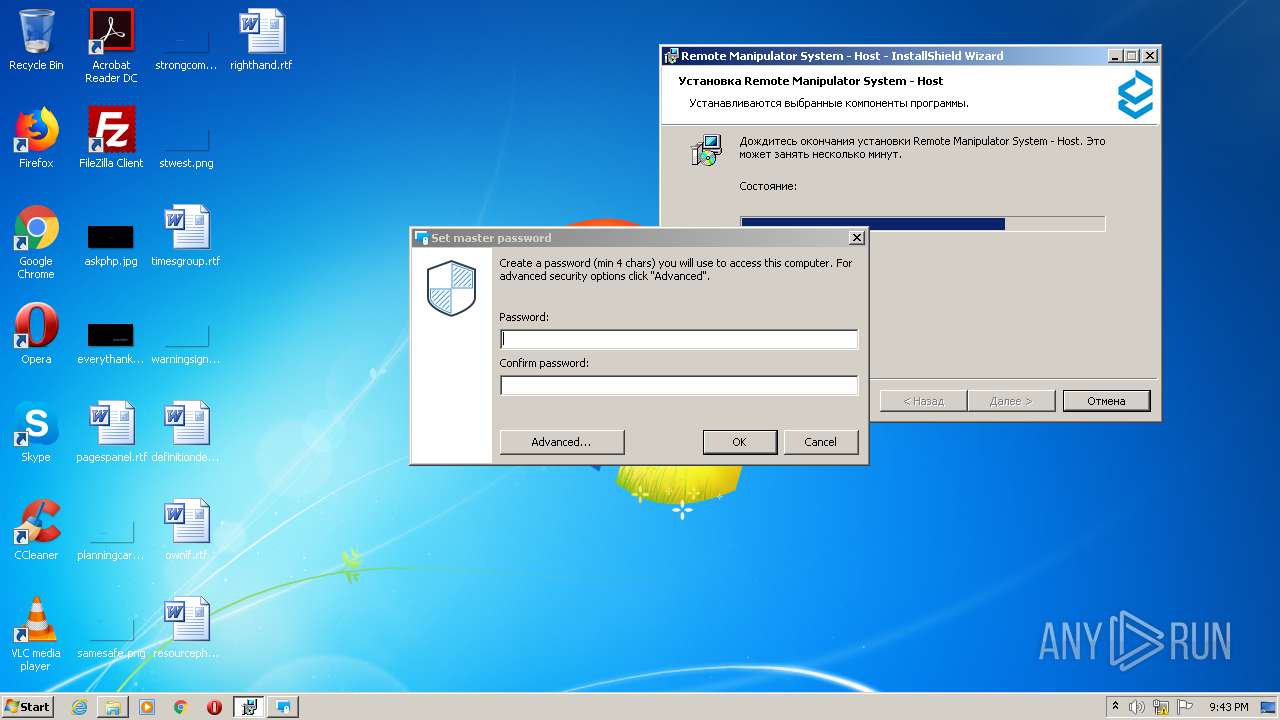
| Verdict: | Malicious activity |
| Threats: | Remote access trojans (RATs) are a type of malware that enables attackers to establish complete to partial control over infected computers. Such malicious programs often have a modular design, offering a wide range of functionalities for conducting illicit activities on compromised systems. Some of the most common features of RATs include access to the users’ data, webcam, and keystrokes. This malware is often distributed through phishing emails and links. |
| Analysis date: | August 31, 2020, 20:40:40 |
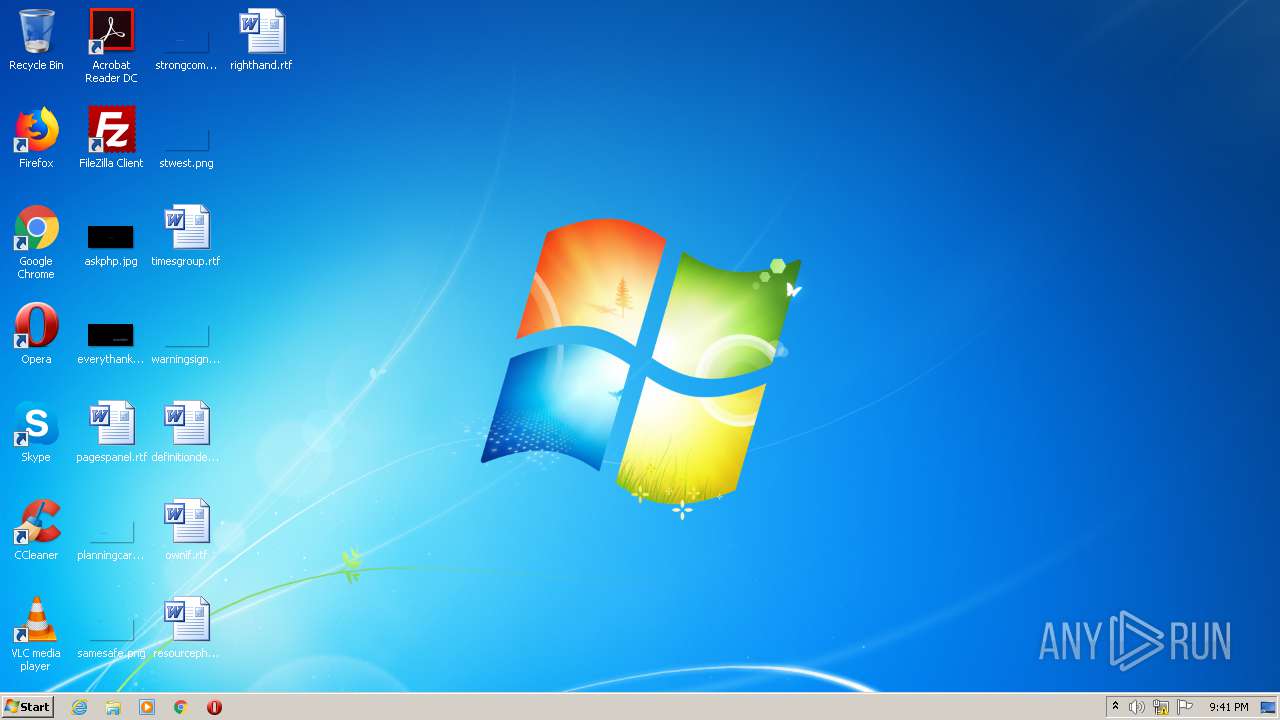
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | D759293057842101840C21EF94B97CE0 |
| SHA1: | 0F2120565276AED3EF133807B67CF3584797B3AC |
| SHA256: | 76A27BD7646D6AFDBFE968B11B96B1B0A293006757CA645F105749C9F0306DEB |
| SSDEEP: | 3:N8eDYIYNeALfMV:2eU5t4 |
MALICIOUS
Application was dropped or rewritten from another process
- rms.host.6.10.ru.exe (PID: 2828)
- rms.host.6.10.ru.exe (PID: 128)
- rutserv.exe (PID: 2336)
- rutserv.exe (PID: 704)
- rutserv.exe (PID: 4020)
- rutserv.exe (PID: 3024)
- rfusclient.exe (PID: 2032)
- rfusclient.exe (PID: 304)
- rfusclient.exe (PID: 2712)
- rfusclient.exe (PID: 2944)
- rutserv.exe (PID: 1412)
- rutserv.exe (PID: 1504)
Changes settings of System certificates
- msiexec.exe (PID: 2556)
Loads dropped or rewritten executable
- rutserv.exe (PID: 2336)
- rutserv.exe (PID: 4020)
- rutserv.exe (PID: 704)
- rutserv.exe (PID: 3024)
- rutserv.exe (PID: 1504)
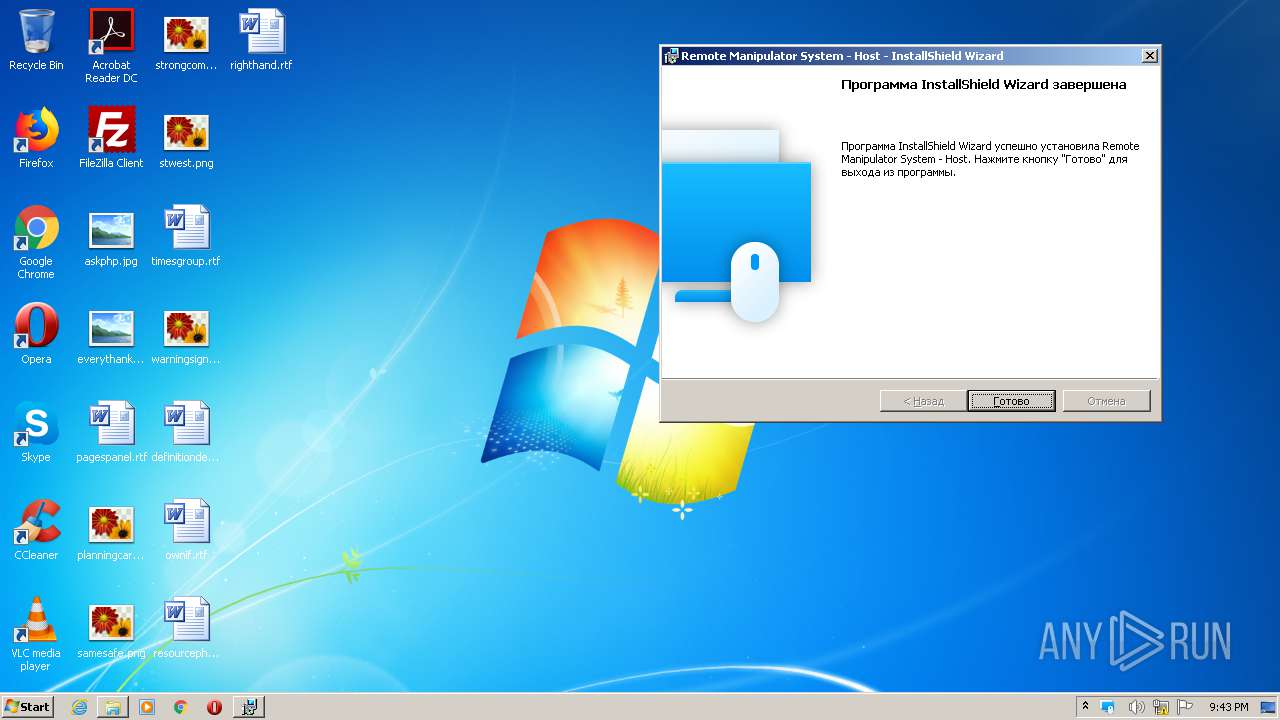
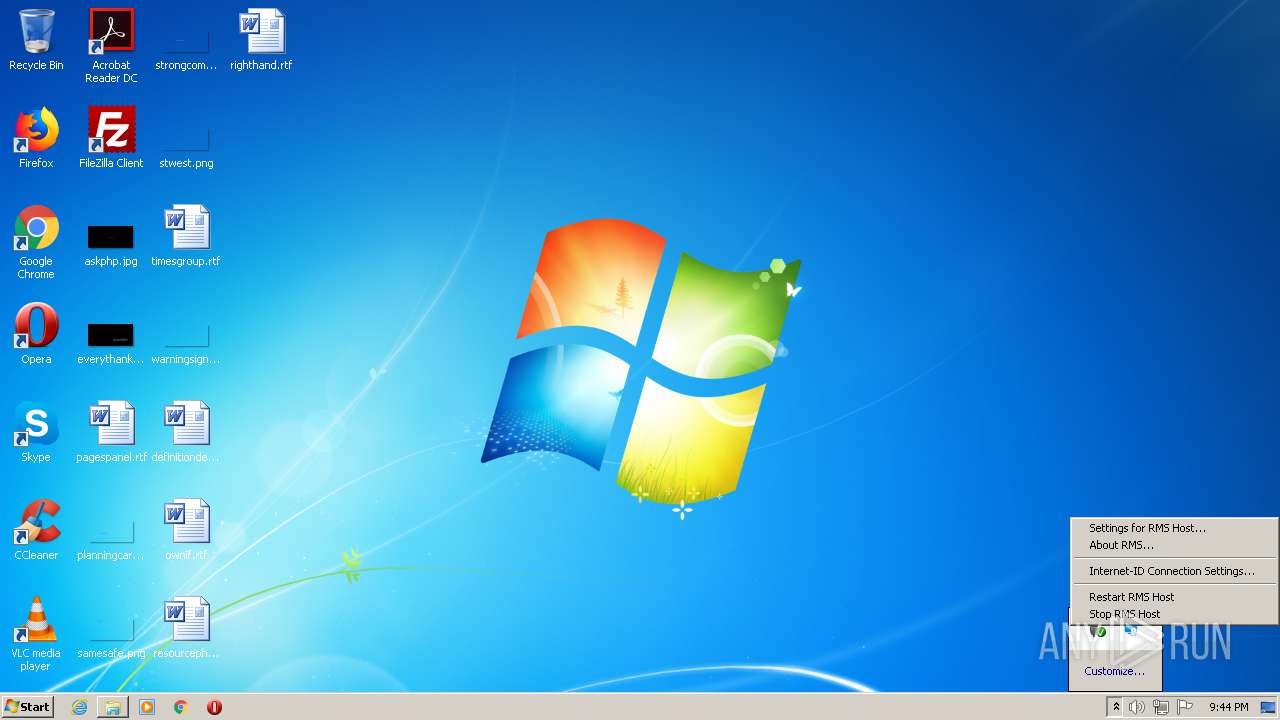
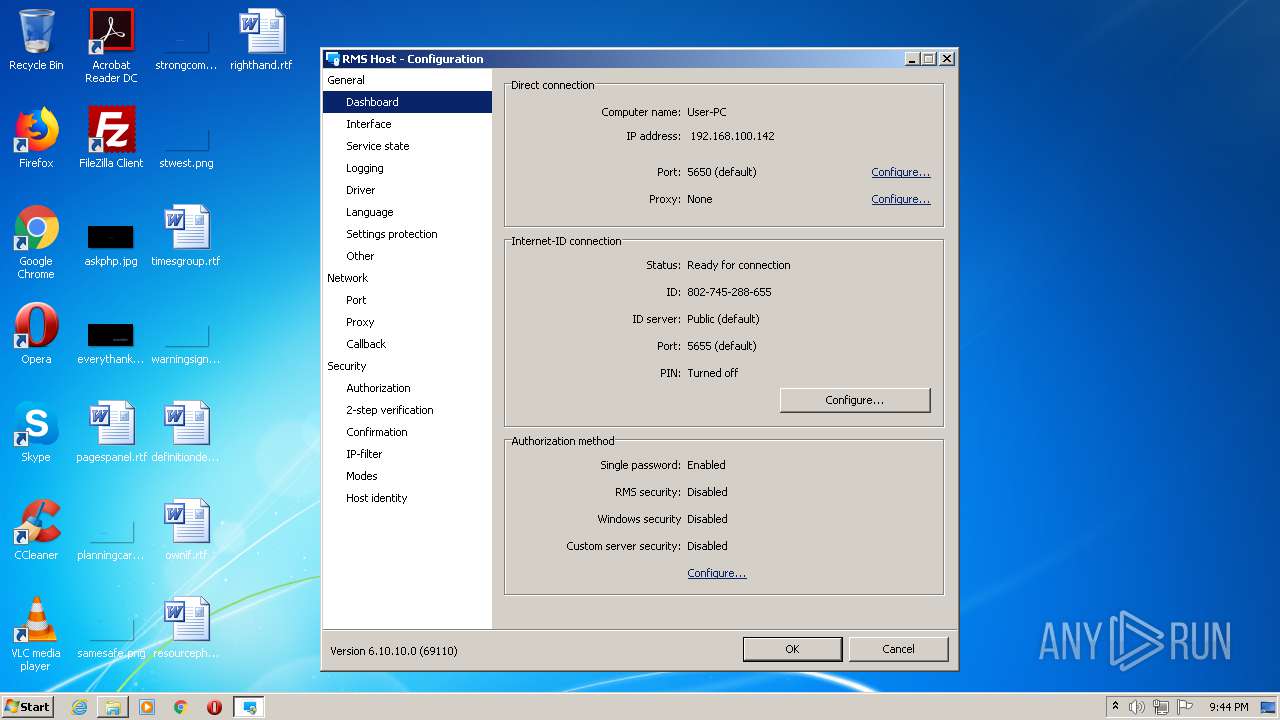
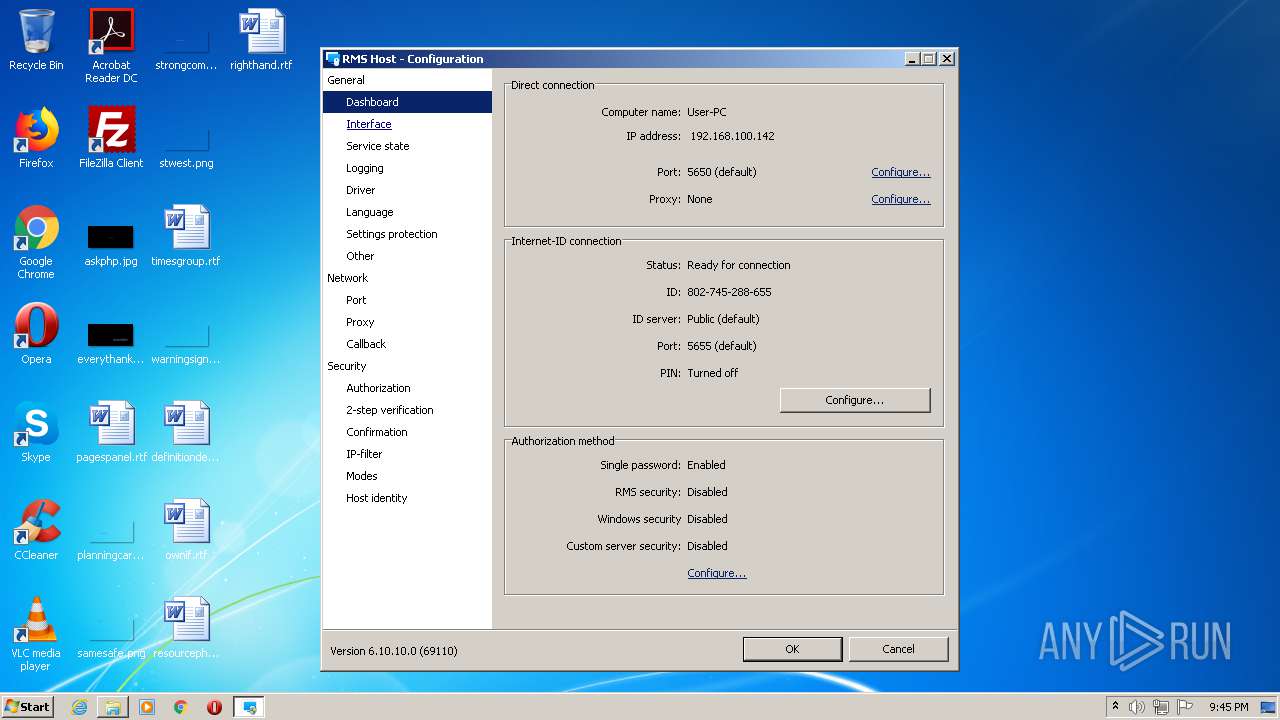
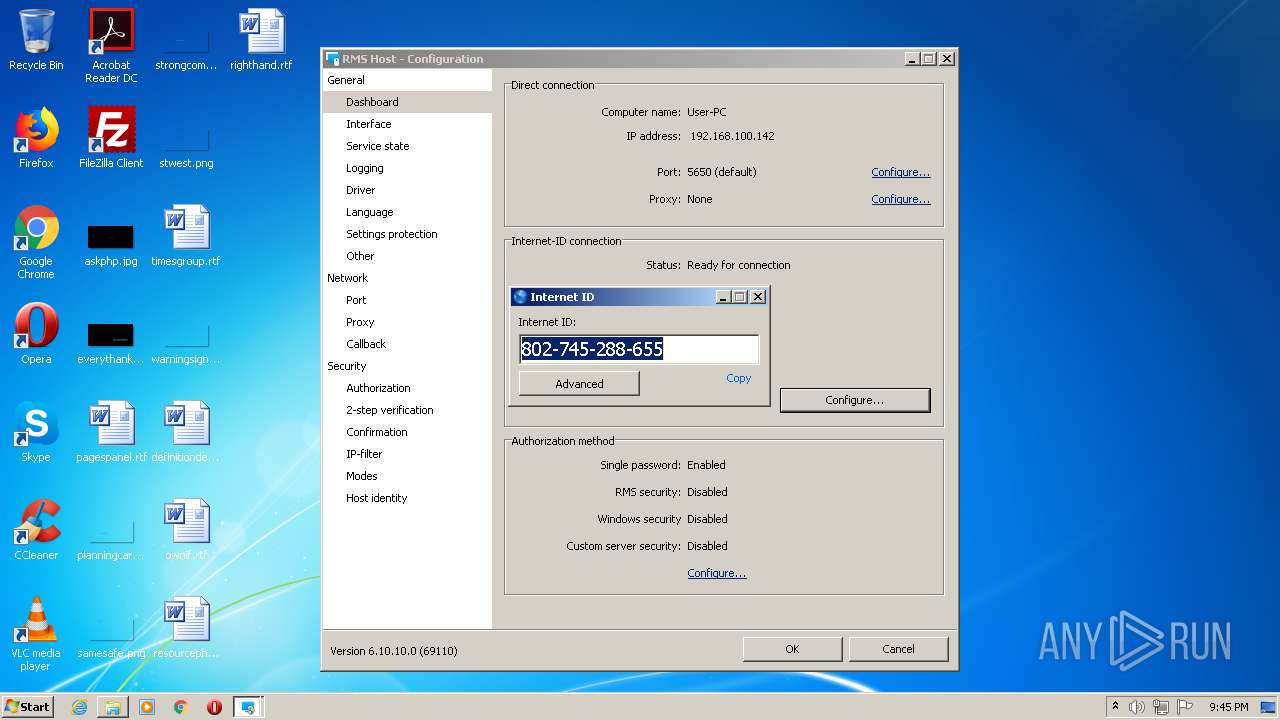
RMS was detected
- rutserv.exe (PID: 3024)
SUSPICIOUS
Creates files in the program directory
- firefox.exe (PID: 3932)
- firefox.exe (PID: 3860)
- rms.host.6.10.ru.exe (PID: 2828)
- rfusclient.exe (PID: 304)
- rutserv.exe (PID: 3024)
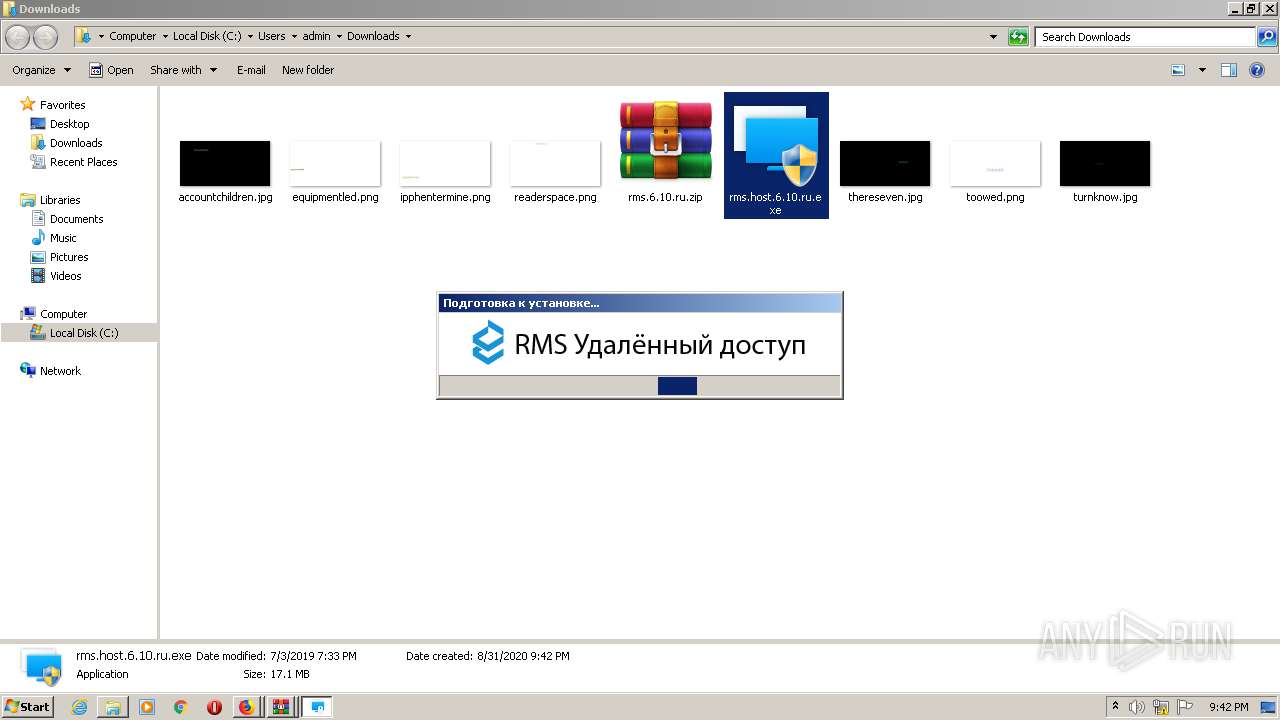
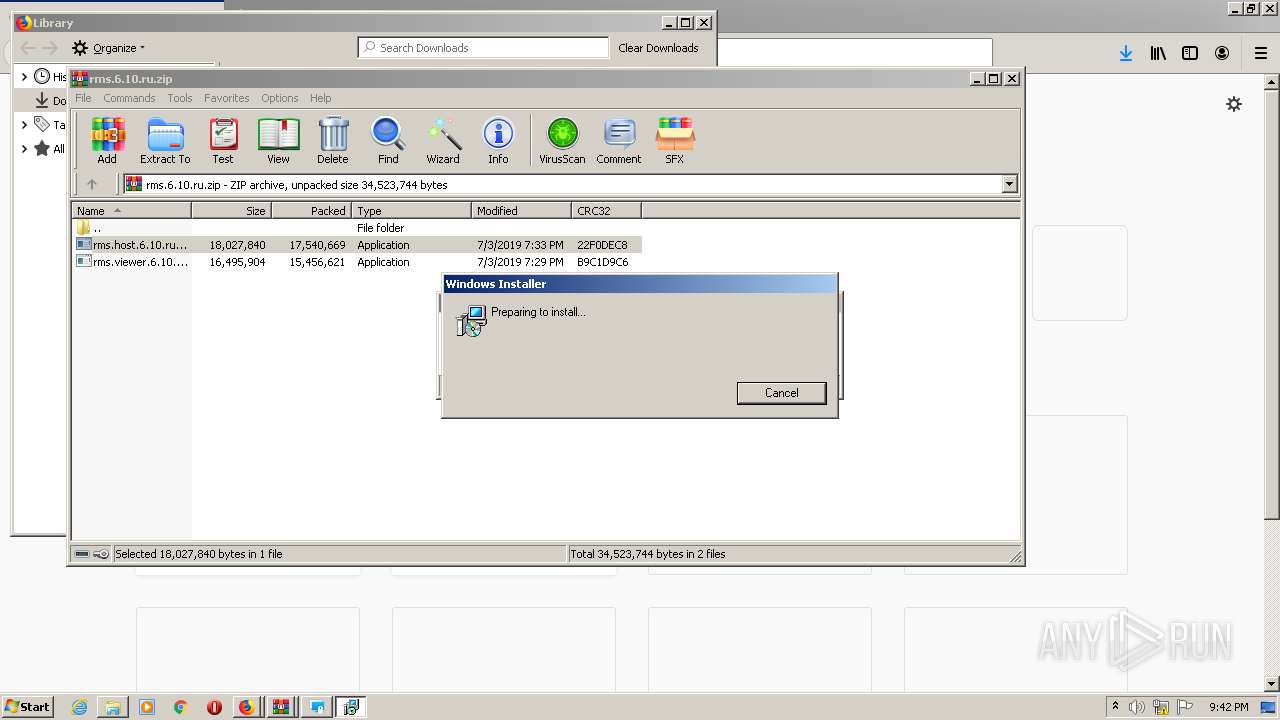
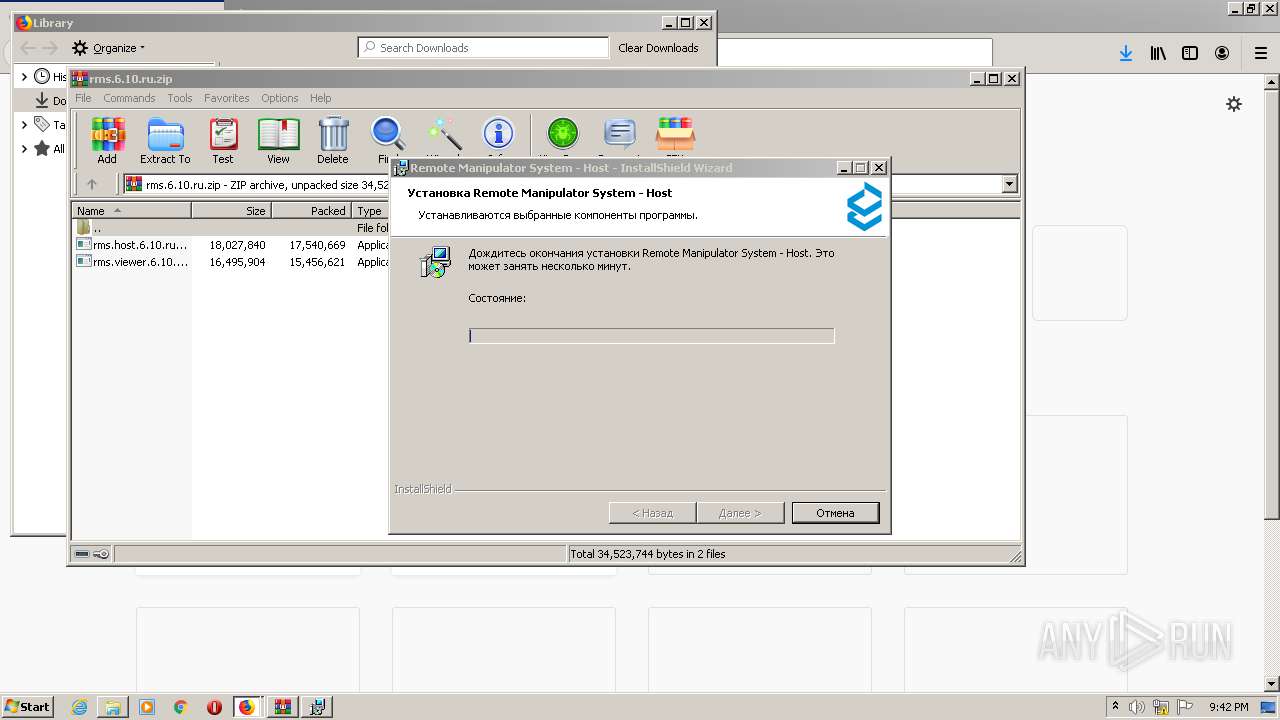
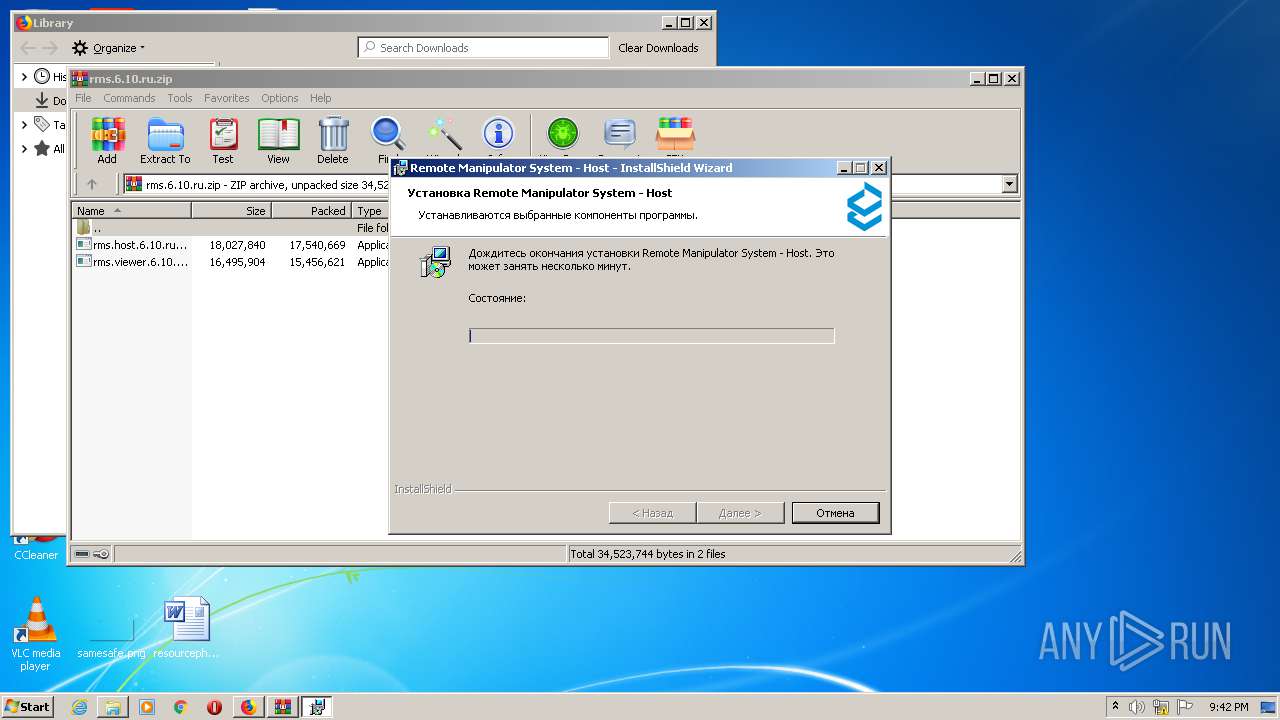
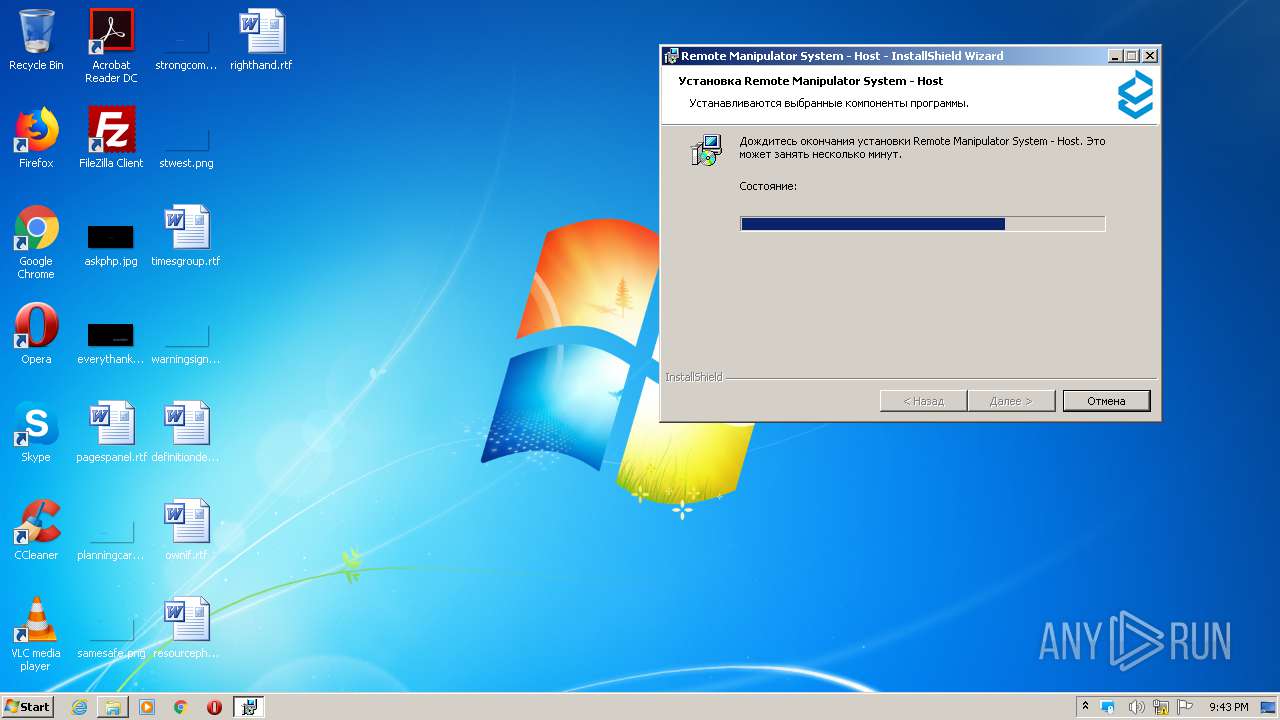
Starts Microsoft Installer
- rms.host.6.10.ru.exe (PID: 2828)
Adds / modifies Windows certificates
- msiexec.exe (PID: 2556)
Reads Environment values
- rfusclient.exe (PID: 304)
- rutserv.exe (PID: 704)
- rutserv.exe (PID: 3024)
- rfusclient.exe (PID: 2712)
- rfusclient.exe (PID: 2032)
- rutserv.exe (PID: 1504)
- rutserv.exe (PID: 4020)
- rutserv.exe (PID: 2336)
- rfusclient.exe (PID: 2944)
Reads the machine GUID from the registry
- rfusclient.exe (PID: 304)
- rutserv.exe (PID: 2336)
- rutserv.exe (PID: 704)
- rutserv.exe (PID: 3024)
- rfusclient.exe (PID: 2712)
- rfusclient.exe (PID: 2032)
- rfusclient.exe (PID: 2944)
- rutserv.exe (PID: 1504)
- rutserv.exe (PID: 4020)
Reads Windows Product ID
- rfusclient.exe (PID: 304)
- rutserv.exe (PID: 704)
- rutserv.exe (PID: 3024)
- rfusclient.exe (PID: 2712)
- rfusclient.exe (PID: 2032)
- rutserv.exe (PID: 1504)
- rfusclient.exe (PID: 2944)
- rutserv.exe (PID: 2336)
- rutserv.exe (PID: 4020)
Executed as Windows Service
- rutserv.exe (PID: 3024)
Searches for installed software
- rms.host.6.10.ru.exe (PID: 2828)
Removes files from Windows directory
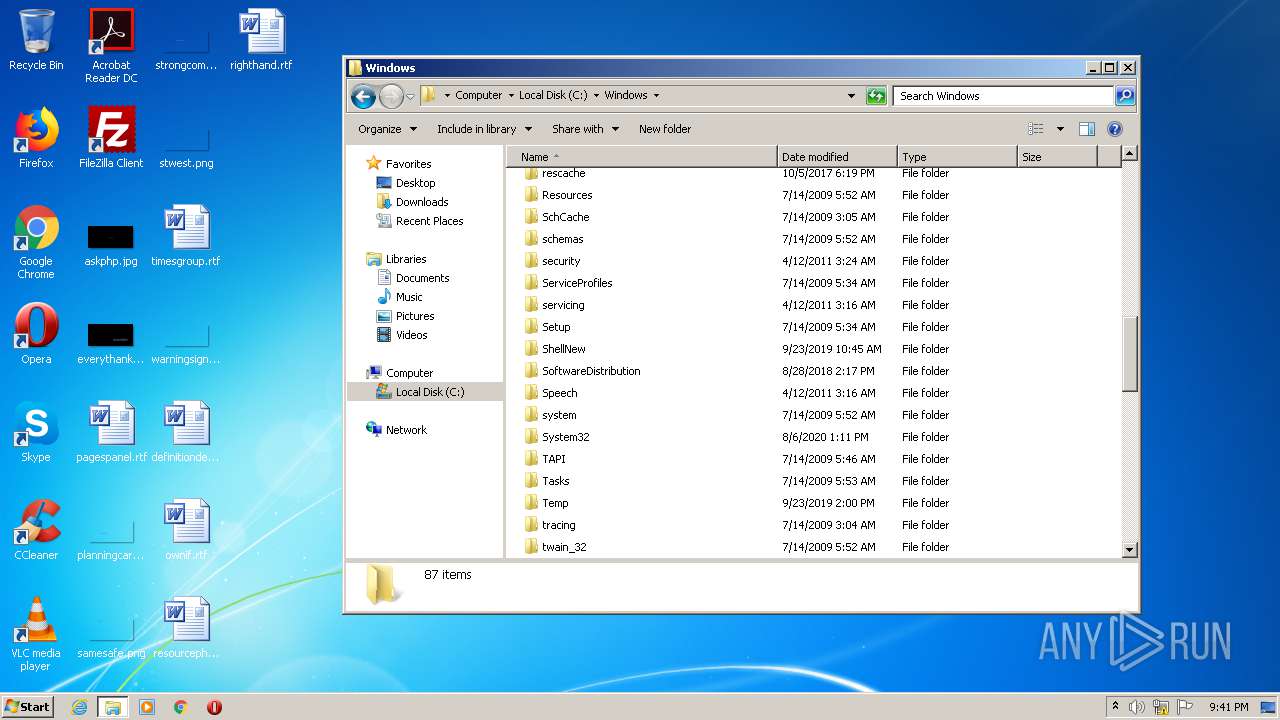
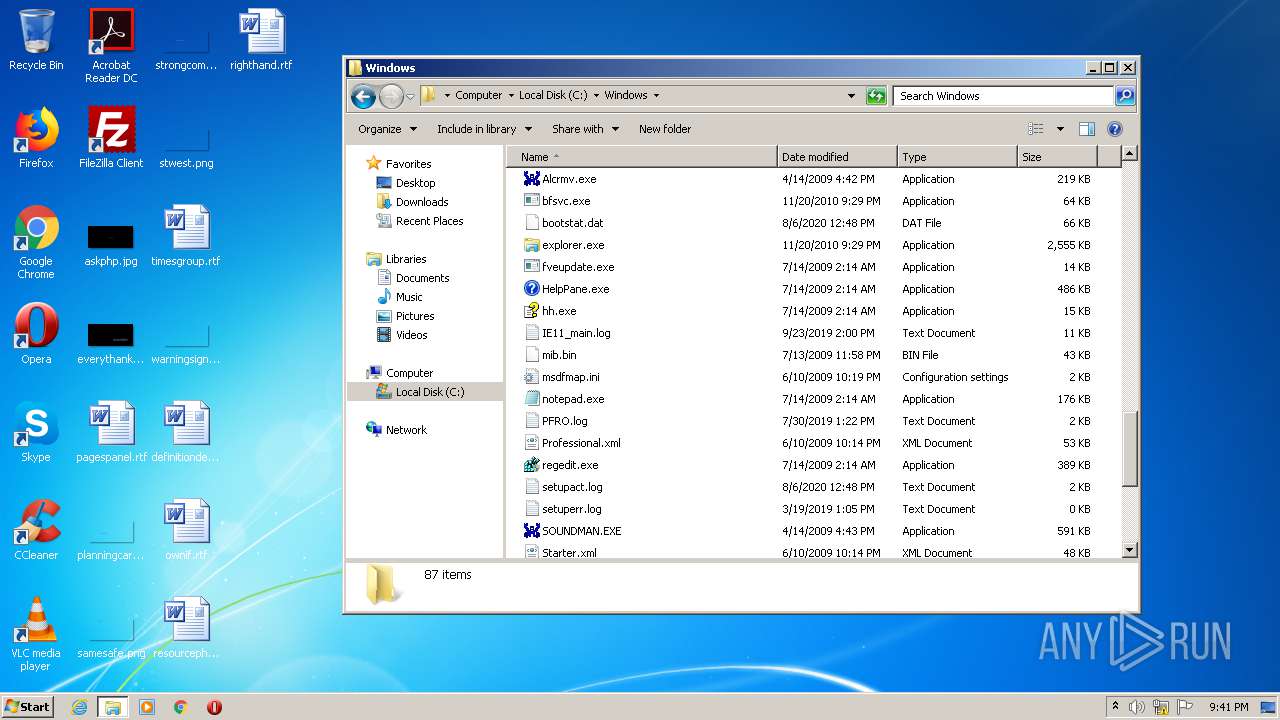
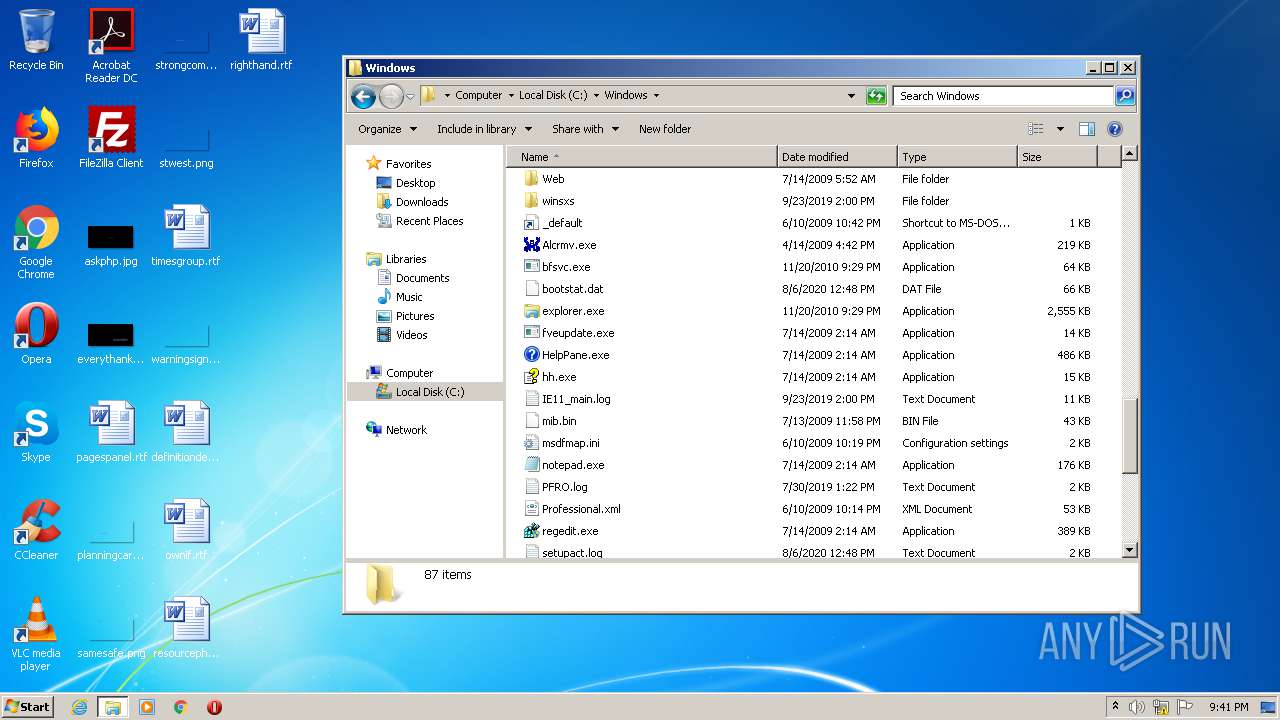
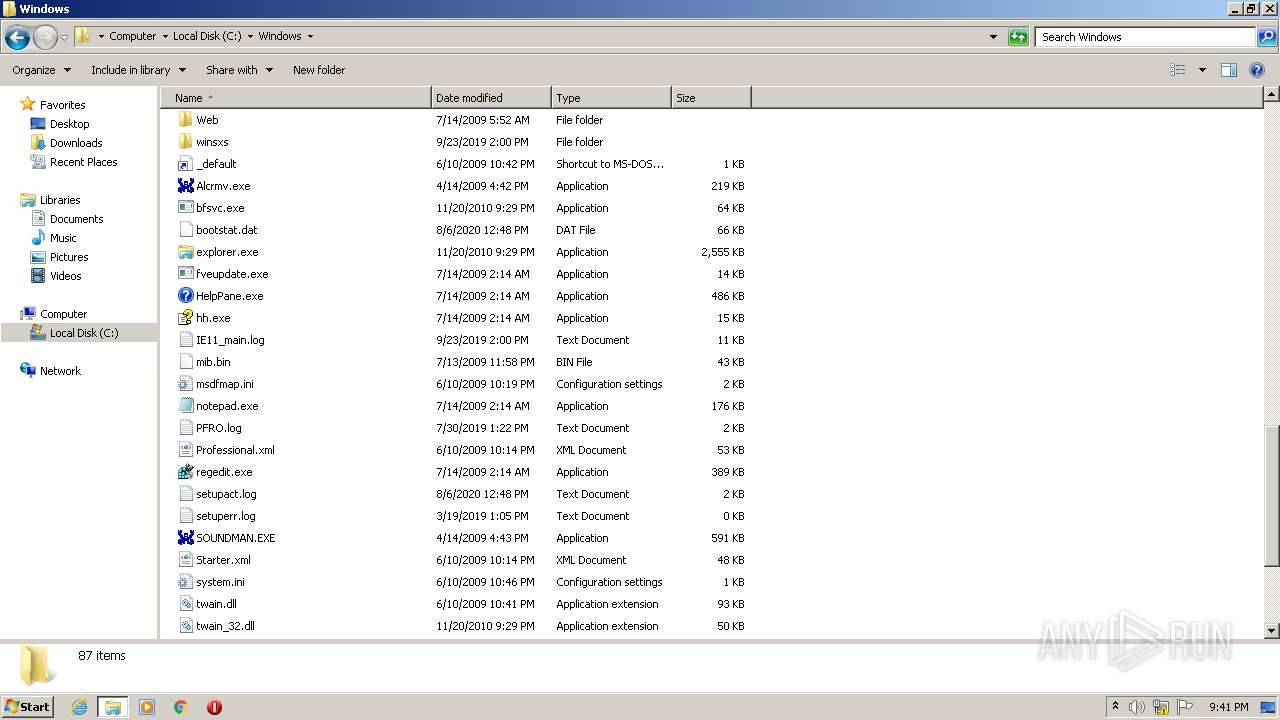
- rutserv.exe (PID: 3024)
Application launched itself
- rfusclient.exe (PID: 2032)
INFO
Application launched itself
- firefox.exe (PID: 2748)
- firefox.exe (PID: 3932)
- firefox.exe (PID: 3860)
- firefox.exe (PID: 2532)
Creates files in the user directory
- firefox.exe (PID: 3932)
- firefox.exe (PID: 3860)
Reads Internet Cache Settings
- pingsender.exe (PID: 672)
- firefox.exe (PID: 3932)
- pingsender.exe (PID: 3112)
- pingsender.exe (PID: 2952)
- firefox.exe (PID: 3860)
- pingsender.exe (PID: 620)
- pingsender.exe (PID: 2372)
Changes settings of System certificates
- pingsender.exe (PID: 2952)
- pingsender.exe (PID: 672)
- pingsender.exe (PID: 3112)
- pingsender.exe (PID: 620)
- pingsender.exe (PID: 2372)
Reads CPU info
- firefox.exe (PID: 3932)
- firefox.exe (PID: 3860)
Adds / modifies Windows certificates
- pingsender.exe (PID: 2952)
- pingsender.exe (PID: 3112)
- pingsender.exe (PID: 672)
- pingsender.exe (PID: 620)
- pingsender.exe (PID: 2372)
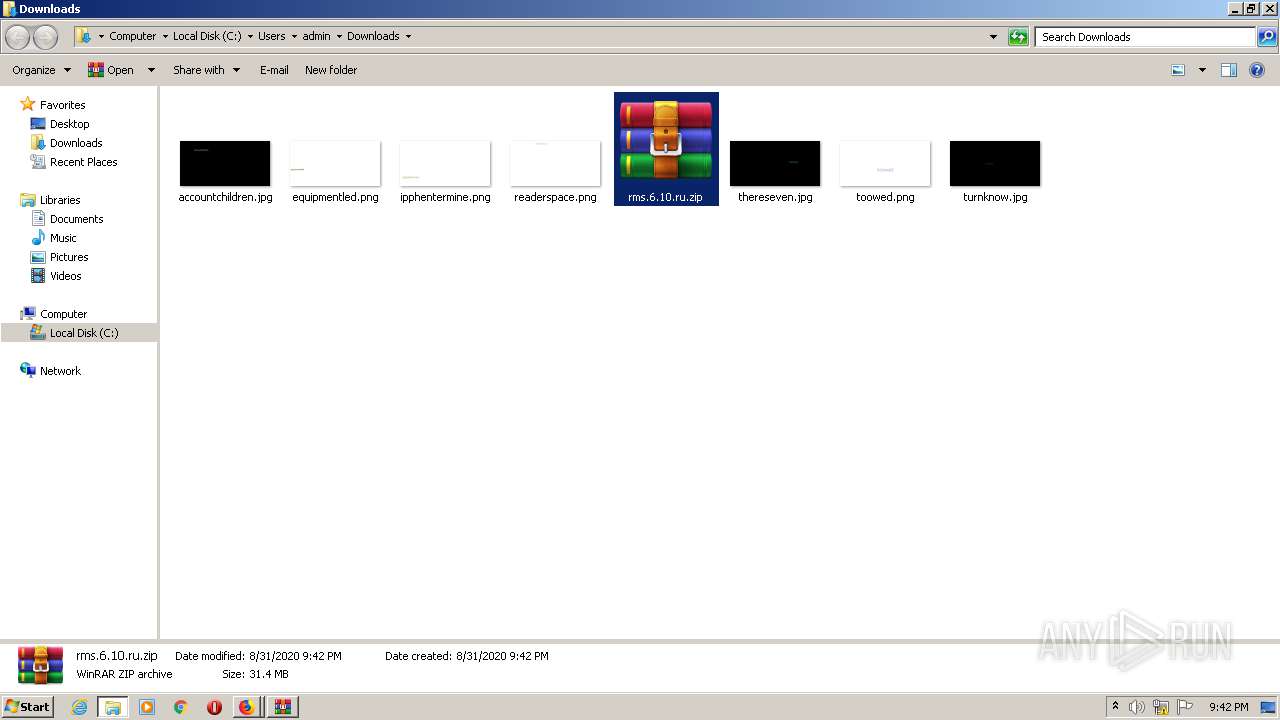
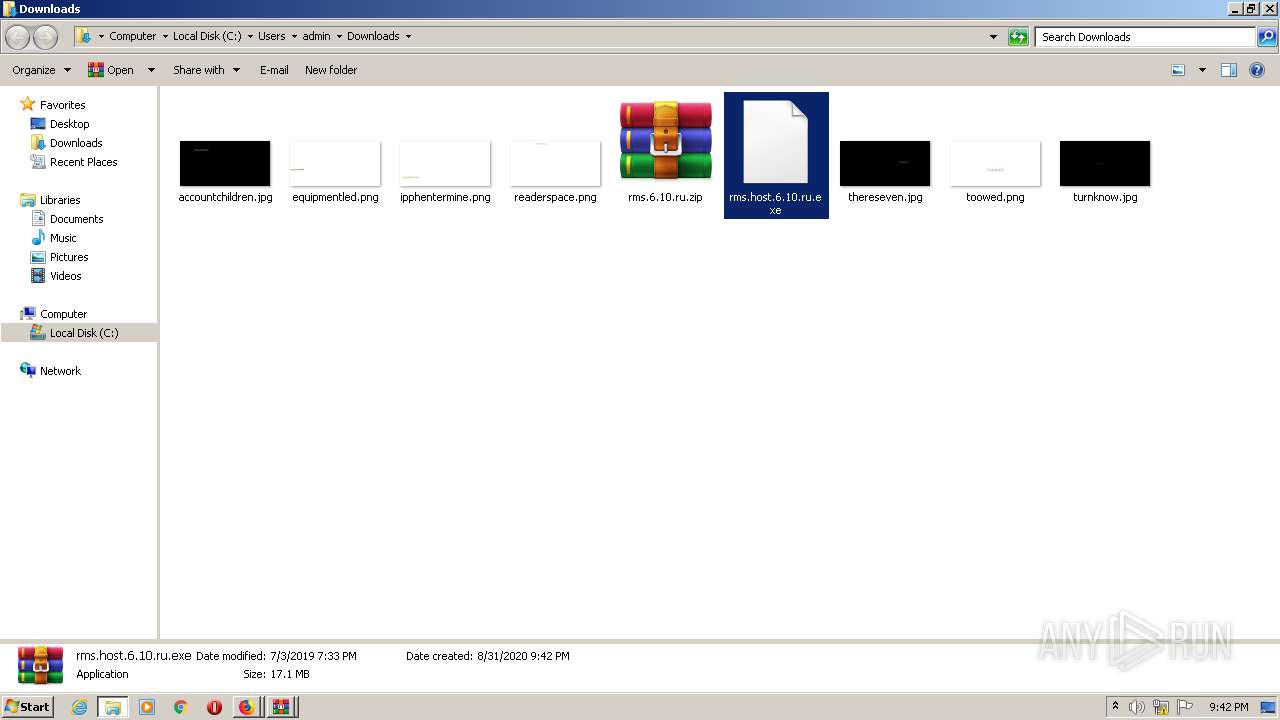
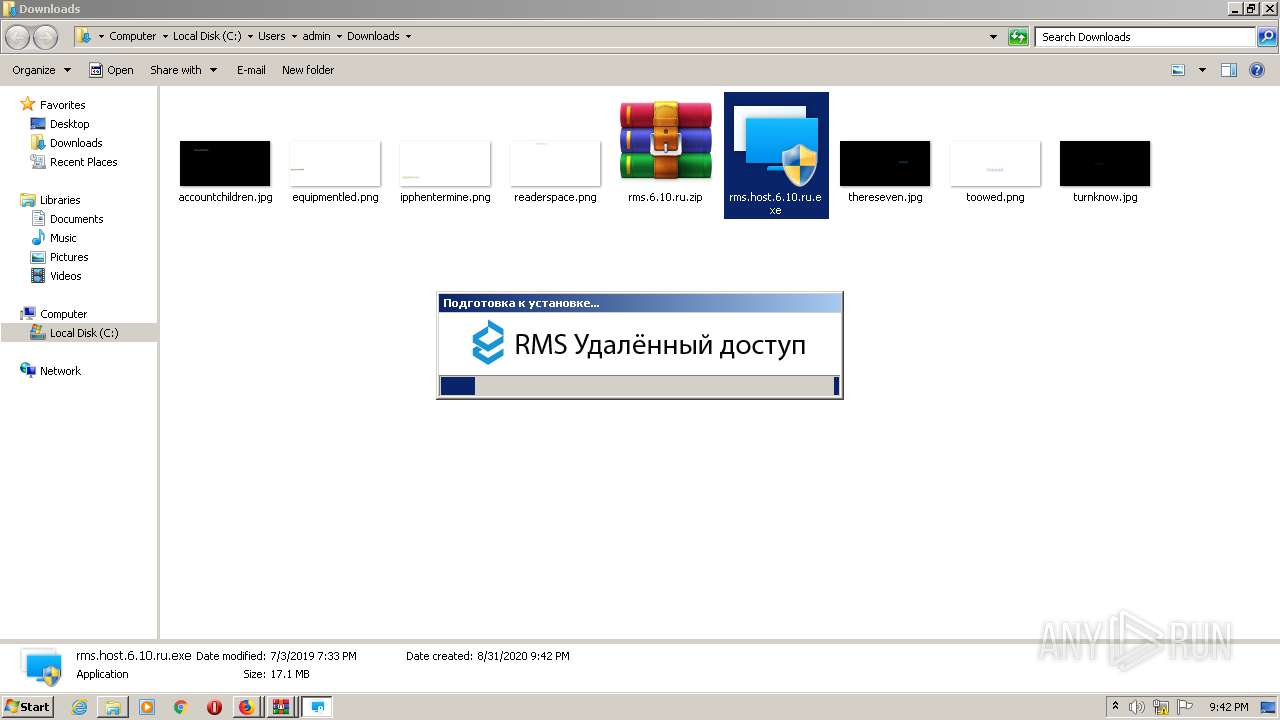
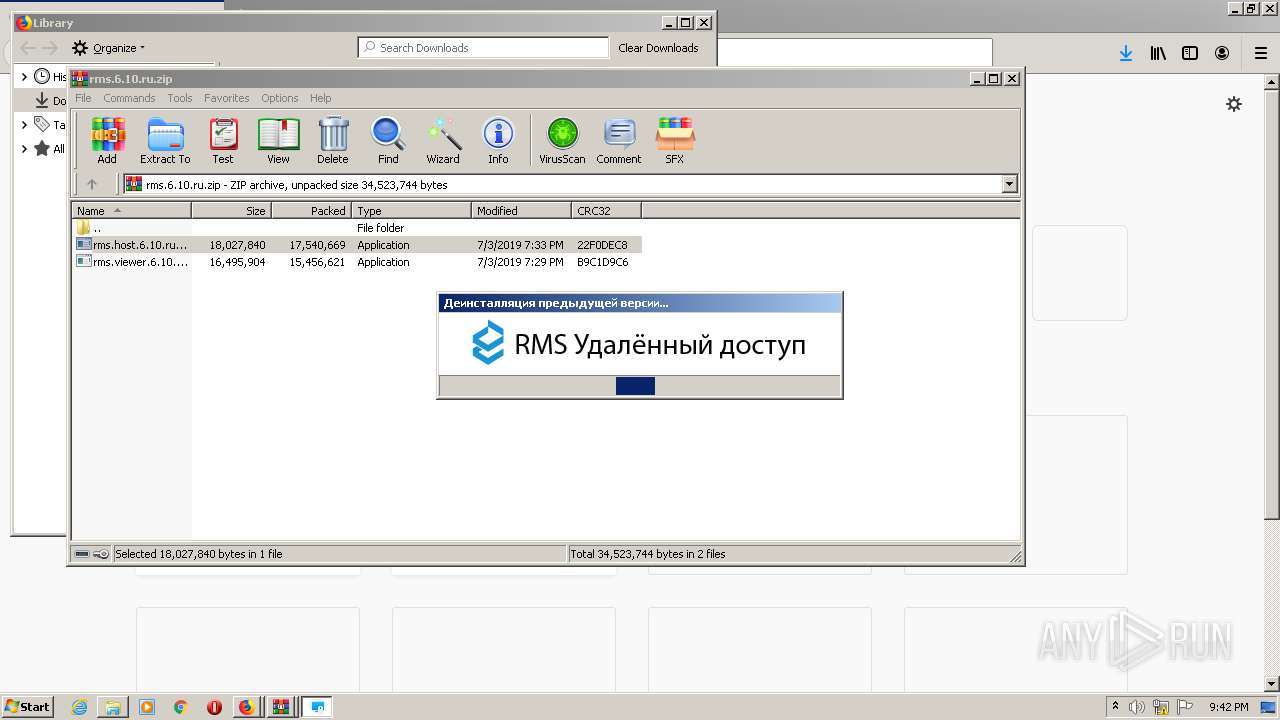
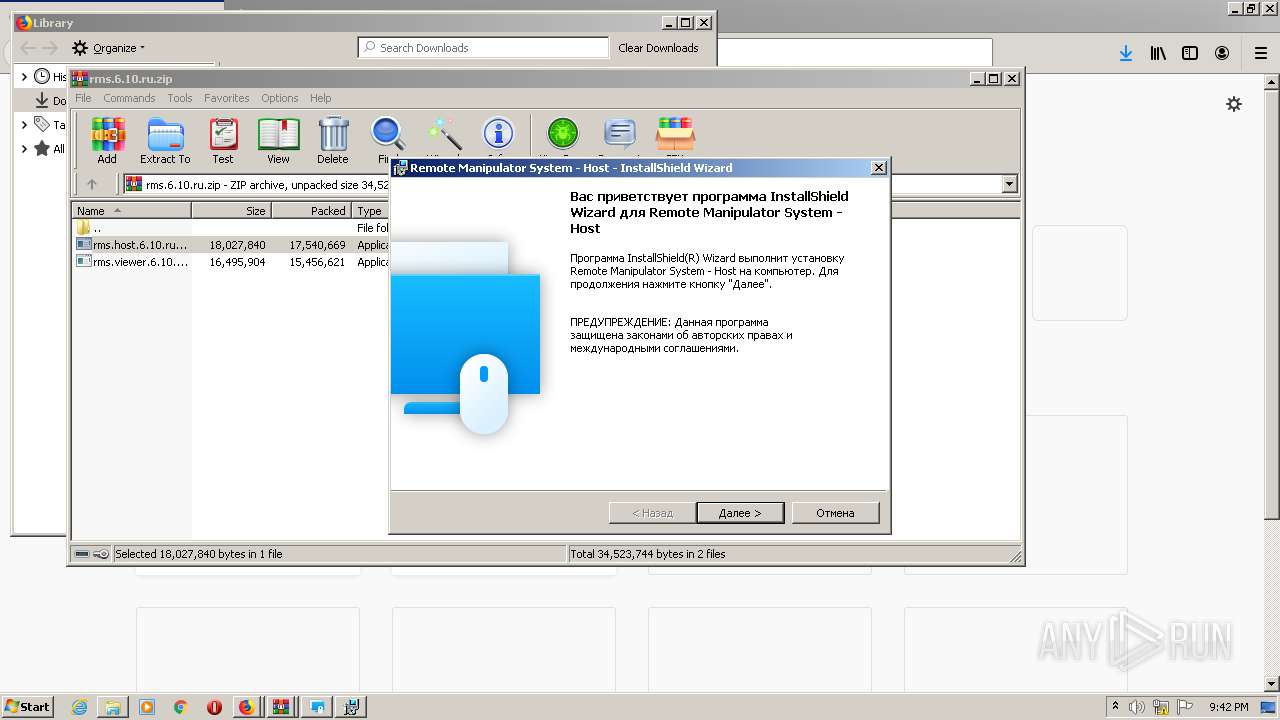
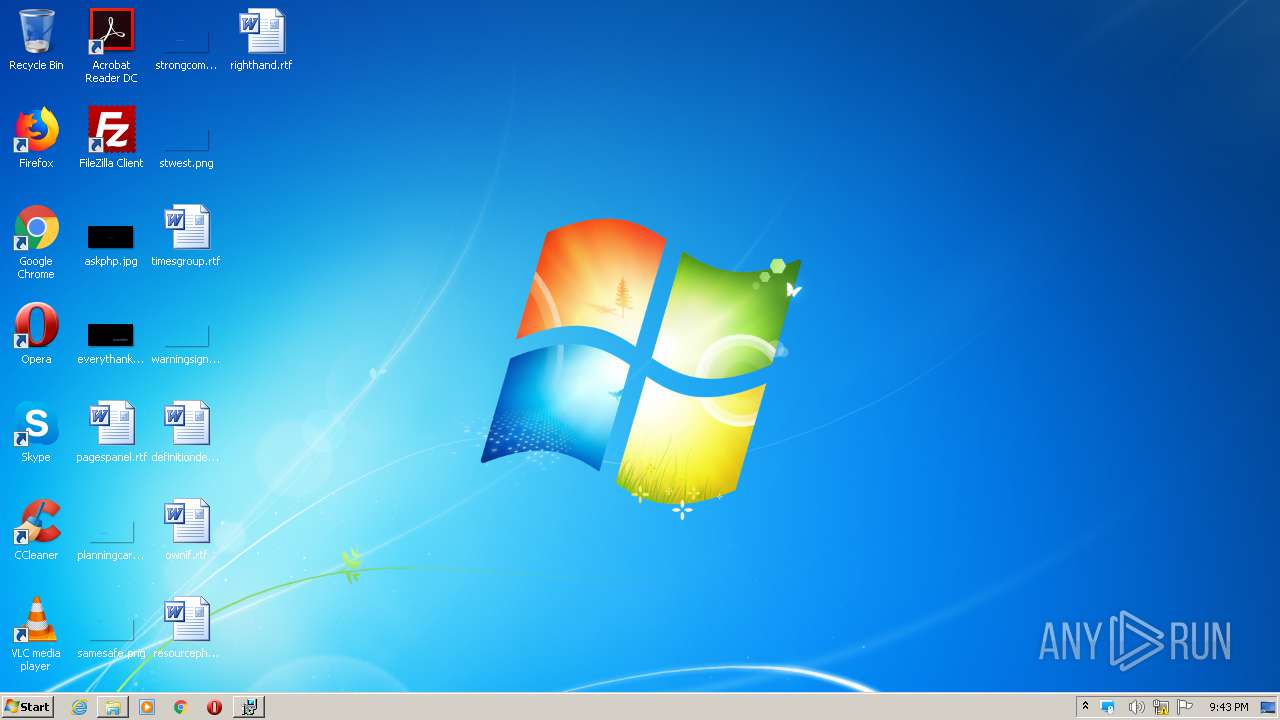
Manual execution by user
- explorer.exe (PID: 2588)
- firefox.exe (PID: 2532)
- rms.host.6.10.ru.exe (PID: 2828)
- WinRAR.exe (PID: 1396)
- rms.host.6.10.ru.exe (PID: 128)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
88
Monitored processes
33
Malicious processes
4
Suspicious processes
5
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
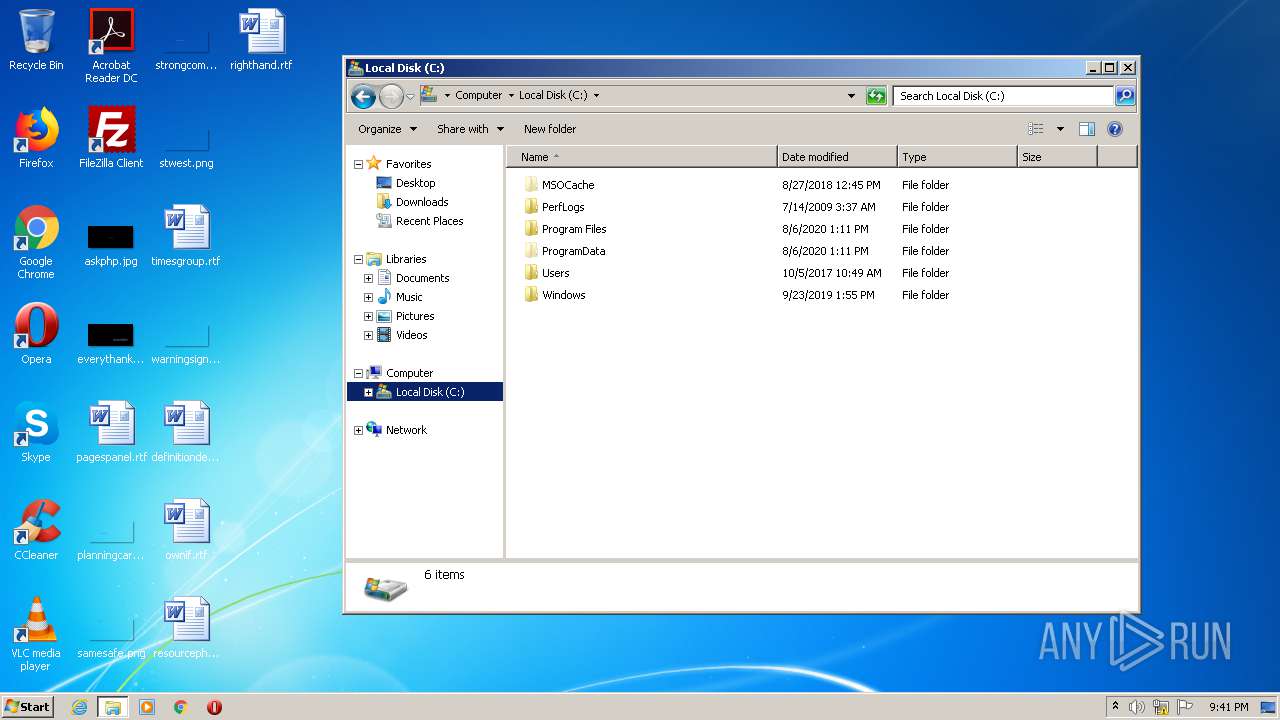
| 128 | "C:\Users\admin\Downloads\rms.host.6.10.ru.exe" | C:\Users\admin\Downloads\rms.host.6.10.ru.exe | — | explorer.exe | |||||||||||
User: admin Company: TektonIT Integrity Level: MEDIUM Description: RMS Exit code: 3221226540 Version: 6.10.10.0 Modules
| |||||||||||||||
| 304 | "C:\Program Files\Remote Manipulator System - Host\rfusclient.exe" -msi_copy "C:\Users\admin\AppData\Local\Temp\RMS_{421ED2E9-5AD0-48A3-BDF2-673AAFB5C847}\installer.msi" | C:\Program Files\Remote Manipulator System - Host\rfusclient.exe | — | msiexec.exe | |||||||||||
User: admin Company: TektonIT Integrity Level: HIGH Description: RMS Exit code: 0 Version: 6.10.10.0 Modules
| |||||||||||||||
| 584 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="3860.3.868804364\1274751971" -childID 1 -isForBrowser -prefsHandle 1716 -prefMapHandle 1712 -prefsLen 1 -prefMapSize 191902 -parentBuildID 20190717172542 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - 3860 "\\.\pipe\gecko-crash-server-pipe.3860" 1736 tab | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 68.0.1 Modules
| |||||||||||||||
| 620 | "C:\Program Files\Mozilla Firefox\pingsender.exe" https://incoming.telemetry.mozilla.org/submit/telemetry/df436b04-67fc-4a3c-84d9-14998e8e6787/health/Firefox/68.0.1/release/20190717172542?v=4 C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\saved-telemetry-pings\df436b04-67fc-4a3c-84d9-14998e8e6787 | C:\Program Files\Mozilla Firefox\pingsender.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Foundation Integrity Level: MEDIUM Exit code: 0 Version: 68.0.1 Modules
| |||||||||||||||
| 672 | "C:\Program Files\Mozilla Firefox\pingsender.exe" https://incoming.telemetry.mozilla.org/submit/telemetry/a6eca880-a86f-4317-8884-baa80ff50546/health/Firefox/68.0.1/release/20190717172542?v=4 C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\saved-telemetry-pings\a6eca880-a86f-4317-8884-baa80ff50546 | C:\Program Files\Mozilla Firefox\pingsender.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Foundation Integrity Level: MEDIUM Exit code: 0 Version: 68.0.1 Modules
| |||||||||||||||
| 704 | "C:\Program Files\Remote Manipulator System - Host\rutserv.exe" /CONFIG /SETSECURITY | C:\Program Files\Remote Manipulator System - Host\rutserv.exe | — | msiexec.exe | |||||||||||
User: admin Company: TektonIT Integrity Level: HIGH Description: RMS Exit code: 0 Version: 6.10.10.0 Modules
| |||||||||||||||
| 1340 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="3932.20.1156754848\214519057" -childID 3 -isForBrowser -prefsHandle 3572 -prefMapHandle 3596 -prefsLen 6718 -prefMapSize 191824 -parentBuildID 20190717172542 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - 3932 "\\.\pipe\gecko-crash-server-pipe.3932" 3800 tab | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 68.0.1 Modules
| |||||||||||||||
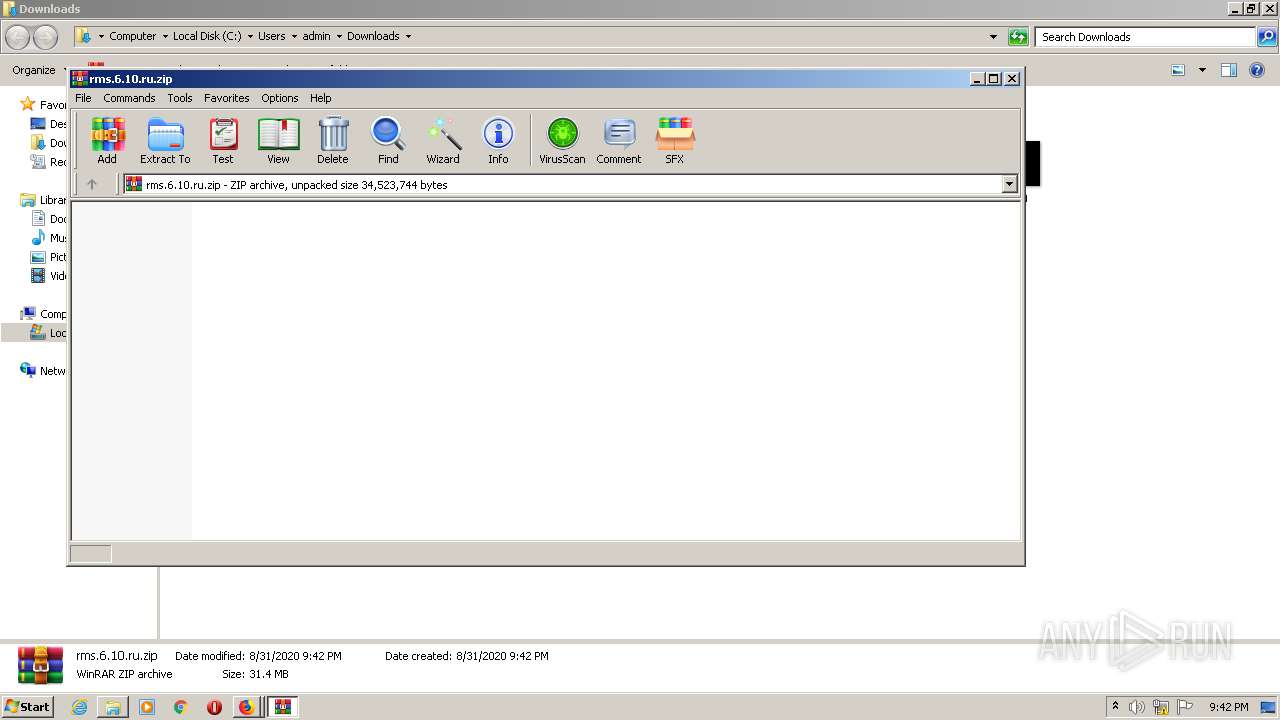
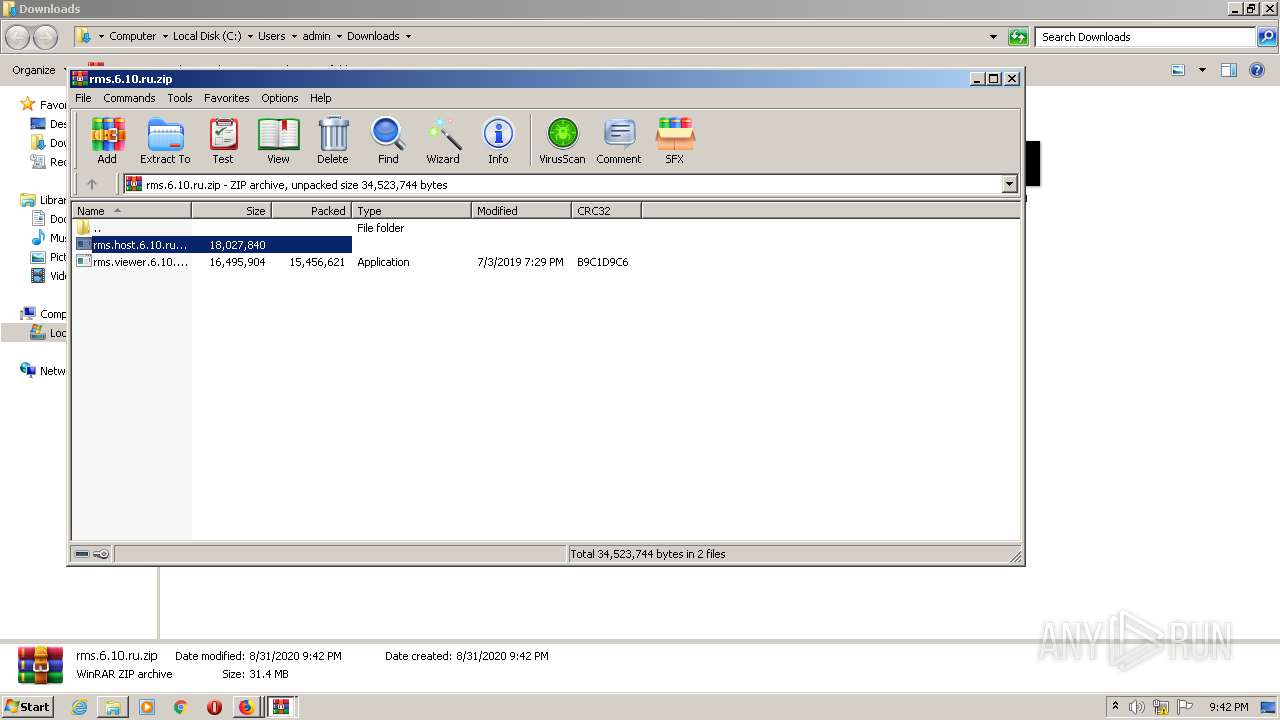
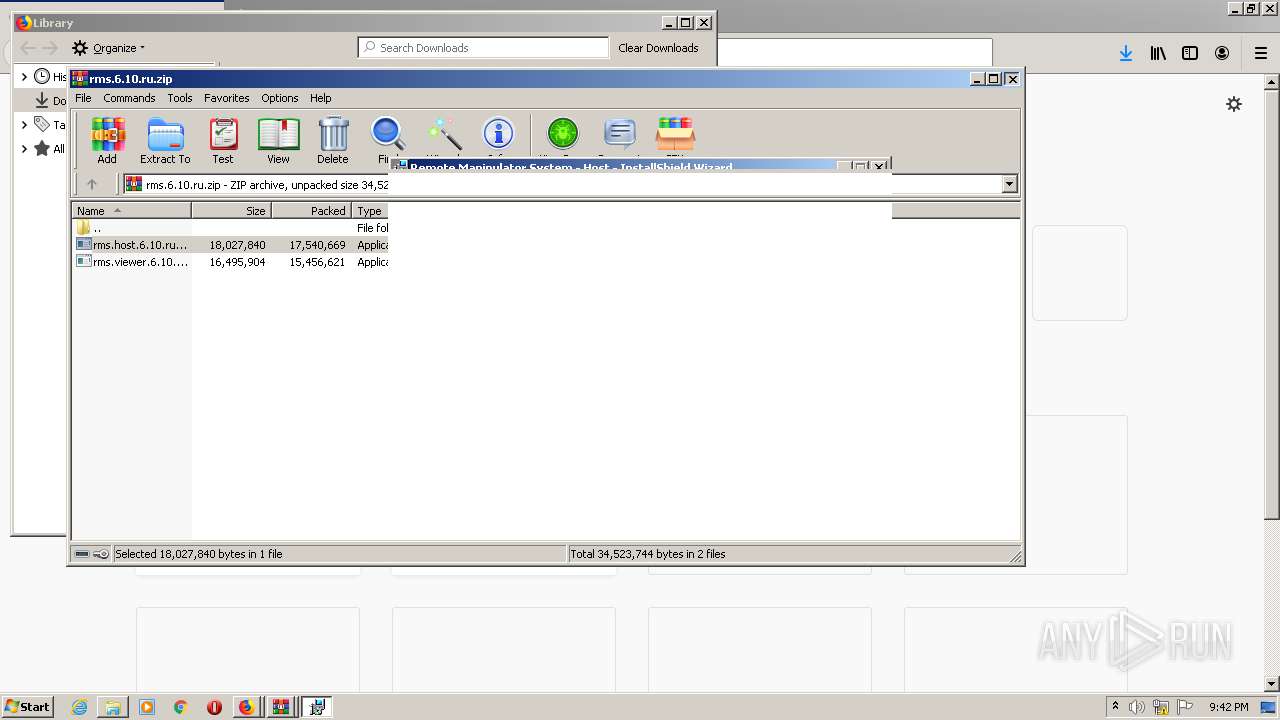
| 1396 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Downloads\rms.6.10.ru.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 1412 | "C:\Program Files\Remote Manipulator System - Host\rutserv.exe" /config | C:\Program Files\Remote Manipulator System - Host\rutserv.exe | — | rfusclient.exe | |||||||||||
User: admin Company: TektonIT Integrity Level: MEDIUM Description: RMS Exit code: 3221226540 Version: 6.10.10.0 Modules
| |||||||||||||||
| 1504 | "C:\Program Files\Remote Manipulator System - Host\rutserv.exe" /config | C:\Program Files\Remote Manipulator System - Host\rutserv.exe | rfusclient.exe | ||||||||||||
User: admin Company: TektonIT Integrity Level: HIGH Description: RMS Exit code: 0 Version: 6.10.10.0 Modules
| |||||||||||||||
Total events
4 264
Read events
4 063
Write events
196
Delete events
5
Modification events
| (PID) Process: | (2748) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Launcher |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Launcher |
Value: 2159C12600000000 | |||
| (PID) Process: | (3932) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Launcher |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Browser |
Value: 3059C12600000000 | |||
| (PID) Process: | (3932) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Launcher |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Telemetry |
Value: 1 | |||
| (PID) Process: | (3932) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3932) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A3000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3112) pingsender.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3112) pingsender.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3112) pingsender.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3112) pingsender.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3112) pingsender.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A5000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
Executable files
0
Suspicious files
75
Text files
81
Unknown types
72
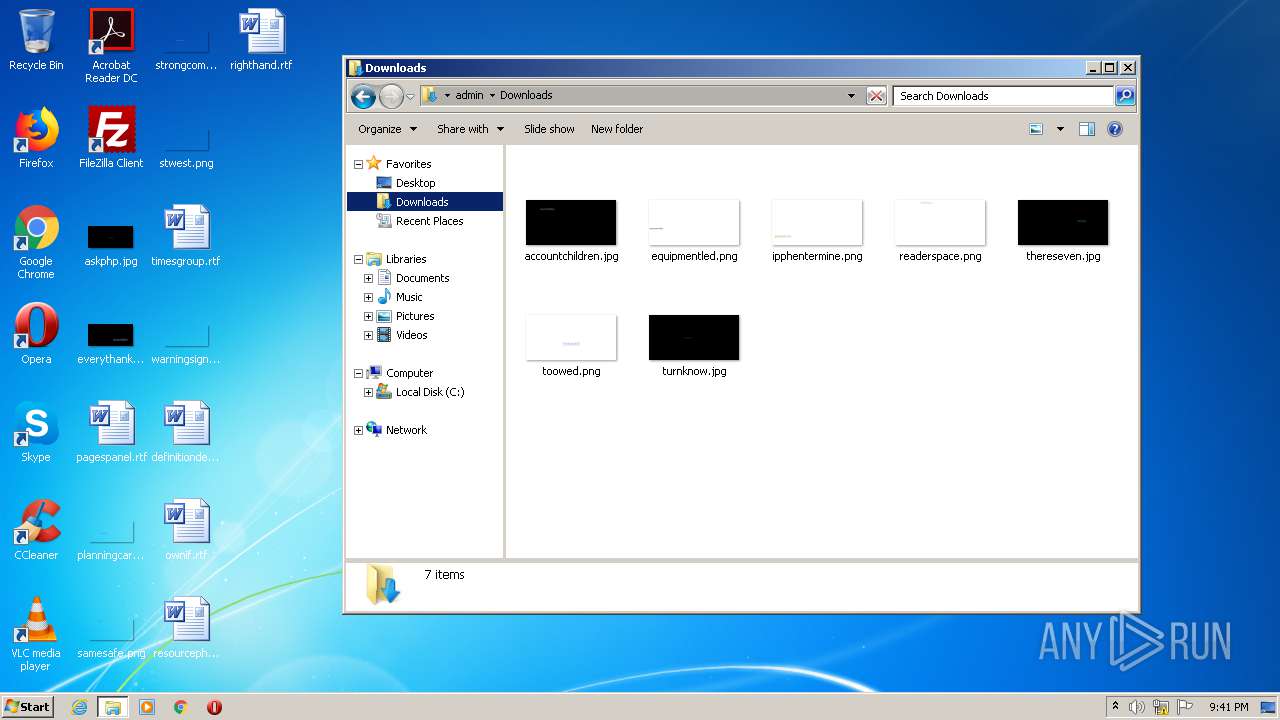
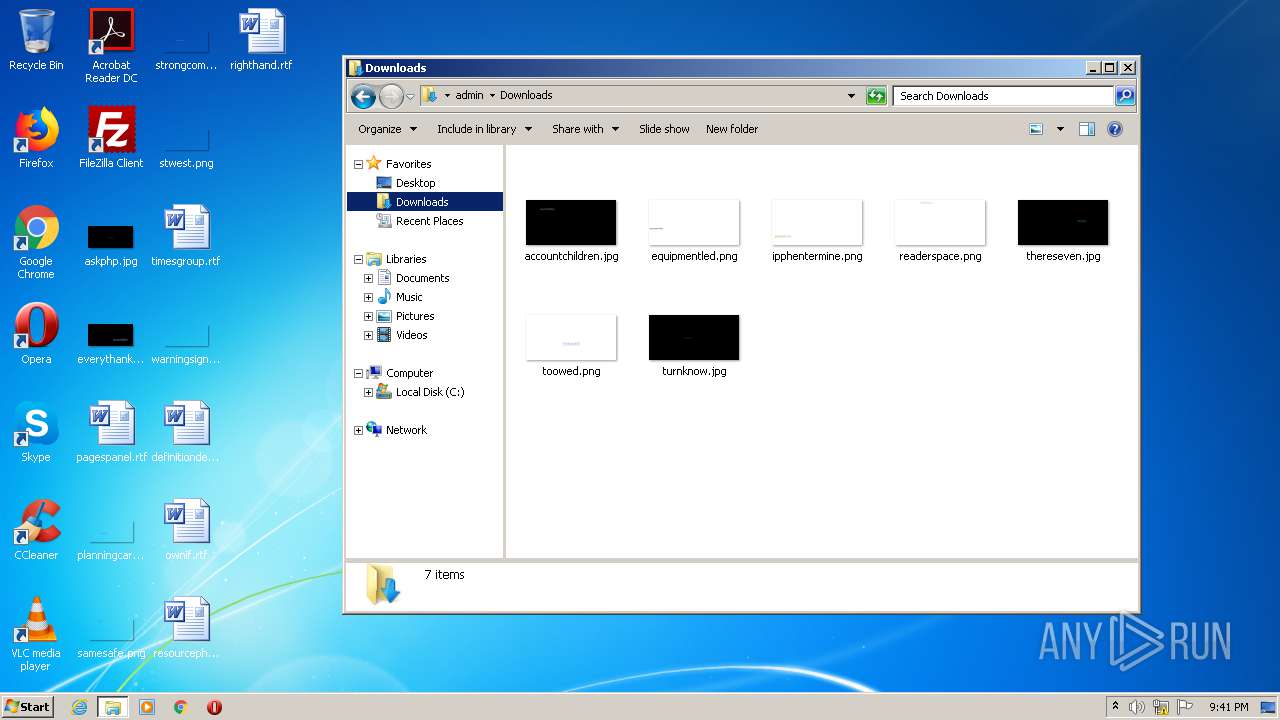
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3932 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\startupCache\scriptCache-current.bin | — | |
MD5:— | SHA256:— | |||
| 3932 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\cookies.sqlite-shm | — | |
MD5:— | SHA256:— | |||
| 3932 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\prefs-1.js | — | |
MD5:— | SHA256:— | |||
| 3932 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\sessionCheckpoints.json.tmp | — | |
MD5:— | SHA256:— | |||
| 3932 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\storage\permanent\chrome\idb\3870112724rsegmnoittet-es.sqlite-shm | — | |
MD5:— | SHA256:— | |||
| 3932 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\search.json.mozlz4.tmp | — | |
MD5:— | SHA256:— | |||
| 3932 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\startupCache\scriptCache-child-current.bin | binary | |
MD5:— | SHA256:— | |||
| 3932 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\startupCache\urlCache-current.bin | binary | |
MD5:— | SHA256:— | |||
| 3932 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\prefs.js | text | |
MD5:— | SHA256:— | |||
| 3932 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\search.json.mozlz4 | jsonlz4 | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
14
TCP/UDP connections
50
DNS requests
91
Threats
13
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3932 | firefox.exe | POST | — | 172.217.23.131:80 | http://ocsp.pki.goog/gts1o1core | US | — | — | whitelisted |
3932 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://status.rapidssl.com/ | US | der | 471 b | shared |
3932 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://status.rapidssl.com/ | US | der | 471 b | shared |
3932 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
672 | pingsender.exe | GET | 200 | 93.184.220.29:80 | http://crl3.digicert.com/DigiCertGlobalRootCA.crl | US | der | 631 b | whitelisted |
3860 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://status.rapidssl.com/ | US | der | 471 b | shared |
3860 | firefox.exe | POST | 200 | 172.217.23.131:80 | http://ocsp.pki.goog/gts1o1core | US | der | 472 b | whitelisted |
2952 | pingsender.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAH9o%2BtuynXIiEOLckvPvJE%3D | US | der | 471 b | whitelisted |
2952 | pingsender.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQQX6Z6gAidtSefNc6DC0OInqPHDQQUD4BhHIIxYdUvKOeNRji0LOHG2eICEAzmtf2PsbB81NVMrv5Nv1c%3D | US | der | 471 b | whitelisted |
1056 | svchost.exe | GET | 200 | 2.16.186.74:80 | http://crl.microsoft.com/pki/crl/products/microsoftrootcert.crl | unknown | der | 781 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3932 | firefox.exe | 93.184.220.29:80 | status.rapidssl.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3932 | firefox.exe | 35.161.199.137:443 | search.services.mozilla.com | Amazon.com, Inc. | US | unknown |
3932 | firefox.exe | 2.16.177.18:80 | detectportal.firefox.com | Akamai International B.V. | — | unknown |
3932 | firefox.exe | 52.42.128.170:443 | push.services.mozilla.com | Amazon.com, Inc. | US | unknown |
3932 | firefox.exe | 143.204.201.119:443 | snippets.cdn.mozilla.net | — | US | suspicious |
3932 | firefox.exe | 172.217.23.170:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
— | — | 143.204.201.119:443 | snippets.cdn.mozilla.net | — | US | suspicious |
3932 | firefox.exe | 2.16.177.99:443 | shavar.services.mozilla.com | Akamai International B.V. | — | unknown |
3932 | firefox.exe | 143.204.201.2:443 | tracking-protection.cdn.mozilla.net | — | US | unknown |
3932 | firefox.exe | 172.217.18.174:443 | www.youtube.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
detectportal.firefox.com |
| whitelisted |
23031.selcdn.ru |
| suspicious |
selcdn.ru |
| whitelisted |
a1089.dscd.akamai.net |
| whitelisted |
search.services.mozilla.com |
| whitelisted |
search.r53-2.services.mozilla.com |
| whitelisted |
status.rapidssl.com |
| shared |
cs9.wac.phicdn.net |
| whitelisted |
push.services.mozilla.com |
| whitelisted |
autopush.prod.mozaws.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1056 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .cloud TLD |
1056 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .cloud TLD |
1056 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .cloud TLD |
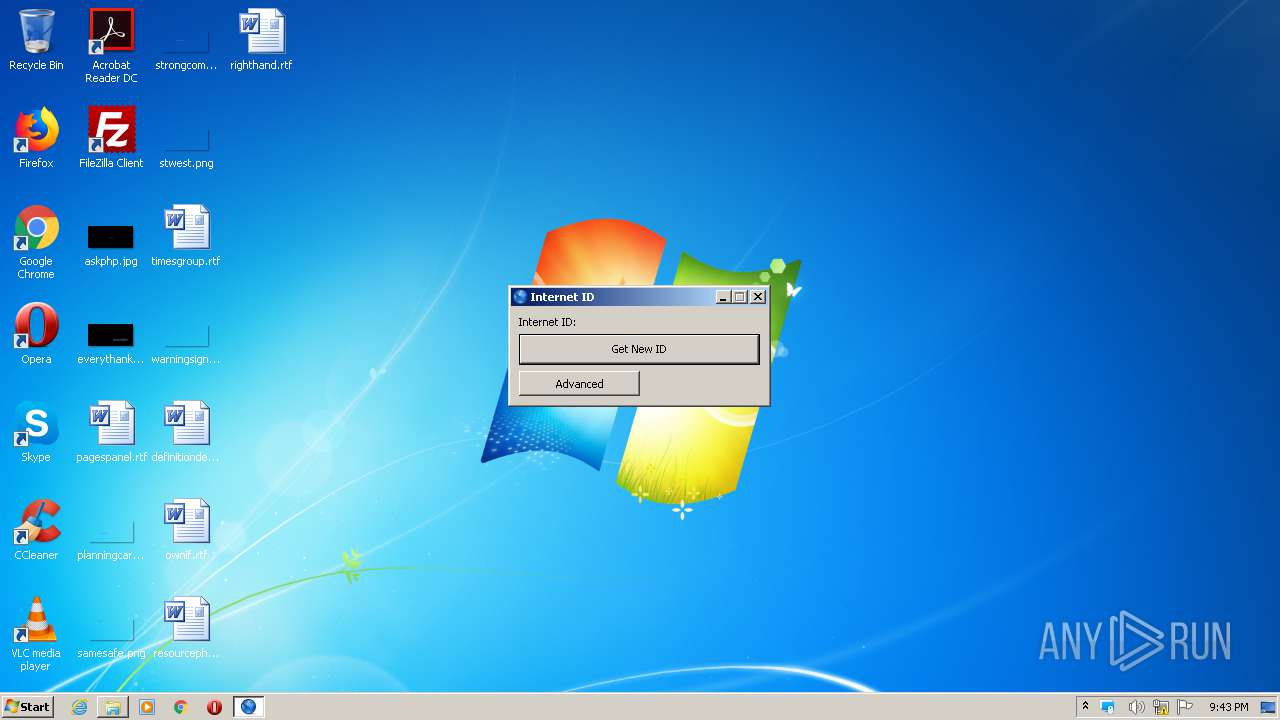
3024 | rutserv.exe | Potential Corporate Privacy Violation | REMOTE [PTsecurity] RMS.Remote Utilities Access Tool |
3024 | rutserv.exe | Potential Corporate Privacy Violation | REMOTE [PTsecurity] RMS.Remote Utilities Access Tool |
3024 | rutserv.exe | Misc activity | REMOTE [PTsecurity] RMS Remote Access Tool (1c-connect) |
3024 | rutserv.exe | Potential Corporate Privacy Violation | REMOTE [PTsecurity] RMS.Remote Utilities Access Tool |
3024 | rutserv.exe | Potential Corporate Privacy Violation | REMOTE [PTsecurity] RMS.Remote Utilities Access Tool |
3024 | rutserv.exe | Misc activity | REMOTE [PTsecurity] RMS Remote Access Tool (1c-connect) |
3024 | rutserv.exe | Potential Corporate Privacy Violation | REMOTE [PTsecurity] RMS.Remote Utilities Access Tool |
2 ETPRO signatures available at the full report
Process | Message |
|---|---|
rutserv.exe | 31-08-2020_21:43:00:955#T:Error NTSetPrivilege - SE_DEBUG_NAME |
rutserv.exe | TMainService.Start |