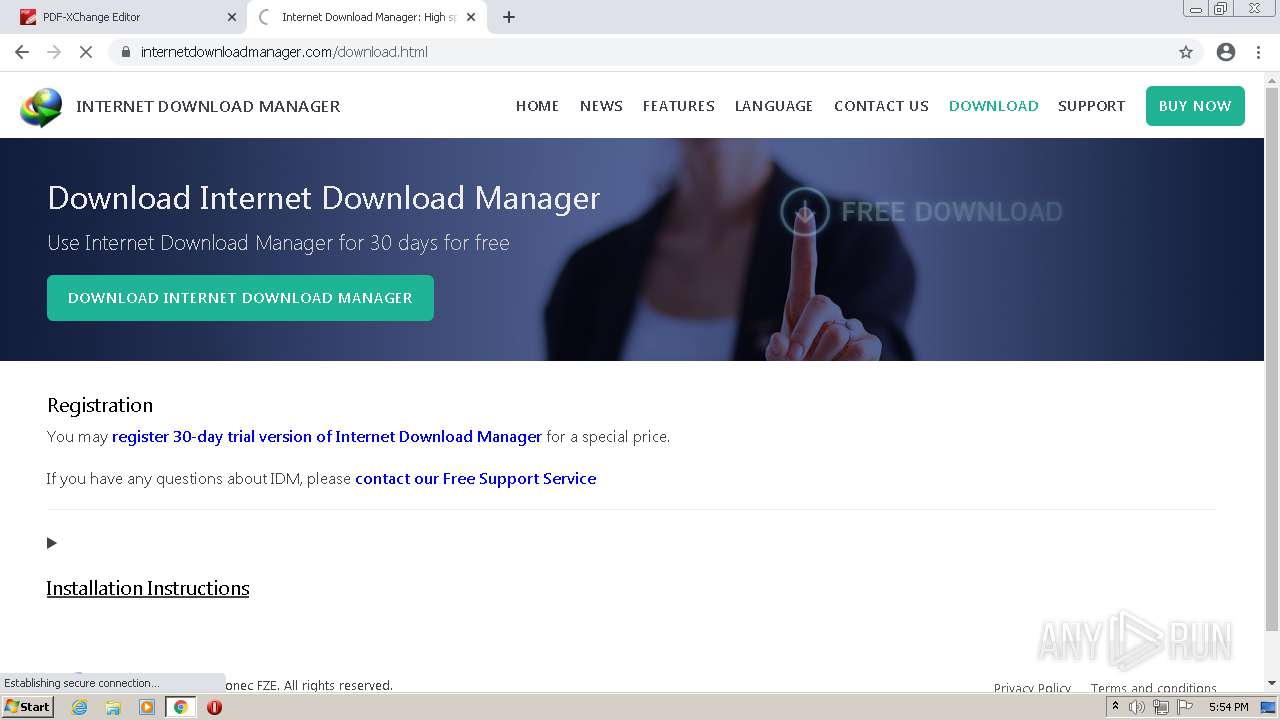
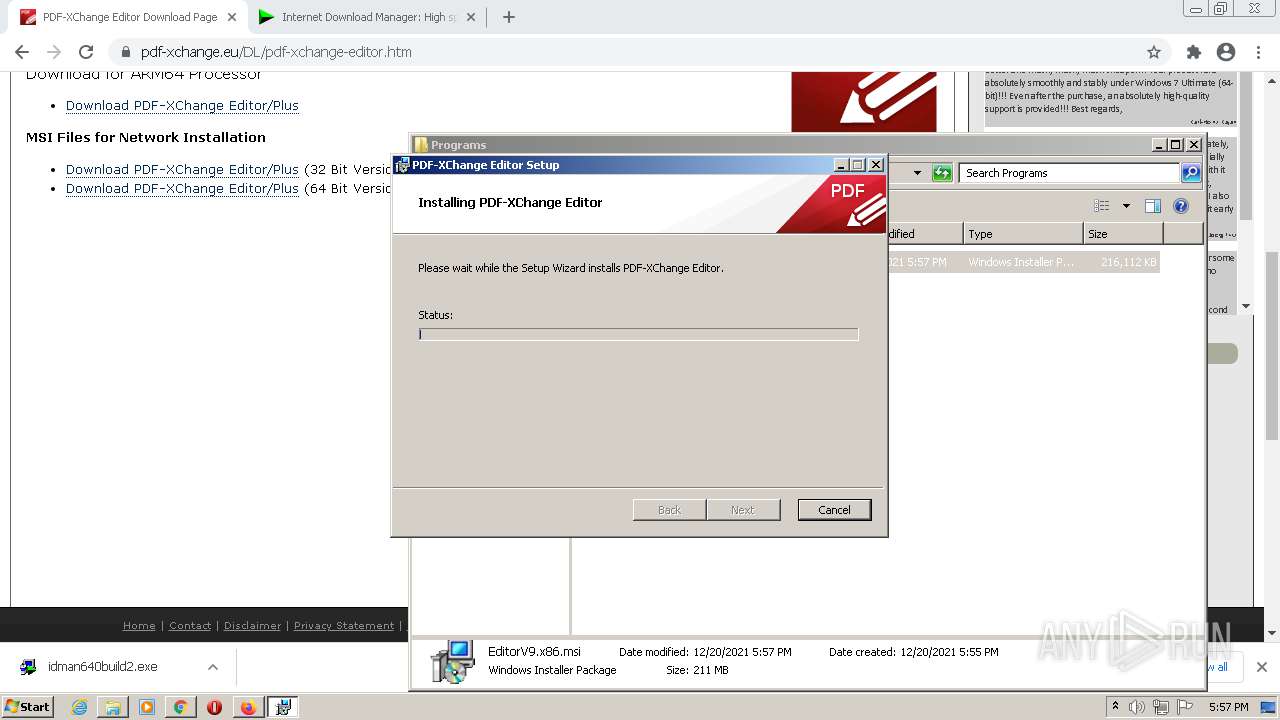
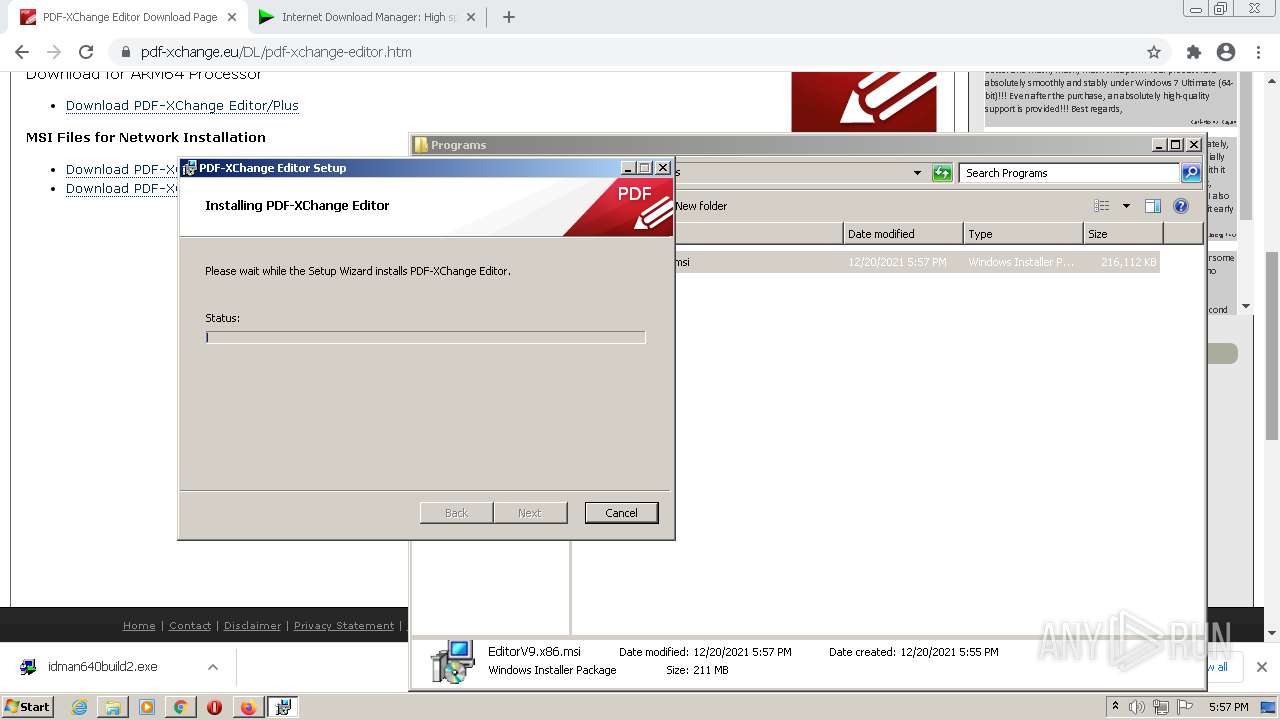
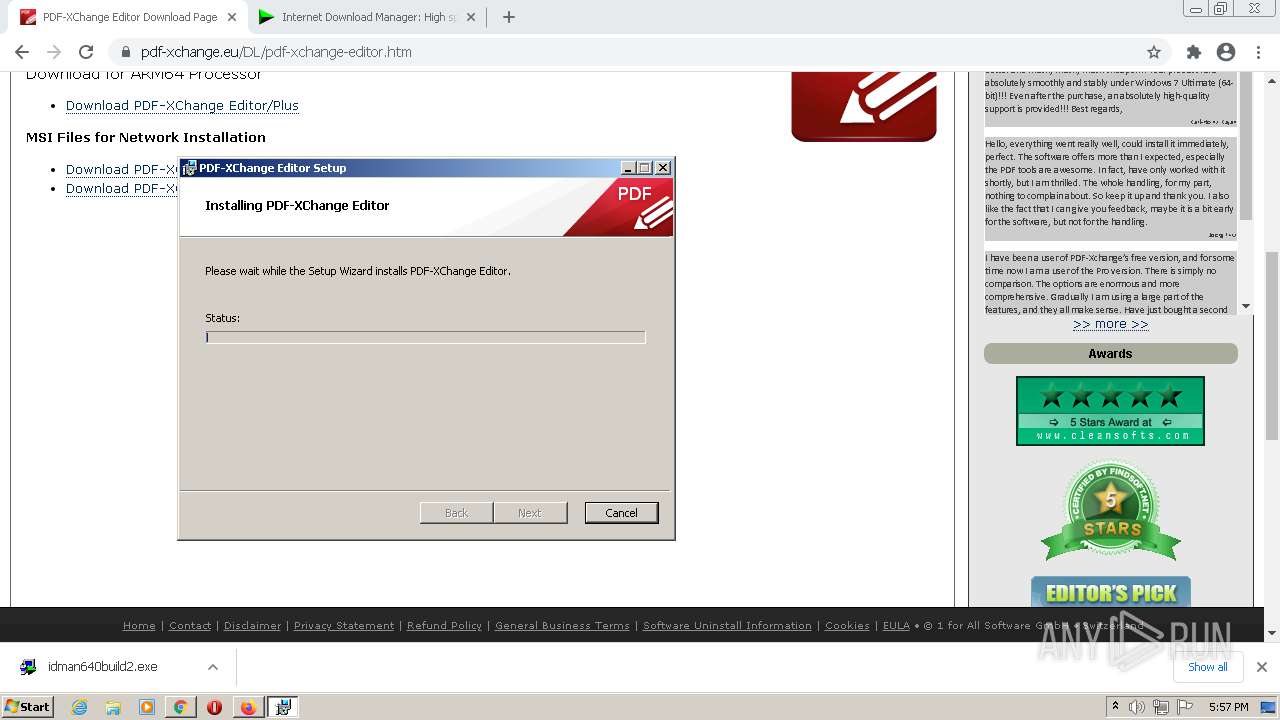
| URL: | https://pdf-xchange.eu/pdf-xchange-editor/ |
| Full analysis: | https://app.any.run/tasks/455c6171-8931-4427-9cad-7f1795aed81f |
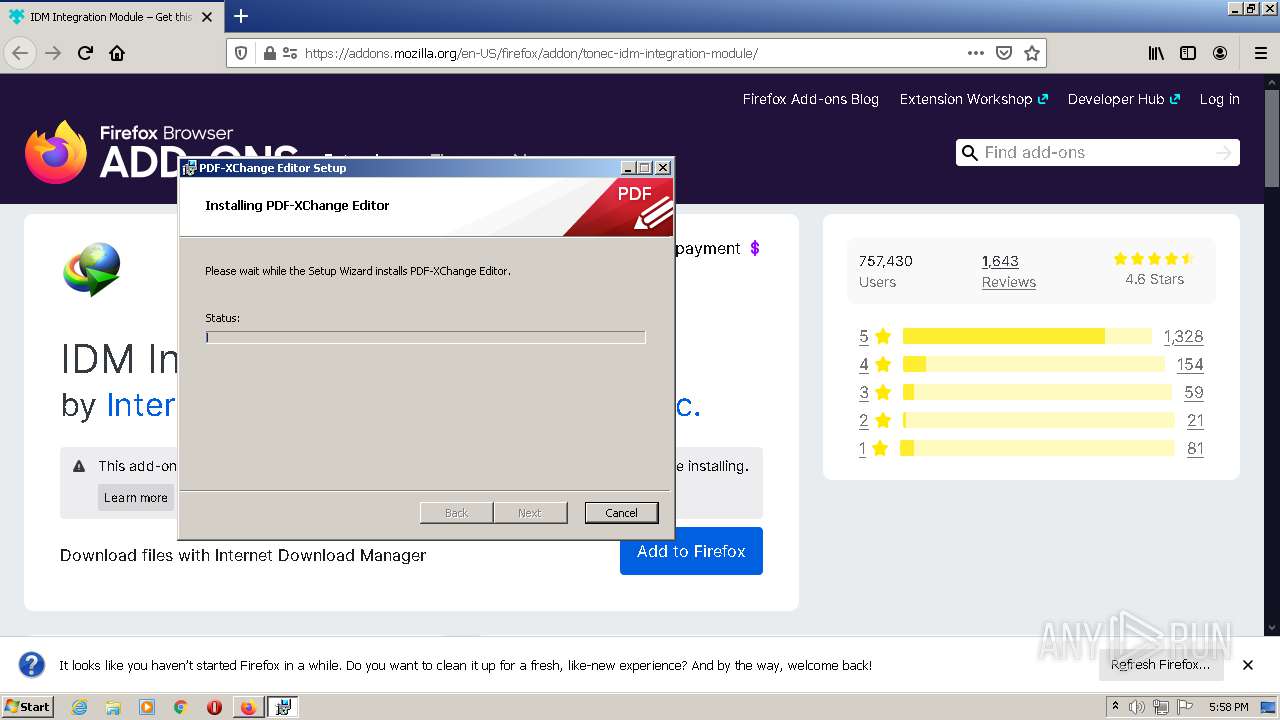
| Verdict: | Malicious activity |
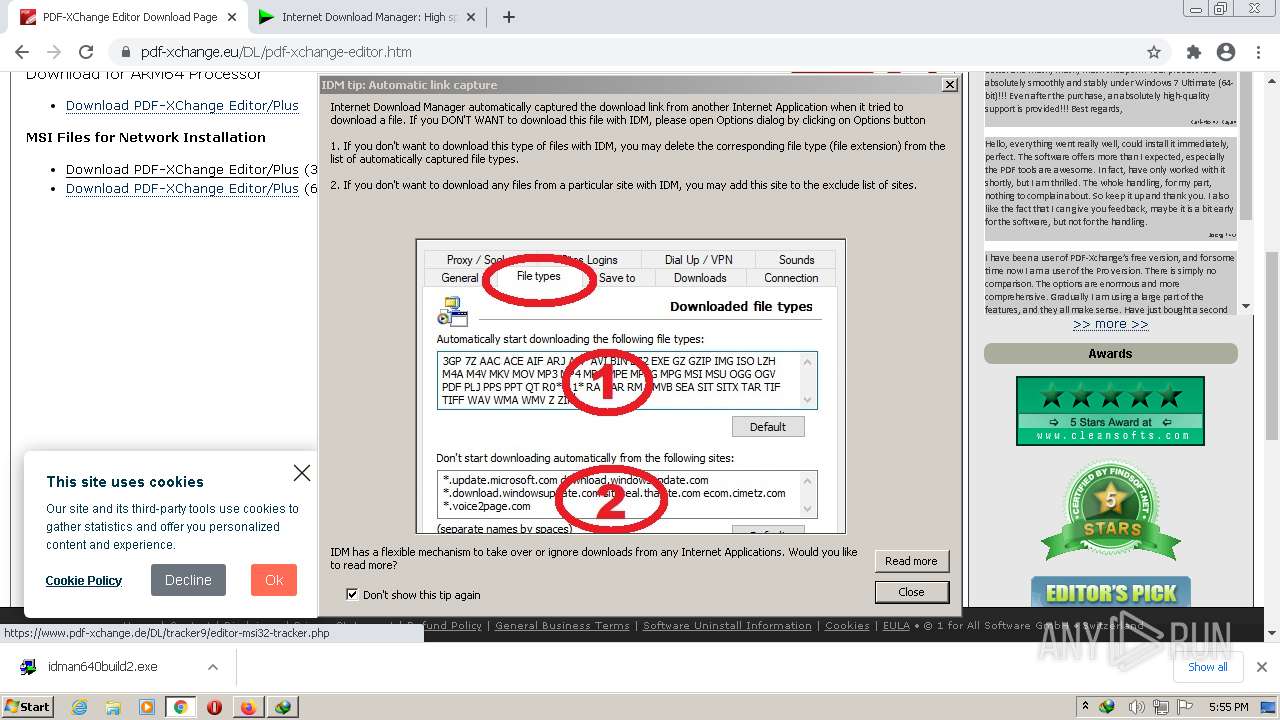
| Threats: | Remote access trojans (RATs) are a type of malware that enables attackers to establish complete to partial control over infected computers. Such malicious programs often have a modular design, offering a wide range of functionalities for conducting illicit activities on compromised systems. Some of the most common features of RATs include access to the users’ data, webcam, and keystrokes. This malware is often distributed through phishing emails and links. |
| Analysis date: | December 20, 2021, 17:53:40 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 4442F96DE9C93EA7D56A8C5ADDFF4587 |
| SHA1: | F086E51D866F1836136B3267EBA3074E83608F33 |
| SHA256: | 76587F358A50382466F82B954F606C7D2B341FF94C6F13FB6EE392066888230A |
| SSDEEP: | 3:N8FEzDpOCdzD962Kn:2qFOWE2Kn |
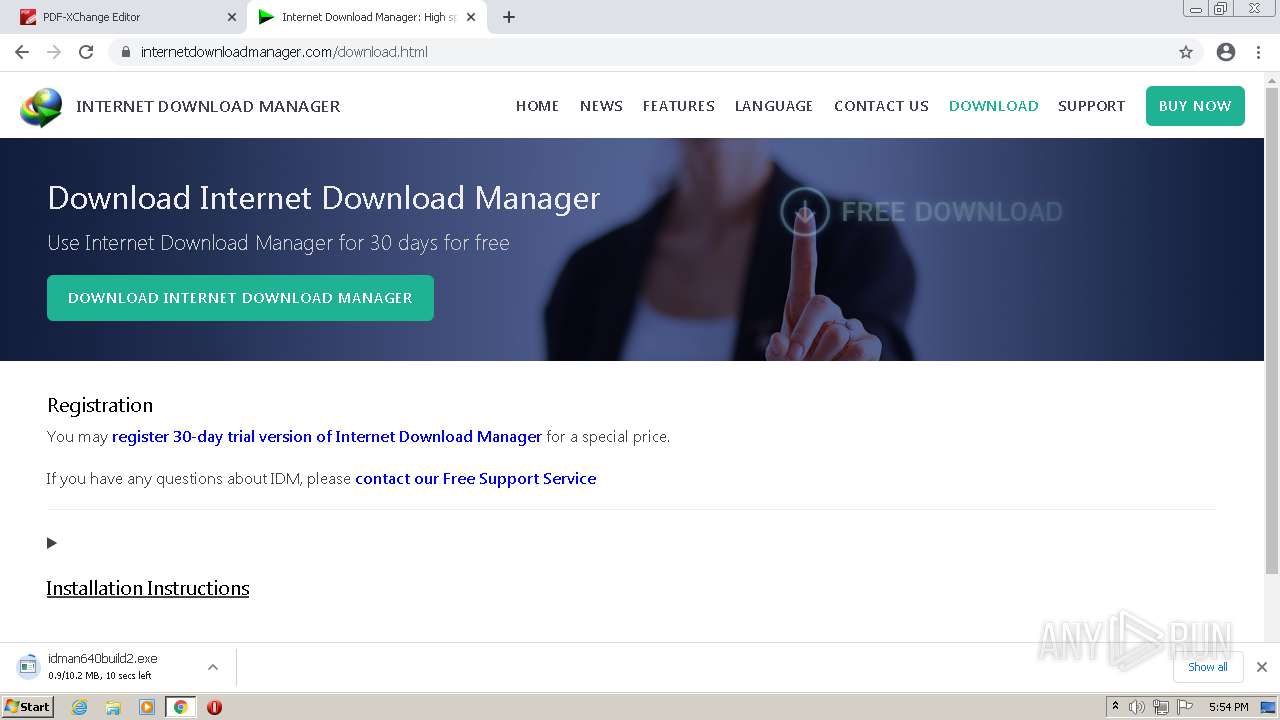
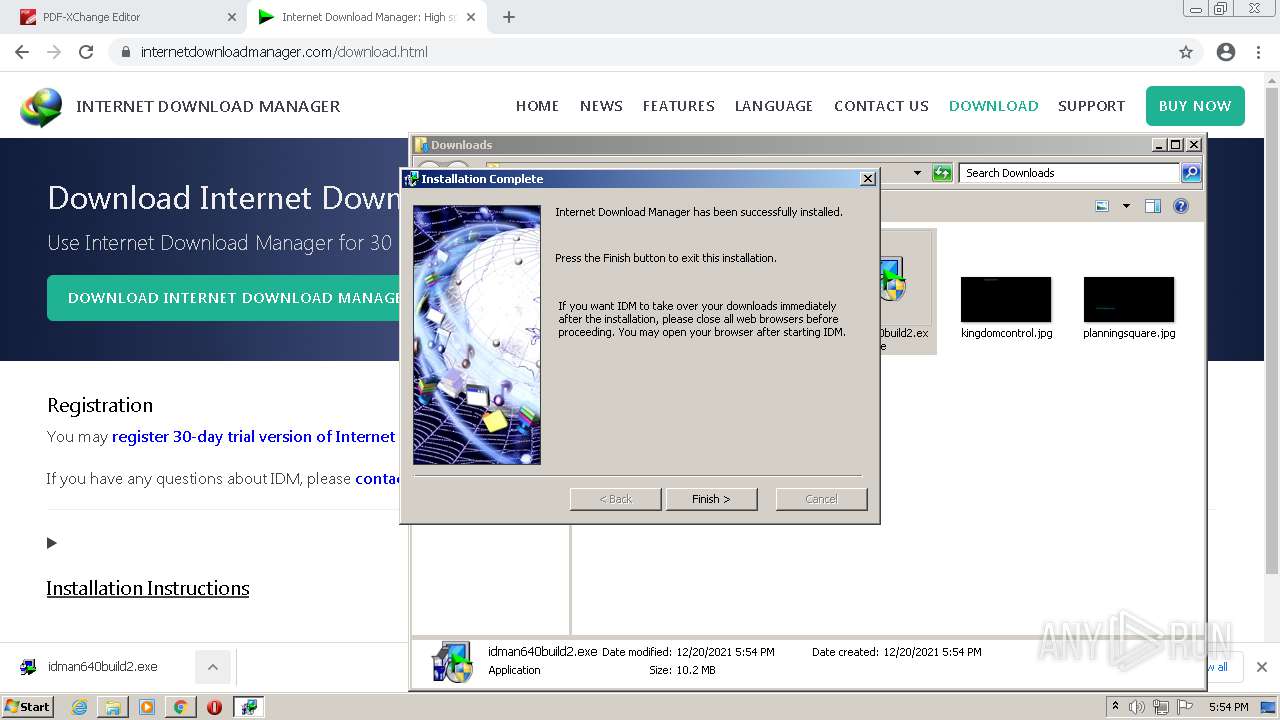
MALICIOUS
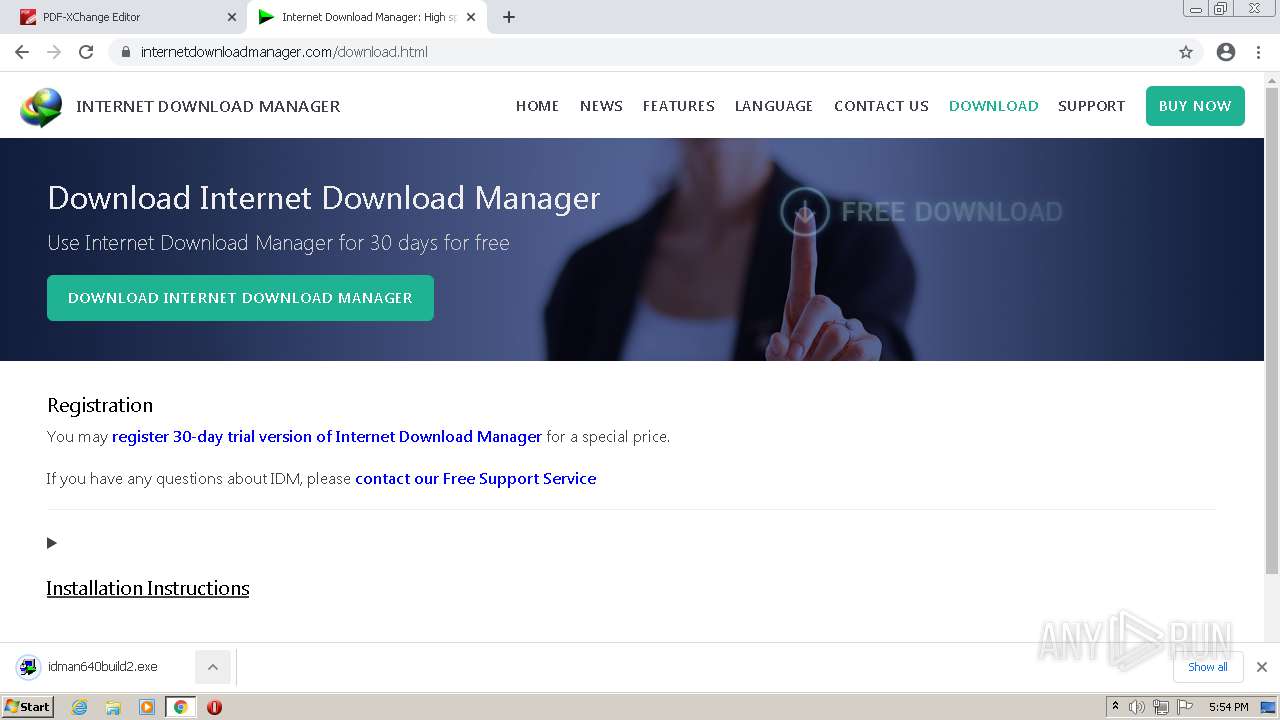
Application was dropped or rewritten from another process
- idman640build2.exe (PID: 2064)
- idman640build2.exe (PID: 3348)
Drops executable file immediately after starts
- rundll32.exe (PID: 2820)
- chrome.exe (PID: 2236)
Changes the autorun value in the registry
- rundll32.exe (PID: 2820)
- IDMan.exe (PID: 1252)
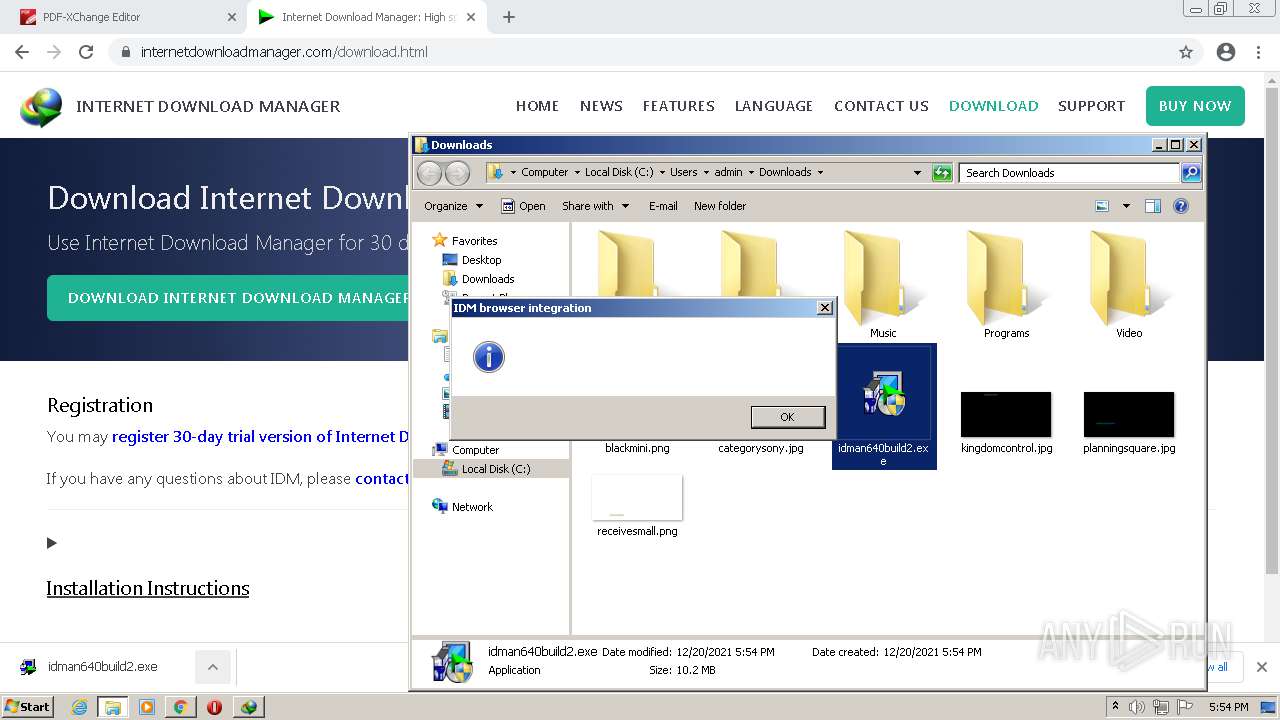
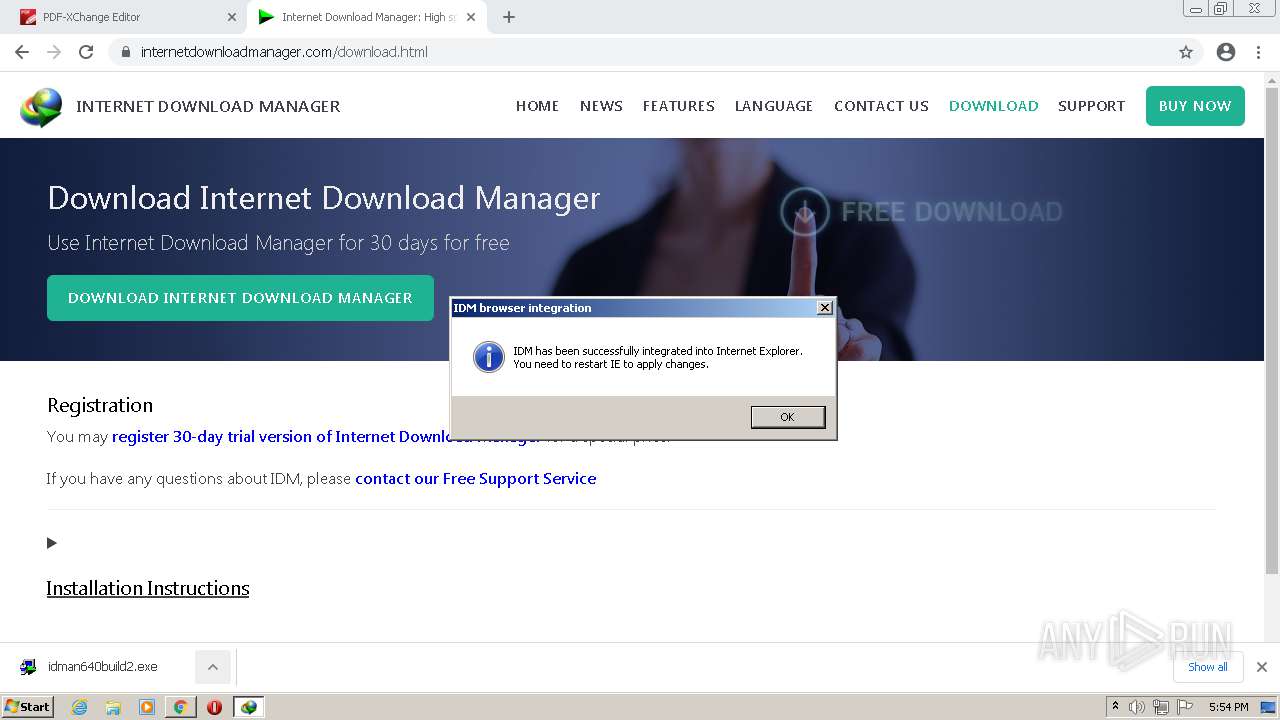
REMCOS was detected
- IDMan.exe (PID: 1252)
Starts NET.EXE for service management
- Uninstall.exe (PID: 1988)
Loads dropped or rewritten executable
- MsiExec.exe (PID: 1400)
- MsiExec.exe (PID: 3716)
SUSPICIOUS
Executable content was dropped or overwritten
- chrome.exe (PID: 3752)
- IDMan.exe (PID: 1252)
- rundll32.exe (PID: 2820)
- firefox.exe (PID: 2512)
- chrome.exe (PID: 2236)
- msiexec.exe (PID: 3204)
- msiexec.exe (PID: 3504)
Drops a file with a compile date too recent
- chrome.exe (PID: 3752)
- msiexec.exe (PID: 3204)
- msiexec.exe (PID: 3504)
Checks supported languages
- idman640build2.exe (PID: 3348)
- IDM1.tmp (PID: 836)
- idmBroker.exe (PID: 3268)
- IDMan.exe (PID: 1252)
- Uninstall.exe (PID: 1988)
- MediumILStart.exe (PID: 3540)
- IDMan.exe (PID: 1292)
- IEMonitor.exe (PID: 3312)
Starts application with an unusual extension
- idman640build2.exe (PID: 3348)
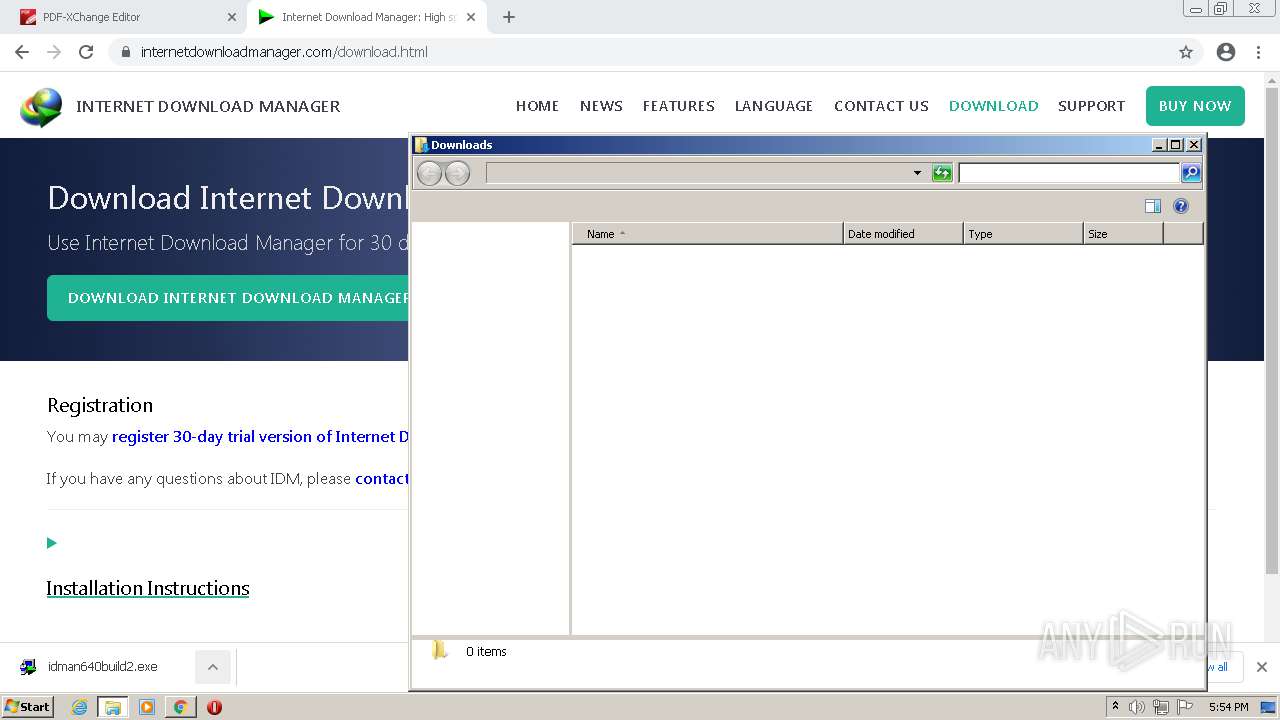
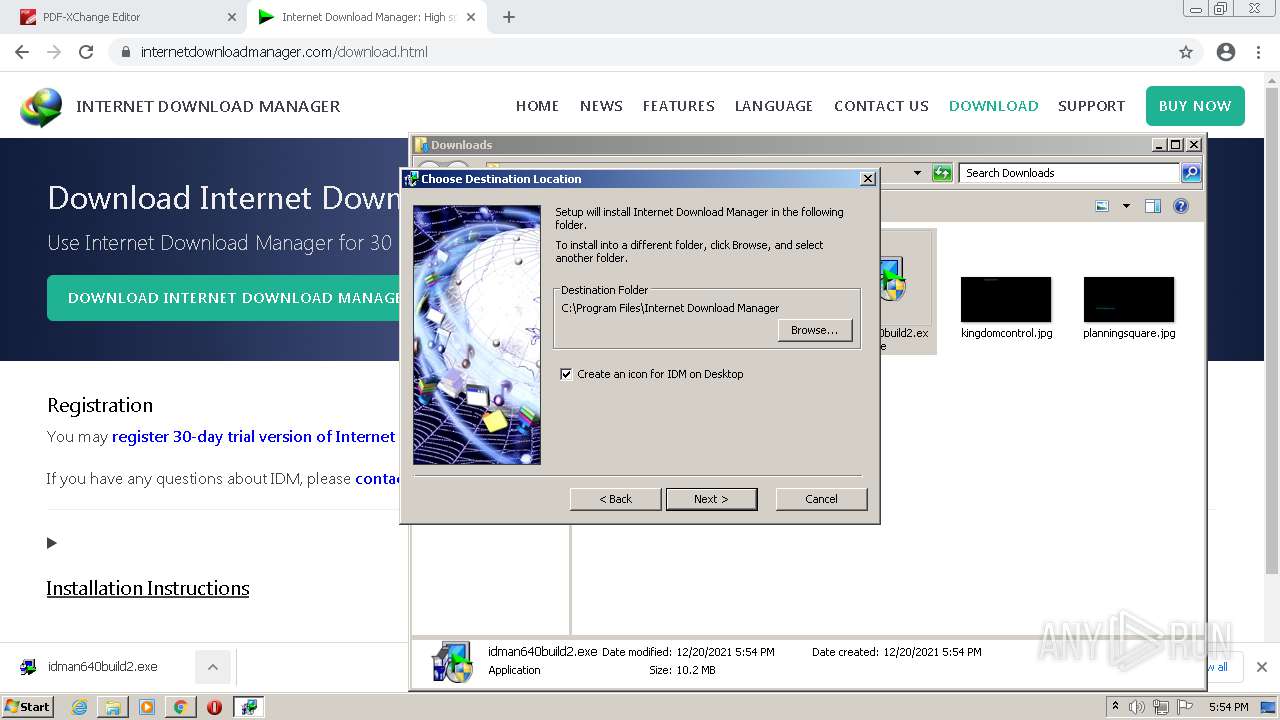
Creates a directory in Program Files
- IDM1.tmp (PID: 836)
- msiexec.exe (PID: 3504)
Creates a software uninstall entry
- IDM1.tmp (PID: 836)
Creates files in the user directory
- IDM1.tmp (PID: 836)
- IDMan.exe (PID: 1252)
- IDMan.exe (PID: 1292)
Reads the computer name
- IDM1.tmp (PID: 836)
- IDMan.exe (PID: 1252)
- Uninstall.exe (PID: 1988)
- MediumILStart.exe (PID: 3540)
- IDMan.exe (PID: 1292)
- IEMonitor.exe (PID: 3312)
Creates/Modifies COM task schedule object
- IDM1.tmp (PID: 836)
- IDMan.exe (PID: 1252)
- Uninstall.exe (PID: 1988)
Drops a file that was compiled in debug mode
- IDMan.exe (PID: 1252)
- rundll32.exe (PID: 2820)
- firefox.exe (PID: 2512)
- chrome.exe (PID: 2236)
- msiexec.exe (PID: 3204)
- msiexec.exe (PID: 3504)
Creates files in the program directory
- IDMan.exe (PID: 1252)
- IDM1.tmp (PID: 836)
- msiexec.exe (PID: 3504)
Uses RUNDLL32.EXE to load library
- Uninstall.exe (PID: 1988)
Creates files in the Windows directory
- rundll32.exe (PID: 2820)
Creates files in the driver directory
- rundll32.exe (PID: 2820)
Removes files from Windows directory
- rundll32.exe (PID: 2820)
Creates or modifies windows services
- Uninstall.exe (PID: 1988)
Reads the time zone
- runonce.exe (PID: 764)
Executed via COM
- IDMan.exe (PID: 1292)
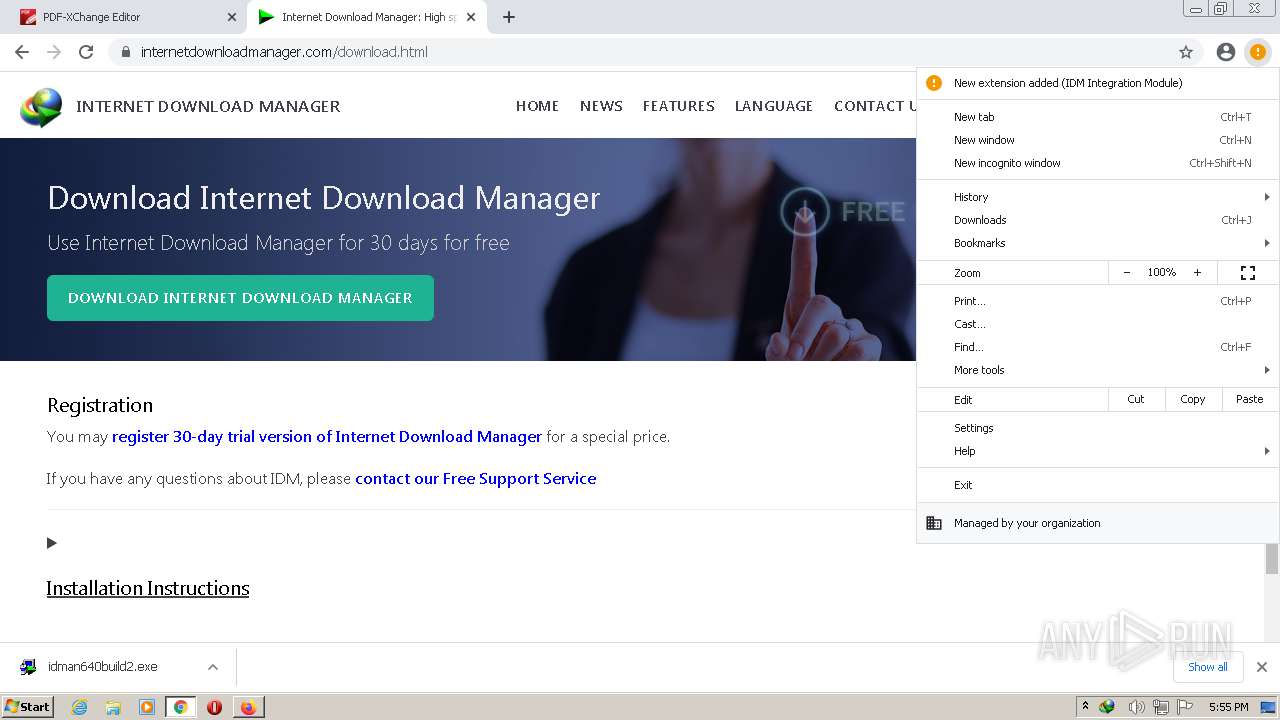
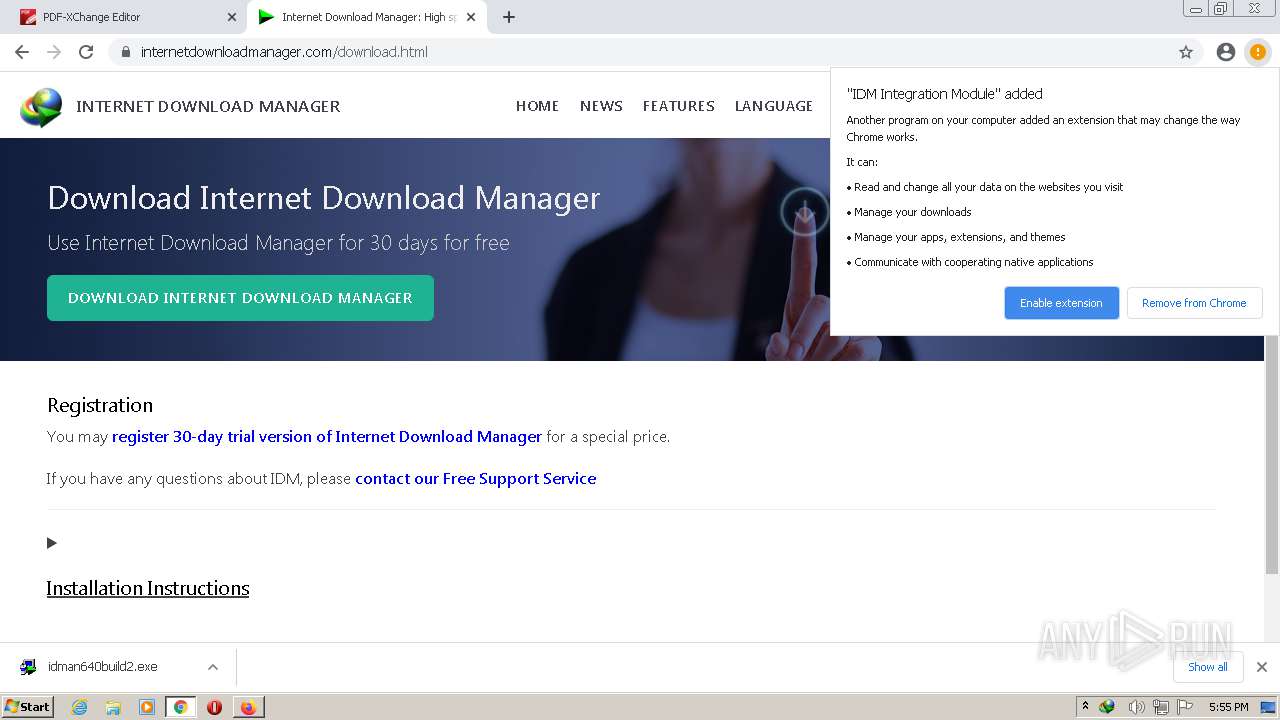
Modifies files in Chrome extension folder
- chrome.exe (PID: 3752)
Executed as Windows Service
- msiexec.exe (PID: 3504)
- vssvc.exe (PID: 396)
Reads Windows owner or organization settings
- msiexec.exe (PID: 3204)
- msiexec.exe (PID: 3504)
Reads Environment values
- vssvc.exe (PID: 396)
Reads the Windows organization settings
- msiexec.exe (PID: 3504)
- msiexec.exe (PID: 3204)
Application launched itself
- msiexec.exe (PID: 3504)
Searches for installed software
- msiexec.exe (PID: 3504)
INFO
Checks supported languages
- chrome.exe (PID: 3752)
- chrome.exe (PID: 396)
- chrome.exe (PID: 1772)
- chrome.exe (PID: 2188)
- chrome.exe (PID: 3120)
- chrome.exe (PID: 2000)
- chrome.exe (PID: 3996)
- chrome.exe (PID: 3892)
- chrome.exe (PID: 1468)
- chrome.exe (PID: 2480)
- chrome.exe (PID: 3792)
- chrome.exe (PID: 520)
- chrome.exe (PID: 3016)
- chrome.exe (PID: 3156)
- chrome.exe (PID: 3968)
- chrome.exe (PID: 3524)
- chrome.exe (PID: 2604)
- chrome.exe (PID: 4084)
- chrome.exe (PID: 3496)
- chrome.exe (PID: 3132)
- chrome.exe (PID: 1108)
- chrome.exe (PID: 3264)
- chrome.exe (PID: 2940)
- chrome.exe (PID: 3408)
- chrome.exe (PID: 4080)
- chrome.exe (PID: 4056)
- chrome.exe (PID: 2404)
- chrome.exe (PID: 1132)
- chrome.exe (PID: 3432)
- chrome.exe (PID: 2236)
- chrome.exe (PID: 1144)
- chrome.exe (PID: 444)
- chrome.exe (PID: 2776)
- chrome.exe (PID: 4052)
- chrome.exe (PID: 2468)
- chrome.exe (PID: 3696)
- chrome.exe (PID: 2172)
- firefox.exe (PID: 3228)
- firefox.exe (PID: 2788)
- chrome.exe (PID: 2756)
- firefox.exe (PID: 2512)
- rundll32.exe (PID: 2820)
- chrome.exe (PID: 3548)
- chrome.exe (PID: 2068)
- net.exe (PID: 2444)
- chrome.exe (PID: 1148)
- net1.exe (PID: 2560)
- grpconv.exe (PID: 288)
- runonce.exe (PID: 764)
- firefox.exe (PID: 2840)
- firefox.exe (PID: 3352)
- firefox.exe (PID: 2556)
- firefox.exe (PID: 1372)
- firefox.exe (PID: 2816)
- chrome.exe (PID: 2152)
- chrome.exe (PID: 2196)
- chrome.exe (PID: 2128)
- chrome.exe (PID: 1676)
- chrome.exe (PID: 2204)
- chrome.exe (PID: 2604)
- chrome.exe (PID: 4016)
- chrome.exe (PID: 520)
- chrome.exe (PID: 2884)
- firefox.exe (PID: 2496)
- firefox.exe (PID: 3316)
- chrome.exe (PID: 2236)
- chrome.exe (PID: 3892)
- chrome.exe (PID: 3912)
- msiexec.exe (PID: 3204)
- msiexec.exe (PID: 3504)
- chrome.exe (PID: 3512)
- MsiExec.exe (PID: 1400)
- vssvc.exe (PID: 396)
- MsiExec.exe (PID: 3716)
Reads the computer name
- chrome.exe (PID: 3752)
- chrome.exe (PID: 396)
- chrome.exe (PID: 1772)
- chrome.exe (PID: 3996)
- chrome.exe (PID: 2604)
- chrome.exe (PID: 4080)
- chrome.exe (PID: 3548)
- chrome.exe (PID: 3432)
- chrome.exe (PID: 2236)
- chrome.exe (PID: 2776)
- chrome.exe (PID: 4052)
- firefox.exe (PID: 3228)
- rundll32.exe (PID: 2820)
- net1.exe (PID: 2560)
- firefox.exe (PID: 2512)
- runonce.exe (PID: 764)
- chrome.exe (PID: 2068)
- firefox.exe (PID: 2816)
- firefox.exe (PID: 2840)
- firefox.exe (PID: 2556)
- firefox.exe (PID: 3352)
- firefox.exe (PID: 1372)
- firefox.exe (PID: 2496)
- firefox.exe (PID: 3316)
- chrome.exe (PID: 2152)
- msiexec.exe (PID: 3204)
- msiexec.exe (PID: 3504)
- MsiExec.exe (PID: 1400)
- vssvc.exe (PID: 396)
- MsiExec.exe (PID: 3716)
Application launched itself
- chrome.exe (PID: 3752)
- firefox.exe (PID: 2788)
- firefox.exe (PID: 2512)
Reads the hosts file
- chrome.exe (PID: 3752)
- chrome.exe (PID: 1772)
Reads settings of System Certificates
- chrome.exe (PID: 1772)
- chrome.exe (PID: 3752)
- IDMan.exe (PID: 1252)
- IDMan.exe (PID: 1292)
- msiexec.exe (PID: 3204)
- msiexec.exe (PID: 3504)
Checks Windows Trust Settings
- chrome.exe (PID: 3752)
- IDMan.exe (PID: 1252)
- IDMan.exe (PID: 1292)
- msiexec.exe (PID: 3204)
- msiexec.exe (PID: 3504)
Reads the date of Windows installation
- chrome.exe (PID: 3432)
- firefox.exe (PID: 2512)
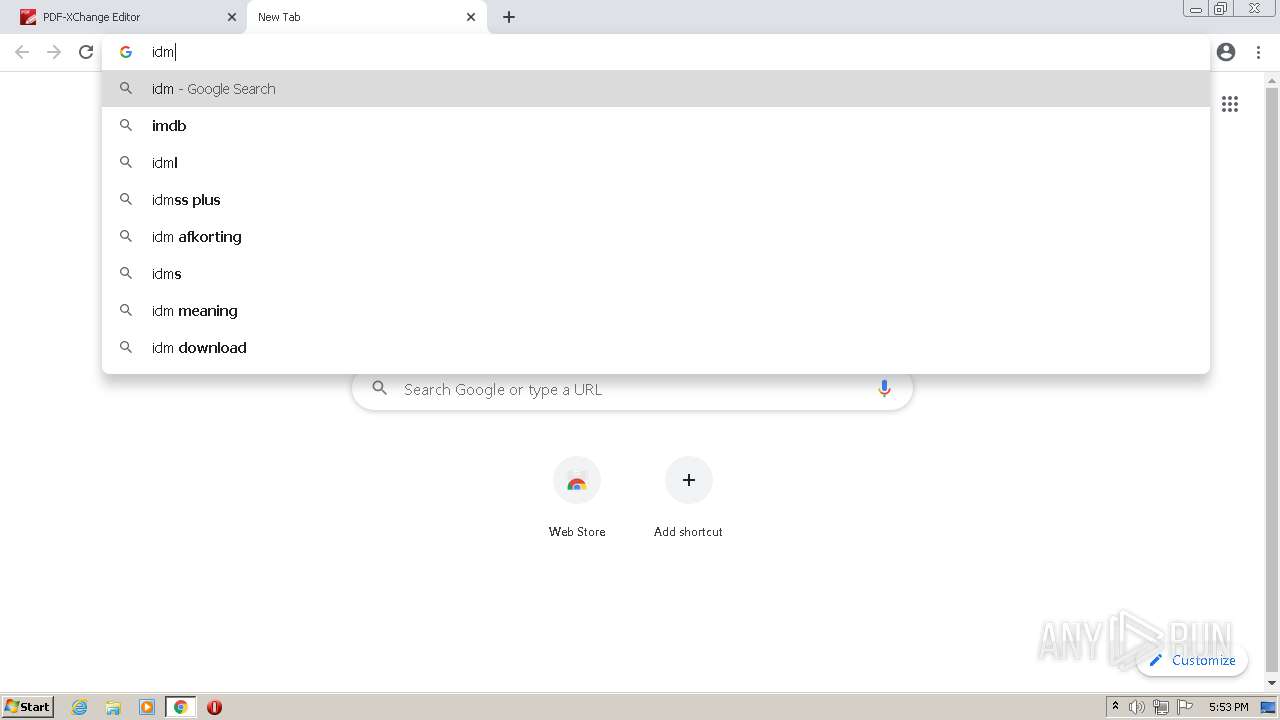
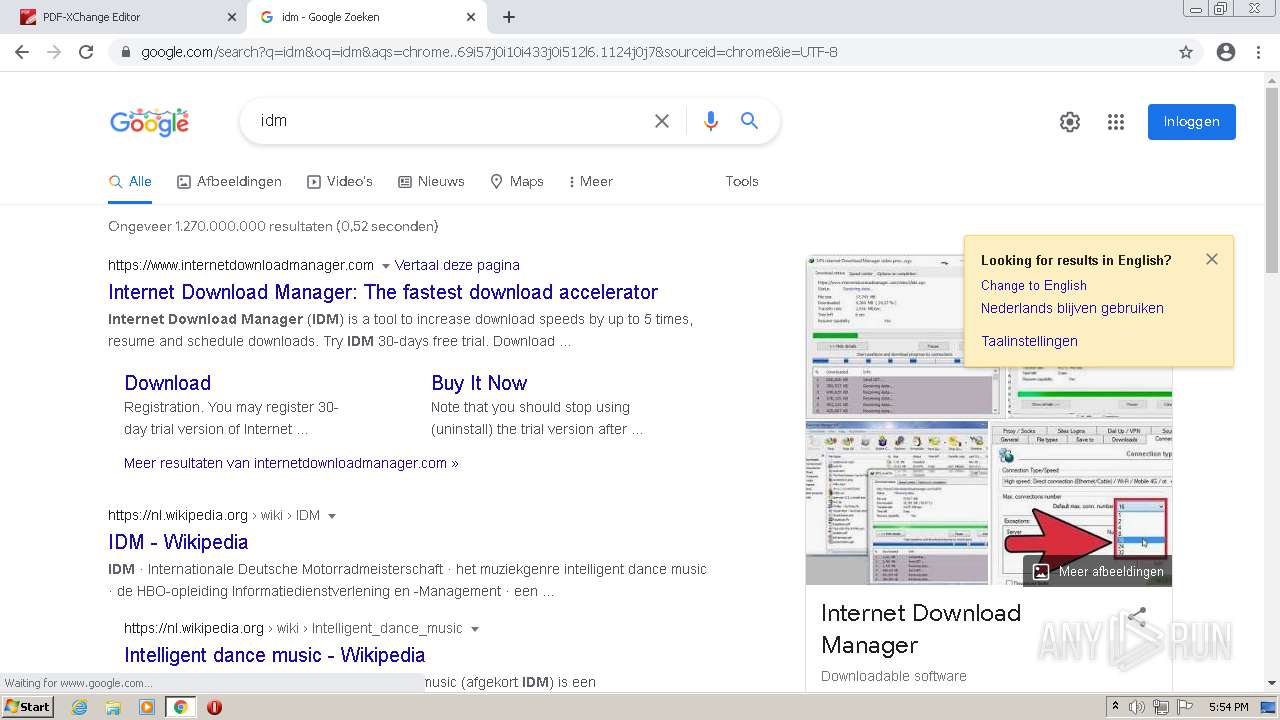
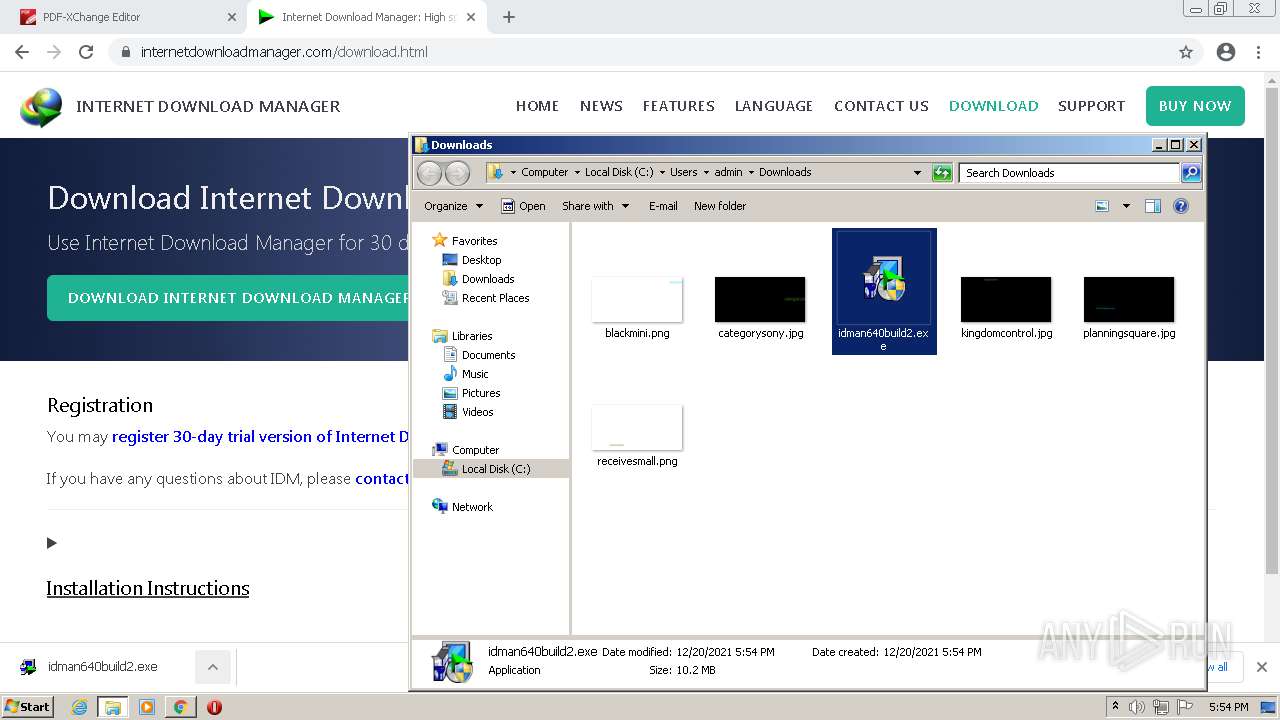
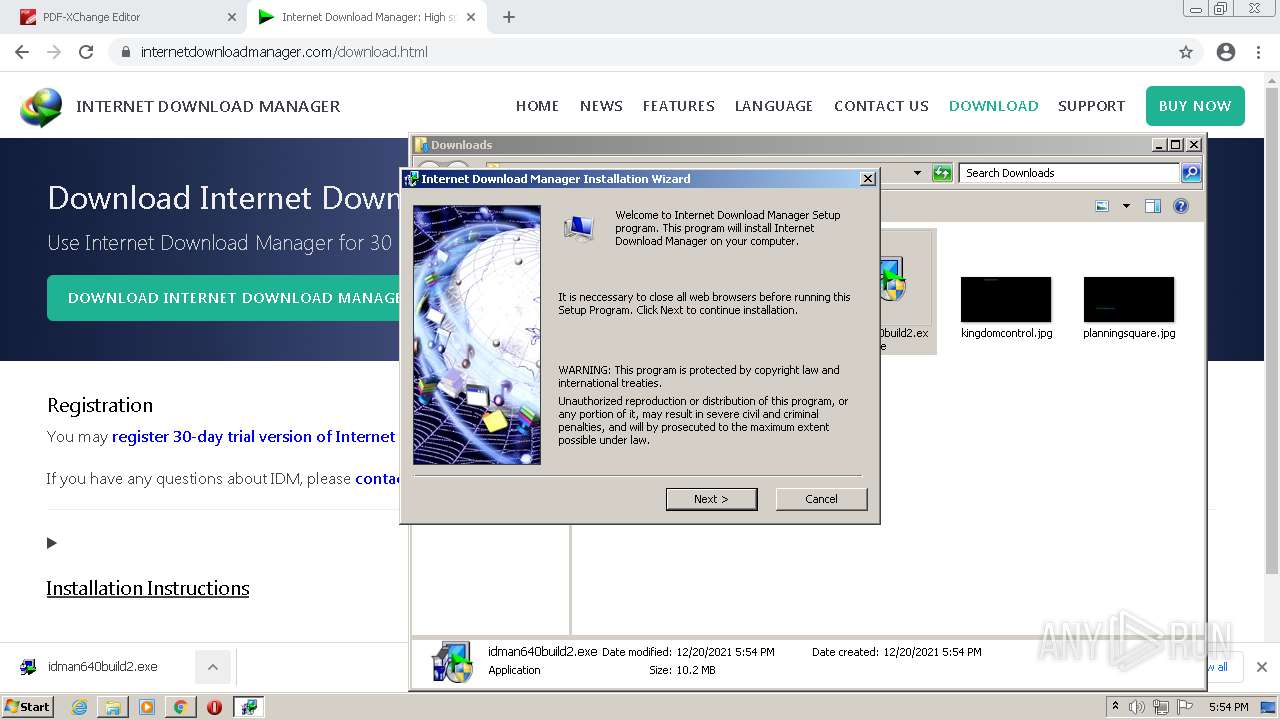
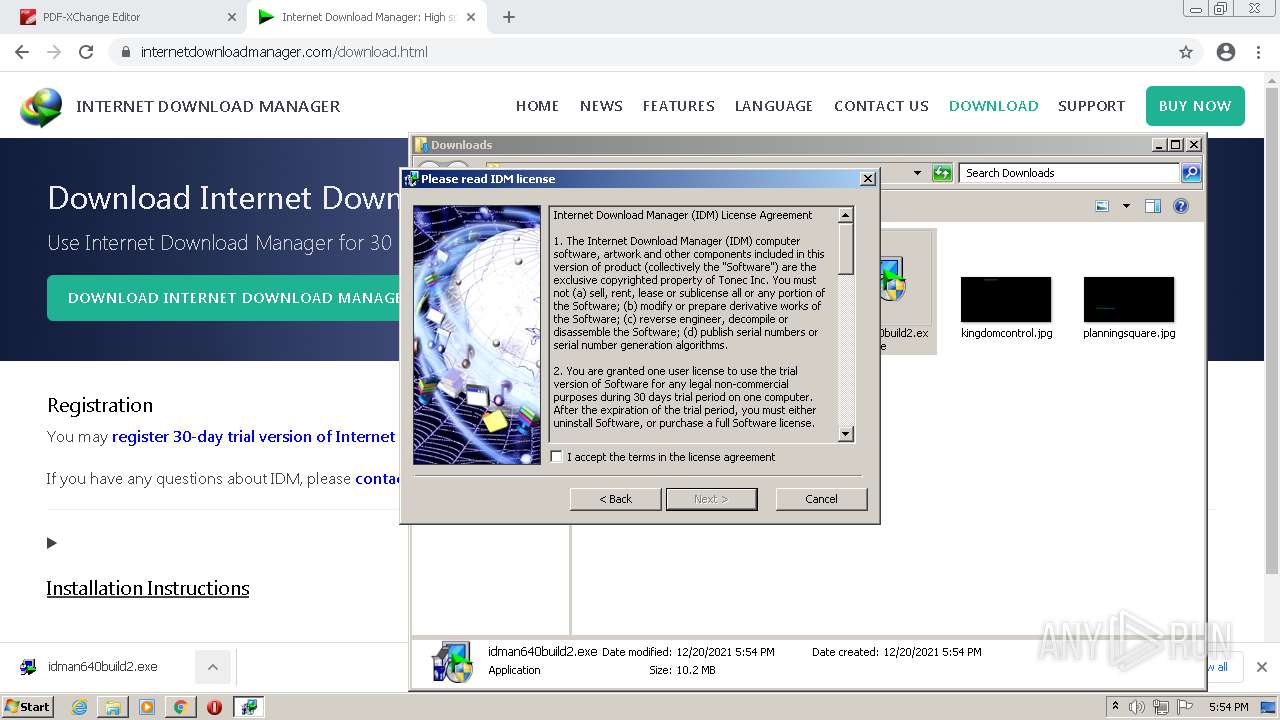
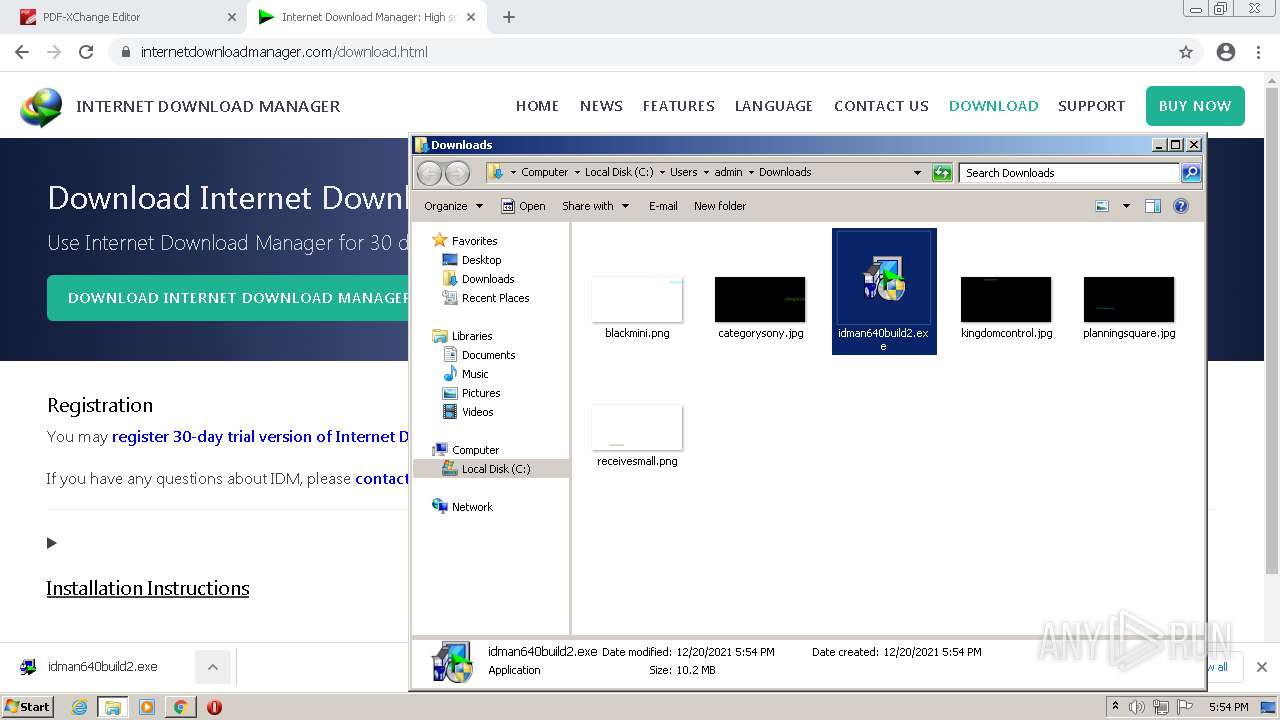
Manual execution by user
- idman640build2.exe (PID: 2064)
- idman640build2.exe (PID: 3348)
- firefox.exe (PID: 2788)
- msiexec.exe (PID: 3204)
Dropped object may contain Bitcoin addresses
- IDMan.exe (PID: 1252)
- firefox.exe (PID: 2512)
- msiexec.exe (PID: 3504)
Reads CPU info
- firefox.exe (PID: 2512)
- runonce.exe (PID: 764)
Creates files in the program directory
- firefox.exe (PID: 2512)
Creates files in the user directory
- firefox.exe (PID: 2512)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
132
Monitored processes
83
Malicious processes
10
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 288 | "C:\Windows\System32\grpconv.exe" -o | C:\Windows\System32\grpconv.exe | — | runonce.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Progman Group Converter Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 396 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1040,16510787205302147161,6534255135655193401,131072 --enable-features=PasswordImport --gpu-preferences=MAAAAAAAAADgACAwAAAAAAAAAAAAAAAAAABgAAAAAAAQAAAAAAAAAAAAAAAAAAAAKAAAAAQAAAAgAAAAAAAAACgAAAAAAAAAMAAAAAAAAAA4AAAAAAAAABAAAAAAAAAAAAAAAAUAAAAQAAAAAAAAAAAAAAAGAAAAEAAAAAAAAAABAAAABQAAABAAAAAAAAAAAQAAAAYAAAA= --mojo-platform-channel-handle=1056 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 396 | C:\Windows\system32\vssvc.exe | C:\Windows\system32\vssvc.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft� Volume Shadow Copy Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 444 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilReadIcon --field-trial-handle=1040,16510787205302147161,6534255135655193401,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=icon_reader --mojo-platform-channel-handle=2256 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 520 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1040,16510787205302147161,6534255135655193401,131072 --enable-features=PasswordImport --lang=en-US --extension-process --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2124 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 520 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --field-trial-handle=1040,16510787205302147161,6534255135655193401,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=3088 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 764 | "C:\Windows\system32\runonce.exe" -r | C:\Windows\system32\runonce.exe | — | rundll32.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Run Once Wrapper Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 836 | "C:\Users\admin\AppData\Local\Temp\IDM_Setup_Temp\IDM1.tmp" -d "C:\Users\admin\AppData\Local\Temp\IDM_Setup_Temp\" | C:\Users\admin\AppData\Local\Temp\IDM_Setup_Temp\IDM1.tmp | — | idman640build2.exe | |||||||||||
User: admin Company: Tonec Inc. Integrity Level: HIGH Description: Internet Download Manager installer Exit code: 0 Version: 6, 38, 22, 1 Modules
| |||||||||||||||
| 1108 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1040,16510787205302147161,6534255135655193401,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=3084 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1132 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilReadIcon --field-trial-handle=1040,16510787205302147161,6534255135655193401,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=icon_reader --mojo-platform-channel-handle=3716 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
Total events
53 953
Read events
51 998
Write events
1 839
Delete events
116
Modification events
| (PID) Process: | (3752) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3752) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3752) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3752) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3752) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3752) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3752) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3752) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (3752) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
| (PID) Process: | (3752) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_installdate |
Value: 0 | |||
Executable files
41
Suspicious files
550
Text files
692
Unknown types
156
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3752 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-61C0C327-EA8.pma | — | |
MD5:— | SHA256:— | |||
| 3752 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\4405fe86-b7c5-4f2f-a1aa-8d10e2f5bc19.tmp | text | |
MD5:— | SHA256:— | |||
| 3752 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Preferences | text | |
MD5:— | SHA256:— | |||
| 3752 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF193157.TMP | text | |
MD5:936EB7280DA791E6DD28EF3A9B46D39C | SHA256:CBAF2AFD831B32F6D1C12337EE5D2F090D6AE1F4DCB40B08BEF49BF52AD9721F | |||
| 3752 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad\settings.dat | binary | |
MD5:9C016064A1F864C8140915D77CF3389A | SHA256:0E7265D4A8C16223538EDD8CD620B8820611C74538E420A88E333BE7F62AC787 | |||
| 3752 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Local Storage\leveldb\LOG.old | text | |
MD5:7721CDA9F5B73CE8A135471EB53B4E0E | SHA256:DD730C576766A46FFC84E682123248ECE1FF1887EC0ACAB22A5CE93A450F4500 | |||
| 3752 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Local Storage\leveldb\LOG.old~RF193176.TMP | text | |
MD5:81F483F77EE490F35306A4F94DB2286B | SHA256:82434CE3C9D13F509EBEEBE3A7A1A1DE9AB4557629D9FC855761E0CFA45E8BCE | |||
| 3752 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:5BD3C311F2136A7A88D3E197E55CF902 | SHA256:FA331915E1797E59979A3E4BCC2BD0D3DEAA039B94D4DB992BE251FD02A224B9 | |||
| 3120 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\CrashpadMetrics.pma | binary | |
MD5:03C4F648043A88675A920425D824E1B3 | SHA256:F91DBB7C64B4582F529C968C480D2DCE1C8727390482F31E4355A27BB3D9B450 | |||
| 3752 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\09dd91e7-f8b0-42ec-8804-b5782dde13dd.tmp | binary | |
MD5:5058F1AF8388633F609CADB75A75DC9D | SHA256:— | |||
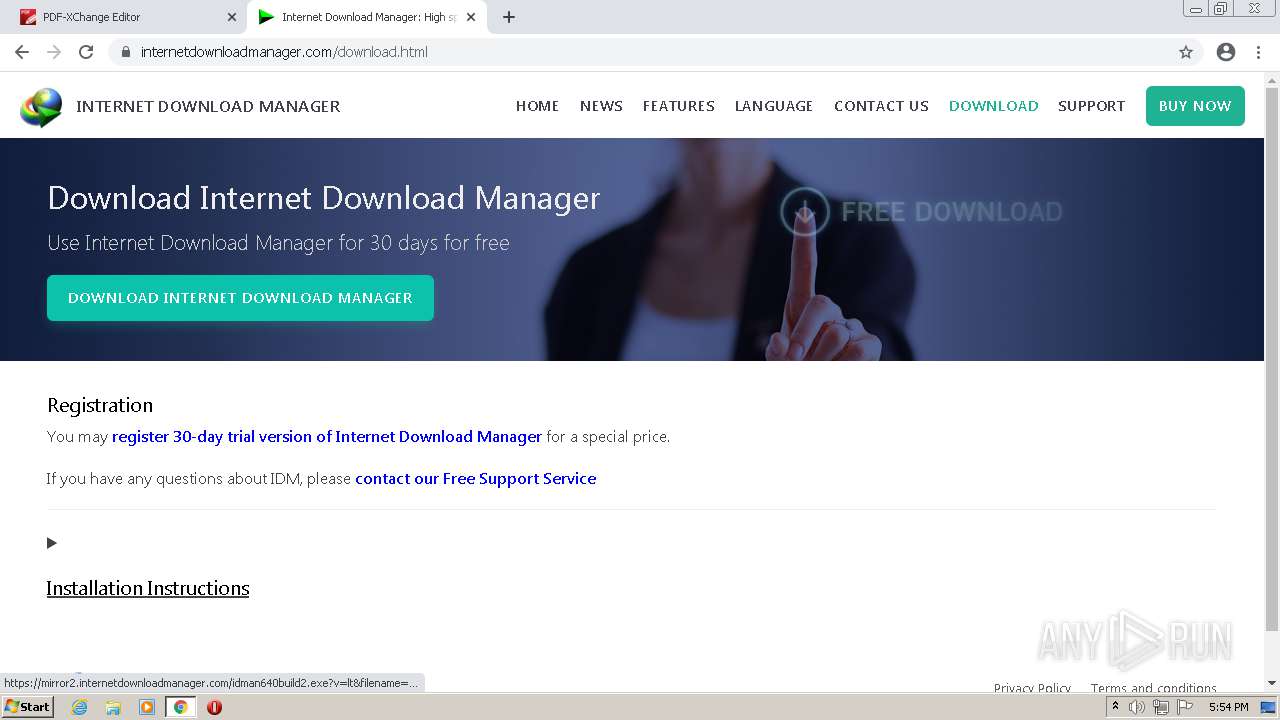
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
47
TCP/UDP connections
138
DNS requests
132
Threats
5
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
884 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adys6mm2sd23z36ns7e4hcs4hrqq_1.3.36.111/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.111_win_ac5lwr5427en7czu7myxmee6c7xq.crx3 | US | — | — | whitelisted |
2512 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
884 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adys6mm2sd23z36ns7e4hcs4hrqq_1.3.36.111/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.111_win_ac5lwr5427en7czu7myxmee6c7xq.crx3 | US | binary | 9.69 Kb | whitelisted |
2512 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
2512 | firefox.exe | POST | 200 | 142.250.185.195:80 | http://ocsp.pki.goog/gts1c3 | US | der | 472 b | whitelisted |
2512 | firefox.exe | POST | 200 | 142.250.185.195:80 | http://ocsp.pki.goog/gts1c3 | US | der | 471 b | whitelisted |
884 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adys6mm2sd23z36ns7e4hcs4hrqq_1.3.36.111/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.111_win_ac5lwr5427en7czu7myxmee6c7xq.crx3 | US | binary | 5.63 Kb | whitelisted |
884 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adys6mm2sd23z36ns7e4hcs4hrqq_1.3.36.111/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.111_win_ac5lwr5427en7czu7myxmee6c7xq.crx3 | US | binary | 358 Kb | whitelisted |
884 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adys6mm2sd23z36ns7e4hcs4hrqq_1.3.36.111/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.111_win_ac5lwr5427en7czu7myxmee6c7xq.crx3 | US | ini | 9.69 Kb | whitelisted |
884 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adys6mm2sd23z36ns7e4hcs4hrqq_1.3.36.111/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.111_win_ac5lwr5427en7czu7myxmee6c7xq.crx3 | US | binary | 9.69 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1772 | chrome.exe | 142.250.184.237:443 | accounts.google.com | Google Inc. | US | suspicious |
1772 | chrome.exe | 216.58.212.174:443 | clients2.google.com | Google Inc. | US | whitelisted |
1772 | chrome.exe | 194.150.248.53:443 | pdf-xchange.eu | NovaTrend Services GmbH | CH | unknown |
1772 | chrome.exe | 104.21.23.106:443 | www.usefomo.com | Cloudflare Inc | US | unknown |
1772 | chrome.exe | 142.250.186.72:443 | www.googletagmanager.com | Google Inc. | US | suspicious |
1772 | chrome.exe | 93.158.134.119:443 | mc.yandex.ru | YANDEX LLC | RU | whitelisted |
1772 | chrome.exe | 172.67.171.240:443 | pro.cookieassistant.com | — | US | suspicious |
1772 | chrome.exe | 67.27.233.126:80 | ctldl.windowsupdate.com | Level 3 Communications, Inc. | US | suspicious |
1772 | chrome.exe | 151.101.2.133:443 | cdn.filestackcontent.com | Fastly | US | malicious |
1772 | chrome.exe | 52.20.78.240:443 | stats.fomo.com | Amazon.com, Inc. | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clients2.google.com |
| whitelisted |
pdf-xchange.eu |
| unknown |
accounts.google.com |
| shared |
www.usefomo.com |
| suspicious |
www.googletagmanager.com |
| whitelisted |
mc.yandex.ru |
| whitelisted |
pro.cookieassistant.com |
| malicious |
e.fomo.com |
| unknown |
geocode.usefomo.com |
| shared |
ctldl.windowsupdate.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2512 | firefox.exe | Potentially Bad Traffic | ET INFO Terse Request for .txt - Likely Hostile |
2512 | firefox.exe | Potentially Bad Traffic | ET INFO Terse Request for .txt - Likely Hostile |
2512 | firefox.exe | Potentially Bad Traffic | ET INFO Terse Request for .txt - Likely Hostile |
2512 | firefox.exe | Potentially Bad Traffic | ET INFO Terse Request for .txt - Likely Hostile |
1292 | IDMan.exe | Potential Corporate Privacy Violation | ET POLICY Outgoing Basic Auth Base64 HTTP Password detected unencrypted |