| File name: | Zrzut ekranu 2025-03-29 142733.png |
| Full analysis: | https://app.any.run/tasks/01783571-3630-4ab4-9188-c494213d1abb |
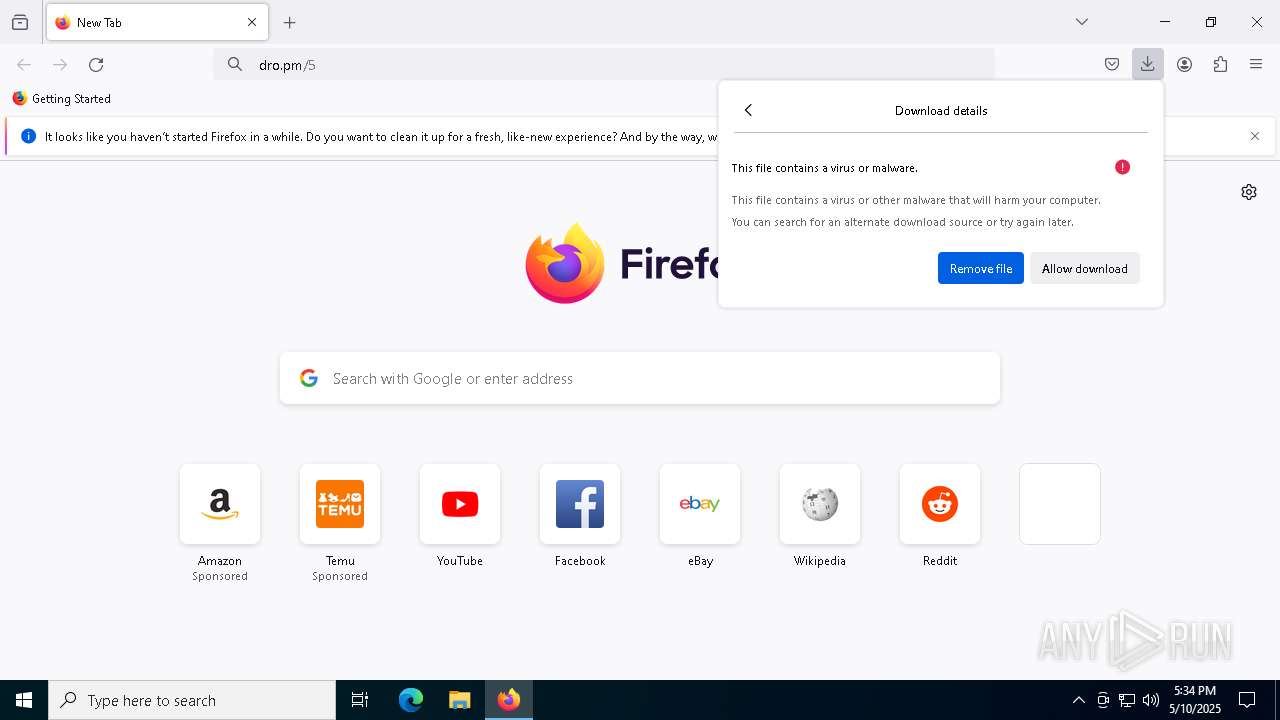
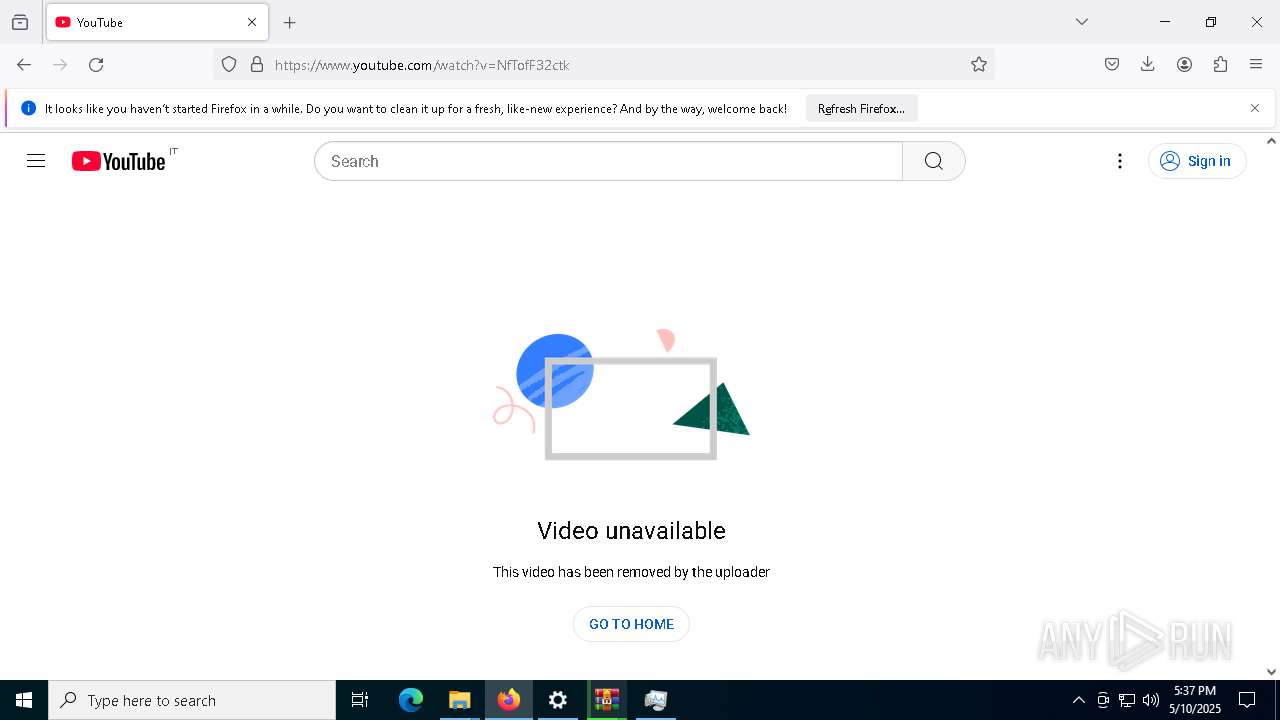
| Verdict: | Malicious activity |
| Threats: | AsyncRAT is a RAT that can monitor and remotely control infected systems. This malware was introduced on Github as a legitimate open-source remote administration software, but hackers use it for its many powerful malicious functions. |
| Analysis date: | May 10, 2025, 17:33:42 |
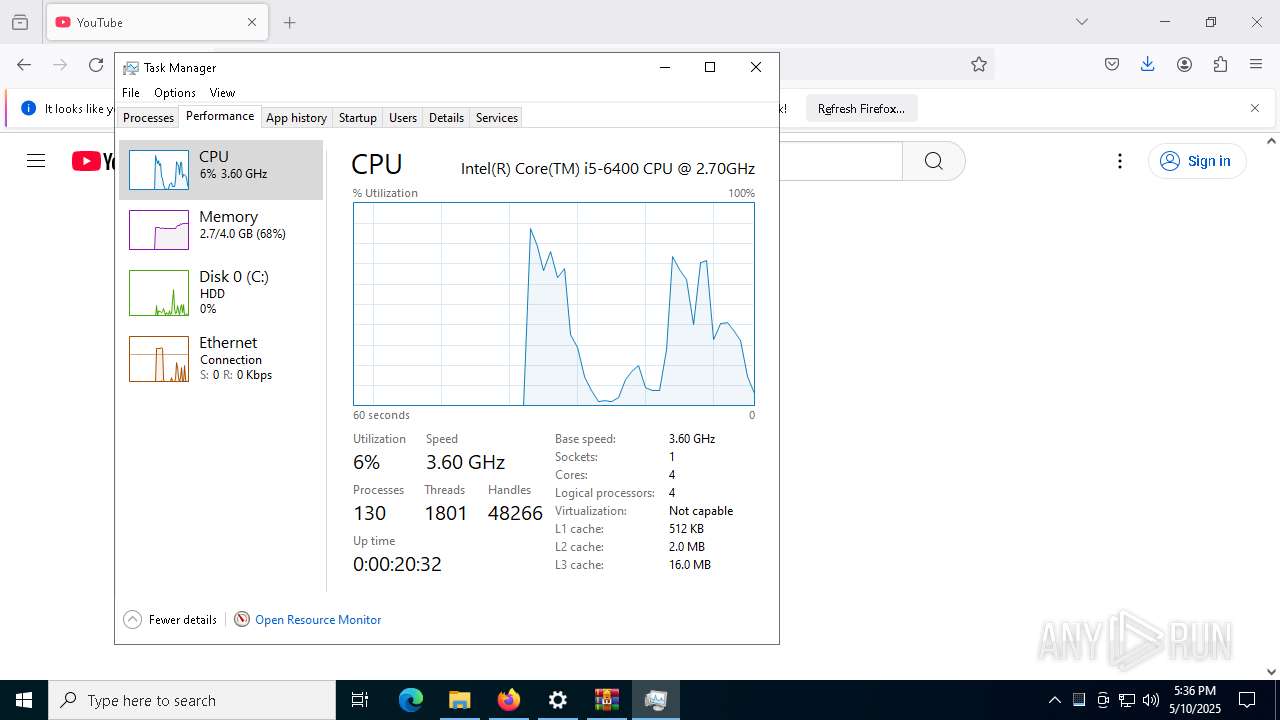
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | image/png |
| File info: | PNG image data, 1919 x 1079, 8-bit/color RGBA, non-interlaced |
| MD5: | 2EAFDB594751B8969EDADF5C50ABCD82 |
| SHA1: | 8B0DEEABC4E309BB4CC4A7FE7A2C09ED559B0588 |
| SHA256: | 7653995814940B5DBC5200079D0CB95B3BCAD4268009DE31EB5474F51101C809 |
| SSDEEP: | 98304:z0cPbWJhRFDlG6oxTP9cn8y2UXrOlBCg2XJepSrF3tSpAiugI0tugwiNCK7PTFan:7u |
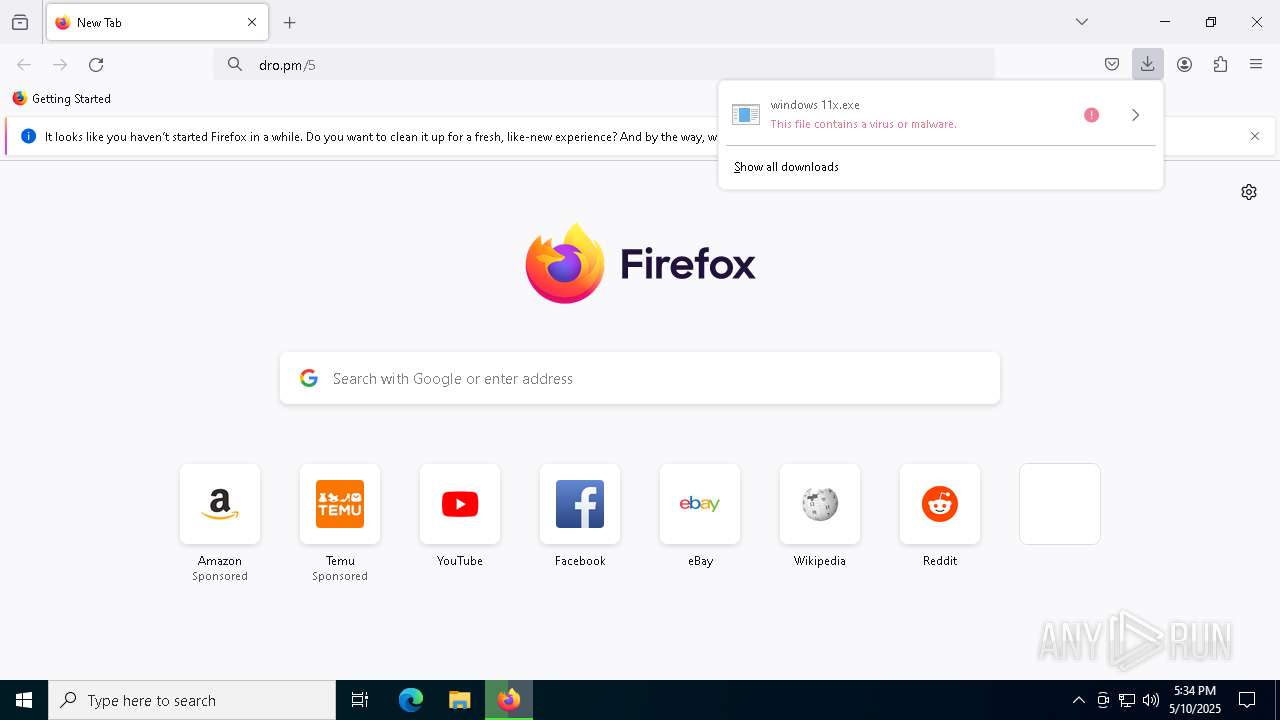
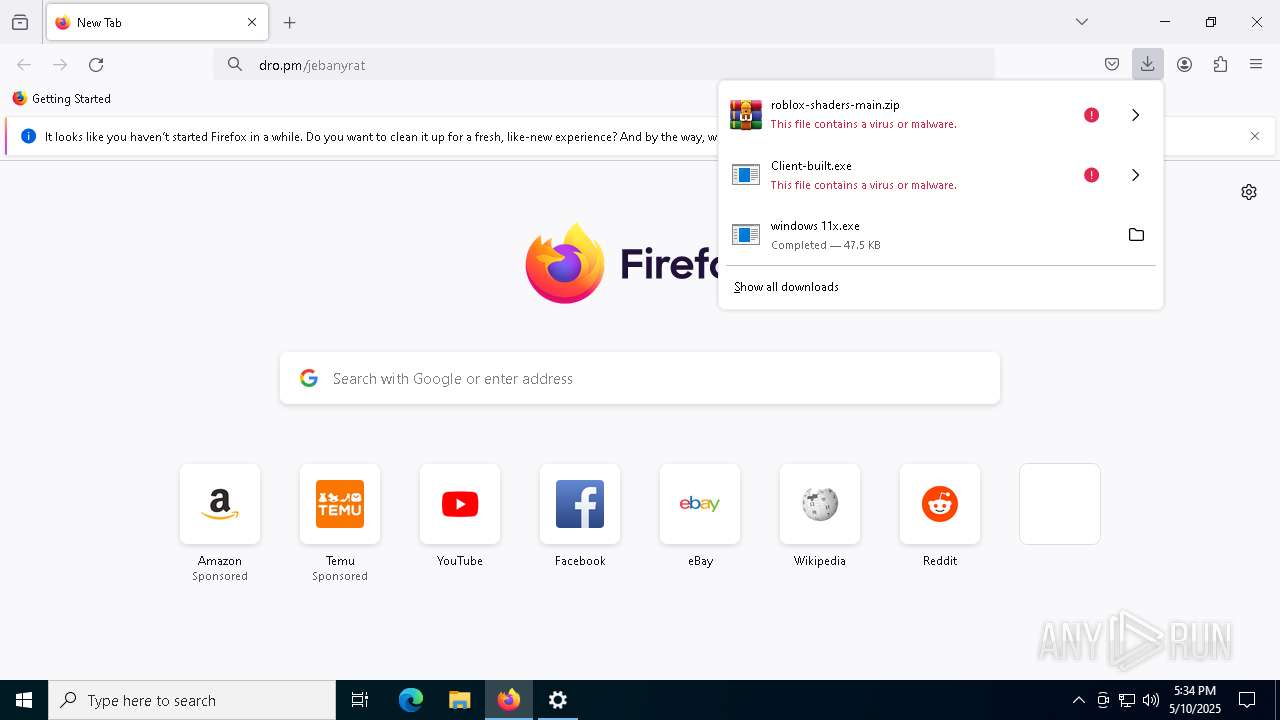
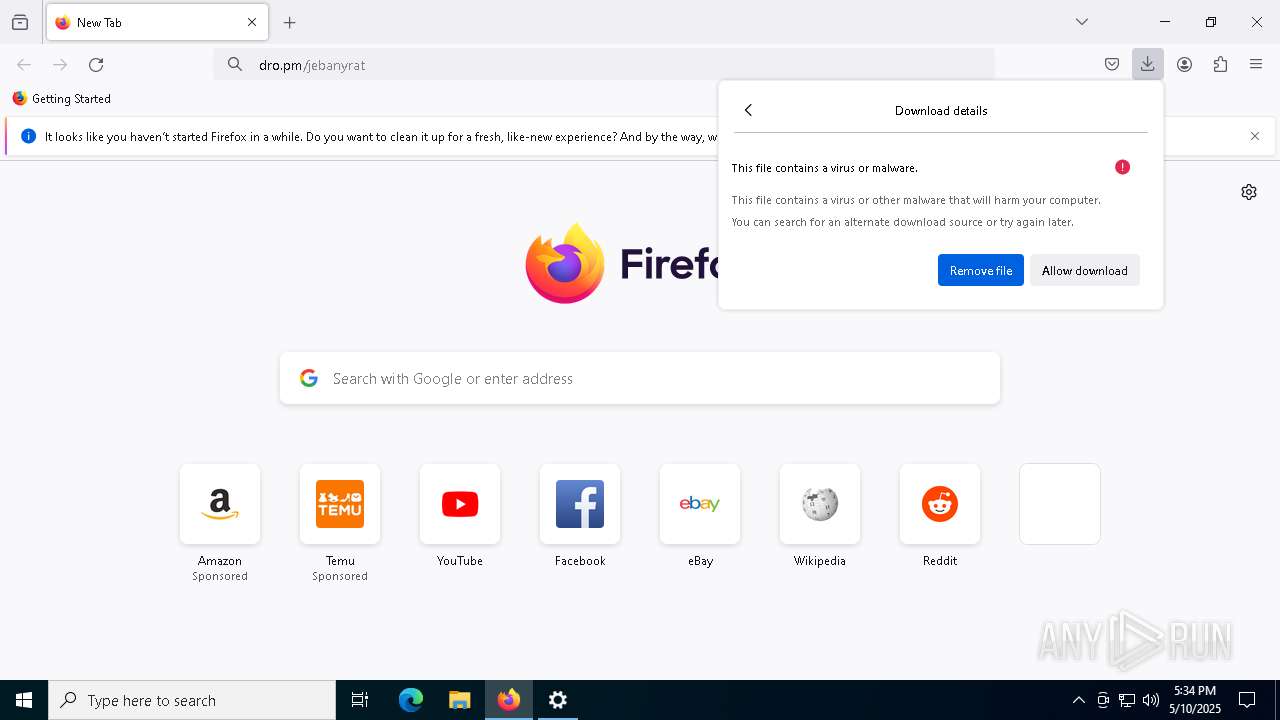
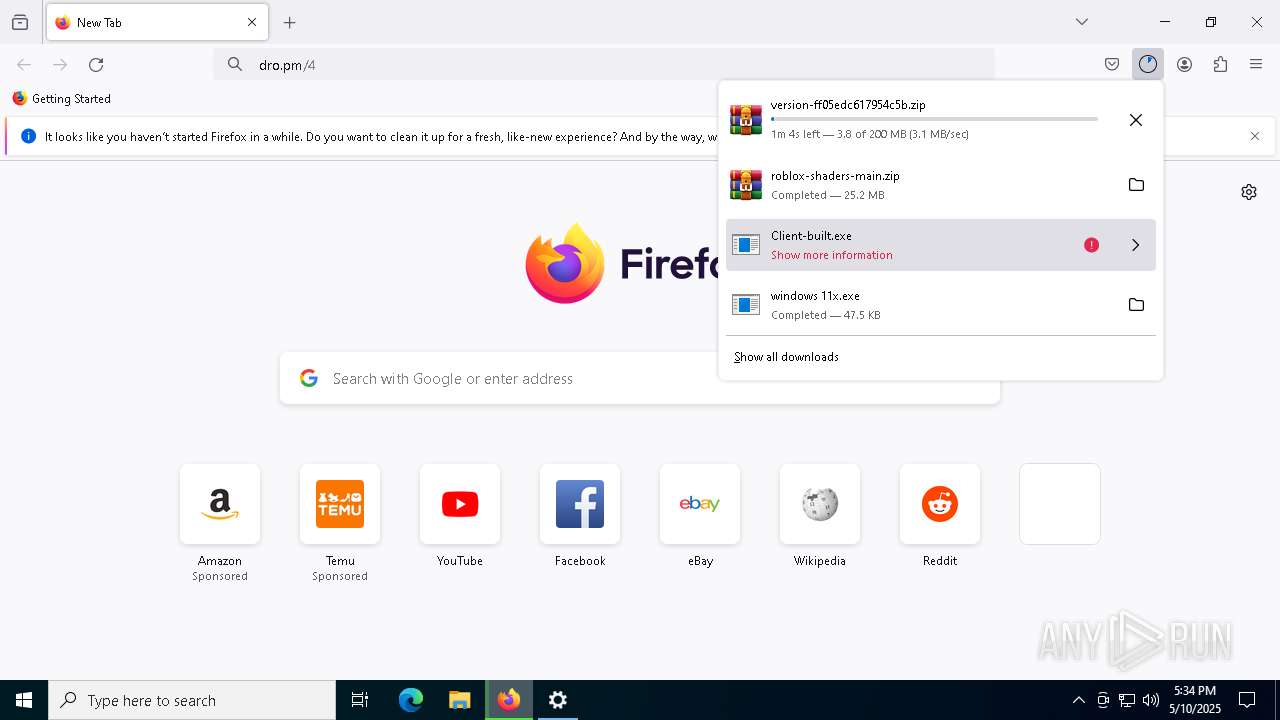
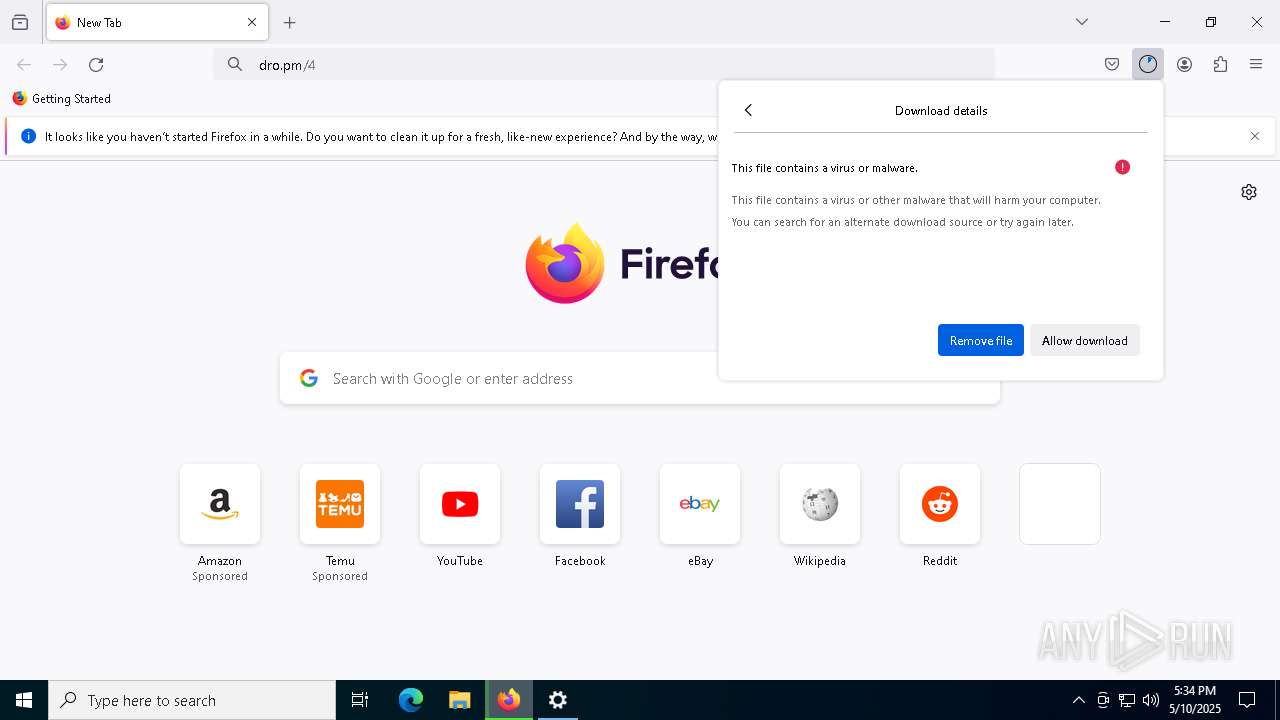
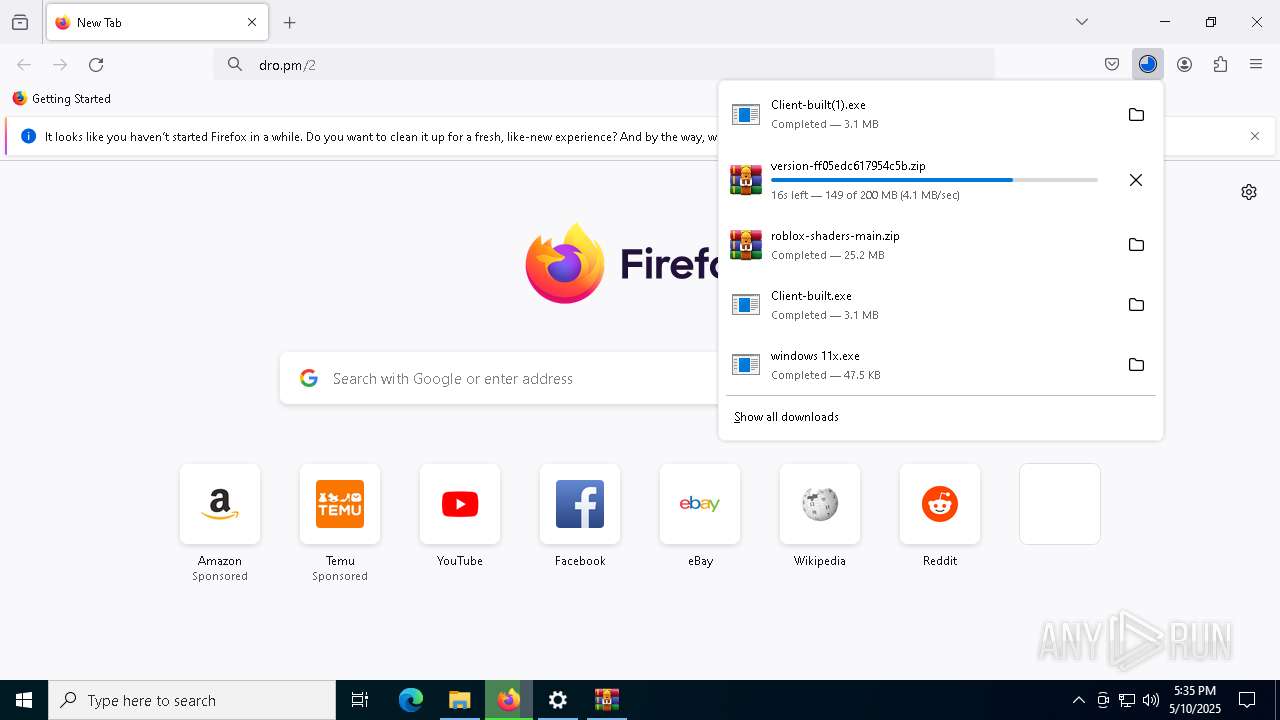
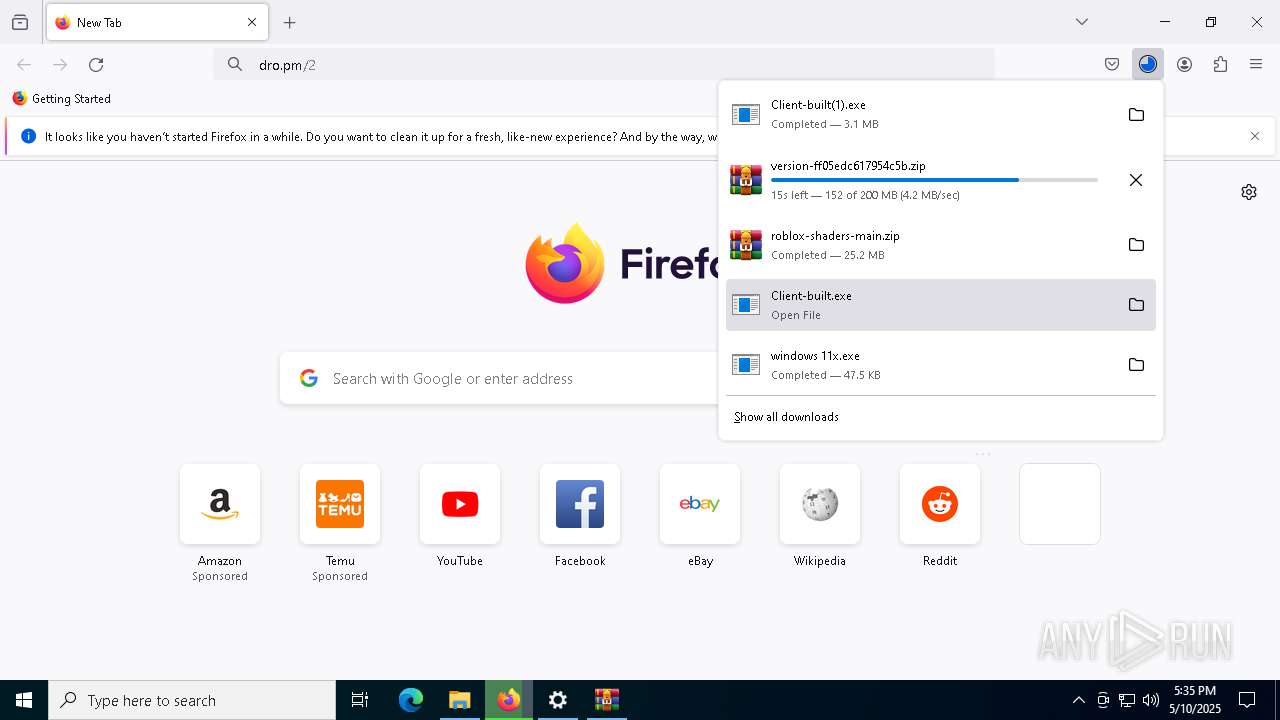
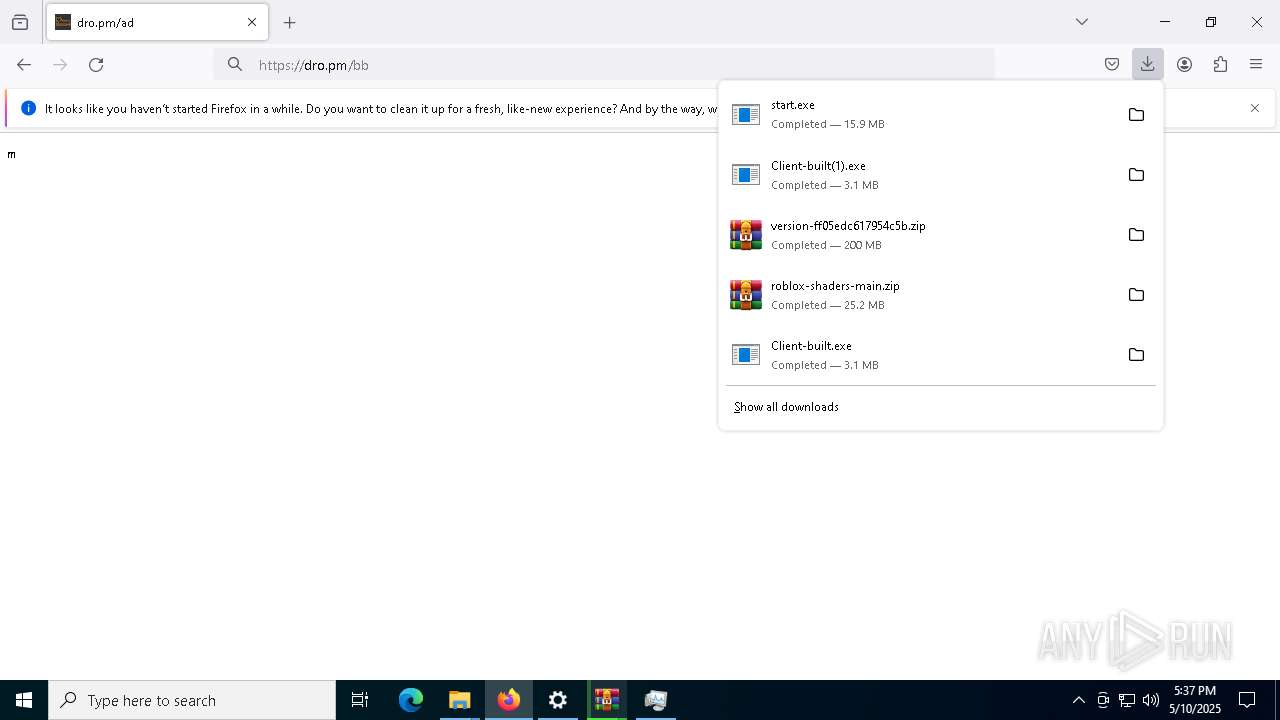
MALICIOUS
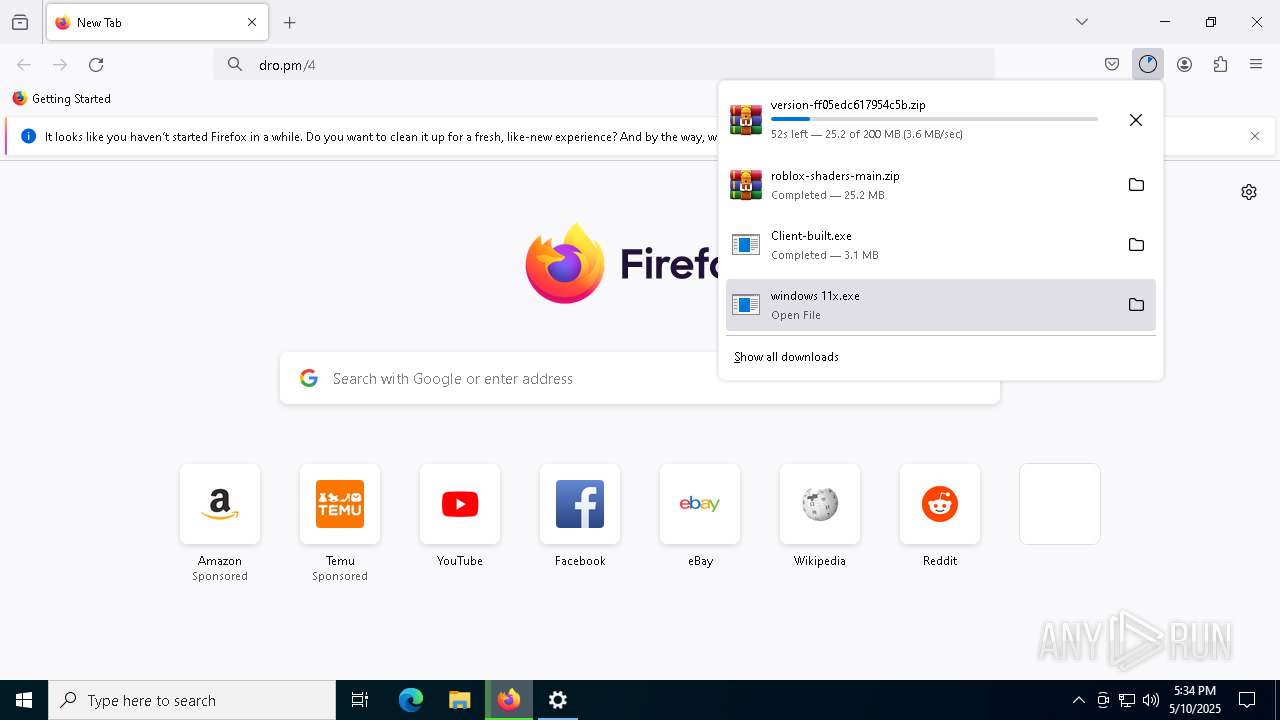
Changes the autorun value in the registry
- windows 11x.exe (PID: 300)
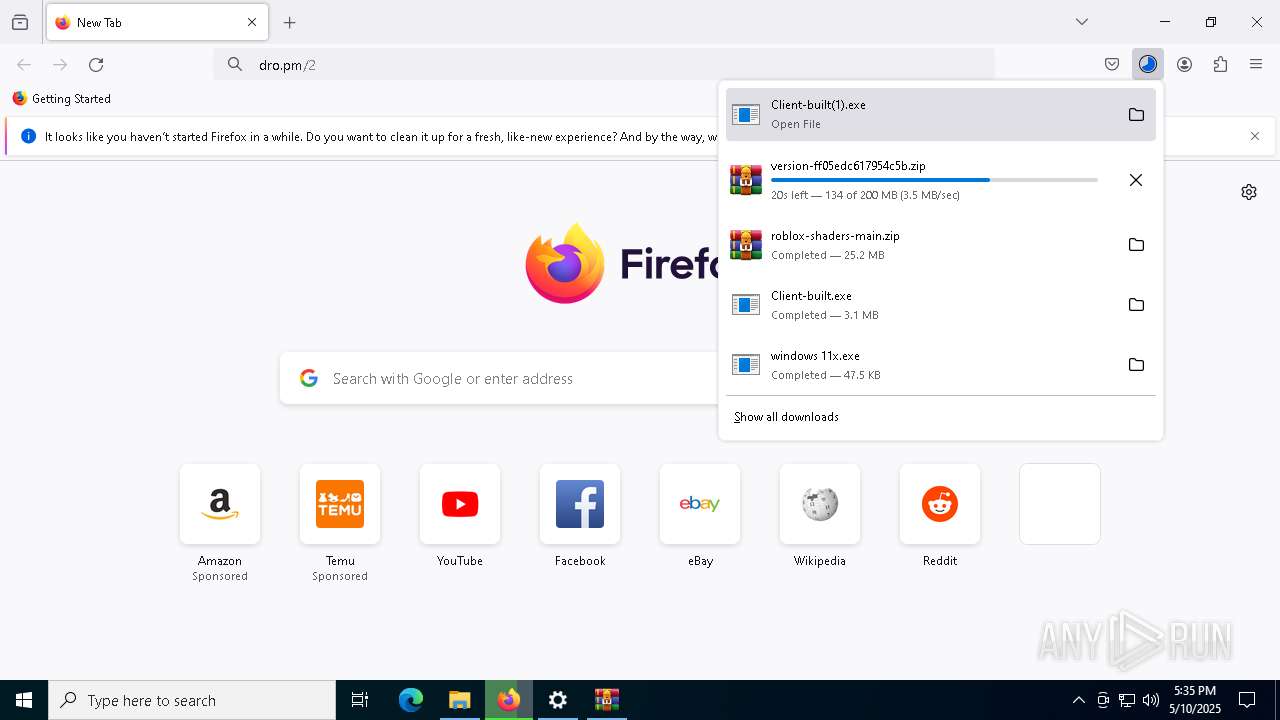
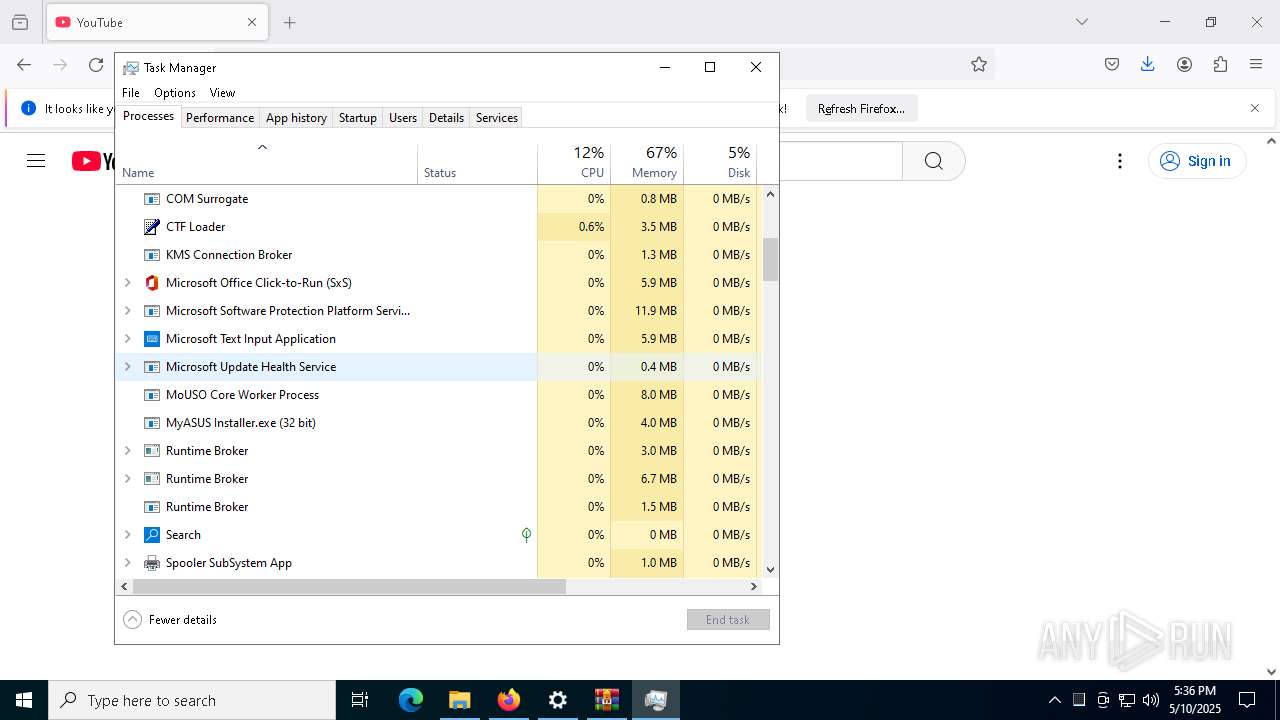
QUASAR has been detected (YARA)
- Client-built.exe (PID: 2560)
- Client-built(1).exe (PID: 9108)
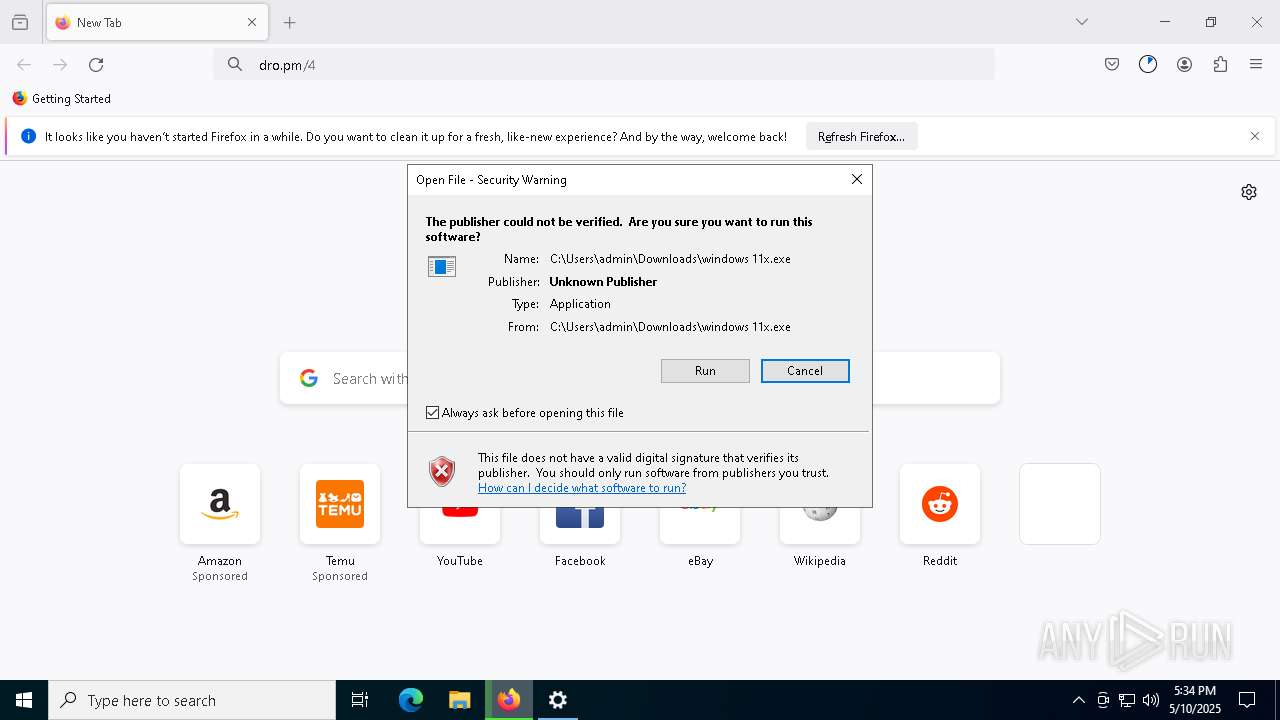
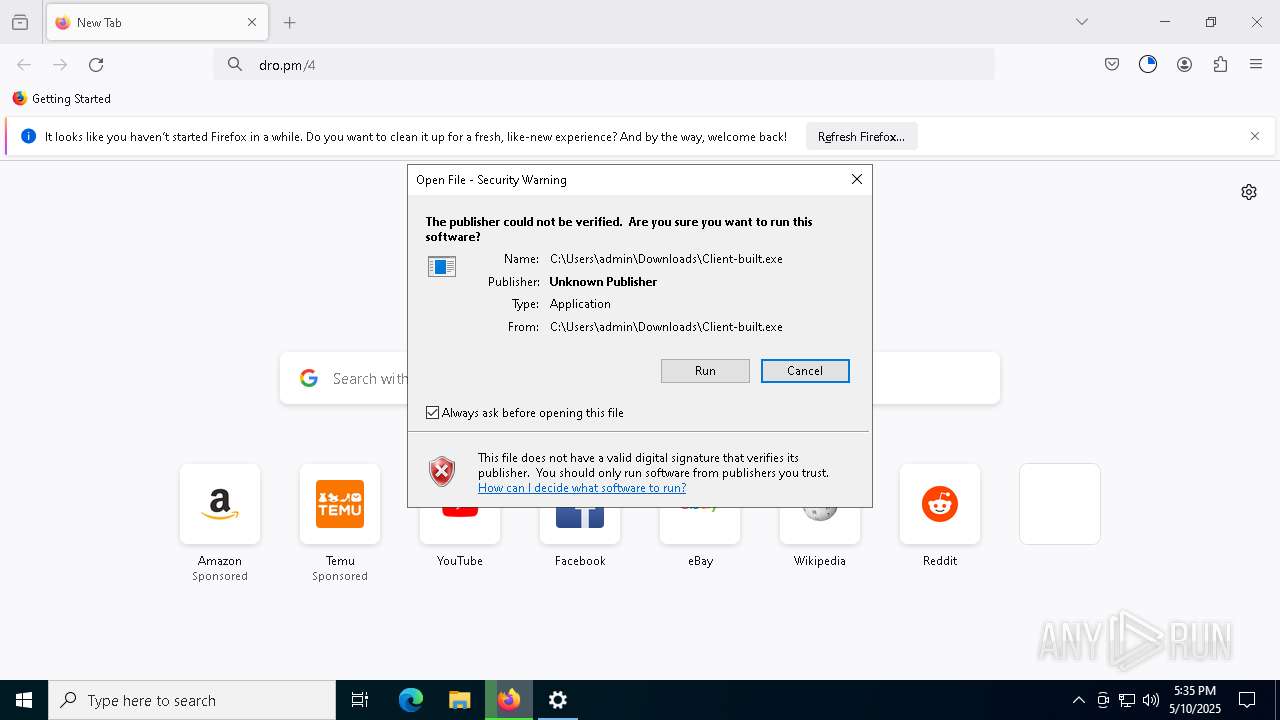
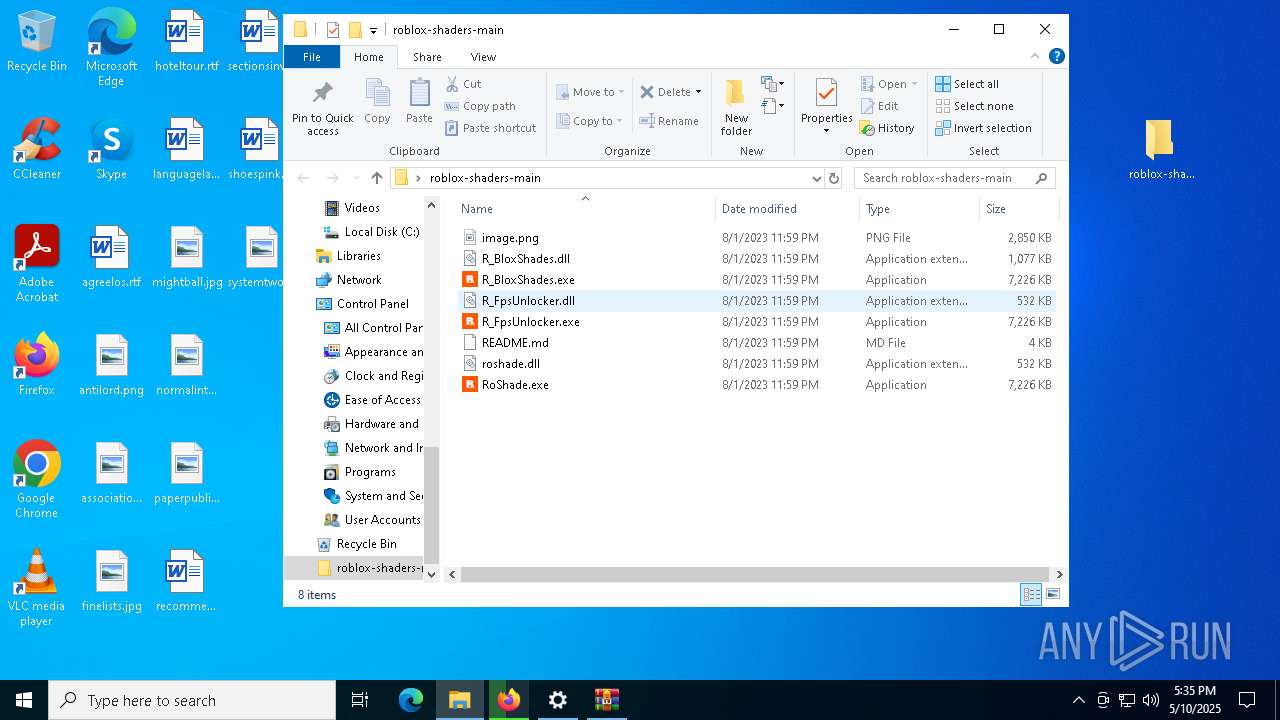
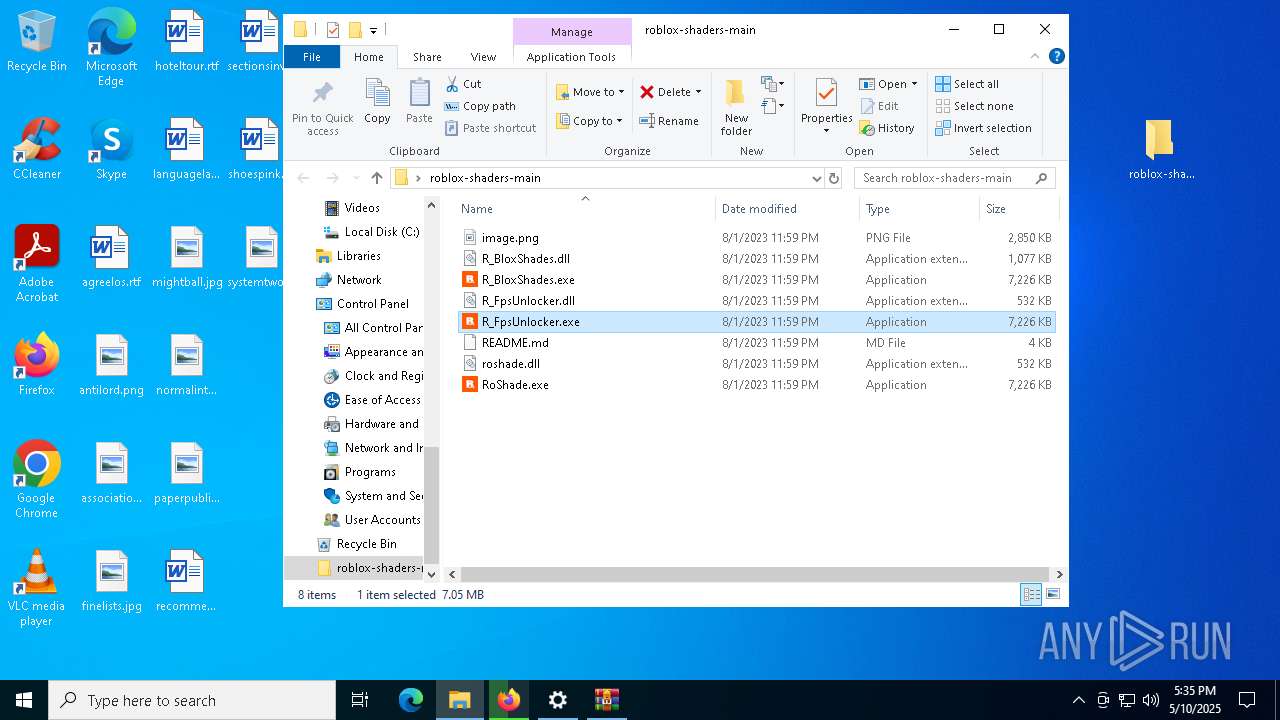
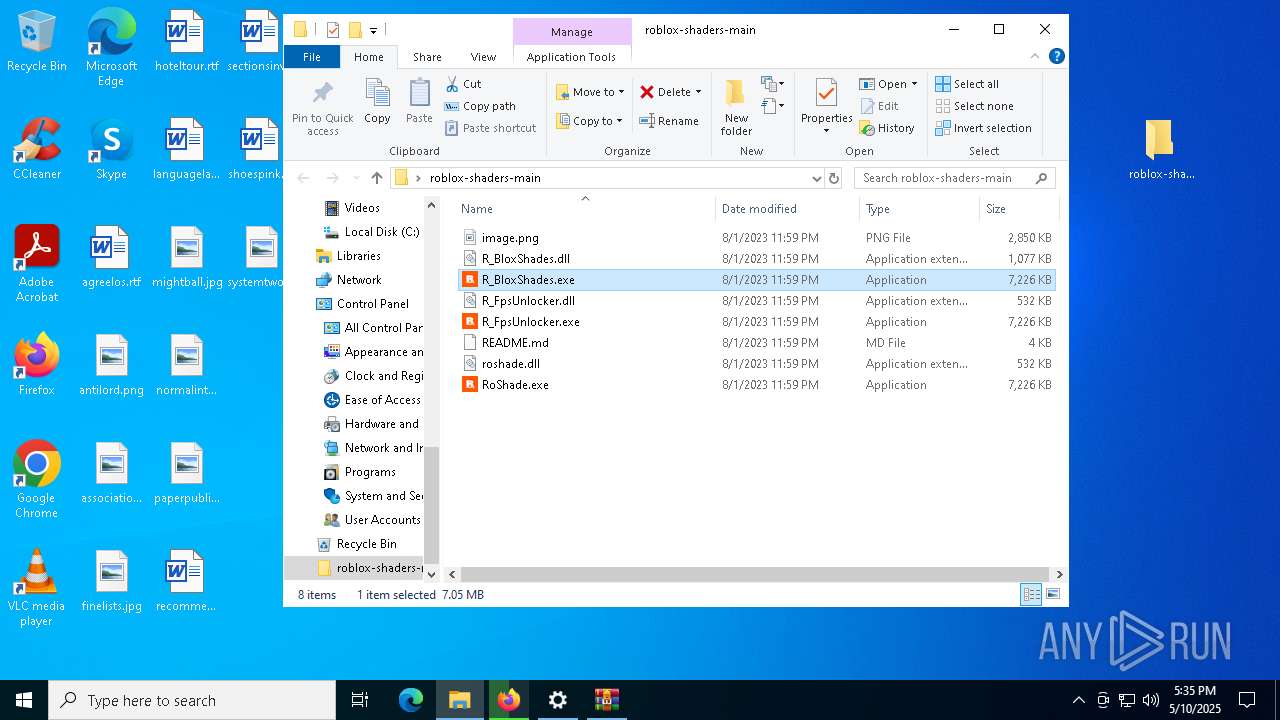
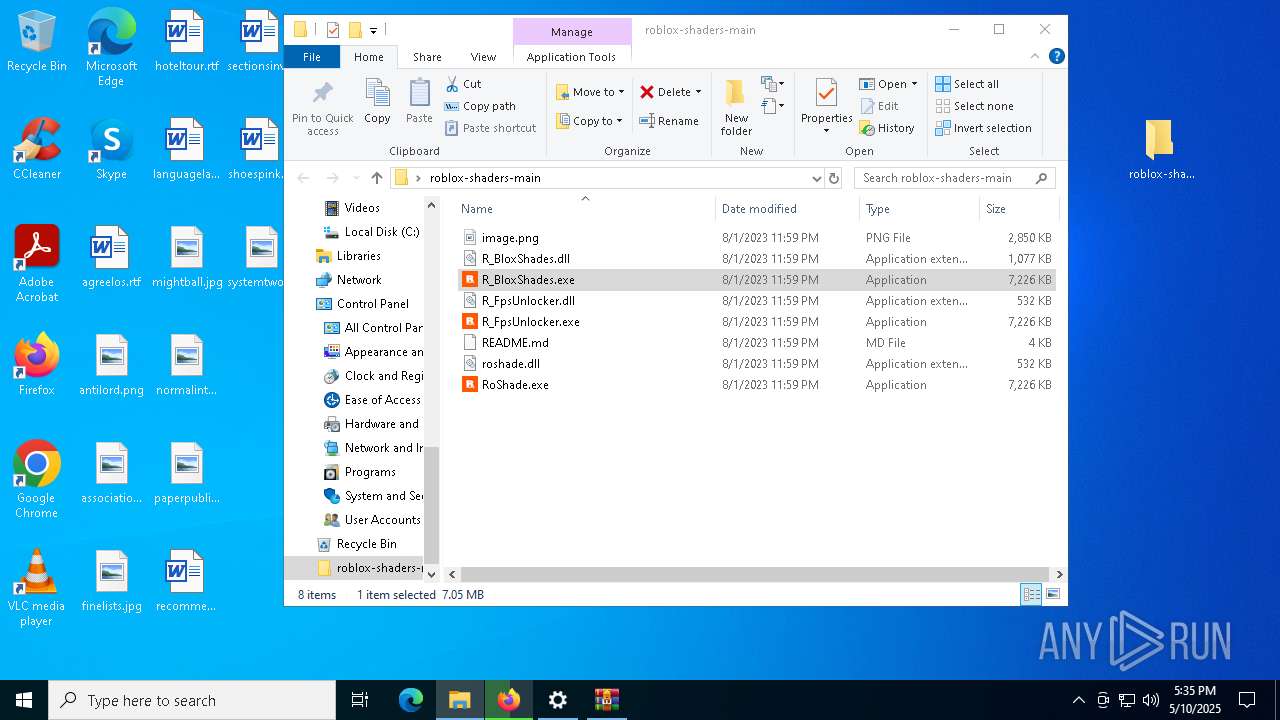
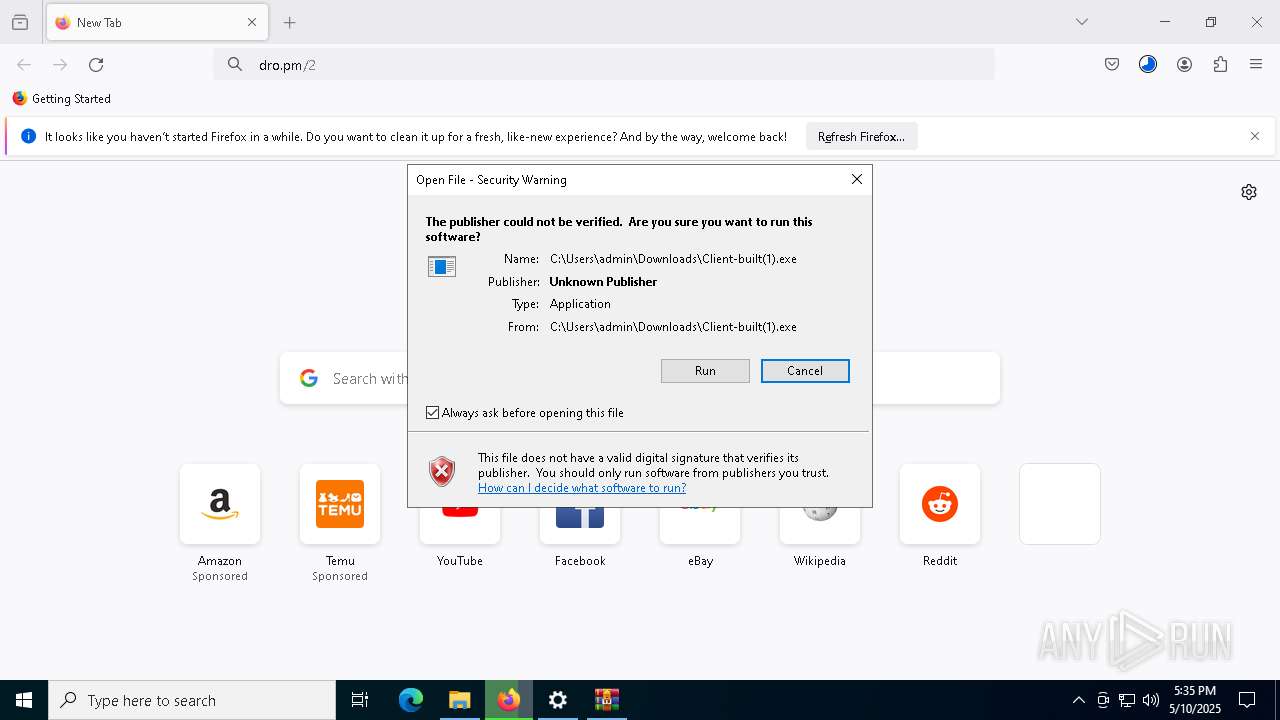
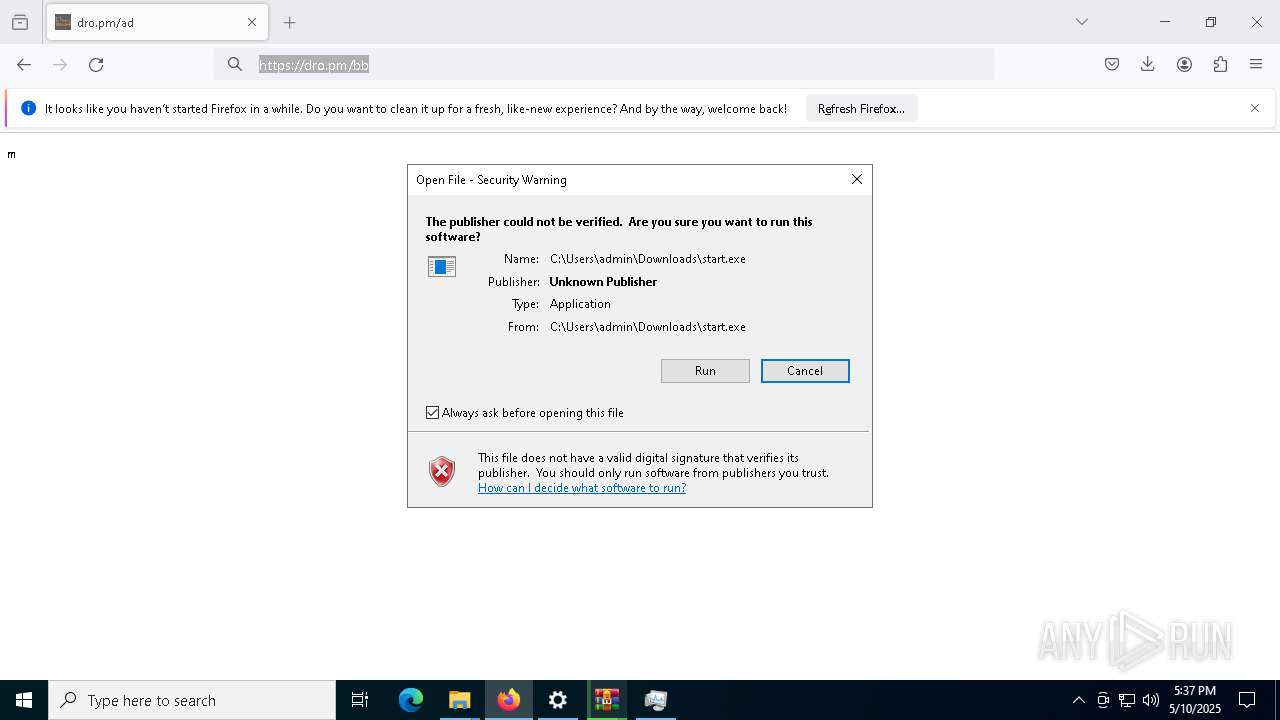
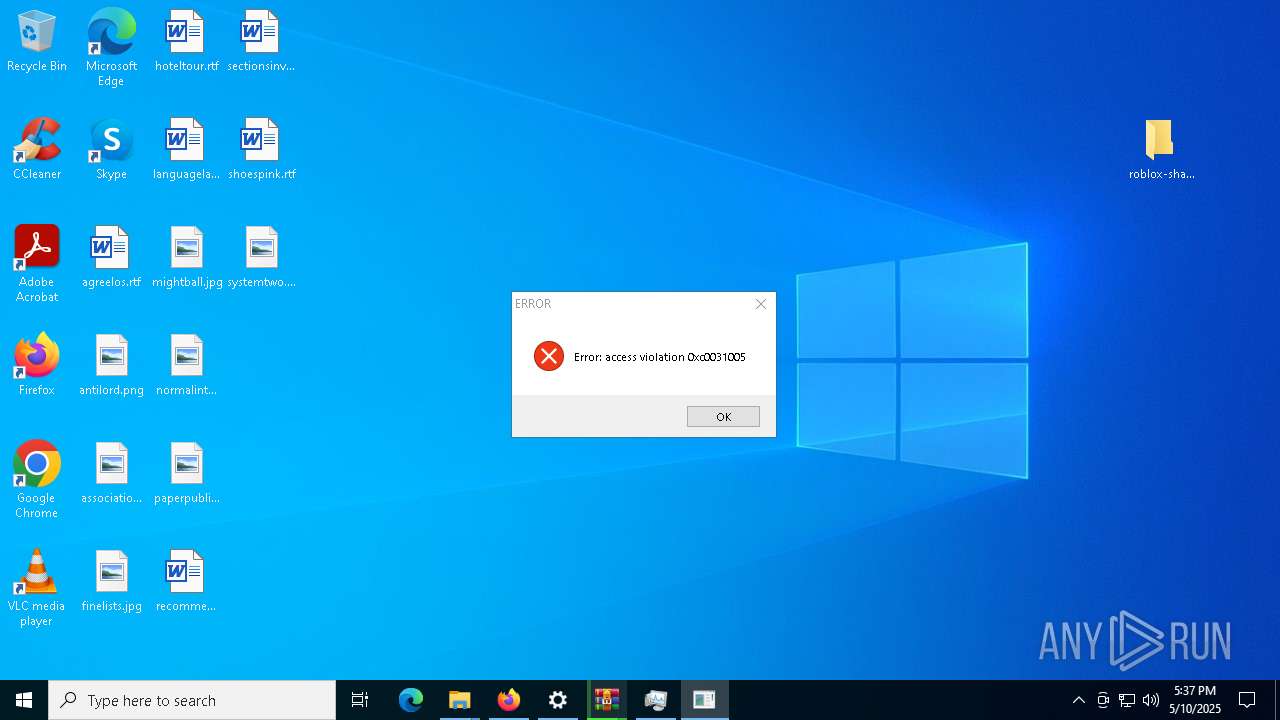
Executing a file with an untrusted certificate
- RoShade.exe (PID: 2084)
- R_FpsUnlocker.exe (PID: 3024)
- RoShade.exe (PID: 7440)
- R_FpsUnlocker.exe (PID: 7928)
- R_BloxShades.exe (PID: 7776)
- RoShade.exe (PID: 7772)
- R_FpsUnlocker.exe (PID: 1616)
- R_BloxShades.exe (PID: 7936)
- RoShade.exe (PID: 7552)
- R_FpsUnlocker.exe (PID: 6028)
- R_BloxShades.exe (PID: 5036)
- R_BloxShades.exe (PID: 8548)
Adds path to the Windows Defender exclusion list
- RoShade.exe (PID: 7552)
- cmd.exe (PID: 6080)
- cmd.exe (PID: 8080)
Antivirus name has been found in the command line (generic signature)
- cmd.exe (PID: 2980)
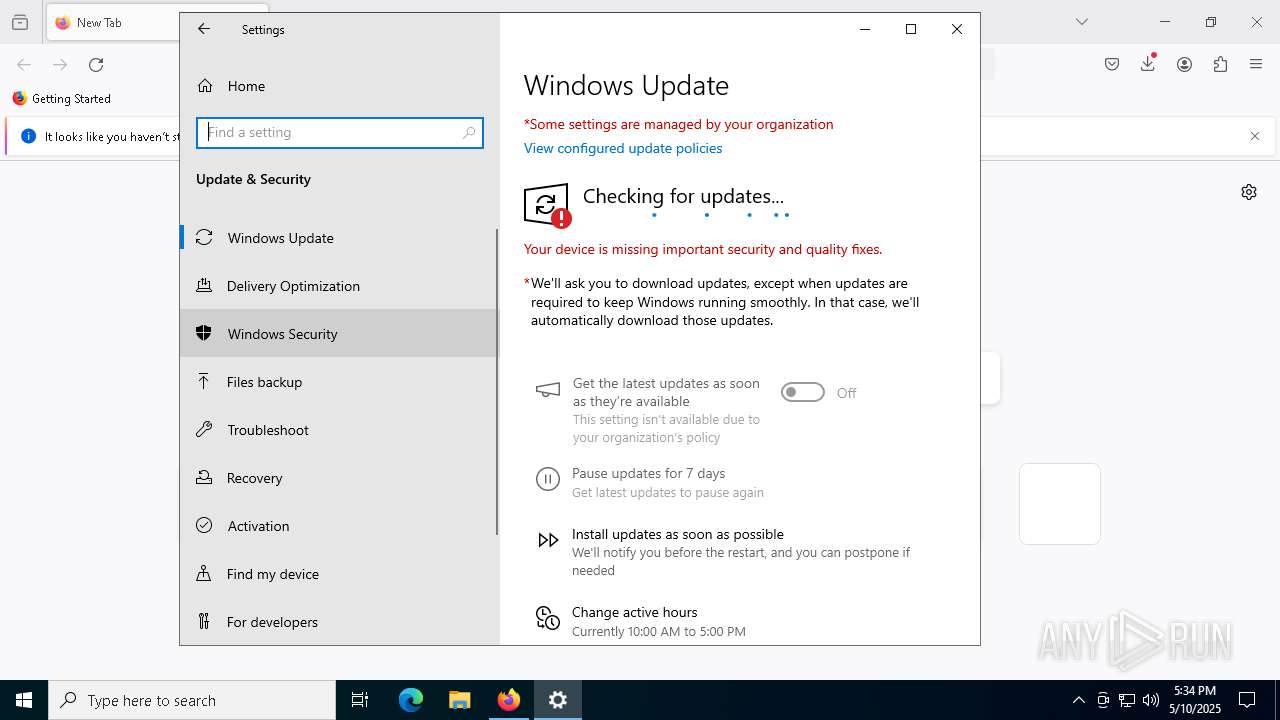
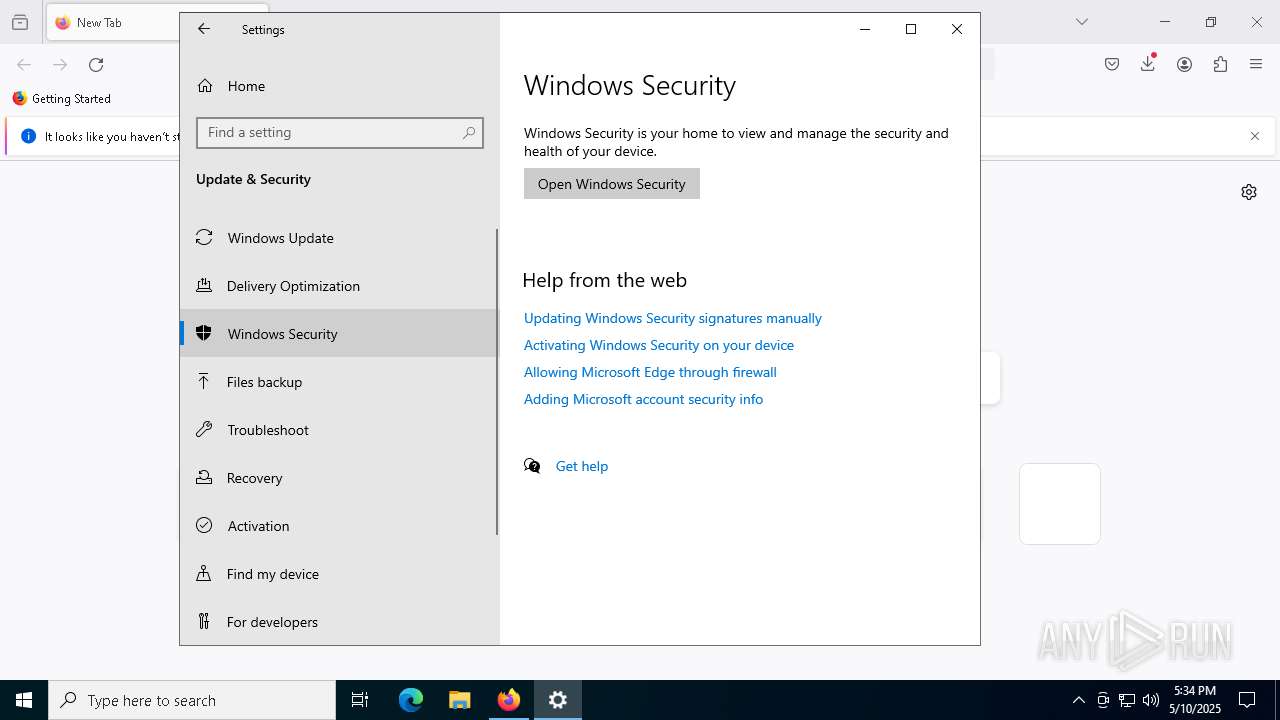
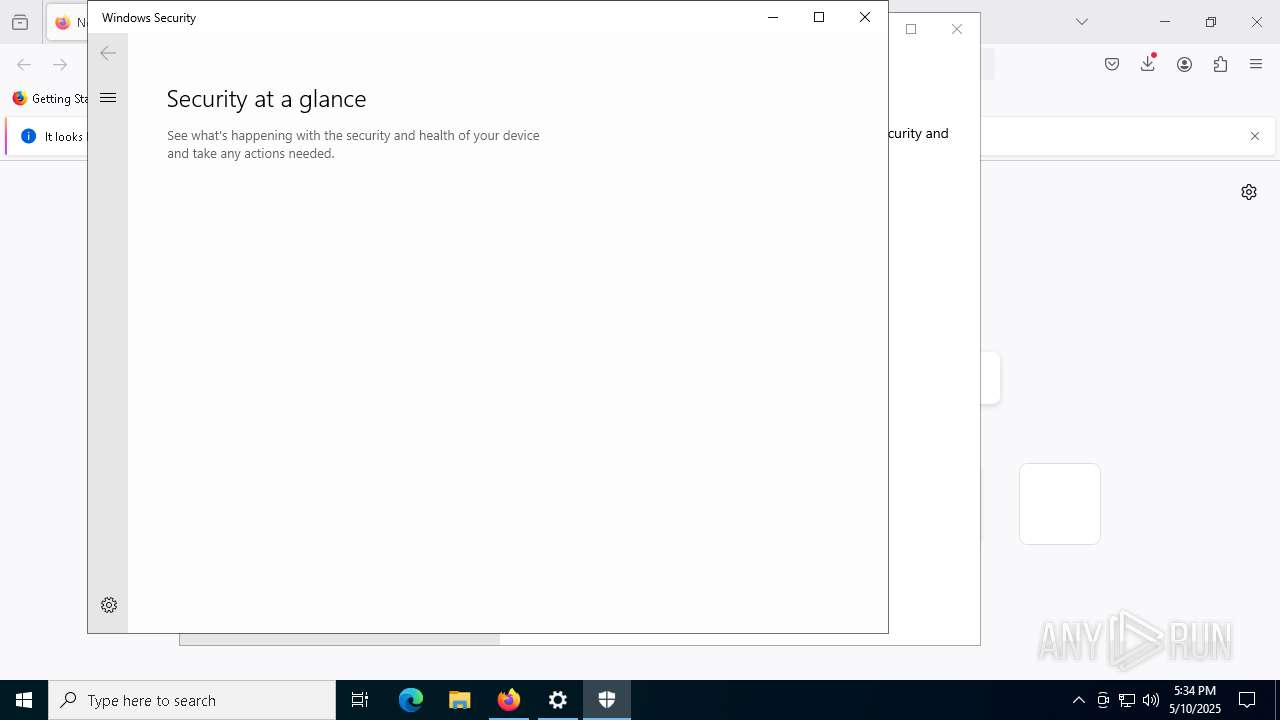
Changes settings for real-time protection
- powershell.exe (PID: 7364)
Changes settings for sending potential threat samples to Microsoft servers
- powershell.exe (PID: 7364)
Changes Controlled Folder Access settings
- powershell.exe (PID: 7364)
Changes settings for checking scripts for malicious actions
- powershell.exe (PID: 7364)
Changes settings for reporting to Microsoft Active Protection Service (MAPS)
- powershell.exe (PID: 7364)
Changes Windows Defender settings
- cmd.exe (PID: 2980)
- cmd.exe (PID: 6080)
- cmd.exe (PID: 8080)
Changes settings for protection against network attacks (IPS)
- powershell.exe (PID: 7364)
Changes antivirus protection settings for downloading files from the Internet (IOAVProtection)
- powershell.exe (PID: 7364)
Bypass execution policy to execute commands
- powershell.exe (PID: 8436)
Changes powershell execution policy (Bypass)
- cmd.exe (PID: 8220)
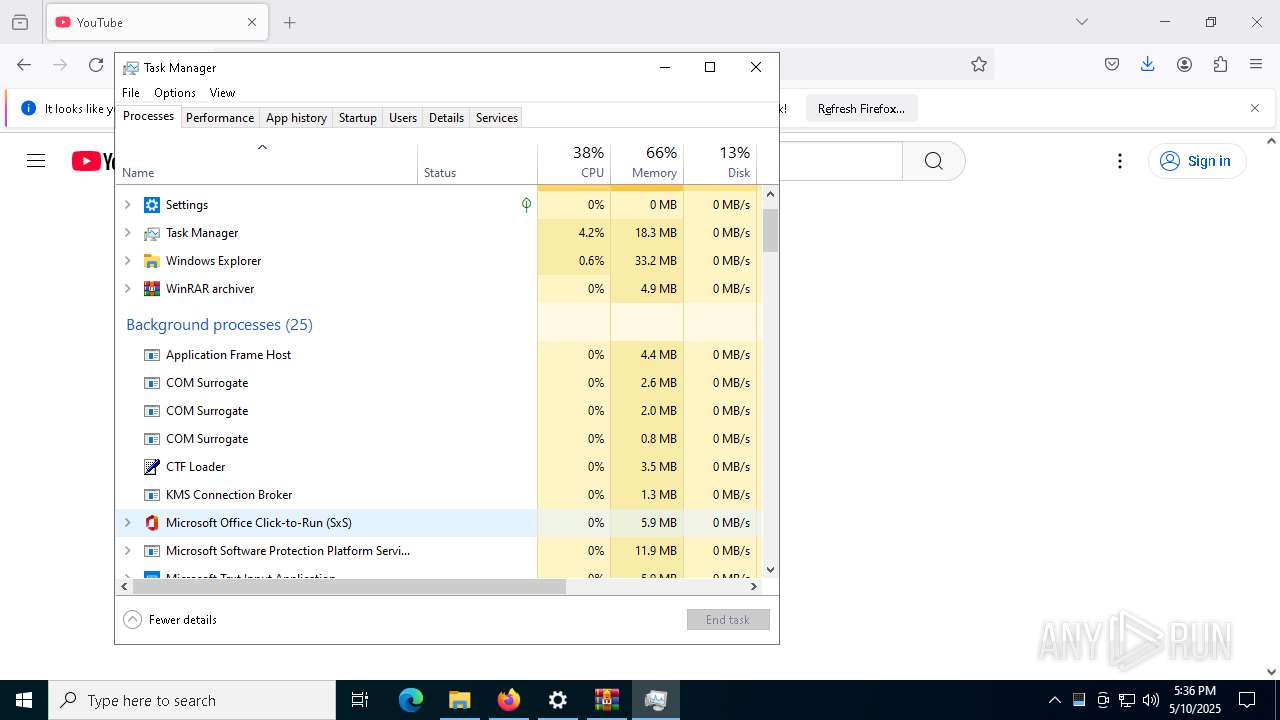
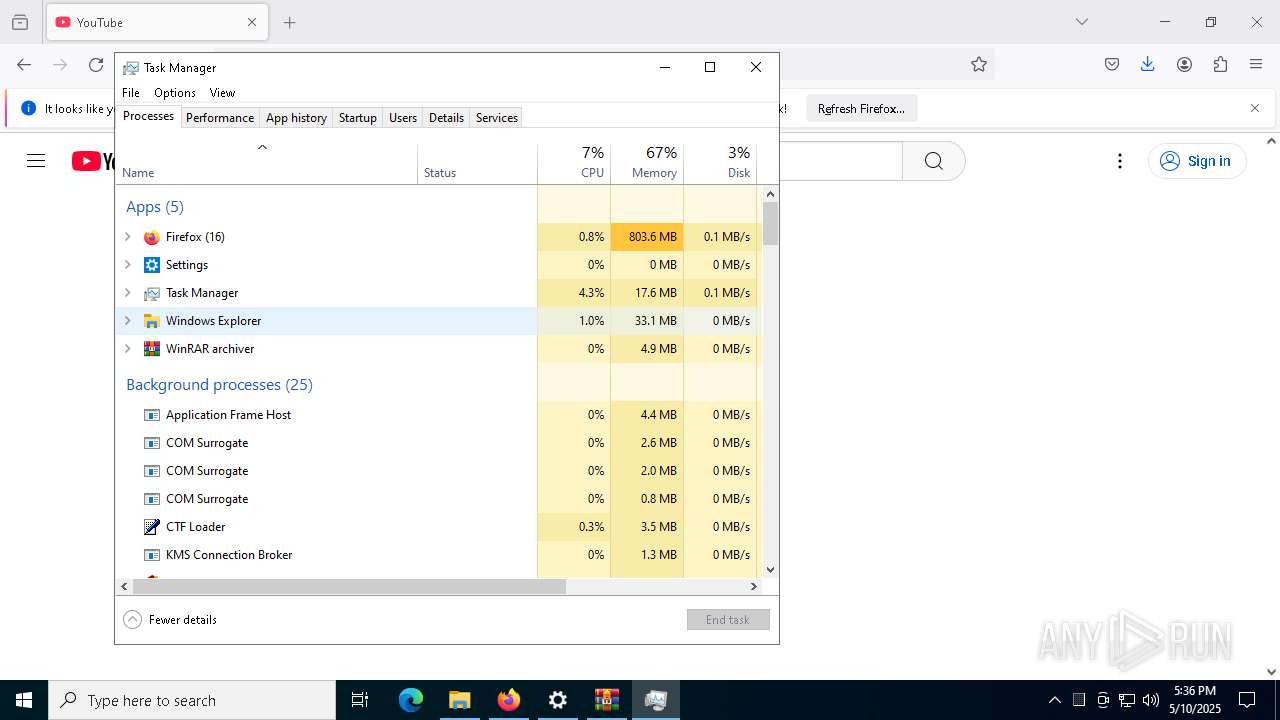
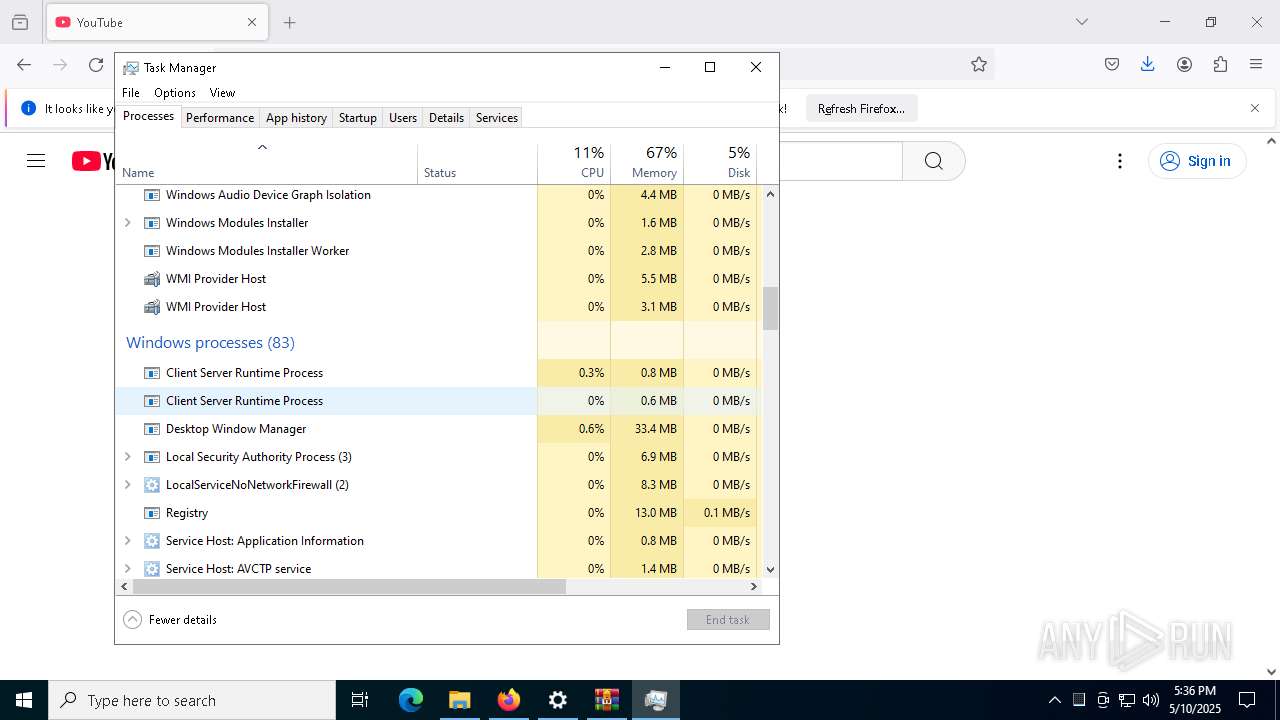
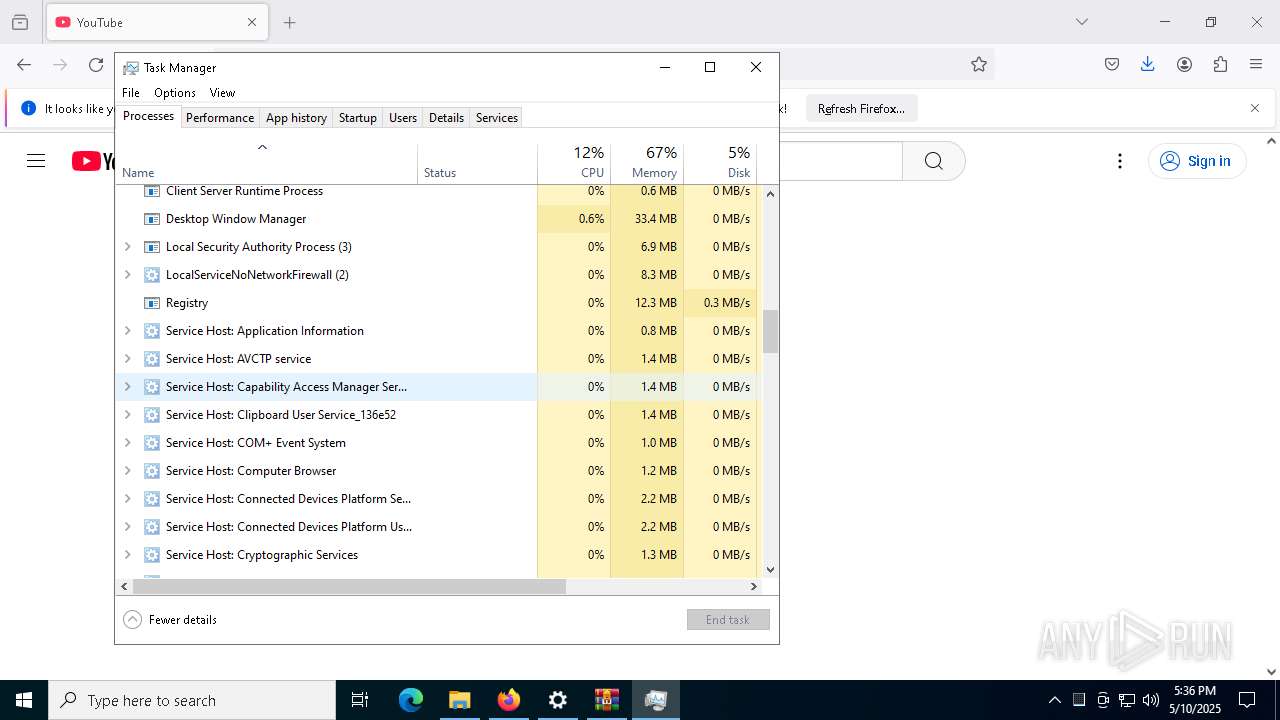
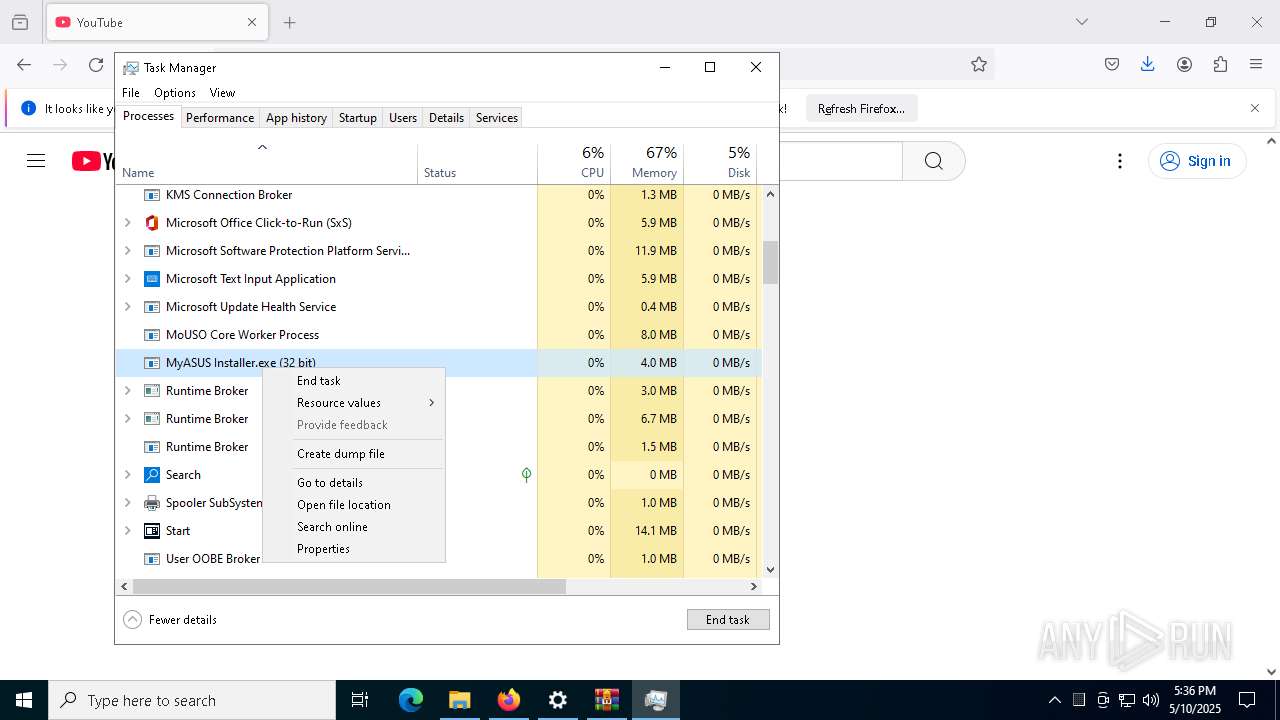
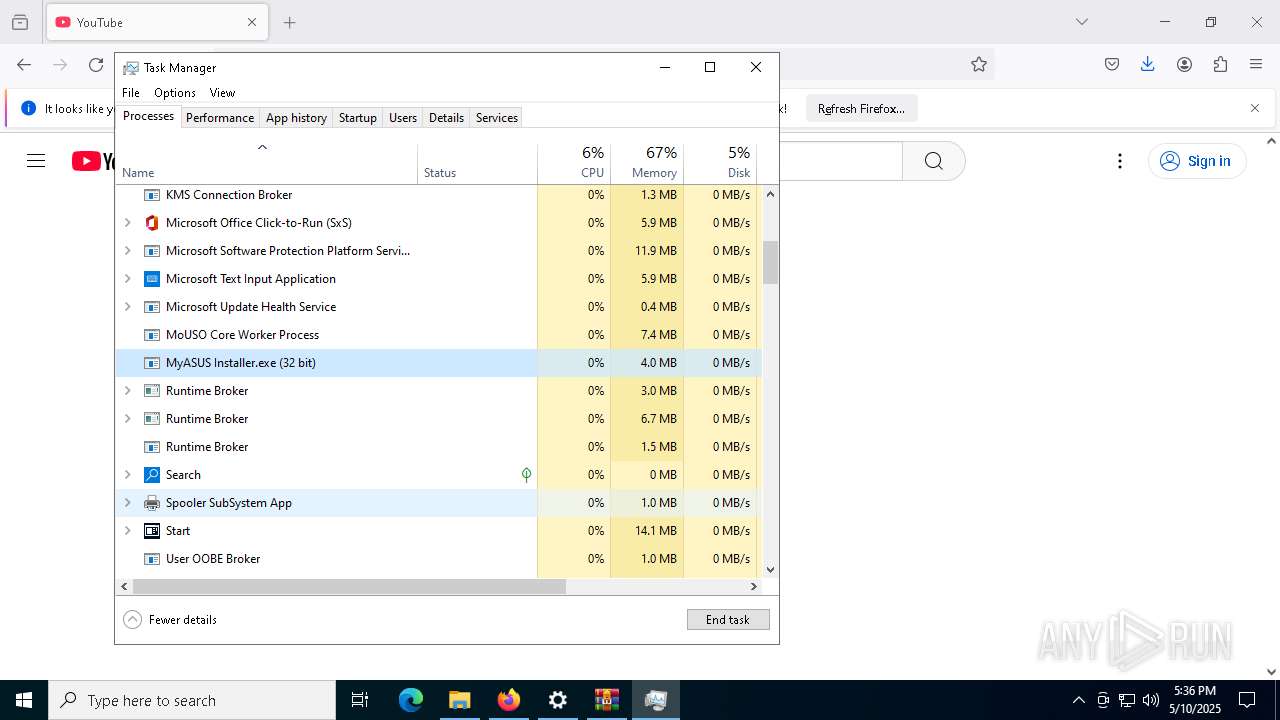
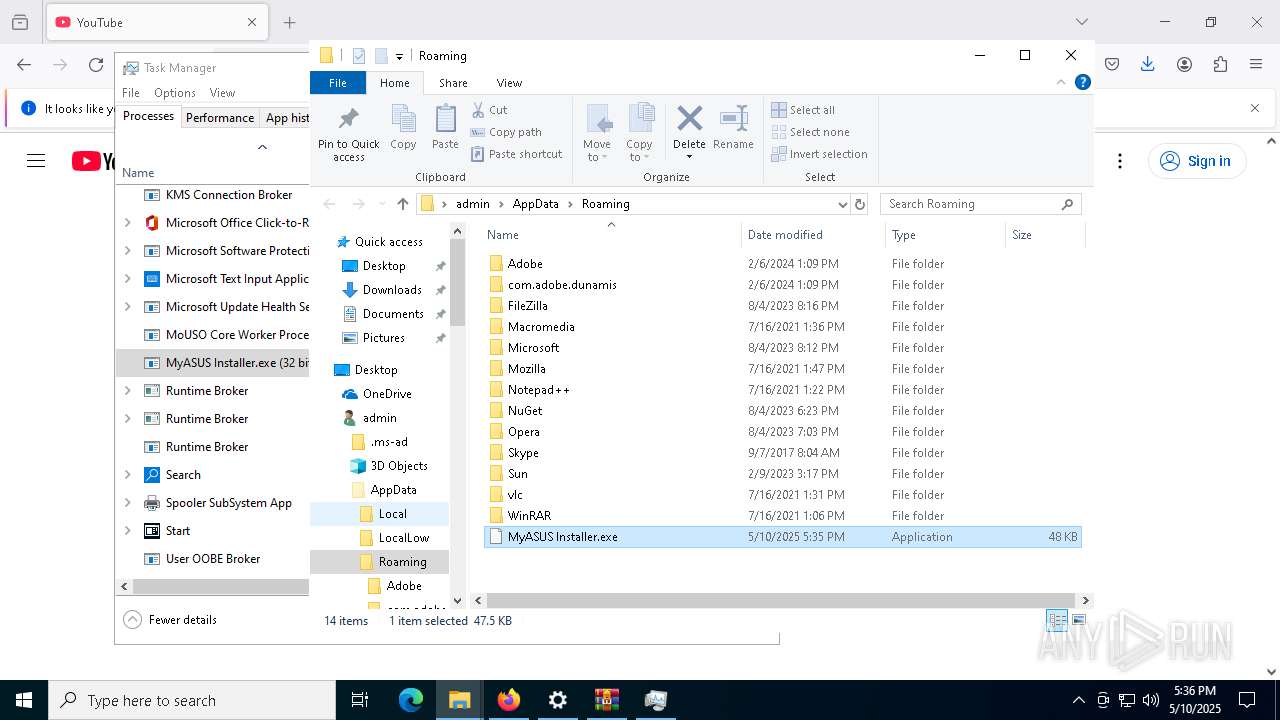
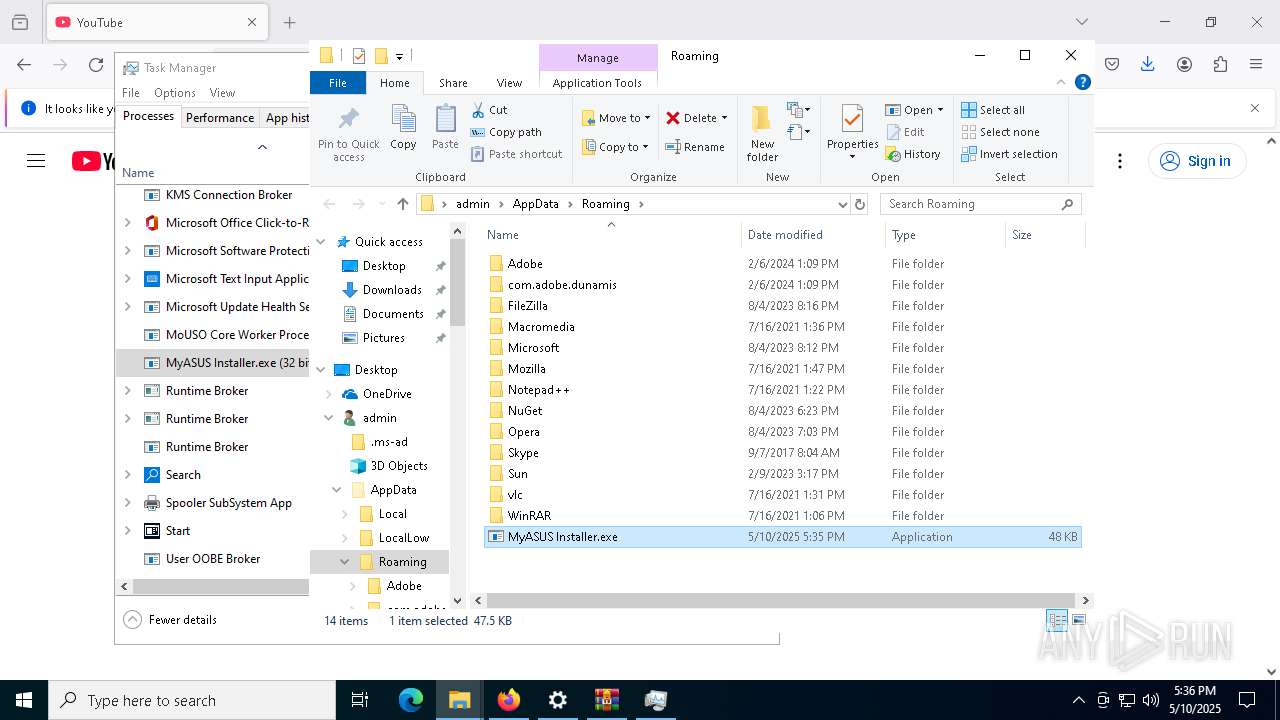
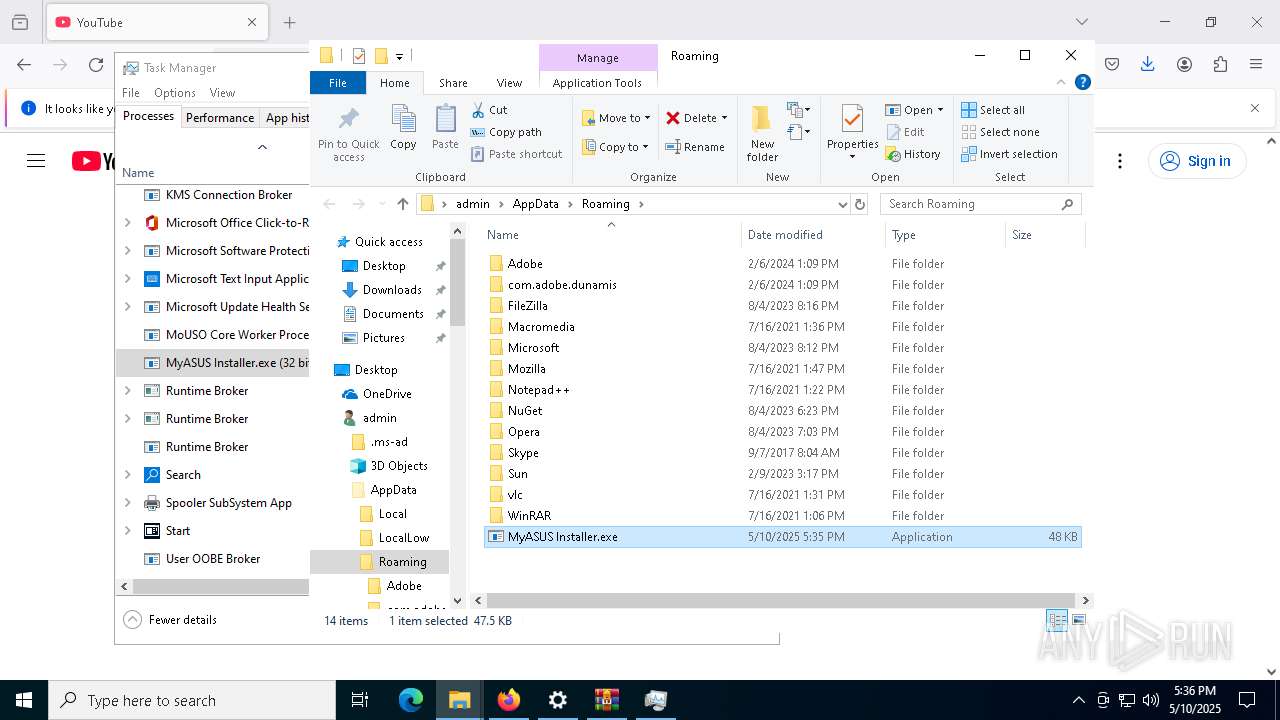
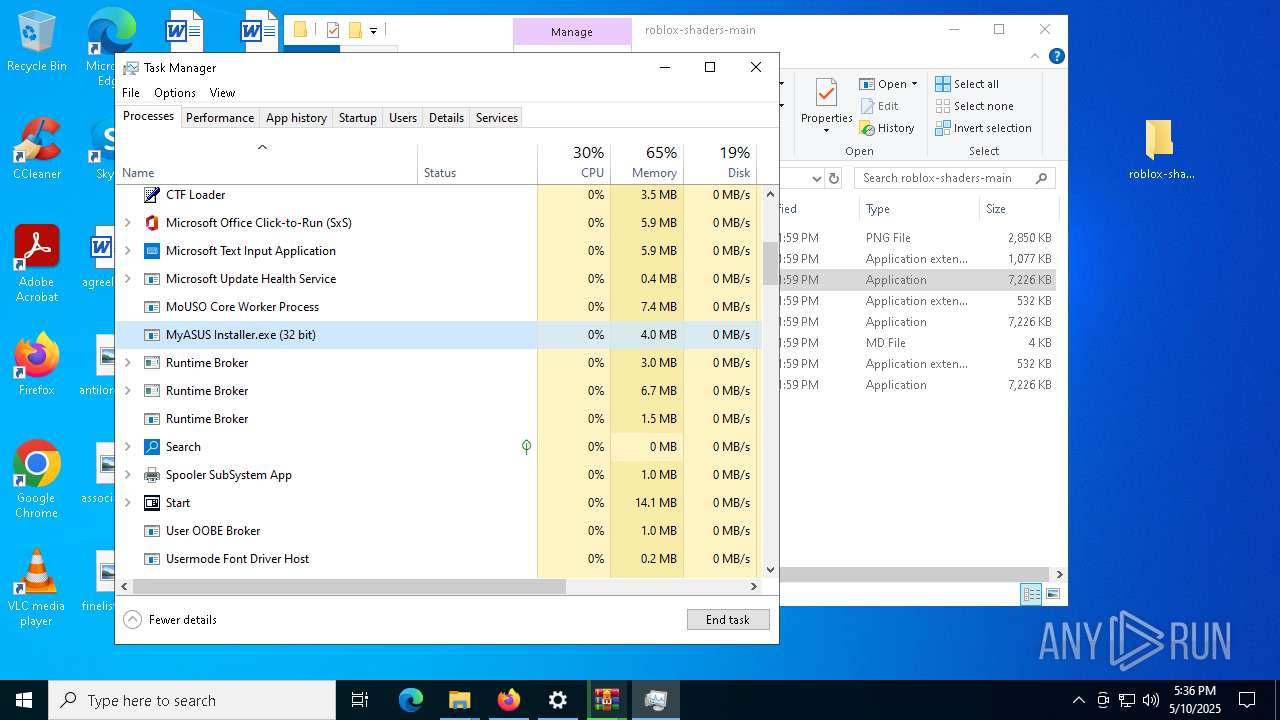
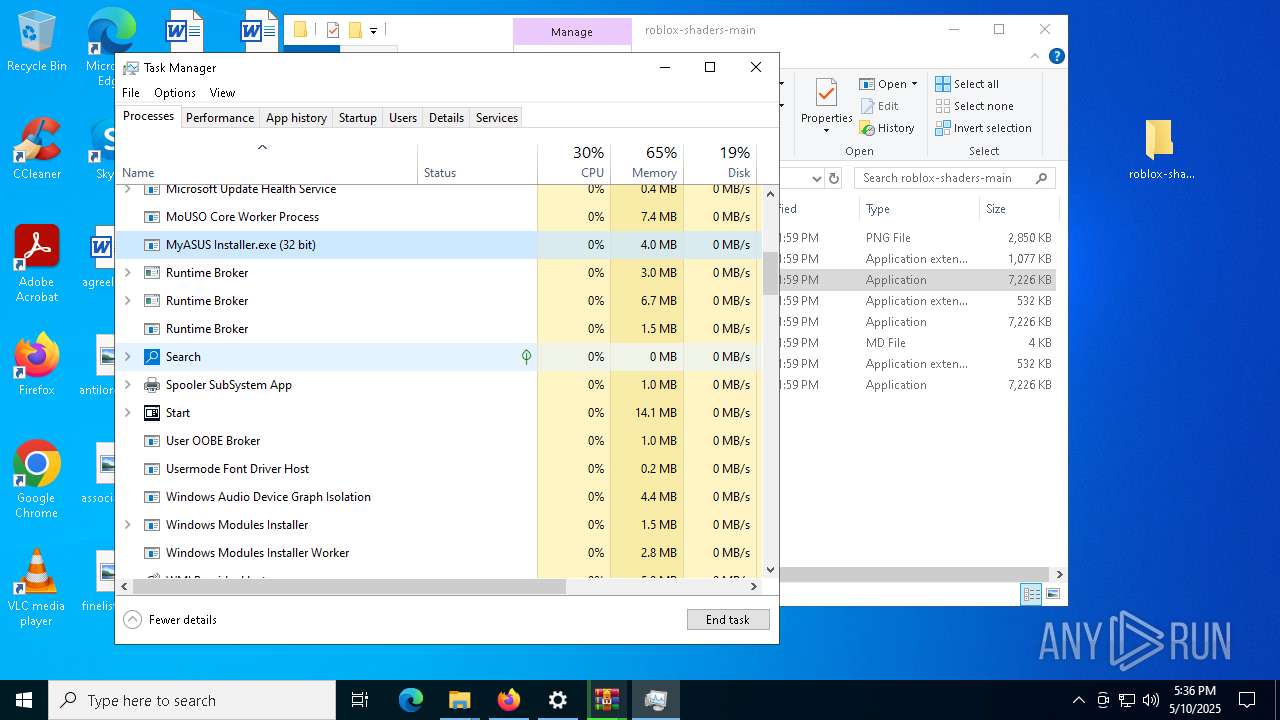
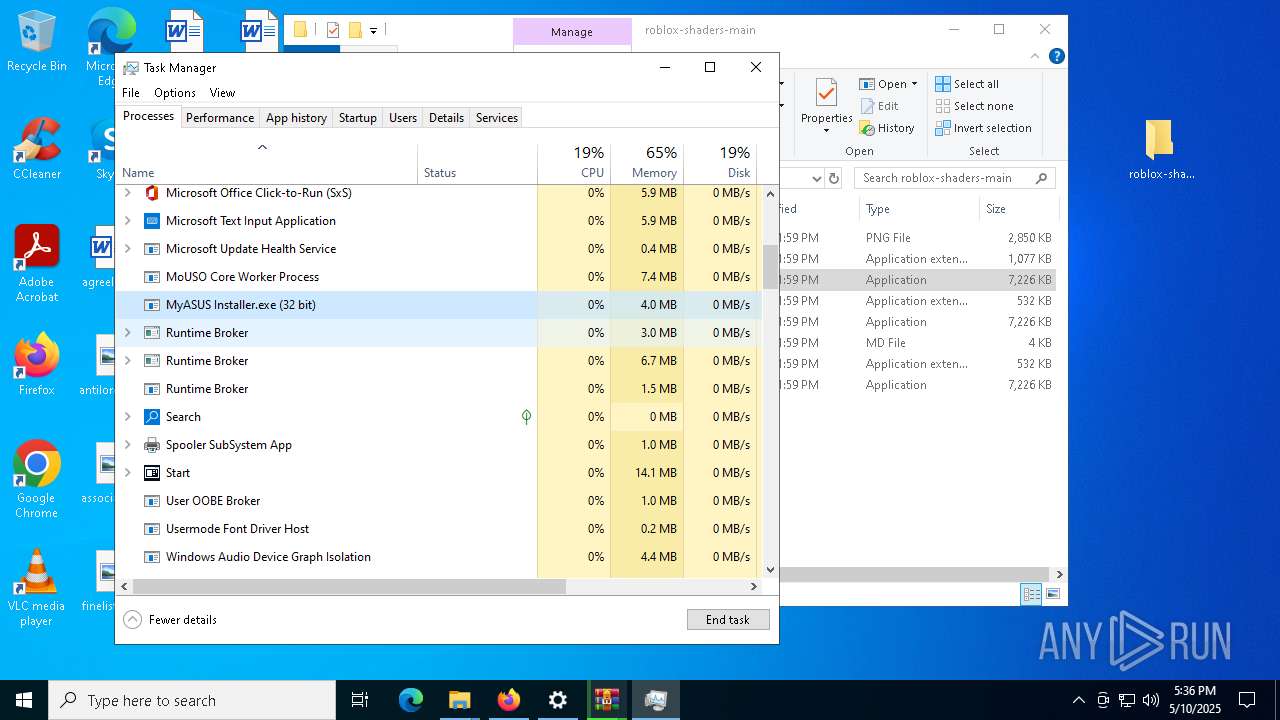
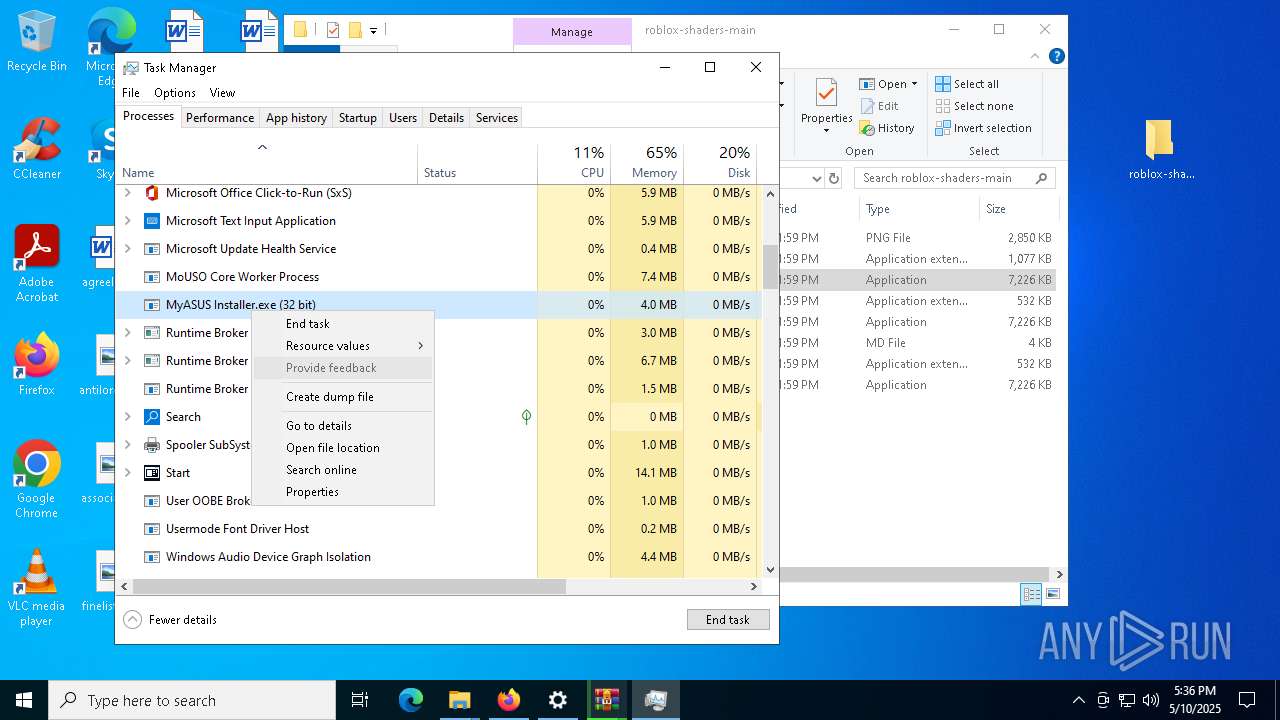
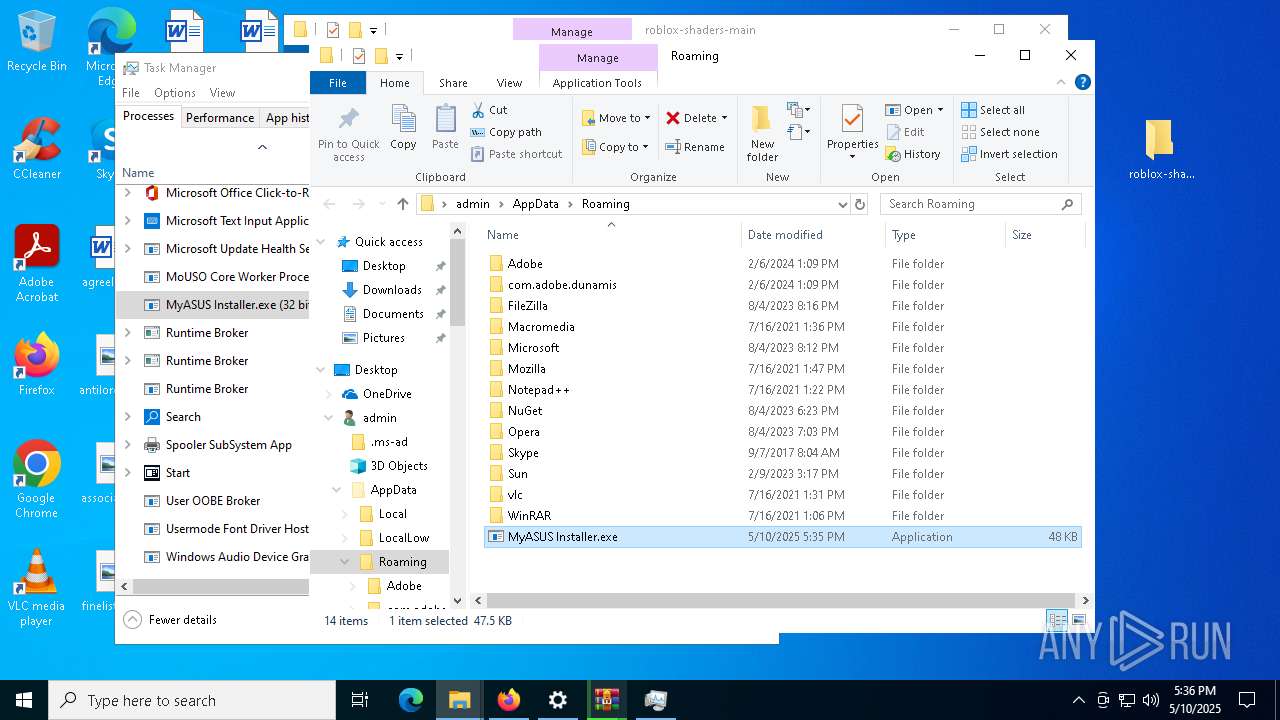
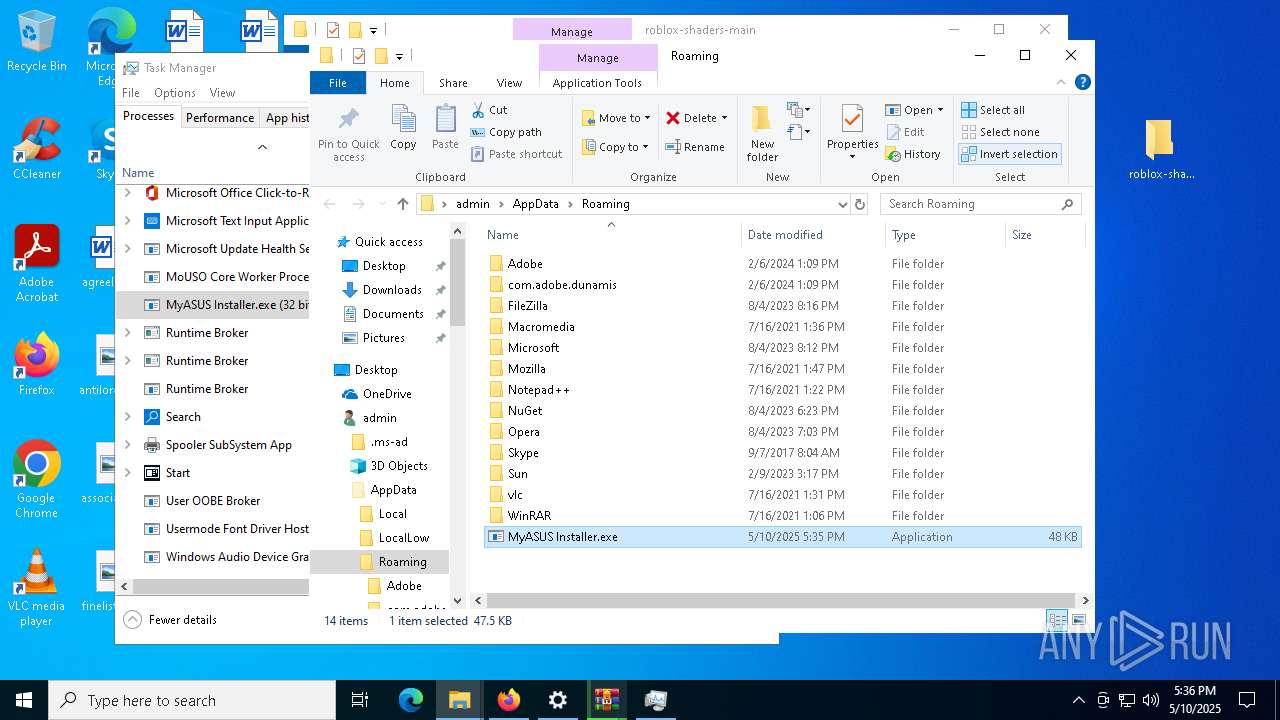
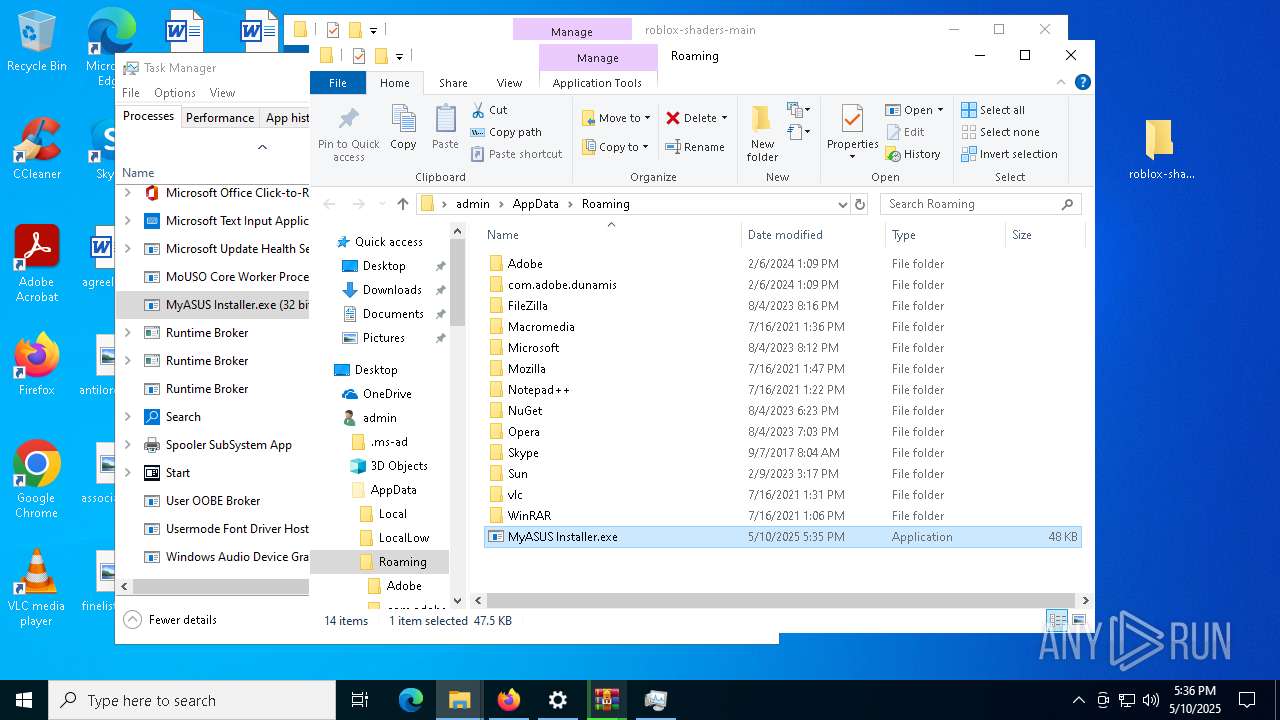
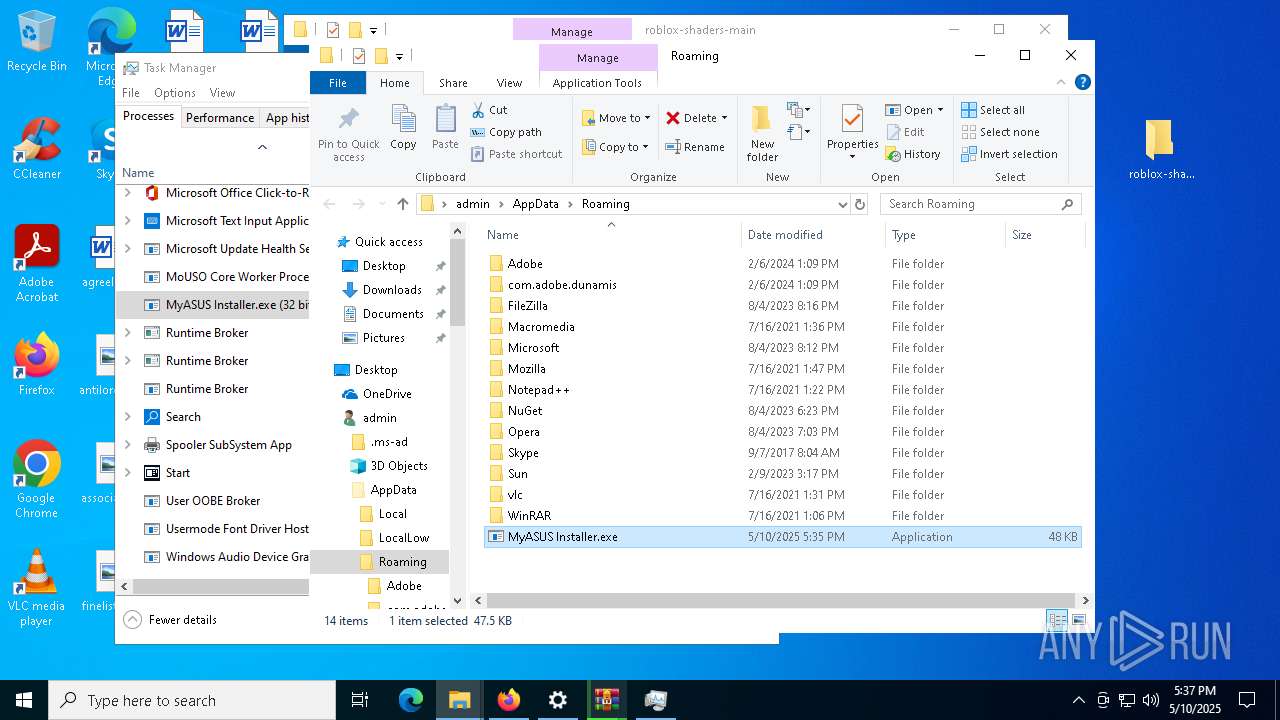
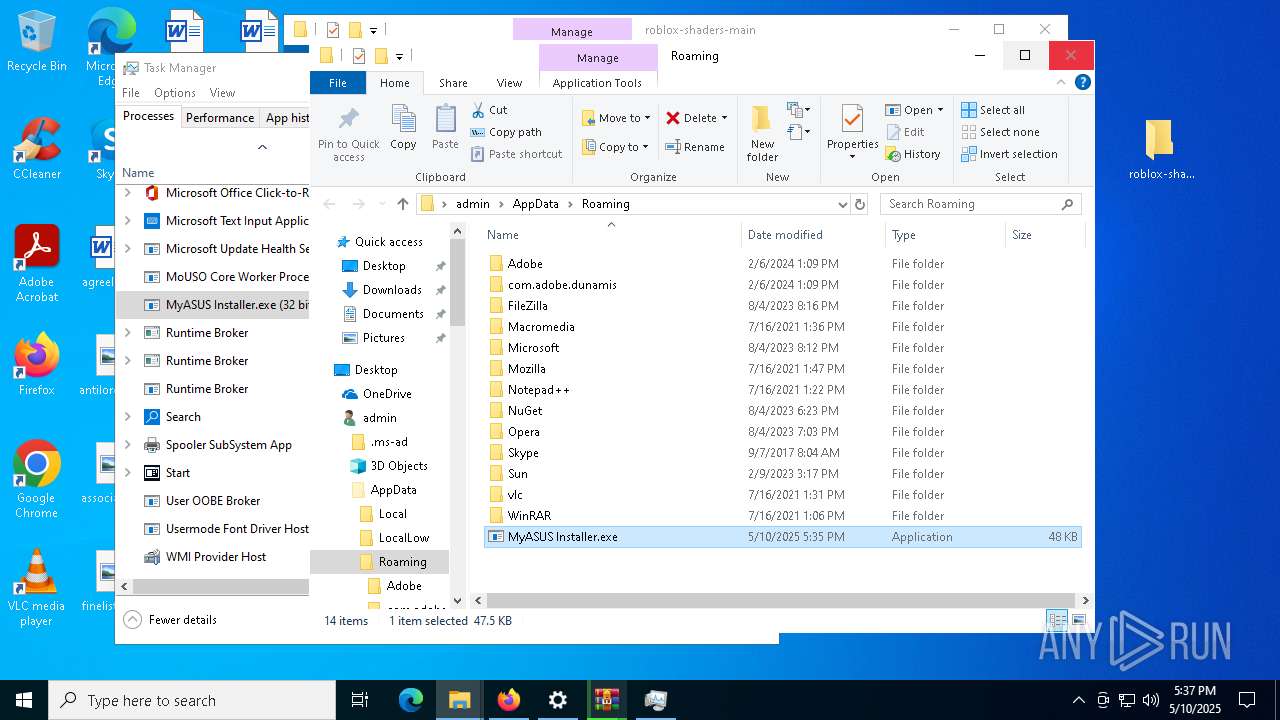
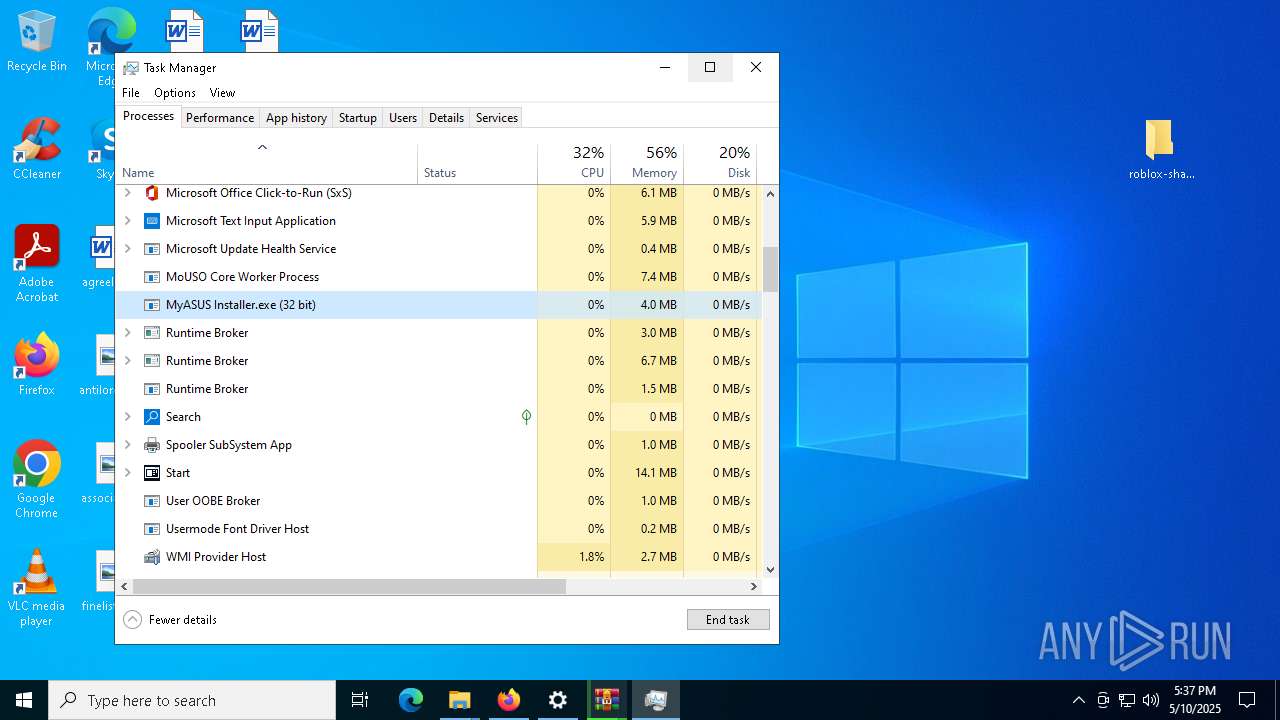
ASYNCRAT has been detected (YARA)
- MyASUS Installer.exe (PID: 5228)
BLANKGRABBER has been detected (SURICATA)
- RoShade.exe (PID: 7552)
Resets Windows Defender malware definitions to the base version
- MpCmdRun.exe (PID: 5740)
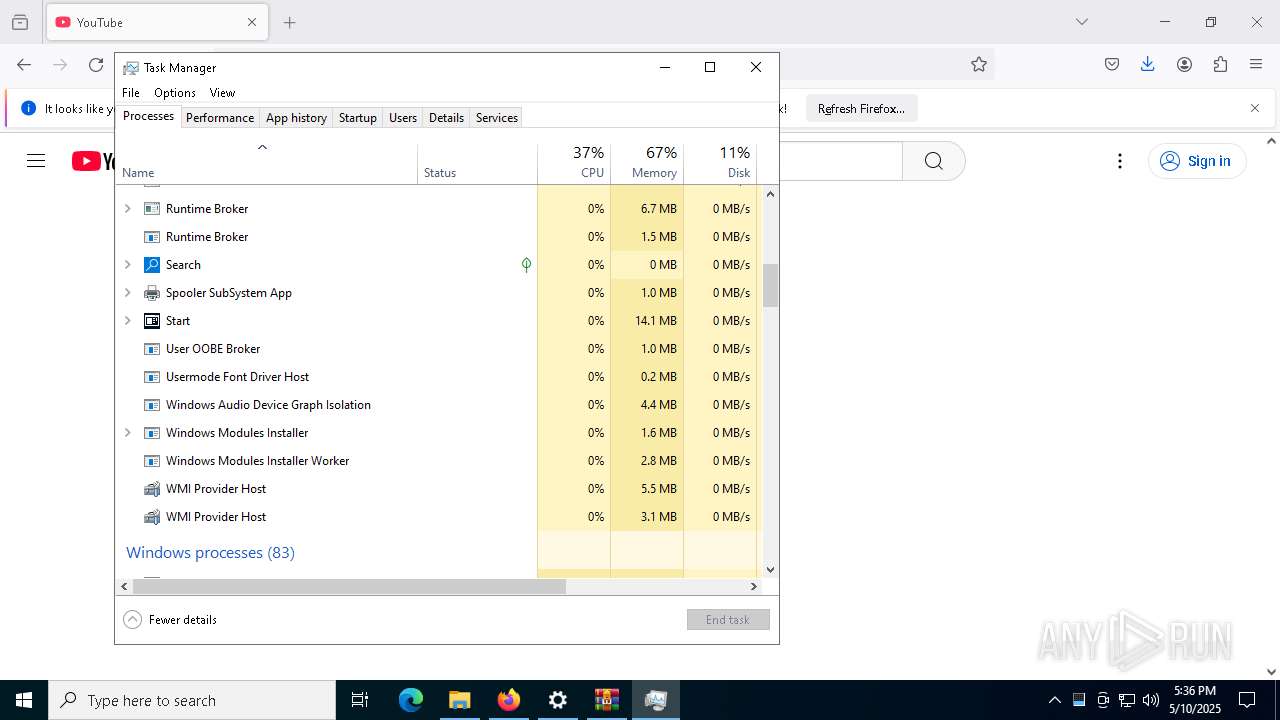
Uses Task Scheduler to run other applications
- cmd.exe (PID: 5036)
SUSPICIOUS
Reads security settings of Internet Explorer
- SecHealthUI.exe (PID: 7796)
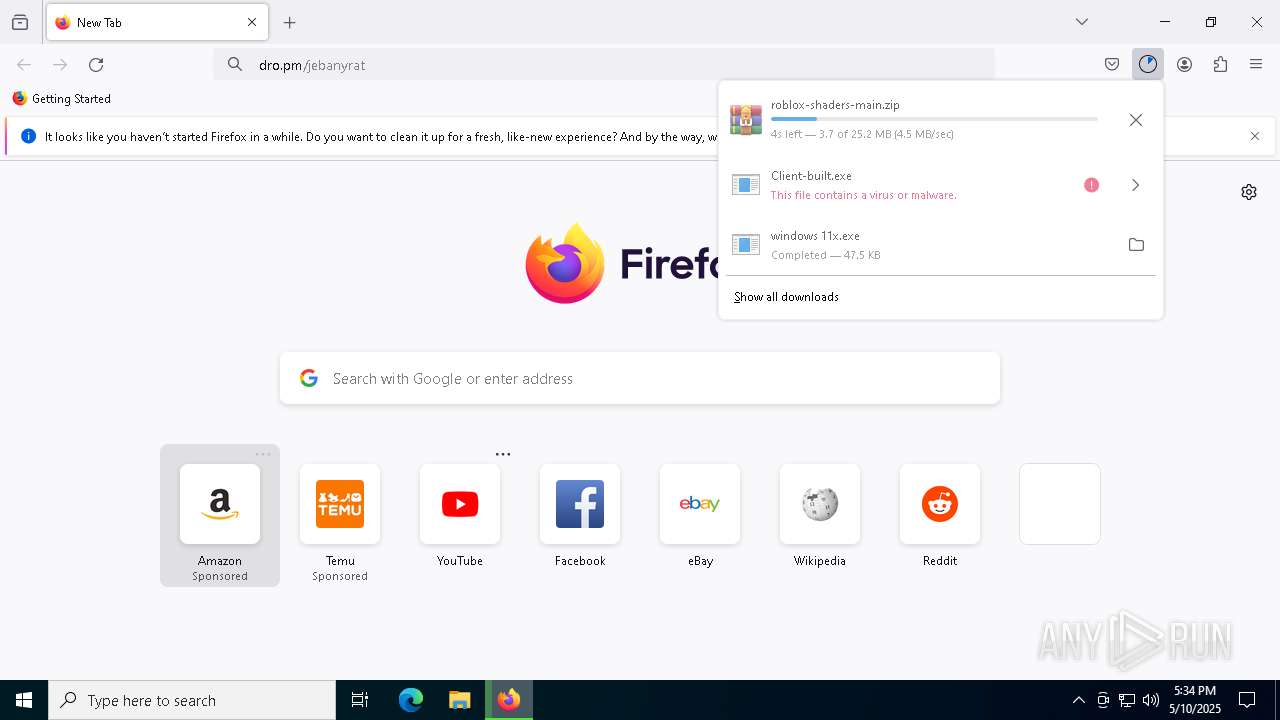
Process drops legitimate windows executable
- firefox.exe (PID: 5200)
- WinRAR.exe (PID: 2656)
- RoShade.exe (PID: 7440)
- R_BloxShades.exe (PID: 7776)
- R_FpsUnlocker.exe (PID: 3024)
- R_FpsUnlocker.exe (PID: 1616)
- RoShade.exe (PID: 7772)
- RoShade.exe (PID: 7552)
- R_BloxShades.exe (PID: 5036)
- WinRAR.exe (PID: 7324)
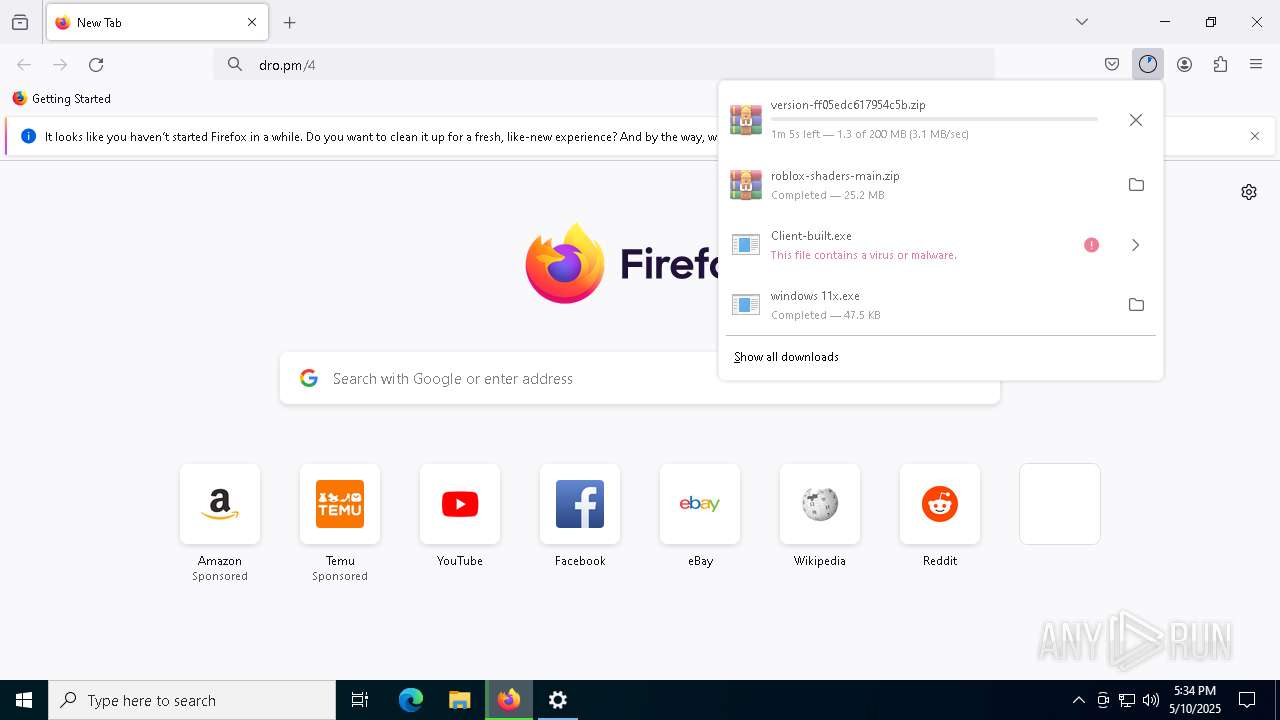
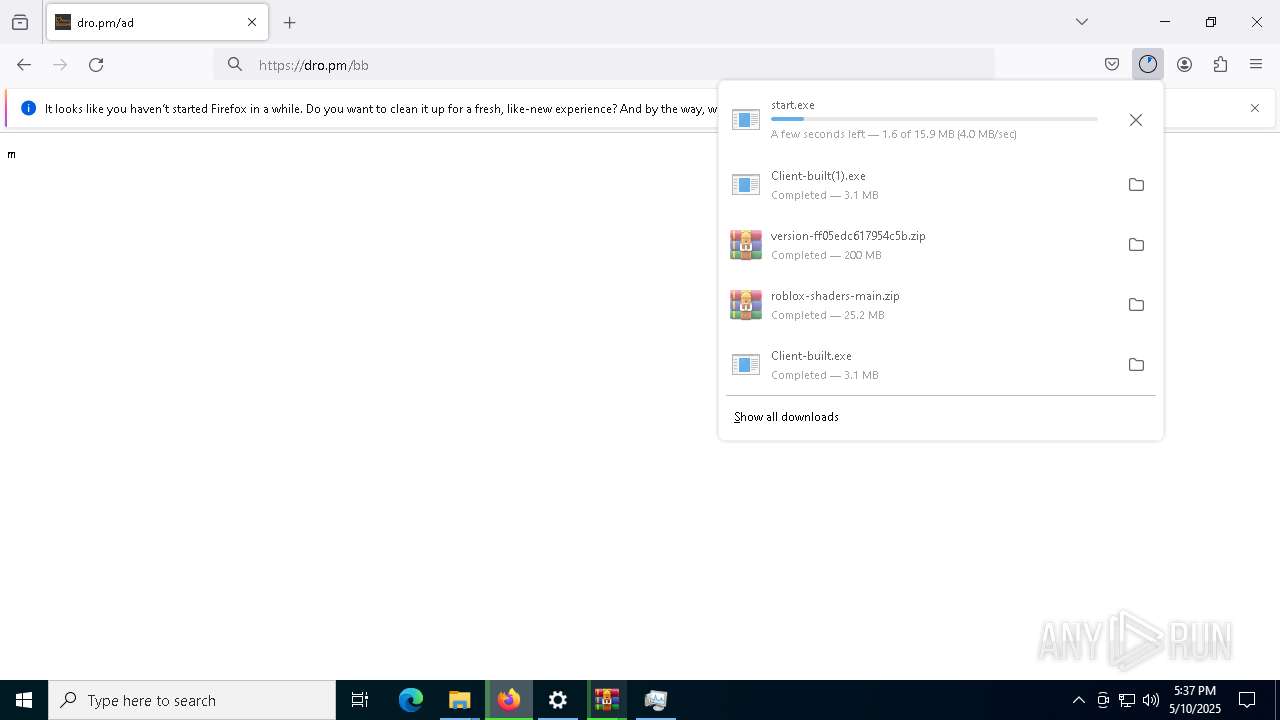
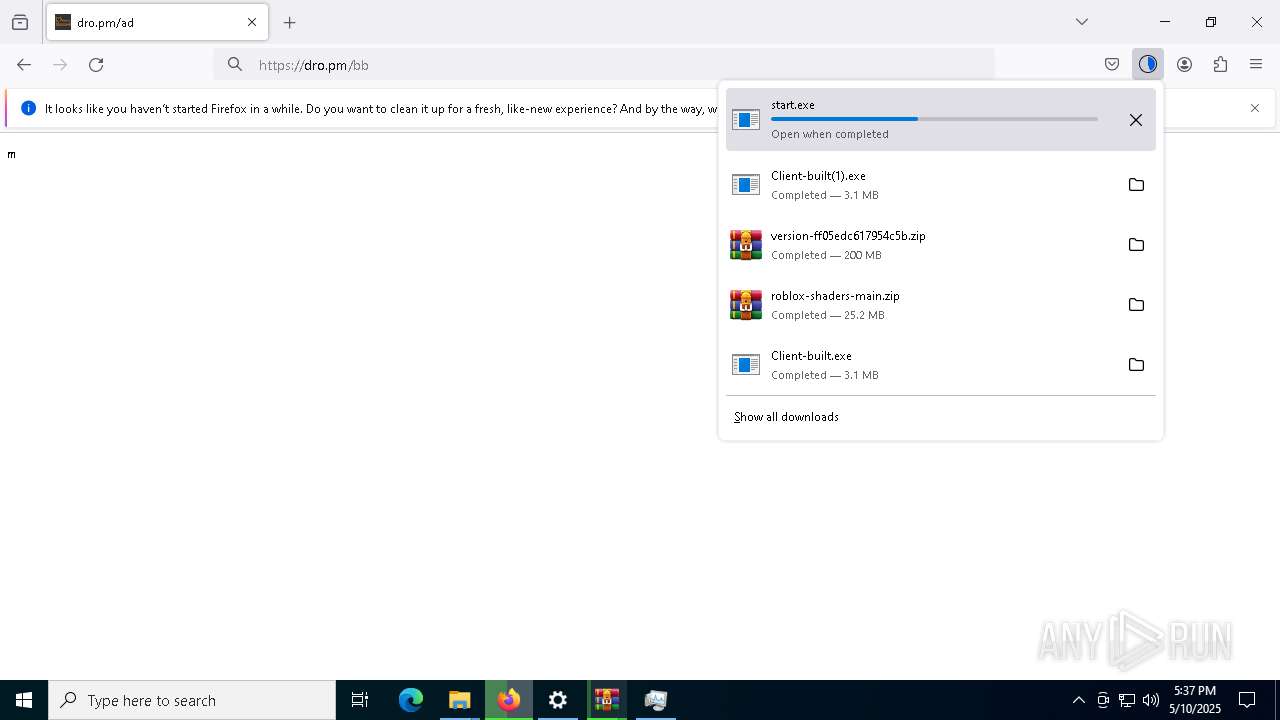
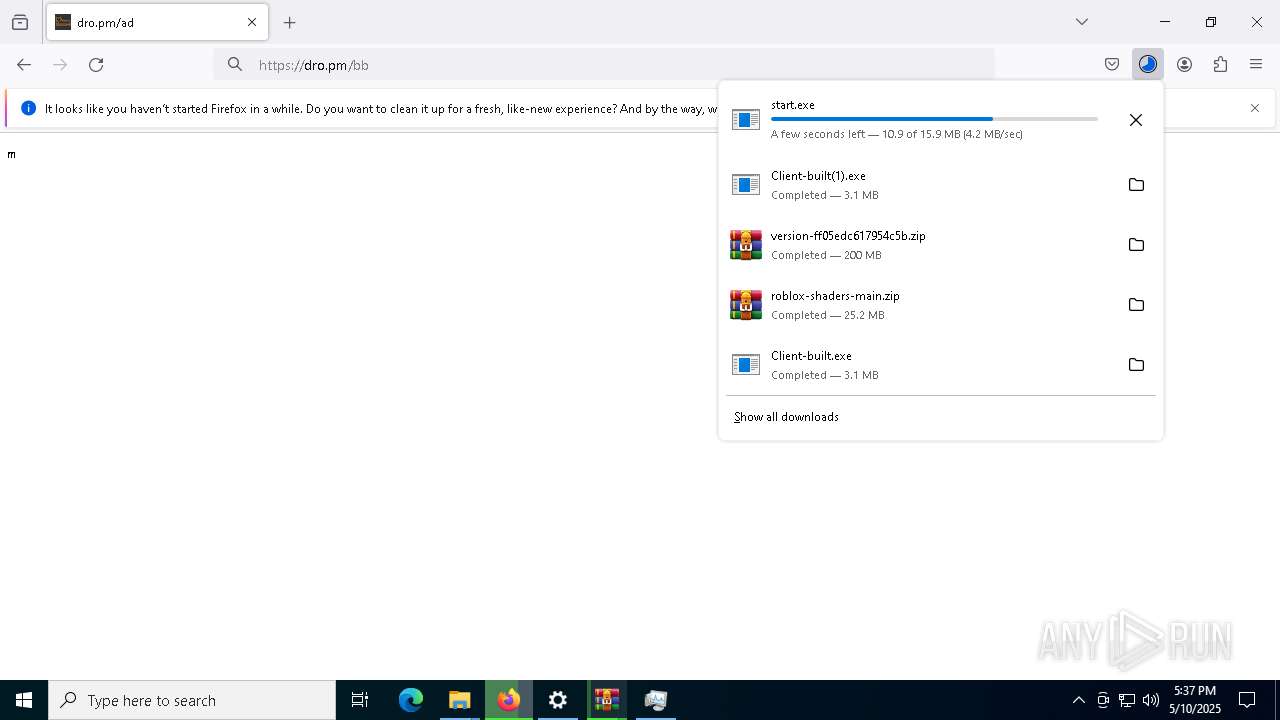
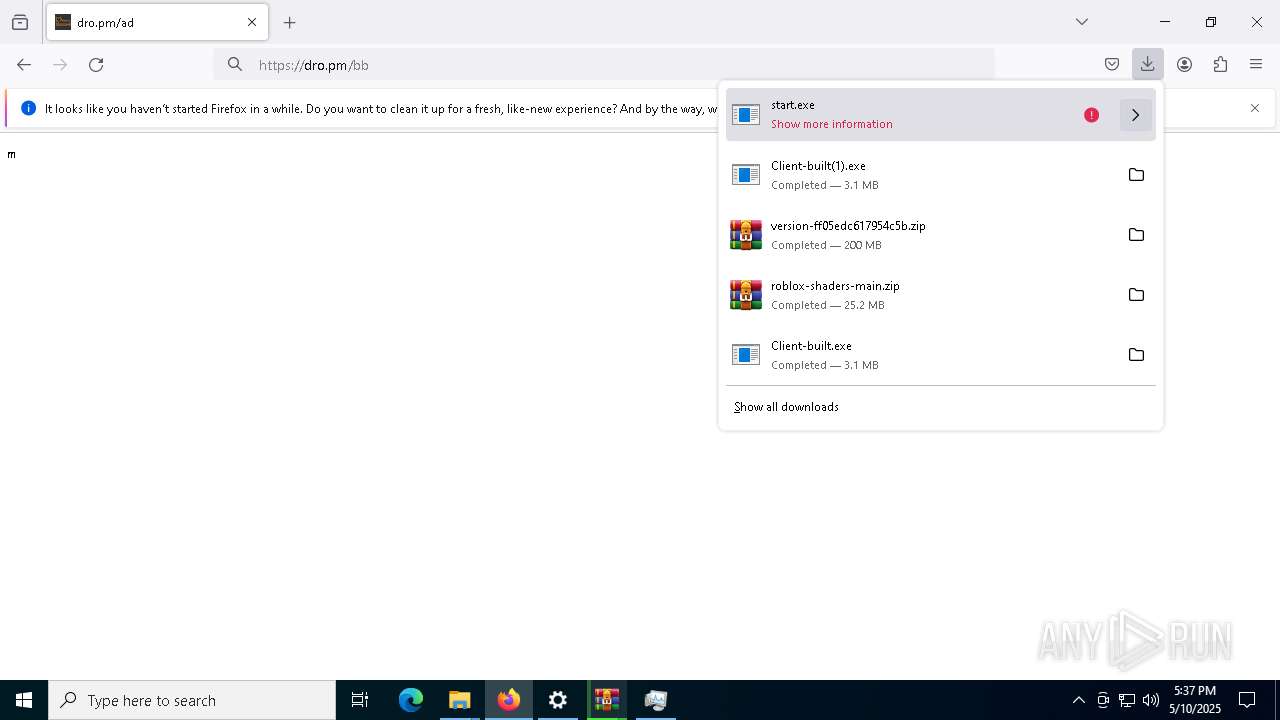
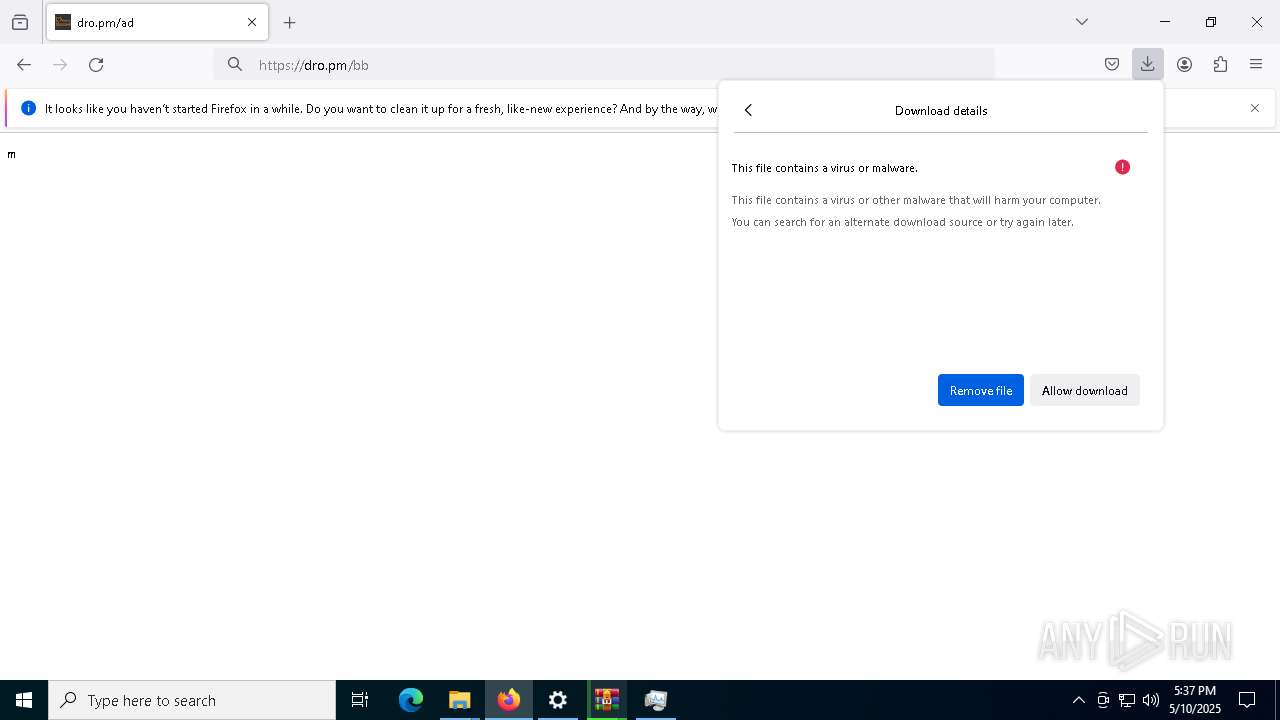
Executable content was dropped or overwritten
- windows 11x.exe (PID: 300)
- RoShade.exe (PID: 7440)
- R_FpsUnlocker.exe (PID: 3024)
- RoShade.exe (PID: 7772)
- R_FpsUnlocker.exe (PID: 1616)
- R_BloxShades.exe (PID: 7776)
- RoShade.exe (PID: 7552)
- R_BloxShades.exe (PID: 5036)
- csc.exe (PID: 8528)
- start.exe (PID: 8036)
- CL_Debug_Log.txt (PID: 7960)
Executing commands from a ".bat" file
- windows 11x.exe (PID: 300)
Uses TIMEOUT.EXE to delay execution
- cmd.exe (PID: 7572)
Cleans NTFS data stream (Zone Identifier)
- Client-built.exe (PID: 2560)
The executable file from the user directory is run by the CMD process
- MyASUS Installer.exe (PID: 5228)
- rar.exe (PID: 8440)
There is functionality for taking screenshot (YARA)
- Client-built.exe (PID: 2560)
- Client-built(1).exe (PID: 9108)
Starts CMD.EXE for commands execution
- windows 11x.exe (PID: 300)
- RoShade.exe (PID: 7552)
- start.exe (PID: 8036)
Starts a Microsoft application from unusual location
- RoShade.exe (PID: 2084)
- R_FpsUnlocker.exe (PID: 3024)
- RoShade.exe (PID: 7440)
- R_FpsUnlocker.exe (PID: 7928)
- RoShade.exe (PID: 7772)
- R_BloxShades.exe (PID: 7776)
- R_BloxShades.exe (PID: 7936)
- RoShade.exe (PID: 7552)
- R_FpsUnlocker.exe (PID: 1616)
- R_FpsUnlocker.exe (PID: 6028)
- R_BloxShades.exe (PID: 5036)
- R_BloxShades.exe (PID: 8548)
Process drops python dynamic module
- RoShade.exe (PID: 7440)
- R_BloxShades.exe (PID: 7776)
- R_FpsUnlocker.exe (PID: 3024)
- RoShade.exe (PID: 7772)
- R_FpsUnlocker.exe (PID: 1616)
- R_BloxShades.exe (PID: 5036)
Application launched itself
- RoShade.exe (PID: 7440)
- RoShade.exe (PID: 2084)
- R_FpsUnlocker.exe (PID: 3024)
- R_BloxShades.exe (PID: 7776)
- R_FpsUnlocker.exe (PID: 7928)
- RoShade.exe (PID: 7772)
- R_FpsUnlocker.exe (PID: 1616)
- R_BloxShades.exe (PID: 7936)
- R_BloxShades.exe (PID: 5036)
- Helper.exe (PID: 6344)
The process drops C-runtime libraries
- RoShade.exe (PID: 7440)
- R_BloxShades.exe (PID: 7776)
- RoShade.exe (PID: 7772)
- R_FpsUnlocker.exe (PID: 3024)
- R_FpsUnlocker.exe (PID: 1616)
- R_BloxShades.exe (PID: 5036)
Found strings related to reading or modifying Windows Defender settings
- RoShade.exe (PID: 7552)
Script disables Windows Defender's real-time protection
- cmd.exe (PID: 2980)
Script disables Windows Defender's IPS
- cmd.exe (PID: 2980)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 2980)
- cmd.exe (PID: 6080)
- cmd.exe (PID: 8080)
- cmd.exe (PID: 8220)
- cmd.exe (PID: 132)
- cmd.exe (PID: 5740)
- cmd.exe (PID: 7820)
- cmd.exe (PID: 6632)
- cmd.exe (PID: 8324)
Script adds exclusion path to Windows Defender
- cmd.exe (PID: 6080)
- cmd.exe (PID: 8080)
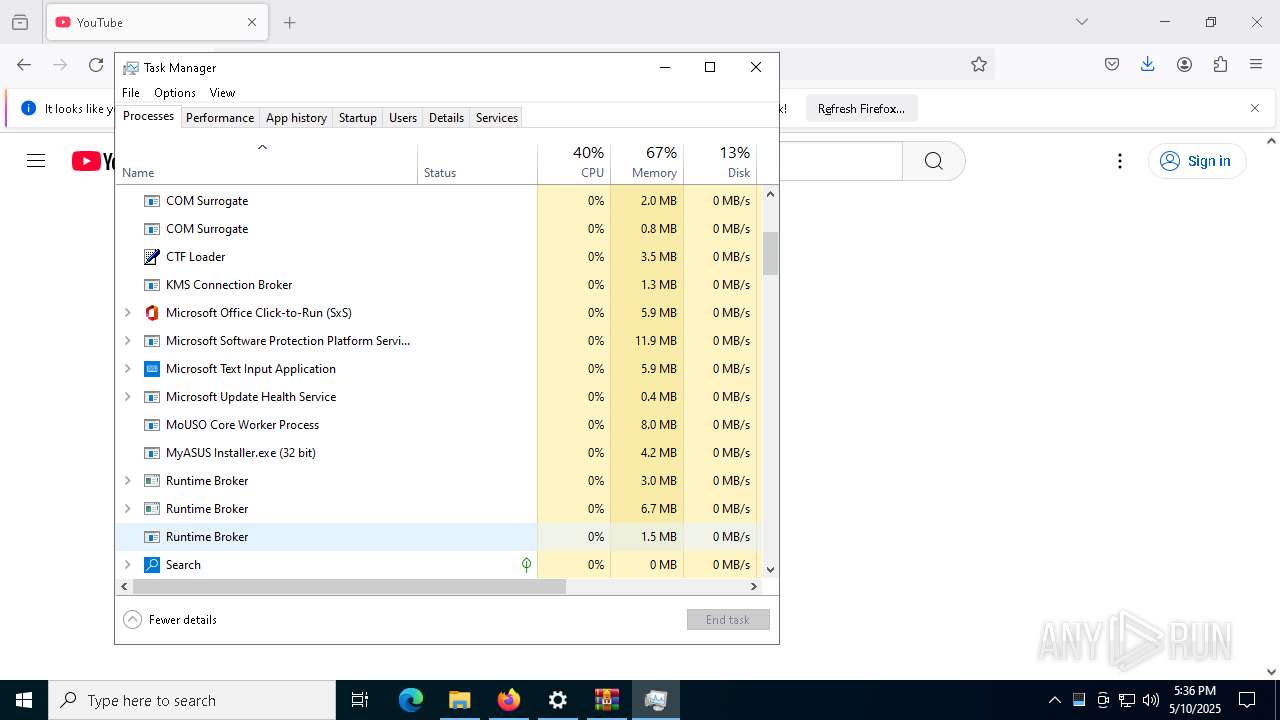
Get information on the list of running processes
- RoShade.exe (PID: 7552)
- cmd.exe (PID: 6876)
- cmd.exe (PID: 3016)
- cmd.exe (PID: 7960)
The process bypasses the loading of PowerShell profile settings
- cmd.exe (PID: 8220)
Uses WMIC.EXE to obtain Windows Installer data
- cmd.exe (PID: 5260)
- cmd.exe (PID: 9140)
Starts application with an unusual extension
- cmd.exe (PID: 5020)
- cmd.exe (PID: 8652)
- cmd.exe (PID: 8944)
- cmd.exe (PID: 9156)
- cmd.exe (PID: 5952)
- cmd.exe (PID: 8780)
- start.exe (PID: 8036)
BASE64 encoded PowerShell command has been detected
- cmd.exe (PID: 8220)
Base64-obfuscated command line is found
- cmd.exe (PID: 8220)
Connects to unusual port
- MyASUS Installer.exe (PID: 5228)
CSC.EXE is used to compile C# code
- csc.exe (PID: 8528)
Uses NETSH.EXE to obtain data on the network
- cmd.exe (PID: 7000)
Uses SYSTEMINFO.EXE to read the environment
- cmd.exe (PID: 7144)
Uses WMIC.EXE to obtain operating system information
- cmd.exe (PID: 8228)
Uses WMIC.EXE to obtain computer system information
- cmd.exe (PID: 9128)
Uses WMIC.EXE to obtain a list of video controllers
- cmd.exe (PID: 2980)
Checks for external IP
- svchost.exe (PID: 2196)
- RoShade.exe (PID: 7552)
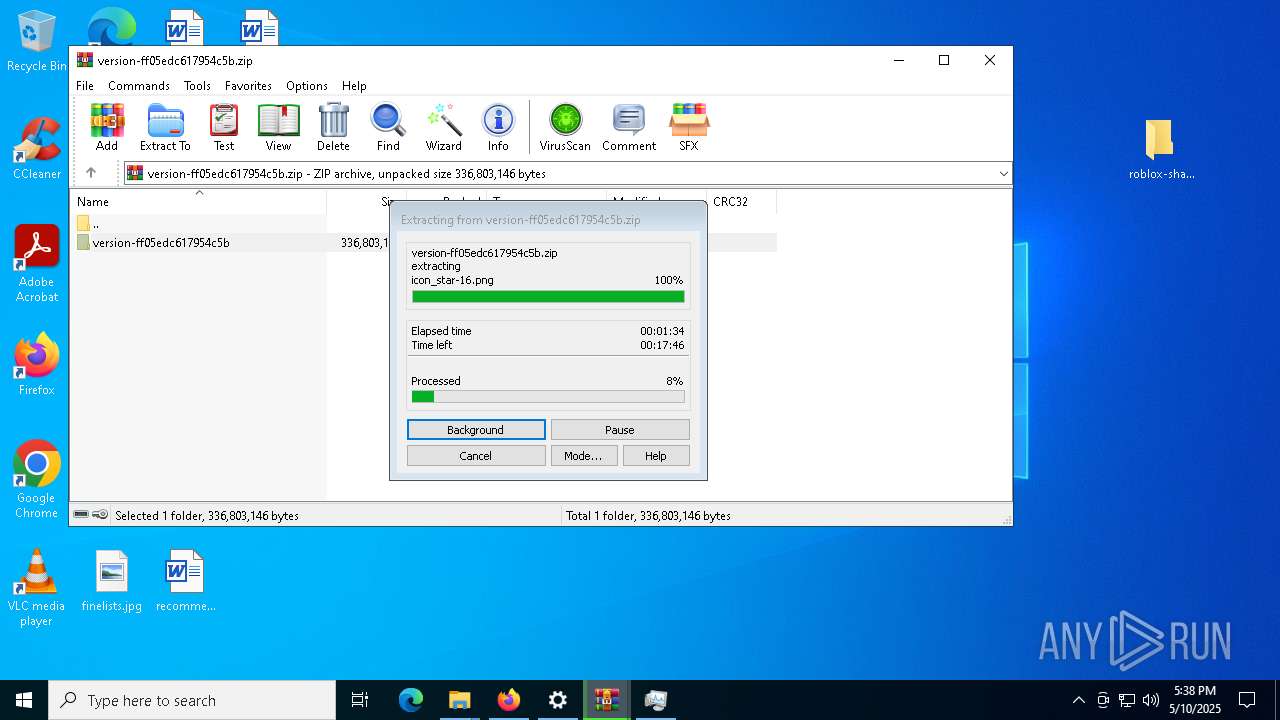
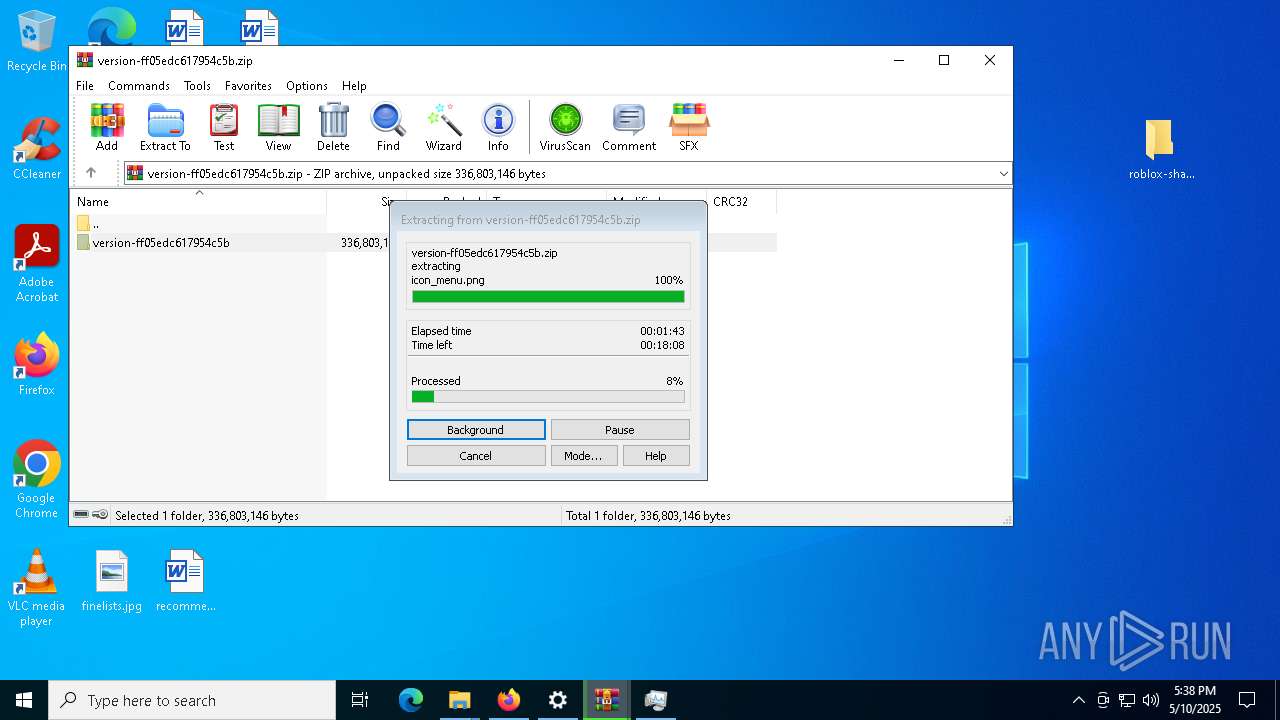
Drops 7-zip archiver for unpacking
- start.exe (PID: 8036)
The process executes via Task Scheduler
- Helper.exe (PID: 6344)
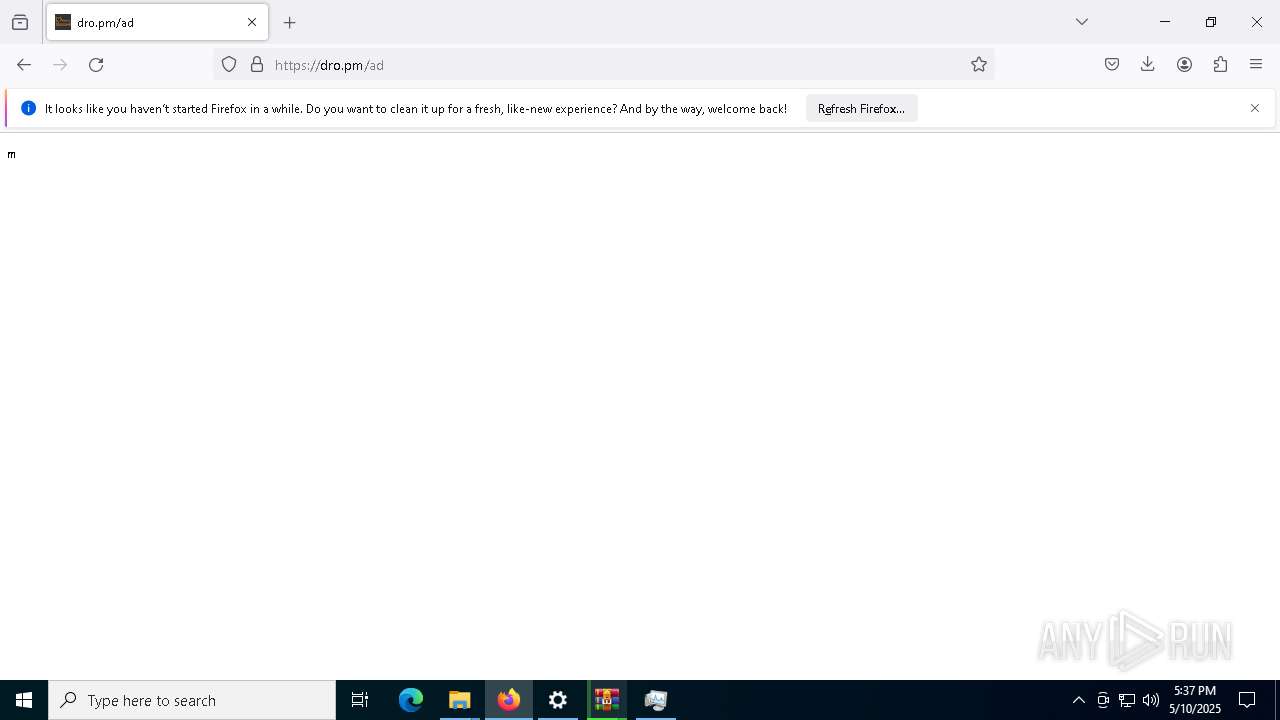
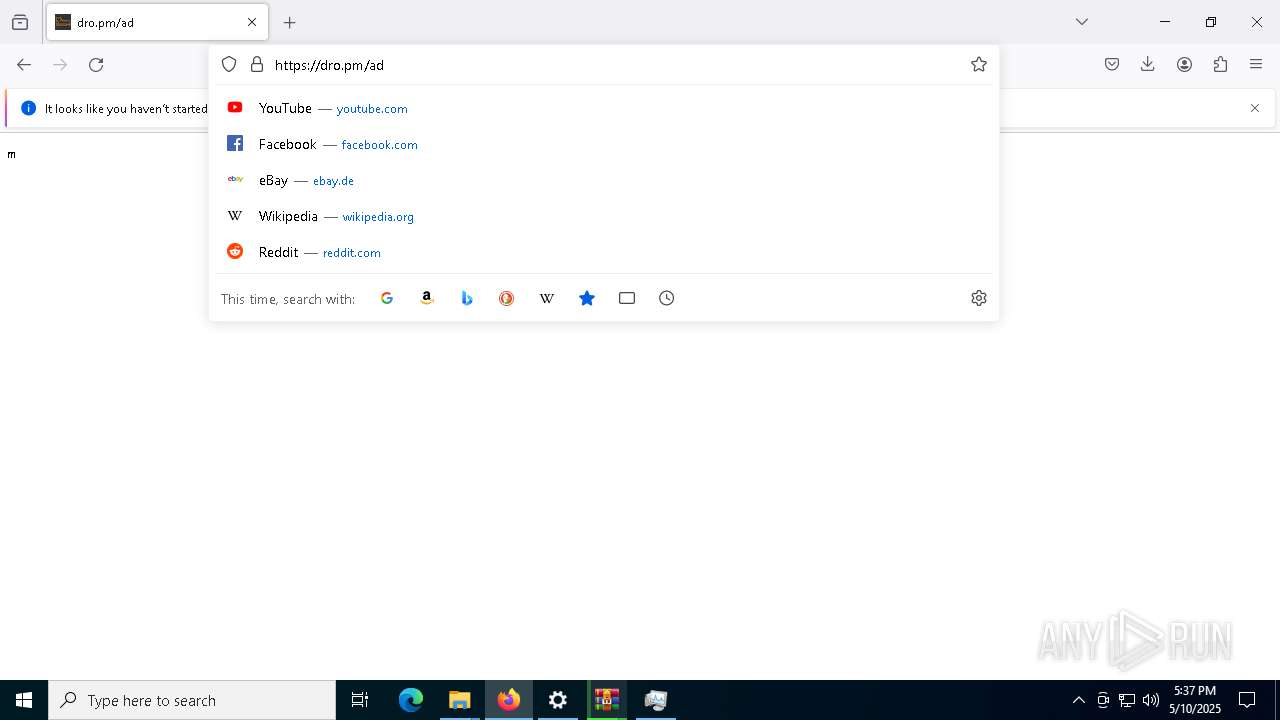
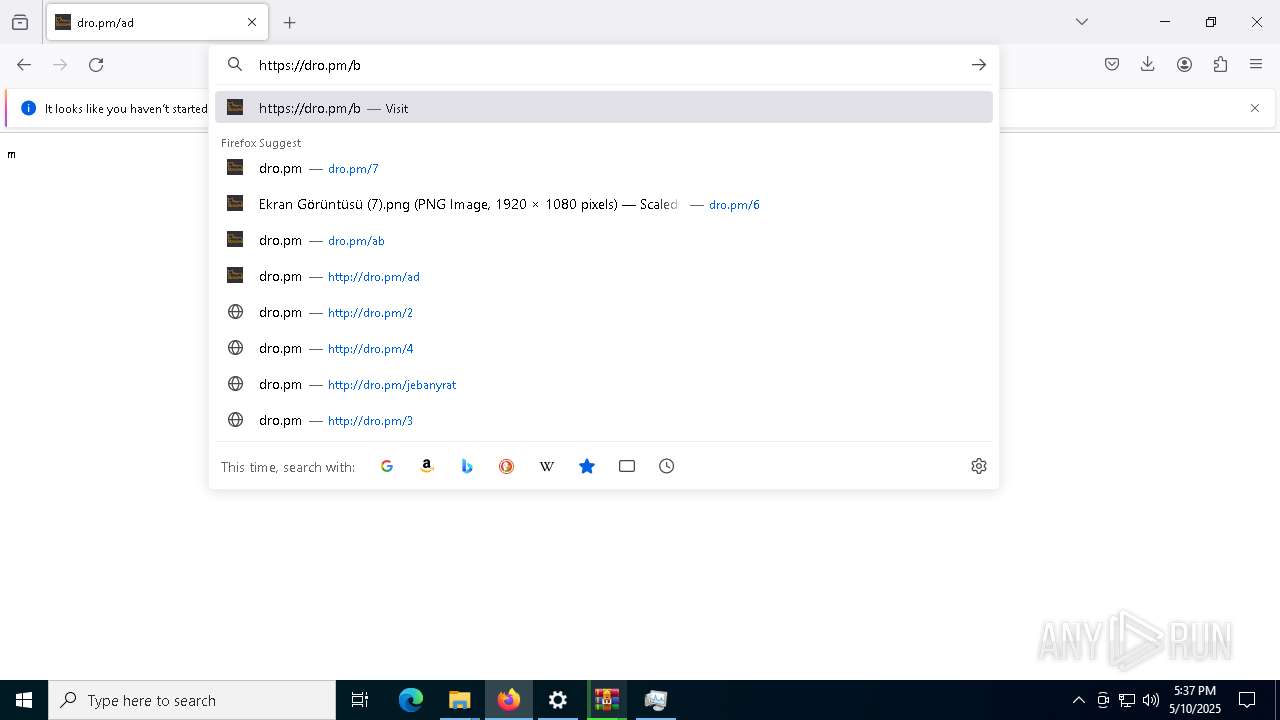
INFO
Application launched itself
- firefox.exe (PID: 456)
- firefox.exe (PID: 5200)
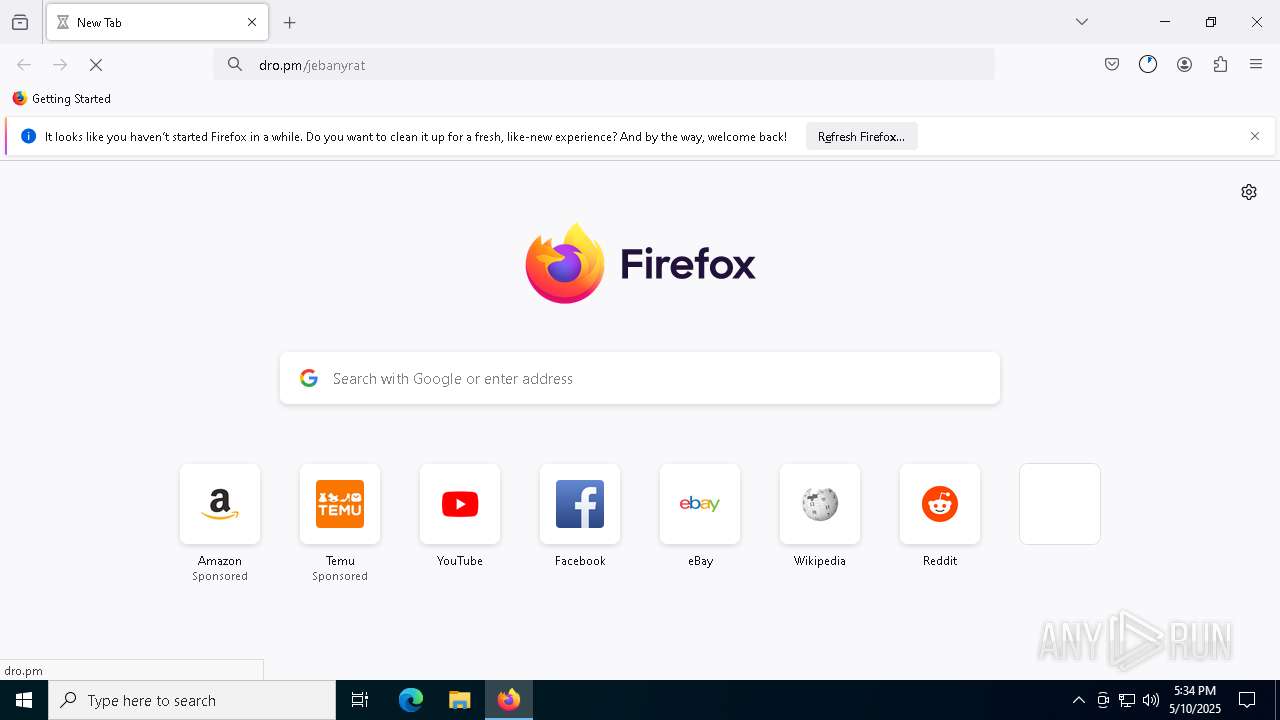
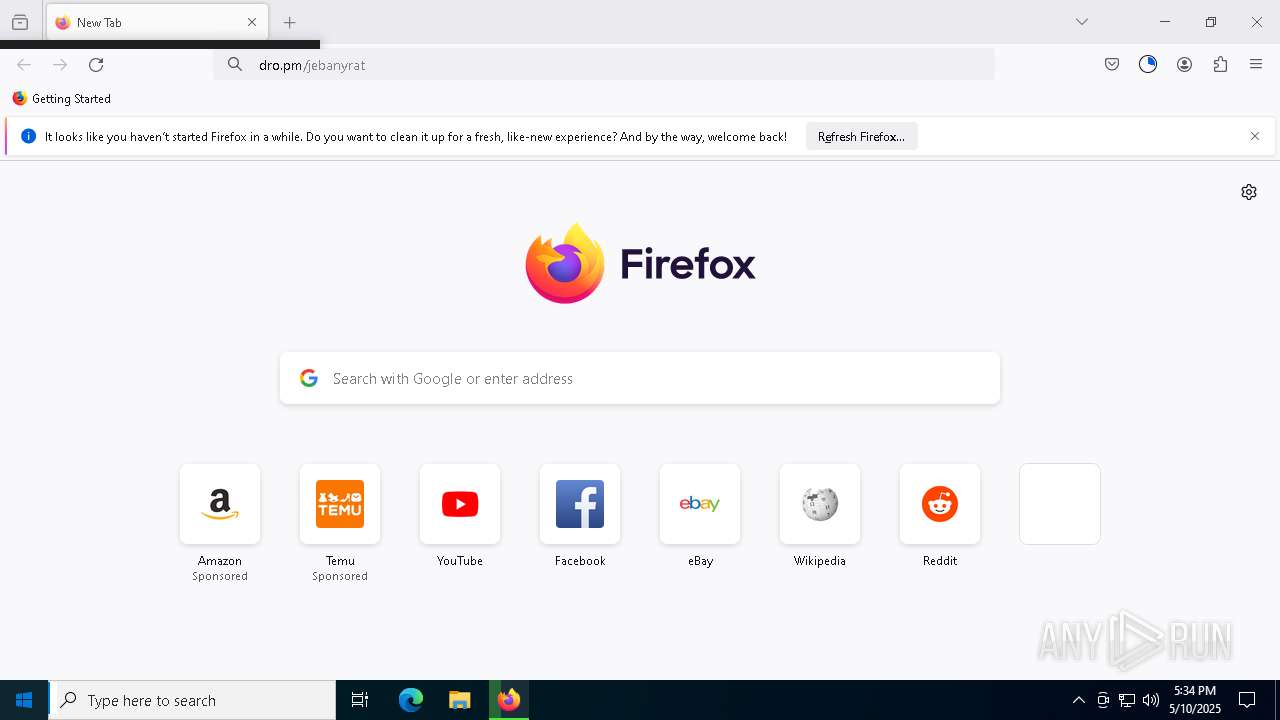
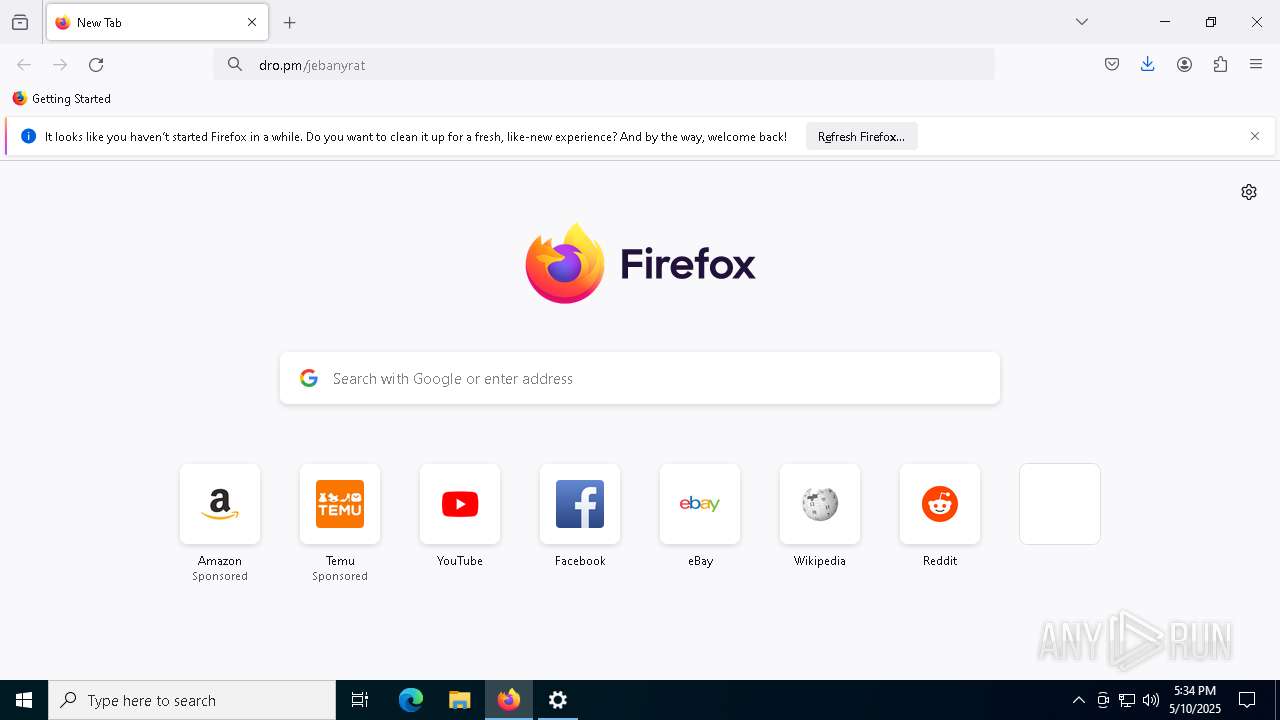
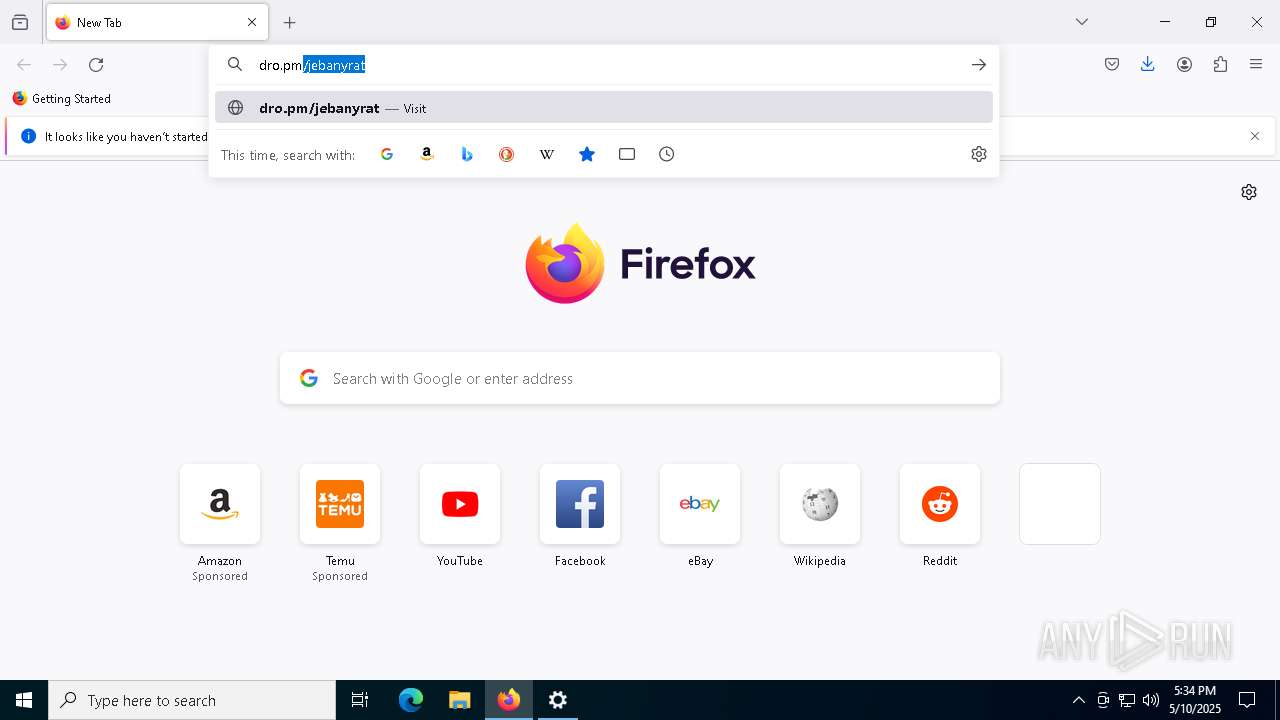
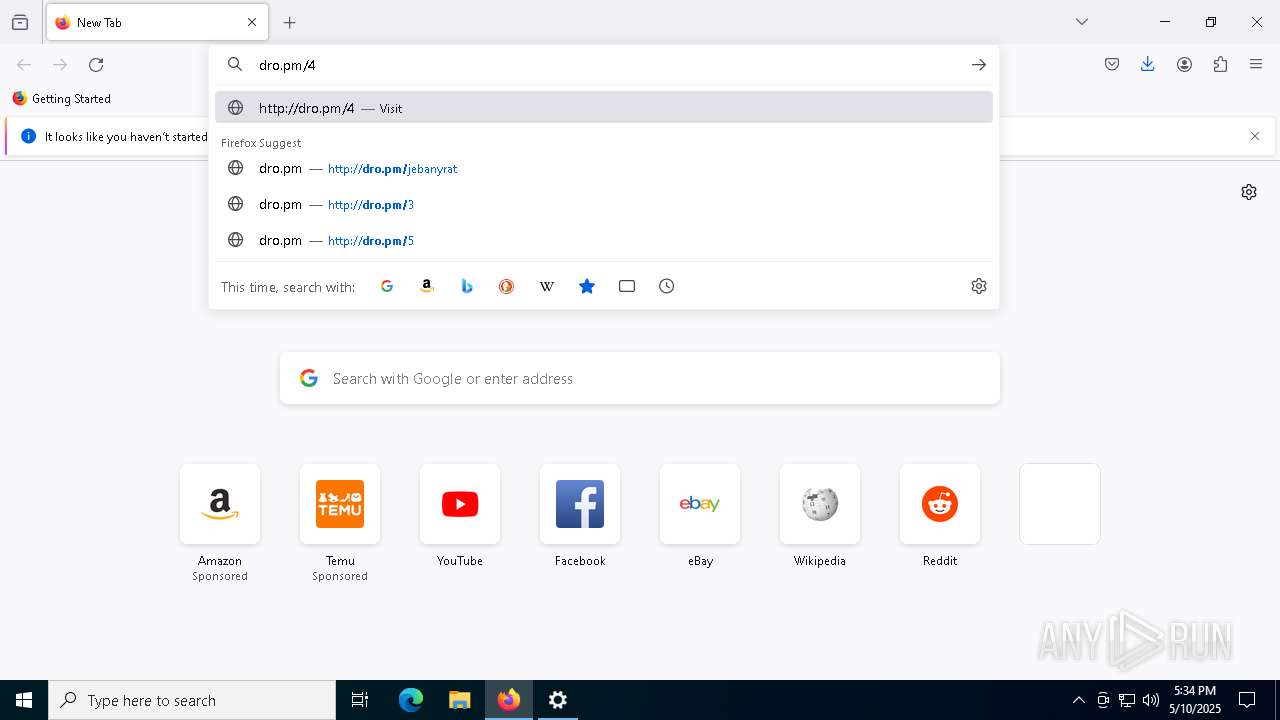
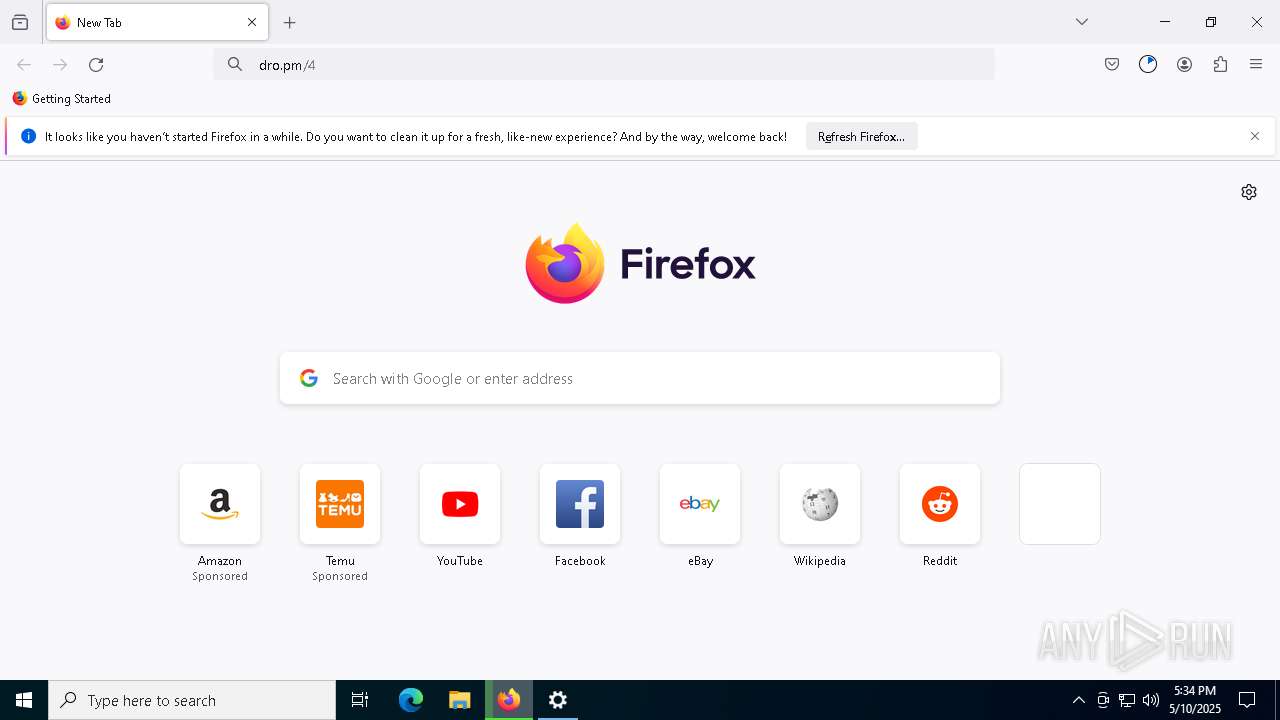
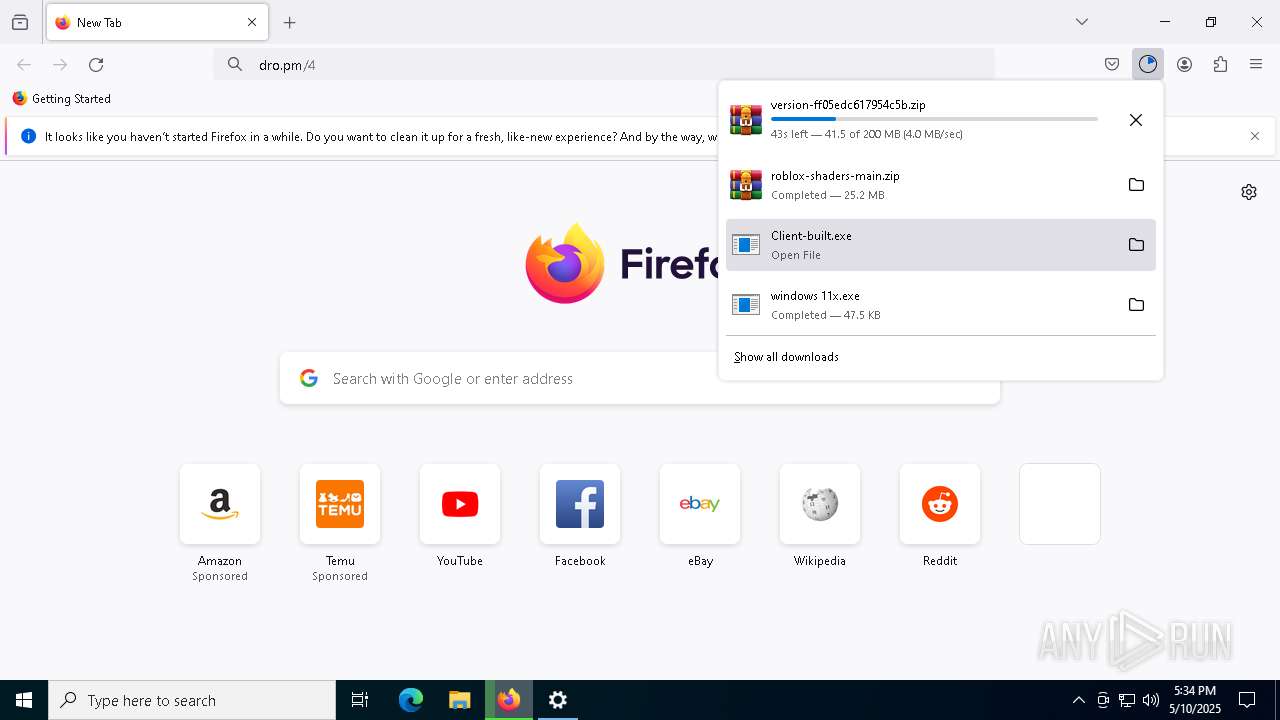
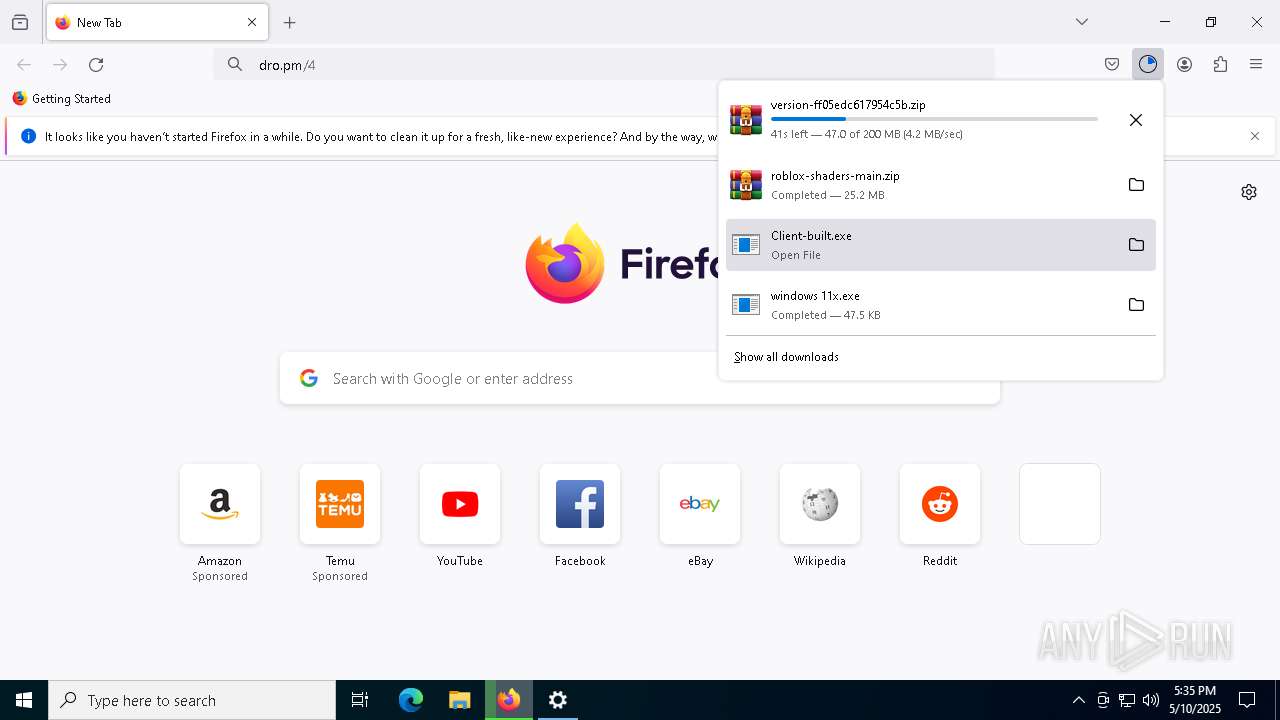
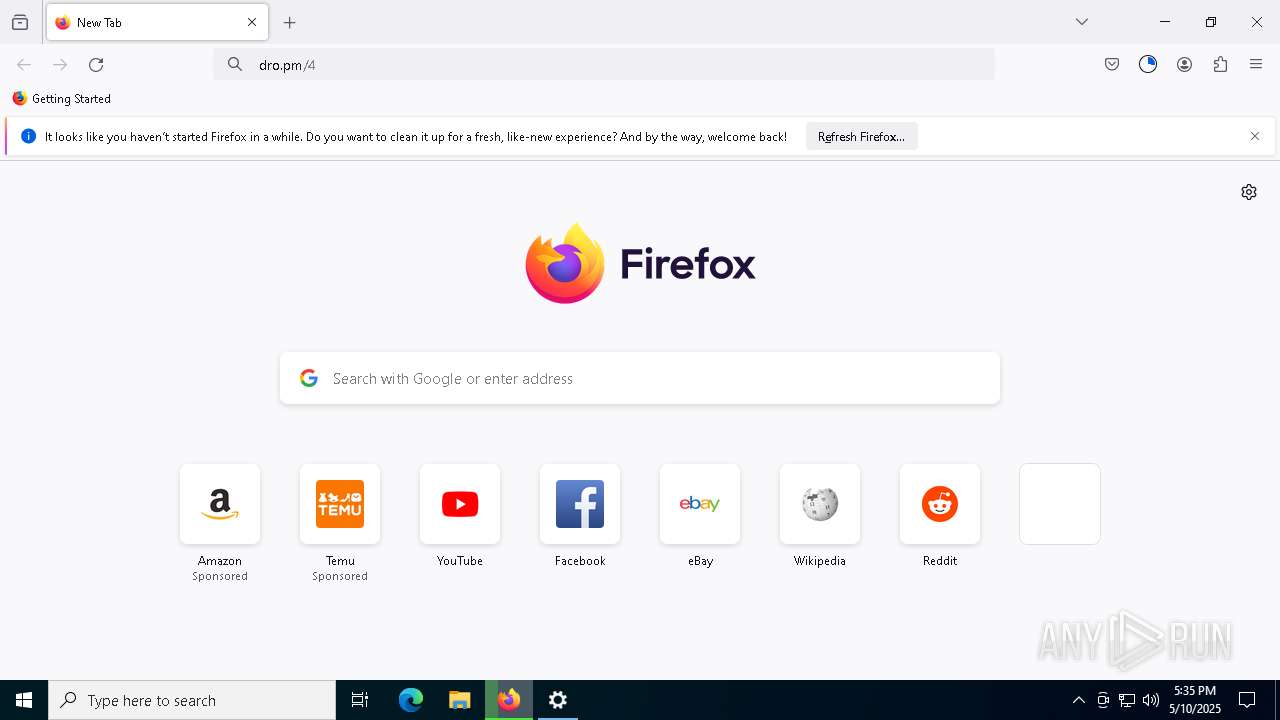
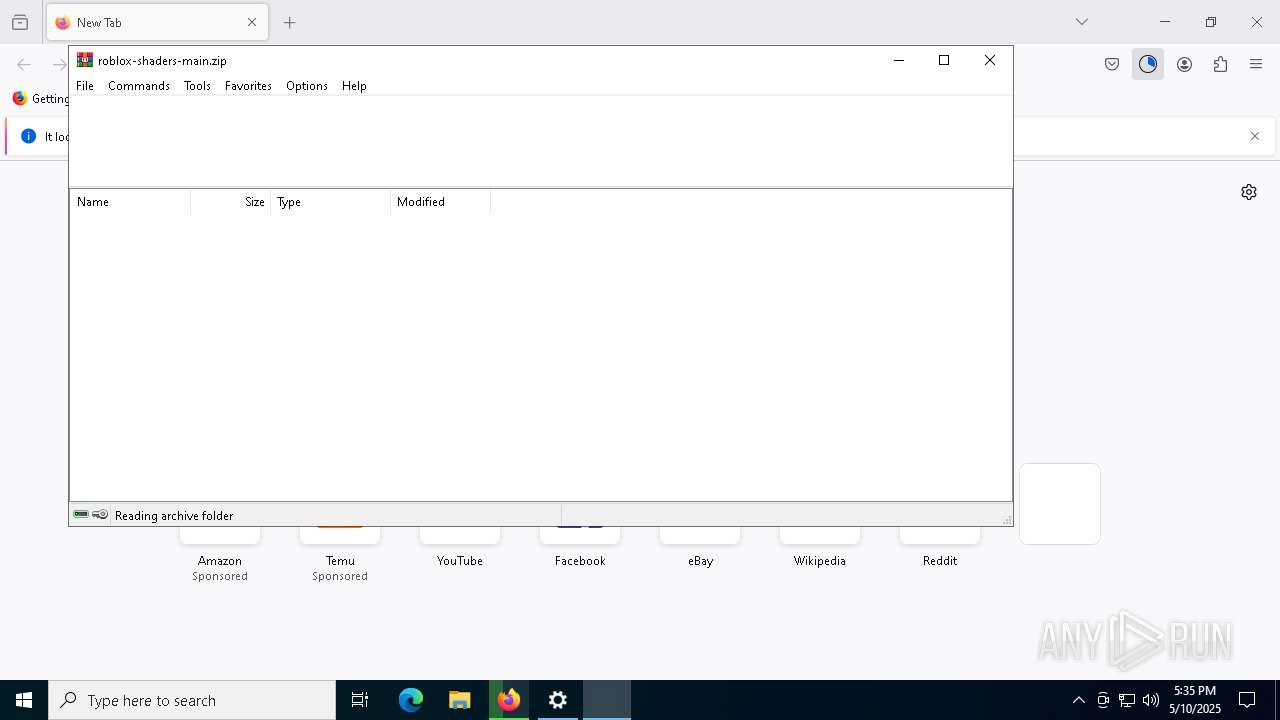
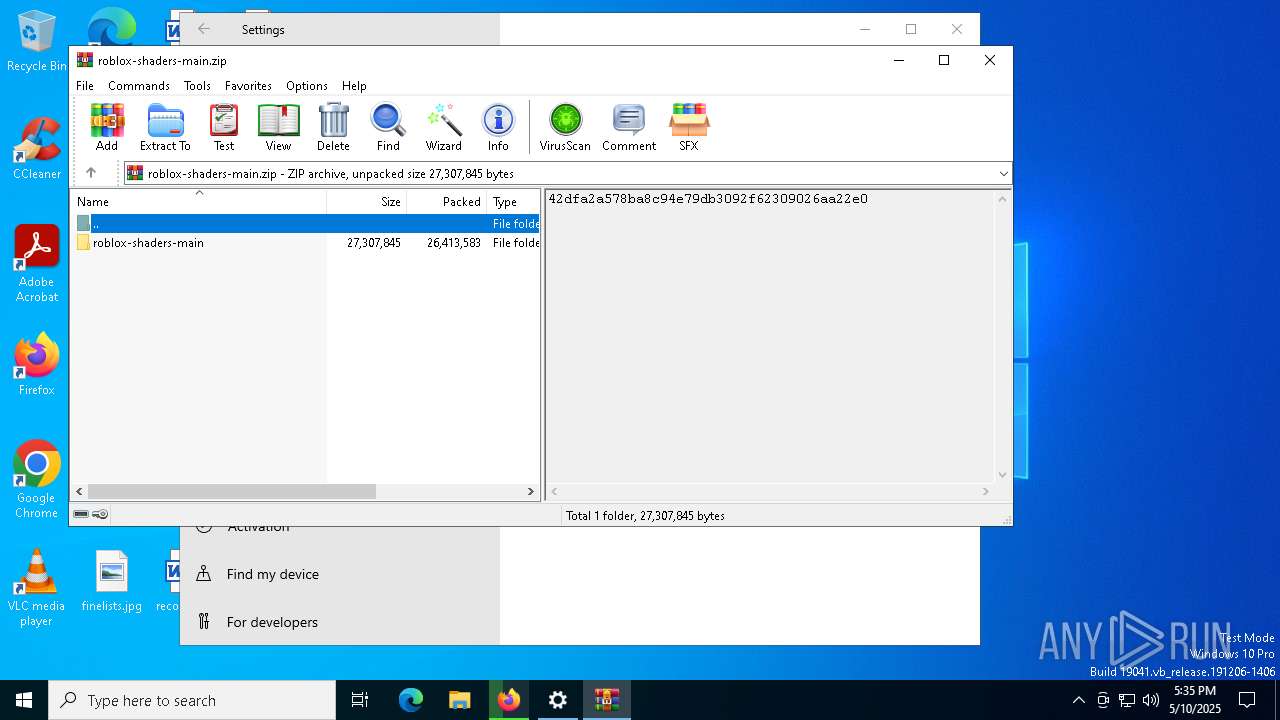
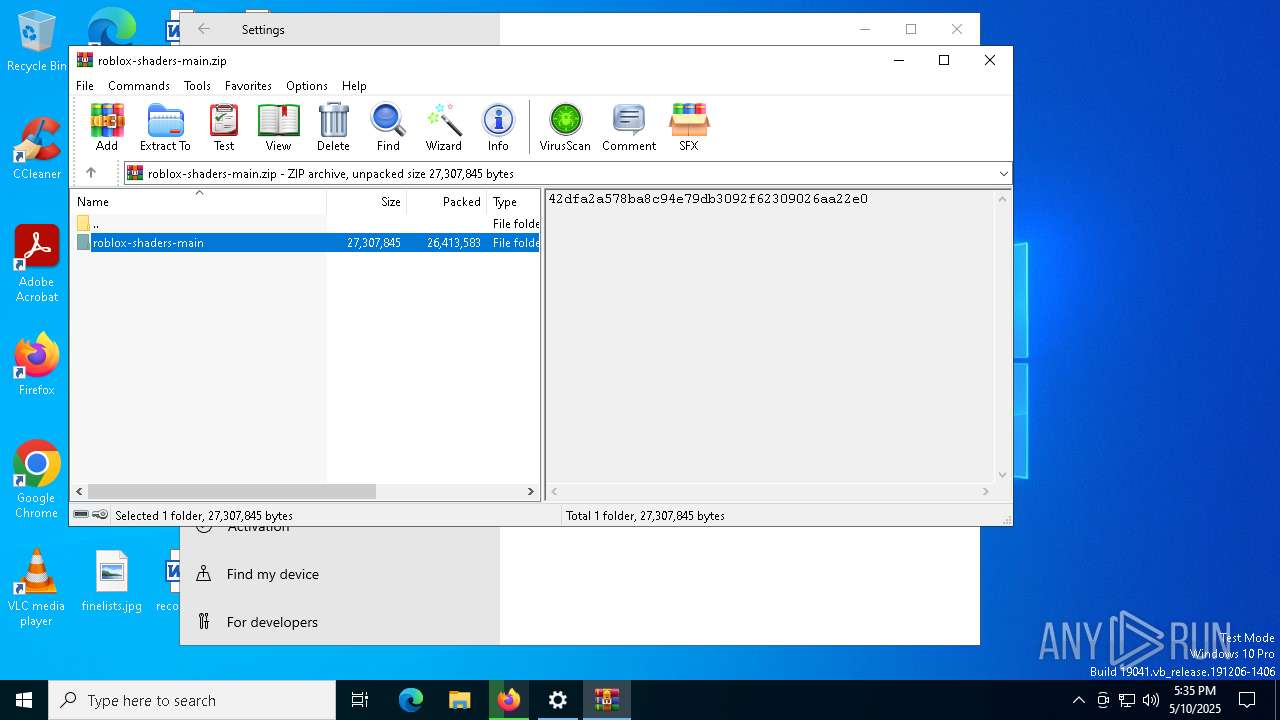
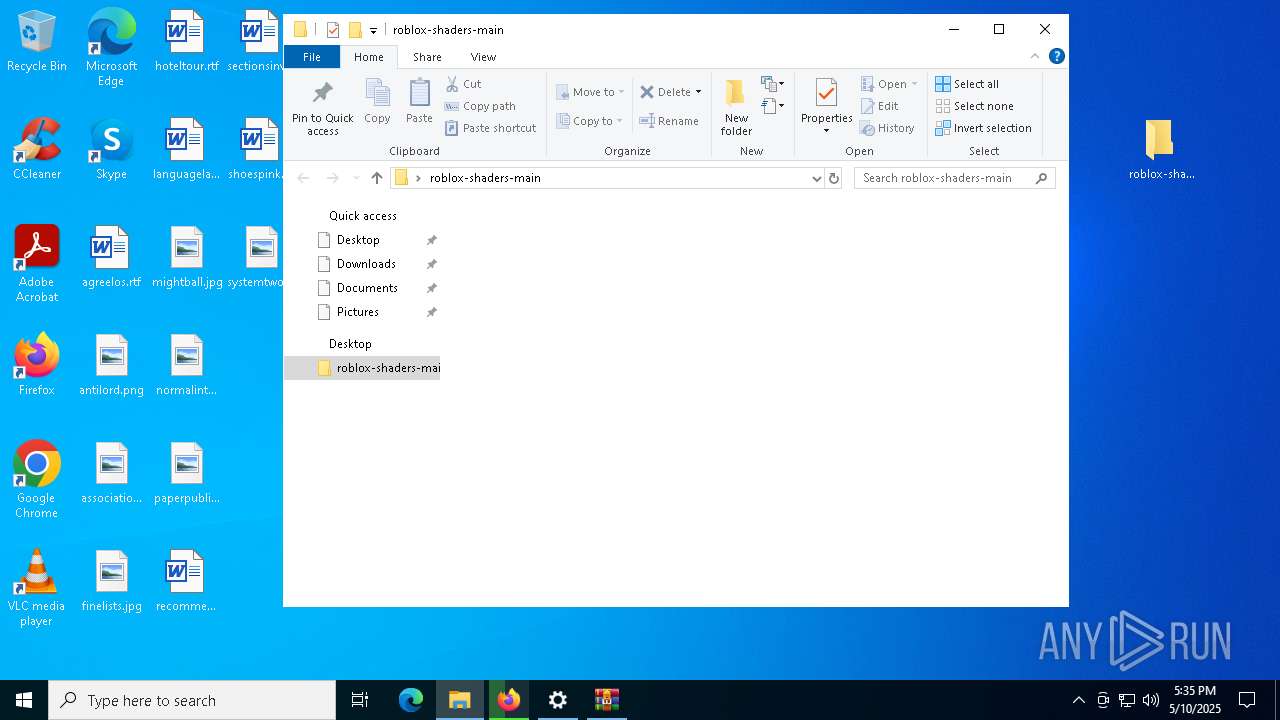
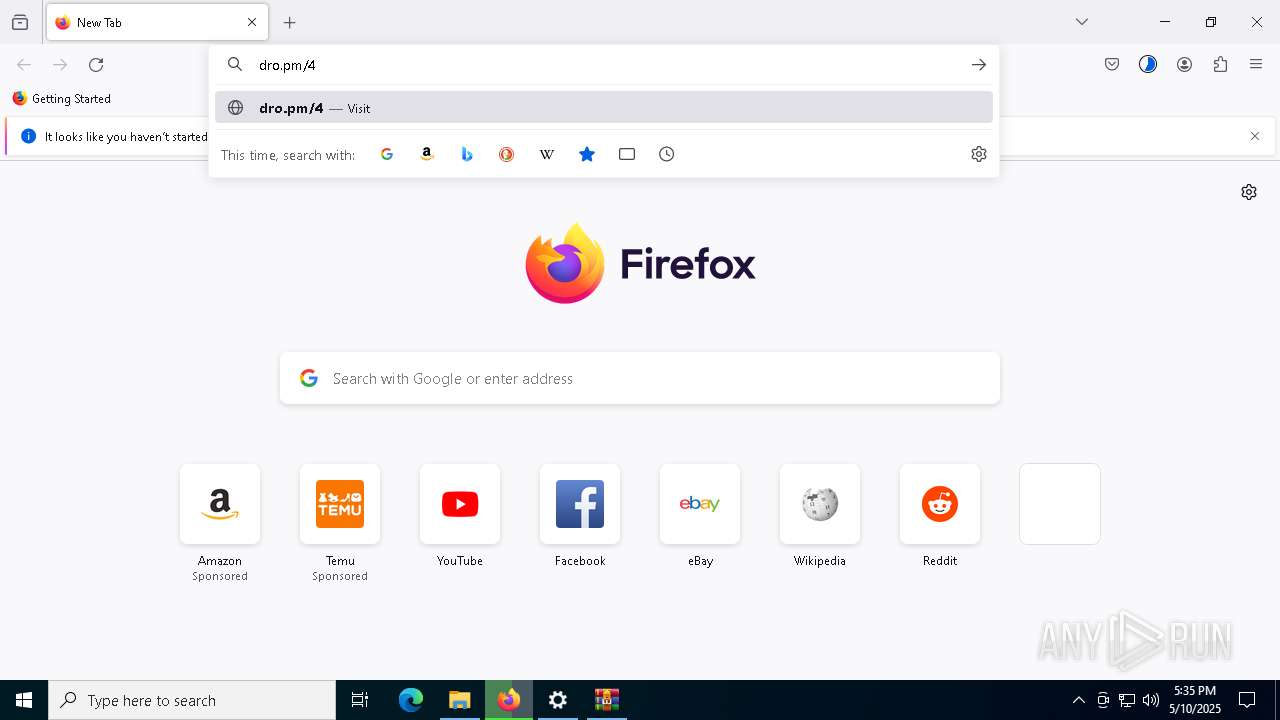
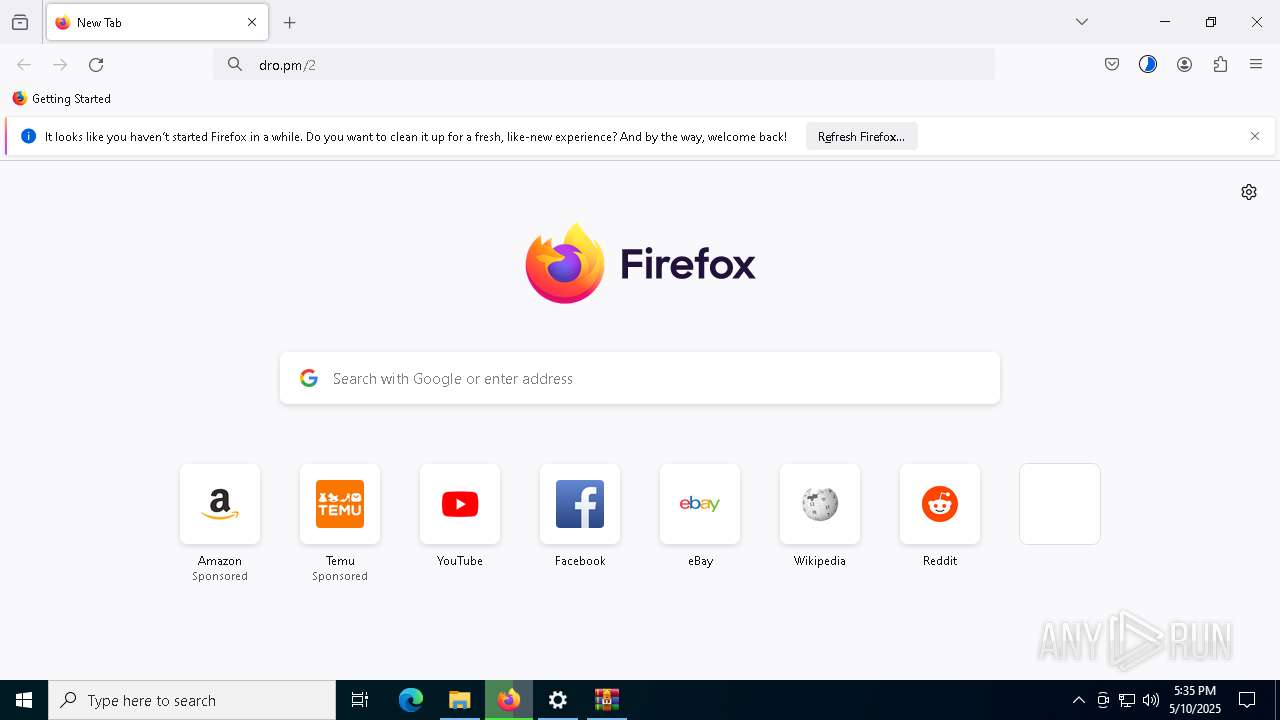
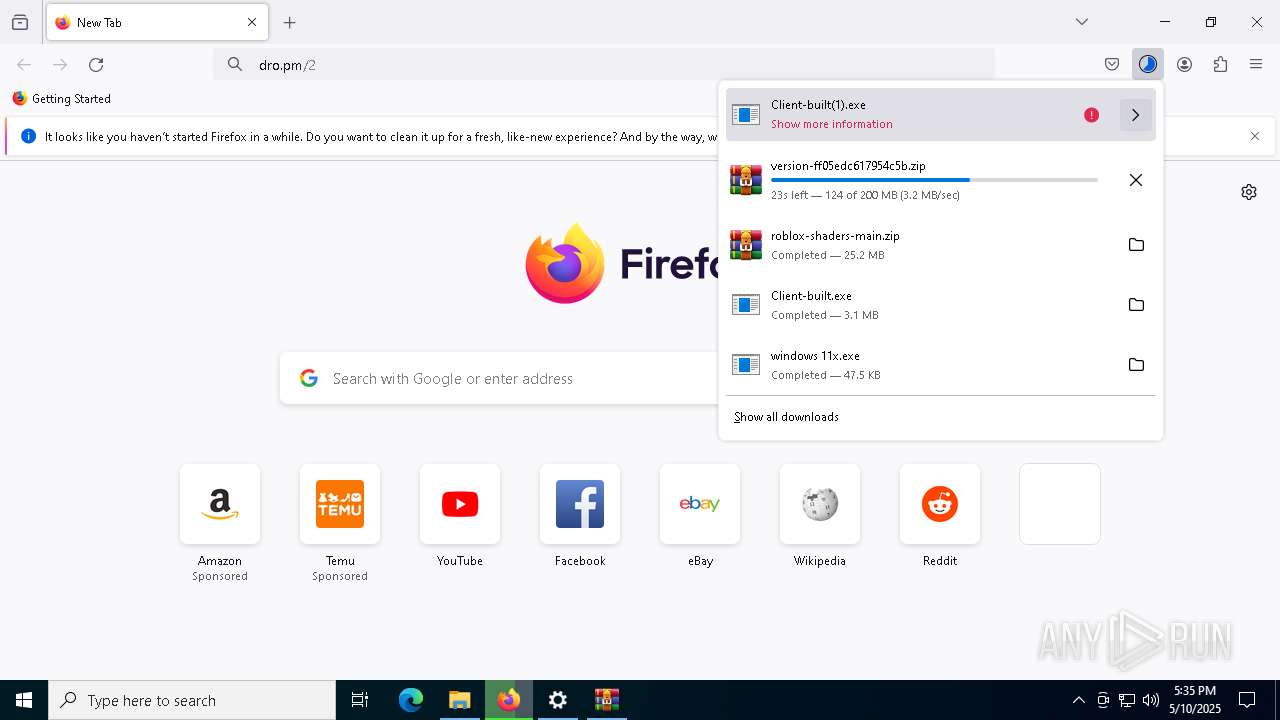
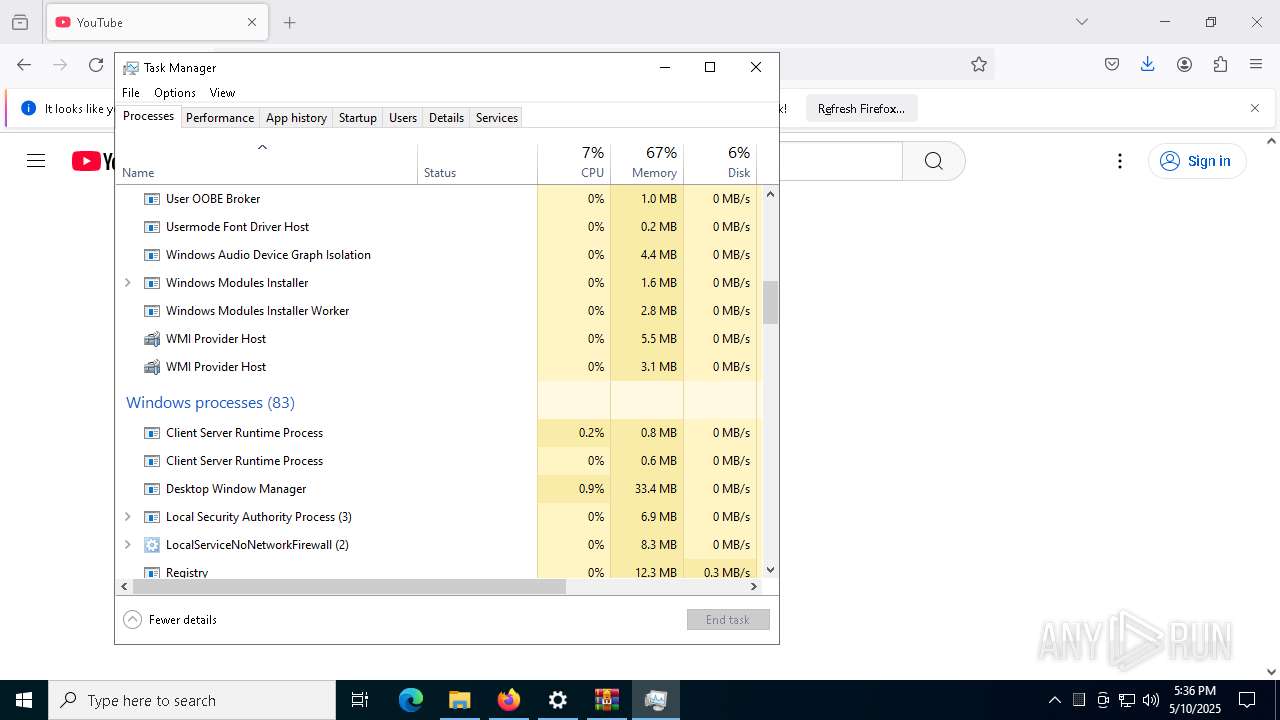
Manual execution by a user
- firefox.exe (PID: 456)
- WinRAR.exe (PID: 2656)
- R_FpsUnlocker.exe (PID: 3024)
- RoShade.exe (PID: 7440)
- R_BloxShades.exe (PID: 7776)
- Taskmgr.exe (PID: 8892)
- Taskmgr.exe (PID: 132)
- WinRAR.exe (PID: 7324)
- MyASUS Installer.exe (PID: 7948)
- MyASUS Installer.exe (PID: 7764)
- MyASUS Installer.exe (PID: 5116)
- MyASUS Installer.exe (PID: 7616)
Reads the computer name
- SecHealthUI.exe (PID: 7796)
- windows 11x.exe (PID: 300)
- Client-built.exe (PID: 2560)
- MyASUS Installer.exe (PID: 5228)
Reads the software policy settings
- slui.exe (PID: 2320)
The sample compiled with english language support
- firefox.exe (PID: 5200)
- WinRAR.exe (PID: 2656)
- RoShade.exe (PID: 7440)
- R_FpsUnlocker.exe (PID: 3024)
- RoShade.exe (PID: 7772)
- R_FpsUnlocker.exe (PID: 1616)
- R_BloxShades.exe (PID: 7776)
- RoShade.exe (PID: 7552)
- R_BloxShades.exe (PID: 5036)
- WinRAR.exe (PID: 7324)
- CL_Debug_Log.txt (PID: 7960)
- start.exe (PID: 8036)
Checks supported languages
- SecHealthUI.exe (PID: 7796)
- Client-built.exe (PID: 2560)
- windows 11x.exe (PID: 300)
- MyASUS Installer.exe (PID: 5228)
Reads Environment values
- Client-built.exe (PID: 2560)
Reads the machine GUID from the registry
- windows 11x.exe (PID: 300)
- Client-built.exe (PID: 2560)
- MyASUS Installer.exe (PID: 5228)
Executable content was dropped or overwritten
- firefox.exe (PID: 5200)
- WinRAR.exe (PID: 2656)
- WinRAR.exe (PID: 7324)
Create files in a temporary directory
- windows 11x.exe (PID: 300)
Creates files or folders in the user directory
- windows 11x.exe (PID: 300)
The Powershell gets current clipboard
- powershell.exe (PID: 8312)
Checks the directory tree
- tree.com (PID: 8496)
- tree.com (PID: 8812)
- tree.com (PID: 7856)
- tree.com (PID: 9120)
- tree.com (PID: 7860)
- tree.com (PID: 8888)
Displays MAC addresses of computer network adapters
- getmac.exe (PID: 8260)
PyInstaller has been detected (YARA)
- RoShade.exe (PID: 7772)
Attempting to use instant messaging service
- svchost.exe (PID: 2196)
Found Base64 encoded reflection usage via PowerShell (YARA)
- RoShade.exe (PID: 7552)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Quasar
(PID) Process(2560) Client-built.exe
Version1.4.1
C2 (2)192.168.0.48:4782
Sub_DirSubDir
Install_NameClient.exe
Mutexfa88088a-1870-4f87-8bdd-183fddbaf441
StartupQuasar Client Startup
TagOffice04
LogDirLogs
Signaturejx816KXlPeIyb7X6e3TTDSoB0wrLVW1uOUFPZh+qHVmaokqkqmHrbIRcslpges8iPWhzPPsor6Uw46ugTb+zyWyr9aY0dYzBZ5MHP7AUV61u5oSwN7tjX20qV1dhw33NrKem6tpi/oajELr7UjUWPMNfIrgXK2dIEzS9FW//ys4Uga55frmzMmT+gipjKB7e5B78ZDZmJNUyQmTfYSQZ+MqAyqMs7ZF82P4dMuNlsqyUJoua7e533Mlj0dP4+TPwTSk09IjgploIv9ExtgSGjJWGEVbllMwGe2JAAvgEsUPw...
CertificateMIIE9DCCAtygAwIBAgIQANxCwvrAyUtQD4s3ZIeSSzANBgkqhkiG9w0BAQ0FADAbMRkwFwYDVQQDDBBRdWFzYXIgU2VydmVyIENBMCAXDTI1MDUwODA2MzI0OFoYDzk5OTkxMjMxMjM1OTU5WjAbMRkwFwYDVQQDDBBRdWFzYXIgU2VydmVyIENBMIICIjANBgkqhkiG9w0BAQEFAAOCAg8AMIICCgKCAgEAnMwFCBG8fzjfmjnkJ/wVVII0h2jzK0PYPly5+PJRAjFD226LvF+b3bJSWSBIEYnphDJn9ObT...
(PID) Process(9108) Client-built(1).exe
Version1.4.1
C2 (2)192.168.0.48:4782
Sub_DirSubDir
Install_NameClient.exe
Mutexfa88088a-1870-4f87-8bdd-183fddbaf441
StartupQuasar Client Startup
TagOffice04
LogDirLogs
Signaturejx816KXlPeIyb7X6e3TTDSoB0wrLVW1uOUFPZh+qHVmaokqkqmHrbIRcslpges8iPWhzPPsor6Uw46ugTb+zyWyr9aY0dYzBZ5MHP7AUV61u5oSwN7tjX20qV1dhw33NrKem6tpi/oajELr7UjUWPMNfIrgXK2dIEzS9FW//ys4Uga55frmzMmT+gipjKB7e5B78ZDZmJNUyQmTfYSQZ+MqAyqMs7ZF82P4dMuNlsqyUJoua7e533Mlj0dP4+TPwTSk09IjgploIv9ExtgSGjJWGEVbllMwGe2JAAvgEsUPw...
CertificateMIIE9DCCAtygAwIBAgIQANxCwvrAyUtQD4s3ZIeSSzANBgkqhkiG9w0BAQ0FADAbMRkwFwYDVQQDDBBRdWFzYXIgU2VydmVyIENBMCAXDTI1MDUwODA2MzI0OFoYDzk5OTkxMjMxMjM1OTU5WjAbMRkwFwYDVQQDDBBRdWFzYXIgU2VydmVyIENBMIICIjANBgkqhkiG9w0BAQEFAAOCAg8AMIICCgKCAgEAnMwFCBG8fzjfmjnkJ/wVVII0h2jzK0PYPly5+PJRAjFD226LvF+b3bJSWSBIEYnphDJn9ObT...
AsyncRat
(PID) Process(5228) MyASUS Installer.exe
C2 (2)127.0.0.1
192.168.137.1
Ports (3)6606
7707
8808
Version0.5.8
BotnetDefault
Options
AutoRuntrue
MutexaIyvpStTT3mv
InstallFolder%AppData%
BSoDfalse
AntiVMfalse
Certificates
Cert1MIIE6DCCAtCgAwIBAgIQANhaLVfp4qyhet/QSQcBYzANBgkqhkiG9w0BAQ0FADAVMRMwEQYDVQQDDAp2YWliaGF2IGRjMCAXDTI1MDQwOTA5NTQ1OVoYDzk5OTkxMjMxMjM1OTU5WjAVMRMwEQYDVQQDDAp2YWliaGF2IGRjMIICIjANBgkqhkiG9w0BAQEFAAOCAg8AMIICCgKCAgEAzqTLUUmCdKSx1T5JdRDPlEU3urreaM/hDPK228m8dN0/3A4EWohzqvyFAHeJMVDetSPmJOk2kQuywKS9KtSwOIY5...
Server_SignaturesdR09c+kCbQOP9EkH+4fAS55ZbJxZ/5XxqUQJUV6K22eLmL0NLX8SkSLcnFEi1B/LyHkSoNX8o4vJljEy1b53uft/ROJkngY6UAgQC4jhFuk3F//iZidrDCxXiWKbJmb1tbtDQH7G/ETSuLFF9llb3HWTaXpA5VqVUD8/hjP8jk22zMxGDLXq8O2FaPtkYg2Rt24AkCmiLVob5KkrVZJPii3er03Hrjh/5AVkLMx/efIRFCl6Wr6KPg1264vj7uh9inmeiV0WrswmqobxEjz2Y15fb6LJYf09nE23Rb49cKR...
Keys
AESca94745b53a305113fec5e894abd4bd8a88ed411f4c67ad19148ab0d396debc1
Saltbfeb1e56fbcd973bb219022430a57843003d5644d21e62b9d4f180e7e6c33941
TRiD
| .png | | | Portable Network Graphics (100) |
|---|
EXIF
PNG
| ImageWidth: | 1919 |
|---|---|
| ImageHeight: | 1079 |
| BitDepth: | 8 |
| ColorType: | RGB with Alpha |
| Compression: | Deflate/Inflate |
| Filter: | Adaptive |
| Interlace: | Noninterlaced |
| SRGBRendering: | Perceptual |
| Gamma: | 2.2 |
| PixelsPerUnitX: | 3779 |
| PixelsPerUnitY: | 3779 |
| PixelUnits: | meters |
Composite
| ImageSize: | 1919x1079 |
|---|---|
| Megapixels: | 2.1 |
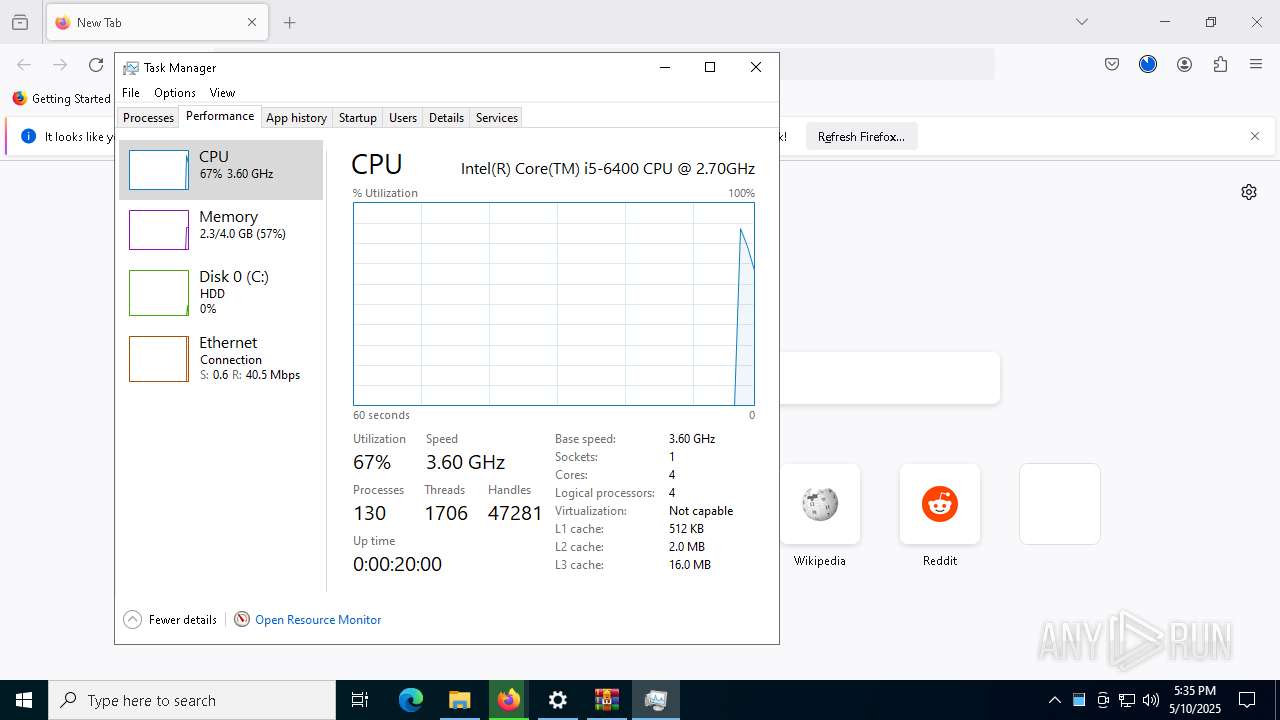
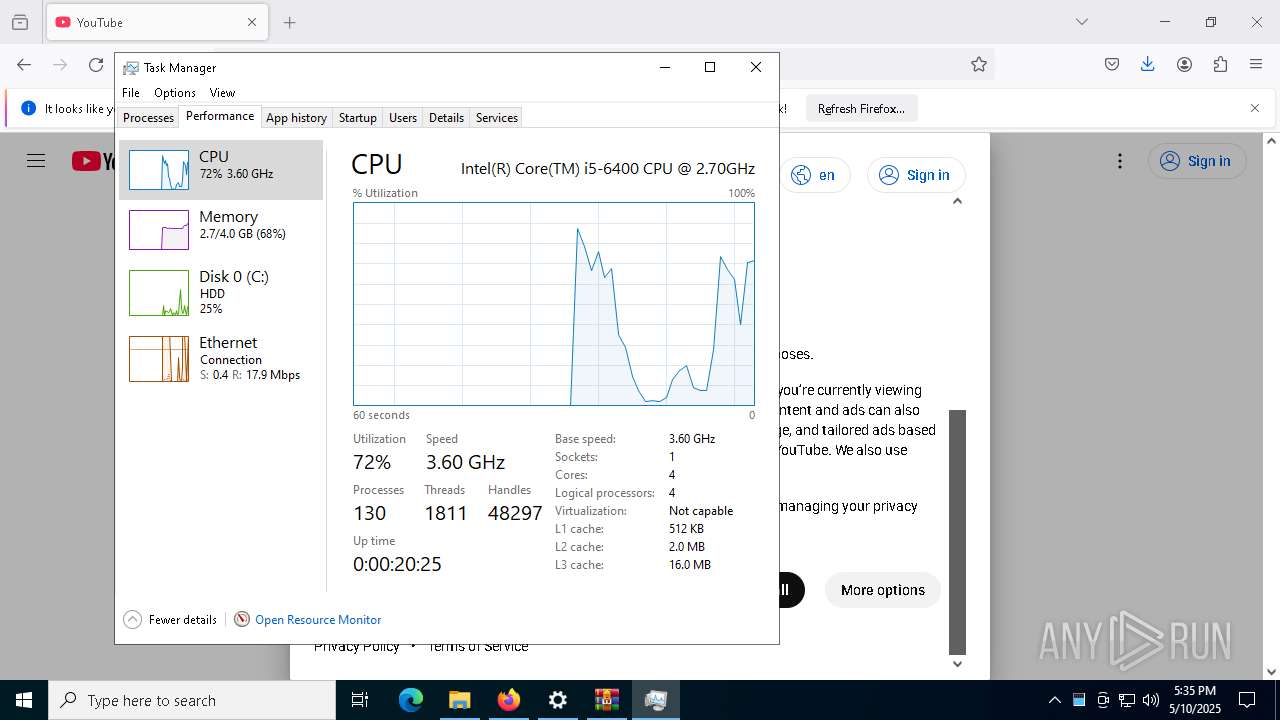
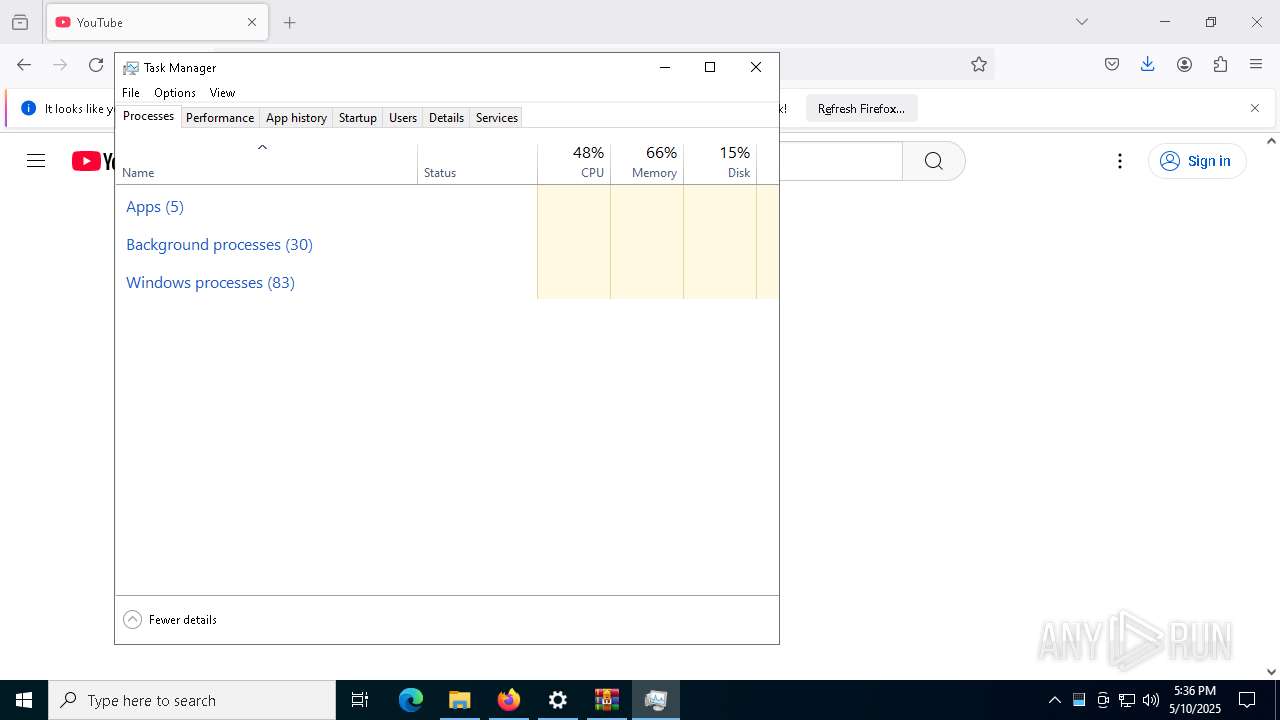
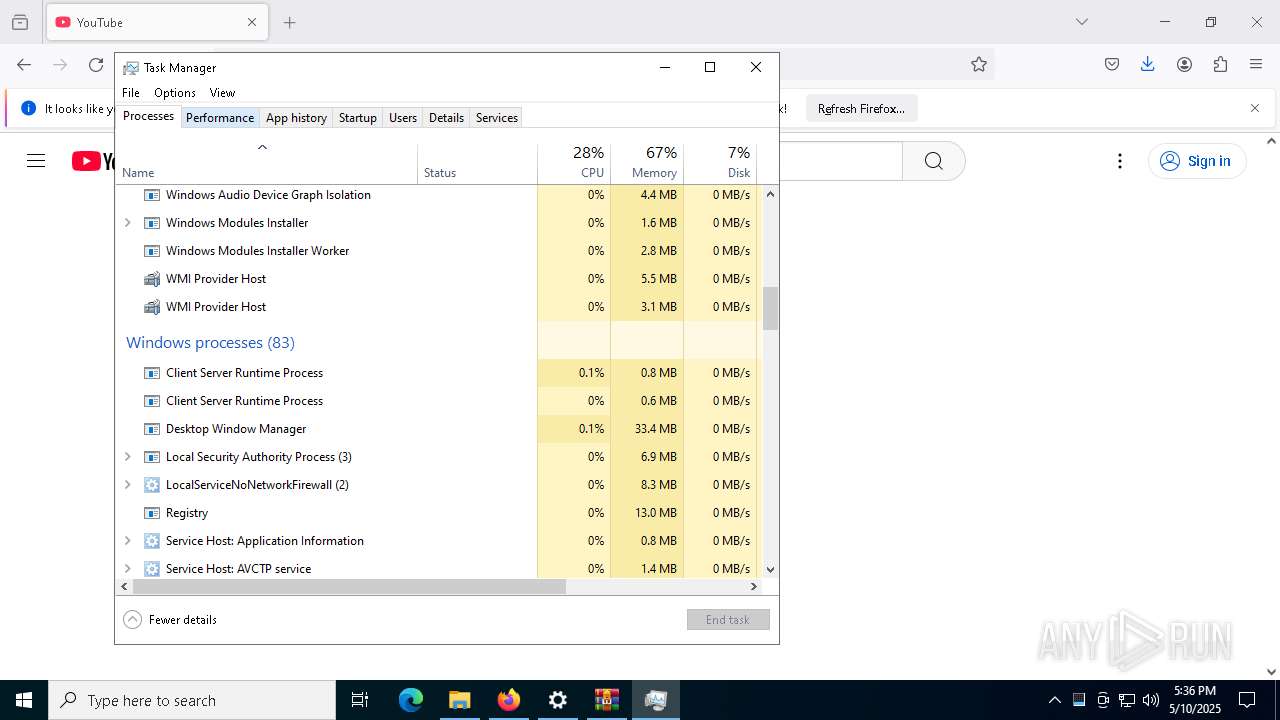
Total processes
291
Monitored processes
150
Malicious processes
22
Suspicious processes
5
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 132 | C:\WINDOWS\system32\cmd.exe /c "powershell Get-Clipboard" | C:\Windows\System32\cmd.exe | — | RoShade.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 132 | "C:\WINDOWS\system32\taskmgr.exe" /4 | C:\Windows\System32\Taskmgr.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Task Manager Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
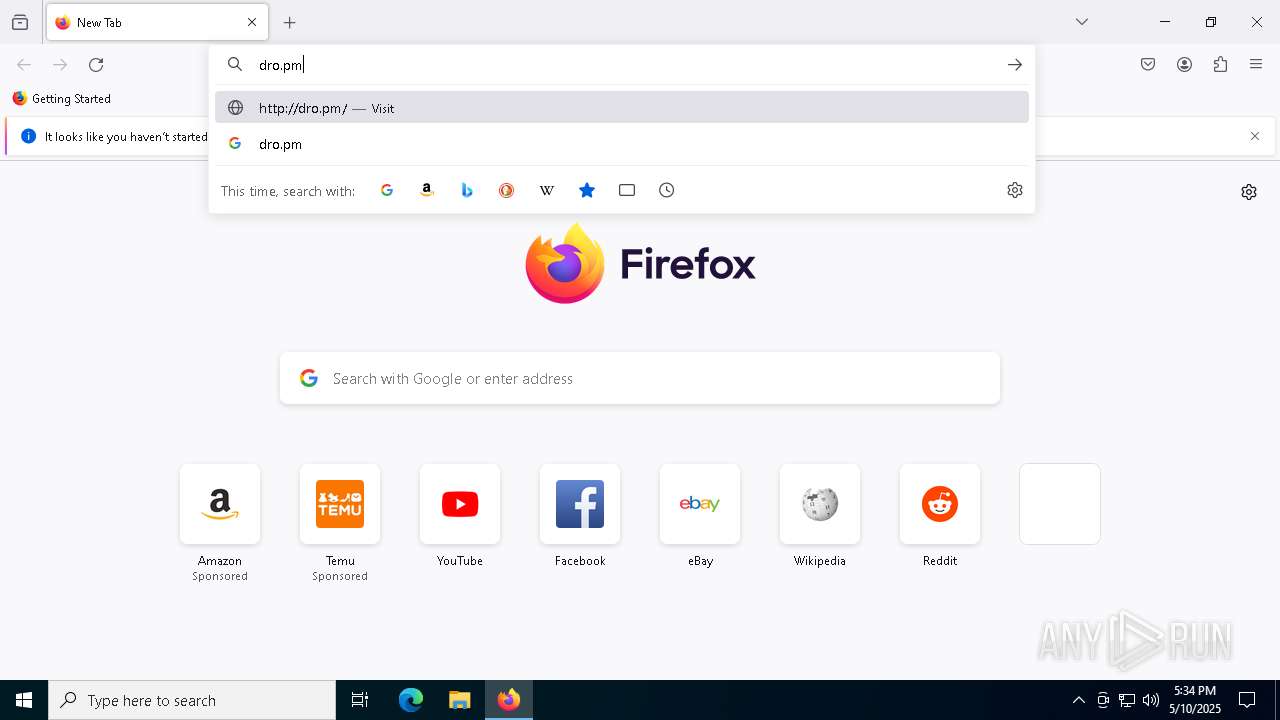
| 300 | "C:\Users\admin\Downloads\windows 11x.exe" | C:\Users\admin\Downloads\windows 11x.exe | firefox.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 300 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=6592 -childID 9 -isForBrowser -prefsHandle 6804 -prefMapHandle 6296 -prefsLen 31645 -prefMapSize 244583 -jsInitHandle 1512 -jsInitLen 235124 -parentBuildID 20240213221259 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {2065eb4b-396b-4a42-adb6-4b3303e96f46} 5200 "\\.\pipe\gecko-crash-server-pipe.5200" 22d32d37850 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Version: 123.0 Modules
| |||||||||||||||
| 456 | "C:\Program Files\Mozilla Firefox\firefox.exe" | C:\Program Files\Mozilla Firefox\firefox.exe | — | explorer.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 123.0 Modules
| |||||||||||||||
| 720 | wmic computersystem get totalphysicalmemory | C:\Windows\System32\wbem\WMIC.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: WMI Commandline Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 872 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1052 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=2152 -parentBuildID 20240213221259 -prefsHandle 2144 -prefMapHandle 2140 -prefsLen 31031 -prefMapSize 244583 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {7534dc34-9606-4ba8-a6ce-721ac8450be4} 5200 "\\.\pipe\gecko-crash-server-pipe.5200" 22d1a182d10 socket | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Version: 123.0 Modules
| |||||||||||||||
| 1096 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1280 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
91 555
Read events
91 530
Write events
24
Delete events
1
Modification events
| (PID) Process: | (5968) rundll32.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows Photo Viewer\Viewer |
| Operation: | write | Name: | MainWndPos |
Value: 6000000033000000A00400007502000000000000 | |||
| (PID) Process: | (5200) firefox.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Mozilla\Firefox\DllPrefetchExperiment |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe |
Value: 0 | |||
| (PID) Process: | (5200) firefox.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer |
| Operation: | write | Name: | SlowContextMenuEntries |
Value: 6024B221EA3A6910A2DC08002B30309D0A010000BD0E0C47735D584D9CEDE91E22E23282770100000114020000000000C0000000000000468D0000006078A409B011A54DAFA526D86198A780390100009AD298B2EDA6DE11BA8CA68E55D895936E000000 | |||
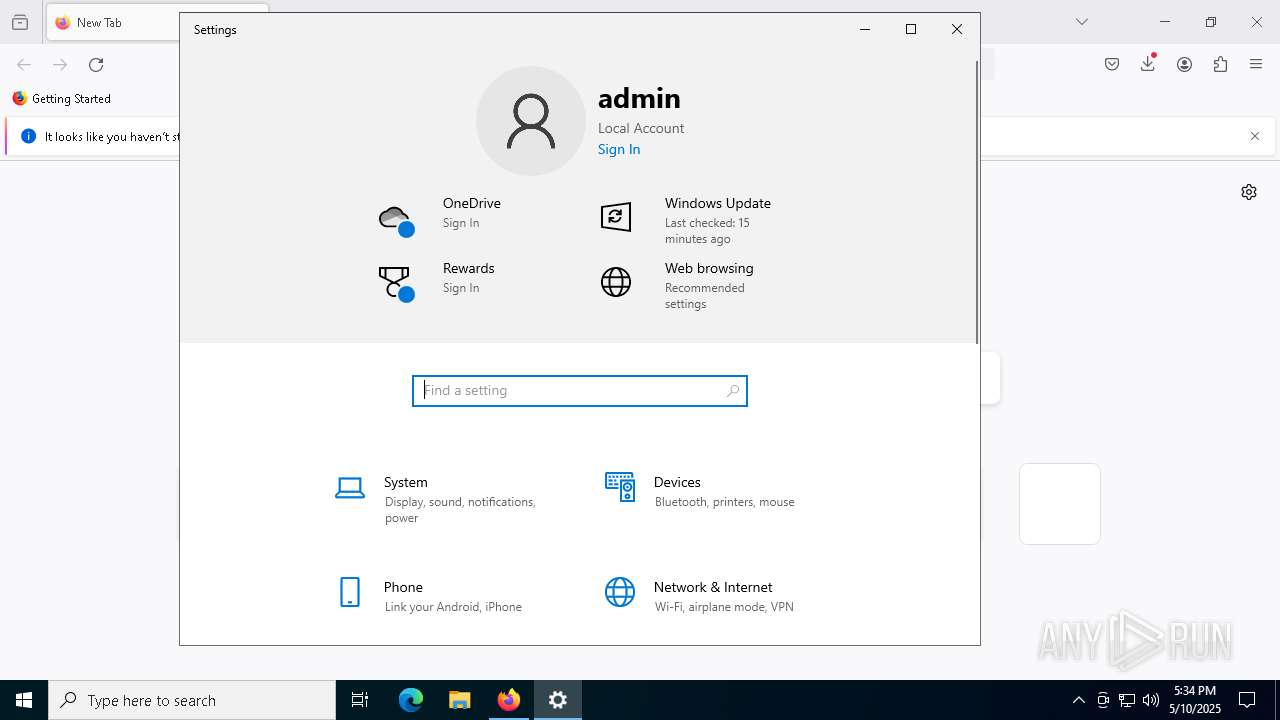
| (PID) Process: | (300) windows 11x.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | MyASUS Installer |
Value: "C:\Users\admin\AppData\Roaming\MyASUS Installer.exe" | |||
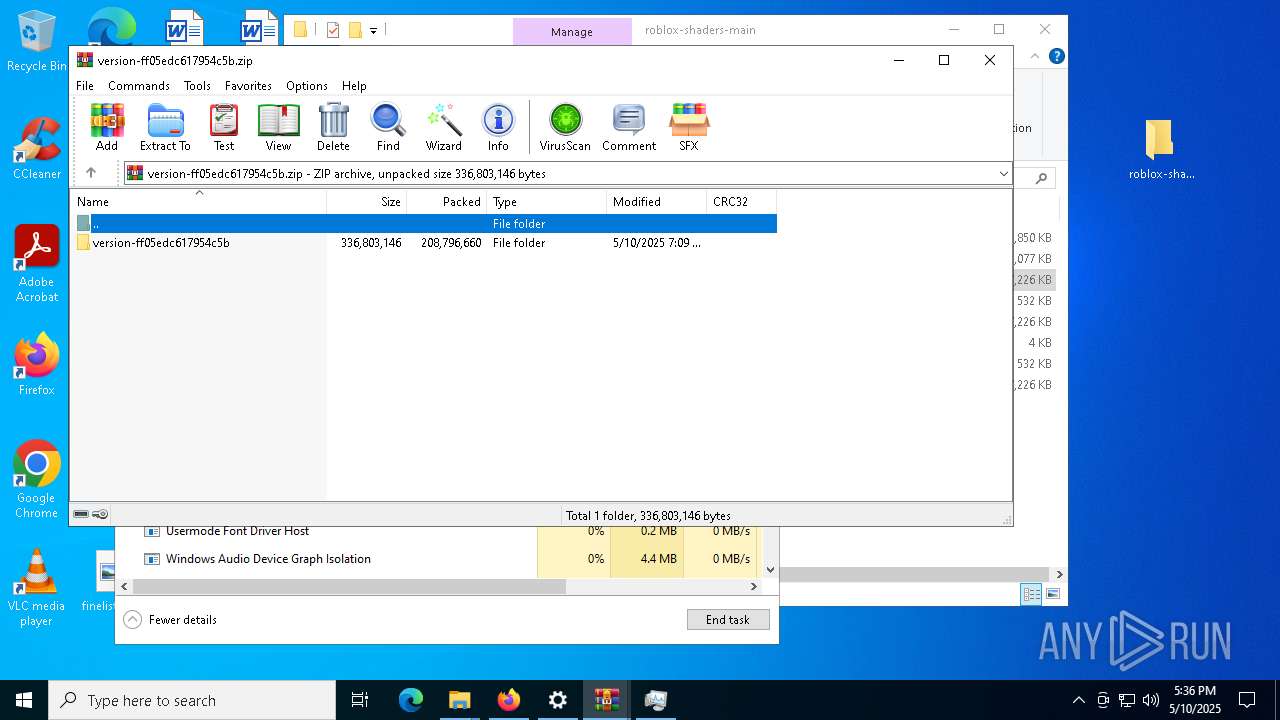
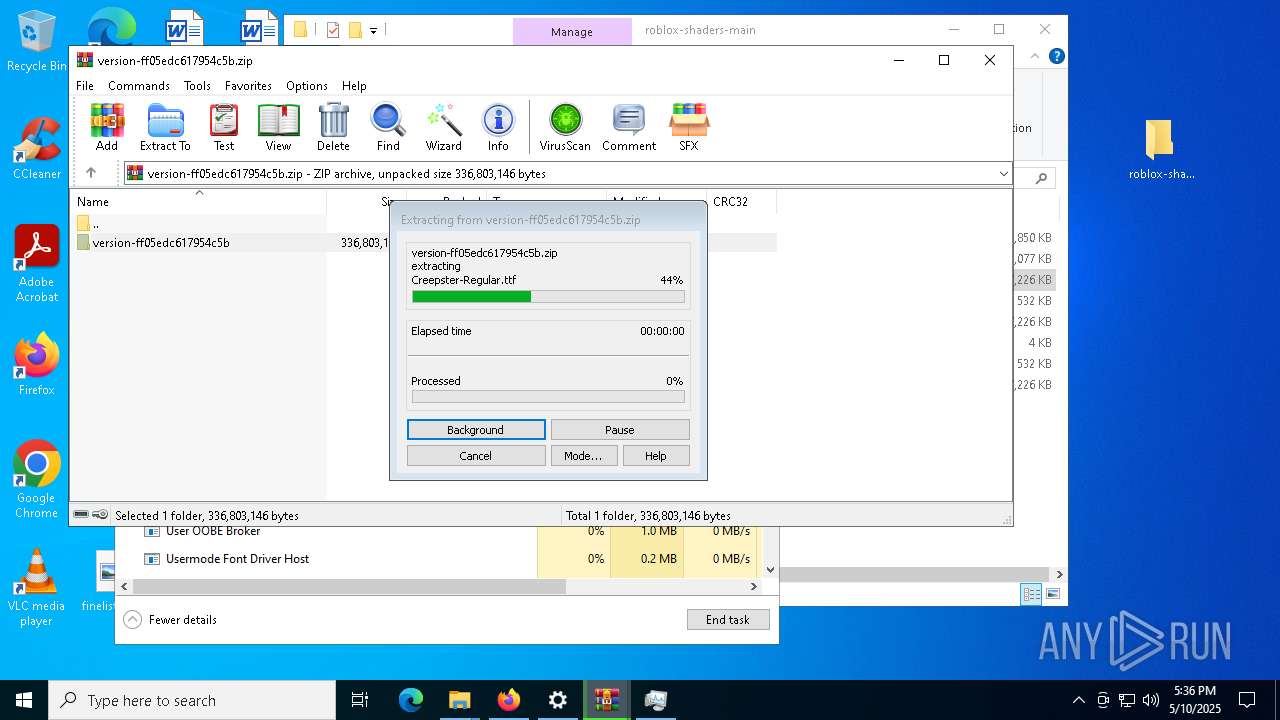
| (PID) Process: | (2656) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (2656) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (2656) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (2656) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Downloads\roblox-shaders-main.zip | |||
| (PID) Process: | (2656) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2656) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
Executable files
174
Suspicious files
774
Text files
2 452
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5200 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\9kie7cg6.default-release\startupCache\scriptCache-current.bin | — | |
MD5:— | SHA256:— | |||
| 5200 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\9kie7cg6.default-release\startupCache\scriptCache-child-current.bin | binary | |
MD5:C95DDC2B1A525D1A243E4C294DA2F326 | SHA256:3A5919E086BFB31E36110CF636D2D5109EB51F2C410B107F126126AB25D67363 | |||
| 5200 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\sessionCheckpoints.json.tmp | binary | |
MD5:EA8B62857DFDBD3D0BE7D7E4A954EC9A | SHA256:792955295AE9C382986222C6731C5870BD0E921E7F7E34CC4615F5CD67F225DA | |||
| 5200 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\1657114595AmcateirvtiSty.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 5200 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\prefs-1.js | text | |
MD5:885A5B6781718C2BB438A61159E824D2 | SHA256:D7B07619BA93B8BE3054D1374FCBA7556177076D95E182B625688C499E390AB1 | |||
| 5200 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\3870112724rsegmnoittet-es.sqlite | — | |
MD5:— | SHA256:— | |||
| 5200 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\1451318868ntouromlalnodry--epcr.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 5200 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\3561288849sdhlie.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 5200 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\9kie7cg6.default-release\startupCache\urlCache-current.bin | binary | |
MD5:297E88D7CEB26E549254EC875649F4EB | SHA256:8B75D4FB1845BAA06122888D11F6B65E6A36B140C54A72CC13DF390FD7C95702 | |||
| 5200 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\2918063365piupsah.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
59
TCP/UDP connections
162
DNS requests
168
Threats
8
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.48.23.184:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5200 | firefox.exe | POST | 200 | 184.24.77.65:80 | http://r11.o.lencr.org/ | unknown | — | — | whitelisted |
5200 | firefox.exe | POST | 200 | 172.217.16.195:80 | http://o.pki.goog/we2 | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5200 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/success.txt?ipv4 | unknown | — | — | whitelisted |
5200 | firefox.exe | POST | 200 | 172.217.16.195:80 | http://o.pki.goog/s/wr3/FIY | unknown | — | — | whitelisted |
5200 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/canonical.html | unknown | — | — | whitelisted |
5200 | firefox.exe | POST | 200 | 184.24.77.65:80 | http://r11.o.lencr.org/ | unknown | — | — | whitelisted |
5200 | firefox.exe | POST | 200 | 184.24.77.56:80 | http://r10.o.lencr.org/ | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 23.48.23.184:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2104 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3216 | svchost.exe | 172.211.123.250:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
5200 | firefox.exe | 34.36.137.203:443 | contile.services.mozilla.com | — | — | whitelisted |
5200 | firefox.exe | 34.107.221.82:80 | detectportal.firefox.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
detectportal.firefox.com |
| whitelisted |
prod.detectportal.prod.cloudops.mozgcp.net |
| whitelisted |
example.org |
| whitelisted |
ipv4only.arpa |
| whitelisted |
contile.services.mozilla.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | Device Retrieving External IP Address Detected | INFO [ANY.RUN] External IP Check (ip-api .com) |
2196 | svchost.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup Domain in DNS Lookup (ip-api .com) |
2196 | svchost.exe | Misc activity | ET INFO Discord Chat Service Domain in DNS Lookup (discord .com) |
7552 | RoShade.exe | A Network Trojan was detected | STEALER [ANY.RUN] BlankGrabber (SkochGrabber) Generic External IP Check |
7552 | RoShade.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup ip-api.com |
2196 | svchost.exe | Misc activity | ET INFO Observed Discord Domain in DNS Lookup (discord .com) |
7552 | RoShade.exe | Misc activity | ET INFO Observed Discord Domain (discord .com in TLS SNI) |
7552 | RoShade.exe | Misc activity | ET INFO Observed Discord Service Domain (discord .com) in TLS SNI |