| File name: | sample.zip |
| Full analysis: | https://app.any.run/tasks/10dc57bf-f4bd-4780-8db6-d97d58d5f31a |
| Verdict: | Malicious activity |
| Threats: | FormBook is a data stealer that is being distributed as a MaaS. FormBook differs from a lot of competing malware by its extreme ease of use that allows even the unexperienced threat actors to use FormBook virus. |
| Analysis date: | October 14, 2019, 14:14:42 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
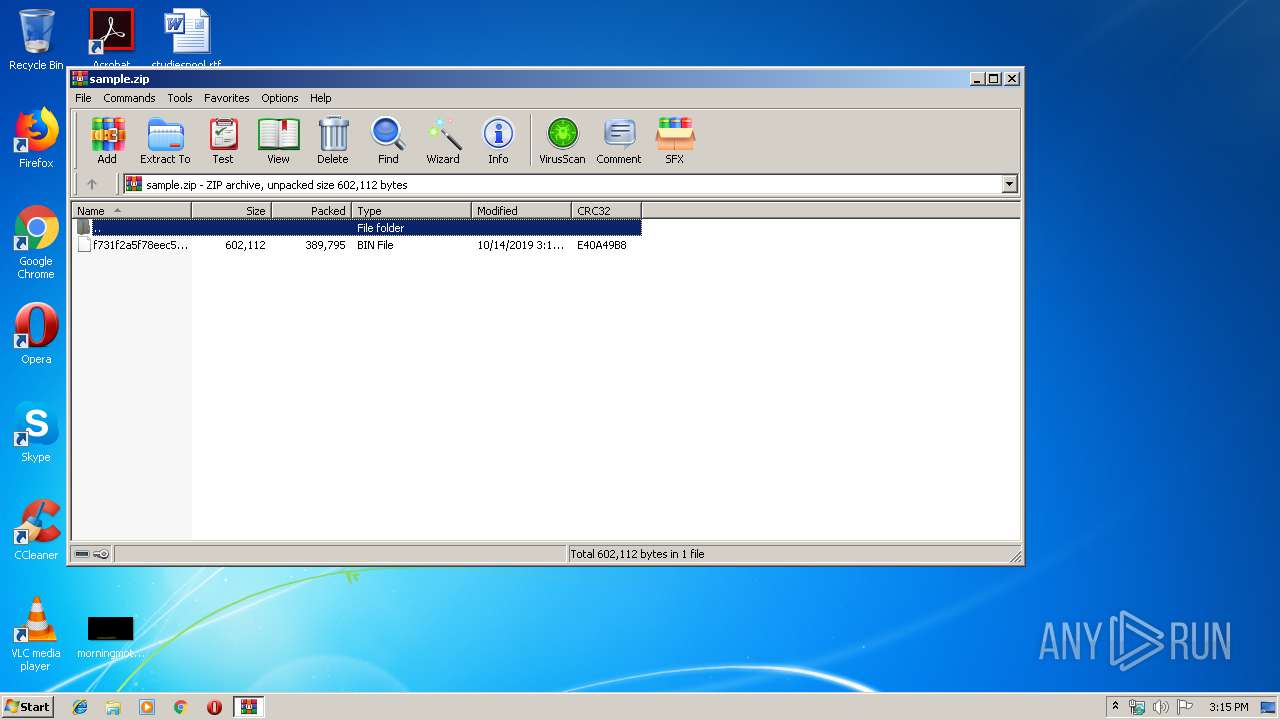
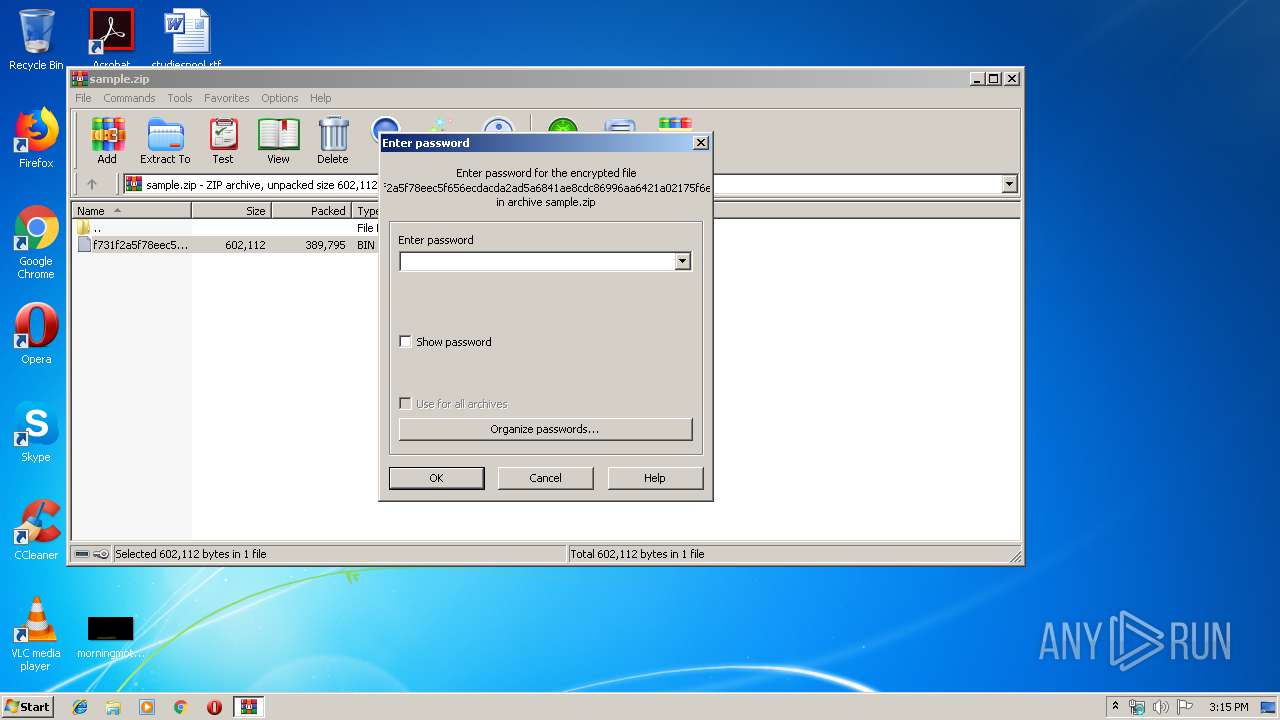
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | B3310E2292C110142D25BBD4AD6B342D |
| SHA1: | 9D89FD4FC996DA5FEF2E65A975EF45446563D5FC |
| SHA256: | 764F17B690D1FCDA21A28E6CD93C9AF4F190B62EFD31E311EE04FB686B04BD0F |
| SSDEEP: | 6144:7seOcYlJOjAHkeF4XoQhH33RhWUPmlg/iWVlusz5TntXFZVEnwxVAgXKReYYprl:4yY3OmPGhKhCvVwszv1nEwYEYQ |
MALICIOUS
Application was dropped or rewritten from another process
- omg.exe (PID: 2504)
- advhftbpe60dc.exe (PID: 3936)
- omg.exe (PID: 2580)
FORMBOOK was detected
- explorer.exe (PID: 352)
- msiexec.exe (PID: 4028)
- Firefox.exe (PID: 3896)
Connects to CnC server
- explorer.exe (PID: 352)
Changes the autorun value in the registry
- msiexec.exe (PID: 4028)
Actions looks like stealing of personal data
- msiexec.exe (PID: 4028)
Stealing of credential data
- msiexec.exe (PID: 4028)
SUSPICIOUS
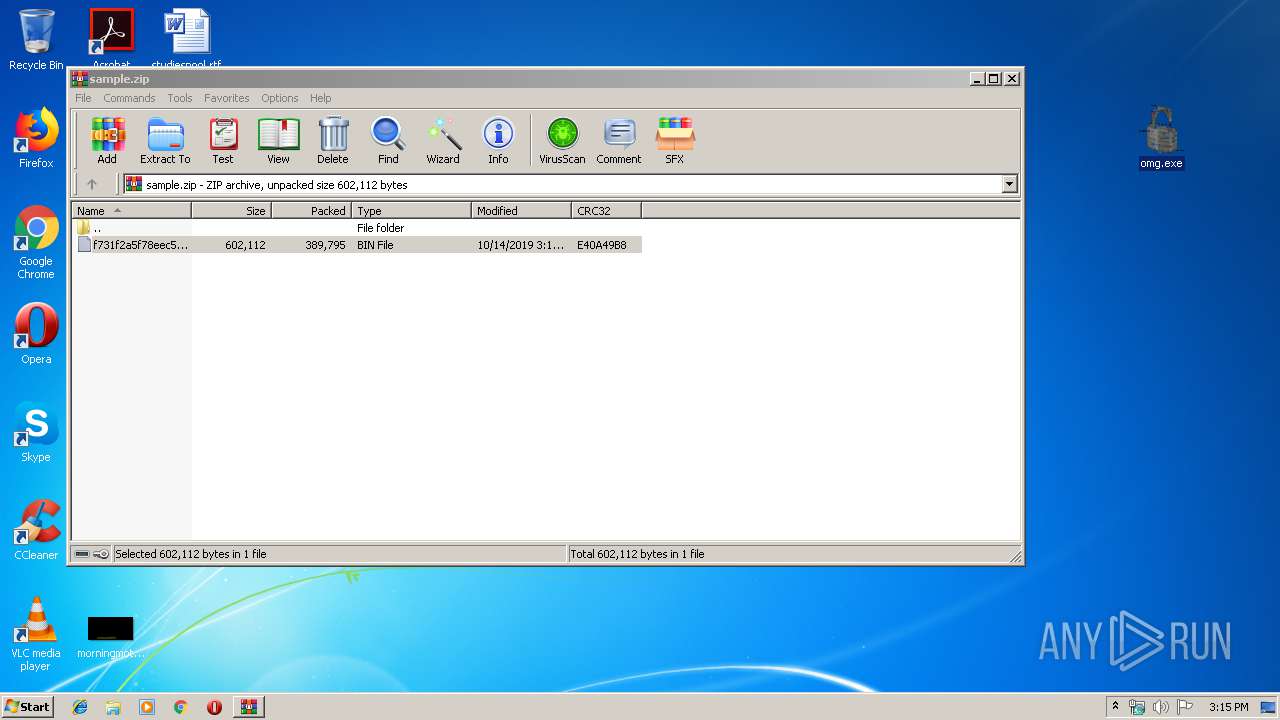
Application launched itself
- omg.exe (PID: 2504)
Executed via COM
- DllHost.exe (PID: 4040)
Starts CMD.EXE for commands execution
- msiexec.exe (PID: 4028)
Creates files in the program directory
- DllHost.exe (PID: 4040)
Loads DLL from Mozilla Firefox
- msiexec.exe (PID: 4028)
Executable content was dropped or overwritten
- explorer.exe (PID: 352)
- DllHost.exe (PID: 4040)
Creates files in the user directory
- msiexec.exe (PID: 4028)
INFO
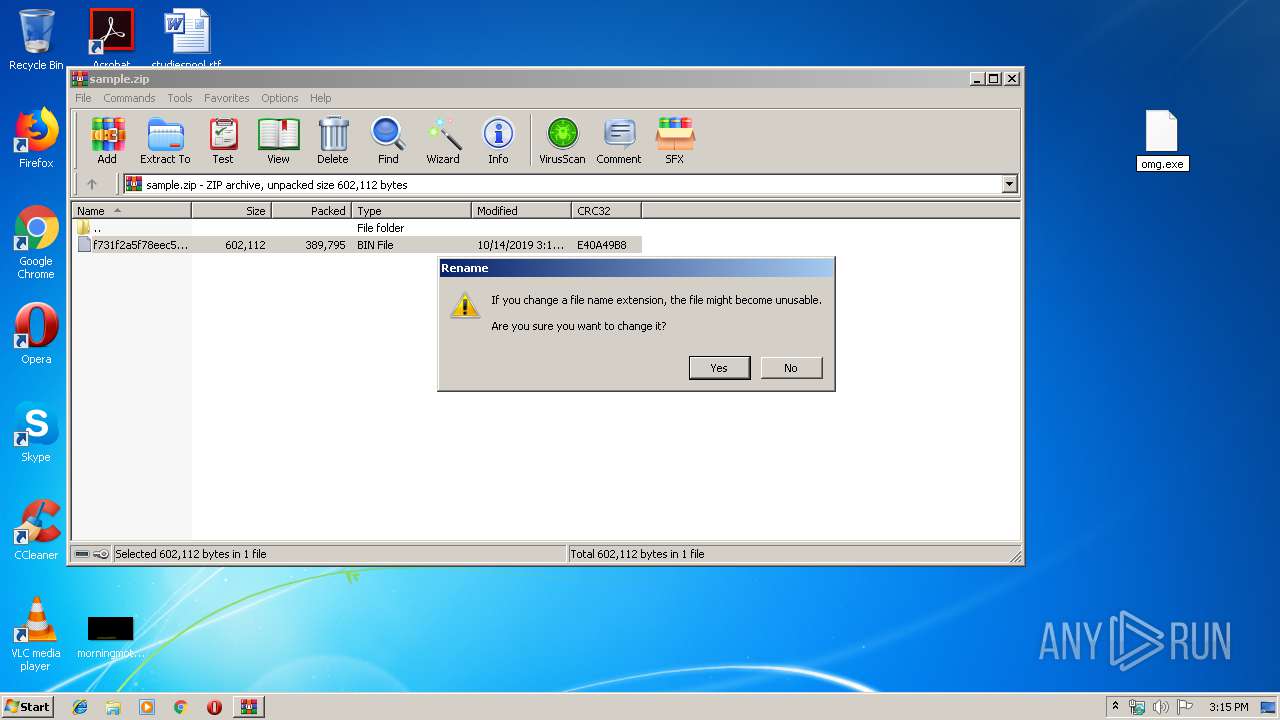
Manual execution by user
- omg.exe (PID: 2504)
- msiexec.exe (PID: 4028)
Reads the hosts file
- msiexec.exe (PID: 4028)
Creates files in the user directory
- Firefox.exe (PID: 3896)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
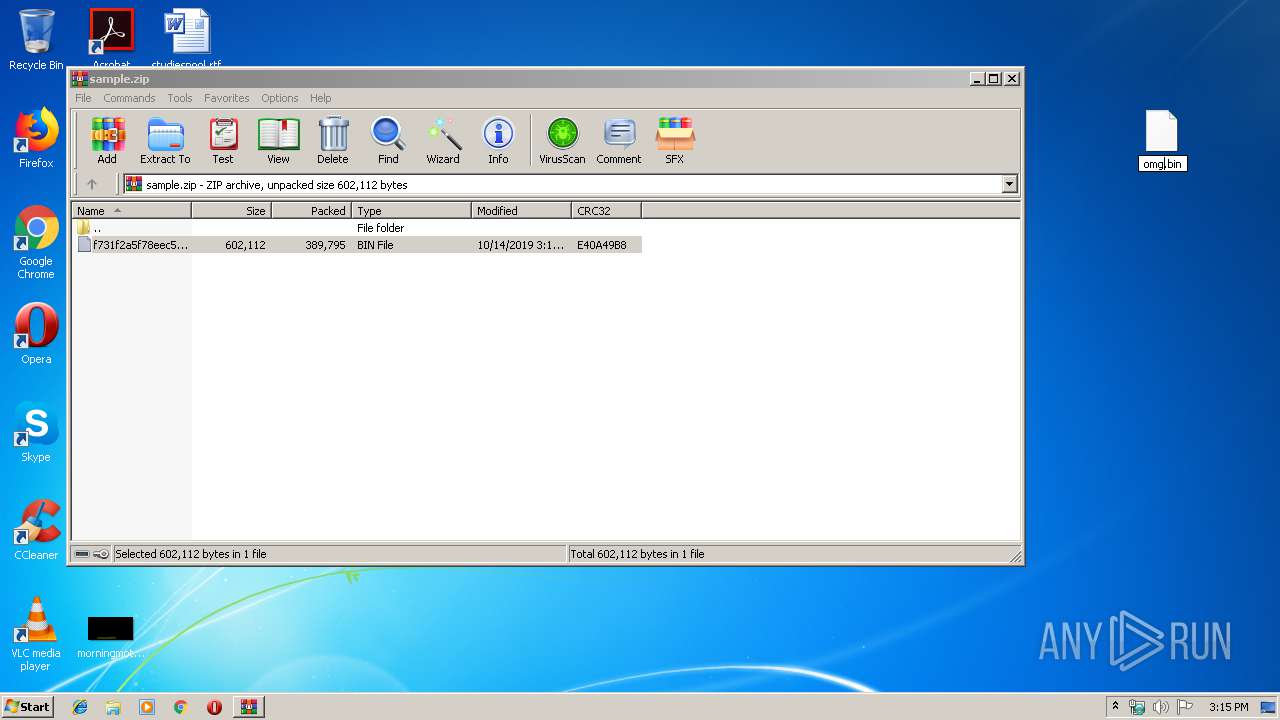
| ZipRequiredVersion: | 788 |
|---|---|
| ZipBitFlag: | 0x0001 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2019:10:14 14:12:23 |
| ZipCRC: | 0xe40a49b8 |
| ZipCompressedSize: | 389795 |
| ZipUncompressedSize: | 602112 |
| ZipFileName: | f731f2a5f78eec5f656ecdacda2ad5a6841ae8cdc86996aa6421a02175f6eebb.bin |
Total processes
46
Monitored processes
9
Malicious processes
3
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 352 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2200 | /c del "C:\Users\admin\Desktop\omg.exe" | C:\Windows\System32\cmd.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
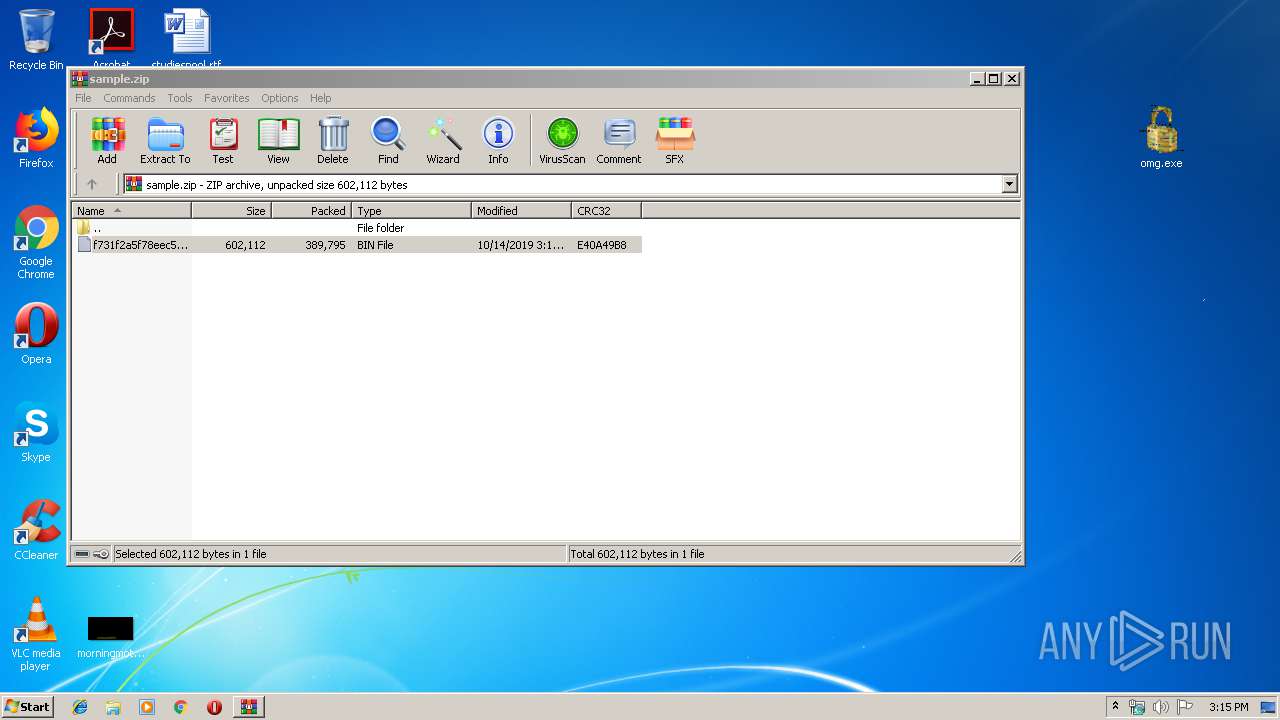
| 2456 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\sample.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 2504 | "C:\Users\admin\Desktop\omg.exe" | C:\Users\admin\Desktop\omg.exe | — | explorer.exe | |||||||||||
User: admin Company: MECHANUnderbreath Integrity Level: MEDIUM Exit code: 0 Version: 1.08.0007 Modules
| |||||||||||||||
| 2580 | "C:\Users\admin\Desktop\omg.exe" | C:\Users\admin\Desktop\omg.exe | — | omg.exe | |||||||||||
User: admin Company: MECHANUnderbreath Integrity Level: MEDIUM Exit code: 0 Version: 1.08.0007 Modules
| |||||||||||||||
| 3896 | "C:\Program Files\Mozilla Firefox\Firefox.exe" | C:\Program Files\Mozilla Firefox\Firefox.exe | msiexec.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 68.0.1 Modules
| |||||||||||||||
| 3936 | "C:\Program Files\G0ph\advhftbpe60dc.exe" | C:\Program Files\G0ph\advhftbpe60dc.exe | — | explorer.exe | |||||||||||
User: admin Company: MECHANUnderbreath Integrity Level: MEDIUM Exit code: 0 Version: 1.08.0007 Modules
| |||||||||||||||
| 4028 | "C:\Windows\System32\msiexec.exe" | C:\Windows\System32\msiexec.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 4040 | C:\Windows\system32\DllHost.exe /Processid:{3AD05575-8857-4850-9277-11B85BDB8E09} | C:\Windows\system32\DllHost.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
3 060
Read events
3 038
Write events
22
Delete events
0
Modification events
| (PID) Process: | (352) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2456) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2456) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2456) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2456) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\sample.zip | |||
| (PID) Process: | (2456) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2456) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2456) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2456) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (352) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.zip\OpenWithList |
| Operation: | write | Name: | a |
Value: WinRAR.exe | |||
Executable files
4
Suspicious files
73
Text files
1
Unknown types
0
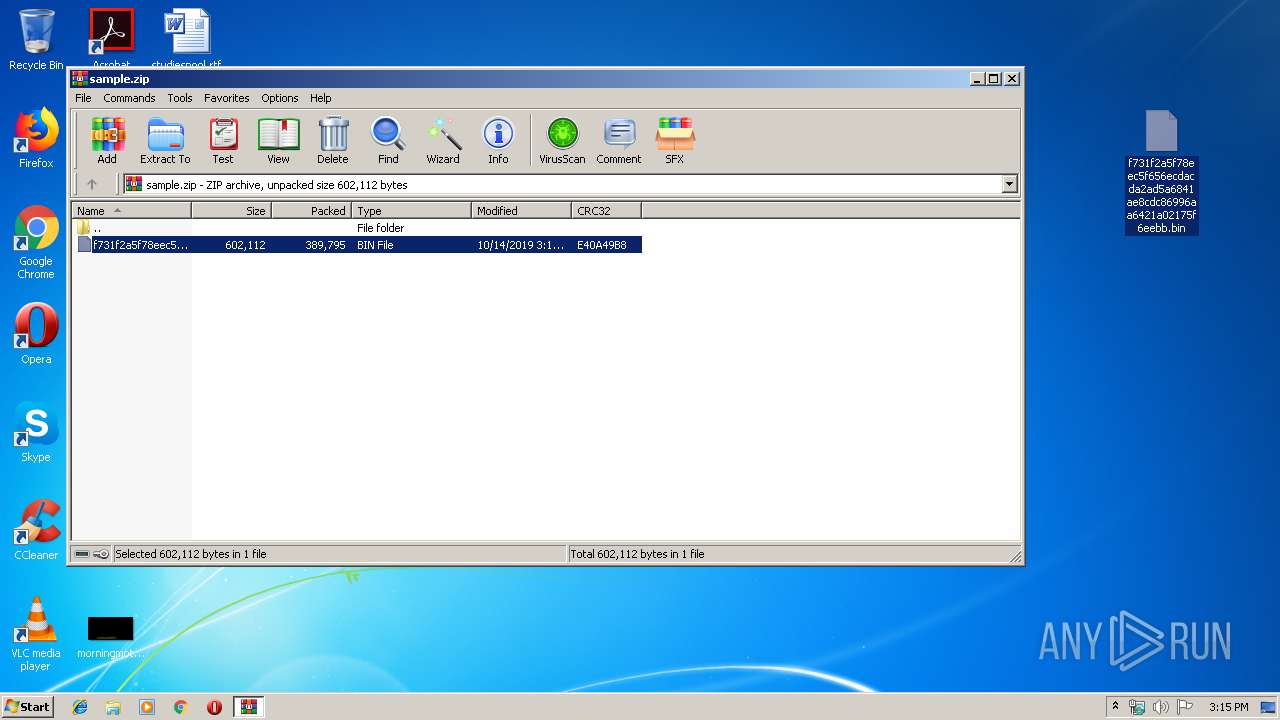
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2456 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb2456.1071\f731f2a5f78eec5f656ecdacda2ad5a6841ae8cdc86996aa6421a02175f6eebb.bin | — | |
MD5:— | SHA256:— | |||
| 4028 | msiexec.exe | C:\Users\admin\AppData\Roaming\892R8X6E\892logrc.ini | binary | |
MD5:— | SHA256:— | |||
| 352 | explorer.exe | C:\Users\admin\Desktop\f731f2a5f78eec5f656ecdacda2ad5a6841ae8cdc86996aa6421a02175f6eebb.bin | executable | |
MD5:— | SHA256:— | |||
| 4028 | msiexec.exe | C:\Users\admin\AppData\Roaming\892R8X6E\892logim.jpeg | image | |
MD5:— | SHA256:— | |||
| 4040 | DllHost.exe | C:\Program Files\G0ph\advhftbpe60dc.exe | executable | |
MD5:— | SHA256:— | |||
| 352 | explorer.exe | C:\Users\admin\Desktop\omg.exe | executable | |
MD5:— | SHA256:— | |||
| 352 | explorer.exe | C:\Users\admin\AppData\Local\Temp\G0ph\advhftbpe60dc.exe | executable | |
MD5:— | SHA256:— | |||
| 4028 | msiexec.exe | C:\Users\admin\AppData\Roaming\892R8X6E\892logrv.ini | binary | |
MD5:BA3B6BC807D4F76794C4B81B09BB9BA5 | SHA256:6EEBF968962745B2E9DE2CA969AF7C424916D4E3FE3CC0BB9B3D414ABFCE9507 | |||
| 4028 | msiexec.exe | C:\Users\admin\AppData\Roaming\892R8X6E\892logri.ini | binary | |
MD5:D63A82E5D81E02E399090AF26DB0B9CB | SHA256:EAECE2EBA6310253249603033C744DD5914089B0BB26BDE6685EC9813611BAAE | |||
| 3896 | Firefox.exe | C:\Users\admin\AppData\Roaming\892R8X6E\892logrf.ini | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
5
DNS requests
5
Threats
9
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
352 | explorer.exe | POST | — | 54.152.17.83:80 | http://www.colleenblake.com/sg/ | US | — | — | malicious |
352 | explorer.exe | GET | 301 | 54.152.17.83:80 | http://www.colleenblake.com/sg/?3f9L=RKYwUGtsyxq/LqeValKDRIGed7Ogr0G53QEm84mZqi7V+lhB2HOfDGYAy/BElzROWa8c2g==&BbBX=LhTpETx8Zdn&sql=1 | US | html | 176 b | malicious |
352 | explorer.exe | POST | — | 54.152.17.83:80 | http://www.colleenblake.com/sg/ | US | — | — | malicious |
352 | explorer.exe | POST | — | 54.152.17.83:80 | http://www.colleenblake.com/sg/ | US | — | — | malicious |
352 | explorer.exe | GET | 302 | 213.186.33.5:80 | http://www.freenfield.com/sg/?3f9L=Sm+YPTeSv3486SfJgEujGF5Gek30Oxw53f6RJd3EbhL1PPilrZfqOaJHRsSa5Pf7xeKhsg==&BbBX=LhTpETx8Zdn | FR | html | 154 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
352 | explorer.exe | 54.152.17.83:80 | www.colleenblake.com | Amazon.com, Inc. | US | malicious |
— | — | 54.152.17.83:80 | www.colleenblake.com | Amazon.com, Inc. | US | malicious |
352 | explorer.exe | 213.186.33.5:80 | www.freenfield.com | OVH SAS | FR | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.freenfield.com |
| malicious |
www.avalonpersonaltraining.com |
| unknown |
www.colleenblake.com |
| malicious |
www.alexpitch.com |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
352 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] FormBook CnC Checkin (GET) |
352 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] FormBook CnC Checkin (GET) |
352 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] TrojanSpy:FormBook CnC Checkin (POST) |
352 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] TrojanSpy:FormBook CnC Checkin (POST) |
352 | explorer.exe | A Network Trojan was detected | MALWARE [PTsecurity] FormBook CnC Checkin (POST) |
4 ETPRO signatures available at the full report