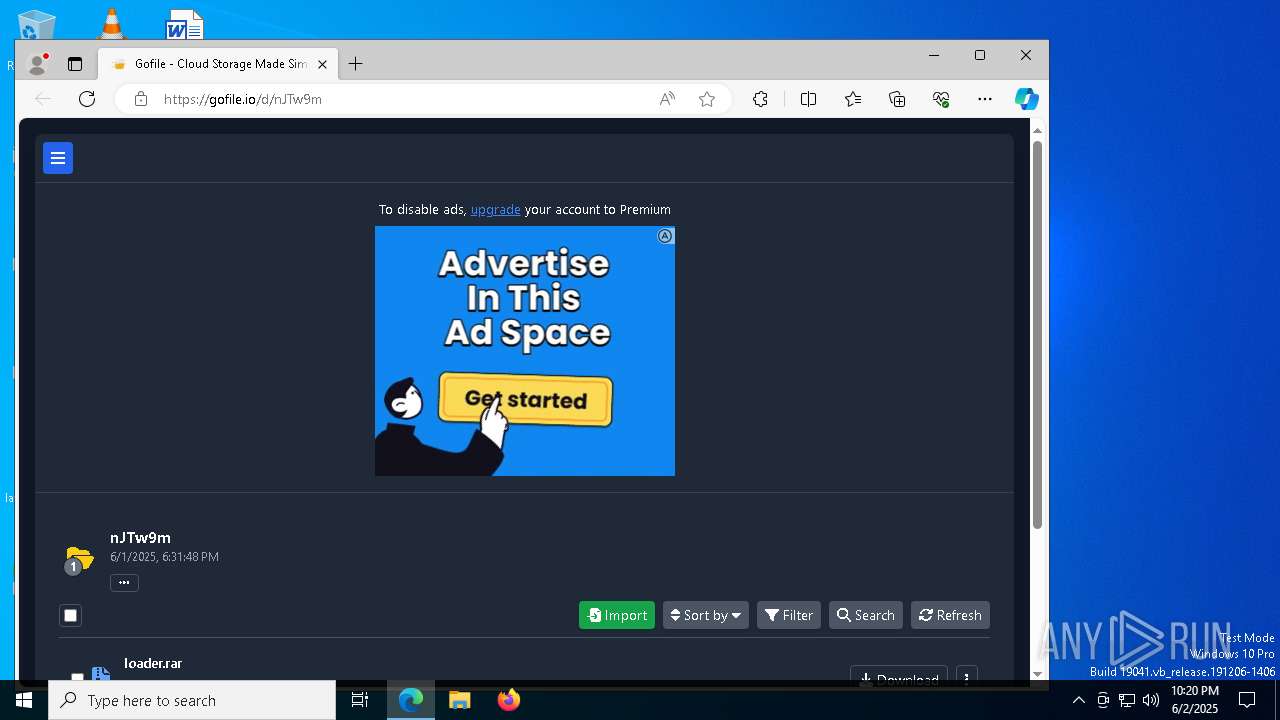
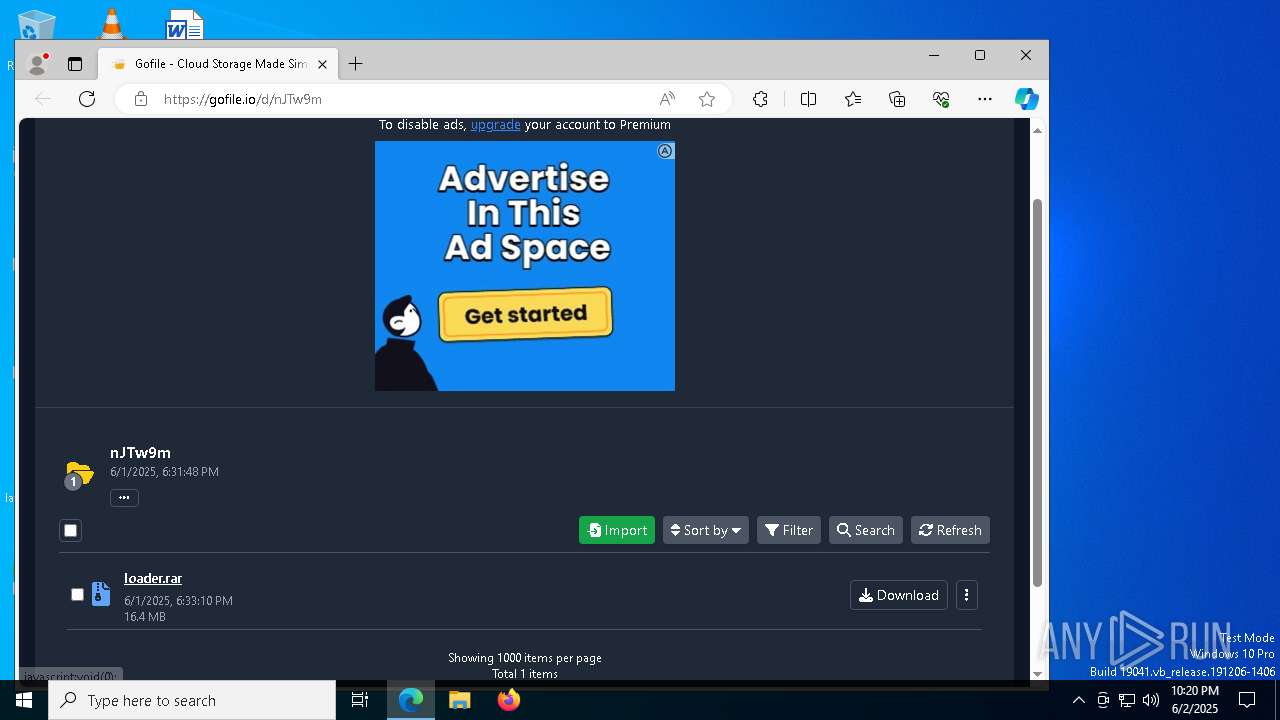
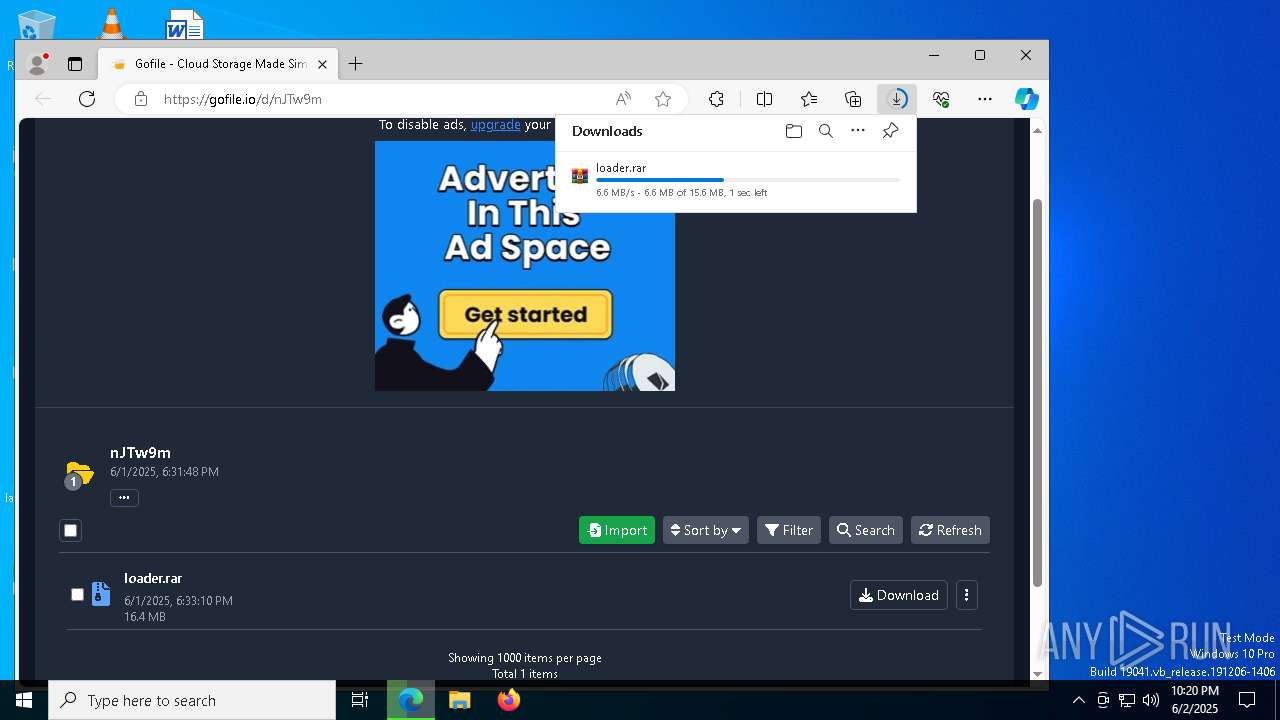
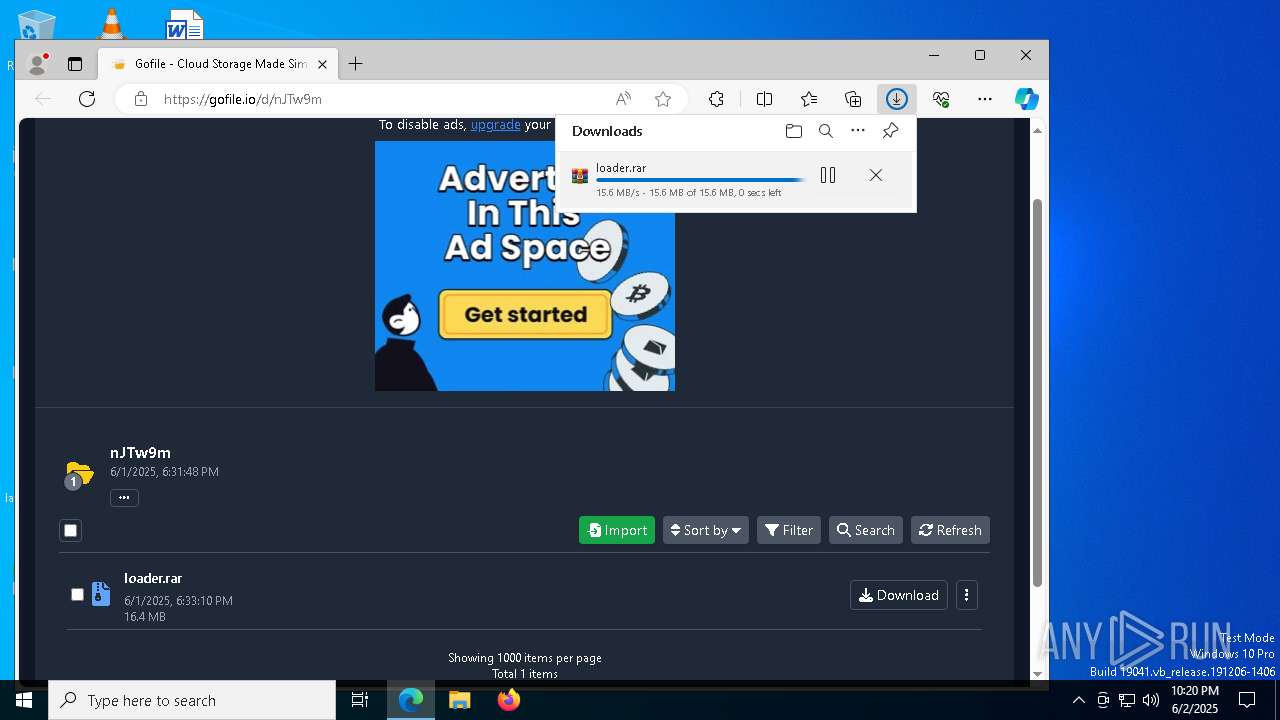
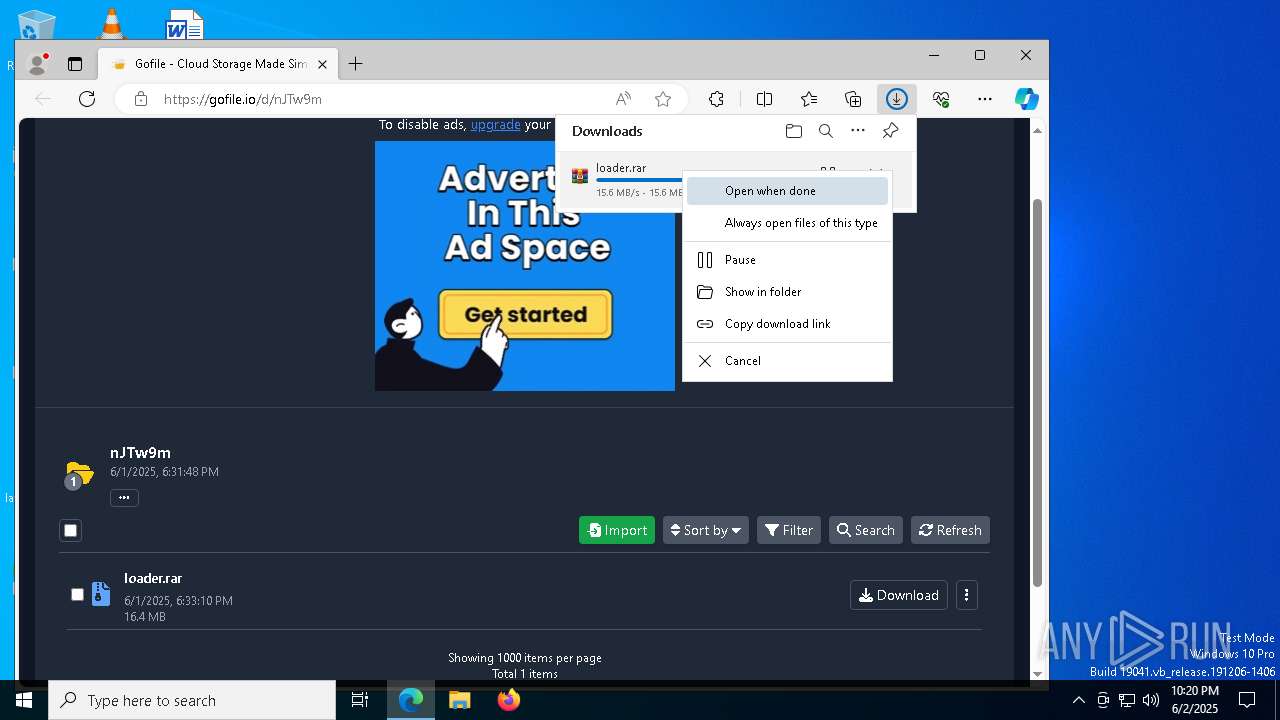
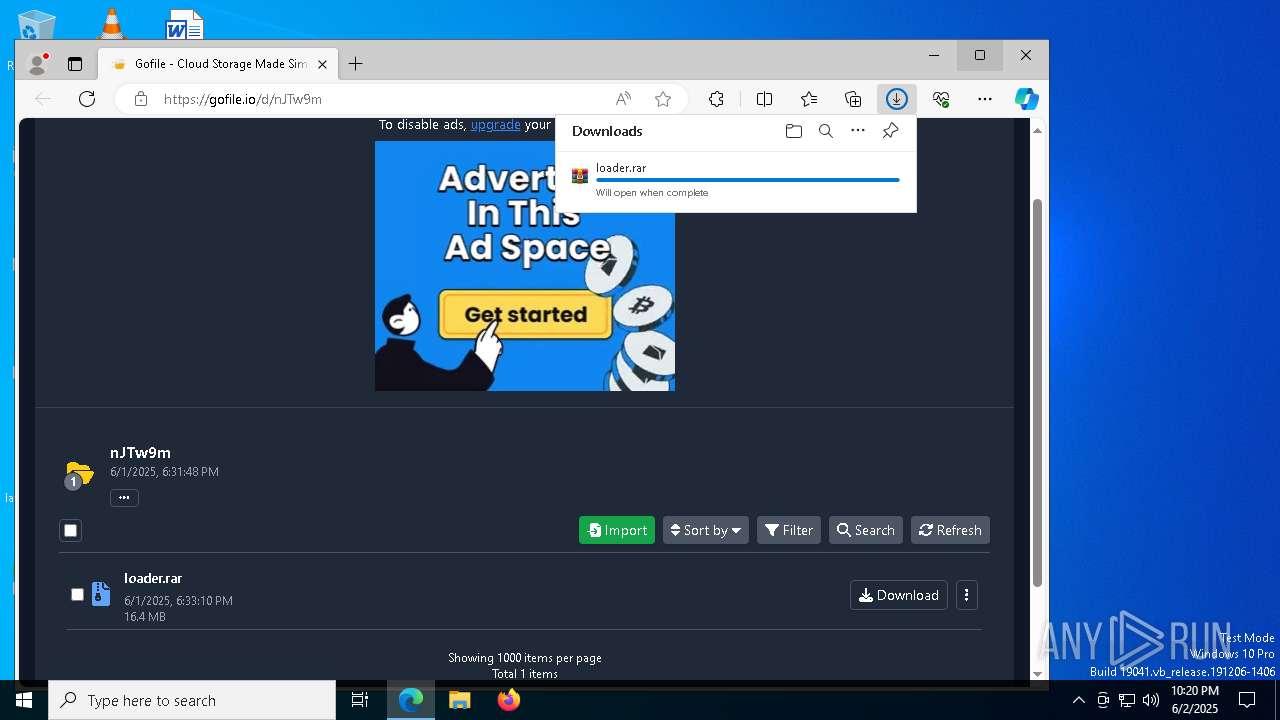
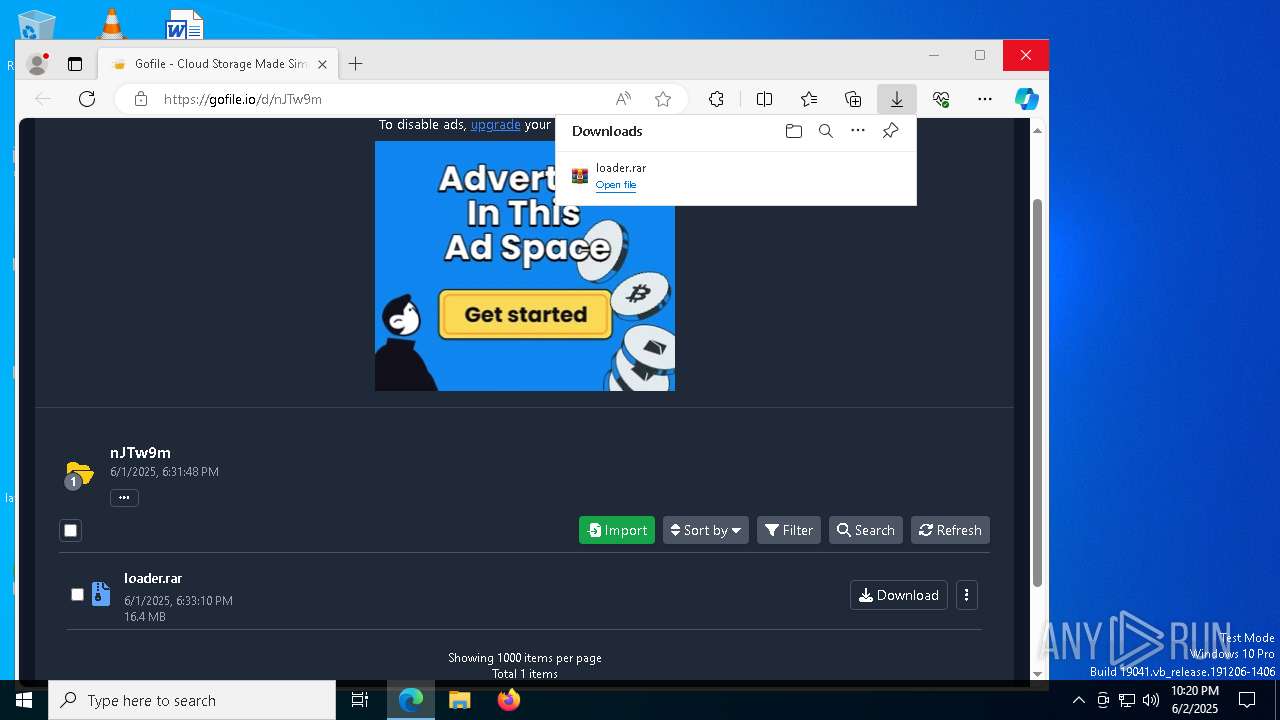
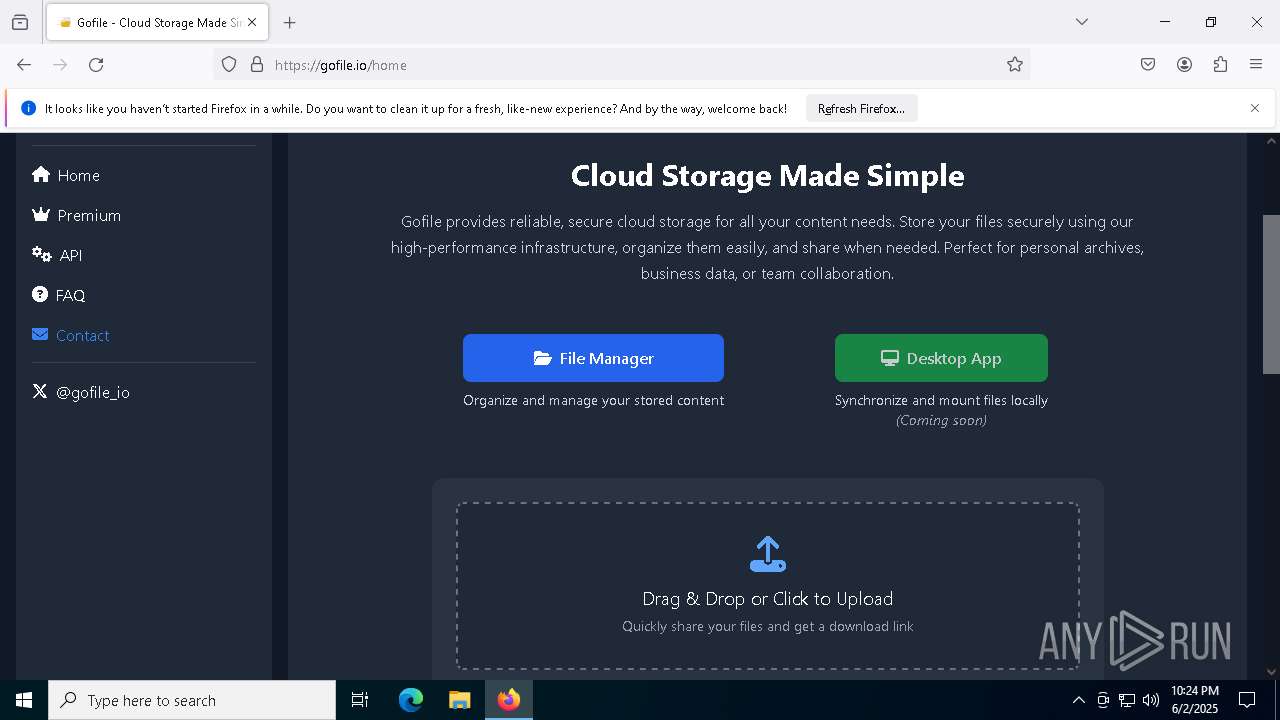
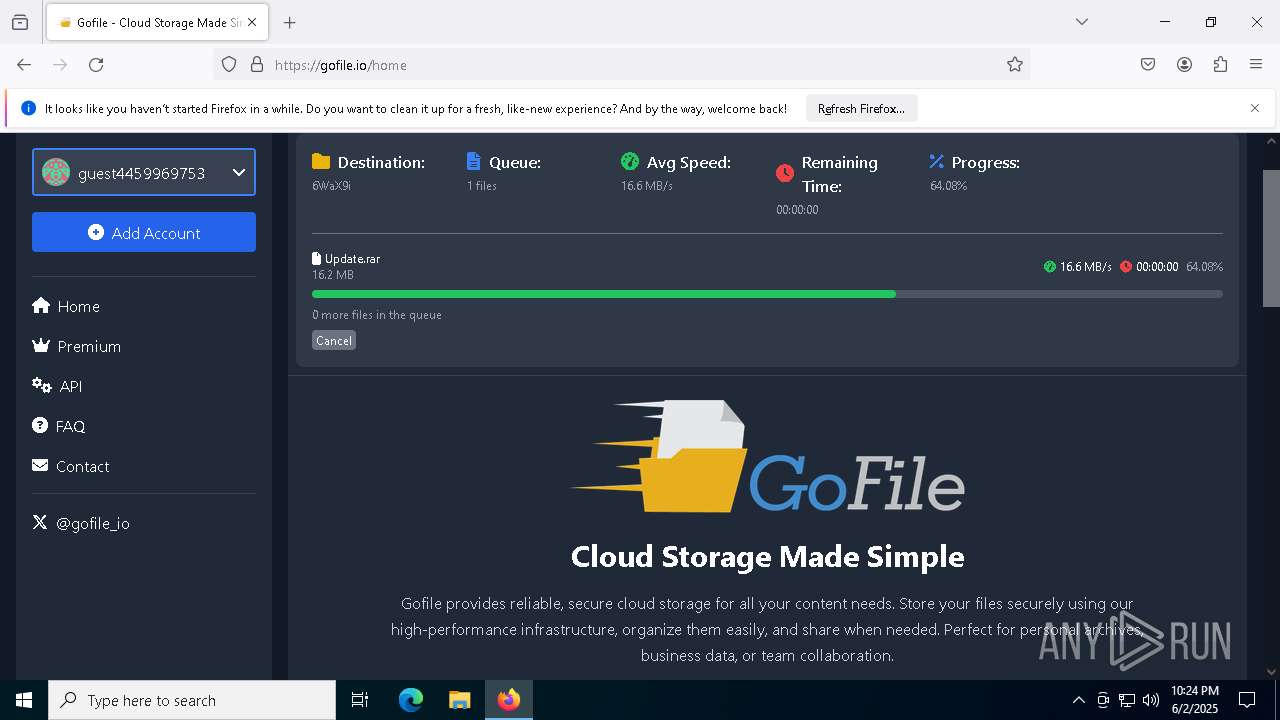
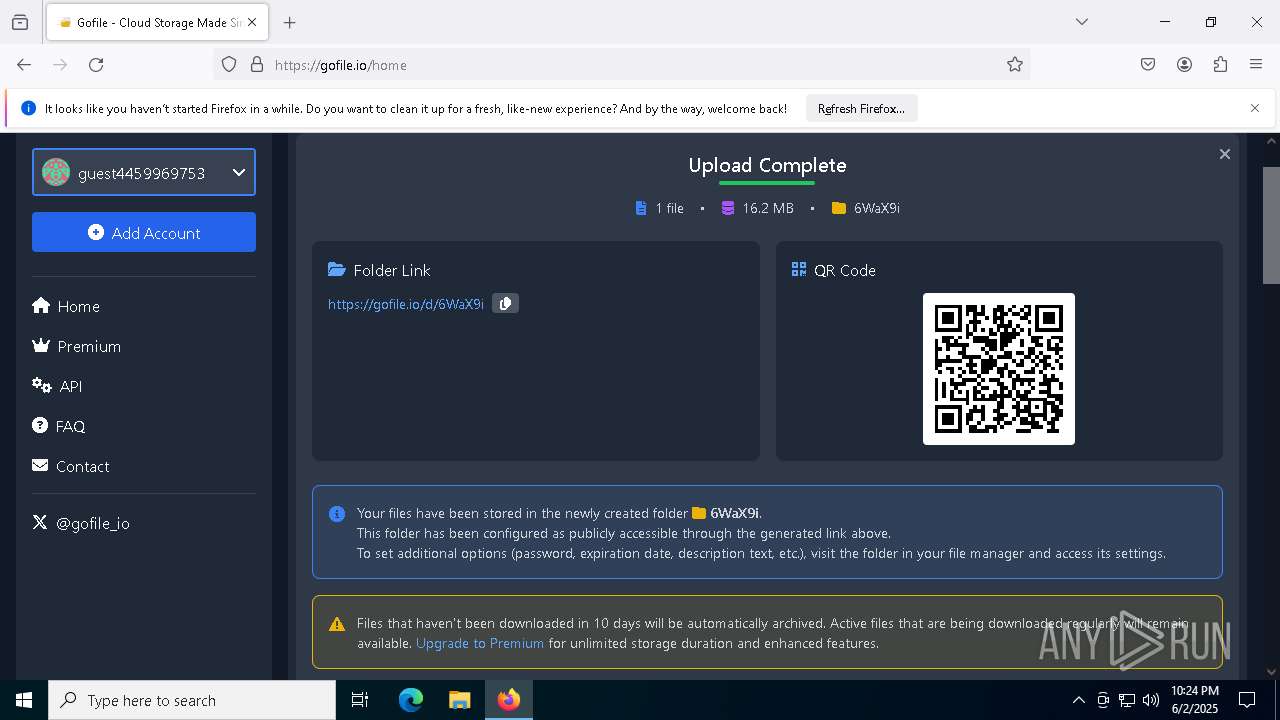
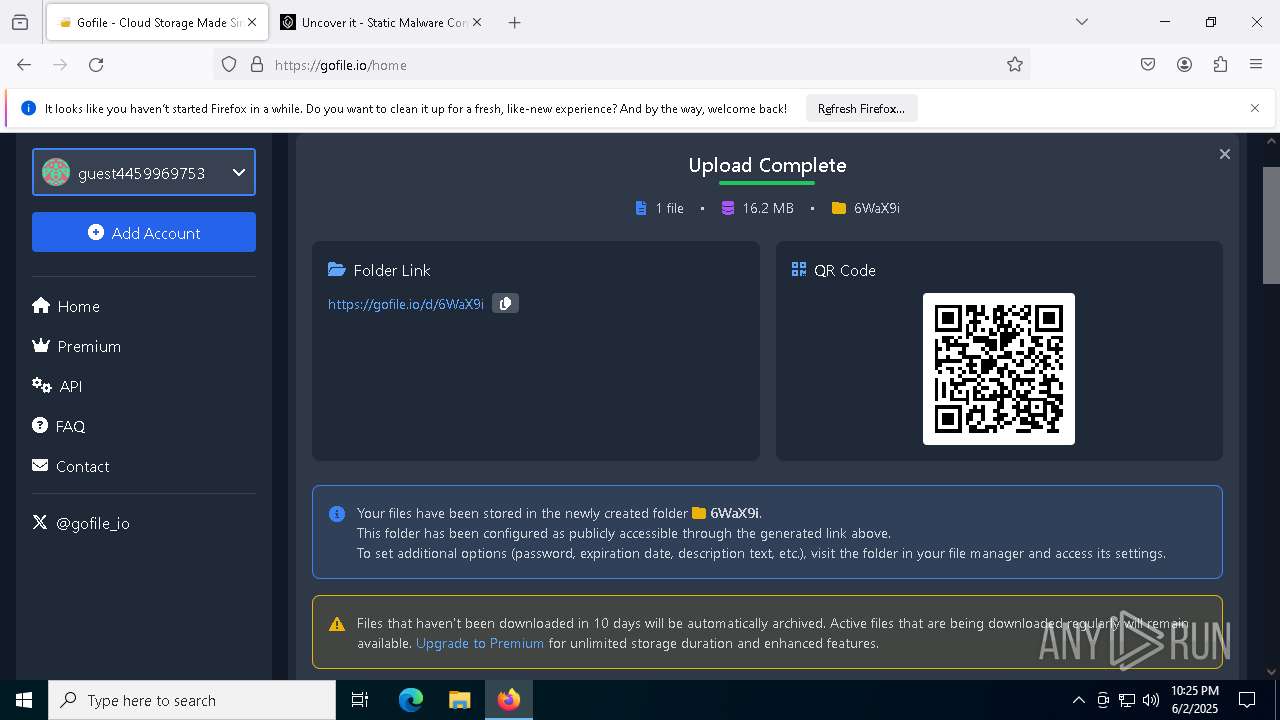
| URL: | https://gofile.io/d/nJTw9m |
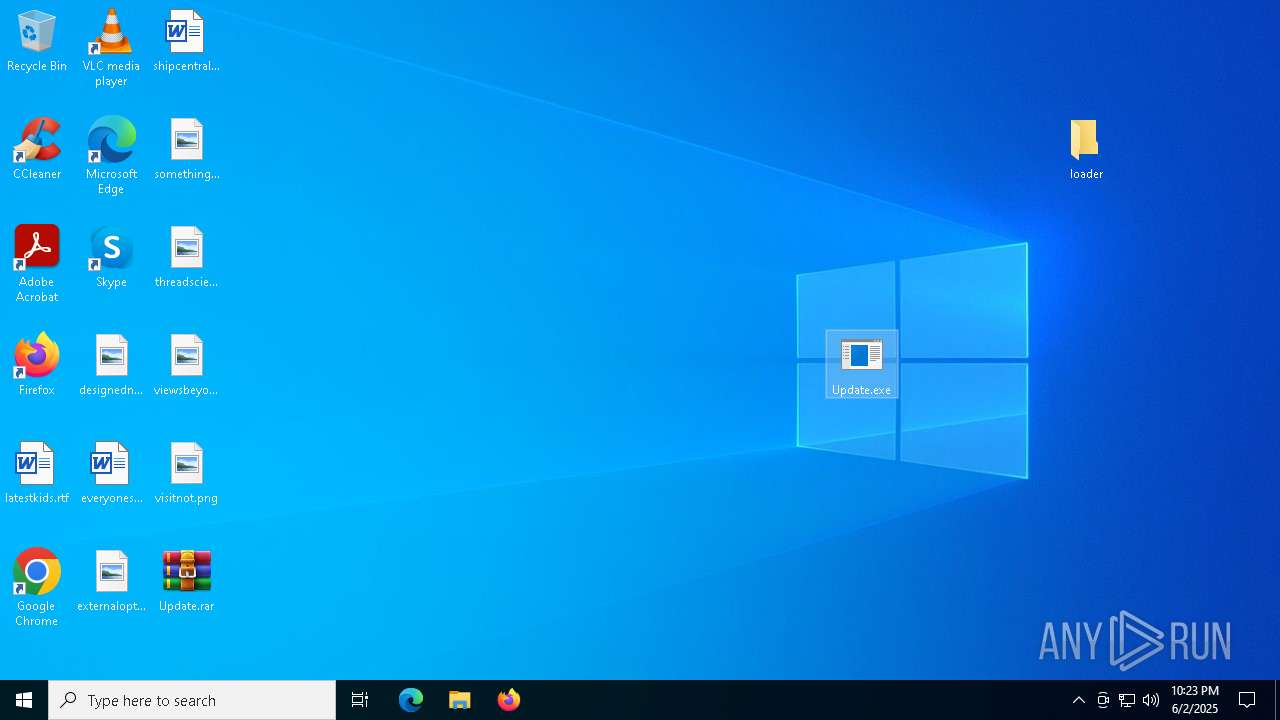
| Full analysis: | https://app.any.run/tasks/5ec58471-9830-46c6-bf21-1dee4cfb985c |
| Verdict: | Malicious activity |
| Threats: | Lumma is an information stealer, developed using the C programming language. It is offered for sale as a malware-as-a-service, with several plans available. It usually targets cryptocurrency wallets, login credentials, and other sensitive information on a compromised system. The malicious software regularly gets updates that improve and expand its functionality, making it a serious stealer threat. |
| Analysis date: | June 02, 2025, 22:20:13 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | A10478E175CC7525B97BE4839DB96CCE |
| SHA1: | DB5BAC8FC33DC0E0E0D9468B403156379766D5CD |
| SHA256: | 75D7756DBE41994E7A537562DA9694DA059DED6C777F9531265E9F15B3929BCF |
| SSDEEP: | 3:N8rxL1VScIn:2ZqcI |
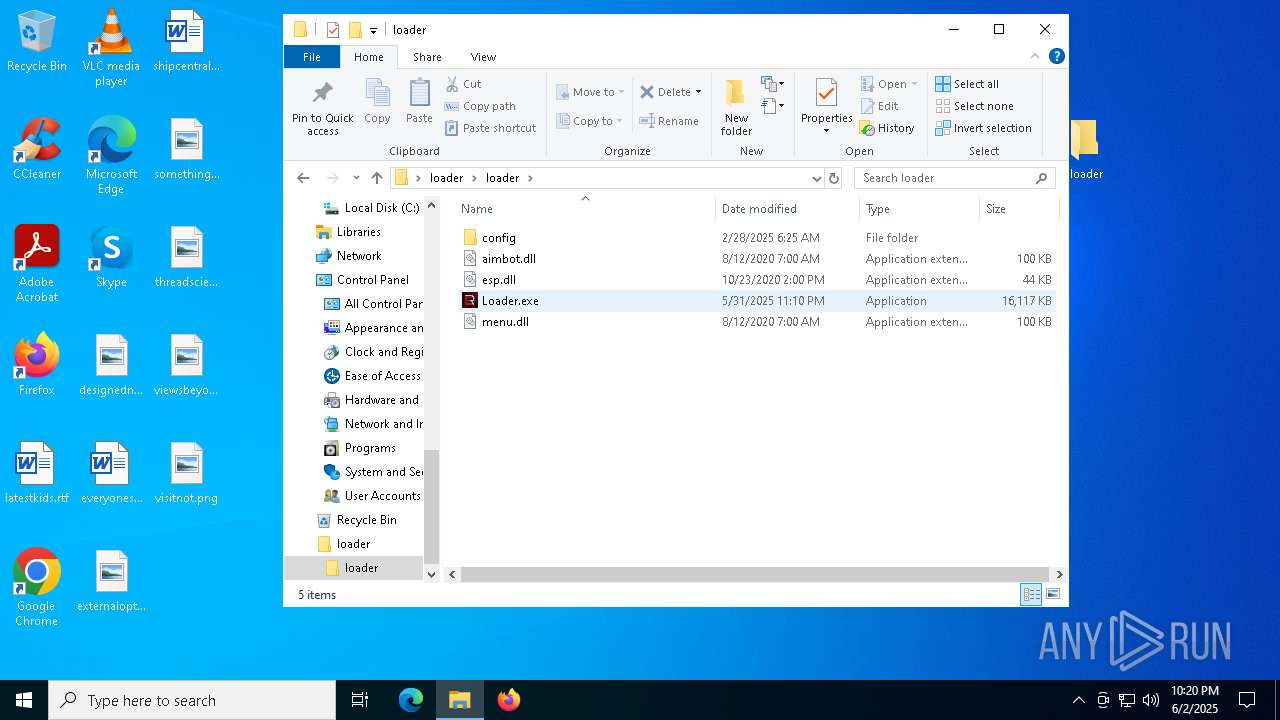
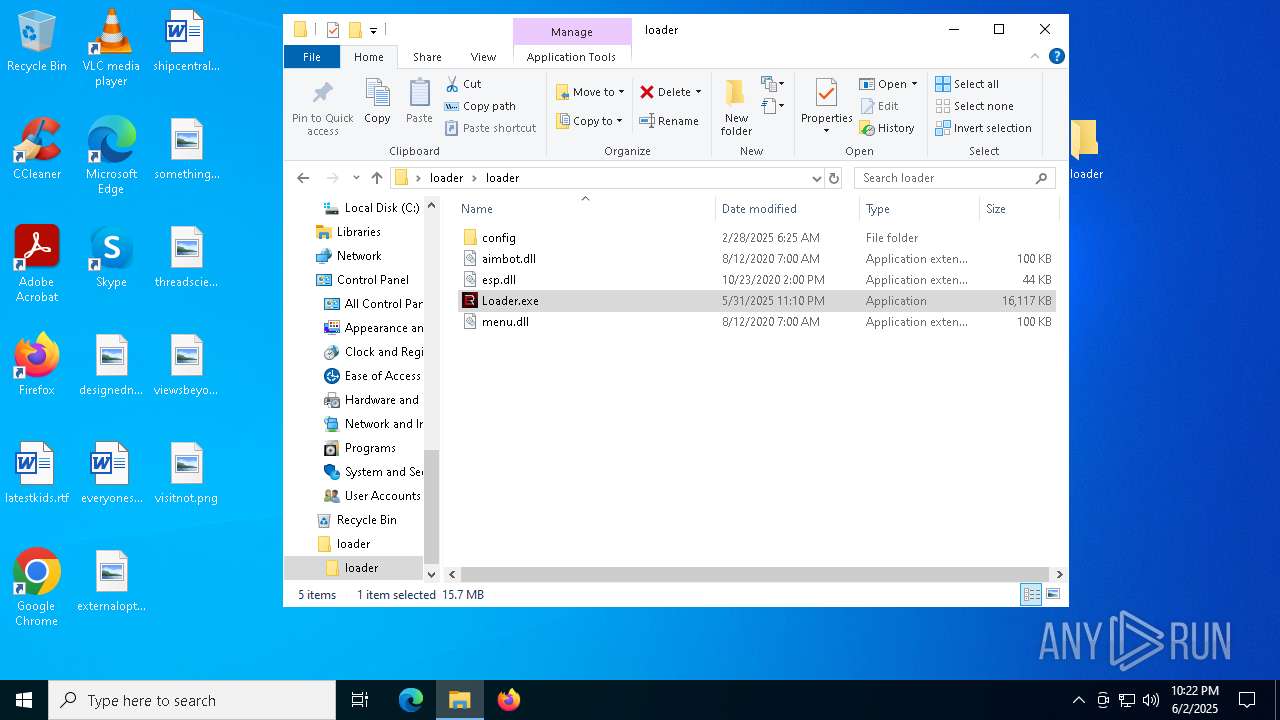
MALICIOUS
TROX has been detected
- Loader.exe (PID: 7048)
- Loader.exe (PID: 5020)
Starts NET.EXE for service management
- net.exe (PID: 7368)
- cmd.exe (PID: 3272)
- cmd.exe (PID: 7964)
- net.exe (PID: 8060)
Actions looks like stealing of personal data
- Loader.exe (PID: 7984)
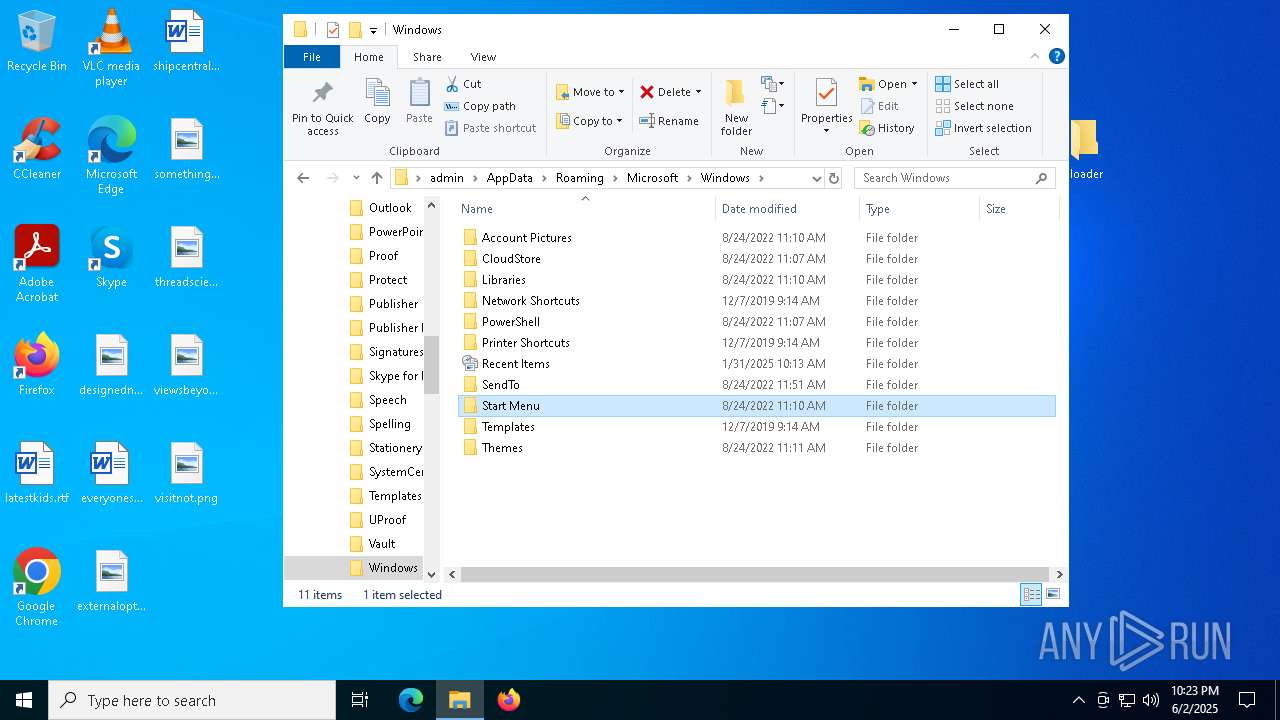
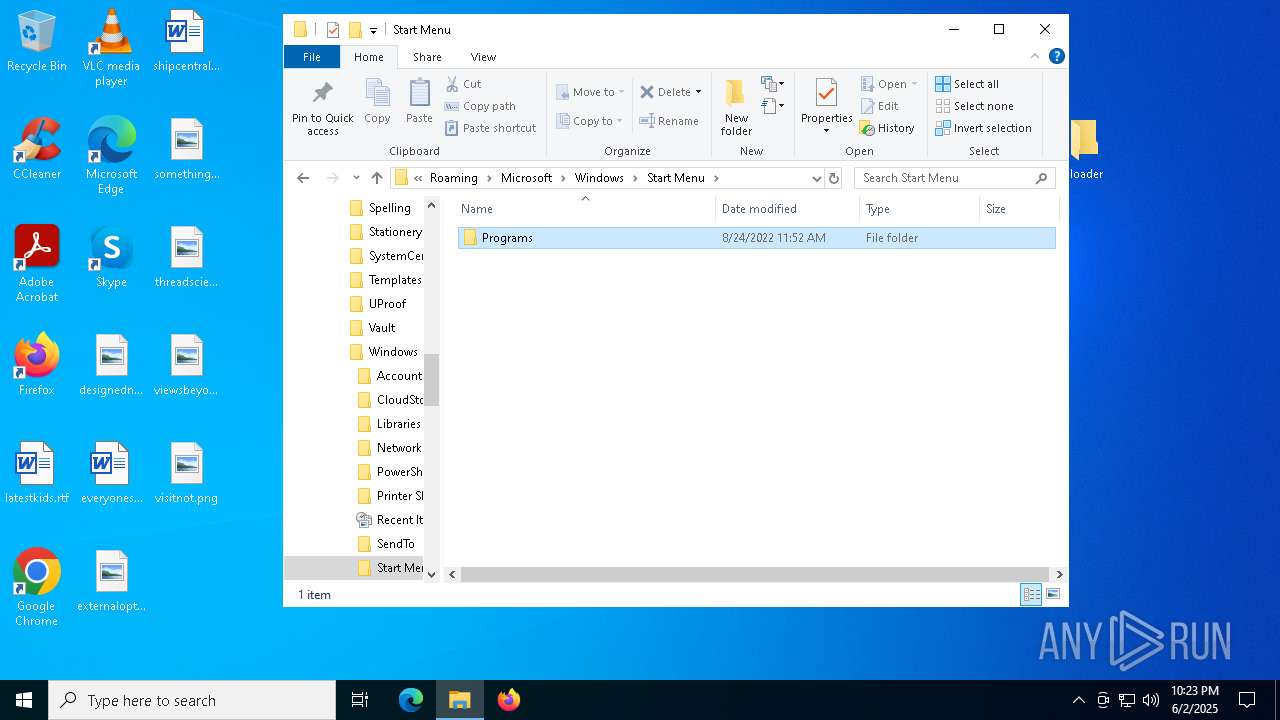
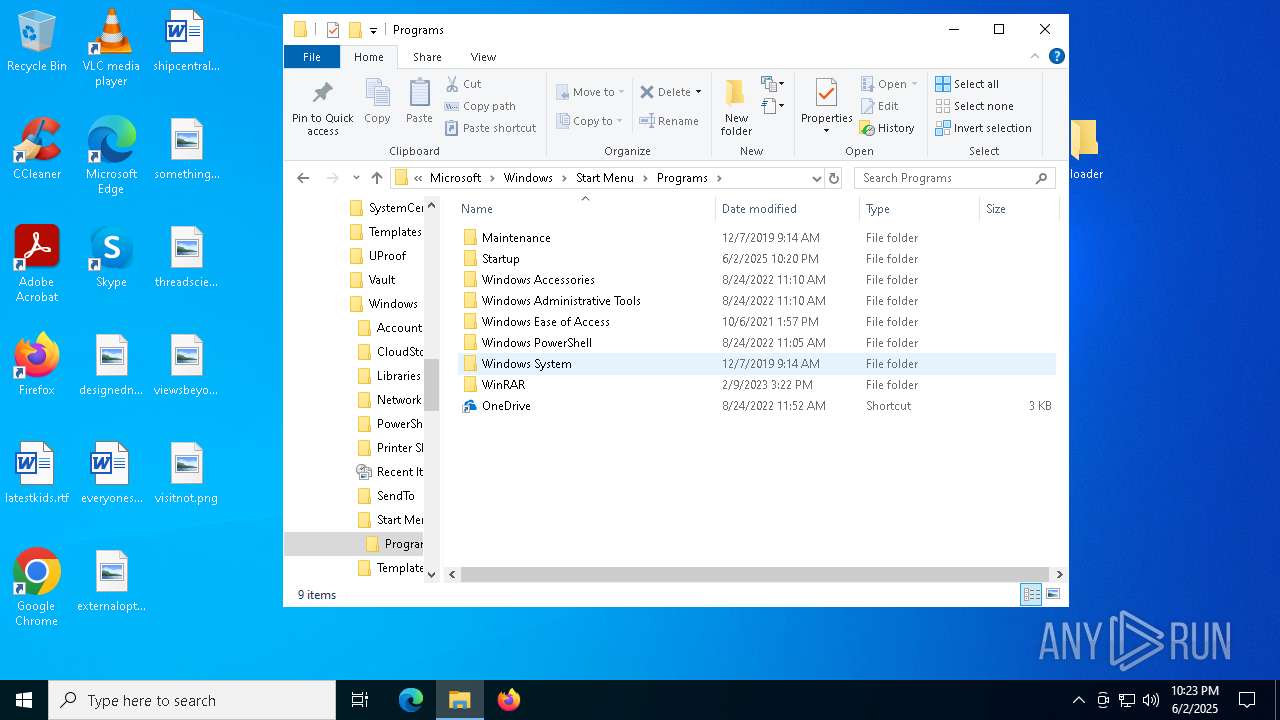
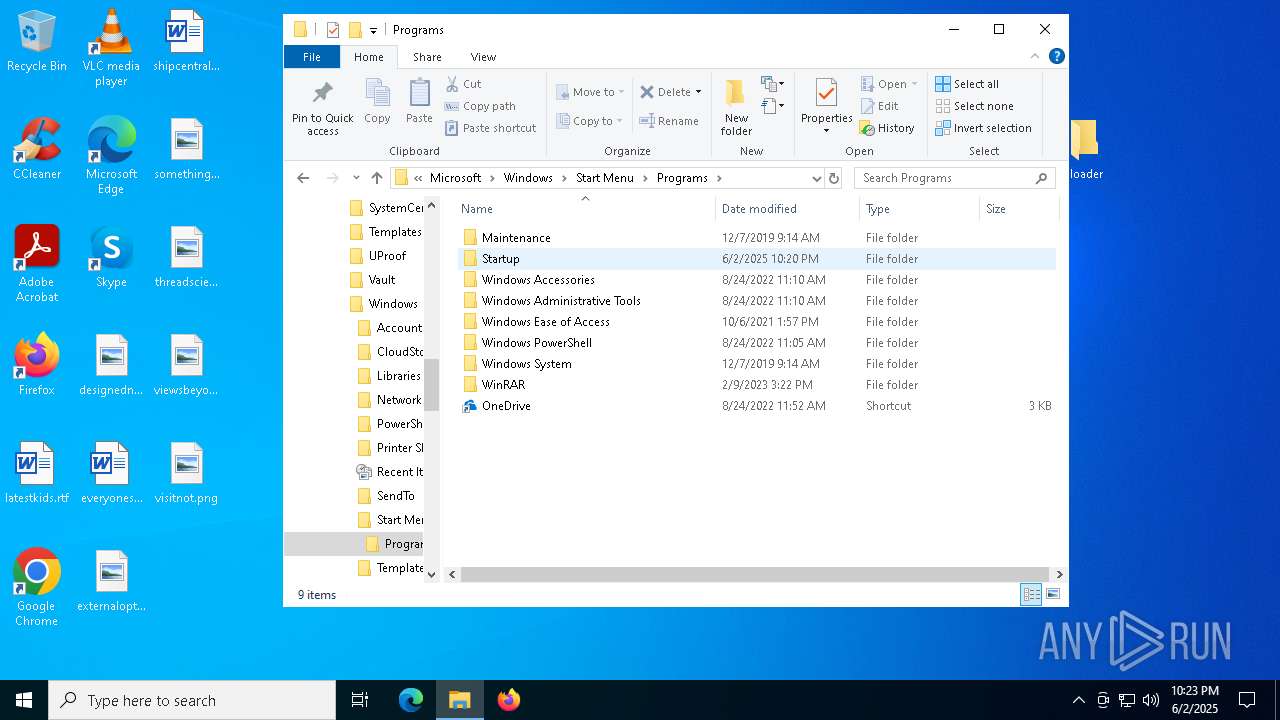
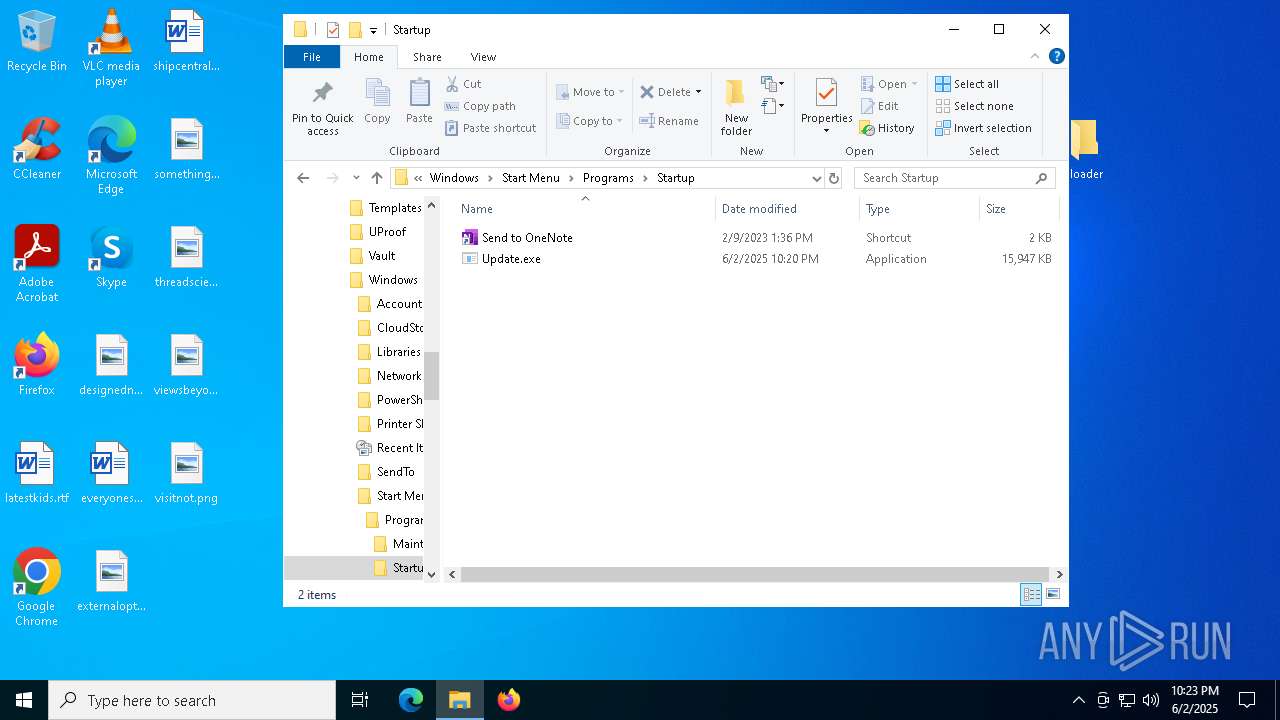
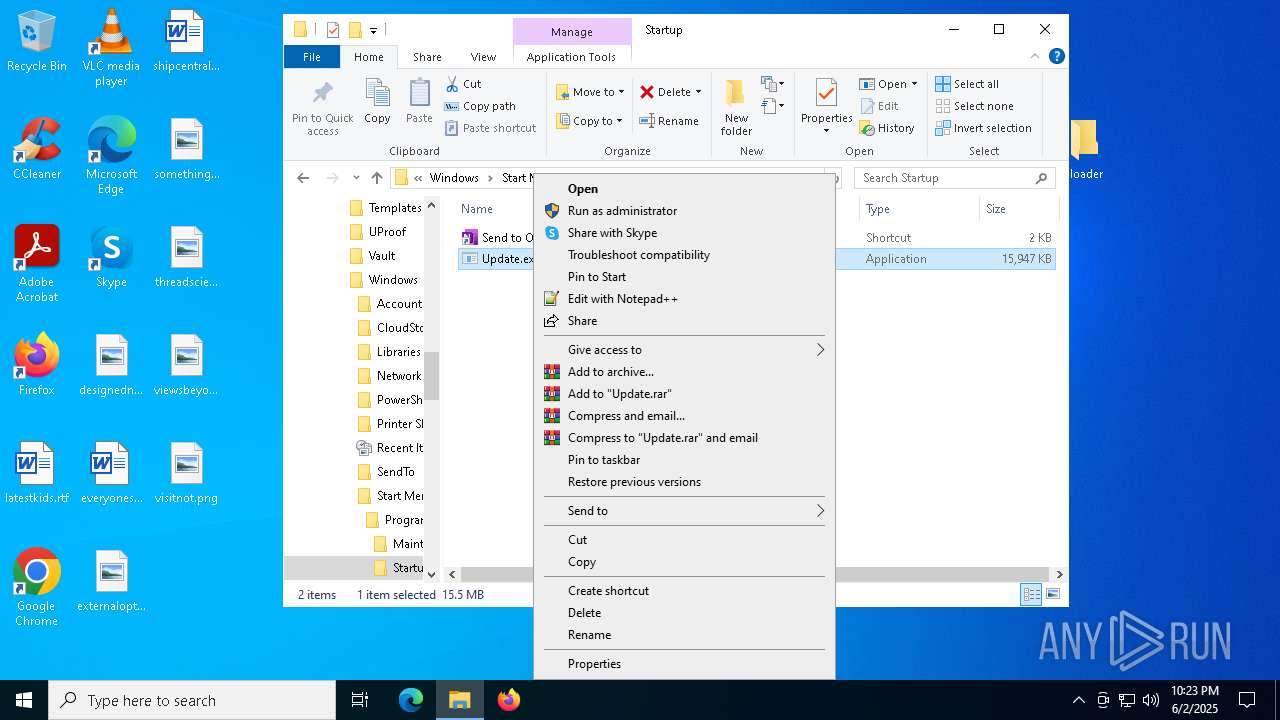
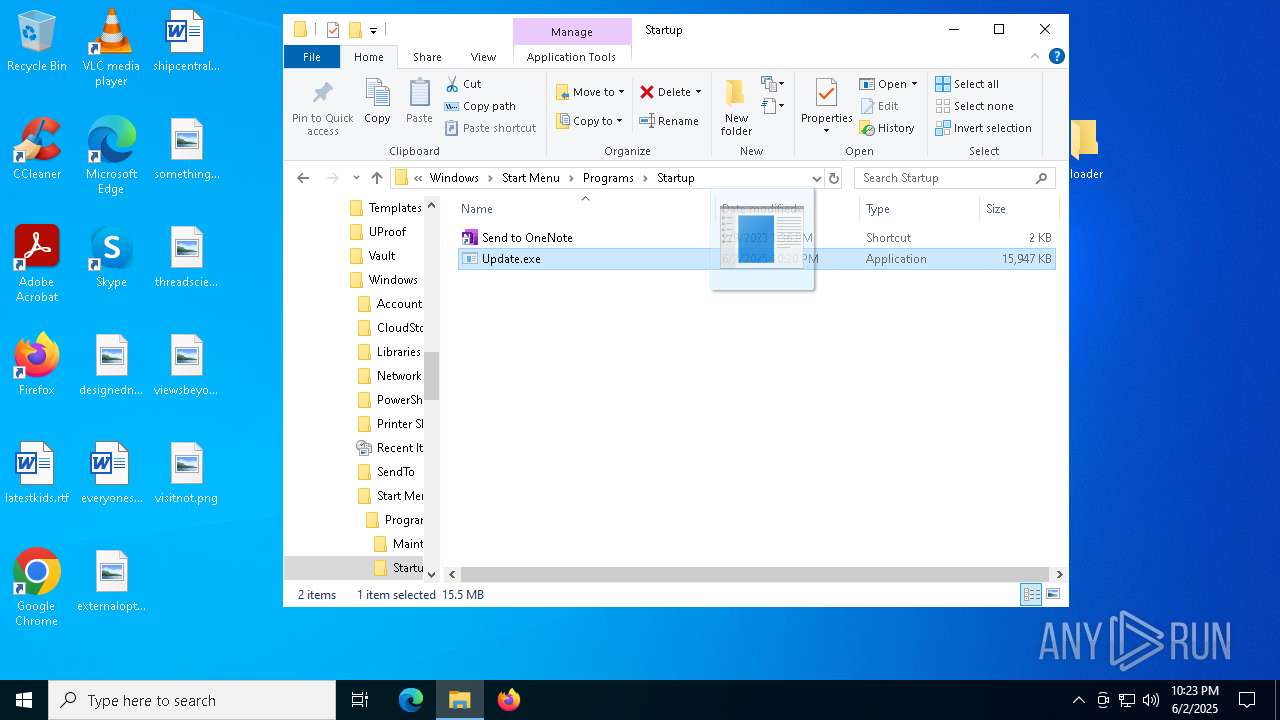
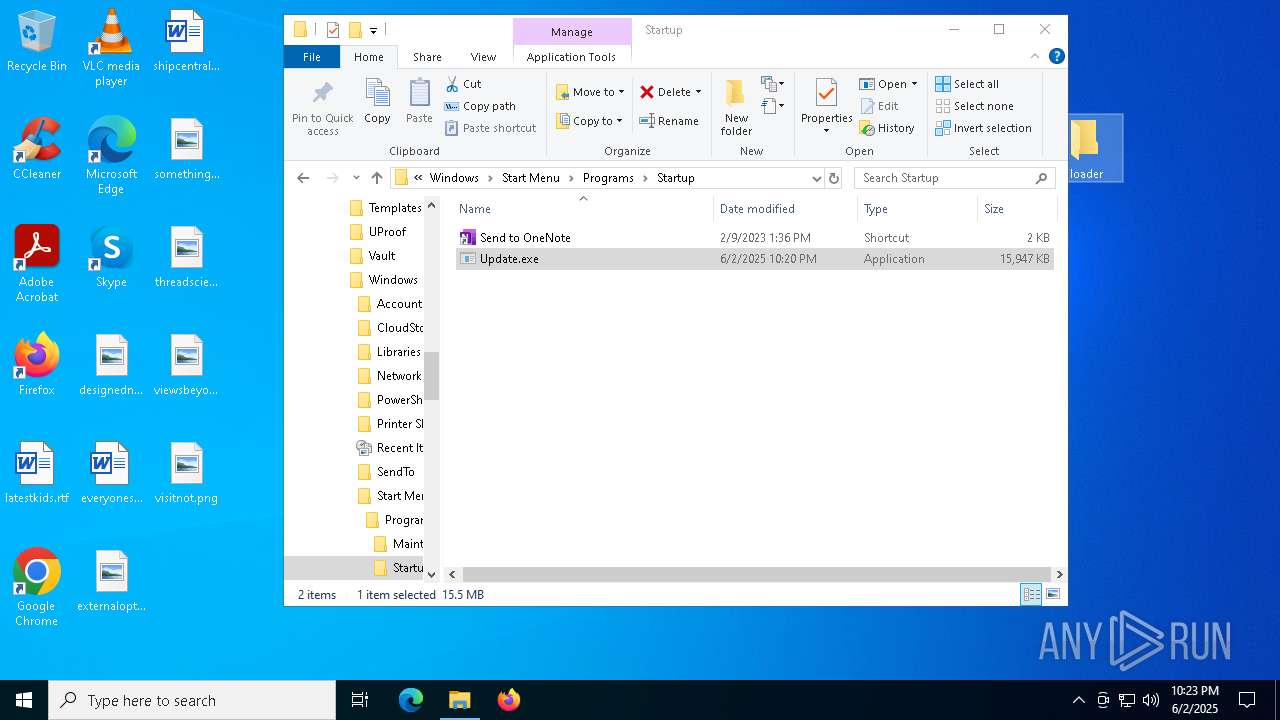
Create files in the Startup directory
- Loader.exe (PID: 7984)
MINT has been detected (YARA)
- Loader.exe (PID: 7984)
- Loader.exe (PID: 2316)
DISCORDGRABBER has been detected (YARA)
- Loader.exe (PID: 7984)
- Loader.exe (PID: 2316)
PHISHING has been detected (SURICATA)
- svchost.exe (PID: 2196)
LUMMA has been detected (SURICATA)
- svchost.exe (PID: 2196)
Stealers network behavior
- svchost.exe (PID: 2196)
SUSPICIOUS
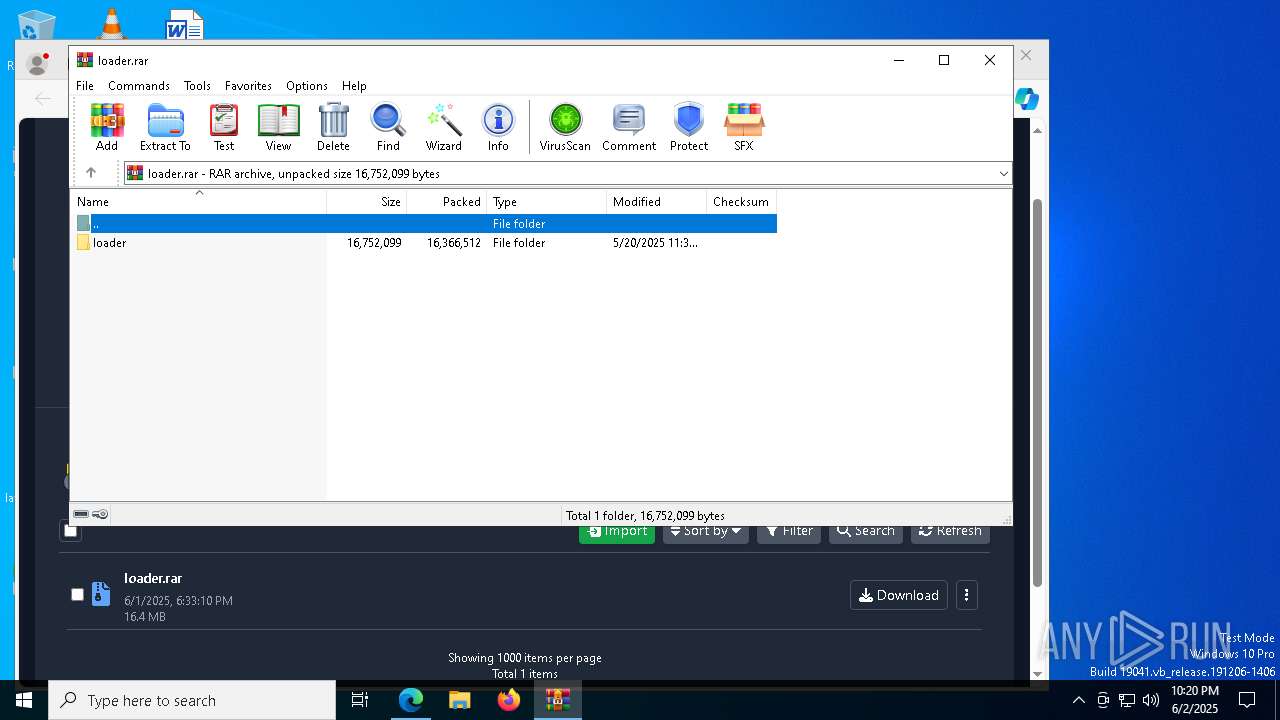
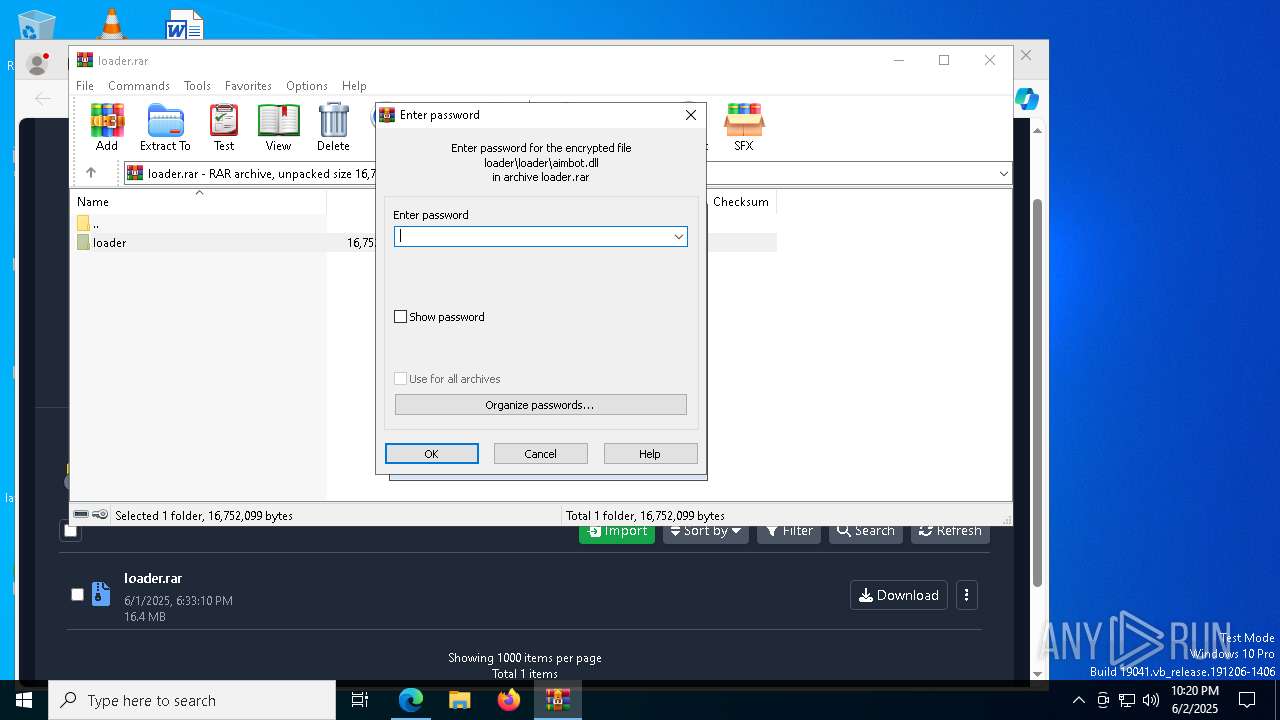
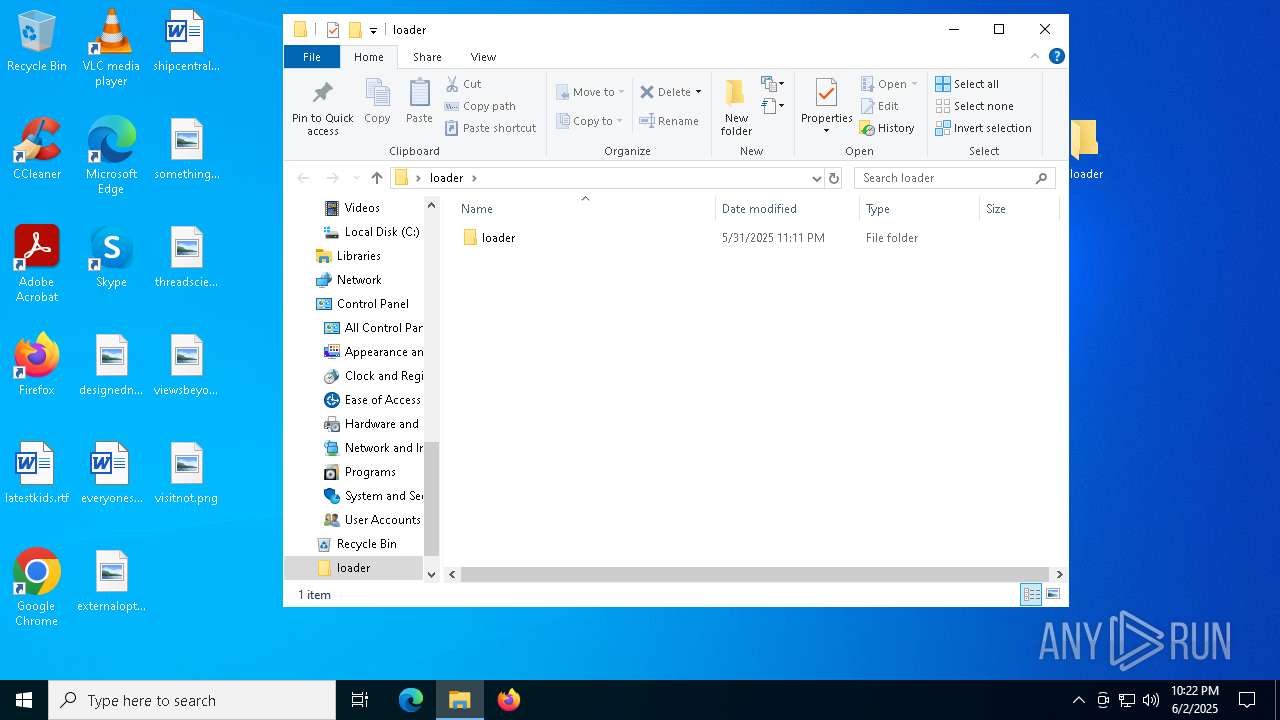
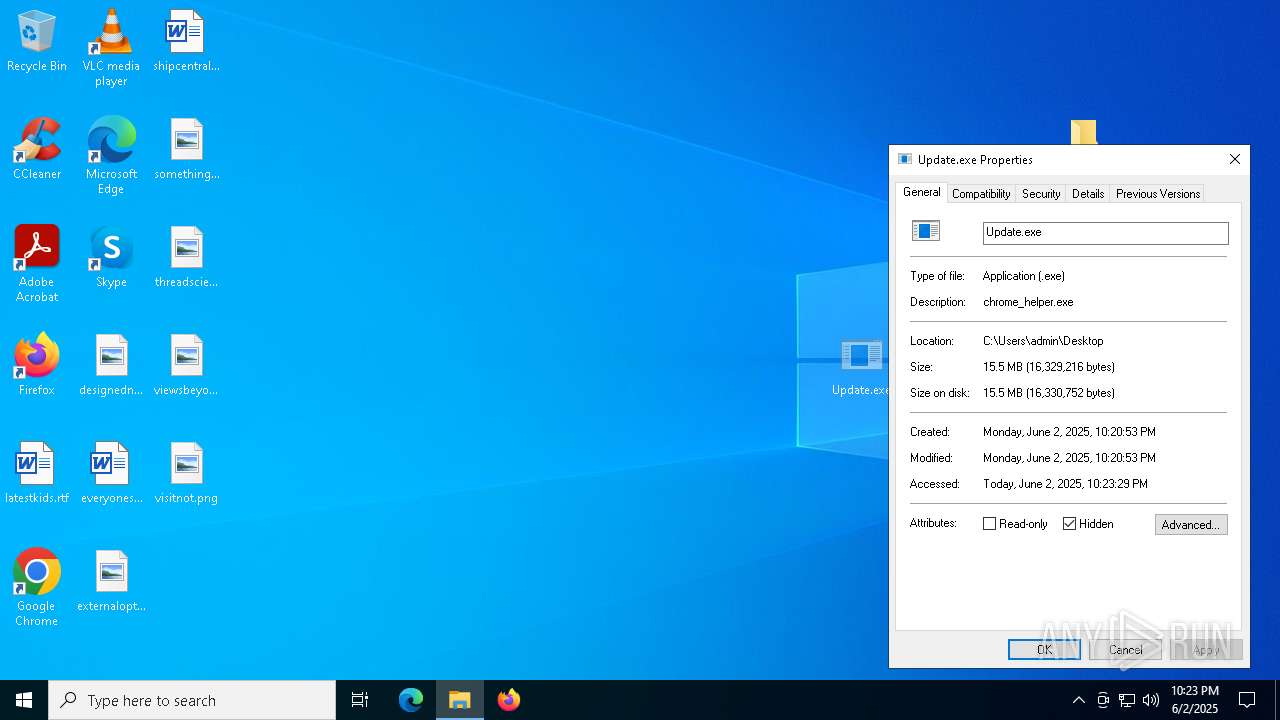
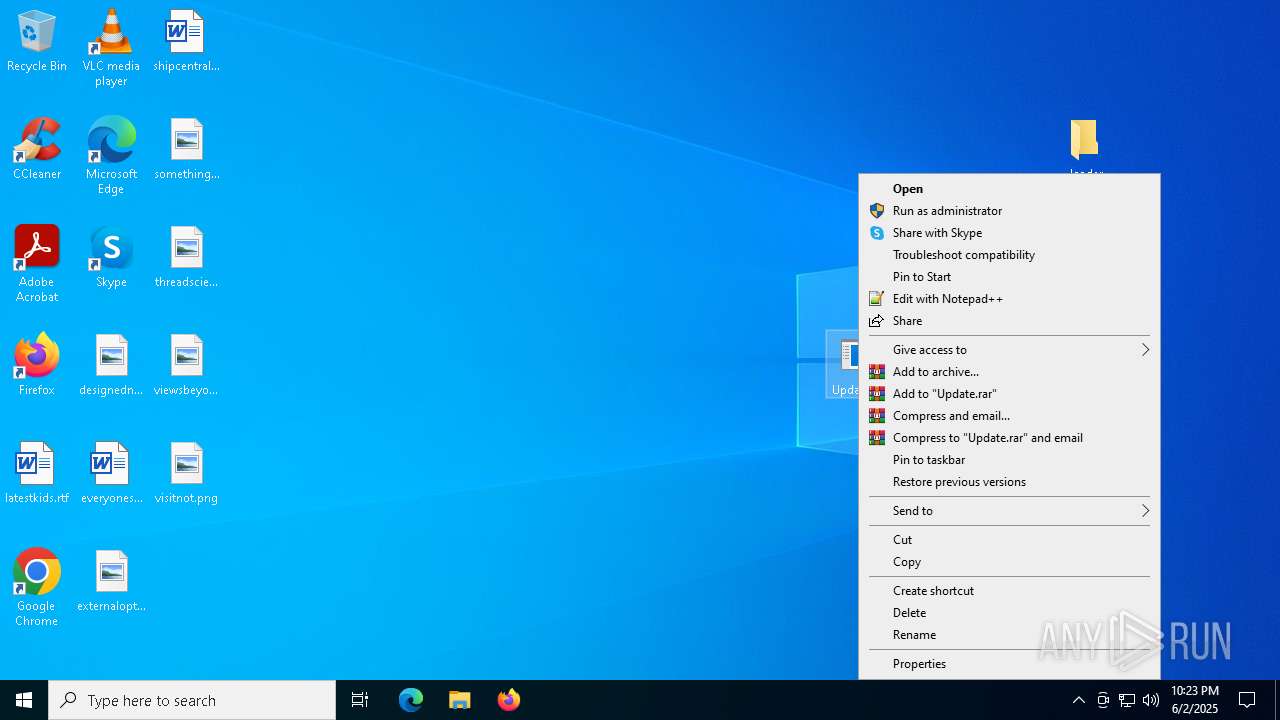
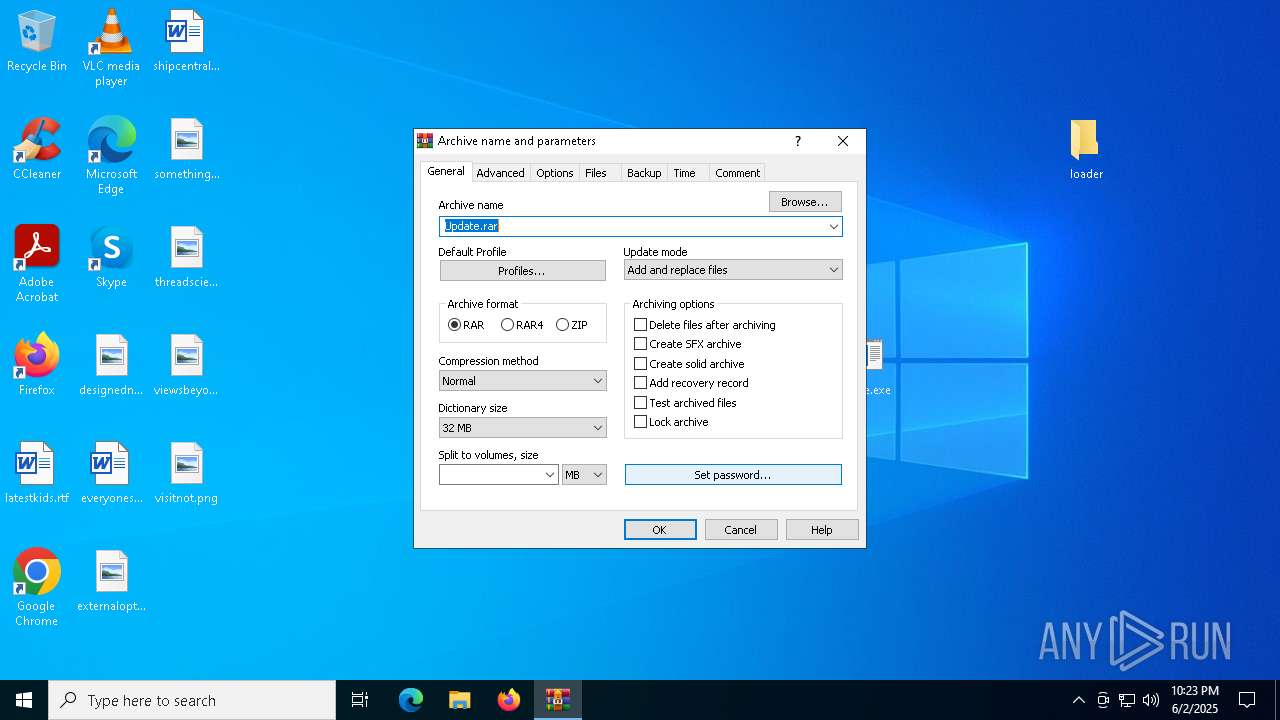
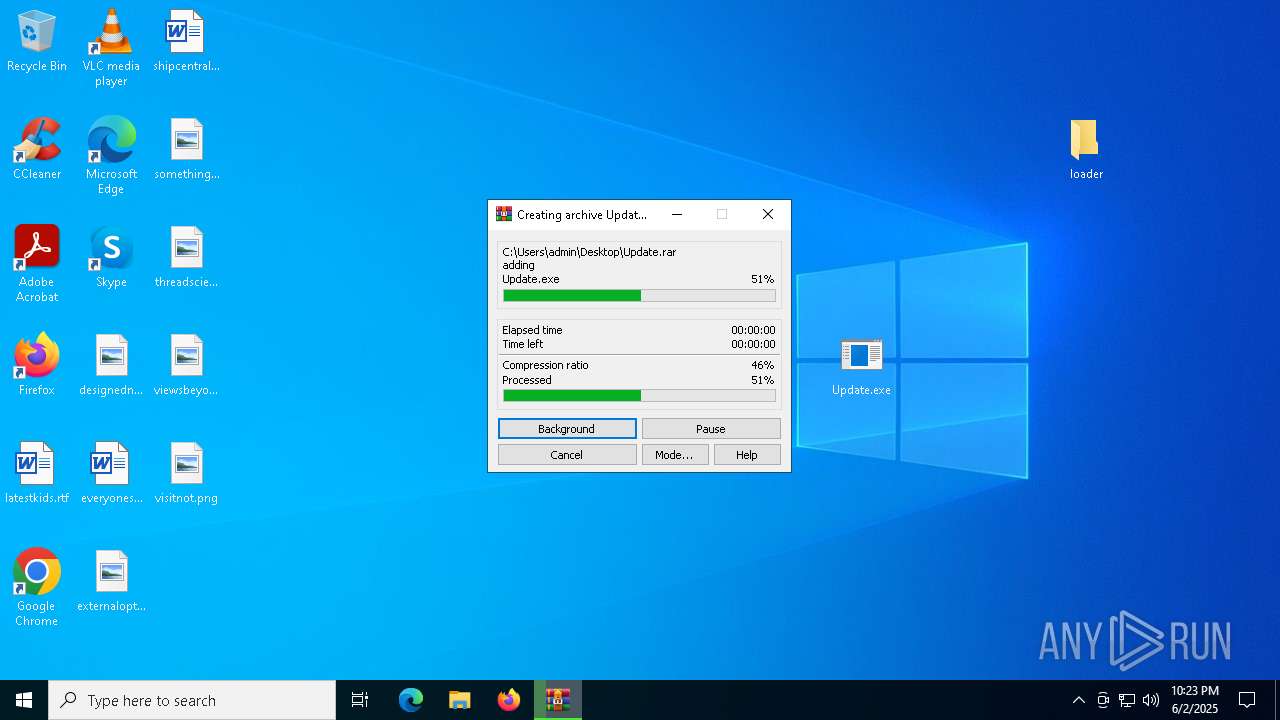
Process drops legitimate windows executable
- WinRAR.exe (PID: 444)
- Loader.exe (PID: 7048)
- Loader.exe (PID: 7984)
- Loader.exe (PID: 5020)
- Loader.exe (PID: 2316)
Process drops python dynamic module
- Loader.exe (PID: 7048)
- Loader.exe (PID: 5020)
The process creates files with name similar to system file names
- Loader.exe (PID: 7048)
Executable content was dropped or overwritten
- Loader.exe (PID: 7048)
- Loader.exe (PID: 7984)
- Menu.exe (PID: 7228)
- Loader.exe (PID: 5020)
- Loader.exe (PID: 2316)
- Menu.exe (PID: 6876)
The process drops C-runtime libraries
- Loader.exe (PID: 7048)
- Loader.exe (PID: 7984)
- Loader.exe (PID: 5020)
- Loader.exe (PID: 2316)
Application launched itself
- Loader.exe (PID: 7048)
- Loader.exe (PID: 5020)
Loads Python modules
- Loader.exe (PID: 7984)
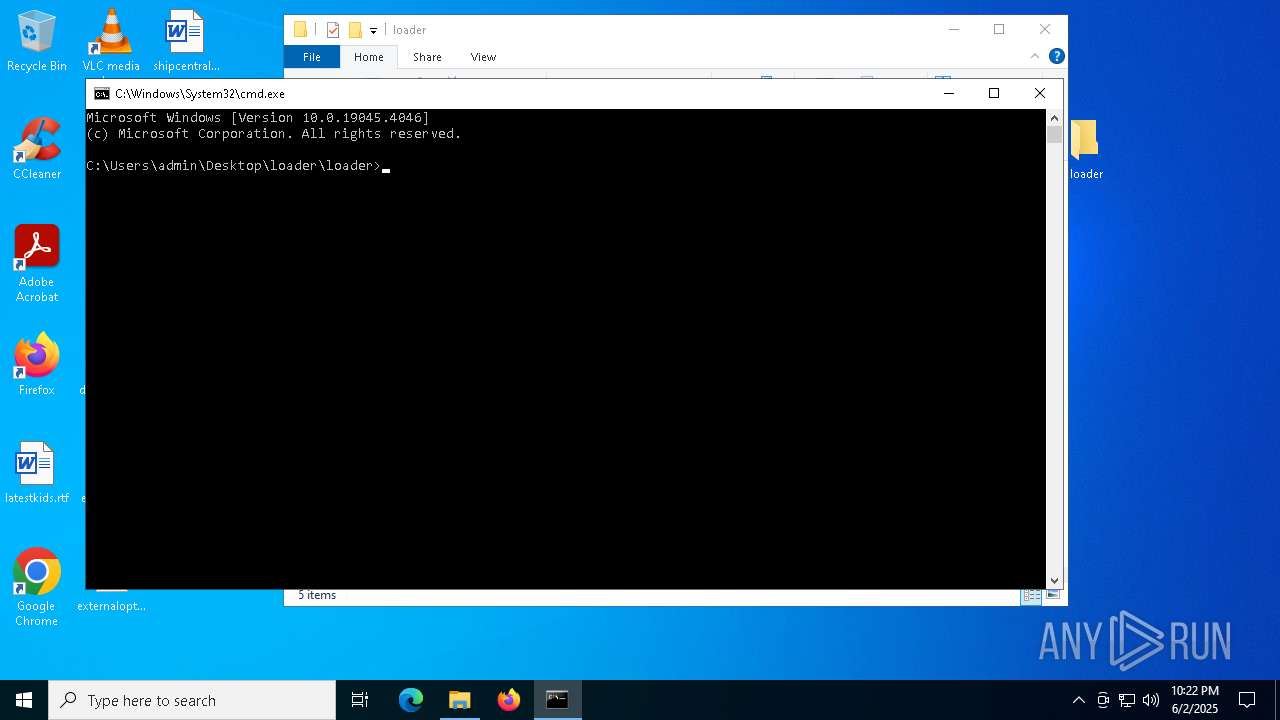
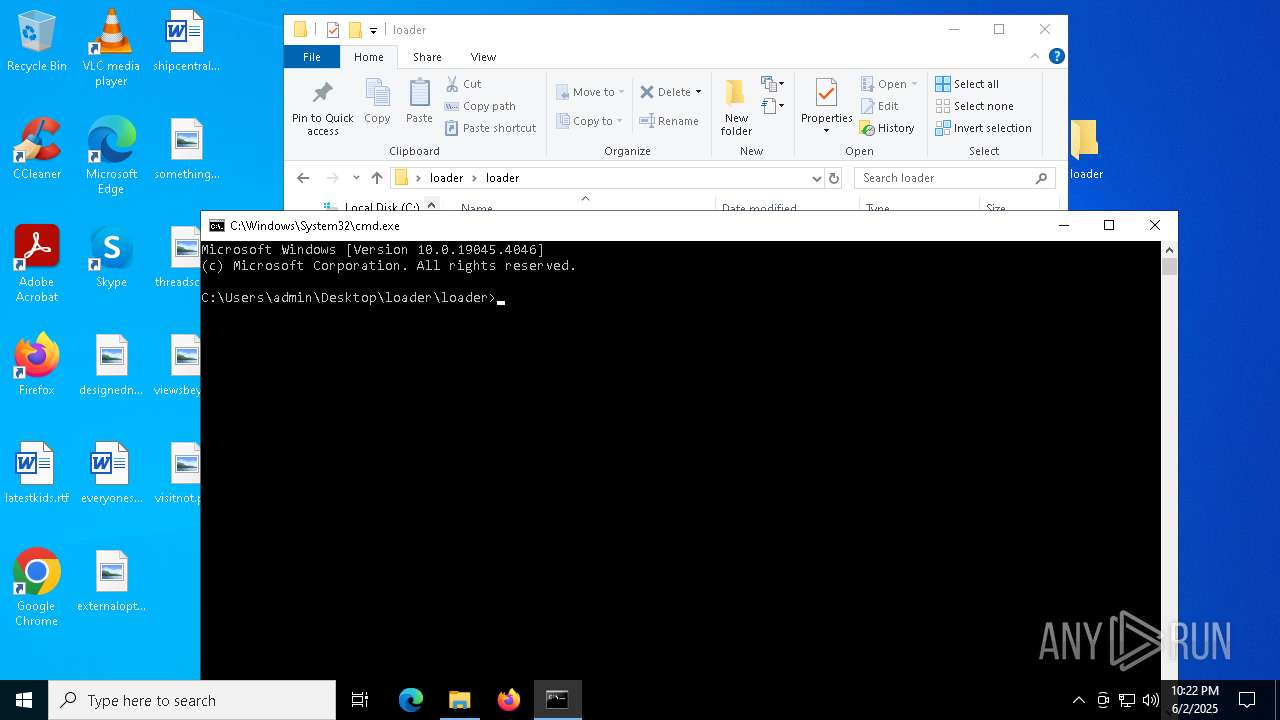
Starts CMD.EXE for commands execution
- Loader.exe (PID: 7984)
- Menu.exe (PID: 7228)
- Loader.exe (PID: 2316)
- Menu.exe (PID: 6876)
Uses WMIC.EXE to obtain physical disk drive information
- Loader.exe (PID: 7984)
- Loader.exe (PID: 2316)
Checks for external IP
- svchost.exe (PID: 2196)
Process communicates with Telegram (possibly using it as an attacker's C2 server)
- Loader.exe (PID: 7984)
- Loader.exe (PID: 2316)
Process drops SQLite DLL files
- Loader.exe (PID: 7984)
- Loader.exe (PID: 2316)
Reads security settings of Internet Explorer
- Menu.exe (PID: 7228)
Hides command output
- cmd.exe (PID: 3096)
- cmd.exe (PID: 6060)
Uses TASKKILL.EXE to kill Browsers
- cmd.exe (PID: 3096)
- cmd.exe (PID: 6060)
Get information on the list of running processes
- Loader.exe (PID: 7984)
- Loader.exe (PID: 2316)
Possible usage of Discord/Telegram API has been detected (YARA)
- Loader.exe (PID: 7984)
- Loader.exe (PID: 2316)
There is functionality for capture public ip (YARA)
- Loader.exe (PID: 7984)
Contacting a server suspected of hosting an CnC
- svchost.exe (PID: 2196)
INFO
Executable content was dropped or overwritten
- WinRAR.exe (PID: 444)
- msedge.exe (PID: 5508)
Reads Microsoft Office registry keys
- msedge.exe (PID: 5324)
Application launched itself
- msedge.exe (PID: 5324)
- msedge.exe (PID: 968)
- firefox.exe (PID: 6264)
- firefox.exe (PID: 2568)
Reads Environment values
- identity_helper.exe (PID: 4560)
- identity_helper.exe (PID: 7936)
Checks supported languages
- identity_helper.exe (PID: 4560)
- Loader.exe (PID: 7048)
- identity_helper.exe (PID: 7936)
- Loader.exe (PID: 7984)
- Menu.exe (PID: 7228)
- chrome_inject_x64.exe (PID: 7196)
Reads the computer name
- identity_helper.exe (PID: 4560)
- identity_helper.exe (PID: 7936)
- Loader.exe (PID: 7984)
- Menu.exe (PID: 7228)
The sample compiled with english language support
- WinRAR.exe (PID: 444)
- Loader.exe (PID: 7048)
- Loader.exe (PID: 7984)
- Loader.exe (PID: 5020)
- msedge.exe (PID: 5508)
- Loader.exe (PID: 2316)
Create files in a temporary directory
- Loader.exe (PID: 7048)
- Menu.exe (PID: 7228)
- chrome_inject_x64.exe (PID: 7196)
- Loader.exe (PID: 7984)
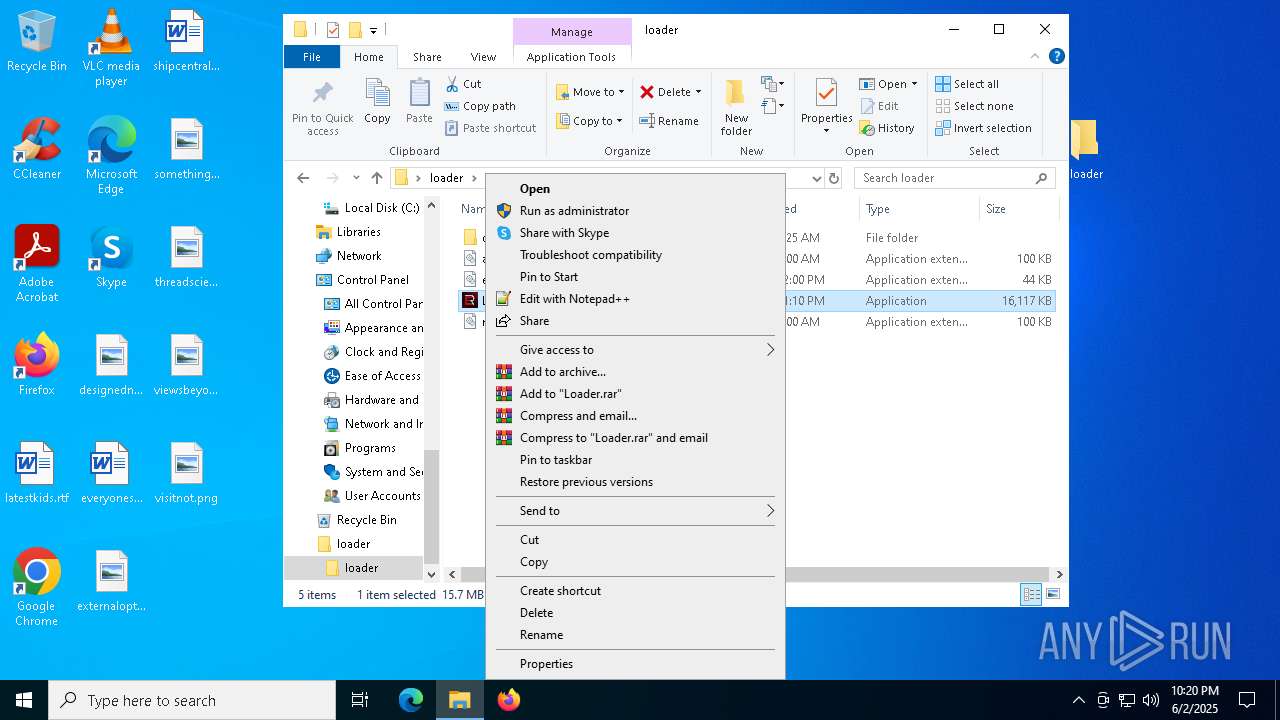
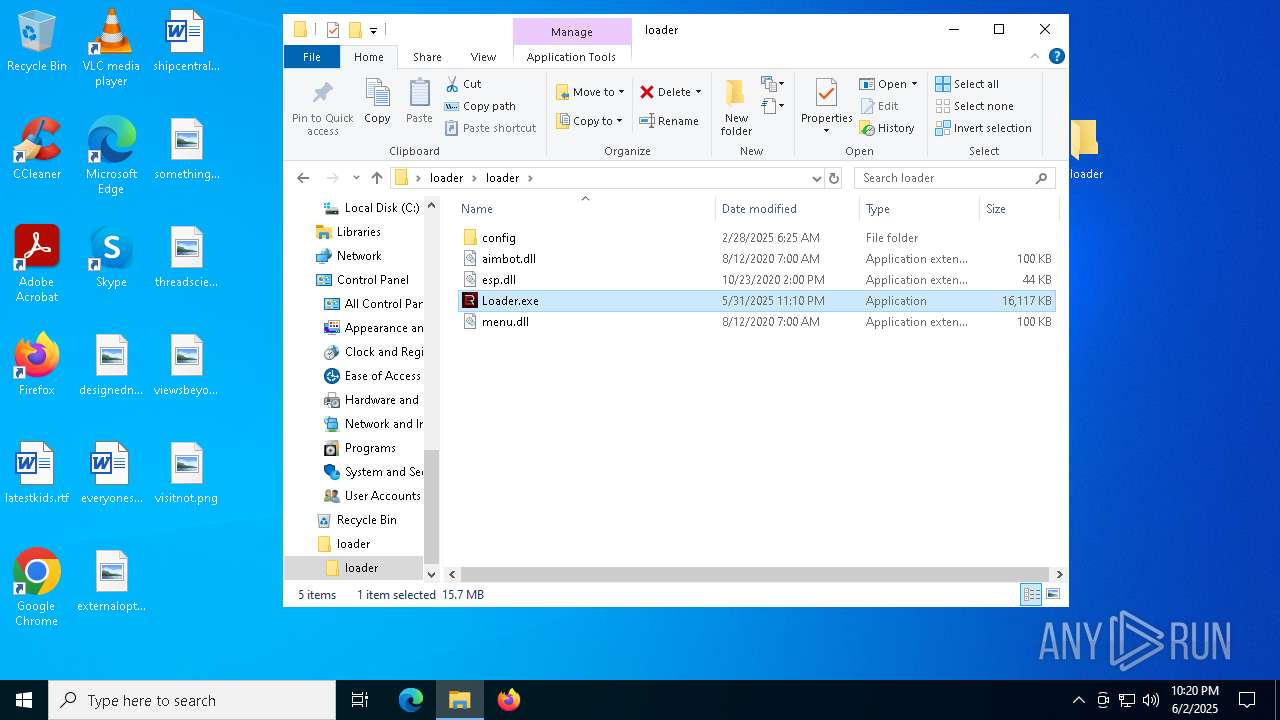
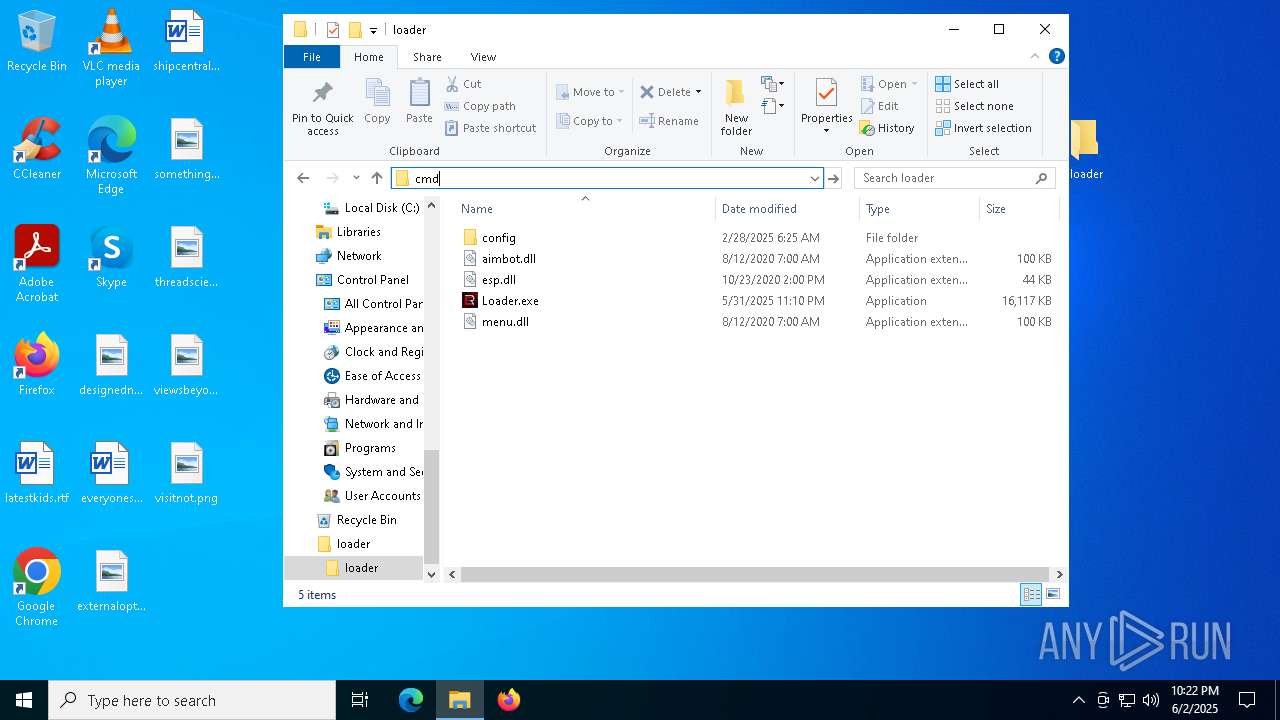
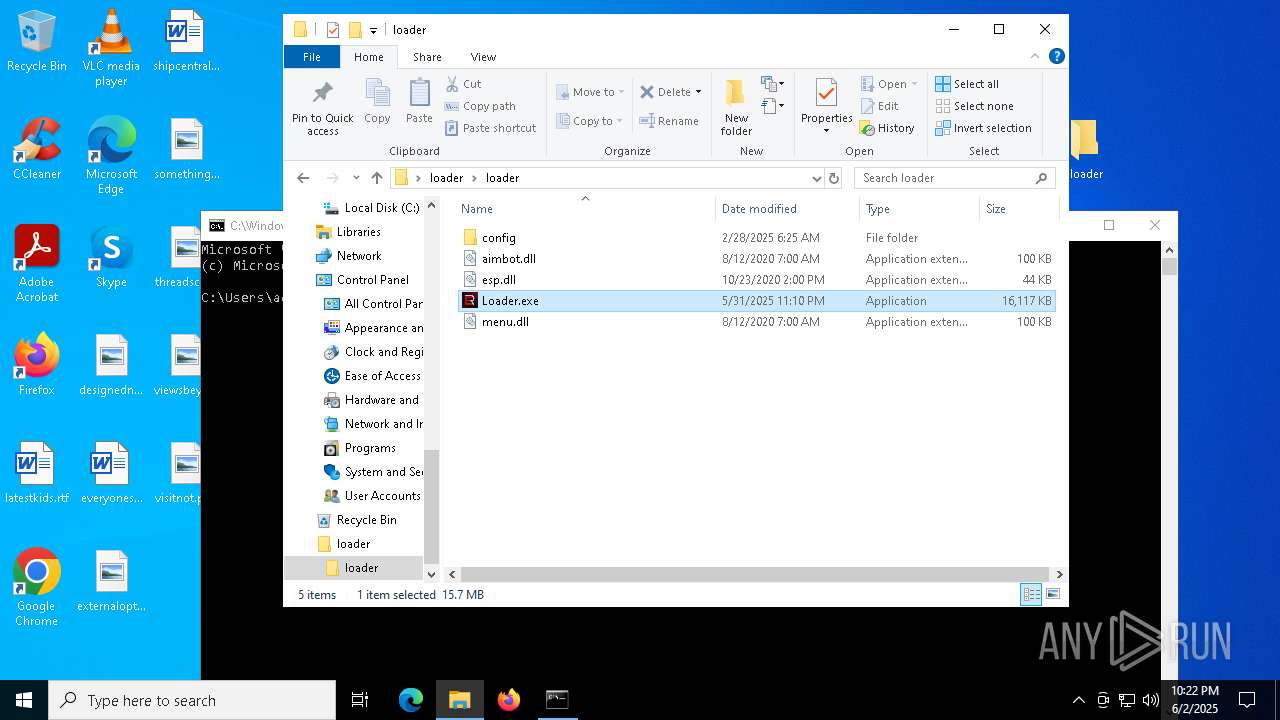
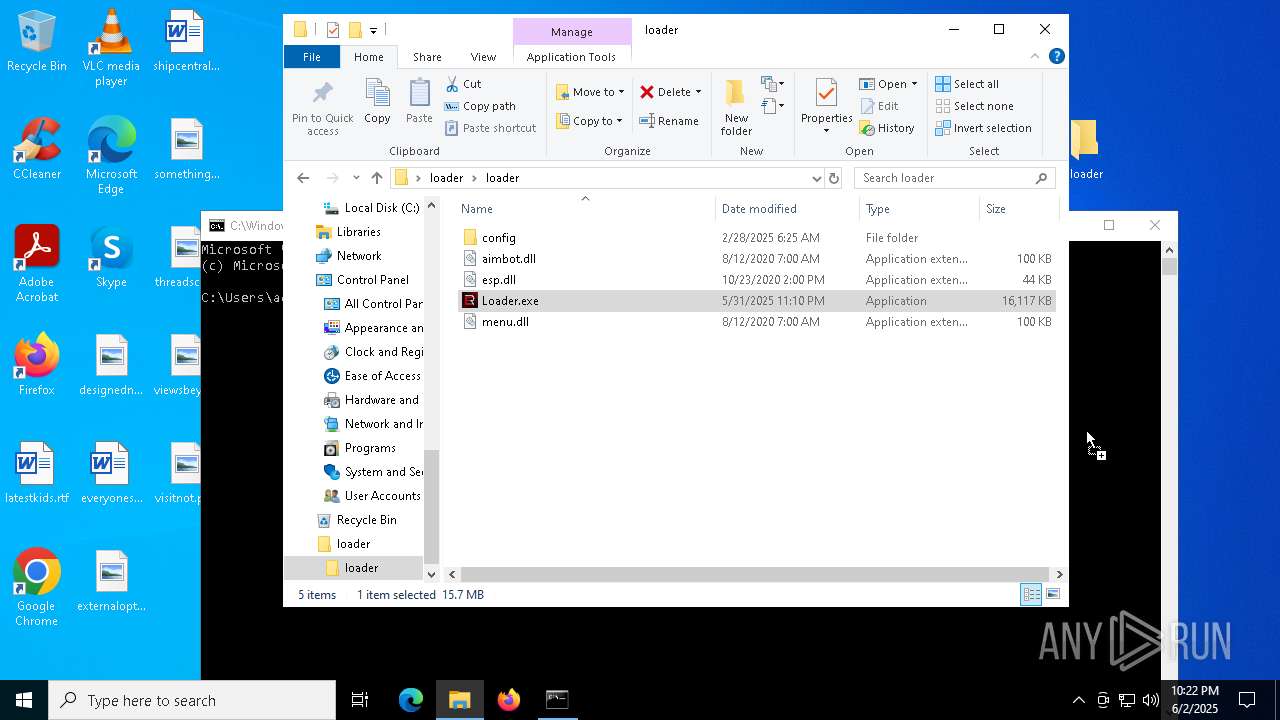
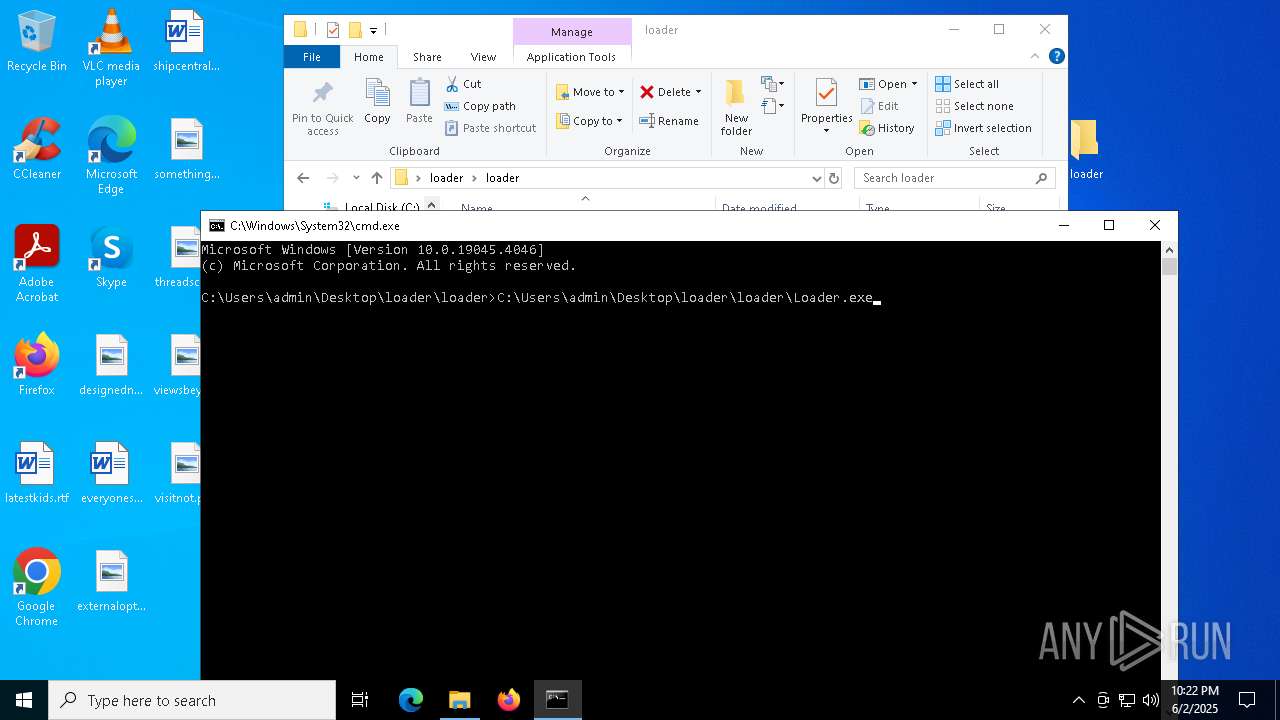
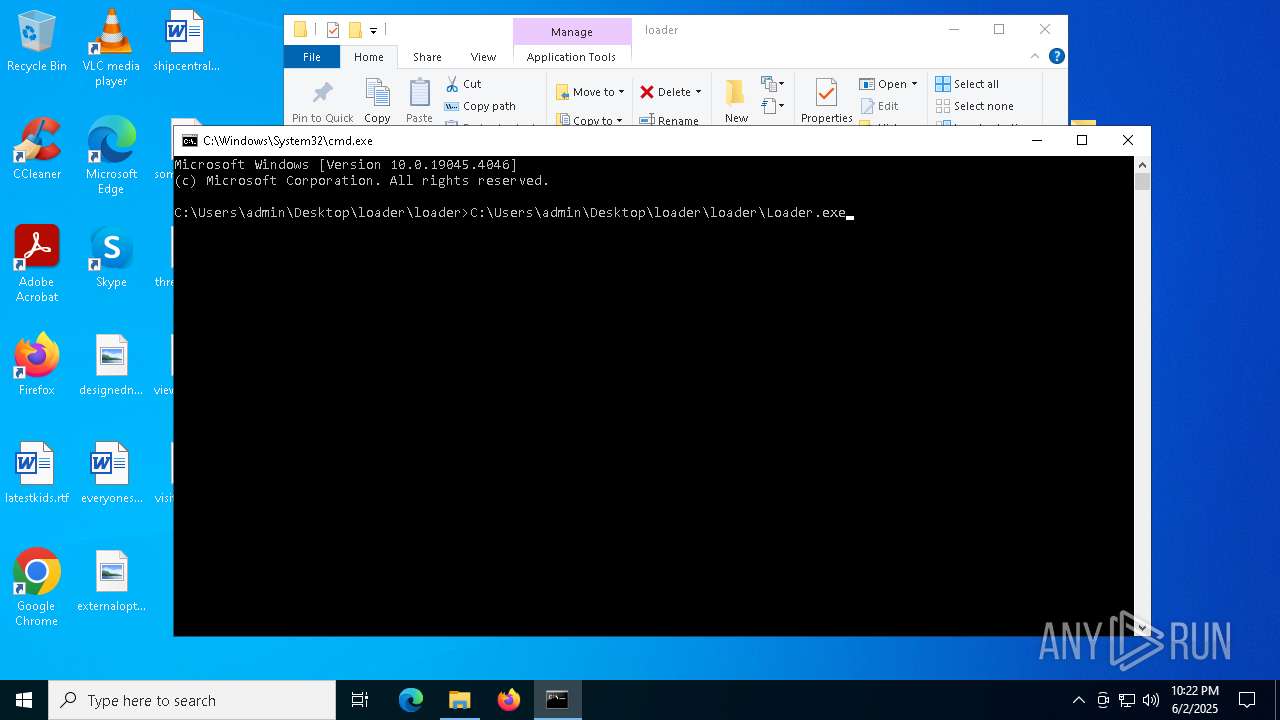
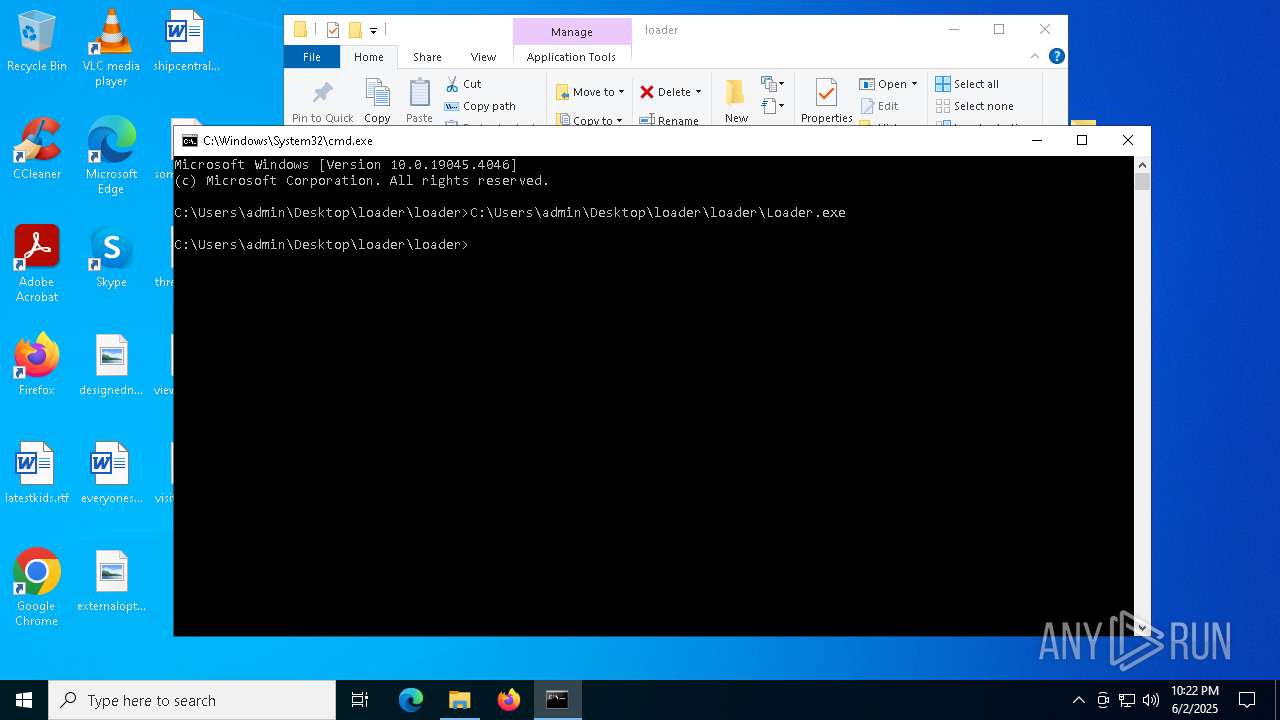
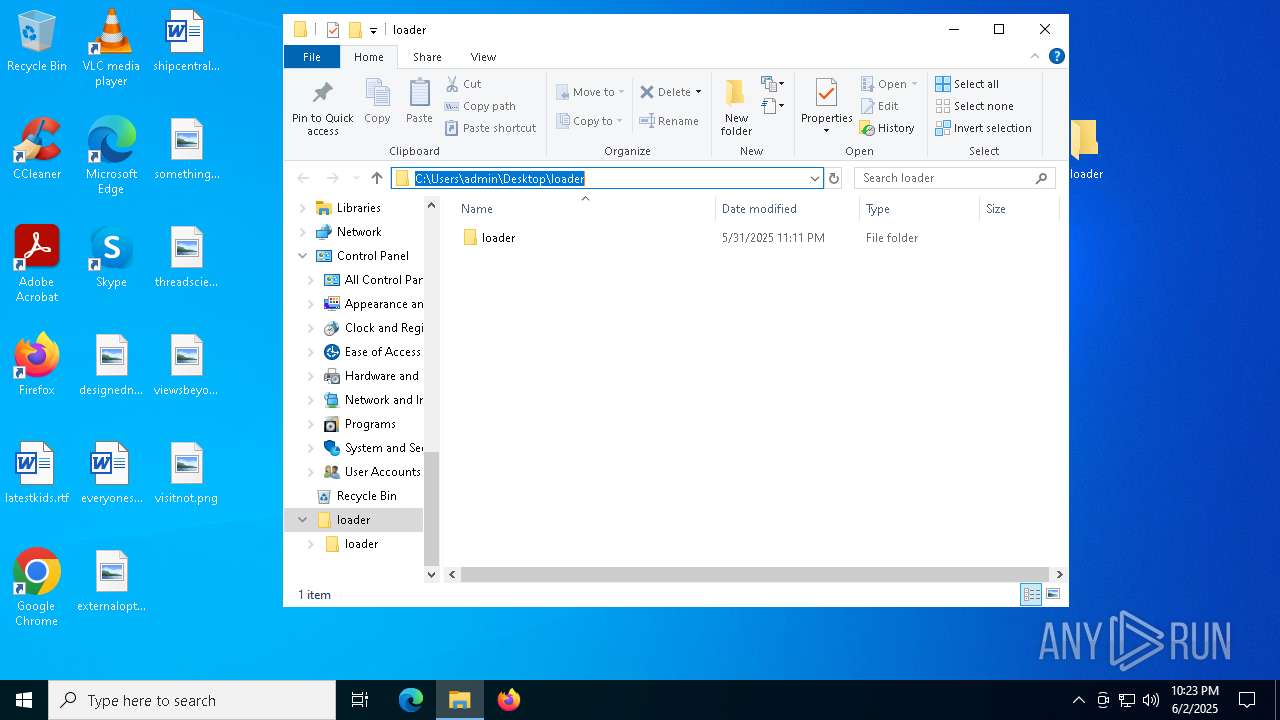
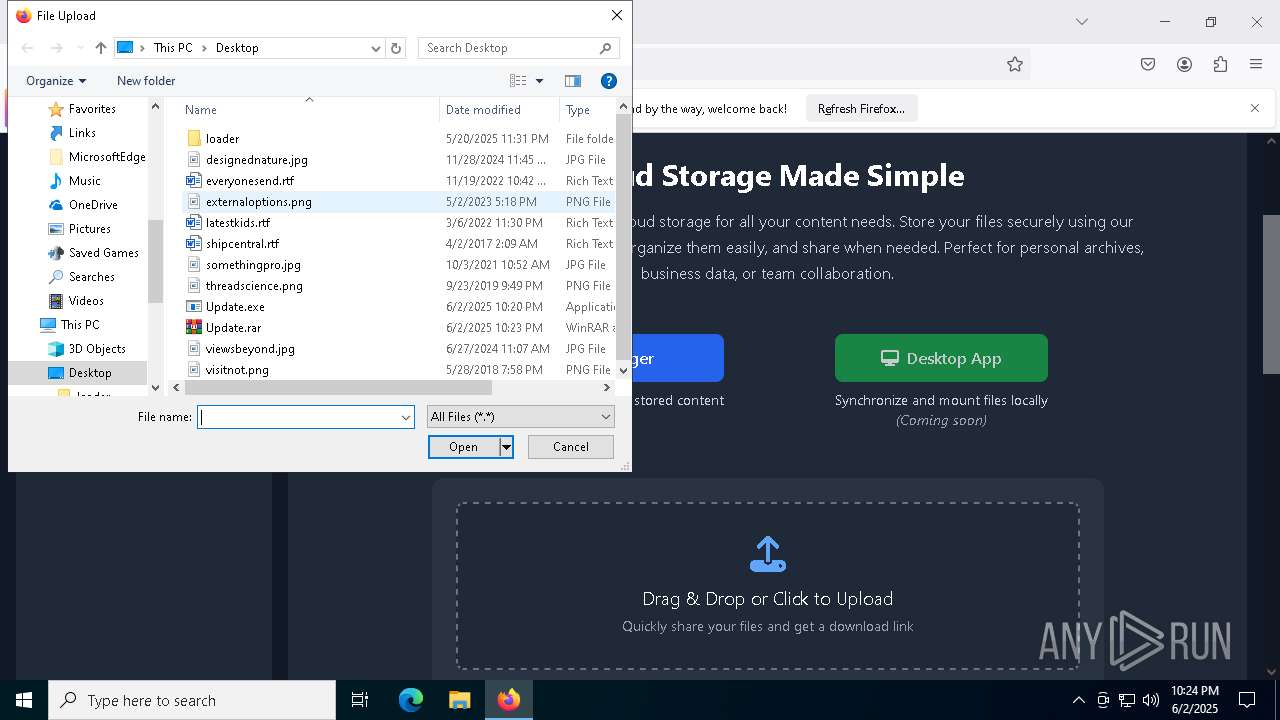
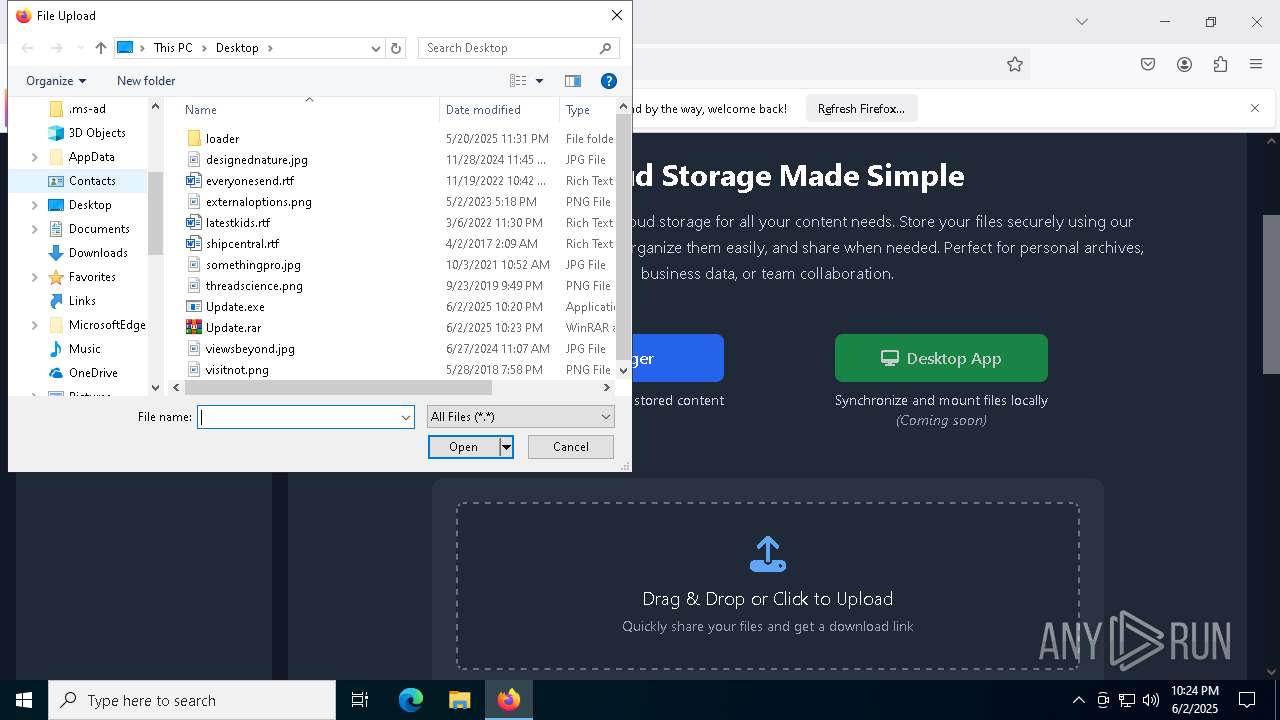
Manual execution by a user
- Loader.exe (PID: 7048)
- cmd.exe (PID: 4028)
- WinRAR.exe (PID: 8040)
- firefox.exe (PID: 6264)
Reads the machine GUID from the registry
- Loader.exe (PID: 7984)
- Menu.exe (PID: 7228)
Creates files or folders in the user directory
- Loader.exe (PID: 7984)
- Menu.exe (PID: 7228)
Launch of the file from Startup directory
- Loader.exe (PID: 7984)
Reads security settings of Internet Explorer
- WMIC.exe (PID: 1164)
Checks proxy server information
- Loader.exe (PID: 7984)
- Menu.exe (PID: 7228)
Checks operating system version
- Loader.exe (PID: 7984)
- Loader.exe (PID: 2316)
Reads the software policy settings
- Menu.exe (PID: 7228)
Attempting to use instant messaging service
- Loader.exe (PID: 2316)
- svchost.exe (PID: 2196)
- Loader.exe (PID: 7984)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
269
Monitored processes
136
Malicious processes
6
Suspicious processes
4
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 300 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=asset_store.mojom.AssetStoreService --lang=en-US --service-sandbox-type=asset_store_service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=5456 --field-trial-handle=2356,i,15964388394053660426,3406159924768023952,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
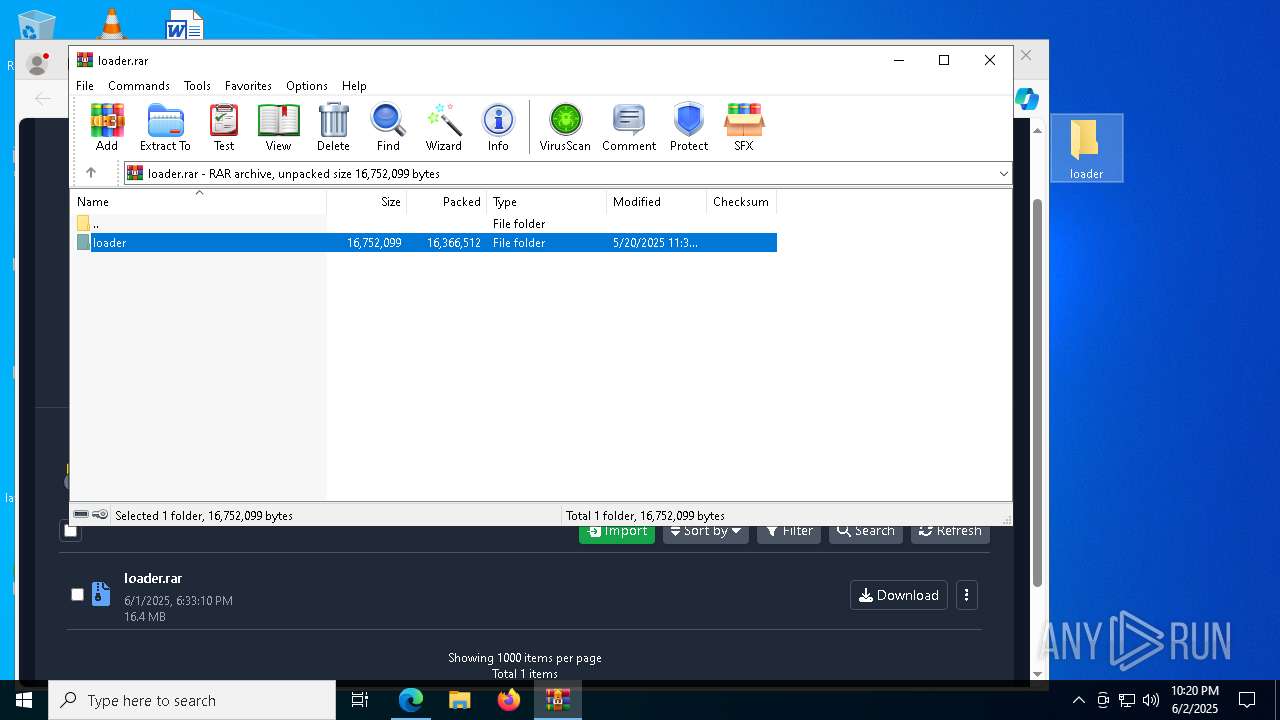
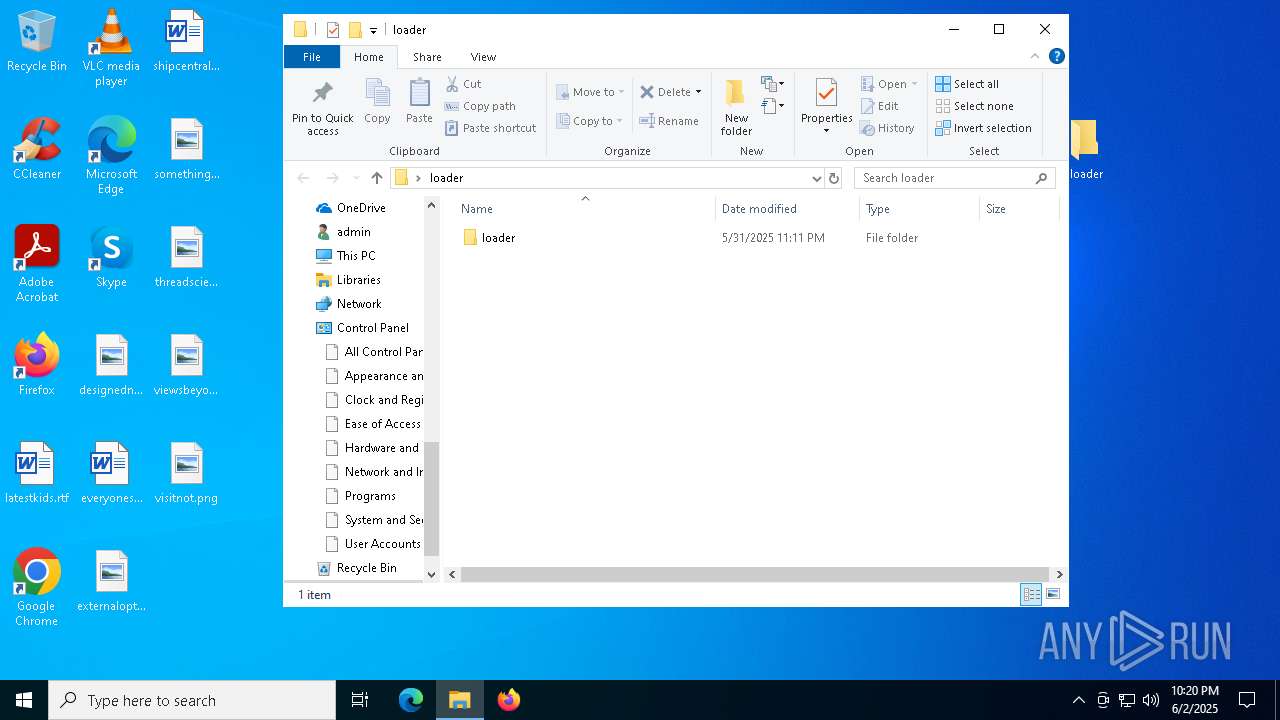
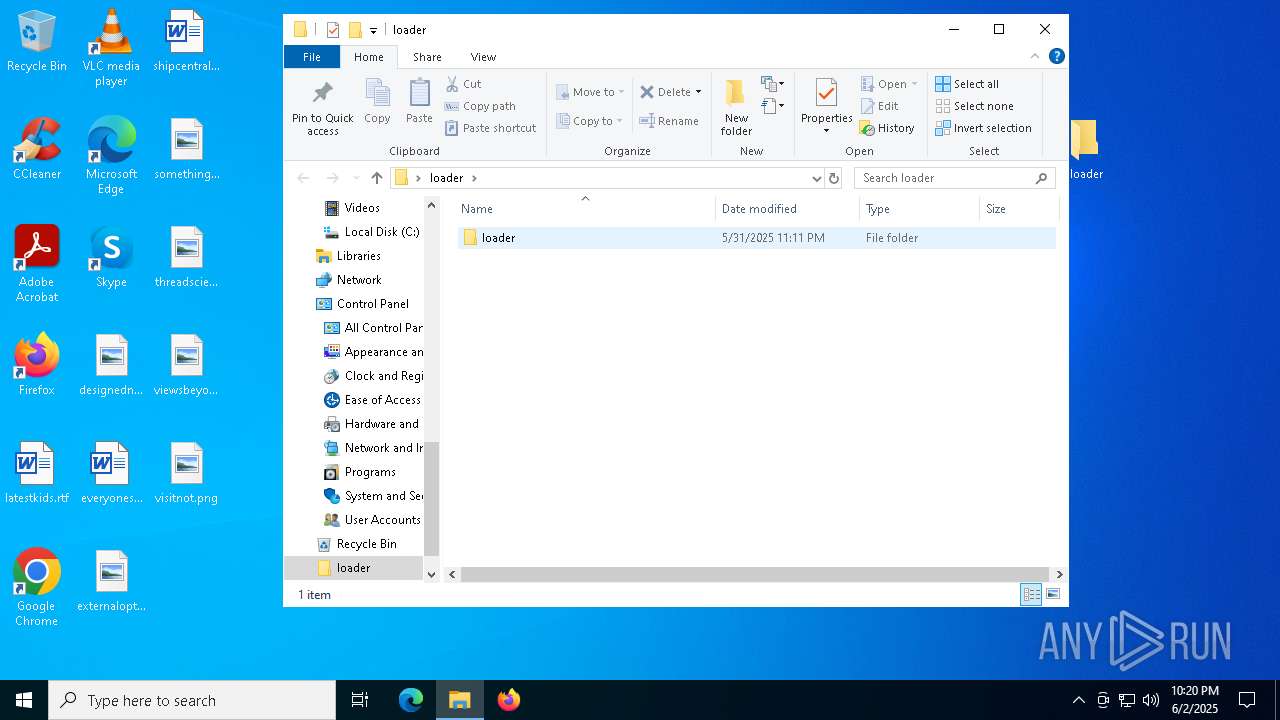
| 444 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Downloads\loader.rar" | C:\Program Files\WinRAR\WinRAR.exe | msedge.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 660 | C:\Users\admin\AppData\Local\Temp\KLHnk1iAR7\chrome_inject_x64.exe --method nt chrome | C:\Users\admin\AppData\Local\Temp\KLHnk1iAR7\chrome_inject_x64.exe | — | Loader.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 1 Modules
| |||||||||||||||
| 776 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=4852 --field-trial-handle=2356,i,15964388394053660426,3406159924768023952,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 908 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=5304 -childID 7 -isForBrowser -prefsHandle 5672 -prefMapHandle 5644 -prefsLen 31366 -prefMapSize 244583 -jsInitHandle 1440 -jsInitLen 235124 -parentBuildID 20240213221259 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {96f0ed5a-61af-4275-9215-20402056c46f} 2568 "\\.\pipe\gecko-crash-server-pipe.2568" 1dbe403e690 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Version: 123.0 Modules
| |||||||||||||||
| 968 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --no-startup-window | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | msedge.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1164 | wmic diskdrive get SerialNumber | C:\Windows\System32\wbem\WMIC.exe | — | Loader.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: WMI Commandline Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1176 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1176 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=5340 --field-trial-handle=2356,i,15964388394053660426,3406159924768023952,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1240 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=6452 --field-trial-handle=2272,i,14360204201202887519,7775418286530662770,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
38 358
Read events
38 239
Write events
116
Delete events
3
Modification events
| (PID) Process: | (5324) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\263034 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {F668529E-766B-40DE-9854-C15DD1A45CEA} | |||
| (PID) Process: | (5324) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (5324) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (5324) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (5324) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (5324) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: EA36C77334952F00 | |||
| (PID) Process: | (5324) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 9687D07334952F00 | |||
| (PID) Process: | (5324) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\263034 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {E26FB65E-F964-4E05-AE0D-4343AA548078} | |||
| (PID) Process: | (5324) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\263034 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {8627F85B-6CF6-4F86-A48E-70836F85C3AE} | |||
| (PID) Process: | (5324) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\263034 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {378A21AB-AFBB-4BBA-B753-A177DF8005D0} | |||
Executable files
170
Suspicious files
728
Text files
135
Unknown types
7
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5324 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Local State~RF11fa99.TMP | — | |
MD5:— | SHA256:— | |||
| 5324 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\Service Worker\Database\LOG.old~RF11faa9.TMP | — | |
MD5:— | SHA256:— | |||
| 5324 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\Sync Data\LevelDB\LOG.old~RF11faa9.TMP | — | |
MD5:— | SHA256:— | |||
| 5324 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\Service Worker\Database\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5324 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\Sync Data\LevelDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5324 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\Site Characteristics Database\LOG.old~RF11fab8.TMP | — | |
MD5:— | SHA256:— | |||
| 5324 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF11faf7.TMP | — | |
MD5:— | SHA256:— | |||
| 5324 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5324 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF11faf7.TMP | — | |
MD5:— | SHA256:— | |||
| 5324 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF11fae7.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
57
TCP/UDP connections
183
DNS requests
255
Threats
73
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.216.77.18:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
7228 | Menu.exe | GET | 200 | 192.124.249.31:80 | http://crl.starfieldtech.com/sfroot-g2.crl | unknown | — | — | whitelisted |
7816 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7228 | Menu.exe | GET | 200 | 151.101.67.3:80 | http://ocsp.int-r1.certainly.com/MFMwUTBPME0wSzAJBgUrDgMCGgUABBQ9Cy058uESb%2B0ddJm5bqXlFvfbcAQUvZed36HYGyWZ4wwEBolkEtdlJMcCEnbQG4No9mE0fGLlixi0yFiWaQ%3D%3D | unknown | — | — | unknown |
7816 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
4652 | svchost.exe | HEAD | 200 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/84d3e481-77df-49da-bc37-0a994069ddb9?P1=1748976257&P2=404&P3=2&P4=LxRzdNmPGNmUo1CGm19vF1FT%2f6ZCAOP0aygNEfWBenXAvWVe49WEzVOiMbU%2byPnDnL1rX13q4W%2fSS9sezY%2fDMw%3d%3d | unknown | — | — | whitelisted |
4652 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/b649b6c2-4484-495a-96f2-2fd1ee2b66ca?P1=1748976267&P2=404&P3=2&P4=SGd6ni76%2fWAwjg%2fJlRzLr2r%2bD4CUC7MX4%2bVLYR5VXPVG%2f1H8ju2VjanLwrRvxkTKV1rOPk21e131%2fniJ5ZgNzw%3d%3d | unknown | — | — | whitelisted |
4652 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/b649b6c2-4484-495a-96f2-2fd1ee2b66ca?P1=1748976267&P2=404&P3=2&P4=SGd6ni76%2fWAwjg%2fJlRzLr2r%2bD4CUC7MX4%2bVLYR5VXPVG%2f1H8ju2VjanLwrRvxkTKV1rOPk21e131%2fniJ5ZgNzw%3d%3d | unknown | — | — | whitelisted |
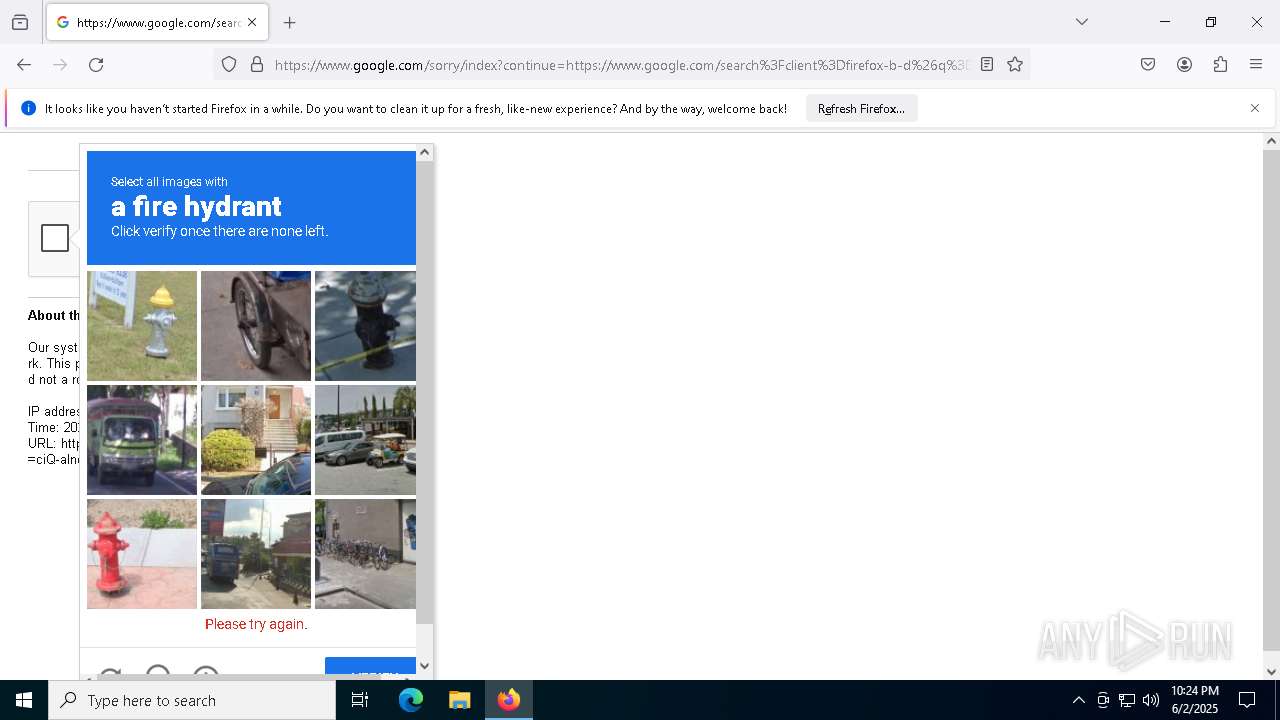
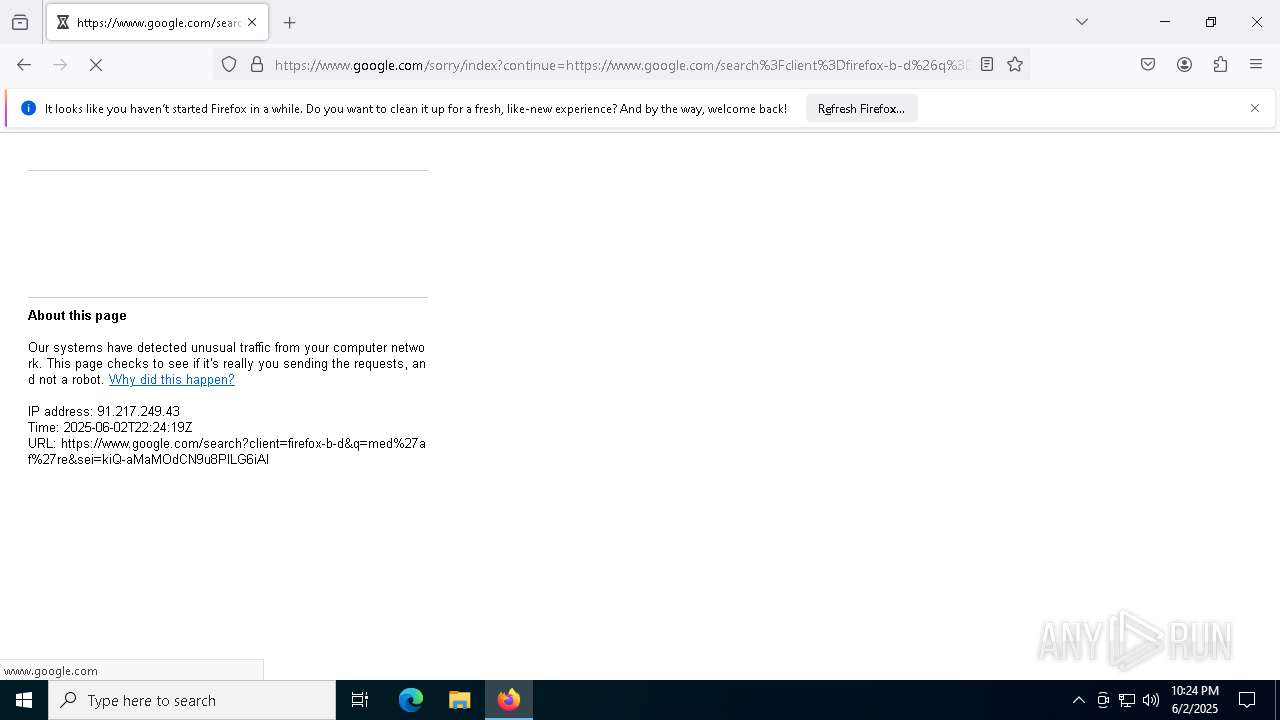
7984 | Loader.exe | GET | — | 142.250.186.68:80 | http://www.google.com/ | unknown | — | — | whitelisted |
4652 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/84d3e481-77df-49da-bc37-0a994069ddb9?P1=1748976257&P2=404&P3=2&P4=LxRzdNmPGNmUo1CGm19vF1FT%2f6ZCAOP0aygNEfWBenXAvWVe49WEzVOiMbU%2byPnDnL1rX13q4W%2fSS9sezY%2fDMw%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.216.77.18:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
6544 | svchost.exe | 20.190.159.23:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
5324 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5228 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5228 | msedge.exe | 45.112.123.126:443 | gofile.io | AMAZON-02 | SG | whitelisted |
5228 | msedge.exe | 150.171.27.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
gofile.io |
| whitelisted |
edge.microsoft.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
business.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
5228 | msedge.exe | Potentially Bad Traffic | ET FILE_SHARING Online File Storage Domain in DNS Lookup (gofile .io) |
5228 | msedge.exe | Potentially Bad Traffic | ET FILE_SHARING Online File Storage Domain in DNS Lookup (gofile .io) |
5228 | msedge.exe | Misc activity | ET FILE_SHARING File Sharing Related Domain in TLS SNI (gofile .io) |
5228 | msedge.exe | Potentially Bad Traffic | ET FILE_SHARING Online File Storage Domain in DNS Lookup (gofile .io) |
5228 | msedge.exe | Potentially Bad Traffic | ET FILE_SHARING Online File Storage Domain in DNS Lookup (gofile .io) |
5228 | msedge.exe | Potentially Bad Traffic | ET FILE_SHARING Online File Storage Domain in DNS Lookup (gofile .io) |
5228 | msedge.exe | Potentially Bad Traffic | ET FILE_SHARING Online File Storage Domain in DNS Lookup (gofile .io) |
5228 | msedge.exe | Misc activity | ET FILE_SHARING File Sharing Related Domain in TLS SNI (gofile .io) |
5228 | msedge.exe | Misc activity | ET FILE_SHARING File Sharing Related Domain in TLS SNI (gofile .io) |
5228 | msedge.exe | Misc activity | ET FILE_SHARING File Sharing Related Domain in TLS SNI (gofile .io) |