| File name: | eh.exe |
| Full analysis: | https://app.any.run/tasks/b945cc2b-5774-447b-9e28-b3c39558fe06 |
| Verdict: | Malicious activity |
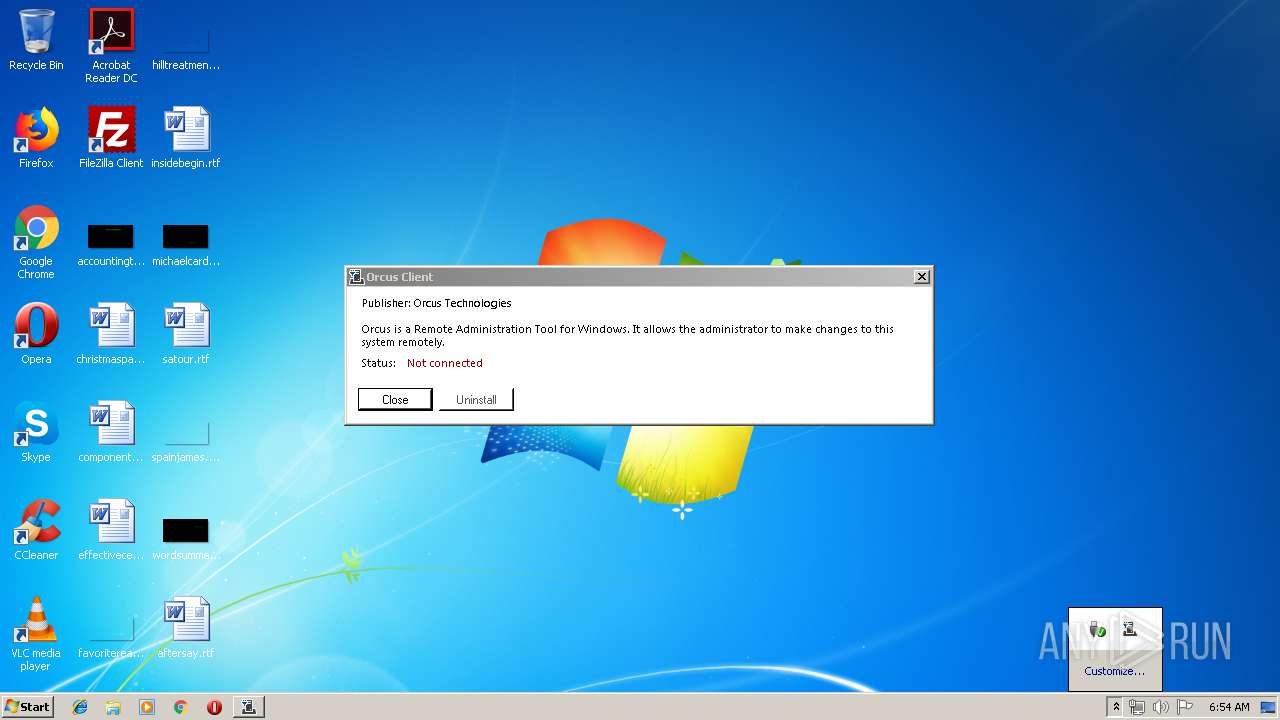
| Threats: | Orcus is a modular Remote Access Trojan with some unusual functions. This RAT enables attackers to create plugins using a custom development library and offers a robust core feature set that makes it one of the most dangerous malicious programs in its class. |
| Analysis date: | June 12, 2019, 05:53:38 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | 7A2C5E81C7FD4E0C567276A703C6D261 |
| SHA1: | A44A38C0317DC067A180C4AAACED6D463ABEE92D |
| SHA256: | 75C095F08824F2682C08E4FE7EEA0855F218C9D9CC39F7F0162029CEE2FB2CBD |
| SSDEEP: | 24576:Zqd4MROxnFj30xXFHXRrZlI0AilFEvxHisvn:ZqqMi1sRhrZlI0AilFEvxHi |
MALICIOUS
Starts Visual C# compiler
- eh.exe (PID: 3364)
- eh.exe (PID: 1004)
Orcus was detected
- eh.exe (PID: 3364)
- eh.exe (PID: 1004)
Loads the Task Scheduler COM API
- eh.exe (PID: 3364)
Application was dropped or rewritten from another process
- Skype.exe (PID: 620)
- Skype.exe (PID: 3648)
Orcus RAT was detected
- Skype.exe (PID: 3648)
SUSPICIOUS
Creates files in the user directory
- eh.exe (PID: 3364)
Executable content was dropped or overwritten
- eh.exe (PID: 3364)
Application launched itself
- Skype.exe (PID: 3648)
Executed via Task Scheduler
- eh.exe (PID: 1004)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (56.7) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (21.3) |
| .scr | | | Windows screen saver (10.1) |
| .dll | | | Win32 Dynamic Link Library (generic) (5) |
| .exe | | | Win32 Executable (generic) (3.4) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:06:12 07:52:46+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 8 |
| CodeSize: | 924672 |
| InitializedDataSize: | 4608 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xe3a5e |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | - |
| CompanyName: | - |
| FileDescription: | - |
| FileVersion: | 1.0.0.0 |
| InternalName: | Orcus.exe |
| LegalCopyright: | - |
| LegalTrademarks: | - |
| OriginalFileName: | Orcus.exe |
| ProductName: | - |
| ProductVersion: | 1.0.0.0 |
| AssemblyVersion: | 1.0.0.0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 12-Jun-2019 05:52:46 |
| Comments: | - |
| CompanyName: | - |
| FileDescription: | - |
| FileVersion: | 1.0.0.0 |
| InternalName: | Orcus.exe |
| LegalCopyright: | - |
| LegalTrademarks: | - |
| OriginalFilename: | Orcus.exe |
| ProductName: | - |
| ProductVersion: | 1.0.0.0 |
| Assembly Version: | 1.0.0.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 12-Jun-2019 05:52:46 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00002000 | 0x000E1A64 | 0x000E1C00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 7.15415 |
.rsrc | 0x000E4000 | 0x00001000 | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.99491 |
.reloc | 0x000E6000 | 0x0000000C | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 0.10191 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.99793 | 3128 | UNKNOWN | UNKNOWN | RT_MANIFEST |
Imports
mscoree.dll |
Total processes
41
Monitored processes
8
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 620 | "C:\Users\admin\AppData\Roaming\Skype.exe" /watchProcess "C:\Users\admin\AppData\Local\Temp\eh.exe" 3364 "/protectFile" | C:\Users\admin\AppData\Roaming\Skype.exe | — | Skype.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 1004 | C:\Users\admin\AppData\Local\Temp\eh.exe | C:\Users\admin\AppData\Local\Temp\eh.exe | taskeng.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 1876 | "C:\Windows\Microsoft.NET\Framework\v2.0.50727\csc.exe" /noconfig /fullpaths @"C:\Users\admin\AppData\Local\Temp\gjj6wyc3.cmdline" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\csc.exe | — | eh.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Visual C# Command Line Compiler Exit code: 0 Version: 8.0.50727.4927 (NetFXspW7.050727-4900) Modules
| |||||||||||||||
| 2388 | C:\Windows\Microsoft.NET\Framework\v2.0.50727\cvtres.exe /NOLOGO /READONLY /MACHINE:IX86 "/OUT:C:\Users\admin\AppData\Local\Temp\RES4A6B.tmp" "c:\Users\admin\AppData\Local\Temp\CSC4A5A.tmp" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\cvtres.exe | — | csc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft® Resource File To COFF Object Conversion Utility Exit code: 0 Version: 8.00.50727.4940 (Win7SP1.050727-5400) Modules
| |||||||||||||||
| 3144 | C:\Windows\Microsoft.NET\Framework\v2.0.50727\cvtres.exe /NOLOGO /READONLY /MACHINE:IX86 "/OUT:C:\Users\admin\AppData\Local\Temp\RES473E.tmp" "c:\Users\admin\AppData\Local\Temp\CSC473D.tmp" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\cvtres.exe | — | csc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft® Resource File To COFF Object Conversion Utility Exit code: 0 Version: 8.00.50727.4940 (Win7SP1.050727-5400) Modules
| |||||||||||||||
| 3364 | "C:\Users\admin\AppData\Local\Temp\eh.exe" | C:\Users\admin\AppData\Local\Temp\eh.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 3648 | "C:\Users\admin\AppData\Roaming\Skype.exe" /launchSelfAndExit "C:\Users\admin\AppData\Local\Temp\eh.exe" 3364 /protectFile | C:\Users\admin\AppData\Roaming\Skype.exe | eh.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 620 Version: 1.0.0.0 Modules
| |||||||||||||||
| 3872 | "C:\Windows\Microsoft.NET\Framework\v2.0.50727\csc.exe" /noconfig /fullpaths @"C:\Users\admin\AppData\Local\Temp\cvuqmaot.cmdline" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\csc.exe | — | eh.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Visual C# Command Line Compiler Exit code: 0 Version: 8.0.50727.4927 (NetFXspW7.050727-4900) Modules
| |||||||||||||||
Total events
763
Read events
745
Write events
18
Delete events
0
Modification events
| (PID) Process: | (3364) eh.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3364) eh.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3364) eh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3648) Skype.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3648) Skype.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
1
Suspicious files
0
Text files
5
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3872 | csc.exe | C:\Users\admin\AppData\Local\Temp\CSC473D.tmp | — | |
MD5:— | SHA256:— | |||
| 3144 | cvtres.exe | C:\Users\admin\AppData\Local\Temp\RES473E.tmp | — | |
MD5:— | SHA256:— | |||
| 3872 | csc.exe | C:\Users\admin\AppData\Local\Temp\cvuqmaot.dll | — | |
MD5:— | SHA256:— | |||
| 3872 | csc.exe | C:\Users\admin\AppData\Local\Temp\cvuqmaot.out | — | |
MD5:— | SHA256:— | |||
| 1876 | csc.exe | C:\Users\admin\AppData\Local\Temp\CSC4A5A.tmp | — | |
MD5:— | SHA256:— | |||
| 2388 | cvtres.exe | C:\Users\admin\AppData\Local\Temp\RES4A6B.tmp | — | |
MD5:— | SHA256:— | |||
| 1876 | csc.exe | C:\Users\admin\AppData\Local\Temp\gjj6wyc3.dll | — | |
MD5:— | SHA256:— | |||
| 1876 | csc.exe | C:\Users\admin\AppData\Local\Temp\gjj6wyc3.out | — | |
MD5:— | SHA256:— | |||
| 3364 | eh.exe | C:\Users\admin\AppData\Local\Temp\Cab4B93.tmp | — | |
MD5:— | SHA256:— | |||
| 3364 | eh.exe | C:\Users\admin\AppData\Local\Temp\Tar4B94.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
3
DNS requests
1
Threats
4
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3364 | eh.exe | 199.195.250.222:9161 | — | FranTech Solutions | US | malicious |
3364 | eh.exe | 93.184.221.240:80 | www.download.windowsupdate.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.download.windowsupdate.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3364 | eh.exe | A Network Trojan was detected | MALWARE [PTsecurity] Observed Malicious SSL Certificate (Orcus RAT) |
3364 | eh.exe | A Network Trojan was detected | MALWARE [PTsecurity] Observed Malicious SSL Certificate (Orcus RAT) |
3364 | eh.exe | A Network Trojan was detected | MALWARE [PTsecurity] Malicious SSL connection (Orcus RAT) |
1 ETPRO signatures available at the full report