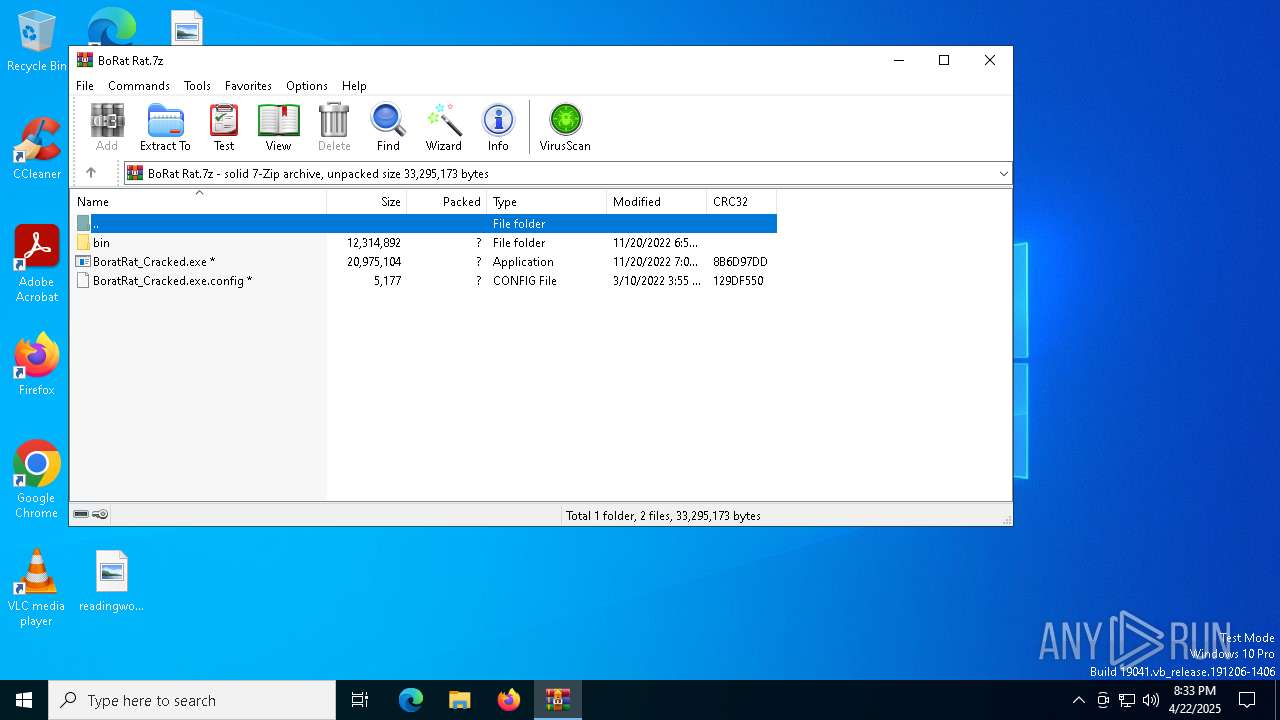
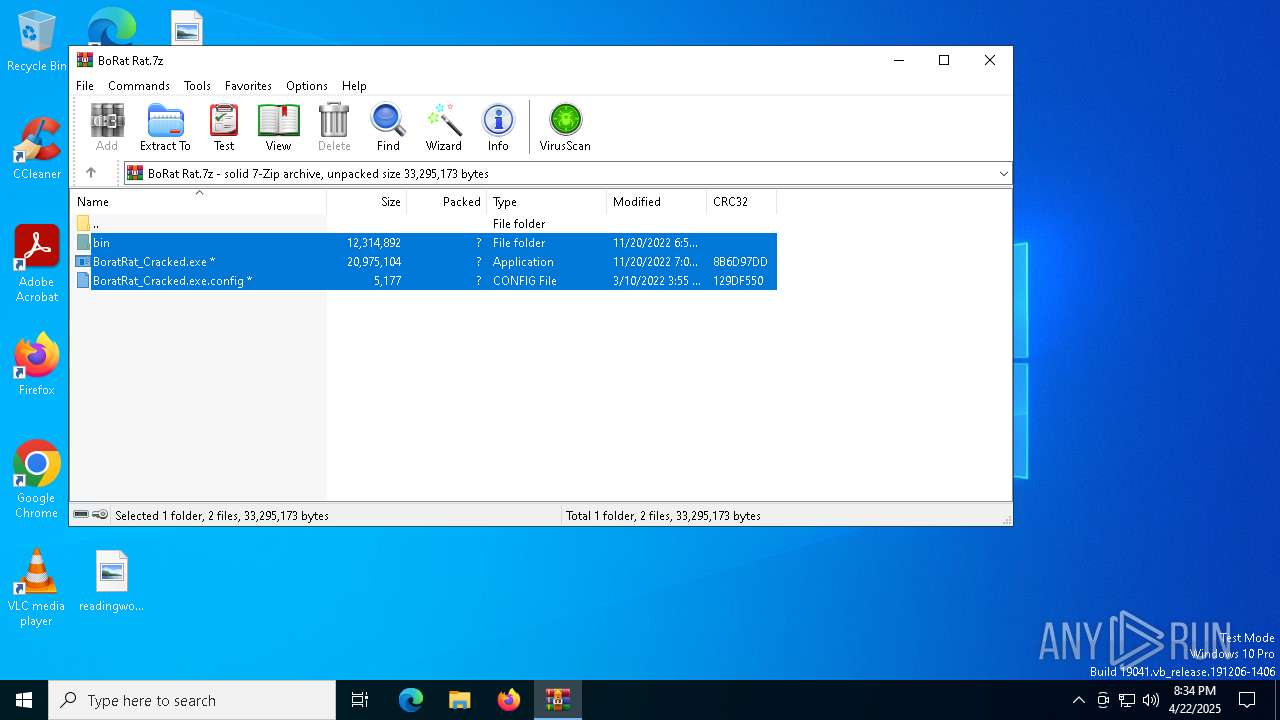
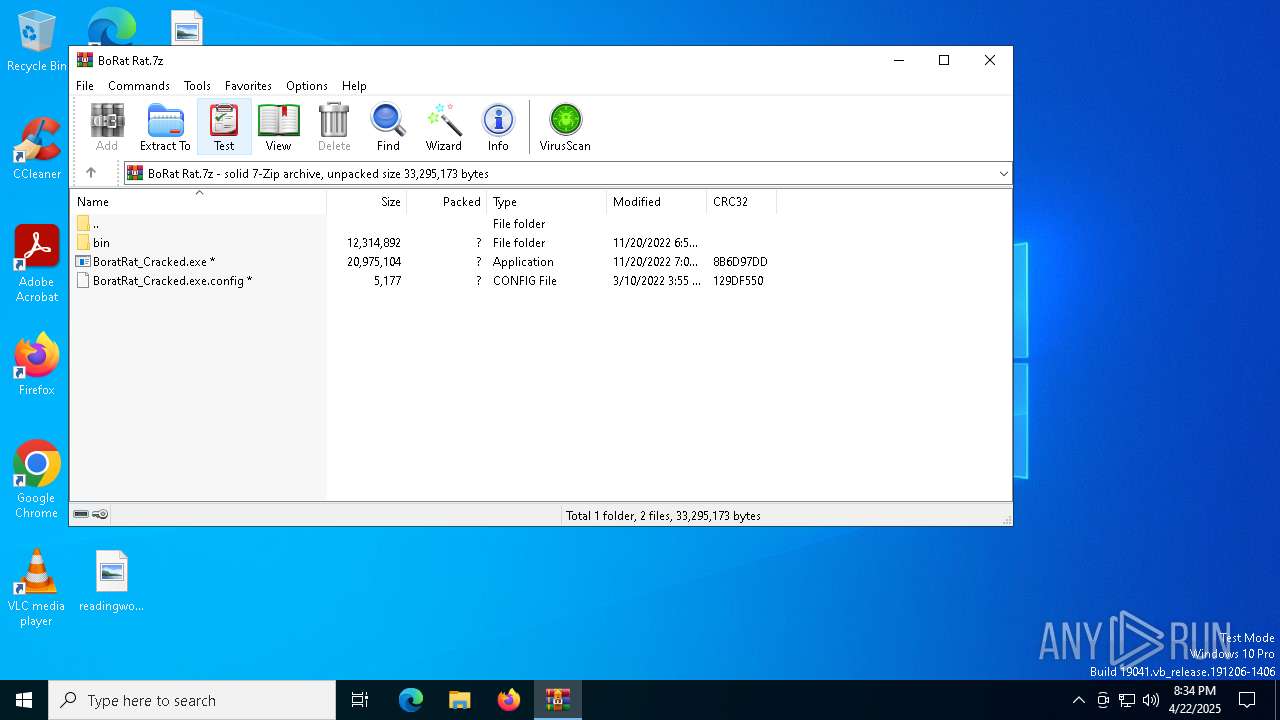
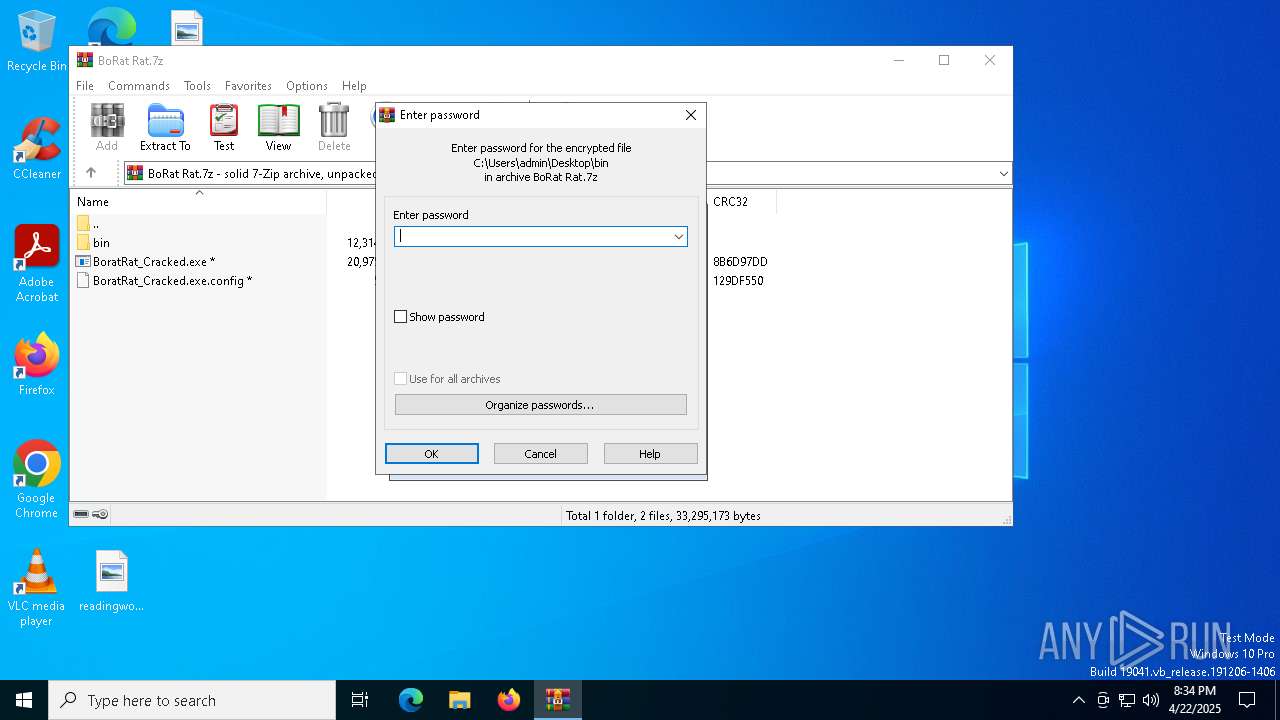
| File name: | BoRat Rat.7z |
| Full analysis: | https://app.any.run/tasks/beb77057-b6b2-4a33-8b51-8b9ce23df81b |
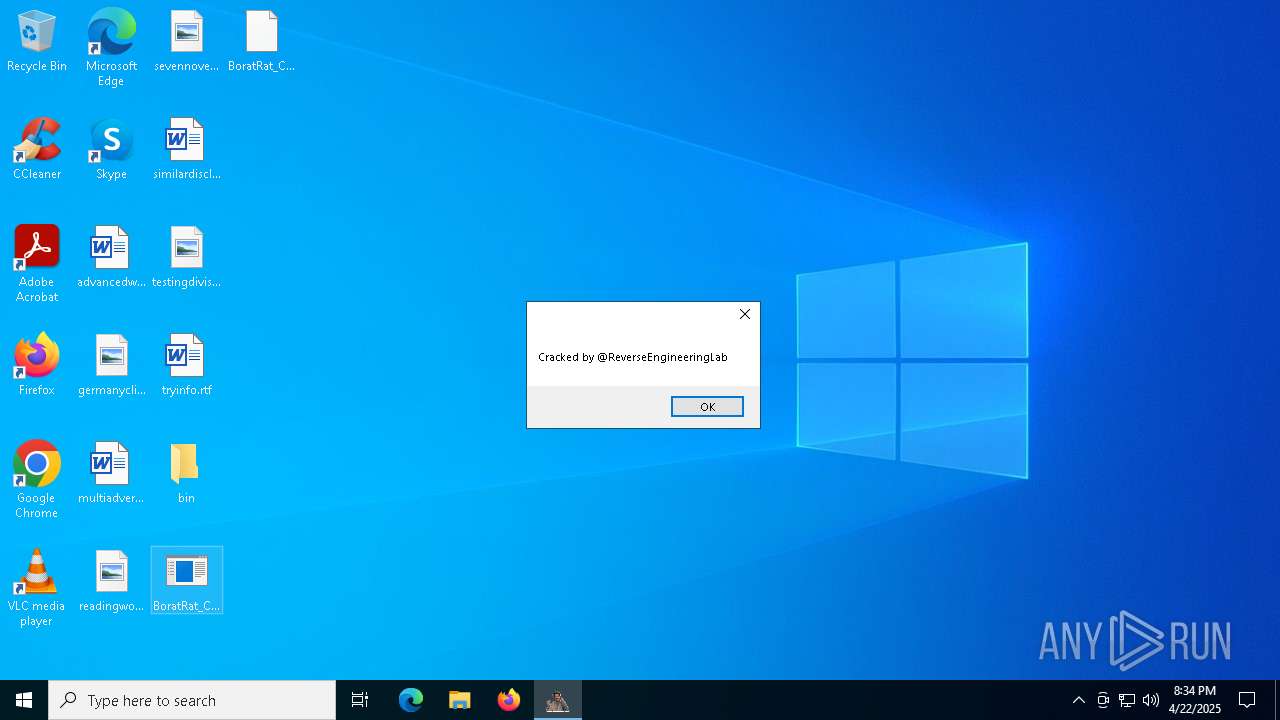
| Verdict: | Malicious activity |
| Threats: | AsyncRAT is a RAT that can monitor and remotely control infected systems. This malware was introduced on Github as a legitimate open-source remote administration software, but hackers use it for its many powerful malicious functions. |
| Analysis date: | April 22, 2025, 20:33:45 |
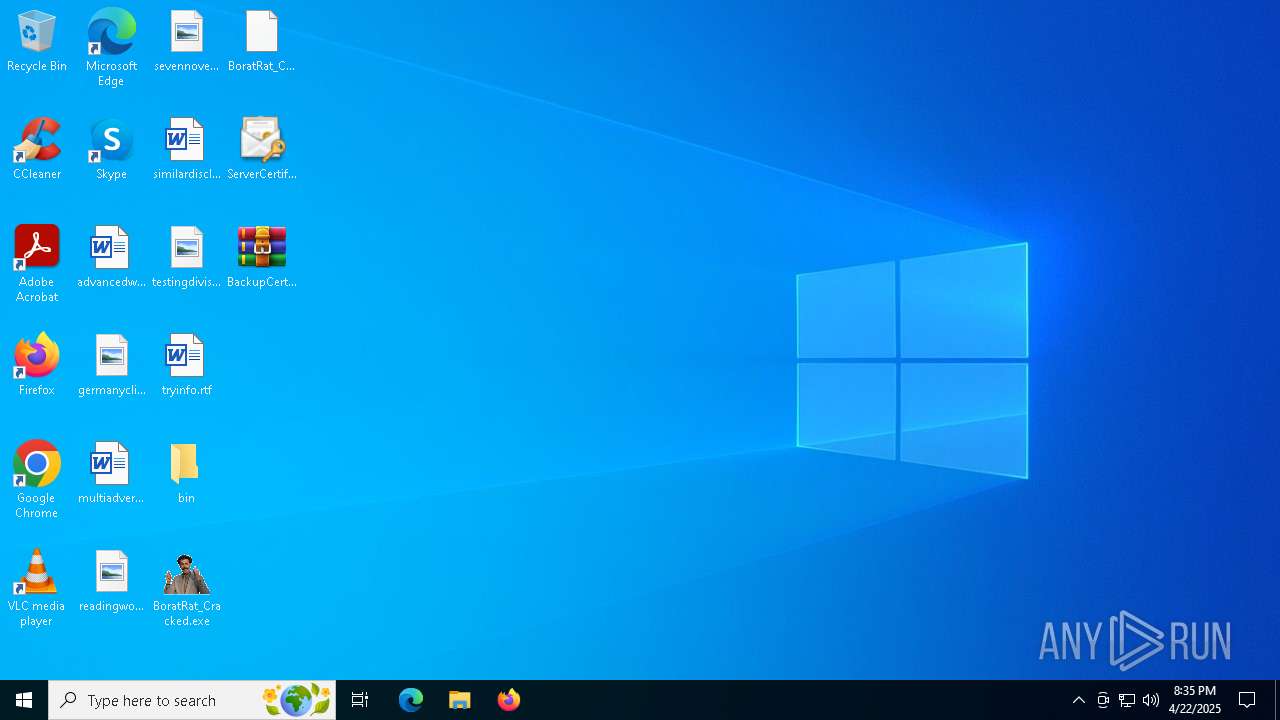
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-7z-compressed |
| File info: | 7-zip archive data, version 0.4 |
| MD5: | 320967EA4C3F77C31CF5B8A7C7281DB1 |
| SHA1: | 4604180A62E0C5E8DF87B9713213551AEF8F911D |
| SHA256: | 758DA04589FAF3A8AEDEAE4F9E26C90C4A7530F5E8368A368EFE8EF792F167D9 |
| SSDEEP: | 98304:tFKpSjCYPyJMSg85p6oVj62iFUCNTeGCYWw9H549XokuXIc9zeBtyMACjnmwWdZm:Mvro8YGfvocaJhGa+I54p |
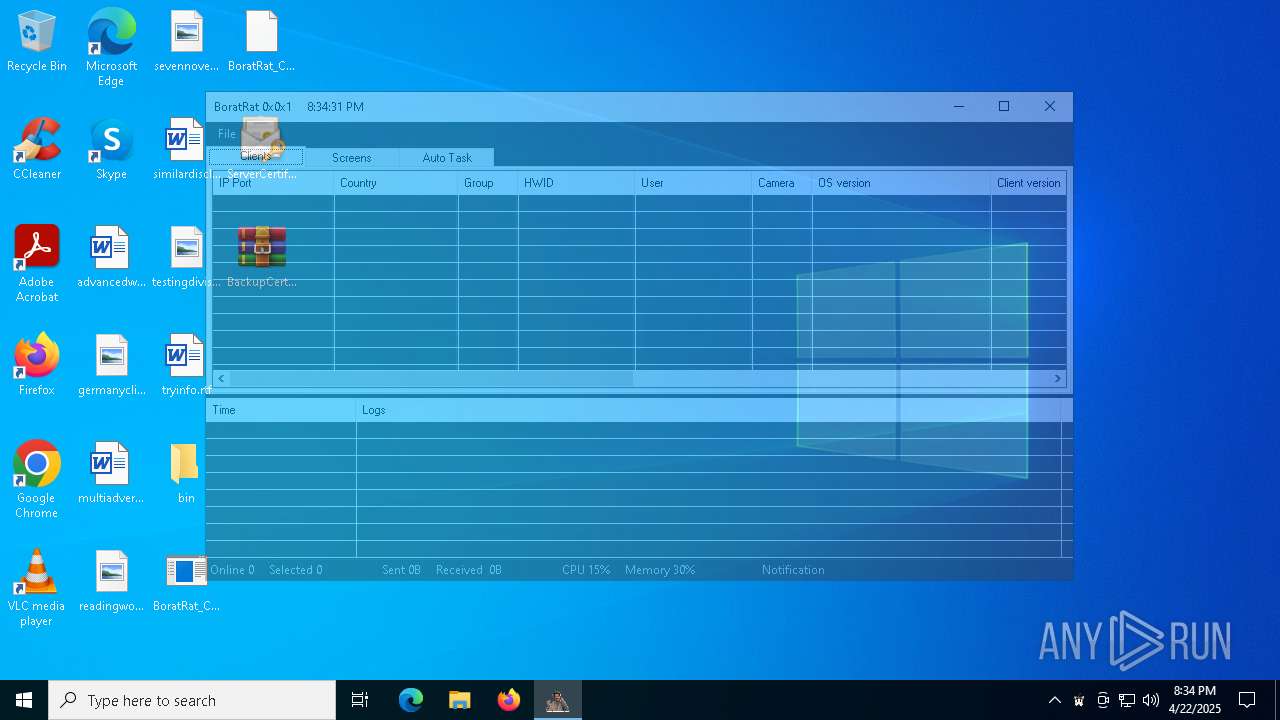
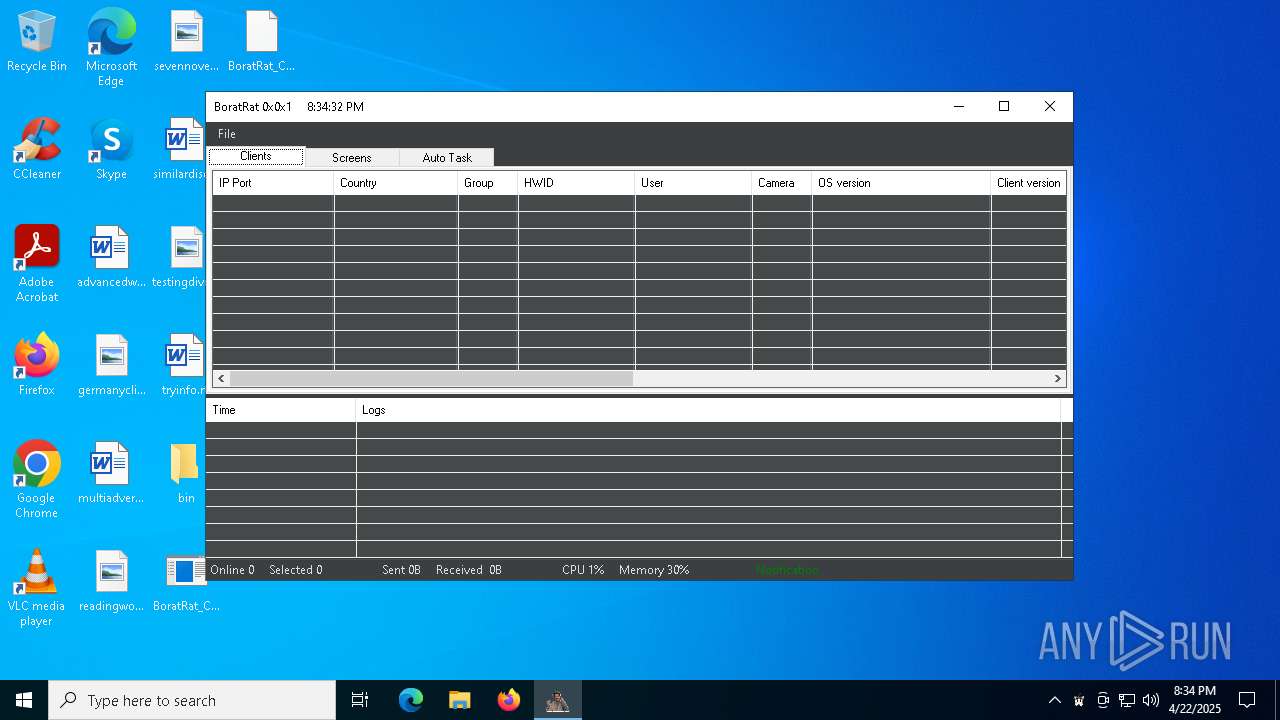
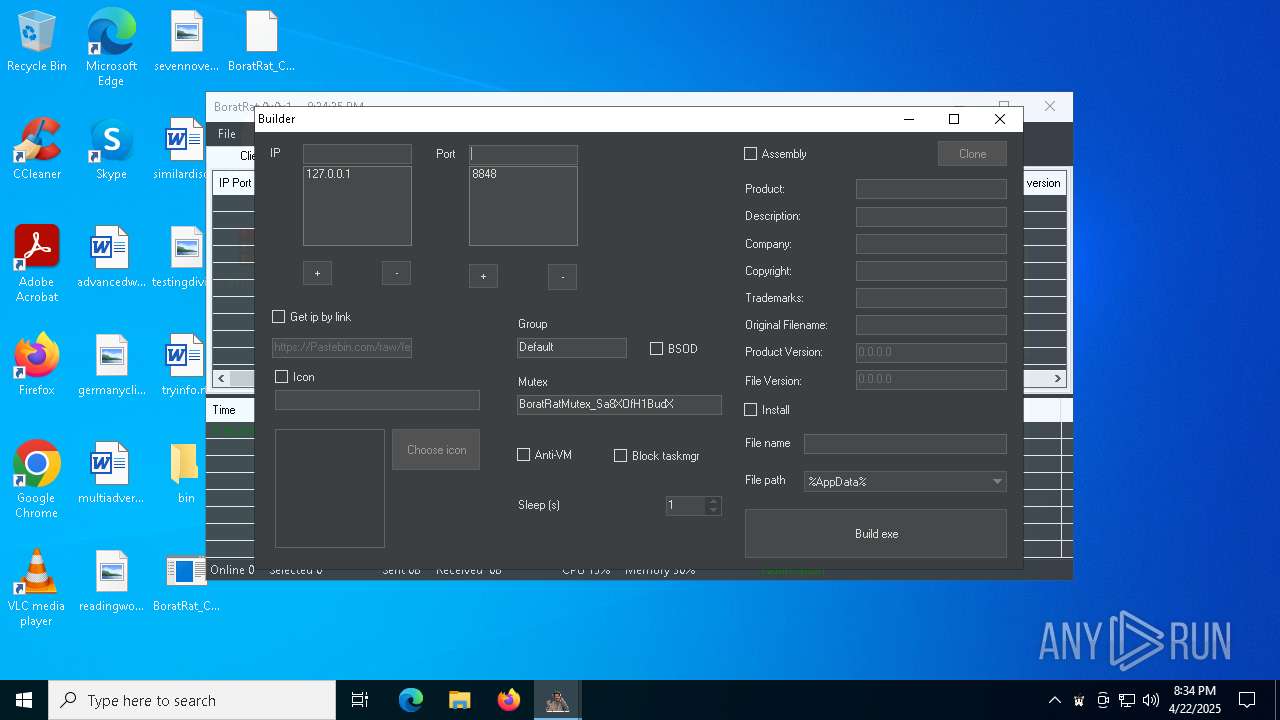
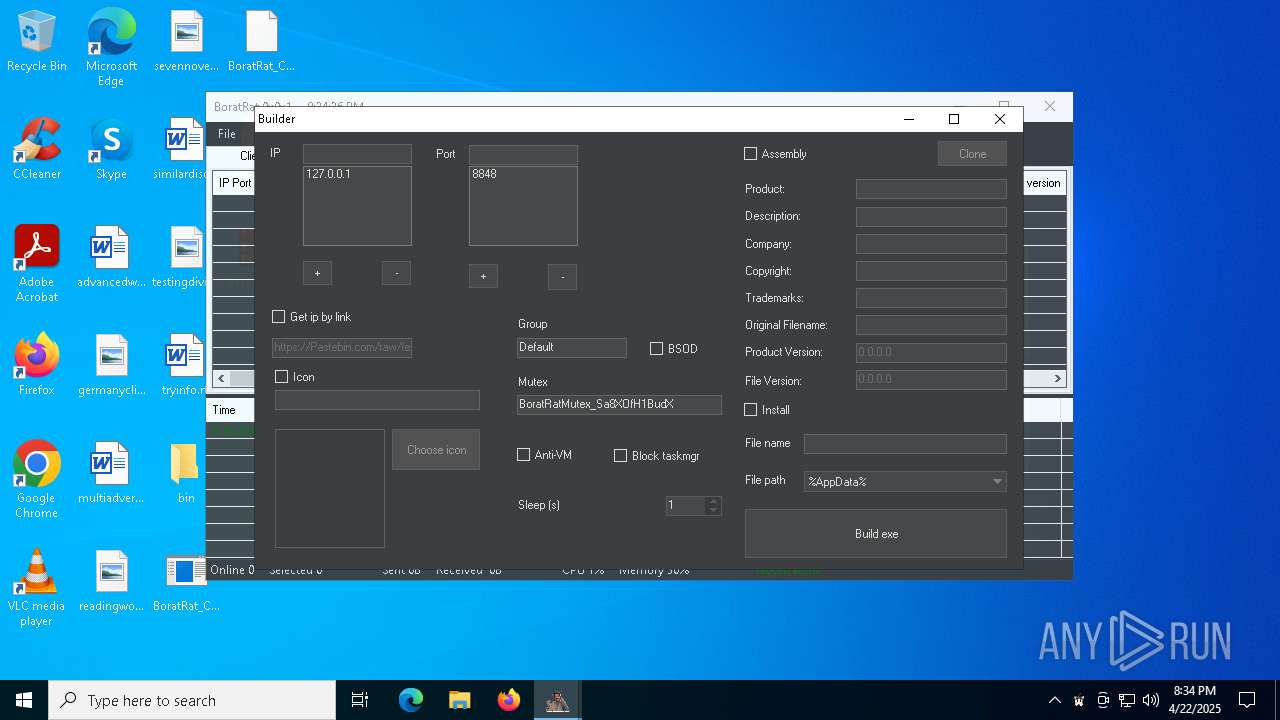
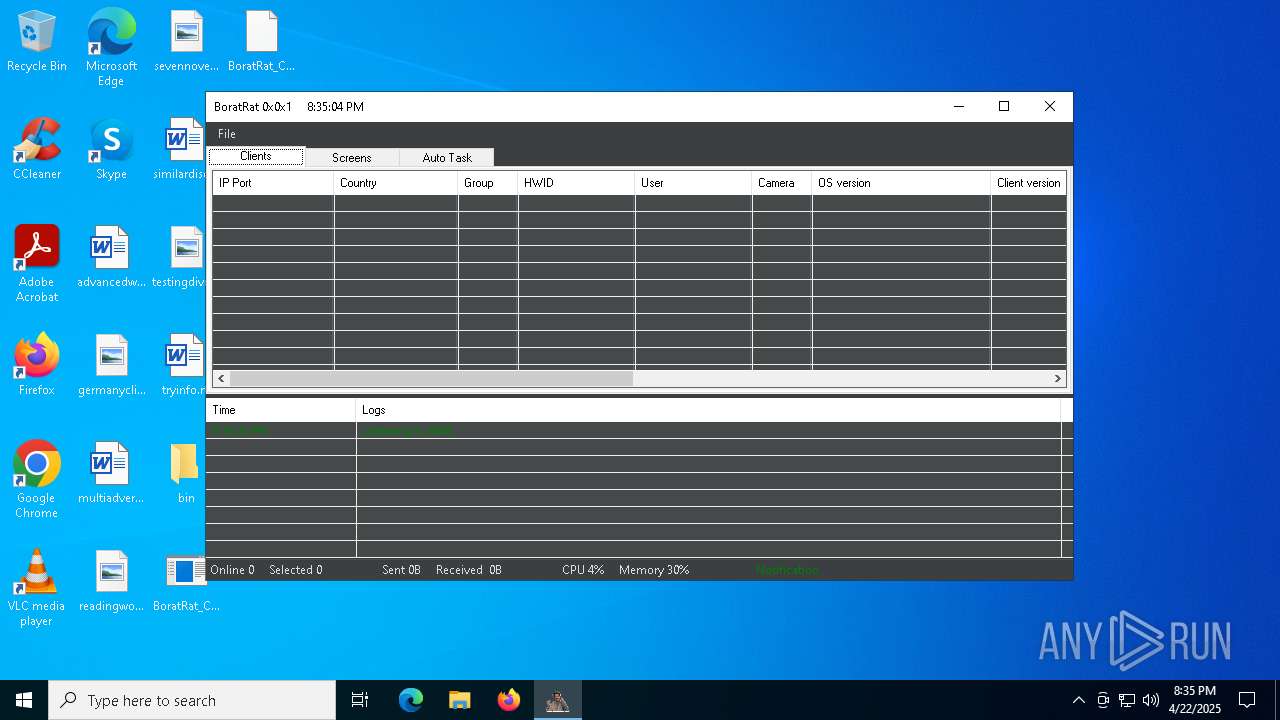
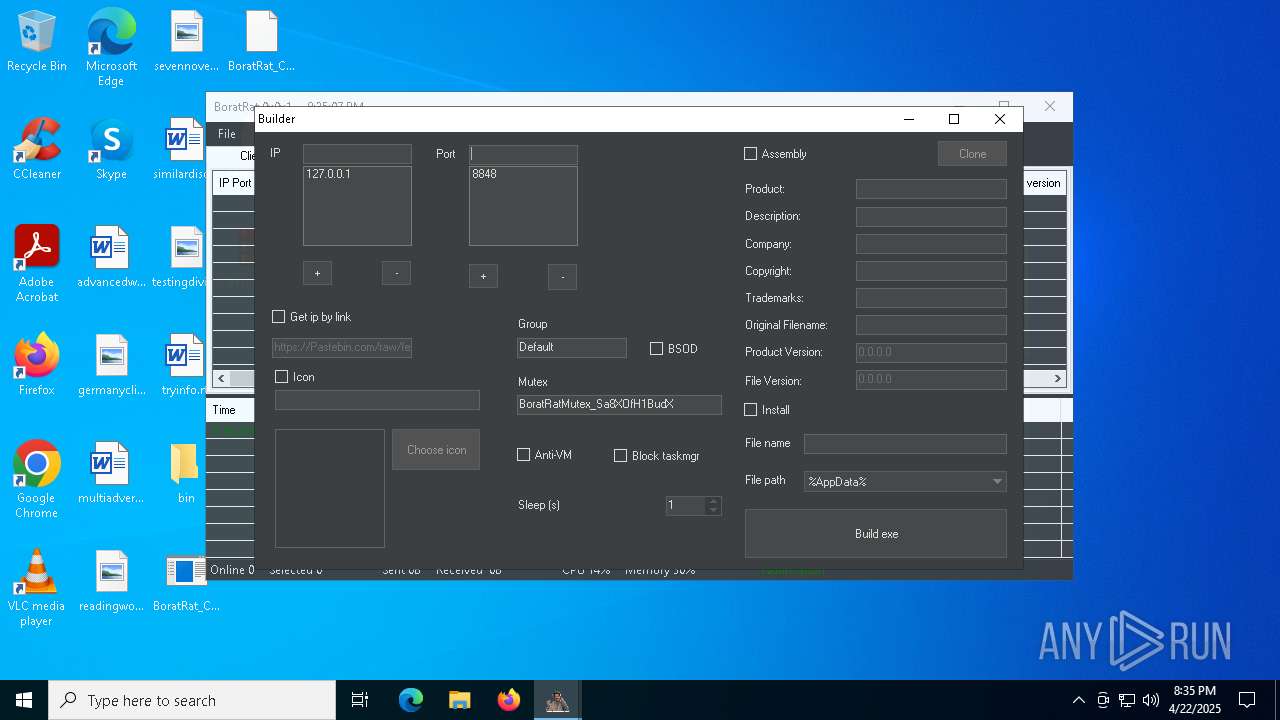
MALICIOUS
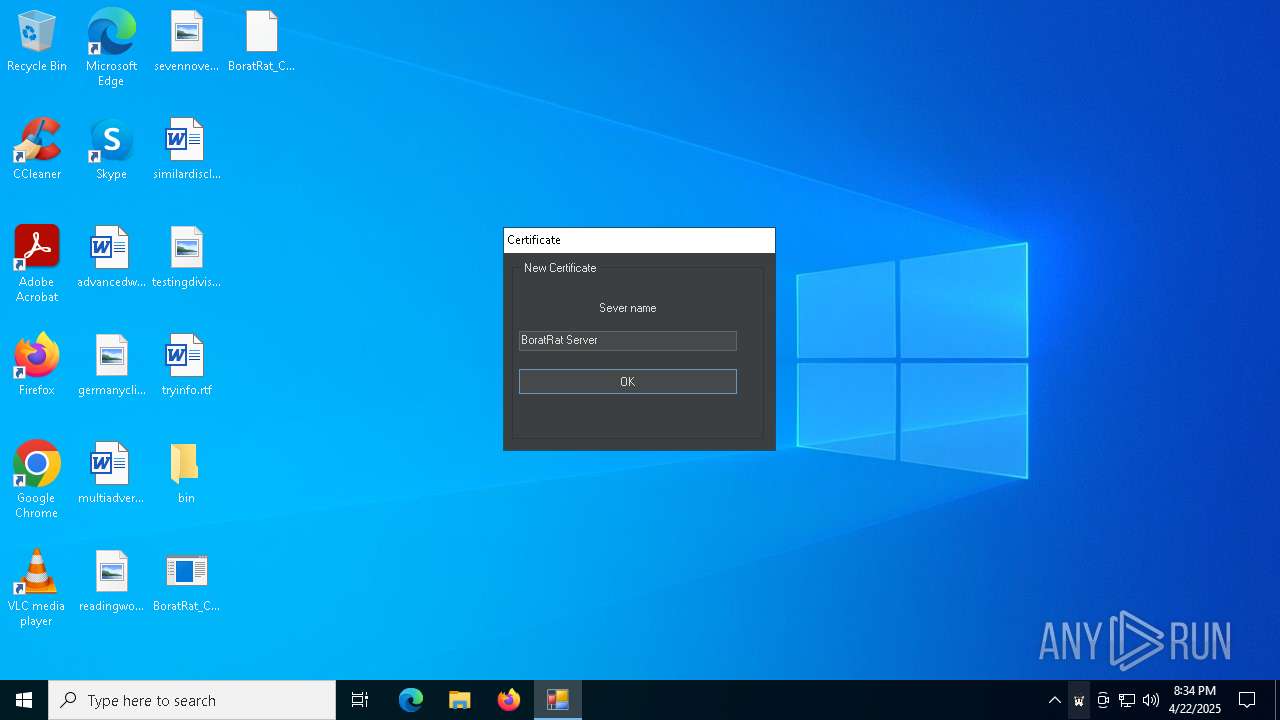
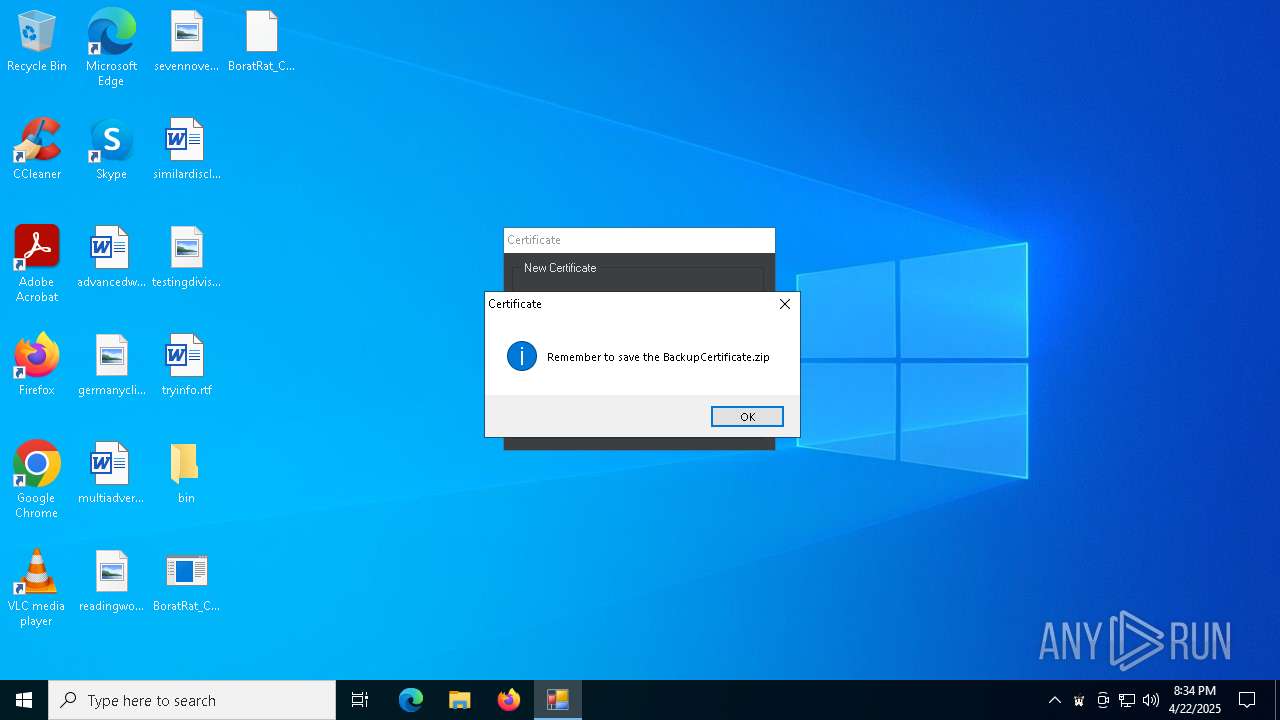
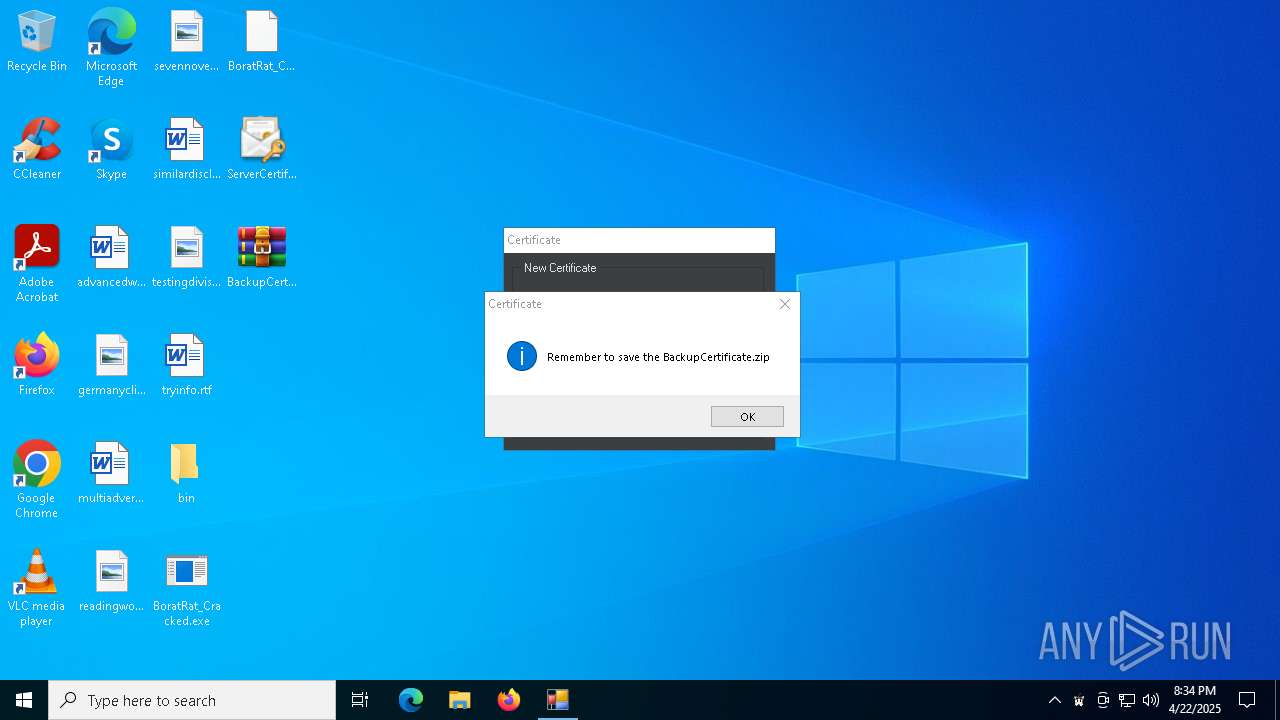
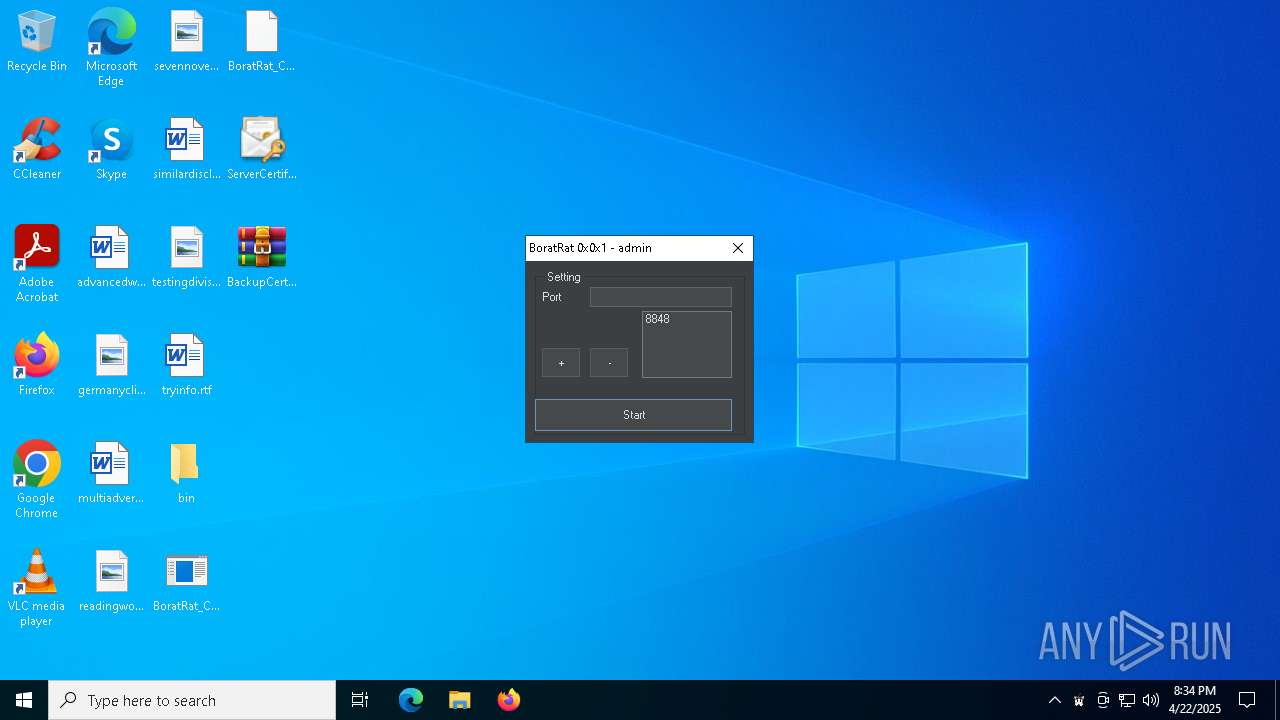
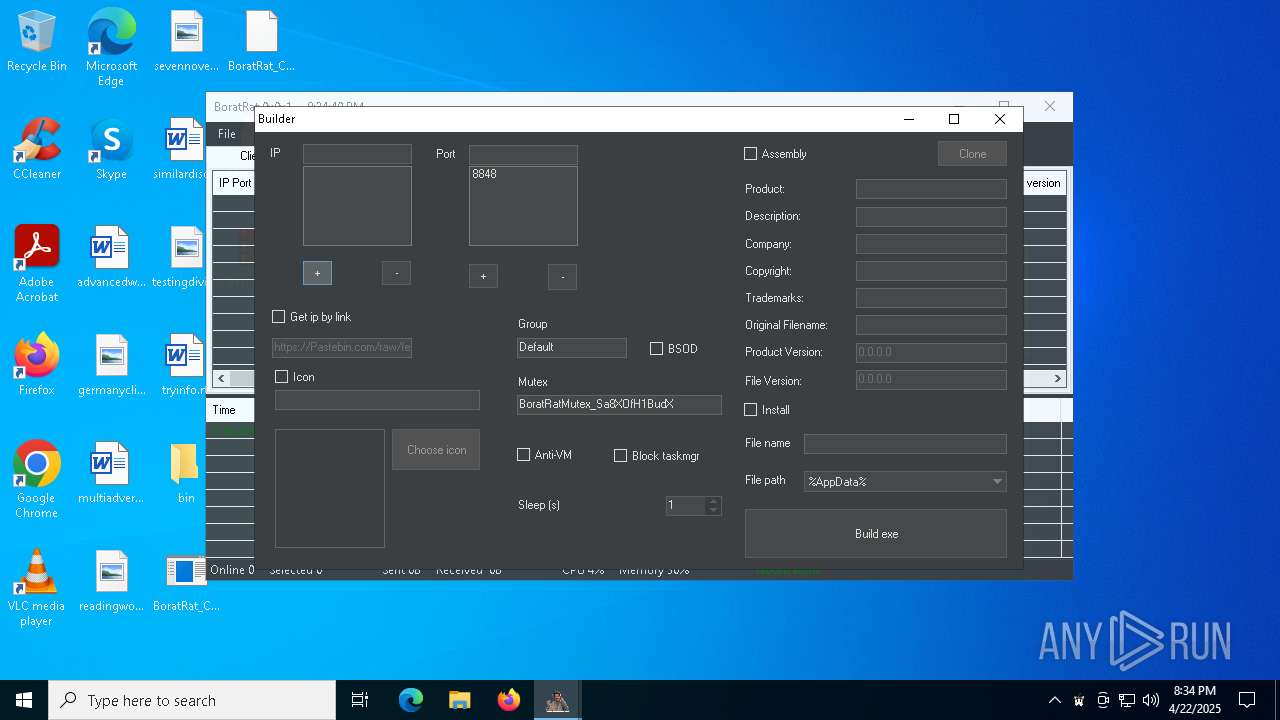
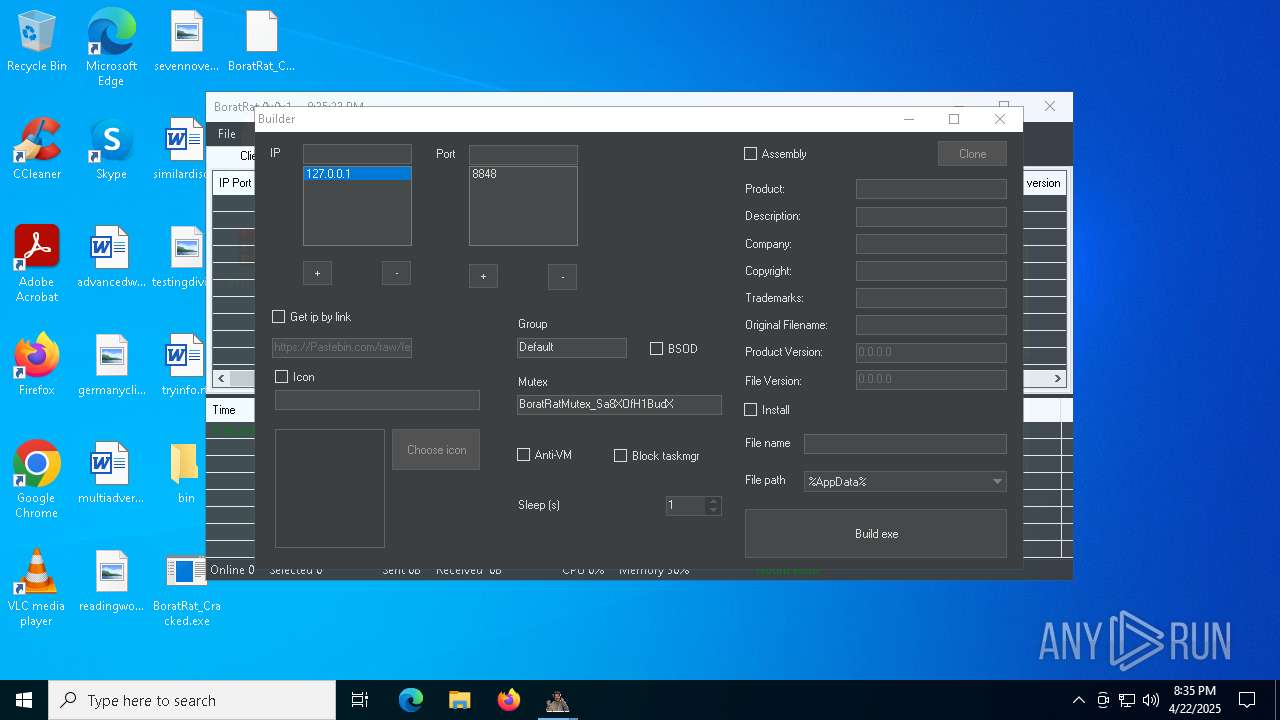
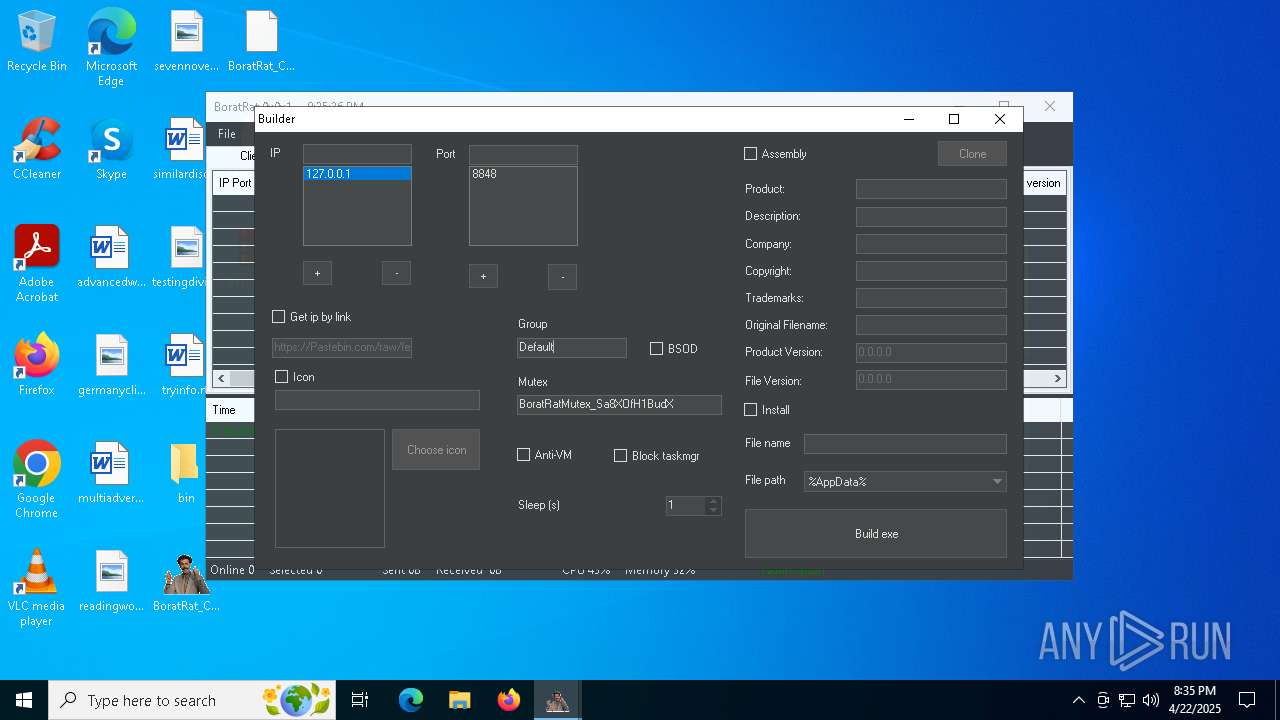
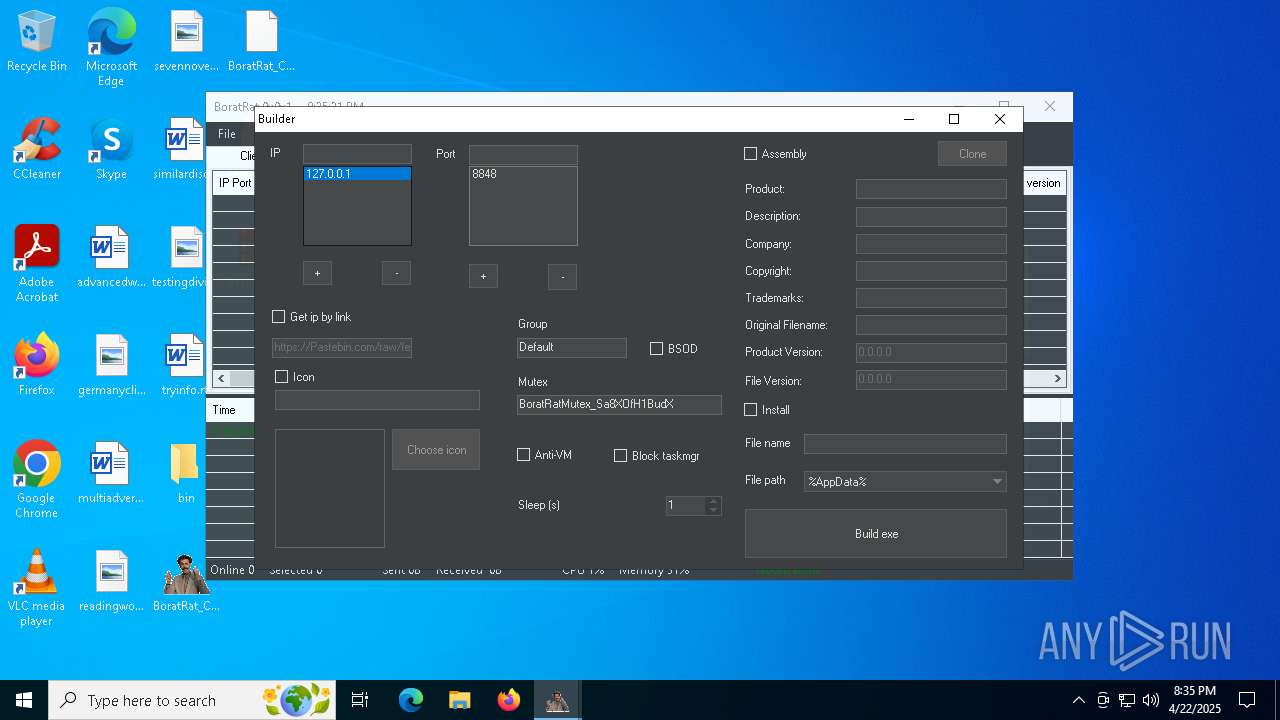
ASYNCRAT has been detected (YARA)
- BoratRat_Cracked.exe (PID: 5548)
SUSPICIOUS
The process creates files with name similar to system file names
- WinRAR.exe (PID: 6028)
The process checks if it is being run in the virtual environment
- BoratRat_Cracked.exe (PID: 5548)
There is functionality for taking screenshot (YARA)
- BoratRat_Cracked.exe (PID: 5548)
Reads security settings of Internet Explorer
- BoratRat_Cracked.exe (PID: 5548)
INFO
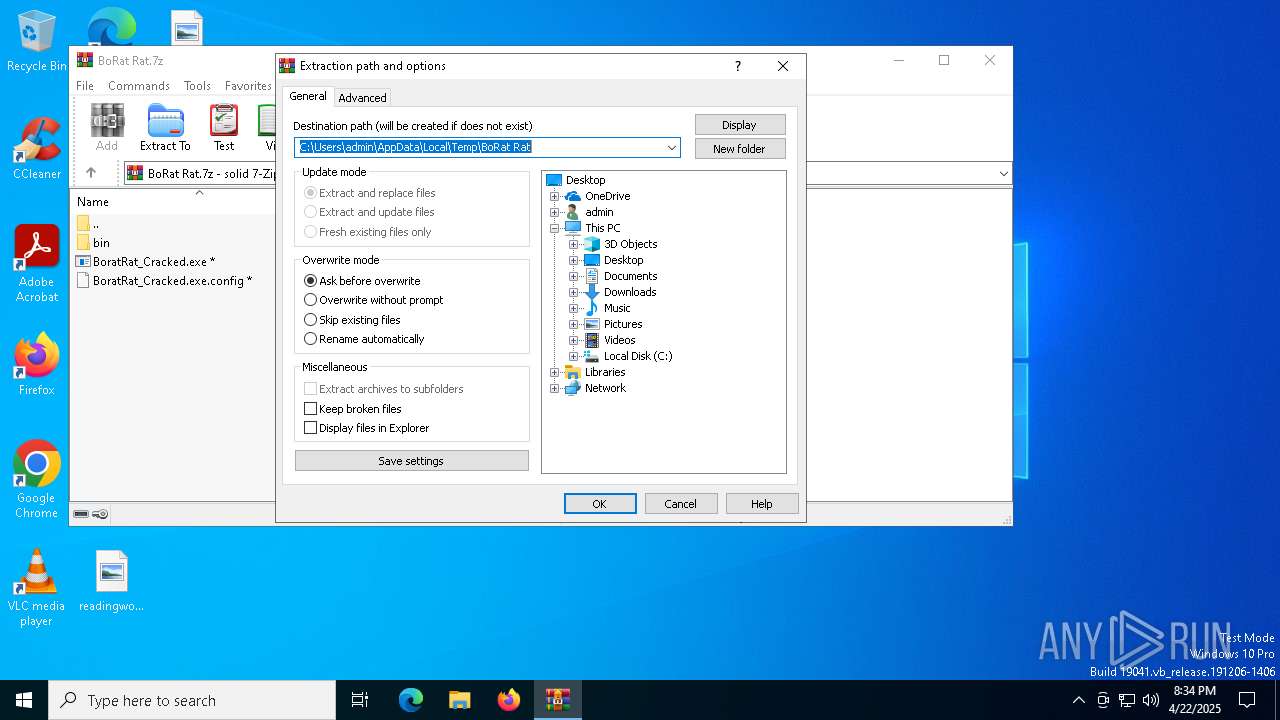
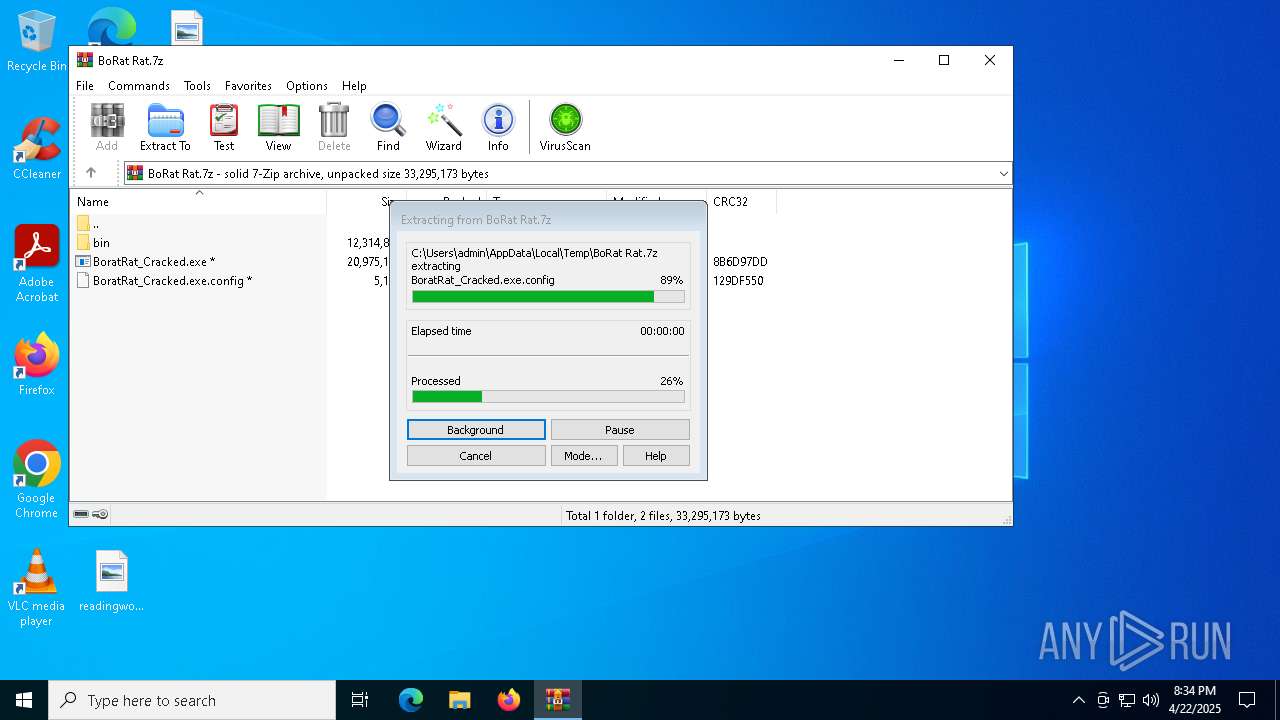
Executable content was dropped or overwritten
- WinRAR.exe (PID: 6028)
Manual execution by a user
- BoratRat_Cracked.exe (PID: 5548)
Reads the machine GUID from the registry
- BoratRat_Cracked.exe (PID: 5548)
Creates files or folders in the user directory
- BoratRat_Cracked.exe (PID: 5548)
Reads the computer name
- BoratRat_Cracked.exe (PID: 5548)
Checks supported languages
- BoratRat_Cracked.exe (PID: 5548)
Potential access to remote process (Base64 Encoded 'OpenProcess')
- BoratRat_Cracked.exe (PID: 5548)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .7z | | | 7-Zip compressed archive (v0.4) (57.1) |
|---|---|---|
| .7z | | | 7-Zip compressed archive (gen) (42.8) |
EXIF
ZIP
| FileVersion: | 7z v0.04 |
|---|---|
| ModifyDate: | 2022:11:20 18:57:23+00:00 |
| ArchivedFileName: | bin |
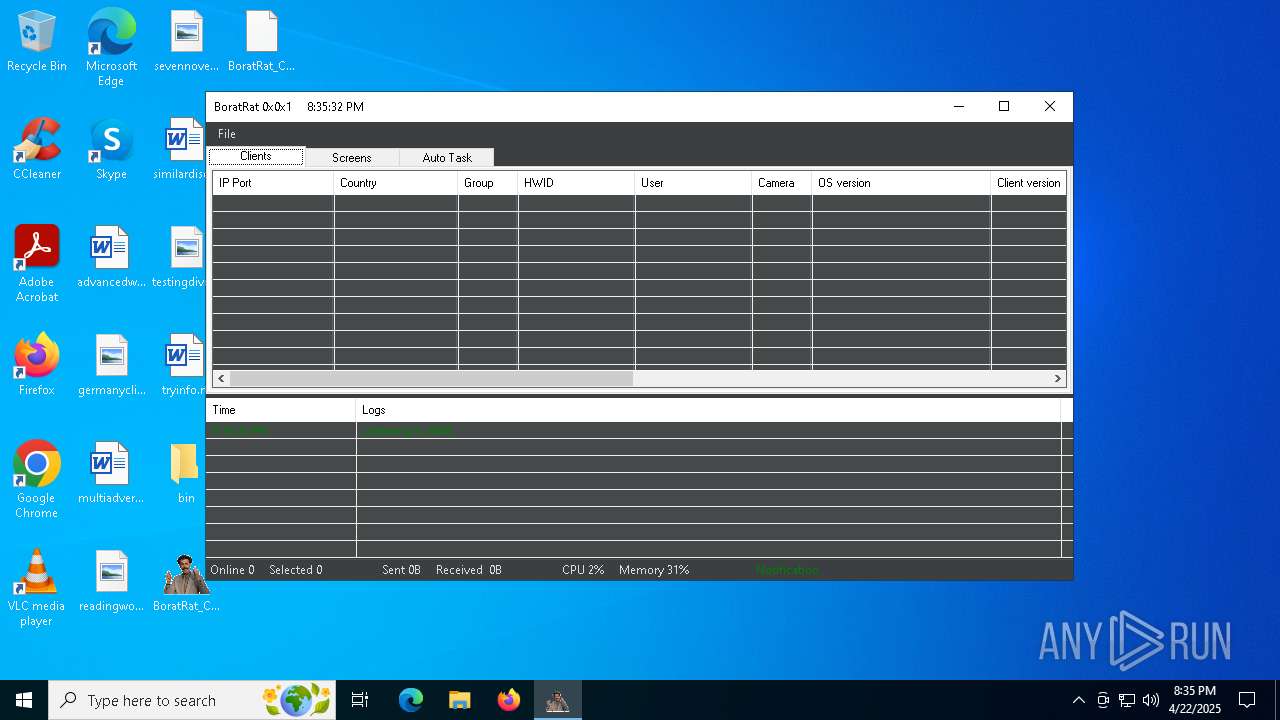
Total processes
133
Monitored processes
3
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
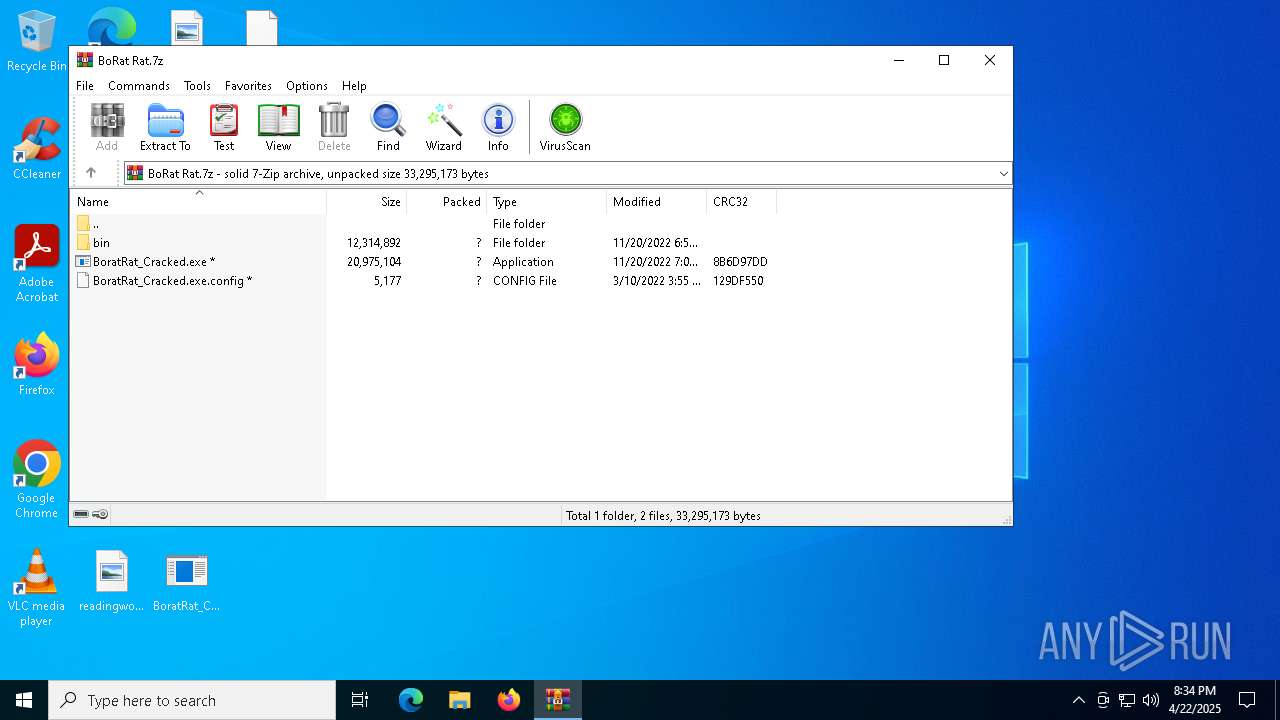
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3332 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5548 | "C:\Users\admin\Desktop\BoratRat_Cracked.exe" | C:\Users\admin\Desktop\BoratRat_Cracked.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: BoratRat Exit code: 0 Version: 1.0.7.0 Modules
| |||||||||||||||
| 6028 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\BoRat Rat.7z" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
Total events
4 283
Read events
4 248
Write events
22
Delete events
13
Modification events
| (PID) Process: | (6028) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (6028) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (6028) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (6028) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\BoRat Rat.7z | |||
| (PID) Process: | (6028) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (6028) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (6028) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (6028) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (6028) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | delete value | Name: | 15 |
Value: | |||
| (PID) Process: | (6028) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | delete value | Name: | 14 |
Value: | |||
Executable files
23
Suspicious files
3
Text files
3
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6028 | WinRAR.exe | C:\Users\admin\Desktop\bin\ip2region.db | — | |
MD5:— | SHA256:— | |||
| 6028 | WinRAR.exe | C:\Users\admin\Desktop\BoratRat_Cracked.exe.config | xml | |
MD5:3E645CCCA1C44A00210924A3B0780955 | SHA256:F29E697EFD7C5ECB928C0310EA832325BF6518786C8E1585E1B85CDC8701602F | |||
| 6028 | WinRAR.exe | C:\Users\admin\Desktop\bin\Audio.dll | executable | |
MD5:9726D7FE49C8BA43845AD8E5E2802BB8 | SHA256:DF31A70CEB0C481646EEAF94189242200FAFD3DF92F8B3EC97C0D0670F0E2259 | |||
| 6028 | WinRAR.exe | C:\Users\admin\Desktop\bin\Regedit.dll | executable | |
MD5:8749C78B8AD09A3B240DD1384A17539B | SHA256:657E3F1F449C0B710B0C571EC8EEE689AE16793FB63B996E0182420D768F89BD | |||
| 6028 | WinRAR.exe | C:\Users\admin\Desktop\bin\Information.dll | executable | |
MD5:87651B12453131DAFD3E91F60D8AEF5A | SHA256:A15D72D990686D06D89D7E11DF2B16BCD5719A40298C19D046FA22C40D56AF44 | |||
| 6028 | WinRAR.exe | C:\Users\admin\Desktop\bin\MessagePackLib.dll | executable | |
MD5:590B00C87D5FF2FFE09079F0406EB2CD | SHA256:ADB00DEE751B4BA620D3B0E002F5B6D8B89CF63B062F74EC65BBA72294D553D1 | |||
| 6028 | WinRAR.exe | C:\Users\admin\Desktop\bin\Discord.dll | executable | |
MD5:7EE673594BBB20F65448AAB05F1361D0 | SHA256:8FA7634B7DCA1A451CF8940429BE6AD2440821ED04D5D70B6E727E5968E0B5F6 | |||
| 6028 | WinRAR.exe | C:\Users\admin\Desktop\bin\RemoteDesktop.dll | executable | |
MD5:0F93650DD78557F41B7C5467E3B6B6A7 | SHA256:CC5B49D2A2821D4F6EF6AF8A1E50994C6690D6A4DAA41BD048FE79BD8B578988 | |||
| 6028 | WinRAR.exe | C:\Users\admin\Desktop\bin\ProcessManager.dll | executable | |
MD5:91EDCB945924DF5FBF4FF123AA63199C | SHA256:5B1F80FF787BDCD7EE12AA64BE1F2F5F1F658BD644BBC5FD73527B51DA6CE0D6 | |||
| 6028 | WinRAR.exe | C:\Users\admin\Desktop\bin\Miscellaneous.dll | executable | |
MD5:509D41DA4A688A2E50FC8E3AFCA074C7 | SHA256:F91973113FD01465999CE317F3E7A89DF8C91A5EFADCFA61E5CCCE687BF3580A | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
10
TCP/UDP connections
36
DNS requests
19
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.48.23.173:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
2104 | svchost.exe | GET | 200 | 23.48.23.173:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 2.16.253.202:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.48.23.173:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
2104 | svchost.exe | GET | 200 | 2.16.253.202:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 2.16.253.202:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5720 | SIHClient.exe | GET | 200 | 23.219.150.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
5720 | SIHClient.exe | GET | 200 | 23.219.150.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
2924 | SearchApp.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.48.23.173:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
2104 | svchost.exe | 23.48.23.173:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 23.48.23.173:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5496 | MoUsoCoreWorker.exe | 2.16.253.202:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
2104 | svchost.exe | 2.16.253.202:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
— | — | 2.16.253.202:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
3216 | svchost.exe | 172.211.123.248:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |