| File name: | Shipping Details.ace |
| Full analysis: | https://app.any.run/tasks/d98cebf7-23e7-47e1-abe4-875d4b532fe7 |
| Verdict: | Malicious activity |
| Threats: | Agent Tesla is spyware that collects information about the actions of its victims by recording keystrokes and user interactions. It is falsely marketed as a legitimate software on the dedicated website where this malware is sold. |
| Analysis date: | November 30, 2020, 00:41:12 |
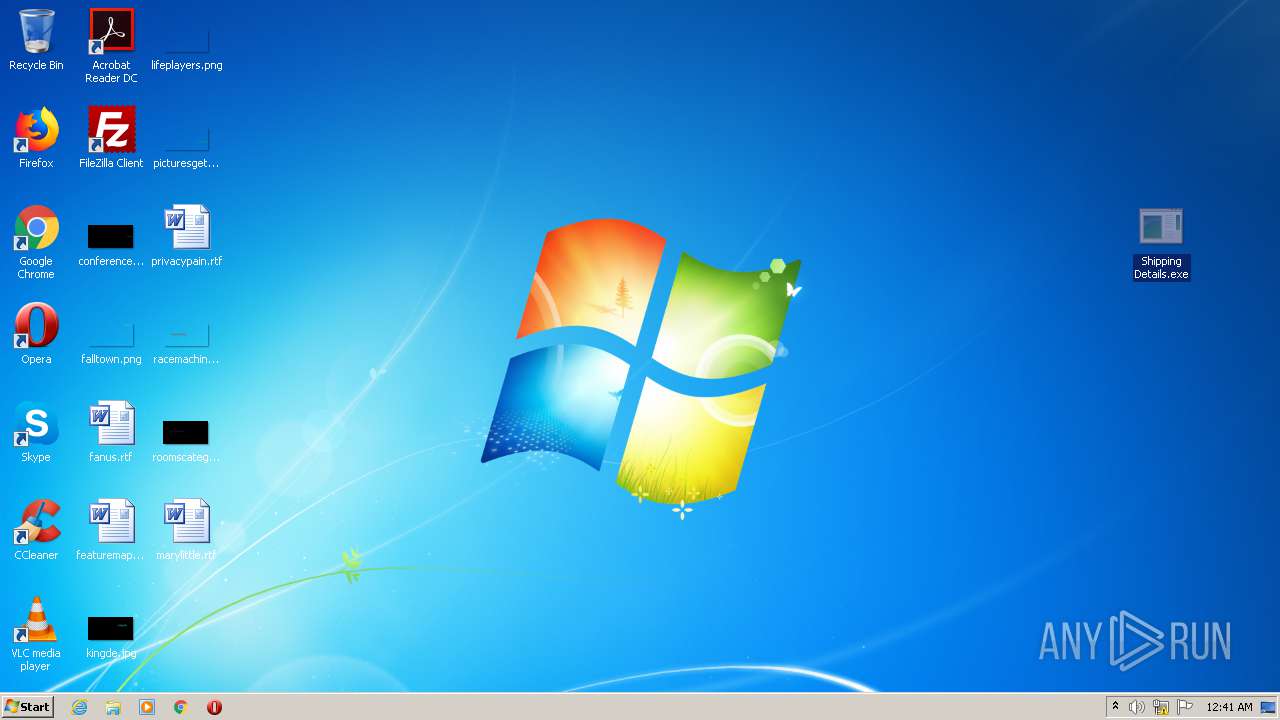
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
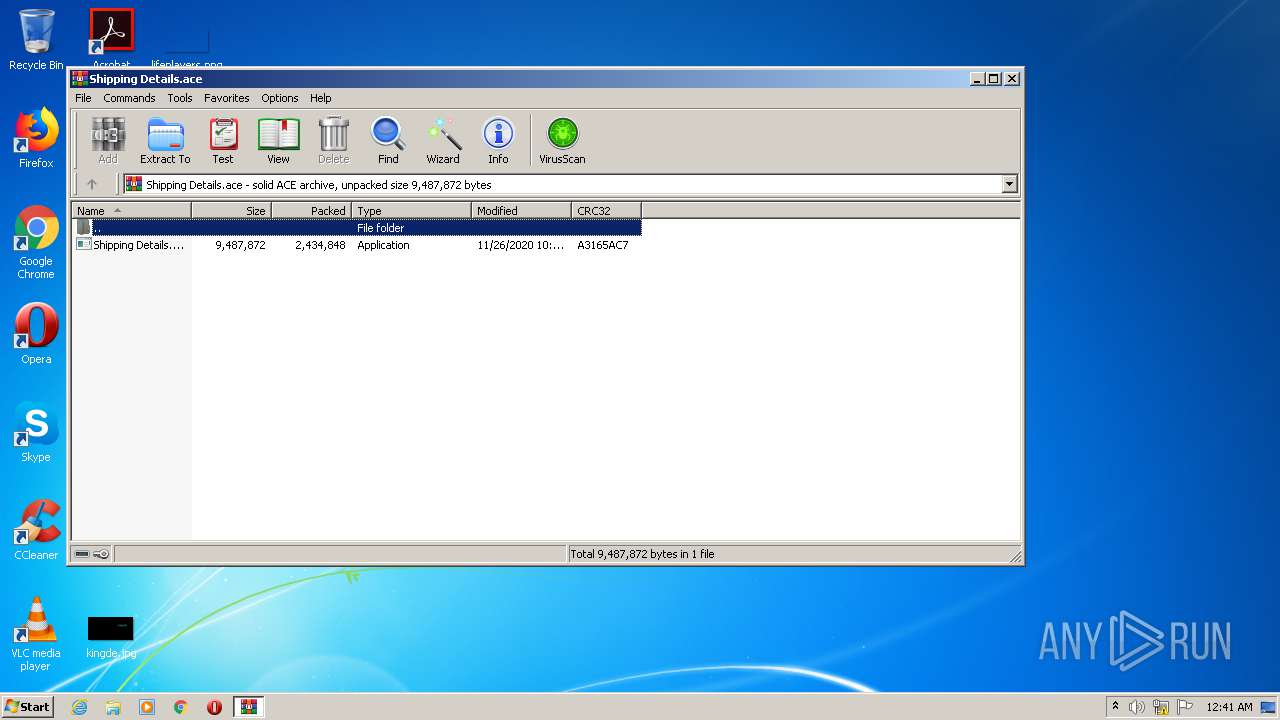
| MIME: | application/octet-stream |
| File info: | ACE archive data version 20, from Win/32, version 20 to extract, contains AV-String (unregistered), solid |
| MD5: | 11E88A20552BC318E875F60D01E1A2F0 |
| SHA1: | E81FD99B743EF8FA8E0428DBB4AE917BFE51C119 |
| SHA256: | 754A3E830B7E83E3E29D1C0DC83A7365089B408F6E6A3381D66FBFB8D4EEE2D7 |
| SSDEEP: | 49152:yJD0ZqRsiO42/E8kZL66vvGA4F9UiI8bkgqqj74oC5vS/Kmat:MD0eON/Eb26vvyF9xI8bkgqqj7NC5uat |
MALICIOUS
Changes the autorun value in the registry
- Shipping Details.exe (PID: 3104)
Application was dropped or rewritten from another process
- Shipping Details.exe (PID: 3104)
- Shipping Details.exe (PID: 1532)
Writes to a start menu file
- Shipping Details.exe (PID: 3104)
Changes the login/logoff helper path in the registry
- Shipping Details.exe (PID: 3104)
Changes settings of System certificates
- Shipping Details.exe (PID: 3104)
- Shipping Details.exe (PID: 1532)
Disables Windows Defender
- Shipping Details.exe (PID: 3104)
Actions looks like stealing of personal data
- Shipping Details.exe (PID: 1532)
AGENTTESLA was detected
- Shipping Details.exe (PID: 1532)
SUSPICIOUS
Executable content was dropped or overwritten
- Shipping Details.exe (PID: 3104)
Creates files in the user directory
- Shipping Details.exe (PID: 3104)
- powershell.exe (PID: 2660)
- powershell.exe (PID: 2952)
- powershell.exe (PID: 2452)
- powershell.exe (PID: 1692)
Drops a file with a compile date too recent
- Shipping Details.exe (PID: 3104)
Executes PowerShell scripts
- Shipping Details.exe (PID: 3104)
Reads Environment values
- Shipping Details.exe (PID: 3104)
Adds / modifies Windows certificates
- Shipping Details.exe (PID: 3104)
- Shipping Details.exe (PID: 1532)
Application launched itself
- Shipping Details.exe (PID: 3104)
INFO
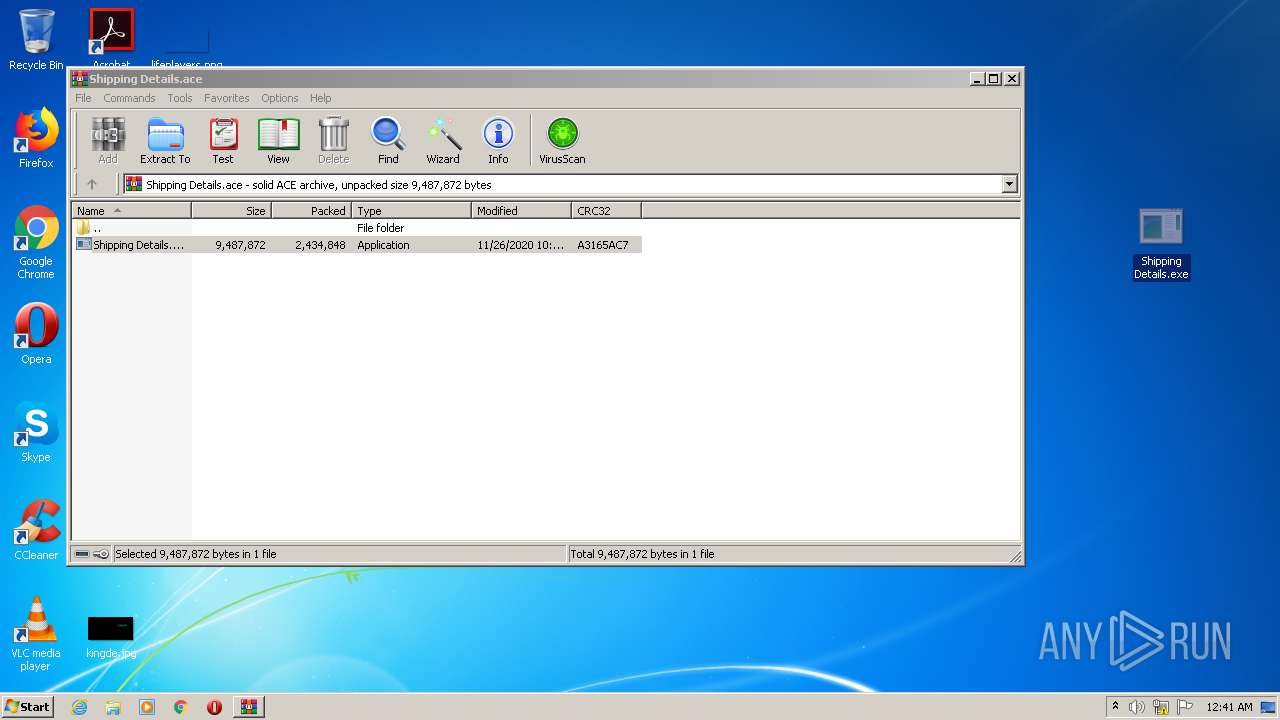
Manual execution by user
- Shipping Details.exe (PID: 3104)
Reads settings of System Certificates
- Shipping Details.exe (PID: 3104)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .ace | | | ACE compressed archive (100) |
|---|
Total processes
46
Monitored processes
7
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1532 | "C:\Users\admin\Desktop\Shipping Details.exe" | C:\Users\admin\Desktop\Shipping Details.exe | Shipping Details.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1692 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" Add-MpPreference -ExclusionPath "C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\Shipping Details.exe" -Force | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | Shipping Details.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2452 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" Add-MpPreference -ExclusionPath "C:\Users\admin\Desktop\Shipping Details.exe" -Force | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | Shipping Details.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2532 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\Shipping Details.ace" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 2660 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" Add-MpPreference -ExclusionPath "C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\Shipping Details.exe" -Force | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | Shipping Details.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2952 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" Add-MpPreference -ExclusionPath "C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\Shipping Details.exe" -Force | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | Shipping Details.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3104 | "C:\Users\admin\Desktop\Shipping Details.exe" | C:\Users\admin\Desktop\Shipping Details.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 1 Modules
| |||||||||||||||
Total events
1 632
Read events
1 336
Write events
294
Delete events
2
Modification events
| (PID) Process: | (2532) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2532) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2532) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2532) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Shipping Details.ace | |||
| (PID) Process: | (2532) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2532) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2532) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2532) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2532) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\ACE Compression Software\ActiveAce\2.0 |
| Operation: | write | Name: | Count |
Value: 0 | |||
| (PID) Process: | (2532) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\ACE Compression Software\ActiveAce\2.0 |
| Operation: | write | Name: | Name |
Value: 542D4B42647265644B76737A7E794B566767537663764B5B7874767B4B43727A674B447F7E67677E797037537263767E7B6439767472171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171700 | |||
Executable files
1
Suspicious files
8
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2532 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2532.23091\Shipping Details.exe | — | |
MD5:— | SHA256:— | |||
| 2660 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\XDKINBJC9FWE2CISEGC6.temp | — | |
MD5:— | SHA256:— | |||
| 2952 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\UAIMR4WEZ9ZHXLCXYZOL.temp | — | |
MD5:— | SHA256:— | |||
| 1692 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\2E27ACK8GYYG7EOZWHV3.temp | — | |
MD5:— | SHA256:— | |||
| 2452 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\JBU5K7TJIFGW4GVF71A2.temp | — | |
MD5:— | SHA256:— | |||
| 2660 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF15a32f.TMP | binary | |
MD5:— | SHA256:— | |||
| 2660 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 3104 | Shipping Details.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\Shipping Details.exe | executable | |
MD5:— | SHA256:— | |||
| 1692 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF15a37d.TMP | binary | |
MD5:— | SHA256:— | |||
| 2952 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF15a34e.TMP | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
3
DNS requests
3
Threats
5
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3104 | Shipping Details.exe | 104.23.99.190:443 | pastebin.com | Cloudflare Inc | US | malicious |
1532 | Shipping Details.exe | 23.21.42.25:443 | api.ipify.org | Amazon.com, Inc. | US | malicious |
1532 | Shipping Details.exe | 144.208.71.113:587 | mail.gayaceramic.com | InMotion Hosting, Inc. | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
pastebin.com |
| malicious |
api.ipify.org |
| shared |
mail.gayaceramic.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1532 | Shipping Details.exe | Misc activity | SUSPICIOUS [PTsecurity] ipify.org External IP Check |
1532 | Shipping Details.exe | Misc activity | SUSPICIOUS [PTsecurity] ipify.org External IP Check |
1532 | Shipping Details.exe | Generic Protocol Command Decode | SURICATA Applayer Detect protocol only one direction |
1532 | Shipping Details.exe | A Network Trojan was detected | SPYWARE [PTsecurity] AgentTesla Exfiltration |
1 ETPRO signatures available at the full report
Process | Message |
|---|---|
Shipping Details.exe | dewfew few fewfew we off
|
Shipping Details.exe | fewfew fewf ewfewfewf off
|