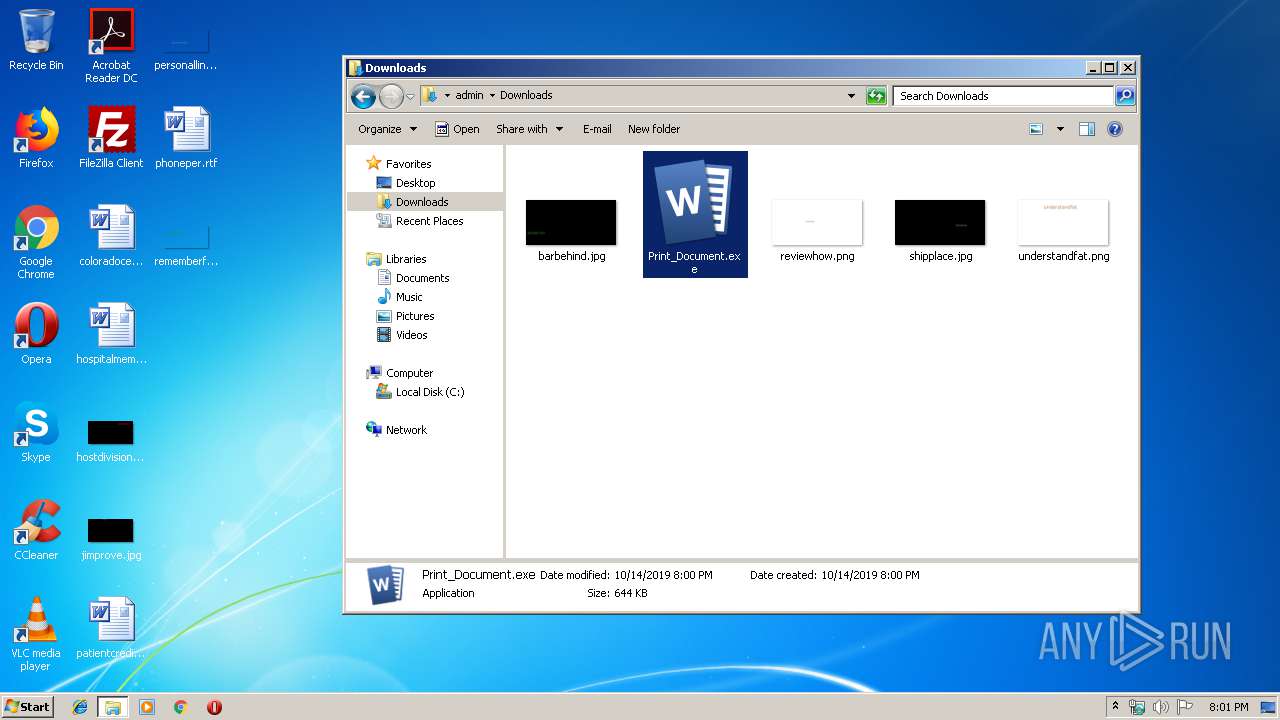
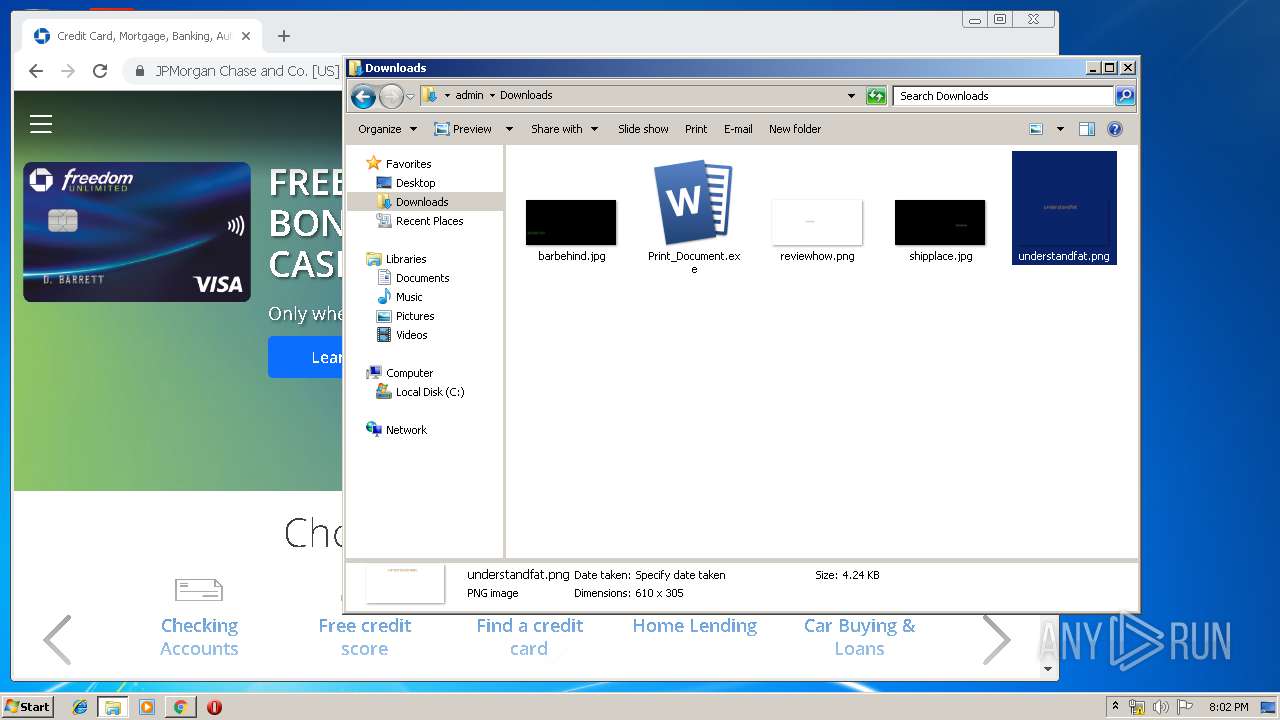
| File name: | Print_Document.exe |
| Full analysis: | https://app.any.run/tasks/7d62431c-c584-4893-9e9f-b9ff6c2f34dc |
| Verdict: | Malicious activity |
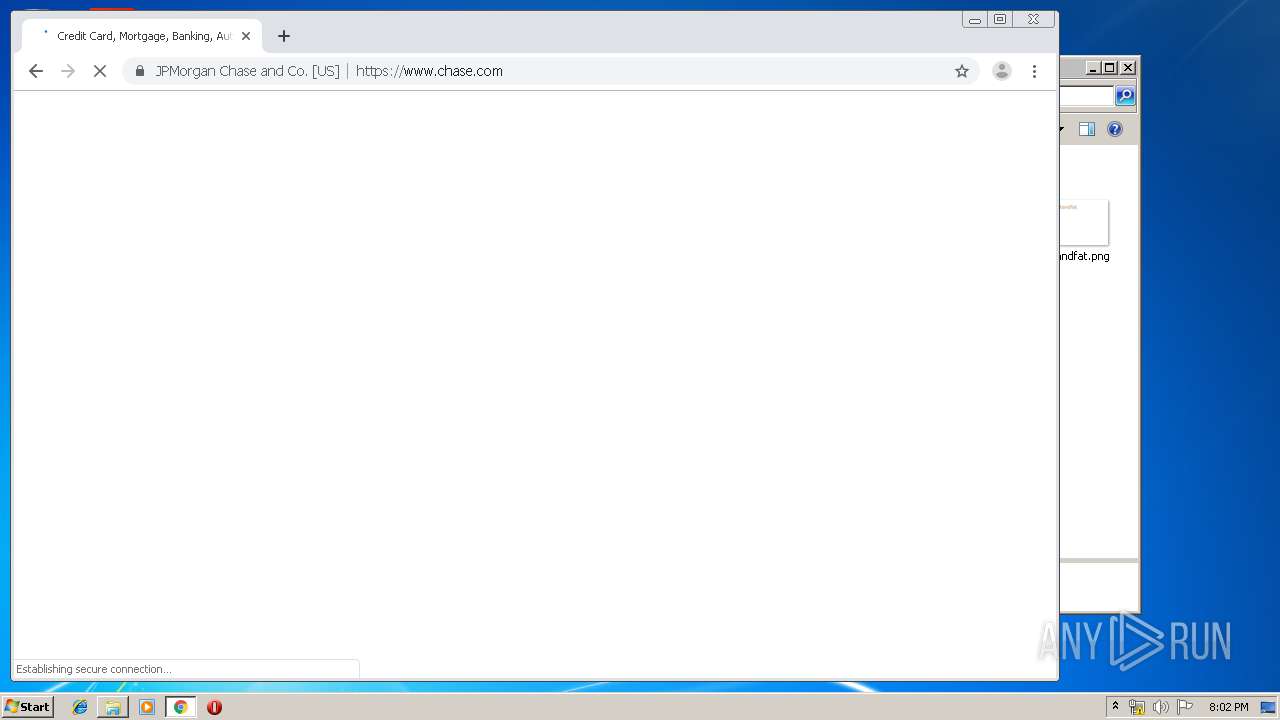
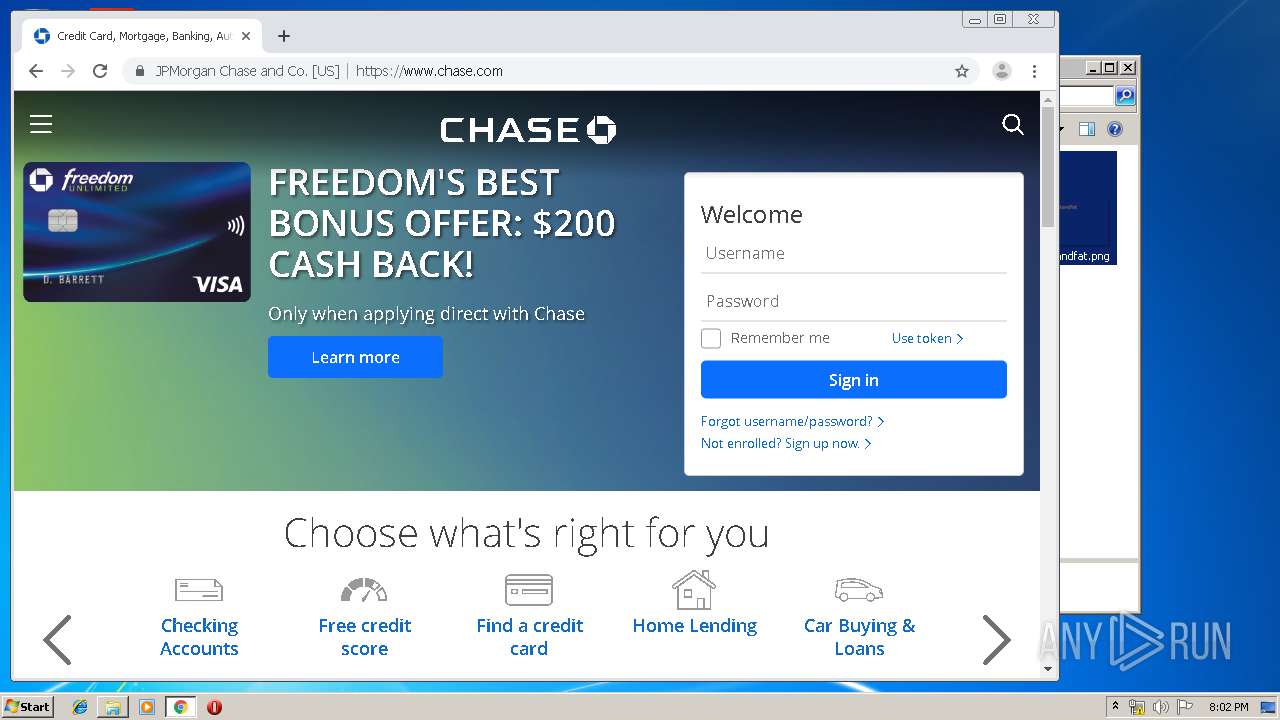
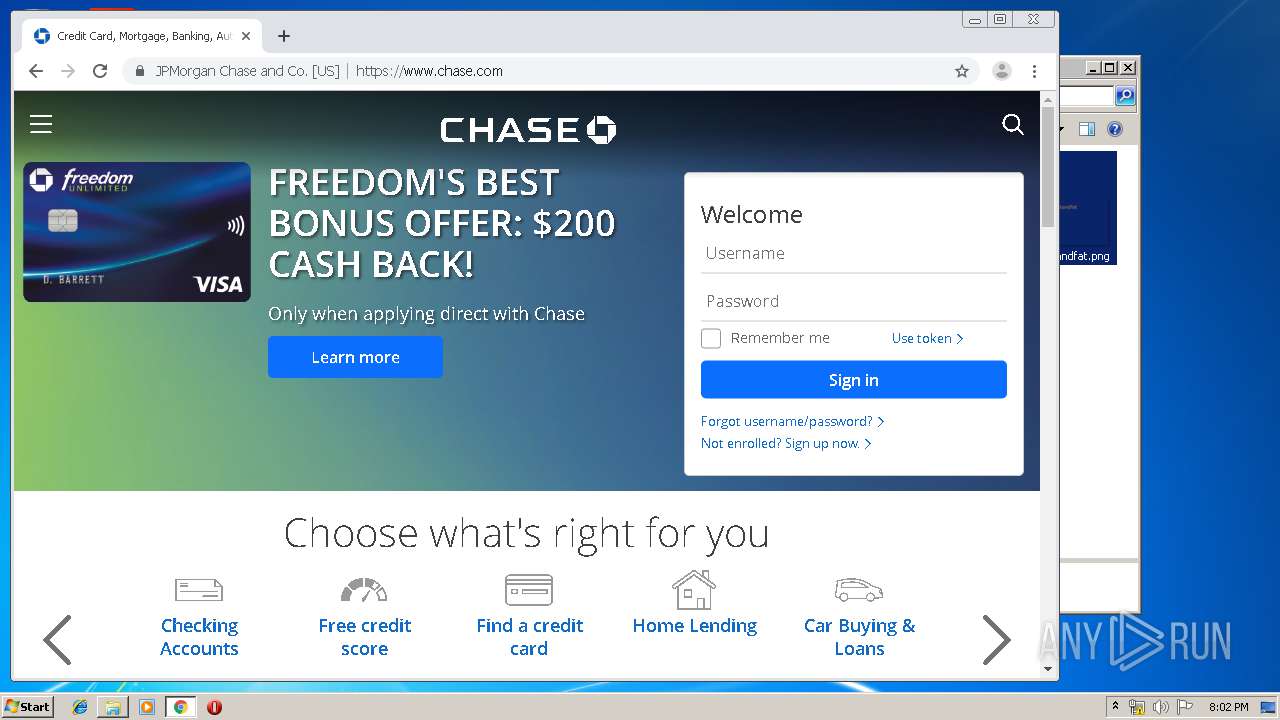
| Threats: | TrickBot is an advanced banking trojan that attackers can use to steal payment credentials from the victims. It can redirect the victim to a fake banking cabinet and retrieve credentials typed in on the webpage. |
| Analysis date: | October 14, 2019, 19:00:39 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 2753B4018A37B93D1670B89087160ABE |
| SHA1: | 5E10E00763394AB2B52F3C1F18F9DBD965948E4D |
| SHA256: | 753851E7FA1E0080333F93109D7DD4E18A32CA75047FB5A37DE2FE8C6D671F51 |
| SSDEEP: | 12288:qoJ16MBvYz8jIX3xrtmUgj7jdWxYZ3E89:XSucZZt1gj7ZC6 |
MALICIOUS
Loads the Task Scheduler COM API
- كلاحخألرنانطماصل.exe (PID: 520)
- Print_Document.exe (PID: 3832)
- print_document.exe (PID: 2588)
Known privilege escalation attack
- DllHost.exe (PID: 2720)
- DllHost.exe (PID: 460)
TRICKBOT was detected
- print_document.exe (PID: 2588)
SUSPICIOUS
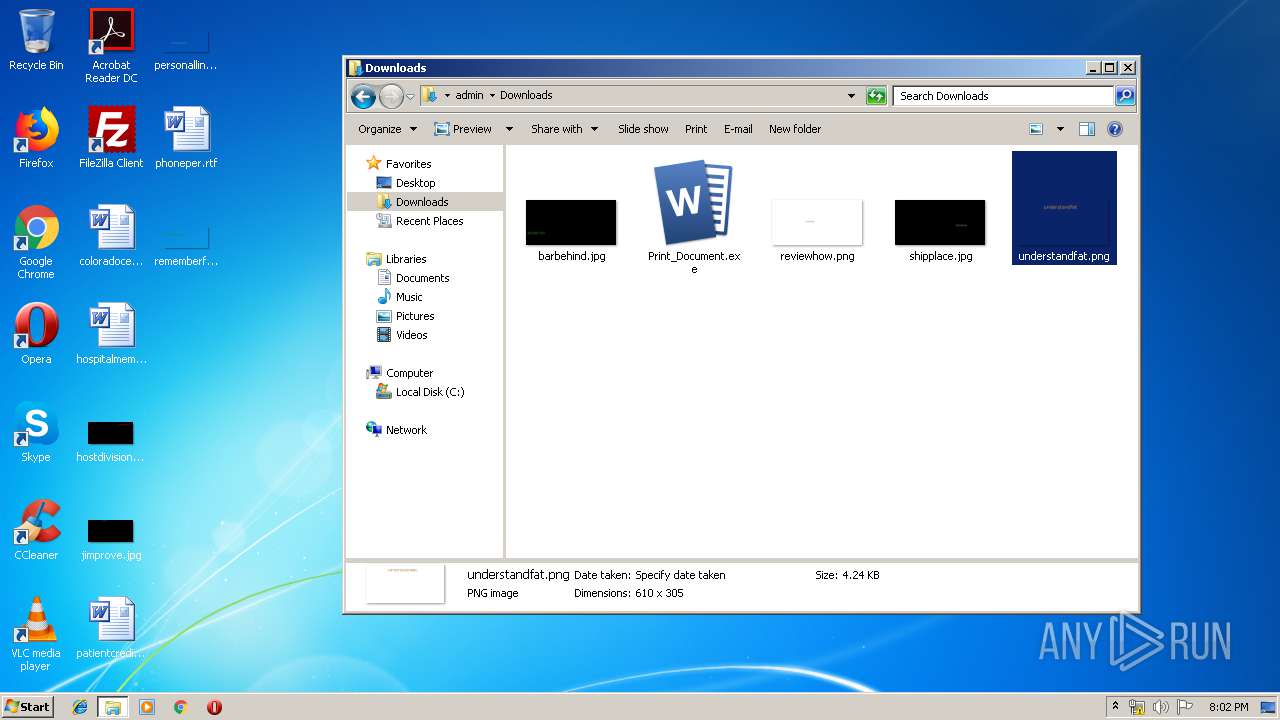
Creates files in the user directory
- كلاحخألرنانطماصل.exe (PID: 520)
- Print_Document.exe (PID: 3832)
- print_document.exe (PID: 2588)
Executable content was dropped or overwritten
- Print_Document.exe (PID: 2924)
- كلاحخألرنانطماصل.exe (PID: 520)
- Print_Document.exe (PID: 3832)
- print_document.exe (PID: 2588)
Creates files in the program directory
- Print_Document.exe (PID: 2924)
Executed via COM
- DllHost.exe (PID: 2720)
- DllHost.exe (PID: 460)
Executed via Task Scheduler
- rtipt_dqcuoept.exe (PID: 1884)
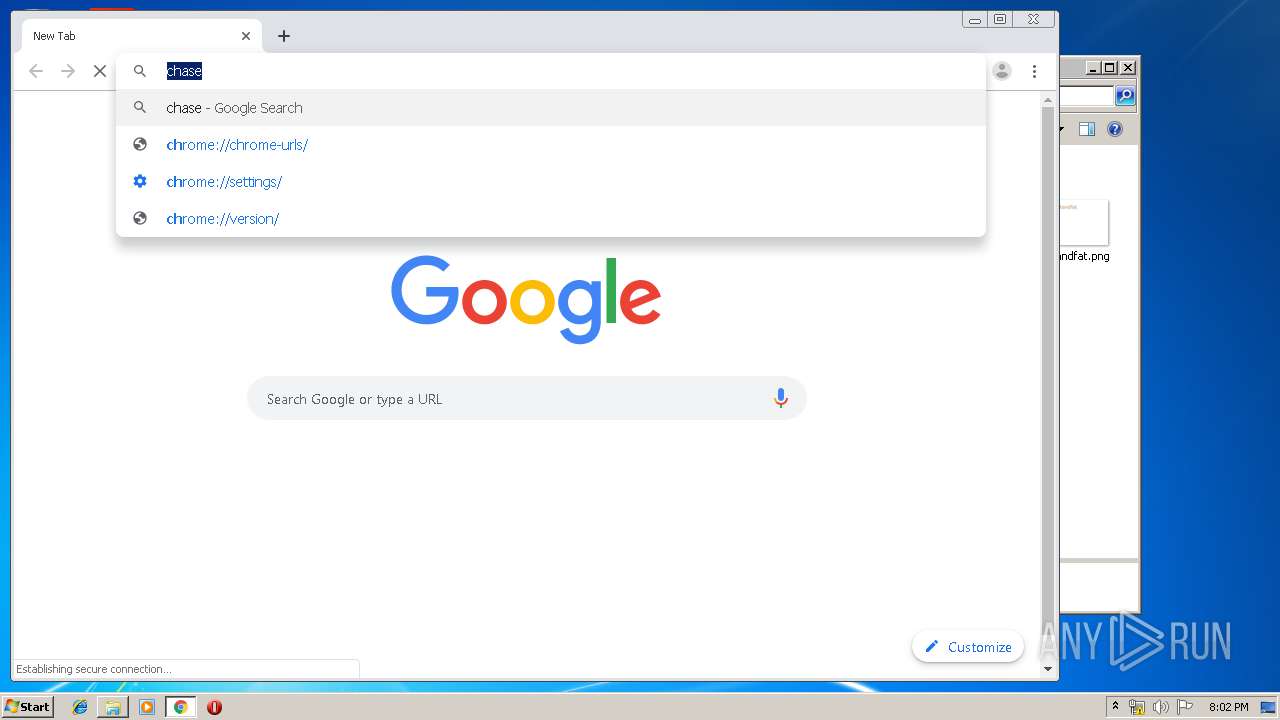
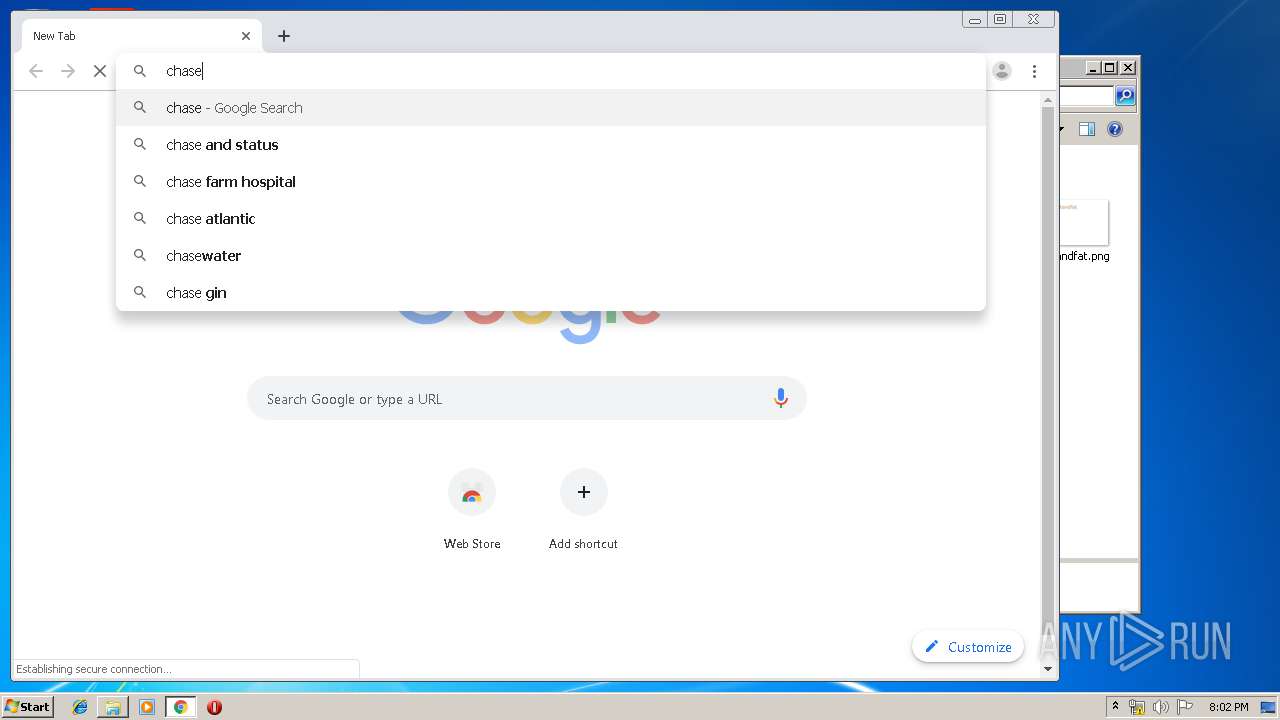
Modifies files in Chrome extension folder
- chrome.exe (PID: 2388)
INFO
Dropped object may contain Bitcoin addresses
- Print_Document.exe (PID: 2924)
- كلاحخألرنانطماصل.exe (PID: 520)
- Print_Document.exe (PID: 3832)
- print_document.exe (PID: 2588)
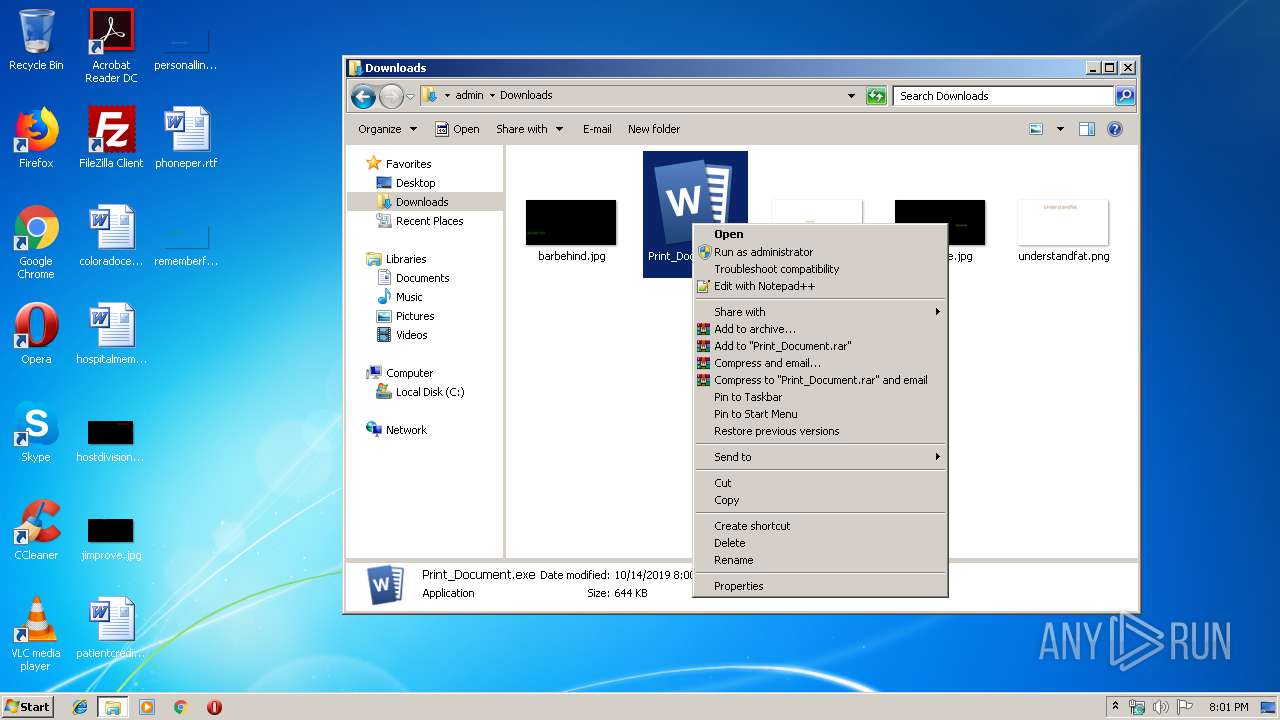
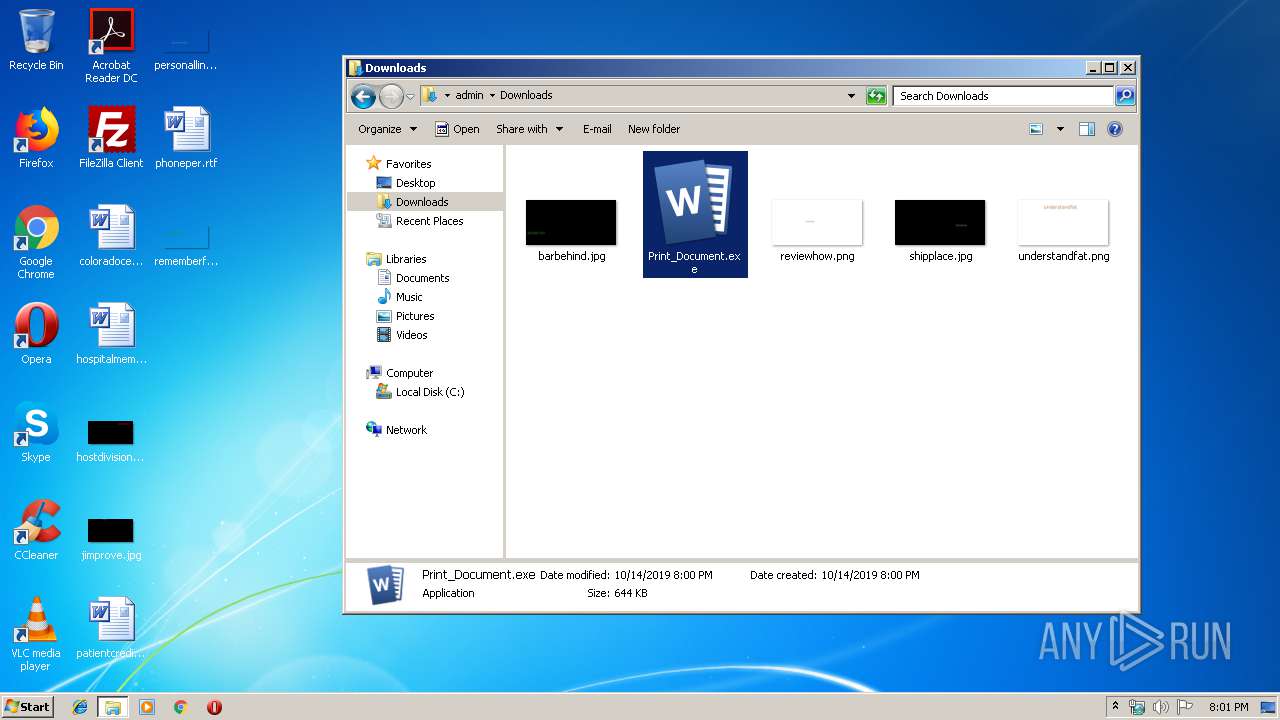
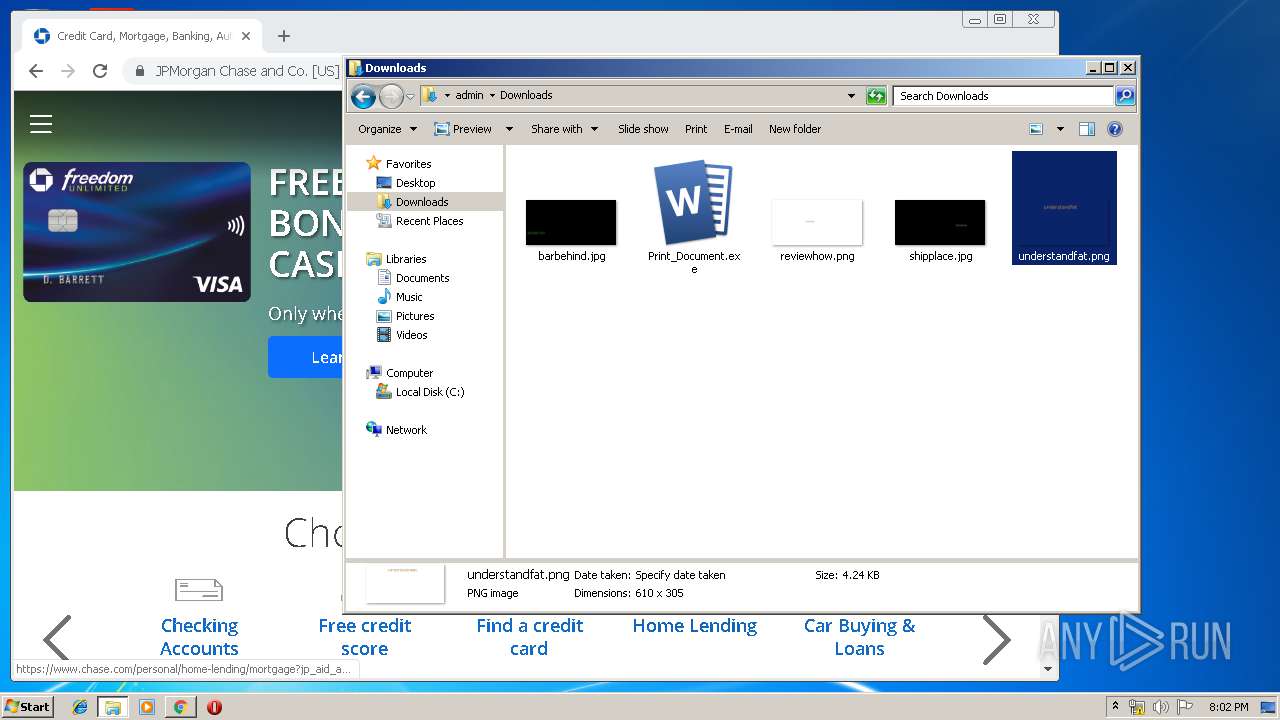
Manual execution by user
- explorer.exe (PID: 3908)
- Print_Document.exe (PID: 3448)
- Print_Document.exe (PID: 3832)
- chrome.exe (PID: 2388)
Reads the hosts file
- chrome.exe (PID: 2388)
- chrome.exe (PID: 976)
Modifies the open verb of a shell class
- chrome.exe (PID: 2388)
Application launched itself
- chrome.exe (PID: 2388)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (67.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.2) |
| .exe | | | Win32 Executable (generic) (9.7) |
| .exe | | | Generic Win/DOS Executable (4.3) |
| .exe | | | DOS Executable Generic (4.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:10:11 11:36:11+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 28672 |
| InitializedDataSize: | 454656 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x7b76 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.1 |
| ProductVersionNumber: | 1.0.0.1 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | German |
| CharacterSet: | Unicode |
| CompanyName: | - |
| FileDescription: | MFC-Anwendung Tranquilizer |
| FileVersion: | 1, 0, 0, 1 |
| InternalName: | Tranquilizer |
| LegalCopyright: | Copyright (C) 2001 |
| LegalTrademarks: | - |
| OriginalFileName: | Tranquilizer.EXE |
| ProductName: | Anwendung Tranquilizer |
| ProductVersion: | 1, 0, 0, 1 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 11-Oct-2019 09:36:11 |
| Detected languages: |
|
| CompanyName: | - |
| FileDescription: | MFC-Anwendung Tranquilizer |
| FileVersion: | 1, 0, 0, 1 |
| InternalName: | Tranquilizer |
| LegalCopyright: | Copyright (C) 2001 |
| LegalTrademarks: | - |
| OriginalFilename: | Tranquilizer.EXE |
| ProductName: | Anwendung Tranquilizer |
| ProductVersion: | 1, 0, 0, 1 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000E8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 4 |
| Time date stamp: | 11-Oct-2019 09:36:11 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00006EE0 | 0x00007000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.72757 |
.rdata | 0x00008000 | 0x00001967 | 0x00002000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.5471 |
.data | 0x0000A000 | 0x0003AA34 | 0x0003B000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 6.02277 |
.rsrc | 0x00045000 | 0x000313CC | 0x00032000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.23394 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.34989 | 796 | UNKNOWN | German - Germany | RT_VERSION |
2 | 4.18928 | 1384 | UNKNOWN | German - Germany | RT_ICON |
3 | 4.06069 | 2216 | UNKNOWN | German - Germany | RT_ICON |
4 | 7.94635 | 24638 | UNKNOWN | UNKNOWN | RT_ICON |
5 | 4.52566 | 67624 | UNKNOWN | UNKNOWN | RT_ICON |
6 | 4.76405 | 38056 | UNKNOWN | UNKNOWN | RT_ICON |
7 | 4.76941 | 21640 | UNKNOWN | UNKNOWN | RT_ICON |
8 | 4.75478 | 16936 | UNKNOWN | UNKNOWN | RT_ICON |
9 | 4.90536 | 9640 | UNKNOWN | UNKNOWN | RT_ICON |
10 | 5.04259 | 4264 | UNKNOWN | UNKNOWN | RT_ICON |
Imports
ADVAPI32.dll |
GDI32.dll |
KERNEL32.dll |
MFC42.DLL |
MSVCP60.dll |
MSVCRT.dll |
SHELL32.dll |
USER32.dll |
WINMM.dll |
Exports
Title | Ordinal | Address |
|---|---|---|
Run | 1 | 0x000022D4 |
Total processes
87
Monitored processes
43
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 284 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=976,9015798925932272915,3622851006746826117,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=12725528257818729859 --mojo-platform-channel-handle=3928 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 388 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=976,9015798925932272915,3622851006746826117,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=15241098912814091783 --mojo-platform-channel-handle=4584 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 408 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=976,9015798925932272915,3622851006746826117,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=1649349270670462887 --mojo-platform-channel-handle=3708 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 460 | C:\Windows\system32\DllHost.exe /Processid:{3E5FC7F9-9A51-4367-9063-A120244FBEC7} | C:\Windows\system32\DllHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 520 | "C:\ProgramData\كلاحخألرنانطماصل.exe" | C:\ProgramData\كلاحخألرنانطماصل.exe | DllHost.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: MFC-Anwendung Tranquilizer Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 564 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=976,9015798925932272915,3622851006746826117,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=668552635463768103 --mojo-platform-channel-handle=3508 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 656 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=976,9015798925932272915,3622851006746826117,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=10689527361030041550 --mojo-platform-channel-handle=3328 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 976 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=976,9015798925932272915,3622851006746826117,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=18114556766654991084 --mojo-platform-channel-handle=1532 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1160 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=75.0.3770.100 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x6fc1a9d0,0x6fc1a9e0,0x6fc1a9ec | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1584 | "C:\ProgramData\كلاحخألرنانطماصل.exe" | C:\ProgramData\كلاحخألرنانطماصل.exe | — | Print_Document.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: MFC-Anwendung Tranquilizer Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
Total events
822
Read events
695
Write events
119
Delete events
8
Modification events
| (PID) Process: | (2924) Print_Document.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2924) Print_Document.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2720) DllHost.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2720) DllHost.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (460) DllHost.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (460) DllHost.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3884) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2388-13215553325902570 |
Value: 259 | |||
| (PID) Process: | (2388) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2388) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2388) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
Executable files
4
Suspicious files
78
Text files
288
Unknown types
23
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2388 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\a93b7510-aa9a-4e04-b894-534e8bd5a38d.tmp | — | |
MD5:— | SHA256:— | |||
| 2388 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2388 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2388 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000020.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2388 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old~RF3ab991.TMP | text | |
MD5:— | SHA256:— | |||
| 2388 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF3ab934.TMP | text | |
MD5:— | SHA256:— | |||
| 2388 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\AvailabilityDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2588 | print_document.exe | C:\Users\admin\AppData\Roaming\netRest\revocations.txt | text | |
MD5:— | SHA256:— | |||
| 2388 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF3ab934.TMP | text | |
MD5:— | SHA256:— | |||
| 2388 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
12
TCP/UDP connections
71
DNS requests
38
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
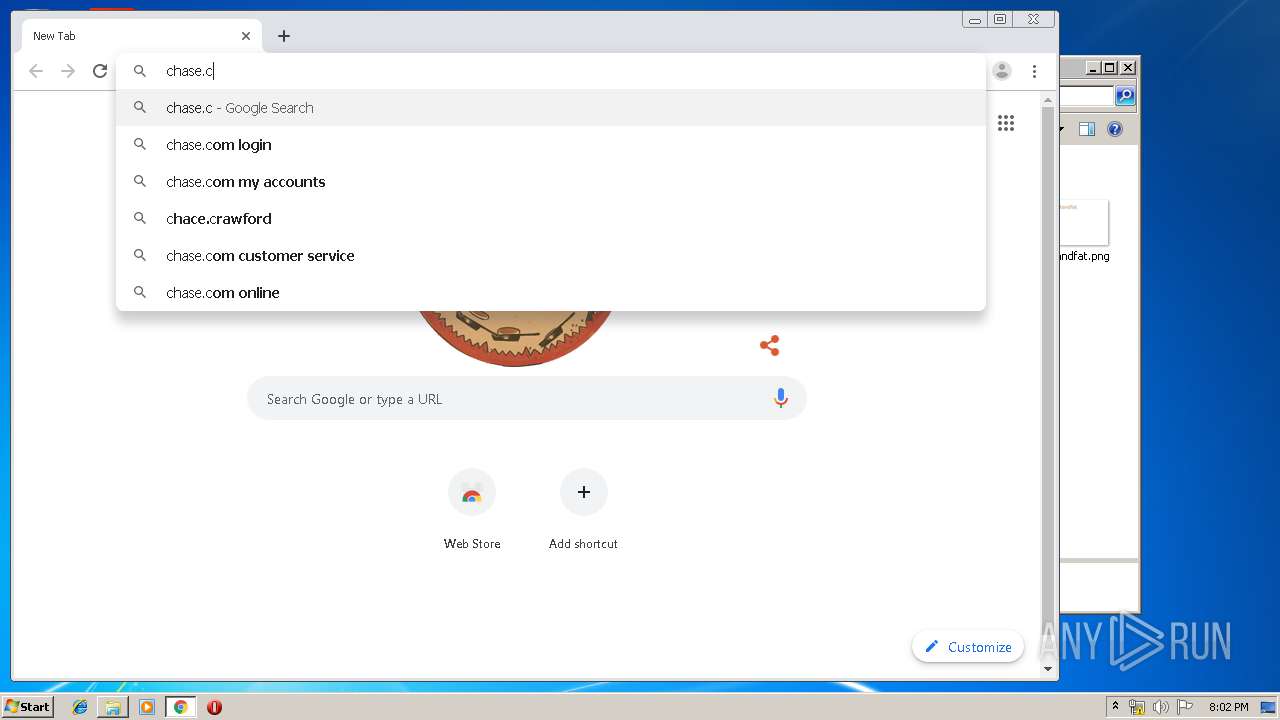
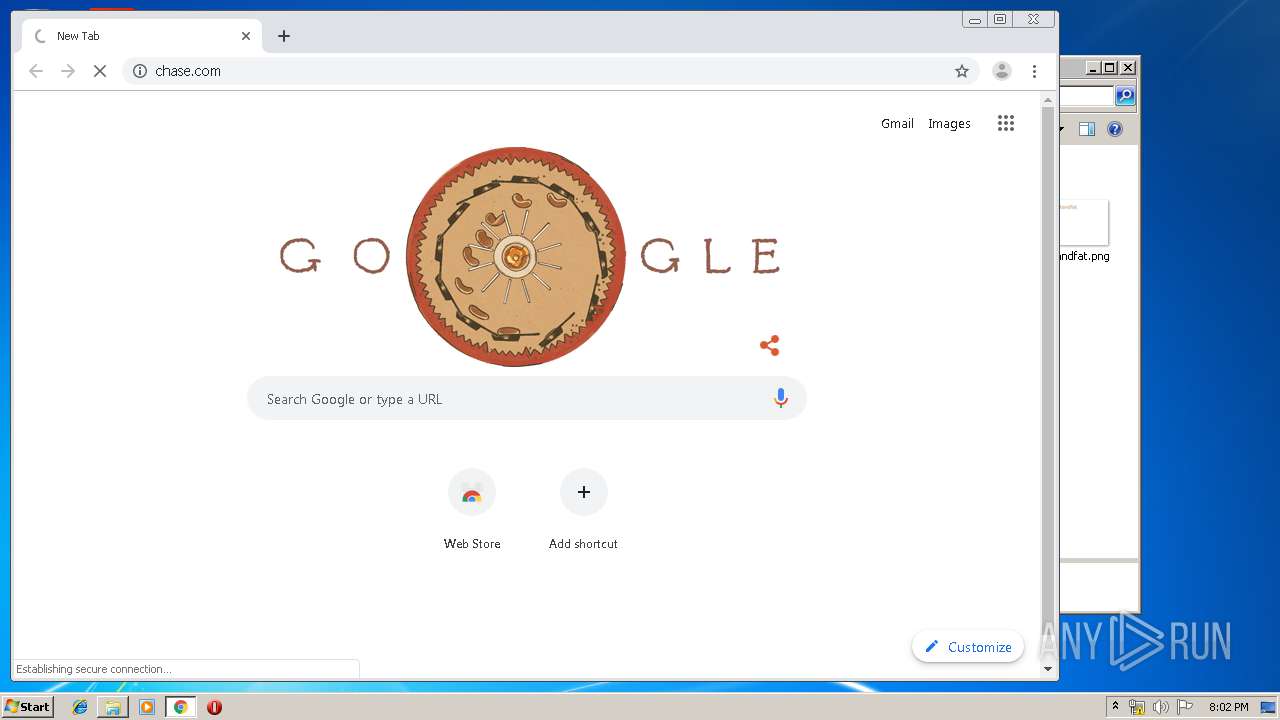
976 | chrome.exe | GET | 301 | 159.53.44.60:80 | http://chase.com/ | US | — | — | suspicious |
976 | chrome.exe | GET | 302 | 172.217.22.110:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 508 b | whitelisted |
976 | chrome.exe | GET | 302 | 172.217.22.110:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 513 b | whitelisted |
976 | chrome.exe | GET | 200 | 23.67.130.203:80 | http://ocsp.entrust.net/ME0wSzBJMEcwRTAJBgUrDgMCGgUABBTLXNCzDvBhHecWjg70iJhBW0InywQUanImetAe733nO2lR1GyNn5ASZqsCDGGh59IAAAAAUdNmpg%3D%3D | NL | der | 1.95 Kb | whitelisted |
976 | chrome.exe | GET | 200 | 23.67.130.203:80 | http://ocsp.entrust.net/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBQnuEQcScL%2FkljKed%2BRzpzFYOq9kwQUw%2FfQtSowra8NkSFwOVTdvIlwxzoCEQCJobWPMAgjhwAAAABUz5Ro | NL | der | 1.90 Kb | whitelisted |
976 | chrome.exe | GET | 200 | 23.67.130.203:80 | http://ocsp.entrust.net/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBQnuEQcScL%2FkljKed%2BRzpzFYOq9kwQUw%2FfQtSowra8NkSFwOVTdvIlwxzoCEQD9e1BR8AutbgAAAABUz5cI | NL | der | 1.90 Kb | whitelisted |
976 | chrome.exe | GET | 200 | 23.67.130.203:80 | http://ocsp.entrust.net/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQnuEQcScL%2FkljKed%2BRzpzFYOq9kwQUw%2FfQtSowra8NkSFwOVTdvIlwxzoCEG67fF3Yi%2FOjAAAAAFTPtuM%3D | NL | der | 1.90 Kb | whitelisted |
976 | chrome.exe | GET | 200 | 23.67.130.203:80 | http://ocsp.entrust.net/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQnuEQcScL%2FkljKed%2BRzpzFYOq9kwQUw%2FfQtSowra8NkSFwOVTdvIlwxzoCEBDrW8qbyLR3AAAAAFTP5hg%3D | NL | der | 1.90 Kb | whitelisted |
976 | chrome.exe | GET | 200 | 23.67.130.203:80 | http://ocsp.entrust.net/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQnuEQcScL%2FkljKed%2BRzpzFYOq9kwQUw%2FfQtSowra8NkSFwOVTdvIlwxzoCEEhX3tOSiXkaAAAAAFTPzbw%3D | NL | der | 1.90 Kb | whitelisted |
976 | chrome.exe | GET | 200 | 173.194.183.103:80 | http://r2---sn-aigl6nek.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx?cms_redirect=yes&mip=185.92.25.20&mm=28&mn=sn-aigl6nek&ms=nvh&mt=1571079621&mv=m&mvi=1&pl=24&shardbypass=yes | US | crx | 293 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2588 | print_document.exe | 109.234.34.135:443 | — | Webzilla B.V. | RU | suspicious |
976 | chrome.exe | 172.217.22.77:443 | accounts.google.com | Google Inc. | US | whitelisted |
976 | chrome.exe | 172.217.18.10:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
976 | chrome.exe | 216.58.207.35:443 | www.google.com.ua | Google Inc. | US | whitelisted |
976 | chrome.exe | 172.217.18.99:443 | www.gstatic.com | Google Inc. | US | whitelisted |
976 | chrome.exe | 172.217.23.163:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
976 | chrome.exe | 172.217.18.14:443 | apis.google.com | Google Inc. | US | whitelisted |
976 | chrome.exe | 172.217.16.142:443 | ogs.google.com | Google Inc. | US | whitelisted |
976 | chrome.exe | 216.58.205.228:443 | www.google.com | Google Inc. | US | whitelisted |
976 | chrome.exe | 172.217.18.3:443 | www.google.co.uk | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com.ua |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
ogs.google.com |
| whitelisted |
www.google.com |
| malicious |
www.google.co.uk |
| whitelisted |