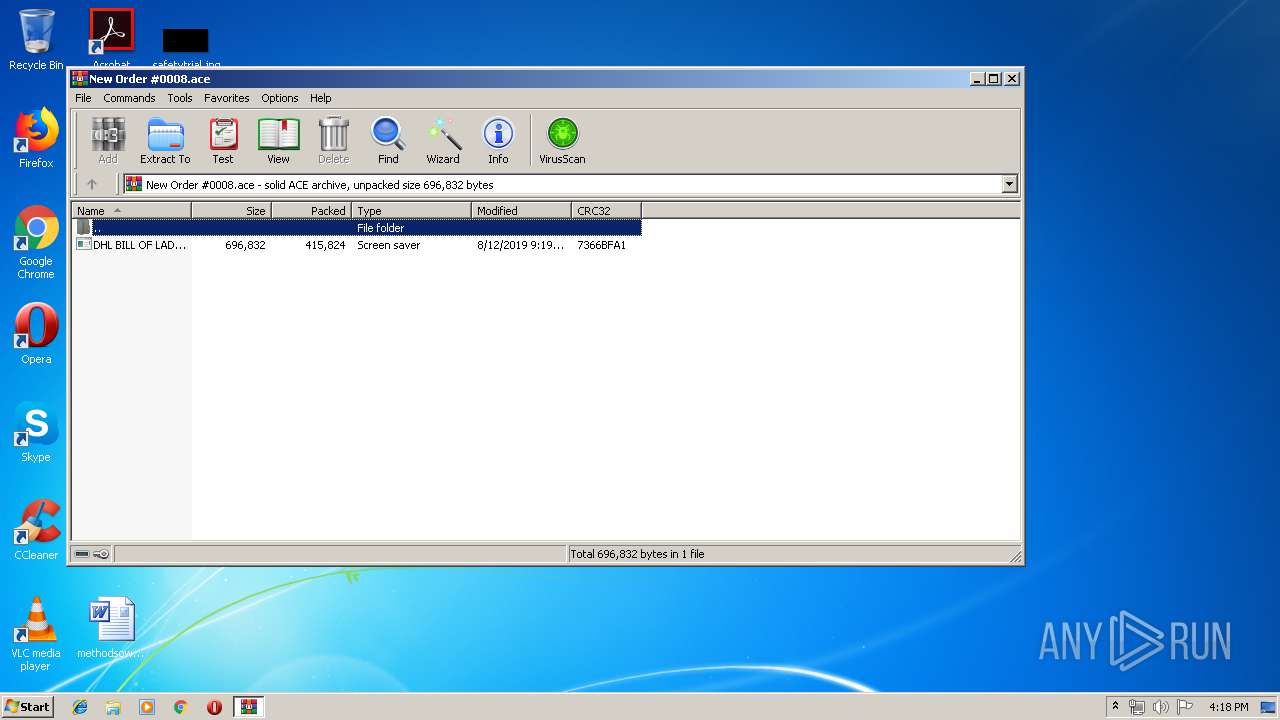
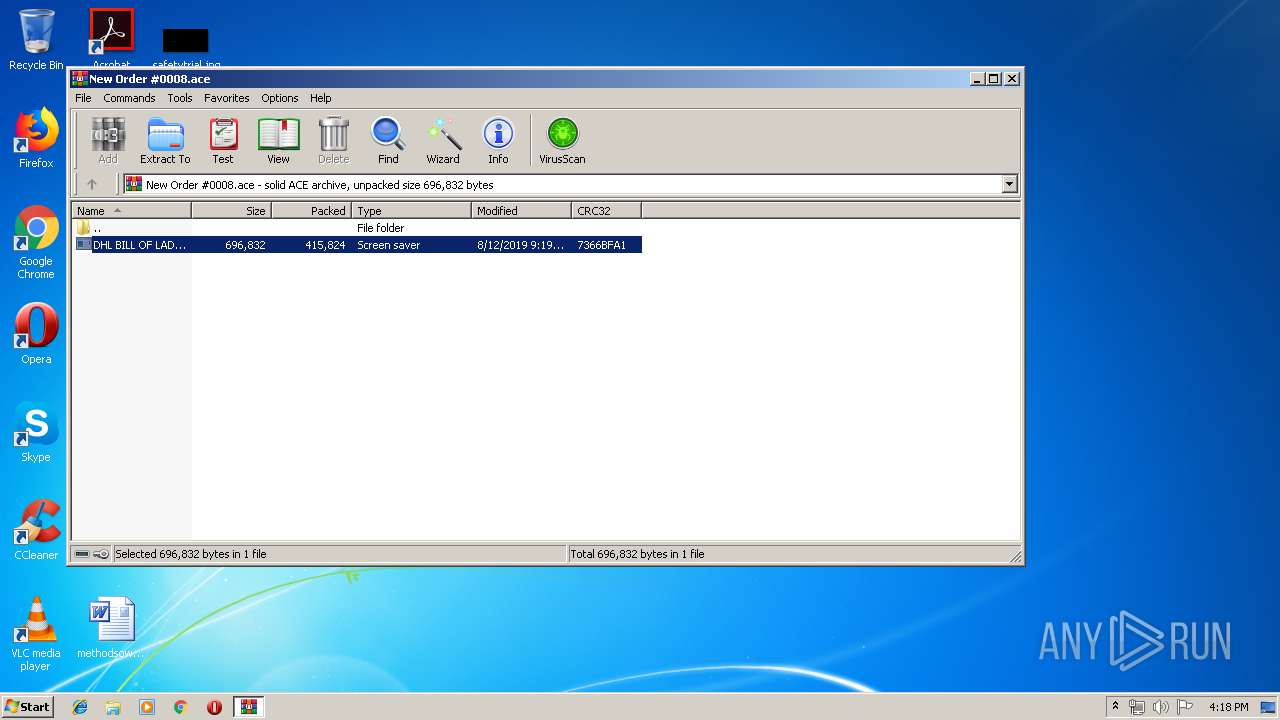
| File name: | New Order #0008.ace |
| Full analysis: | https://app.any.run/tasks/01fd5249-5716-4821-969e-68b5fd5891b0 |
| Verdict: | Malicious activity |
| Threats: | Agent Tesla is spyware that collects information about the actions of its victims by recording keystrokes and user interactions. It is falsely marketed as a legitimate software on the dedicated website where this malware is sold. |
| Analysis date: | August 13, 2019, 15:18:09 |
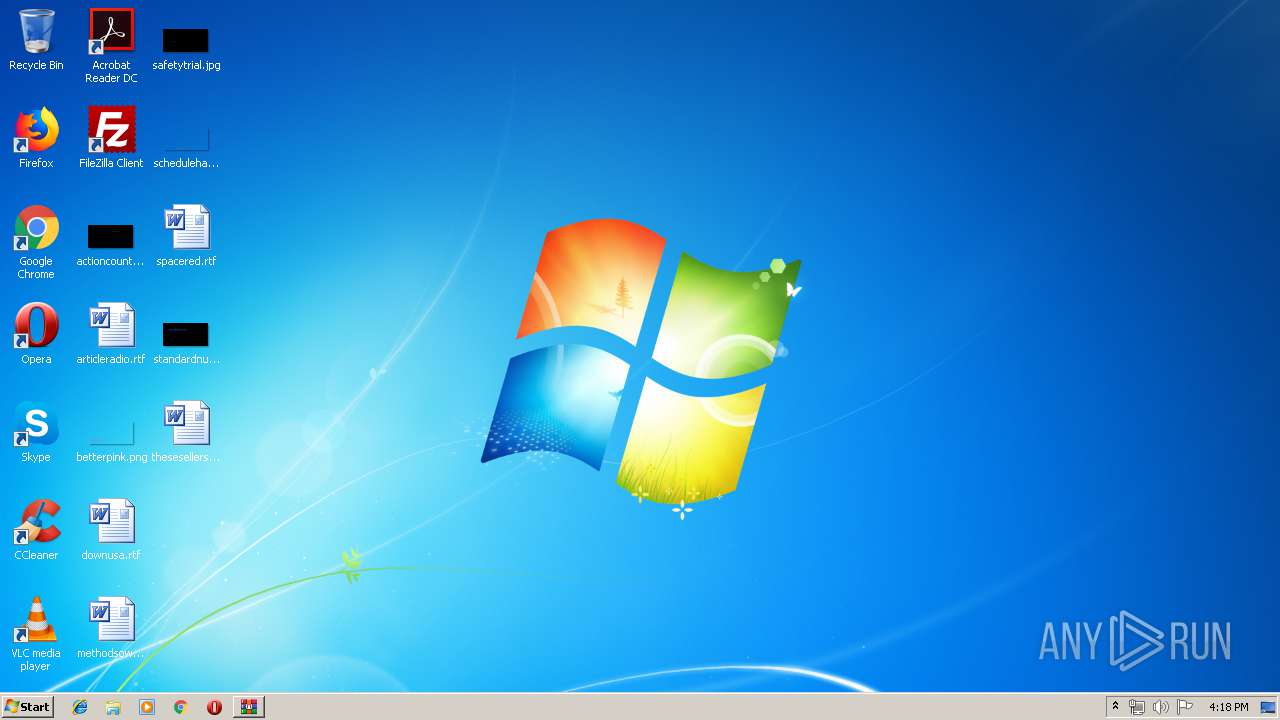
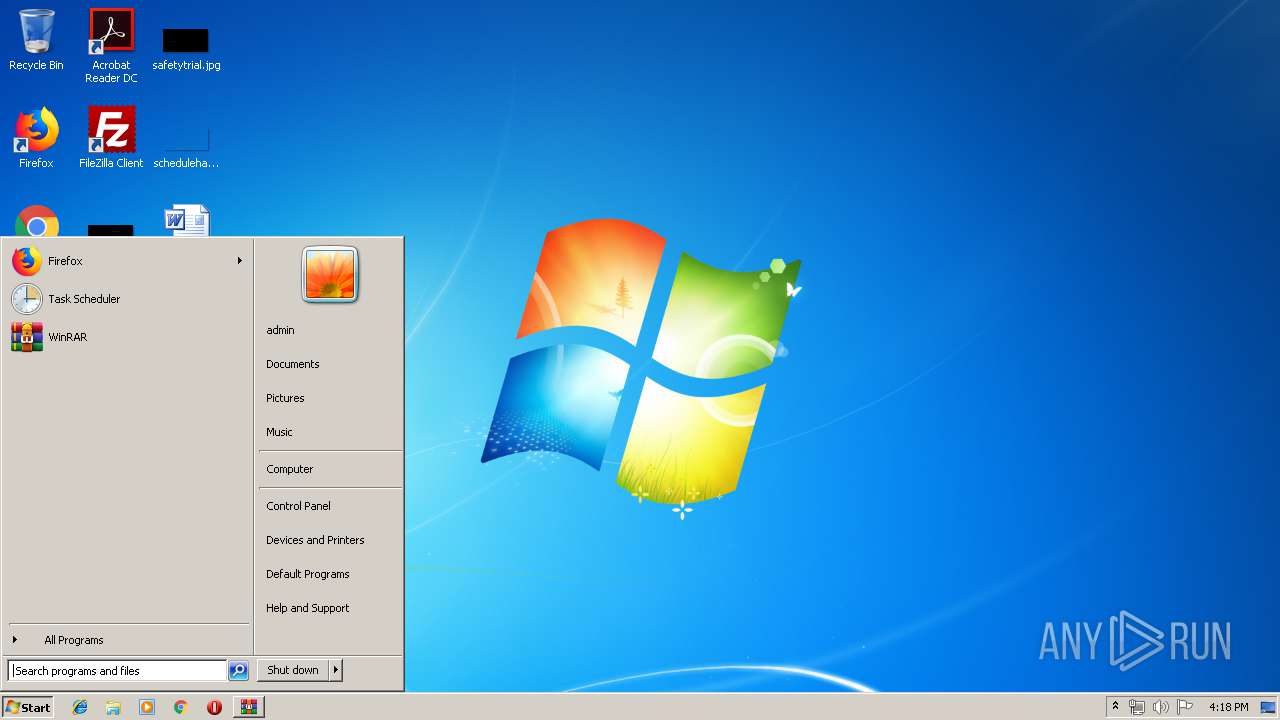
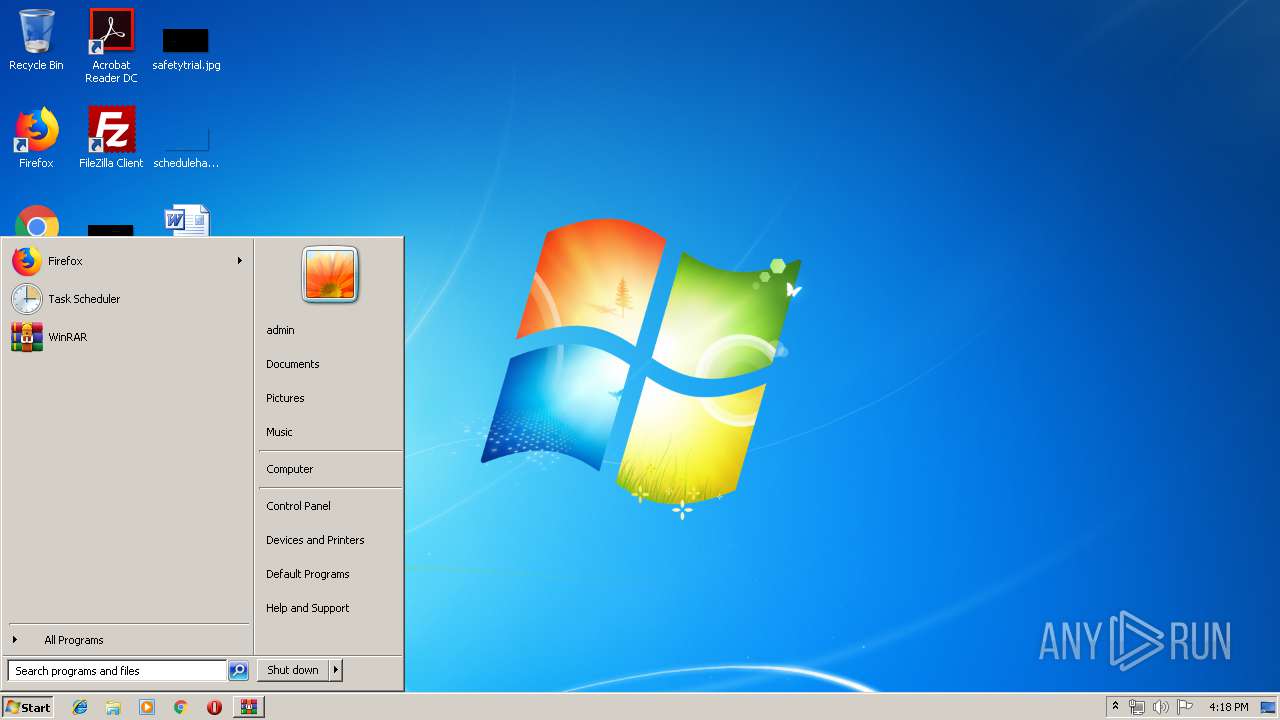
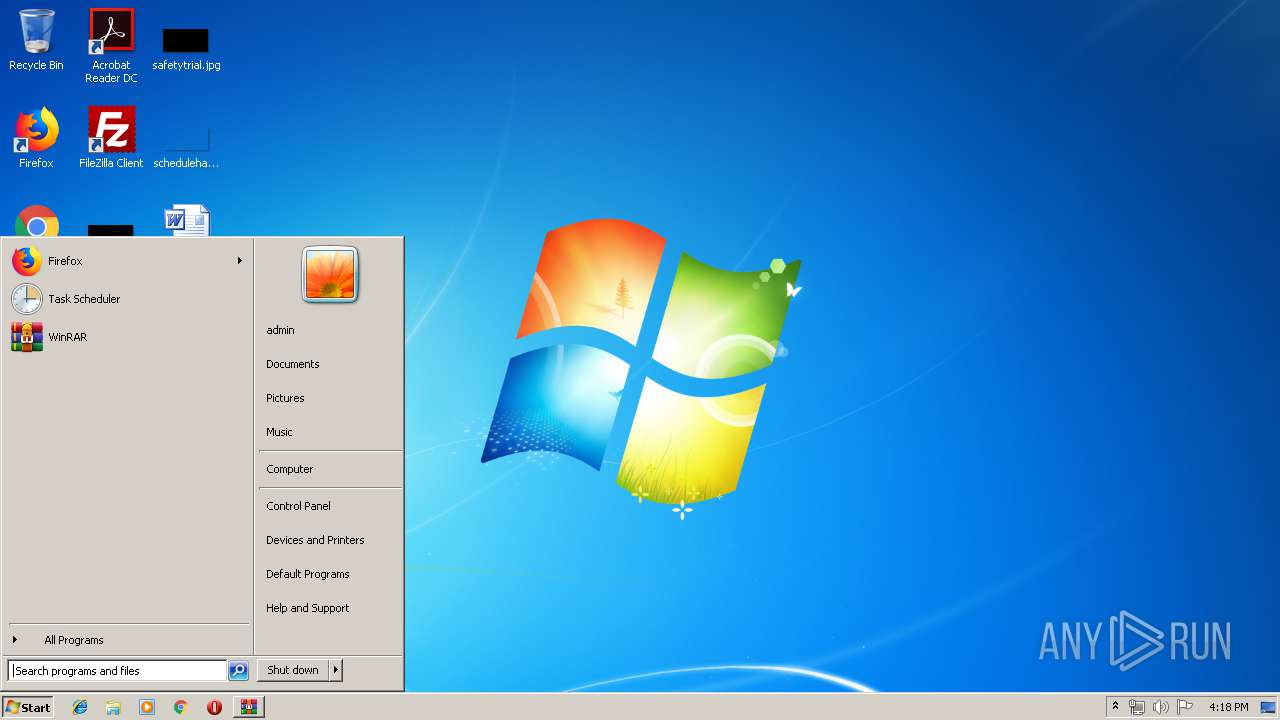
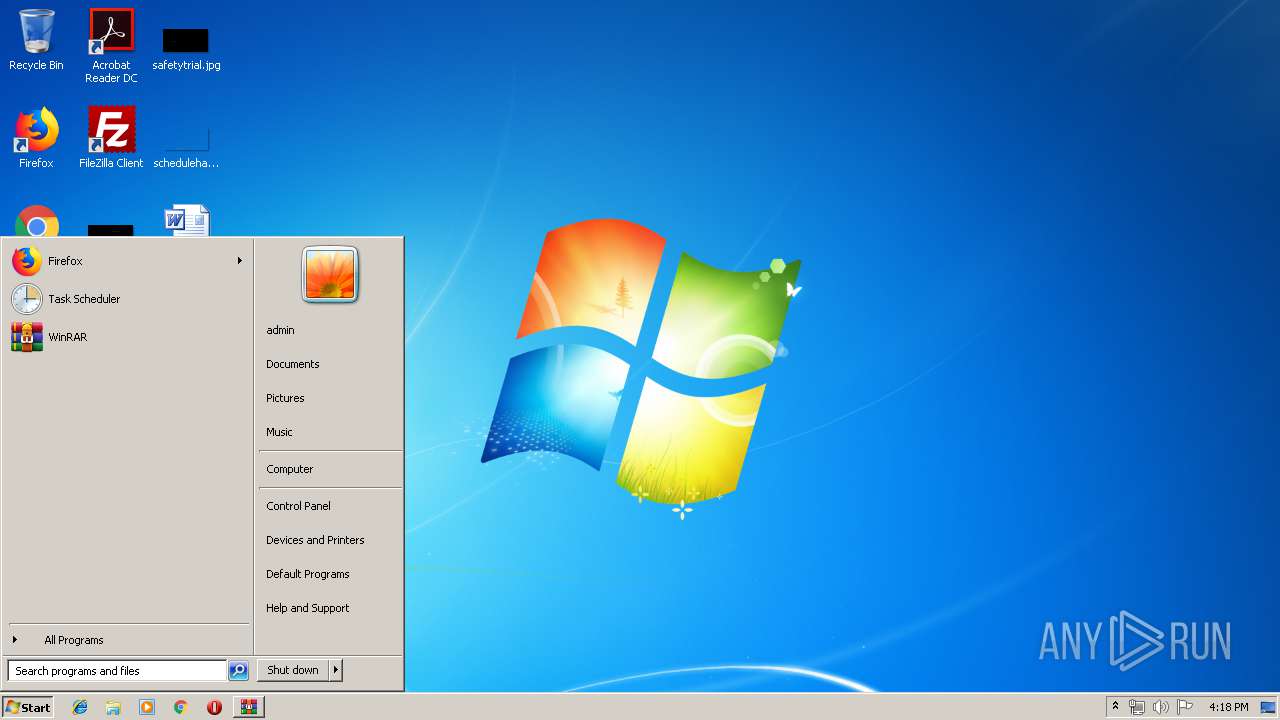
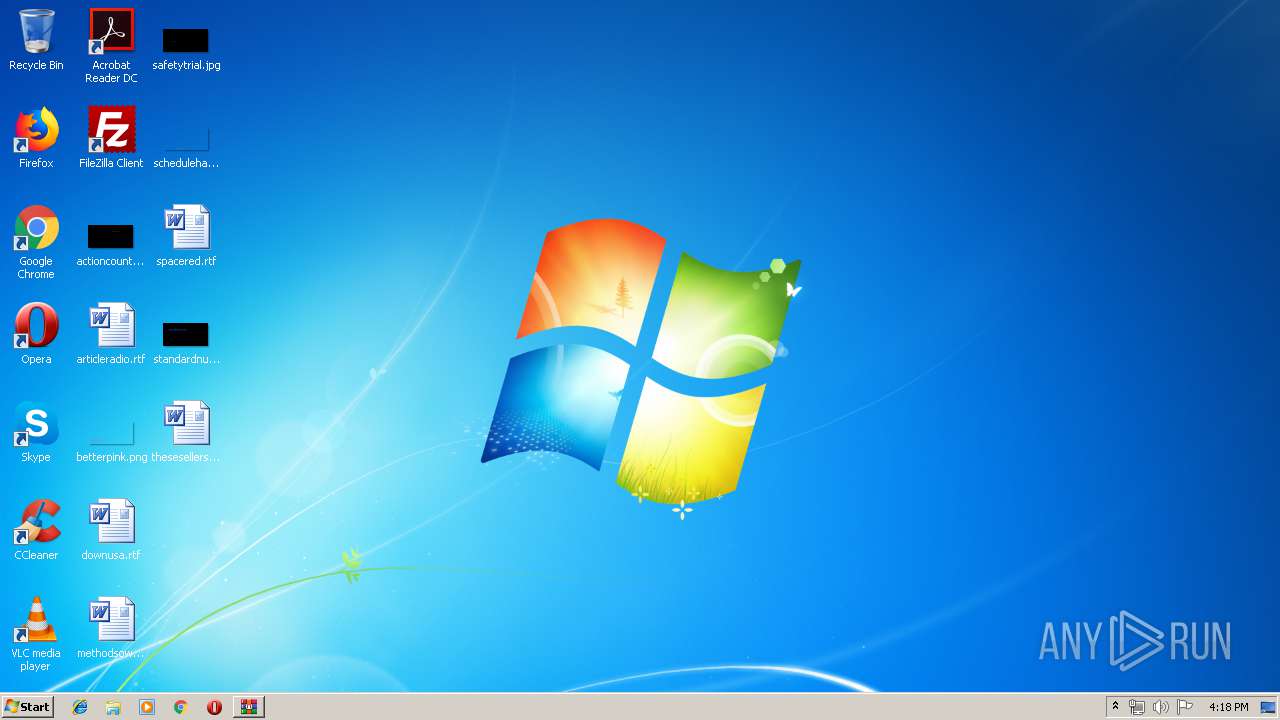
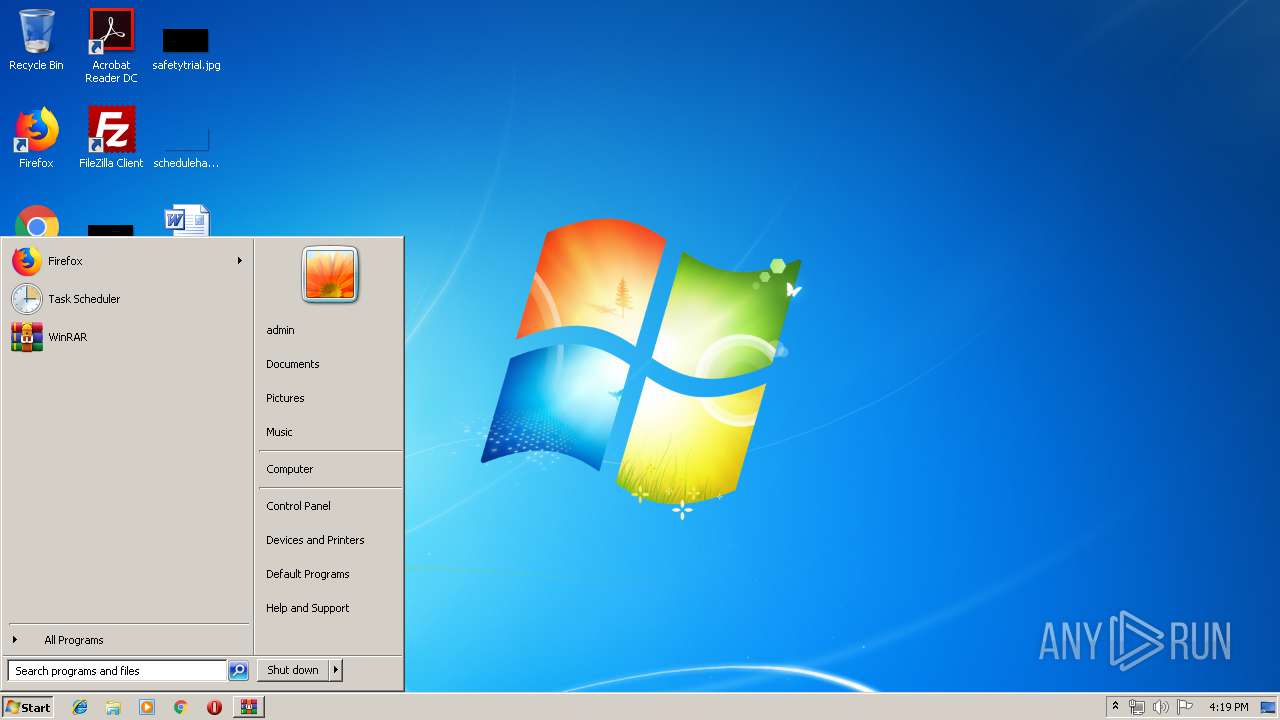
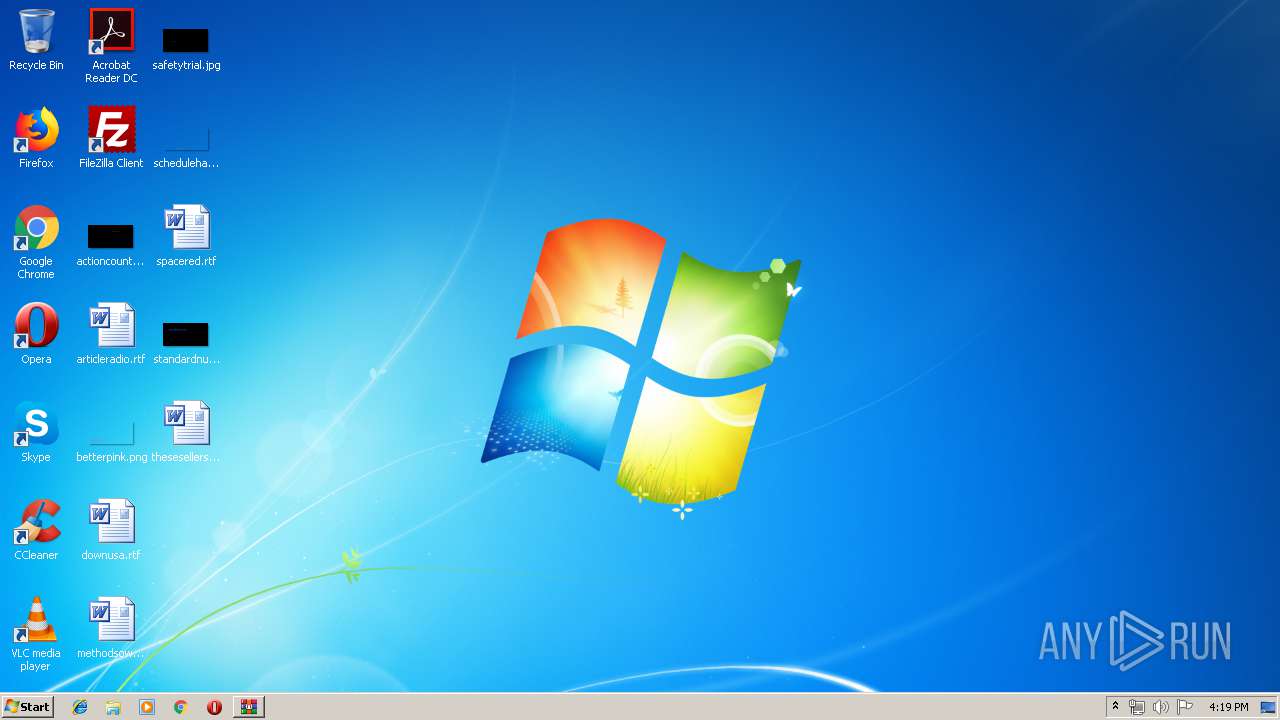
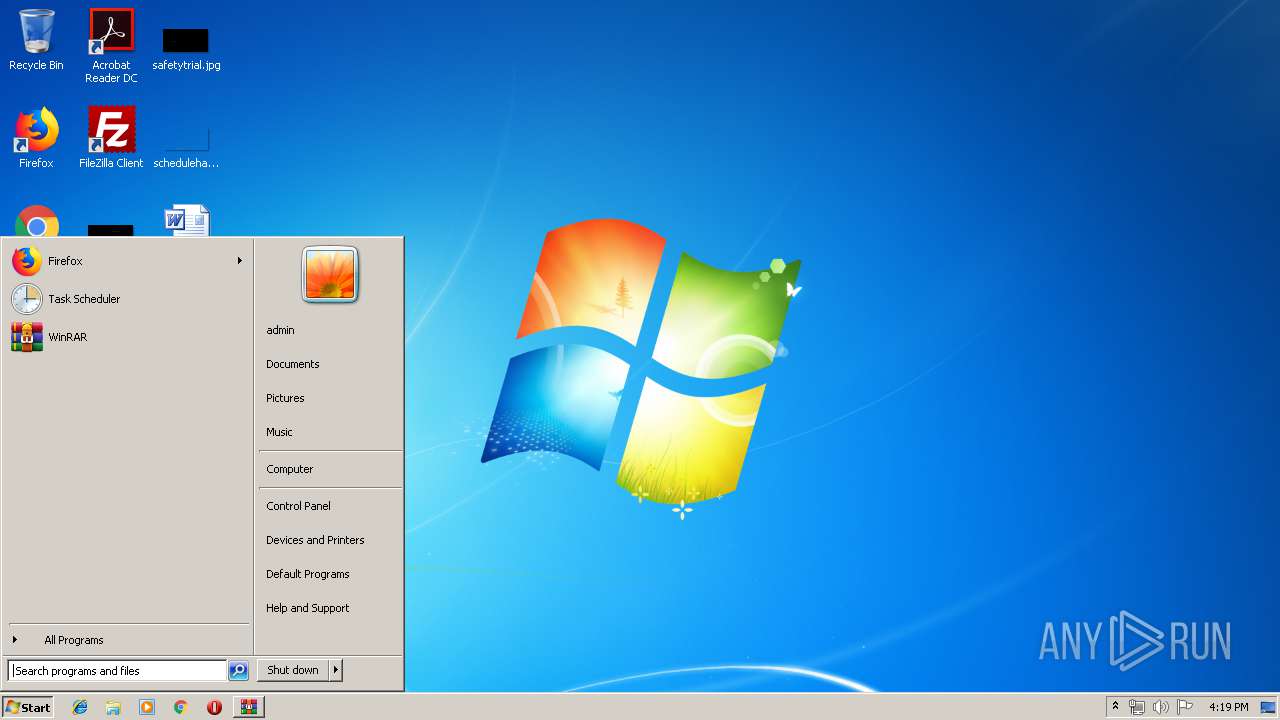
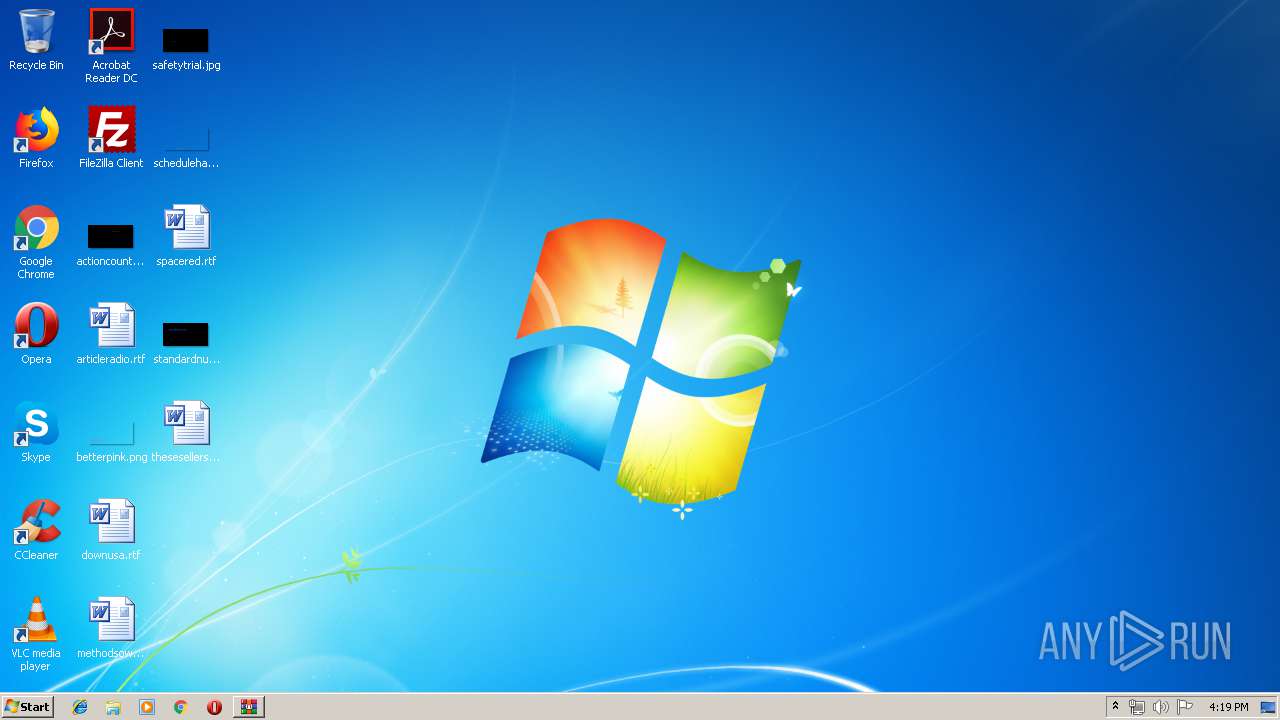
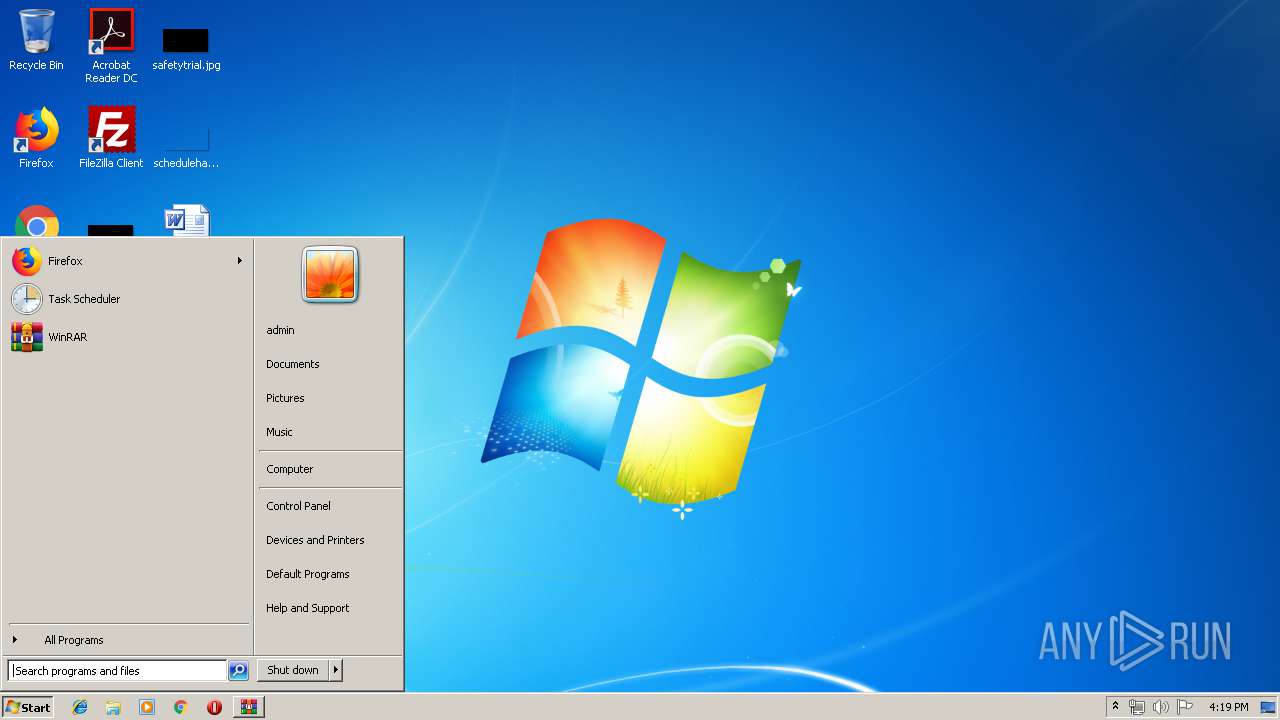
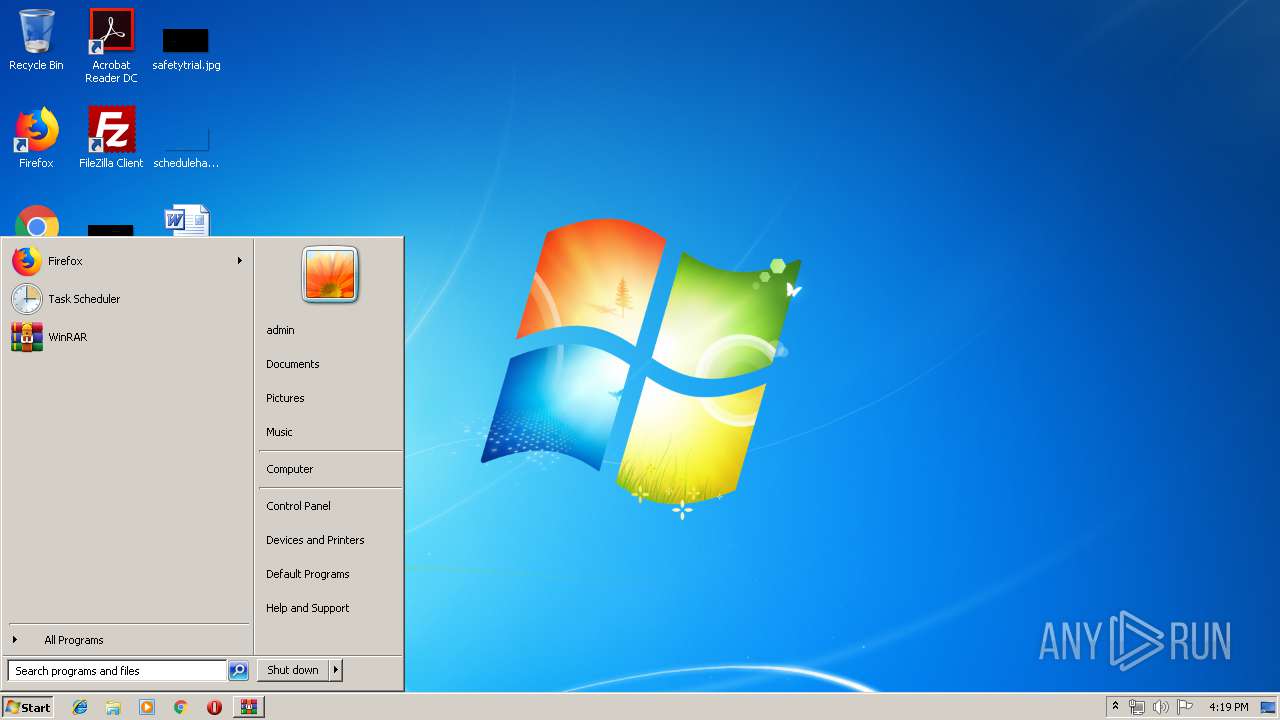
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/octet-stream |
| File info: | ACE archive data version 20, from Win/32, version 20 to extract, contains AV-String (unregistered), solid |
| MD5: | 6207CF32EBB1F0730F3DC1FFD7547748 |
| SHA1: | 75074312D7A4668C31B918E5F0509E3CF62B20EC |
| SHA256: | 751FF30F7CEFE00FCA4839E30B9252F37D0B9676DC9BDFC8EE88E2A2E85B0902 |
| SSDEEP: | 12288:DVfyZkcGhwOerwr9d9p23N2+/CXkvN7dn62WLcXZ:hu086pM/oaJ1DXZ |
MALICIOUS
Application was dropped or rewritten from another process
- DHL BILL OF LADING INVOICE82003184.scr (PID: 2780)
- DHL BILL OF LADING INVOICE82003184.scr (PID: 3164)
AGENTTESLA was detected
- DHL BILL OF LADING INVOICE82003184.scr (PID: 3164)
Actions looks like stealing of personal data
- DHL BILL OF LADING INVOICE82003184.scr (PID: 3164)
SUSPICIOUS
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3268)
Application launched itself
- DHL BILL OF LADING INVOICE82003184.scr (PID: 2780)
Starts application with an unusual extension
- DHL BILL OF LADING INVOICE82003184.scr (PID: 2780)
- WinRAR.exe (PID: 3268)
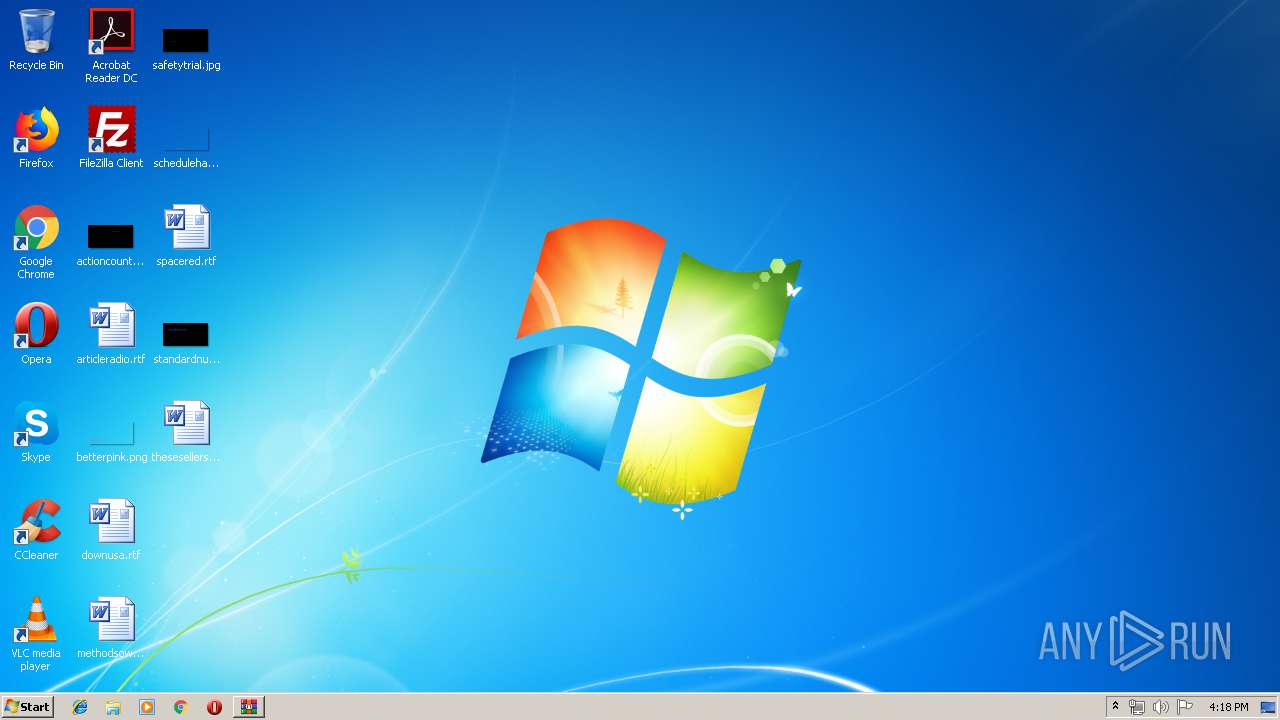
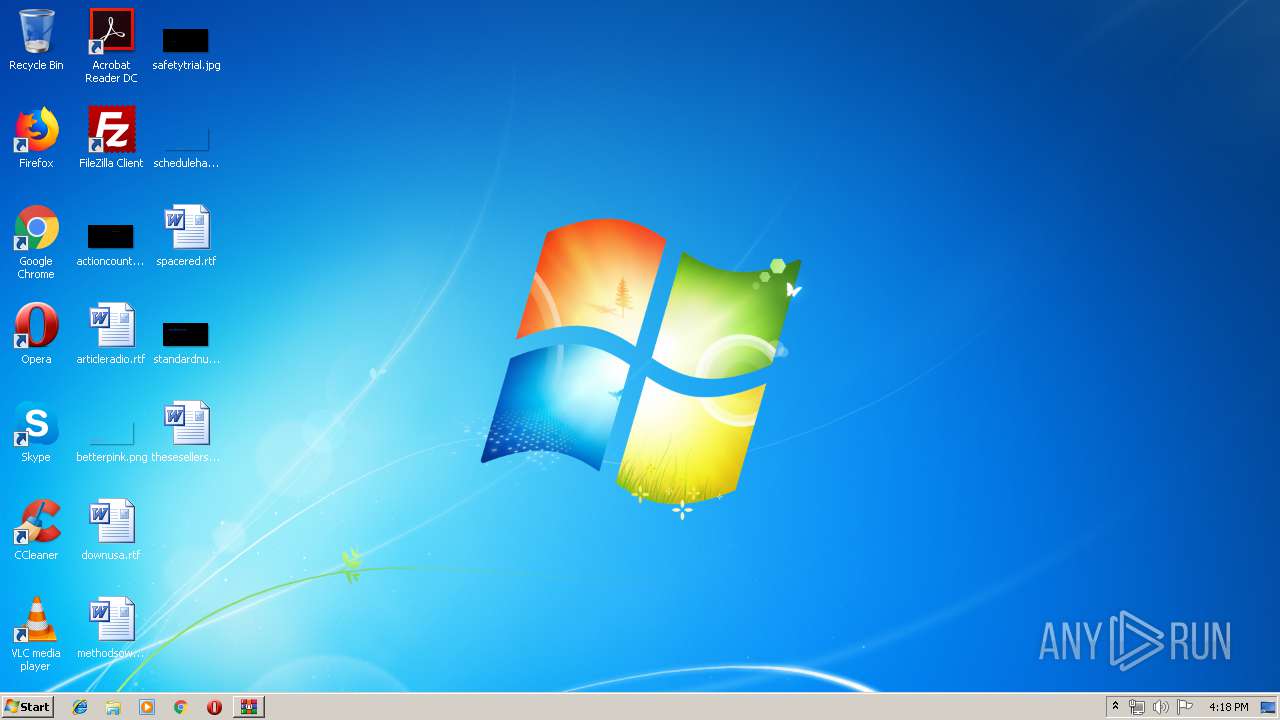
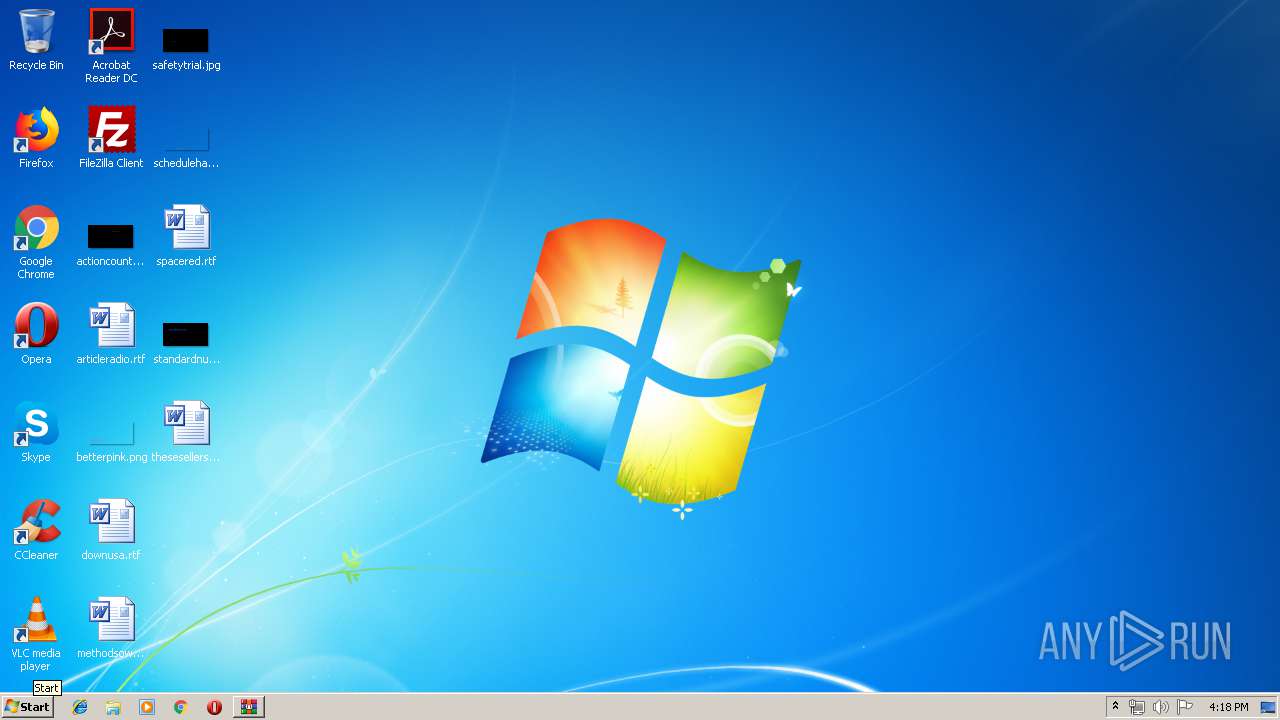
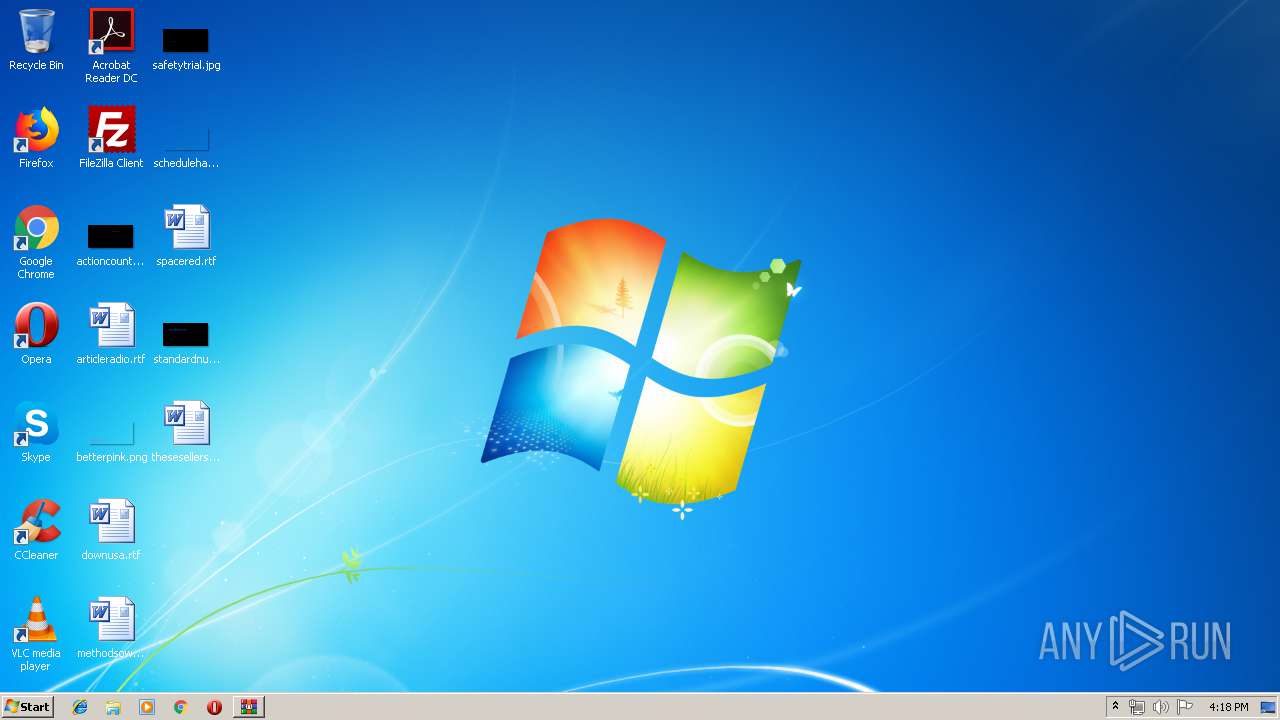
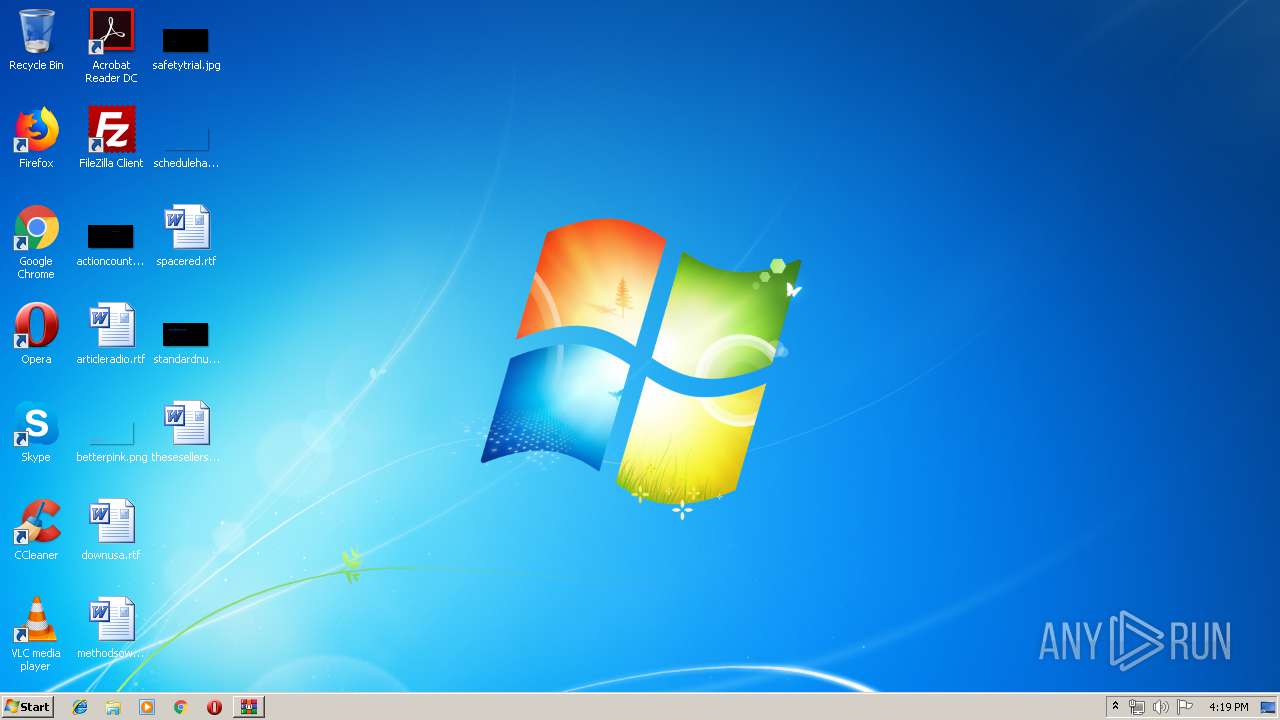
Creates files in the user directory
- DHL BILL OF LADING INVOICE82003184.scr (PID: 3164)
Reads the cookies of Google Chrome
- DHL BILL OF LADING INVOICE82003184.scr (PID: 3164)
Reads the cookies of Mozilla Firefox
- DHL BILL OF LADING INVOICE82003184.scr (PID: 3164)
Checks for external IP
- DHL BILL OF LADING INVOICE82003184.scr (PID: 3164)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .ace | | | ACE compressed archive (100) |
|---|
Total processes
36
Monitored processes
3
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2780 | "C:\Users\admin\AppData\Local\Temp\Rar$DIa3268.1319\DHL BILL OF LADING INVOICE82003184.scr" /S | C:\Users\admin\AppData\Local\Temp\Rar$DIa3268.1319\DHL BILL OF LADING INVOICE82003184.scr | — | WinRAR.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3164 | "C:\Users\admin\AppData\Local\Temp\Rar$DIa3268.1319\DHL BILL OF LADING INVOICE82003184.scr" /S | C:\Users\admin\AppData\Local\Temp\Rar$DIa3268.1319\DHL BILL OF LADING INVOICE82003184.scr | DHL BILL OF LADING INVOICE82003184.scr | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3268 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\New Order #0008.ace" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
Total events
515
Read events
480
Write events
35
Delete events
0
Modification events
| (PID) Process: | (3268) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3268) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3268) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\72\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3268) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\New Order #0008.ace | |||
| (PID) Process: | (3268) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3268) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3268) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3268) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (3268) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\ACE Compression Software\ActiveAce\2.0 |
| Operation: | write | Name: | Count |
Value: 0 | |||
| (PID) Process: | (3268) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\ACE Compression Software\ActiveAce\2.0 |
| Operation: | write | Name: | Name |
Value: 542D4B42647265644B76737A7E794B566767537663764B5B7874767B4B43727A674B59726037586573726537342727272F3976747217171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171717171700 | |||
Executable files
1
Suspicious files
1
Text files
0
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3164 | DHL BILL OF LADING INVOICE82003184.scr | C:\Users\admin\AppData\Roaming\ajkcw145.s4v\Chrome\Default\Cookies | — | |
MD5:— | SHA256:— | |||
| 3164 | DHL BILL OF LADING INVOICE82003184.scr | C:\Users\admin\AppData\Roaming\ajkcw145.s4v\Firefox\Profiles\qldyz51w.default\cookies.sqlite | — | |
MD5:— | SHA256:— | |||
| 3268 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DIa3268.1319\DHL BILL OF LADING INVOICE82003184.scr | executable | |
MD5:— | SHA256:— | |||
| 3164 | DHL BILL OF LADING INVOICE82003184.scr | C:\Users\admin\AppData\Local\Temp\637013099395216250_5de89d2b-e0e9-454d-8c7e-7bcfff24d0d9.db | sqlite | |
MD5:— | SHA256:— | |||
| 3164 | DHL BILL OF LADING INVOICE82003184.scr | C:\Users\admin\AppData\Roaming\ajkcw145.s4v.zip | compressed | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
3
DNS requests
2
Threats
6
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3164 | DHL BILL OF LADING INVOICE82003184.scr | GET | 200 | 34.196.181.158:80 | http://checkip.amazonaws.com/ | US | text | 16 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3164 | DHL BILL OF LADING INVOICE82003184.scr | 34.196.181.158:80 | checkip.amazonaws.com | Amazon.com, Inc. | US | shared |
3164 | DHL BILL OF LADING INVOICE82003184.scr | 202.146.241.47:587 | mail.hervitama.co.id | PT Centrin Utama | ID | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
checkip.amazonaws.com |
| malicious |
mail.hervitama.co.id |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3164 | DHL BILL OF LADING INVOICE82003184.scr | A Network Trojan was detected | MALWARE [PTsecurity] AgentTesla IP Check |
3164 | DHL BILL OF LADING INVOICE82003184.scr | Generic Protocol Command Decode | SURICATA Applayer Detect protocol only one direction |
3164 | DHL BILL OF LADING INVOICE82003184.scr | Generic Protocol Command Decode | SURICATA Applayer Detect protocol only one direction |
3 ETPRO signatures available at the full report