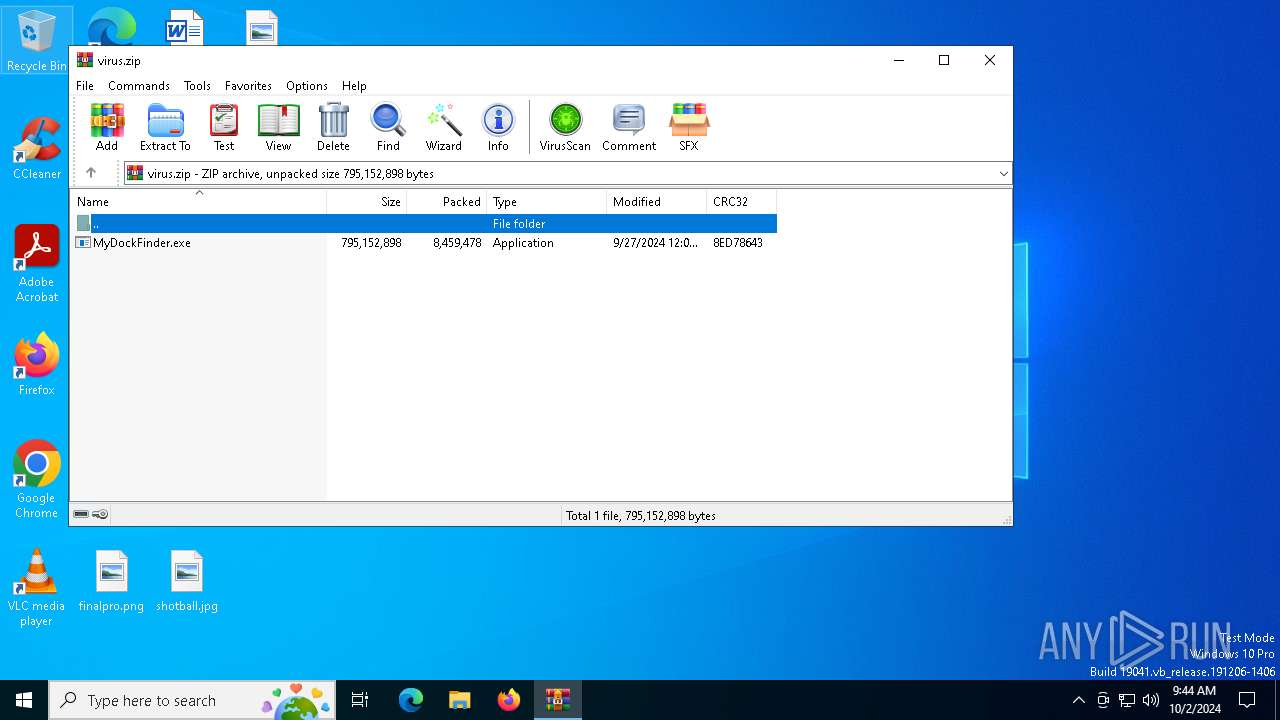
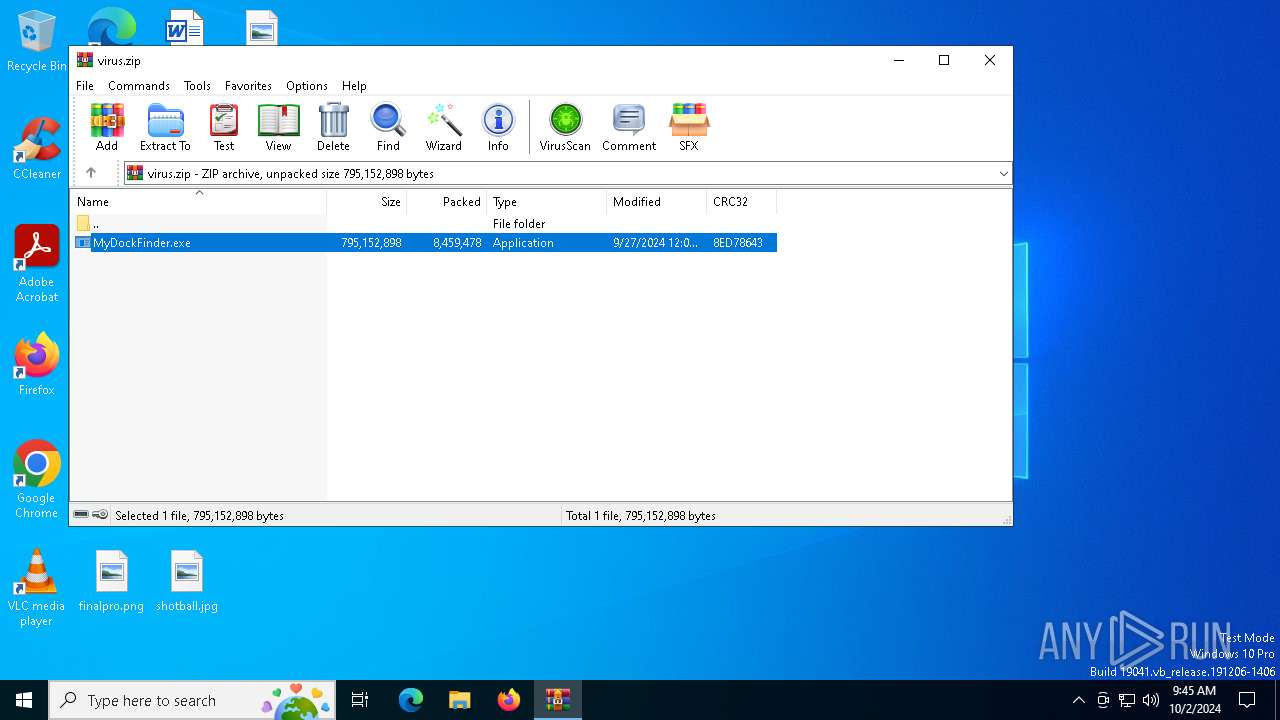
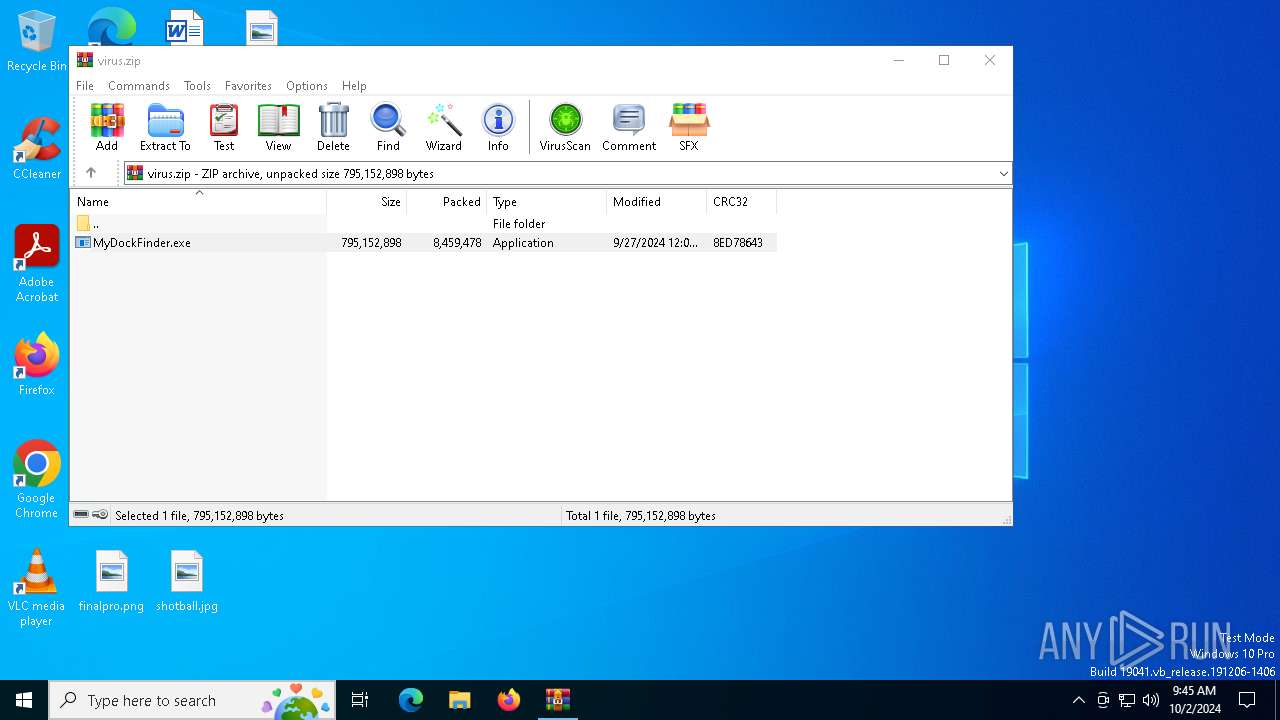
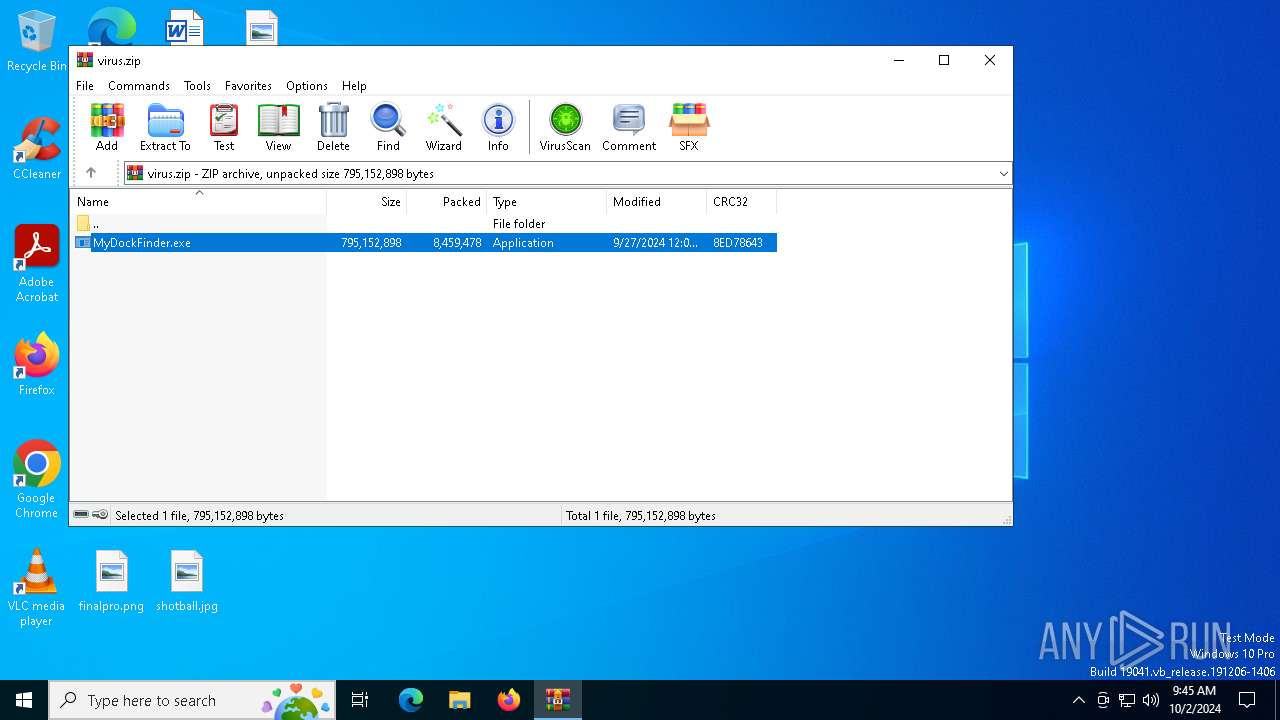
| File name: | virus.zip |
| Full analysis: | https://app.any.run/tasks/a8dce1be-dc5b-433b-948f-30b64e2c5f50 |
| Verdict: | Malicious activity |
| Threats: | Lumma is an information stealer, developed using the C programming language. It is offered for sale as a malware-as-a-service, with several plans available. It usually targets cryptocurrency wallets, login credentials, and other sensitive information on a compromised system. The malicious software regularly gets updates that improve and expand its functionality, making it a serious stealer threat. |
| Analysis date: | October 02, 2024, 09:44:45 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=deflate |
| MD5: | E33660C8F270334CF479D63109D8A5C0 |
| SHA1: | EA939EB07F93D57C6FD59E38139083AAAD4BAA12 |
| SHA256: | 7515316ACBC9EC2AE66A0A112AE37F3E85F2999371D8C0A7735694BF24D3B1C7 |
| SSDEEP: | 98304:Hb5kJ6jNKEAJMivNJUC52jvUYBQliNsh0+CMkhfE7SW845OOUOYyjwktWPh0rHdm:Zr49S4GJ0YcgT |
MALICIOUS
LUMMA has been detected (SURICATA)
- svchost.exe (PID: 2256)
Connects to the CnC server
- svchost.exe (PID: 2256)
Actions looks like stealing of personal data
- BitLockerToGo.exe (PID: 5164)
STEALC has been detected (YARA)
- GS640SXBVR2HI6MX82RPH55K.exe (PID: 2036)
- BitLockerToGo.exe (PID: 1640)
AutoIt loader has been detected (YARA)
- Voyuer.pif (PID: 6644)
SUSPICIOUS
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 752)
- 3LOGPKWKR5BES4FPDWN7LI4DZRKBQLT.exe (PID: 4092)
Contacting a server suspected of hosting an CnC
- svchost.exe (PID: 2256)
Executable content was dropped or overwritten
- BitLockerToGo.exe (PID: 5164)
- cmd.exe (PID: 6028)
- Voyuer.pif (PID: 6644)
Starts CMD.EXE for commands execution
- 3LOGPKWKR5BES4FPDWN7LI4DZRKBQLT.exe (PID: 4092)
- cmd.exe (PID: 6028)
Executing commands from a ".bat" file
- 3LOGPKWKR5BES4FPDWN7LI4DZRKBQLT.exe (PID: 4092)
Get information on the list of running processes
- cmd.exe (PID: 6028)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 6028)
Application launched itself
- cmd.exe (PID: 6028)
- Voyuer.pif (PID: 6644)
Starts application with an unusual extension
- cmd.exe (PID: 6028)
- Voyuer.pif (PID: 6644)
The executable file from the user directory is run by the CMD process
- Voyuer.pif (PID: 6644)
There is functionality for communication over UDP network (YARA)
- GS640SXBVR2HI6MX82RPH55K.exe (PID: 2036)
INFO
Reads the computer name
- BitLockerToGo.exe (PID: 5164)
- MyDockFinder.exe (PID: 2212)
- 3LOGPKWKR5BES4FPDWN7LI4DZRKBQLT.exe (PID: 4092)
Checks supported languages
- BitLockerToGo.exe (PID: 5164)
- MyDockFinder.exe (PID: 2212)
- GS640SXBVR2HI6MX82RPH55K.exe (PID: 2036)
- 3LOGPKWKR5BES4FPDWN7LI4DZRKBQLT.exe (PID: 4092)
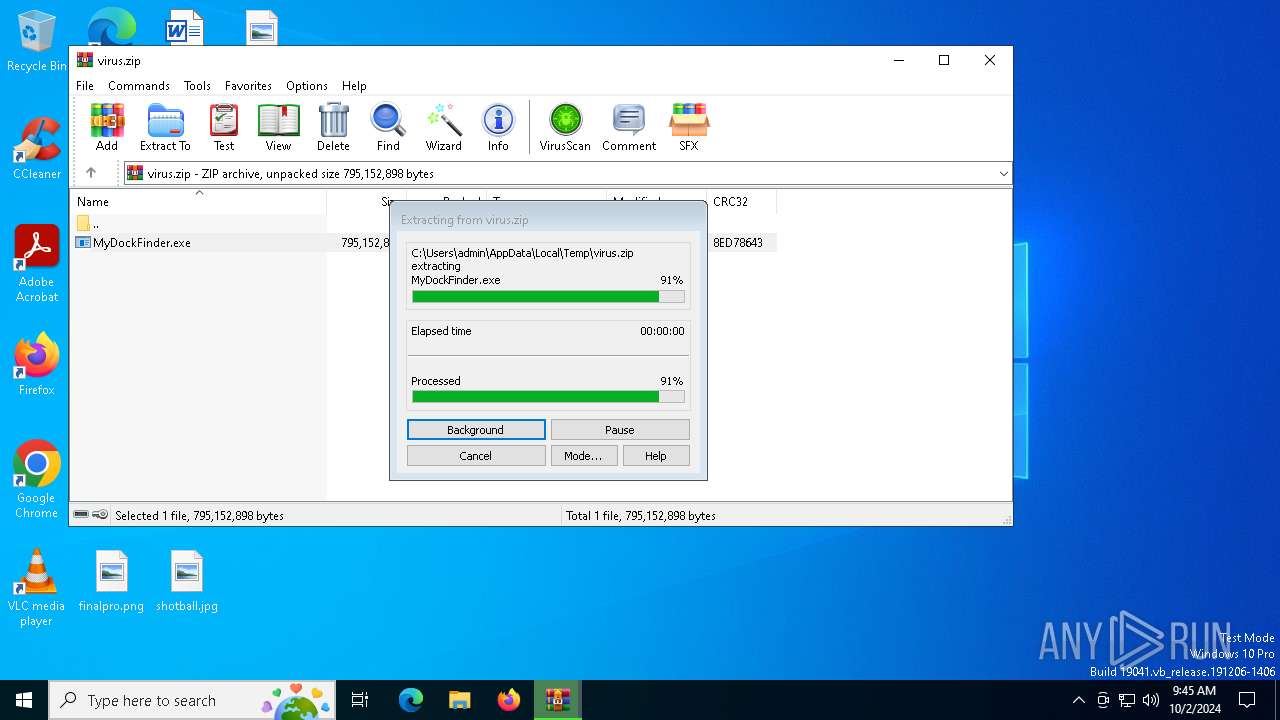
The process uses the downloaded file
- WinRAR.exe (PID: 752)
- 3LOGPKWKR5BES4FPDWN7LI4DZRKBQLT.exe (PID: 4092)
Reads the software policy settings
- BitLockerToGo.exe (PID: 5164)
Process checks computer location settings
- 3LOGPKWKR5BES4FPDWN7LI4DZRKBQLT.exe (PID: 4092)
Create files in a temporary directory
- BitLockerToGo.exe (PID: 5164)
- 3LOGPKWKR5BES4FPDWN7LI4DZRKBQLT.exe (PID: 4092)
Manual execution by a user
- cmd.exe (PID: 3148)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Stealc
(PID) Process(1640) BitLockerToGo.exe
C245.200.149.53
Strings (353)INSERT_KEY_HERE
17
10
20
24
GetProcAddress
LoadLibraryA
lstrcatA
OpenEventA
CreateEventA
CloseHandle
Sleep
GetUserDefaultLangID
VirtualAllocExNuma
VirtualFree
GetSystemInfo
VirtualAlloc
HeapAlloc
GetComputerNameA
lstrcpyA
GetProcessHeap
GetCurrentProcess
lstrlenA
ExitProcess
GlobalMemoryStatusEx
GetSystemTime
SystemTimeToFileTime
advapi32.dll
gdi32.dll
user32.dll
crypt32.dll
ntdll.dll
GetUserNameA
CreateDCA
GetDeviceCaps
ReleaseDC
CryptStringToBinaryA
sscanf
VMwareVMware
HAL9TH
JohnDoe
DISPLAY
%hu/%hu/%hu
http://45.200.149.53
ilnur
!|
/281e4696f6bc0de6.php
/b36b1de18388ebbc/
c1
GetEnvironmentVariableA
GetFileAttributesA
GlobalLock
HeapFree
GetFileSize
GlobalSize
CreateToolhelp32Snapshot
IsWow64Process
Process32Next
GetLocalTime
FreeLibrary
GetTimeZoneInformation
GetSystemPowerStatus
GetVolumeInformationA
GetWindowsDirectoryA
Process32First
GetLocaleInfoA
GetUserDefaultLocaleName
GetModuleFileNameA
DeleteFileA
FindNextFileA
LocalFree
FindClose
SetEnvironmentVariableA
LocalAlloc
GetFileSizeEx
ReadFile
SetFilePointer
WriteFile
CreateFileA
FindFirstFileA
CopyFileA
VirtualProtect
GetLogicalProcessorInformationEx
GetLastError
lstrcpynA
MultiByteToWideChar
GlobalFree
WideCharToMultiByte
GlobalAlloc
OpenProcess
TerminateProcess
GetCurrentProcessId
gdiplus.dll
ole32.dll
bcrypt.dll
wininet.dll
shlwapi.dll
shell32.dll
psapi.dll
rstrtmgr.dll
CreateCompatibleBitmap
SelectObject
BitBlt
DeleteObject
CreateCompatibleDC
GdipGetImageEncodersSize
GdipGetImageEncoders
GdipCreateBitmapFromHBITMAP
GdiplusStartup
GdiplusShutdown
GdipSaveImageToStream
GdipDisposeImage
GdipFree
GetHGlobalFromStream
CreateStreamOnHGlobal
CoUninitialize
CoInitialize
CoCreateInstance
BCryptGenerateSymmetricKey
BCryptCloseAlgorithmProvider
BCryptDecrypt
BCryptSetProperty
BCryptDestroyKey
BCryptOpenAlgorithmProvider
GetWindowRect
GetDesktopWindow
GetDC
CloseWindow
wsprintfA
EnumDisplayDevicesA
GetKeyboardLayoutList
CharToOemW
wsprintfW
RegQueryValueExA
RegEnumKeyExA
RegOpenKeyExA
RegCloseKey
RegEnumValueA
CryptBinaryToStringA
CryptUnprotectData
SHGetFolderPathA
ShellExecuteExA
InternetOpenUrlA
InternetConnectA
InternetCloseHandle
InternetOpenA
HttpSendRequestA
HttpOpenRequestA
InternetReadFile
InternetCrackUrlA
StrCmpCA
StrStrA
StrCmpCW
PathMatchSpecA
GetModuleFileNameExA
RmStartSession
RmRegisterResources
RmGetList
RmEndSession
sqlite3_open
sqlite3_prepare_v2
sqlite3_step
sqlite3_column_text
sqlite3_finalize
sqlite3_close
sqlite3_column_bytes
sqlite3_column_blob
encrypted_key
PATH
C:\ProgramData\nss3.dll
NSS_Init
NSS_Shutdown
PK11_GetInternalKeySlot
PK11_FreeSlot
PK11_Authenticate
PK11SDR_Decrypt
C:\ProgramData\
SELECT origin_url, username_value, password_value FROM logins
browser:
profile:
url:
login:
password:
Opera
OperaGX
Network
cookies
.txt
SELECT HOST_KEY, is_httponly, path, is_secure, (expires_utc/1000000)-11644480800, name, encrypted_value from cookies
TRUE
FALSE
autofill
SELECT name, value FROM autofill
history
SELECT url FROM urls LIMIT 1000
cc
SELECT name_on_card, expiration_month, expiration_year, card_number_encrypted FROM credit_cards
name:
month:
year:
card:
Cookies
Login Data
Web Data
History
logins.json
formSubmitURL
usernameField
encryptedUsername
encryptedPassword
guid
SELECT host, isHttpOnly, path, isSecure, expiry, name, value FROM moz_cookies
SELECT fieldname, value FROM moz_formhistory
SELECT url FROM moz_places LIMIT 1000
cookies.sqlite
formhistory.sqlite
places.sqlite
plugins
Local Extension Settings
Sync Extension Settings
IndexedDB
Opera Stable
Opera GX Stable
CURRENT
chrome-extension_
_0.indexeddb.leveldb
Local State
profiles.ini
chrome
opera
firefox
wallets
%08lX%04lX%lu
SOFTWARE\Microsoft\Windows NT\CurrentVersion
ProductName
x32
x64
%d/%d/%d %d:%d:%d
HARDWARE\DESCRIPTION\System\CentralProcessor\0
ProcessorNameString
SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall
DisplayName
DisplayVersion
Network Info:
- IP: IP?
- Country: ISO?
System Summary:
- HWID:
- OS:
- Architecture:
- UserName:
- Computer Name:
- Local Time:
- UTC:
- Language:
- Keyboards:
- Laptop:
- Running Path:
- CPU:
- Threads:
- Cores:
- RAM:
- Display Resolution:
- GPU:
User Agents:
Installed Apps:
All Users:
Current User:
Process List:
system_info.txt
freebl3.dll
mozglue.dll
msvcp140.dll
nss3.dll
softokn3.dll
vcruntime140.dll
\Temp\
.exe
runas
open
/c start
%DESKTOP%
%APPDATA%
%LOCALAPPDATA%
%USERPROFILE%
%DOCUMENTS%
%PROGRAMFILES%
%PROGRAMFILES_86%
%RECENT%
*.lnk
files
\discord\
\Local Storage\leveldb\CURRENT
\Local Storage\leveldb
\Telegram Desktop\
key_datas
D877F783D5D3EF8C*
map*
A7FDF864FBC10B77*
A92DAA6EA6F891F2*
F8806DD0C461824F*
Telegram
Tox
*.tox
*.ini
Password
Software\Microsoft\Windows NT\CurrentVersion\Windows Messaging Subsystem\Profiles\Outlook\9375CFF0413111d3B88A00104B2A6676\
Software\Microsoft\Office\13.0\Outlook\Profiles\Outlook\9375CFF0413111d3B88A00104B2A6676\
Software\Microsoft\Office\14.0\Outlook\Profiles\Outlook\9375CFF0413111d3B88A00104B2A6676\
Software\Microsoft\Office\15.0\Outlook\Profiles\Outlook\9375CFF0413111d3B88A00104B2A6676\
Software\Microsoft\Office\16.0\Outlook\Profiles\Outlook\9375CFF0413111d3B88A00104B2A6676\
oftware\Microsoft\Windows Messaging Subsystem\Profiles\9375CFF0413111d3B88A00104B2A6676\
00000001
00000002
00000003
00000004
\Outlook\accounts.txt
Pidgin
\.purple\
accounts.xml
dQw4w9WgXcQ
token:
Software\Valve\Steam
SteamPath
\config\
ssfn*
config.vdf
DialogConfig.vdf
DialogConfigOverlay*.vdf
libraryfolders.vdf
loginusers.vdf
\Steam\
sqlite3.dll
browsers
done
soft
\Discord\tokens.txt
/c timeout /t 5 & del /f /q "
" & del "C:\ProgramData\*.dll"" & exit
C:\Windows\system32\cmd.exe
https
Content-Type: multipart/form-data; boundary=----
POST
HTTP/1.1
Content-Disposition: form-data; name="
hwid
build
token
file_name
file
message
ABCDEFGHIJKLMNOPQRSTUVWXYZ1234567890
screenshot.jpg
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2024:09:27 05:08:00 |
| ZipCRC: | 0x8ed78643 |
| ZipCompressedSize: | 8459478 |
| ZipUncompressedSize: | 795152898 |
| ZipFileName: | MyDockFinder.exe |
Total processes
152
Monitored processes
21
Malicious processes
9
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 752 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\AppData\Local\Temp\virus.zip | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
| 1076 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1436 | C:\Users\admin\AppData\Local\Temp\10518\Voyuer.pif | C:\Users\admin\AppData\Local\Temp\10518\Voyuer.pif | — | Voyuer.pif | |||||||||||
User: admin Company: AutoIt Team Integrity Level: MEDIUM Description: AutoIt v3 Script Exit code: 0 Version: 3, 3, 14, 3 Modules
| |||||||||||||||
| 1640 | "C:\Windows\BitLockerDiscoveryVolumeContents\BitLockerToGo.exe" | C:\Windows\BitLockerDiscoveryVolumeContents\BitLockerToGo.exe | GS640SXBVR2HI6MX82RPH55K.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: BitLocker To Go Reader Exit code: 3221225477 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
Stealc(PID) Process(1640) BitLockerToGo.exe C245.200.149.53 Strings (353)INSERT_KEY_HERE 17 10 20 24 GetProcAddress LoadLibraryA lstrcatA OpenEventA CreateEventA CloseHandle Sleep GetUserDefaultLangID VirtualAllocExNuma VirtualFree GetSystemInfo VirtualAlloc HeapAlloc GetComputerNameA lstrcpyA GetProcessHeap GetCurrentProcess lstrlenA ExitProcess GlobalMemoryStatusEx GetSystemTime SystemTimeToFileTime advapi32.dll gdi32.dll user32.dll crypt32.dll ntdll.dll GetUserNameA CreateDCA GetDeviceCaps ReleaseDC CryptStringToBinaryA sscanf VMwareVMware HAL9TH JohnDoe DISPLAY %hu/%hu/%hu http://45.200.149.53 ilnur !| /281e4696f6bc0de6.php /b36b1de18388ebbc/ c1 GetEnvironmentVariableA GetFileAttributesA GlobalLock HeapFree GetFileSize GlobalSize CreateToolhelp32Snapshot IsWow64Process Process32Next GetLocalTime FreeLibrary GetTimeZoneInformation GetSystemPowerStatus GetVolumeInformationA GetWindowsDirectoryA Process32First GetLocaleInfoA GetUserDefaultLocaleName GetModuleFileNameA DeleteFileA FindNextFileA LocalFree FindClose SetEnvironmentVariableA LocalAlloc GetFileSizeEx ReadFile SetFilePointer WriteFile CreateFileA FindFirstFileA CopyFileA VirtualProtect GetLogicalProcessorInformationEx GetLastError lstrcpynA MultiByteToWideChar GlobalFree WideCharToMultiByte GlobalAlloc OpenProcess TerminateProcess GetCurrentProcessId gdiplus.dll ole32.dll bcrypt.dll wininet.dll shlwapi.dll shell32.dll psapi.dll rstrtmgr.dll CreateCompatibleBitmap SelectObject BitBlt DeleteObject CreateCompatibleDC GdipGetImageEncodersSize GdipGetImageEncoders GdipCreateBitmapFromHBITMAP GdiplusStartup GdiplusShutdown GdipSaveImageToStream GdipDisposeImage GdipFree GetHGlobalFromStream CreateStreamOnHGlobal CoUninitialize CoInitialize CoCreateInstance BCryptGenerateSymmetricKey BCryptCloseAlgorithmProvider BCryptDecrypt BCryptSetProperty BCryptDestroyKey BCryptOpenAlgorithmProvider GetWindowRect GetDesktopWindow GetDC CloseWindow wsprintfA EnumDisplayDevicesA GetKeyboardLayoutList CharToOemW wsprintfW RegQueryValueExA RegEnumKeyExA RegOpenKeyExA RegCloseKey RegEnumValueA CryptBinaryToStringA CryptUnprotectData SHGetFolderPathA ShellExecuteExA InternetOpenUrlA InternetConnectA InternetCloseHandle InternetOpenA HttpSendRequestA HttpOpenRequestA InternetReadFile InternetCrackUrlA StrCmpCA StrStrA StrCmpCW PathMatchSpecA GetModuleFileNameExA RmStartSession RmRegisterResources RmGetList RmEndSession sqlite3_open sqlite3_prepare_v2 sqlite3_step sqlite3_column_text sqlite3_finalize sqlite3_close sqlite3_column_bytes sqlite3_column_blob encrypted_key PATH C:\ProgramData\nss3.dll NSS_Init NSS_Shutdown PK11_GetInternalKeySlot PK11_FreeSlot PK11_Authenticate PK11SDR_Decrypt C:\ProgramData\ SELECT origin_url, username_value, password_value FROM logins browser: profile: url: login: password: Opera OperaGX Network cookies .txt SELECT HOST_KEY, is_httponly, path, is_secure, (expires_utc/1000000)-11644480800, name, encrypted_value from cookies TRUE FALSE autofill SELECT name, value FROM autofill history SELECT url FROM urls LIMIT 1000 cc SELECT name_on_card, expiration_month, expiration_year, card_number_encrypted FROM credit_cards name: month: year: card: Cookies Login Data Web Data History logins.json formSubmitURL usernameField encryptedUsername encryptedPassword guid SELECT host, isHttpOnly, path, isSecure, expiry, name, value FROM moz_cookies SELECT fieldname, value FROM moz_formhistory SELECT url FROM moz_places LIMIT 1000 cookies.sqlite formhistory.sqlite places.sqlite plugins Local Extension Settings Sync Extension Settings IndexedDB Opera Stable Opera GX Stable CURRENT chrome-extension_ _0.indexeddb.leveldb Local State profiles.ini chrome opera firefox wallets %08lX%04lX%lu SOFTWARE\Microsoft\Windows NT\CurrentVersion ProductName x32 x64 %d/%d/%d %d:%d:%d HARDWARE\DESCRIPTION\System\CentralProcessor\0 ProcessorNameString SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall DisplayName DisplayVersion Network Info: - IP: IP? - Country: ISO? System Summary: - HWID: - OS: - Architecture: - UserName: - Computer Name: - Local Time: - UTC: - Language: - Keyboards: - Laptop: - Running Path: - CPU: - Threads: - Cores: - RAM: - Display Resolution: - GPU: User Agents: Installed Apps: All Users: Current User: Process List: system_info.txt freebl3.dll mozglue.dll msvcp140.dll nss3.dll softokn3.dll vcruntime140.dll \Temp\ .exe runas open /c start %DESKTOP% %APPDATA% %LOCALAPPDATA% %USERPROFILE% %DOCUMENTS% %PROGRAMFILES% %PROGRAMFILES_86% %RECENT% *.lnk files \discord\ \Local Storage\leveldb\CURRENT \Local Storage\leveldb \Telegram Desktop\ key_datas D877F783D5D3EF8C* map* A7FDF864FBC10B77* A92DAA6EA6F891F2* F8806DD0C461824F* Telegram Tox *.tox *.ini Password Software\Microsoft\Windows NT\CurrentVersion\Windows Messaging Subsystem\Profiles\Outlook\9375CFF0413111d3B88A00104B2A6676\ Software\Microsoft\Office\13.0\Outlook\Profiles\Outlook\9375CFF0413111d3B88A00104B2A6676\ Software\Microsoft\Office\14.0\Outlook\Profiles\Outlook\9375CFF0413111d3B88A00104B2A6676\ Software\Microsoft\Office\15.0\Outlook\Profiles\Outlook\9375CFF0413111d3B88A00104B2A6676\ Software\Microsoft\Office\16.0\Outlook\Profiles\Outlook\9375CFF0413111d3B88A00104B2A6676\ oftware\Microsoft\Windows Messaging Subsystem\Profiles\9375CFF0413111d3B88A00104B2A6676\ 00000001 00000002 00000003 00000004 \Outlook\accounts.txt Pidgin \.purple\ accounts.xml dQw4w9WgXcQ token: Software\Valve\Steam SteamPath \config\ ssfn* config.vdf DialogConfig.vdf DialogConfigOverlay*.vdf libraryfolders.vdf loginusers.vdf \Steam\ sqlite3.dll browsers done soft \Discord\tokens.txt /c timeout /t 5 & del /f /q " " & del "C:\ProgramData\*.dll"" & exit C:\Windows\system32\cmd.exe https Content-Type: multipart/form-data; boundary=---- POST HTTP/1.1 Content-Disposition: form-data; name=" hwid build token file_name file message ABCDEFGHIJKLMNOPQRSTUVWXYZ1234567890 screenshot.jpg | |||||||||||||||
| 2036 | "C:\Users\admin\AppData\Local\Temp\GS640SXBVR2HI6MX82RPH55K.exe" | C:\Users\admin\AppData\Local\Temp\GS640SXBVR2HI6MX82RPH55K.exe | BitLockerToGo.exe | ||||||||||||
User: admin Company: MiTeC Integrity Level: MEDIUM Description: Desktop Explorer Exit code: 666 Version: 1.1.0.0 Modules
| |||||||||||||||
| 2212 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa752.11311\MyDockFinder.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa752.11311\MyDockFinder.exe | — | WinRAR.exe | |||||||||||
User: admin Company: ASUS Integrity Level: MEDIUM Description: The installer for MyDockFinder. Exit code: 666 Version: 3.2.11.2 Modules
| |||||||||||||||
| 2256 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2280 | choice /d y /t 5 | C:\Windows\SysWOW64\choice.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Offers the user a choice Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2628 | findstr /I "wrsa opssvc" | C:\Windows\SysWOW64\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Find String (QGREP) Utility Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3148 | cmd /k echo [InternetShortcut] > "C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\QuantumLink.url" & echo URL="C:\Users\admin\AppData\Local\QuantumCom Innovations Ltd\QuantumLink.js" >> "C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\QuantumLink.url" & exit | C:\Windows\SysWOW64\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
6 177
Read events
6 168
Write events
9
Delete events
0
Modification events
| (PID) Process: | (752) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\GoogleChromeEnterpriseBundle64.zip | |||
| (PID) Process: | (752) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\virus.zip | |||
| (PID) Process: | (752) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (752) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (752) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (752) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (1640) BitLockerToGo.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (1640) BitLockerToGo.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (1640) BitLockerToGo.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
Executable files
4
Suspicious files
10
Text files
4
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 752 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa752.11311\MyDockFinder.exe | — | |
MD5:— | SHA256:— | |||
| 5164 | BitLockerToGo.exe | C:\Users\admin\AppData\Local\Temp\3LOGPKWKR5BES4FPDWN7LI4DZRKBQLT.exe | executable | |
MD5:88F2F4DF57C115AB7062C7A2A23E454A | SHA256:08F30ECE5F7E77A69E58A970B3684C2A0EBA1AA203AC97836DAD32FC10A15E90 | |||
| 4092 | 3LOGPKWKR5BES4FPDWN7LI4DZRKBQLT.exe | C:\Users\admin\AppData\Local\Temp\Explains | binary | |
MD5:D32CBD96F1A1A04DDCC9A1A208FB81E5 | SHA256:603230F8180F5D1D68621254976467ACEF4EAED5DD4193AA6C03F7384AD27DD1 | |||
| 4092 | 3LOGPKWKR5BES4FPDWN7LI4DZRKBQLT.exe | C:\Users\admin\AppData\Local\Temp\Victor | binary | |
MD5:C823E5A74879DA9CBFF89361425B11B3 | SHA256:7B39896A8D5A68E5F3DA8EC64F9CEAB3F533D05FDB18754DB5B0A48ED308341B | |||
| 4092 | 3LOGPKWKR5BES4FPDWN7LI4DZRKBQLT.exe | C:\Users\admin\AppData\Local\Temp\Diseases | binary | |
MD5:D857861493EBEFA86A1E73C6DF657E94 | SHA256:D1812729D79680D65002AAB3836D732F5EBDFF0468D134654406A085CCCC7BE6 | |||
| 4092 | 3LOGPKWKR5BES4FPDWN7LI4DZRKBQLT.exe | C:\Users\admin\AppData\Local\Temp\Uniprotkb | binary | |
MD5:69D07759583AFA982405CEDF0B879B8E | SHA256:2B3F63621C8AE1EB1BC3DFC4683EC983277AC17AEA03ACECEBC54969A723AB72 | |||
| 4092 | 3LOGPKWKR5BES4FPDWN7LI4DZRKBQLT.exe | C:\Users\admin\AppData\Local\Temp\Killing | text | |
MD5:632076E43FF6F1C2EC3FC59D2AC115C5 | SHA256:432A473F21A57610DF93773A79AE94365D6C2B6AA1555123BFDD658A6F28CF2F | |||
| 6028 | cmd.exe | C:\Users\admin\AppData\Local\Temp\Killing.bat | text | |
MD5:632076E43FF6F1C2EC3FC59D2AC115C5 | SHA256:432A473F21A57610DF93773A79AE94365D6C2B6AA1555123BFDD658A6F28CF2F | |||
| 4092 | 3LOGPKWKR5BES4FPDWN7LI4DZRKBQLT.exe | C:\Users\admin\AppData\Local\Temp\Delegation | binary | |
MD5:E82A72CAE193B8525A968245FE8934CC | SHA256:3D701EA1DDC78F91919E733B8E8992C708A43B40DD58CE46E0500A6684456B06 | |||
| 4092 | 3LOGPKWKR5BES4FPDWN7LI4DZRKBQLT.exe | C:\Users\admin\AppData\Local\Temp\Www | binary | |
MD5:D7DB0C4F504D819DE277753119685589 | SHA256:AAF0659F2BFF006009684C04963CE6B4FD996FC341C96E1DB85CE9EA5332DAB4 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
54
DNS requests
33
Threats
8
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6984 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
4792 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
5388 | svchost.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6564 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
6564 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
5336 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5388 | svchost.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
3888 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5388 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
3260 | svchost.exe | 40.113.103.199:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6984 | svchost.exe | 40.126.32.138:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6984 | svchost.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
3712 | svchost.exe | 184.28.89.167:443 | go.microsoft.com | AKAMAI-AS | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
arc.msn.com |
| whitelisted |
fd.api.iris.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2256 | svchost.exe | Domain Observed Used for C2 Detected | ET MALWARE Win32/Lumma Stealer Related CnC Domain in DNS Lookup (pumpkinkwquo .shop) |
2256 | svchost.exe | Domain Observed Used for C2 Detected | ET MALWARE Win32/Lumma Stealer Related CnC Domain in DNS Lookup (defenddsouneuw .shop) |
2256 | svchost.exe | Domain Observed Used for C2 Detected | ET MALWARE Win32/Lumma Stealer Related CnC Domain in DNS Lookup (racedsuitreow .shop) |
2256 | svchost.exe | Domain Observed Used for C2 Detected | ET MALWARE Win32/Lumma Stealer Related CnC Domain in DNS Lookup (surroundeocw .shop) |
2256 | svchost.exe | Domain Observed Used for C2 Detected | ET MALWARE Win32/Lumma Stealer Related CnC Domain in DNS Lookup (priooozekw .shop) |
2256 | svchost.exe | Domain Observed Used for C2 Detected | ET MALWARE Win32/Lumma Stealer Related CnC Domain in DNS Lookup (abortinoiwiam .shop) |
2256 | svchost.exe | Domain Observed Used for C2 Detected | ET MALWARE Win32/Lumma Stealer Related CnC Domain in DNS Lookup (deallyharvenw .shop) |
2256 | svchost.exe | Domain Observed Used for C2 Detected | ET MALWARE Win32/Lumma Stealer Related CnC Domain in DNS Lookup (covvercilverow .shop) |