| File name: | USD38900.EXE |
| Full analysis: | https://app.any.run/tasks/093ebe5e-3588-4f86-9c62-bd4bec07e1f7 |
| Verdict: | Malicious activity |
| Threats: | Remote access trojans (RATs) are a type of malware that enables attackers to establish complete to partial control over infected computers. Such malicious programs often have a modular design, offering a wide range of functionalities for conducting illicit activities on compromised systems. Some of the most common features of RATs include access to the users’ data, webcam, and keystrokes. This malware is often distributed through phishing emails and links. |
| Analysis date: | March 31, 2020, 02:10:33 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | EA710C5F0A39A9D3B524977066ACDE36 |
| SHA1: | EE738124DECD05B712F615BCB1E8227D9B1BA3BB |
| SHA256: | 74FEB165656F8F823D446F77D8E791630359BC1F7A749964001FEADB286C56B1 |
| SSDEEP: | 3072:nhz3Jl6hYIbM4rOOCNr4TDsPqbDyplNmNq2E+PKqGEMsjP96s/gDXslCUZFADWat:hDz6hYIbMuOZqgqbDAx+Pd8sLs0hEW |
MALICIOUS
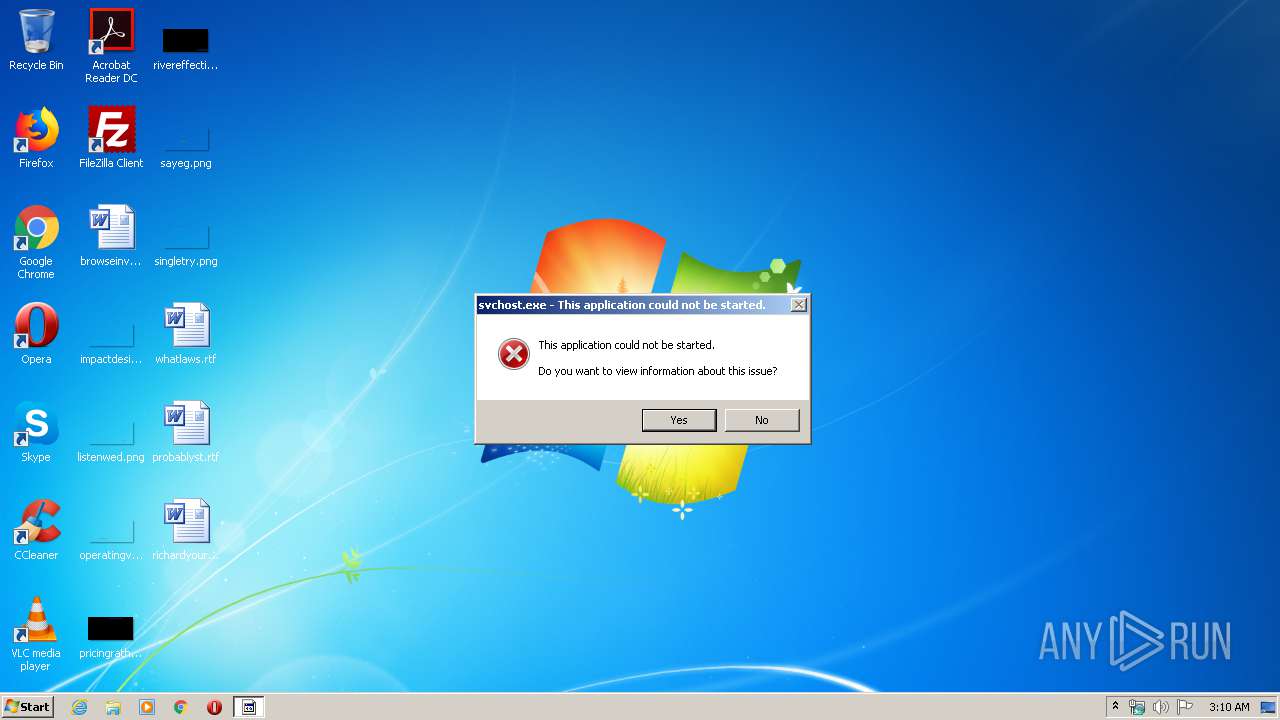
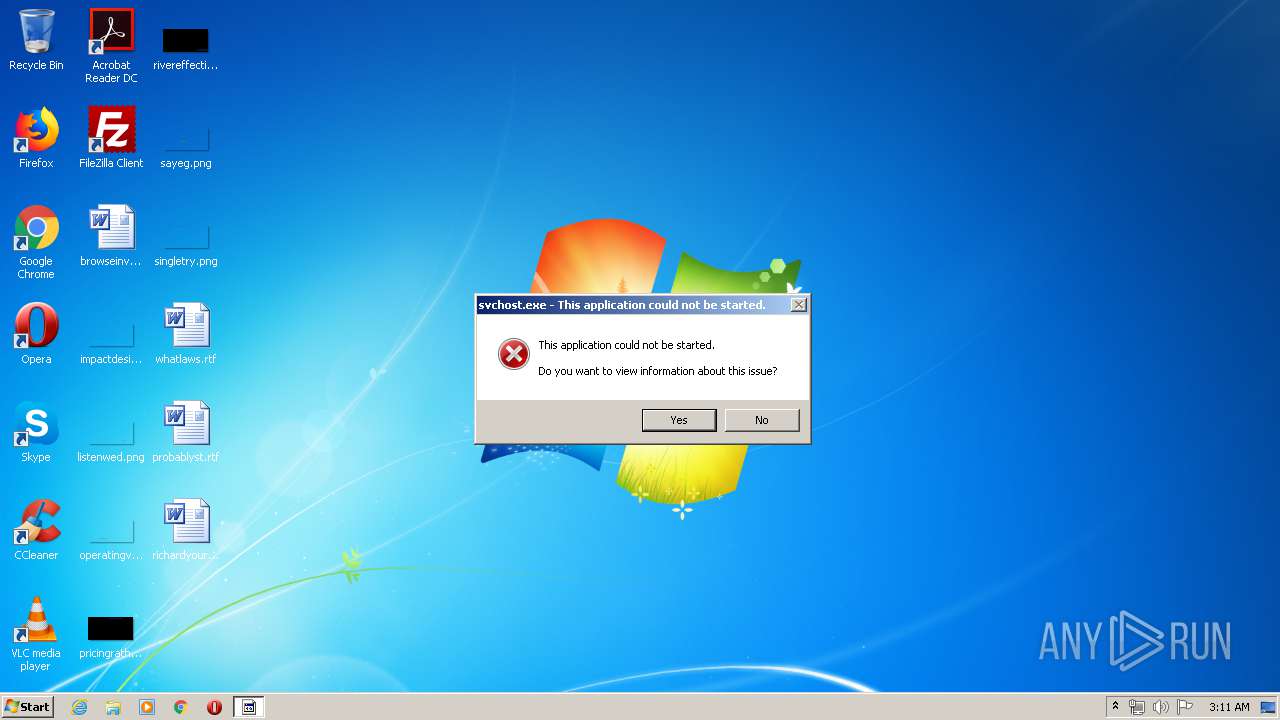
Uses SVCHOST.EXE for hidden code execution
- USD38900.EXE (PID: 2696)
REMCOS was detected
- USD38900.EXE (PID: 2696)
Connects to CnC server
- iexplore.exe (PID: 820)
Uses Task Scheduler to run other applications
- USD38900.EXE (PID: 3580)
Loads the Task Scheduler COM API
- schtasks.exe (PID: 2948)
SUSPICIOUS
Starts Internet Explorer
- svchost.exe (PID: 2820)
Application launched itself
- USD38900.EXE (PID: 3580)
Creates files in the user directory
- USD38900.EXE (PID: 3580)
- USD38900.EXE (PID: 2696)
Executable content was dropped or overwritten
- USD38900.EXE (PID: 3580)
INFO
Reads Internet Cache Settings
- iexplore.exe (PID: 540)
- iexplore.exe (PID: 820)
Changes internet zones settings
- iexplore.exe (PID: 540)
Reads internet explorer settings
- iexplore.exe (PID: 820)
Creates files in the user directory
- iexplore.exe (PID: 820)
Application launched itself
- iexplore.exe (PID: 540)
Reads settings of System Certificates
- iexplore.exe (PID: 540)
- iexplore.exe (PID: 820)
Dropped object may contain Bitcoin addresses
- iexplore.exe (PID: 540)
Adds / modifies Windows certificates
- iexplore.exe (PID: 540)
Changes settings of System certificates
- iexplore.exe (PID: 540)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (63.1) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (23.8) |
| .dll | | | Win32 Dynamic Link Library (generic) (5.6) |
| .exe | | | Win32 Executable (generic) (3.8) |
| .exe | | | Generic Win/DOS Executable (1.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2020:03:30 17:34:14+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 48 |
| CodeSize: | 223744 |
| InitializedDataSize: | 2048 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x387fe |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | - |
| CompanyName: | - |
| FileDescription: | SudokuSolver |
| FileVersion: | 1.0.0.0 |
| InternalName: | UwUZnaYlPxs.exe |
| LegalCopyright: | Copyright © 2019 |
| LegalTrademarks: | - |
| OriginalFileName: | UwUZnaYlPxs.exe |
| ProductName: | SudokuSolver |
| ProductVersion: | 1.0.0.0 |
| AssemblyVersion: | 1.0.0.0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 30-Mar-2020 15:34:14 |
| Comments: | - |
| CompanyName: | - |
| FileDescription: | SudokuSolver |
| FileVersion: | 1.0.0.0 |
| InternalName: | UwUZnaYlPxs.exe |
| LegalCopyright: | Copyright © 2019 |
| LegalTrademarks: | - |
| OriginalFilename: | UwUZnaYlPxs.exe |
| ProductName: | SudokuSolver |
| ProductVersion: | 1.0.0.0 |
| Assembly Version: | 1.0.0.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 30-Mar-2020 15:34:14 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00002000 | 0x00036804 | 0x00036A00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 7.72071 |
.rsrc | 0x0003A000 | 0x000005C0 | 0x00000600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.13907 |
.reloc | 0x0003C000 | 0x0000000C | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 0.0815394 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.00112 | 490 | UNKNOWN | UNKNOWN | RT_MANIFEST |
Imports
mscoree.dll |
Total processes
46
Monitored processes
11
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
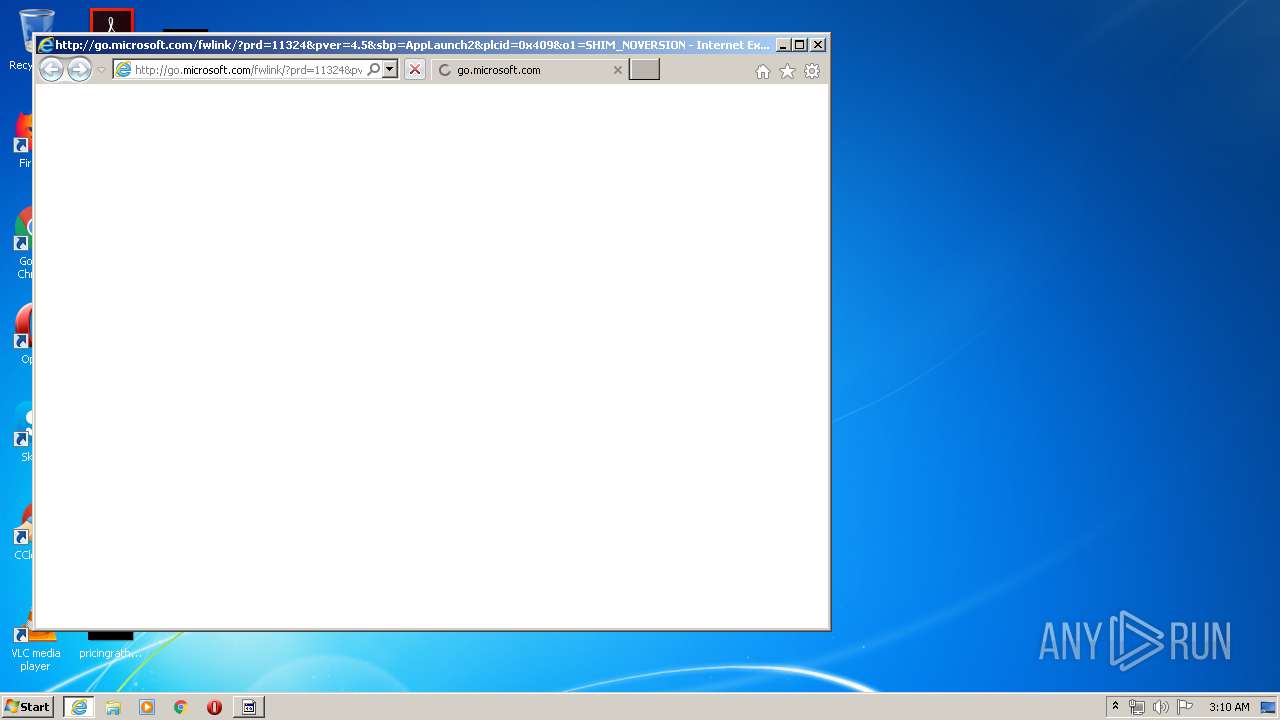
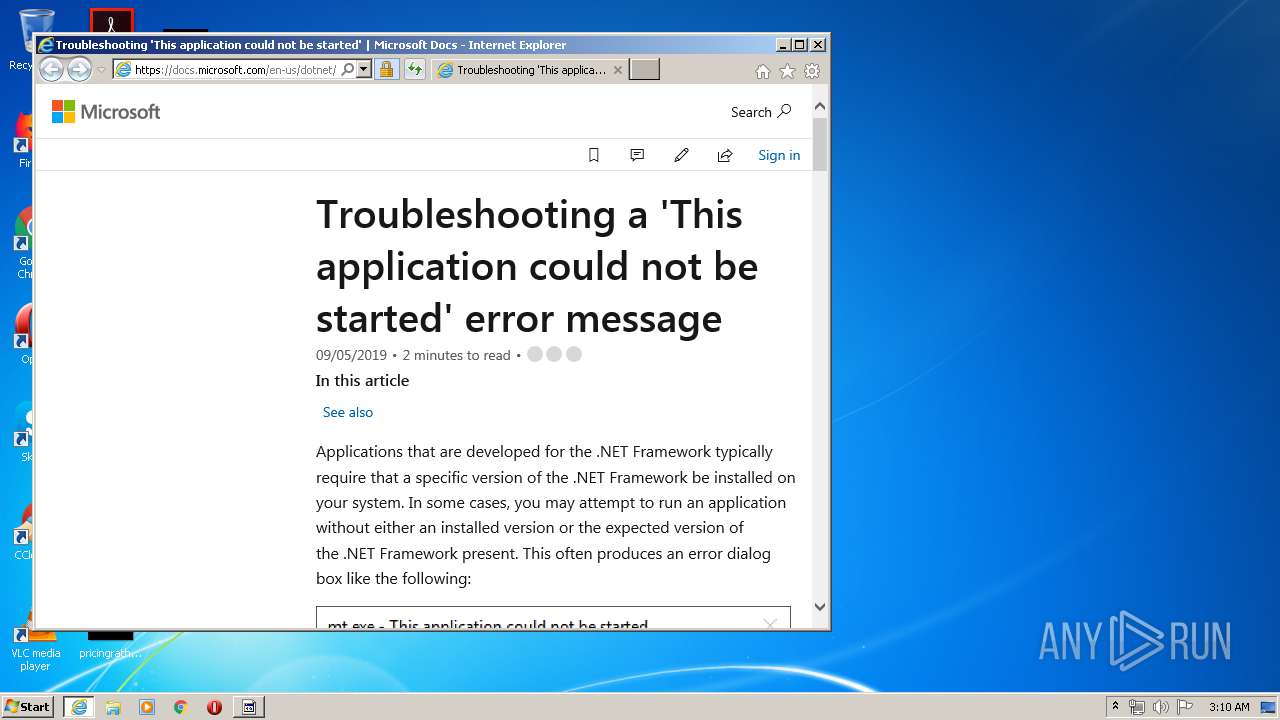
| 540 | "C:\Program Files\Internet Explorer\iexplore.exe" http://go.microsoft.com/fwlink/?prd=11324&pver=4.5&sbp=AppLaunch2&plcid=0x409&o1=SHIM_NOVERSION_FOUND&version=(null)&processName=svchost.exe&platform=0000&osver=5&isServer=0&shimver=4.0.30319.0 | C:\Program Files\Internet Explorer\iexplore.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 820 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:540 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2516 | C:\Windows\system32\svchost.exe | C:\Windows\system32\svchost.exe | — | USD38900.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Host Process for Windows Services Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2664 | C:\Windows\system32\svchost.exe | C:\Windows\system32\svchost.exe | — | USD38900.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Host Process for Windows Services Exit code: 2148734720 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2696 | "{path}" | C:\Users\admin\AppData\Local\Temp\USD38900.EXE | USD38900.EXE | ||||||||||||
User: admin Integrity Level: MEDIUM Description: SudokuSolver Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 2724 | C:\Windows\system32\svchost.exe | C:\Windows\system32\svchost.exe | — | USD38900.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Host Process for Windows Services Exit code: 2148734720 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2820 | C:\Windows\system32\svchost.exe | C:\Windows\system32\svchost.exe | — | USD38900.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Host Process for Windows Services Exit code: 2148734720 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2948 | "C:\Windows\System32\schtasks.exe" /Create /TN "Updates\mnpRWGHeiLUUV" /XML "C:\Users\admin\AppData\Local\Temp\tmp6B84.tmp" | C:\Windows\System32\schtasks.exe | — | USD38900.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Manages scheduled tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3076 | C:\Windows\system32\svchost.exe | C:\Windows\system32\svchost.exe | — | USD38900.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Host Process for Windows Services Exit code: 2148734720 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3136 | C:\Windows\system32\svchost.exe | C:\Windows\system32\svchost.exe | — | USD38900.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Host Process for Windows Services Exit code: 2148734720 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
5 963
Read events
761
Write events
3 482
Delete events
1 720
Modification events
| (PID) Process: | (3580) USD38900.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3580) USD38900.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2696) USD38900.EXE | Key: | HKEY_CURRENT_USER\Software\Remcos-SPSHQY |
| Operation: | write | Name: | exepath |
Value: 75F9C5A7D9727312DE16FE7B4E39DB7C4046E8315975C40029B89E11945F9F376781324DA85A712AAD74CA9E37574C78E00F0CC81654A9697A3003215BC3CD26FECB6BAE11656A36845C87F4B3296CBF79BF5F4F57E5C9C1E306C30B8442 | |||
| (PID) Process: | (2696) USD38900.EXE | Key: | HKEY_CURRENT_USER\Software\Remcos-SPSHQY |
| Operation: | write | Name: | licence |
Value: FCAD3D99840B2D67C081EC973A1A6057 | |||
| (PID) Process: | (2696) USD38900.EXE | Key: | HKEY_CURRENT_USER\Software\Remcos-SPSHQY |
| Operation: | write | Name: | WD |
Value: 2696 | |||
| (PID) Process: | (2820) svchost.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Shell Extensions\Cached |
| Operation: | write | Name: | {17FE9752-0B5A-4665-84CD-569794602F5C} {7F9185B0-CB92-43C5-80A9-92277A4F7B54} 0xFFFF |
Value: 0100000000000000FCA6169D0107D601 | |||
| (PID) Process: | (540) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 2937069952 | |||
| (PID) Process: | (540) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30803713 | |||
| (PID) Process: | (540) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (540) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
Executable files
1
Suspicious files
62
Text files
34
Unknown types
26
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 820 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Cab9284.tmp | — | |
MD5:— | SHA256:— | |||
| 820 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Tar9285.tmp | — | |
MD5:— | SHA256:— | |||
| 3580 | USD38900.EXE | C:\Users\admin\AppData\Roaming\mnpRWGHeiLUUV.exe | executable | |
MD5:— | SHA256:— | |||
| 820 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\6BADA8974A10C4BD62CC921D13E43B18_88614FFAD35D353421B8A7E1FE18FCE4 | der | |
MD5:— | SHA256:— | |||
| 2696 | USD38900.EXE | C:\Users\admin\AppData\Roaming\remcos\logs.dat | binary | |
MD5:— | SHA256:— | |||
| 820 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\application-not-started[1].htm | html | |
MD5:— | SHA256:— | |||
| 820 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\YTOWV792\672b4bb0.conceptual[1].css | text | |
MD5:— | SHA256:— | |||
| 820 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\6BADA8974A10C4BD62CC921D13E43B18_D9817BD5013875AD517DA73475345203 | der | |
MD5:— | SHA256:— | |||
| 3580 | USD38900.EXE | C:\Users\admin\AppData\Local\Temp\tmp6B84.tmp | xml | |
MD5:— | SHA256:— | |||
| 820 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\6BADA8974A10C4BD62CC921D13E43B18_88614FFAD35D353421B8A7E1FE18FCE4 | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
26
TCP/UDP connections
82
DNS requests
26
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
820 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8sEMlbBsCTf7jUSfg%2BhWk%3D | US | der | 1.47 Kb | whitelisted |
820 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRJ9L2KGL92BpjF3kAtaDtxauTmhgQUPdNQpdagre7zSmAKZdMh1Pj41g8CEAoGMEJ%2FW7ztaVc5ZZO2RR8%3D | US | der | 471 b | whitelisted |
820 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEAtqs7A%2Bsan2xGCSaqjN%2FrM%3D | US | der | 1.47 Kb | whitelisted |
820 | iexplore.exe | GET | 200 | 104.18.20.226:80 | http://ocsp.globalsign.com/rootr1/ME8wTTBLMEkwRzAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCDkbwjNvPLFRm7zMB3V80 | US | der | 1.49 Kb | whitelisted |
820 | iexplore.exe | GET | 200 | 104.18.20.226:80 | http://ocsp.globalsign.com/rootr1/ME8wTTBLMEkwRzAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCDkbwjNvPLFRm7zMB3V80 | US | der | 1.49 Kb | whitelisted |
820 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8sEMlbBsCTf7jUSfg%2BhWk%3D | US | der | 1.47 Kb | whitelisted |
820 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEAtqs7A%2Bsan2xGCSaqjN%2FrM%3D | US | der | 1.47 Kb | whitelisted |
820 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfqhLjKLEJQZPin0KCzkdAQpVYowQUsT7DaQP4v0cB1JgmGggC72NkK8MCEAx5qUSwjBGVIJJhX%2BJrHYM%3D | US | der | 471 b | whitelisted |
820 | iexplore.exe | GET | 200 | 216.58.210.3:80 | http://ocsp.pki.goog/gts1o1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEFeh1L3VO0beCAAAAAAyCgc%3D | US | der | 471 b | whitelisted |
820 | iexplore.exe | GET | 304 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEAtqs7A%2Bsan2xGCSaqjN%2FrM%3D | US | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2696 | USD38900.EXE | 185.140.53.154:8760 | — | myLoc managed IT AG | DE | malicious |
820 | iexplore.exe | 104.111.238.86:80 | go.microsoft.com | Akamai International B.V. | NL | whitelisted |
820 | iexplore.exe | 92.123.151.23:443 | docs.microsoft.com | Akamai Technologies, Inc. | — | unknown |
820 | iexplore.exe | 152.199.19.160:443 | ajax.aspnetcdn.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
820 | iexplore.exe | 104.111.243.151:443 | static.docs.com | Akamai International B.V. | NL | unknown |
820 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
820 | iexplore.exe | 104.18.20.226:80 | ocsp.globalsign.com | Cloudflare Inc | US | shared |
— | — | 151.101.2.217:443 | cdn.speedcurve.com | Fastly | US | suspicious |
820 | iexplore.exe | 204.79.197.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
820 | iexplore.exe | 13.225.87.148:80 | o.ss2.us | — | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
go.microsoft.com |
| whitelisted |
docs.microsoft.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
ajax.aspnetcdn.com |
| whitelisted |
static.docs.com |
| suspicious |
az725175.vo.msecnd.net |
| whitelisted |
web.vortex.data.microsoft.com |
| whitelisted |
c1.microsoft.com |
| whitelisted |
github.com |
| malicious |
www.google-analytics.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
820 | iexplore.exe | A Network Trojan was detected | AV TROJAN Samas Ransom CnC Beacon |