| File name: | 74b7bf0e893610d5503068c61fdb05d8b48da82aa10c073a4027dfc34fd9f141.bin |
| Full analysis: | https://app.any.run/tasks/a3894f01-a935-4b23-a151-dc12128b6f5b |
| Verdict: | Malicious activity |
| Threats: | Amadey is a formidable Windows infostealer threat, characterized by its persistence mechanisms, modular design, and ability to execute various malicious tasks. |
| Analysis date: | June 21, 2025, 18:03:23 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 7 sections |
| MD5: | B440EFF46B4EB01391403D79BA7DFB7B |
| SHA1: | AD814FD3B68B0F0FE9EB0821C79D053A8AB755C8 |
| SHA256: | 74B7BF0E893610D5503068C61FDB05D8B48DA82AA10C073A4027DFC34FD9F141 |
| SSDEEP: | 98304:zkzBWS/3OpLspKc3uNy7eqtrfSCpxkbzRcXGdHFHR+JcDEKnSxseMJTtWJ:Vt |
MALICIOUS
LUMMA mutex has been found
- 74b7bf0e893610d5503068c61fdb05d8b48da82aa10c073a4027dfc34fd9f141.bin.exe (PID: 6004)
- MSBuild.exe (PID: 9044)
LUMMA has been detected (YARA)
- 74b7bf0e893610d5503068c61fdb05d8b48da82aa10c073a4027dfc34fd9f141.bin.exe (PID: 6004)
Steals credentials from Web Browsers
- 74b7bf0e893610d5503068c61fdb05d8b48da82aa10c073a4027dfc34fd9f141.bin.exe (PID: 6004)
- MSBuild.exe (PID: 1164)
Actions looks like stealing of personal data
- 74b7bf0e893610d5503068c61fdb05d8b48da82aa10c073a4027dfc34fd9f141.bin.exe (PID: 6004)
- MSBuild.exe (PID: 1164)
AMADEY mutex has been found
- ramez.exe (PID: 5564)
- ramez.exe (PID: 5232)
- YAW73OBHW69MMTDXGY4M5.exe (PID: 3936)
- ramez.exe (PID: 8744)
Connects to the CnC server
- ramez.exe (PID: 5564)
- svchost.exe (PID: 2200)
AMADEY has been detected (SURICATA)
- ramez.exe (PID: 5564)
AMADEY has been detected (YARA)
- ramez.exe (PID: 5564)
VIDAR mutex has been found
- MSBuild.exe (PID: 1164)
PUREHVNC has been detected (YARA)
- MSBuild.exe (PID: 6164)
LCLIPPER mutex has been found
- 288801f818.exe (PID: 1484)
- GoogleChrome.exe (PID: 6172)
- GoogleChrome.exe (PID: 1028)
Changes the autorun value in the registry
- 288801f818.exe (PID: 1484)
- reg.exe (PID: 7292)
- reg.exe (PID: 7388)
- reg.exe (PID: 8060)
Executing a file with an untrusted certificate
- blOahSM.exe (PID: 7660)
- blOahSM.exe (PID: 7740)
- EG11t89.exe (PID: 6772)
- EG11t89.exe (PID: 8740)
Run PowerShell with an invisible window
- powershell.exe (PID: 8476)
- powershell.exe (PID: 8856)
Changes powershell execution policy
- wscript.exe (PID: 8416)
- powershell.exe (PID: 8476)
Uses Task Scheduler to run other applications
- EG11t89.exe (PID: 6772)
- Client.exe (PID: 6364)
- XClient.exe (PID: 7092)
STEGOCAMPAIGN has been detected
- powershell.exe (PID: 8856)
Runs injected code in another process
- EG11t89.exe (PID: 8740)
Downloads the requested resource (POWERSHELL)
- powershell.exe (PID: 8856)
Application was injected by another process
- explorer.exe (PID: 4772)
LUMMA has been detected (SURICATA)
- svchost.exe (PID: 2200)
- MSBuild.exe (PID: 9044)
QUASAR mutex has been found
- AddInProcess32.exe (PID: 8456)
Dynamically loads an assembly (POWERSHELL)
- powershell.exe (PID: 8856)
Create files in the Startup directory
- Client.exe (PID: 6364)
- XClient.exe (PID: 7092)
STEALC has been detected
- MSBuild.exe (PID: 8760)
REVERSELOADER has been detected (SURICATA)
- powershell.exe (PID: 8856)
SUSPICIOUS
Reads the BIOS version
- 74b7bf0e893610d5503068c61fdb05d8b48da82aa10c073a4027dfc34fd9f141.bin.exe (PID: 6004)
- YAW73OBHW69MMTDXGY4M5.exe (PID: 3936)
- ramez.exe (PID: 5564)
- ramez.exe (PID: 5232)
- 288801f818.exe (PID: 1484)
- GoogleChrome.exe (PID: 6172)
- GoogleChrome.exe (PID: 1028)
Connects to the server without a host name
- 74b7bf0e893610d5503068c61fdb05d8b48da82aa10c073a4027dfc34fd9f141.bin.exe (PID: 6004)
- ramez.exe (PID: 5564)
- powershell.exe (PID: 8856)
- MSBuild.exe (PID: 8760)
Process requests binary or script from the Internet
- 74b7bf0e893610d5503068c61fdb05d8b48da82aa10c073a4027dfc34fd9f141.bin.exe (PID: 6004)
- ramez.exe (PID: 5564)
Executable content was dropped or overwritten
- 74b7bf0e893610d5503068c61fdb05d8b48da82aa10c073a4027dfc34fd9f141.bin.exe (PID: 6004)
- YAW73OBHW69MMTDXGY4M5.exe (PID: 3936)
- ramez.exe (PID: 5564)
- 288801f818.exe (PID: 1484)
- winservicex32.exe (PID: 2780)
- blOahSM.exe (PID: 7740)
- csc.exe (PID: 7684)
- csc.exe (PID: 7744)
- csc.exe (PID: 8656)
- csc.exe (PID: 8800)
- csc.exe (PID: 8992)
- csc.exe (PID: 8880)
- lab.exe (PID: 9168)
- lab.exe (PID: 9192)
- EG11t89.exe (PID: 6772)
- Python.exe (PID: 7504)
- MSBuild.exe (PID: 8132)
- XClient.exe (PID: 7092)
Reads security settings of Internet Explorer
- YAW73OBHW69MMTDXGY4M5.exe (PID: 3936)
- ramez.exe (PID: 5564)
- MSBuild.exe (PID: 1164)
- 288801f818.exe (PID: 1484)
- GoogleChrome.exe (PID: 6172)
- blOahSM.exe (PID: 7660)
- blOahSM.exe (PID: 7740)
- AutoIt3_x64.exe (PID: 7808)
Searches for installed software
- 74b7bf0e893610d5503068c61fdb05d8b48da82aa10c073a4027dfc34fd9f141.bin.exe (PID: 6004)
- MSBuild.exe (PID: 1164)
Contacting a server suspected of hosting an CnC
- ramez.exe (PID: 5564)
- svchost.exe (PID: 2200)
- MSBuild.exe (PID: 9044)
There is functionality for taking screenshot (YARA)
- ramez.exe (PID: 5564)
Starts itself from another location
- YAW73OBHW69MMTDXGY4M5.exe (PID: 3936)
- winservicex32.exe (PID: 2780)
There is functionality for enable RDP (YARA)
- ramez.exe (PID: 5564)
Starts a Microsoft application from unusual location
- winservicex32.exe (PID: 6636)
- 4eTHv9F.exe (PID: 4236)
- winservicex32.exe (PID: 2780)
- v999f8.exe (PID: 4804)
- 4TQHprw.exe (PID: 7672)
- 08IyOOF.exe (PID: 1944)
- nxTpPrk.exe (PID: 1136)
Potential Corporate Privacy Violation
- ramez.exe (PID: 5564)
- 74b7bf0e893610d5503068c61fdb05d8b48da82aa10c073a4027dfc34fd9f141.bin.exe (PID: 6004)
Process drops legitimate windows executable
- ramez.exe (PID: 5564)
- winservicex32.exe (PID: 2780)
- blOahSM.exe (PID: 7740)
- lab.exe (PID: 9168)
- lab.exe (PID: 9192)
- Python.exe (PID: 7504)
Application launched itself
- winservicex32.exe (PID: 6636)
- cmd.exe (PID: 4224)
- blOahSM.exe (PID: 7660)
- upgngcodhcfv.exe (PID: 7528)
- upgngcodhcfv.exe (PID: 7452)
- lab.exe (PID: 9168)
- EG11t89.exe (PID: 6772)
- powershell.exe (PID: 8476)
Connects to unusual port
- MSBuild.exe (PID: 6164)
- AddInProcess32.exe (PID: 8456)
Checks for external IP
- svchost.exe (PID: 2200)
- 09NlD7c.exe (PID: 5612)
- 288801f818.exe (PID: 1484)
- GoogleChrome.exe (PID: 6172)
- AddInProcess32.exe (PID: 8456)
Process communicates with Telegram (possibly using it as an attacker's C2 server)
- MSBuild.exe (PID: 1164)
- GoogleChrome.exe (PID: 6172)
The process executes via Task Scheduler
- ramez.exe (PID: 5232)
- ramez.exe (PID: 8744)
- salie.exe (PID: 7740)
- Client.exe (PID: 9004)
Starts CMD.EXE for commands execution
- 288801f818.exe (PID: 1484)
- cmd.exe (PID: 4224)
- blOahSM.exe (PID: 7740)
- lab.exe (PID: 9192)
- 4TQHprw.exe (PID: 7672)
Runs PING.EXE to delay simulation
- cmd.exe (PID: 5644)
The executable file from the user directory is run by the CMD process
- GoogleChrome.exe (PID: 6172)
- Python.exe (PID: 7504)
Reads the date of Windows installation
- jzQILRF.exe (PID: 7220)
- blOahSM.exe (PID: 7660)
- blOahSM.exe (PID: 7740)
Uses REG/REGEDIT.EXE to modify registry
- winservicex32.exe (PID: 2780)
- upgngcodhcfv.exe (PID: 7876)
- upgngcodhcfv.exe (PID: 7968)
The process bypasses the loading of PowerShell profile settings
- MSBuild.exe (PID: 1164)
The process drops C-runtime libraries
- blOahSM.exe (PID: 7740)
- lab.exe (PID: 9168)
- lab.exe (PID: 9192)
- Python.exe (PID: 7504)
Starts the AutoIt3 executable file
- blOahSM.exe (PID: 7740)
The process hide an interactive prompt from the user
- MSBuild.exe (PID: 1164)
Starts POWERSHELL.EXE for commands execution
- MSBuild.exe (PID: 1164)
- wscript.exe (PID: 8416)
- powershell.exe (PID: 8476)
Base64-obfuscated command line is found
- MSBuild.exe (PID: 1164)
BASE64 encoded PowerShell command has been detected
- MSBuild.exe (PID: 1164)
Executing commands from ".cmd" file
- blOahSM.exe (PID: 7740)
Uses base64 encoding (POWERSHELL)
- powershell.exe (PID: 7376)
- powershell.exe (PID: 4324)
- powershell.exe (PID: 8116)
- powershell.exe (PID: 7860)
- powershell.exe (PID: 8300)
- powershell.exe (PID: 4560)
- powershell.exe (PID: 8476)
- powershell.exe (PID: 8856)
Gets content of a file (POWERSHELL)
- powershell.exe (PID: 7376)
- powershell.exe (PID: 4324)
- powershell.exe (PID: 7860)
- powershell.exe (PID: 8116)
- powershell.exe (PID: 4560)
- powershell.exe (PID: 8300)
CSC.EXE is used to compile C# code
- csc.exe (PID: 7744)
- csc.exe (PID: 7684)
- csc.exe (PID: 8656)
- csc.exe (PID: 8800)
- csc.exe (PID: 8880)
- csc.exe (PID: 8992)
Process drops python dynamic module
- lab.exe (PID: 9168)
Executing commands from a ".bat" file
- lab.exe (PID: 9192)
Accesses computer name via WMI (SCRIPT)
- wscript.exe (PID: 8416)
The process executes VB scripts
- cmd.exe (PID: 5248)
Probably obfuscated PowerShell command line is found
- wscript.exe (PID: 8416)
Runs shell command (SCRIPT)
- wscript.exe (PID: 8416)
Found IP address in command line
- powershell.exe (PID: 8856)
Get information on the list of running processes
- powershell.exe (PID: 8476)
Probably download files using WebClient
- powershell.exe (PID: 8476)
Gets or sets the security protocol (POWERSHELL)
- powershell.exe (PID: 8856)
Uses TASKKILL.EXE to kill process
- powershell.exe (PID: 8856)
INFO
Checks supported languages
- 74b7bf0e893610d5503068c61fdb05d8b48da82aa10c073a4027dfc34fd9f141.bin.exe (PID: 6004)
- YAW73OBHW69MMTDXGY4M5.exe (PID: 3936)
- ramez.exe (PID: 5564)
- winservicex32.exe (PID: 6636)
- 4eTHv9F.exe (PID: 4236)
- 09NlD7c.exe (PID: 5612)
- winservicex32.exe (PID: 2780)
- MSBuild.exe (PID: 6164)
- ramez.exe (PID: 5232)
- MSBuild.exe (PID: 1164)
- v999f8.exe (PID: 4804)
- 288801f818.exe (PID: 1484)
- GoogleChrome.exe (PID: 6172)
- GoogleChrome.exe (PID: 1028)
- jzQILRF.exe (PID: 7220)
- upgngcodhcfv.exe (PID: 7452)
- upgngcodhcfv.exe (PID: 7528)
- blOahSM.exe (PID: 7660)
- blOahSM.exe (PID: 7740)
- AutoIt3_x64.exe (PID: 7808)
- EG11t89.exe (PID: 6772)
- upgngcodhcfv.exe (PID: 7876)
- upgngcodhcfv.exe (PID: 7968)
- cvtres.exe (PID: 7508)
- csc.exe (PID: 7684)
- csc.exe (PID: 7744)
- cvtres.exe (PID: 8232)
- csc.exe (PID: 8656)
- cvtres.exe (PID: 8760)
- csc.exe (PID: 8800)
- cvtres.exe (PID: 8840)
- csc.exe (PID: 8880)
- cvtres.exe (PID: 8900)
- cvtres.exe (PID: 9044)
Reads the machine GUID from the registry
- 74b7bf0e893610d5503068c61fdb05d8b48da82aa10c073a4027dfc34fd9f141.bin.exe (PID: 6004)
- ramez.exe (PID: 5564)
- MSBuild.exe (PID: 6164)
- 09NlD7c.exe (PID: 5612)
- MSBuild.exe (PID: 1164)
- GoogleChrome.exe (PID: 6172)
- jzQILRF.exe (PID: 7220)
- AutoIt3_x64.exe (PID: 7808)
- EG11t89.exe (PID: 6772)
- csc.exe (PID: 7684)
- csc.exe (PID: 7744)
- csc.exe (PID: 8656)
- csc.exe (PID: 8800)
- csc.exe (PID: 8880)
- csc.exe (PID: 8992)
Reads the software policy settings
- 74b7bf0e893610d5503068c61fdb05d8b48da82aa10c073a4027dfc34fd9f141.bin.exe (PID: 6004)
- ramez.exe (PID: 5564)
- 09NlD7c.exe (PID: 5612)
- MSBuild.exe (PID: 1164)
- GoogleChrome.exe (PID: 6172)
- powershell.exe (PID: 3100)
- jzQILRF.exe (PID: 7220)
- slui.exe (PID: 3716)
- powershell.exe (PID: 7912)
- powershell.exe (PID: 4324)
- powershell.exe (PID: 7564)
- powershell.exe (PID: 8048)
- powershell.exe (PID: 7376)
- powershell.exe (PID: 6392)
- powershell.exe (PID: 7860)
- powershell.exe (PID: 8116)
- powershell.exe (PID: 7528)
- powershell.exe (PID: 4560)
- powershell.exe (PID: 8460)
Reads the computer name
- 74b7bf0e893610d5503068c61fdb05d8b48da82aa10c073a4027dfc34fd9f141.bin.exe (PID: 6004)
- YAW73OBHW69MMTDXGY4M5.exe (PID: 3936)
- ramez.exe (PID: 5564)
- 09NlD7c.exe (PID: 5612)
- MSBuild.exe (PID: 6164)
- MSBuild.exe (PID: 1164)
- 288801f818.exe (PID: 1484)
- GoogleChrome.exe (PID: 6172)
- jzQILRF.exe (PID: 7220)
- blOahSM.exe (PID: 7660)
- blOahSM.exe (PID: 7740)
- AutoIt3_x64.exe (PID: 7808)
- EG11t89.exe (PID: 6772)
Application launched itself
- chrome.exe (PID: 6384)
- chrome.exe (PID: 5564)
- chrome.exe (PID: 1948)
- chrome.exe (PID: 4088)
- msedge.exe (PID: 2620)
- msedge.exe (PID: 6292)
- msedge.exe (PID: 5764)
- msedge.exe (PID: 7160)
- msedge.exe (PID: 2532)
- msedge.exe (PID: 3724)
- chrome.exe (PID: 5456)
- chrome.exe (PID: 7904)
- chrome.exe (PID: 8036)
- chrome.exe (PID: 8184)
- chrome.exe (PID: 7352)
- chrome.exe (PID: 7556)
- chrome.exe (PID: 188)
- chrome.exe (PID: 8044)
- chrome.exe (PID: 7812)
- chrome.exe (PID: 7584)
- chrome.exe (PID: 8288)
- chrome.exe (PID: 8448)
- chrome.exe (PID: 4800)
- msedge.exe (PID: 8028)
- msedge.exe (PID: 8032)
- chrome.exe (PID: 3644)
- chrome.exe (PID: 8996)
Themida protector has been detected
- 74b7bf0e893610d5503068c61fdb05d8b48da82aa10c073a4027dfc34fd9f141.bin.exe (PID: 6004)
- ramez.exe (PID: 5564)
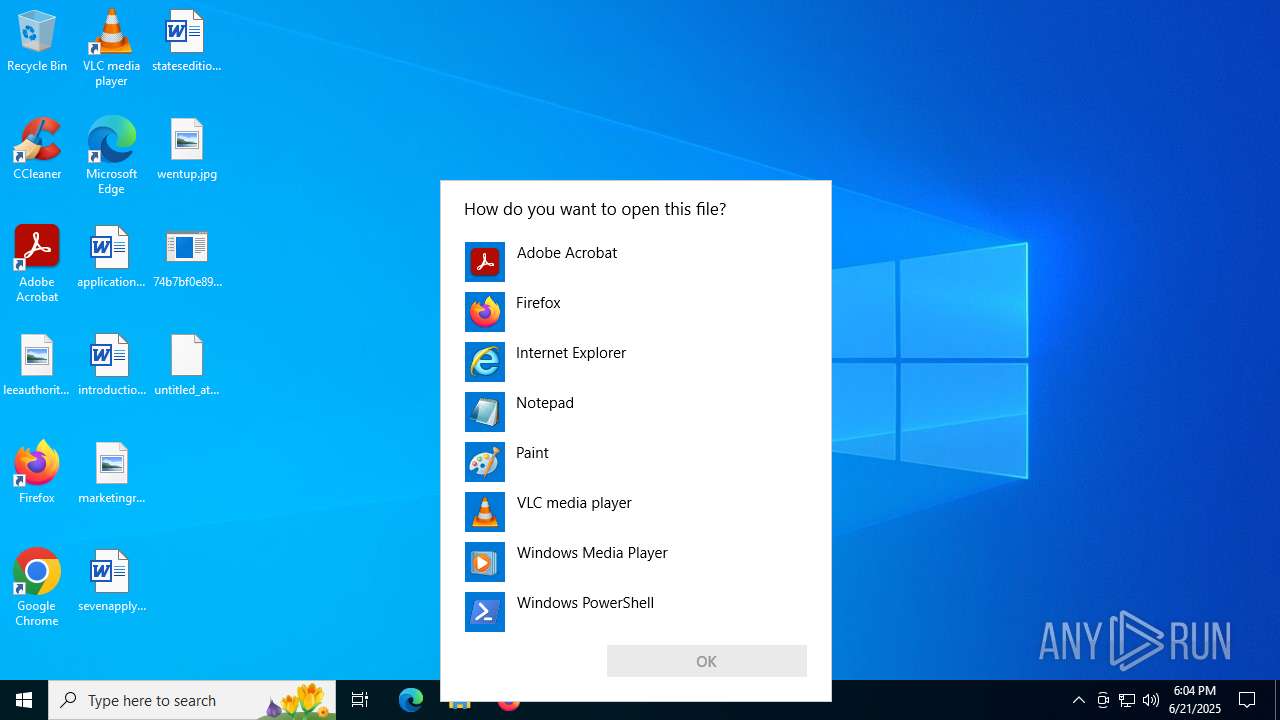
Manual execution by a user
- OpenWith.exe (PID: 1232)
- GoogleChrome.exe (PID: 1028)
- upgngcodhcfv.exe (PID: 7528)
Create files in a temporary directory
- 74b7bf0e893610d5503068c61fdb05d8b48da82aa10c073a4027dfc34fd9f141.bin.exe (PID: 6004)
- YAW73OBHW69MMTDXGY4M5.exe (PID: 3936)
- ramez.exe (PID: 5564)
- MSBuild.exe (PID: 1164)
- powershell.exe (PID: 3100)
- blOahSM.exe (PID: 7740)
- AutoIt3_x64.exe (PID: 7808)
- powershell.exe (PID: 8048)
- powershell.exe (PID: 7912)
- powershell.exe (PID: 4324)
- powershell.exe (PID: 7564)
- powershell.exe (PID: 7376)
- powershell.exe (PID: 6392)
- powershell.exe (PID: 8116)
- powershell.exe (PID: 7528)
- cvtres.exe (PID: 7508)
- cvtres.exe (PID: 8232)
- csc.exe (PID: 7684)
- csc.exe (PID: 7744)
- powershell.exe (PID: 4560)
- powershell.exe (PID: 8300)
- powershell.exe (PID: 8460)
- csc.exe (PID: 8656)
- cvtres.exe (PID: 8760)
- powershell.exe (PID: 7860)
- csc.exe (PID: 8800)
- cvtres.exe (PID: 8840)
- cvtres.exe (PID: 8900)
- csc.exe (PID: 8880)
- csc.exe (PID: 8992)
- lab.exe (PID: 9168)
- cvtres.exe (PID: 9044)
- lab.exe (PID: 9192)
- 4TQHprw.exe (PID: 7672)
- EG11t89.exe (PID: 6772)
- powershell.exe (PID: 8856)
Reads security settings of Internet Explorer
- explorer.exe (PID: 4772)
- powershell.exe (PID: 3100)
- powershell.exe (PID: 7912)
- powershell.exe (PID: 7376)
- powershell.exe (PID: 8048)
- powershell.exe (PID: 7564)
- powershell.exe (PID: 4324)
- powershell.exe (PID: 6392)
- powershell.exe (PID: 8116)
- powershell.exe (PID: 7860)
- powershell.exe (PID: 7528)
- powershell.exe (PID: 8460)
- powershell.exe (PID: 4560)
- powershell.exe (PID: 8300)
Checks proxy server information
- ramez.exe (PID: 5564)
- 09NlD7c.exe (PID: 5612)
- MSBuild.exe (PID: 1164)
- 288801f818.exe (PID: 1484)
- GoogleChrome.exe (PID: 6172)
- jzQILRF.exe (PID: 7220)
- slui.exe (PID: 3716)
Process checks computer location settings
- YAW73OBHW69MMTDXGY4M5.exe (PID: 3936)
- ramez.exe (PID: 5564)
- blOahSM.exe (PID: 7660)
- blOahSM.exe (PID: 7740)
The sample compiled with english language support
- ramez.exe (PID: 5564)
- winservicex32.exe (PID: 2780)
- blOahSM.exe (PID: 7740)
- lab.exe (PID: 9168)
- lab.exe (PID: 9192)
- Python.exe (PID: 7504)
Creates files or folders in the user directory
- ramez.exe (PID: 5564)
- MSBuild.exe (PID: 1164)
- 288801f818.exe (PID: 1484)
- GoogleChrome.exe (PID: 6172)
- winservicex32.exe (PID: 2780)
- EG11t89.exe (PID: 6772)
- MSBuild.exe (PID: 8132)
- Client.exe (PID: 6364)
- XClient.exe (PID: 7092)
- explorer.exe (PID: 4772)
Creates files in the program directory
- MSBuild.exe (PID: 1164)
.NET Reactor protector has been detected
- MSBuild.exe (PID: 6164)
Reads Microsoft Office registry keys
- OpenWith.exe (PID: 1232)
Launching a file from a Registry key
- 288801f818.exe (PID: 1484)
- reg.exe (PID: 7388)
- reg.exe (PID: 7292)
- reg.exe (PID: 8060)
Reads product name
- MSBuild.exe (PID: 1164)
Reads CPU info
- MSBuild.exe (PID: 1164)
Reads Environment values
- MSBuild.exe (PID: 1164)
- AutoIt3_x64.exe (PID: 7808)
Converts byte array into ASCII string (POWERSHELL)
- powershell.exe (PID: 3100)
- powershell.exe (PID: 7912)
- powershell.exe (PID: 8048)
- powershell.exe (PID: 7564)
- powershell.exe (PID: 6392)
- powershell.exe (PID: 7528)
- powershell.exe (PID: 8460)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 3100)
- powershell.exe (PID: 8048)
- powershell.exe (PID: 7912)
- powershell.exe (PID: 7564)
- powershell.exe (PID: 6392)
- powershell.exe (PID: 7376)
- powershell.exe (PID: 4324)
- powershell.exe (PID: 7528)
- powershell.exe (PID: 8116)
- powershell.exe (PID: 7860)
- powershell.exe (PID: 8460)
- powershell.exe (PID: 4560)
- powershell.exe (PID: 8300)
- powershell.exe (PID: 8856)
Reads mouse settings
- AutoIt3_x64.exe (PID: 7808)
Uses string replace method (POWERSHELL)
- powershell.exe (PID: 8476)
Converts byte array into Unicode string (POWERSHELL)
- powershell.exe (PID: 8476)
Gets a random number, or selects objects randomly from a collection (POWERSHELL)
- powershell.exe (PID: 8476)
Gets data length (POWERSHELL)
- powershell.exe (PID: 8856)
Launching a file from the Startup directory
- Client.exe (PID: 6364)
- XClient.exe (PID: 7092)
Python executable
- Python.exe (PID: 7504)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Lumma
(PID) Process(6004) 74b7bf0e893610d5503068c61fdb05d8b48da82aa10c073a4027dfc34fd9f141.bin.exe
C2 (9)ropyi.xyz/zadf
skjgx.xyz/riuw
gewgb.xyz/axgh
baviip.xyz/twiw
equidn.xyz/xapq
spjeo.xyz/axka
firddy.xyz/yhbc
shaeb.xyz/ikxz
trqqe.xyz/xudu
Amadey
(PID) Process(5564) ramez.exe
C2185.156.72.96
URLhttp://185.156.72.96/te4h2nus/index.php
Version5.34
Options
Drop directoryd610cf342e
Drop nameramez.exe
Strings (125)Powershell.exe
/te4h2nus/index.php
ramez.exe
bi:
185.156.72.96
AVAST Software
/Plugins/
------
id:
\0000
wb
Programs
-%lu
.jpg
AVG
r=
dm:
-executionpolicy remotesigned -File "
SOFTWARE\Microsoft\Windows NT\CurrentVersion
\
ProgramData\
Avira
e2
os:
http://
vs:
<c>
2025
ComputerName
og:
00000419
rb
2022
Content-Type: application/x-www-form-urlencoded
shell32.dll
https://
Main
Sophos
Norton
GET
#
S-%lu-
st=s
cmd /C RMDIR /s/q
lv:
msi
Content-Disposition: form-data; name="data"; filename="
5.34
d1
2016
ar:
cred.dll|clip.dll|
rundll32
WinDefender
Content-Type: multipart/form-data; boundary=----
Rem
CurrentBuild
0123456789
&& Exit"
un:
Kaspersky Lab
d610cf342e
Bitdefender
+++
av:
rundll32.exe
random
<d>
Keyboard Layout\Preload
shutdown -s -t 0
DefaultSettings.XResolution
/quiet
--
0000043f
Startup
e1
Doctor Web
2019
GetNativeSystemInfo
VideoID
SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\User Shell Folders
SYSTEM\CurrentControlSet\Control\UnitedVideo\CONTROL\VIDEO\
:::
ESET
DefaultSettings.YResolution
SOFTWARE\Microsoft\Windows\CurrentVersion\RunOnce
" && ren
abcdefghijklmnopqrstuvwxyz0123456789-_
cmd
"taskkill /f /im "
00000423
-unicode-
SYSTEM\CurrentControlSet\Control\ComputerName\ComputerName
cred.dll
360TotalSecurity
"
exe
00000422
SOFTWARE\Microsoft\Windows\CurrentVersion\Run
&&
Comodo
"
Content-Type: application/octet-stream
------
?scr=1
SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\Shell Folders
zip
dll
/k
&unit=
ps1
" && timeout 1 && del
kernel32.dll
ProductName
%-lu
clip.dll
%USERPROFILE%
\App
SYSTEM\ControlSet001\Services\BasicDisplay\Video
pc:
sd:
POST
Panda Security
e3
|
=
TRiD
| .exe | | | Generic Win/DOS Executable (50) |
|---|---|---|
| .exe | | | DOS Executable Generic (49.9) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2025:06:16 14:51:43+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 14 |
| CodeSize: | 311296 |
| InitializedDataSize: | 37888 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x48f000 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
Total processes
381
Monitored processes
247
Malicious processes
34
Suspicious processes
15
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 188 | "C:\Program Files\Google\Chrome\Application\chrome.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | — | MSBuild.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 21 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 304 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data" /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Crashpad" --annotation=IsOfficialBuild=1 --annotation=channel= --annotation=chromium-version=133.0.6943.142 "--annotation=exe=C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --annotation=plat=Win64 --annotation=prod=Edge --annotation=ver=133.0.3065.92 --initial-client-data=0x290,0x294,0x298,0x288,0x2a0,0x7ffc4534f208,0x7ffc4534f214,0x7ffc4534f220 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 416 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=gpu-process --string-annotations --gpu-preferences=UAAAAAAAAADgAAAEAAAAAAAAAAAAAAAAAABgAAEAAAAAAAAAAAAAAAAAAAACAAAAAAAAAAAAAAAAAAAAAAAAABAAAAAAAAAAEAAAAAAAAAAIAAAAAAAAAAgAAAAAAAAA --always-read-main-dll --field-trial-handle=2180,i,7947793088315216646,6290140522145081848,262144 --variations-seed-version --mojo-platform-channel-handle=2188 /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 472 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --always-read-main-dll --field-trial-handle=3560,i,15554927266699597839,16055555364832260817,262144 --variations-seed-version --mojo-platform-channel-handle=3656 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 620 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --edge-skip-compat-layer-relaunch | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 768 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win64 --annotation=prod=Chrome --annotation=ver=133.0.6943.127 --initial-client-data=0x220,0x224,0x228,0x1fc,0x22c,0x7ffc4516fff8,0x7ffc45170004,0x7ffc45170010 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 1028 | C:\Users\admin\AppData\Local\GoogleChrome.exe | C:\Users\admin\AppData\Local\GoogleChrome.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1056 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --string-annotations --gpu-preferences=UAAAAAAAAADgAAAEAAAAAAAAAAAAAAAAAABgAAEAAAAAAAAAAAAAAAAAAAACAAAAAAAAAAAAAAAAAAAAAAAAABAAAAAAAAAAEAAAAAAAAAAIAAAAAAAAAAgAAAAAAAAA --field-trial-handle=2144,i,11868809586788631281,4390833379704565529,262144 --variations-seed-version --mojo-platform-channel-handle=2124 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 1096 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win64 --annotation=prod=Chrome --annotation=ver=133.0.6943.127 --initial-client-data=0x220,0x224,0x228,0x1fc,0x22c,0x7ffc44ecfff8,0x7ffc44ed0004,0x7ffc44ed0010 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 1132 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
138 791
Read events
138 629
Write events
158
Delete events
4
Modification events
| (PID) Process: | (4772) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\Shell\Bags\1\Desktop |
| Operation: | write | Name: | IconLayouts |
Value: 0000000000000000000000000000000003000100010001000F000000000000002C000000000000003A003A007B00360034003500460046003000340030002D0035003000380031002D0031003000310042002D0039004600300038002D003000300041004100300030003200460039003500340045007D003E002000200000001000000000000000430043006C00650061006E00650072002E006C006E006B003E0020007C0000001500000000000000410064006F006200650020004100630072006F006200610074002E006C006E006B003E0020007C00000014000000000000006C006500650061007500740068006F0072006900740079002E006A00700067003E002000200000000F00000000000000460069007200650066006F0078002E006C006E006B003E0020007C000000150000000000000047006F006F0067006C00650020004300680072006F006D0065002E006C006E006B003E0020007C000000180000000000000056004C00430020006D006500640069006100200070006C0061007900650072002E006C006E006B003E0020007C00000016000000000000004D006900630072006F0073006F0066007400200045006400670065002E006C006E006B003E0020007C00000016000000000000006100700070006C00690063006100740069006F006E00740065006E002E007200740066003E00200020000000210000000000000069006E00740072006F00640075006300740069006F006E0064006F00630075006D0065006E0074006100740069006F006E002E007200740066003E0020002000000019000000000000006D00610072006B006500740069006E006700720065006C00650061007300650073002E006A00700067003E00200020000000120000000000000073006500760065006E006100700070006C0079002E007200740066003E002000200000001500000000000000730074006100740065007300650064006900740069006F006E002E007200740066003E002000200000000E00000000000000770065006E007400750070002E006A00700067003E002000200000004C0000000000000037003400620037006200660030006500380039003300360031003000640035003500300033003000360038006300360031006600640062003000350064003800620034003800640061003800320061006100310030006300300037003300610034003000320037006400660063003300340066006400390066003100340031002E00620069006E002E006500780065003E00200020000000010000000000000002000100000000000000000001000000000000000200010000000000000000001100000006000000010000000F00000000000000000000000000000000000000803F0000004008000000803F000040400900000000000000404003000000803F000080400A000000803F0000A0400B0000000040000000000C00000000400000803F0D00000000000000803F01000000000000000040020000000000000080400400000000000000A04005000000803F0000000006000000803F0000803F070000000040000000400E00 | |||
| (PID) Process: | (4772) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\Shell\Bags\1\Desktop |
| Operation: | write | Name: | IconNameVersion |
Value: 1 | |||
| (PID) Process: | (4772) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\OneDrive\Accounts |
| Operation: | write | Name: | LastUpdate |
Value: F5F3566800000000 | |||
| (PID) Process: | (6384) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (6384) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (6384) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (6384) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (6384) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (5564) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (5564) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
Executable files
79
Suspicious files
162
Text files
337
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6384 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\ClientCertificates\LOG.old~RF1783e5.TMP | — | |
MD5:— | SHA256:— | |||
| 6384 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\ClientCertificates\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6384 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old~RF1783f5.TMP | — | |
MD5:— | SHA256:— | |||
| 6384 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6384 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Segmentation Platform\SegmentInfoDB\LOG.old~RF178414.TMP | — | |
MD5:— | SHA256:— | |||
| 6384 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF178424.TMP | — | |
MD5:— | SHA256:— | |||
| 6384 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old~RF178424.TMP | — | |
MD5:— | SHA256:— | |||
| 6384 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old~RF178414.TMP | — | |
MD5:— | SHA256:— | |||
| 6384 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6384 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
219
TCP/UDP connections
229
DNS requests
180
Threats
90
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5944 | MoUsoCoreWorker.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5708 | RUXIMICS.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 142.250.185.99:443 | https://clientservices.googleapis.com/chrome-variations/seed?osname=win&channel=stable&milestone=133 | unknown | compressed | 59.2 Kb | whitelisted |
— | — | POST | 200 | 142.250.27.84:443 | https://accounts.google.com/ListAccounts?gpsia=1&source=ChromiumBrowser&json=standard | unknown | text | 17 b | whitelisted |
4012 | chrome.exe | GET | 200 | 142.250.185.206:80 | http://clients2.google.com/time/1/current?cup2key=8:pejhUdzjobBrYqAKu4t9P_lYvLblYyO2tep7aSZP_WA&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | unknown | — | — | whitelisted |
— | — | GET | 200 | 172.217.16.138:443 | https://safebrowsingohttpgateway.googleapis.com/v1/ohttp/hpkekeyconfig?key=AIzaSyA2KlwBX3mkFo30om9LUFYQhpqLoa_BNhE | unknown | binary | 41 b | whitelisted |
— | — | GET | 200 | 172.217.16.196:443 | https://www.google.com/complete/search?client=chrome-omni&gs_ri=chrome-ext-ansg&xssi=t&q=&oit=0&oft=1&pgcl=20&gs_rn=42&sugkey=AIzaSyA2KlwBX3mkFo30om9LUFYQhpqLoa_BNhE | unknown | text | 7.63 Kb | whitelisted |
— | — | GET | 200 | 172.217.16.196:443 | https://www.google.com/async/newtab_promos | unknown | text | 29 b | whitelisted |
— | — | GET | 200 | 172.217.16.196:443 | https://www.google.com/async/ddljson?async=ntp:2 | unknown | text | 19 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1268 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5708 | RUXIMICS.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | 184.24.77.41:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
1268 | svchost.exe | 184.24.77.41:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5708 | RUXIMICS.exe | 184.24.77.41:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
6004 | 74b7bf0e893610d5503068c61fdb05d8b48da82aa10c073a4027dfc34fd9f141.bin.exe | 85.90.196.155:443 | equidn.xyz | — | UA | unknown |
5944 | MoUsoCoreWorker.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
equidn.xyz |
| unknown |
www.microsoft.com |
| whitelisted |
clients2.google.com |
| whitelisted |
safebrowsingohttpgateway.googleapis.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| whitelisted |
www.google.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6004 | 74b7bf0e893610d5503068c61fdb05d8b48da82aa10c073a4027dfc34fd9f141.bin.exe | Potentially Bad Traffic | ET INFO Executable Download from dotted-quad Host |
6004 | 74b7bf0e893610d5503068c61fdb05d8b48da82aa10c073a4027dfc34fd9f141.bin.exe | Potential Corporate Privacy Violation | ET INFO PE EXE or DLL Windows file download HTTP |
6004 | 74b7bf0e893610d5503068c61fdb05d8b48da82aa10c073a4027dfc34fd9f141.bin.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
6004 | 74b7bf0e893610d5503068c61fdb05d8b48da82aa10c073a4027dfc34fd9f141.bin.exe | Misc activity | ET INFO Packed Executable Download |
6004 | 74b7bf0e893610d5503068c61fdb05d8b48da82aa10c073a4027dfc34fd9f141.bin.exe | Potentially Bad Traffic | ET HUNTING SUSPICIOUS Dotted Quad Host MZ Response |
5564 | ramez.exe | Malware Command and Control Activity Detected | BOTNET [ANY.RUN] Amadey HTTP POST Request (st=s) |
5564 | ramez.exe | Malware Command and Control Activity Detected | ET MALWARE Amadey CnC Response |
2200 | svchost.exe | Potentially Bad Traffic | ET INFO DNS Query for Suspicious .icu Domain |
5564 | ramez.exe | Potentially Bad Traffic | ET INFO Suspicious Domain (*.icu) in TLS SNI |
— | — | Potential Corporate Privacy Violation | ET INFO PE EXE or DLL Windows file download HTTP |
Process | Message |
|---|---|
74b7bf0e893610d5503068c61fdb05d8b48da82aa10c073a4027dfc34fd9f141.bin.exe |
%s------------------------------------------------
--- Themida Professional ---
--- (c)2012 Oreans Technologies ---
------------------------------------------------
|