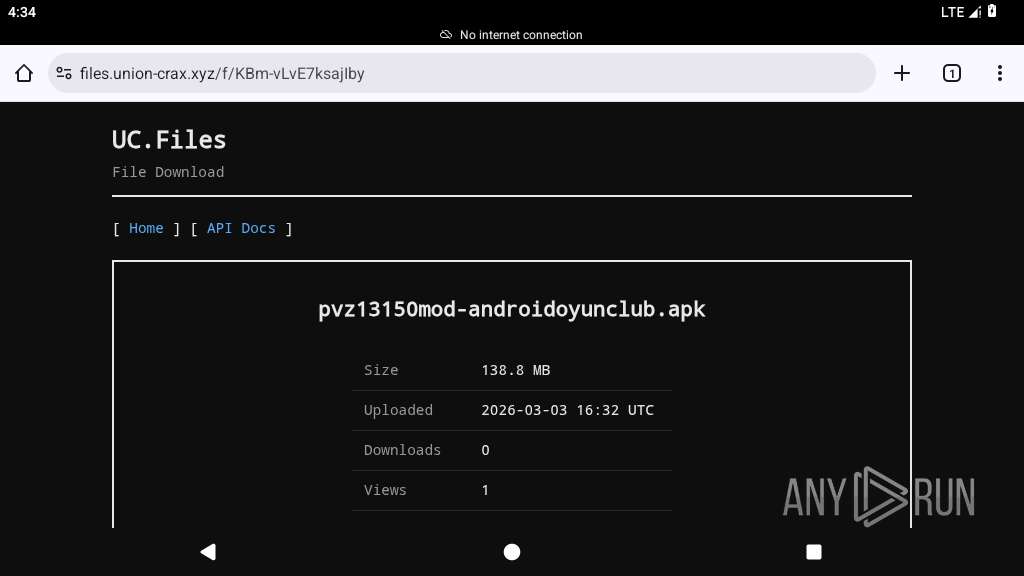
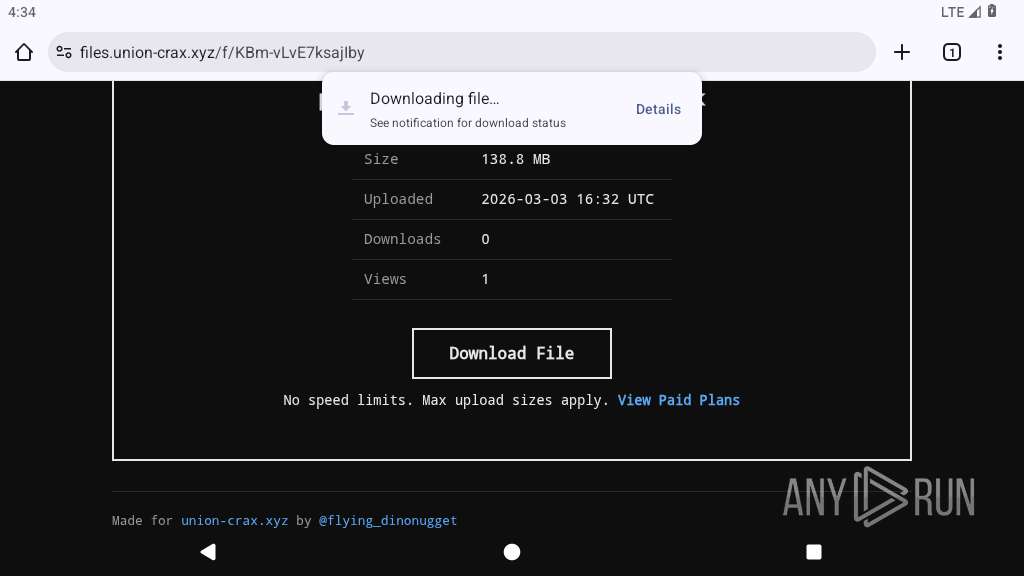
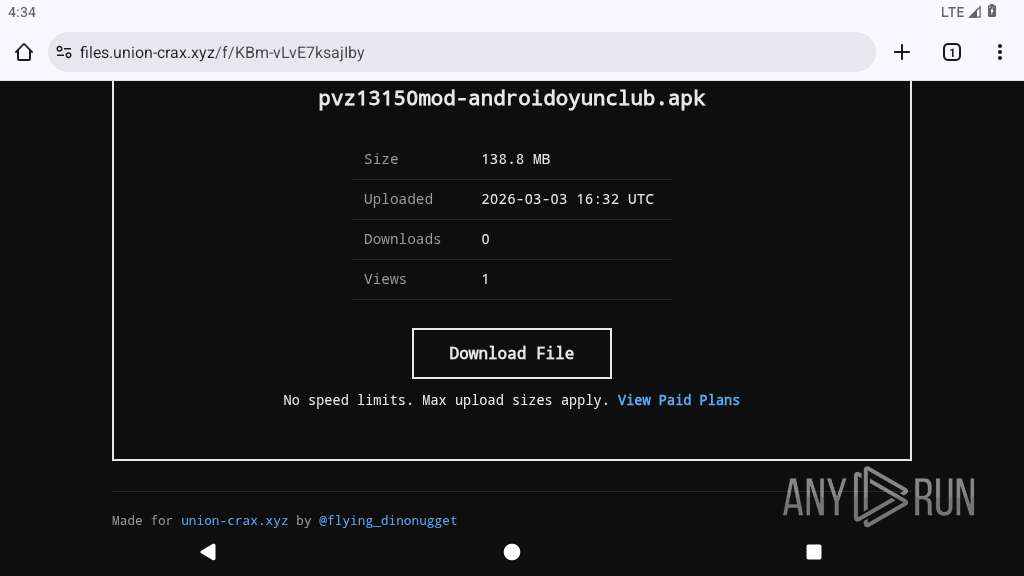
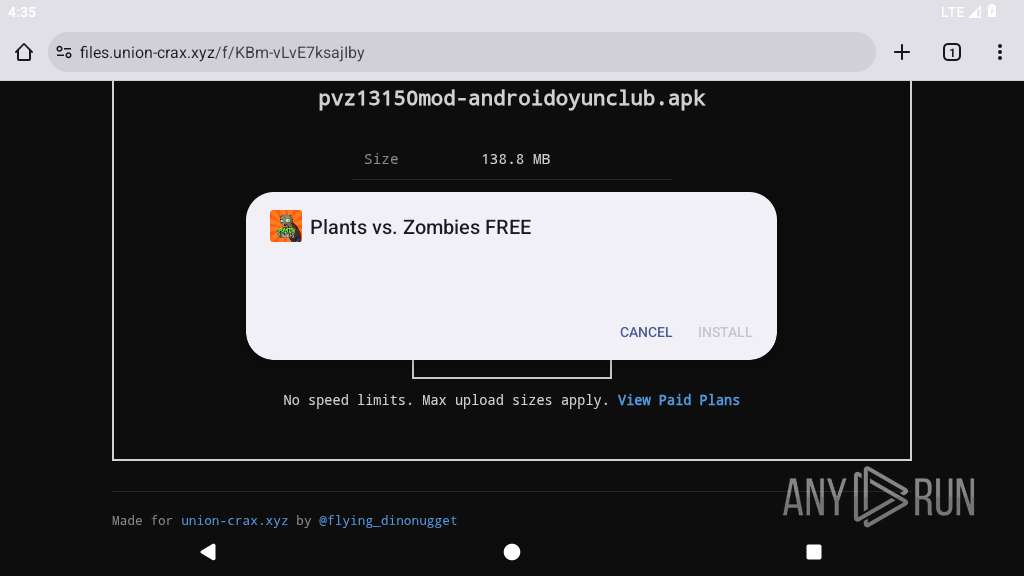
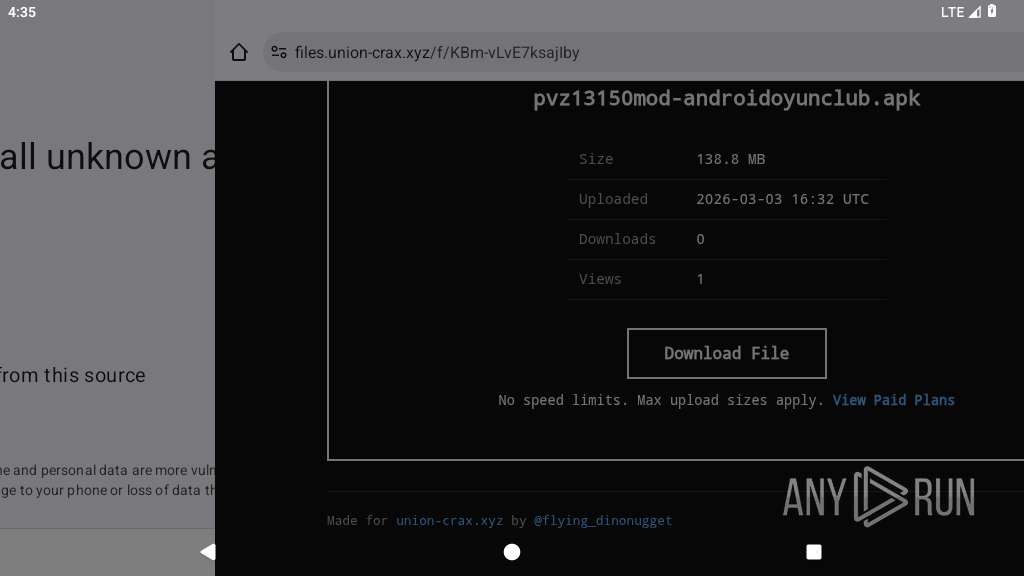
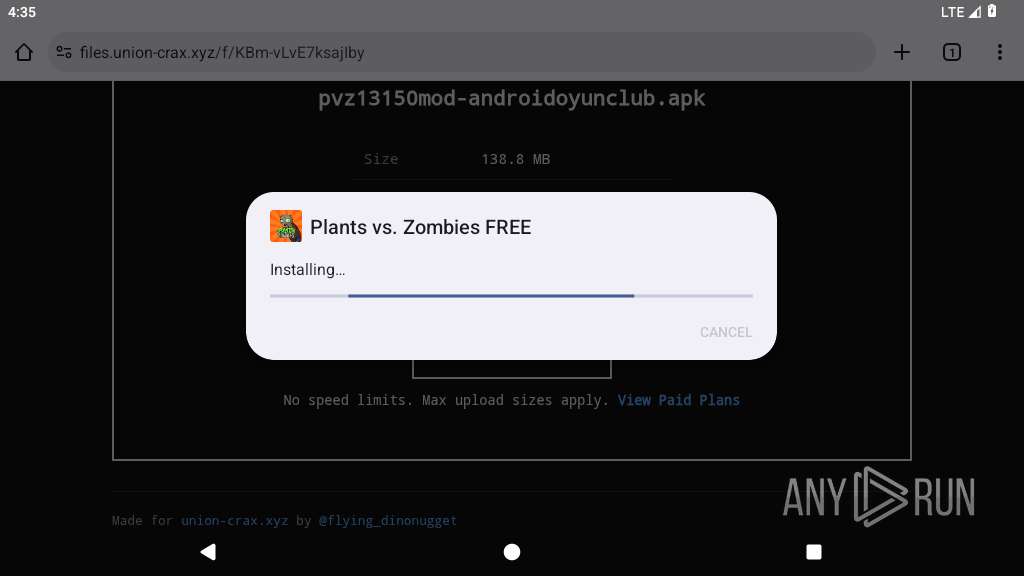
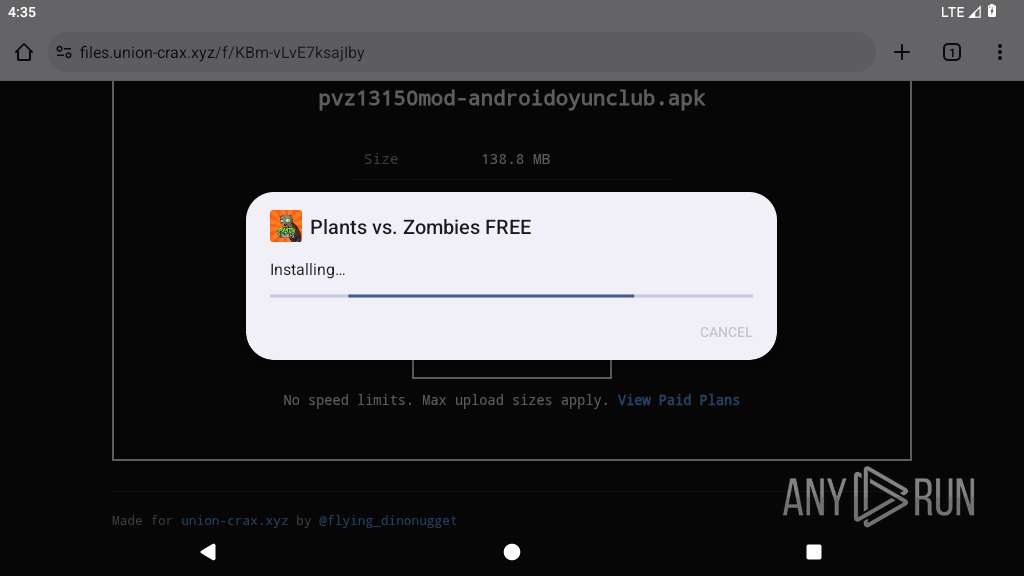
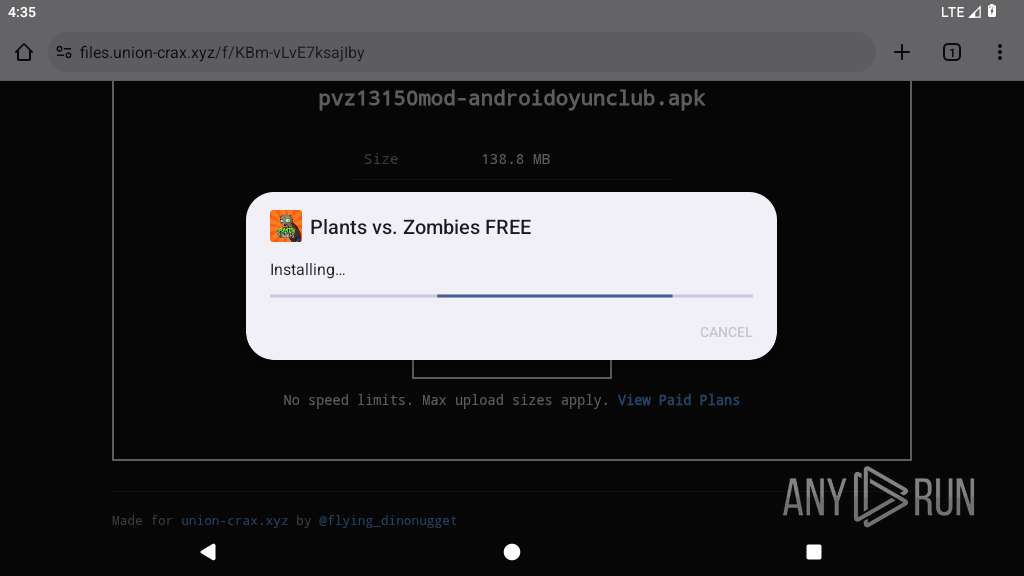
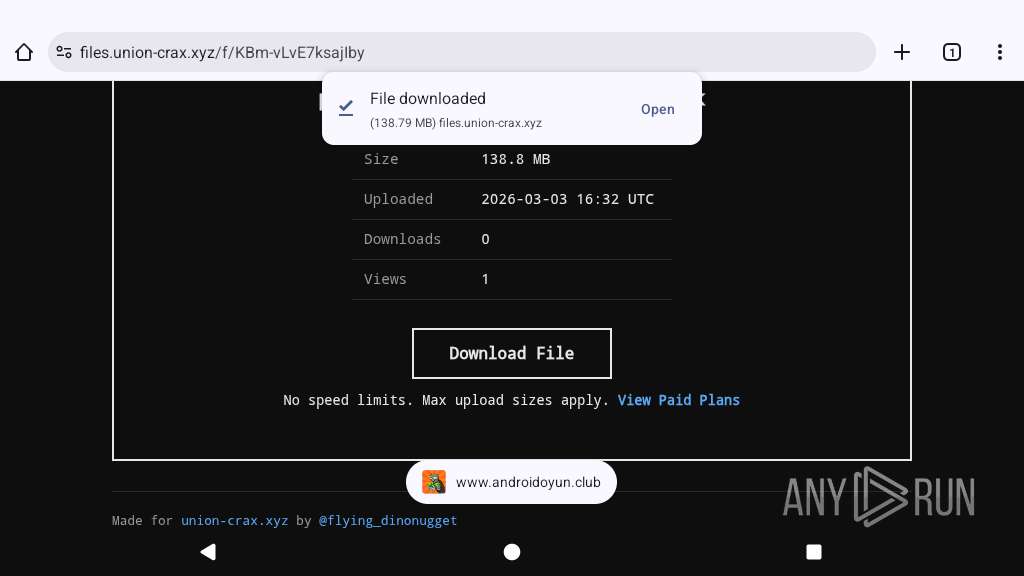
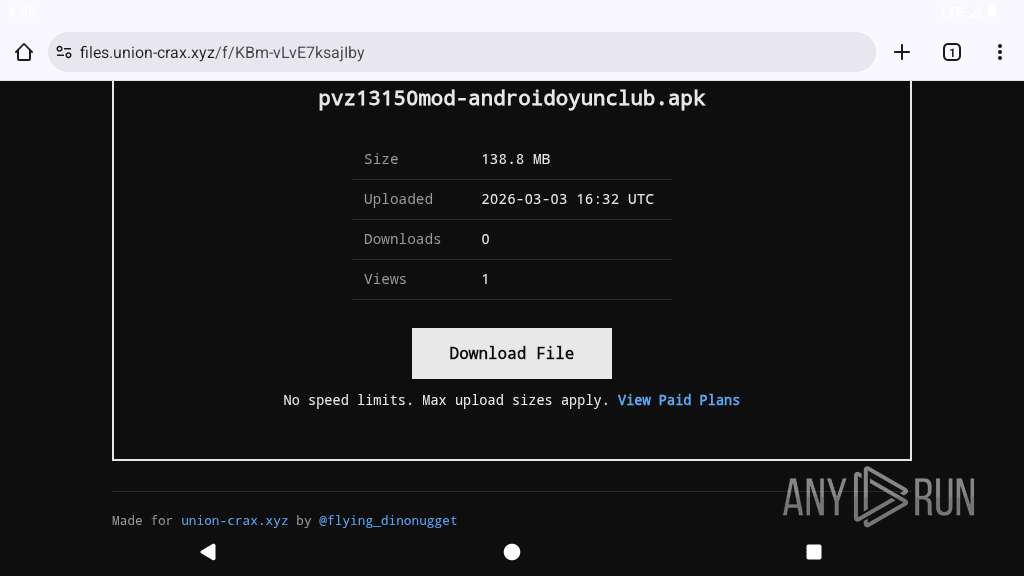
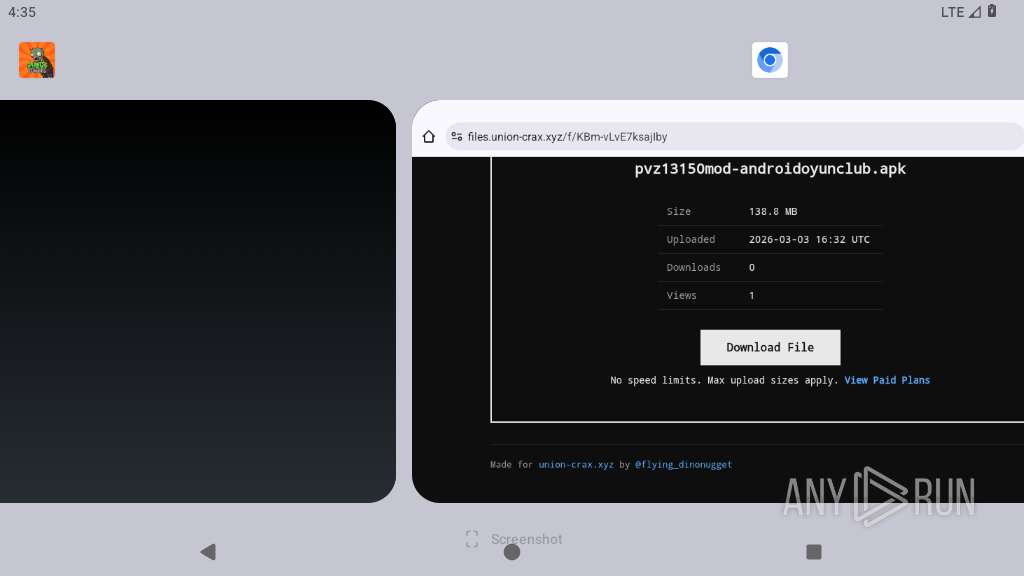
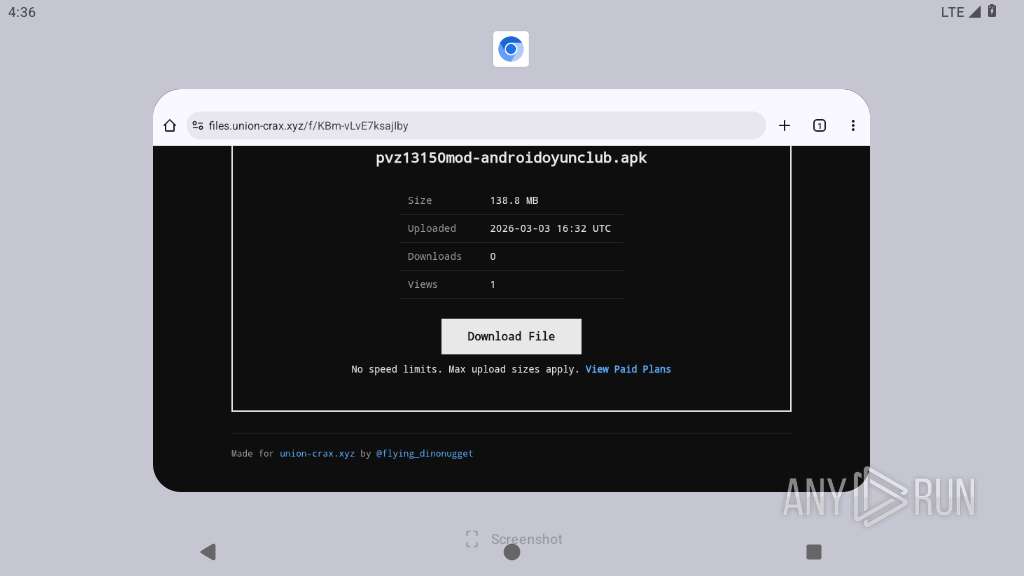
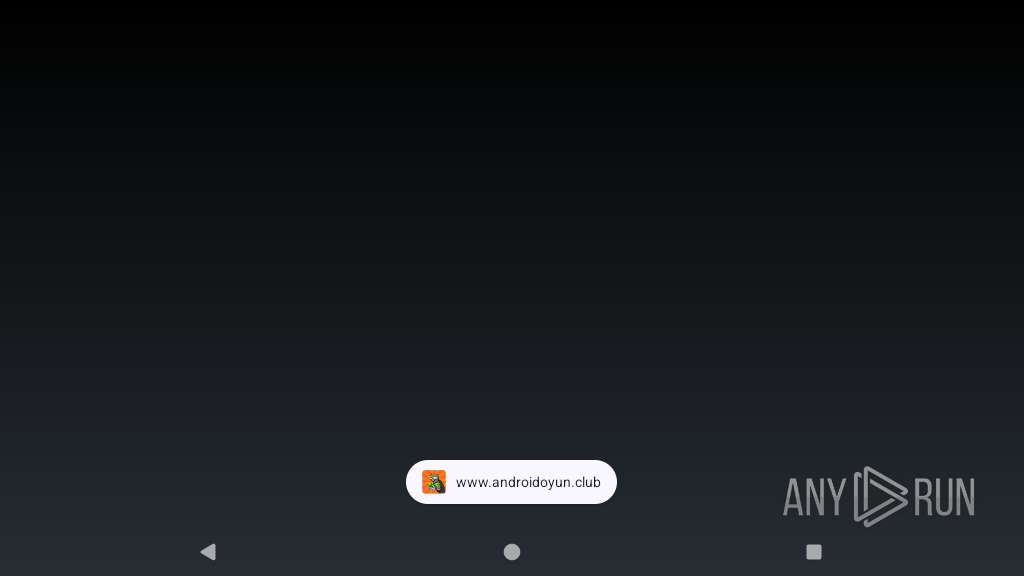
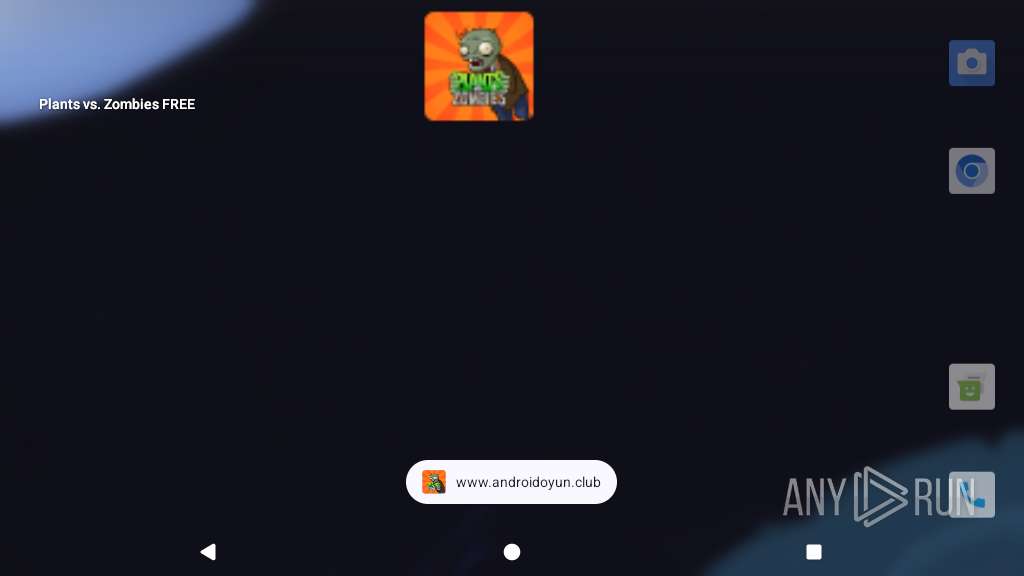
| URL: | https://files.union-crax.xyz/f/KBm-vLvE7ksajIby |
| Full analysis: | https://app.any.run/tasks/e1bfec23-8e36-43f5-98fa-eb429643d9dd |
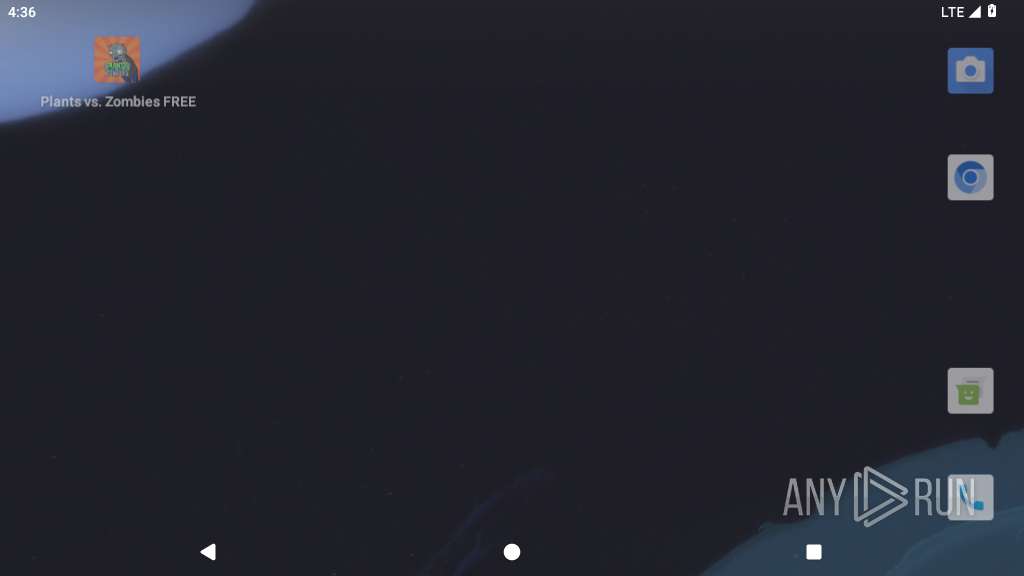
| Verdict: | Malicious activity |
| Threats: | Spyware is a stealth form of malware whose primary objective is to gather sensitive information, such as personal data, login credentials, and financial details, by monitoring user activities and exploiting system vulnerabilities. Spyware operates secretly in the background, evading detection while transmitting collected data to cybercriminals, who can then use it for malicious purposes like identity theft, financial fraud, or espionage. |
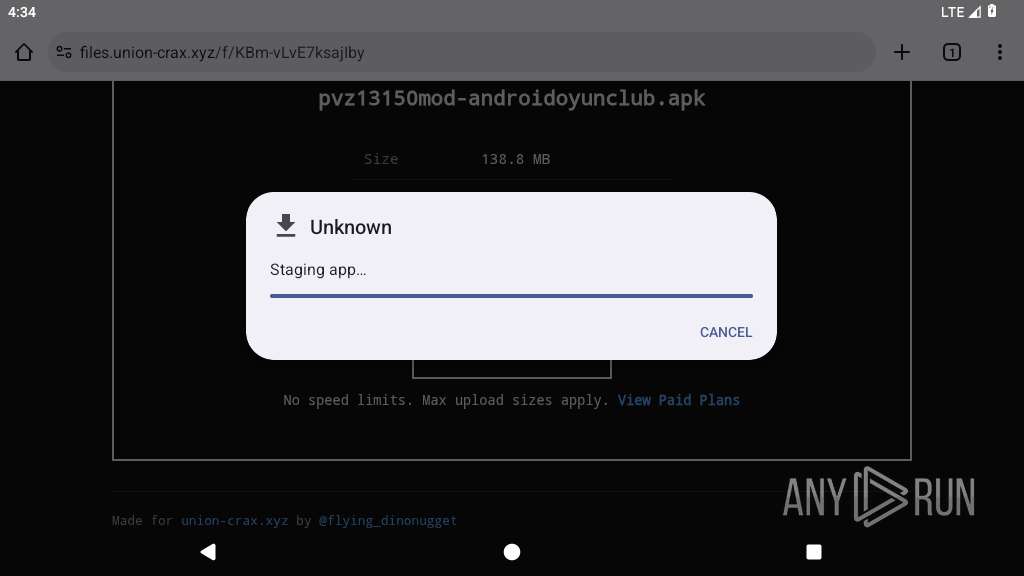
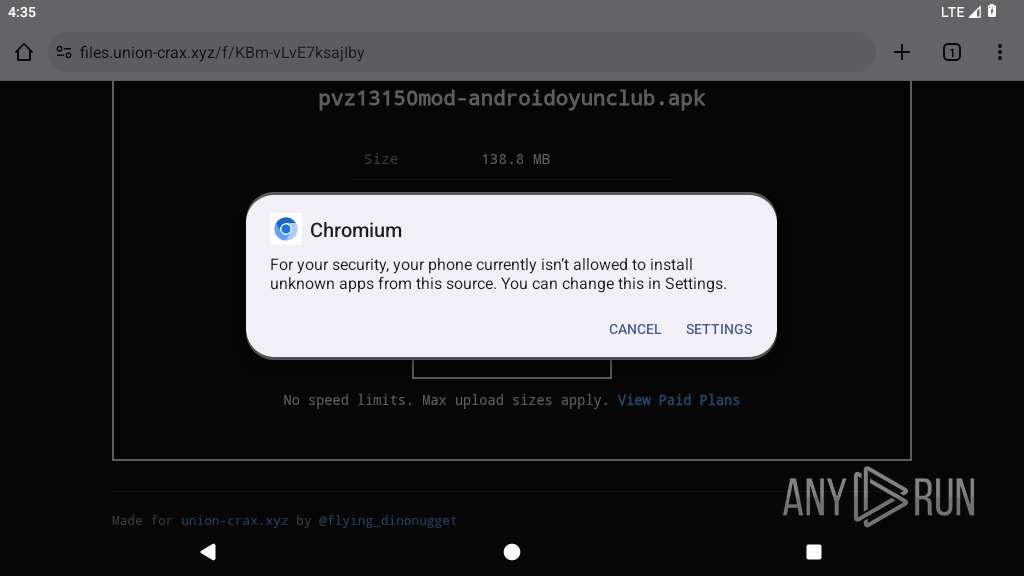
| Analysis date: | March 03, 2026, 16:34:00 |
| OS: | Android 14 |
| Tags: | |
| Indicators: | |
| MD5: | 6193493C36F48C3A9F99DE95E42E6772 |
| SHA1: | 0C9B784FE847FAE6C522C36622856637C338F4C6 |
| SHA256: | 74A7513A873FD7A4E195E6FBBC8E7196C987820E07BBE951D51E7BA5F66C094E |
| SSDEEP: | 3:N8McOd51nZpTOn:2McOxDO |
MALICIOUS
PROMPTSPY has been detected
- app_process64 (PID: 4479)
SUSPICIOUS
Accesses system-level resources
- app_process64 (PID: 4479)
- app_process64 (PID: 5124)
Returns the name of the current network operator
- app_process64 (PID: 4479)
- app_process64 (PID: 5124)
Collects data about the device's environment (JVM version)
- app_process64 (PID: 4479)
- app_process64 (PID: 5124)
Accesses external device storage files
- app_process64 (PID: 4479)
- app_process64 (PID: 5124)
Retrieves the ISO country code of the current network
- app_process64 (PID: 4479)
- app_process64 (PID: 5124)
Uses encryption API functions
- app_process64 (PID: 4479)
- app_process64 (PID: 5124)
Establishing a connection
- app_process64 (PID: 4479)
- app_process64 (PID: 5124)
Updates data in the storage of application settings (SharedPreferences)
- app_process64 (PID: 4479)
- app_process64 (PID: 5124)
Creates a WakeLock to manage power state
- app_process64 (PID: 4479)
- app_process64 (PID: 5124)
INFO
Loads a native library into the application
- app_process64 (PID: 4479)
- app_process64 (PID: 5124)
Dynamically inspects or modifies classes, methods, and fields at runtime
- app_process64 (PID: 4479)
- app_process64 (PID: 5124)
Dynamically registers broadcast event listeners
- app_process64 (PID: 4479)
- app_process64 (PID: 5124)
Dynamically loads a class in Java
- app_process64 (PID: 4479)
- app_process64 (PID: 5124)
Retrieves the value of a secure system setting
- app_process64 (PID: 4479)
- app_process64 (PID: 5124)
Gets the display metrics associated with the device's screen
- app_process64 (PID: 4479)
- app_process64 (PID: 5124)
Verifies whether the device is connected to the internet
- app_process64 (PID: 4479)
- app_process64 (PID: 5124)
Retrieves data from storage of application settings (SharedPreferences)
- app_process64 (PID: 4479)
- app_process64 (PID: 5124)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
183
Monitored processes
55
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process |
|---|---|---|---|---|
| 3967 | org.chromium.chrome | /system/bin/app_process64 | app_process64 | |
User: root Integrity Level: UNKNOWN Exit code: 9 | ||||
| 4014 | com.android.traceur | /system/bin/app_process64 | — | app_process64 |
User: u0_a54 Integrity Level: UNKNOWN Exit code: 512 | ||||
| 4027 | org.chromium.chrome_zygote | /system/bin/app_process64 | — | app_process64 |
User: root Integrity Level: UNKNOWN Exit code: 9 | ||||
| 4049 | org.chromium.chrome_zygote | /system/bin/app_process64 | — | app_process64 |
User: u0_a72 Integrity Level: UNKNOWN Exit code: 9 | ||||
| 4064 | org.chromium.chrome:privileged_process0 | /system/bin/app_process64 | — | app_process64 |
User: root Integrity Level: UNKNOWN Exit code: 9 | ||||
| 4106 | com.android.adservices.api | /system/bin/app_process64 | — | app_process64 |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 4143 | org.chromium.chrome_zygote | /system/bin/app_process64 | — | app_process64 |
User: u0_a72 Integrity Level: UNKNOWN Exit code: 0 | ||||
| 4169 | com.android.providers.partnerbookmarks | /system/bin/app_process64 | — | app_process64 |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 4230 | org.chromium.chrome_zygote | /system/bin/app_process64 | — | app_process64 |
User: u0_a72 Integrity Level: UNKNOWN Exit code: 0 | ||||
| 4319 | /system/bin/dmesgd | /system/bin/dmesgd | — | init |
User: dmesgd Integrity Level: UNKNOWN Exit code: 0 | ||||
Total events
0
Read events
0
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
382
Text files
129
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4353 | app_process64 | /data/data/org.chromium.chrome/cache/.org.chromium.Chromium.UdpywT/list.pb | binary | |
MD5:— | SHA256:— | |||
| 4353 | app_process64 | /data/data/org.chromium.chrome/cache/.org.chromium.Chromium.UdpywT/manifest.json | text | |
MD5:— | SHA256:— | |||
| 4353 | app_process64 | /data/data/org.chromium.chrome/cache/.org.chromium.Chromium.UdpywT/LICENSE | text | |
MD5:— | SHA256:— | |||
| 4353 | app_process64 | /data/data/org.chromium.chrome/cache/.org.chromium.Chromium.UdpywT/_metadata/verified_contents.json | text | |
MD5:— | SHA256:— | |||
| 4353 | app_process64 | /data/data/org.chromium.chrome/app_chrome/component_crx_cache/cab4d1f0a6a2a1afecae808a520f6690dd2b9d58bf54762877f2dc9715d55461 | binary | |
MD5:— | SHA256:— | |||
| 4372 | app_process64 | /data/data/org.chromium.chrome/cache/.org.chromium.Chromium.4j6aIu/privacy-sandbox-attestations.dat | binary | |
MD5:— | SHA256:— | |||
| 4372 | app_process64 | /data/data/org.chromium.chrome/cache/.org.chromium.Chromium.4j6aIu/manifest.json | text | |
MD5:— | SHA256:— | |||
| 4372 | app_process64 | /data/data/org.chromium.chrome/cache/.org.chromium.Chromium.4j6aIu/_metadata/verified_contents.json | text | |
MD5:— | SHA256:— | |||
| 4372 | app_process64 | /data/data/org.chromium.chrome/app_chrome/component_crx_cache/38c89b12bb20a8f2751c9c7cd2e31c173a47af08c115e1ecccc2f5151a2cf2c6 | binary | |
MD5:— | SHA256:— | |||
| 4391 | app_process64 | /data/data/org.chromium.chrome/cache/.org.chromium.Chromium.MfdpRx/decoded_xz | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
62
TCP/UDP connections
37
DNS requests
37
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3967 | app_process64 | OPTIONS | 200 | 35.190.80.1:443 | https://a.nel.cloudflare.com/report/v4?s=vlm%2FP%2FpHpMtEp6kfkb0CKardjjBrbDXyms3CKAPqTWAEXDrE3UJihyvD4ww0XE3f6y5qU1kjoFIr%2FnWnXX9Eu9Tm786T2WuL2%2BjbIfRAevArnv1V | unknown | — | — | unknown |
1921 | app_process64 | GET | 204 | 142.251.36.100:443 | https://www.google.com/generate_204 | unknown | — | — | whitelisted |
— | — | GET | 204 | 142.251.36.100:80 | http://www.google.com/gen_204 | unknown | — | — | whitelisted |
3967 | app_process64 | POST | 200 | 35.190.80.1:443 | https://a.nel.cloudflare.com/report/v4?s=vlm%2FP%2FpHpMtEp6kfkb0CKardjjBrbDXyms3CKAPqTWAEXDrE3UJihyvD4ww0XE3f6y5qU1kjoFIr%2FnWnXX9Eu9Tm786T2WuL2%2BjbIfRAevArnv1V | unknown | — | — | unknown |
4479 | app_process64 | HEAD | 200 | 52.86.188.173:443 | https://ping1.tnt-ea.com/ | unknown | — | — | unknown |
3967 | app_process64 | GET | 200 | 104.16.80.73:443 | https://static.cloudflareinsights.com/beacon.min.js/v67327c56f0bb4ef8b305cae61679db8f1769101564043 | unknown | text | 29.4 Kb | whitelisted |
3967 | app_process64 | POST | 200 | 142.251.127.84:443 | https://accounts.google.com/ListAccounts?gpsia=1&source=ChromiumBrowser&laf=b64bin&json=standard | unknown | — | — | whitelisted |
1921 | app_process64 | GET | 204 | 142.251.36.99:80 | http://connectivitycheck.gstatic.com/generate_204 | unknown | — | — | whitelisted |
2931 | app_process64 | POST | 200 | 142.251.168.81:443 | https://staging-remoteprovisioning.sandbox.googleapis.com/v1:fetchEekChain | unknown | binary | 778 b | whitelisted |
2931 | app_process64 | POST | 200 | 142.251.168.81:443 | https://staging-remoteprovisioning.sandbox.googleapis.com/v1:signCertificates?challenge=AAABnLSNF7MBILStY-JsQE-MBmhRTxmkYSFBvgY=&request_id=60879d73-bda9-474d-98b2-42fed074d478 | unknown | binary | 11.8 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
452 | mdnsd | 224.0.0.251:5353 | — | — | — | whitelisted |
— | — | 142.251.36.100:80 | www.google.com | GOOGLE | US | whitelisted |
— | — | 142.251.36.99:80 | connectivitycheck.gstatic.com | GOOGLE | US | whitelisted |
— | — | 142.251.36.100:443 | www.google.com | GOOGLE | US | whitelisted |
3967 | app_process64 | 216.58.206.46:80 | clients2.google.com | GOOGLE | US | whitelisted |
3967 | app_process64 | 188.114.96.3:443 | files.union-crax.xyz | CLOUDFLARENET | US | whitelisted |
3967 | app_process64 | 142.251.127.84:443 | accounts.google.com | GOOGLE | US | whitelisted |
3967 | app_process64 | 142.251.36.100:443 | www.google.com | GOOGLE | US | whitelisted |
3967 | app_process64 | 104.16.80.73:443 | static.cloudflareinsights.com | CLOUDFLARENET | US | whitelisted |
3967 | app_process64 | 35.190.80.1:443 | a.nel.cloudflare.com | GOOGLE-CLOUD-PLATFORM | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
www.google.com |
| whitelisted |
clients2.google.com |
| whitelisted |
files.union-crax.xyz |
| unknown |
accounts.google.com |
| whitelisted |
static.cloudflareinsights.com |
| whitelisted |
a.nel.cloudflare.com |
| whitelisted |
connectivitycheck.gstatic.com |
| whitelisted |
time.android.com |
| whitelisted |
staging-remoteprovisioning.sandbox.googleapis.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3967 | app_process64 | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
3967 | app_process64 | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
1921 | app_process64 | Misc activity | ET INFO Android Device Connectivity Check |