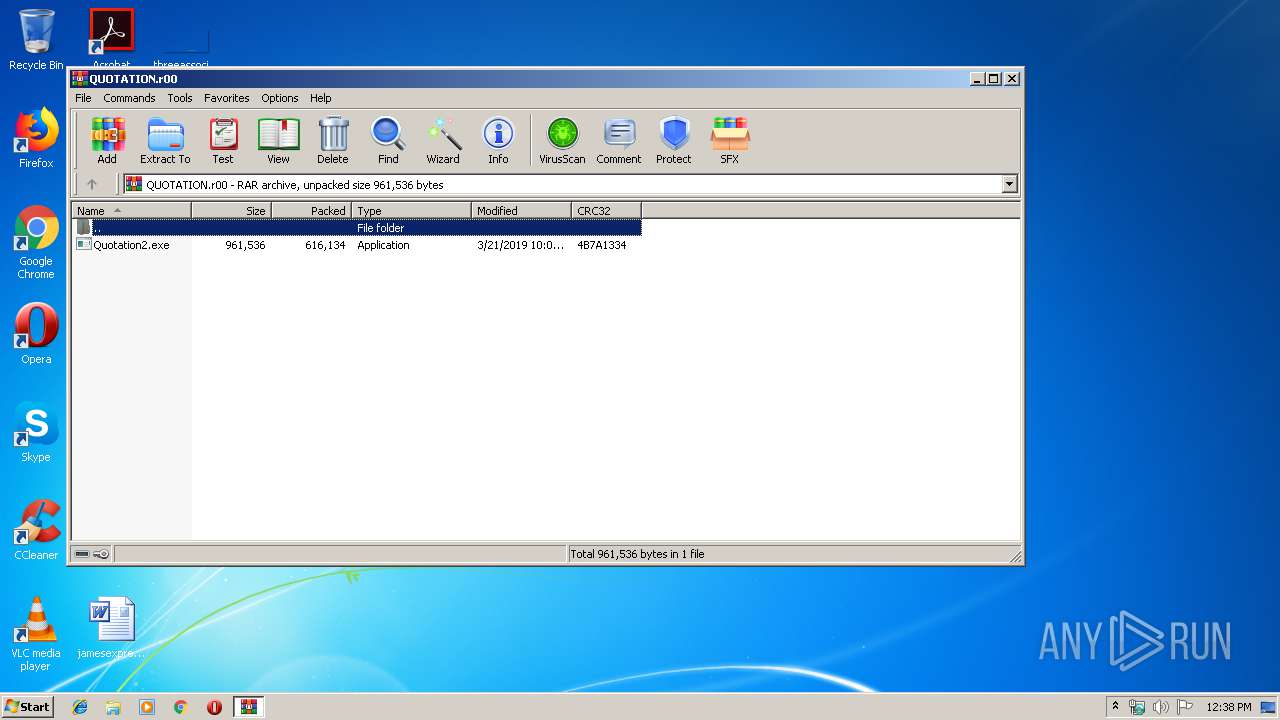
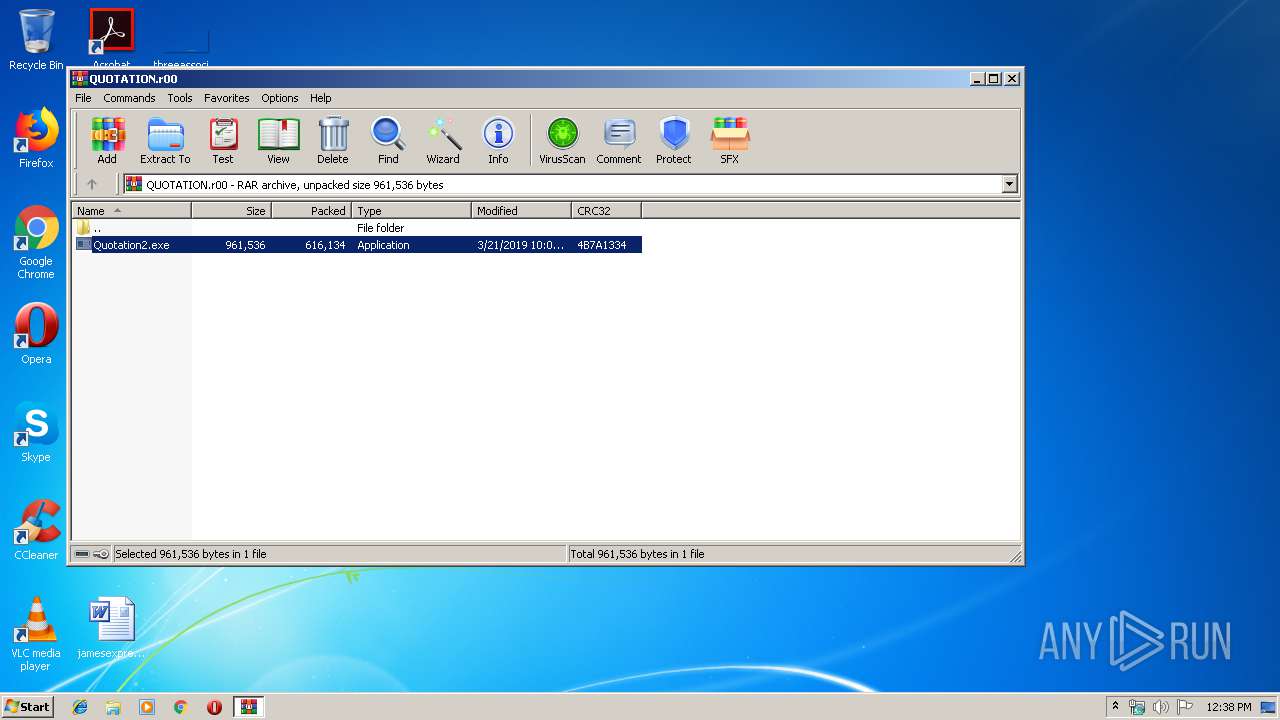
| File name: | QUOTATION.r00 |
| Full analysis: | https://app.any.run/tasks/88c54215-1daf-43db-993e-8f6b3b70c68d |
| Verdict: | Malicious activity |
| Threats: | Hawkeye often gets installed in a bundle with other malware. This is a Trojan and keylogger that is used to retrieve private information such as passwords and login credentials. This is an advanced malware that features strong anti-evasion functions. |
| Analysis date: | March 22, 2019, 12:37:54 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | D89A9D17B87DDC331666B7ACE28DD98F |
| SHA1: | DAE89ECD465A55561BA27B9768B037BF97F80F75 |
| SHA256: | 73EDDD439F87DA34B3B2ABAC9C563B96D7E0E48E02CEE938ED8772776E5ECB3A |
| SSDEEP: | 12288:HWjmi2NLtDk0qj0kpmwlIeiGg0WNDKta7wrbR/AiQuDV0VLjUah8:HWjm3hDkP0ImwlIeiRJIKsbR4AeVv3e |
MALICIOUS
Application was dropped or rewritten from another process
- Quotation2.exe (PID: 236)
- Quotation2.exe (PID: 2088)
- Quotation2.exe (PID: 3804)
Stealing of credential data
- vbc.exe (PID: 1248)
- vbc.exe (PID: 2996)
Detected Hawkeye Keylogger
- Quotation2.exe (PID: 236)
Actions looks like stealing of personal data
- vbc.exe (PID: 1248)
- vbc.exe (PID: 2996)
Changes settings of System certificates
- Quotation2.exe (PID: 236)
SUSPICIOUS
Executable content was dropped or overwritten
- WinRAR.exe (PID: 1476)
Application launched itself
- Quotation2.exe (PID: 2088)
Adds / modifies Windows certificates
- Quotation2.exe (PID: 236)
Loads DLL from Mozilla Firefox
- vbc.exe (PID: 2996)
Connects to SMTP port
- Quotation2.exe (PID: 236)
Executes scripts
- Quotation2.exe (PID: 236)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
Total processes
35
Monitored processes
6
Malicious processes
4
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 236 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa1476.31210\Quotation2.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa1476.31210\Quotation2.exe | Quotation2.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1248 | "C:\Windows\Microsoft.NET\Framework\v2.0.50727\vbc.exe" /stext "C:\Users\admin\AppData\Local\Temp\tmp2465.tmp" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\vbc.exe | Quotation2.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Visual Basic Command Line Compiler Exit code: 0 Version: 8.0.50727.5420 Modules
| |||||||||||||||
| 1476 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\QUOTATION.r00" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 2088 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa1476.31210\Quotation2.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa1476.31210\Quotation2.exe | — | WinRAR.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2996 | "C:\Windows\Microsoft.NET\Framework\v2.0.50727\vbc.exe" /stext "C:\Users\admin\AppData\Local\Temp\tmpF7F5.tmp" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\vbc.exe | Quotation2.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Visual Basic Command Line Compiler Exit code: 0 Version: 8.0.50727.5420 Modules
| |||||||||||||||
| 3804 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa1476.31210\Quotation2.exe" 2 236 1232015 | C:\Users\admin\AppData\Local\Temp\Rar$EXa1476.31210\Quotation2.exe | — | Quotation2.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
512
Read events
469
Write events
40
Delete events
3
Modification events
| (PID) Process: | (1476) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (1476) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (1476) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1476) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\QUOTATION.r00 | |||
| (PID) Process: | (1476) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (1476) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (1476) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (1476) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (1476) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (1476) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
1
Suspicious files
0
Text files
3
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1476 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa1476.31210\Quotation2.exe | executable | |
MD5:— | SHA256:— | |||
| 236 | Quotation2.exe | C:\Users\admin\AppData\Local\Temp\c4e681c3-f0d5-5260-1e84-0e7fc68922c3 | text | |
MD5:— | SHA256:— | |||
| 1248 | vbc.exe | C:\Users\admin\AppData\Local\Temp\tmp2465.tmp | text | |
MD5:7FB9A9AD0FD9B1E0108ED71FBB276048 | SHA256:7D63C301317E144B0133A72250AE2D8E09AF65A92E6A807EC58A71939FE530A9 | |||
| 2996 | vbc.exe | C:\Users\admin\AppData\Local\Temp\tmpF7F5.tmp | text | |
MD5:3E1E093DCCE32C716267A28292E0EE27 | SHA256:56285445424AD06DC043154819B5BDABAA7C26F5779CA3E37E08424ED9926CB8 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
2
DNS requests
2
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
236 | Quotation2.exe | GET | 200 | 66.171.248.178:80 | http://bot.whatismyipaddress.com/ | US | text | 13 b | shared |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
236 | Quotation2.exe | 66.171.248.178:80 | bot.whatismyipaddress.com | Alchemy Communications, Inc. | US | malicious |
236 | Quotation2.exe | 77.88.21.38:587 | smtp.yandex.com | YANDEX LLC | RU | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
bot.whatismyipaddress.com |
| shared |
smtp.yandex.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
236 | Quotation2.exe | A Network Trojan was detected | MALWARE [PTsecurity] Spy.HawkEye IP Check |
2 ETPRO signatures available at the full report