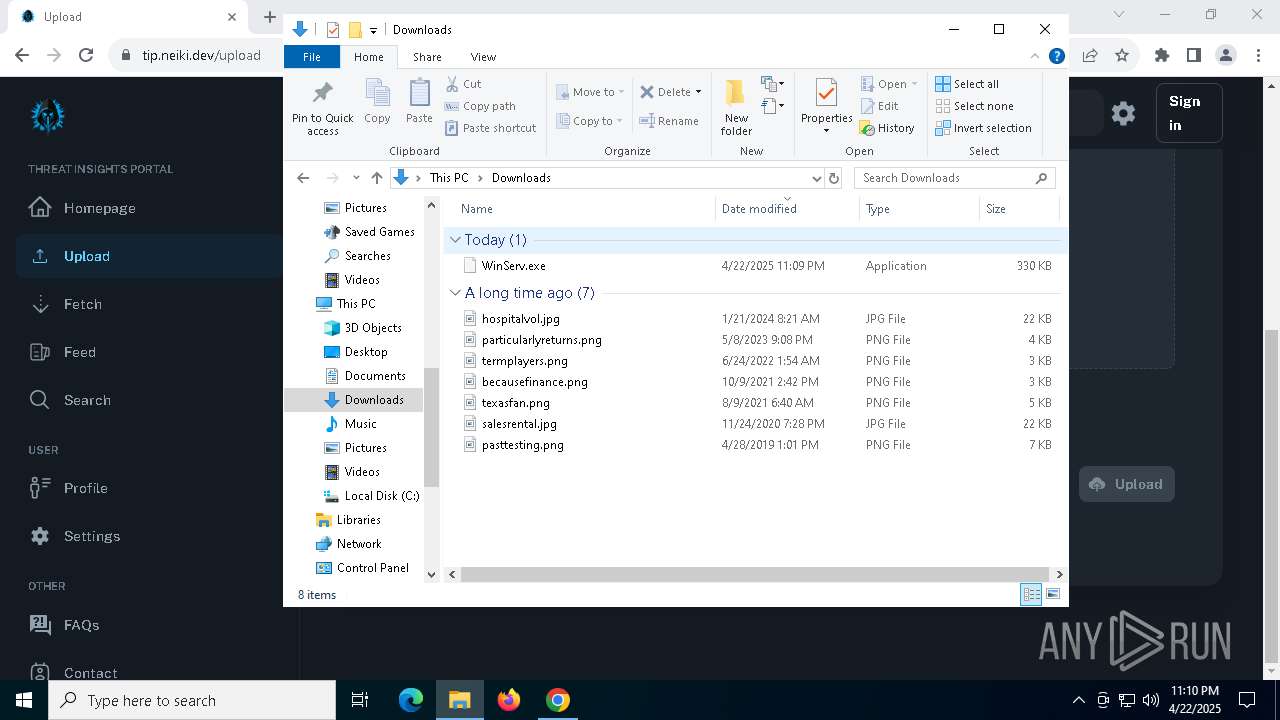
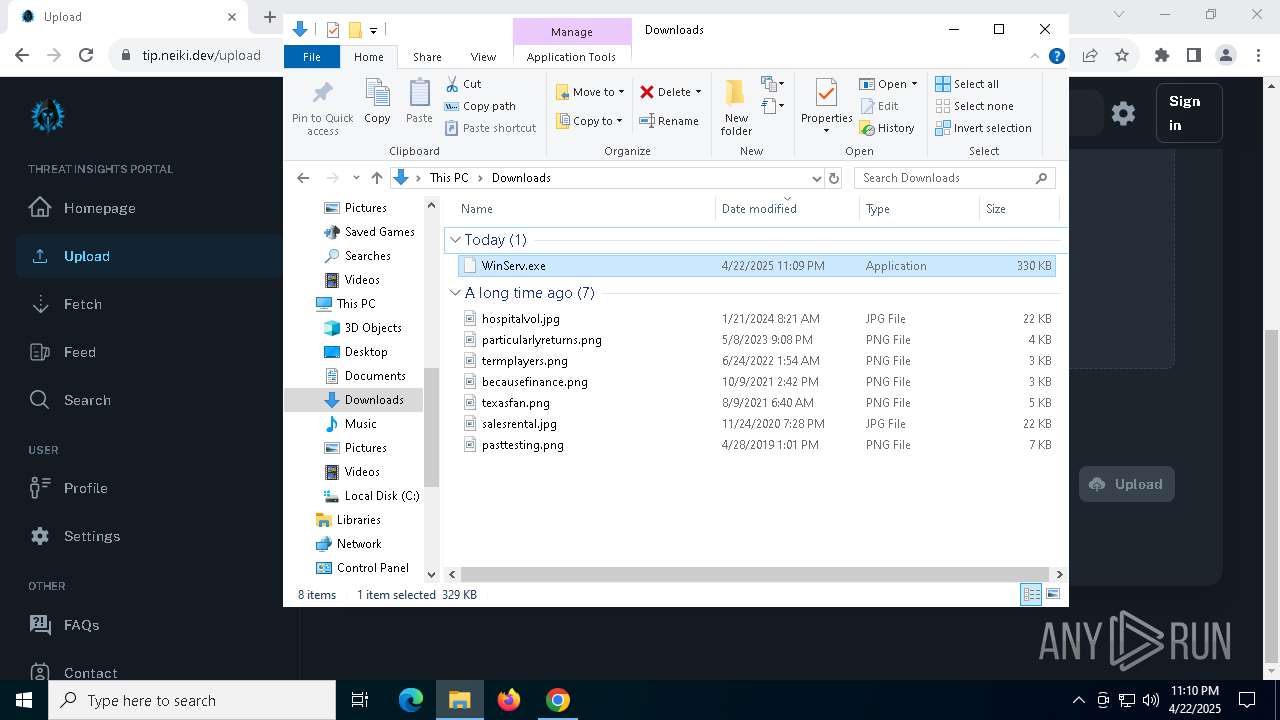
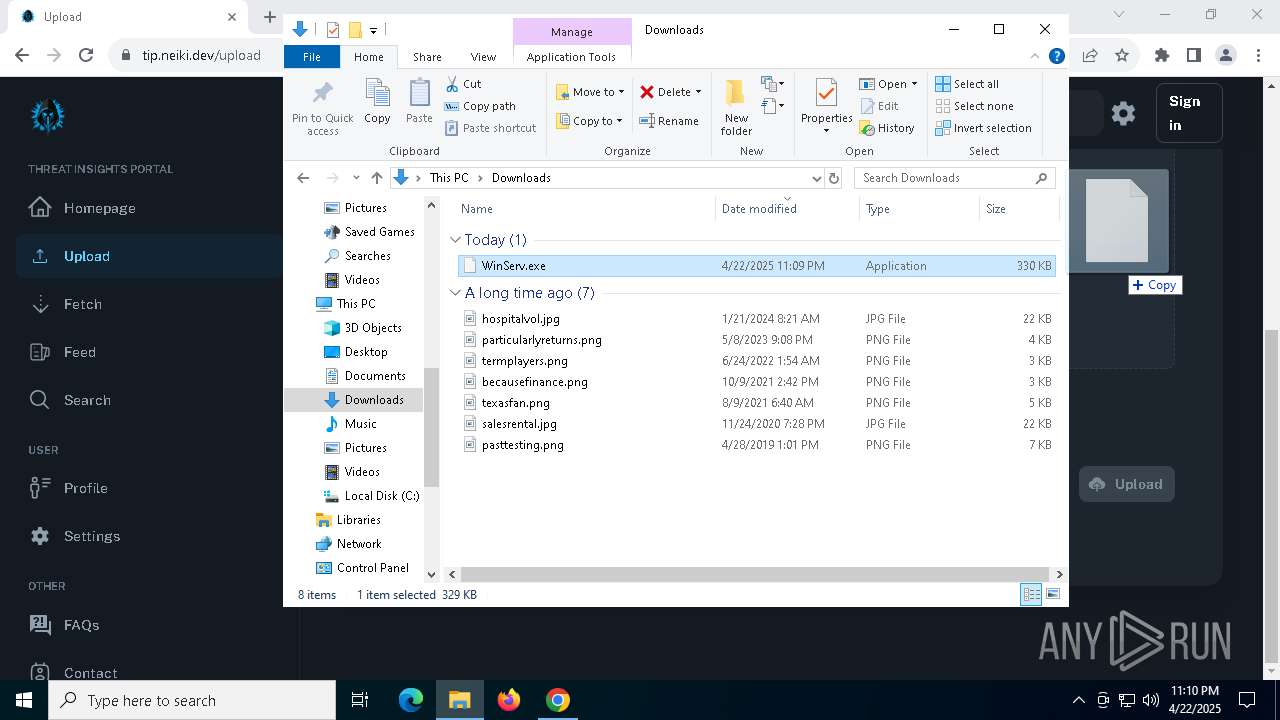
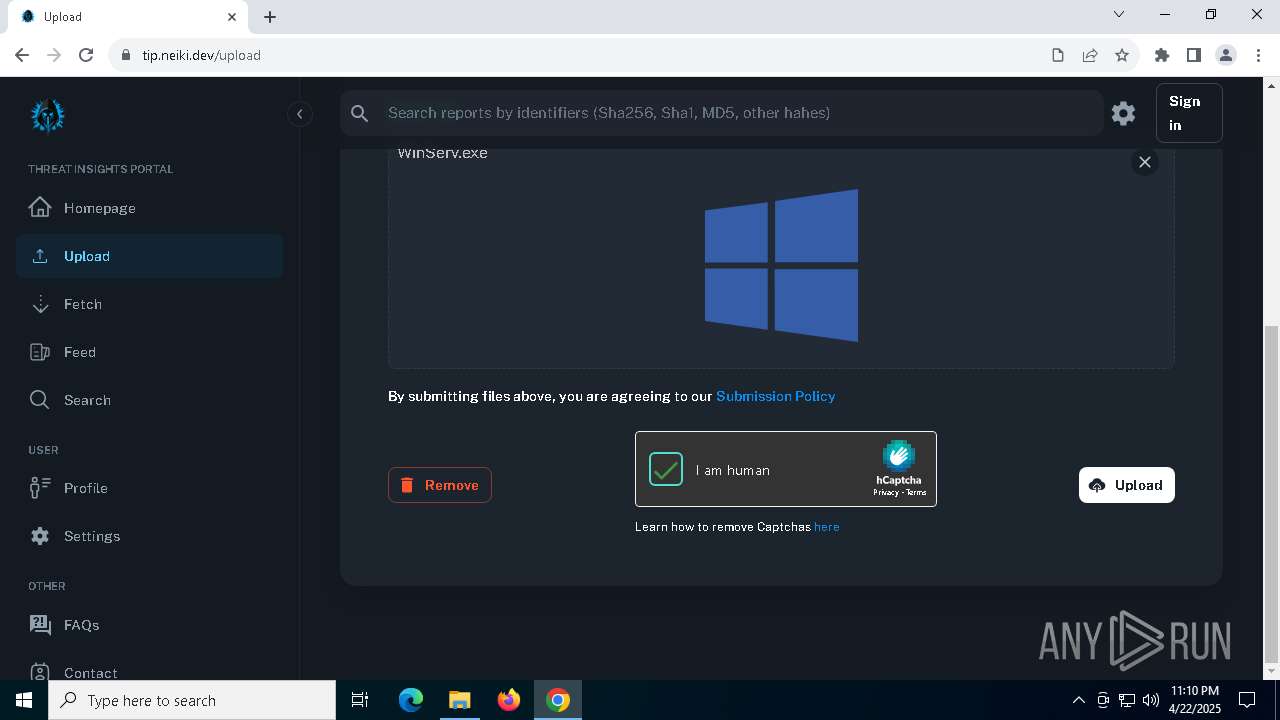
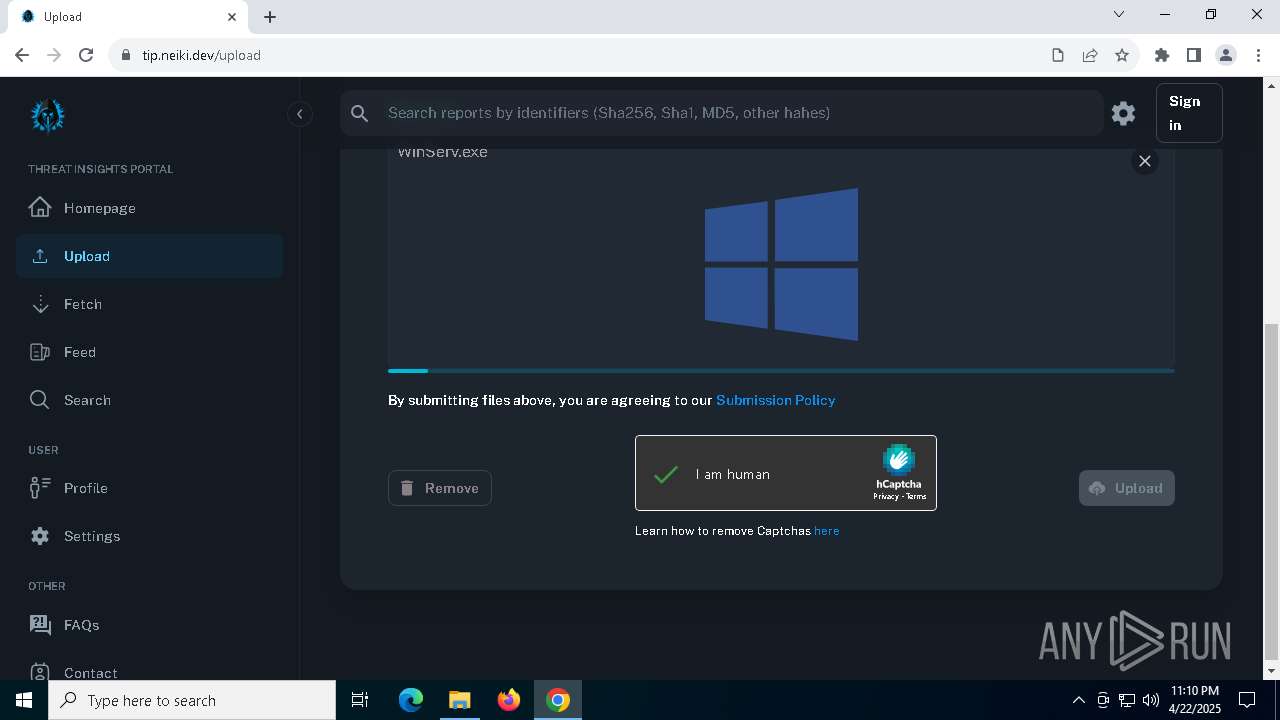
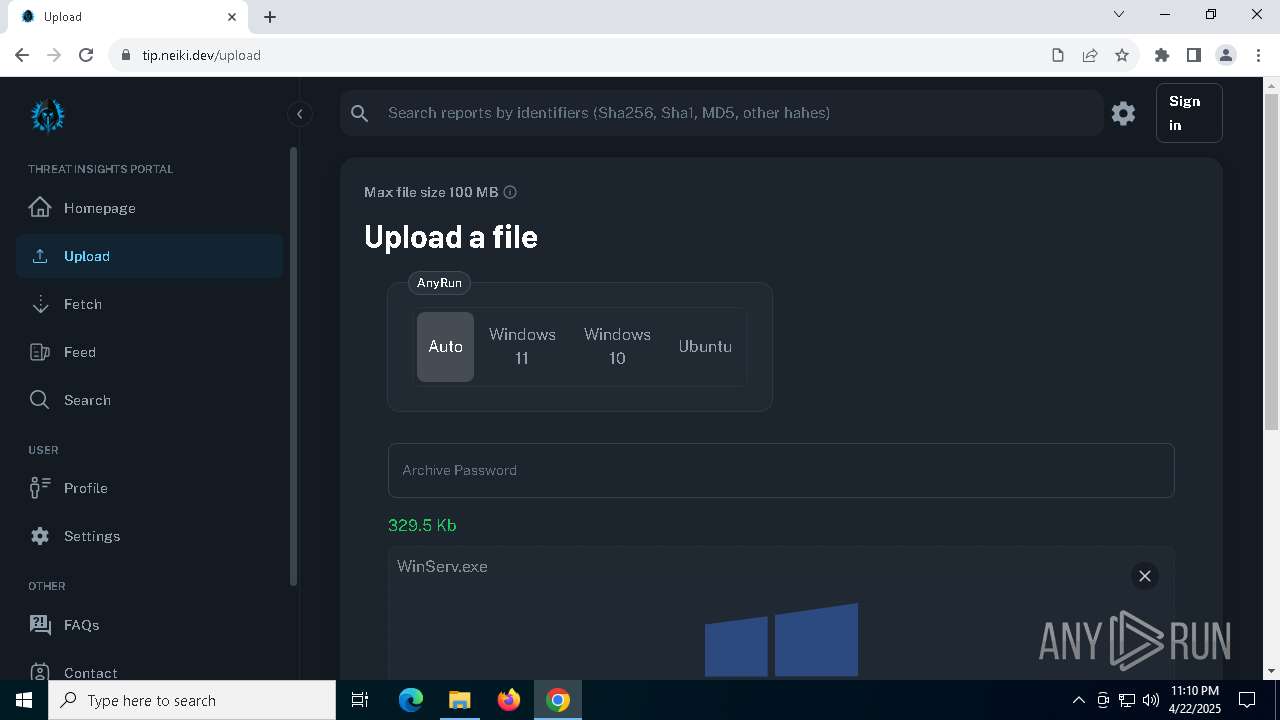
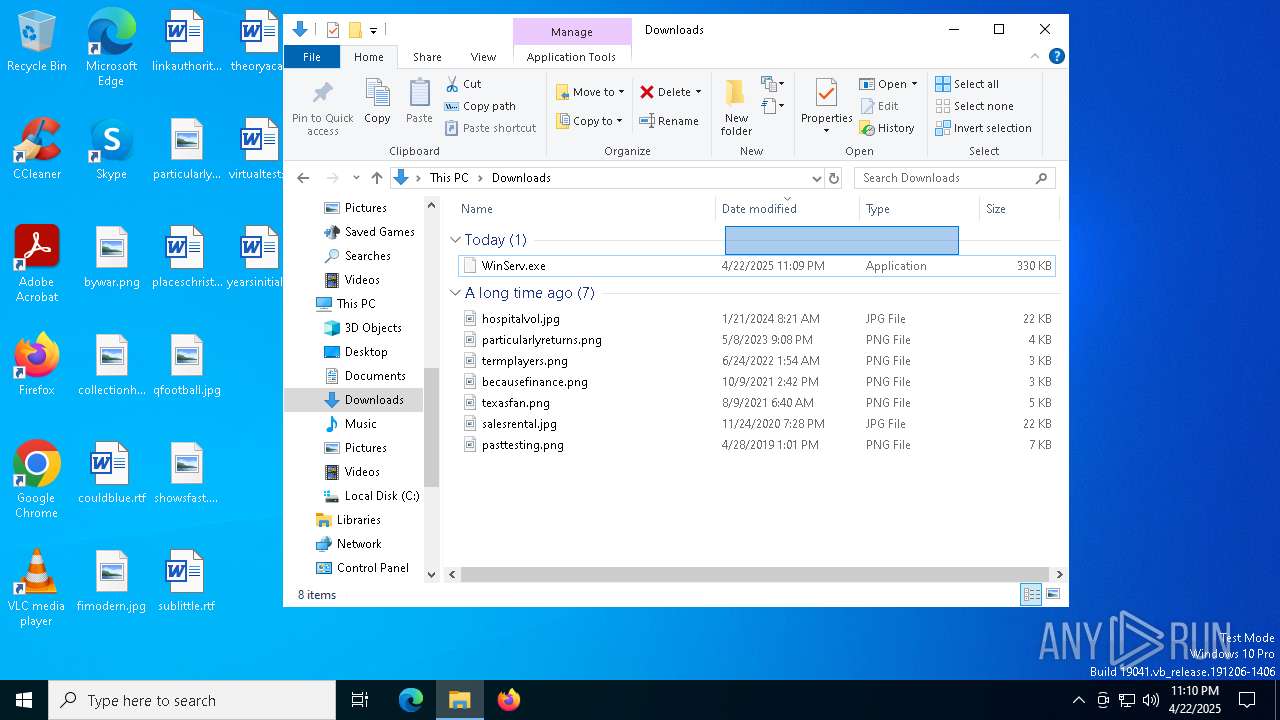
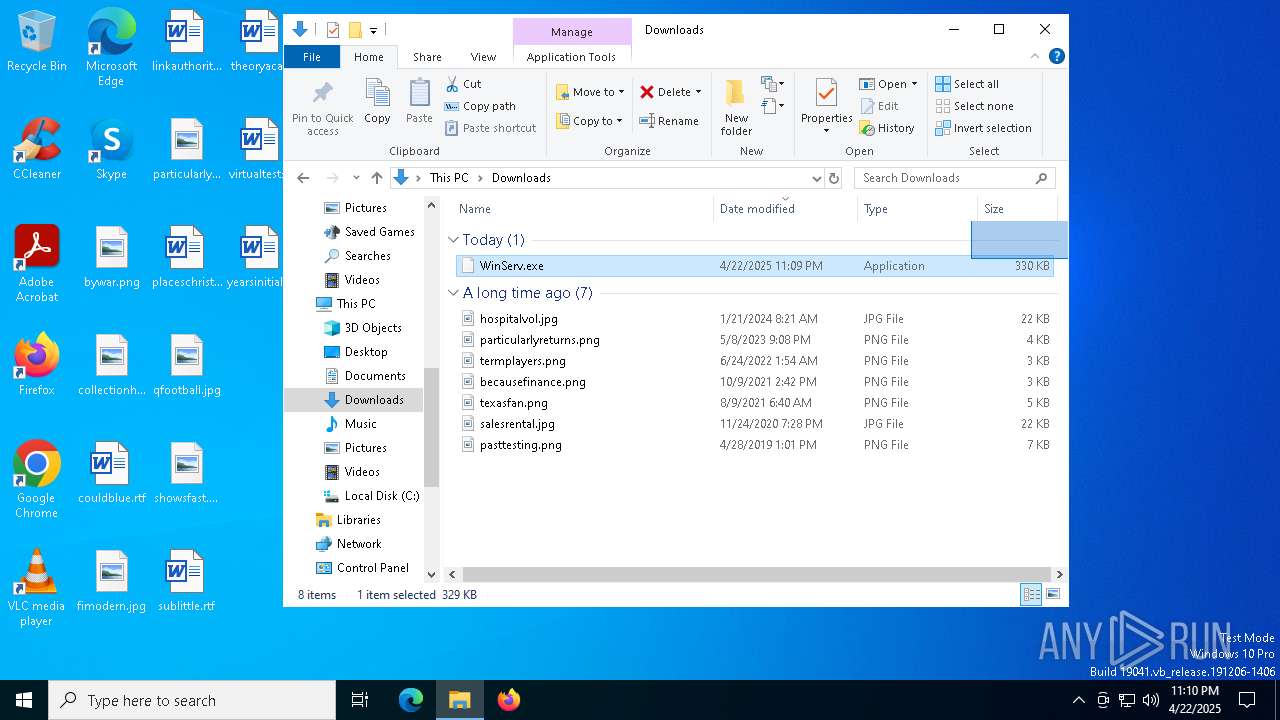
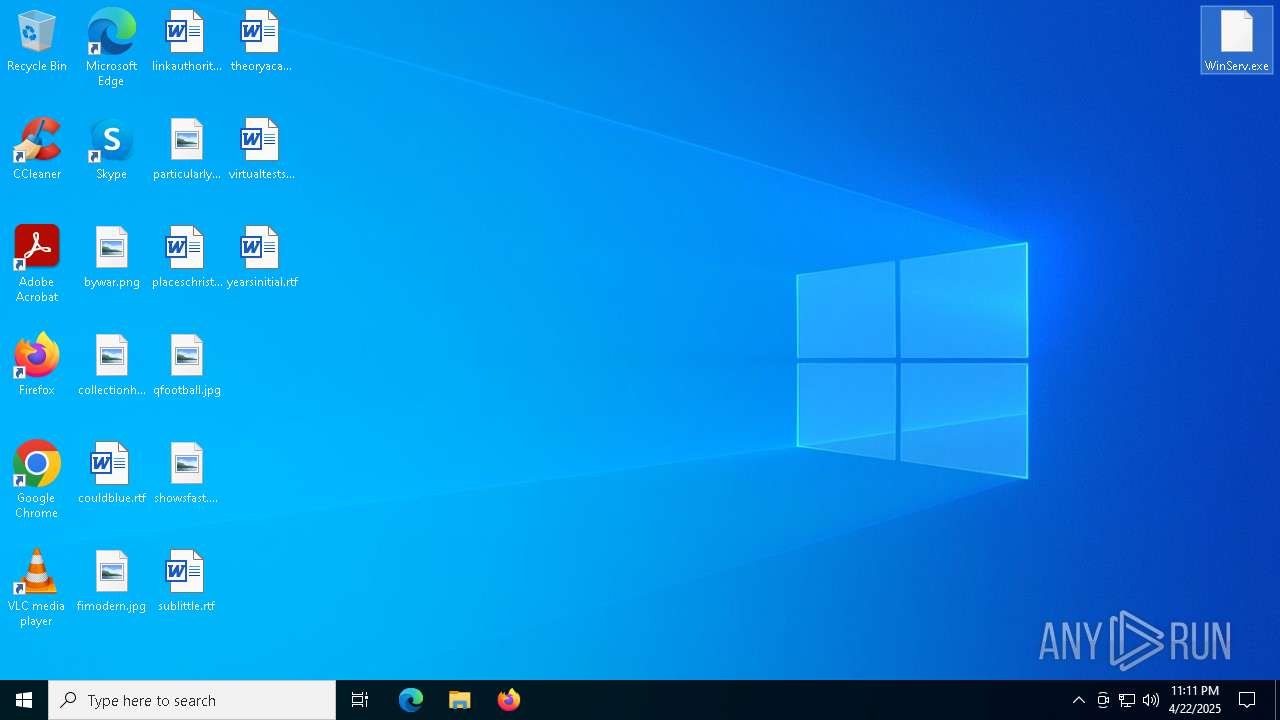
| File name: | WinServ.exe |
| Full analysis: | https://app.any.run/tasks/900647ed-7fe6-4fd9-b965-d74231ff9d97 |
| Verdict: | Malicious activity |
| Threats: | njRAT is a remote access trojan. It is one of the most widely accessible RATs on the market that features an abundance of educational information. Interested attackers can even find tutorials on YouTube. This allows it to become one of the most popular RATs in the world. |
| Analysis date: | April 22, 2025, 23:09:27 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows, 3 sections |
| MD5: | 5D15A9550907D1EB27C436DC26662416 |
| SHA1: | E249515F18D0A81B64D9E8E0075DFF3F9E3F125E |
| SHA256: | 73AEA567E0D32BBB93BFFF7BD9CDB03E662A16835353A73DD919531B1500EE99 |
| SSDEEP: | 6144:RriNke5kkkxQ7ESx4CCCC1zkjkkkkcyp8kfZX3IuFwCCC9Jiokkkj2KNkS:RriNke5kkkxQ7ESx4CCCC1zkjkkkkcyS |
MALICIOUS
Create files in the Startup directory
- csrss.exe (PID: 2236)
NJRAT mutex has been found
- csrss.exe (PID: 2236)
- Serv.exe (PID: 7860)
Changes the autorun value in the registry
- csrss.exe (PID: 2236)
NJRAT has been detected (YARA)
- Serv.exe (PID: 7860)
SUSPICIOUS
Reads security settings of Internet Explorer
- WinServ.exe (PID: 7584)
- csrss.exe (PID: 2236)
- WinServ.exe (PID: 896)
- WinServ.exe (PID: 684)
- WinServ.exe (PID: 6572)
- WinServ.exe (PID: 7736)
- WinServ.exe (PID: 7488)
- WinServ.exe (PID: 5136)
- WinServ.exe (PID: 3140)
- WinServ.exe (PID: 7200)
- WinServ.exe (PID: 5260)
- WinServ.exe (PID: 5048)
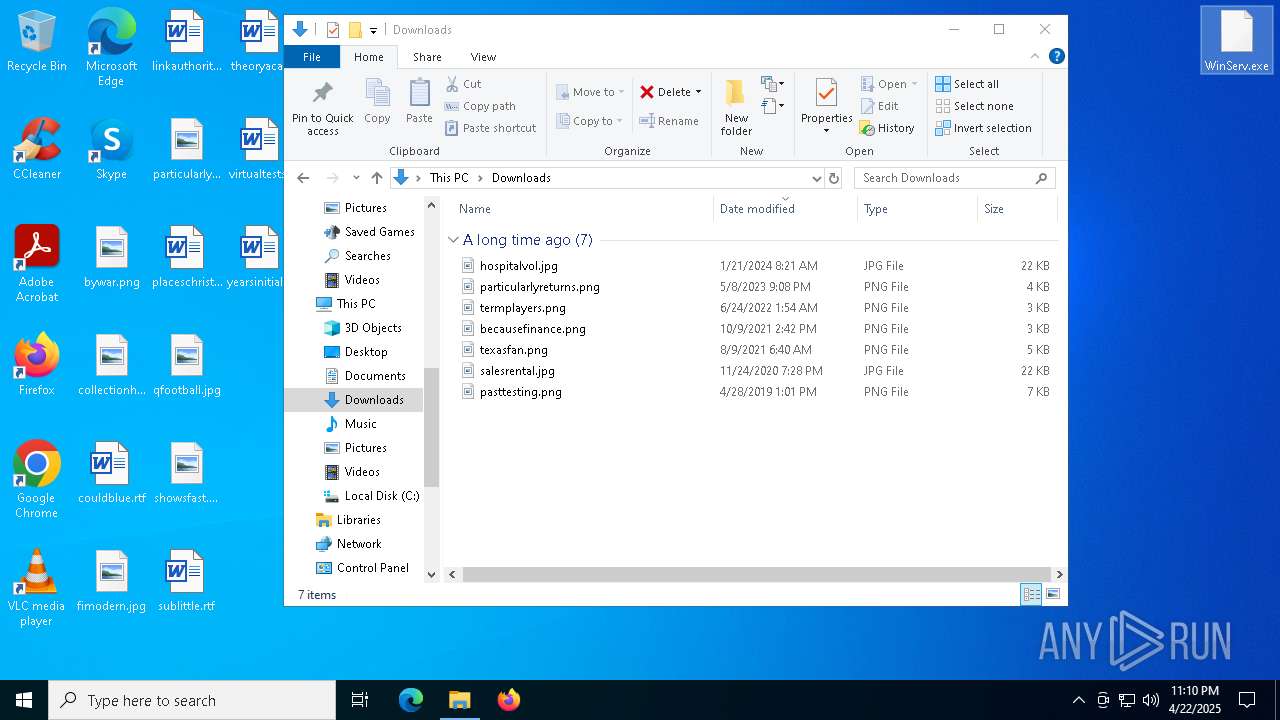
Executable content was dropped or overwritten
- WinServ.exe (PID: 7584)
- csrss.exe (PID: 2236)
- WinServ.exe (PID: 3140)
The process creates files with name similar to system file names
- WinServ.exe (PID: 7584)
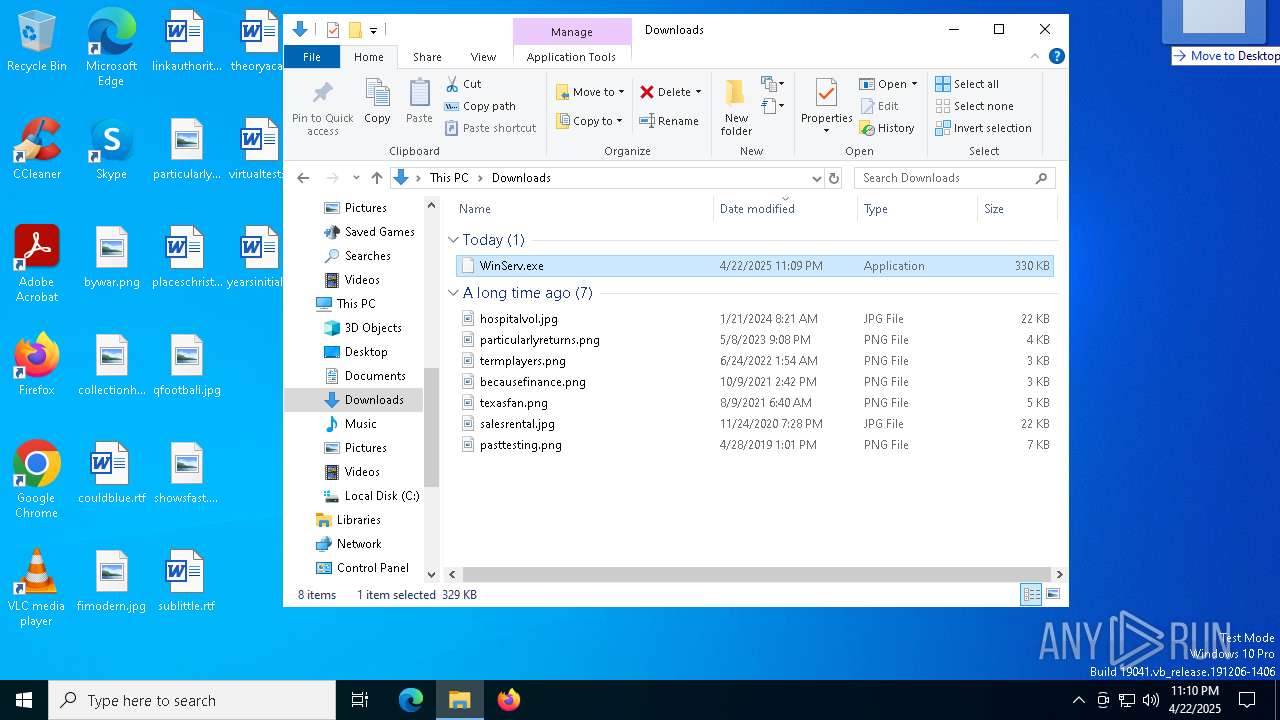
Starts itself from another location
- csrss.exe (PID: 2236)
- WinServ.exe (PID: 6572)
- WinServ.exe (PID: 5136)
- WinServ.exe (PID: 7736)
- WinServ.exe (PID: 896)
- WinServ.exe (PID: 7488)
- WinServ.exe (PID: 684)
- WinServ.exe (PID: 3140)
- WinServ.exe (PID: 7200)
- WinServ.exe (PID: 5260)
- WinServ.exe (PID: 5048)
Uses ATTRIB.EXE to modify file attributes
- Serv.exe (PID: 7860)
- csrss.exe (PID: 2236)
Connects to unusual port
- Serv.exe (PID: 7860)
INFO
Application launched itself
- chrome.exe (PID: 7800)
- chrome.exe (PID: 7744)
- chrome.exe (PID: 7756)
- chrome.exe (PID: 812)
- chrome.exe (PID: 7908)
- chrome.exe (PID: 5404)
- chrome.exe (PID: 1184)
- chrome.exe (PID: 1196)
- chrome.exe (PID: 5416)
- chrome.exe (PID: 8084)
- msedge.exe (PID: 5212)
Reads the computer name
- WinServ.exe (PID: 7584)
- csrss.exe (PID: 2236)
- Serv.exe (PID: 7860)
- WinServ.exe (PID: 6572)
- WinServ.exe (PID: 684)
- WinServ.exe (PID: 896)
- WinServ.exe (PID: 5136)
- WinServ.exe (PID: 7488)
- WinServ.exe (PID: 7736)
- WinServ.exe (PID: 3140)
- WinServ.exe (PID: 5260)
- WinServ.exe (PID: 6592)
- WinServ.exe (PID: 7200)
- WinServ.exe (PID: 5048)
- WinServ.exe (PID: 6244)
- WinServ.exe (PID: 7312)
- WinServ.exe (PID: 672)
- WinServ.exe (PID: 5328)
- WinServ.exe (PID: 924)
- WinServ.exe (PID: 3024)
- csrss.exe (PID: 780)
- csrss.exe (PID: 7452)
- csrss.exe (PID: 7268)
- csrss.exe (PID: 5544)
- csrss.exe (PID: 1764)
- csrss.exe (PID: 7340)
- WinServ.exe (PID: 2140)
- WinServ.exe (PID: 8188)
- WinServ.exe (PID: 1012)
- WinServ.exe (PID: 6264)
- WinServ.exe (PID: 1512)
- WinServ.exe (PID: 5680)
- WinServ.exe (PID: 8056)
- WinServ.exe (PID: 7336)
- WinServ.exe (PID: 8124)
- WinServ.exe (PID: 7980)
- WinServ.exe (PID: 7988)
- WinServ.exe (PID: 7196)
- WinServ.exe (PID: 8024)
- WinServ.exe (PID: 8100)
- WinServ.exe (PID: 5512)
- WinServ.exe (PID: 5084)
- WinServ.exe (PID: 1128)
- WinServ.exe (PID: 5936)
- WinServ.exe (PID: 5232)
- WinServ.exe (PID: 2432)
- WinServ.exe (PID: 6424)
- WinServ.exe (PID: 6808)
- WinServ.exe (PID: 4728)
- WinServ.exe (PID: 7316)
- WinServ.exe (PID: 732)
- WinServ.exe (PID: 4736)
- WinServ.exe (PID: 3760)
- WinServ.exe (PID: 4380)
- WinServ.exe (PID: 4112)
- WinServ.exe (PID: 6820)
- WinServ.exe (PID: 7284)
- WinServ.exe (PID: 7364)
- WinServ.exe (PID: 3976)
- WinServ.exe (PID: 2344)
- WinServ.exe (PID: 7724)
- WinServ.exe (PID: 5244)
- WinServ.exe (PID: 5984)
- WinServ.exe (PID: 2644)
- WinServ.exe (PID: 4528)
- WinServ.exe (PID: 2420)
- WinServ.exe (PID: 6136)
- WinServ.exe (PID: 6572)
- WinServ.exe (PID: 5200)
- WinServ.exe (PID: 232)
- WinServ.exe (PID: 8048)
- WinServ.exe (PID: 7420)
- WinServ.exe (PID: 6028)
- WinServ.exe (PID: 8232)
- WinServ.exe (PID: 6700)
- WinServ.exe (PID: 7492)
- WinServ.exe (PID: 7904)
- WinServ.exe (PID: 5216)
- WinServ.exe (PID: 6816)
- WinServ.exe (PID: 5132)
- WinServ.exe (PID: 5980)
- WinServ.exe (PID: 1116)
- WinServ.exe (PID: 8308)
- WinServ.exe (PID: 8384)
- WinServ.exe (PID: 7760)
- WinServ.exe (PID: 4028)
- WinServ.exe (PID: 4572)
- WinServ.exe (PID: 8292)
- WinServ.exe (PID: 8448)
- WinServ.exe (PID: 8460)
- WinServ.exe (PID: 8252)
- WinServ.exe (PID: 8332)
- WinServ.exe (PID: 8796)
- WinServ.exe (PID: 8856)
- WinServ.exe (PID: 8784)
- WinServ.exe (PID: 8836)
- WinServ.exe (PID: 8772)
- WinServ.exe (PID: 8904)
- WinServ.exe (PID: 8808)
- WinServ.exe (PID: 8916)
- WinServ.exe (PID: 9200)
- WinServ.exe (PID: 9140)
- WinServ.exe (PID: 9212)
- WinServ.exe (PID: 9172)
- WinServ.exe (PID: 6072)
- WinServ.exe (PID: 9184)
- WinServ.exe (PID: 9156)
- WinServ.exe (PID: 7888)
- WinServ.exe (PID: 8300)
- WinServ.exe (PID: 8304)
- WinServ.exe (PID: 8204)
- WinServ.exe (PID: 5500)
- WinServ.exe (PID: 6712)
- WinServ.exe (PID: 9132)
- csrss.exe (PID: 9720)
- csrss.exe (PID: 9732)
- csrss.exe (PID: 4120)
- csrss.exe (PID: 3176)
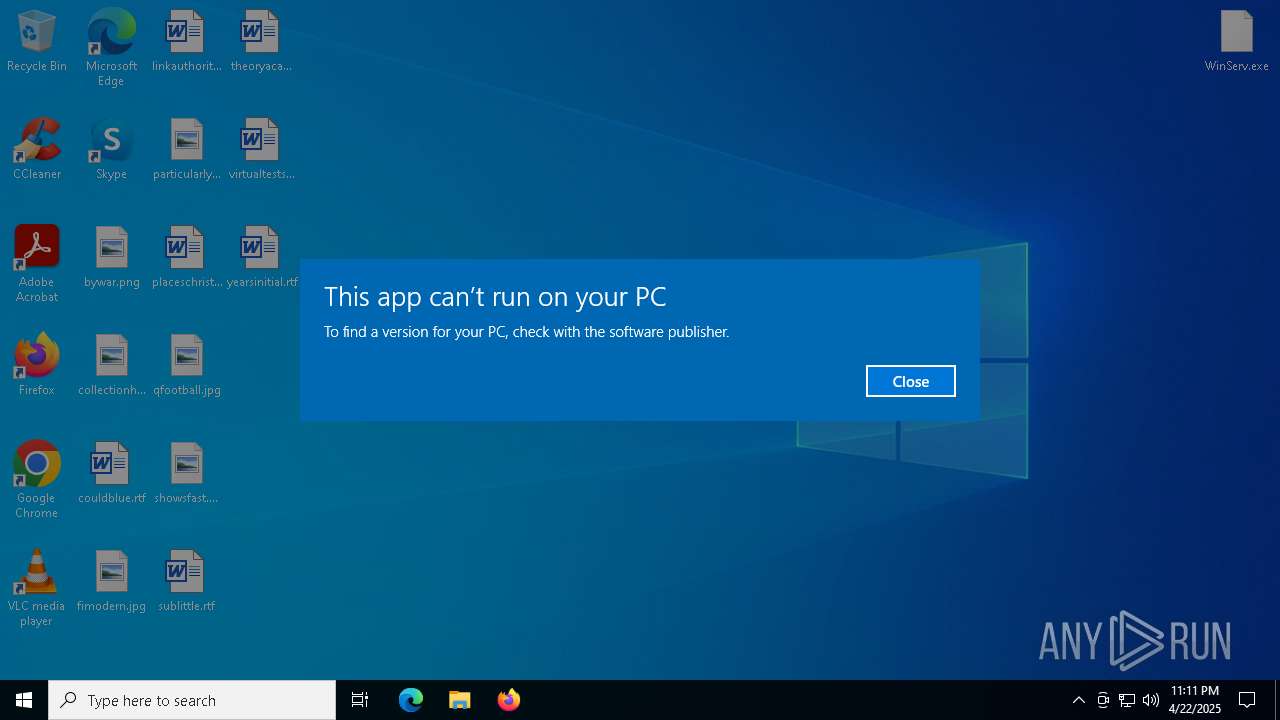
Failed to create an executable file in Windows directory
- WinServ.exe (PID: 7584)
- WinServ.exe (PID: 896)
- WinServ.exe (PID: 5136)
- WinServ.exe (PID: 7488)
- WinServ.exe (PID: 7736)
- WinServ.exe (PID: 684)
- WinServ.exe (PID: 6572)
- WinServ.exe (PID: 7200)
- WinServ.exe (PID: 5260)
- WinServ.exe (PID: 6592)
- WinServ.exe (PID: 5048)
- WinServ.exe (PID: 6244)
Checks supported languages
- WinServ.exe (PID: 7584)
- csrss.exe (PID: 2236)
- Serv.exe (PID: 7860)
- WinServ.exe (PID: 684)
- WinServ.exe (PID: 6572)
- WinServ.exe (PID: 896)
- WinServ.exe (PID: 5136)
- WinServ.exe (PID: 7488)
- WinServ.exe (PID: 7736)
- WinServ.exe (PID: 3140)
- WinServ.exe (PID: 6592)
- WinServ.exe (PID: 7200)
- WinServ.exe (PID: 5260)
- WinServ.exe (PID: 5048)
- WinServ.exe (PID: 672)
- WinServ.exe (PID: 7312)
- WinServ.exe (PID: 5328)
- WinServ.exe (PID: 3024)
- WinServ.exe (PID: 924)
- WinServ.exe (PID: 6244)
- csrss.exe (PID: 7452)
- csrss.exe (PID: 780)
- csrss.exe (PID: 5544)
- csrss.exe (PID: 1764)
- csrss.exe (PID: 7268)
- csrss.exe (PID: 7340)
- WinServ.exe (PID: 8188)
- WinServ.exe (PID: 2140)
- WinServ.exe (PID: 1012)
- WinServ.exe (PID: 6816)
- WinServ.exe (PID: 6264)
- WinServ.exe (PID: 1512)
- WinServ.exe (PID: 8124)
- WinServ.exe (PID: 5680)
- WinServ.exe (PID: 8056)
- WinServ.exe (PID: 7196)
- WinServ.exe (PID: 7336)
- WinServ.exe (PID: 7980)
- WinServ.exe (PID: 7988)
- WinServ.exe (PID: 8024)
- WinServ.exe (PID: 8100)
- WinServ.exe (PID: 5512)
- WinServ.exe (PID: 5084)
- WinServ.exe (PID: 1128)
- WinServ.exe (PID: 5936)
- WinServ.exe (PID: 6424)
- WinServ.exe (PID: 2432)
- WinServ.exe (PID: 5232)
- WinServ.exe (PID: 4728)
- WinServ.exe (PID: 6808)
- WinServ.exe (PID: 732)
- WinServ.exe (PID: 4736)
- WinServ.exe (PID: 5216)
- WinServ.exe (PID: 4112)
- WinServ.exe (PID: 3760)
- WinServ.exe (PID: 4380)
- WinServ.exe (PID: 3976)
- WinServ.exe (PID: 6820)
- WinServ.exe (PID: 7284)
- WinServ.exe (PID: 2344)
- WinServ.exe (PID: 7364)
- WinServ.exe (PID: 7724)
- WinServ.exe (PID: 5244)
- WinServ.exe (PID: 5984)
- WinServ.exe (PID: 2644)
- WinServ.exe (PID: 6572)
- WinServ.exe (PID: 4528)
- WinServ.exe (PID: 6136)
- WinServ.exe (PID: 2420)
- WinServ.exe (PID: 8048)
- WinServ.exe (PID: 232)
- WinServ.exe (PID: 5200)
- WinServ.exe (PID: 7420)
- WinServ.exe (PID: 6700)
- WinServ.exe (PID: 5132)
- WinServ.exe (PID: 7904)
- WinServ.exe (PID: 7492)
- WinServ.exe (PID: 8232)
- WinServ.exe (PID: 4028)
- WinServ.exe (PID: 6028)
- WinServ.exe (PID: 1116)
- WinServ.exe (PID: 8332)
- WinServ.exe (PID: 8384)
- WinServ.exe (PID: 4572)
- WinServ.exe (PID: 7760)
- WinServ.exe (PID: 8292)
- WinServ.exe (PID: 8460)
- WinServ.exe (PID: 8448)
- WinServ.exe (PID: 8796)
- WinServ.exe (PID: 8784)
- WinServ.exe (PID: 8772)
- WinServ.exe (PID: 8856)
- WinServ.exe (PID: 8916)
- WinServ.exe (PID: 8904)
- WinServ.exe (PID: 8808)
- WinServ.exe (PID: 8836)
- WinServ.exe (PID: 9140)
- WinServ.exe (PID: 9200)
- WinServ.exe (PID: 9184)
- WinServ.exe (PID: 7888)
- WinServ.exe (PID: 9172)
- WinServ.exe (PID: 9212)
- WinServ.exe (PID: 6072)
- WinServ.exe (PID: 9156)
- WinServ.exe (PID: 8300)
- WinServ.exe (PID: 8204)
- WinServ.exe (PID: 7316)
- WinServ.exe (PID: 6712)
- WinServ.exe (PID: 5500)
- WinServ.exe (PID: 9132)
- WinServ.exe (PID: 8308)
- WinServ.exe (PID: 8304)
- csrss.exe (PID: 9720)
- csrss.exe (PID: 9732)
- csrss.exe (PID: 4120)
- csrss.exe (PID: 3176)
Reads the machine GUID from the registry
- WinServ.exe (PID: 7584)
- Serv.exe (PID: 7860)
- WinServ.exe (PID: 6572)
- WinServ.exe (PID: 7488)
- WinServ.exe (PID: 7736)
- WinServ.exe (PID: 684)
- WinServ.exe (PID: 5136)
- WinServ.exe (PID: 3140)
- WinServ.exe (PID: 6244)
- WinServ.exe (PID: 5260)
- WinServ.exe (PID: 6592)
- WinServ.exe (PID: 7200)
- WinServ.exe (PID: 5048)
- WinServ.exe (PID: 896)
- WinServ.exe (PID: 924)
- WinServ.exe (PID: 672)
- WinServ.exe (PID: 3024)
- WinServ.exe (PID: 7312)
- csrss.exe (PID: 7452)
- csrss.exe (PID: 780)
- csrss.exe (PID: 5544)
- csrss.exe (PID: 1764)
- csrss.exe (PID: 7340)
- WinServ.exe (PID: 1012)
- WinServ.exe (PID: 5328)
- csrss.exe (PID: 7268)
- WinServ.exe (PID: 6816)
- WinServ.exe (PID: 8188)
- WinServ.exe (PID: 2140)
- WinServ.exe (PID: 7336)
- WinServ.exe (PID: 7980)
- WinServ.exe (PID: 1512)
- WinServ.exe (PID: 8056)
- WinServ.exe (PID: 8124)
- WinServ.exe (PID: 5680)
- WinServ.exe (PID: 6264)
- WinServ.exe (PID: 7196)
- WinServ.exe (PID: 8024)
- WinServ.exe (PID: 7988)
- WinServ.exe (PID: 8100)
- WinServ.exe (PID: 1128)
- WinServ.exe (PID: 2432)
- WinServ.exe (PID: 6424)
- WinServ.exe (PID: 5232)
- WinServ.exe (PID: 5936)
- WinServ.exe (PID: 5084)
- WinServ.exe (PID: 5512)
- WinServ.exe (PID: 7284)
- WinServ.exe (PID: 4736)
- WinServ.exe (PID: 6028)
- WinServ.exe (PID: 5216)
- WinServ.exe (PID: 4380)
- WinServ.exe (PID: 6136)
- WinServ.exe (PID: 2644)
- WinServ.exe (PID: 3760)
- WinServ.exe (PID: 5244)
- WinServ.exe (PID: 8048)
- WinServ.exe (PID: 2420)
- WinServ.exe (PID: 7492)
- WinServ.exe (PID: 7724)
- WinServ.exe (PID: 6820)
- WinServ.exe (PID: 7364)
- WinServ.exe (PID: 4528)
- WinServ.exe (PID: 1116)
- WinServ.exe (PID: 7316)
- WinServ.exe (PID: 6700)
- WinServ.exe (PID: 4728)
- WinServ.exe (PID: 4112)
- WinServ.exe (PID: 732)
- WinServ.exe (PID: 5984)
- WinServ.exe (PID: 8384)
- WinServ.exe (PID: 2344)
- WinServ.exe (PID: 7760)
- WinServ.exe (PID: 8308)
- WinServ.exe (PID: 8460)
- WinServ.exe (PID: 4028)
- WinServ.exe (PID: 7904)
- WinServ.exe (PID: 6572)
- WinServ.exe (PID: 8332)
- WinServ.exe (PID: 8292)
- WinServ.exe (PID: 5980)
- WinServ.exe (PID: 8232)
- WinServ.exe (PID: 8252)
- WinServ.exe (PID: 232)
- WinServ.exe (PID: 8836)
- WinServ.exe (PID: 4572)
- WinServ.exe (PID: 3976)
- WinServ.exe (PID: 8796)
- WinServ.exe (PID: 8784)
- WinServ.exe (PID: 8856)
- WinServ.exe (PID: 8808)
- WinServ.exe (PID: 7420)
- WinServ.exe (PID: 6808)
- WinServ.exe (PID: 8448)
- WinServ.exe (PID: 5132)
- WinServ.exe (PID: 9172)
- WinServ.exe (PID: 8916)
- WinServ.exe (PID: 9200)
- WinServ.exe (PID: 9212)
- WinServ.exe (PID: 5500)
- WinServ.exe (PID: 9184)
- WinServ.exe (PID: 9132)
- csrss.exe (PID: 9720)
- WinServ.exe (PID: 8772)
- WinServ.exe (PID: 8300)
- WinServ.exe (PID: 9156)
- WinServ.exe (PID: 8304)
- WinServ.exe (PID: 7888)
- WinServ.exe (PID: 8904)
- WinServ.exe (PID: 8204)
- WinServ.exe (PID: 6072)
- WinServ.exe (PID: 9140)
- csrss.exe (PID: 9732)
- csrss.exe (PID: 3176)
- csrss.exe (PID: 4120)
- WinServ.exe (PID: 6712)
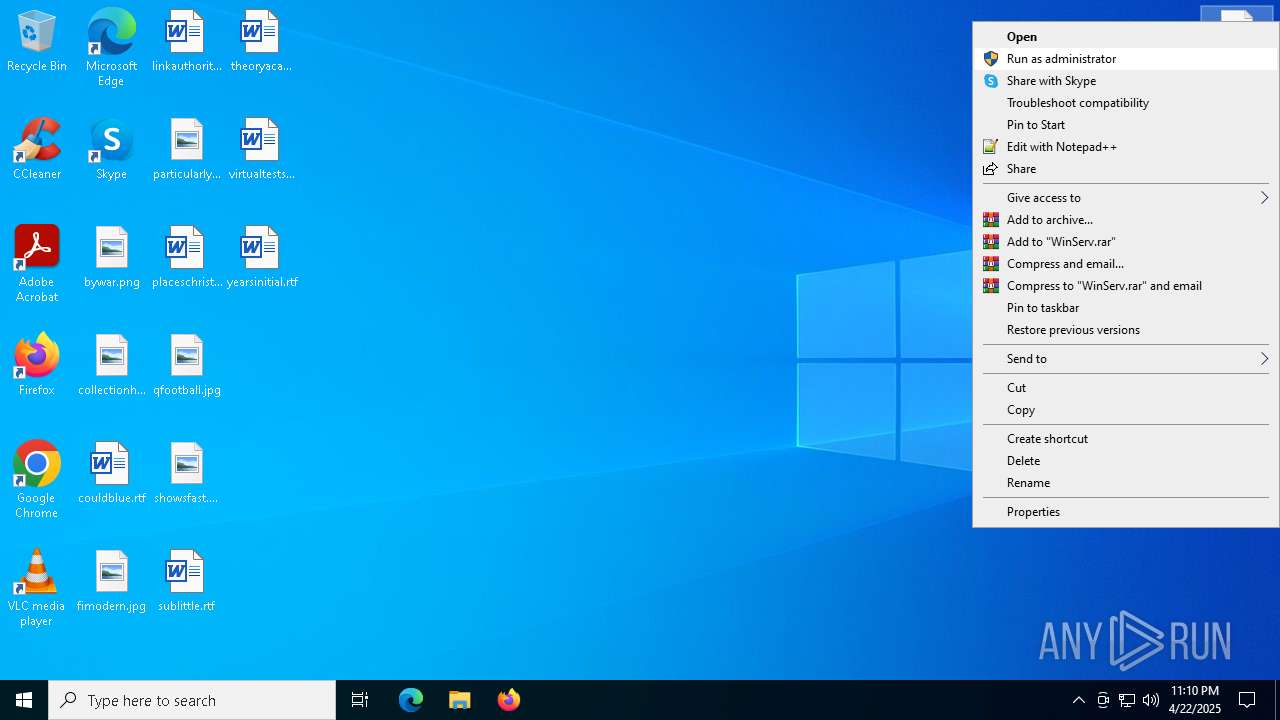
Manual execution by a user
- chrome.exe (PID: 7756)
- chrome.exe (PID: 7744)
- chrome.exe (PID: 7800)
- WinServ.exe (PID: 6572)
- WinServ.exe (PID: 684)
- WinServ.exe (PID: 5136)
- WinServ.exe (PID: 896)
- WinServ.exe (PID: 7736)
- WinServ.exe (PID: 7488)
- WinServ.exe (PID: 3140)
- WinServ.exe (PID: 6592)
- WinServ.exe (PID: 7200)
- WinServ.exe (PID: 6244)
- WinServ.exe (PID: 5260)
- WinServ.exe (PID: 7312)
- WinServ.exe (PID: 672)
- WinServ.exe (PID: 5328)
- WinServ.exe (PID: 3024)
- WinServ.exe (PID: 924)
- WinServ.exe (PID: 5048)
- WinServ.exe (PID: 2140)
- WinServ.exe (PID: 8188)
- WinServ.exe (PID: 1012)
- WinServ.exe (PID: 6816)
- WinServ.exe (PID: 1512)
- WinServ.exe (PID: 6264)
- WinServ.exe (PID: 5680)
- WinServ.exe (PID: 7336)
- WinServ.exe (PID: 7196)
- WinServ.exe (PID: 8056)
- WinServ.exe (PID: 7980)
- WinServ.exe (PID: 8024)
- WinServ.exe (PID: 8100)
- WinServ.exe (PID: 5084)
- WinServ.exe (PID: 1128)
- WinServ.exe (PID: 5936)
- WinServ.exe (PID: 2432)
- WinServ.exe (PID: 6424)
- WinServ.exe (PID: 5232)
- WinServ.exe (PID: 7316)
- WinServ.exe (PID: 4728)
- WinServ.exe (PID: 6808)
- WinServ.exe (PID: 732)
- WinServ.exe (PID: 4736)
- WinServ.exe (PID: 5216)
- WinServ.exe (PID: 3760)
- WinServ.exe (PID: 4112)
- WinServ.exe (PID: 8124)
- WinServ.exe (PID: 4380)
- WinServ.exe (PID: 3976)
- WinServ.exe (PID: 7284)
- WinServ.exe (PID: 7364)
- WinServ.exe (PID: 6820)
- WinServ.exe (PID: 7988)
- WinServ.exe (PID: 2344)
- WinServ.exe (PID: 7724)
- WinServ.exe (PID: 5244)
- WinServ.exe (PID: 5984)
- WinServ.exe (PID: 2644)
- WinServ.exe (PID: 5512)
- WinServ.exe (PID: 7492)
- WinServ.exe (PID: 4528)
- WinServ.exe (PID: 2420)
- WinServ.exe (PID: 6136)
- WinServ.exe (PID: 6572)
- WinServ.exe (PID: 5200)
- WinServ.exe (PID: 8048)
- WinServ.exe (PID: 7420)
- WinServ.exe (PID: 232)
- WinServ.exe (PID: 4028)
- WinServ.exe (PID: 7904)
- WinServ.exe (PID: 5132)
- WinServ.exe (PID: 5980)
- WinServ.exe (PID: 7760)
- WinServ.exe (PID: 4572)
- WinServ.exe (PID: 1116)
- WinServ.exe (PID: 8252)
- WinServ.exe (PID: 6700)
- WinServ.exe (PID: 8232)
- WinServ.exe (PID: 8308)
- WinServ.exe (PID: 8292)
- WinServ.exe (PID: 8332)
- WinServ.exe (PID: 6028)
- WinServ.exe (PID: 8460)
- WinServ.exe (PID: 8384)
- WinServ.exe (PID: 8448)
- WinServ.exe (PID: 8796)
- WinServ.exe (PID: 8772)
- WinServ.exe (PID: 8784)
- WinServ.exe (PID: 8836)
- WinServ.exe (PID: 8808)
- WinServ.exe (PID: 8856)
- WinServ.exe (PID: 8904)
- WinServ.exe (PID: 8916)
- WinServ.exe (PID: 9140)
- WinServ.exe (PID: 9156)
- WinServ.exe (PID: 9132)
- WinServ.exe (PID: 9172)
- WinServ.exe (PID: 9184)
- WinServ.exe (PID: 9200)
- WinServ.exe (PID: 9212)
- WinServ.exe (PID: 7888)
- WinServ.exe (PID: 6072)
- WinServ.exe (PID: 8304)
- WinServ.exe (PID: 6712)
- WinServ.exe (PID: 5500)
- WinServ.exe (PID: 8204)
- WinServ.exe (PID: 8300)
- chrome.exe (PID: 5416)
- chrome.exe (PID: 1196)
- chrome.exe (PID: 812)
- chrome.exe (PID: 1184)
- chrome.exe (PID: 5404)
- chrome.exe (PID: 8084)
- chrome.exe (PID: 7908)
- msedge.exe (PID: 5212)
Create files in a temporary directory
- WinServ.exe (PID: 7584)
- csrss.exe (PID: 2236)
Process checks computer location settings
- WinServ.exe (PID: 7584)
- csrss.exe (PID: 2236)
- WinServ.exe (PID: 896)
- WinServ.exe (PID: 7736)
- WinServ.exe (PID: 7488)
- WinServ.exe (PID: 684)
- WinServ.exe (PID: 6572)
- WinServ.exe (PID: 5136)
- WinServ.exe (PID: 3140)
- WinServ.exe (PID: 5260)
- WinServ.exe (PID: 7200)
- WinServ.exe (PID: 5048)
Reads the software policy settings
- slui.exe (PID: 7668)
- slui.exe (PID: 7396)
Creates files or folders in the user directory
- csrss.exe (PID: 2236)
Checks proxy server information
- slui.exe (PID: 7396)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
NjRat
(PID) Process(7860) Serv.exe
C2channel-hitting.gl.at.ply.gg
Ports32050
BotnetCULT
Options
Auto-run registry keySoftware\Microsoft\Windows\CurrentVersion\Run\Windows
Splitter|-F-|
Versionnull
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (63.1) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (23.8) |
| .dll | | | Win32 Dynamic Link Library (generic) (5.6) |
| .exe | | | Win32 Executable (generic) (3.8) |
| .exe | | | Generic Win/DOS Executable (1.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2053:10:20 16:57:27+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32 |
| LinkerVersion: | 80 |
| CodeSize: | 287744 |
| InitializedDataSize: | 49152 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x4834a |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | - |
| CompanyName: | - |
| FileDescription: | WinServ |
| FileVersion: | 1.0.0.0 |
| InternalName: | WinServ.exe |
| LegalCopyright: | Copyright © WinServ 2013 |
| LegalTrademarks: | - |
| OriginalFileName: | WinServ.exe |
| ProductName: | WinServ |
| ProductVersion: | 1.0.0.0 |
| AssemblyVersion: | 1.0.0.0 |
Total processes
328
Monitored processes
191
Malicious processes
3
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 232 | "C:\Users\admin\Desktop\WinServ.exe" | C:\Users\admin\Desktop\WinServ.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: WinServ Version: 1.0.0.0 Modules
| |||||||||||||||
| 672 | "C:\Users\admin\Desktop\WinServ.exe" | C:\Users\admin\Desktop\WinServ.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: WinServ Version: 1.0.0.0 Modules
| |||||||||||||||
| 684 | "C:\Users\admin\Desktop\WinServ.exe" | C:\Users\admin\Desktop\WinServ.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: WinServ Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 684 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data" /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Crashpad" --annotation=IsOfficialBuild=1 --annotation=channel= --annotation=chromium-version=122.0.6261.70 "--annotation=exe=C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --annotation=plat=Win64 "--annotation=prod=Microsoft Edge" --annotation=ver=122.0.2365.59 --initial-client-data=0x310,0x314,0x318,0x30c,0x320,0x7ffc85e15fd8,0x7ffc85e15fe4,0x7ffc85e15ff0 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 732 | "C:\Users\admin\Desktop\WinServ.exe" | C:\Users\admin\Desktop\WinServ.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: WinServ Version: 1.0.0.0 Modules
| |||||||||||||||
| 780 | "C:\Users\admin\AppData\Local\Temp\csrss.exe" | C:\Users\admin\AppData\Local\Temp\csrss.exe | — | WinServ.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: WinServ Version: 1.0.0.0 Modules
| |||||||||||||||
| 812 | "C:\Program Files\Google\Chrome\Application\chrome.exe" "--disable-features=OptimizationGuideModelDownloading,OptimizationHintsFetching,OptimizationTargetPrediction,OptimizationHints" | C:\Program Files\Google\Chrome\Application\chrome.exe | — | explorer.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 864 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | attrib.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 896 | "C:\Users\admin\Desktop\WinServ.exe" | C:\Users\admin\Desktop\WinServ.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: WinServ Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 920 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=5332 --field-trial-handle=1928,i,6829945983906611514,7975242745023379903,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
Total events
21 992
Read events
21 931
Write events
59
Delete events
2
Modification events
| (PID) Process: | (7744) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 1 | |||
| (PID) Process: | (7756) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 3 | |||
| (PID) Process: | (7756) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 2 | |||
| (PID) Process: | (7800) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (7800) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (7744) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (7744) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (7744) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 0 | |||
| (PID) Process: | (7744) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\PreferenceMACs\Default\extensions.settings |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (7744) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\PreferenceMACs\Default\extensions.settings |
| Operation: | write | Name: | ahfgeienlihckogmohjhadlkjgocpleb |
Value: 3B08F722C14555E595AF269F140EE426CE8DEBAD90D03EE9FF33B95CB34233F6 | |||
Executable files
14
Suspicious files
316
Text files
99
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7744 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF10d9c8.TMP | — | |
MD5:— | SHA256:— | |||
| 7744 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7744 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RF10d9d7.TMP | — | |
MD5:— | SHA256:— | |||
| 7744 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7744 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old~RF10d9c8.TMP | — | |
MD5:— | SHA256:— | |||
| 7744 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7744 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old~RF10d9b8.TMP | — | |
MD5:— | SHA256:— | |||
| 7744 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old~RF10d9e7.TMP | — | |
MD5:— | SHA256:— | |||
| 7744 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7744 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old~RF10d9e7.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
123
DNS requests
135
Threats
9
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.219.150.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5328 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/success.txt?ipv4 | unknown | — | — | whitelisted |
5328 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/canonical.html | unknown | — | — | whitelisted |
208 | SIHClient.exe | GET | 200 | 23.219.150.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
208 | SIHClient.exe | GET | 200 | 23.219.150.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 2.16.164.120:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | 2.16.164.120:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.219.150.101:80 | www.microsoft.com | AKAMAI-AS | CL | whitelisted |
2104 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3216 | svchost.exe | 172.211.123.249:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
7744 | chrome.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
8056 | chrome.exe | 172.217.18.3:443 | clientservices.googleapis.com | GOOGLE | US | whitelisted |
8056 | chrome.exe | 74.125.71.84:443 | accounts.google.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| whitelisted |
www.google.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
update.googleapis.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
8056 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
8056 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
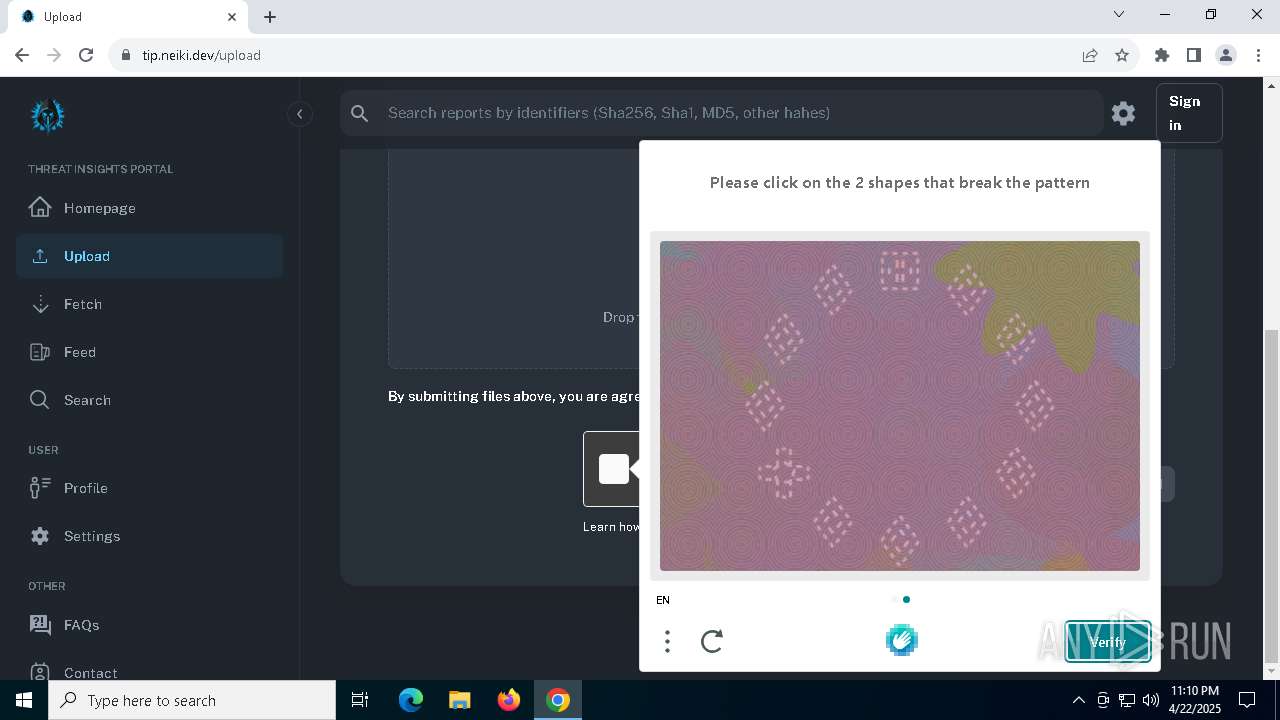
8056 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] hCaptcha Enterprise Challenge |
8056 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] hCaptcha Enterprise Challenge |
2196 | svchost.exe | A Network Trojan was detected | MALWARE [ANY.RUN] Suspected domain Associated with Malware Distribution (.ply .gg) |
2196 | svchost.exe | Misc activity | ET TA_ABUSED_SERVICES Tunneling Service in DNS Lookup (* .ply .gg) |
2196 | svchost.exe | Potentially Bad Traffic | ET INFO playit .gg Tunneling Domain in DNS Lookup |
6132 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] hCaptcha Enterprise Challenge |
6132 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] hCaptcha Enterprise Challenge |