| File name: | t.exe.bin |
| Full analysis: | https://app.any.run/tasks/5def1b46-726a-45c9-bd5e-e260770352cd |
| Verdict: | Malicious activity |
| Threats: | Phorpiex is a malicious software that has been a significant threat in the cybersecurity landscape since 2016. It is a modular malware known for its ability to maintain an extensive botnet. Unlike other botnets, Phorpiex does not concentrate on DDoS attacks. Instead, it has been involved in numerous large-scale spam email campaigns and the distribution of other malicious payloads, such as LockBit. |
| Analysis date: | November 14, 2018, 08:07:16 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 system file, for MS Windows |
| MD5: | EADF7F8807156817BF33516E370F88F0 |
| SHA1: | 997C8FA7A578BBDA7D85CAE670D2317090DDD21D |
| SHA256: | 73651197E4C2712B5781C9B1A37C3CE2848C272018E23782793C1DCCAAF09FB9 |
| SSDEEP: | 3072:yeMvl/ZLoa/qw+e7T9aFmE9VVNS6SodPM9WsN2TLHy9+Msrj:y5ZLotwe52cJMoHLykMIj |
MALICIOUS
Changes Security Center notification settings
- winsvcs.exe (PID: 3116)
Disables Windows Defender Real-time monitoring
- winsvcs.exe (PID: 3116)
PHORPIEX was detected
- winsvcs.exe (PID: 3116)
Connects to CnC server
- winsvcs.exe (PID: 3116)
Changes the autorun value in the registry
- t.exe.bin.exe (PID: 184)
Disables Windows System Restore
- winsvcs.exe (PID: 3116)
SUSPICIOUS
Executable content was dropped or overwritten
- t.exe.bin.exe (PID: 184)
- winsvcs.exe (PID: 3116)
Starts itself from another location
- t.exe.bin.exe (PID: 184)
Creates files in the user directory
- winsvcs.exe (PID: 3116)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:01:17 14:37:29+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 12 |
| CodeSize: | 61952 |
| InitializedDataSize: | 161280 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x5170 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 7.0.0.0 |
| ProductVersionNumber: | 3.0.0.0 |
| FileFlagsMask: | 0x004f |
| FileFlags: | (none) |
| FileOS: | Unknown (0x40534) |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Unknown (457A) |
| CharacterSet: | Unknown (A56B) |
| FileVersion: | 1.0.0.12 |
| ProductVersion: | 1.0.0.12 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 17-Jan-2018 13:37:29 |
| Detected languages: |
|
| FileVersion: | 1.0.0.12 |
| ProductVersion: | 1.0.0.12 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000E8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 7 |
| Time date stamp: | 17-Jan-2018 13:37:29 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00018000 | 0x0000F2E0 | 0x0000D400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.09103 |
.rdata | 0x00011000 | 0x00006838 | 0x00006A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.68962 |
.version\x01 | 0x00028000 | 0x00000001 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.version\x14\x10 | 0x00029000 | 0x00001014 | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0.187535 |
.rsrc | 0x0002B000 | 0x0000FCD0 | 0x0000FE00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.29157 |
.reloc | 0x0003B000 | 0x0000121C | 0x00001400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.24498 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.11786 | 328 | UNKNOWN | Process Default Language | RT_VERSION |
2 | 4.98743 | 9640 | UNKNOWN | Process Default Language | RT_ICON |
3 | 4.25592 | 4264 | UNKNOWN | Process Default Language | RT_ICON |
4 | 7.97458 | 42592 | UNKNOWN | Process Default Language | RT_ICON |
7 | 3.2344 | 864 | UNKNOWN | Process Default Language | RT_STRING |
8 | 3.31012 | 1310 | UNKNOWN | Process Default Language | RT_STRING |
9 | 3.29725 | 1390 | UNKNOWN | Process Default Language | RT_STRING |
10 | 3.26578 | 1248 | UNKNOWN | Process Default Language | RT_STRING |
150 | 4.49098 | 334 | UNKNOWN | Process Default Language | LUPASISU |
170 | 4.45229 | 334 | UNKNOWN | Process Default Language | SENIMUPEZUMOTIBOPINECESAXIKU |
Imports
ADVAPI32.dll |
KERNEL32.dll |
MSIMG32.dll |
SHELL32.dll |
WINHTTP.dll |
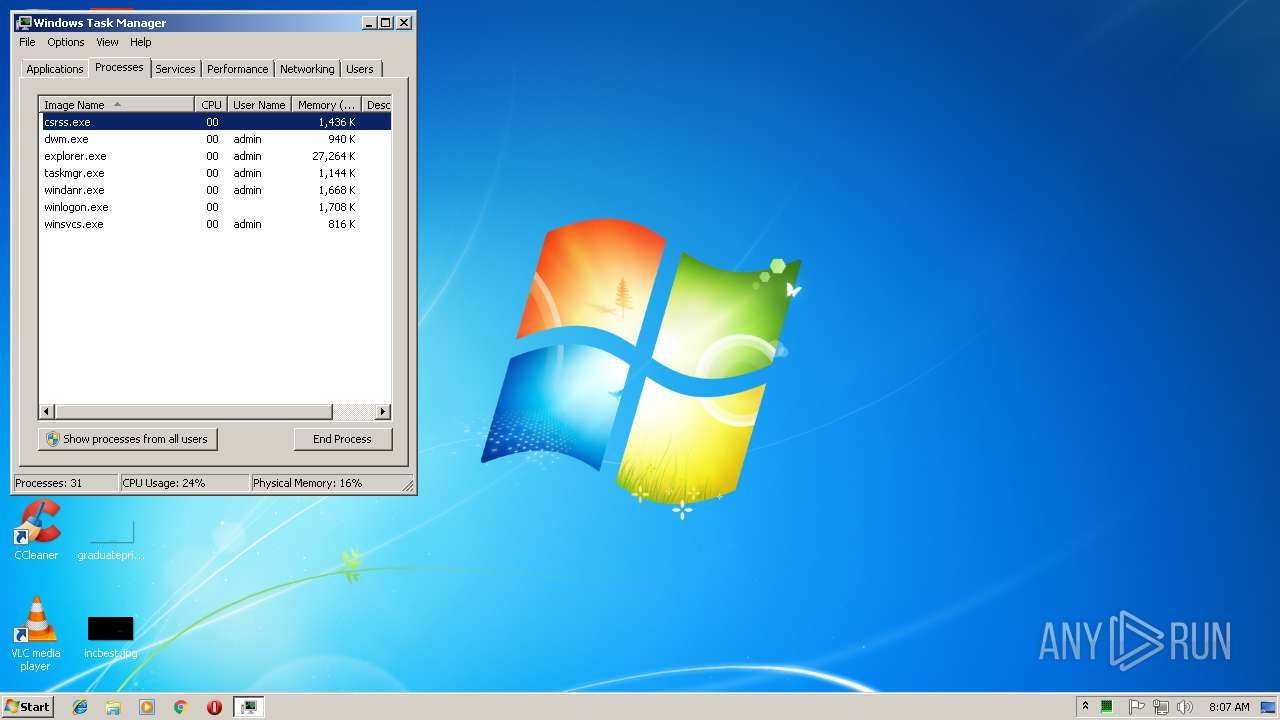
Total processes
33
Monitored processes
3
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 184 | "C:\Users\admin\AppData\Local\Temp\t.exe.bin.exe" | C:\Users\admin\AppData\Local\Temp\t.exe.bin.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3116 | C:\Users\admin\T8094087040787080\winsvcs.exe | C:\Users\admin\T8094087040787080\winsvcs.exe | t.exe.bin.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3772 | "C:\Windows\system32\taskmgr.exe" /4 | C:\Windows\system32\taskmgr.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Task Manager Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
71
Read events
40
Write events
31
Delete events
0
Modification events
| (PID) Process: | (184) t.exe.bin.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | Microsoft Windows Services |
Value: C:\Users\admin\T8094087040787080\winsvcs.exe | |||
| (PID) Process: | (184) t.exe.bin.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | Microsoft Windows Services |
Value: C:\Users\admin\T8094087040787080\winsvcs.exe | |||
| (PID) Process: | (3116) winsvcs.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Microsoft\Windows Defender\Real-time Protection |
| Operation: | write | Name: | DisableScanOnRealtimeEnable |
Value: 1 | |||
| (PID) Process: | (3116) winsvcs.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Microsoft\Windows Defender\Real-time Protection |
| Operation: | write | Name: | DisableOnAccessProtection |
Value: 1 | |||
| (PID) Process: | (3116) winsvcs.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Microsoft\Windows Defender\Real-time Protection |
| Operation: | write | Name: | DisableBehaviorMonitoring |
Value: 1 | |||
| (PID) Process: | (3116) winsvcs.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Security Center |
| Operation: | write | Name: | AntiVirusOverride |
Value: 1 | |||
| (PID) Process: | (3116) winsvcs.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Security Center |
| Operation: | write | Name: | UpdatesOverride |
Value: 1 | |||
| (PID) Process: | (3116) winsvcs.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Security Center |
| Operation: | write | Name: | FirewallOverride |
Value: 1 | |||
| (PID) Process: | (3116) winsvcs.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Security Center |
| Operation: | write | Name: | AntiVirusDisableNotify |
Value: 1 | |||
| (PID) Process: | (3116) winsvcs.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Security Center |
| Operation: | write | Name: | UpdatesDisableNotify |
Value: 1 | |||
Executable files
2
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 184 | t.exe.bin.exe | C:\Users\admin\T8094087040787080\winsvcs.exe | executable | |
MD5:— | SHA256:— | |||
| 3116 | winsvcs.exe | C:\Users\admin\AppData\Local\Temp\Windows Archive Manager.exe | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
1
DNS requests
88
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3116 | winsvcs.exe | GET | 200 | 92.63.197.48:80 | http://92.63.197.48/t.php?new=1 | RU | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3116 | winsvcs.exe | 92.63.197.48:80 | — | — | RU | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
ssofhoseuegsgrfnu.ru |
| malicious |
slpsrgpsrhojifdij.ru |
| malicious |
aiiaiafrzrueuedur.ru |
| malicious |
fuaiuebndieufeufu.ru |
| unknown |
eiifngjfksisiufjf.ru |
| unknown |
eoroooskfogihisrg.ru |
| malicious |
noeuaoenriusfiruu.ru |
| malicious |
iuirshriuisruruuf.ru |
| malicious |
afeifieuuufufufuf.ru |
| malicious |
srndndubsbsifurfd.ru |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3116 | winsvcs.exe | A Network Trojan was detected | MALWARE [PTsecurity] Win32/Phorpiex Bot Checkin (HTTP) |
1 ETPRO signatures available at the full report