| File name: | Venom RAT + HVNC + Stealer + Grabber.exe |
| Full analysis: | https://app.any.run/tasks/d7a0722f-a530-4b4b-9f47-85c0ea836e19 |
| Verdict: | Malicious activity |
| Threats: | AsyncRAT is a RAT that can monitor and remotely control infected systems. This malware was introduced on Github as a legitimate open-source remote administration software, but hackers use it for its many powerful malicious functions. |
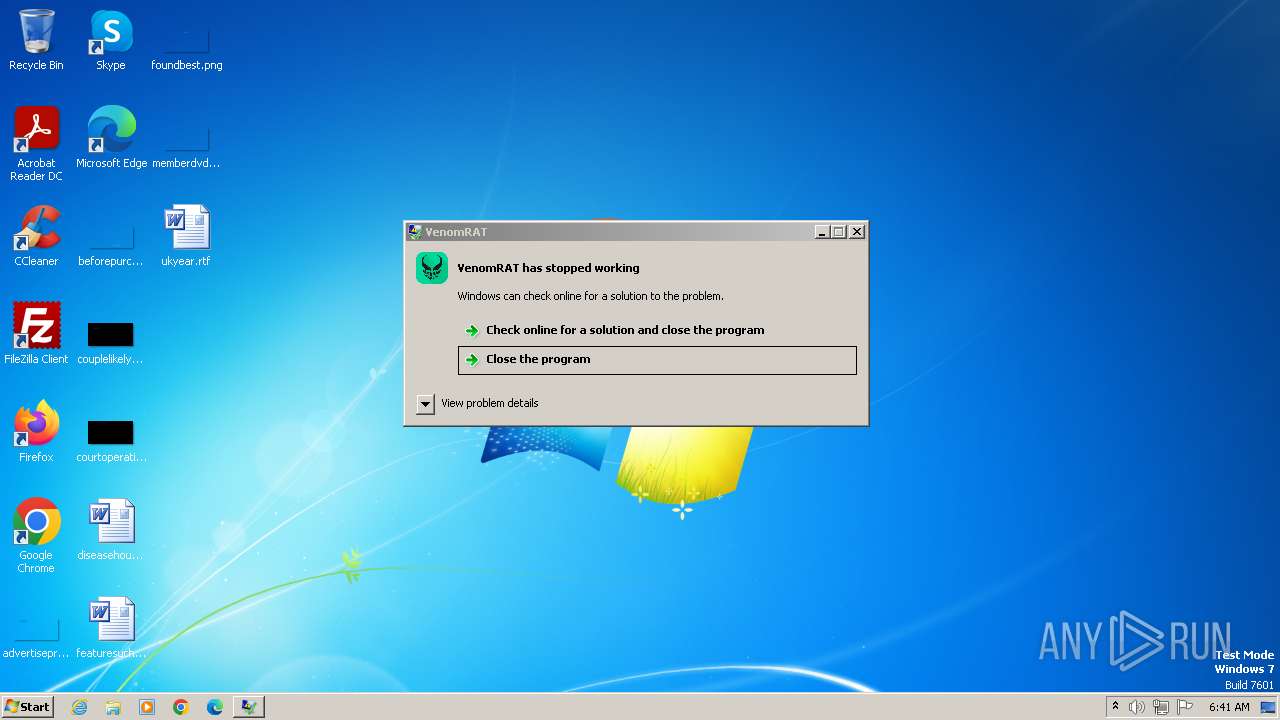
| Analysis date: | October 22, 2023, 05:41:45 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | 3B3A304C6FC7A3A1D9390D7CBFF56634 |
| SHA1: | E8BD5244E6362968F5017680DA33F1E90AE63DD7 |
| SHA256: | 7331368C01B2A16BDA0F013F376A039E6AEB4CB2DD8B0C2AFC7CA208FB544C58 |
| SSDEEP: | 196608:Nja6chUZX81lbFklbYJygrP7aIBhLkNPFCZZwiJl1NLIsPA8fxvuIMzd/95UhS1G:qT+P+Zw6NLIsFfskh1BmXG04N |
MALICIOUS
ASYNCRAT has been detected (YARA)
- Venom RAT + HVNC + Stealer + Grabber.exe (PID: 3852)
SUSPICIOUS
No suspicious indicators.INFO
Checks supported languages
- Venom RAT + HVNC + Stealer + Grabber.exe (PID: 3852)
Reads the computer name
- Venom RAT + HVNC + Stealer + Grabber.exe (PID: 3852)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (42.9) |
|---|---|---|
| .exe | | | Win32 EXE PECompact compressed (generic) (24.3) |
| .exe | | | Win64 Executable (generic) (16.1) |
| .scr | | | Windows screen saver (7.6) |
| .dll | | | Win32 Dynamic Link Library (generic) (3.8) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2068:12:31 08:38:15+01:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32 |
| LinkerVersion: | 48 |
| CodeSize: | 14857728 |
| InitializedDataSize: | 10240 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xe2d4ae |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 6.0.1.0 |
| ProductVersionNumber: | 6.0.1.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | - |
| CompanyName: | - |
| FileDescription: | VenomRAT |
| FileVersion: | 6.0.1 |
| InternalName: | Venom RAT + HVNC + Stealer + Grabber.exe |
| LegalCopyright: | Copyright © 2023 |
| LegalTrademarks: | - |
| OriginalFileName: | Venom RAT + HVNC + Stealer + Grabber.exe |
| ProductName: | - |
| ProductVersion: | 6.0.1 |
| AssemblyVersion: | 6.0.1.0 |
Total processes
37
Monitored processes
1
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3852 | "C:\Users\admin\AppData\Local\Temp\Venom RAT + HVNC + Stealer + Grabber.exe" | C:\Users\admin\AppData\Local\Temp\Venom RAT + HVNC + Stealer + Grabber.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: VenomRAT Exit code: 3762504530 Version: 6.0.1 Modules
| |||||||||||||||
Total events
28
Read events
28
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
2
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |