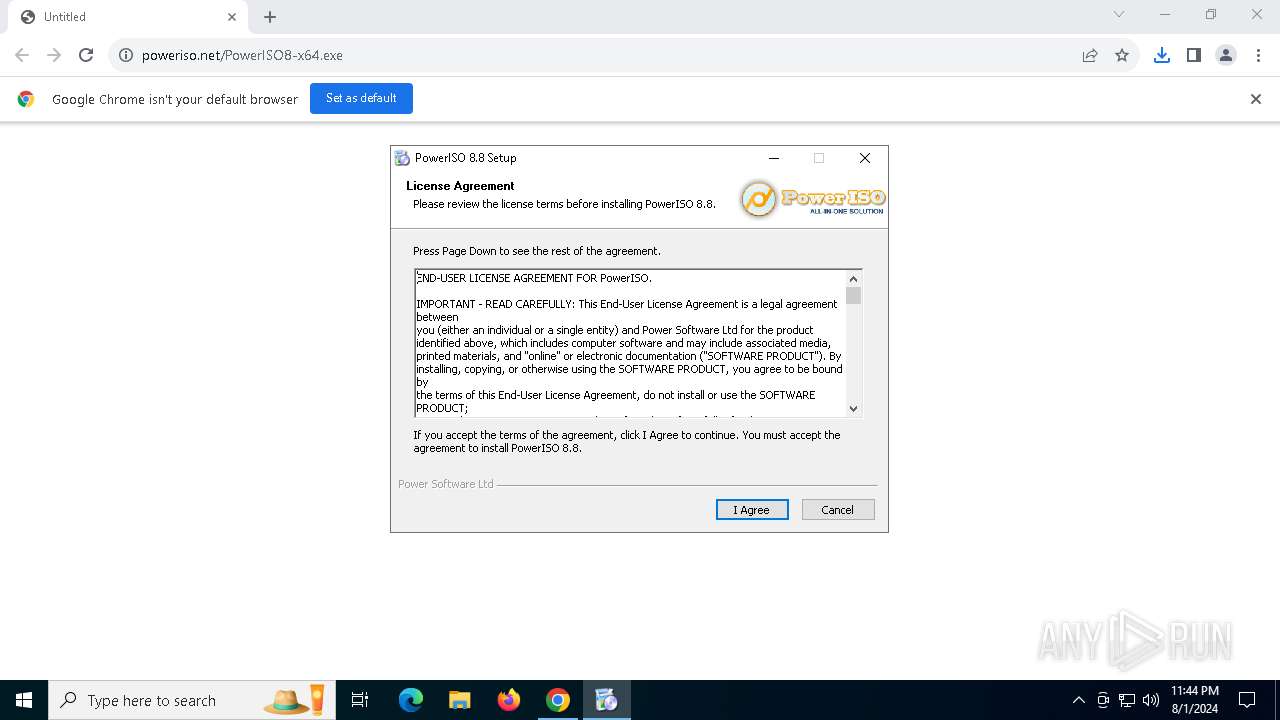
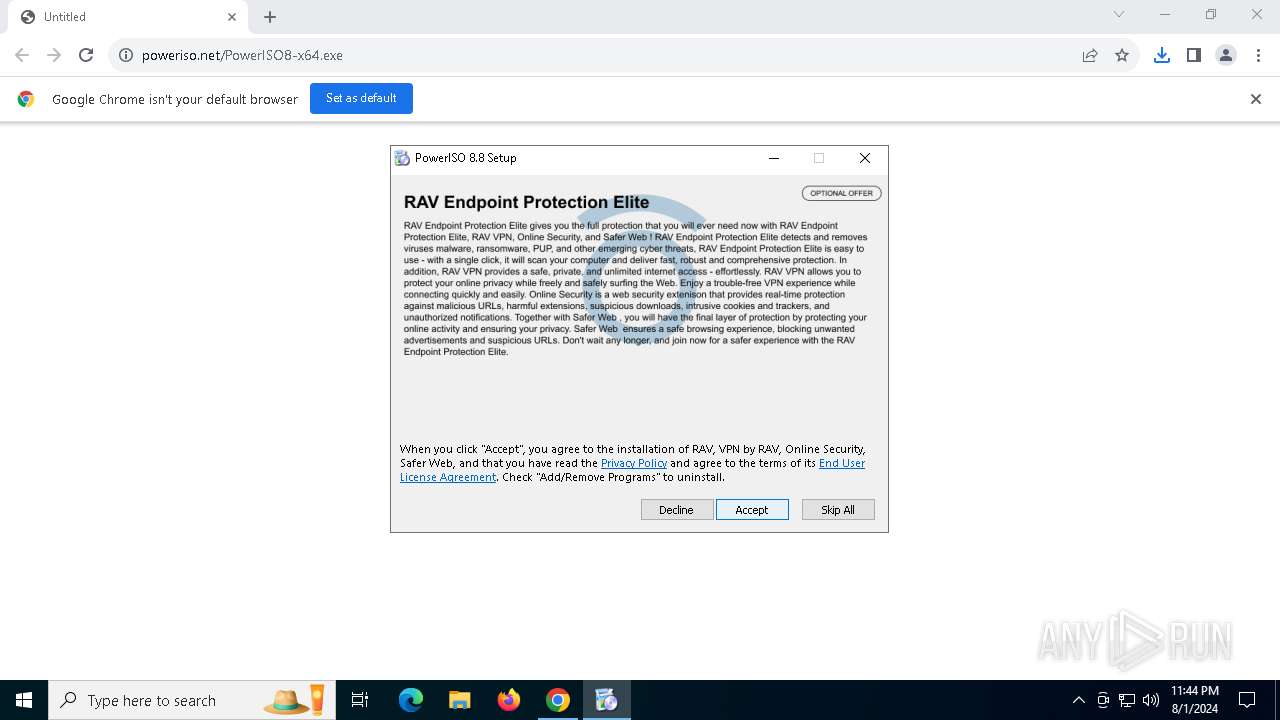
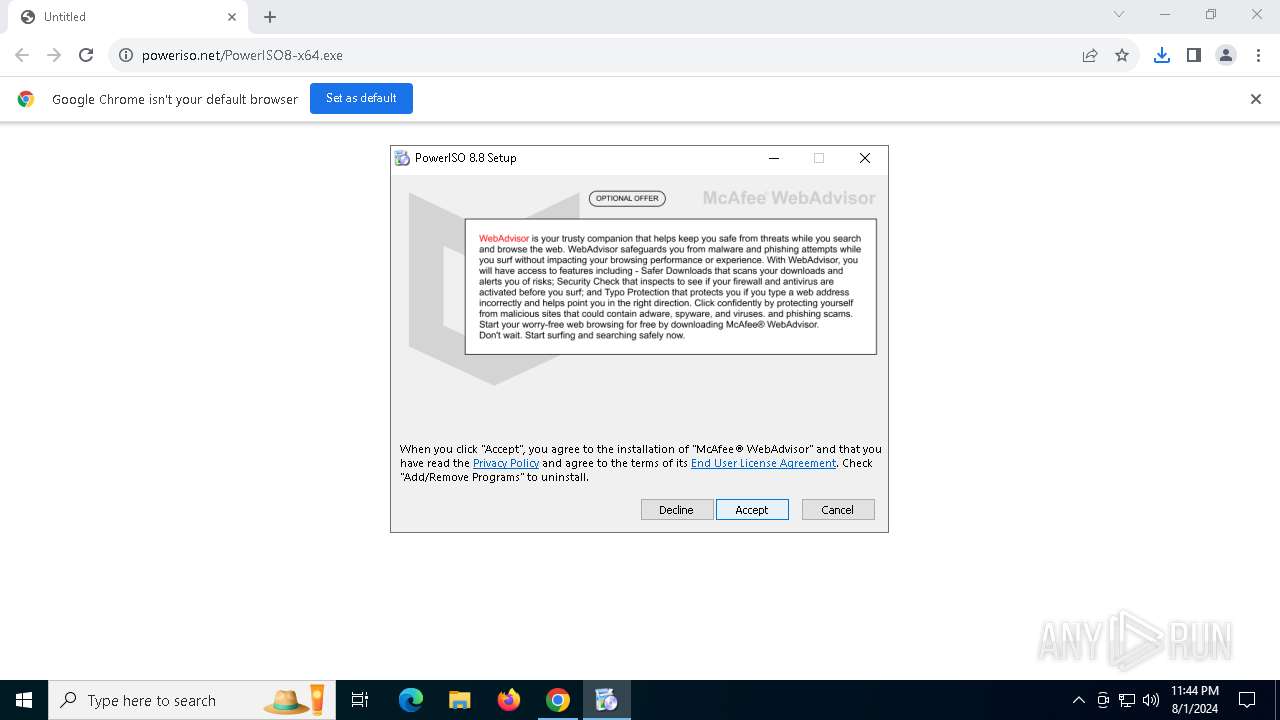
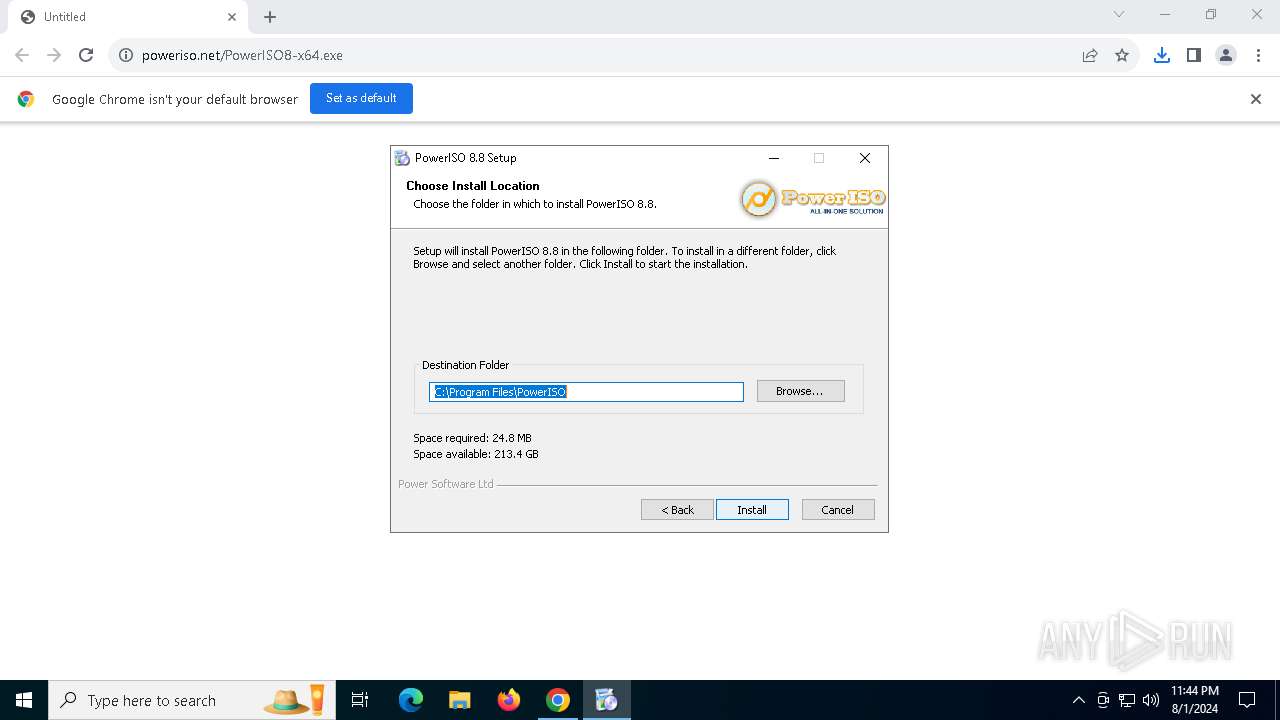
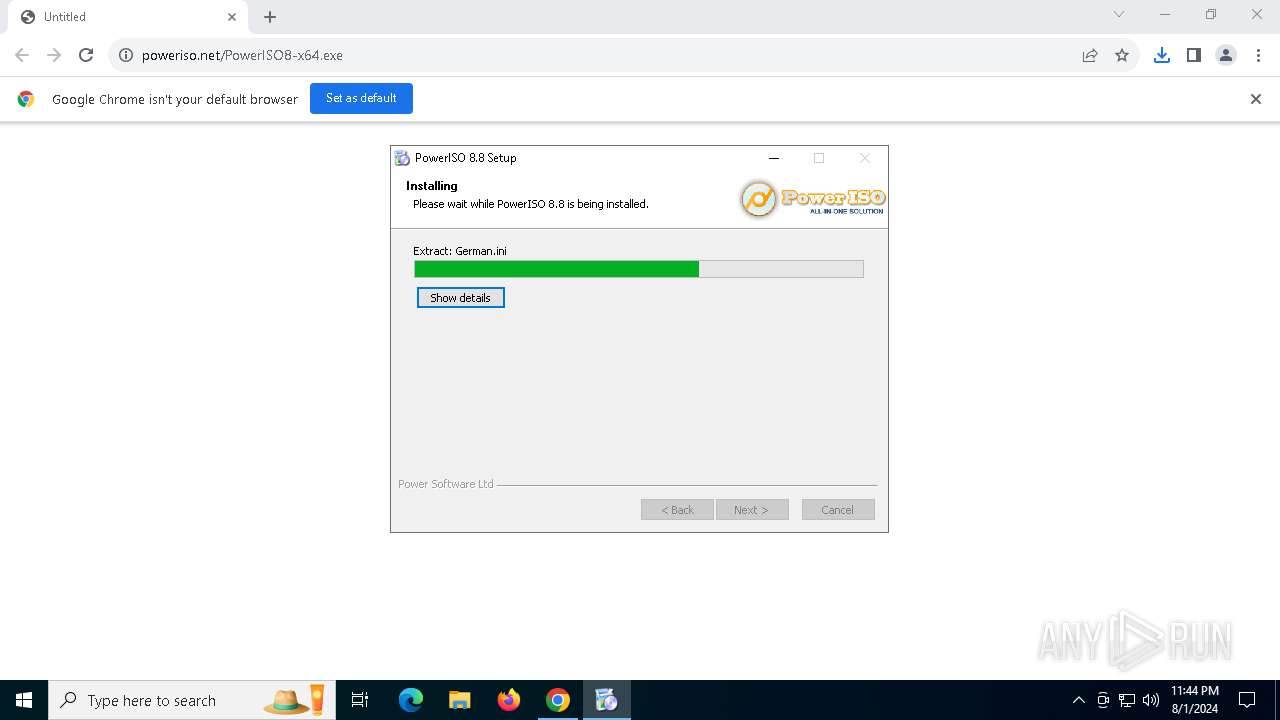
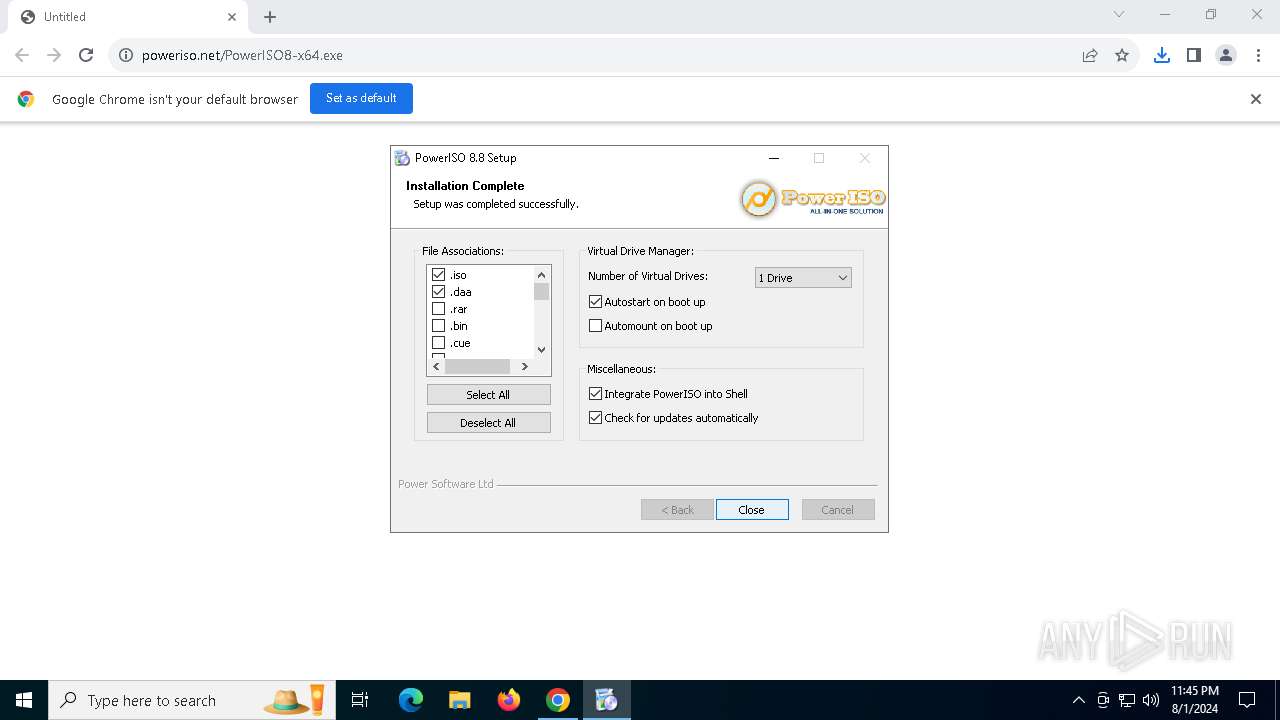
| URL: | https://www.poweriso.net/PowerISO8-x64.exe |
| Full analysis: | https://app.any.run/tasks/69470cf8-c9a8-4cec-a6ed-6c9b9d46f585 |
| Verdict: | Malicious activity |
| Threats: | Crypto mining malware is a resource-intensive threat that infiltrates computers with the purpose of mining cryptocurrencies. This type of threat can be deployed either on an infected machine or a compromised website. In both cases the miner will utilize the computing power of the device and its network bandwidth. |
| Analysis date: | August 01, 2024, 23:44:09 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | B34820E23EE1A9BA3A71C3F95EB62962 |
| SHA1: | 07B1A6AC9CB2A9BC5D1C6DDCD4BDAC285EE85C1A |
| SHA256: | 72887DACDEAA9EEC93E0C2F4F816A2F47D117F959AF627085E30BA8408FCB292 |
| SSDEEP: | 3:N8DSLCMWKLLAs1JyX/RtAdA:2OLFLLA/pOA |
MALICIOUS
Drops the executable file immediately after the start
- PowerISO8-x64.exe (PID: 4292)
- setup64.exe (PID: 7848)
- rsStubActivator.exe (PID: 7884)
- kjq2uri2.exe (PID: 8048)
- installer.exe (PID: 4540)
- installer.exe (PID: 7808)
- UnifiedStub-installer.exe (PID: 8084)
Registers / Runs the DLL via REGSVR32.EXE
- PowerISO8-x64.exe (PID: 4292)
- installer.exe (PID: 7808)
Changes the autorun value in the registry
- PowerISO8-x64.exe (PID: 4292)
- rundll32.exe (PID: 8552)
- rundll32.exe (PID: 6304)
Actions looks like stealing of personal data
- servicehost.exe (PID: 6212)
- uihost.exe (PID: 8032)
- UnifiedStub-installer.exe (PID: 8084)
- rsEngineSvc.exe (PID: 7532)
- rsVPNSvc.exe (PID: 8268)
- rsDNSSvc.exe (PID: 4424)
SUSPICIOUS
Malware-specific behavior (creating "System.dll" in Temp)
- PowerISO8-x64.exe (PID: 4292)
The process creates files with name similar to system file names
- PowerISO8-x64.exe (PID: 4292)
- installer.exe (PID: 7808)
- UnifiedStub-installer.exe (PID: 8084)
Executable content was dropped or overwritten
- PowerISO8-x64.exe (PID: 4292)
- setup64.exe (PID: 7848)
- kjq2uri2.exe (PID: 8048)
- rsStubActivator.exe (PID: 7884)
- UnifiedStub-installer.exe (PID: 8084)
- installer.exe (PID: 4540)
- installer.exe (PID: 7808)
Drops a system driver (possible attempt to evade defenses)
- setup64.exe (PID: 7848)
- UnifiedStub-installer.exe (PID: 8084)
Creates files in the driver directory
- setup64.exe (PID: 7848)
- UnifiedStub-installer.exe (PID: 8084)
Reads security settings of Internet Explorer
- PowerISO8-x64.exe (PID: 4292)
- saBSI.exe (PID: 7924)
- rsStubActivator.exe (PID: 7884)
- installer.exe (PID: 7808)
- uihost.exe (PID: 8032)
- UnifiedStub-installer.exe (PID: 8084)
- rsWSC.exe (PID: 1860)
- rsEngineSvc.exe (PID: 8996)
- rsEDRSvc.exe (PID: 8560)
- rsEngineSvc.exe (PID: 7532)
- rsVPNSvc.exe (PID: 9864)
- rsDNSSvc.exe (PID: 9428)
Creates or modifies Windows services
- PowerISO8-x64.exe (PID: 4292)
- UnifiedStub-installer.exe (PID: 8084)
- rundll32.exe (PID: 8552)
Checks Windows Trust Settings
- saBSI.exe (PID: 7924)
- installer.exe (PID: 7808)
- servicehost.exe (PID: 6212)
- uihost.exe (PID: 8032)
- updater.exe (PID: 8784)
- UnifiedStub-installer.exe (PID: 8084)
- rsWSC.exe (PID: 1860)
- rsEngineSvc.exe (PID: 8996)
- rsWSC.exe (PID: 208)
- rsEDRSvc.exe (PID: 8560)
- rsEngineSvc.exe (PID: 7532)
- rsEDRSvc.exe (PID: 8100)
- rsVPNSvc.exe (PID: 9864)
- rsDNSSvc.exe (PID: 9428)
Drops 7-zip archiver for unpacking
- PowerISO8-x64.exe (PID: 4292)
- UnifiedStub-installer.exe (PID: 8084)
Creates a software uninstall entry
- PowerISO8-x64.exe (PID: 4292)
- UnifiedStub-installer.exe (PID: 8084)
- installer.exe (PID: 7808)
- servicehost.exe (PID: 6212)
Process drops legitimate windows executable
- kjq2uri2.exe (PID: 8048)
- installer.exe (PID: 7808)
- UnifiedStub-installer.exe (PID: 8084)
The process verifies whether the antivirus software is installed
- saBSI.exe (PID: 7924)
- installer.exe (PID: 4540)
- installer.exe (PID: 7808)
- regsvr32.exe (PID: 7920)
- regsvr32.exe (PID: 4064)
- regsvr32.exe (PID: 7140)
- cmd.exe (PID: 8520)
- uihost.exe (PID: 8032)
- servicehost.exe (PID: 6212)
- updater.exe (PID: 8784)
- cmd.exe (PID: 8608)
- cmd.exe (PID: 8832)
- cmd.exe (PID: 8968)
- cmd.exe (PID: 9036)
- cmd.exe (PID: 8868)
- rsEngineSvc.exe (PID: 7532)
- rsVPNSvc.exe (PID: 8268)
- rsDNSSvc.exe (PID: 4424)
Reads the date of Windows installation
- rsStubActivator.exe (PID: 7884)
- PowerISO8-x64.exe (PID: 4292)
- rsEDRSvc.exe (PID: 8100)
- rsEngineSvc.exe (PID: 7532)
Searches for installed software
- UnifiedStub-installer.exe (PID: 8084)
- updater.exe (PID: 8784)
- rsVPNSvc.exe (PID: 8268)
Executes as Windows Service
- rsSyncSvc.exe (PID: 3540)
- servicehost.exe (PID: 6212)
- rsClientSvc.exe (PID: 8872)
- rsWSC.exe (PID: 208)
- rsEngineSvc.exe (PID: 7532)
- rsEDRSvc.exe (PID: 8100)
- WmiApSrv.exe (PID: 6376)
- rsVPNClientSvc.exe (PID: 7120)
- rsVPNSvc.exe (PID: 8268)
- WmiApSrv.exe (PID: 1644)
- rsDNSClientSvc.exe (PID: 7632)
- rsDNSResolver.exe (PID: 9212)
- rsDNSSvc.exe (PID: 4424)
- WmiApSrv.exe (PID: 2464)
Creates/Modifies COM task schedule object
- regsvr32.exe (PID: 7392)
- regsvr32.exe (PID: 7140)
- regsvr32.exe (PID: 7920)
Adds/modifies Windows certificates
- saBSI.exe (PID: 7924)
- servicehost.exe (PID: 6212)
- UnifiedStub-installer.exe (PID: 8084)
- rsEngineSvc.exe (PID: 7532)
Reads Mozilla Firefox installation path
- servicehost.exe (PID: 6212)
- uihost.exe (PID: 8032)
Starts CMD.EXE for commands execution
- servicehost.exe (PID: 6212)
- updater.exe (PID: 8784)
- rsDNSSvc.exe (PID: 4424)
Hides command output
- cmd.exe (PID: 8520)
- cmd.exe (PID: 8832)
- cmd.exe (PID: 8608)
- cmd.exe (PID: 8868)
The process drops C-runtime libraries
- UnifiedStub-installer.exe (PID: 8084)
Uses RUNDLL32.EXE to load library
- UnifiedStub-installer.exe (PID: 8084)
Uses WEVTUTIL.EXE to install publishers and event logs from the manifest
- UnifiedStub-installer.exe (PID: 8084)
Reads the BIOS version
- rsEDRSvc.exe (PID: 8100)
- rsEngineSvc.exe (PID: 7532)
Dropped object may contain URLs of mainers pools
- rsEngineSvc.exe (PID: 7532)
The process checks if it is being run in the virtual environment
- rsEngineSvc.exe (PID: 7532)
- rsVPNSvc.exe (PID: 8268)
- rsDNSSvc.exe (PID: 4424)
Application launched itself
- rsAppUI.exe (PID: 3360)
- rsAppUI.exe (PID: 9900)
- rsAppUI.exe (PID: 10164)
Process checks is Powershell's Script Block Logging on
- rsEDRSvc.exe (PID: 8100)
Process uses IPCONFIG to clear DNS cache
- cmd.exe (PID: 10212)
- cmd.exe (PID: 10700)
There is functionality for taking screenshot (YARA)
- rsVPNSvc.exe (PID: 8268)
INFO
Reads Microsoft Office registry keys
- chrome.exe (PID: 6392)
- msedge.exe (PID: 420)
- PowerISO8-x64.exe (PID: 4292)
- msedge.exe (PID: 8076)
Executable content was dropped or overwritten
- chrome.exe (PID: 6392)
Drops the executable file immediately after the start
- chrome.exe (PID: 6392)
The process uses the downloaded file
- chrome.exe (PID: 304)
- chrome.exe (PID: 6392)
Checks supported languages
- PowerISO8-x64.exe (PID: 4292)
- rsStubActivator.exe (PID: 7884)
- setup64.exe (PID: 7848)
- devcon.exe (PID: 7824)
- saBSI.exe (PID: 7924)
- UnifiedStub-installer.exe (PID: 8084)
- kjq2uri2.exe (PID: 8048)
- rsSyncSvc.exe (PID: 2248)
- rsSyncSvc.exe (PID: 3540)
- PWRISOVM.EXE (PID: 7496)
- installer.exe (PID: 7808)
- installer.exe (PID: 4540)
- servicehost.exe (PID: 6212)
- uihost.exe (PID: 8032)
- updater.exe (PID: 8784)
- rsWSC.exe (PID: 1860)
- rsWSC.exe (PID: 208)
- rsClientSvc.exe (PID: 8872)
- rsEngineSvc.exe (PID: 8996)
- rsClientSvc.exe (PID: 6300)
- identity_helper.exe (PID: 1984)
- rsEngineSvc.exe (PID: 7532)
- rsHelper.exe (PID: 8784)
- rsEDRSvc.exe (PID: 8560)
- rsEDRSvc.exe (PID: 8100)
- EPP.exe (PID: 7468)
- rsAppUI.exe (PID: 3360)
- rsAppUI.exe (PID: 9416)
- rsAppUI.exe (PID: 9436)
- rsAppUI.exe (PID: 9464)
- rsAppUI.exe (PID: 9700)
- rsLitmus.A.exe (PID: 9828)
- rsVPNClientSvc.exe (PID: 7880)
- rsVPNClientSvc.exe (PID: 7120)
- rsVPNSvc.exe (PID: 9864)
- rsVPNSvc.exe (PID: 8268)
- VPN.exe (PID: 10020)
- rsAppUI.exe (PID: 9900)
- rsAppUI.exe (PID: 10224)
- rsAppUI.exe (PID: 6176)
- rsDNSClientSvc.exe (PID: 7064)
- rsAppUI.exe (PID: 7232)
- rsAppUI.exe (PID: 4664)
- rsDNSResolver.exe (PID: 9212)
- rsDNSSvc.exe (PID: 9428)
- rsDNSClientSvc.exe (PID: 7632)
- rsDNSResolver.exe (PID: 10100)
- rsDNSResolver.exe (PID: 9844)
- rsDNSSvc.exe (PID: 4424)
- rsAppUI.exe (PID: 10384)
- rsAppUI.exe (PID: 10416)
- DNS.exe (PID: 1644)
- rsAppUI.exe (PID: 10164)
- rsAppUI.exe (PID: 10012)
- rsAppUI.exe (PID: 4292)
- rsAppUI.exe (PID: 10432)
Reads the computer name
- PowerISO8-x64.exe (PID: 4292)
- rsStubActivator.exe (PID: 7884)
- saBSI.exe (PID: 7924)
- UnifiedStub-installer.exe (PID: 8084)
- rsSyncSvc.exe (PID: 2248)
- rsSyncSvc.exe (PID: 3540)
- installer.exe (PID: 7808)
- uihost.exe (PID: 8032)
- servicehost.exe (PID: 6212)
- updater.exe (PID: 8784)
- rsWSC.exe (PID: 1860)
- rsClientSvc.exe (PID: 6300)
- rsWSC.exe (PID: 208)
- rsEngineSvc.exe (PID: 8996)
- rsClientSvc.exe (PID: 8872)
- rsEngineSvc.exe (PID: 7532)
- identity_helper.exe (PID: 1984)
- rsEDRSvc.exe (PID: 8560)
- rsHelper.exe (PID: 8784)
- rsEDRSvc.exe (PID: 8100)
- rsAppUI.exe (PID: 3360)
- rsAppUI.exe (PID: 9416)
- rsAppUI.exe (PID: 9436)
- rsVPNClientSvc.exe (PID: 7880)
- rsVPNClientSvc.exe (PID: 7120)
- rsVPNSvc.exe (PID: 9864)
- rsVPNSvc.exe (PID: 8268)
- rsAppUI.exe (PID: 9900)
- rsAppUI.exe (PID: 10224)
- rsAppUI.exe (PID: 7232)
- rsDNSResolver.exe (PID: 9212)
- rsDNSSvc.exe (PID: 9428)
- rsDNSClientSvc.exe (PID: 7632)
- rsDNSClientSvc.exe (PID: 7064)
- rsDNSResolver.exe (PID: 9844)
- rsDNSSvc.exe (PID: 4424)
- rsAppUI.exe (PID: 10164)
- rsAppUI.exe (PID: 10384)
- rsAppUI.exe (PID: 10012)
- rsAppUI.exe (PID: 4292)
- rsAppUI.exe (PID: 10416)
Reads the machine GUID from the registry
- PowerISO8-x64.exe (PID: 4292)
- rsStubActivator.exe (PID: 7884)
- saBSI.exe (PID: 7924)
- UnifiedStub-installer.exe (PID: 8084)
- installer.exe (PID: 7808)
- servicehost.exe (PID: 6212)
- uihost.exe (PID: 8032)
- updater.exe (PID: 8784)
- rsWSC.exe (PID: 1860)
- rsWSC.exe (PID: 208)
- rsEngineSvc.exe (PID: 8996)
- rsEngineSvc.exe (PID: 7532)
- rsHelper.exe (PID: 8784)
- rsEDRSvc.exe (PID: 8560)
- rsEDRSvc.exe (PID: 8100)
- rsAppUI.exe (PID: 3360)
- rsVPNSvc.exe (PID: 9864)
- rsVPNSvc.exe (PID: 8268)
- rsAppUI.exe (PID: 9900)
- rsDNSSvc.exe (PID: 9428)
- rsDNSSvc.exe (PID: 4424)
- rsAppUI.exe (PID: 10164)
- rsAppUI.exe (PID: 10012)
- rsAppUI.exe (PID: 4292)
Create files in a temporary directory
- PowerISO8-x64.exe (PID: 4292)
- rsStubActivator.exe (PID: 7884)
- kjq2uri2.exe (PID: 8048)
- saBSI.exe (PID: 7924)
- installer.exe (PID: 7808)
- UnifiedStub-installer.exe (PID: 8084)
- rsAppUI.exe (PID: 3360)
- rsAppUI.exe (PID: 9900)
- rsAppUI.exe (PID: 10164)
Reads Environment values
- PowerISO8-x64.exe (PID: 4292)
- rsStubActivator.exe (PID: 7884)
- UnifiedStub-installer.exe (PID: 8084)
- servicehost.exe (PID: 6212)
- rsEngineSvc.exe (PID: 7532)
- identity_helper.exe (PID: 1984)
- rsEDRSvc.exe (PID: 8100)
- rsAppUI.exe (PID: 3360)
- rsVPNSvc.exe (PID: 8268)
- rsAppUI.exe (PID: 9900)
- rsDNSSvc.exe (PID: 4424)
- rsAppUI.exe (PID: 10164)
Disables trace logs
- PowerISO8-x64.exe (PID: 4292)
- rsStubActivator.exe (PID: 7884)
- UnifiedStub-installer.exe (PID: 8084)
- rsEngineSvc.exe (PID: 7532)
- rsEDRSvc.exe (PID: 8100)
- rsVPNSvc.exe (PID: 8268)
- rsDNSSvc.exe (PID: 4424)
Checks proxy server information
- PowerISO8-x64.exe (PID: 4292)
- rsStubActivator.exe (PID: 7884)
- saBSI.exe (PID: 7924)
- UnifiedStub-installer.exe (PID: 8084)
- rsWSC.exe (PID: 1860)
- rsAppUI.exe (PID: 3360)
- rsAppUI.exe (PID: 9900)
- rsAppUI.exe (PID: 10164)
Reads the software policy settings
- PowerISO8-x64.exe (PID: 4292)
- rsStubActivator.exe (PID: 7884)
- saBSI.exe (PID: 7924)
- UnifiedStub-installer.exe (PID: 8084)
- installer.exe (PID: 7808)
- servicehost.exe (PID: 6212)
- uihost.exe (PID: 8032)
- updater.exe (PID: 8784)
- rsWSC.exe (PID: 1860)
- rsEngineSvc.exe (PID: 8996)
- rsEngineSvc.exe (PID: 7532)
- rsEDRSvc.exe (PID: 8560)
- rsWSC.exe (PID: 208)
- rsEDRSvc.exe (PID: 8100)
- rsVPNSvc.exe (PID: 9864)
- rsVPNSvc.exe (PID: 8268)
- rsDNSSvc.exe (PID: 4424)
- rsDNSSvc.exe (PID: 9428)
Creates files in the program directory
- PowerISO8-x64.exe (PID: 4292)
- saBSI.exe (PID: 7924)
- UnifiedStub-installer.exe (PID: 8084)
- installer.exe (PID: 4540)
- installer.exe (PID: 7808)
- servicehost.exe (PID: 6212)
- uihost.exe (PID: 8032)
- rsWSC.exe (PID: 1860)
- rsEngineSvc.exe (PID: 7532)
- rsEngineSvc.exe (PID: 8996)
- rsEDRSvc.exe (PID: 8560)
- rsEDRSvc.exe (PID: 8100)
- rsVPNSvc.exe (PID: 9864)
- rsVPNSvc.exe (PID: 8268)
- rsDNSResolver.exe (PID: 9844)
- rsDNSResolver.exe (PID: 9212)
- rsDNSSvc.exe (PID: 9428)
- rsDNSSvc.exe (PID: 4424)
Application launched itself
- chrome.exe (PID: 6392)
- msedge.exe (PID: 8076)
- msedge.exe (PID: 420)
Process checks computer location settings
- rsStubActivator.exe (PID: 7884)
- PowerISO8-x64.exe (PID: 4292)
- servicehost.exe (PID: 6212)
- rsAppUI.exe (PID: 9464)
- rsAppUI.exe (PID: 3360)
- rsAppUI.exe (PID: 9700)
- rsVPNSvc.exe (PID: 8268)
- rsAppUI.exe (PID: 6176)
- rsAppUI.exe (PID: 9900)
- rsAppUI.exe (PID: 4664)
- rsAppUI.exe (PID: 10164)
- rsAppUI.exe (PID: 10432)
Manual execution by a user
- msedge.exe (PID: 8076)
.NET Reactor protector has been detected
- UnifiedStub-installer.exe (PID: 8084)
- rsWSC.exe (PID: 208)
- rsEngineSvc.exe (PID: 7532)
- rsHelper.exe (PID: 8784)
- rsEDRSvc.exe (PID: 8100)
- rsVPNSvc.exe (PID: 8268)
Reads product name
- servicehost.exe (PID: 6212)
- rsEDRSvc.exe (PID: 8100)
- rsEngineSvc.exe (PID: 7532)
- rsAppUI.exe (PID: 3360)
- rsAppUI.exe (PID: 9900)
- rsAppUI.exe (PID: 10164)
Creates files or folders in the user directory
- UnifiedStub-installer.exe (PID: 8084)
- rsWSC.exe (PID: 1860)
- rsEngineSvc.exe (PID: 7532)
- rsAppUI.exe (PID: 3360)
- rsAppUI.exe (PID: 9436)
- rsVPNSvc.exe (PID: 8268)
- rsAppUI.exe (PID: 9900)
- rsAppUI.exe (PID: 10224)
- rsAppUI.exe (PID: 10164)
- rsDNSSvc.exe (PID: 4424)
- rsAppUI.exe (PID: 10012)
- rsAppUI.exe (PID: 10416)
Reads the time zone
- runonce.exe (PID: 8588)
- rsEngineSvc.exe (PID: 7532)
- rsEDRSvc.exe (PID: 8100)
- rsVPNSvc.exe (PID: 8268)
- runonce.exe (PID: 9776)
- rsDNSSvc.exe (PID: 4424)
Reads security settings of Internet Explorer
- runonce.exe (PID: 8588)
- runonce.exe (PID: 9776)
Reads CPU info
- rsEngineSvc.exe (PID: 7532)
- rsEDRSvc.exe (PID: 8100)
- rsVPNSvc.exe (PID: 8268)
- rsDNSSvc.exe (PID: 4424)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
310
Monitored processes
159
Malicious processes
19
Suspicious processes
13
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 188 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilReadIcon --lang=en-US --service-sandbox-type=icon_reader --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=5276 --field-trial-handle=1924,i,1393912668836374800,16656991985116250627,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 208 | "C:\Program Files\ReasonLabs\EPP\rsWSC.exe" | C:\Program Files\ReasonLabs\EPP\rsWSC.exe | services.exe | ||||||||||||
User: SYSTEM Company: Reason Software Company Inc. Integrity Level: SYSTEM Description: rsWSC Version: 6.0.3.0 Modules
| |||||||||||||||
| 232 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=5424 --field-trial-handle=2444,i,16781215879842267963,2587808254250671105,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 240 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | wevtutil.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 304 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=5136 --field-trial-handle=1924,i,1393912668836374800,16656991985116250627,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 420 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --single-argument http://www.poweriso.com/thankyou.htm | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | PowerISO8-x64.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Edge Exit code: 1 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1140 | ipconfig /flushdns | C:\Windows\System32\ipconfig.exe | — | cmd.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: IP Configuration Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1644 | C:\WINDOWS\system32\wbem\WmiApSrv.exe | C:\Windows\System32\wbem\WmiApSrv.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: WMI Performance Reverse Adapter Exit code: 0 Version: 10.0.19041.3758 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1644 | "c:\program files\reasonlabs\DNS\ui\DNS.exe" --minimized --focused --first-run | C:\Program Files\ReasonLabs\DNS\ui\DNS.exe | — | rsDNSSvc.exe | |||||||||||
User: admin Company: Reason Cybersecurity Ltd. Integrity Level: MEDIUM Description: SaferWeb Client Exit code: 0 Version: 3.15.0 Modules
| |||||||||||||||
| 1860 | "C:\Program Files\ReasonLabs\EPP\rsWSC.exe" -i | C:\Program Files\ReasonLabs\EPP\rsWSC.exe | UnifiedStub-installer.exe | ||||||||||||
User: admin Company: Reason Software Company Inc. Integrity Level: HIGH Description: rsWSC Exit code: 0 Version: 6.0.3.0 Modules
| |||||||||||||||
Total events
150 137
Read events
149 078
Write events
836
Delete events
223
Modification events
| (PID) Process: | (6392) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (6392) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (6392) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (6392) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (6392) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (6392) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (6392) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (6392) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (6392) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (6392) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
Executable files
923
Suspicious files
962
Text files
1 118
Unknown types
84
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6392 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6392 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6392 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6392 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RFe5705.TMP | — | |
MD5:— | SHA256:— | |||
| 6392 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6392 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6392 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RFe5714.TMP | — | |
MD5:— | SHA256:— | |||
| 6392 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6392 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RFe5705.TMP | text | |
MD5:139F545948FC1F10256A27E3C2CEF062 | SHA256:9399CC6F9C335015E086DB37208B1816A7831221A005B04AC83C4F86CC04230D | |||
| 6392 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | text | |
MD5:4B26172585D38A3DD6697E274D0608AC | SHA256:85899A7AF1BD1939EA8264009EC427930FC5C092C8C3193984D6391526319268 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
98
TCP/UDP connections
224
DNS requests
173
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5336 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
6228 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/V3P1l2hLvLw_7/7_all_sslErrorAssistant.crx3 | unknown | — | — | whitelisted |
7120 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
3160 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5152 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
6228 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/V3P1l2hLvLw_7/7_all_sslErrorAssistant.crx3 | unknown | — | — | whitelisted |
6228 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/V3P1l2hLvLw_7/7_all_sslErrorAssistant.crx3 | unknown | — | — | whitelisted |
6228 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/V3P1l2hLvLw_7/7_all_sslErrorAssistant.crx3 | unknown | — | — | whitelisted |
8084 | UnifiedStub-installer.exe | GET | 200 | 204.79.197.203:80 | http://oneocsp.microsoft.com/ocsp/MFQwUjBQME4wTDAJBgUrDgMCGgUABBTDHsfuqfubd3pihvq4mgQVWgHWNwQUyH7SaoUqG8oZmAQHJ89QEE9oqKICEzMAAAAHh6M0o3uljhwAAAAAAAc%3D | unknown | — | — | whitelisted |
8084 | UnifiedStub-installer.exe | GET | 200 | 204.79.197.203:80 | http://oneocsp.microsoft.com/ocsp/MFQwUjBQME4wTDAJBgUrDgMCGgUABBTh4QXD3xfHaxna9yfH20h%2Ft5LfbQQUZZ9RzoVofy%2BKRYiq3acxux4NAF4CEzMAAJV0yDQshyPtjUMAAAAAlXQ%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3888 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4788 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4560 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2120 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6392 | chrome.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
6680 | chrome.exe | 166.62.97.162:443 | www.poweriso.net | AS-26496-GO-DADDY-COM-LLC | US | unknown |
6680 | chrome.exe | 74.125.128.84:443 | accounts.google.com | GOOGLE | US | whitelisted |
6392 | chrome.exe | 224.0.0.251:5353 | — | — | — | unknown |
4788 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.poweriso.net |
| unknown |
accounts.google.com |
| whitelisted |
www.google.com |
| whitelisted |
sb-ssl.google.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
login.live.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7692 | msedge.exe | Potentially Bad Traffic | ET DNS Query for .cc TLD |
7692 | msedge.exe | Potentially Bad Traffic | ET DNS Query for .cc TLD |
Process | Message |
|---|---|
saBSI.exe | NotComDllGetInterface: C:\Users\admin\AppData\Local\Temp\PowerISO_Pub_files\saBSI.exe loading C:\Users\admin\AppData\Local\Temp\PowerISO_Pub_files\mfeaaca.dll, WinVerifyTrust failed with 80092003
|
saBSI.exe | NCPrivateLoadAndValidateMPTDll: Looking in current directory
|
saBSI.exe | NCPrivateLoadAndValidateMPTDll: Looking in EXE directory
|
saBSI.exe | NotComDllGetInterface: C:\Users\admin\AppData\Local\Temp\PowerISO_Pub_files\saBSI.exe loading C:\Users\admin\AppData\Local\Temp\PowerISO_Pub_files\mfeaaca.dll, WinVerifyTrust failed with 80092003
|
saBSI.exe | NCPrivateLoadAndValidateMPTDll: Looking in current directory
|
saBSI.exe | NCPrivateLoadAndValidateMPTDll: Looking in EXE directory
|
saBSI.exe | NotComDllGetInterface: C:\Users\admin\AppData\Local\Temp\PowerISO_Pub_files\saBSI.exe loading C:\Users\admin\AppData\Local\Temp\PowerISO_Pub_files\mfeaaca.dll, WinVerifyTrust failed with 80092003
|
saBSI.exe | NCPrivateLoadAndValidateMPTDll: Looking in current directory
|
saBSI.exe | NCPrivateLoadAndValidateMPTDll: Looking in EXE directory
|
saBSI.exe | NotComDllGetInterface: C:\Users\admin\AppData\Local\Temp\PowerISO_Pub_files\saBSI.exe loading C:\Users\admin\AppData\Local\Temp\PowerISO_Pub_files\mfeaaca.dll, WinVerifyTrust failed with 80092003
|