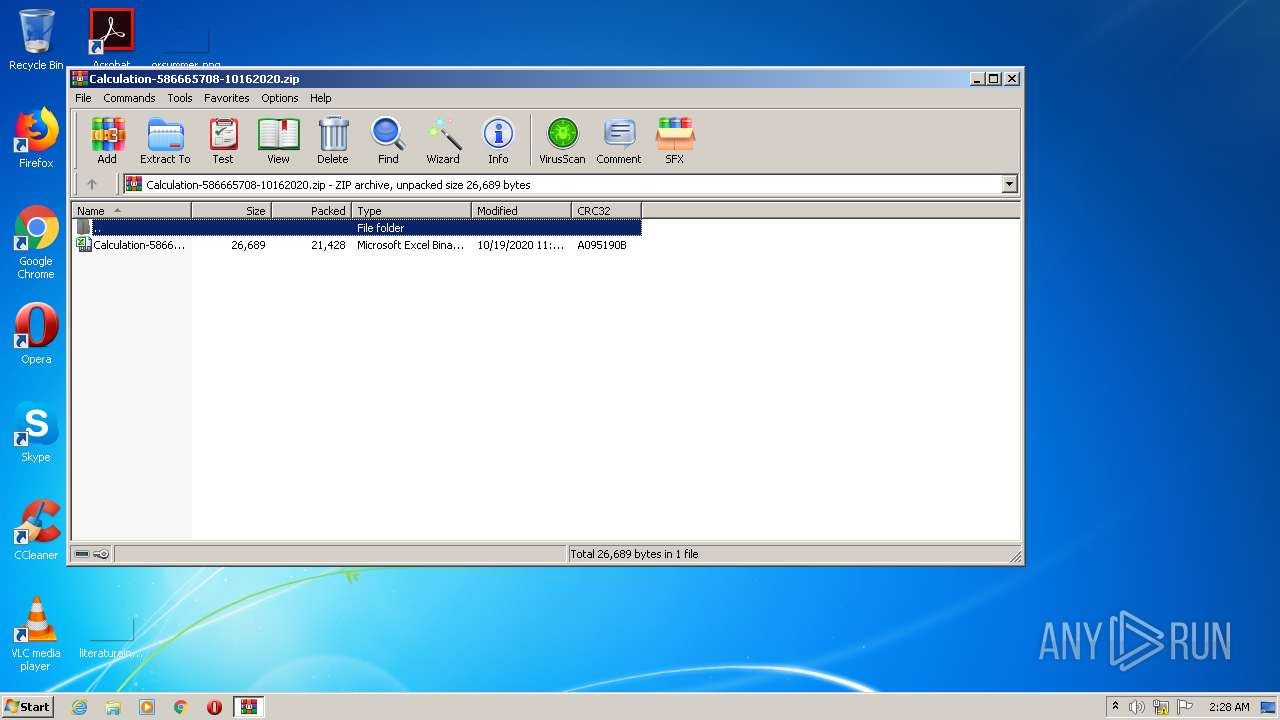
| File name: | Calculation-586665708-10162020.zip |
| Full analysis: | https://app.any.run/tasks/7c484d26-36ef-451d-bbe6-33d7c3ef031b |
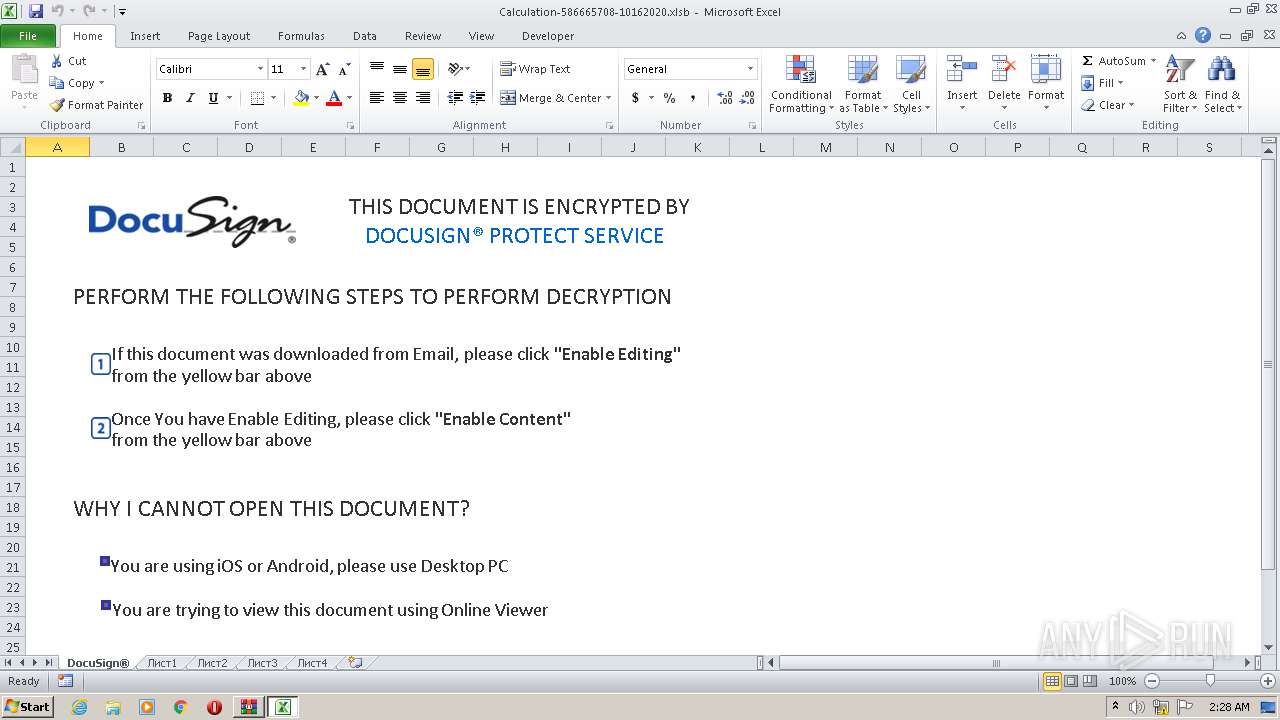
| Verdict: | Malicious activity |
| Threats: | Qbot is a banking Trojan — a malware designed to collect banking information from victims. Qbot targets organizations mostly in the US. It is equipped with various sophisticated evasion and info-stealing functions and worm-like functionality, and a strong persistence mechanism. |
| Analysis date: | October 20, 2020, 01:27:56 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | C0AB96C98553A66C60506A8384DD8E35 |
| SHA1: | C830E65B2697BFF062BBC4A3273B0CFA664F4547 |
| SHA256: | 72773C67B585B4D57F039F63CA934B9C8F984C7BF702508A47DDC82D1F85815C |
| SSDEEP: | 384:ugGvXzg6Zr4VCNmoWOjLhHmd1sKFfcL73TL6idzRSyJdwk/hwmVp3JIEorlJoAdS:kg6Zr4VFNkh3KFfg6K5Jdw+hzXOLlJoT |
MALICIOUS
Executable content was dropped or overwritten
- EXCEL.EXE (PID: 2464)
Application was dropped or rewritten from another process
- nosto.exe (PID: 3804)
- nosto.exe (PID: 2168)
- ytfovlym.exe (PID: 2676)
- ytfovlym.exe (PID: 2356)
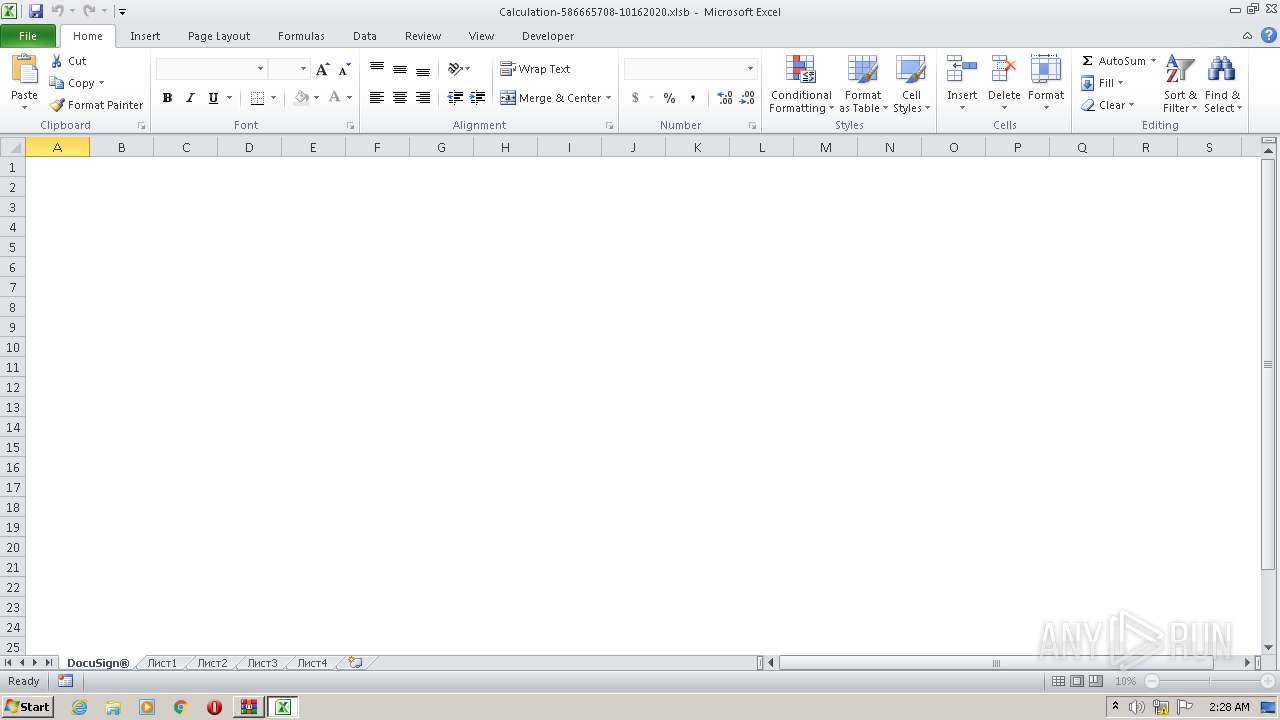
Unusual execution from Microsoft Office
- EXCEL.EXE (PID: 2464)
QBOT was detected
- nosto.exe (PID: 3804)
Runs PING.EXE for delay simulation
- cmd.exe (PID: 3836)
SUSPICIOUS
Starts Microsoft Office Application
- WinRAR.exe (PID: 2452)
Application launched itself
- nosto.exe (PID: 3804)
- ytfovlym.exe (PID: 2676)
Creates files in the user directory
- nosto.exe (PID: 3804)
Executable content was dropped or overwritten
- nosto.exe (PID: 3804)
- cmd.exe (PID: 3836)
Starts itself from another location
- nosto.exe (PID: 3804)
Starts CMD.EXE for commands execution
- nosto.exe (PID: 3804)
INFO
Reads Microsoft Office registry keys
- EXCEL.EXE (PID: 2464)
Reads Internet Cache Settings
- EXCEL.EXE (PID: 2464)
Dropped object may contain Bitcoin addresses
- cmd.exe (PID: 3836)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2020:10:19 16:24:18 |
| ZipCRC: | 0xa095190b |
| ZipCompressedSize: | 21428 |
| ZipUncompressedSize: | 26689 |
| ZipFileName: | Calculation-586665708-10162020.xlsb |
Total processes
47
Monitored processes
9
Malicious processes
3
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 544 | ping.exe -n 6 127.0.0.1 | C:\Windows\system32\PING.EXE | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: TCP/IP Ping Command Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2168 | C:\Hromo\Nivadalo\nosto.exe /C | C:\Hromo\Nivadalo\nosto.exe | — | nosto.exe | |||||||||||
User: admin Company: QIHU 360 SOFTWARE CO. LIMITED Integrity Level: MEDIUM Description: 360 SystemRegistryClean Exit code: 0 Version: 1, 0, 0, 1003 Modules
| |||||||||||||||
| 2356 | C:\Users\admin\AppData\Roaming\Microsoft\Zulycjadyc\ytfovlym.exe /C | C:\Users\admin\AppData\Roaming\Microsoft\Zulycjadyc\ytfovlym.exe | — | ytfovlym.exe | |||||||||||
User: admin Company: QIHU 360 SOFTWARE CO. LIMITED Integrity Level: MEDIUM Description: 360 SystemRegistryClean Exit code: 0 Version: 1, 0, 0, 1003 Modules
| |||||||||||||||
| 2452 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\Calculation-586665708-10162020.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 2464 | "C:\Program Files\Microsoft Office\Office14\EXCEL.EXE" /dde | C:\Program Files\Microsoft Office\Office14\EXCEL.EXE | WinRAR.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Excel Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2676 | C:\Users\admin\AppData\Roaming\Microsoft\Zulycjadyc\ytfovlym.exe | C:\Users\admin\AppData\Roaming\Microsoft\Zulycjadyc\ytfovlym.exe | — | nosto.exe | |||||||||||
User: admin Company: QIHU 360 SOFTWARE CO. LIMITED Integrity Level: MEDIUM Description: 360 SystemRegistryClean Exit code: 0 Version: 1, 0, 0, 1003 Modules
| |||||||||||||||
| 3804 | "C:\Hromo\Nivadalo\nosto.exe" | C:\Hromo\Nivadalo\nosto.exe | EXCEL.EXE | ||||||||||||
User: admin Company: QIHU 360 SOFTWARE CO. LIMITED Integrity Level: MEDIUM Description: 360 SystemRegistryClean Exit code: 0 Version: 1, 0, 0, 1003 Modules
| |||||||||||||||
| 3832 | C:\Windows\explorer.exe | C:\Windows\explorer.exe | — | ytfovlym.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3836 | "C:\Windows\System32\cmd.exe" /c ping.exe -n 6 127.0.0.1 & type "C:\Windows\System32\calc.exe" > "C:\Hromo\Nivadalo\nosto.exe" | C:\Windows\System32\cmd.exe | nosto.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
1 153
Read events
1 087
Write events
55
Delete events
11
Modification events
| (PID) Process: | (2452) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2452) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2452) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2452) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Calculation-586665708-10162020.zip | |||
| (PID) Process: | (2452) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2452) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2452) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2452) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2452) WinRAR.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | EXCELFiles |
Value: 1364459553 | |||
| (PID) Process: | (2464) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency\StartupItems |
| Operation: | write | Name: | )06 |
Value: 29303600A0090000010000000000000000000000 | |||
Executable files
4
Suspicious files
2
Text files
0
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2464 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\CVR7479.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2452 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DIa2452.13354\Calculation-586665708-10162020.xlsb | document | |
MD5:— | SHA256:— | |||
| 2464 | EXCEL.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\6Z2BCOUL\3415201[1].png | executable | |
MD5:— | SHA256:— | |||
| 2464 | EXCEL.EXE | C:\Hromo\Nivadalo\nosto.exe | executable | |
MD5:— | SHA256:— | |||
| 3804 | nosto.exe | C:\Users\admin\AppData\Roaming\Microsoft\Zulycjadyc\ytfovlym.exe | executable | |
MD5:— | SHA256:— | |||
| 3804 | nosto.exe | C:\Users\admin\AppData\Roaming\Microsoft\Zulycjadyc\ytfovlym.dat | binary | |
MD5:— | SHA256:— | |||
| 3832 | explorer.exe | C:\Users\admin\AppData\Roaming\Microsoft\Zulycjadyc\ytfovlym.dat | pgc | |
MD5:— | SHA256:— | |||
| 3836 | cmd.exe | C:\Hromo\Nivadalo\nosto.exe | executable | |
MD5:60B7C0FEAD45F2066E5B805A91F4F0FC | SHA256:80C10EE5F21F92F89CBC293A59D2FD4C01C7958AACAD15642558DB700943FA22 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
1
DNS requests
1
Threats
6
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2464 | EXCEL.EXE | GET | 200 | 183.181.83.123:80 | http://home-delivery-cleaning.net/ecbmuibsl/3415201.png | JP | executable | 1.02 Mb | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2464 | EXCEL.EXE | 183.181.83.123:80 | home-delivery-cleaning.net | SAKURA Internet Inc. | JP | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
home-delivery-cleaning.net |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2464 | EXCEL.EXE | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
2464 | EXCEL.EXE | A Network Trojan was detected | ET CURRENT_EVENTS Likely Evil EXE download from MSXMLHTTP non-exe extension M2 |
2464 | EXCEL.EXE | A Network Trojan was detected | ET TROJAN JS/WSF Downloader Dec 08 2016 M4 |
2464 | EXCEL.EXE | A Network Trojan was detected | AV POLICY EXE or DLL in HTTP Image Content Inbound - Likely Malicious |
2464 | EXCEL.EXE | Misc activity | ET INFO EXE - Served Attached HTTP |
2464 | EXCEL.EXE | Misc activity | SUSPICIOUS [PTsecurity] PE as Image Content type mismatch |