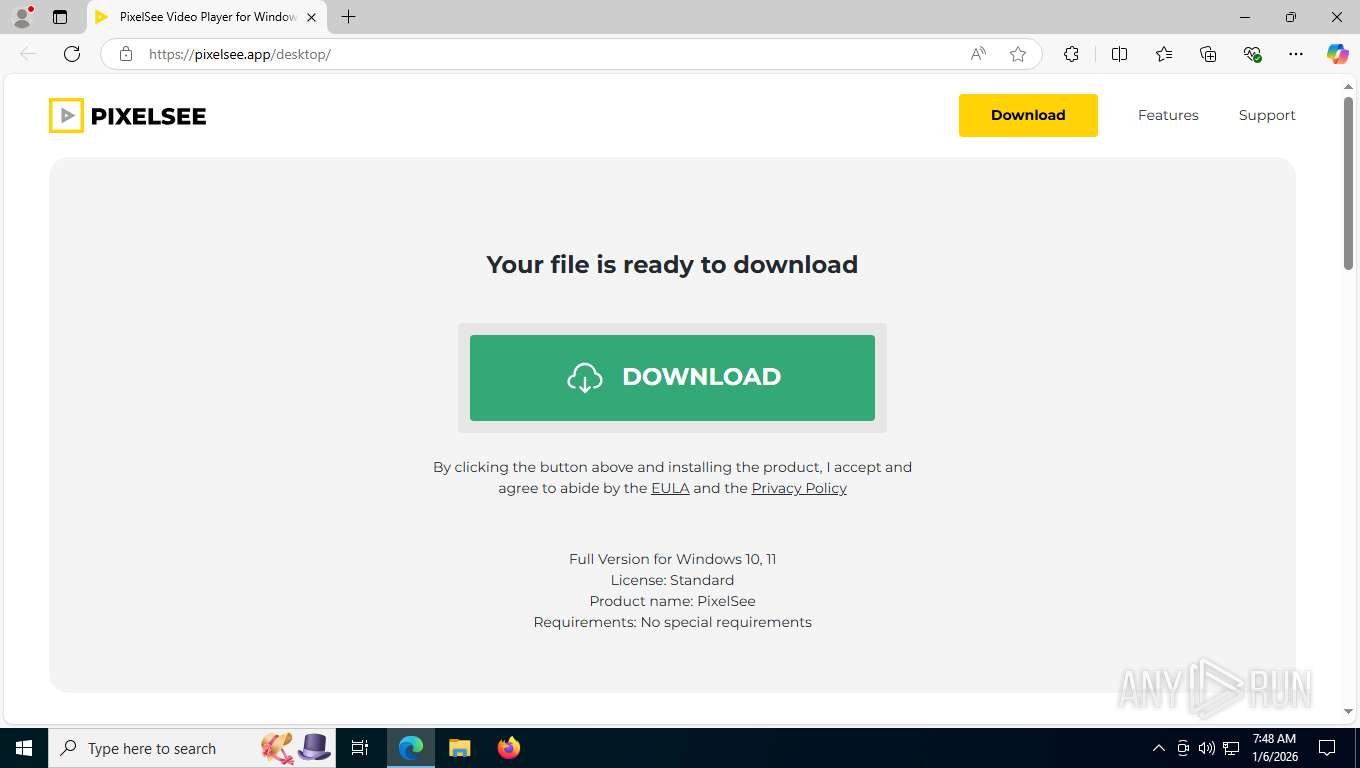
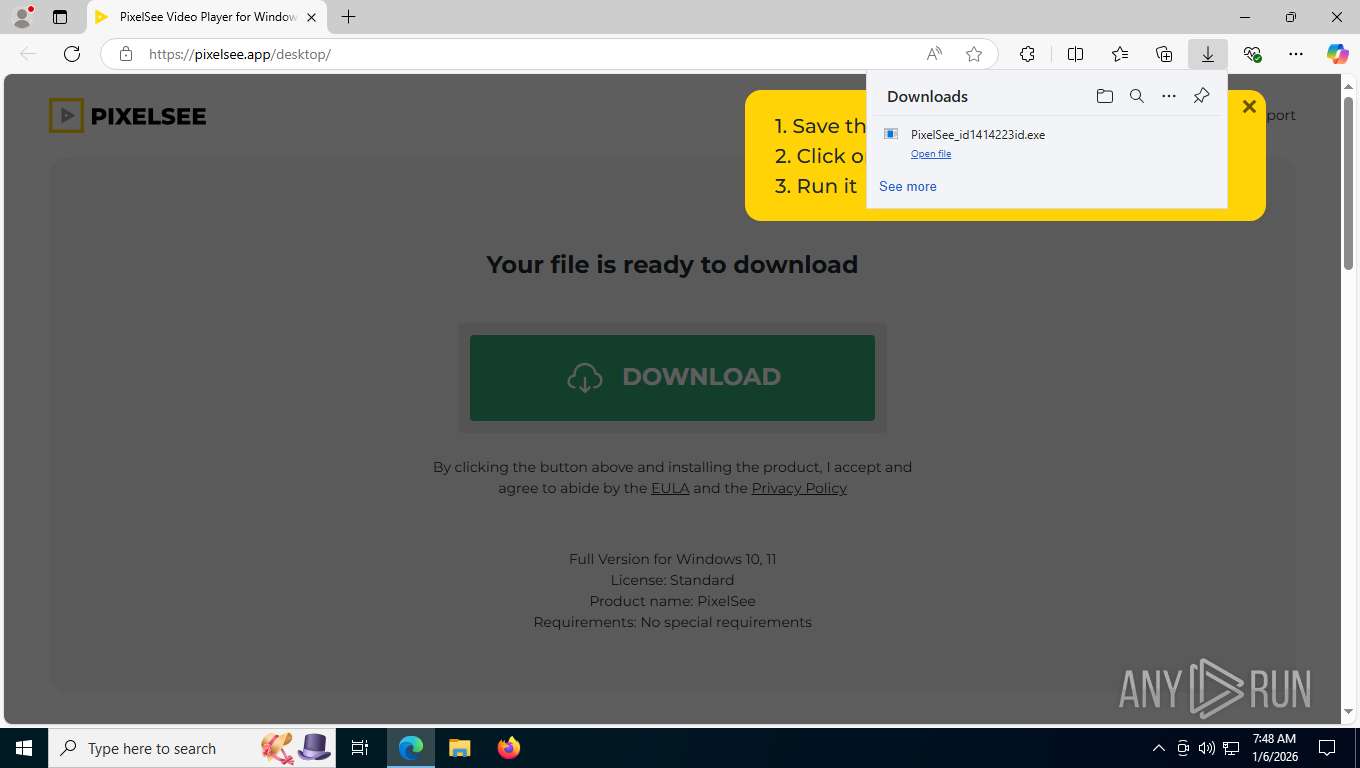
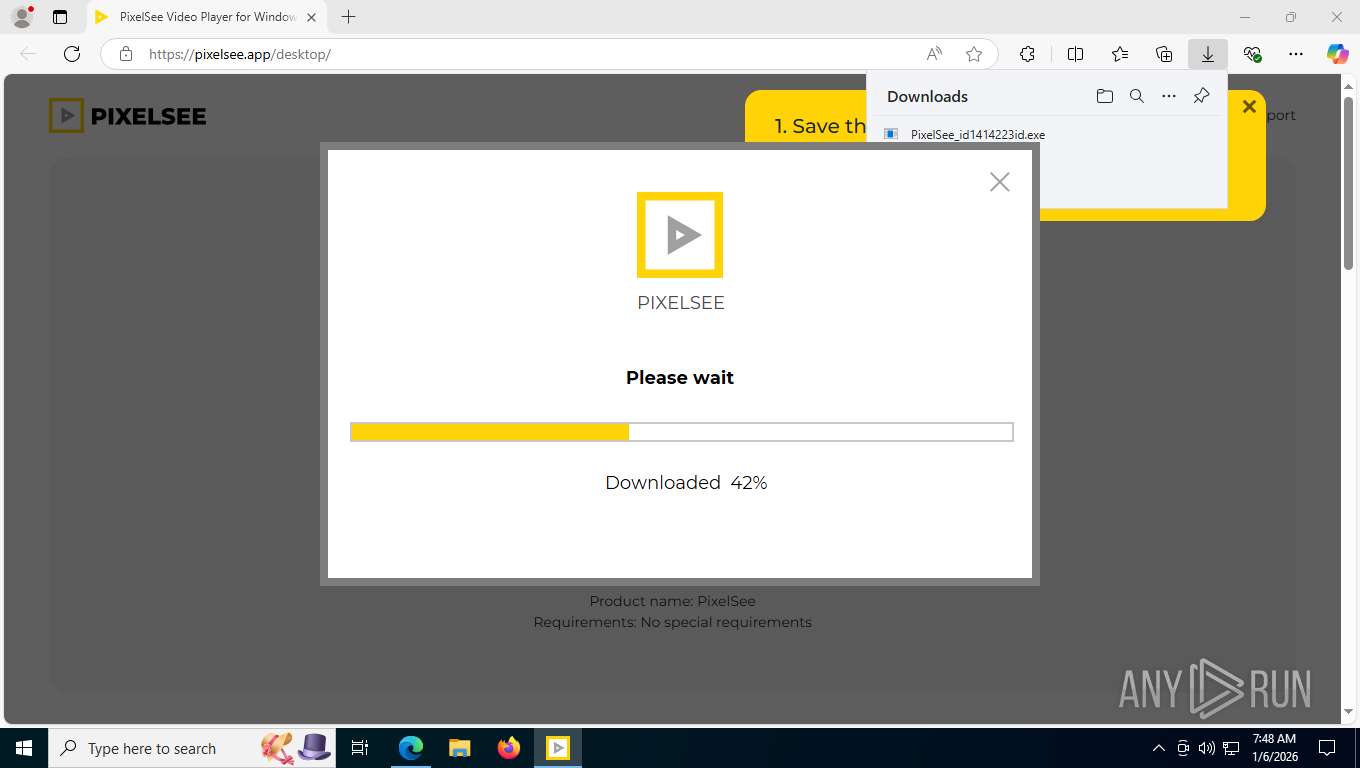
| URL: | https://pixelsee.app/desktop/ |
| Full analysis: | https://app.any.run/tasks/a8a38e37-95bf-49ac-9c49-8f0b4e41f030 |
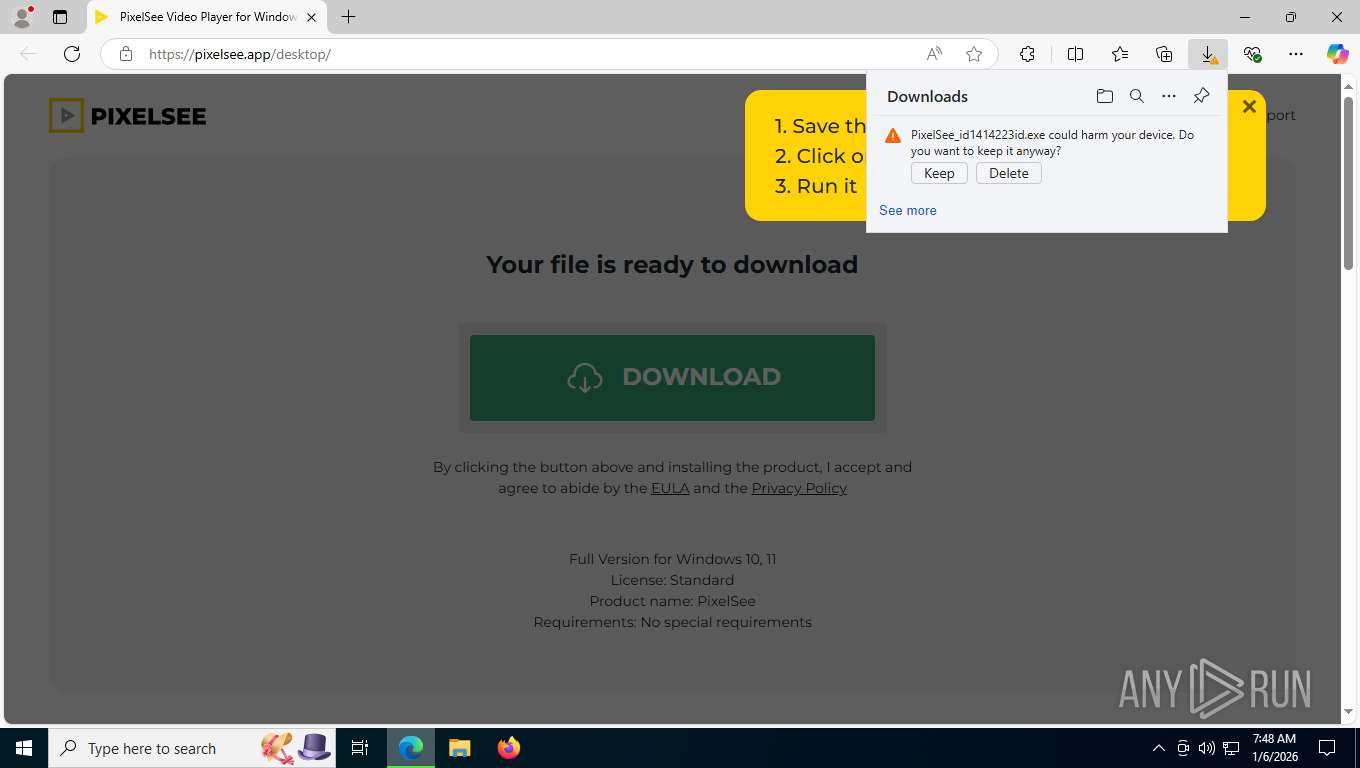
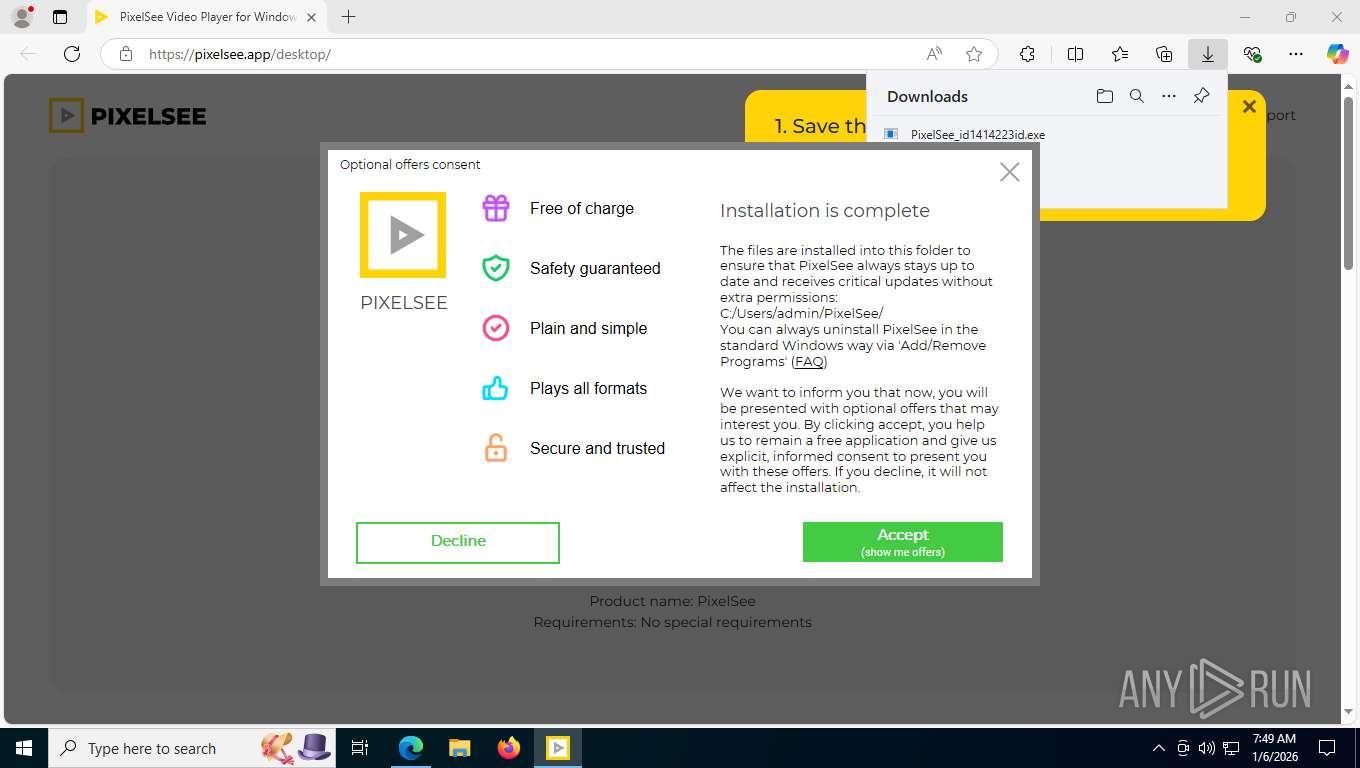
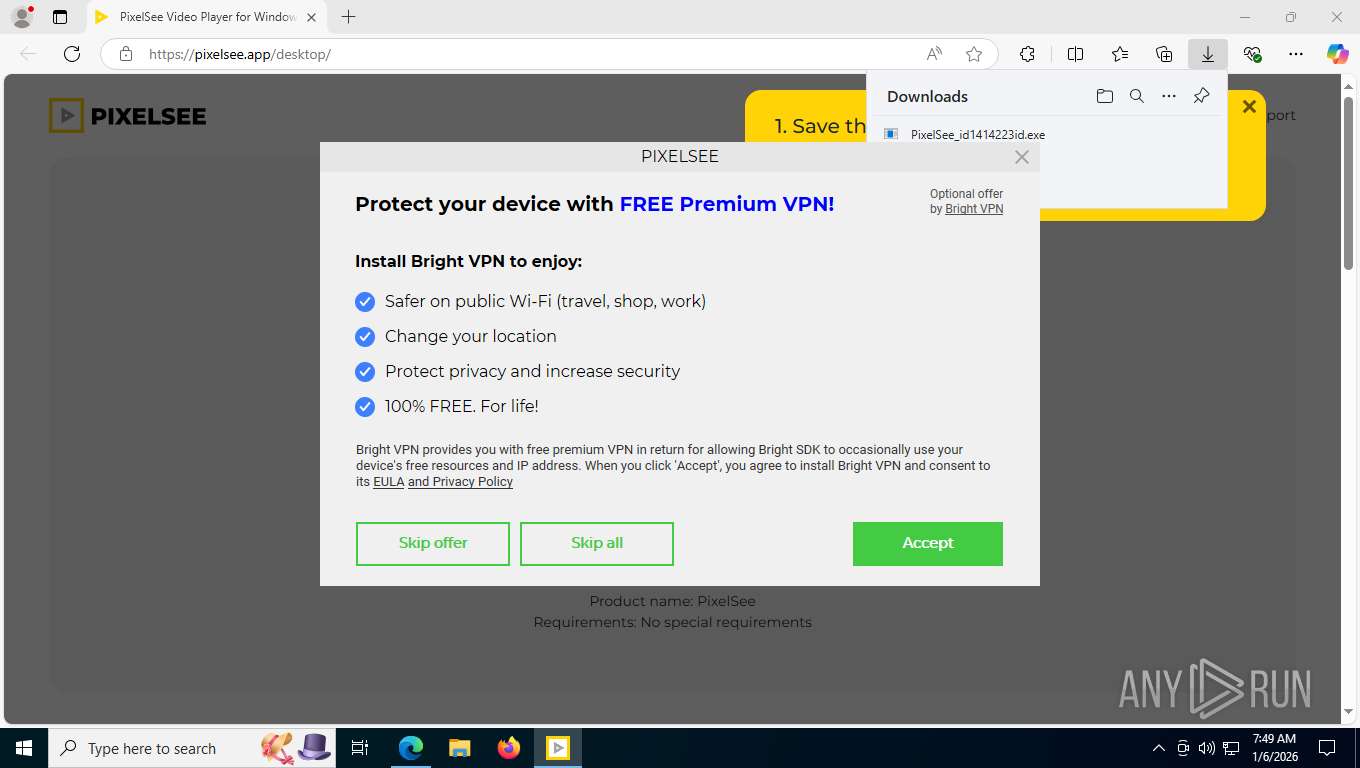
| Verdict: | Malicious activity |
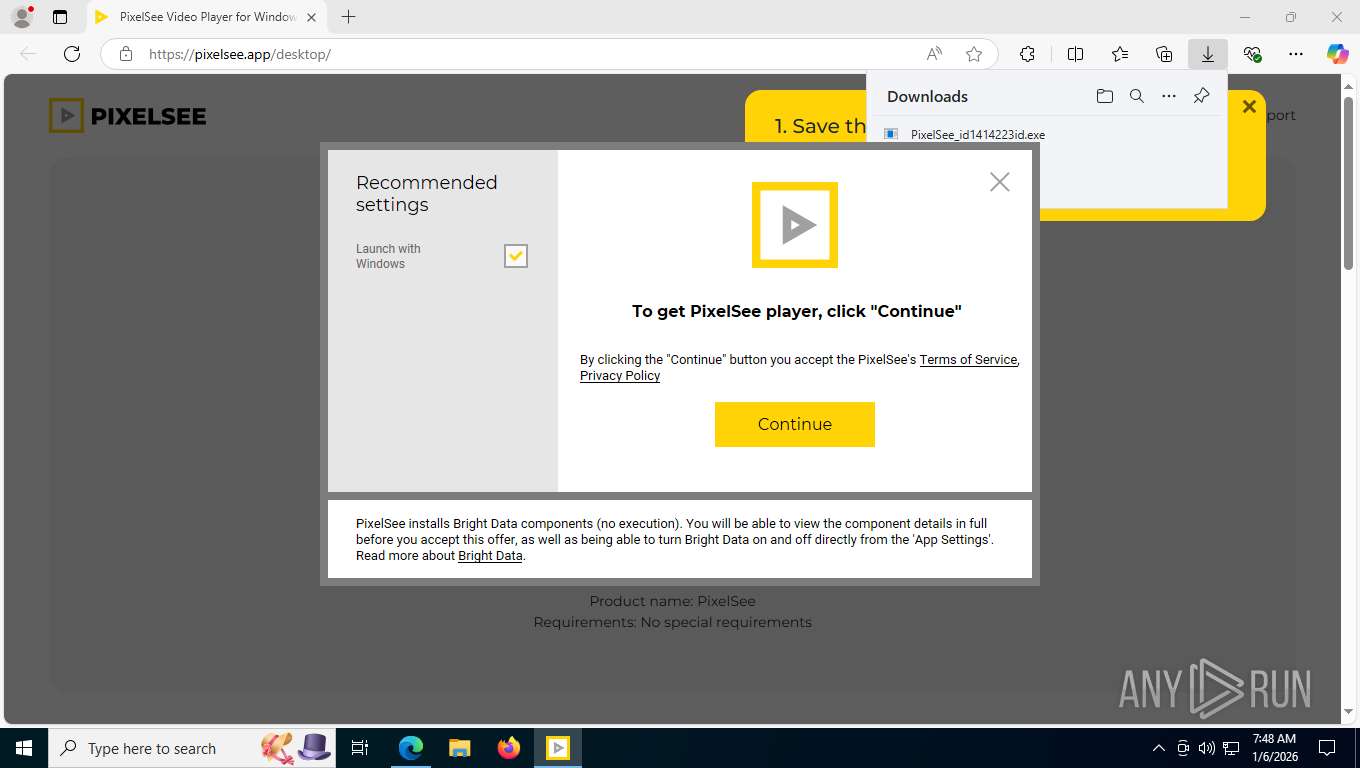
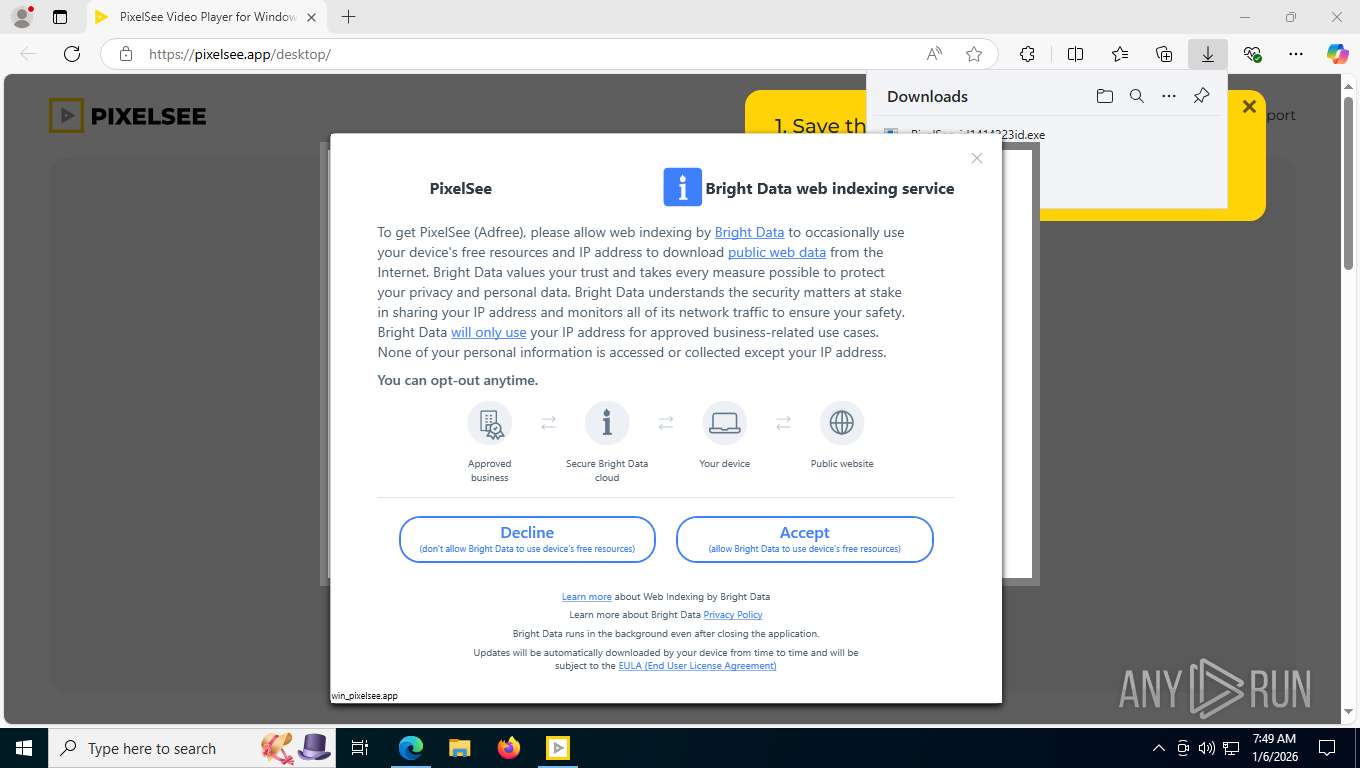
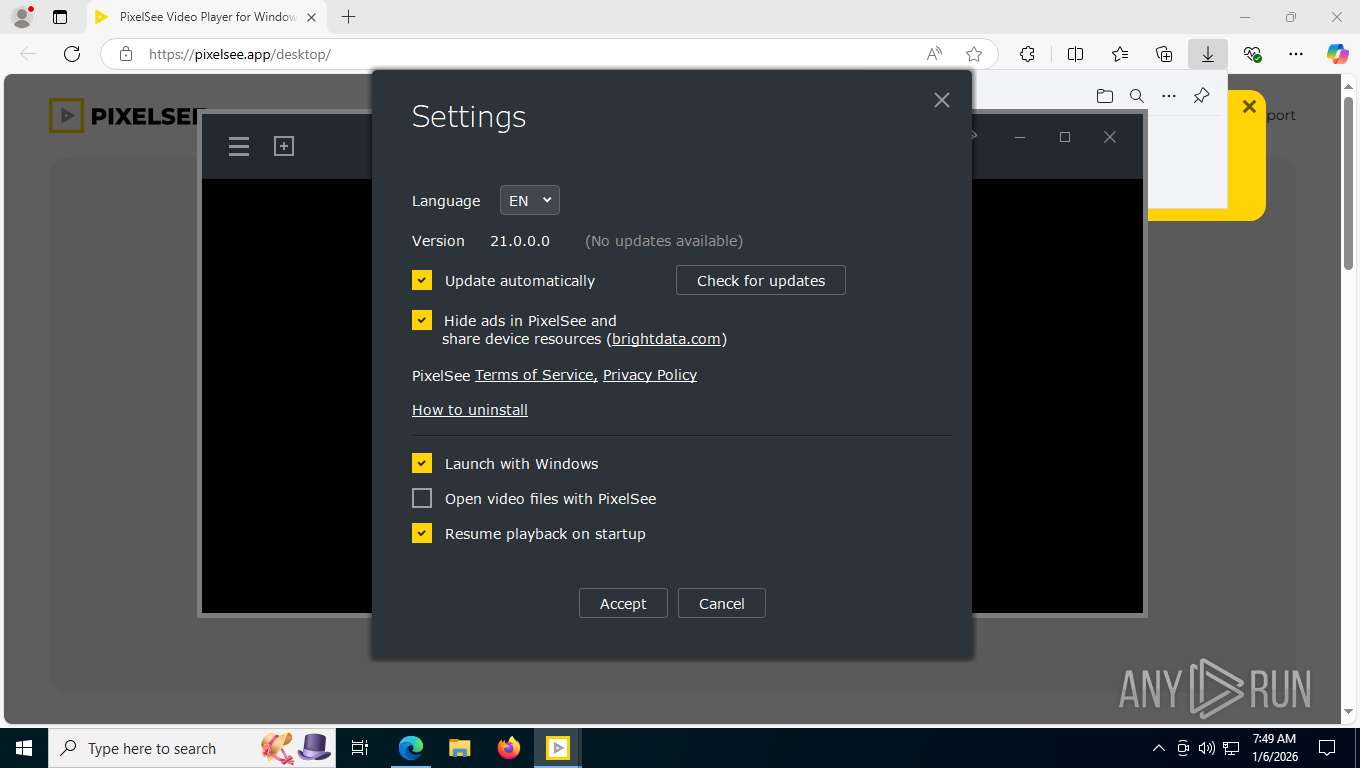
| Threats: | Adware is a form of malware that targets users with unwanted advertisements, often disrupting their browsing experience. It typically infiltrates systems through software bundling, malicious websites, or deceptive downloads. Once installed, it may track user activity, collect sensitive data, and display intrusive ads, including pop-ups or banners. Some advanced adware variants can bypass security measures and establish persistence on devices, making removal challenging. Additionally, adware can create vulnerabilities that other malware can exploit, posing a significant risk to user privacy and system security. |
| Analysis date: | January 06, 2026, 12:48:17 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | F0B52C80C5659460AE8097423907192C |
| SHA1: | 74717ED6D476E981994470D1E25560A16CB727E7 |
| SHA256: | 724B06C7D832B4D9241D12F8D9C73F499F41FD7C1C19AB3F3E50657D4239C6AA |
| SSDEEP: | 3:N8ISDKBZVKn:2IEKBrK |
MALICIOUS
Actions looks like stealing of personal data
- PixelSee_id1414223id.exe (PID: 8348)
MENTALMENTOR mutex has been found
- luminati-m-controller.exe (PID: 4104)
- luminati-m-controller.exe (PID: 2992)
Changes the autorun value in the registry
- pixelsee.exe (PID: 5168)
SUSPICIOUS
Reads Microsoft Outlook installation path
- PixelSee_id1414223id.exe (PID: 8348)
Reads Internet Explorer settings
- PixelSee_id1414223id.exe (PID: 8348)
Executable content was dropped or overwritten
- PixelSee_id1414223id.exe (PID: 8348)
- lum_inst.exe (PID: 1840)
- lum_inst.tmp (PID: 2760)
- luminati-m-controller.exe (PID: 4104)
- net_updater32.exe (PID: 5784)
- luminati-m-controller.exe (PID: 2992)
Reads security settings of Internet Explorer
- PixelSee_id1414223id.exe (PID: 8348)
- lum_inst.tmp (PID: 2760)
- luminati-m-controller.exe (PID: 4104)
- pixelsee.exe (PID: 5168)
Process drops legitimate windows executable
- PixelSee_id1414223id.exe (PID: 8348)
- luminati-m-controller.exe (PID: 4104)
Reads the Windows owner or organization settings
- lum_inst.tmp (PID: 2760)
The process drops C-runtime libraries
- PixelSee_id1414223id.exe (PID: 8348)
- luminati-m-controller.exe (PID: 4104)
Executes as Windows Service
- net_updater32.exe (PID: 5784)
- WmiApSrv.exe (PID: 8556)
Uses NETSH.EXE to add a firewall rule or allowed programs
- PixelSee_id1414223id.exe (PID: 8348)
The process checks if it is being run in the virtual environment
- net_updater32.exe (PID: 5784)
Checks for external IP
- net_updater32.exe (PID: 5784)
Creates file in the systems drive root
- pixelsee.exe (PID: 5168)
INFO
Application launched itself
- msedge.exe (PID: 7532)
Reads Environment values
- identity_helper.exe (PID: 8576)
Executable content was dropped or overwritten
- msedge.exe (PID: 7860)
- msedge.exe (PID: 7532)
Reads the computer name
- PixelSee_id1414223id.exe (PID: 8348)
- identity_helper.exe (PID: 8576)
- lum_inst.tmp (PID: 2760)
- test_wpf.exe (PID: 424)
- luminati-m-controller.exe (PID: 4104)
- net_updater32.exe (PID: 5784)
- test_wpf.exe (PID: 8292)
- net_updater32.exe (PID: 4036)
- pixelsee.exe (PID: 5168)
- brightdata.exe (PID: 9108)
- idle_report.exe (PID: 5176)
- luminati-m-controller.exe (PID: 2992)
- test_wpf.exe (PID: 2688)
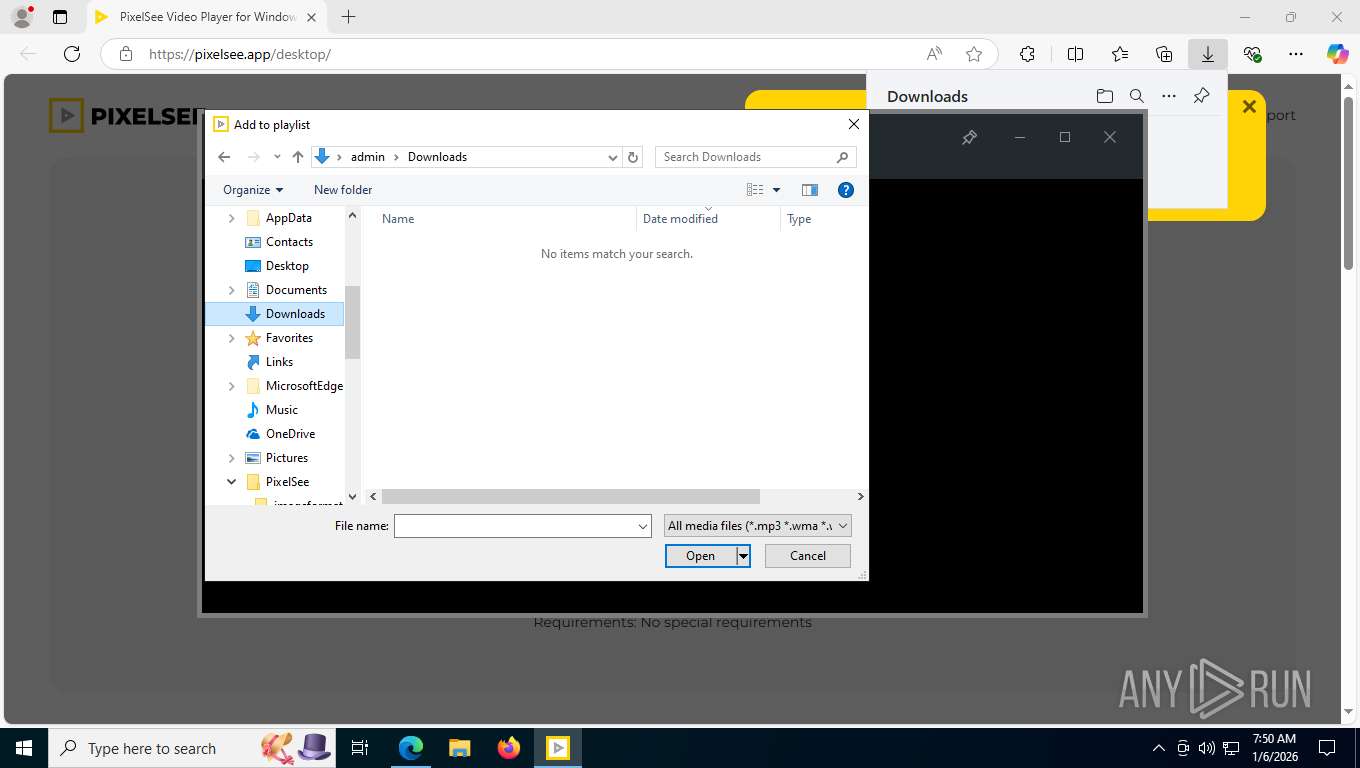
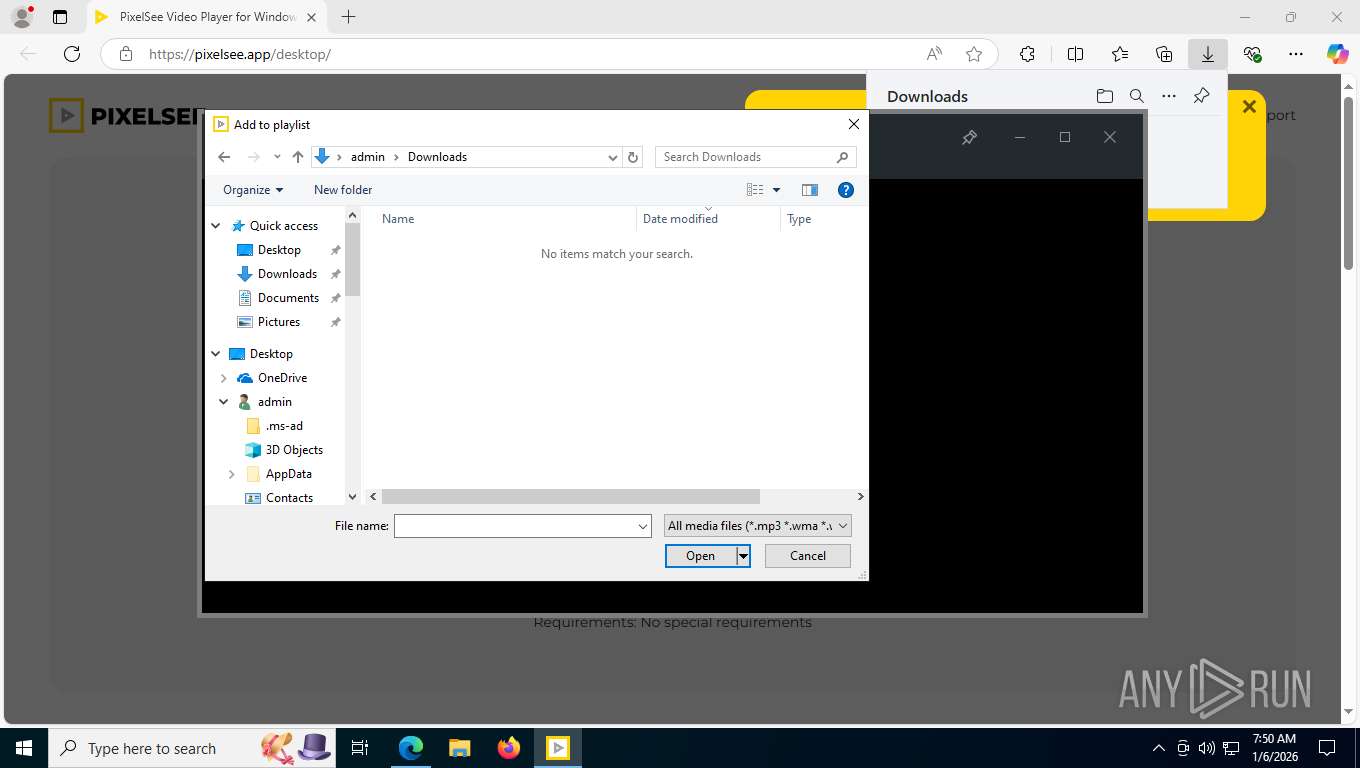
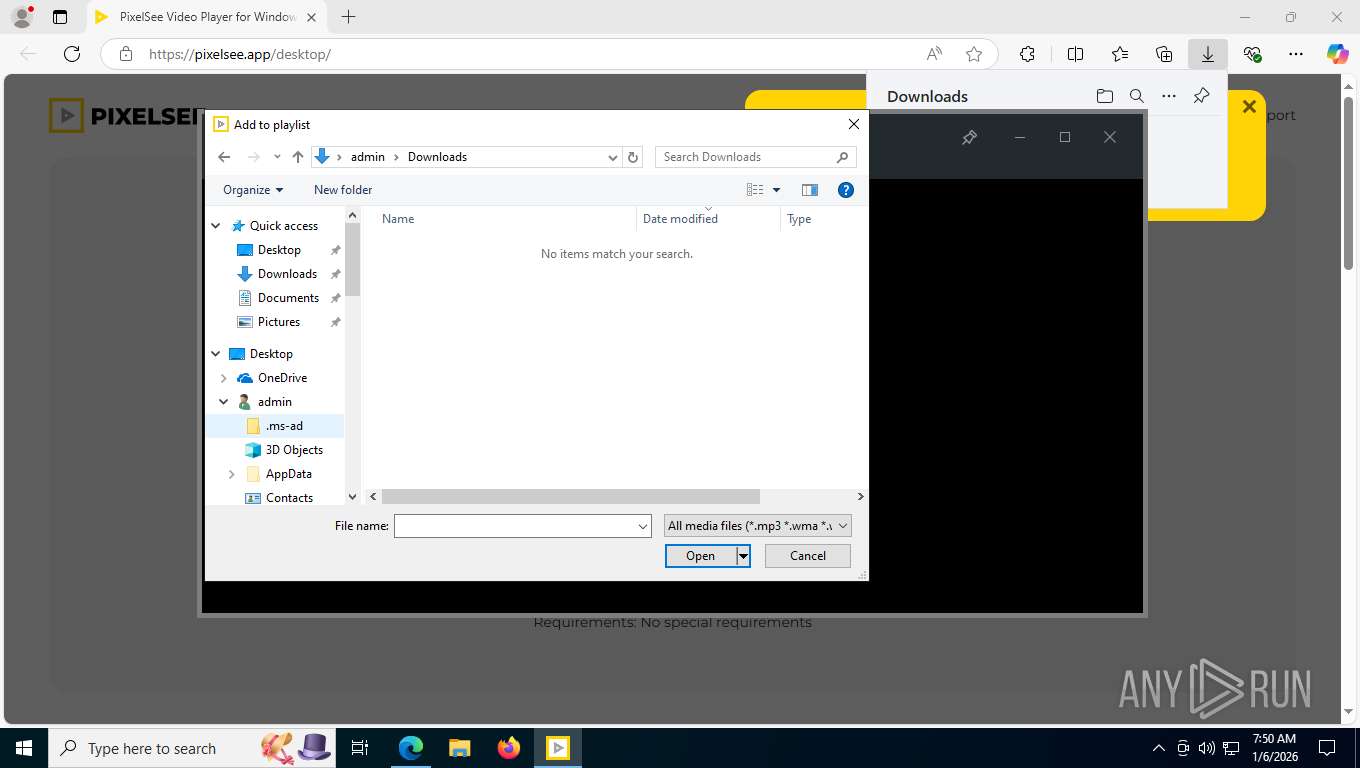
Launching a file from the Downloads directory
- msedge.exe (PID: 7532)
The sample compiled with english language support
- msedge.exe (PID: 7532)
- msedge.exe (PID: 7860)
- PixelSee_id1414223id.exe (PID: 8348)
- lum_inst.tmp (PID: 2760)
- luminati-m-controller.exe (PID: 4104)
Checks proxy server information
- PixelSee_id1414223id.exe (PID: 8348)
- luminati-m-controller.exe (PID: 4104)
- pixelsee.exe (PID: 5168)
- slui.exe (PID: 8912)
Checks supported languages
- identity_helper.exe (PID: 8576)
- PixelSee_id1414223id.exe (PID: 8348)
- lum_inst.exe (PID: 1840)
- lum_inst.tmp (PID: 2760)
- luminati-m-controller.exe (PID: 4104)
- test_wpf.exe (PID: 424)
- net_updater32.exe (PID: 5784)
- test_wpf.exe (PID: 8292)
- net_updater32.exe (PID: 4036)
- idle_report.exe (PID: 5176)
- pixelsee_crashpad_handler.exe (PID: 8276)
- luminati-m-controller.exe (PID: 2992)
- pixelsee.exe (PID: 5168)
- brightdata.exe (PID: 9108)
- test_wpf.exe (PID: 2688)
Create files in a temporary directory
- PixelSee_id1414223id.exe (PID: 8348)
- lum_inst.tmp (PID: 2760)
- lum_inst.exe (PID: 1840)
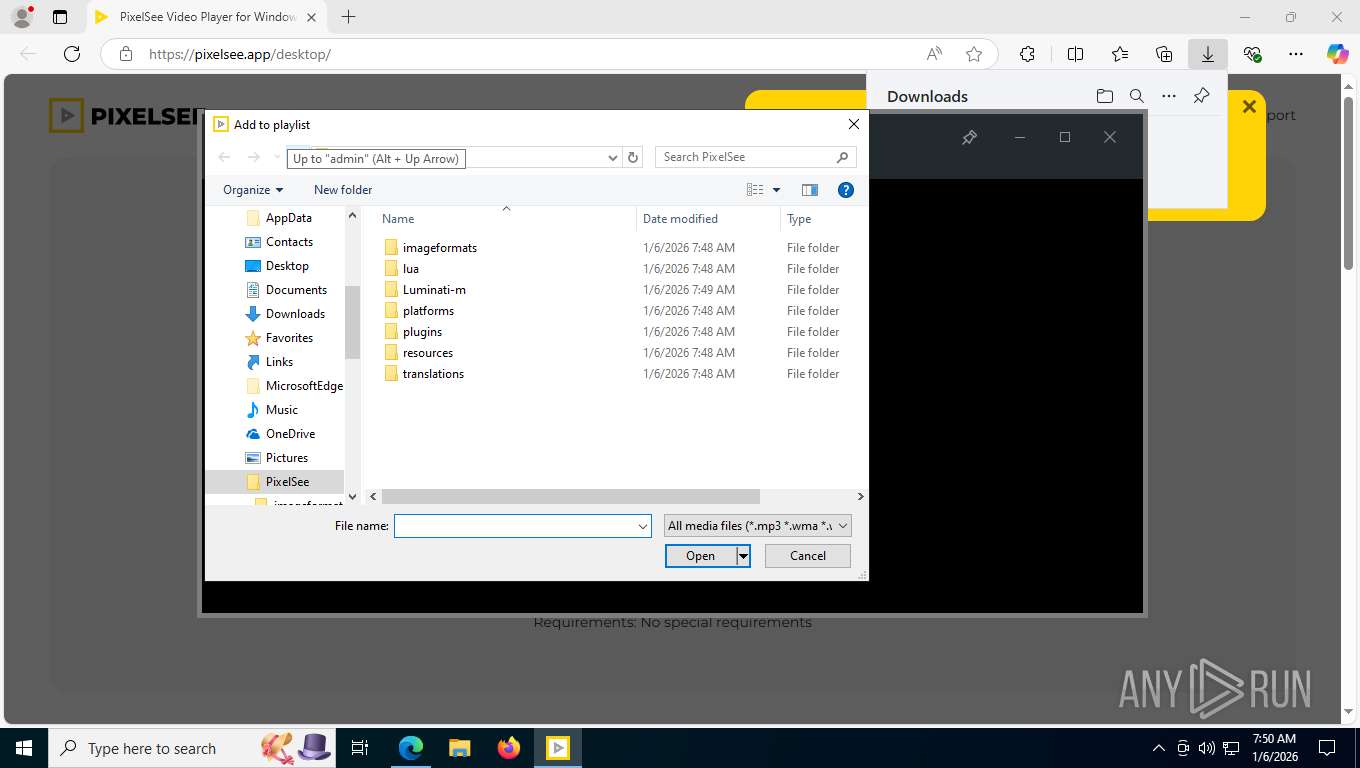
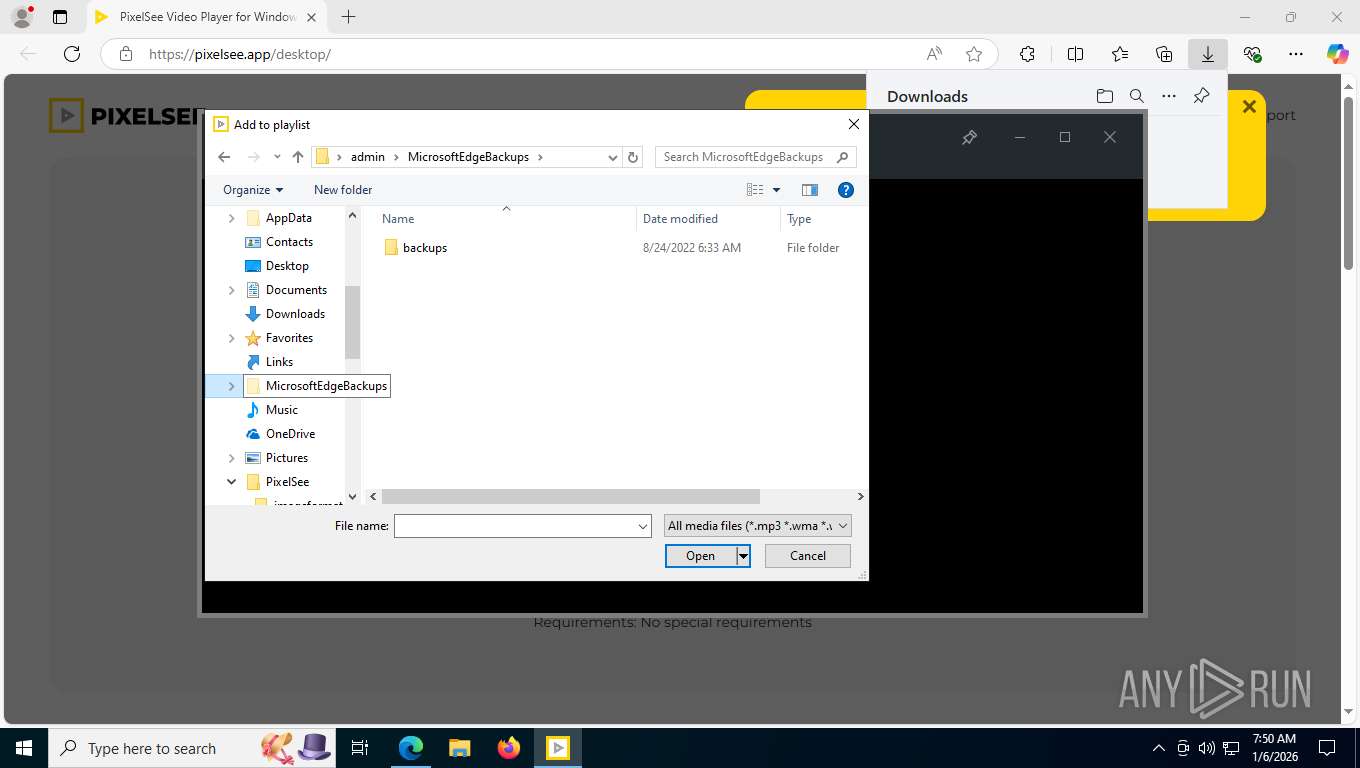
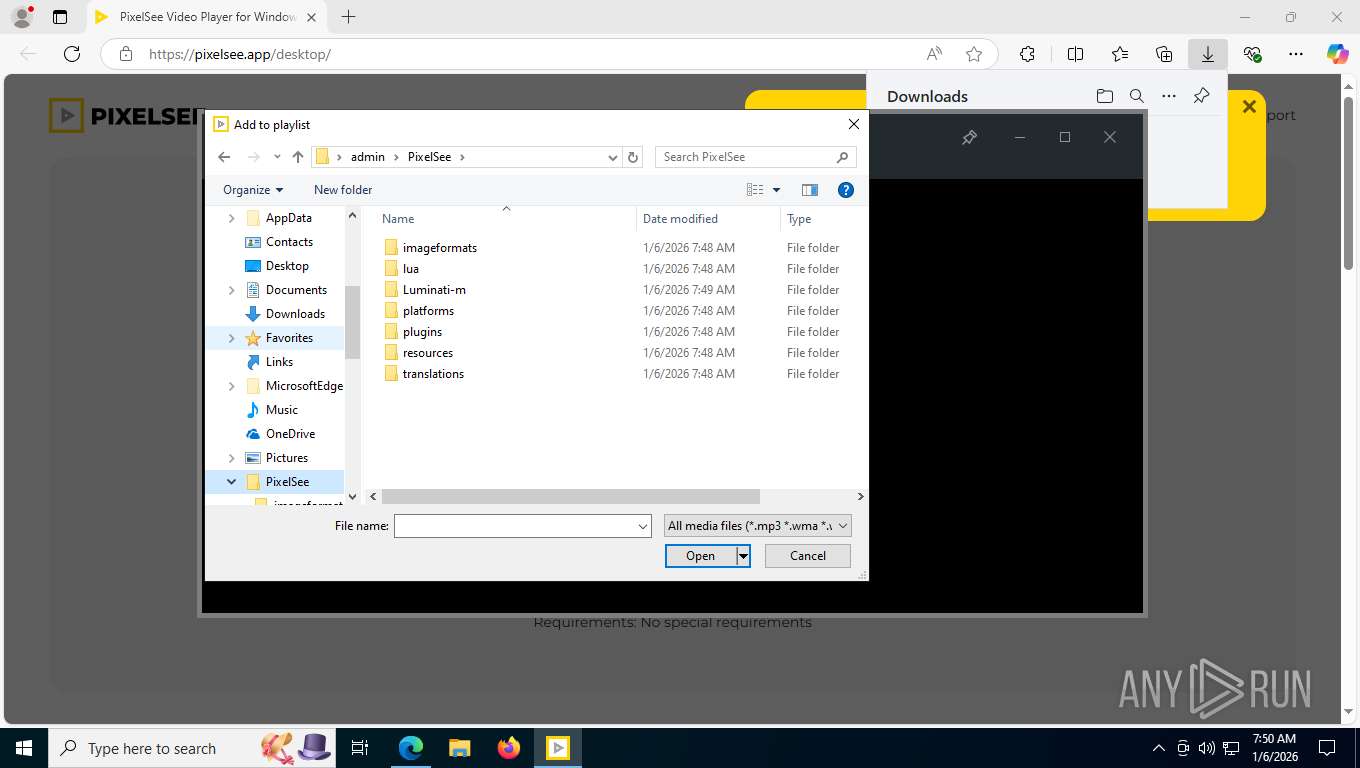
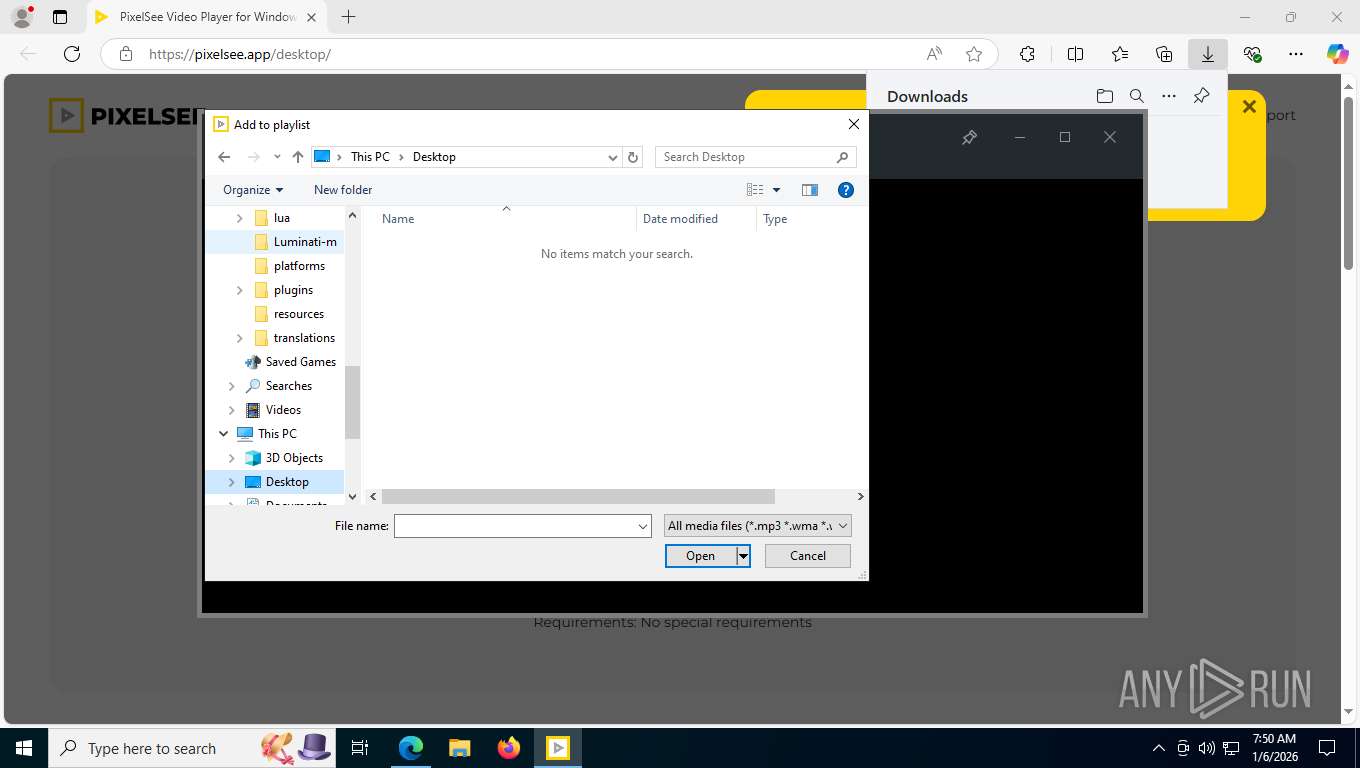
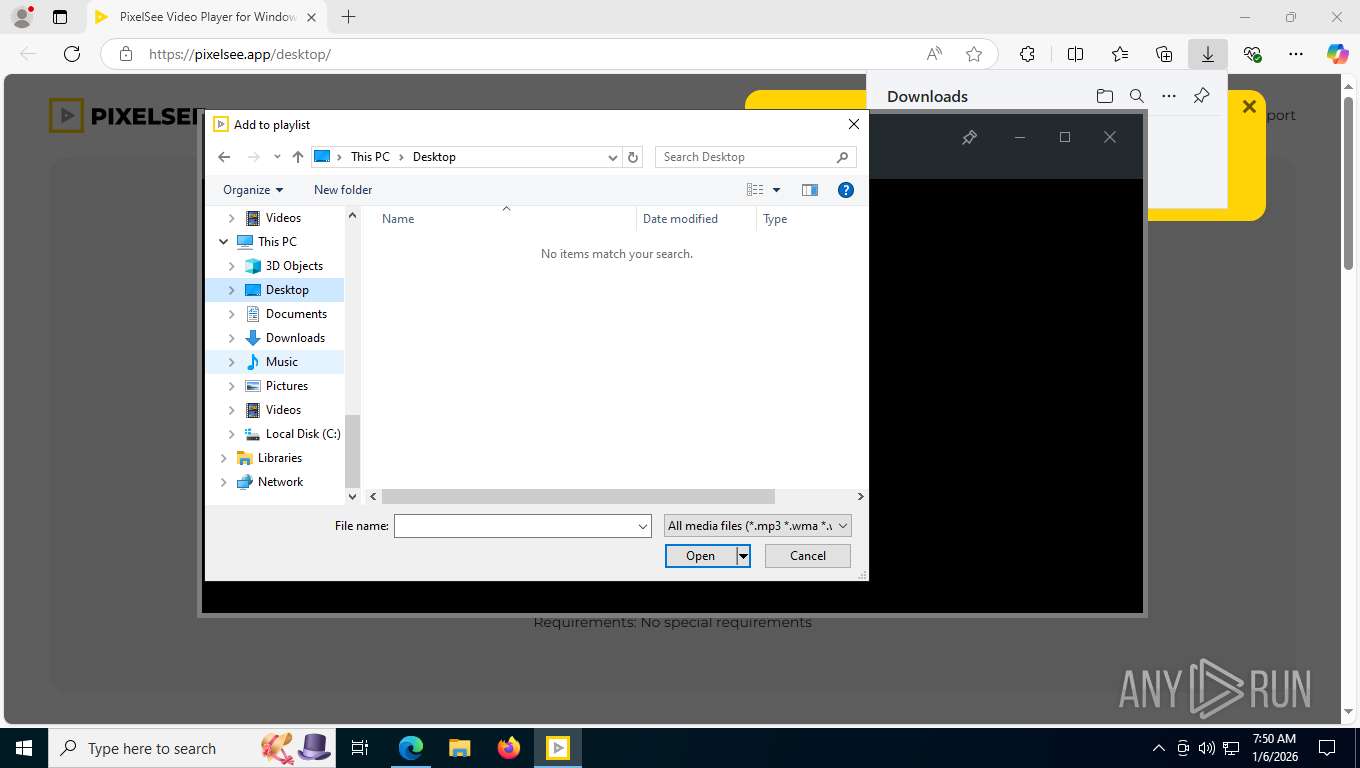
Creates files or folders in the user directory
- PixelSee_id1414223id.exe (PID: 8348)
- luminati-m-controller.exe (PID: 4104)
- pixelsee_crashpad_handler.exe (PID: 8276)
- pixelsee.exe (PID: 5168)
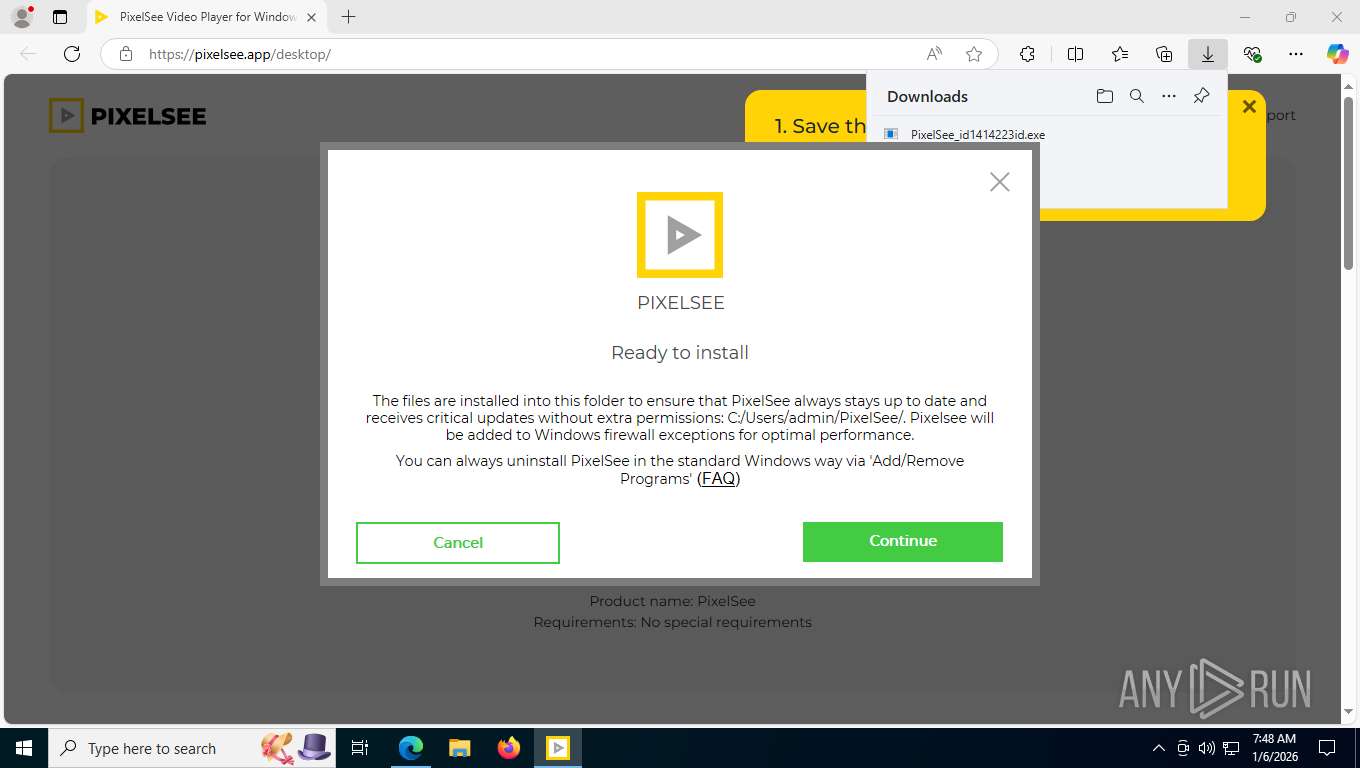
Creates a software uninstall entry
- PixelSee_id1414223id.exe (PID: 8348)
Process checks computer location settings
- PixelSee_id1414223id.exe (PID: 8348)
- lum_inst.tmp (PID: 2760)
- luminati-m-controller.exe (PID: 4104)
- net_updater32.exe (PID: 5784)
- luminati-m-controller.exe (PID: 2992)
Creates files in the program directory
- luminati-m-controller.exe (PID: 4104)
- net_updater32.exe (PID: 4036)
- net_updater32.exe (PID: 5784)
- brightdata.exe (PID: 9108)
- luminati-m-controller.exe (PID: 2992)
Compiled with Borland Delphi (YARA)
- lum_inst.exe (PID: 1840)
- lum_inst.tmp (PID: 2760)
Detects InnoSetup installer (YARA)
- lum_inst.exe (PID: 1840)
- lum_inst.tmp (PID: 2760)
Disables trace logs
- luminati-m-controller.exe (PID: 4104)
- net_updater32.exe (PID: 5784)
Reads the machine GUID from the registry
- luminati-m-controller.exe (PID: 4104)
- test_wpf.exe (PID: 424)
- net_updater32.exe (PID: 5784)
- test_wpf.exe (PID: 8292)
- idle_report.exe (PID: 5176)
- brightdata.exe (PID: 9108)
- pixelsee.exe (PID: 5168)
- test_wpf.exe (PID: 2688)
- luminati-m-controller.exe (PID: 2992)
Reads the time zone
- net_updater32.exe (PID: 5784)
Launching a file from a Registry key
- pixelsee.exe (PID: 5168)
Reads CPU info
- net_updater32.exe (PID: 5784)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
207
Monitored processes
55
Malicious processes
7
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 424 | C:\ProgramData\BrightData\b85f5ef603041f1fc4e7f943c177a0d440a01266\test_wpf.exe | C:\ProgramData\BrightData\b85f5ef603041f1fc4e7f943c177a0d440a01266\test_wpf.exe | — | luminati-m-controller.exe | |||||||||||
User: admin Company: BrightData Ltd. (certified) Integrity Level: HIGH Description: test_wpf Exit code: 0 Version: 1.549.804 Modules
| |||||||||||||||
| 1840 | "C:\Users\admin\AppData\Local\Temp\luminati\lum_inst.exe" /verysilent | C:\Users\admin\AppData\Local\Temp\luminati\lum_inst.exe | PixelSee_id1414223id.exe | ||||||||||||
User: admin Company: SIA Circle Solutions Integrity Level: HIGH Description: luminati_setup Setup Exit code: 101 Version: 1.0 Modules
| |||||||||||||||
| 2688 | C:\ProgramData\BrightData\b85f5ef603041f1fc4e7f943c177a0d440a01266\test_wpf.exe | C:\ProgramData\BrightData\b85f5ef603041f1fc4e7f943c177a0d440a01266\test_wpf.exe | — | luminati-m-controller.exe | |||||||||||
User: admin Company: BrightData Ltd. (certified) Integrity Level: HIGH Description: test_wpf Exit code: 0 Version: 1.549.804 Modules
| |||||||||||||||
| 2760 | "C:\Users\admin\AppData\Local\Temp\is-HJM9N.tmp\lum_inst.tmp" /SL5="$802EE,6761059,832512,C:\Users\admin\AppData\Local\Temp\luminati\lum_inst.exe" /verysilent | C:\Users\admin\AppData\Local\Temp\is-HJM9N.tmp\lum_inst.tmp | lum_inst.exe | ||||||||||||
User: admin Company: SIA Circle Solutions Integrity Level: HIGH Description: Setup/Uninstall Exit code: 101 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 2992 | C:\Users\admin\PixelSee\Luminati-m\luminati-m-controller.exe is_switch_on | C:\Users\admin\PixelSee\Luminati-m\luminati-m-controller.exe | pixelsee.exe | ||||||||||||
User: admin Company: SIA Circle Solutions Integrity Level: HIGH Description: PixelSee Luminati Controller Exit code: 101 Version: 1.0.0.0 Modules
| |||||||||||||||
| 3688 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | net_updater32.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4036 | "C:\Users\admin\PixelSee\Luminati-m\net_updater32.exe" --install win_pixelsee.app --no-cleanup | C:\Users\admin\PixelSee\Luminati-m\net_updater32.exe | luminati-m-controller.exe | ||||||||||||
User: admin Company: BrightData Ltd. (certified) Integrity Level: HIGH Description: BrightData service allows free use of certain features in an app you installed Exit code: 0 Version: 1.549.804 Modules
| |||||||||||||||
| 4104 | "C:\Users\admin\PixelSee\Luminati-m\luminati-m-controller.exe" switch_on | C:\Users\admin\PixelSee\Luminati-m\luminati-m-controller.exe | lum_inst.tmp | ||||||||||||
User: admin Company: SIA Circle Solutions Integrity Level: HIGH Description: PixelSee Luminati Controller Exit code: 101 Version: 1.0.0.0 Modules
| |||||||||||||||
| 4220 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | brightdata.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4344 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | netsh.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
33 508
Read events
32 797
Write events
618
Delete events
93
Modification events
| (PID) Process: | (8348) PixelSee_id1414223id.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\PixelSee LLC\PixelSee-systemScope\pixelsee_info |
| Operation: | write | Name: | hasDownloadedUpdate |
Value: false | |||
| (PID) Process: | (8348) PixelSee_id1414223id.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (8348) PixelSee_id1414223id.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (8348) PixelSee_id1414223id.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (8348) PixelSee_id1414223id.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\Main\WindowsSearch |
| Operation: | write | Name: | Version |
Value: WS not running | |||
| (PID) Process: | (8348) PixelSee_id1414223id.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | DisableFirstRunCustomize |
Value: 1 | |||
| (PID) Process: | (8348) PixelSee_id1414223id.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\PixelSee |
| Operation: | write | Name: | InstallLocation |
Value: C:\Users\admin\PixelSee\ | |||
| (PID) Process: | (8348) PixelSee_id1414223id.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\PixelSee |
| Operation: | write | Name: | DisplayName |
Value: PixelSee | |||
| (PID) Process: | (8348) PixelSee_id1414223id.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\PixelSee |
| Operation: | write | Name: | DisplayIcon |
Value: C:\Users\admin\PixelSee\pixelsee.exe | |||
| (PID) Process: | (8348) PixelSee_id1414223id.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\PixelSee |
| Operation: | write | Name: | UninstallString |
Value: C:\Users\admin\PixelSee\pixelsee-uninstaller.exe | |||
Executable files
471
Suspicious files
213
Text files
432
Unknown types
7
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7532 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old~RFfe054.TMP | — | |
MD5:— | SHA256:— | |||
| 7532 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7532 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RFfe074.TMP | — | |
MD5:— | SHA256:— | |||
| 7532 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RFfe074.TMP | — | |
MD5:— | SHA256:— | |||
| 7532 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old~RFfe074.TMP | — | |
MD5:— | SHA256:— | |||
| 7532 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7532 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7532 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7532 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RFfe064.TMP | — | |
MD5:— | SHA256:— | |||
| 7532 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RFfe093.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
191
TCP/UDP connections
176
DNS requests
104
Threats
44
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
7860 | msedge.exe | GET | 200 | 51.158.227.68:443 | https://pixelsee.app/desktop/css/baloon.min.css | unknown | text | 4.01 Kb | unknown |
7860 | msedge.exe | GET | 200 | 51.158.227.68:443 | https://pixelsee.app/desktop/css/style.min.css | unknown | text | 13.6 Kb | unknown |
7860 | msedge.exe | GET | 200 | 104.18.23.222:443 | https://copilot.microsoft.com/c/api/user/eligibility | unknown | text | 25 b | whitelisted |
7860 | msedge.exe | GET | 200 | 150.171.28.11:443 | https://edge.microsoft.com/serviceexperimentation/v3/?osname=win&channel=stable&osver=10.0.19045&devicefamily=desktop&installdate=1661339457&clientversion=133.0.3065.92&experimentationmode=2&scpguard=0&scpfull=0&scpver=0 | unknown | text | 446 b | whitelisted |
7860 | msedge.exe | GET | 200 | 150.171.22.17:443 | https://config.edge.skype.com/config/v1/Edge/133.0.3065.92?clientId=4489578223053569932&agents=EdgeFirstRun%2CEdgeFirstRunConfig&osname=win&client=edge&channel=stable&scpfre=0&osarch=x86_64&osver=10.0.19045&wu=1&devicefamily=desktop&uma=0&sessionid=65&mngd=0&installdate=1661339457&edu=0&soobedate=1504771245&bphint=2&fg=1&lbfgdate=1741678270&lafgdate=0 | unknown | text | 768 b | whitelisted |
7860 | msedge.exe | GET | 200 | 150.171.27.11:80 | http://edge.microsoft.com/browsernetworktime/time/1/current?cup2key=2:A9_ZTGKzIcBpx4UVCc4ZXpmywr0yDNZkb3HYSCrlZRE&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | unknown | — | — | whitelisted |
7860 | msedge.exe | POST | 204 | 216.239.34.36:443 | https://region1.analytics.google.com/g/collect?v=2&tid=G-TKL2XXV026>m=45je5cc1v869669615za200zd869669615&_p=1767703704874&_gaz=1&gcd=13l3l3l2l1l1&npa=1&dma_cps=syphamo&dma=1&cid=1174668277.1767703705&ul=en-us&sr=1360x768&ir=1&uaa=x86&uab=64&uafvl=Not(A%253ABrand%3B99.0.0.0%7CMicrosoft%2520Edge%3B133.0.3065.92%7CChromium%3B133.0.6943.142&uamb=0&uam=&uap=Windows&uapv=10.0.0&uaw=0&are=1&frm=0&pscdl=noapi&_eu=EA&_s=1&tag_exp=103116026~103200004~104527907~104528501~104684208~104684211~105391252~115583767~115938465~115938469~116184927~116184929~116251938~116251940&sid=1767703705&sct=1&seg=0&dl=https%3A%2F%2Fpixelsee.app%2Fdesktop%2F&dt=PixelSee%20Video%20Player%20for%20Windows%20%E2%80%94%20Download&en=page_view&_fv=1&_nsi=1&_ss=1&_ee=1&tfd=666 | unknown | — | — | whitelisted |
7860 | msedge.exe | GET | 200 | 51.158.227.68:443 | https://pixelsee.app/desktop/images/product/1.png | unknown | image | 10.2 Kb | unknown |
7860 | msedge.exe | GET | 200 | 51.158.227.68:443 | https://pixelsee.app/desktop/images/up-icon.svg | unknown | image | 255 b | unknown |
7860 | msedge.exe | GET | 200 | 51.158.227.68:443 | https://pixelsee.app/desktop/ | unknown | html | 12.6 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1136 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
6768 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5492 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:138 | — | Not routed | — | whitelisted |
7860 | msedge.exe | 150.171.27.11:80 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7860 | msedge.exe | 150.171.22.17:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7860 | msedge.exe | 142.250.186.99:443 | fonts.gstatic.com | GOOGLE | US | whitelisted |
7860 | msedge.exe | 51.158.227.68:443 | pixelsee.app | Online SAS | FR | suspicious |
7860 | msedge.exe | 142.250.185.72:443 | www.googletagmanager.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
pixelsee.app |
| unknown |
copilot.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7860 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
7860 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
7860 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
— | — | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |
— | — | Potentially Bad Traffic | ET INFO PE EXE or DLL Windows file download HTTP |
— | — | Misc activity | ET INFO EXE - Served Attached HTTP |
— | — | Misc activity | ADWARE [ANY.RUN] Bright Data SDK User-Agent in HTTP request |
— | — | Misc activity | ADWARE [ANY.RUN] Bright Data SDK User-Agent in HTTP request |
— | — | Misc activity | ADWARE [ANY.RUN] Bright Data SDK User-Agent in HTTP request |
— | — | Misc activity | ADWARE [ANY.RUN] Bright Data SDK User-Agent in HTTP request |
Process | Message |
|---|---|
pixelsee.exe | > __thiscall Application::Application(int &,char *[])
|
pixelsee.exe | os version: "10.0.19045v" __ os name: "Windows 10 Version 2009"
|
pixelsee.exe | > int __thiscall Application::exec(void)
|
pixelsee.exe | > __thiscall PixelseeSettings::PixelseeSettings(void)
|
pixelsee.exe | INSTALL ID: "" _ OLD ID: ""
|
pixelsee.exe | reseller - "" installId ""
|
pixelsee.exe | > void __thiscall PixelseeSettings::flushSettings(void)
|
pixelsee.exe | main libvlc debug: VLC media player - 3.0.16 Vetinari
|
pixelsee.exe | main libvlc debug: Copyright © 1996-2021 the VideoLAN team
|
pixelsee.exe | main libvlc debug: revision 3.0.16-0-g5e70837d8d
|