| File name: | file |
| Full analysis: | https://app.any.run/tasks/7242e792-dae4-4d31-9e0f-6fd0120aea6d |
| Verdict: | Malicious activity |
| Threats: | Amadey is a formidable Windows infostealer threat, characterized by its persistence mechanisms, modular design, and ability to execute various malicious tasks. |
| Analysis date: | December 13, 2024, 23:54:37 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 6 sections |
| MD5: | 691C2DD42261C667EF6CA6844F8A56CA |
| SHA1: | 252755B9C7ED1AB5CE27826CFD6ECA4956BD6DED |
| SHA256: | 71DA7D1635F8D6162009AE77943109BF19B0FF32DE0E12B4E6079901FD750B8E |
| SSDEEP: | 98304:C6iQ18aSNBN1ymaqakryW5jvmppDAcQJehwgxx3MWoRz+iqUec9zcTG/fMy/sNMT:Mb9 |
MALICIOUS
Connects to the CnC server
- skotes.exe (PID: 6192)
- 2fc5dbca12.exe (PID: 7396)
- svchost.exe (PID: 2192)
AMADEY has been detected (SURICATA)
- skotes.exe (PID: 6192)
AMADEY has been detected (YARA)
- skotes.exe (PID: 6192)
Uses Task Scheduler to run other applications
- in.exe (PID: 5872)
- in.exe (PID: 7120)
LUMMA mutex has been found
- 0c7142c805.exe (PID: 5892)
- 5a29590ad4.exe (PID: 7628)
Steals credentials from Web Browsers
- 0c7142c805.exe (PID: 5892)
- 0faf5ab951.exe (PID: 624)
- 2fc5dbca12.exe (PID: 7396)
- 5a29590ad4.exe (PID: 7628)
Actions looks like stealing of personal data
- 0c7142c805.exe (PID: 5892)
- 0faf5ab951.exe (PID: 624)
- 2fc5dbca12.exe (PID: 7396)
- 5a29590ad4.exe (PID: 7628)
VIDAR mutex has been found
- 0faf5ab951.exe (PID: 624)
StealC has been detected
- 2fc5dbca12.exe (PID: 7396)
STEALC has been detected (SURICATA)
- 2fc5dbca12.exe (PID: 7396)
Possible tool for stealing has been detected
- 0fc84ba819.exe (PID: 6816)
- firefox.exe (PID: 2132)
LUMMA has been found (auto)
- skotes.exe (PID: 6192)
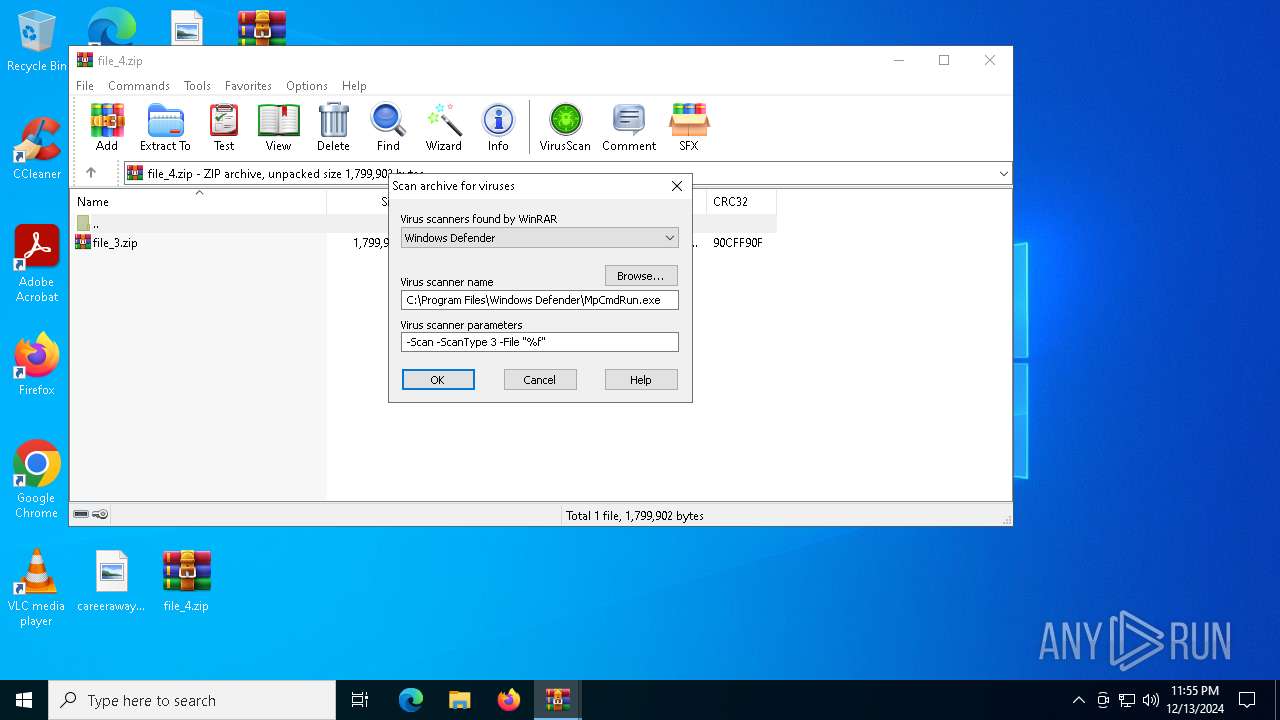
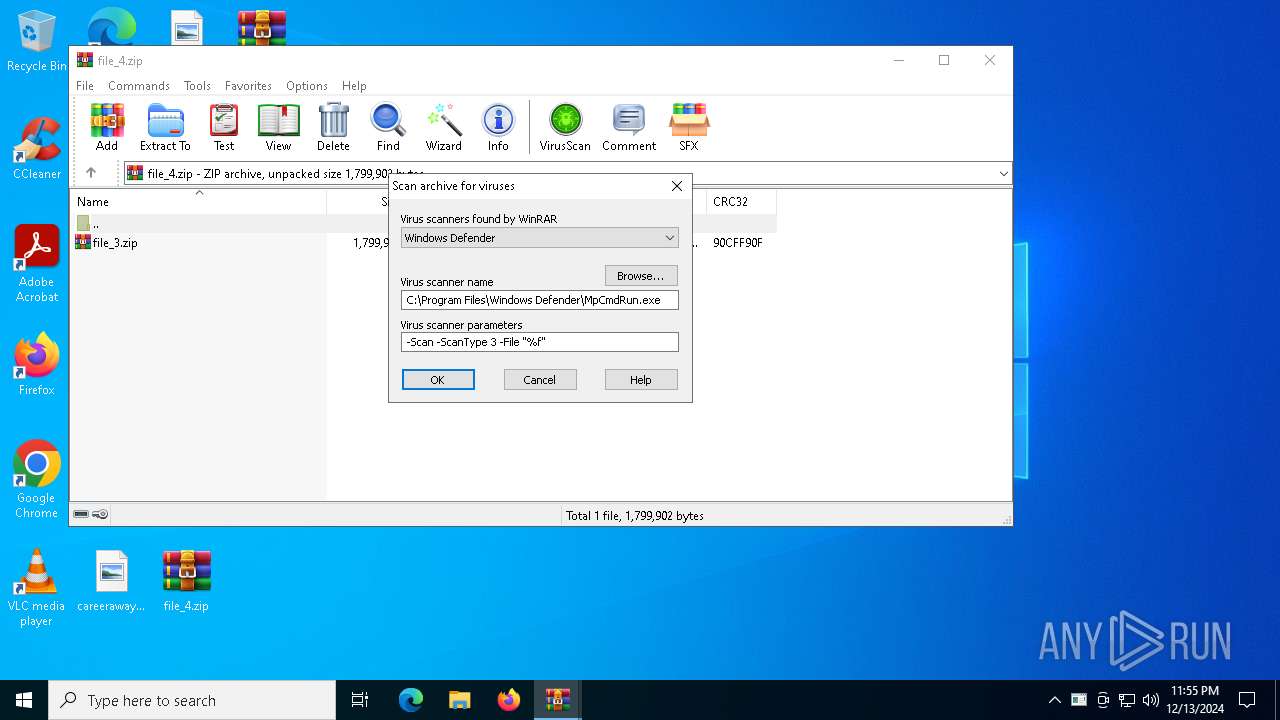
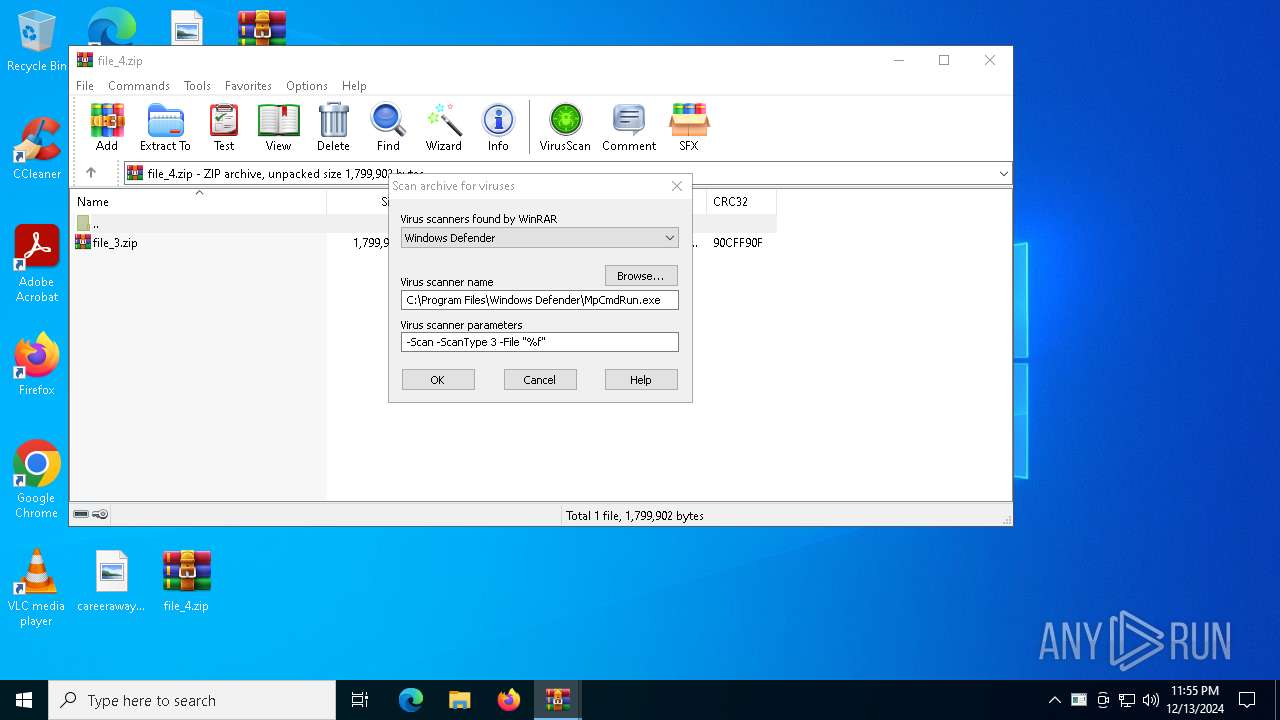
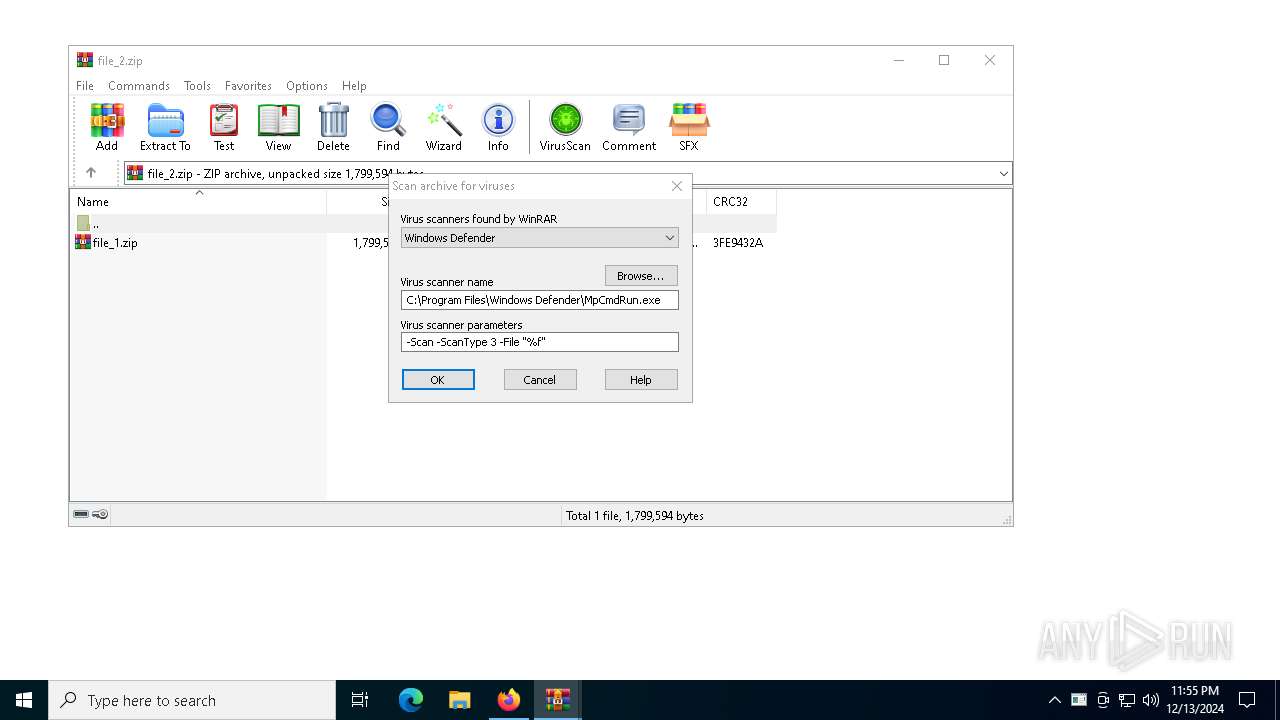
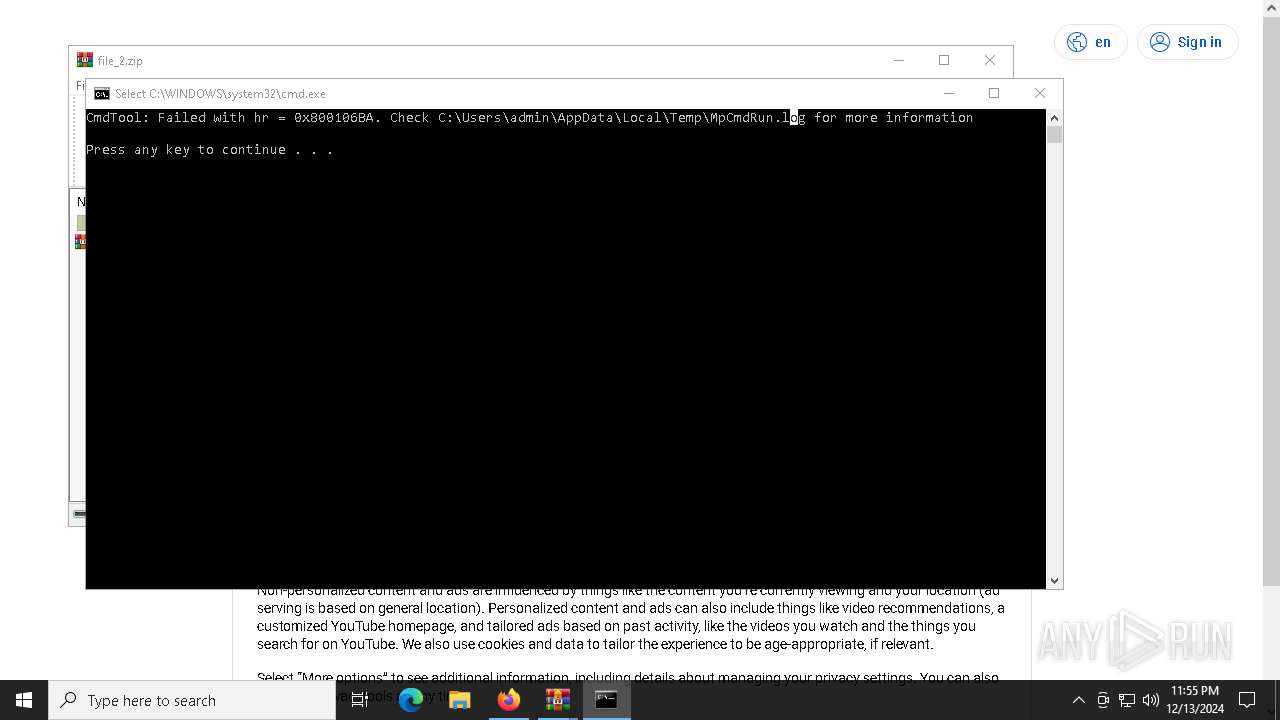
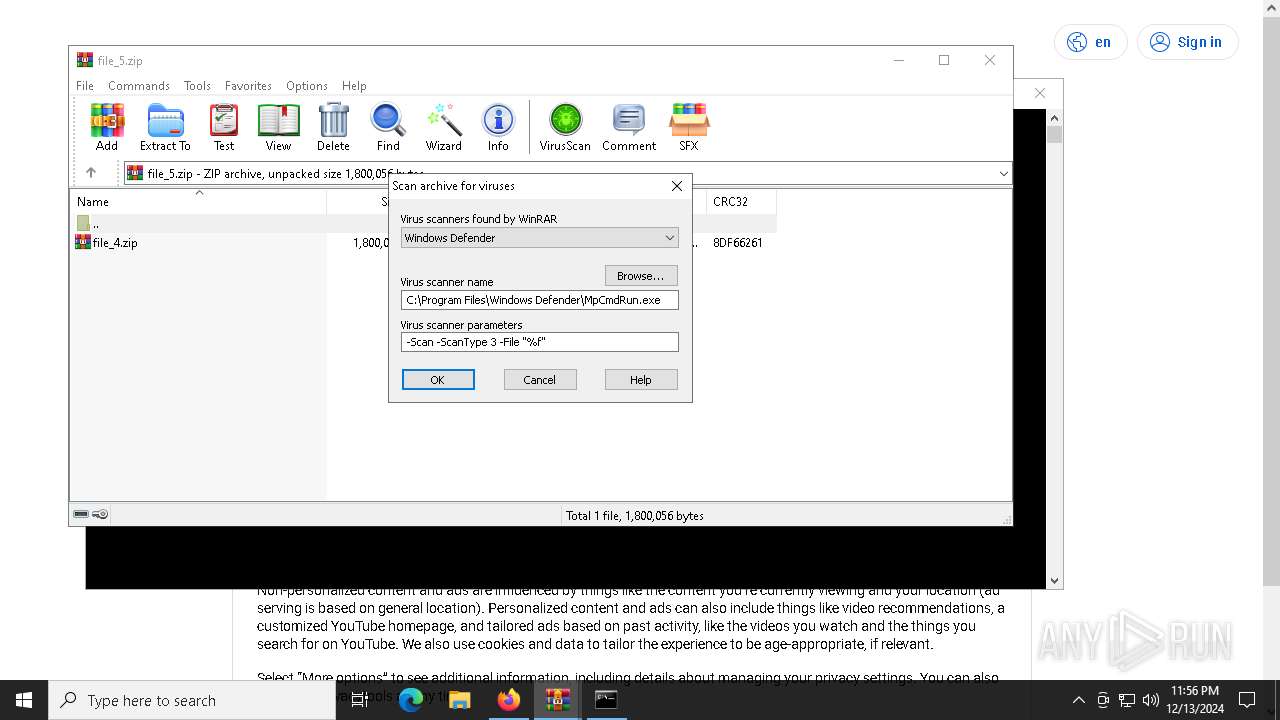
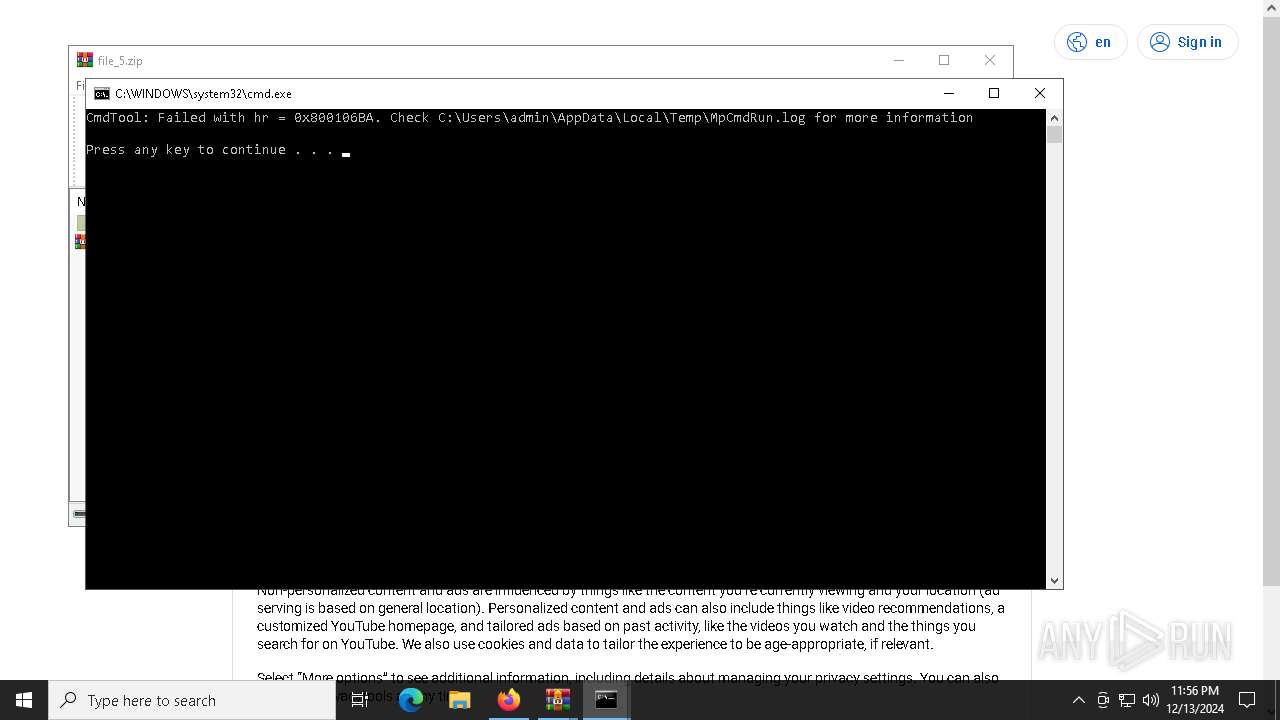
Antivirus name has been found in the command line (generic signature)
- MpCmdRun.exe (PID: 9424)
- MpCmdRun.exe (PID: 3508)
Changes the autorun value in the registry
- skotes.exe (PID: 6192)
LUMMA has been detected (SURICATA)
- svchost.exe (PID: 2192)
- 5a29590ad4.exe (PID: 7628)
SUSPICIOUS
Executable content was dropped or overwritten
- file.exe (PID: 1876)
- skotes.exe (PID: 6192)
- f604866af9.exe (PID: 6612)
- cmd.exe (PID: 6972)
- 7z.exe (PID: 1580)
- in.exe (PID: 5872)
- 2fc5dbca12.exe (PID: 7396)
Starts itself from another location
- file.exe (PID: 1876)
Reads security settings of Internet Explorer
- skotes.exe (PID: 6192)
- f604866af9.exe (PID: 6612)
- 0faf5ab951.exe (PID: 624)
- 2fc5dbca12.exe (PID: 7396)
- WinRAR.exe (PID: 7788)
- d851024040.exe (PID: 6520)
- file.exe (PID: 1876)
- WinRAR.exe (PID: 9928)
Reads the BIOS version
- skotes.exe (PID: 6192)
- skotes.exe (PID: 6464)
- d851024040.exe (PID: 6520)
- 2fc5dbca12.exe (PID: 7396)
- 8e2b19fd9a.exe (PID: 7936)
- file.exe (PID: 1876)
- HIEHDHCFIJ.exe (PID: 2076)
- skotes.exe (PID: 9668)
Connects to the server without a host name
- skotes.exe (PID: 6192)
- 2fc5dbca12.exe (PID: 7396)
Contacting a server suspected of hosting an CnC
- skotes.exe (PID: 6192)
- 2fc5dbca12.exe (PID: 7396)
- svchost.exe (PID: 2192)
- 5a29590ad4.exe (PID: 7628)
Potential Corporate Privacy Violation
- skotes.exe (PID: 6192)
- 2fc5dbca12.exe (PID: 7396)
Process requests binary or script from the Internet
- skotes.exe (PID: 6192)
- 2fc5dbca12.exe (PID: 7396)
Drops 7-zip archiver for unpacking
- f604866af9.exe (PID: 6612)
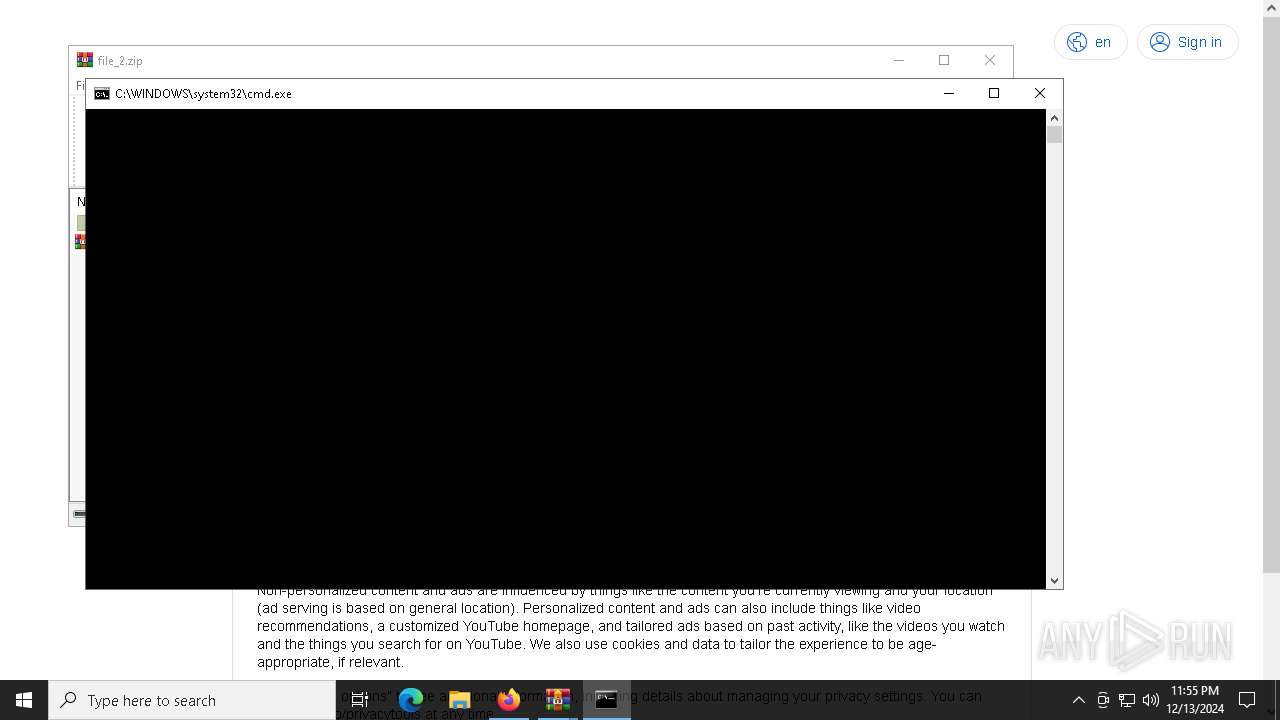
The executable file from the user directory is run by the CMD process
- 7z.exe (PID: 7120)
- 7z.exe (PID: 5208)
- 7z.exe (PID: 3140)
- 7z.exe (PID: 4544)
- 7z.exe (PID: 3724)
- 7z.exe (PID: 4052)
- 7z.exe (PID: 1580)
- 7z.exe (PID: 3680)
- in.exe (PID: 5872)
- HIEHDHCFIJ.exe (PID: 2076)
Application launched itself
- 0c7142c805.exe (PID: 6652)
Executing commands from a ".bat" file
- f604866af9.exe (PID: 6612)
- WinRAR.exe (PID: 7788)
- WinRAR.exe (PID: 9928)
Starts CMD.EXE for commands execution
- f604866af9.exe (PID: 6612)
- WinRAR.exe (PID: 7788)
- 0faf5ab951.exe (PID: 624)
- 2fc5dbca12.exe (PID: 7396)
- WinRAR.exe (PID: 9928)
Starts POWERSHELL.EXE for commands execution
- in.exe (PID: 5872)
- in.exe (PID: 7120)
- Intel_PTT_EK_Recertification.exe (PID: 712)
- Intel_PTT_EK_Recertification.exe (PID: 8956)
Uses ATTRIB.EXE to modify file attributes
- in.exe (PID: 5872)
- cmd.exe (PID: 6972)
- in.exe (PID: 7120)
Found IP address in command line
- powershell.exe (PID: 5868)
- powershell.exe (PID: 440)
- powershell.exe (PID: 2144)
- powershell.exe (PID: 8968)
The process executes via Task Scheduler
- skotes.exe (PID: 6464)
- Intel_PTT_EK_Recertification.exe (PID: 712)
- skotes.exe (PID: 9668)
- Intel_PTT_EK_Recertification.exe (PID: 8956)
Process communicates with Telegram (possibly using it as an attacker's C2 server)
- 0faf5ab951.exe (PID: 624)
Checks Windows Trust Settings
- 0faf5ab951.exe (PID: 624)
Searches for installed software
- 0faf5ab951.exe (PID: 624)
- 2fc5dbca12.exe (PID: 7396)
Uses TASKKILL.EXE to kill Browsers
- 0fc84ba819.exe (PID: 6816)
Windows Defender mutex has been found
- 2fc5dbca12.exe (PID: 7396)
Uses TASKKILL.EXE to kill process
- 0fc84ba819.exe (PID: 6816)
Executes application which crashes
- 0faf5ab951.exe (PID: 624)
Process drops legitimate windows executable
- 2fc5dbca12.exe (PID: 7396)
Uses TIMEOUT.EXE to delay execution
- cmd.exe (PID: 10100)
The process drops Mozilla's DLL files
- 2fc5dbca12.exe (PID: 7396)
The process drops C-runtime libraries
- 2fc5dbca12.exe (PID: 7396)
INFO
Reads the computer name
- skotes.exe (PID: 6192)
- f604866af9.exe (PID: 6612)
- 7z.exe (PID: 7120)
- 7z.exe (PID: 5208)
- 0c7142c805.exe (PID: 5892)
- 7z.exe (PID: 3140)
- 7z.exe (PID: 3724)
- 7z.exe (PID: 4544)
- 7z.exe (PID: 3680)
- 7z.exe (PID: 4052)
- 7z.exe (PID: 1580)
- 0faf5ab951.exe (PID: 624)
- 0fc84ba819.exe (PID: 6816)
- 2fc5dbca12.exe (PID: 7396)
- 8e2b19fd9a.exe (PID: 7936)
- MpCmdRun.exe (PID: 9424)
- d851024040.exe (PID: 6520)
- file.exe (PID: 1876)
- 5a29590ad4.exe (PID: 7628)
- MpCmdRun.exe (PID: 3508)
Process checks computer location settings
- file.exe (PID: 1876)
- skotes.exe (PID: 6192)
- f604866af9.exe (PID: 6612)
- 0faf5ab951.exe (PID: 624)
- 2fc5dbca12.exe (PID: 7396)
Checks proxy server information
- skotes.exe (PID: 6192)
- 0faf5ab951.exe (PID: 624)
- 2fc5dbca12.exe (PID: 7396)
- d851024040.exe (PID: 6520)
- WerFault.exe (PID: 9240)
Checks supported languages
- file.exe (PID: 1876)
- skotes.exe (PID: 6192)
- f604866af9.exe (PID: 6612)
- 0c7142c805.exe (PID: 6652)
- mode.com (PID: 7080)
- 7z.exe (PID: 7120)
- 0c7142c805.exe (PID: 5892)
- 7z.exe (PID: 5208)
- 7z.exe (PID: 4544)
- 7z.exe (PID: 3140)
- 7z.exe (PID: 3724)
- 7z.exe (PID: 3680)
- 7z.exe (PID: 4052)
- 7z.exe (PID: 1580)
- in.exe (PID: 5872)
- 0faf5ab951.exe (PID: 624)
- skotes.exe (PID: 6464)
- d851024040.exe (PID: 6520)
- Intel_PTT_EK_Recertification.exe (PID: 712)
- in.exe (PID: 7120)
- 0fc84ba819.exe (PID: 6816)
- 2fc5dbca12.exe (PID: 7396)
- 8e2b19fd9a.exe (PID: 7936)
- 5a29590ad4.exe (PID: 7628)
- MpCmdRun.exe (PID: 9424)
- HIEHDHCFIJ.exe (PID: 2076)
- Intel_PTT_EK_Recertification.exe (PID: 8956)
- skotes.exe (PID: 9668)
- MpCmdRun.exe (PID: 3508)
Sends debugging messages
- skotes.exe (PID: 6192)
- skotes.exe (PID: 6464)
- d851024040.exe (PID: 6520)
- 8e2b19fd9a.exe (PID: 7936)
- 2fc5dbca12.exe (PID: 7396)
- file.exe (PID: 1876)
- HIEHDHCFIJ.exe (PID: 2076)
- skotes.exe (PID: 9668)
Creates files or folders in the user directory
- skotes.exe (PID: 6192)
- in.exe (PID: 5872)
- 2fc5dbca12.exe (PID: 7396)
- 0faf5ab951.exe (PID: 624)
Create files in a temporary directory
- skotes.exe (PID: 6192)
- f604866af9.exe (PID: 6612)
- 7z.exe (PID: 7120)
- 7z.exe (PID: 5208)
- 7z.exe (PID: 3140)
- 7z.exe (PID: 4544)
- 7z.exe (PID: 3680)
- 7z.exe (PID: 1580)
- 7z.exe (PID: 4052)
- 7z.exe (PID: 3724)
The process uses the downloaded file
- skotes.exe (PID: 6192)
- f604866af9.exe (PID: 6612)
- WinRAR.exe (PID: 7788)
- 0faf5ab951.exe (PID: 624)
- WinRAR.exe (PID: 9928)
The sample compiled with english language support
- f604866af9.exe (PID: 6612)
- skotes.exe (PID: 6192)
- 2fc5dbca12.exe (PID: 7396)
Starts MODE.COM to configure console settings
- mode.com (PID: 7080)
Reads the software policy settings
- 0c7142c805.exe (PID: 5892)
- 0faf5ab951.exe (PID: 624)
- WerFault.exe (PID: 9240)
- 5a29590ad4.exe (PID: 7628)
Themida protector has been detected
- skotes.exe (PID: 6192)
The sample compiled with czech language support
- skotes.exe (PID: 6192)
Reads the machine GUID from the registry
- 0faf5ab951.exe (PID: 624)
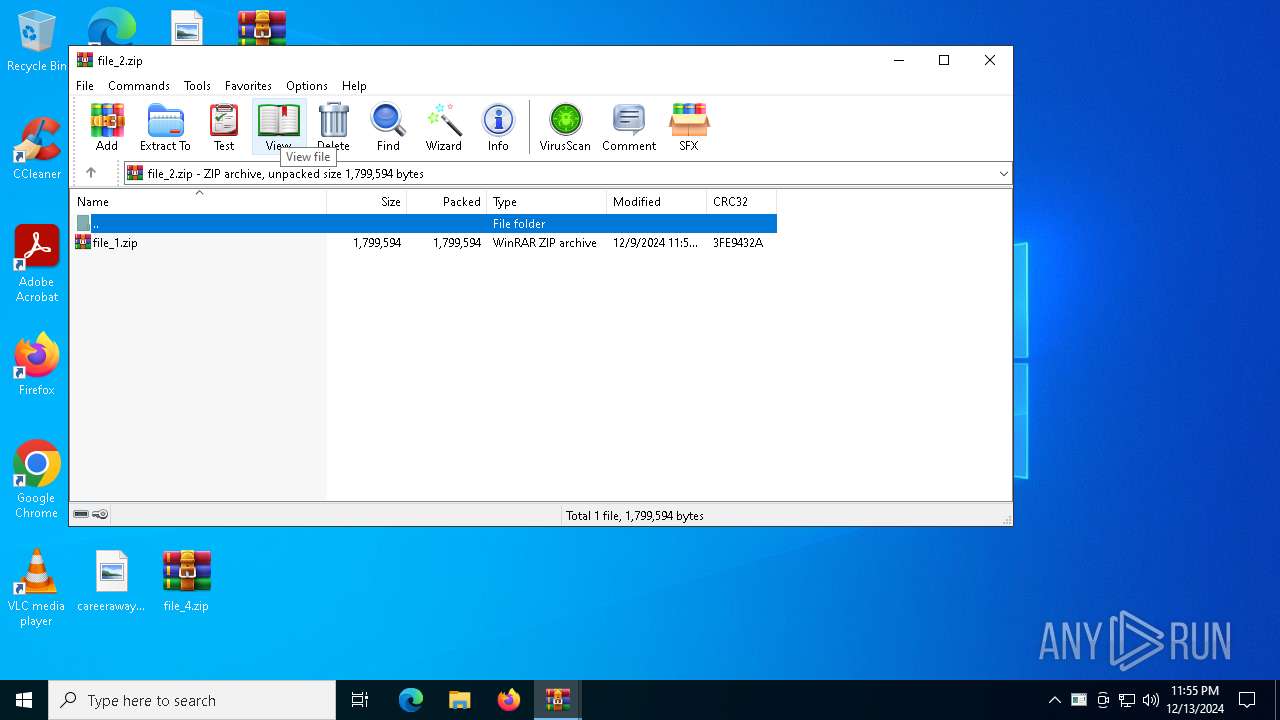
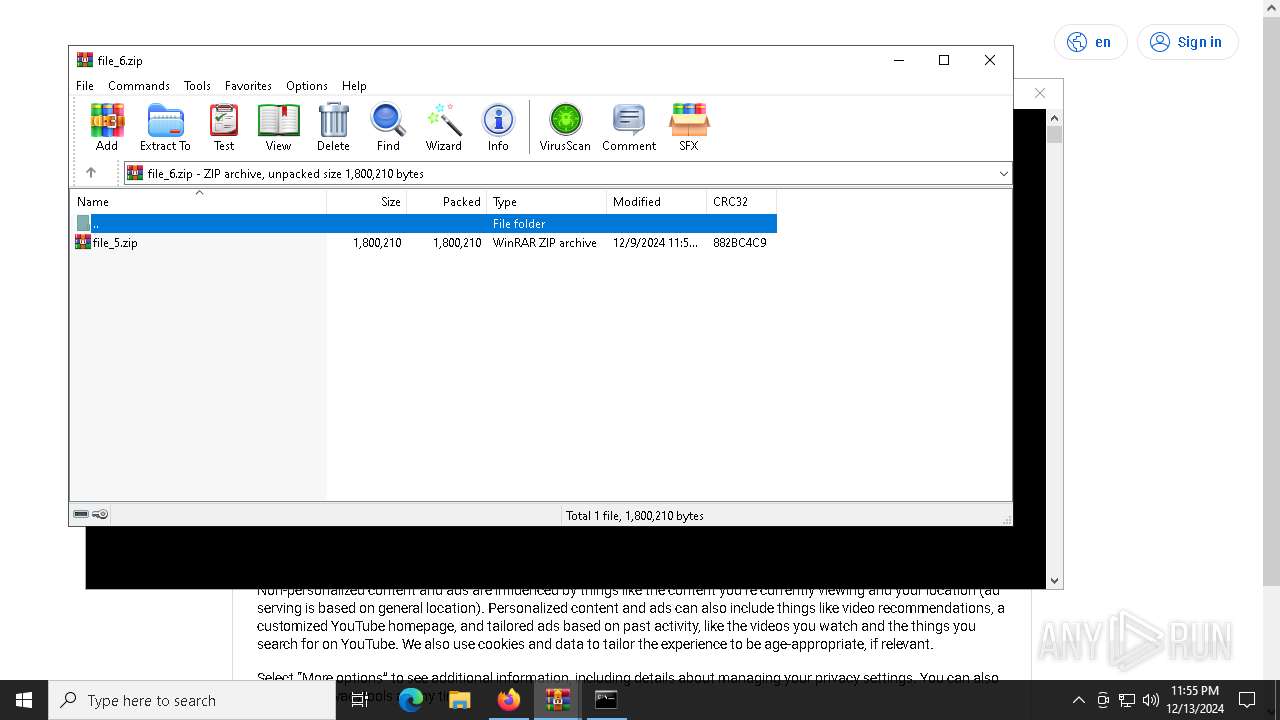
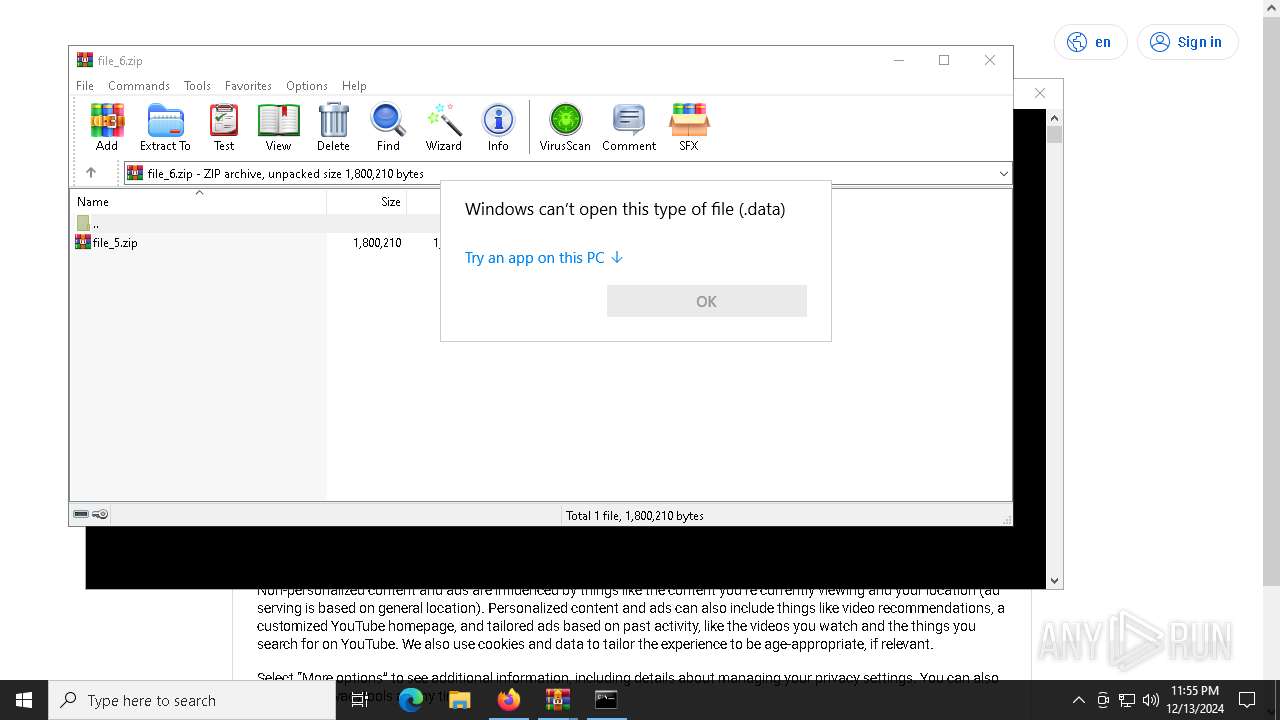
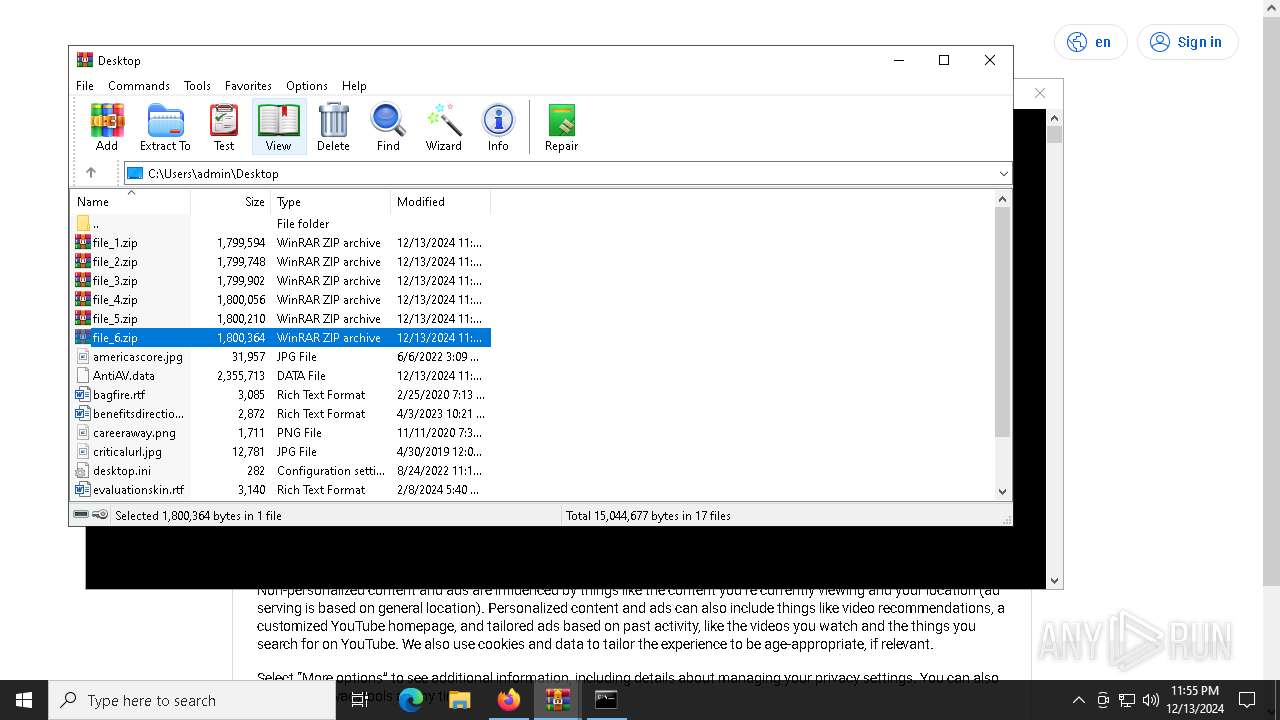
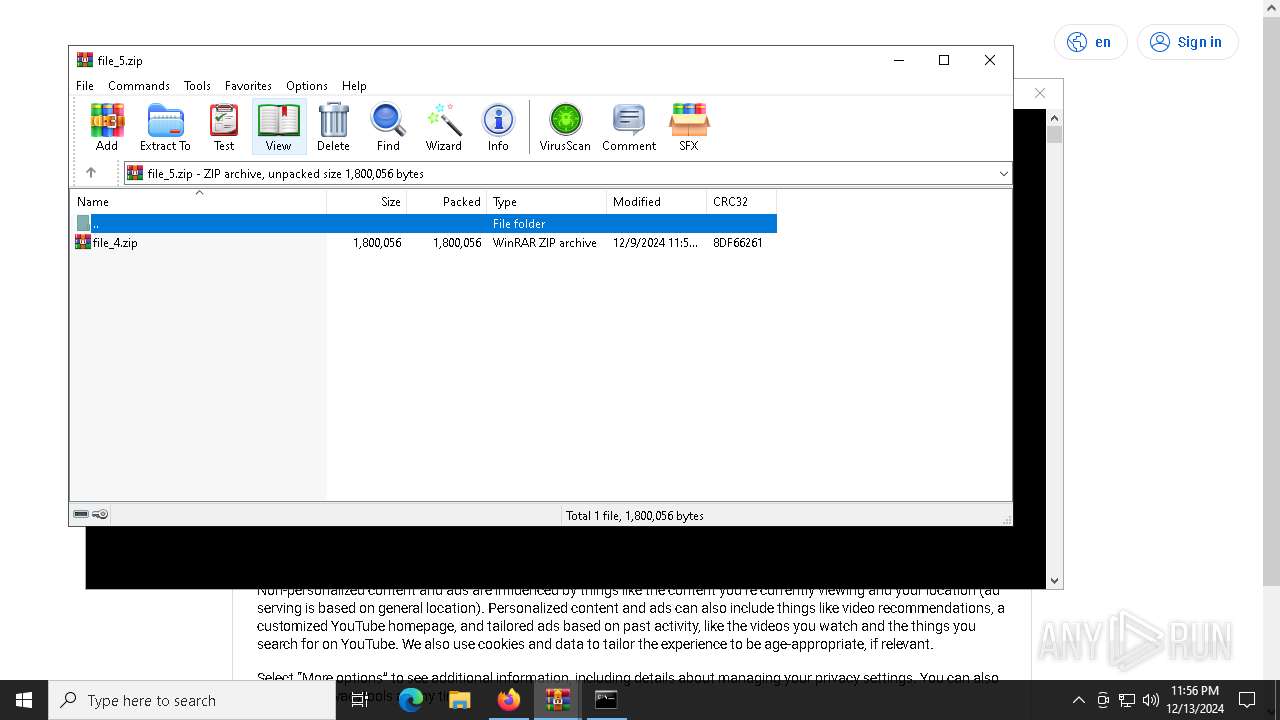
Manual execution by a user
- WinRAR.exe (PID: 6572)
- in.exe (PID: 7120)
- WinRAR.exe (PID: 5652)
- WinRAR.exe (PID: 5992)
- WinRAR.exe (PID: 7788)
- WinRAR.exe (PID: 7468)
- OpenWith.exe (PID: 9992)
- WinRAR.exe (PID: 9928)
Reads product name
- 0faf5ab951.exe (PID: 624)
- 2fc5dbca12.exe (PID: 7396)
Reads Environment values
- 0faf5ab951.exe (PID: 624)
- 2fc5dbca12.exe (PID: 7396)
Reads CPU info
- 0faf5ab951.exe (PID: 624)
- 2fc5dbca12.exe (PID: 7396)
Application launched itself
- chrome.exe (PID: 2456)
- chrome.exe (PID: 2800)
- msedge.exe (PID: 8808)
- firefox.exe (PID: 7896)
- firefox.exe (PID: 2132)
Reads mouse settings
- 0fc84ba819.exe (PID: 6816)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 440)
- powershell.exe (PID: 5868)
- powershell.exe (PID: 2144)
- powershell.exe (PID: 8968)
Creates files in the program directory
- 0faf5ab951.exe (PID: 624)
- 2fc5dbca12.exe (PID: 7396)
Reads Microsoft Office registry keys
- OpenWith.exe (PID: 9992)
Executable content was dropped or overwritten
- firefox.exe (PID: 7896)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Amadey
(PID) Process(6192) skotes.exe
C2185.215.113.43
URLhttp://185.215.113.43/Zu7JuNko/index.php
Version4.42
Options
Drop directoryabc3bc1985
Drop nameskotes.exe
Strings (120)2016
cmd /C RMDIR /s/q
Comodo
st=s
=
skotes.exe
\App
Norton
e1
AVG
" && timeout 1 && del
exe
2019
--
wb
DefaultSettings.YResolution
ProgramData\
:::
VideoID
Rem
SYSTEM\CurrentControlSet\Control\ComputerName\ComputerName
SOFTWARE\Microsoft\Windows\CurrentVersion\RunOnce
SOFTWARE\Microsoft\Windows\CurrentVersion\Run
http://
<d>
2022
Sophos
Programs
lv:
&unit=
------
POST
%-lu
<c>
Content-Type: application/x-www-form-urlencoded
185.215.113.43
Doctor Web
\
id:
SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\Shell Folders
360TotalSecurity
Startup
clip.dll
"
Content-Type: application/octet-stream
Content-Type: multipart/form-data; boundary=----
cred.dll|clip.dll|
S-%lu-
rb
rundll32.exe
0123456789
GetNativeSystemInfo
abc3bc1985
SYSTEM\CurrentControlSet\Control\UnitedVideo\CONTROL\VIDEO\
" && ren
d1
ESET
vs:
"
------
sd:
WinDefender
dll
e0
%USERPROFILE%
Panda Security
SOFTWARE\Microsoft\Windows NT\CurrentVersion
zip
cmd
-unicode-
cred.dll
shell32.dll
ProductName
&&
shutdown -s -t 0
|
/Plugins/
Bitdefender
\0000
Content-Disposition: form-data; name="data"; filename="
/Zu7JuNko/index.php
os:
SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\User Shell Folders
av:
4.42
-%lu
Avira
GET
e2
/quiet
Kaspersky Lab
#
ps1
-executionpolicy remotesigned -File "
DefaultSettings.XResolution
Powershell.exe
bi:
msi
https://
random
pc:
un:
abcdefghijklmnopqrstuvwxyz0123456789-_
ar:
Main
"taskkill /f /im "
ComputerName
2025
AVAST Software
SYSTEM\ControlSet001\Services\BasicDisplay\Video
r=
.jpg
CurrentBuild
og:
dm:
?scr=1
kernel32.dll
/k
&& Exit"
+++
rundll32
TRiD
| .dll | | | Win32 Dynamic Link Library (generic) (43.5) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (29.8) |
| .exe | | | Generic Win/DOS Executable (13.2) |
| .exe | | | DOS Executable Generic (13.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2024:09:22 17:40:44+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 14.24 |
| CodeSize: | 322048 |
| InitializedDataSize: | 104960 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x308000 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
Total processes
255
Monitored processes
126
Malicious processes
13
Suspicious processes
8
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 440 | powershell ping 127.0.0.1; del in.exe | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | in.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 520 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --no-appcompat-clear --gpu-preferences=WAAAAAAAAADgAAAMAAAAAAAAAAAAAAAAAABgAAAAAAA4AAAAAAAAAAAAAAAEAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAGAAAAAAAAAAYAAAAAAAAAAgAAAAAAAAACAAAAAAAAAAIAAAAAAAAAA== --mojo-platform-channel-handle=2060 --field-trial-handle=2064,i,14879182071196262265,14174533788268388606,262144 --variations-seed-version /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 1 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 624 | "C:\Users\admin\AppData\Local\Temp\1014982001\0faf5ab951.exe" | C:\Users\admin\AppData\Local\Temp\1014982001\0faf5ab951.exe | skotes.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221225477 Modules
| |||||||||||||||
| 628 | "C:\WINDOWS\system32\PING.EXE" 127.1.10.1 | C:\Windows\System32\PING.EXE | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: TCP/IP Ping Command Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 712 | "C:\Users\admin\AppData\Roaming\Intel_PTT_EK_Recertification.exe" | C:\Users\admin\AppData\Roaming\Intel_PTT_EK_Recertification.exe | — | svchost.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221225477 Modules
| |||||||||||||||
| 1580 | 7z.exe e extracted/file_1.zip -oextracted | C:\Users\admin\AppData\Local\Temp\main\7z.exe | cmd.exe | ||||||||||||
User: admin Company: Igor Pavlov Integrity Level: MEDIUM Description: 7-Zip Console Exit code: 0 Version: 19.00 Modules
| |||||||||||||||
| 1580 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=2144 --field-trial-handle=2064,i,14879182071196262265,14174533788268388606,262144 --variations-seed-version /prefetch:3 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 1 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 1876 | "C:\Users\admin\AppData\Local\Temp\file.exe" | C:\Users\admin\AppData\Local\Temp\file.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2076 | "C:\Users\admin\Documents\HIEHDHCFIJ.exe" | C:\Users\admin\Documents\HIEHDHCFIJ.exe | cmd.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2132 | "C:\Program Files\Mozilla Firefox\firefox.exe" --kiosk "https://youtube.com/account?=https://accounts.google.com/v3/signin/challenge/pwd" --no-default-browser-check --disable-popup-blocking | C:\Program Files\Mozilla Firefox\firefox.exe | 0fc84ba819.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 123.0 Modules
| |||||||||||||||
Total events
57 841
Read events
57 738
Write events
103
Delete events
0
Modification events
| (PID) Process: | (6192) skotes.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (6192) skotes.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (6192) skotes.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (624) 0faf5ab951.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (624) 0faf5ab951.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (624) 0faf5ab951.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
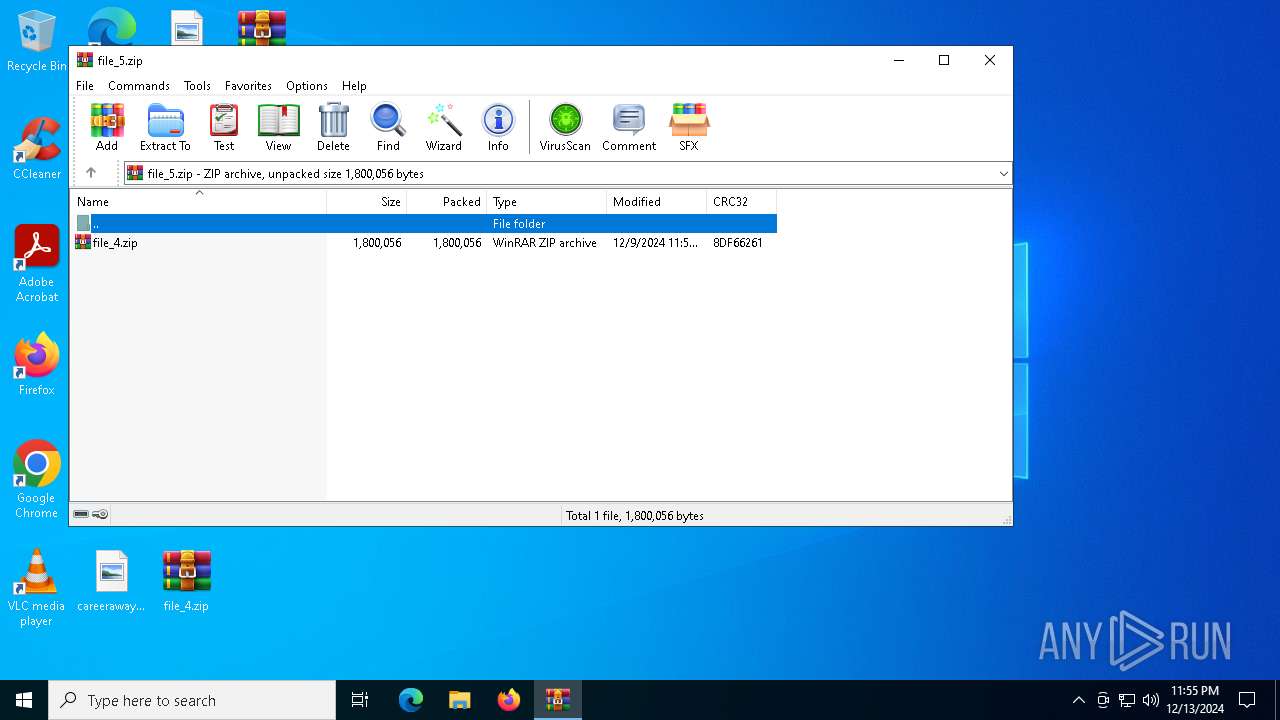
| (PID) Process: | (6572) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (6572) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (6572) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (6572) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\file_5.zip | |||
Executable files
52
Suspicious files
332
Text files
146
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6612 | f604866af9.exe | C:\Users\admin\AppData\Local\Temp\main\main.bat | text | |
MD5:3626532127E3066DF98E34C3D56A1869 | SHA256:2A0E18EF585DB0802269B8C1DDCCB95CE4C0BAC747E207EE6131DEE989788BCA | |||
| 6612 | f604866af9.exe | C:\Users\admin\AppData\Local\Temp\main\7z.exe | executable | |
MD5:619F7135621B50FD1900FF24AADE1524 | SHA256:344F076BB1211CB02ECA9E5ED2C0CE59BCF74CCBC749EC611538FA14ECB9AAD2 | |||
| 6192 | skotes.exe | C:\Users\admin\AppData\Local\Temp\1014981001\0c7142c805.exe | executable | |
MD5:28E568616A7B792CAC1726DEB77D9039 | SHA256:9597798F7789ADC29FBE97707B1BD8CA913C4D5861B0AD4FDD6B913AF7C7A8E2 | |||
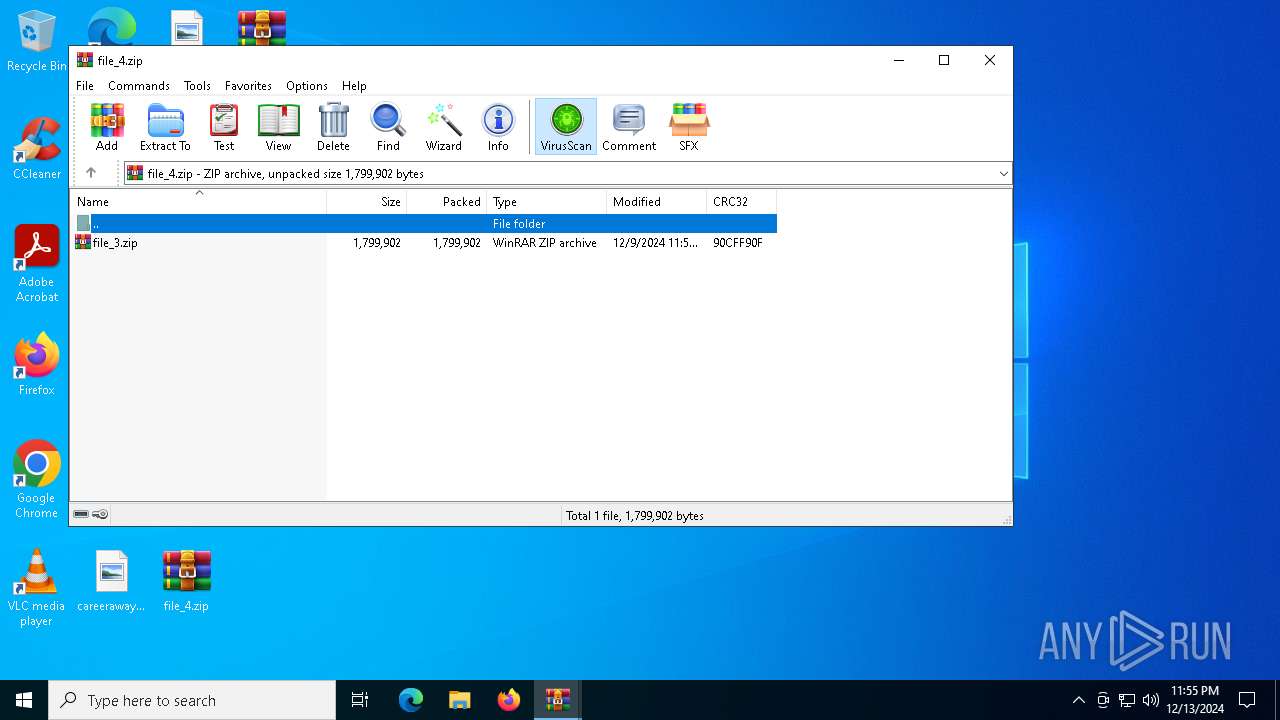
| 7120 | 7z.exe | C:\Users\admin\AppData\Local\Temp\main\extracted\file_7.zip | compressed | |
MD5:CEA368FC334A9AEC1ECFF4B15612E5B0 | SHA256:07E38CAD68B0CDBEA62F55F9BC6EE80545C2E1A39983BAA222E8AF788F028541 | |||
| 6192 | skotes.exe | C:\Users\admin\AppData\Local\Temp\1014980001\f604866af9.exe | executable | |
MD5:3A425626CBD40345F5B8DDDD6B2B9EFA | SHA256:BA9212D2D5CD6DF5EB7933FB37C1B72A648974C1730BF5C32439987558F8E8B1 | |||
| 6192 | skotes.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\IE\KCV3KQBA\random[1].exe | executable | |
MD5:28E568616A7B792CAC1726DEB77D9039 | SHA256:9597798F7789ADC29FBE97707B1BD8CA913C4D5861B0AD4FDD6B913AF7C7A8E2 | |||
| 6612 | f604866af9.exe | C:\Users\admin\AppData\Local\Temp\main\KillDuplicate.cmd | text | |
MD5:68CECDF24AA2FD011ECE466F00EF8450 | SHA256:64929489DC8A0D66EA95113D4E676368EDB576EA85D23564D53346B21C202770 | |||
| 6612 | f604866af9.exe | C:\Users\admin\AppData\Local\Temp\main\file.bin | compressed | |
MD5:045B0A3D5BE6F10DDF19AE6D92DFDD70 | SHA256:94B392E94FA47D1B9B7AE6A29527727268CC2E3484E818C23608F8835BC1104D | |||
| 3140 | 7z.exe | C:\Users\admin\AppData\Local\Temp\main\extracted\file_5.zip | compressed | |
MD5:B7D1E04629BEC112923446FDA5391731 | SHA256:4DA77D4EE30AD0CD56CD620F4E9DC4016244ACE015C5B4B43F8F37DD8E3A8789 | |||
| 6972 | cmd.exe | C:\Users\admin\AppData\Local\Temp\main\file.zip | compressed | |
MD5:045B0A3D5BE6F10DDF19AE6D92DFDD70 | SHA256:94B392E94FA47D1B9B7AE6A29527727268CC2E3484E818C23608F8835BC1104D | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
84
TCP/UDP connections
219
DNS requests
233
Threats
72
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.53.40.178:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6192 | skotes.exe | GET | — | 31.41.244.11:80 | http://31.41.244.11/files/burpin1/random.exe | unknown | — | — | unknown |
6192 | skotes.exe | POST | 200 | 185.215.113.43:80 | http://185.215.113.43/Zu7JuNko/index.php | unknown | — | — | malicious |
6192 | skotes.exe | POST | 200 | 185.215.113.43:80 | http://185.215.113.43/Zu7JuNko/index.php | unknown | — | — | malicious |
6192 | skotes.exe | POST | 200 | 185.215.113.43:80 | http://185.215.113.43/Zu7JuNko/index.php | unknown | — | — | malicious |
1176 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5064 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
6192 | skotes.exe | POST | 200 | 185.215.113.43:80 | http://185.215.113.43/Zu7JuNko/index.php | unknown | — | — | malicious |
6192 | skotes.exe | POST | 200 | 185.215.113.43:80 | http://185.215.113.43/Zu7JuNko/index.php | unknown | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1016 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4712 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 23.53.40.178:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
6192 | skotes.exe | 185.215.113.43:80 | — | 1337team Limited | SC | malicious |
1016 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6192 | skotes.exe | 31.41.244.11:80 | — | Red Bytes LLC | RU | unknown |
5064 | SearchApp.exe | 104.126.37.131:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
login.live.com |
| whitelisted |
drive-connect.cyou |
| malicious |
go.microsoft.com |
| whitelisted |
t.me |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6192 | skotes.exe | Misc Attack | ET DROP Spamhaus DROP Listed Traffic Inbound group 33 |
6192 | skotes.exe | Malware Command and Control Activity Detected | BOTNET [ANY.RUN] Amadey HTTP POST Request (st=s) |
6192 | skotes.exe | Potentially Bad Traffic | ET INFO Executable Download from dotted-quad Host |
6192 | skotes.exe | Misc Attack | ET DROP Spamhaus DROP Listed Traffic Inbound group 2 |
6192 | skotes.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
6192 | skotes.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
6192 | skotes.exe | Potentially Bad Traffic | ET HUNTING SUSPICIOUS Dotted Quad Host MZ Response |
6192 | skotes.exe | Potentially Bad Traffic | ET INFO Executable Download from dotted-quad Host |
6192 | skotes.exe | A Network Trojan was detected | ET MALWARE Win32/Amadey Host Fingerprint Exfil (POST) M2 |
6192 | skotes.exe | A Network Trojan was detected | ET MALWARE Win32/Amadey Host Fingerprint Exfil (POST) M2 |
4 ETPRO signatures available at the full report
Process | Message |
|---|---|
file.exe |
%s------------------------------------------------
--- Themida Professional ---
--- (c)2012 Oreans Technologies ---
------------------------------------------------
|
skotes.exe |
%s------------------------------------------------
--- Themida Professional ---
--- (c)2012 Oreans Technologies ---
------------------------------------------------
|
skotes.exe |
%s------------------------------------------------
--- Themida Professional ---
--- (c)2012 Oreans Technologies ---
------------------------------------------------
|
d851024040.exe |
%s------------------------------------------------
--- Themida Professional ---
--- (c)2012 Oreans Technologies ---
------------------------------------------------
|
2fc5dbca12.exe |
%s------------------------------------------------
--- Themida Professional ---
--- (c)2012 Oreans Technologies ---
------------------------------------------------
|
8e2b19fd9a.exe |
%s------------------------------------------------
--- Themida Professional ---
--- (c)2012 Oreans Technologies ---
------------------------------------------------
|
HIEHDHCFIJ.exe |
%s------------------------------------------------
--- Themida Professional ---
--- (c)2012 Oreans Technologies ---
------------------------------------------------
|
skotes.exe |
%s------------------------------------------------
--- Themida Professional ---
--- (c)2012 Oreans Technologies ---
------------------------------------------------
|