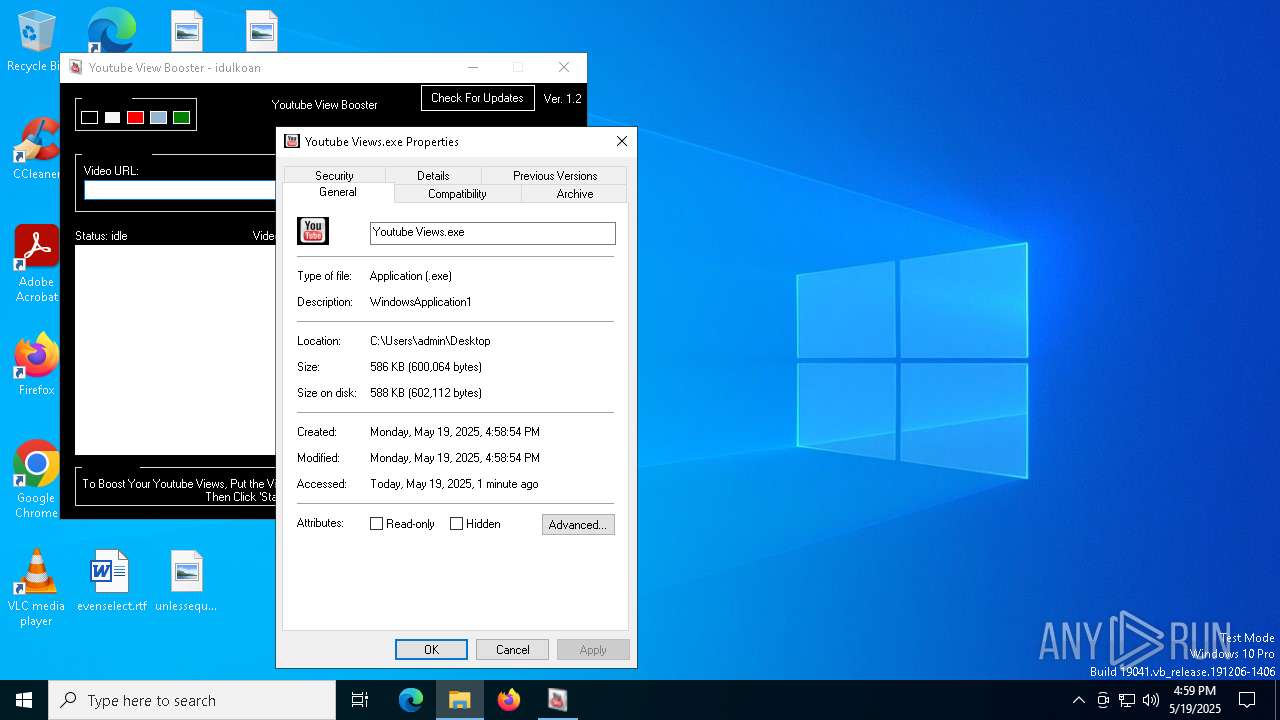
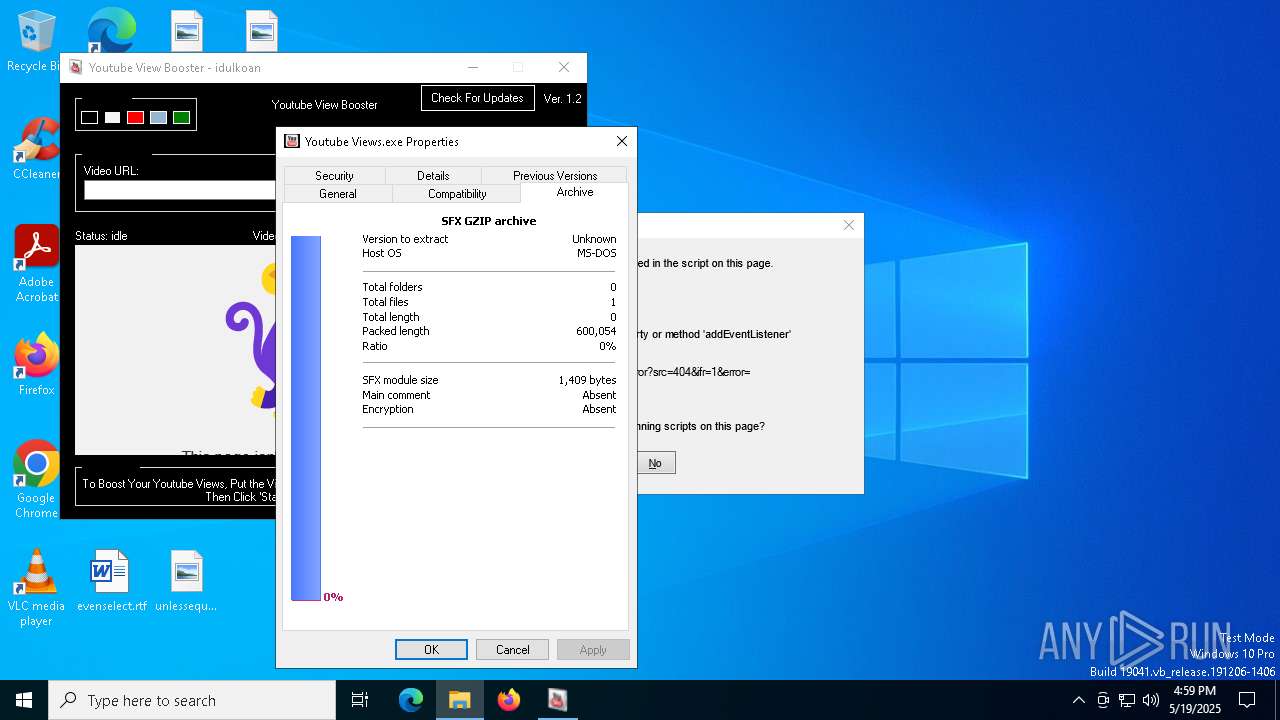
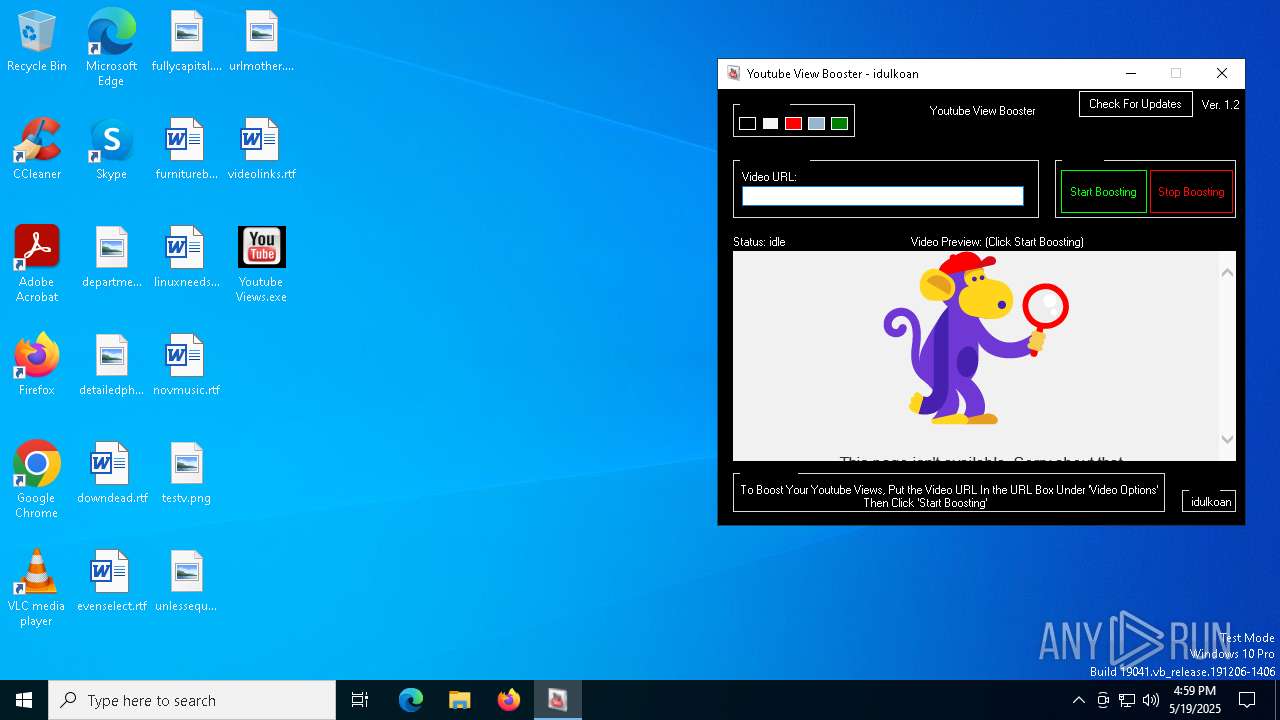
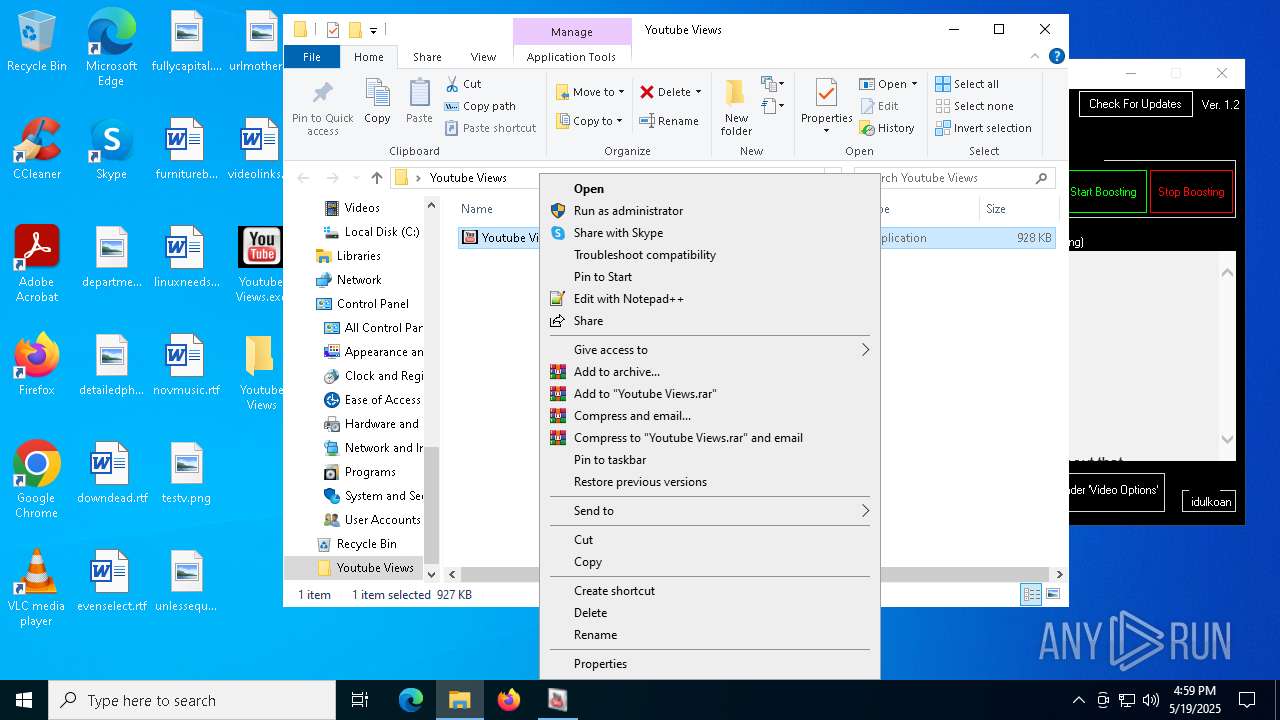
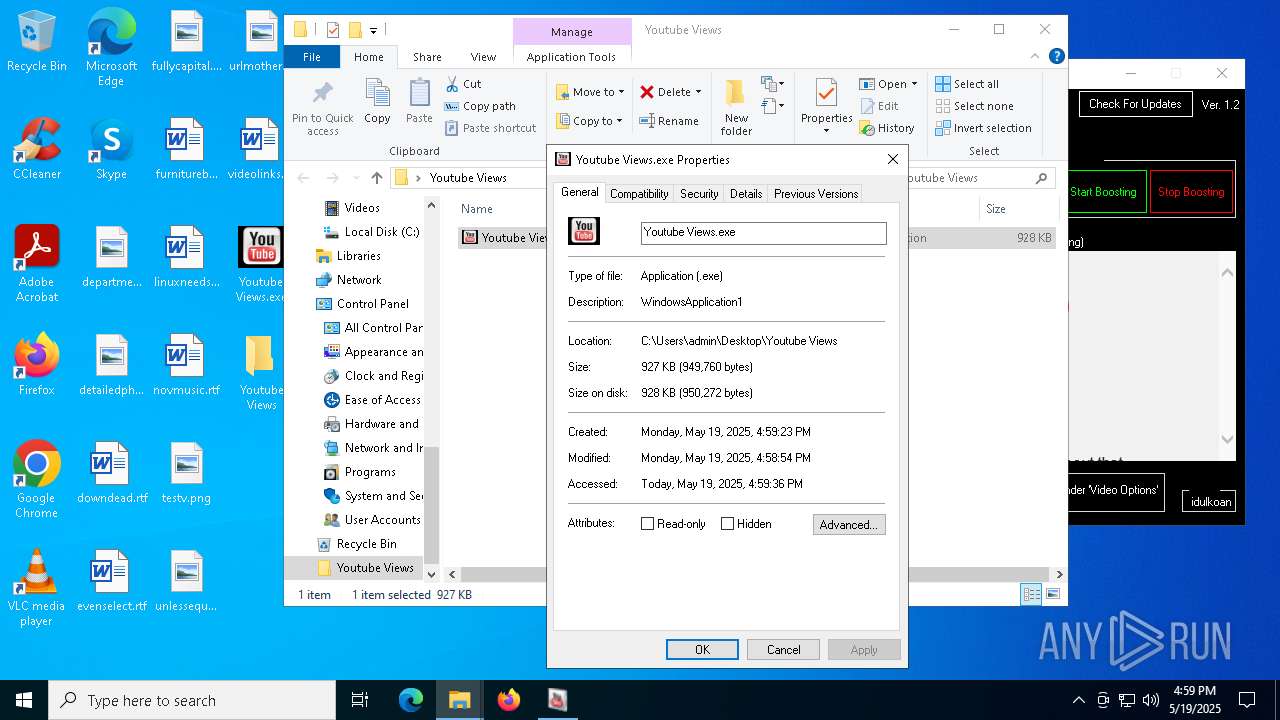
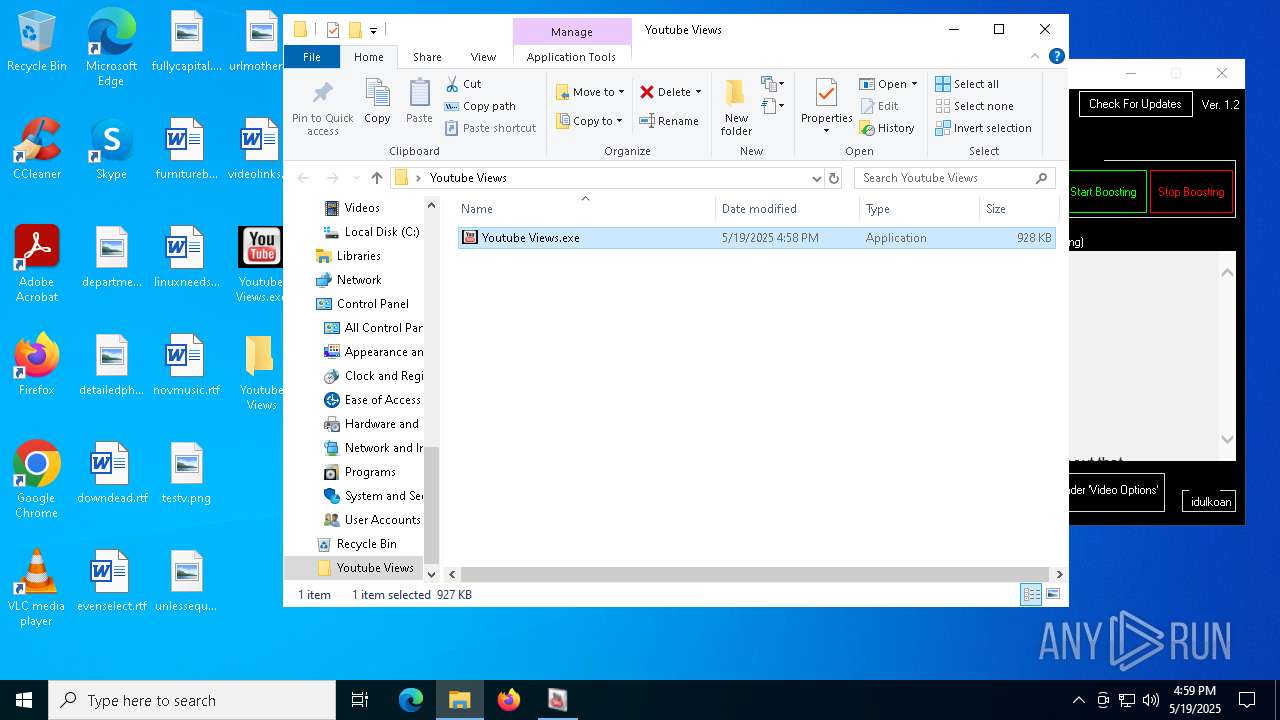
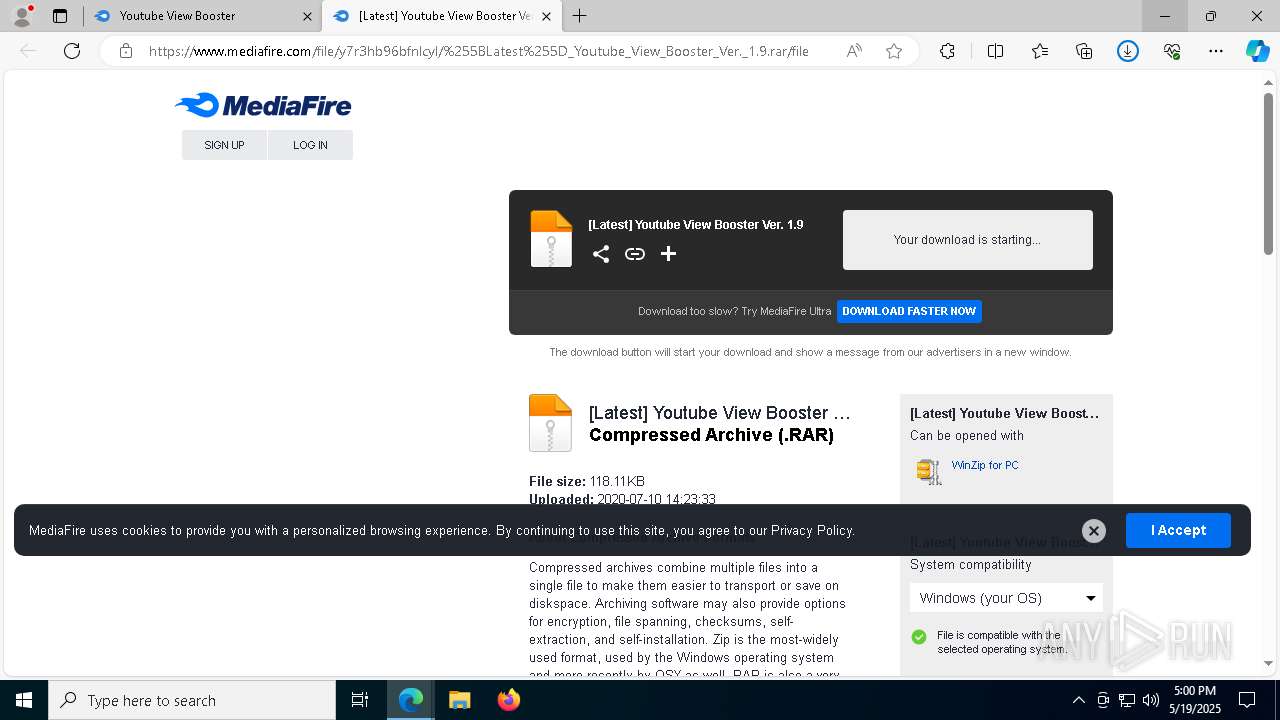
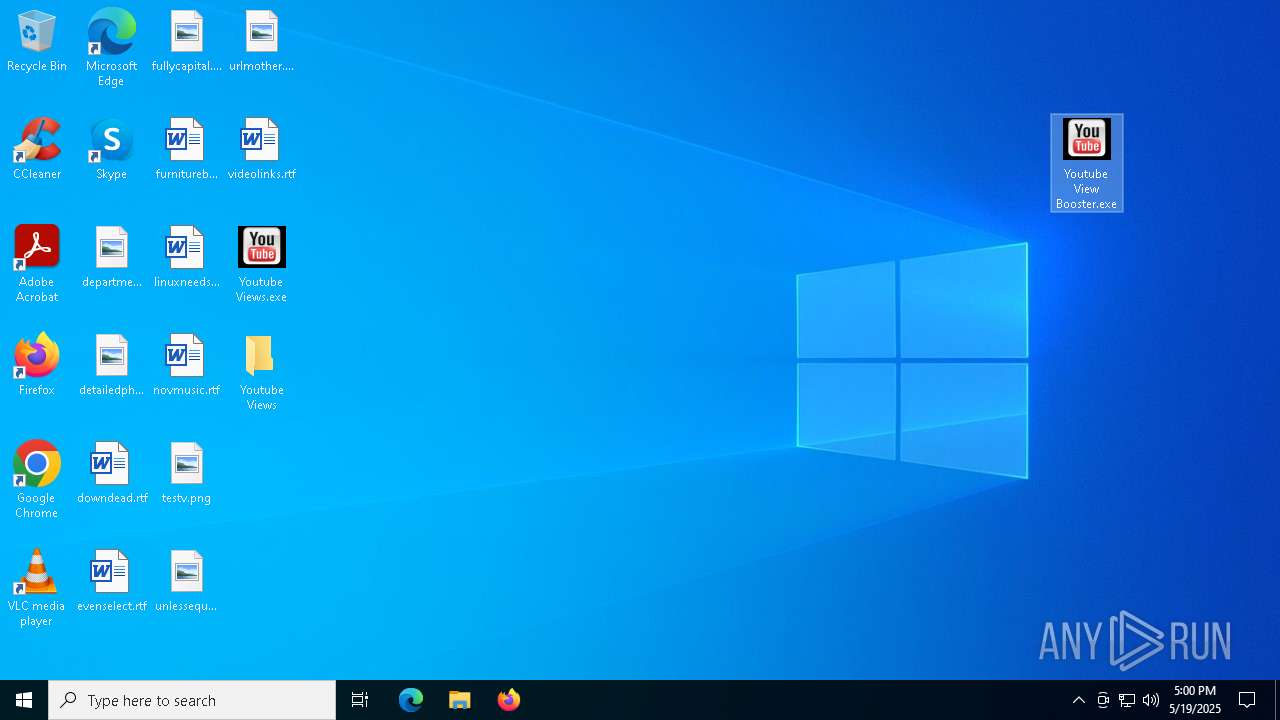
| File name: | Youtube Views.exe |
| Full analysis: | https://app.any.run/tasks/a55a4d7f-e2fe-4476-b6dd-d81b8a3c79dd |
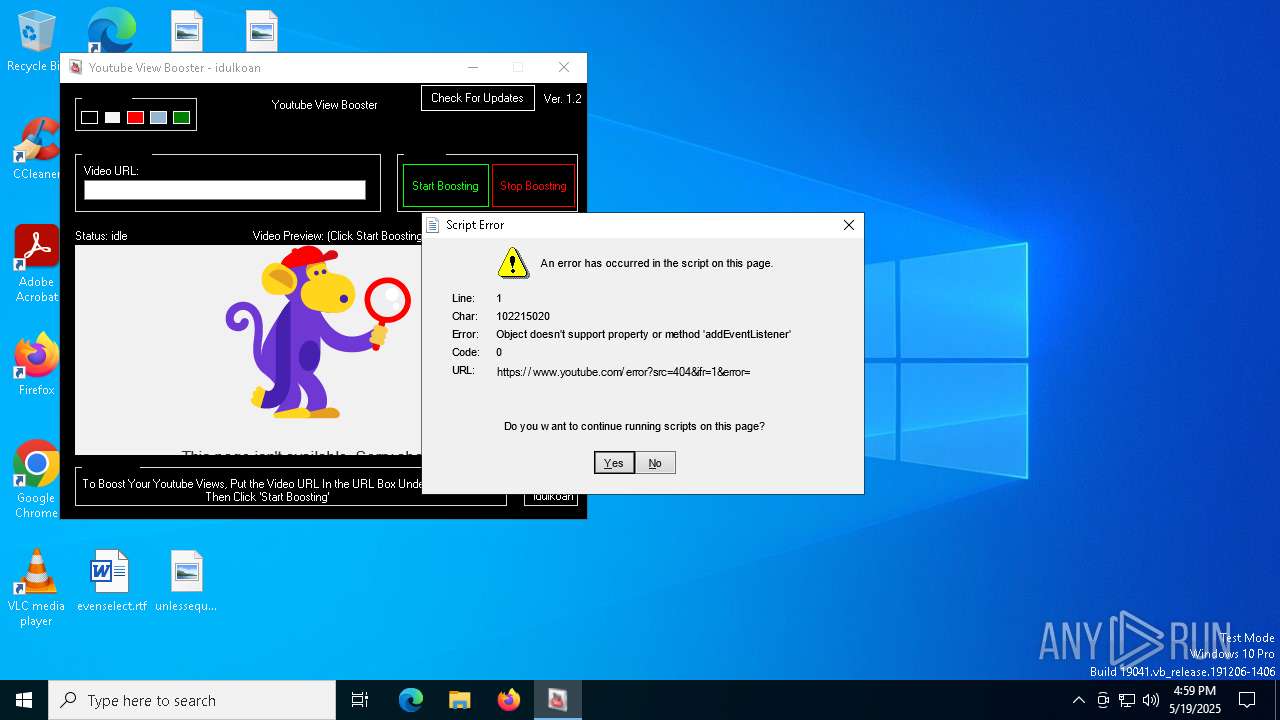
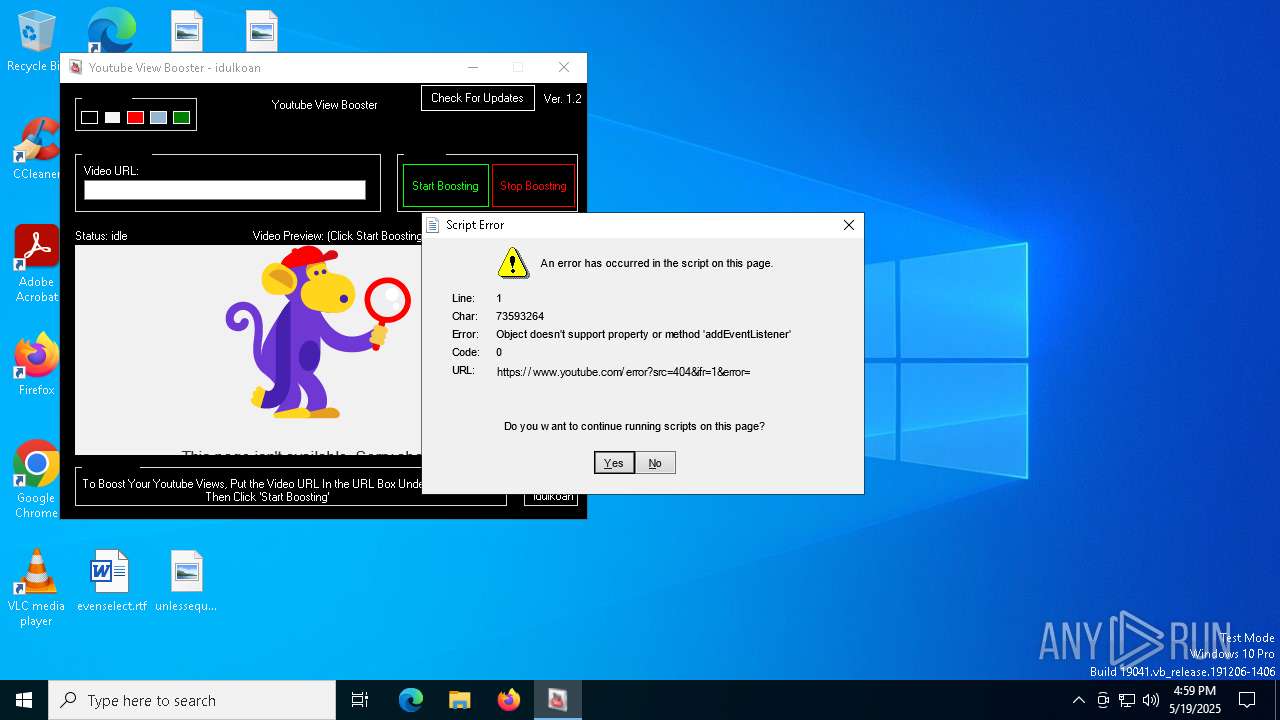
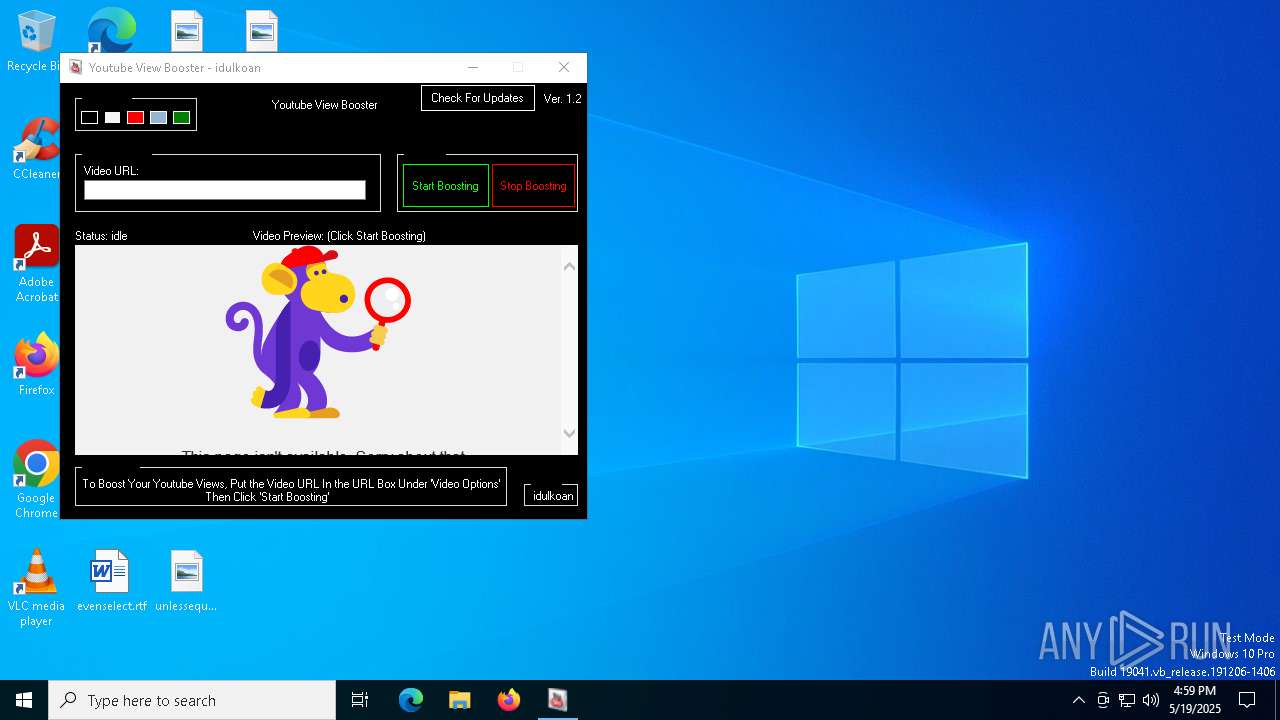
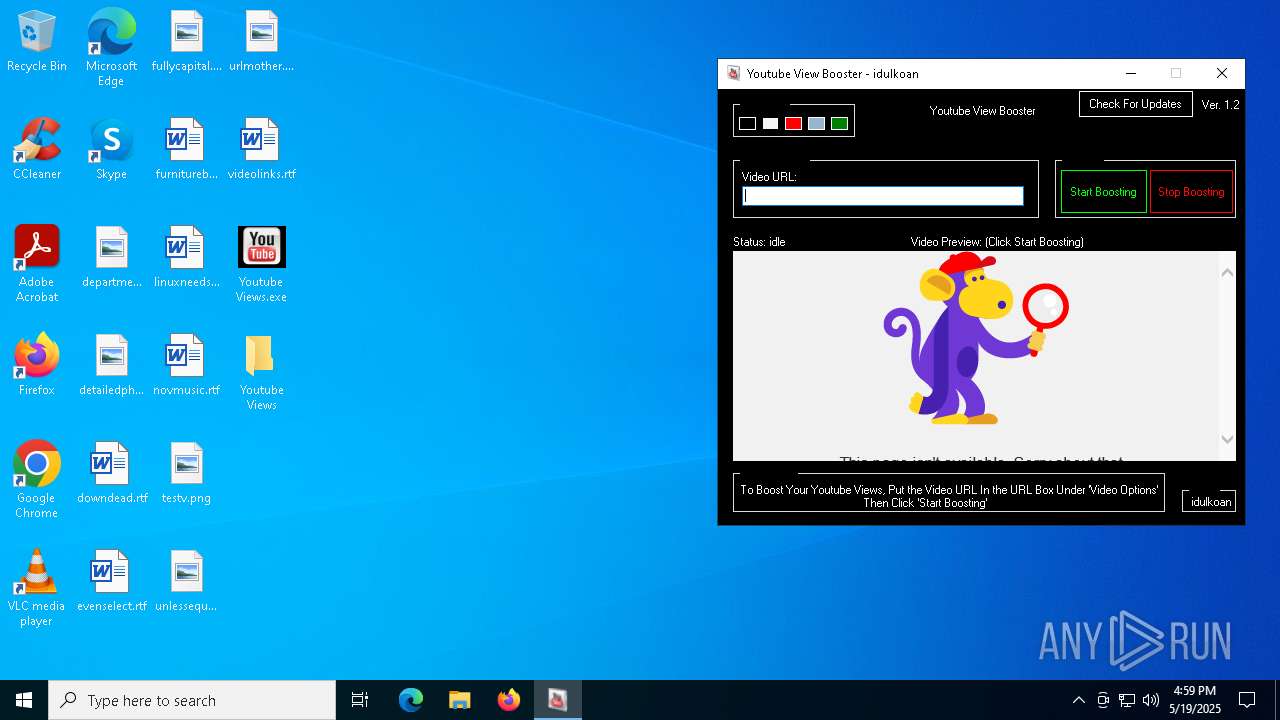
| Verdict: | Malicious activity |
| Threats: | AsyncRAT is a RAT that can monitor and remotely control infected systems. This malware was introduced on Github as a legitimate open-source remote administration software, but hackers use it for its many powerful malicious functions. |
| Analysis date: | May 19, 2025, 16:58:51 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows, 3 sections |
| MD5: | 6382CDB3E275813DCD531E3BCF12A399 |
| SHA1: | 1C64C3F30DC0C271CE018B6884DB052CCBB26F15 |
| SHA256: | 71B5601D4F830B0D0FEB4C4A2AD2E676239C26AD68474A9CC3C8C277401189D3 |
| SSDEEP: | 3072:VRpJ0tdIhQw/JOSdJh5p5eL9FVqHqLsRdhA6zb6abQJWaYPASrZc9aEGYvXOa/5q:VDJ0fI2u3vp5eLLSVqu4S1cw5YN/5 |
MALICIOUS
ASYNCRAT has been detected (MUTEX)
- Muwldtrpxmp.exe (PID: 7604)
- dllhost.exe (PID: 5588)
Changes the autorun value in the registry
- Muwldtrpxmp.exe (PID: 7604)
ASYNCRAT has been detected (YARA)
- dllhost.exe (PID: 5588)
SUSPICIOUS
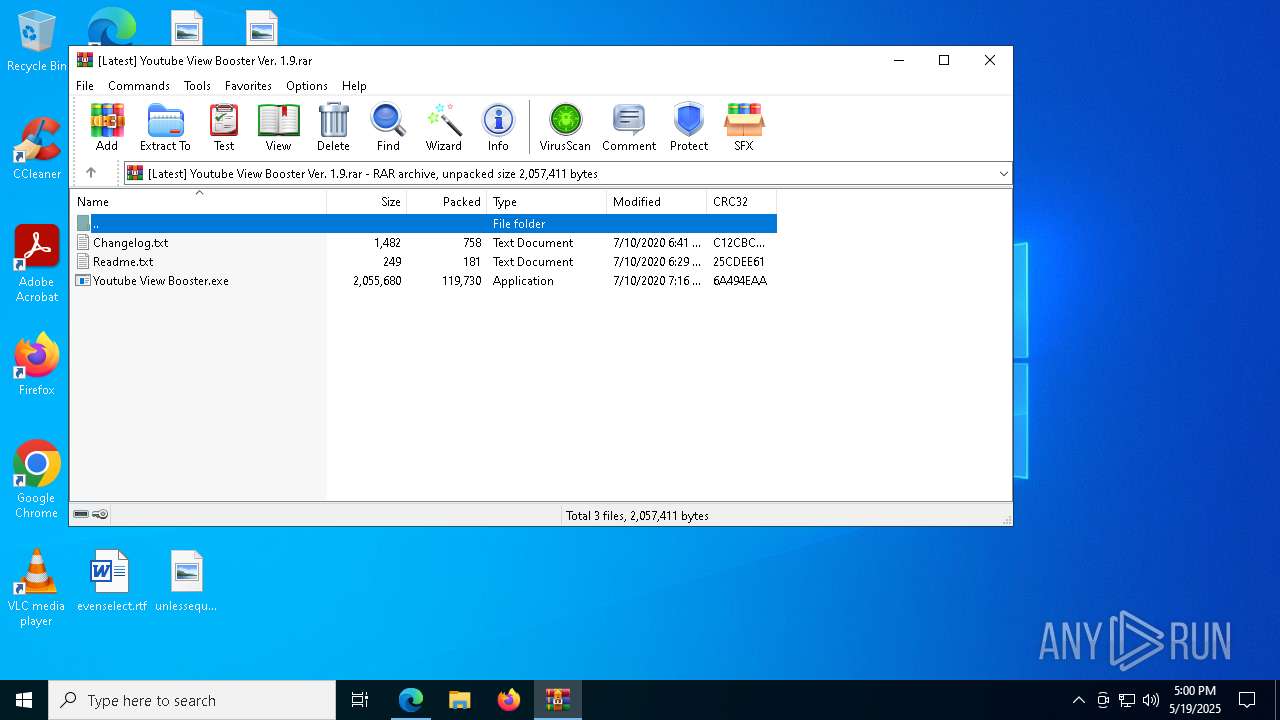
Executable content was dropped or overwritten
- Youtube Views.exe (PID: 7528)
- Muwldtrpxmp.exe (PID: 7604)
Reads the date of Windows installation
- Youtube Views.exe (PID: 7528)
Reads security settings of Internet Explorer
- Youtube Views.exe (PID: 7528)
- Lrvdezvd.exe (PID: 7596)
Reads Microsoft Outlook installation path
- Lrvdezvd.exe (PID: 7596)
Starts a Microsoft application from unusual location
- Muwldtrpxmp.exe (PID: 7604)
The process creates files with name similar to system file names
- Muwldtrpxmp.exe (PID: 7604)
Starts CMD.EXE for commands execution
- Muwldtrpxmp.exe (PID: 7604)
Executing commands from a ".bat" file
- Muwldtrpxmp.exe (PID: 7604)
Uses TIMEOUT.EXE to delay execution
- cmd.exe (PID: 5072)
The executable file from the user directory is run by the CMD process
- dllhost.exe (PID: 5588)
Reads Internet Explorer settings
- Lrvdezvd.exe (PID: 7596)
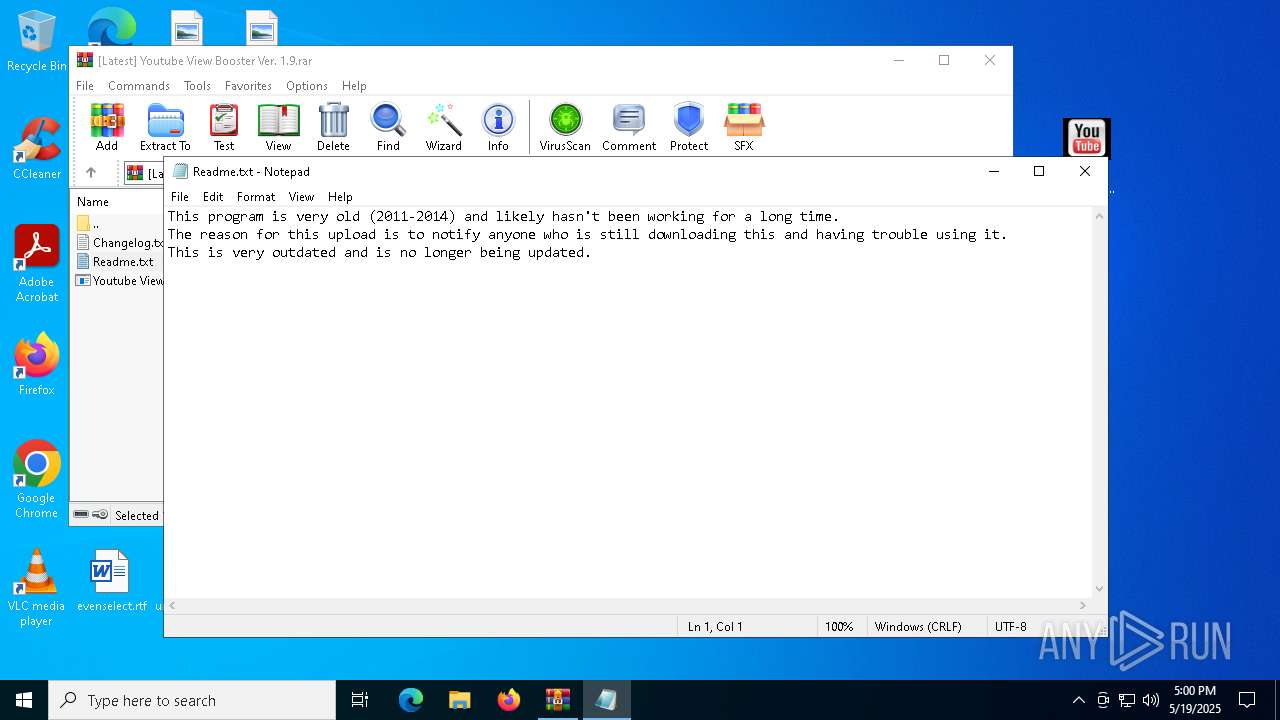
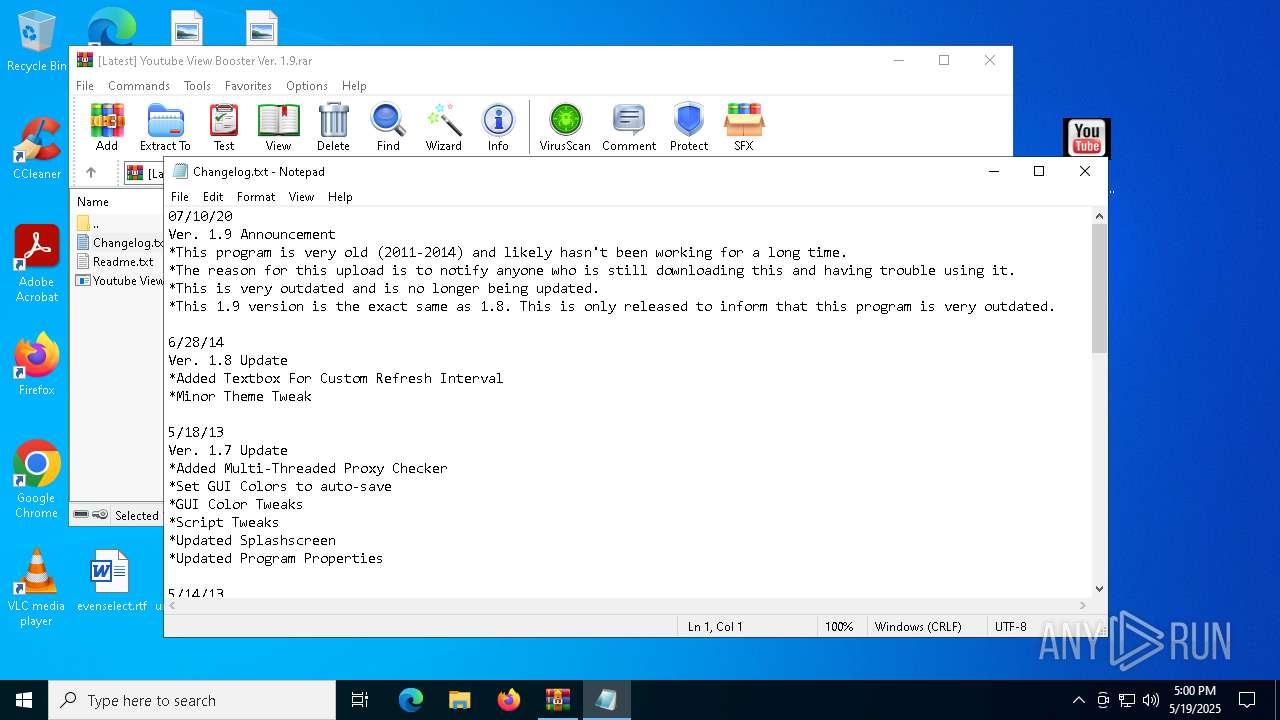
Start notepad (likely ransomware note)
- WinRAR.exe (PID: 1324)
Connects to unusual port
- dllhost.exe (PID: 5588)
INFO
Reads the machine GUID from the registry
- Youtube Views.exe (PID: 7528)
- Lrvdezvd.exe (PID: 7596)
- Muwldtrpxmp.exe (PID: 7604)
- dllhost.exe (PID: 5588)
Reads the computer name
- Youtube Views.exe (PID: 7528)
- Muwldtrpxmp.exe (PID: 7604)
- Lrvdezvd.exe (PID: 7596)
- dllhost.exe (PID: 5588)
- identity_helper.exe (PID: 7712)
Create files in a temporary directory
- Youtube Views.exe (PID: 7528)
- Muwldtrpxmp.exe (PID: 7604)
Checks supported languages
- Muwldtrpxmp.exe (PID: 7604)
- Youtube Views.exe (PID: 7528)
- Lrvdezvd.exe (PID: 7596)
- dllhost.exe (PID: 5588)
- identity_helper.exe (PID: 7712)
Process checks computer location settings
- Youtube Views.exe (PID: 7528)
Reads the software policy settings
- Lrvdezvd.exe (PID: 7596)
Checks proxy server information
- Lrvdezvd.exe (PID: 7596)
Creates files or folders in the user directory
- Lrvdezvd.exe (PID: 7596)
- Muwldtrpxmp.exe (PID: 7604)
Application launched itself
- msedge.exe (PID: 6808)
- msedge.exe (PID: 7208)
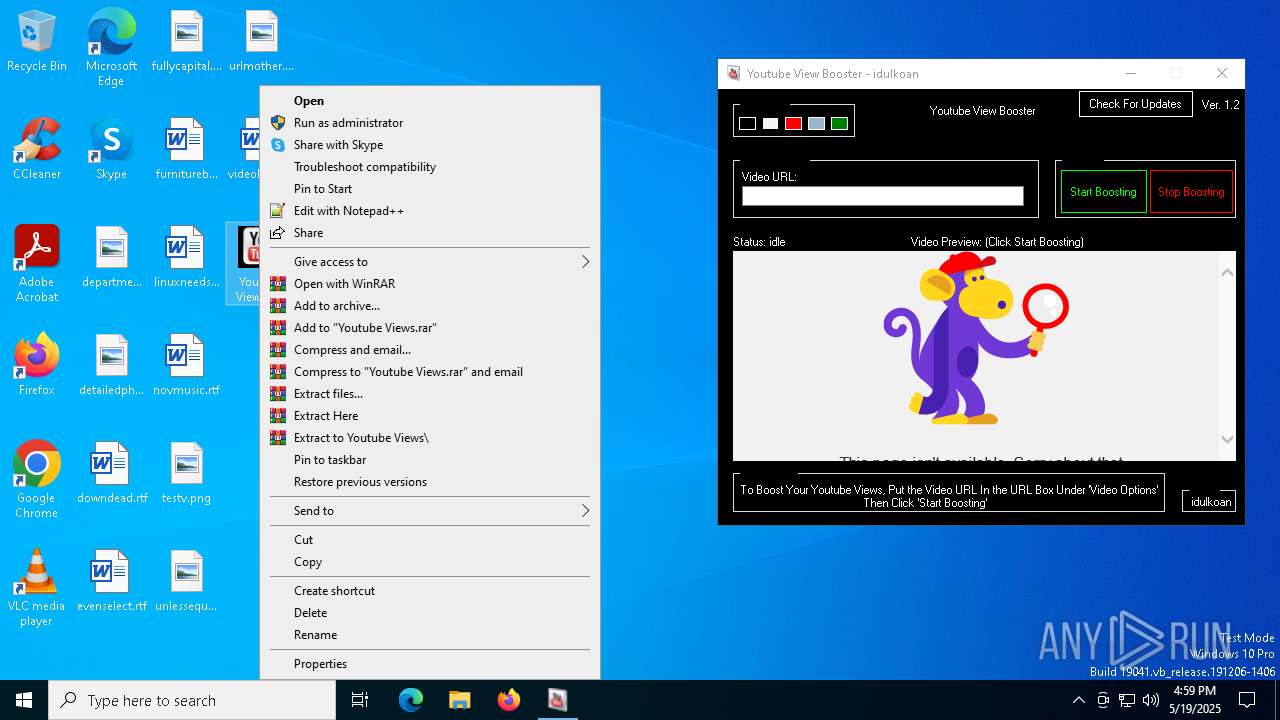
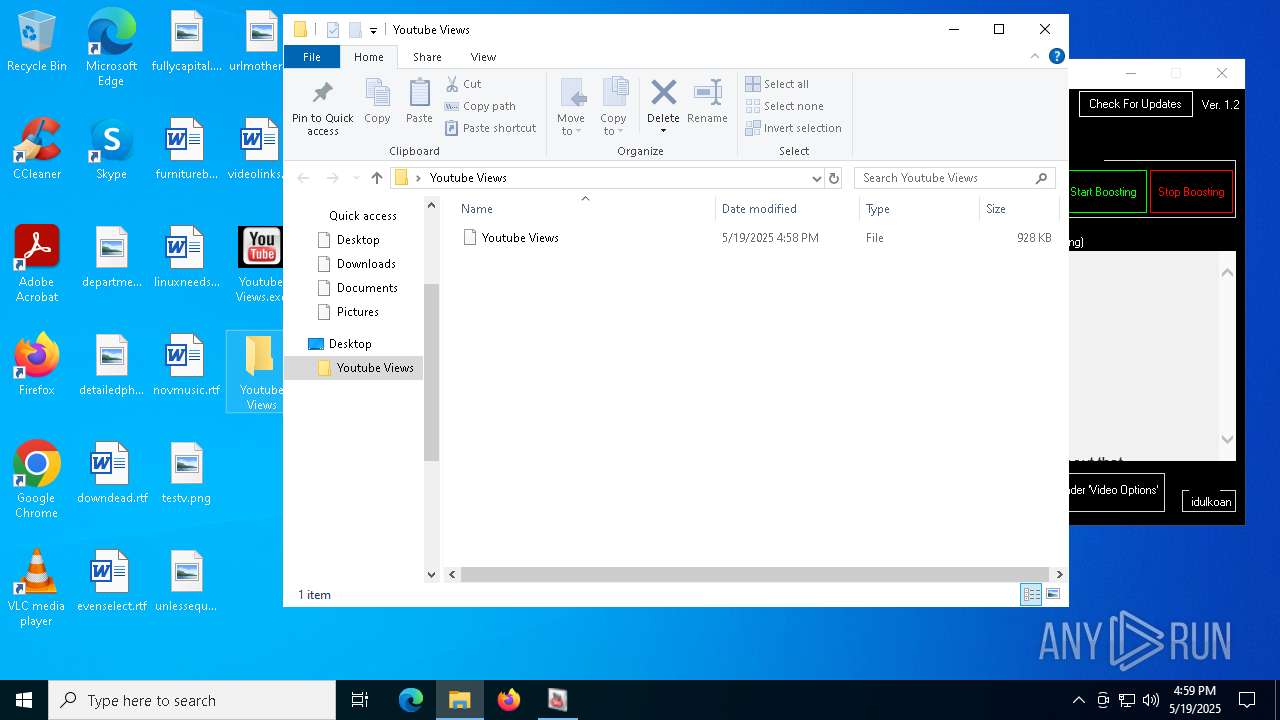
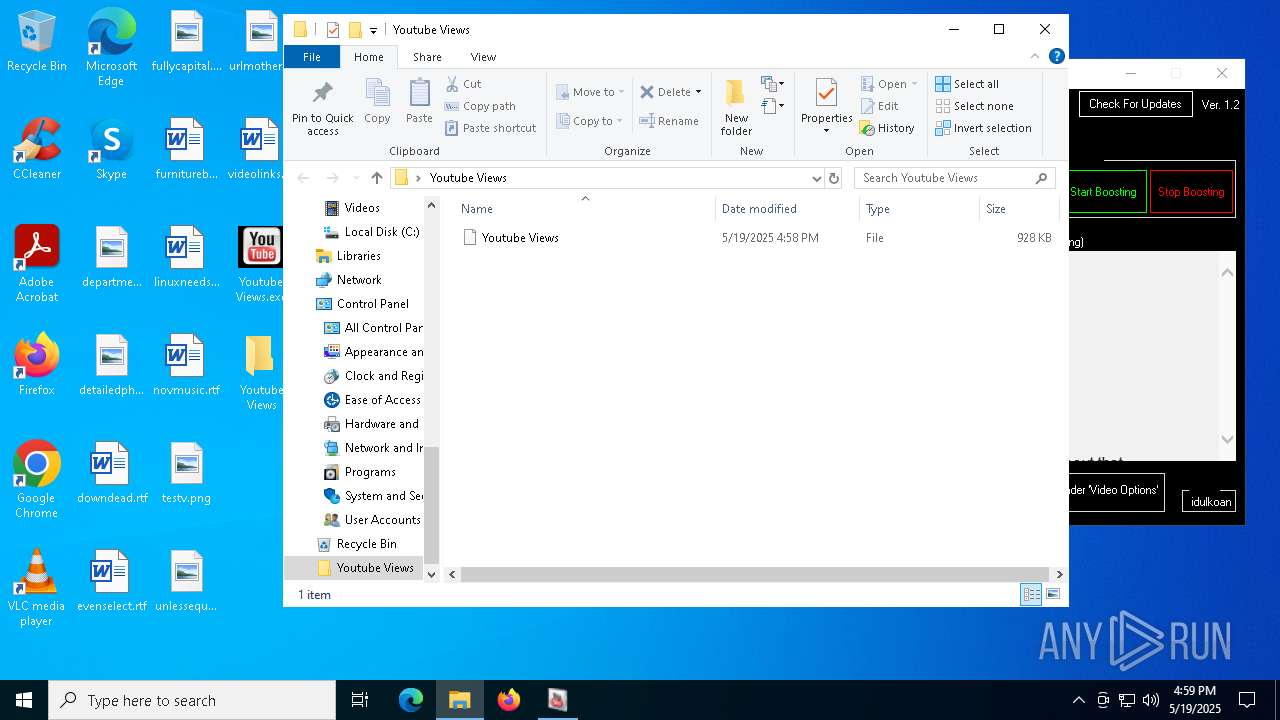
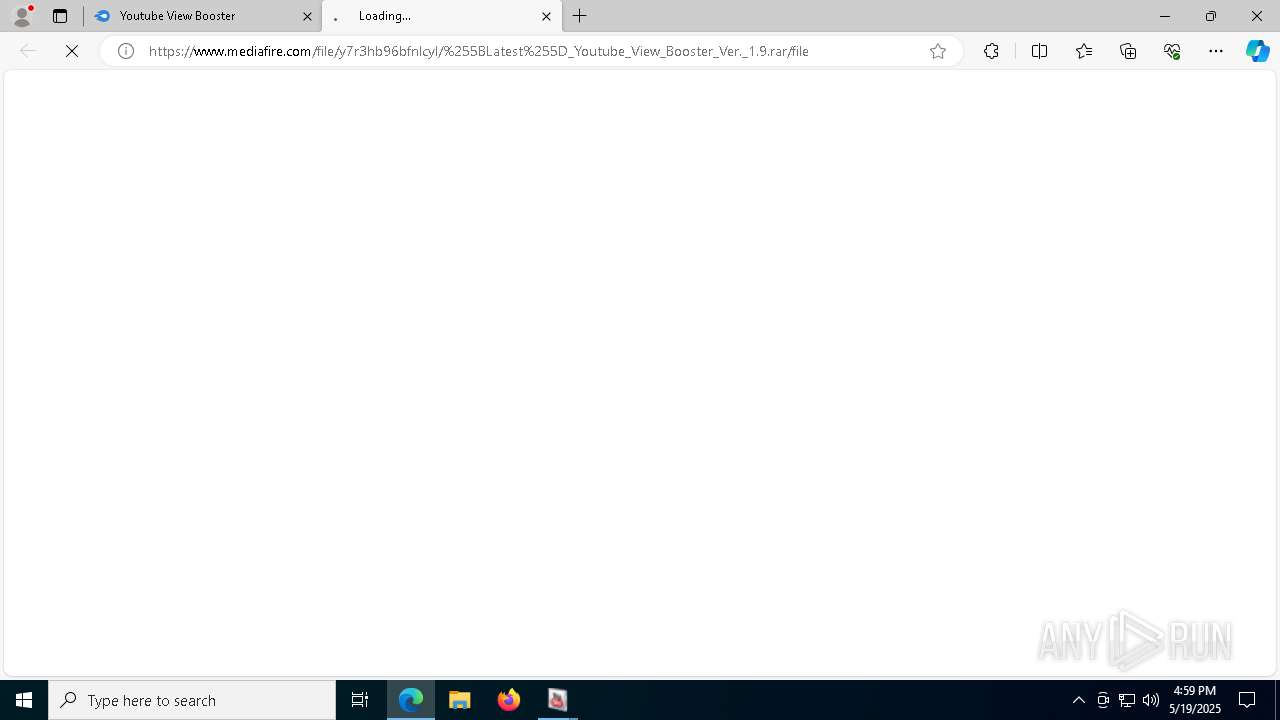
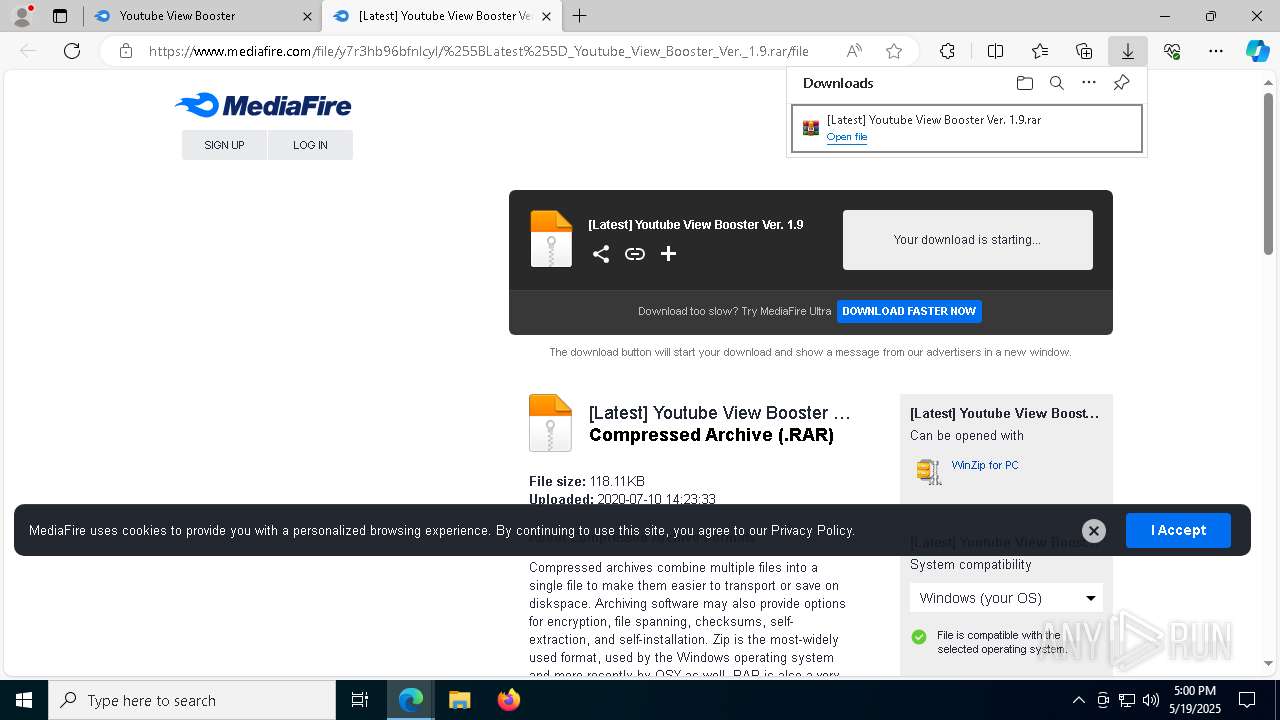
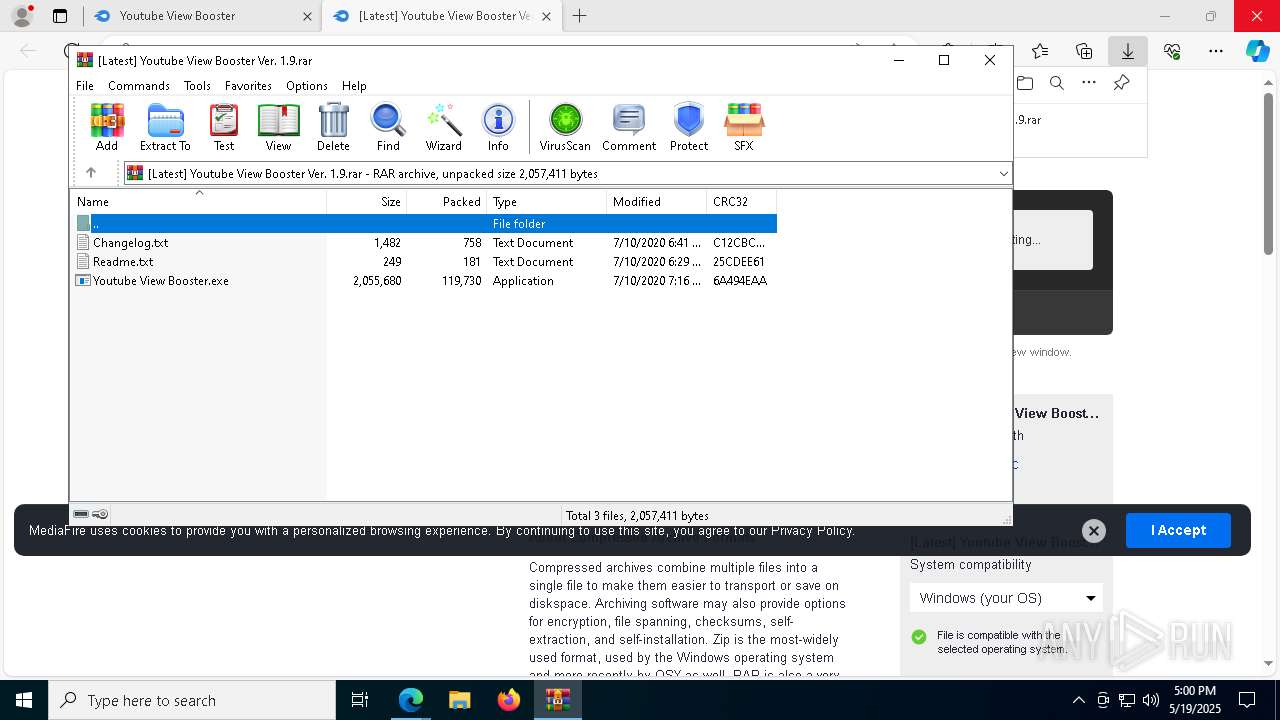
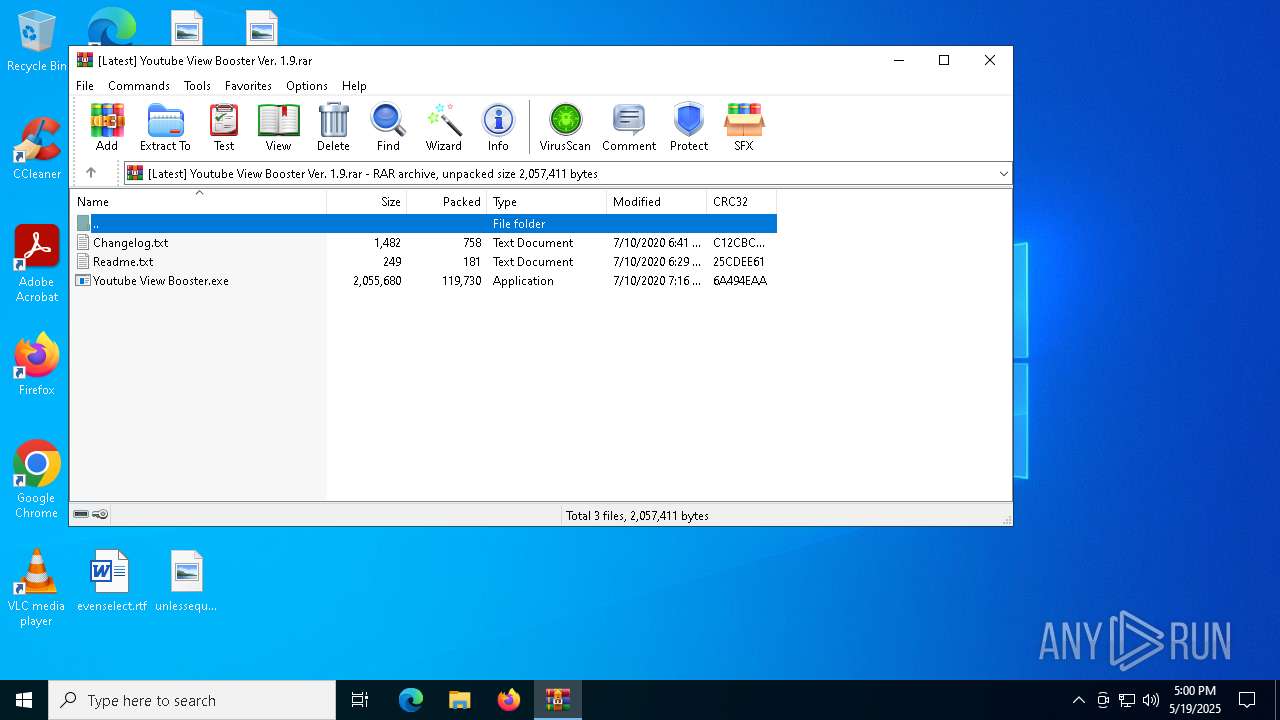
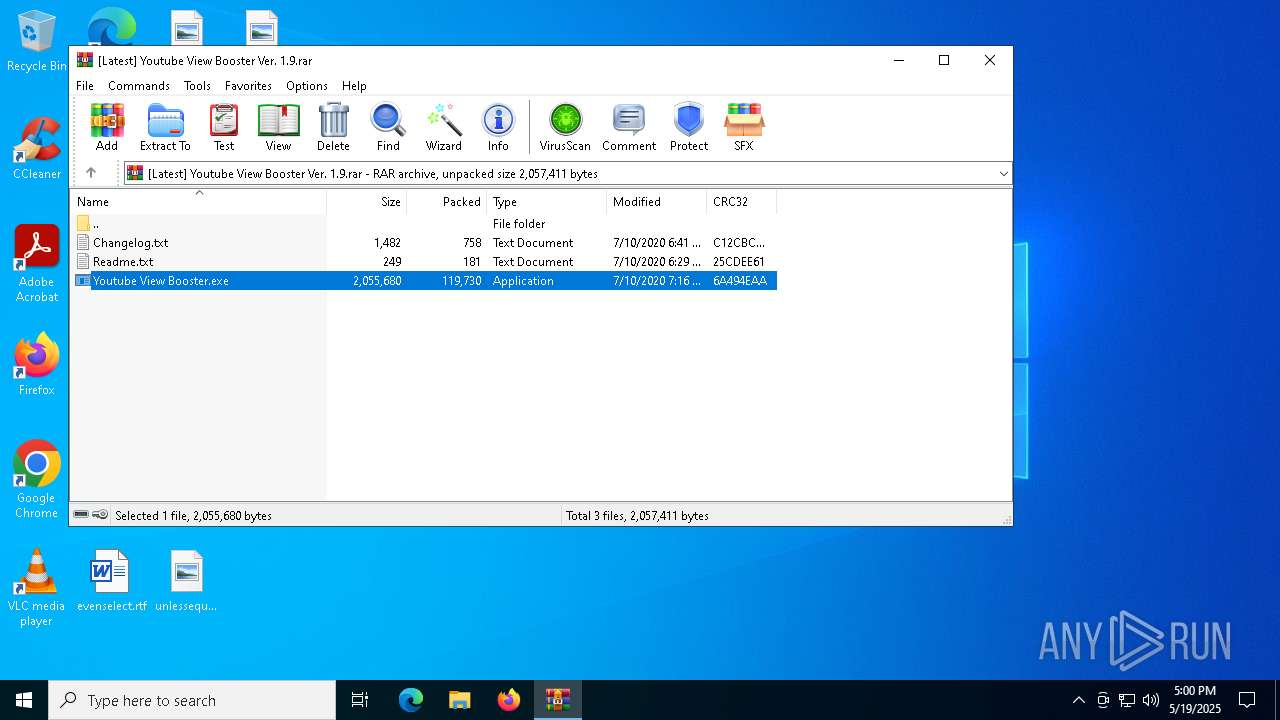
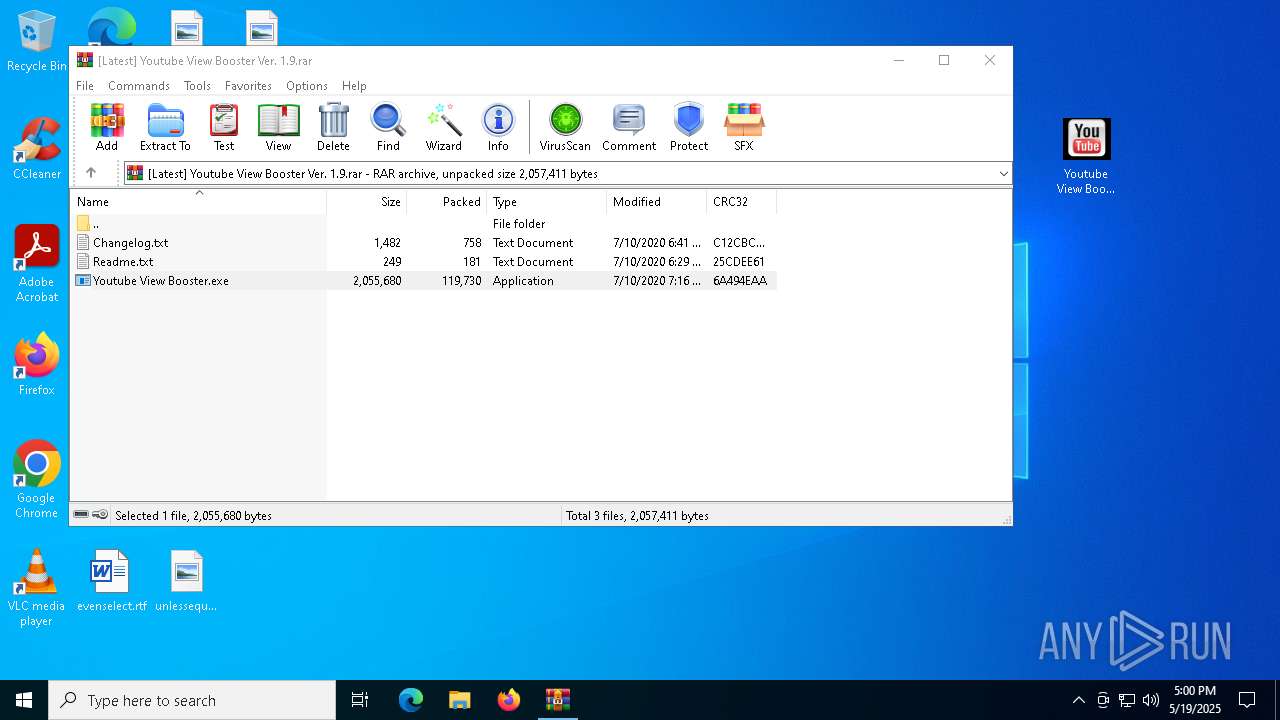
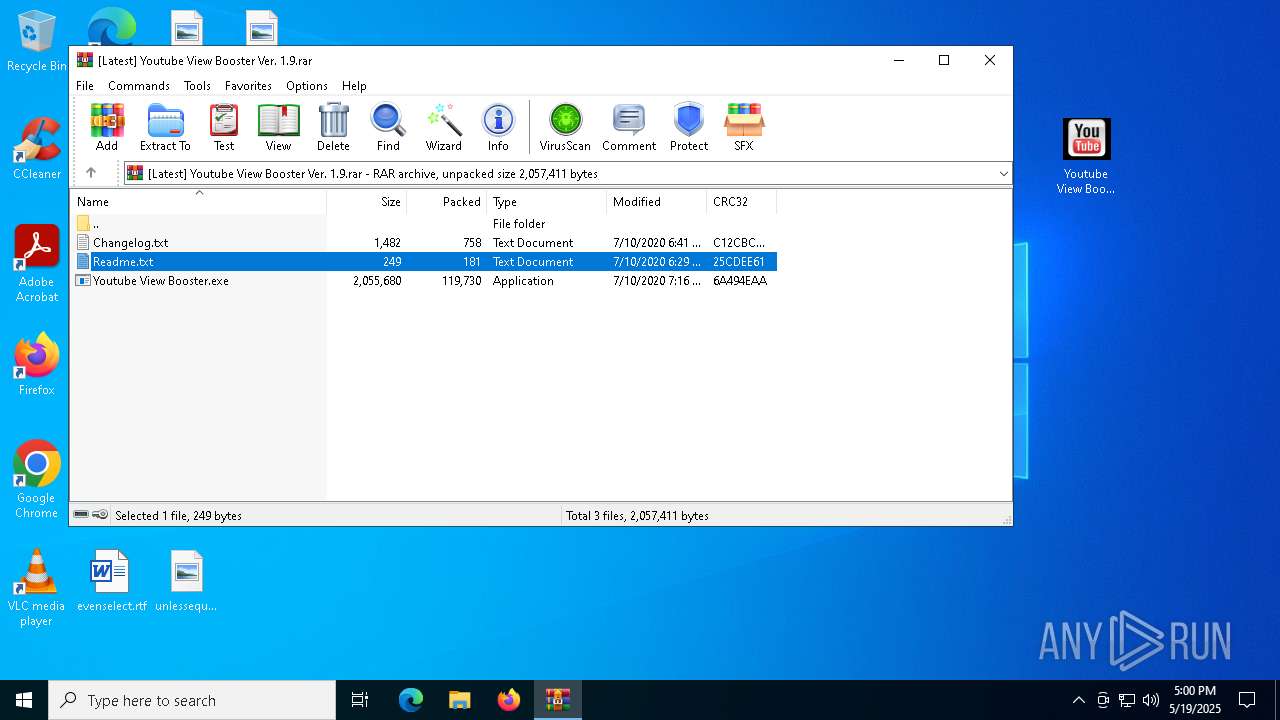
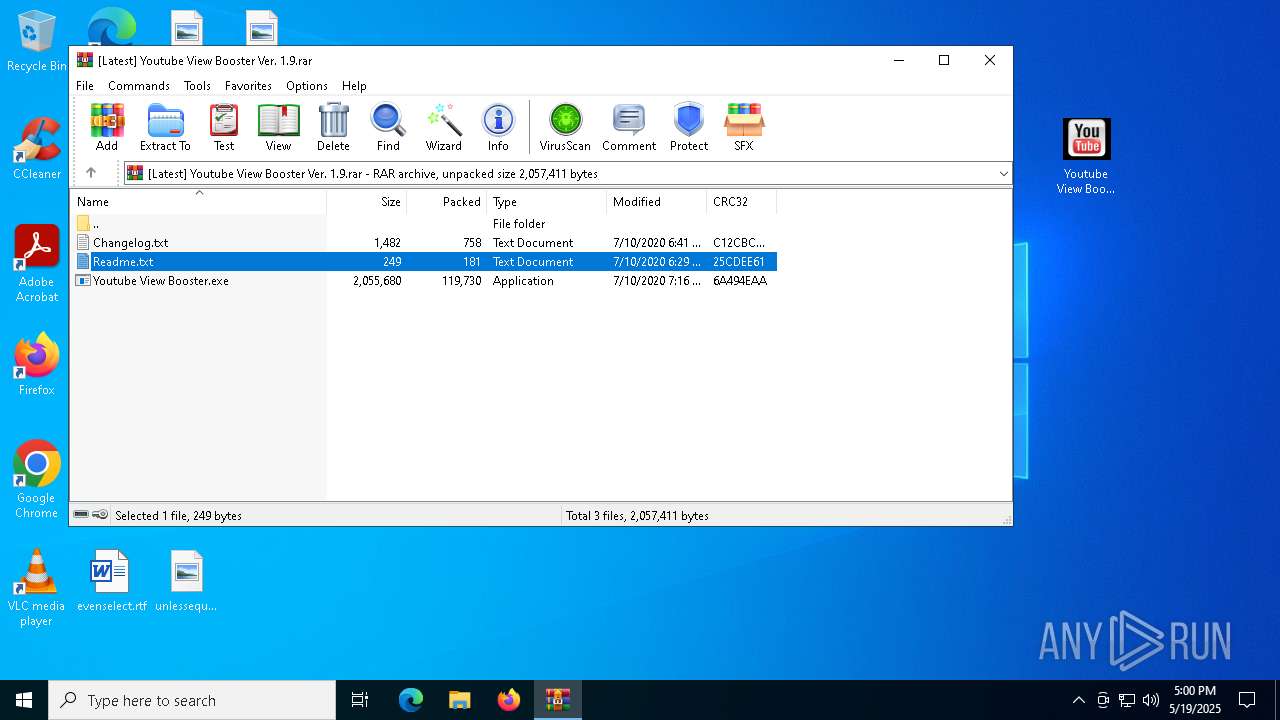
Executable content was dropped or overwritten
- WinRAR.exe (PID: 1324)
- WinRAR.exe (PID: 2244)
Reads Environment values
- identity_helper.exe (PID: 7712)
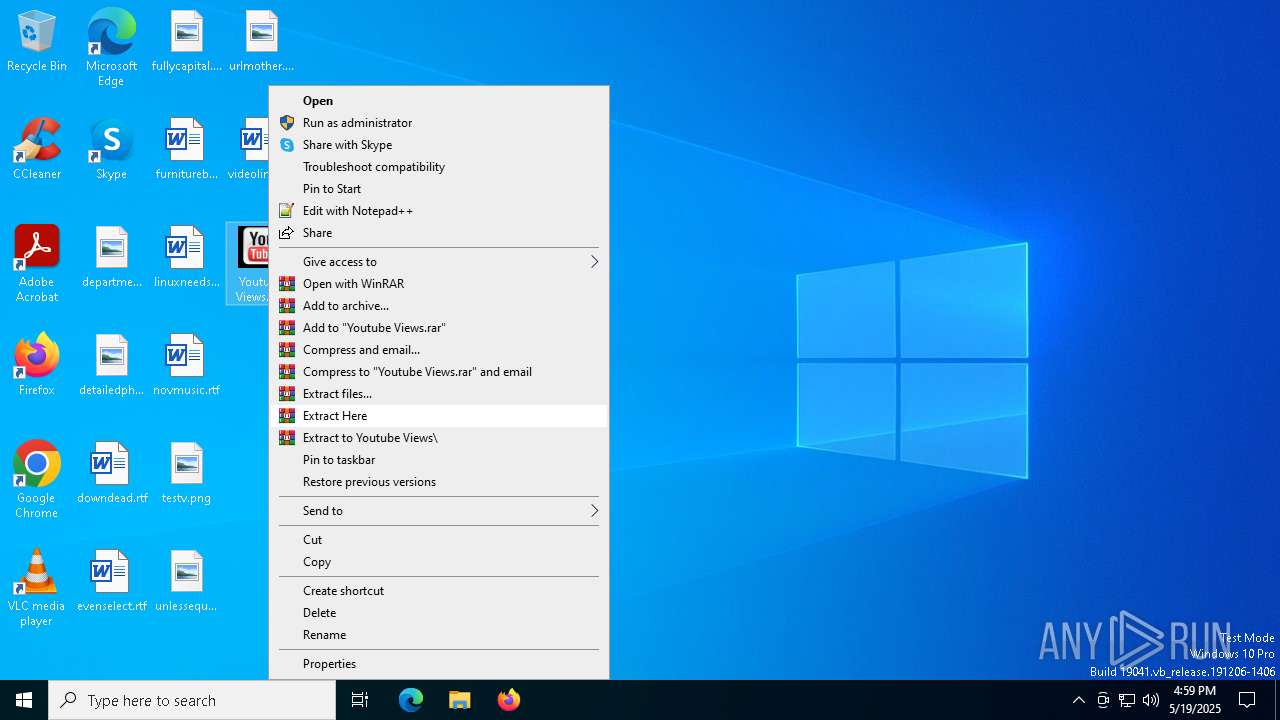
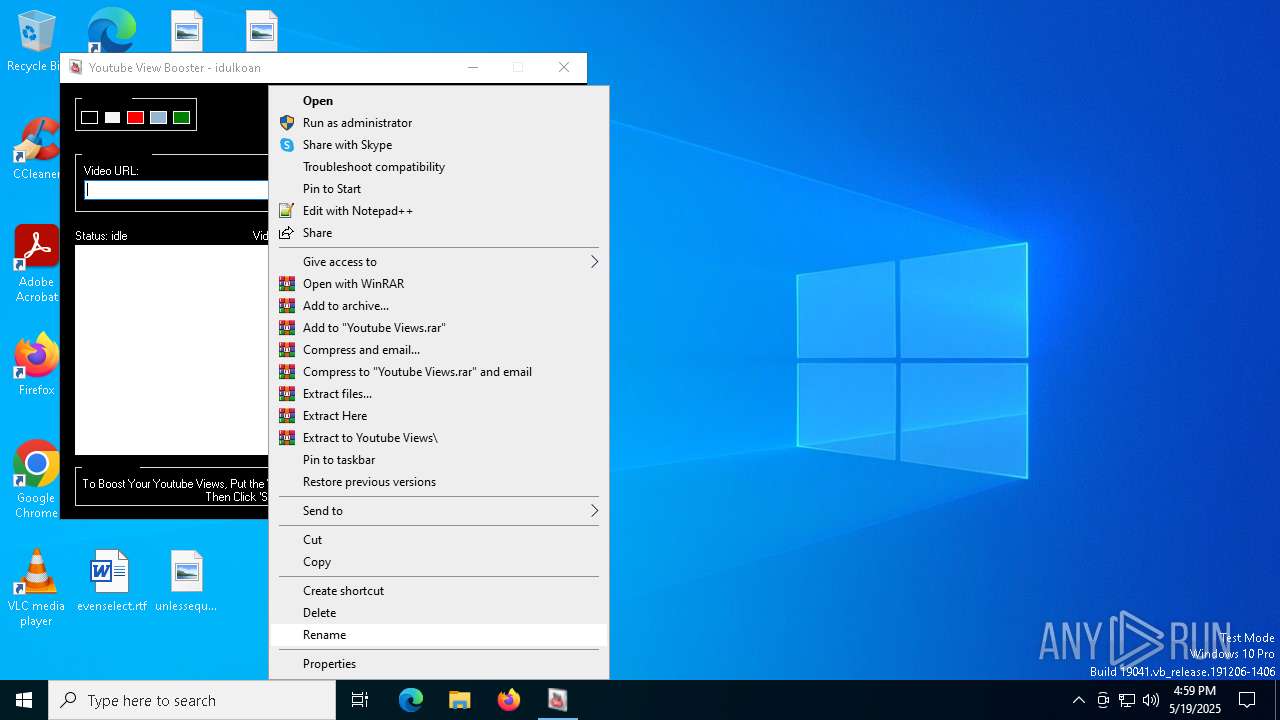
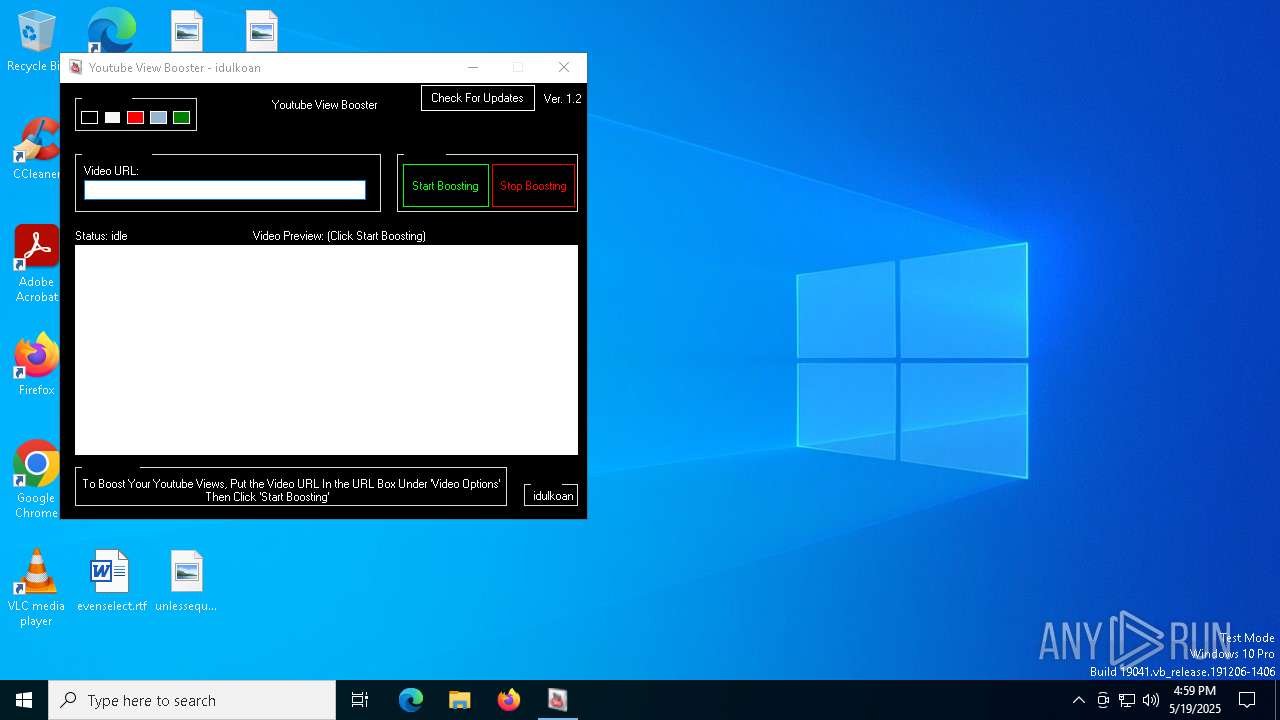
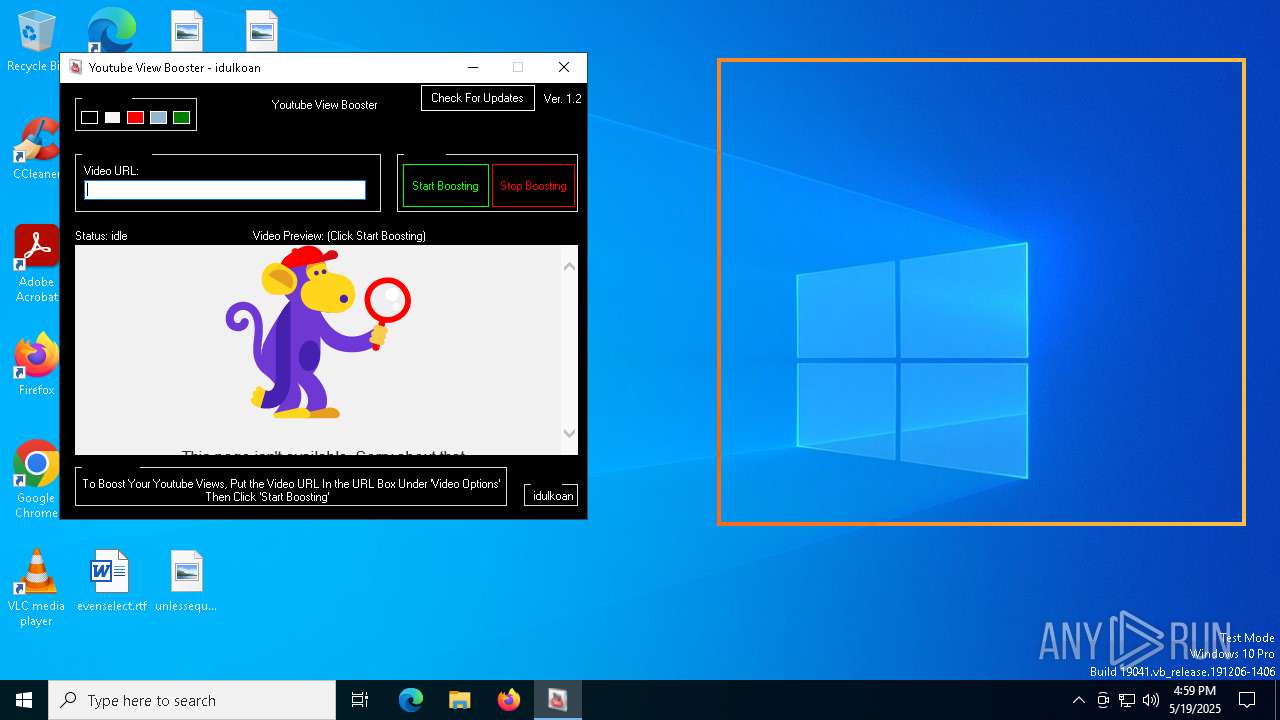
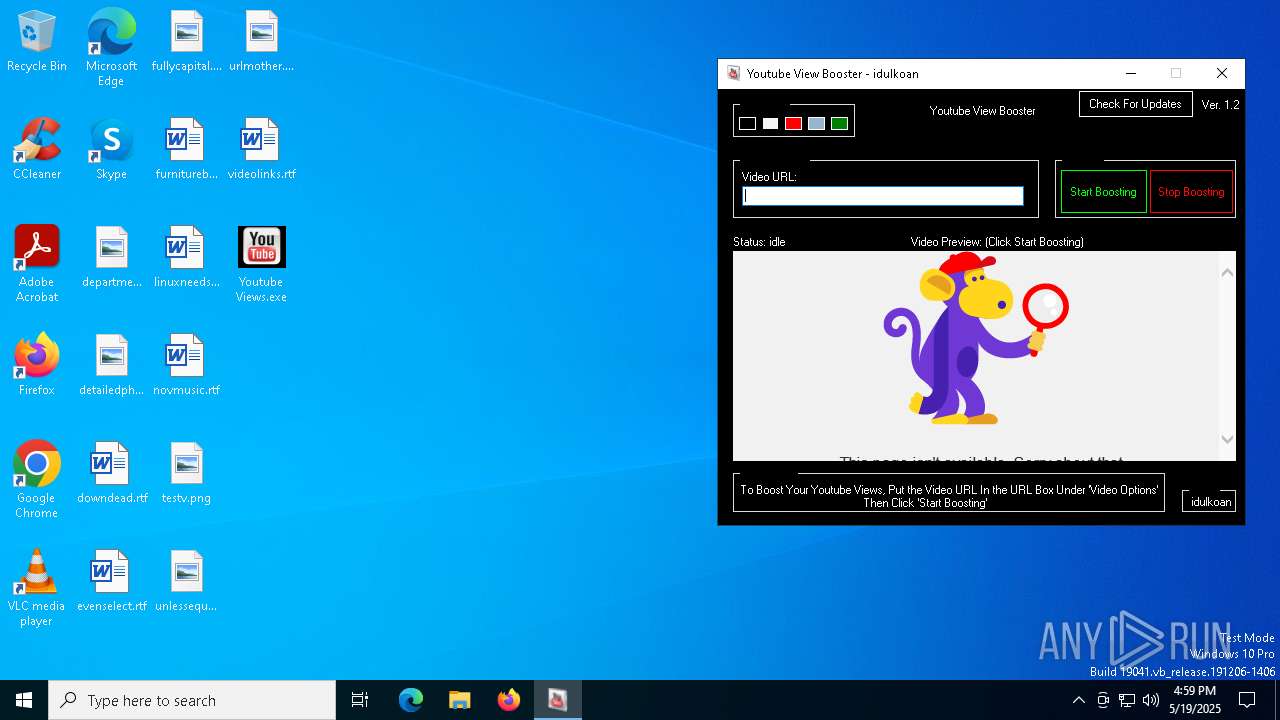
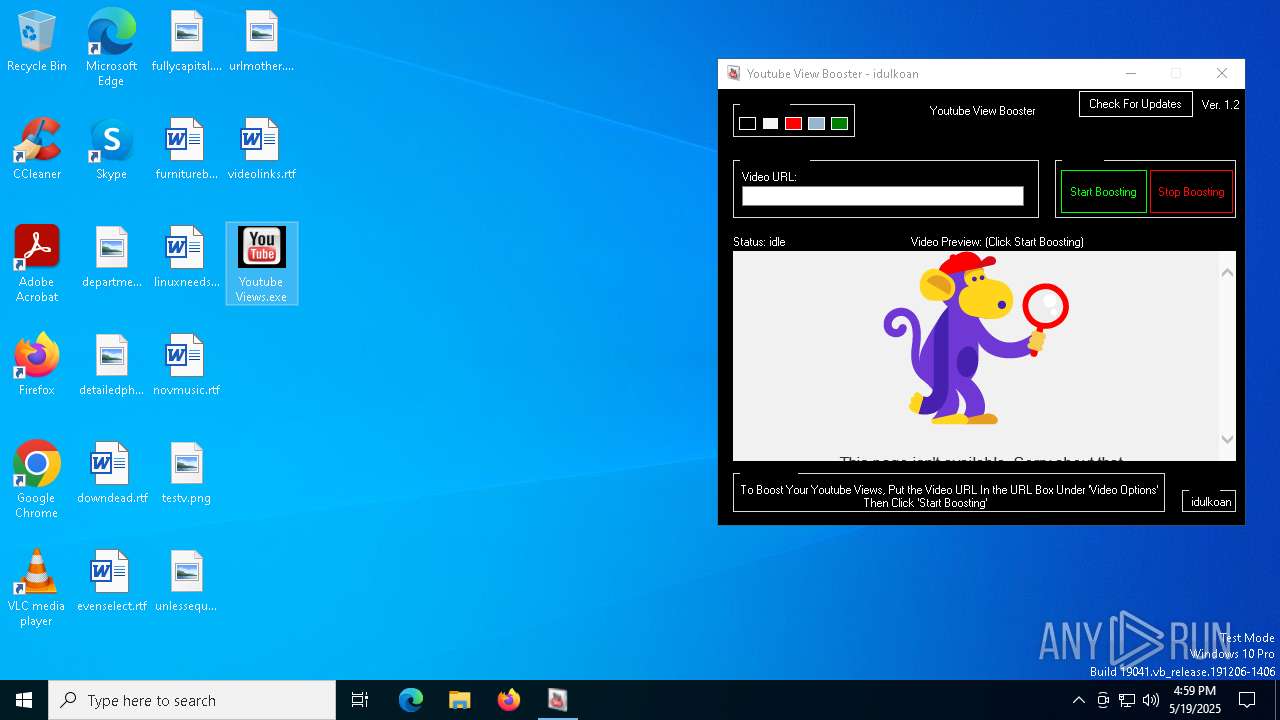
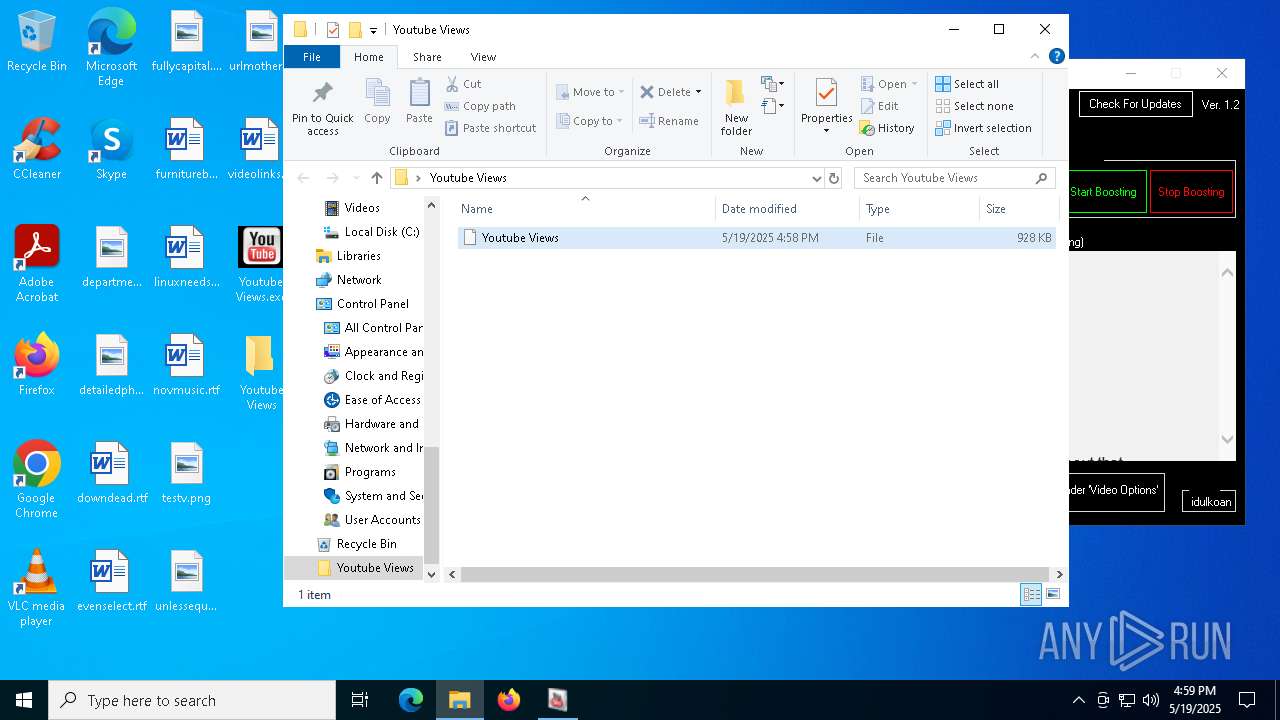
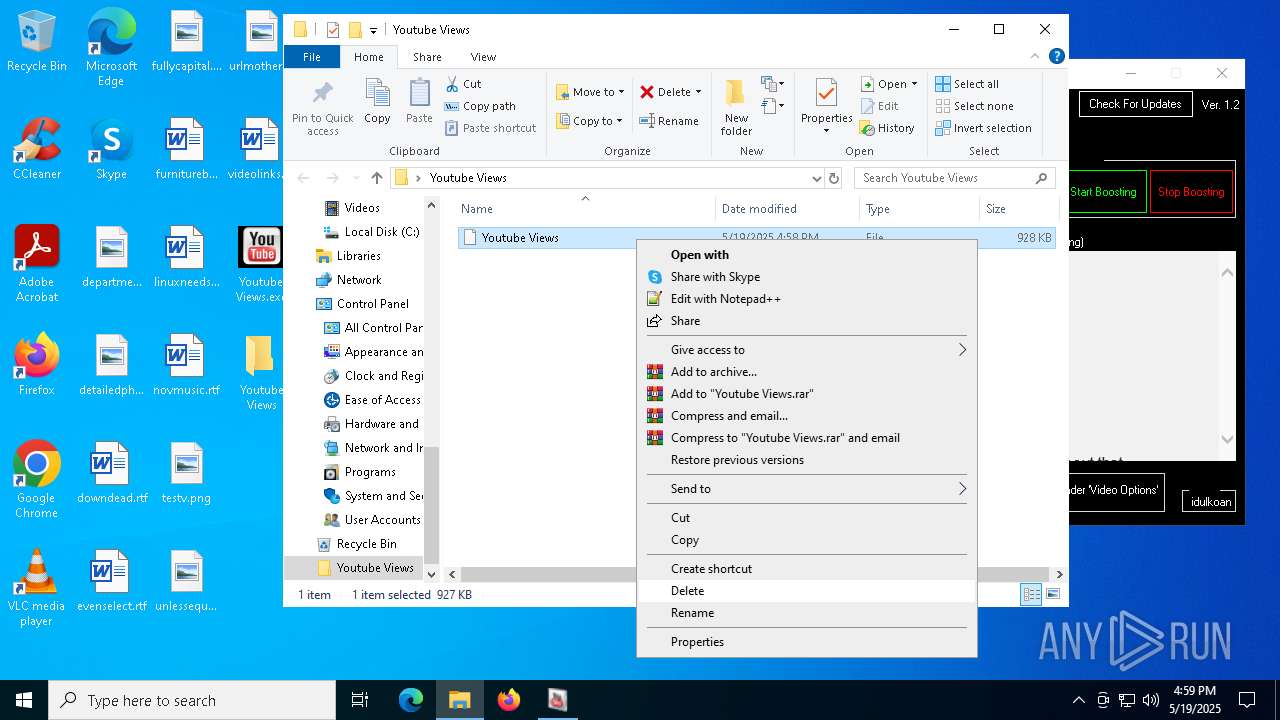
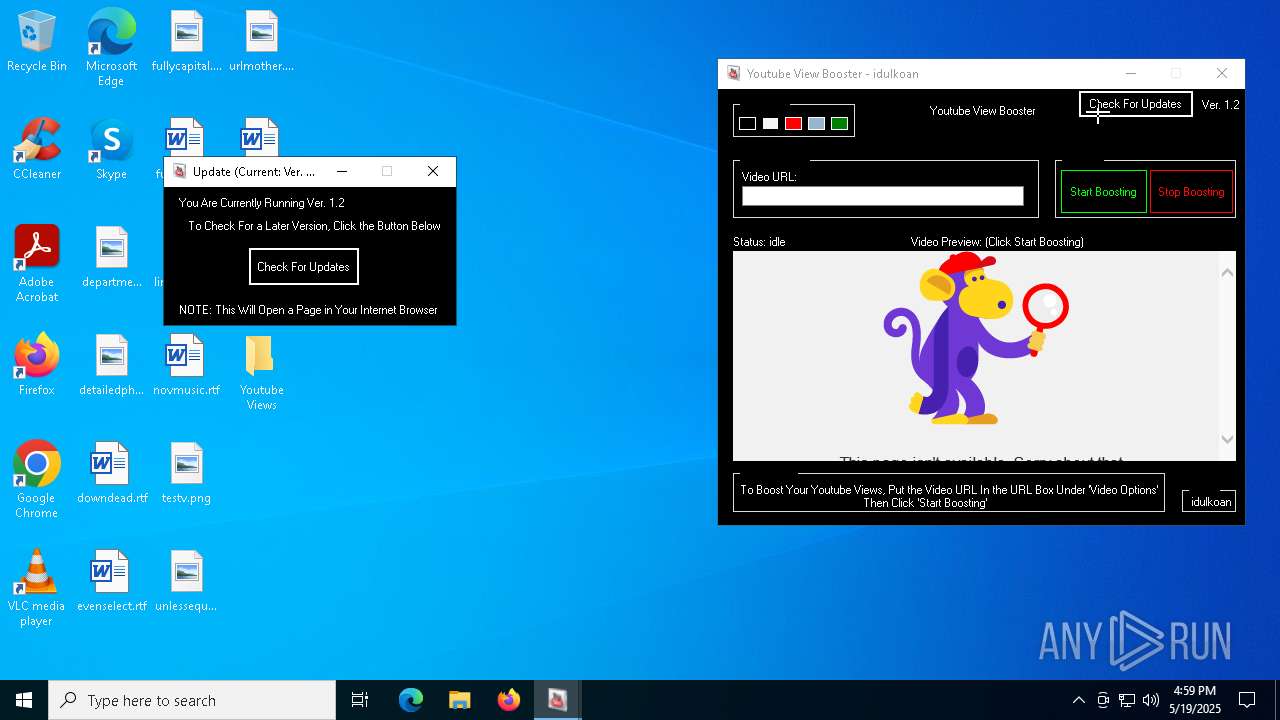
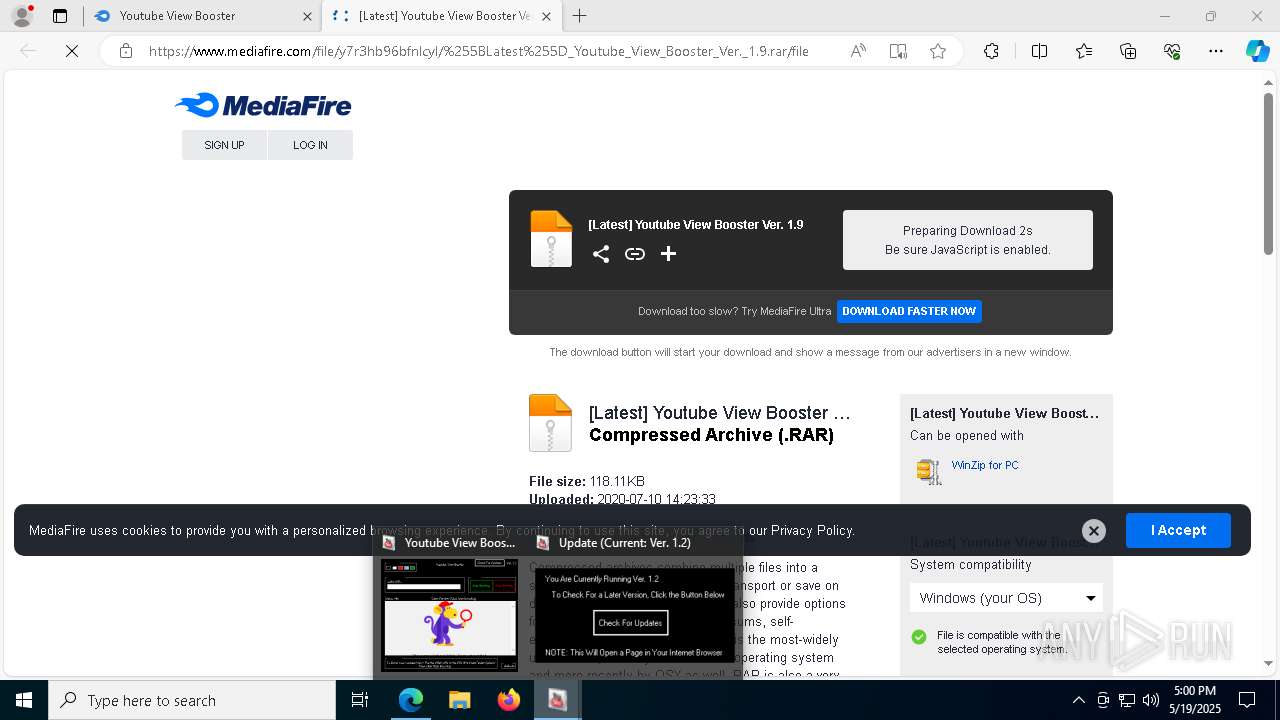
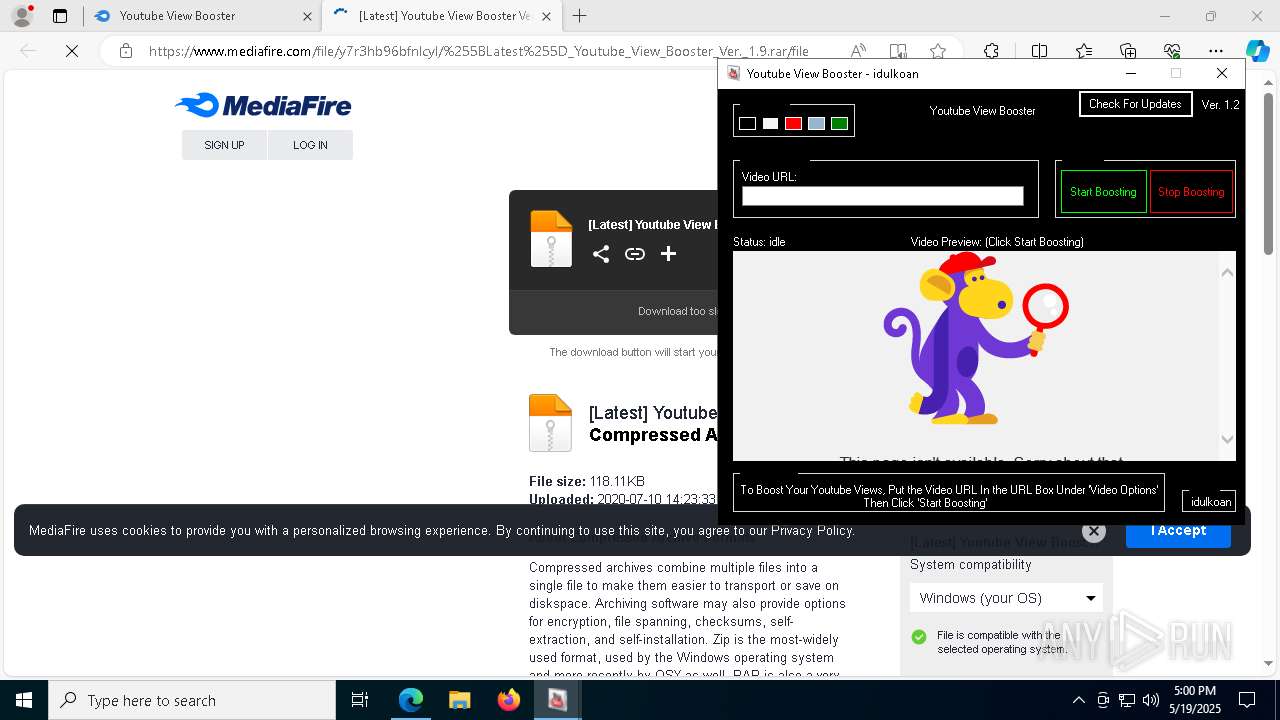
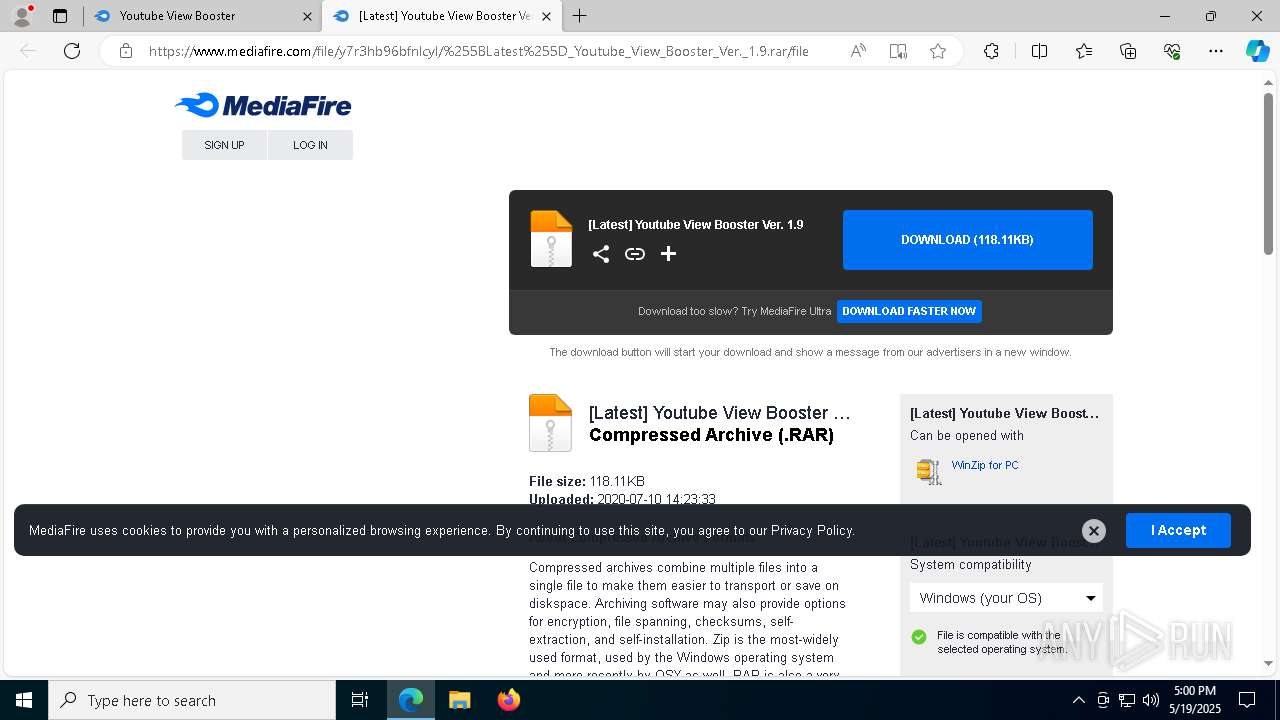
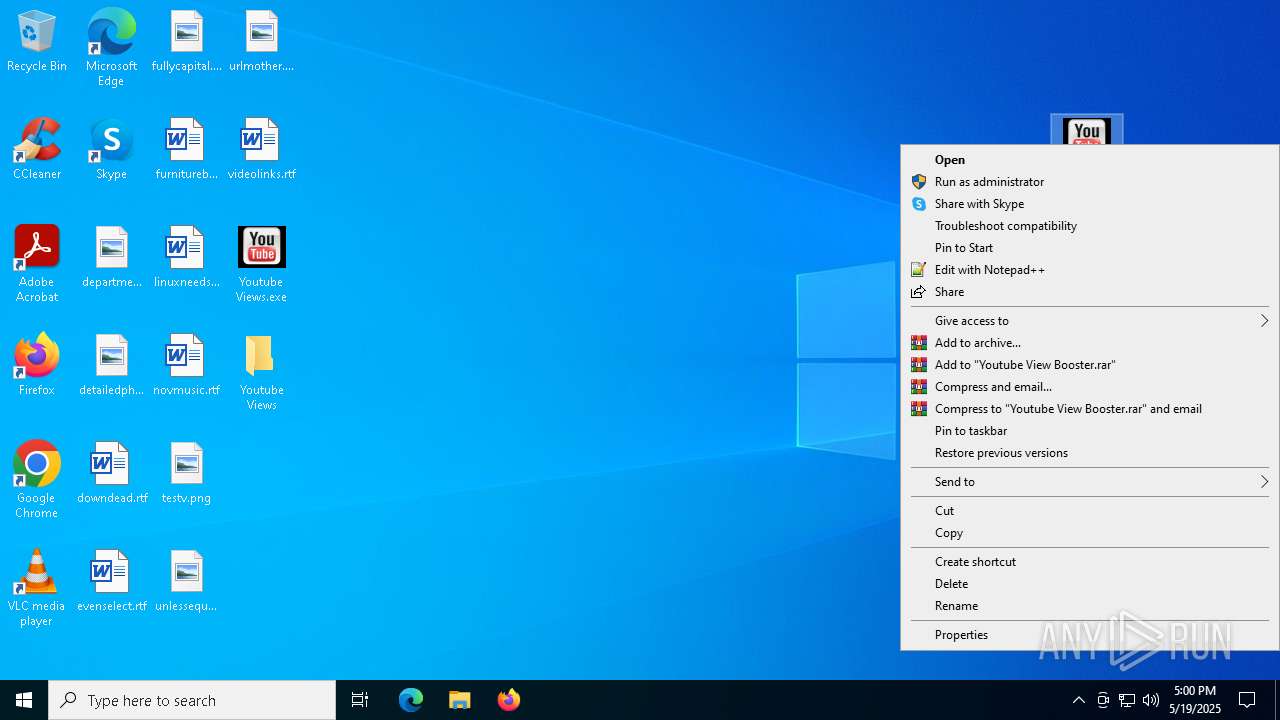
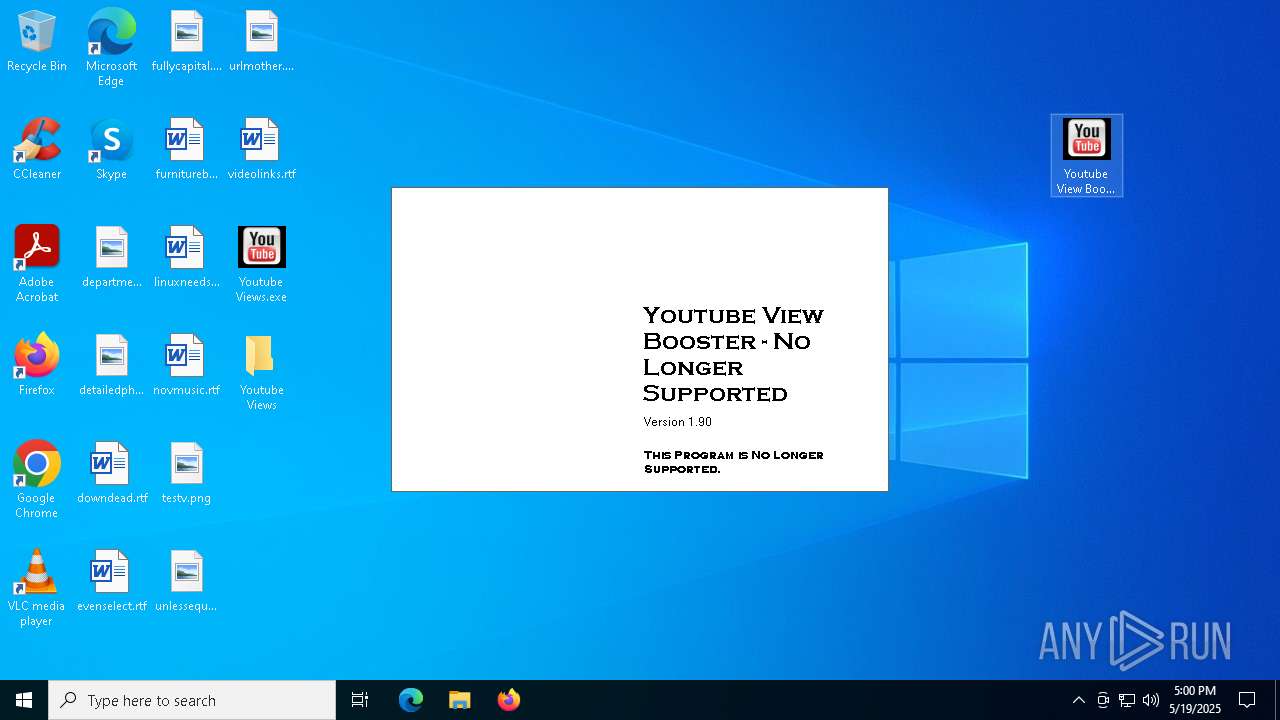
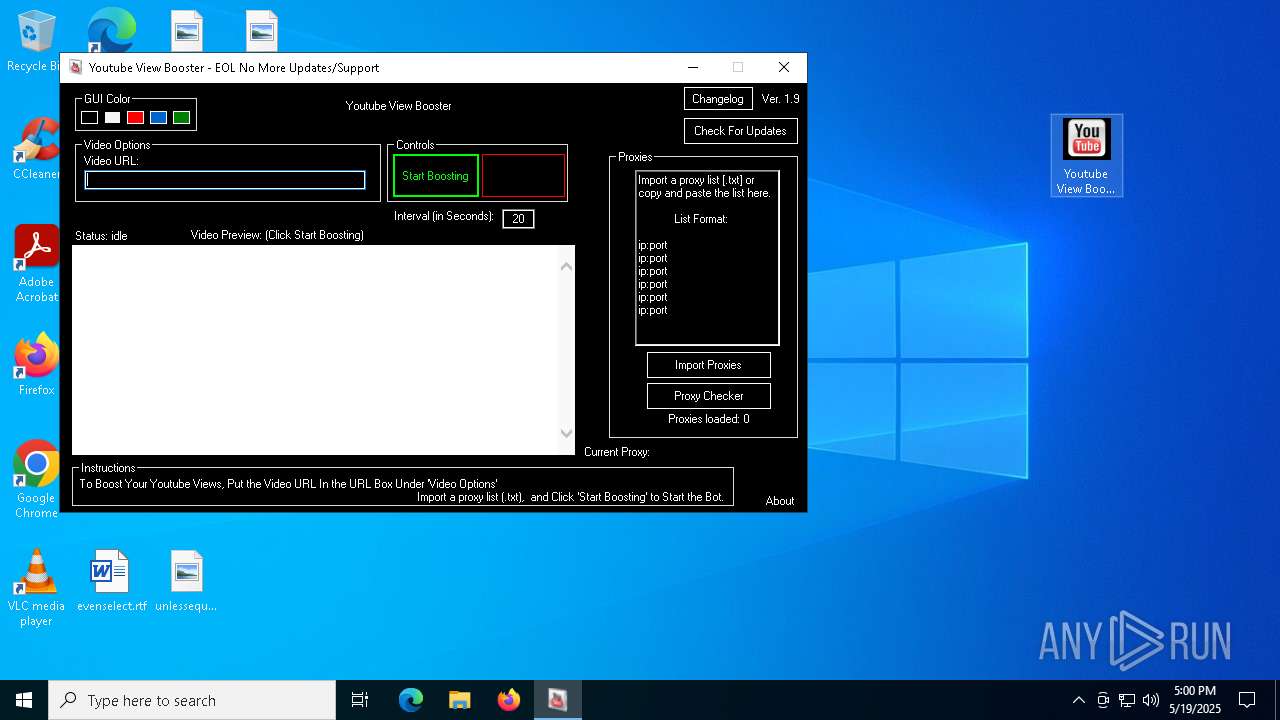
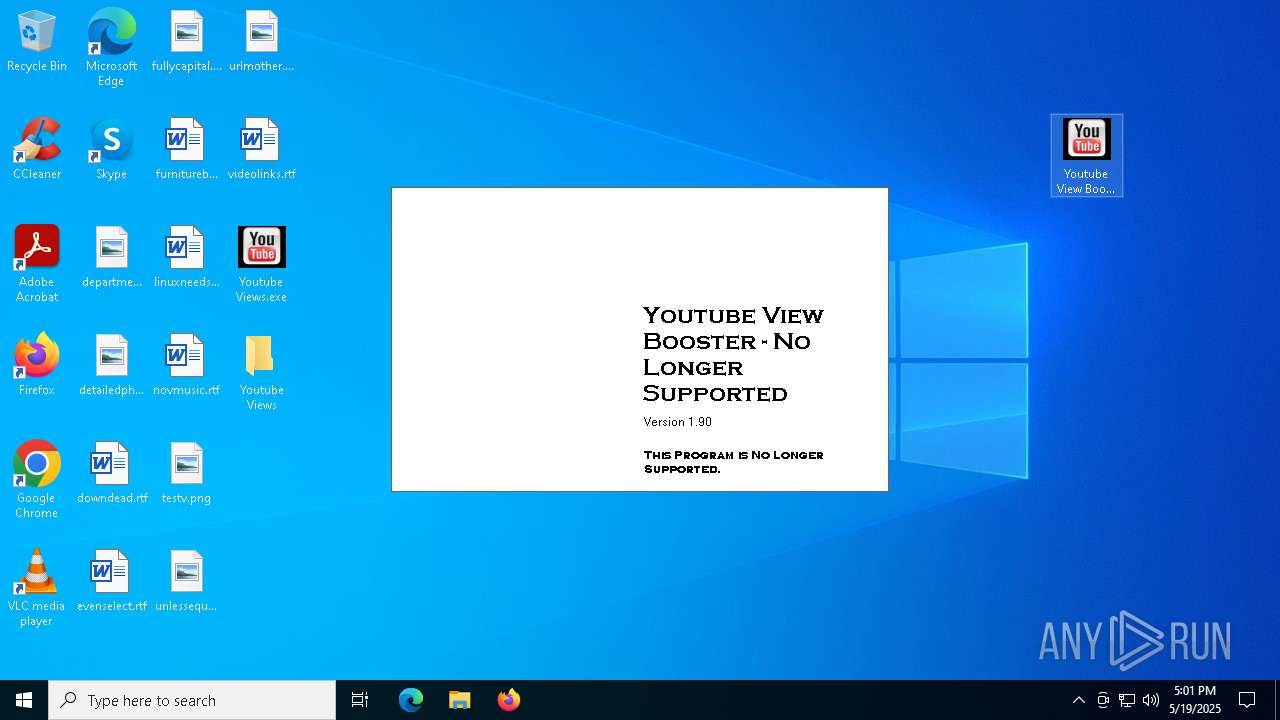
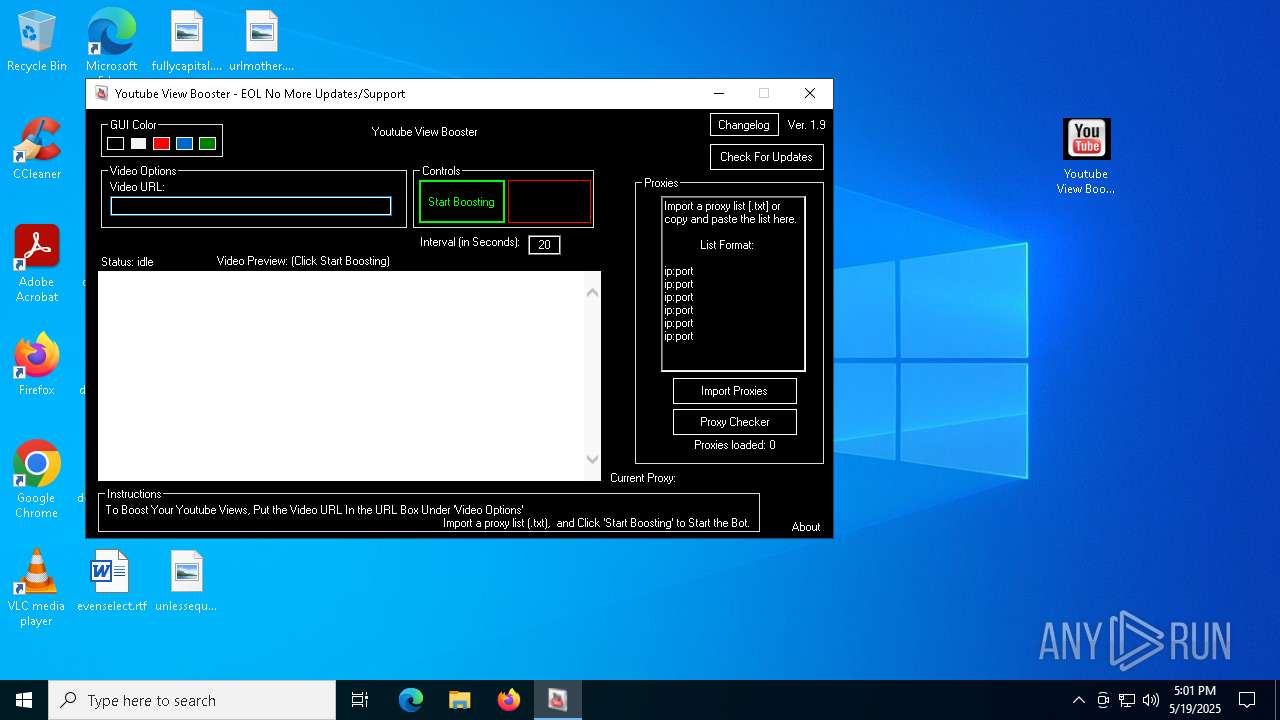
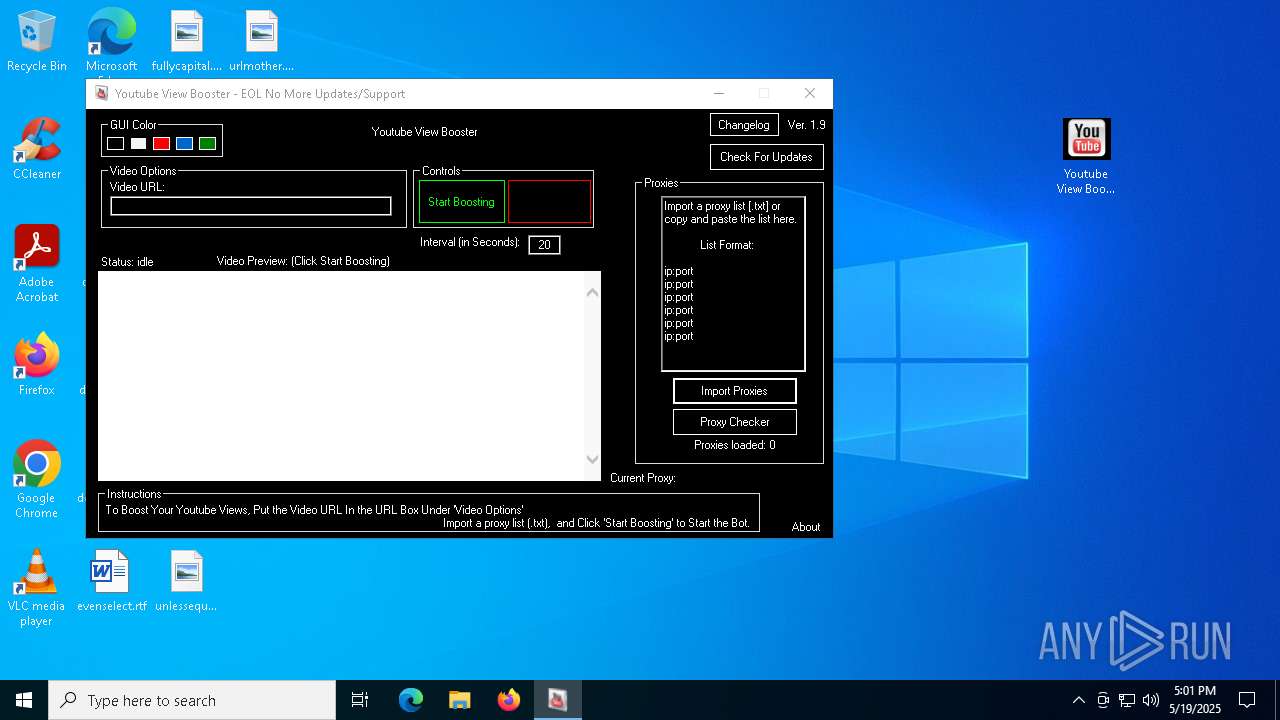
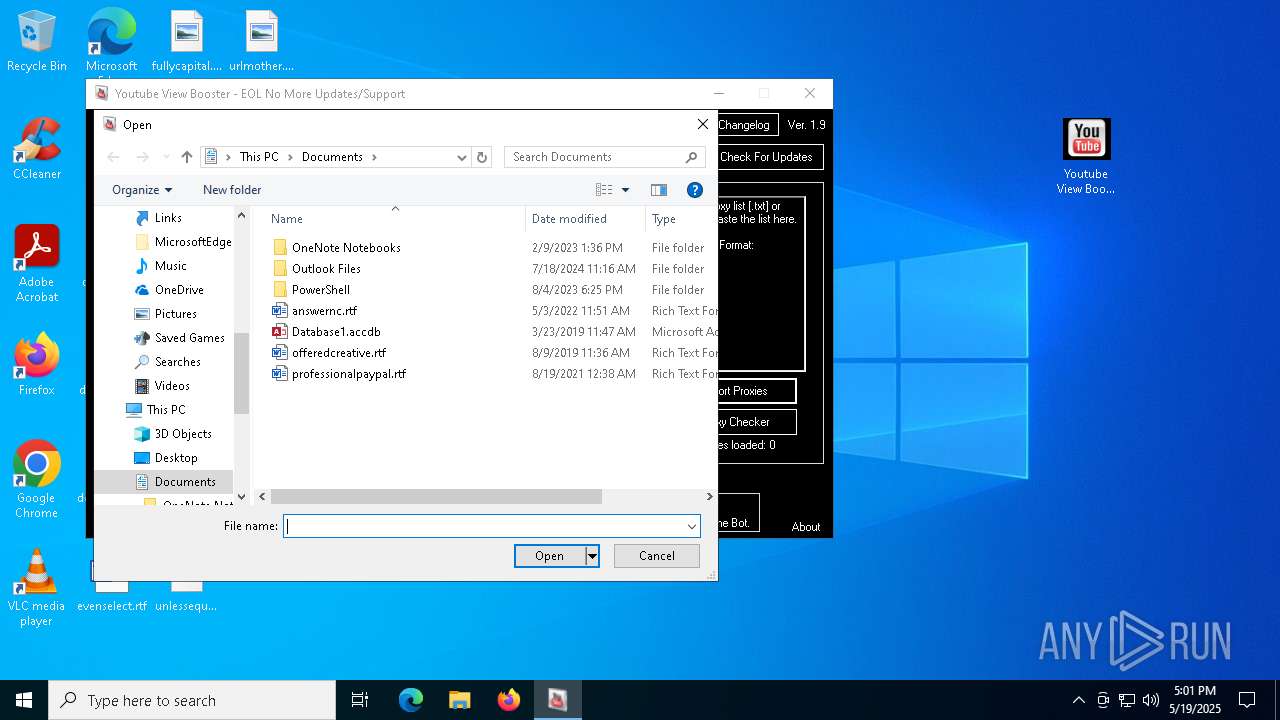
Manual execution by a user
- Youtube View Booster.exe (PID: 8064)
- Youtube View Booster.exe (PID: 6300)
- WinRAR.exe (PID: 2244)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
AsyncRat
(PID) Process(5588) dllhost.exe
C2 (2)127.0.0.1
2.tcp.eu.ngrok.io
Ports (1)17889
Version0.5.7B
BotnetDefault
Options
AutoRuntrue
MutexAsyncMutex_6SI8OkPnk
InstallFolder%AppData%
BSoDtrue
AntiVMtrue
Certificates
Cert1MIIE8jCCAtqgAwIBAgIQAPLde44Dn29hxxrdrhumrTANBgkqhkiG9w0BAQ0FADAaMRgwFgYDVQQDDA9Bc3luY1JBVCBTZXJ2ZXIwIBcNMjAwNjAzMjEyNjA3WhgPOTk5OTEyMzEyMzU5NTlaMBoxGDAWBgNVBAMMD0FzeW5jUkFUIFNlcnZlcjCCAiIwDQYJKoZIhvcNAQEBBQADggIPADCCAgoCggIBAILuQIktxEO93r1JC6k09n2MeRALakvX06gLrOzR05TWTE8WT9+jtDnizwyPh/Nxo+EJM6hHpo+A...
Server_SignaturefbUgCMU/Yi10JC1mU7OgRbszjjqP+YiWAtpyLuv7fl1PBtsbA37AGImx76KNQ+TJ4d5Z3IZwMCbUMOdut7U6xtORshUkjyX5odVWSYbPu4ruK8UbfMzQamWMEB2WqgfkGGIWqiVCB7CohQvCJR2sXDhIPwfTr0YcBHxvvSF9W+ZHEMe93vVceZo9VWduQcerlzKtIDjKXwK2RbMuOoDH5Ht0cTy83nYfWjYtVQ/XdpNwymm654c6qRRZy+SsbgQmNjV0OtBkcmLnSbtmb/dHwn2YL0UXJ0gjN20LX3dYo9xG...
Keys
AES76835fe4f3dea6d1dc8cb937a0689fb2944819cc8732cf85681a6886737d13a1
Saltbfeb1e56fbcd973bb219022430a57843003d5644d21e62b9d4f180e7e6c33941
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (82.9) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (7.4) |
| .exe | | | Win32 Executable (generic) (5.1) |
| .exe | | | Generic Win/DOS Executable (2.2) |
| .exe | | | DOS Executable Generic (2.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2020:06:07 11:08:00+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 11 |
| CodeSize: | 226816 |
| InitializedDataSize: | 372736 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x394ce |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
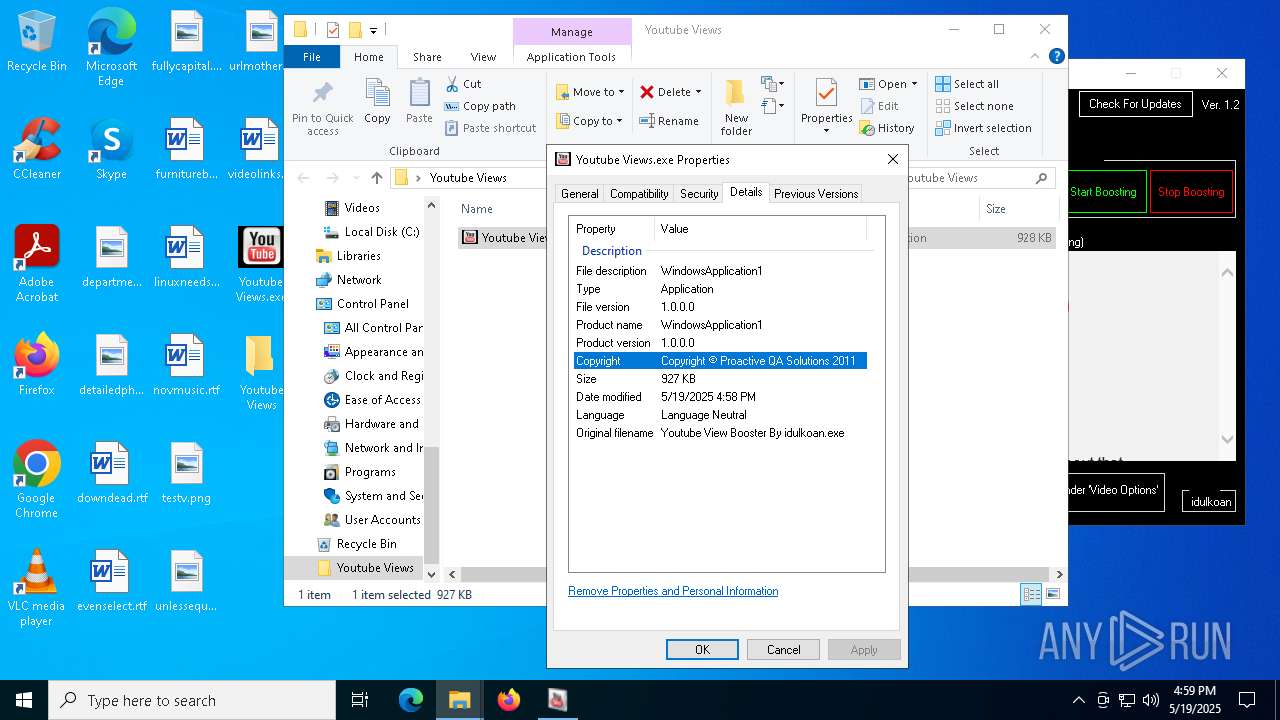
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | WindowsApplication1 |
| CompanyName: | WindowsApplication1 |
| FileDescription: | WindowsApplication1 |
| FileVersion: | 1.0.0.0 |
| InternalName: | Youtube Views.exe |
| LegalCopyright: | Copyright © Proactive QA Solutions 2011 |
| OriginalFileName: | Youtube Views.exe |
| ProductName: | WindowsApplication1 |
| ProductVersion: | 1.0.0.0 |
| AssemblyVersion: | 1.0.0.0 |
Total processes
215
Monitored processes
79
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 660 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data" /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Crashpad" --annotation=IsOfficialBuild=1 --annotation=channel= --annotation=chromium-version=122.0.6261.70 "--annotation=exe=C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --annotation=plat=Win64 "--annotation=prod=Microsoft Edge" --annotation=ver=122.0.2365.59 --initial-client-data=0x31c,0x320,0x324,0x314,0x32c,0x7ffc89875fd8,0x7ffc89875fe4,0x7ffc89875ff0 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 736 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=3320 --field-trial-handle=2316,i,8048829921892957799,14685822368495333473,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 872 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=36 --mojo-platform-channel-handle=8020 --field-trial-handle=2396,i,9561486434117215723,7644873445993720609,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1096 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=gpu-process --no-appcompat-clear --gpu-preferences=WAAAAAAAAADgAAAMAAAAAAAAAAAAAAAAAABgAAAAAAA4AAAAAAAAAAAAAAAEAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAGAAAAAAAAAAYAAAAAAAAAAgAAAAAAAAACAAAAAAAAAAIAAAAAAAAAA== --mojo-platform-channel-handle=2392 --field-trial-handle=2396,i,9561486434117215723,7644873445993720609,262144 --variations-seed-version /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1324 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Downloads\[Latest] Youtube View Booster Ver. 1.9.rar" | C:\Program Files\WinRAR\WinRAR.exe | msedge.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 2088 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=31 --mojo-platform-channel-handle=5280 --field-trial-handle=2396,i,9561486434117215723,7644873445993720609,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2140 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
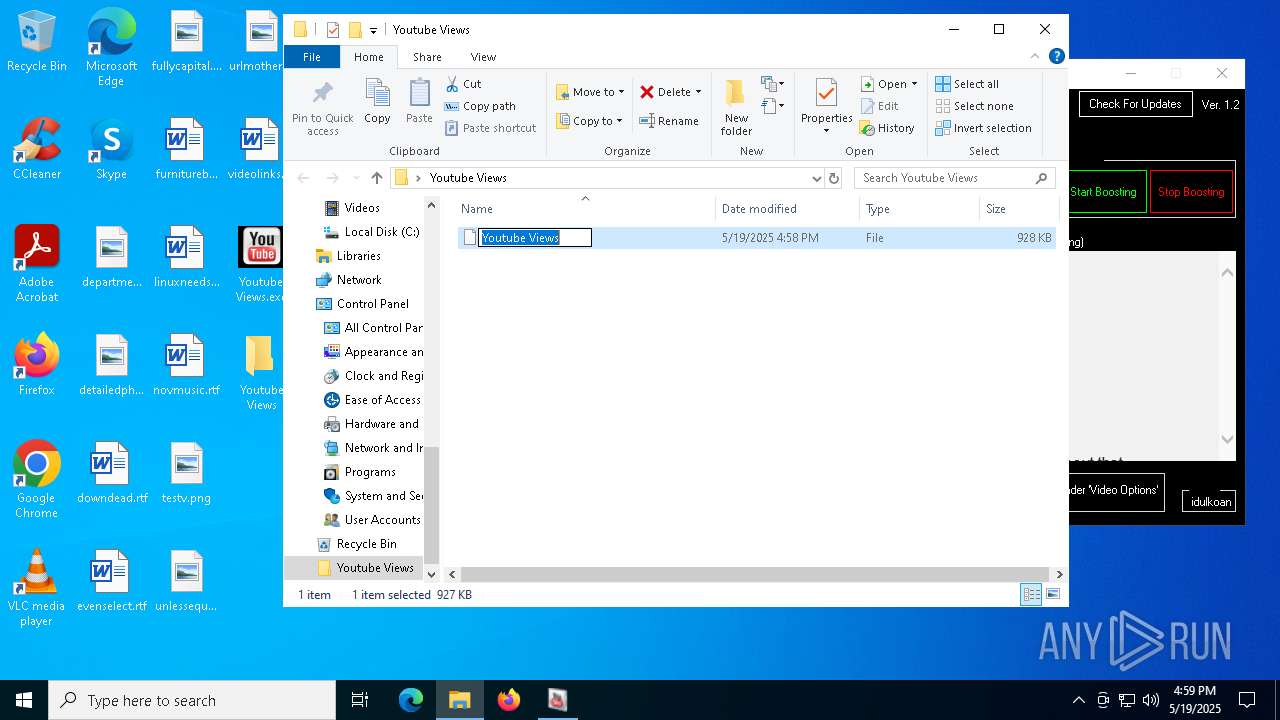
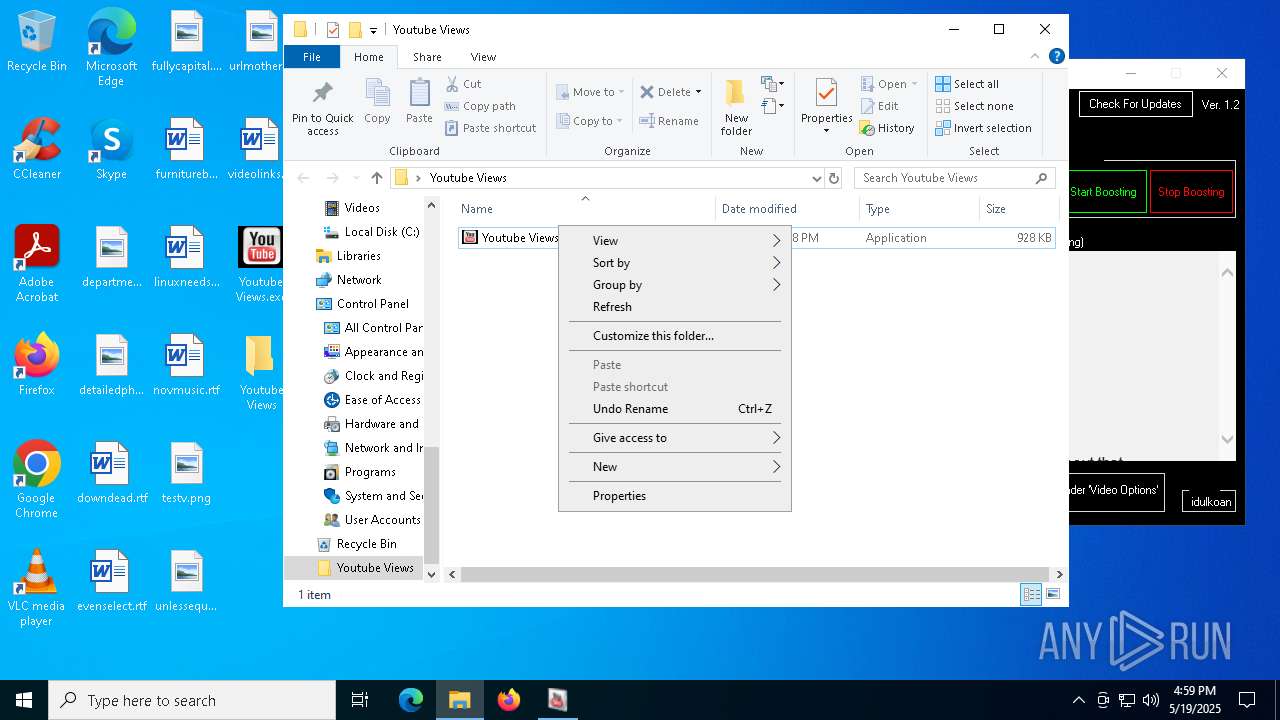
| 2244 | "C:\Program Files\WinRAR\WinRAR.exe" x -iext -ow -ver -- "C:\Users\admin\Desktop\Youtube Views.exe" "C:\Users\admin\Desktop\Youtube Views\" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 2284 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=5424 --field-trial-handle=2316,i,8048829921892957799,14685822368495333473,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2316 | "C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe" --type=utility --utility-sub-type=winrt_app_id.mojom.WinrtAppIdService --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=4352 --field-trial-handle=2316,i,8048829921892957799,14685822368495333473,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: PWA Identity Proxy Host Exit code: 3221226029 Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
19 361
Read events
19 267
Write events
90
Delete events
4
Modification events
| (PID) Process: | (7596) Lrvdezvd.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (7596) Lrvdezvd.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (7596) Lrvdezvd.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (7604) Muwldtrpxmp.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | dllhost |
Value: "C:\Users\admin\AppData\Roaming\dllhost.exe" | |||
| (PID) Process: | (2244) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2244) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2244) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2244) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (7596) Lrvdezvd.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer |
| Operation: | write | Name: | SlowContextMenuEntries |
Value: 6024B221EA3A6910A2DC08002B30309D0A010000BD0E0C47735D584D9CEDE91E22E23282770100000114020000000000C0000000000000468D0000006078A409B011A54DAFA526D86198A780390100009AD298B2EDA6DE11BA8CA68E55D895936E000000 | |||
| (PID) Process: | (6808) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
Executable files
27
Suspicious files
323
Text files
81
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7596 | Lrvdezvd.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\IE\RR3E01RZ\monkey[1].png | image | |
MD5:36976FC2F68172E471BAB4FB2BF21F2C | SHA256:BF6DC026FA12EBC5969663EA8A1298CEE1EB9DD3E7C4D3DE8AF33A94880585D7 | |||
| 7596 | Lrvdezvd.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\2A42127F349D54E7AA939366FF86F74E_2C629BDFE651247CFD4A720315C0F085 | binary | |
MD5:4763857EE0CD4DAAFAAF7CB2DFBCDBF5 | SHA256:3AC7AE86A2B435A6C171DC1F6B380AC85097E9B9E5B73FBA498453E4318166CB | |||
| 7604 | Muwldtrpxmp.exe | C:\Users\admin\AppData\Roaming\dllhost.exe | executable | |
MD5:CBDD34D2506CDBCB6B6AC83F8FF85E9C | SHA256:930CCD4DD57ED9DCCB728D4B98542924173A416210ED2BFF8B1EAB9121817D13 | |||
| 7604 | Muwldtrpxmp.exe | C:\Users\admin\AppData\Local\Temp\tmpFADC.tmp.bat | text | |
MD5:F4997EB5A3CF0ED9C89597E63C320F99 | SHA256:98BBE8BE60631C7C1B39DB0029851E4F63CD87EA719FD9E0C9BC00090399ACFA | |||
| 7528 | Youtube Views.exe | C:\Users\admin\AppData\Local\Temp\Lrvdezvd.exe | executable | |
MD5:456773EF51F0E5F2877CE710386B7ADF | SHA256:641FD5033E881C0F12ED901E66F4151D0392F9F31F079E0E4F5C0A8BB2EE061C | |||
| 7596 | Lrvdezvd.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\2A42127F349D54E7AA939366FF86F74E_2C629BDFE651247CFD4A720315C0F085 | binary | |
MD5:A83A34B78E311A617E41C36EDE6B27D0 | SHA256:A3E0A2381A6DB9FE5E06804B922846F03DCFD13370FB7A39510E415E5C1C1513 | |||
| 6808 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF118b36.TMP | — | |
MD5:— | SHA256:— | |||
| 6808 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6808 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF118b36.TMP | — | |
MD5:— | SHA256:— | |||
| 6808 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
12
TCP/UDP connections
299
DNS requests
328
Threats
26
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
7596 | Lrvdezvd.exe | GET | 200 | 142.250.185.227:80 | http://c.pki.goog/r/gsr1.crl | unknown | — | — | whitelisted |
7596 | Lrvdezvd.exe | GET | 301 | 216.58.212.142:80 | http://www.youtube.com/user/idulkoan | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 2.19.11.105:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
7596 | Lrvdezvd.exe | GET | 200 | 142.250.185.227:80 | http://c.pki.goog/r/r4.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
7596 | Lrvdezvd.exe | GET | 200 | 142.250.181.227:80 | http://o.pki.goog/we2/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTuMJxAT2trYla0jia%2F5EUSmLrk3QQUdb7Ed66J9kQ3fc%2BxaB8dGuvcNFkCEA85wFTvuwmlCdtY0UxEIqg%3D | unknown | — | — | whitelisted |
7596 | Lrvdezvd.exe | GET | 200 | 142.250.181.227:80 | http://o.pki.goog/we2/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTuMJxAT2trYla0jia%2F5EUSmLrk3QQUdb7Ed66J9kQ3fc%2BxaB8dGuvcNFkCEEALuY4zRY58EDp%2FMW%2B6MIw%3D | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 104.81.99.218:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
1184 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
1184 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5496 | MoUsoCoreWorker.exe | 2.19.11.105:80 | crl.microsoft.com | Elisa Oyj | NL | whitelisted |
5496 | MoUsoCoreWorker.exe | 2.23.246.101:80 | www.microsoft.com | Ooredoo Q.S.C. | QA | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3216 | svchost.exe | 172.211.123.248:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
7596 | Lrvdezvd.exe | 216.58.212.142:80 | www.youtube.com | GOOGLE | US | whitelisted |
7596 | Lrvdezvd.exe | 216.58.212.142:443 | www.youtube.com | GOOGLE | US | whitelisted |
7596 | Lrvdezvd.exe | 142.250.185.227:80 | c.pki.goog | GOOGLE | US | whitelisted |
7596 | Lrvdezvd.exe | 142.250.181.227:80 | o.pki.goog | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
www.youtube.com |
| whitelisted |
c.pki.goog |
| whitelisted |
o.pki.goog |
| whitelisted |
www.gstatic.com |
| whitelisted |
login.live.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | Misc activity | ET INFO DNS Query to a *.ngrok domain (ngrok.io) |
5436 | msedge.exe | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain (www .mediafire .com) in DNS Lookup |
5436 | msedge.exe | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain (www .mediafire .com) in DNS Lookup |
5436 | msedge.exe | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain (www .mediafire .com) in DNS Lookup |
5436 | msedge.exe | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain (www .mediafire .com) in DNS Lookup |
5436 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Hosted Libraries (ajax .googleapis .com) |
5436 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Hosted Libraries (ajax .googleapis .com) |
5436 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
5436 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
5436 | msedge.exe | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain (www .mediafire .com) in DNS Lookup |