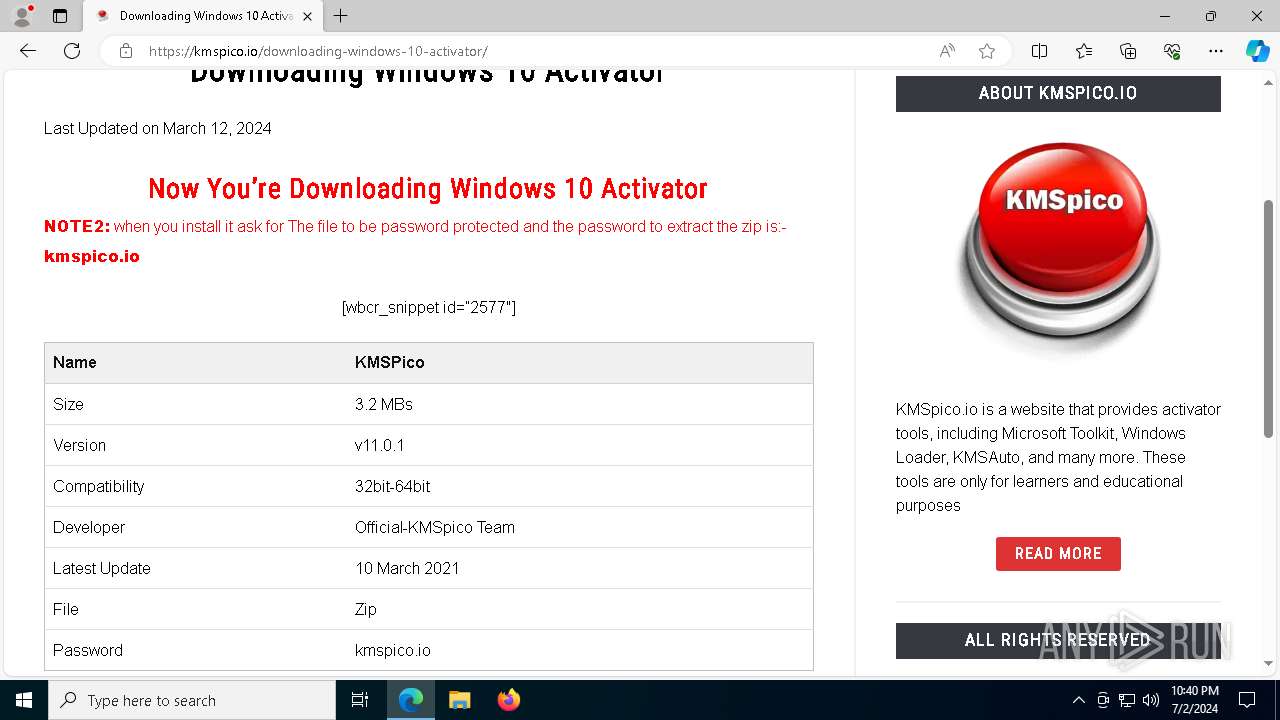
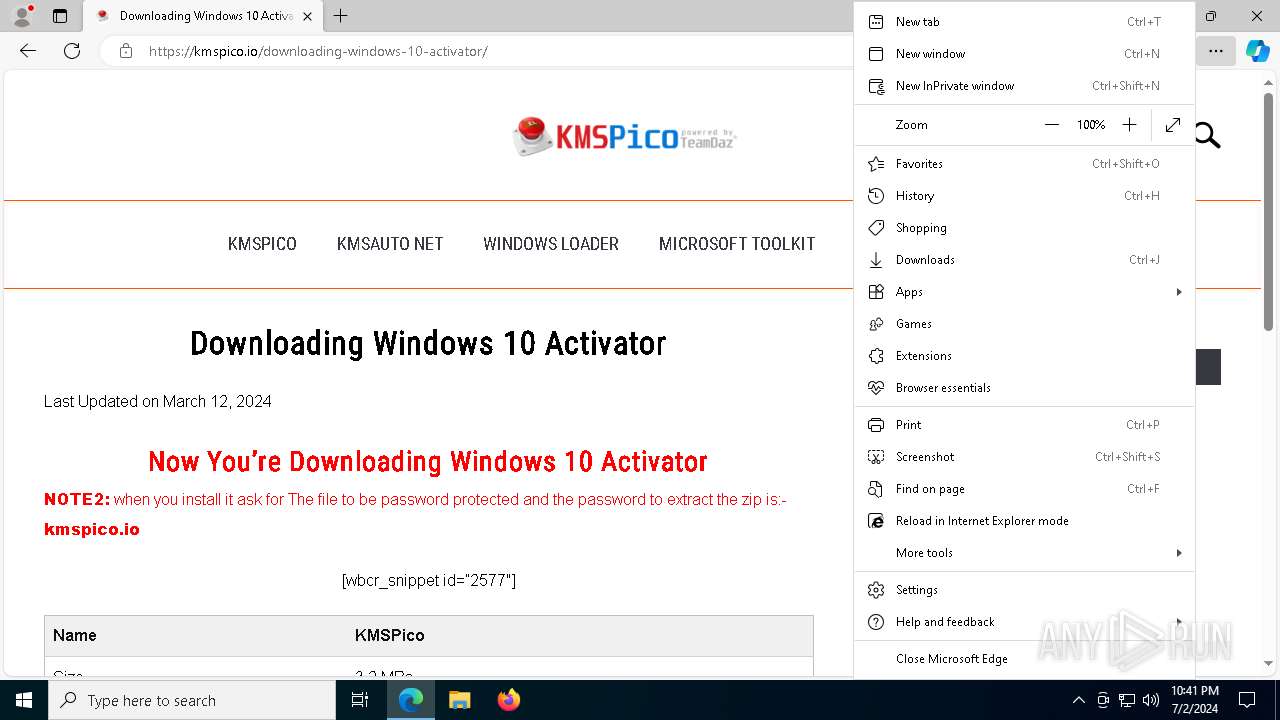
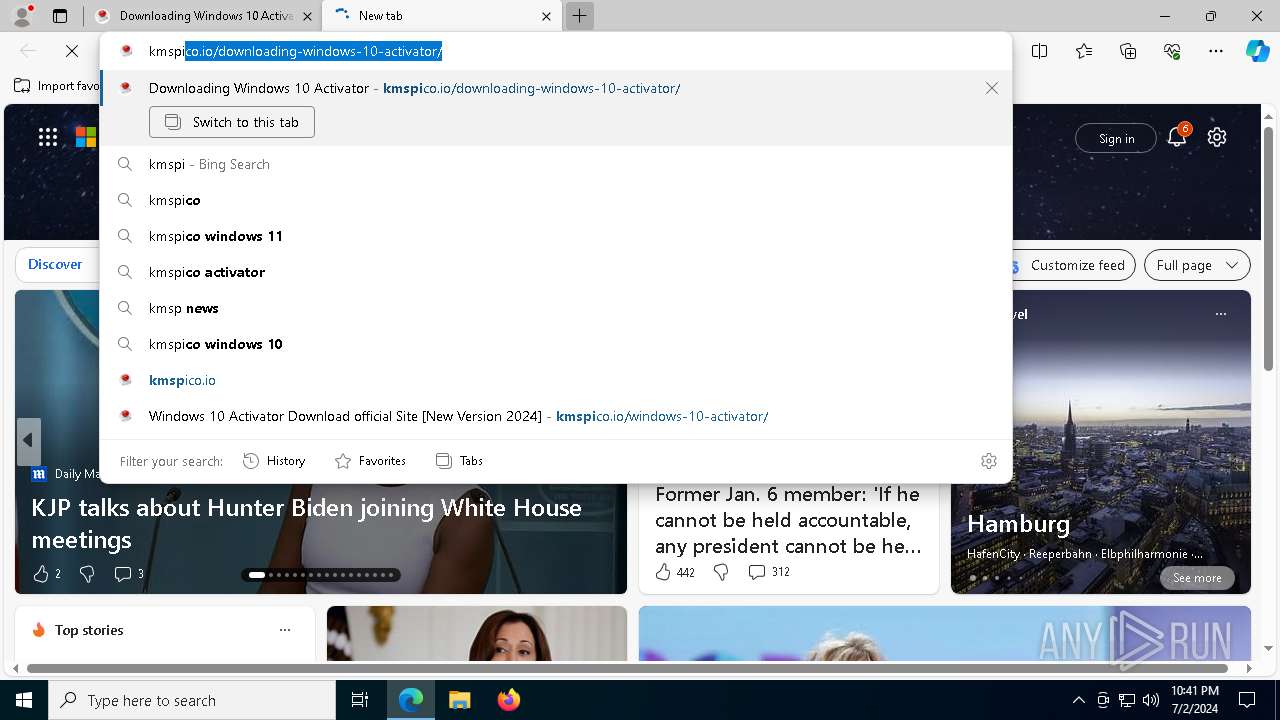
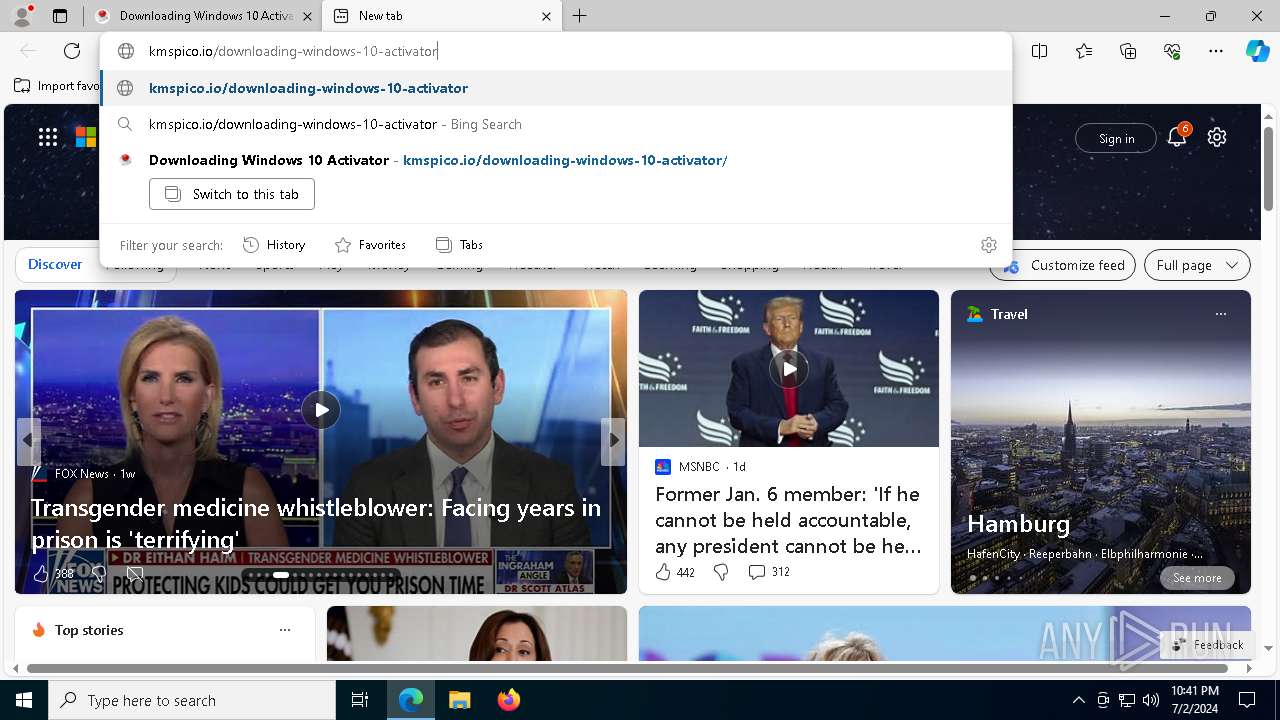
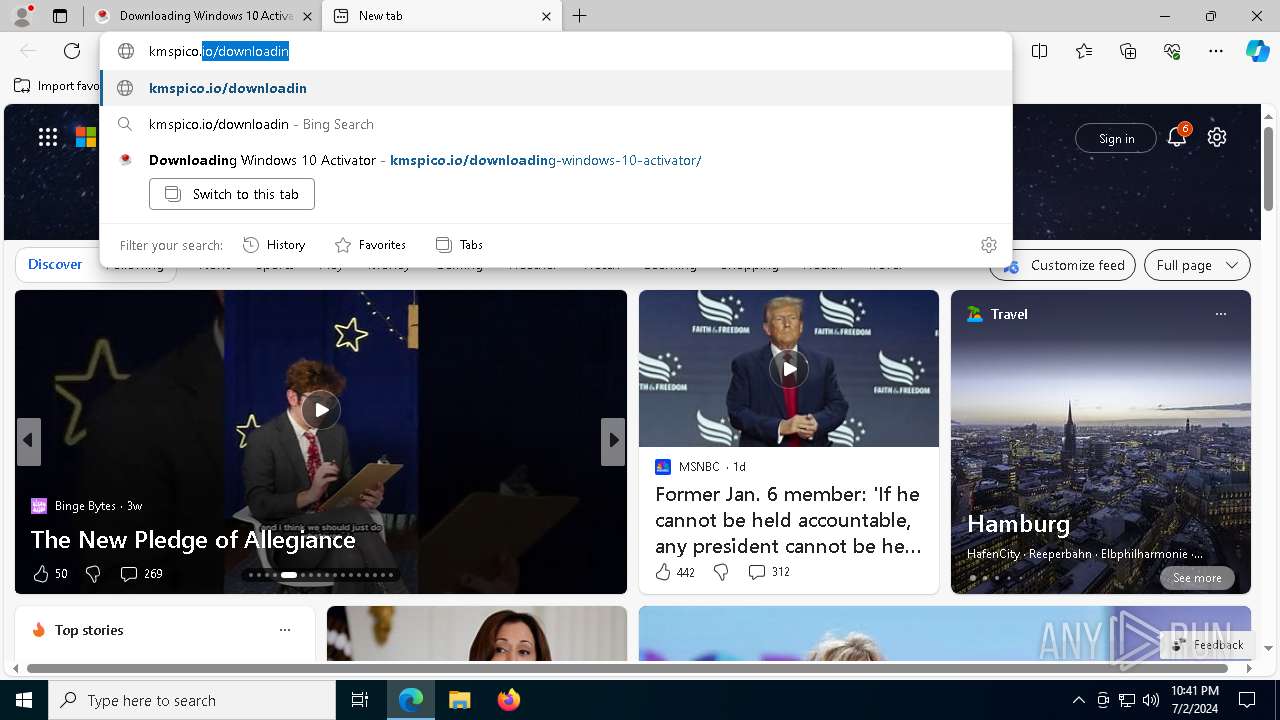
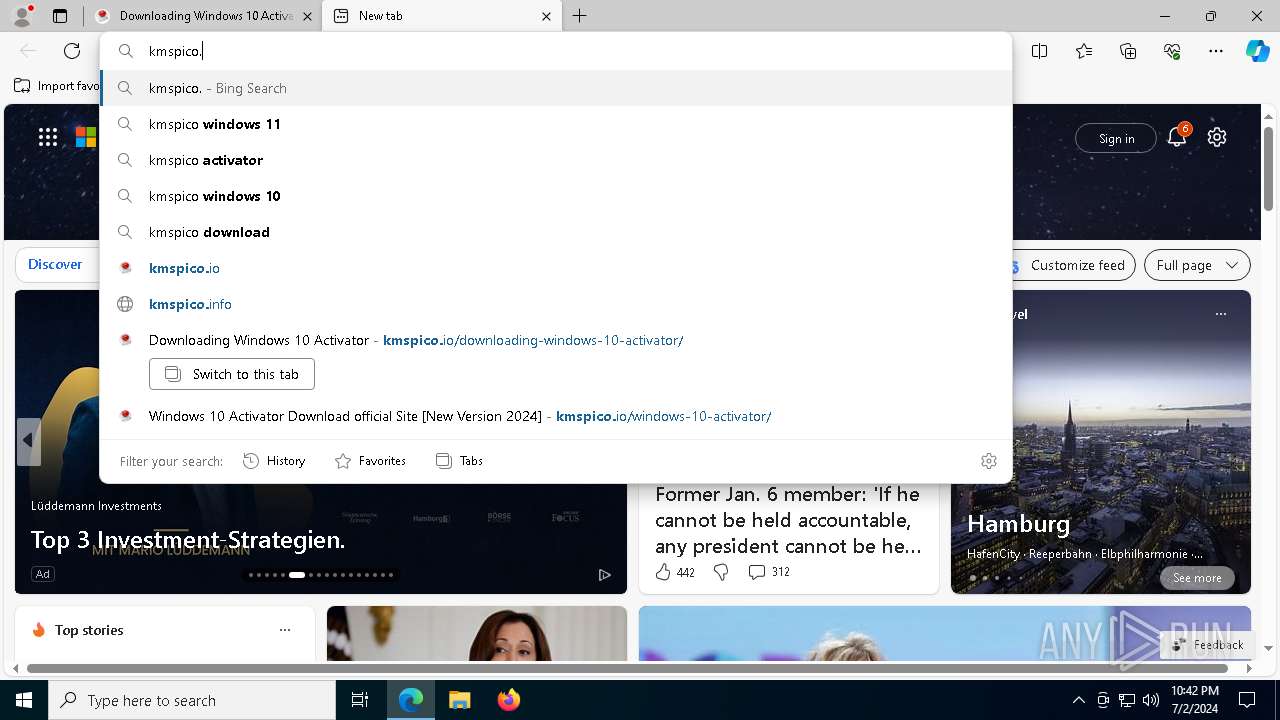
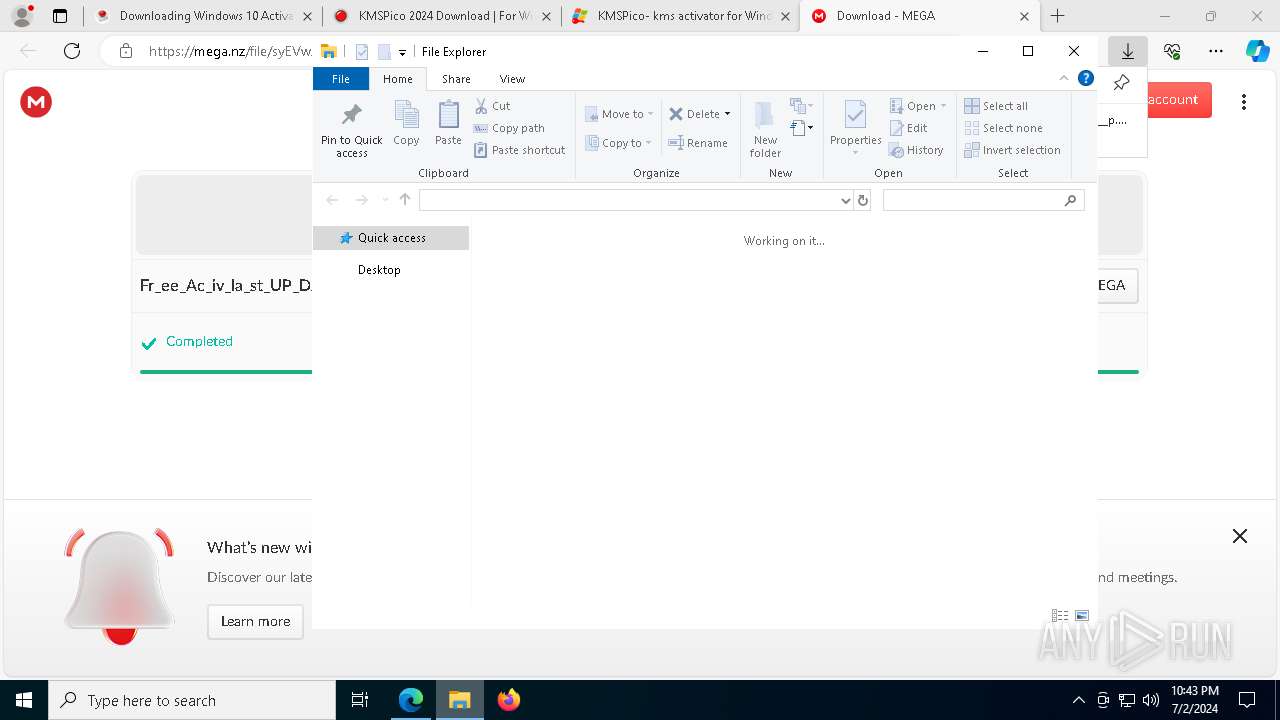
| URL: | https://kmspico.io/windows-10-activator/ |
| Full analysis: | https://app.any.run/tasks/541ba73d-856b-4405-9628-b32eec4e38cb |
| Verdict: | Malicious activity |
| Threats: | Raspberry Robin is a trojan that primarily spreads through infected USB drives and exploits legitimate Windows commands. This malware is known for its advanced obfuscation techniques, anti-debugging mechanisms, and ability to gain persistence on infected systems. Raspberry Robin often communicates with command-and-control servers over the TOR network and can download additional malicious payloads. |
| Analysis date: | July 02, 2024, 22:40:03 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 2A45961727F97444F4CD6B1B93868DE2 |
| SHA1: | 68ABAB3B7B20B42B184F0C7422803F33AF371751 |
| SHA256: | 71B07E499AE5753FC7E24E16711503505DB653BF2FE60AC7C89B1B0252264573 |
| SSDEEP: | 3:N8N/JKJEGqW:2dEJvD |
MALICIOUS
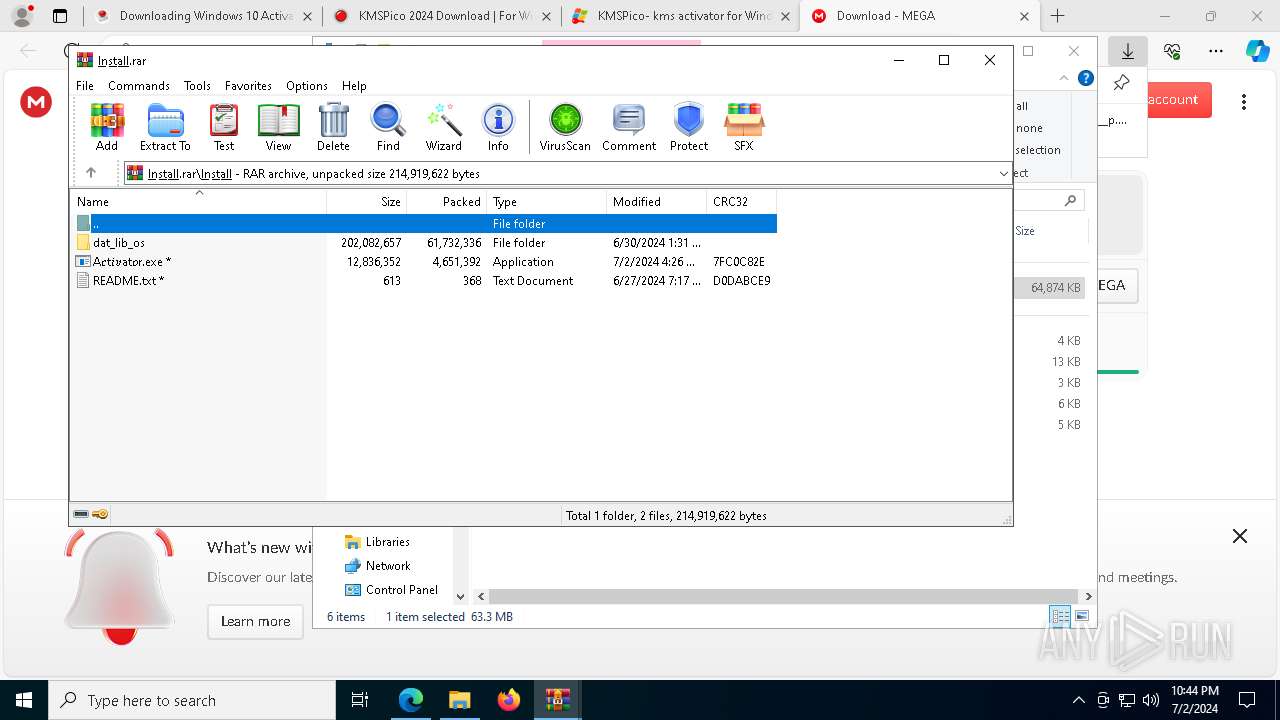
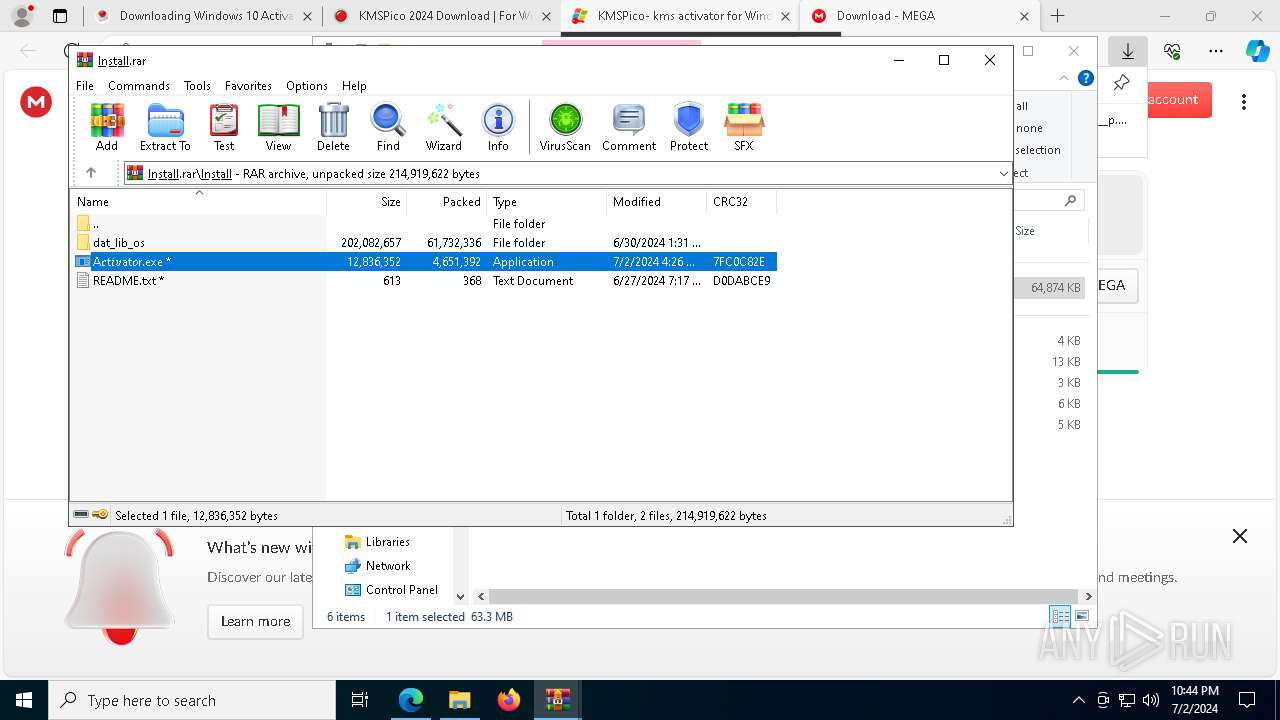
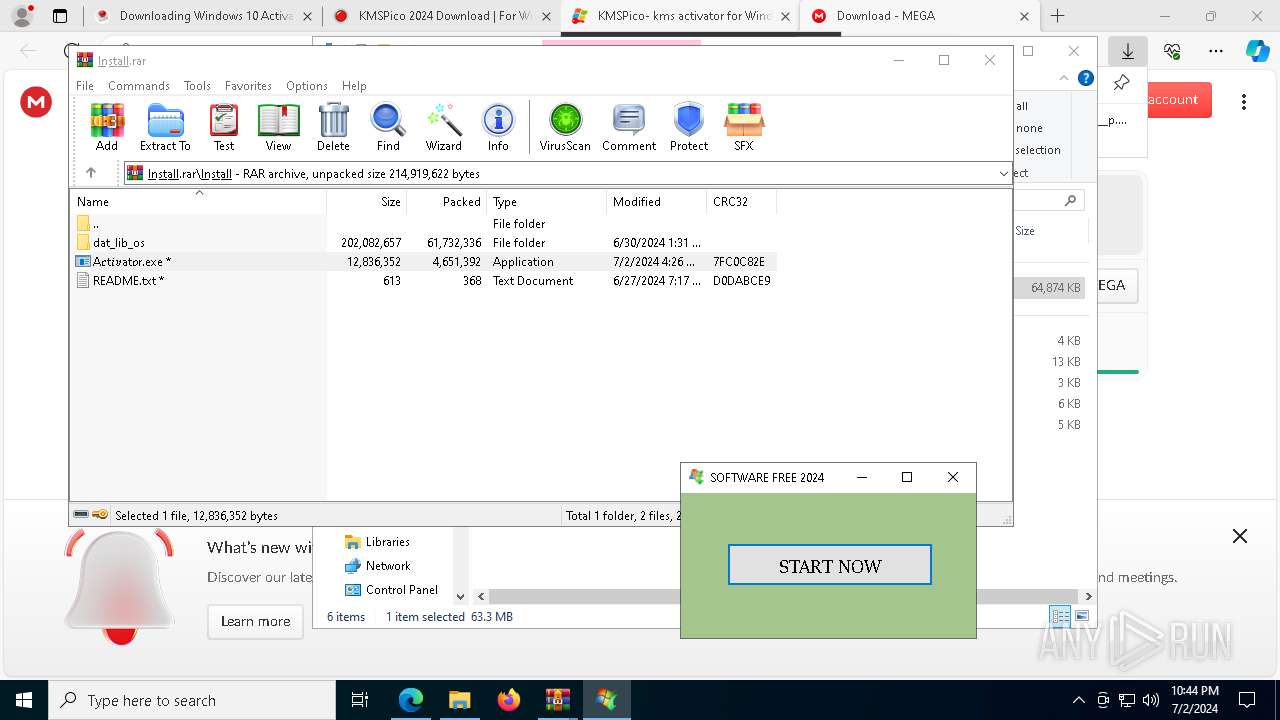
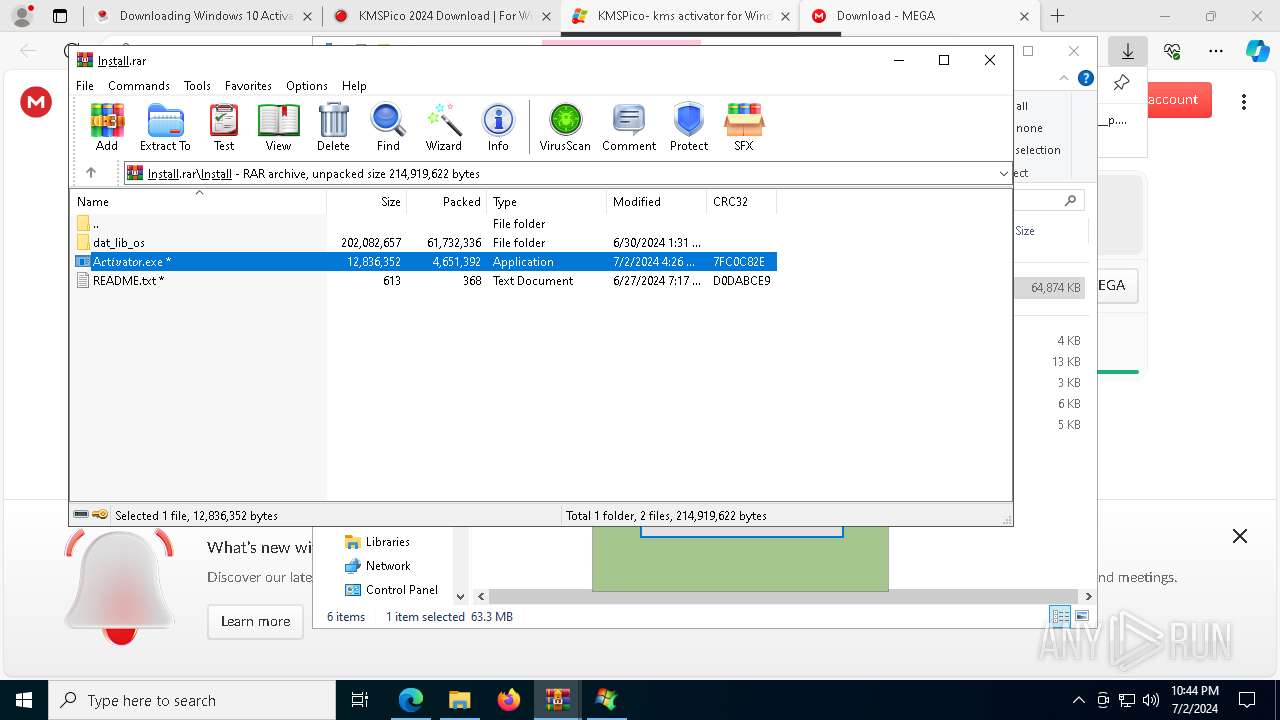
Drops the executable file immediately after the start
- A𝑐t𝑖𝑣at𝑜r.exe (PID: 6368)
RASPBERRYROBIN has been detected (YARA)
- regsvr32.exe (PID: 652)
Registers / Runs the DLL via REGSVR32.EXE
- A𝑐t𝑖𝑣at𝑜r.exe (PID: 6368)
SUSPICIOUS
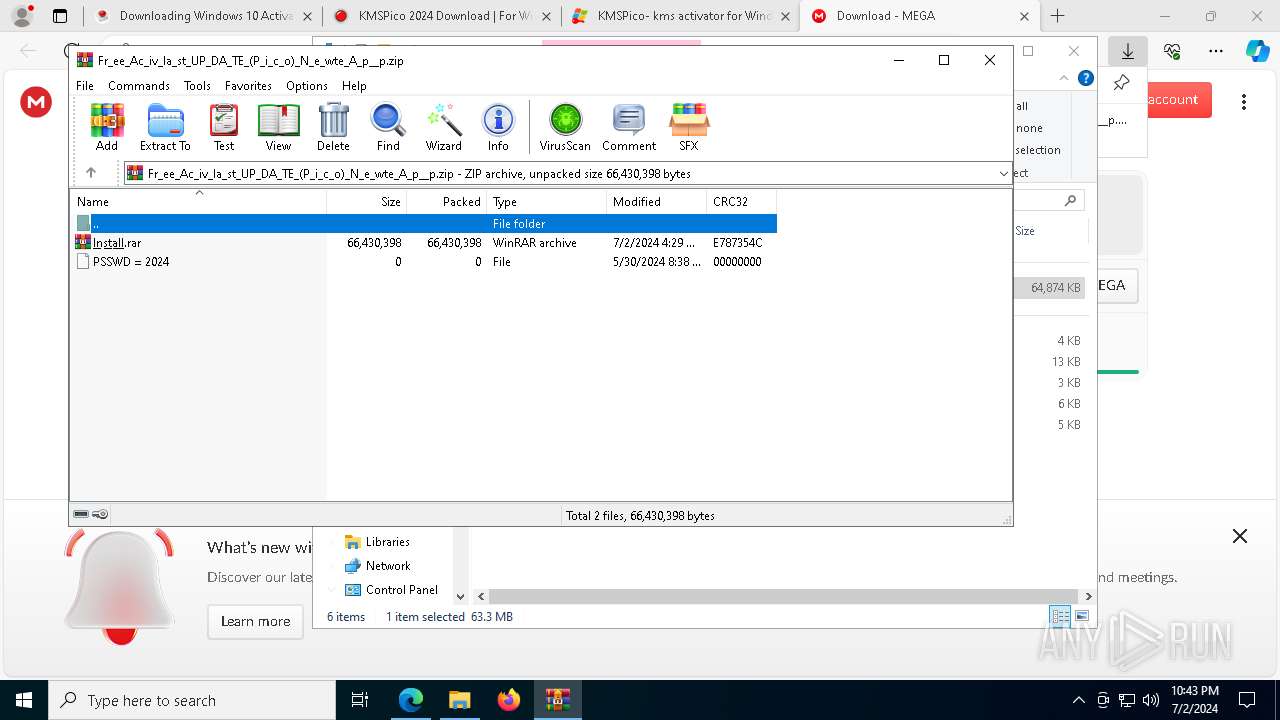
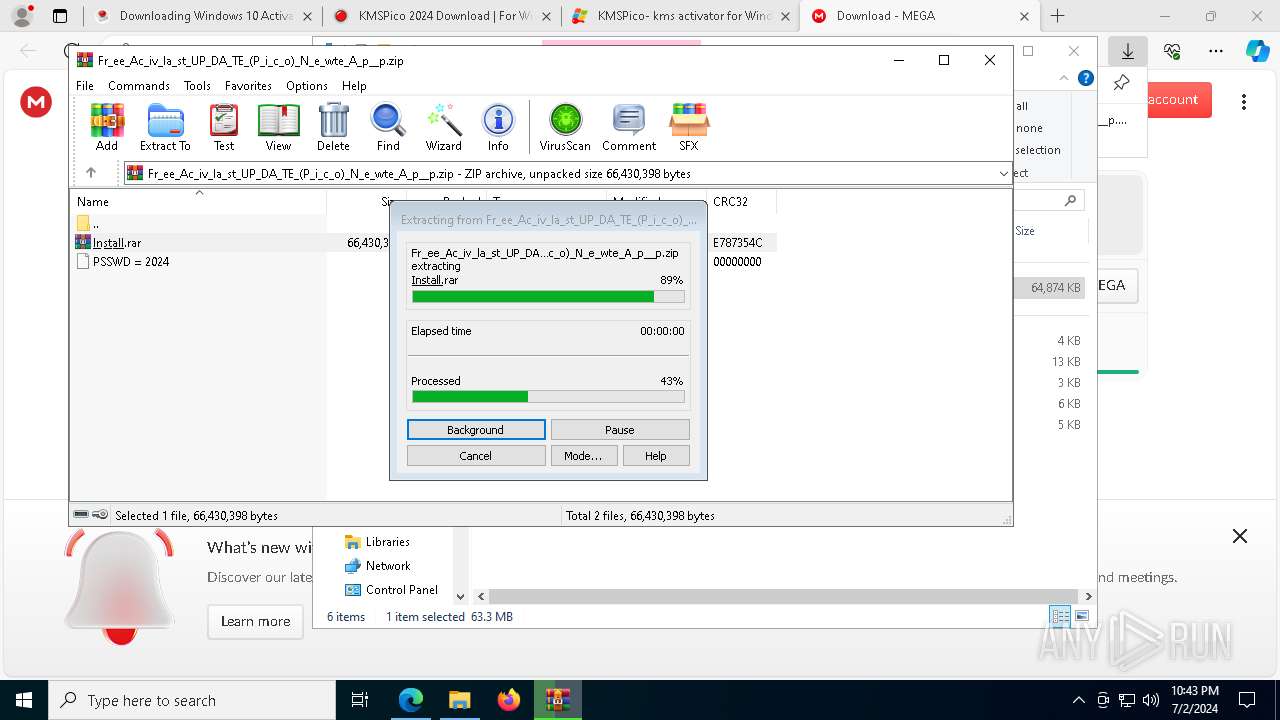
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 5736)
- WinRAR.exe (PID: 5584)
Application launched itself
- WinRAR.exe (PID: 5736)
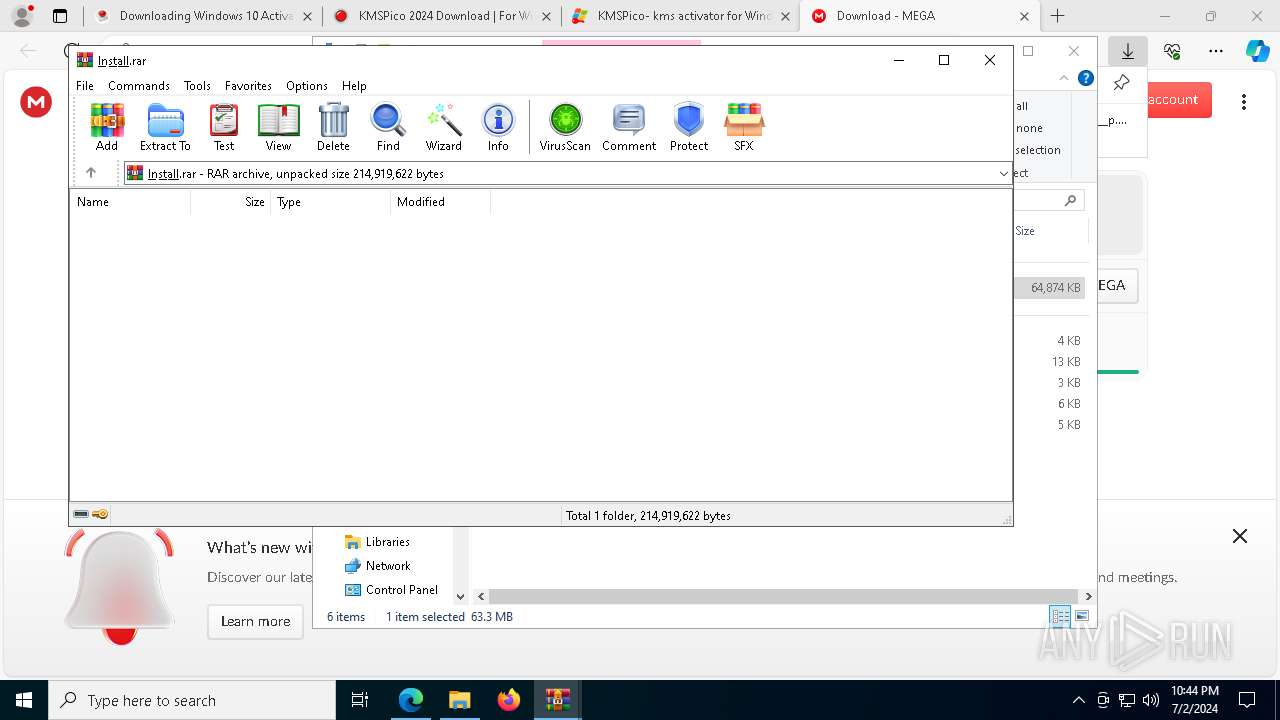
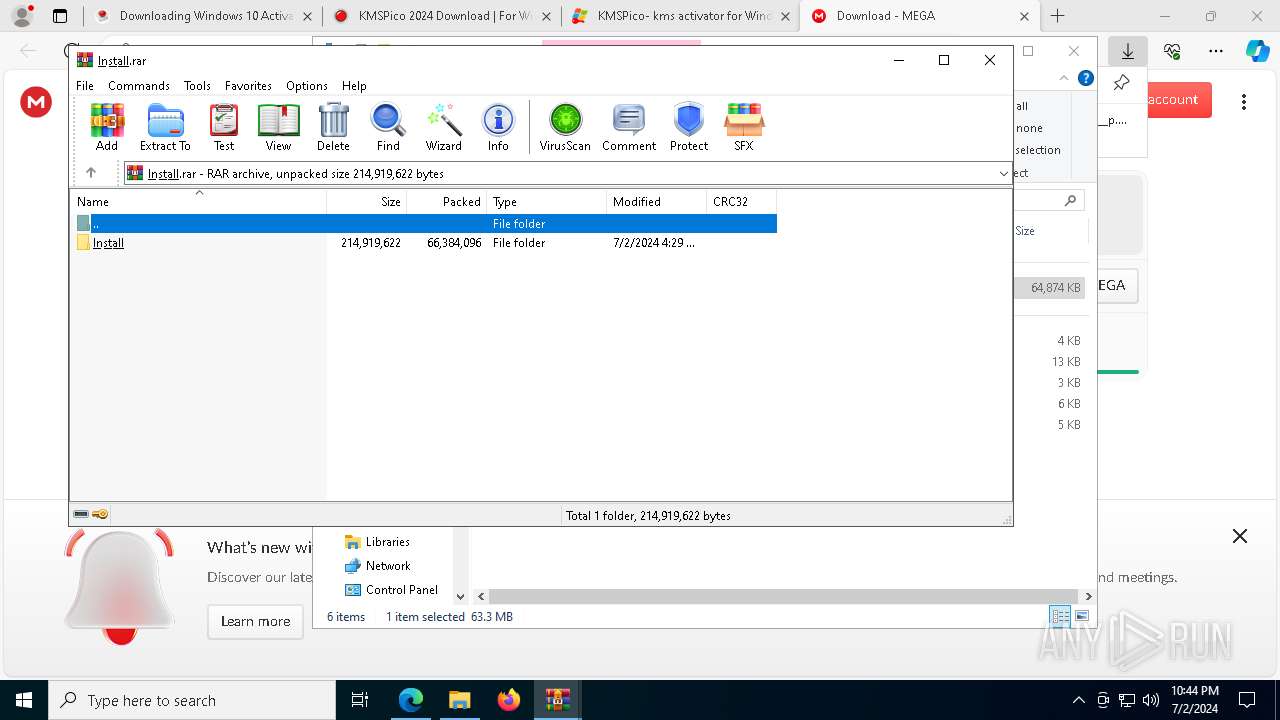
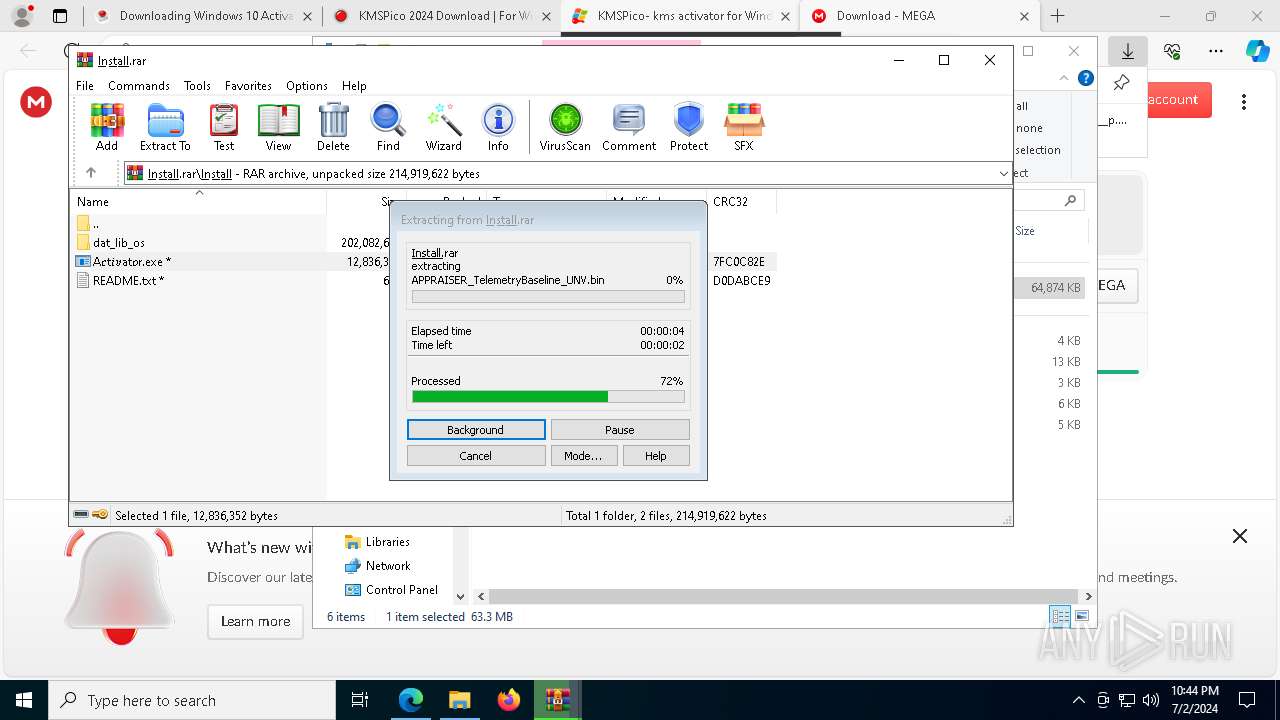
The process creates files with name similar to system file names
- WinRAR.exe (PID: 5584)
Process drops legitimate windows executable
- WinRAR.exe (PID: 5584)
Executable content was dropped or overwritten
- A𝑐t𝑖𝑣at𝑜r.exe (PID: 6368)
The process checks if it is being run in the virtual environment
- regsvr32.exe (PID: 652)
INFO
Application launched itself
- msedge.exe (PID: 752)
Reads the computer name
- TextInputHost.exe (PID: 6980)
- identity_helper.exe (PID: 6828)
- A𝑐t𝑖𝑣at𝑜r.exe (PID: 6368)
- identity_helper.exe (PID: 4448)
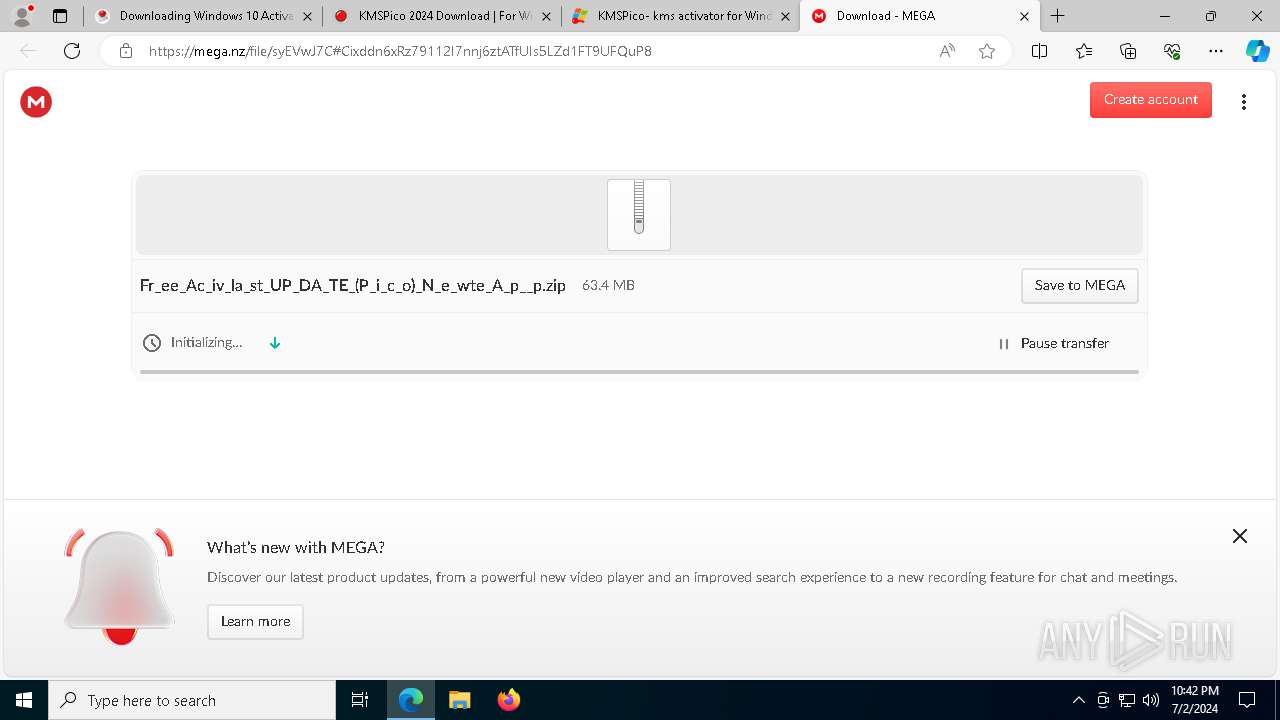
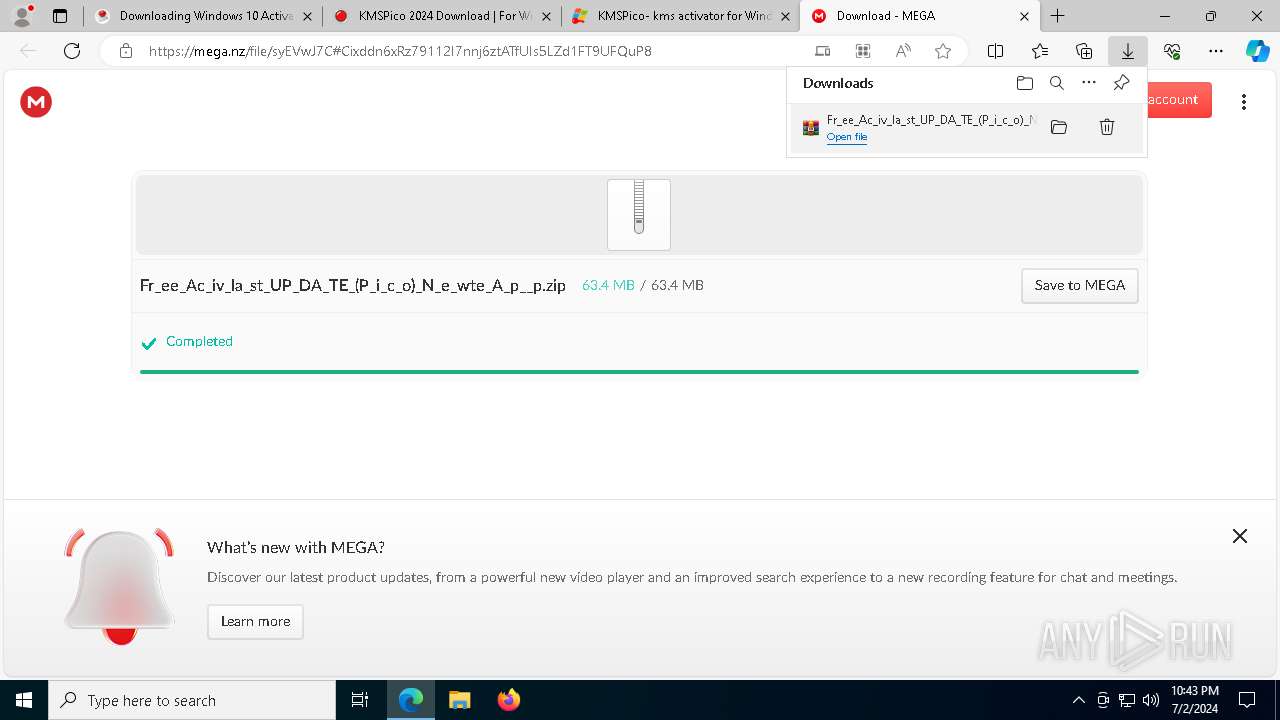
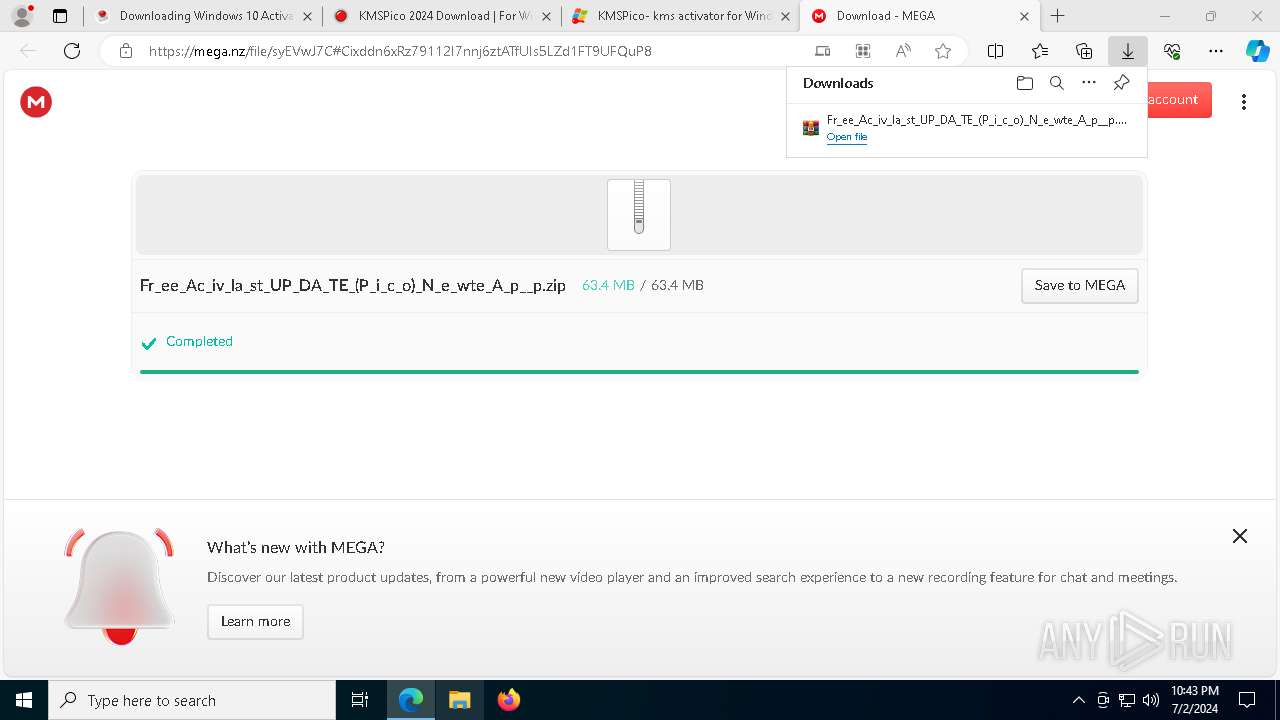
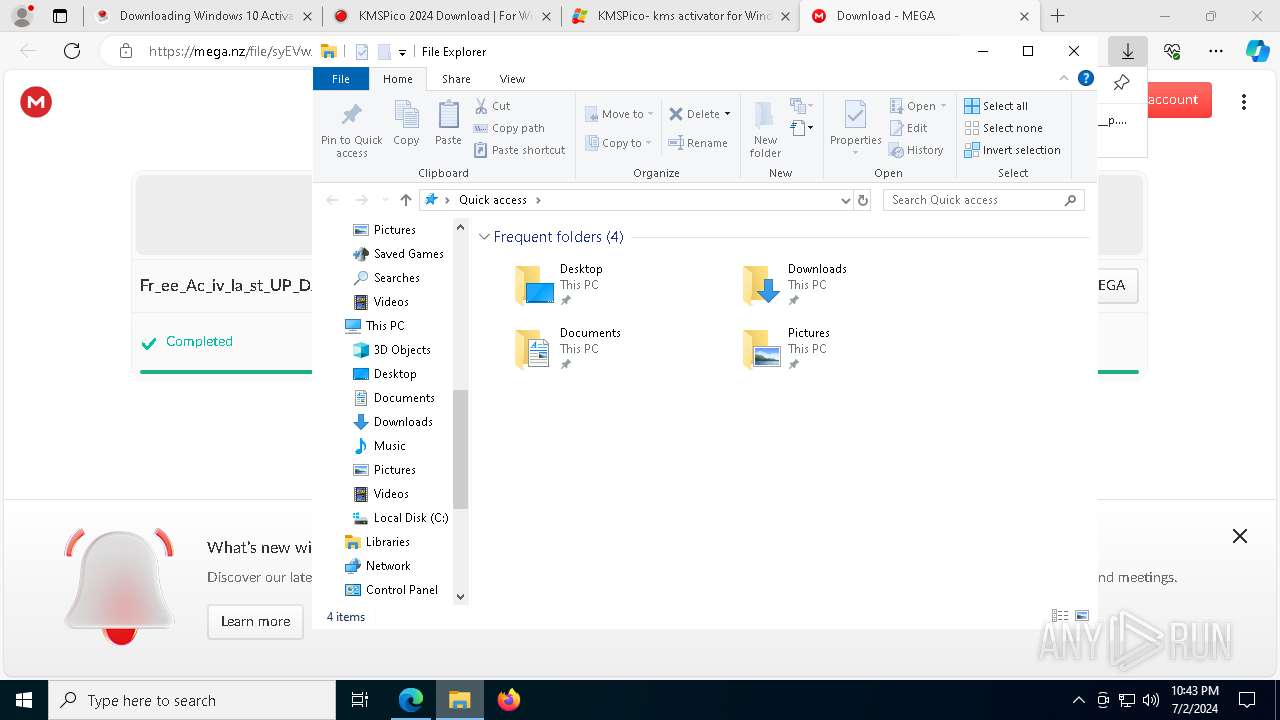
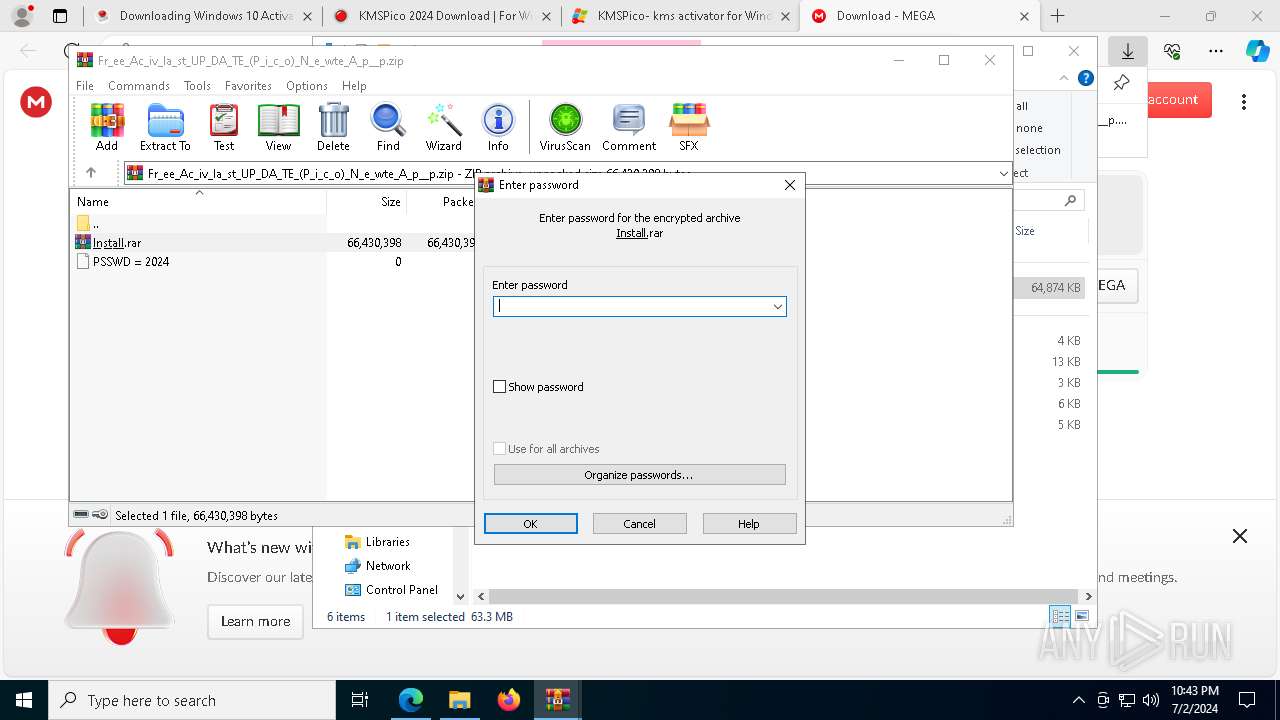
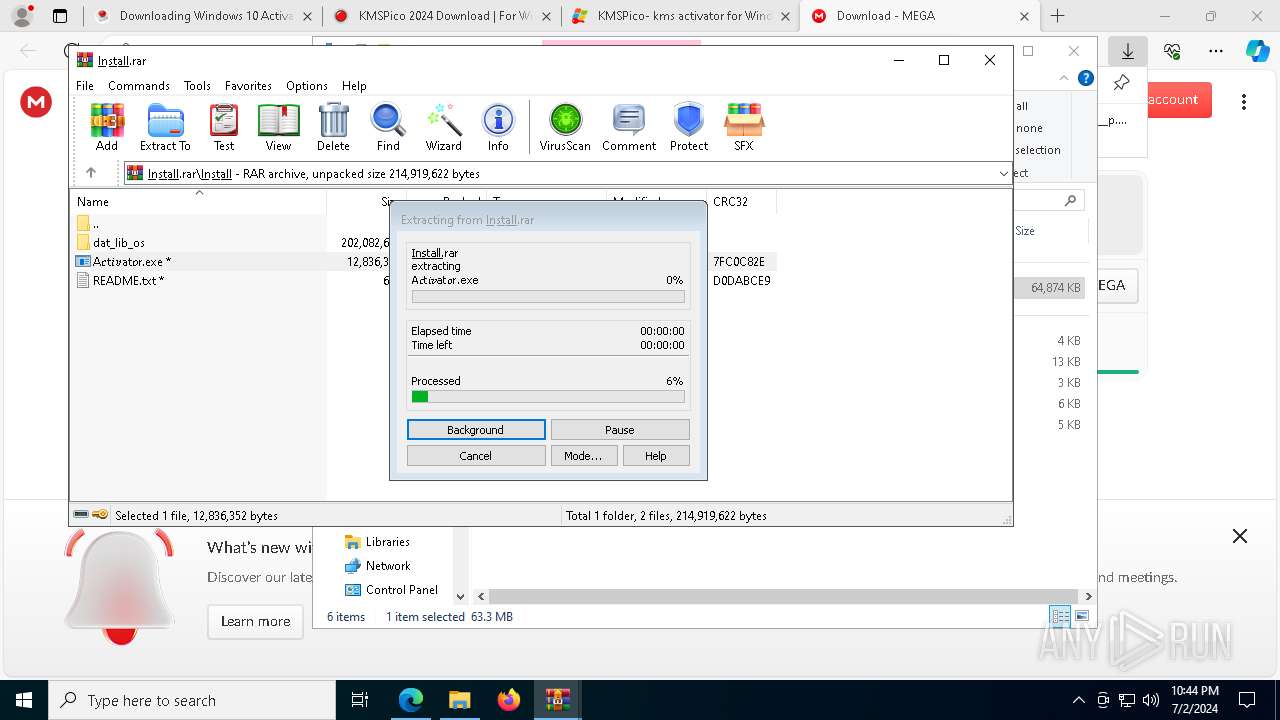
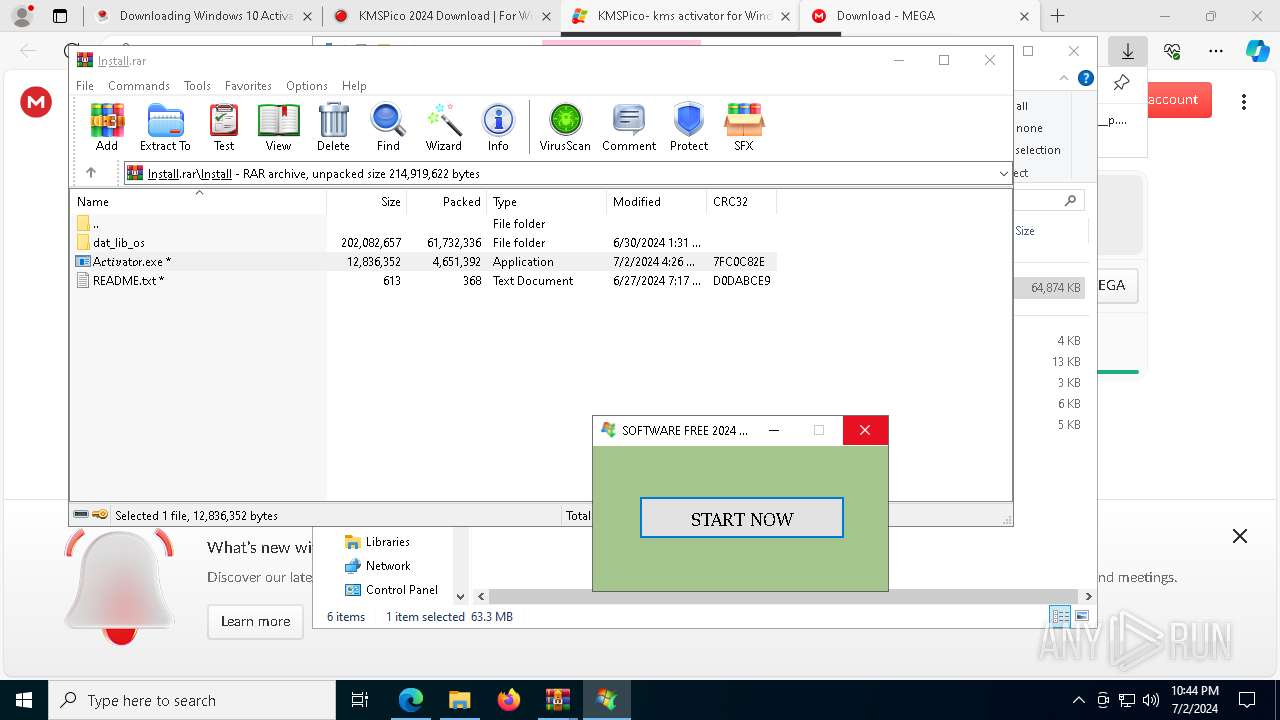
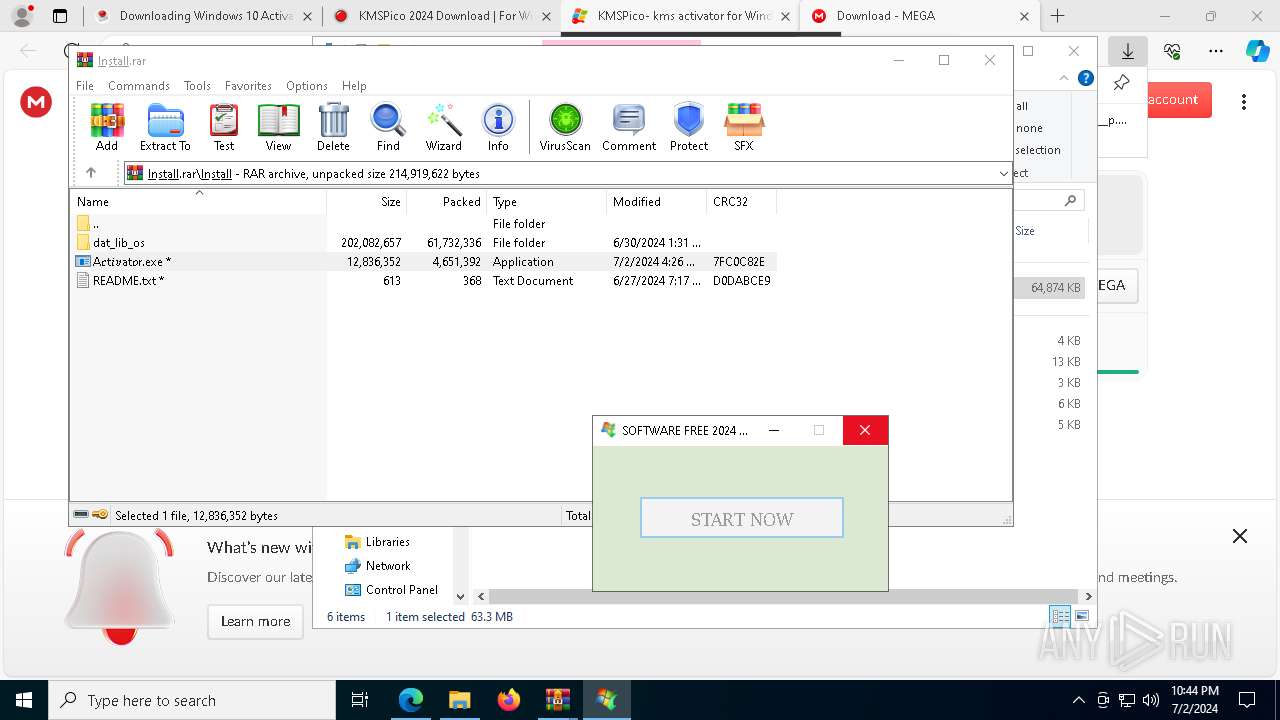
Manual execution by a user
- WinRAR.exe (PID: 5736)
The process uses the downloaded file
- WinRAR.exe (PID: 5736)
- msedge.exe (PID: 6556)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 5584)
Checks supported languages
- A𝑐t𝑖𝑣at𝑜r.exe (PID: 6368)
- identity_helper.exe (PID: 6828)
- TextInputHost.exe (PID: 6980)
- identity_helper.exe (PID: 4448)
Reads Microsoft Office registry keys
- msedge.exe (PID: 752)
Create files in a temporary directory
- A𝑐t𝑖𝑣at𝑜r.exe (PID: 6368)
Found Base64 encoded security-related PowerShell classes (YARA)
- A𝑐t𝑖𝑣at𝑜r.exe (PID: 6368)
Found Base64 encoded environment-related PowerShell classes (YARA)
- A𝑐t𝑖𝑣at𝑜r.exe (PID: 6368)
Found Base64 encoded data-related PowerShell classes (YARA)
- A𝑐t𝑖𝑣at𝑜r.exe (PID: 6368)
Found Base64 encoded code-related PowerShell classes (YARA)
- A𝑐t𝑖𝑣at𝑜r.exe (PID: 6368)
Found Base64 encoded PowerShell cmdlet (YARA)
- A𝑐t𝑖𝑣at𝑜r.exe (PID: 6368)
Drops the executable file immediately after the start
- WinRAR.exe (PID: 5584)
- msedge.exe (PID: 2928)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
222
Monitored processes
79
Malicious processes
3
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 652 | /s C:\Users\admin\AppData\Local\Temp\u8vjodv1.dll | C:\Windows\SysWOW64\regsvr32.exe | regsvr32.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
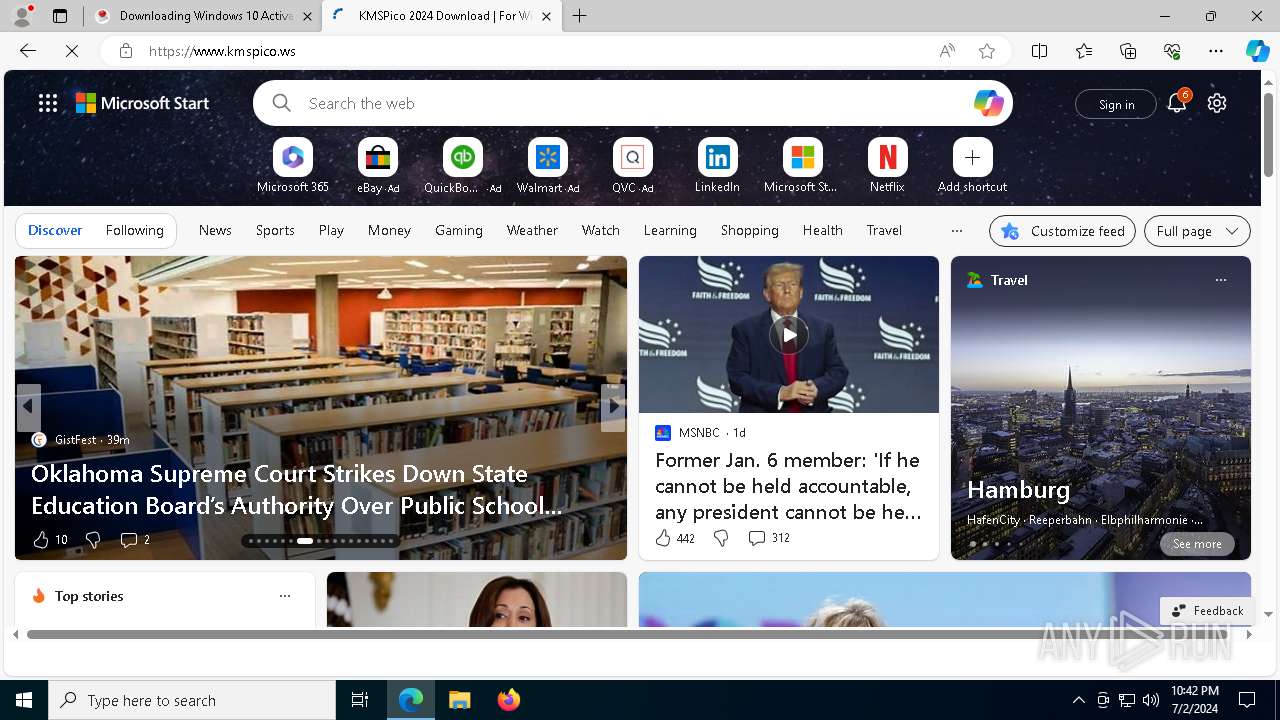
| 752 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" "https://kmspico.io/windows-10-activator/" | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 884 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=3672 --field-trial-handle=2316,i,1371236388331713282,8580266688076359051,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1064 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=gpu-process --disable-gpu-sandbox --use-gl=disabled --gpu-vendor-id=5140 --gpu-device-id=140 --gpu-sub-system-id=0 --gpu-revision=0 --gpu-driver-version=10.0.19041.3636 --no-appcompat-clear --gpu-preferences=WAAAAAAAAADoAAAMAAAAAAAAAAAAAAAAAABgAAAAAAA4AAAAAAAAAAAAAABEAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAGAAAAAAAAAAYAAAAAAAAAAgAAAAAAAAACAAAAAAAAAAIAAAAAAAAAA== --mojo-platform-channel-handle=5628 --field-trial-handle=2316,i,1371236388331713282,8580266688076359051,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1068 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=gpu-process --no-appcompat-clear --gpu-preferences=WAAAAAAAAADgAAAMAAAAAAAAAAAAAAAAAABgAAAAAAA4AAAAAAAAAAAAAAAEAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAGAAAAAAAAAAYAAAAAAAAAAgAAAAAAAAACAAAAAAAAAAIAAAAAAAAAA== --mojo-platform-channel-handle=2312 --field-trial-handle=2316,i,1371236388331713282,8580266688076359051,262144 --variations-seed-version /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1588 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=entity_extraction_service.mojom.Extractor --lang=en-US --service-sandbox-type=entity_extraction --onnx-enabled-for-ee --no-appcompat-clear --mojo-platform-channel-handle=5028 --field-trial-handle=2316,i,1371236388331713282,8580266688076359051,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1616 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=9100 --field-trial-handle=2316,i,1371236388331713282,8580266688076359051,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1760 | "C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe" --type=utility --utility-sub-type=winrt_app_id.mojom.WinrtAppIdService --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=4340 --field-trial-handle=2316,i,1371236388331713282,8580266688076359051,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: PWA Identity Proxy Host Exit code: 3221226029 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2292 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=asset_store.mojom.AssetStoreService --lang=en-US --service-sandbox-type=asset_store_service --no-appcompat-clear --mojo-platform-channel-handle=5116 --field-trial-handle=2316,i,1371236388331713282,8580266688076359051,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2344 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=32 --mojo-platform-channel-handle=6924 --field-trial-handle=2316,i,1371236388331713282,8580266688076359051,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
23 143
Read events
22 855
Write events
285
Delete events
3
Modification events
| (PID) Process: | (752) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (752) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (752) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (752) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (752) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (752) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\EdgeUpdate\ClientState\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (752) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (752) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge |
| Operation: | write | Name: | UsageStatsInSample |
Value: 1 | |||
| (PID) Process: | (752) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (752) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062} |
| Operation: | write | Name: | urlstats |
Value: 0 | |||
Executable files
141
Suspicious files
749
Text files
236
Unknown types
17
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 752 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF1adf55.TMP | — | |
MD5:— | SHA256:— | |||
| 752 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF1adf55.TMP | — | |
MD5:— | SHA256:— | |||
| 752 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF1adf55.TMP | — | |
MD5:— | SHA256:— | |||
| 752 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 752 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 752 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 752 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF1adf55.TMP | — | |
MD5:— | SHA256:— | |||
| 752 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF1adf93.TMP | — | |
MD5:— | SHA256:— | |||
| 752 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 752 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
54
TCP/UDP connections
202
DNS requests
204
Threats
18
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1544 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | unknown |
4656 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | unknown |
5784 | svchost.exe | GET | 200 | 23.48.23.143:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | unknown |
2276 | MoUsoCoreWorker.exe | GET | 200 | 23.48.23.143:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | unknown |
5784 | svchost.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | unknown |
1572 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | unknown |
6560 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | unknown |
1572 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | unknown |
7048 | svchost.exe | HEAD | 200 | 23.48.23.66:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/2f378d42-388a-4b82-807c-8f9c4280864c?P1=1720511868&P2=404&P3=2&P4=WuI8xZtgDq2AjAk9pQnLZdS4VvUR1UWnwZmVAw9HBBoTt%2b8YszLQnUbFg8FtDWaDRaWT8VCOU%2bMiW4NrkxaRLg%3d%3d | unknown | — | — | unknown |
7048 | svchost.exe | GET | 206 | 23.48.23.66:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/2f378d42-388a-4b82-807c-8f9c4280864c?P1=1720511868&P2=404&P3=2&P4=WuI8xZtgDq2AjAk9pQnLZdS4VvUR1UWnwZmVAw9HBBoTt%2b8YszLQnUbFg8FtDWaDRaWT8VCOU%2bMiW4NrkxaRLg%3d%3d | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4032 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
2276 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
752 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
5320 | msedge.exe | 35.208.62.162:443 | kmspico.io | GOOGLE | US | unknown |
5320 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5320 | msedge.exe | 204.79.197.239:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
5320 | msedge.exe | 13.107.6.158:443 | business.bing.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5320 | msedge.exe | 13.107.246.45:443 | edge-mobile-static.azureedge.net | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
5320 | msedge.exe | 23.48.23.51:443 | bzib.nelreports.net | Akamai International B.V. | DE | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.edge.skype.com |
| whitelisted |
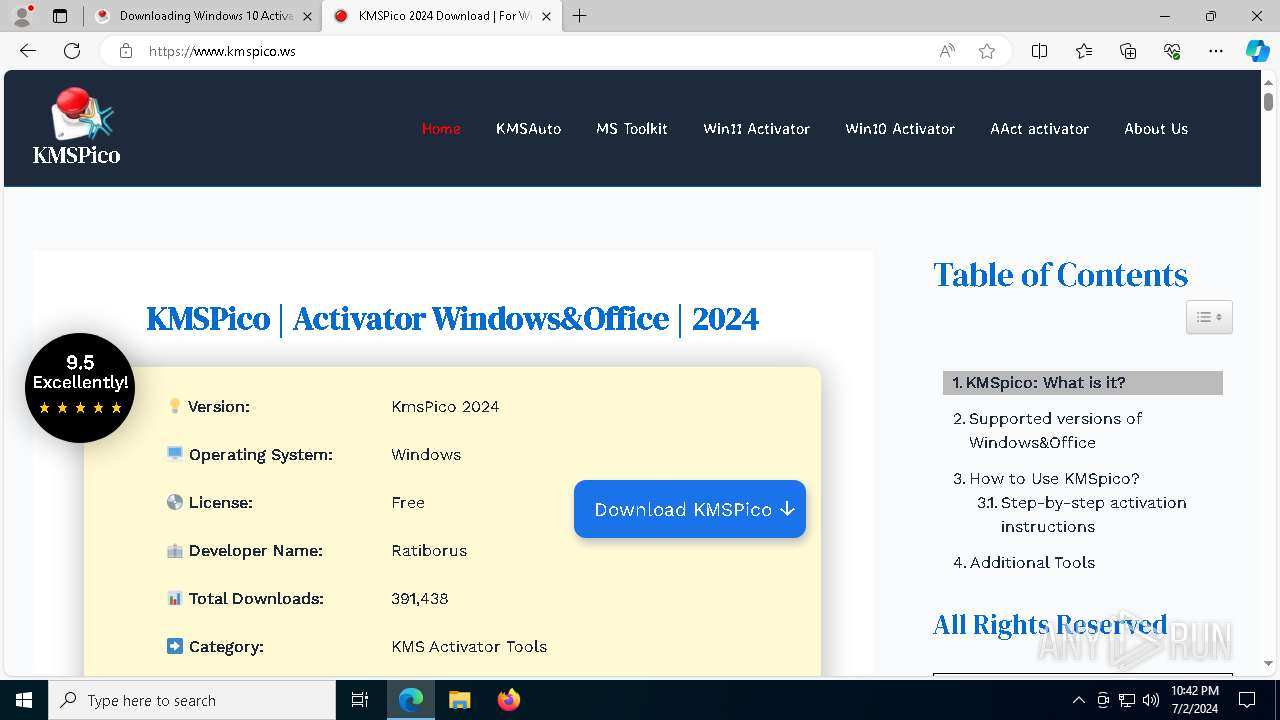
kmspico.io |
| malicious |
edge.microsoft.com |
| whitelisted |
business.bing.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| unknown |
bzib.nelreports.net |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
www.bing.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
5320 | msedge.exe | Potentially Bad Traffic | ET DNS Query for .cc TLD |
5320 | msedge.exe | Potentially Bad Traffic | ET DNS Query for .cc TLD |
5320 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |
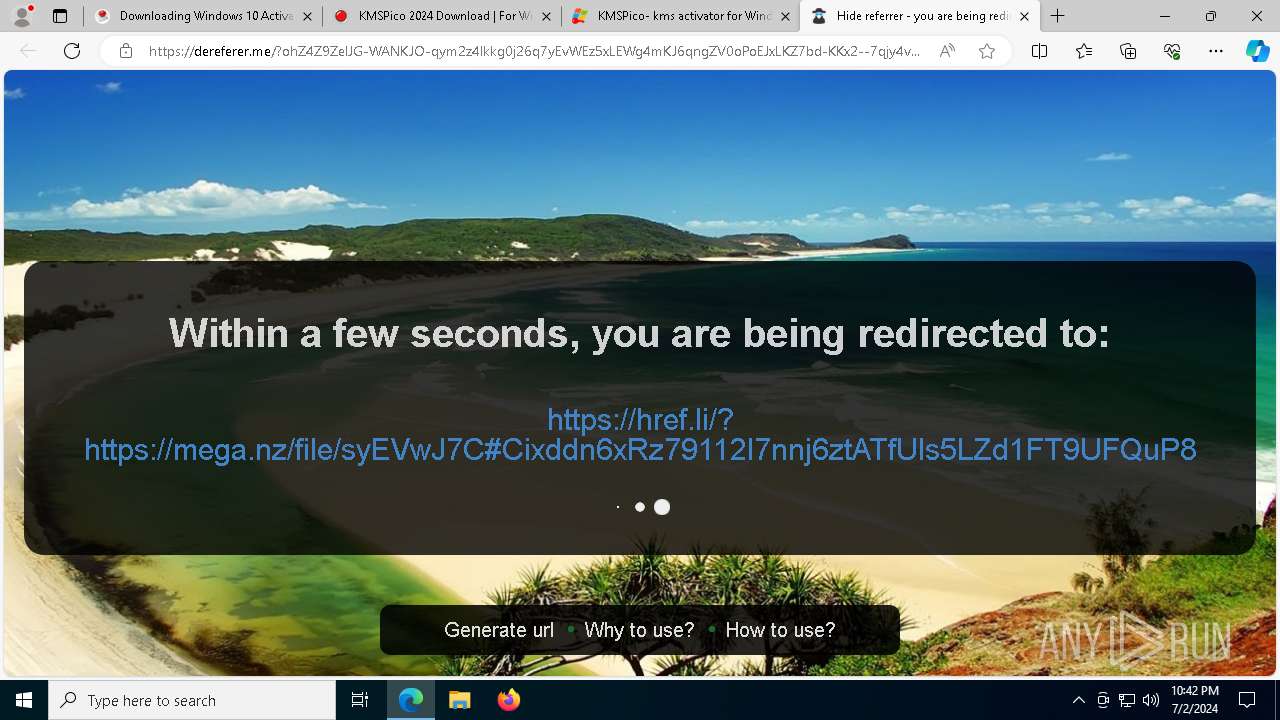
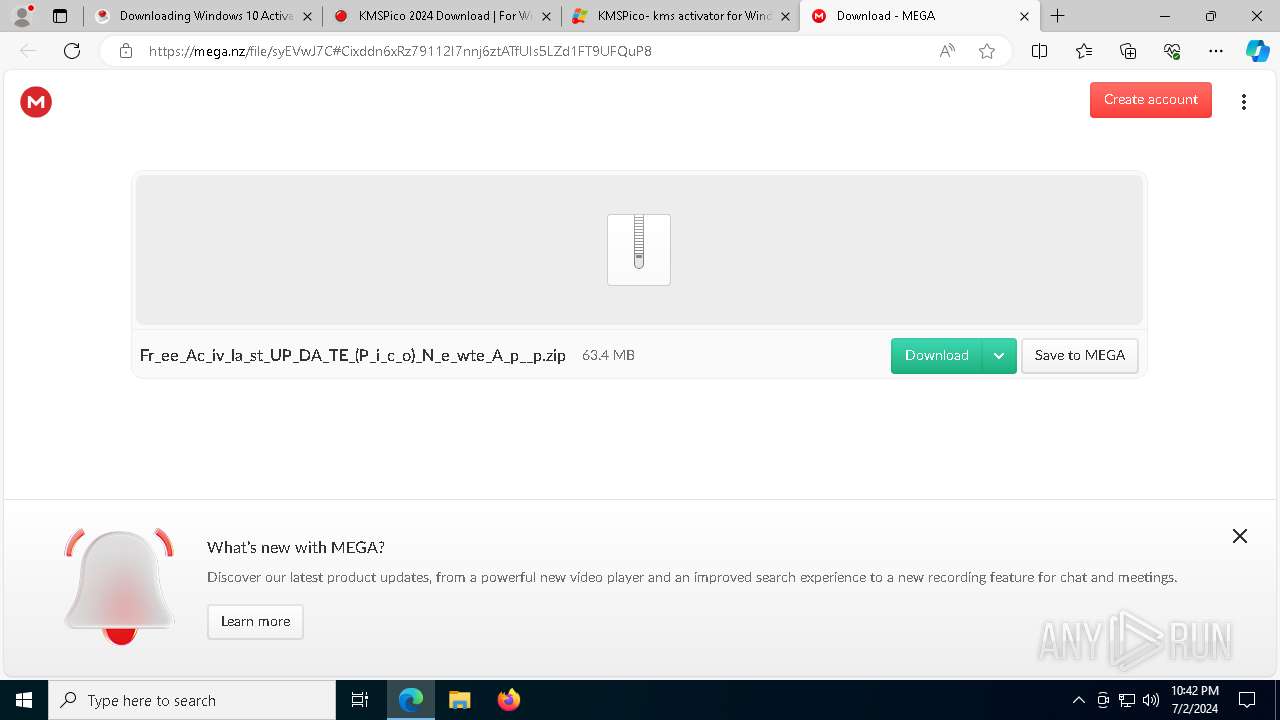
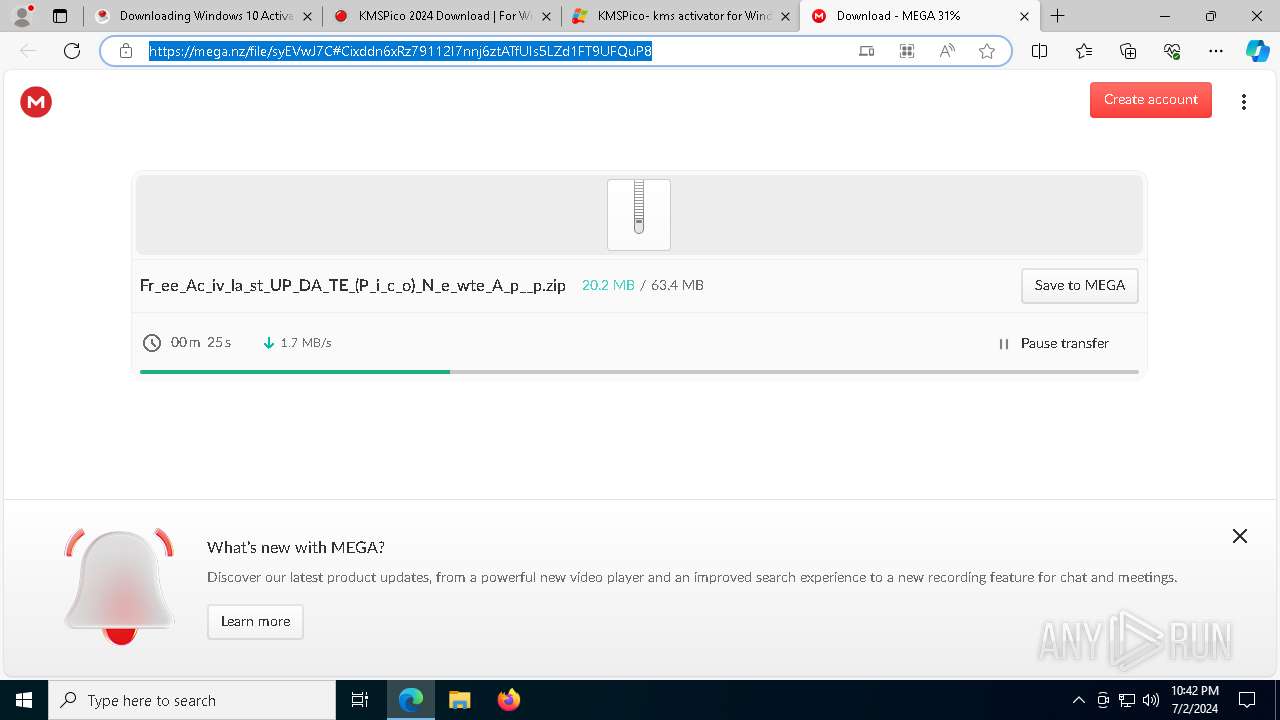
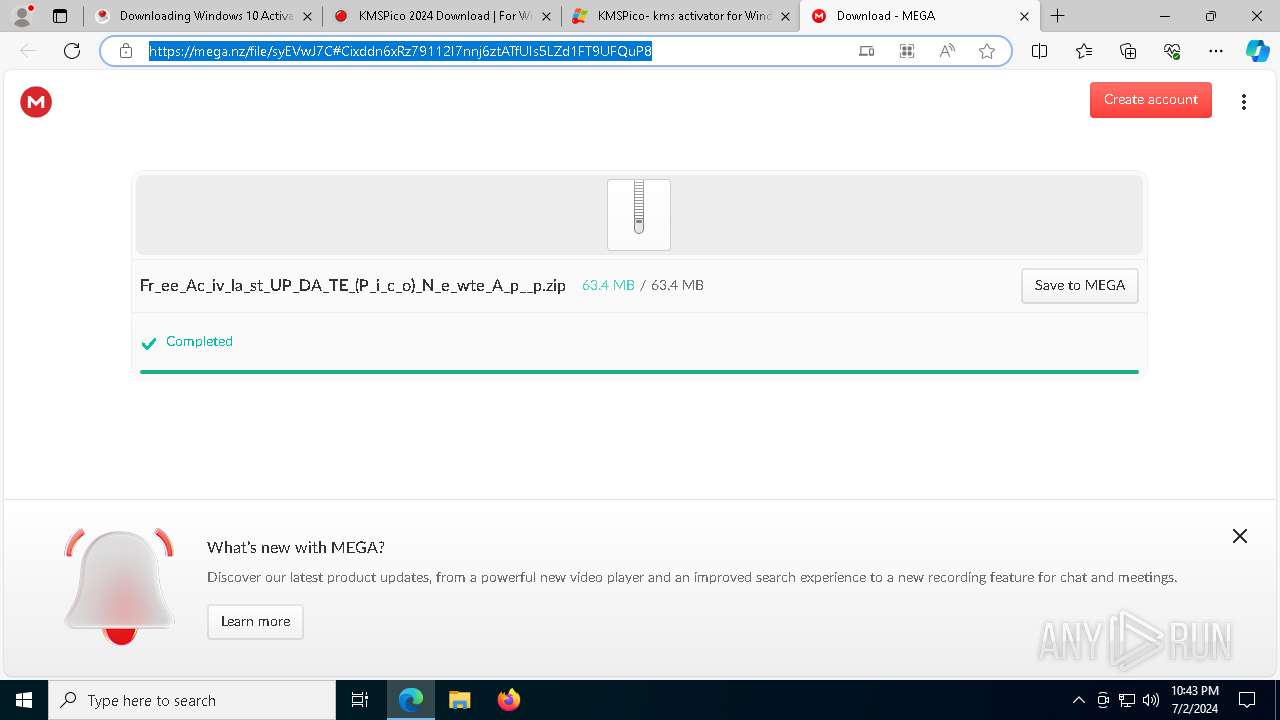
5320 | msedge.exe | Misc activity | ET INFO File Sharing Related Domain in DNS Lookup (mega .nz) |
5320 | msedge.exe | Misc activity | ET INFO File Sharing Related Domain in DNS Lookup (mega .nz) |
5320 | msedge.exe | Misc activity | ET INFO File Sharing Domain Observed in TLS SNI (mega .nz) |
5320 | msedge.exe | Misc activity | ET INFO File Sharing Domain Observed in TLS SNI (mega .nz) |
5320 | msedge.exe | Misc activity | ET INFO Observed DNS Query to Filesharing Service (mega .co .nz) |
5320 | msedge.exe | Misc activity | ET INFO Observed DNS Query to Filesharing Service (mega .co .nz) |
5320 | msedge.exe | Misc activity | ET INFO File Sharing Domain Observed in TLS SNI (mega .nz) |
3 ETPRO signatures available at the full report