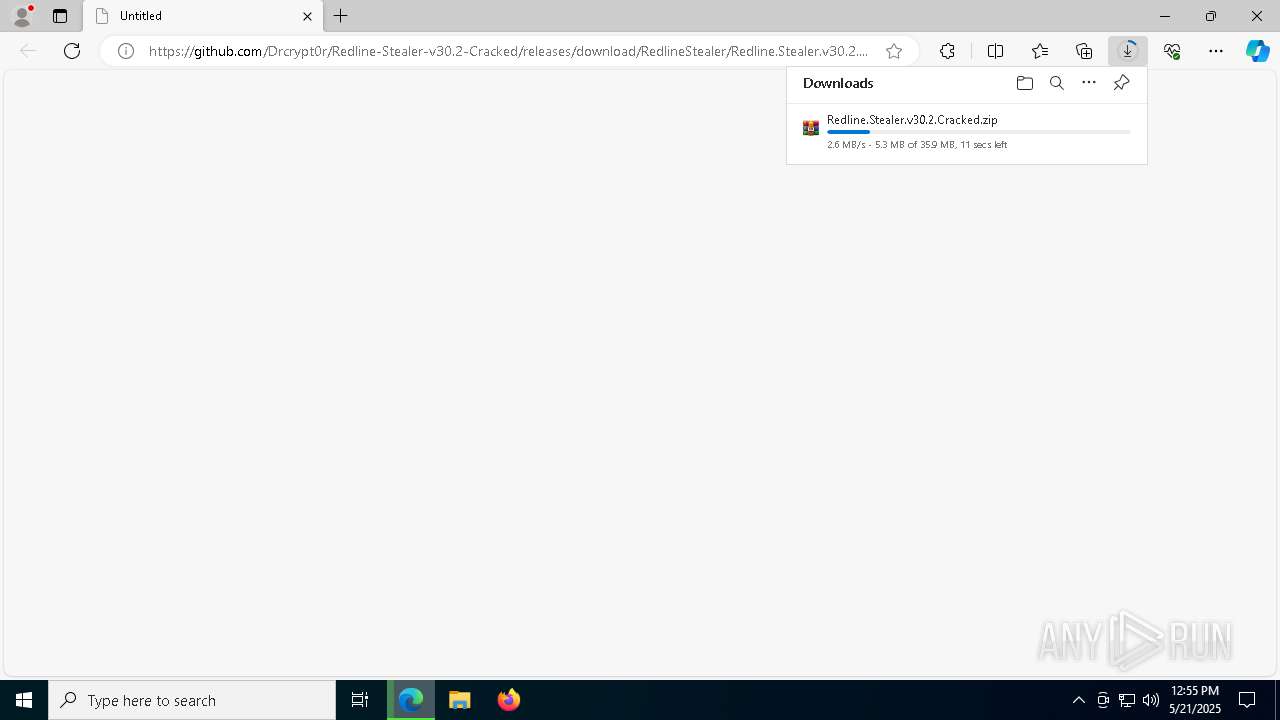
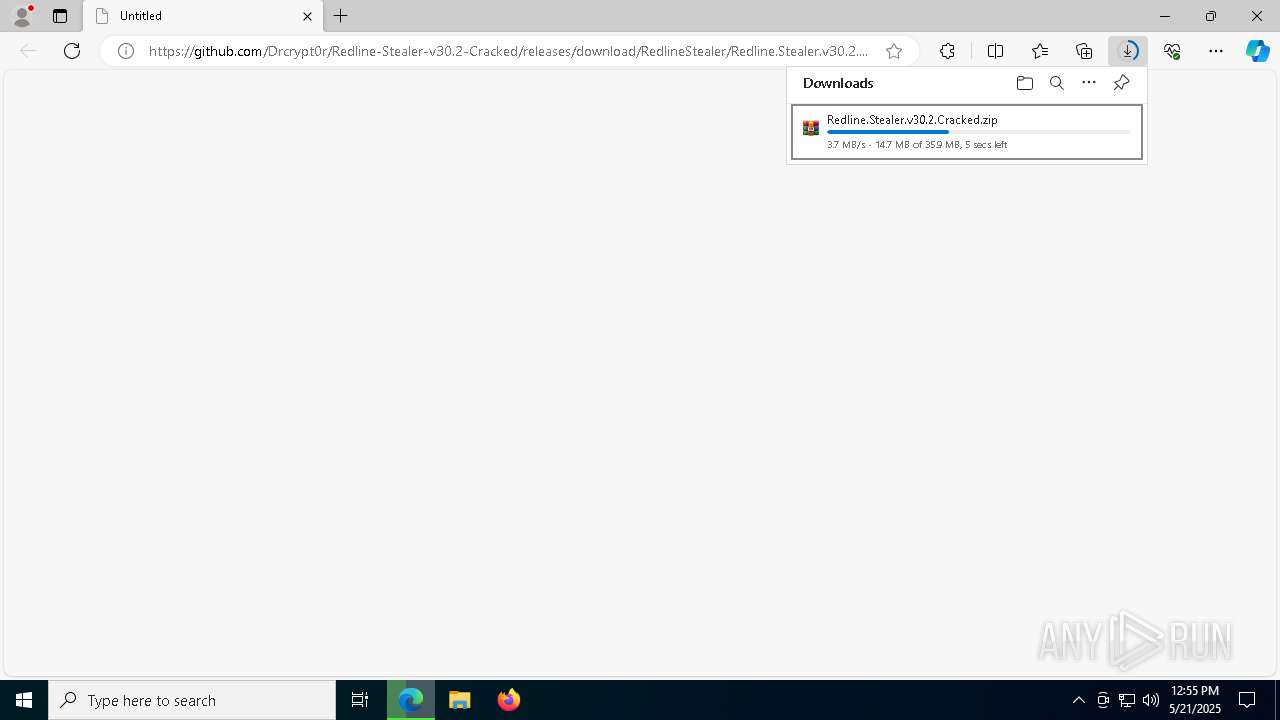
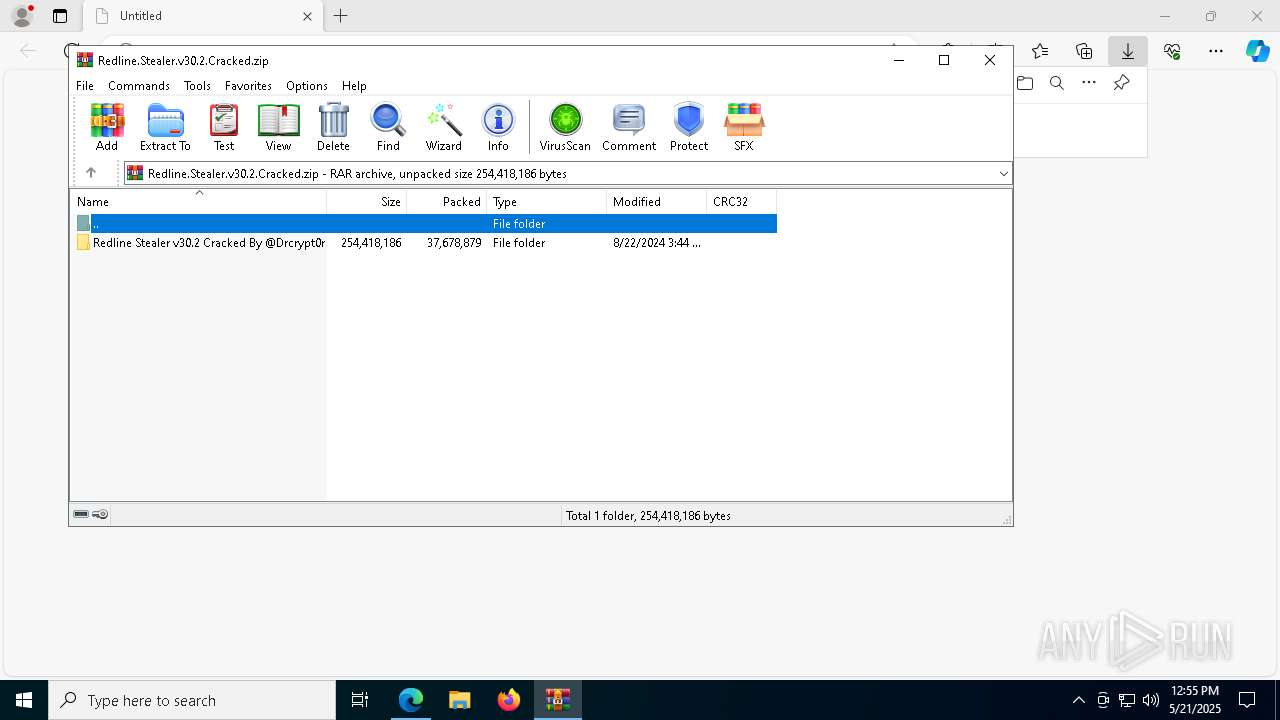
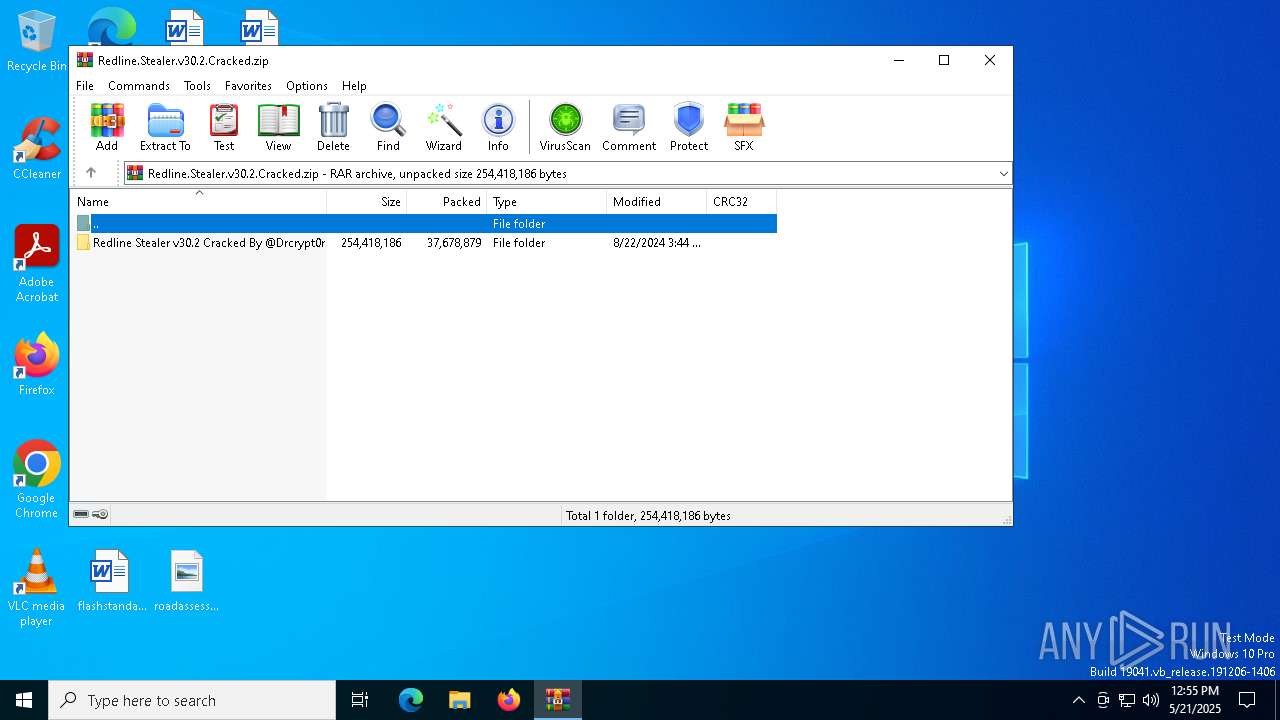
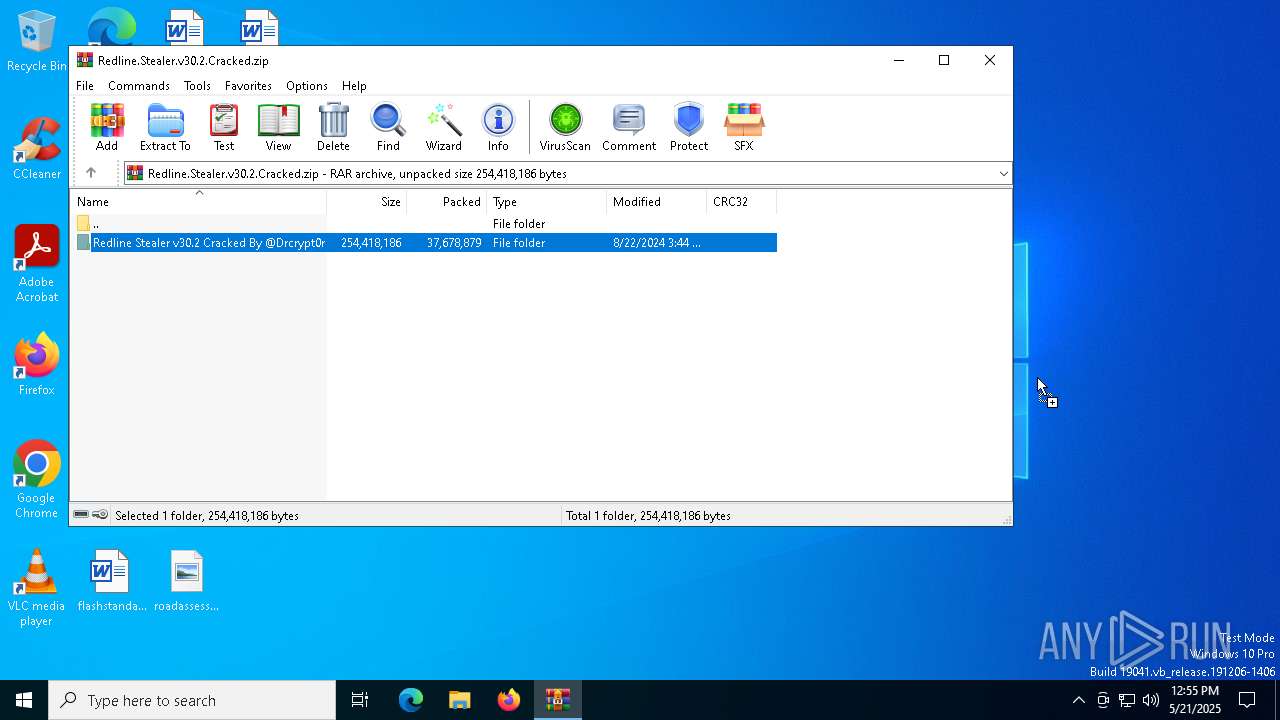
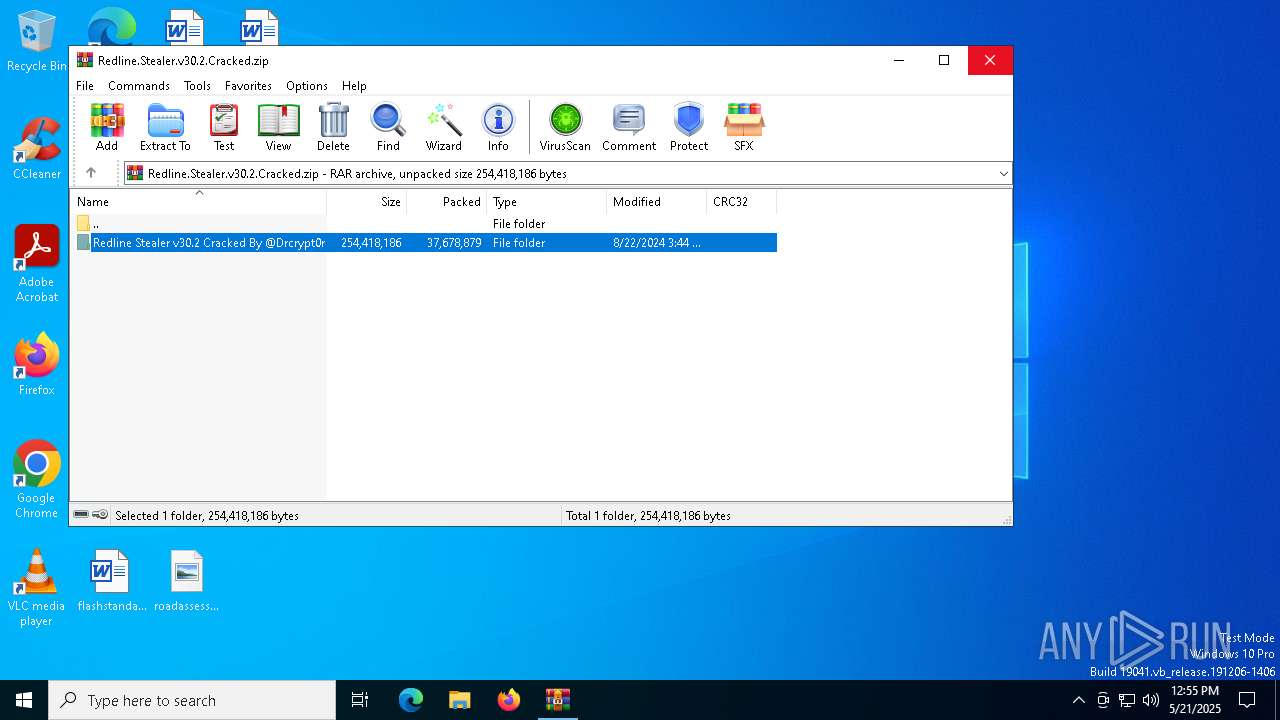
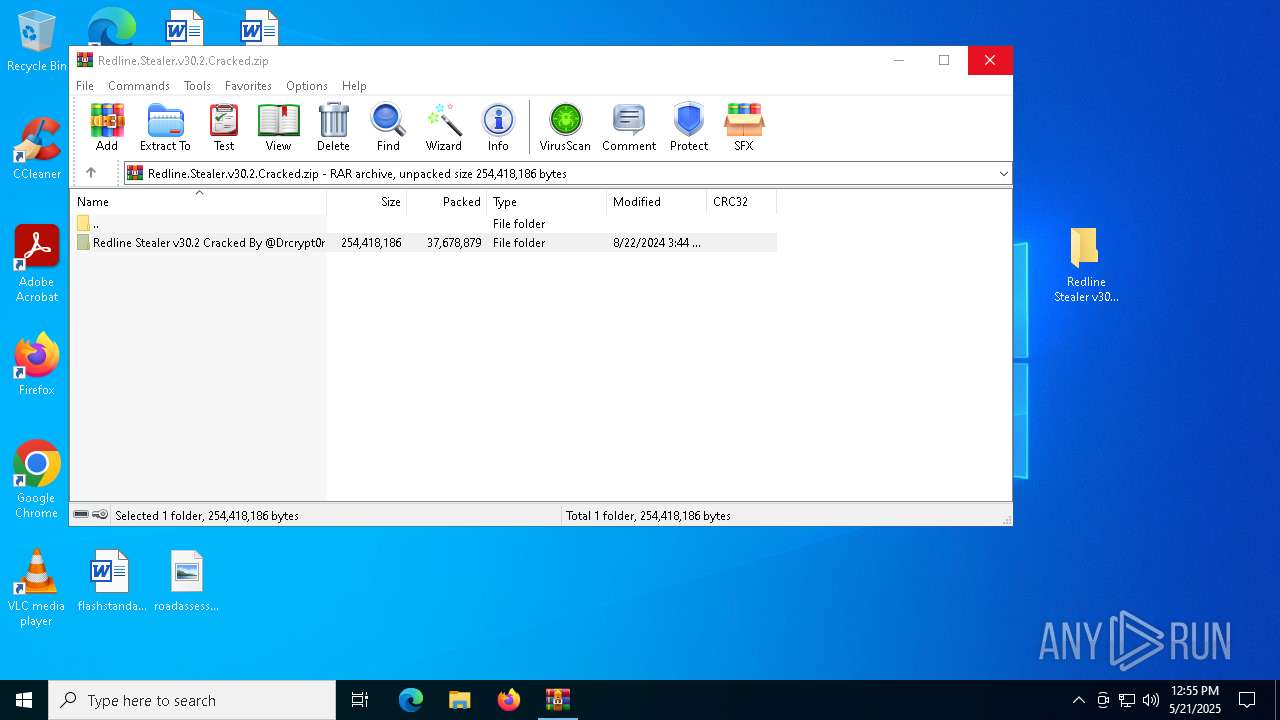
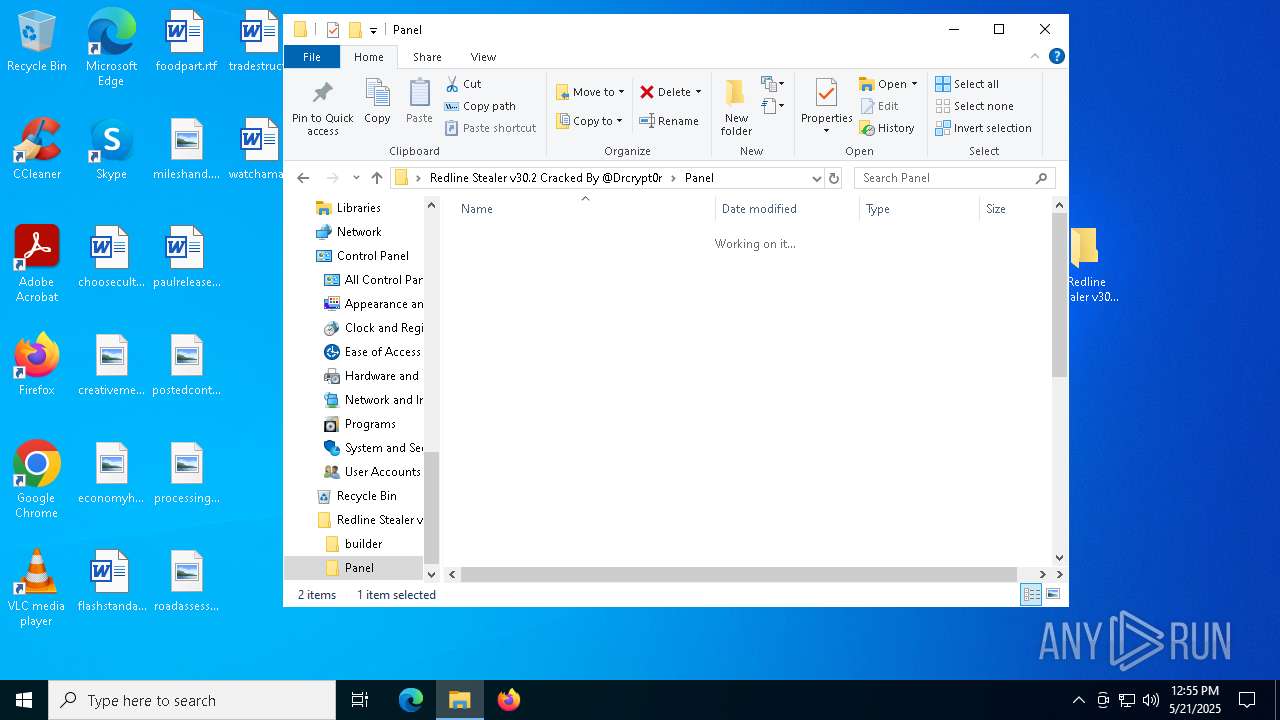
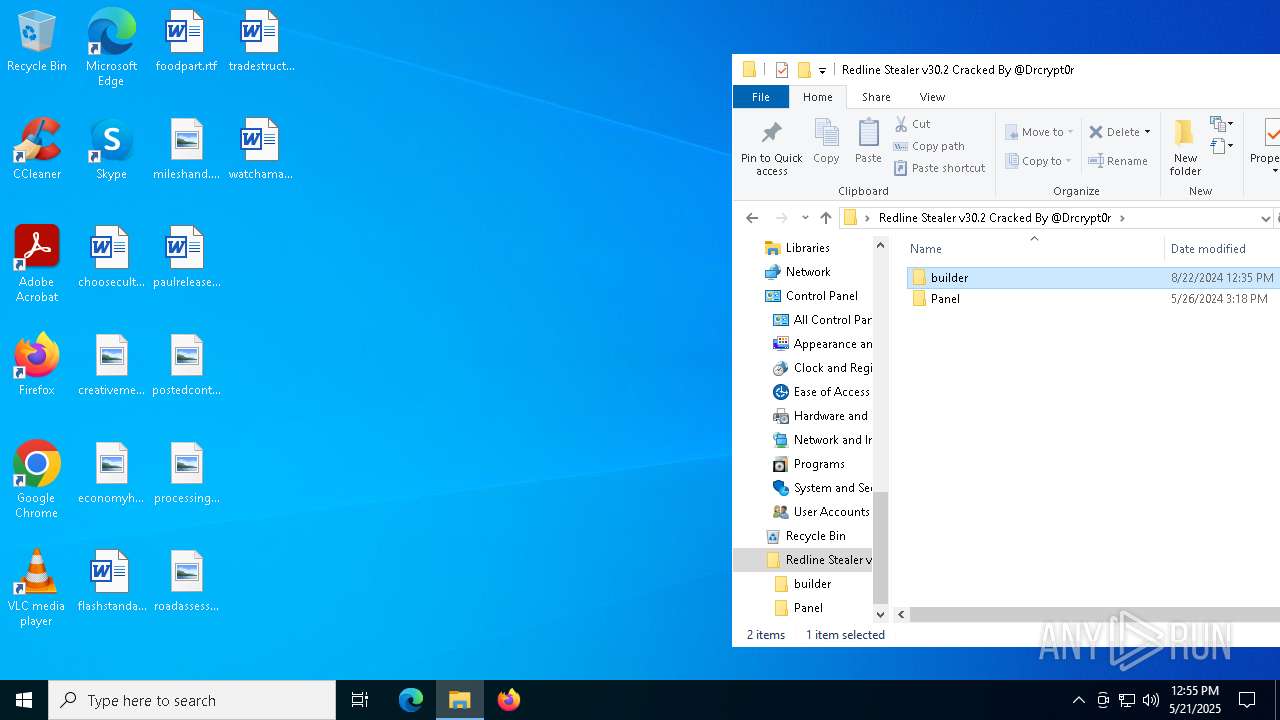
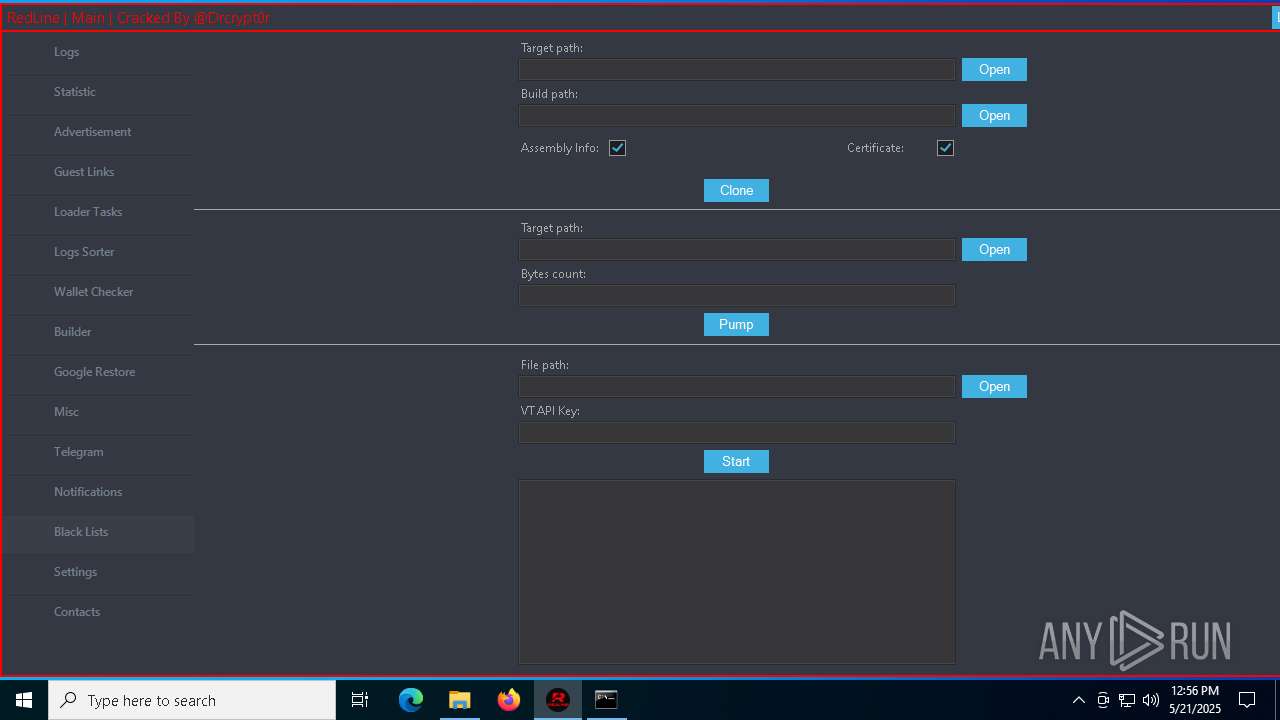
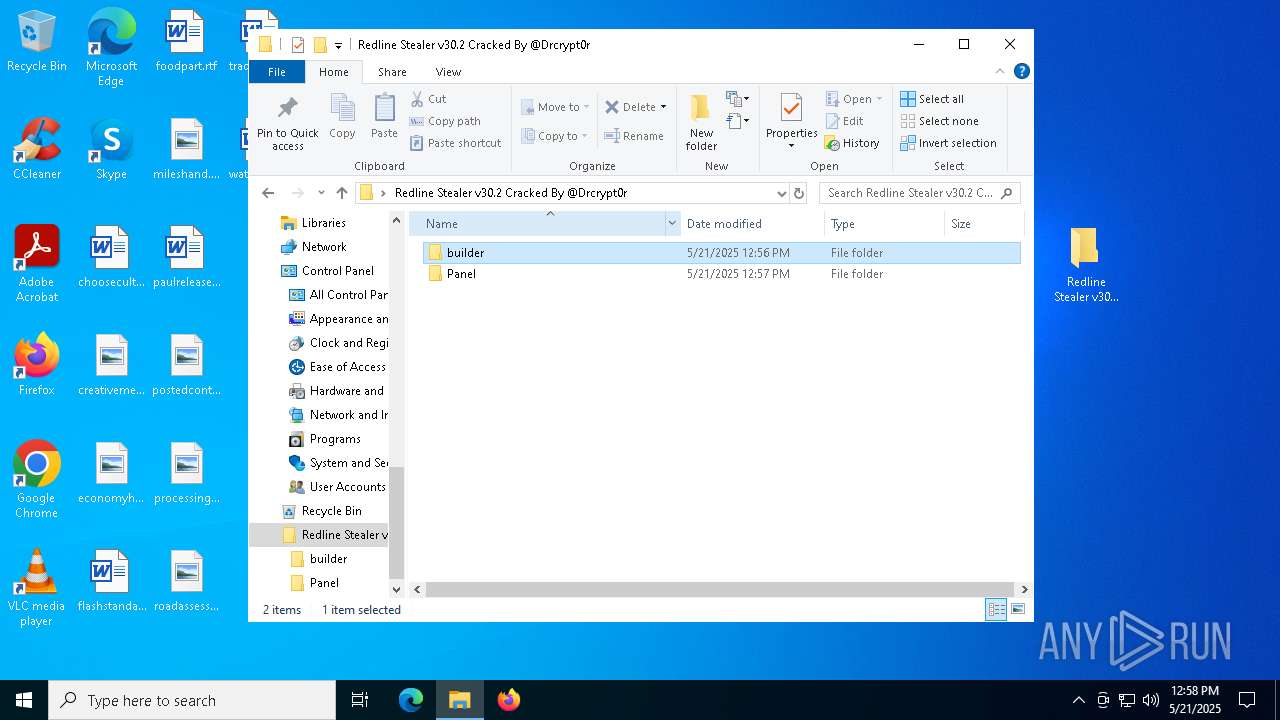
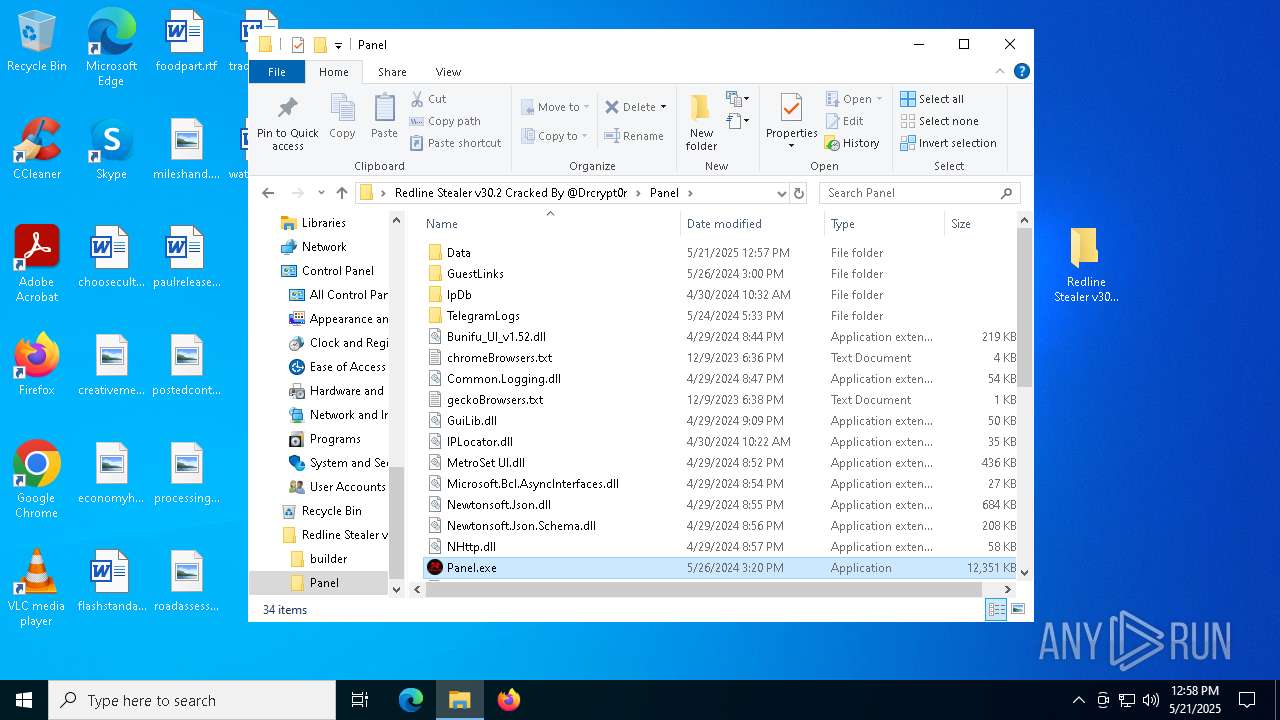
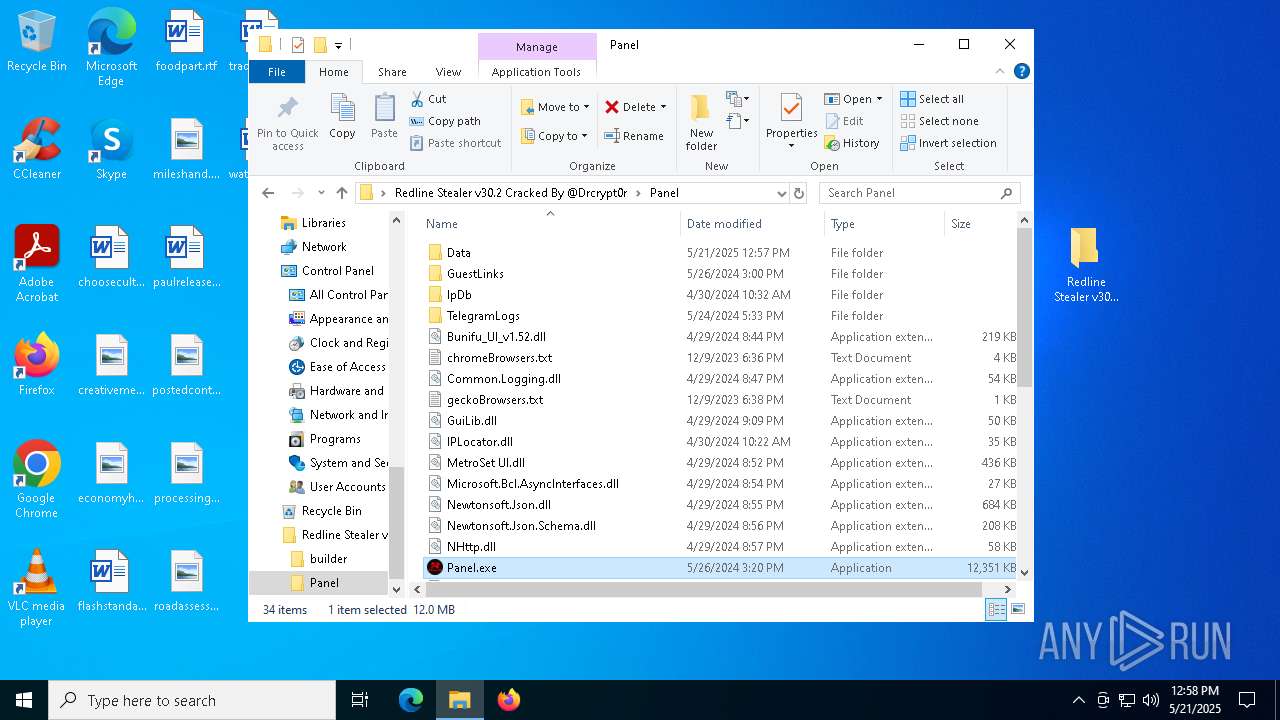
| URL: | https://github.com/Drcrypt0r/Redline-Stealer-v30.2-Cracked/releases/download/RedlineStealer/Redline.Stealer.v30.2.Cracked.zip |
| Full analysis: | https://app.any.run/tasks/68cbecd9-859e-45ff-bc62-036cc51b0efd |
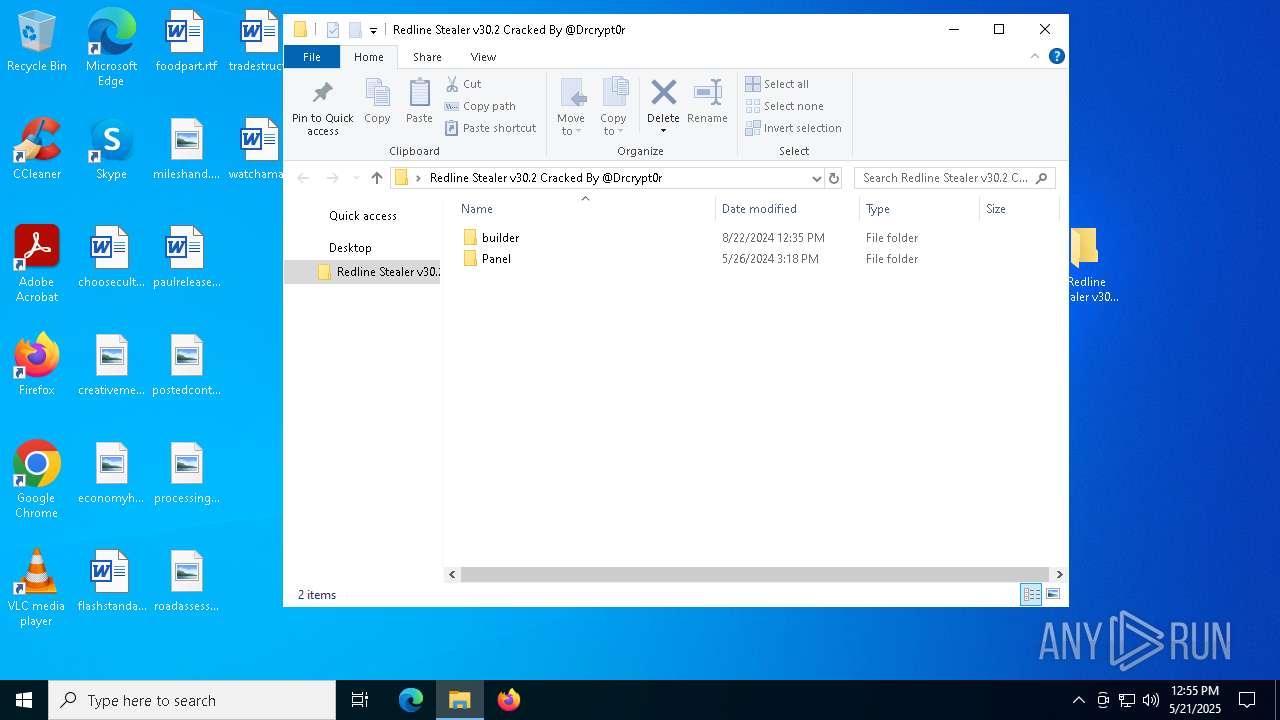
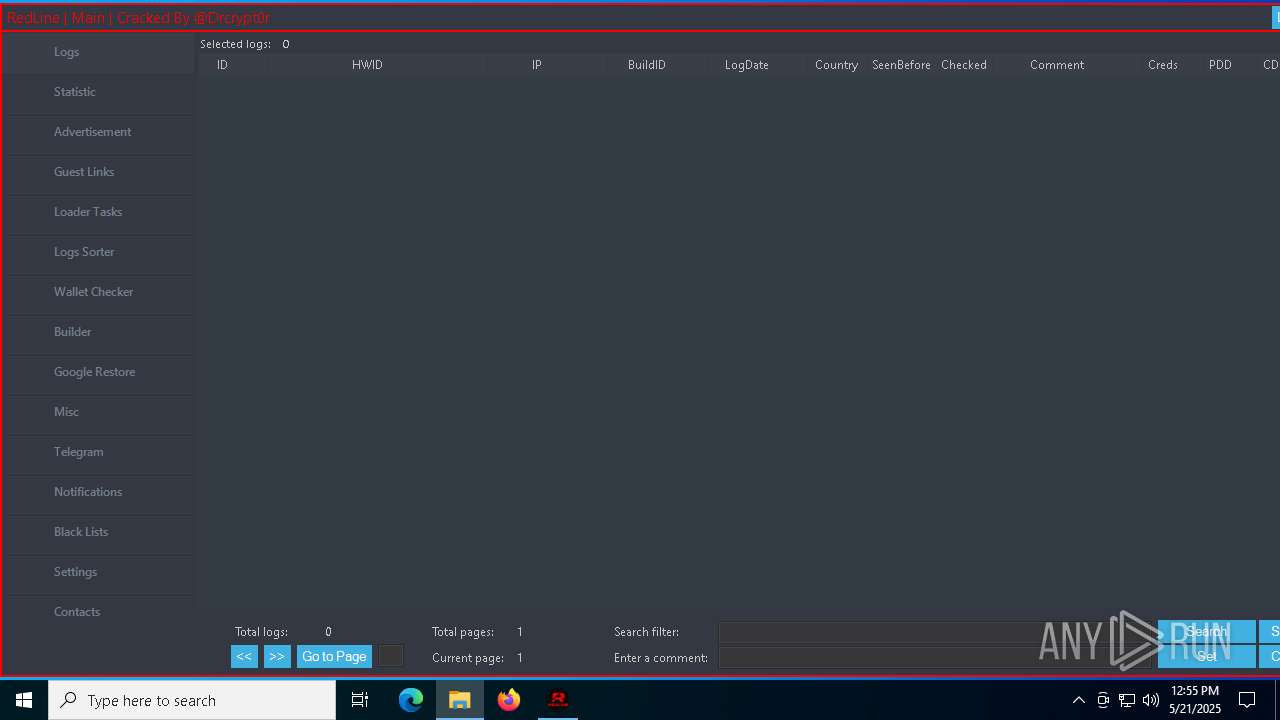
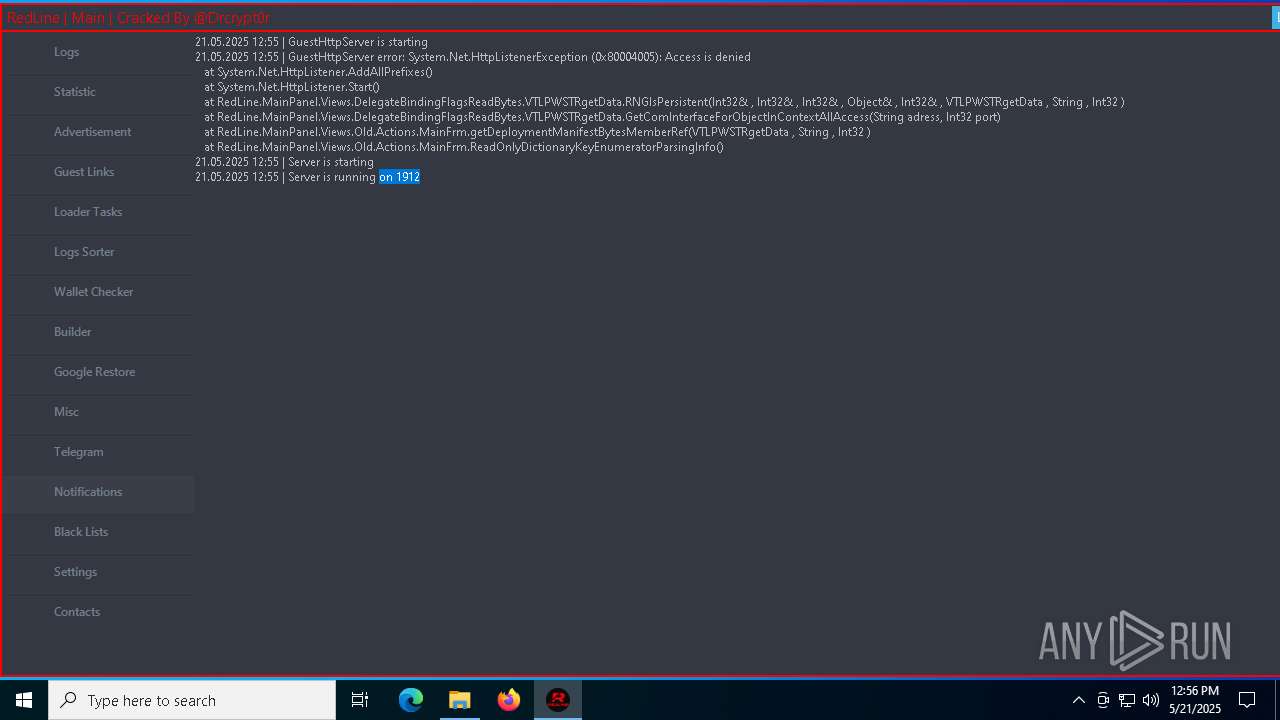
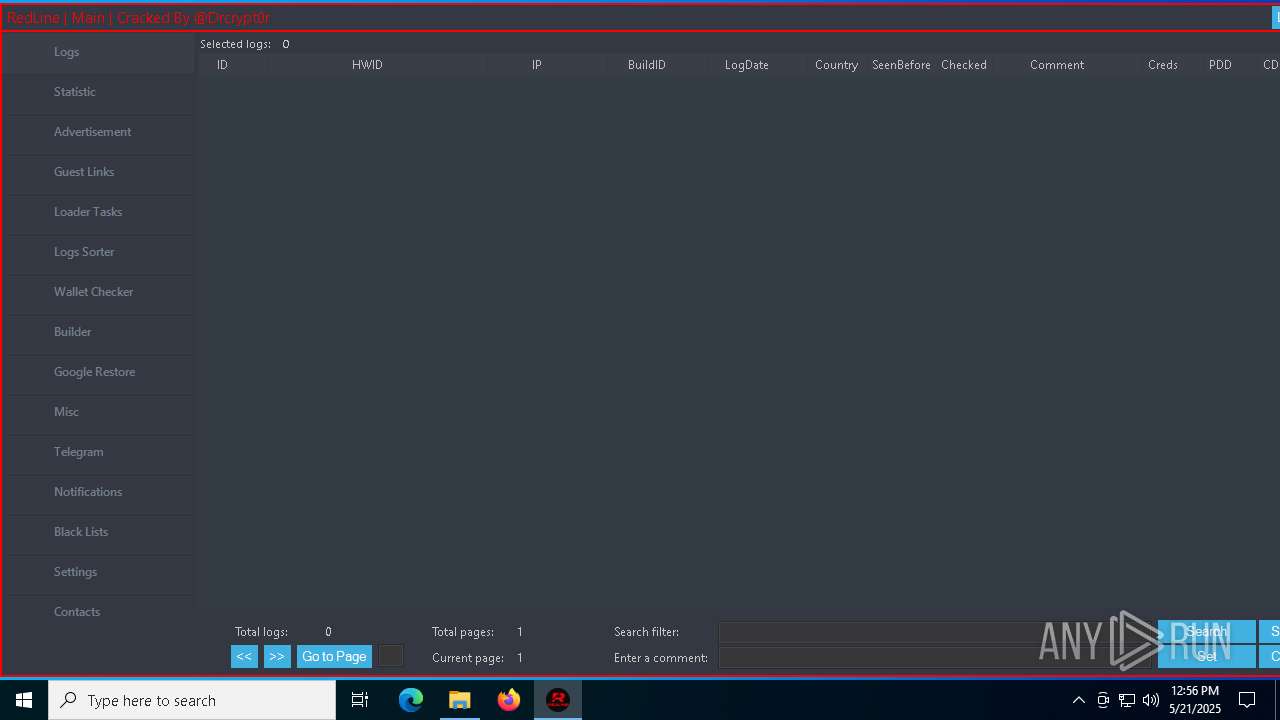
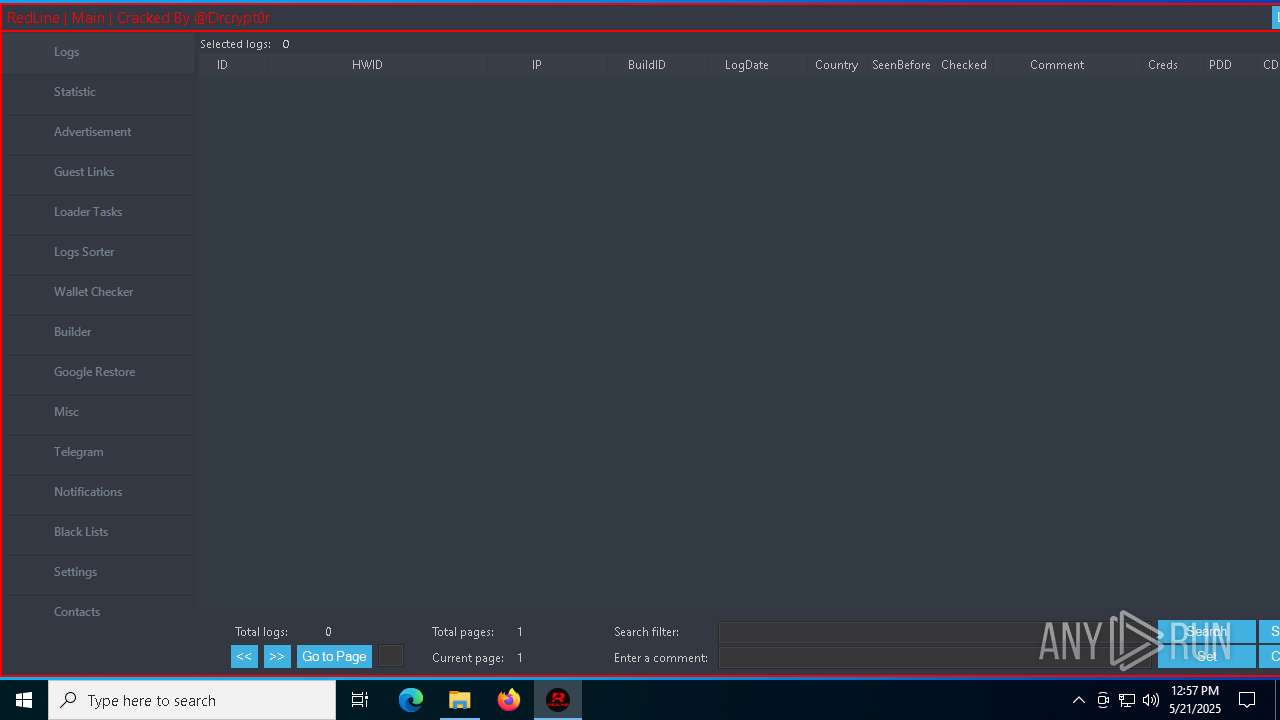
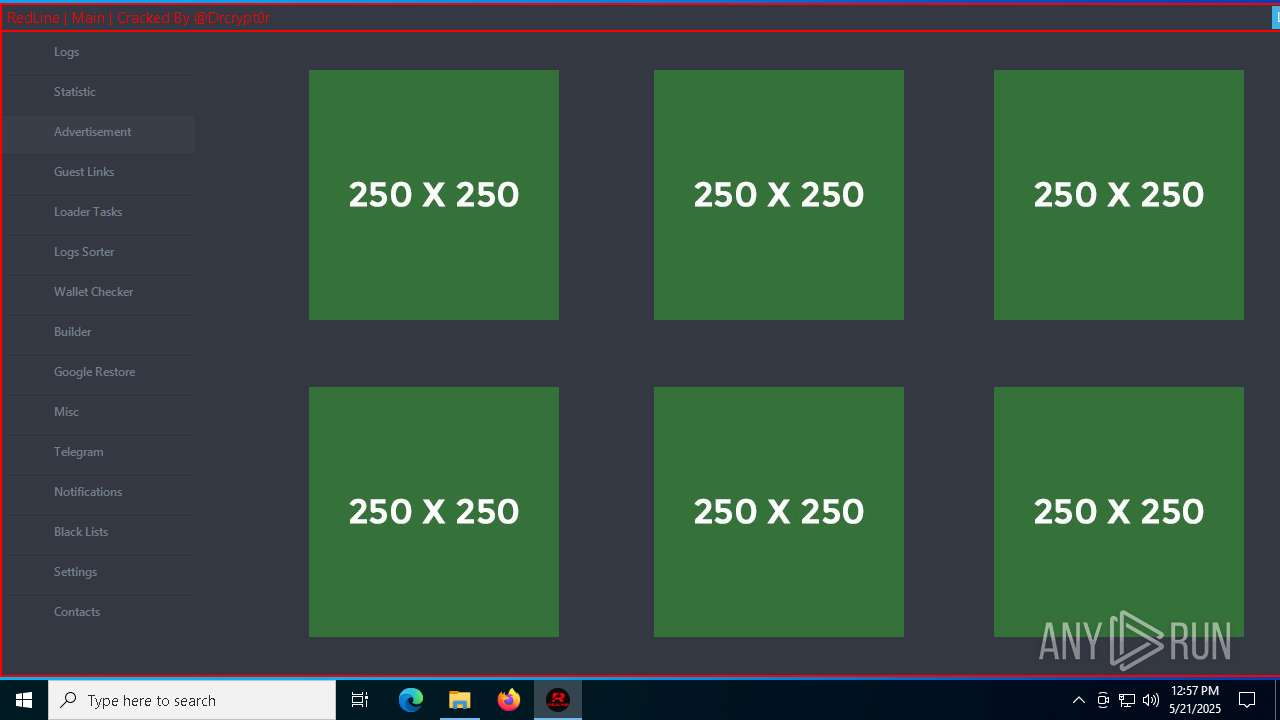
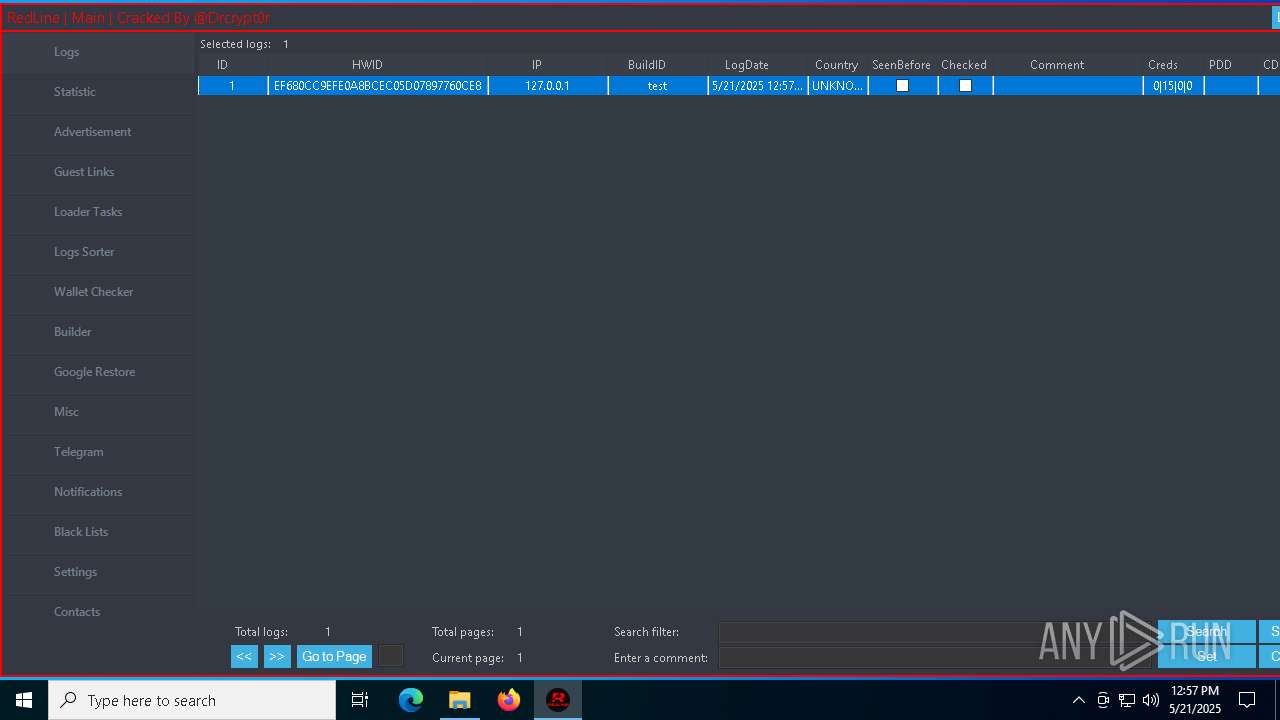
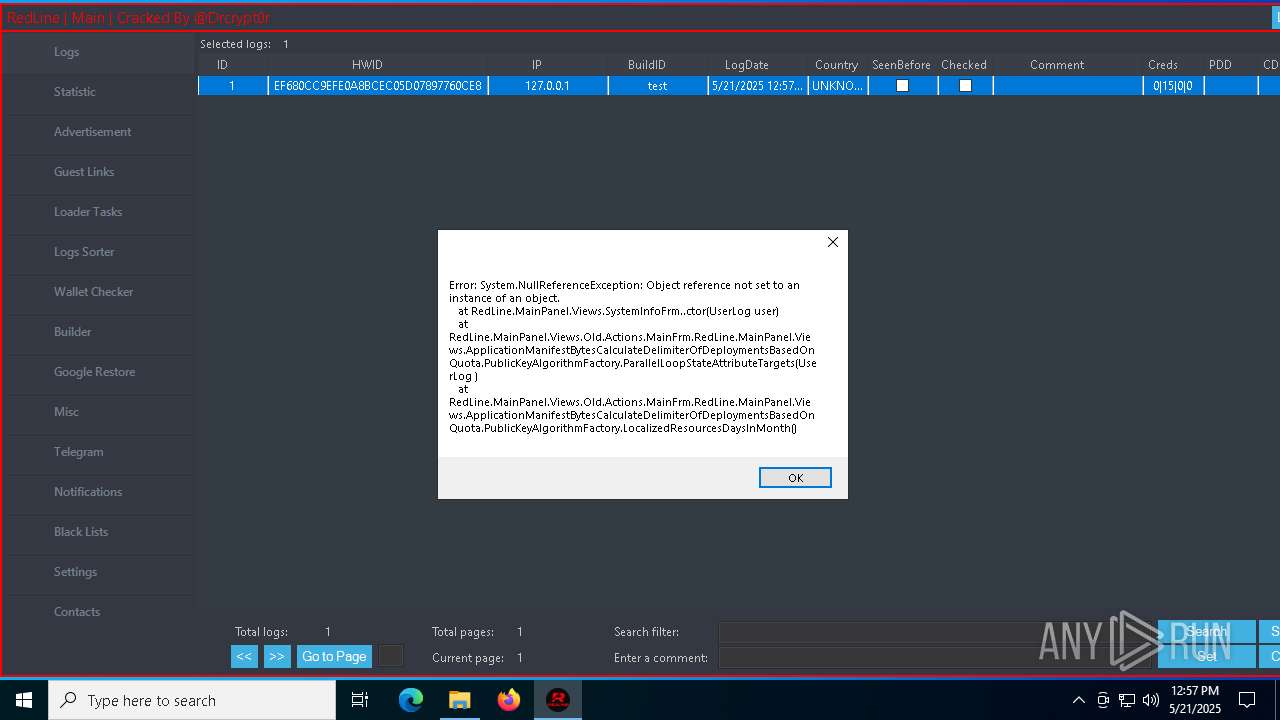
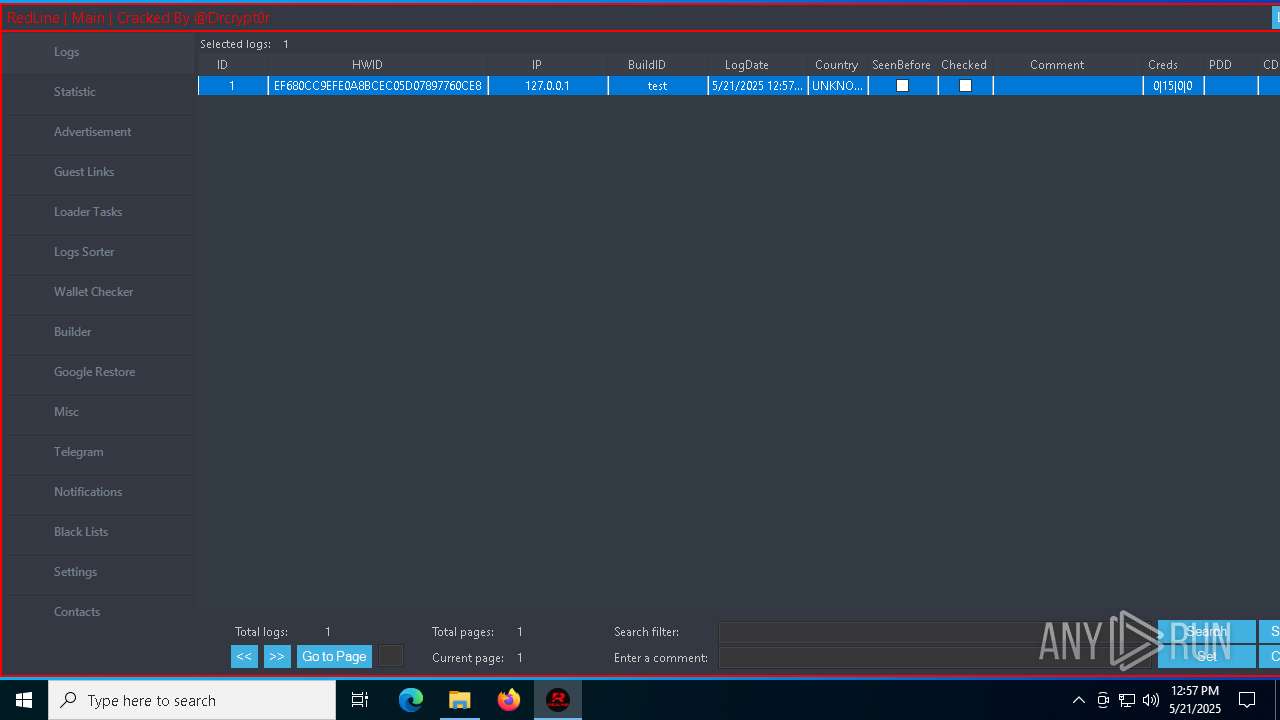
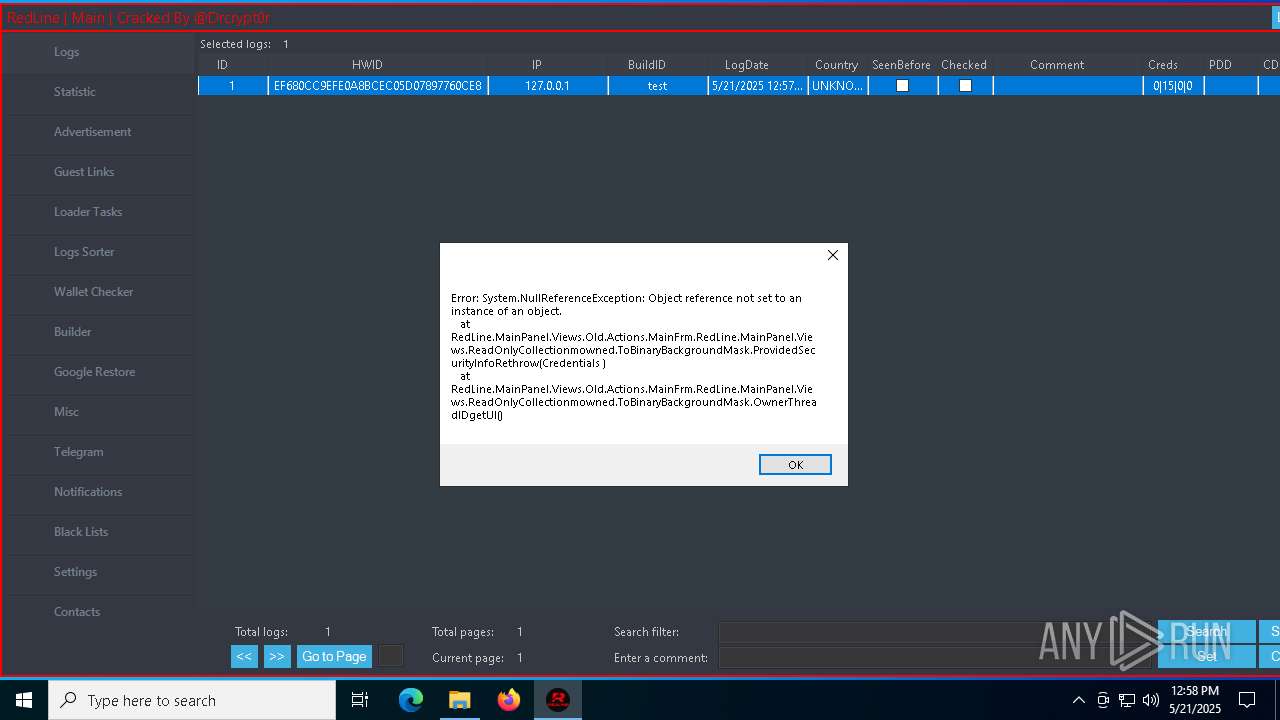
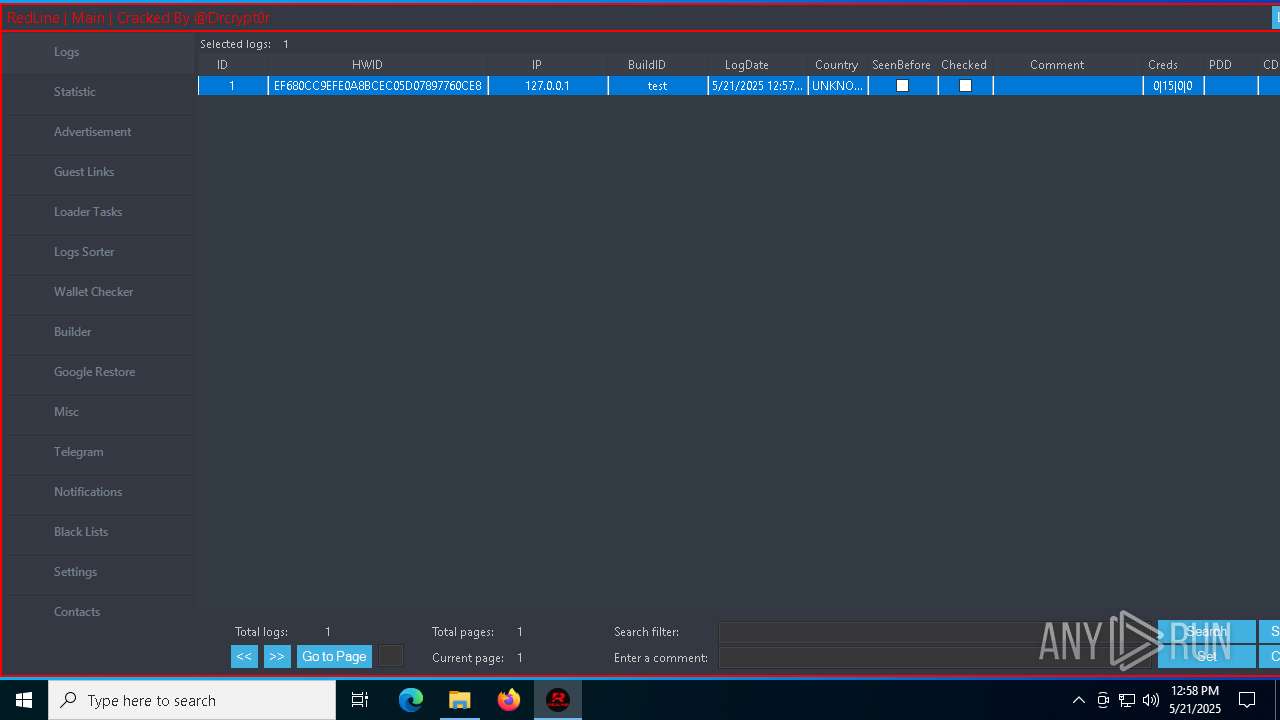
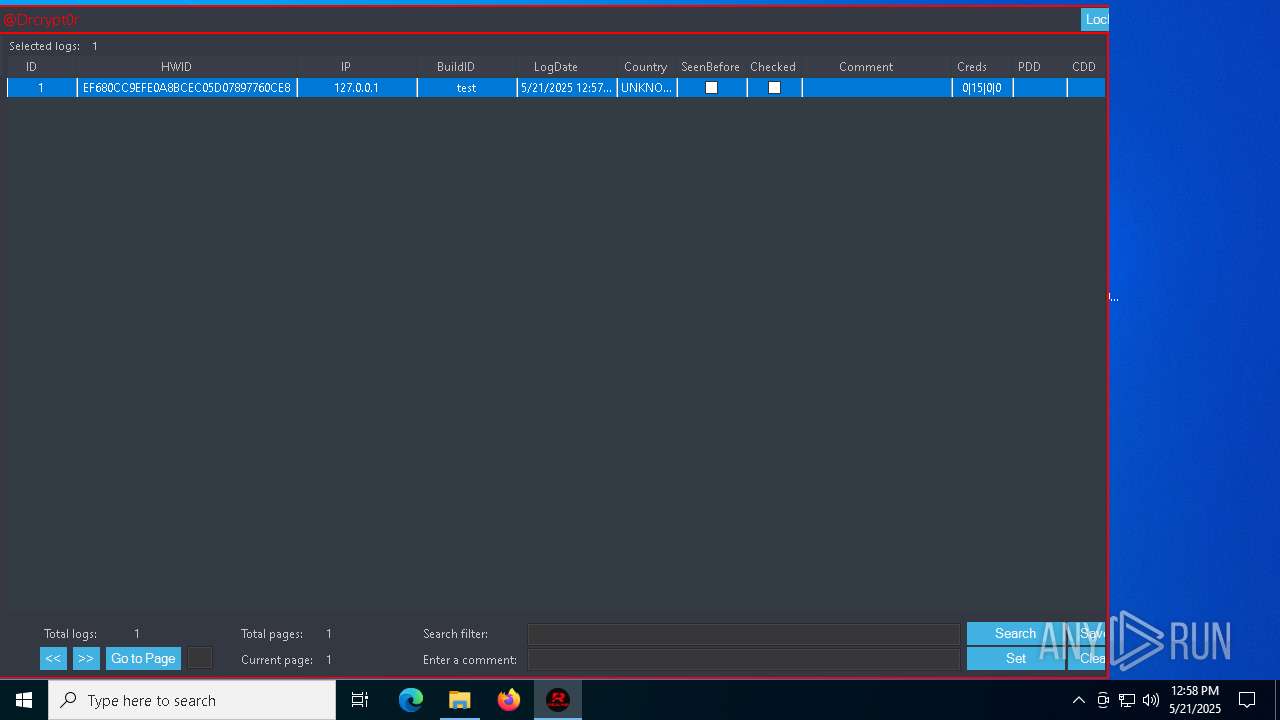
| Verdict: | Malicious activity |
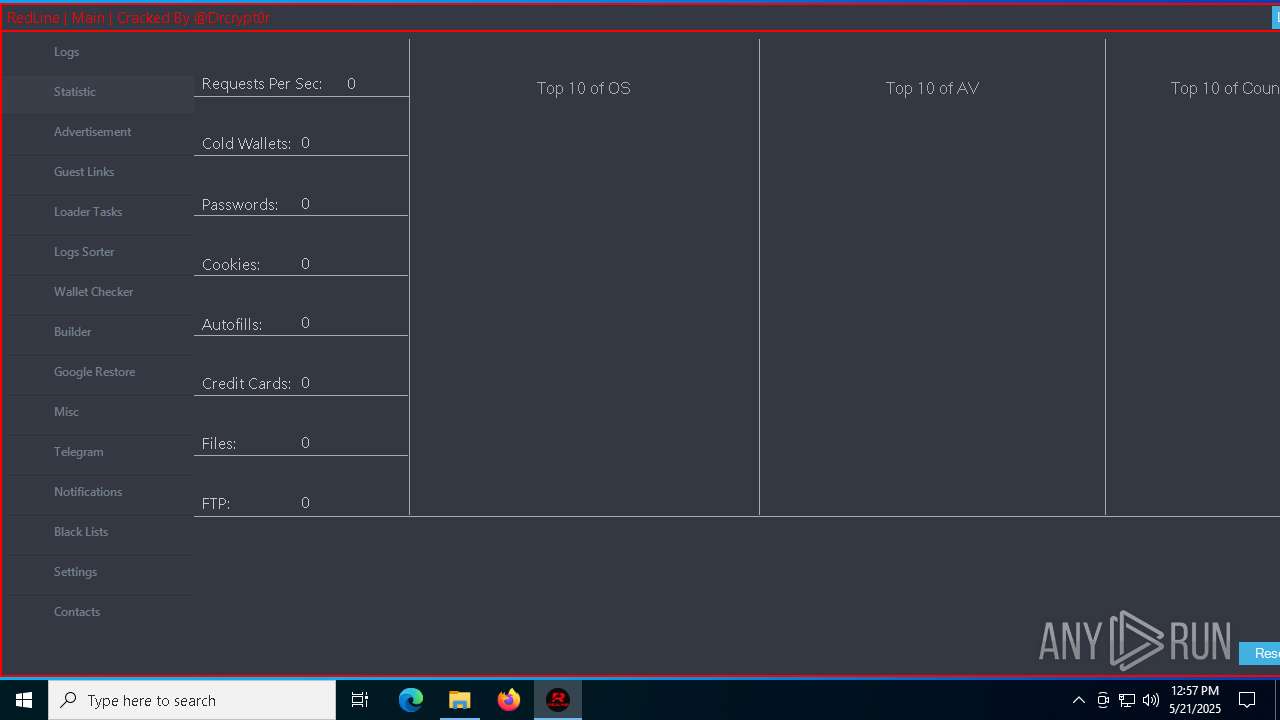
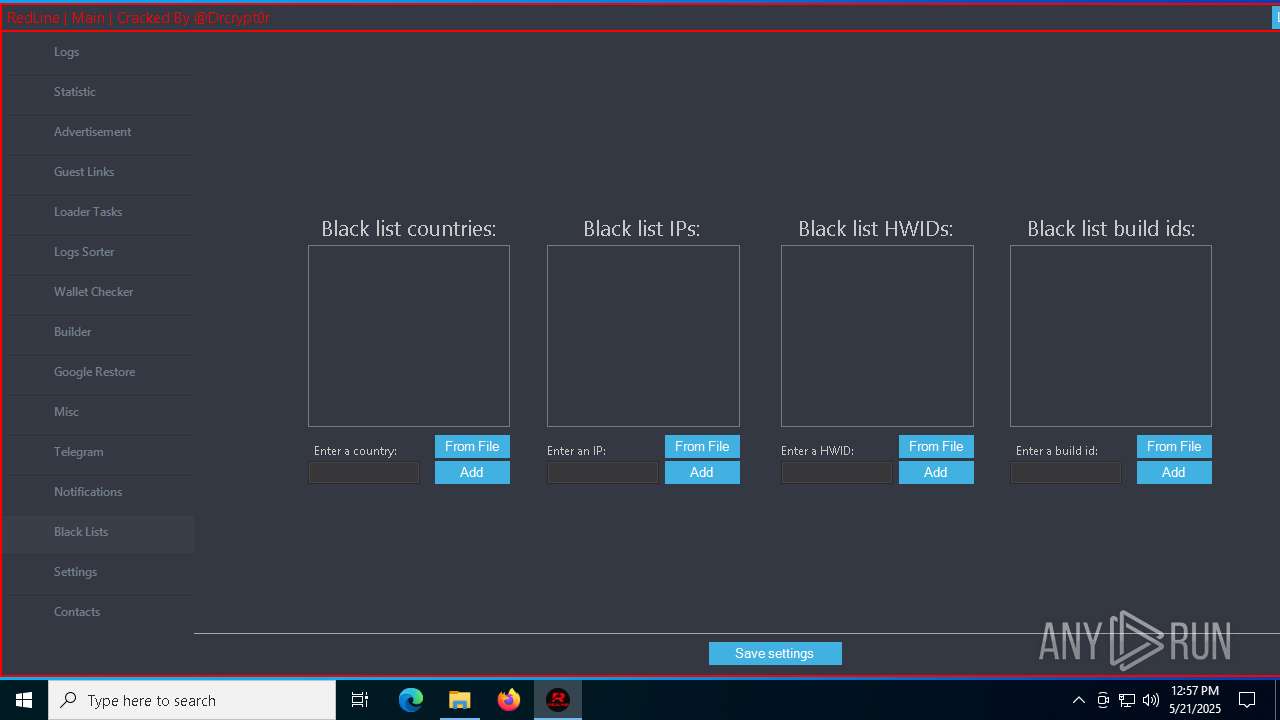
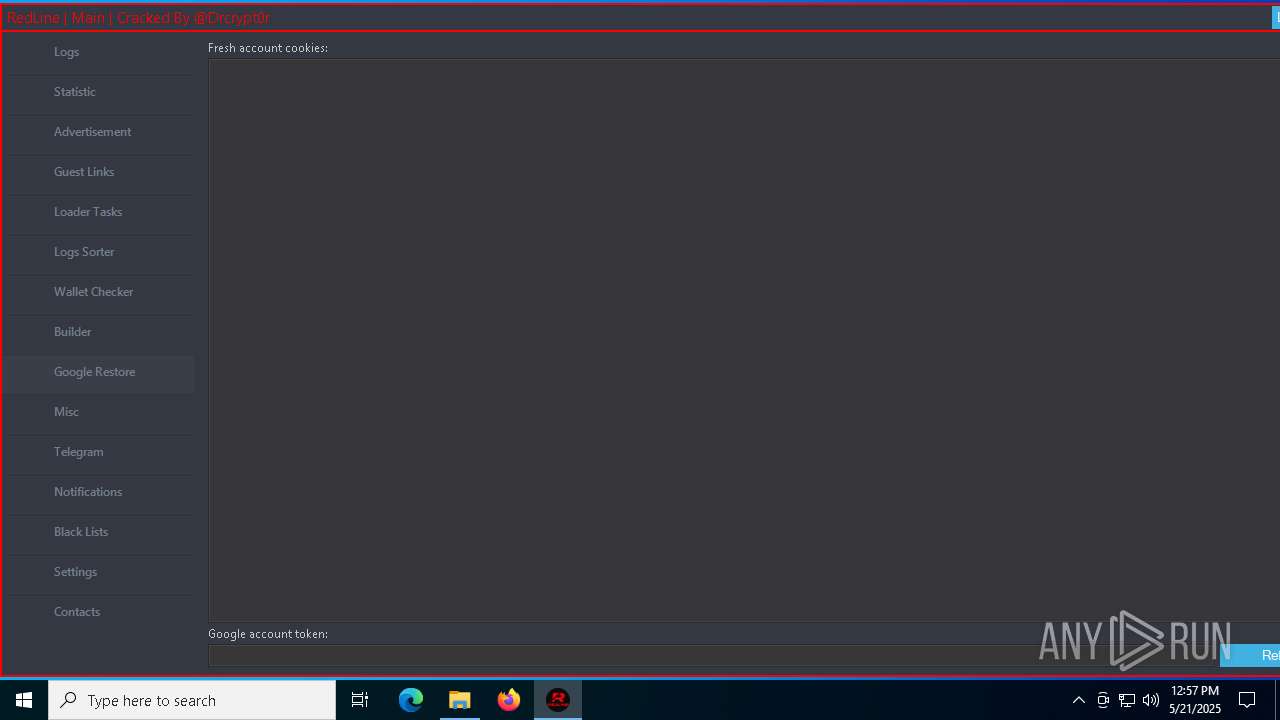
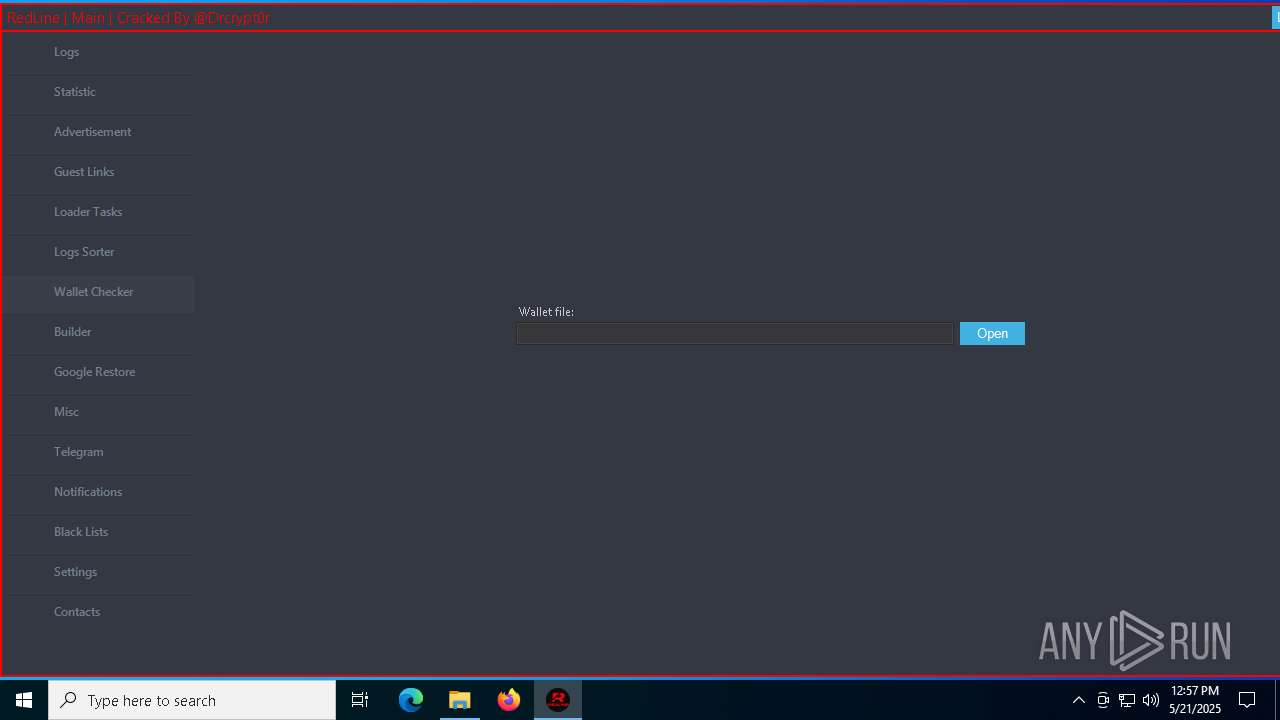
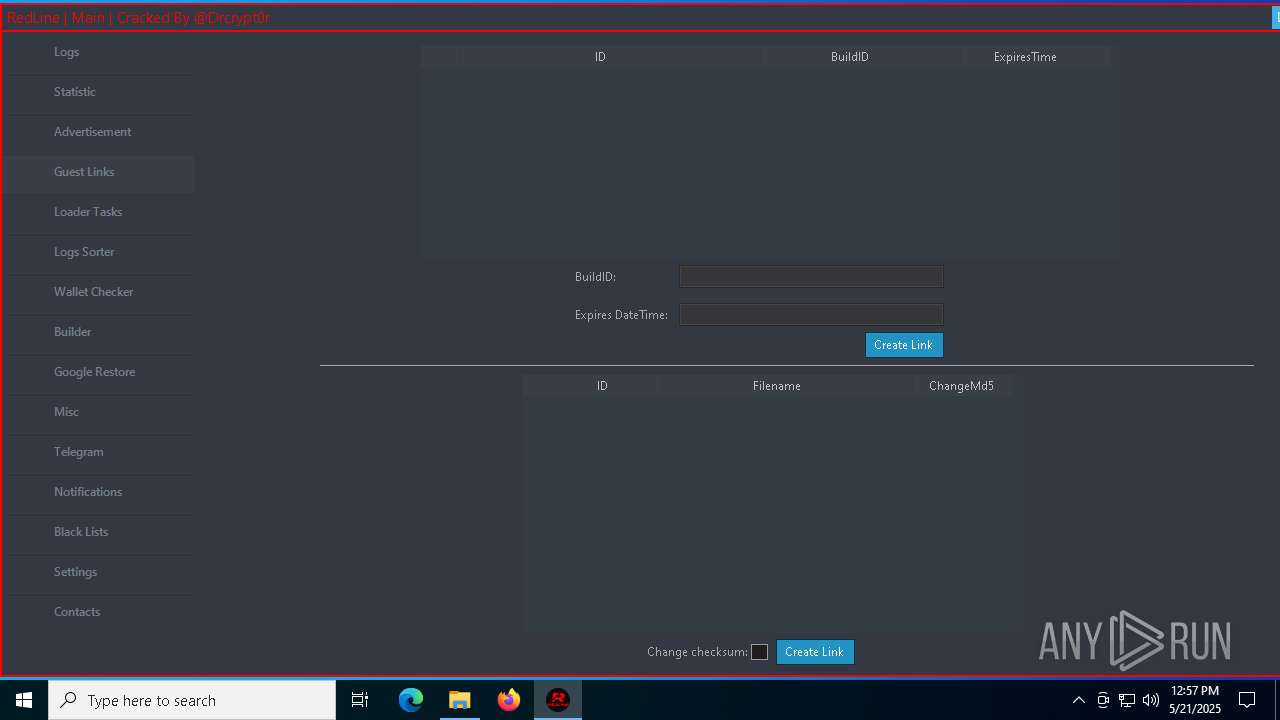
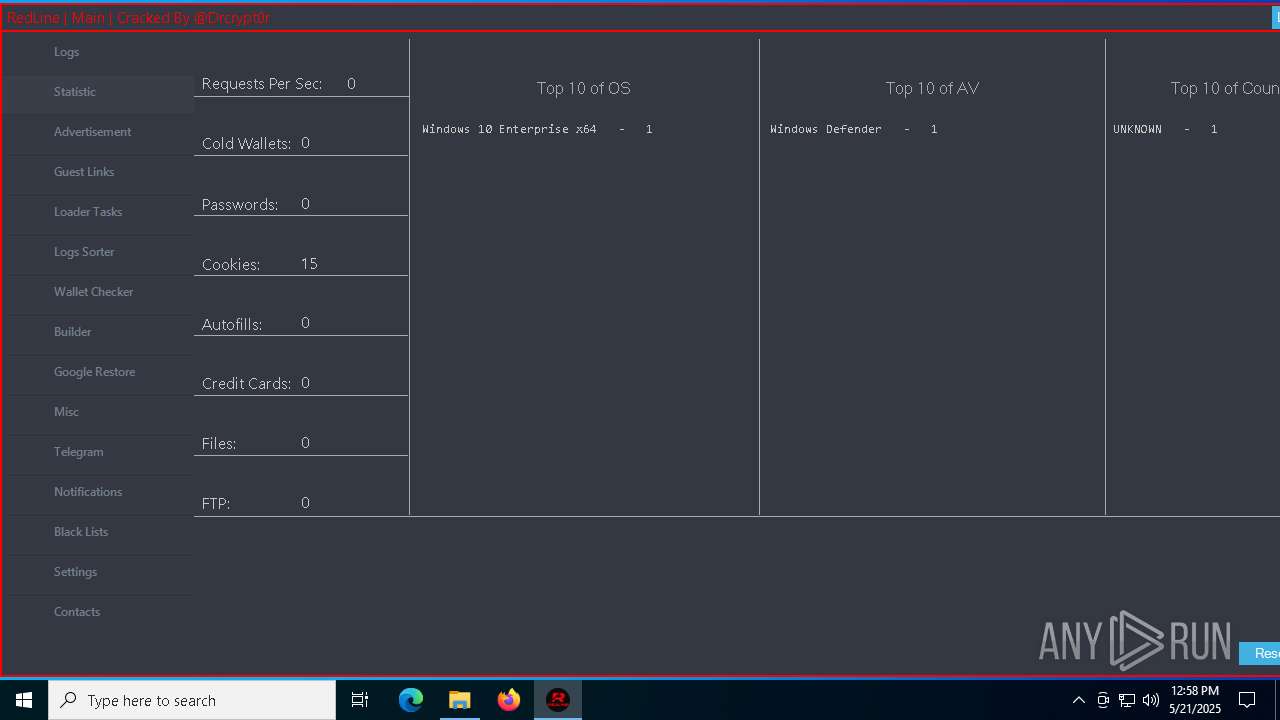
| Threats: | RedLine Stealer is a malicious program that collects users’ confidential data from browsers, systems, and installed software. It also infects operating systems with other malware. |
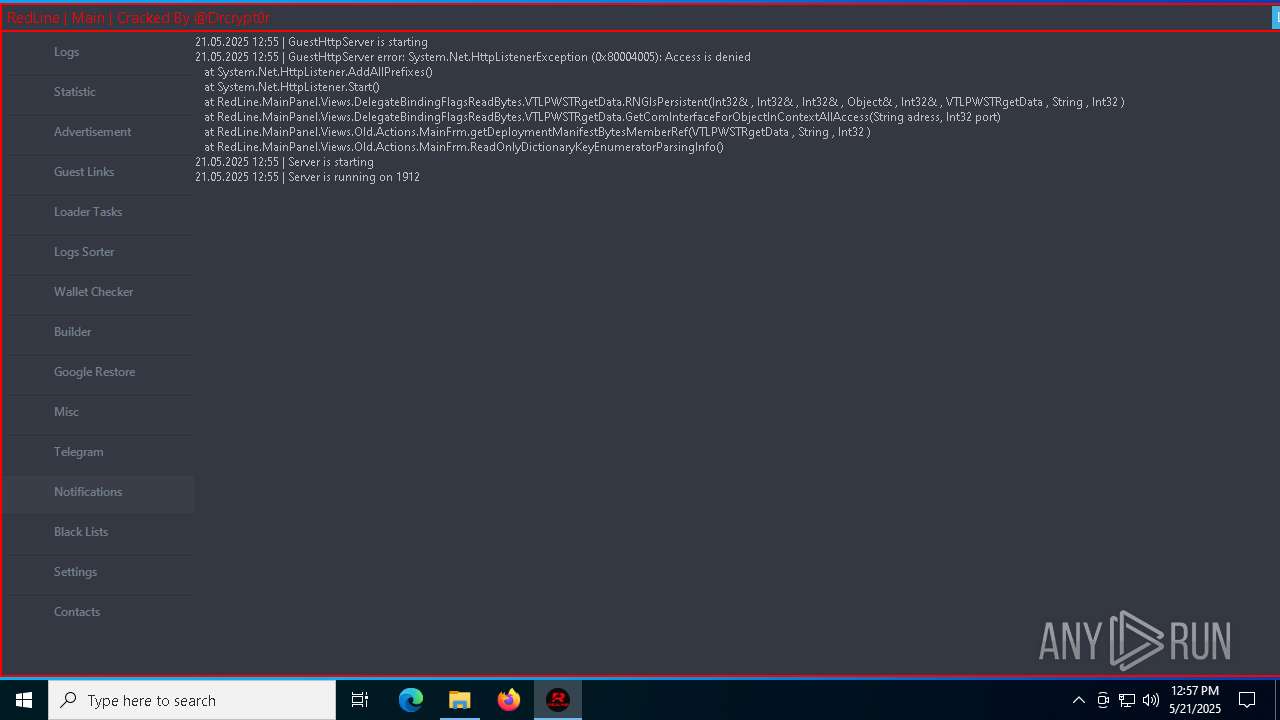
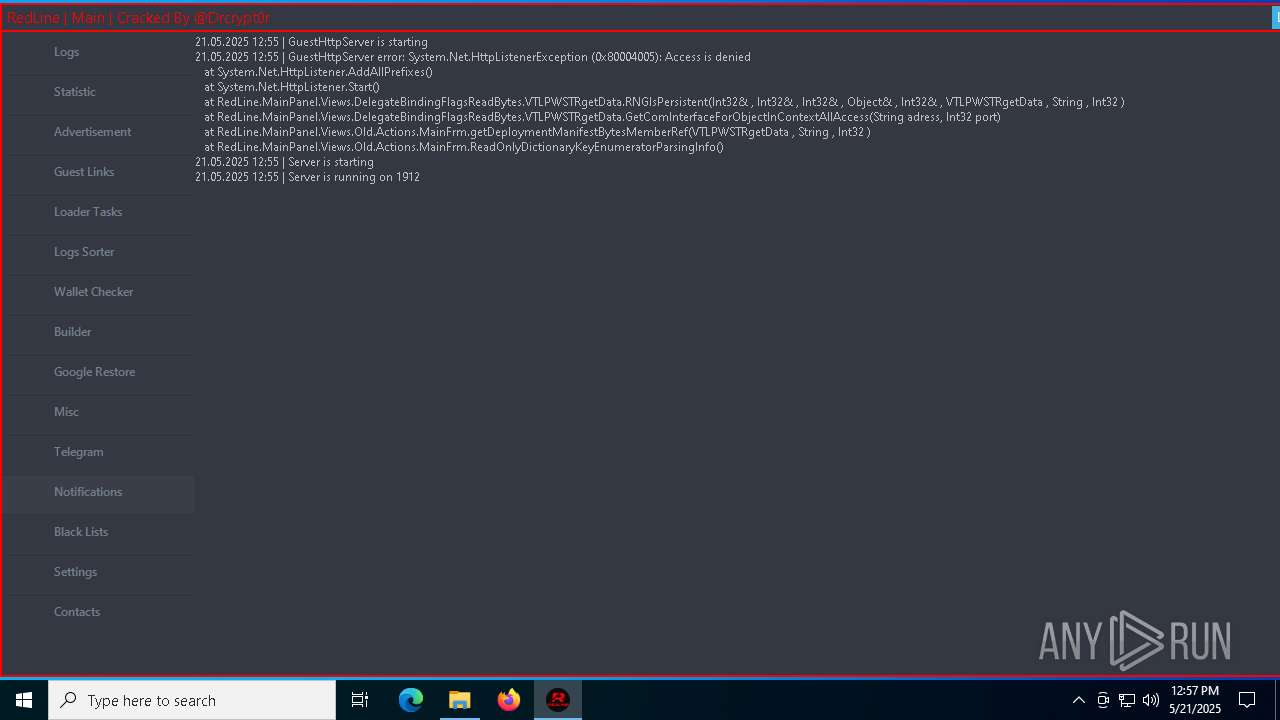
| Analysis date: | May 21, 2025, 12:55:00 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 0C11D3CB653AF998DF4CF7251821D9B0 |
| SHA1: | 23A1447DEBDA81C0F1E08DA37D12489AF2EEF042 |
| SHA256: | 714304EDF1B894E47C859397E95D1D186C8CF510556EB8B88C2DF04A7D0D1E98 |
| SSDEEP: | 3:N8tEdyYqA/KNEJijzEZA72kC0JKTRhJOBJKHAiQvOcMVn:2uUAiD/WJ+ITRhQBIHA7vi |
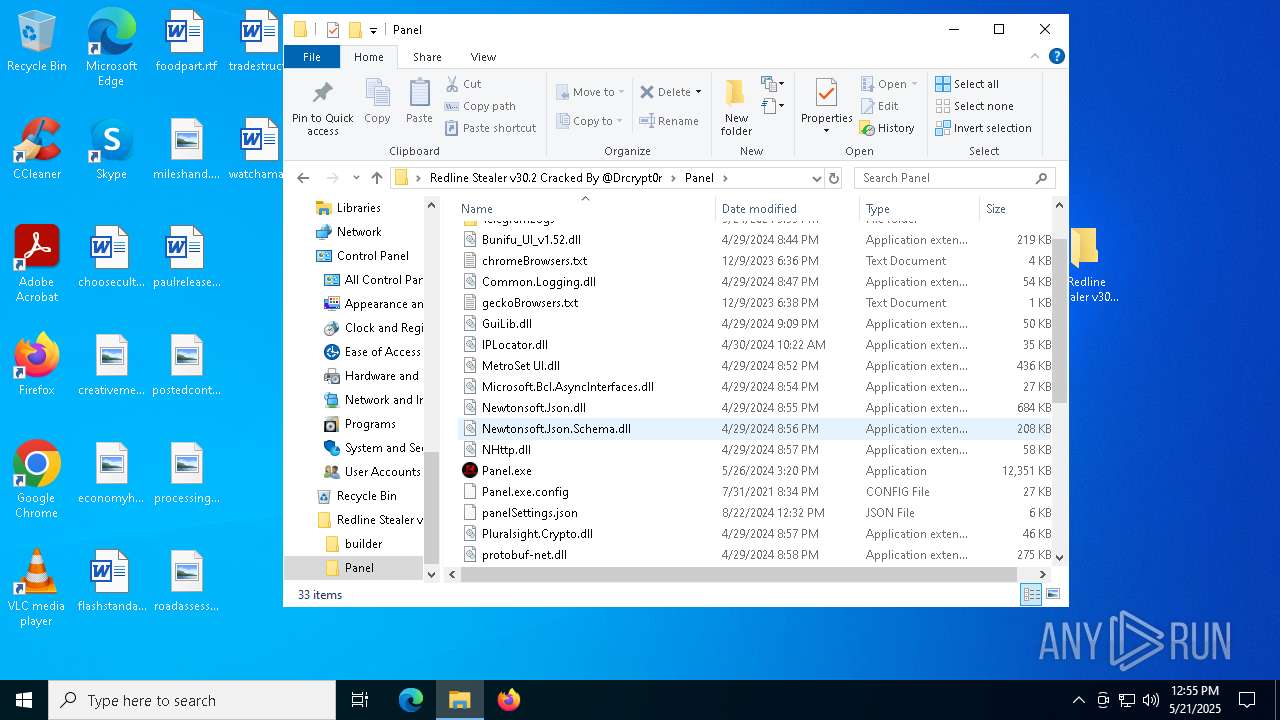
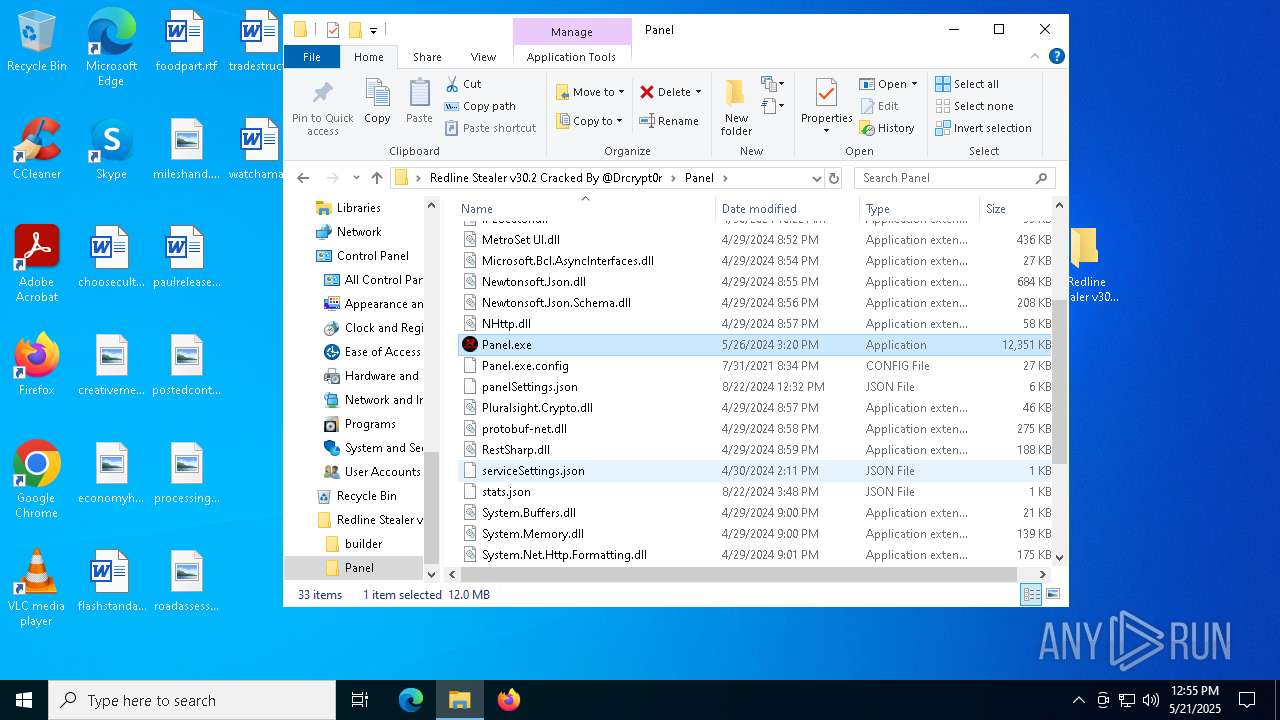
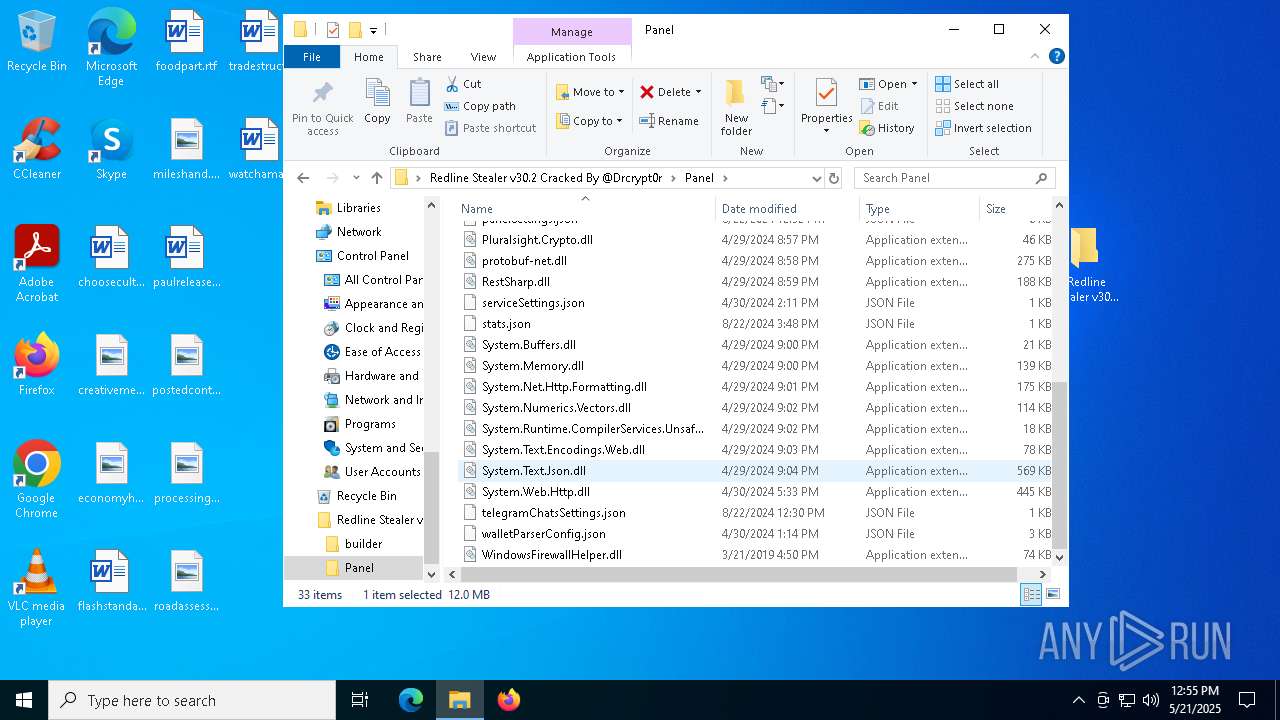
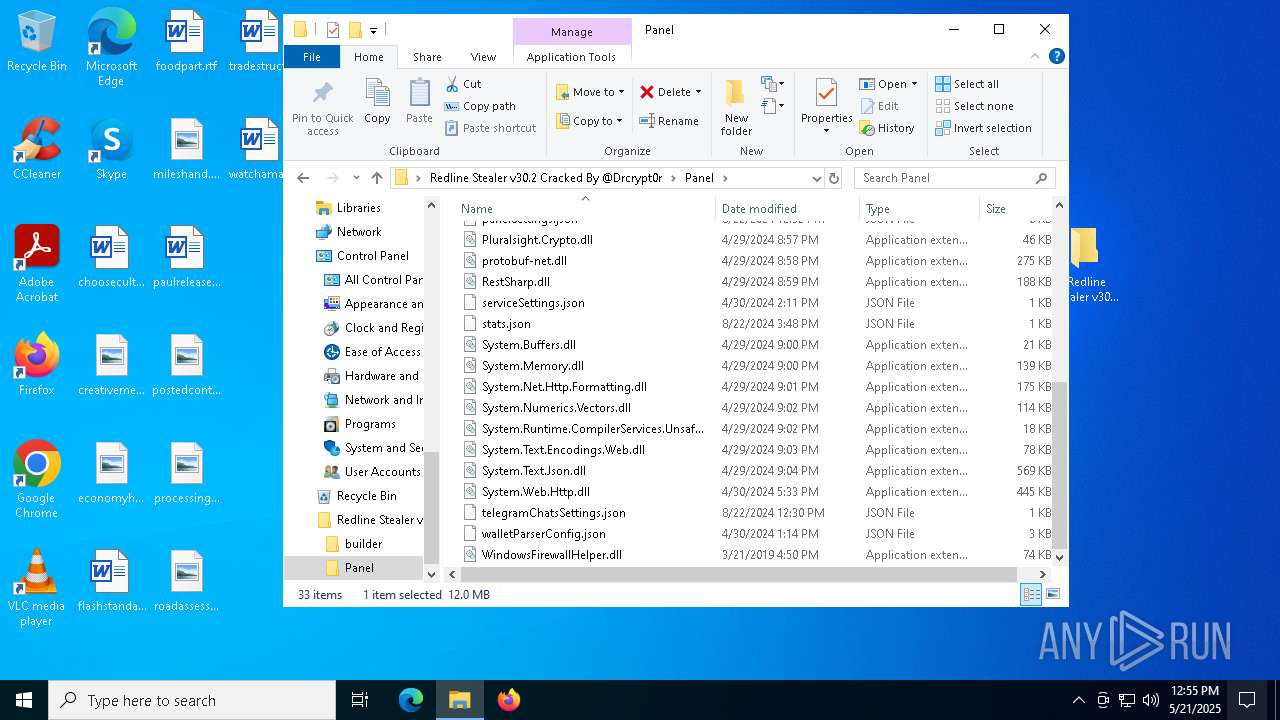
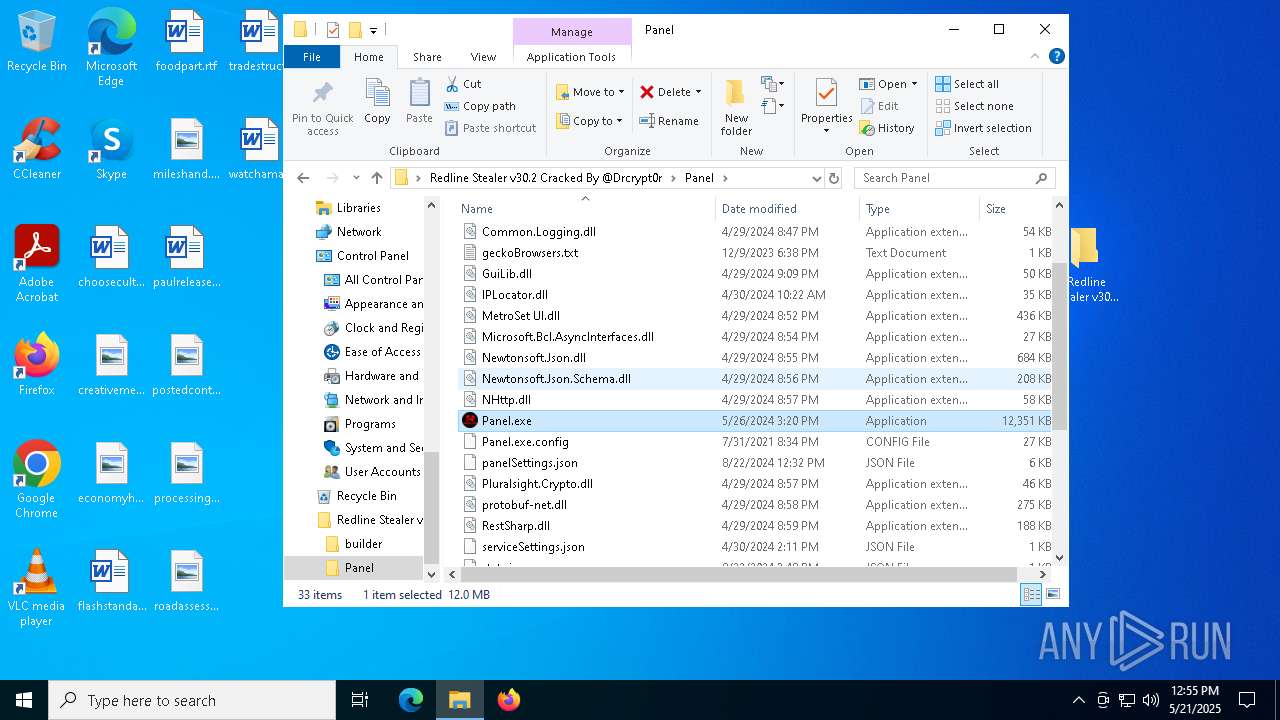
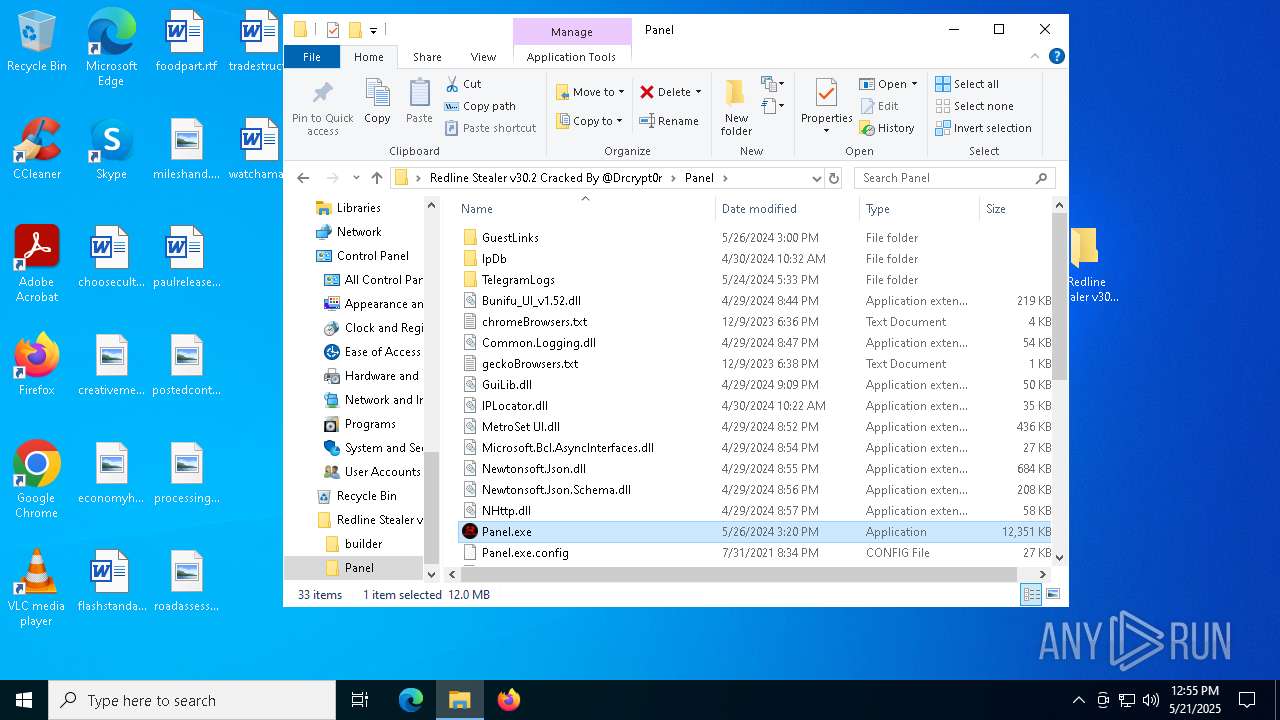
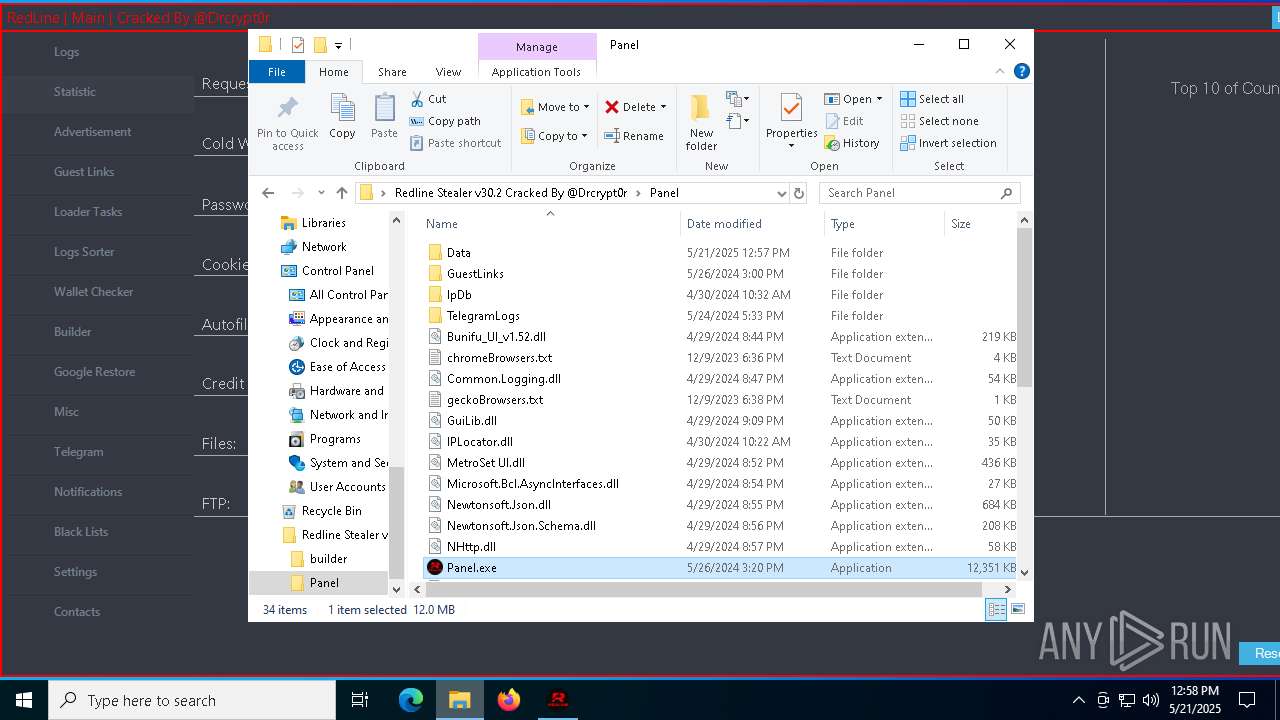
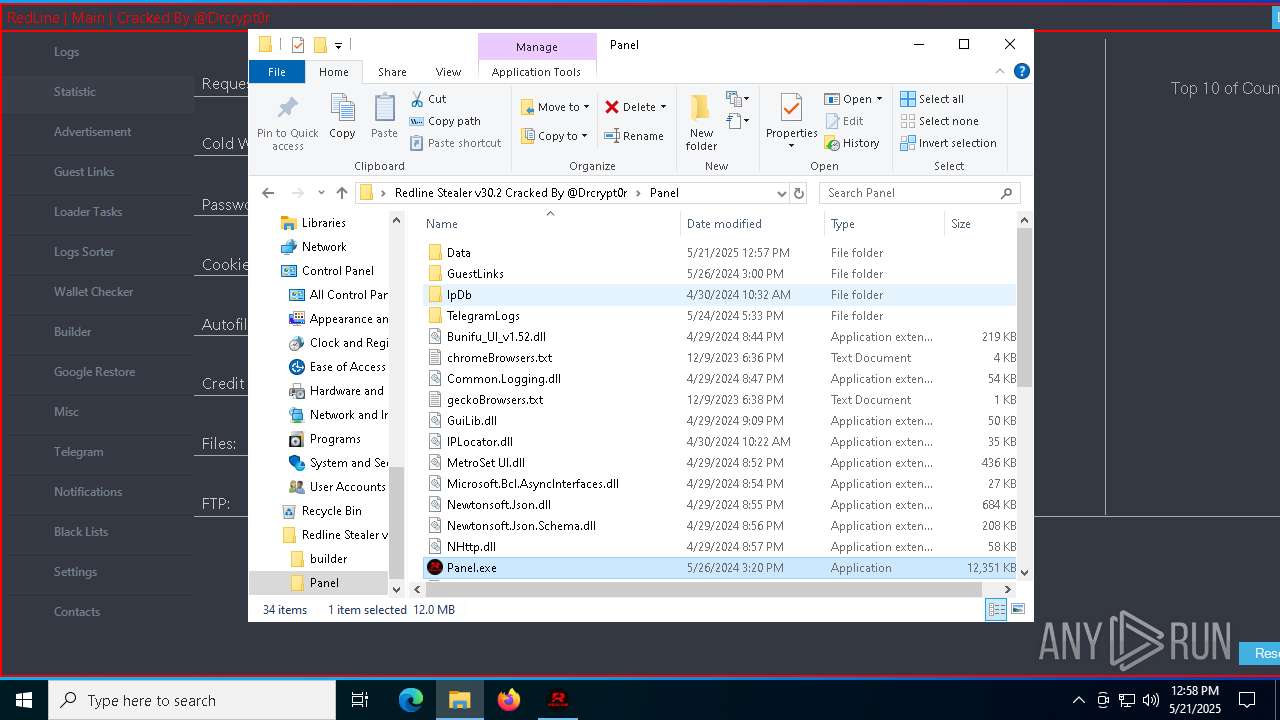
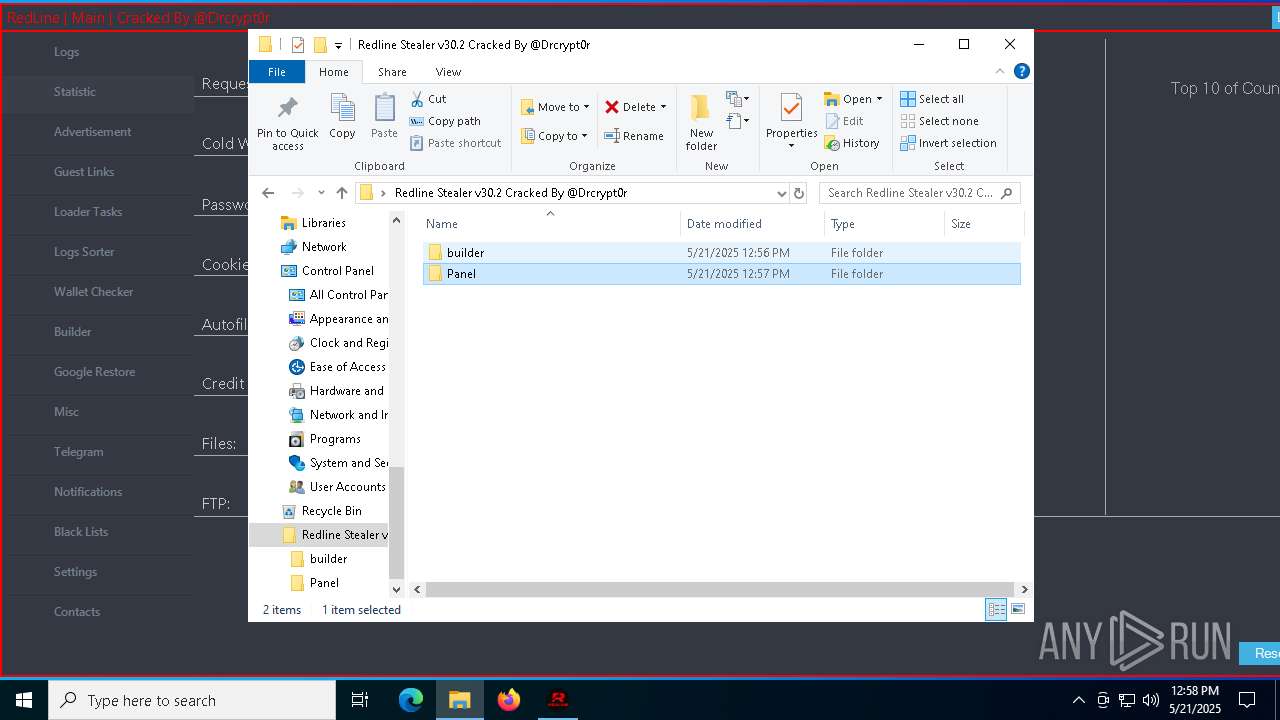
MALICIOUS
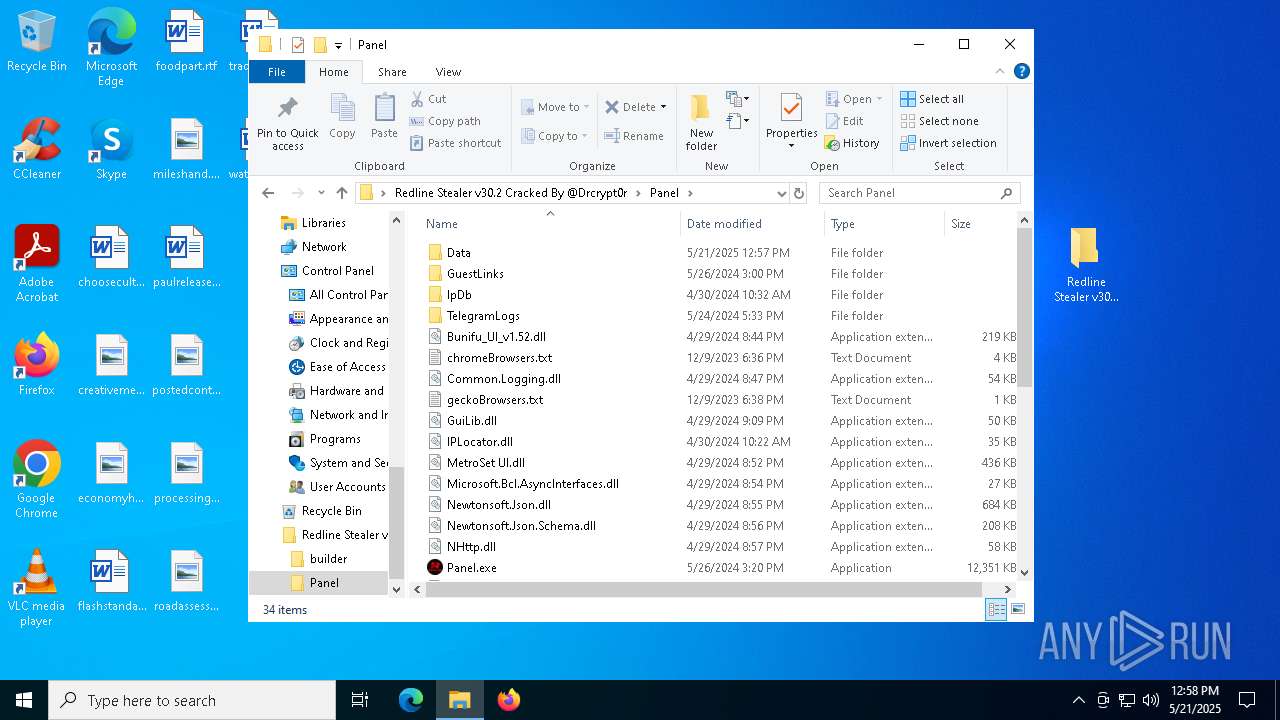
XORed URL has been found (YARA)
- Panel.exe (PID: 5428)
- Panel.exe (PID: 6944)
REDLINE has been detected (YARA)
- Panel.exe (PID: 5428)
- Panel.exe (PID: 6944)
DISCORDGRABBER has been detected (YARA)
- Panel.exe (PID: 5428)
- Panel.exe (PID: 6944)
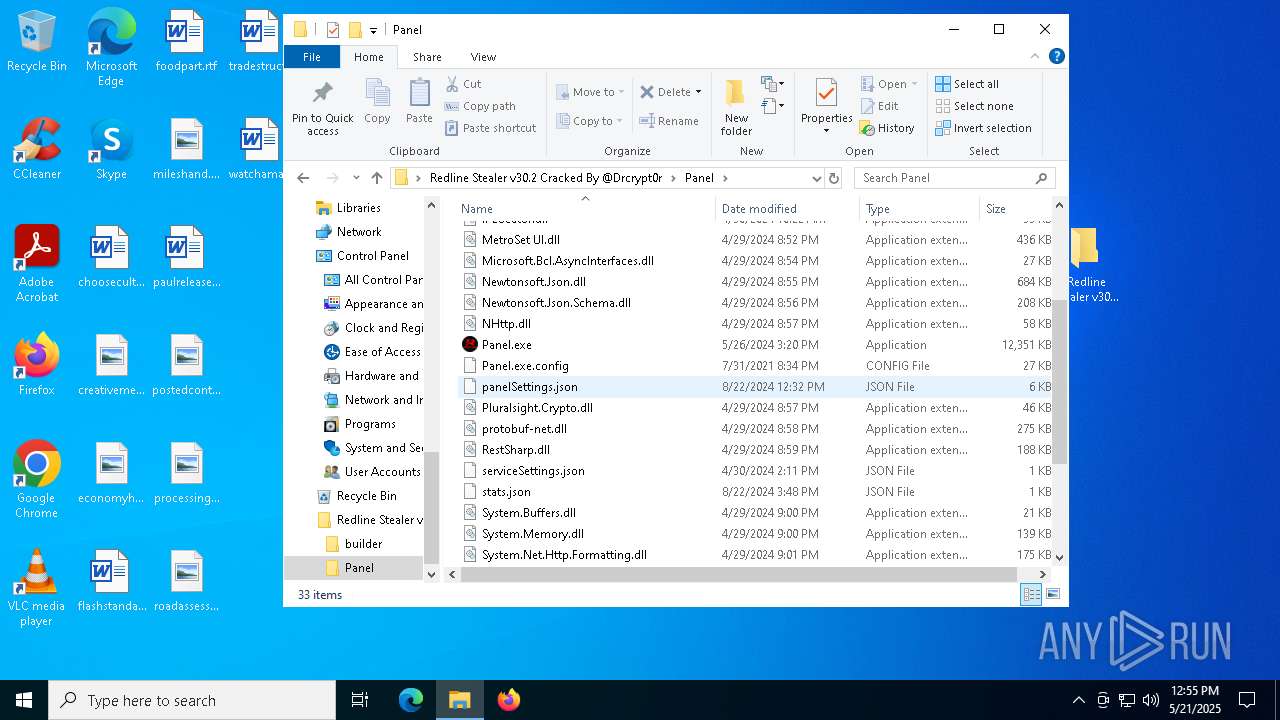
SUSPICIOUS
Reads security settings of Internet Explorer
- Panel.exe (PID: 5428)
- Panel.exe (PID: 6944)
Reads the date of Windows installation
- Panel.exe (PID: 5428)
Application launched itself
- Panel.exe (PID: 5428)
- Panel.exe (PID: 7444)
Found regular expressions for crypto-addresses (YARA)
- Panel.exe (PID: 5428)
- Panel.exe (PID: 6944)
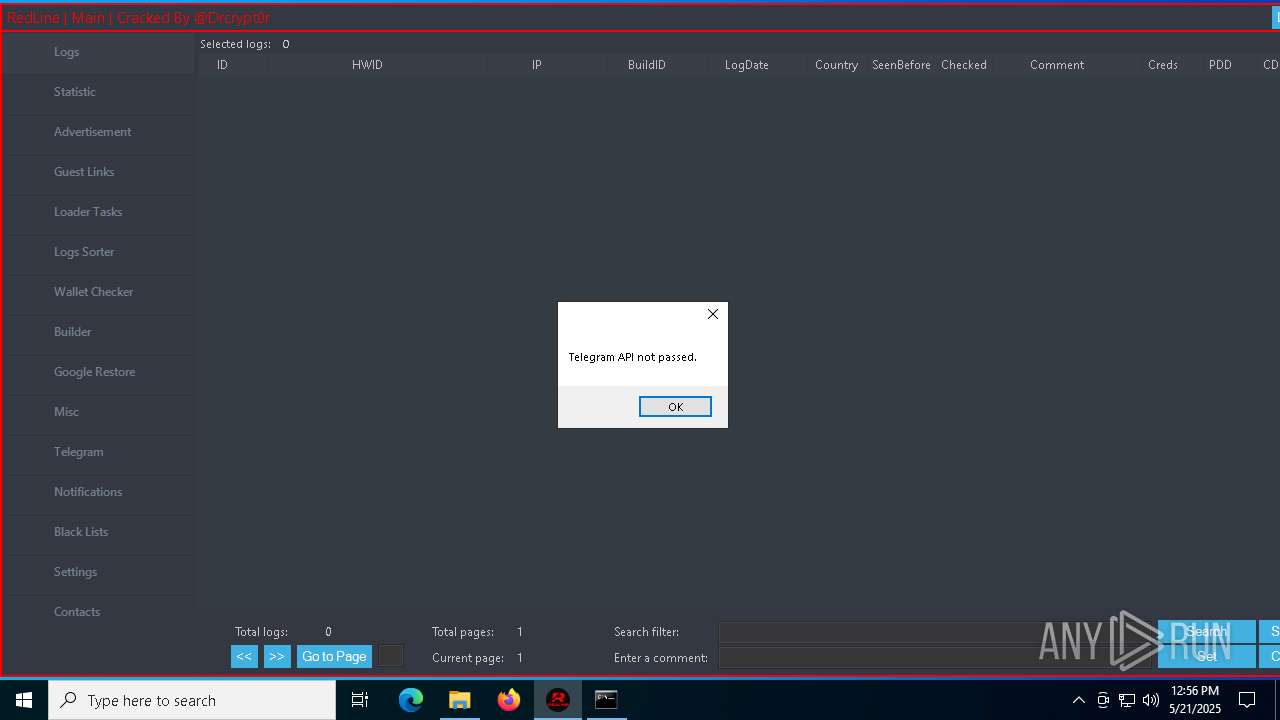
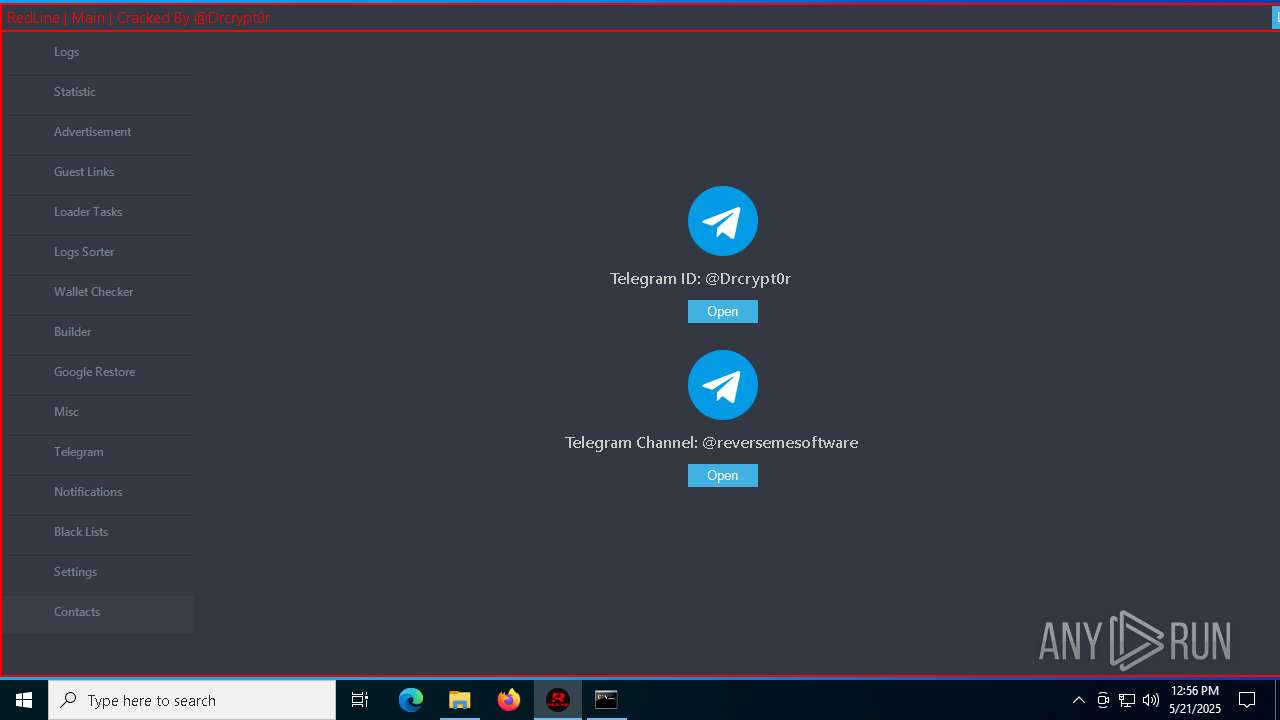
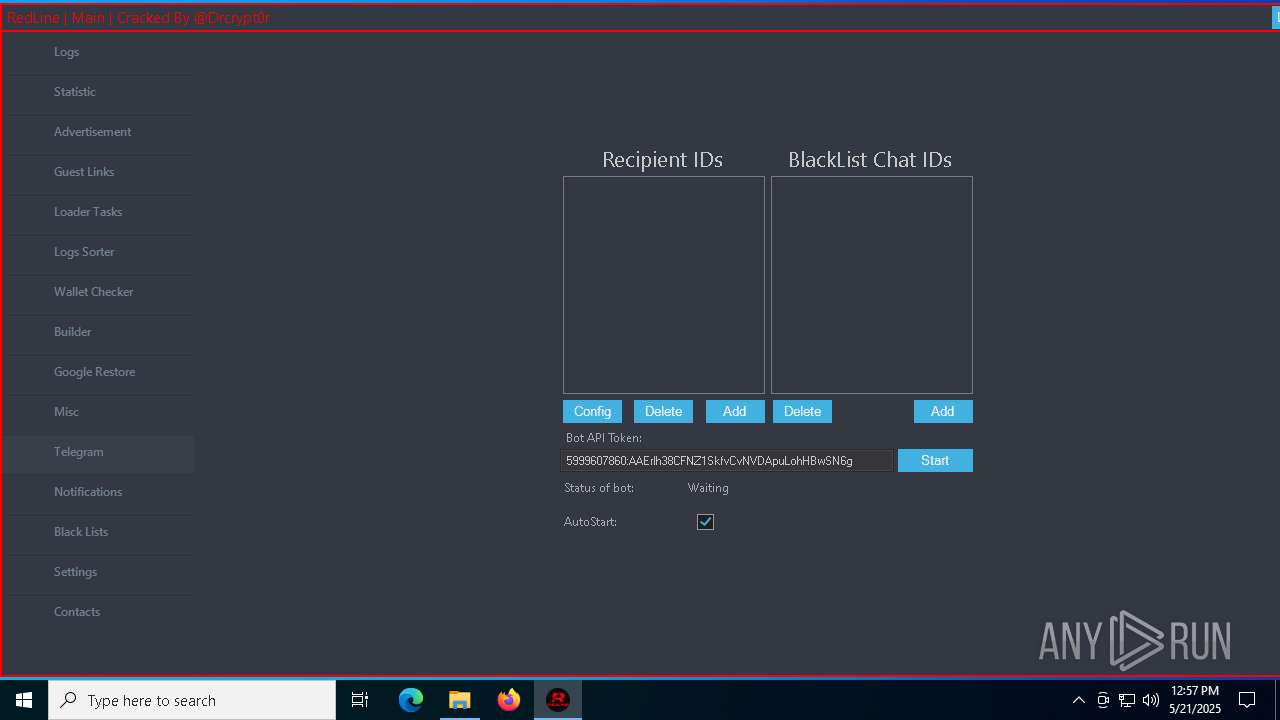
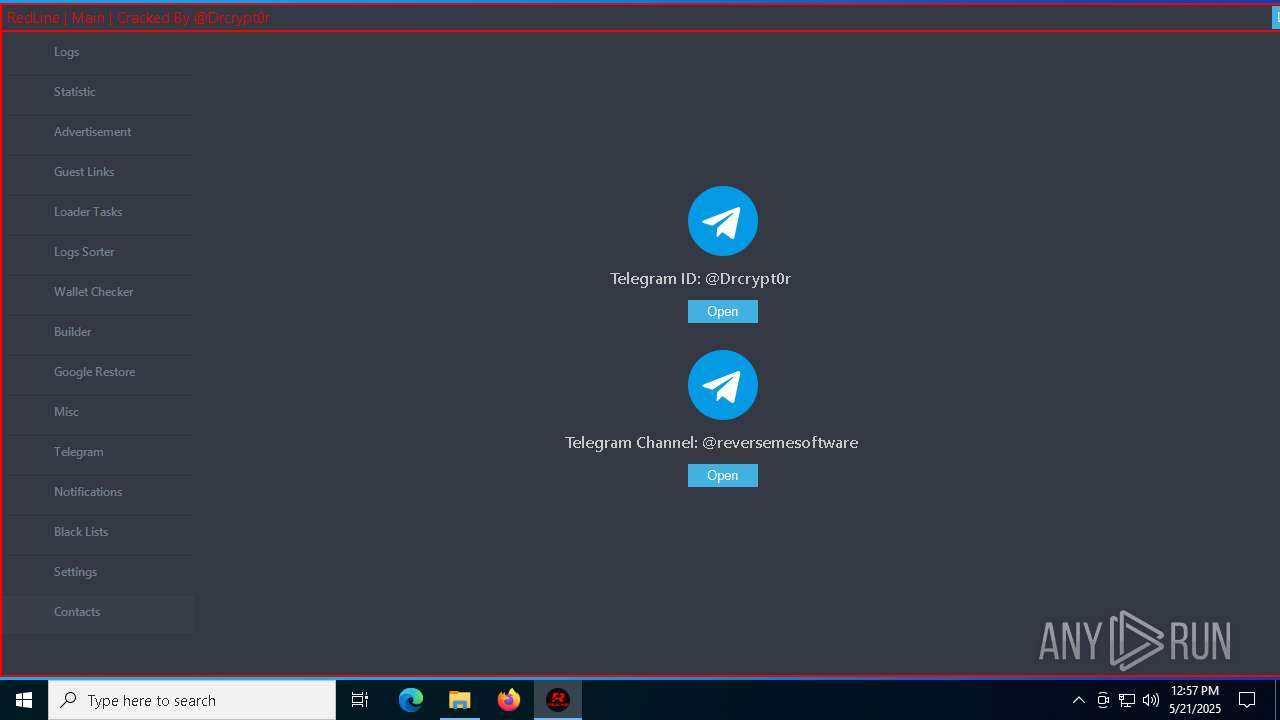
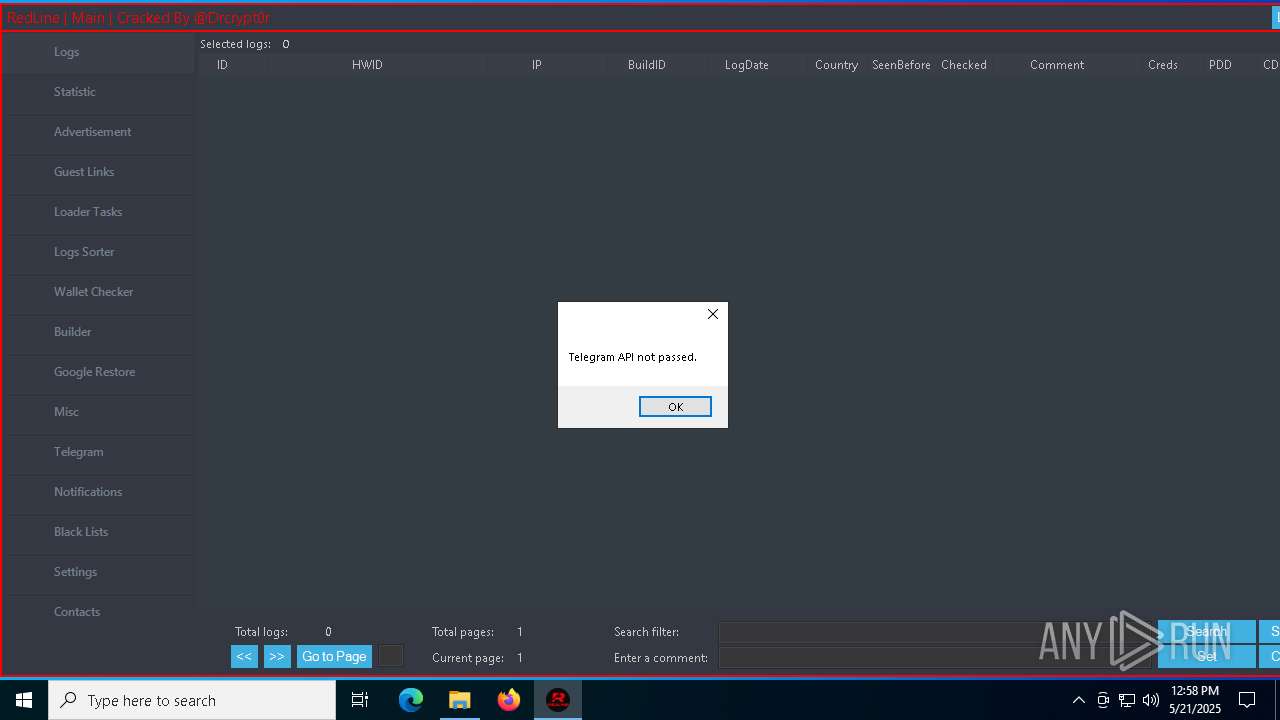
Process communicates with Telegram (possibly using it as an attacker's C2 server)
- Panel.exe (PID: 6944)
- Panel.exe (PID: 7804)
Possible usage of Discord/Telegram API has been detected (YARA)
- Panel.exe (PID: 6944)
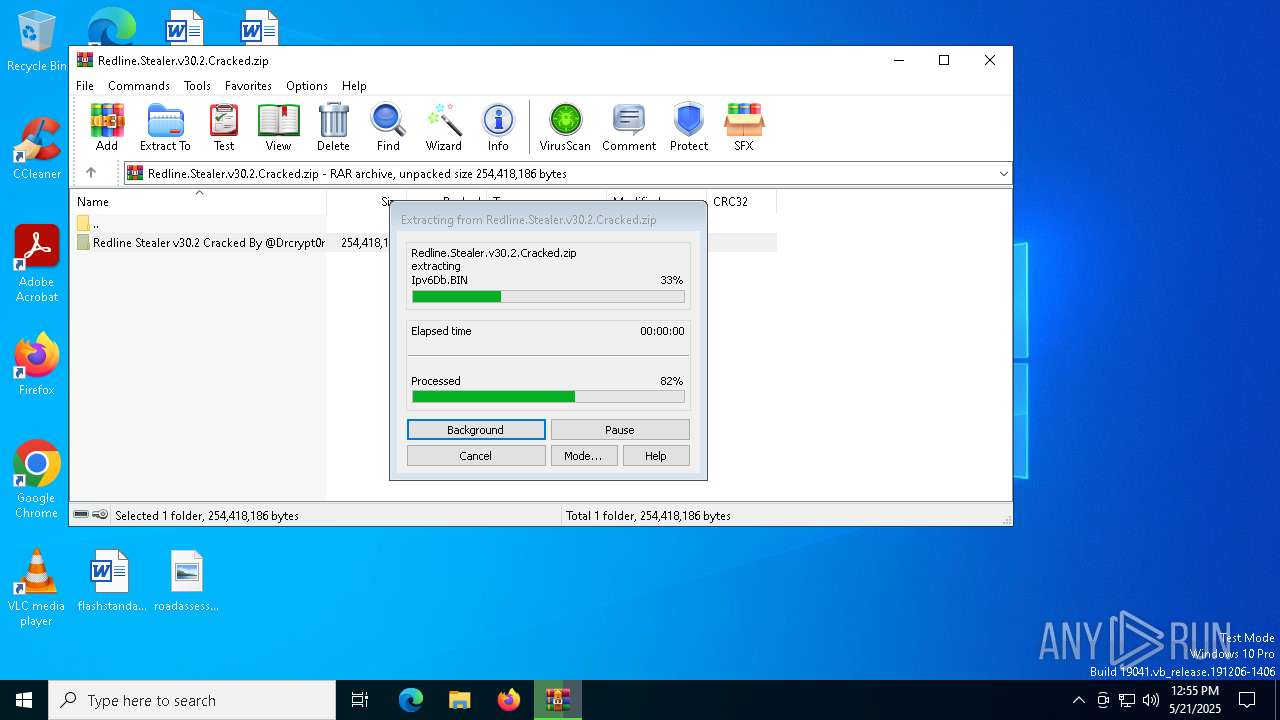
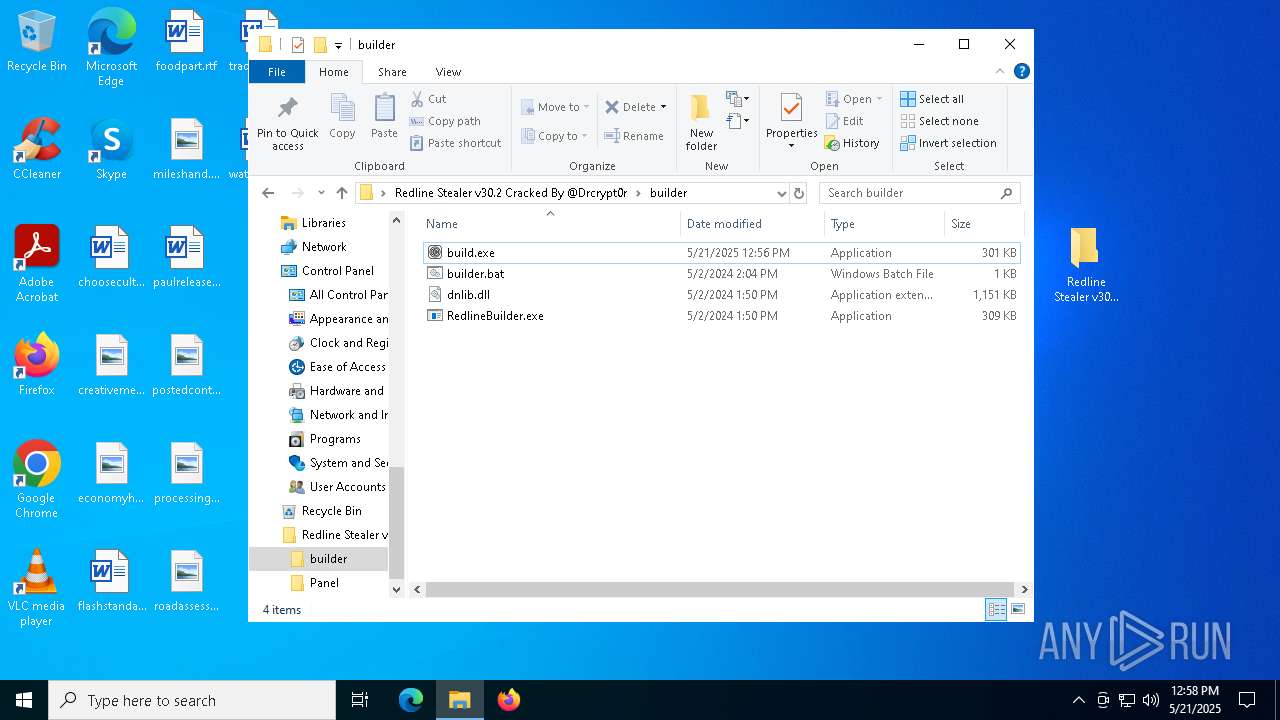
Process drops legitimate windows executable
- WinRAR.exe (PID: 5608)
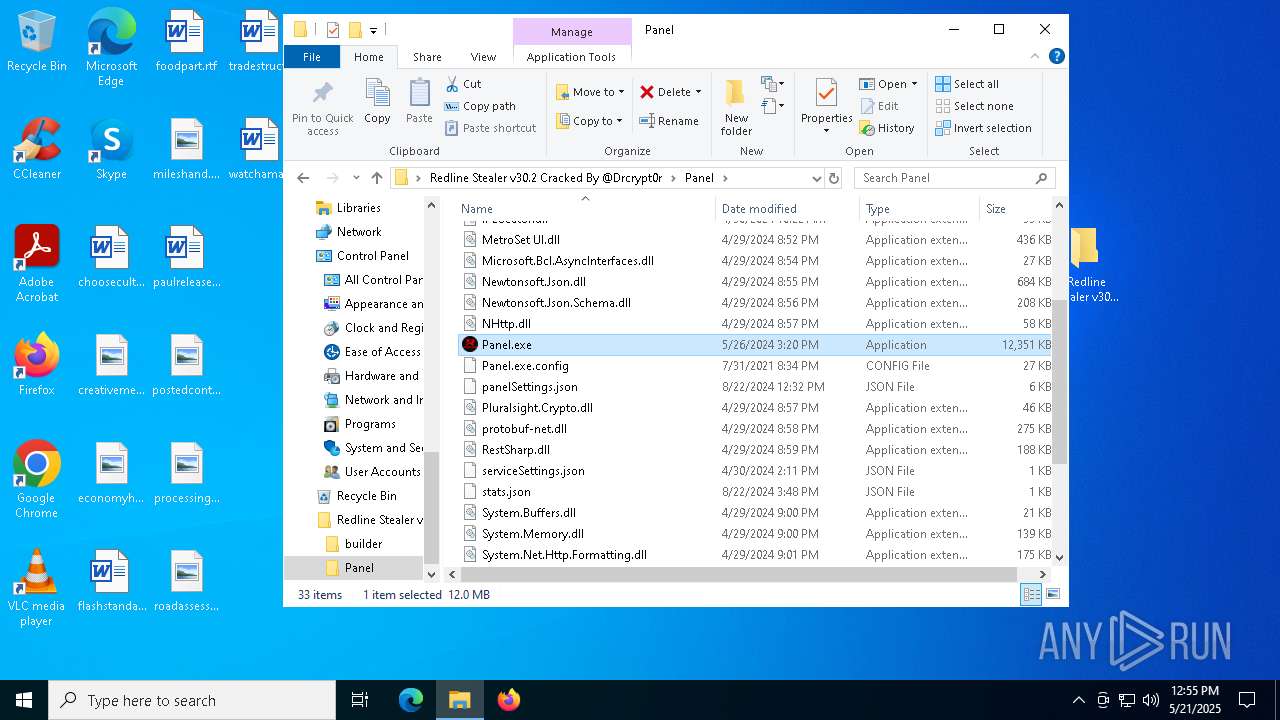
INFO
Reads Environment values
- identity_helper.exe (PID: 5528)
- Panel.exe (PID: 6944)
- identity_helper.exe (PID: 7628)
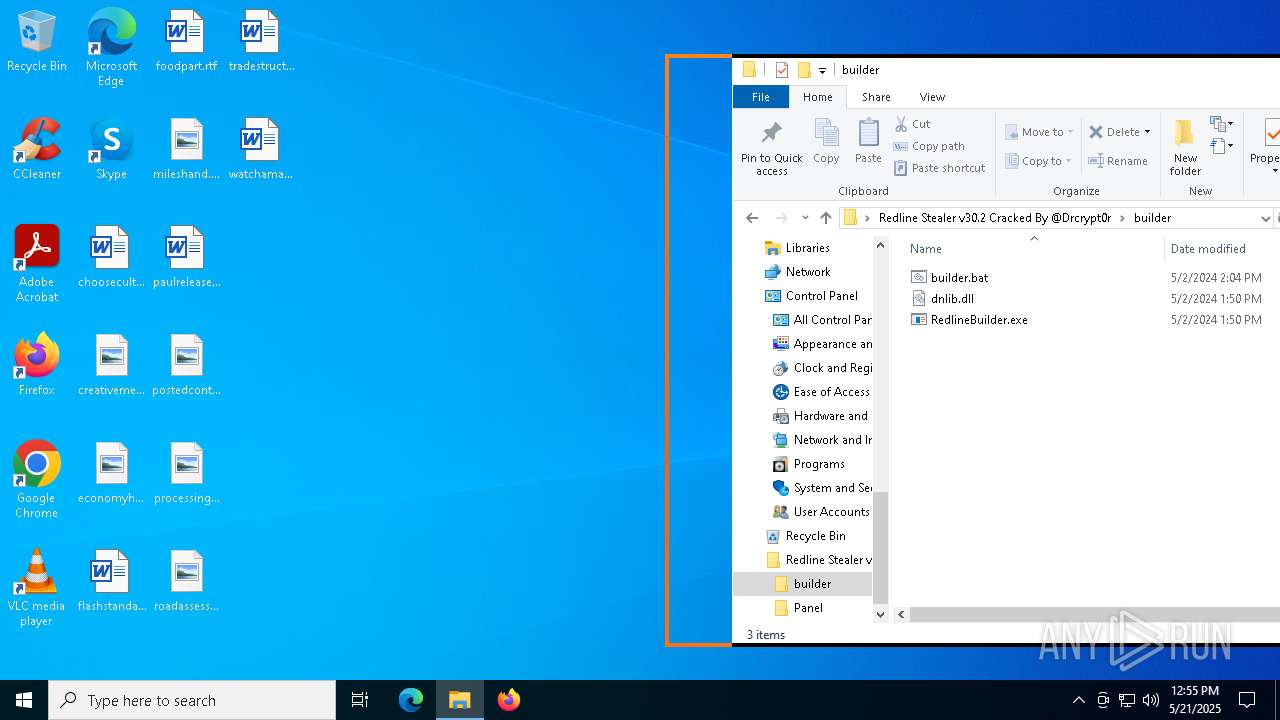
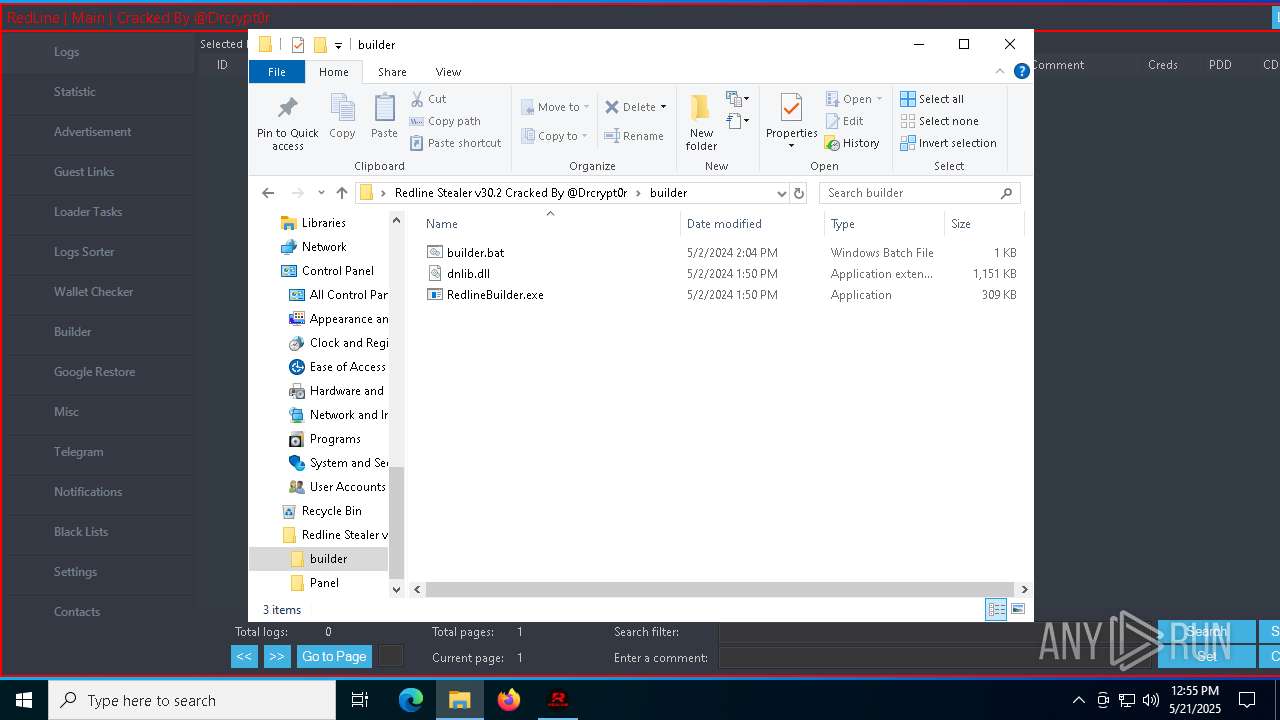
Reads the computer name
- identity_helper.exe (PID: 5528)
- RedlineBuilder.exe (PID: 7700)
- identity_helper.exe (PID: 7628)
Reads Microsoft Office registry keys
- msedge.exe (PID: 1276)
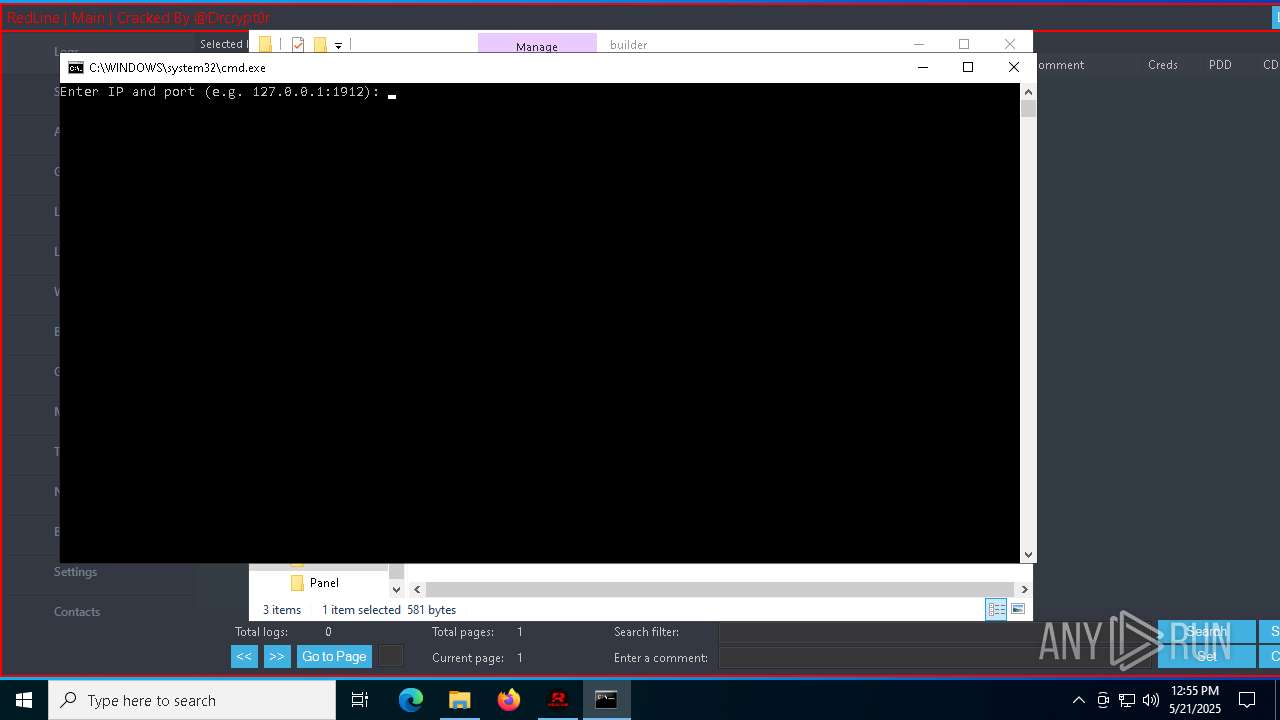
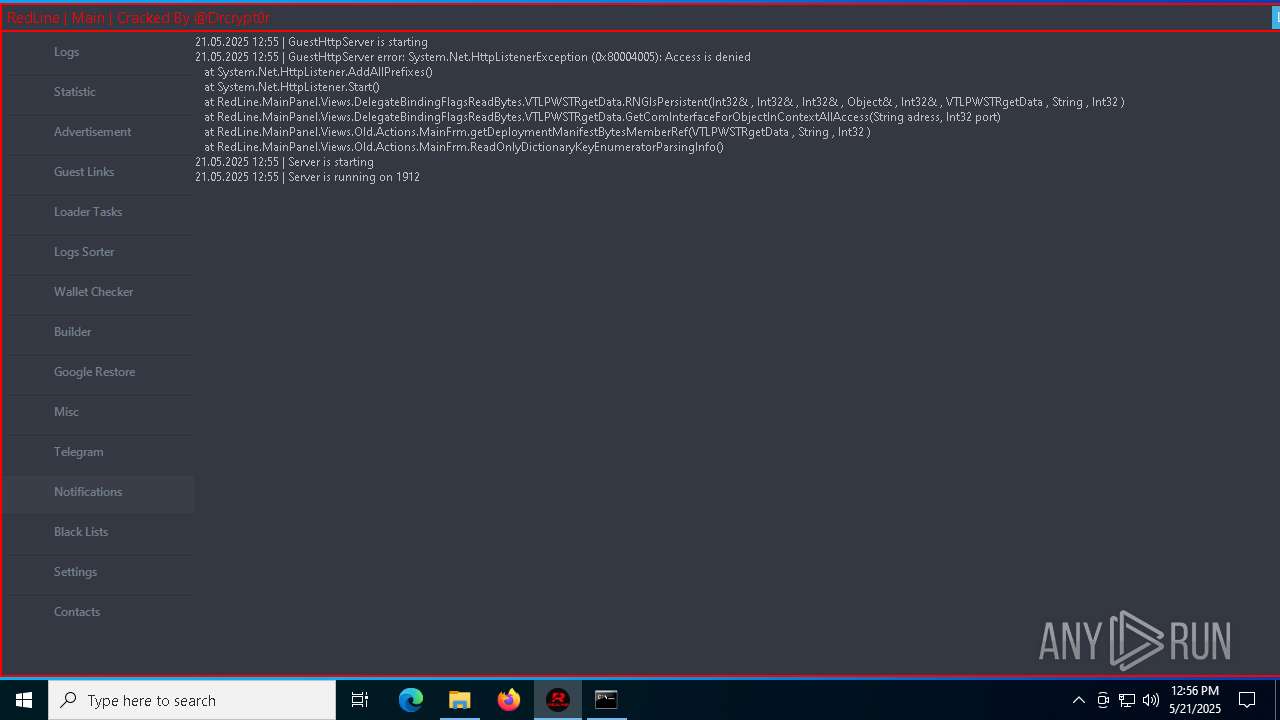
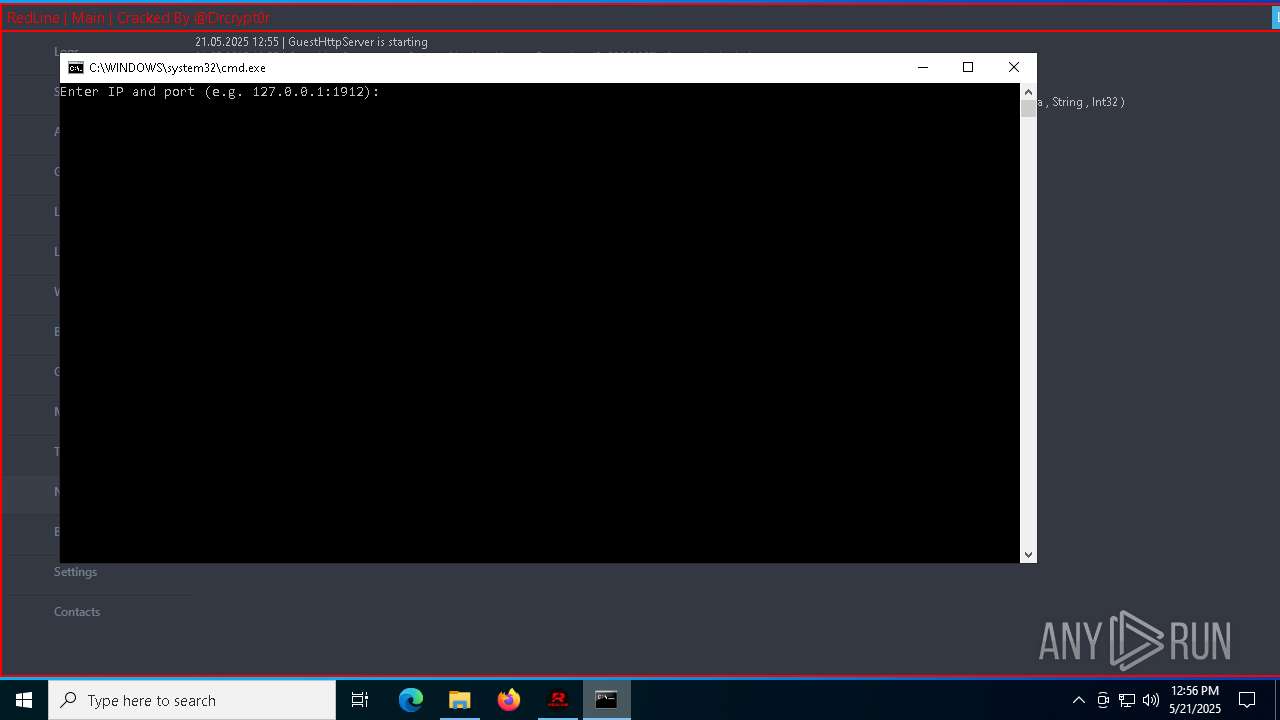
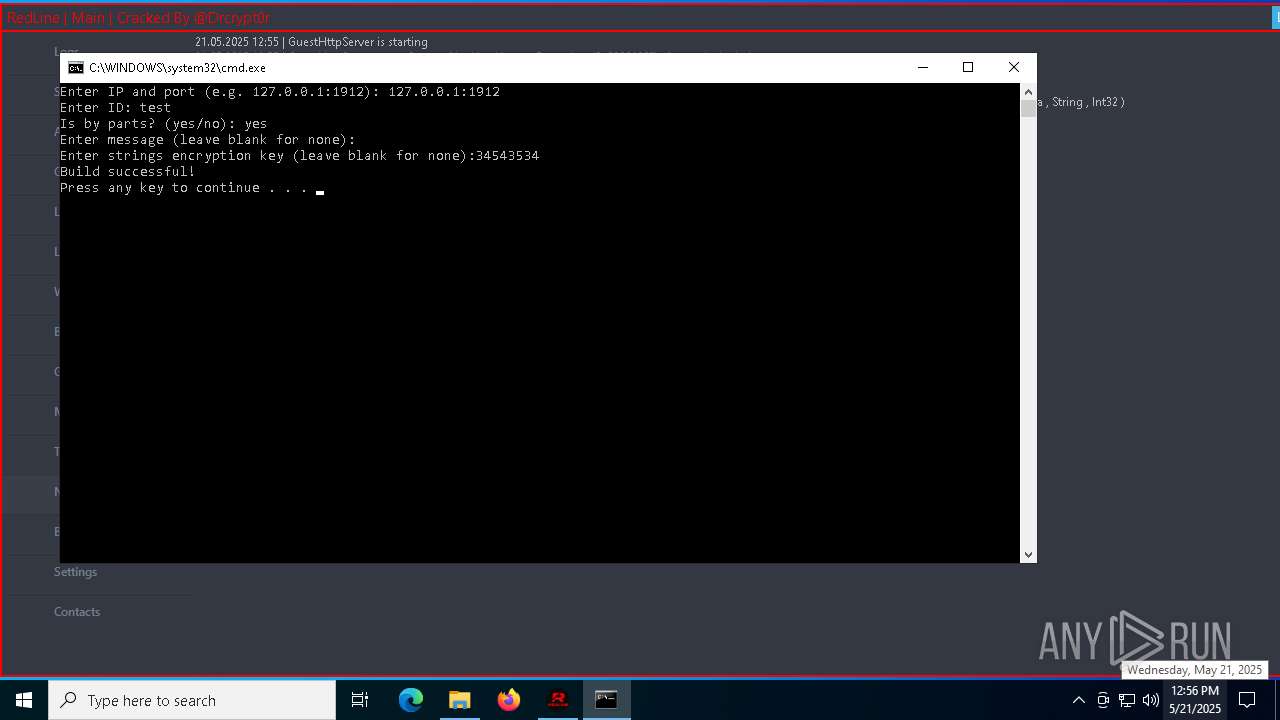
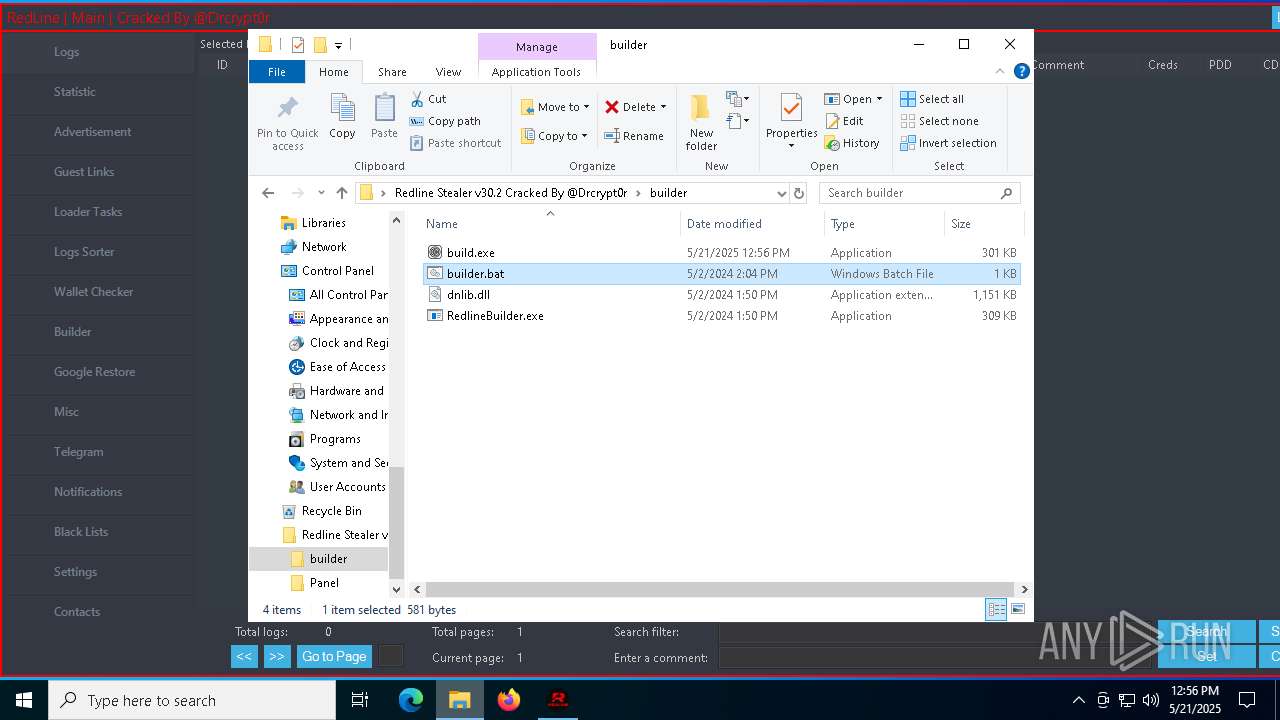
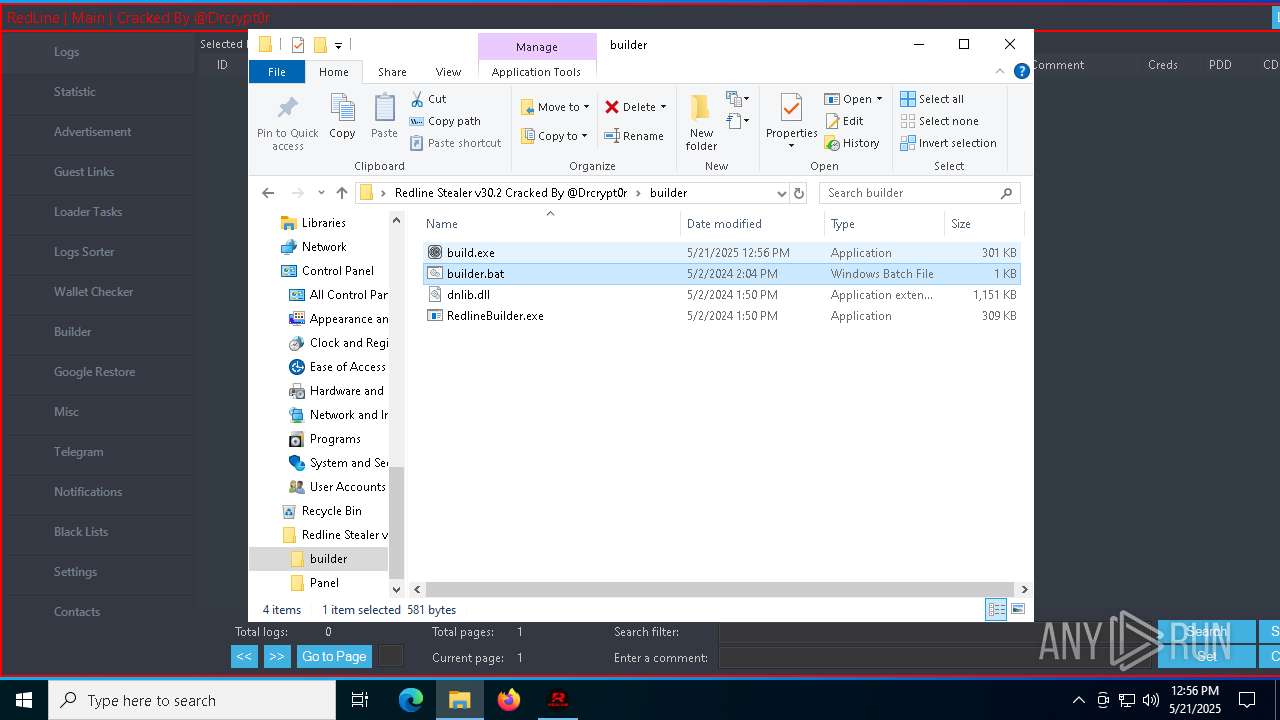
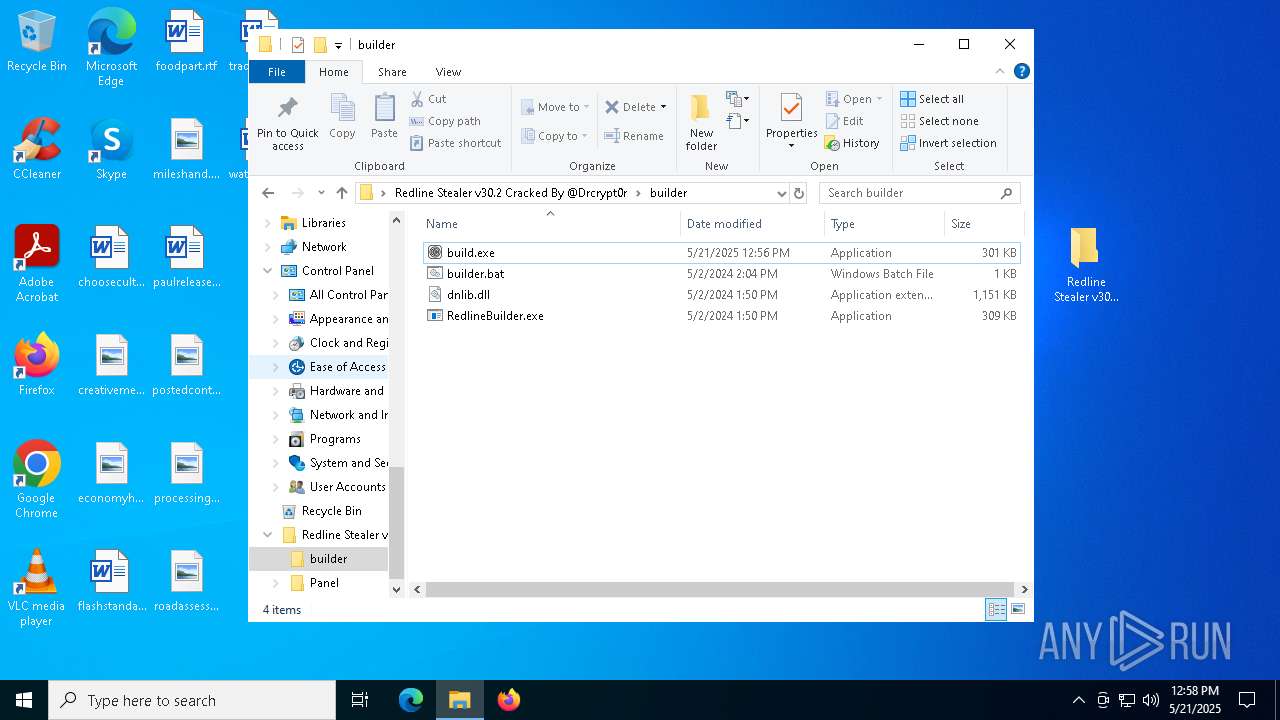
Manual execution by a user
- Panel.exe (PID: 5428)
- cmd.exe (PID: 7036)
- build.exe (PID: 8140)
- Panel.exe (PID: 7444)
Application launched itself
- msedge.exe (PID: 7884)
- msedge.exe (PID: 1276)
Checks supported languages
- Panel.exe (PID: 5428)
- Panel.exe (PID: 6944)
- RedlineBuilder.exe (PID: 7700)
- identity_helper.exe (PID: 5528)
- identity_helper.exe (PID: 7628)
Process checks computer location settings
- Panel.exe (PID: 5428)
Confuser has been detected (YARA)
- Panel.exe (PID: 5428)
- Panel.exe (PID: 6944)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 5608)
- msedge.exe (PID: 3020)
Disables trace logs
- Panel.exe (PID: 6944)
Reads the machine GUID from the registry
- Panel.exe (PID: 6944)
- RedlineBuilder.exe (PID: 7700)
Create files in a temporary directory
- Panel.exe (PID: 6944)
Checks proxy server information
- Panel.exe (PID: 6944)
Reads the software policy settings
- Panel.exe (PID: 6944)
- slui.exe (PID: 1184)
Creates files or folders in the user directory
- Panel.exe (PID: 6944)
The sample compiled with english language support
- msedge.exe (PID: 3020)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
xor-url
(PID) Process(5428) Panel.exe
Decrypted-URLs (11)http://ns.adobe.com/xap/1.0/
http://ns.adobe.com/xap/1.0/mm/
http://ns.adobe.com/xap/1.0/sType/ResourceRef#
http://www.w3.org/1999/02/22-rdf-syntax-ns#
https://api.blockcypher.com/v1/btc/main/addrs/
https://api.telegram.org/bot
https://t.me/Drcrypt0r
https://t.me/REDLINESUPPORT
https://t.me/redline_market_bot
https://t.me/reversemesoftware
https://www.virustotal.com/api/v3/files/
(PID) Process(6944) Panel.exe
Decrypted-URLs (11)http://ns.adobe.com/xap/1.0/
http://ns.adobe.com/xap/1.0/mm/
http://ns.adobe.com/xap/1.0/sType/ResourceRef#
http://www.w3.org/1999/02/22-rdf-syntax-ns#
https://api.blockcypher.com/v1/btc/main/addrs/
https://api.telegram.org/bot
https://t.me/Drcrypt0r
https://t.me/REDLINESUPPORT
https://t.me/redline_market_bot
https://t.me/reversemesoftware
https://www.virustotal.com/api/v3/files/
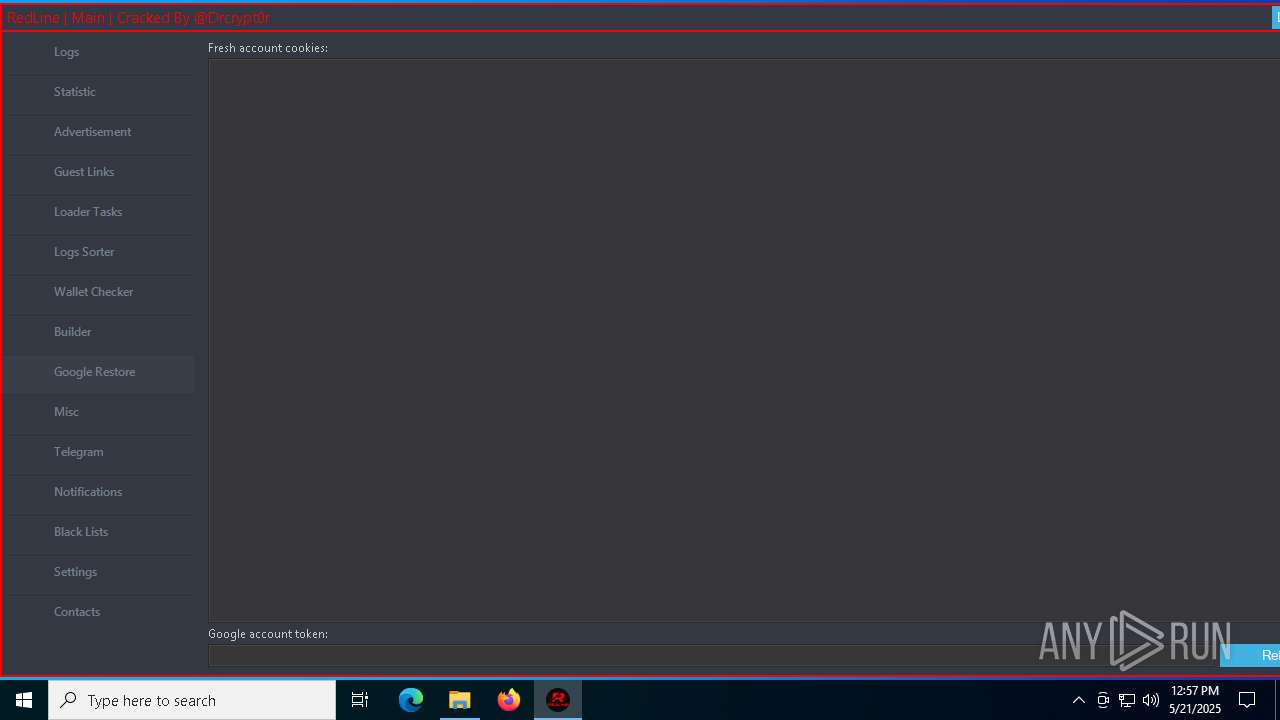
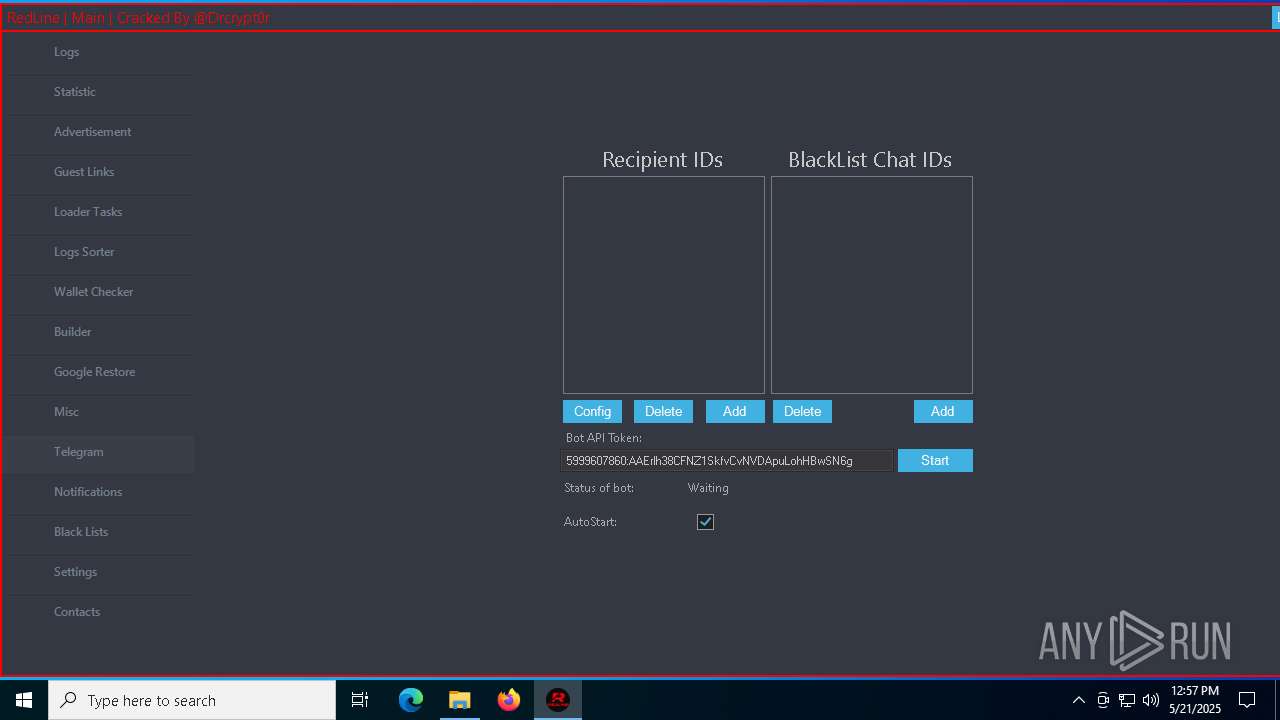
ims-api
(PID) Process(6944) Panel.exe
Telegram-Tokens (1)5999607860:AAErlh38CFNZ1SkfvCvNVDApuLohHBwSN6g
Telegram-Info-Links
5999607860:AAErlh38CFNZ1SkfvCvNVDApuLohHBwSN6g
Get info about bothttps://api.telegram.org/bot5999607860:AAErlh38CFNZ1SkfvCvNVDApuLohHBwSN6g/getMe
Get incoming updateshttps://api.telegram.org/bot5999607860:AAErlh38CFNZ1SkfvCvNVDApuLohHBwSN6g/getUpdates
Get webhookhttps://api.telegram.org/bot5999607860:AAErlh38CFNZ1SkfvCvNVDApuLohHBwSN6g/getWebhookInfo
Delete webhookhttps://api.telegram.org/bot5999607860:AAErlh38CFNZ1SkfvCvNVDApuLohHBwSN6g/deleteWebhook
Drop incoming updateshttps://api.telegram.org/bot5999607860:AAErlh38CFNZ1SkfvCvNVDApuLohHBwSN6g/deleteWebhook?drop_pending_updates=true
Telegram-Requests
Token5999607860:AAErlh38CFNZ1SkfvCvNVDApuLohHBwSN6g
End-PointgetMe
Args
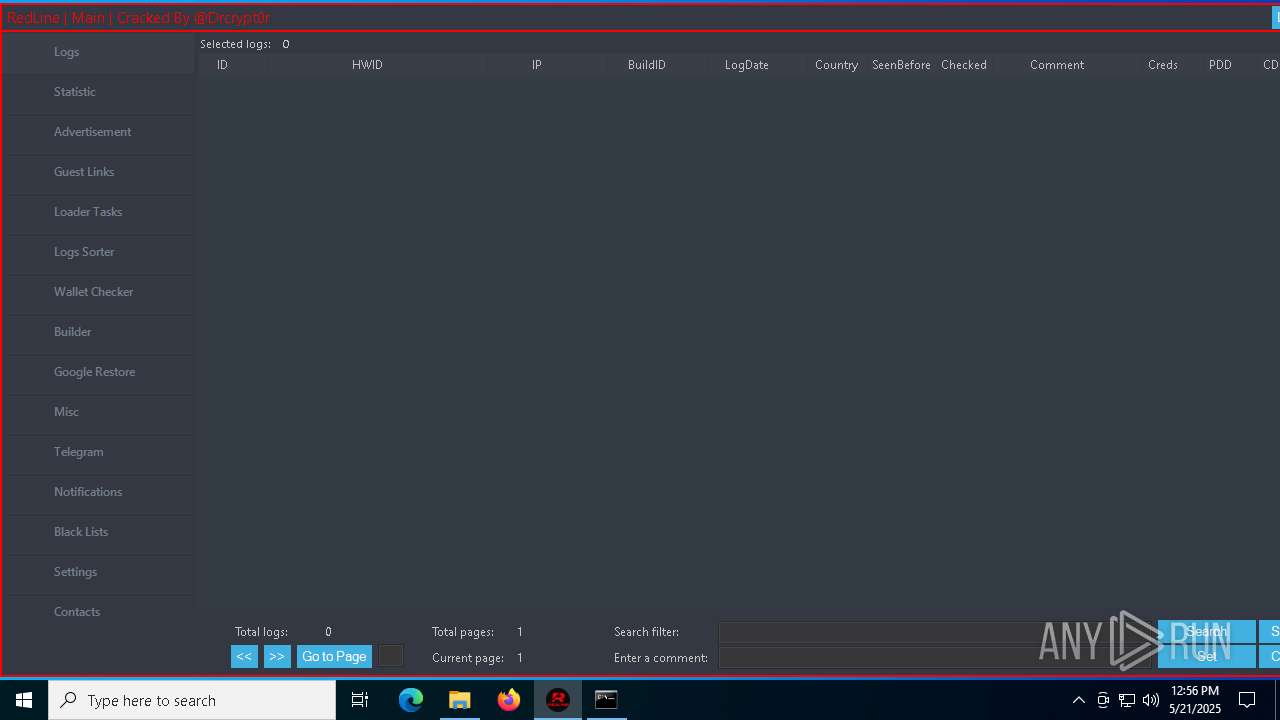
Total processes
196
Monitored processes
62
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 668 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data" /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Crashpad" --annotation=IsOfficialBuild=1 --annotation=channel= --annotation=chromium-version=122.0.6261.70 "--annotation=exe=C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --annotation=plat=Win64 "--annotation=prod=Microsoft Edge" --annotation=ver=122.0.2365.59 --initial-client-data=0x300,0x304,0x308,0x2f8,0x310,0x7ffc88105fd8,0x7ffc88105fe4,0x7ffc88105ff0 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 668 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5296 --field-trial-handle=2376,i,12058881582156714989,4674696404766715862,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 728 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=2848 --field-trial-handle=2376,i,12058881582156714989,4674696404766715862,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1184 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | SppExtComObj.Exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1228 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=792 --field-trial-handle=2376,i,12058881582156714989,4674696404766715862,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1244 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6860 --field-trial-handle=2628,i,2109747789952910996,5692686592370384135,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1276 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" "https://github.com/Drcrypt0r/Redline-Stealer-v30.2-Cracked/releases/download/RedlineStealer/Redline.Stealer.v30.2.Cracked.zip" | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1324 | "C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe" --type=utility --utility-sub-type=winrt_app_id.mojom.WinrtAppIdService --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=6424 --field-trial-handle=2628,i,2109747789952910996,5692686592370384135,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: PWA Identity Proxy Host Exit code: 3221226029 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1348 | "C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe" --type=utility --utility-sub-type=winrt_app_id.mojom.WinrtAppIdService --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=4804 --field-trial-handle=2376,i,12058881582156714989,4674696404766715862,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: PWA Identity Proxy Host Exit code: 3221226029 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1348 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=5316 --field-trial-handle=2376,i,12058881582156714989,4674696404766715862,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
25 862
Read events
25 761
Write events
97
Delete events
4
Modification events
| (PID) Process: | (1276) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (1276) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (1276) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (1276) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (1276) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 12DD66283B942F00 | |||
| (PID) Process: | (1276) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 9A0973283B942F00 | |||
| (PID) Process: | (1276) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\393858 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {921D3F7F-E0B0-4FD5-BD06-C25191C118D5} | |||
| (PID) Process: | (1276) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\393858 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {BFD0DEE0-724F-44F1-93D3-33053CD7CEED} | |||
| (PID) Process: | (1276) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 7AF4B0283B942F00 | |||
| (PID) Process: | (1276) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | MicrosoftEdgeAutoLaunch_29EBC4579851B72EE312C449CF839B1A |
Value: "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --no-startup-window --win-session-start | |||
Executable files
40
Suspicious files
145
Text files
87
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1276 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF10bc1e.TMP | — | |
MD5:— | SHA256:— | |||
| 1276 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF10bc1e.TMP | — | |
MD5:— | SHA256:— | |||
| 1276 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1276 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1276 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF10bc3d.TMP | — | |
MD5:— | SHA256:— | |||
| 1276 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF10bc2e.TMP | — | |
MD5:— | SHA256:— | |||
| 1276 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1276 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1276 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF10bc6c.TMP | — | |
MD5:— | SHA256:— | |||
| 1276 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
24
TCP/UDP connections
47
DNS requests
55
Threats
6
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.219.150.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7208 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
7208 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
4220 | svchost.exe | HEAD | 200 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/3aeadfbf-fadd-43ac-a5d9-c143db5f63d8?P1=1748302734&P2=404&P3=2&P4=PsqB9SKIch1KJ4Eh0j71G%2bU4Bru3XVMEoOzib2ginr3i6Sk5RBj9Xrn88ZEL6%2fOcM15m4Ix1veJ0Nkhqqip2kA%3d%3d | unknown | — | — | whitelisted |
4220 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/3aeadfbf-fadd-43ac-a5d9-c143db5f63d8?P1=1748302734&P2=404&P3=2&P4=PsqB9SKIch1KJ4Eh0j71G%2bU4Bru3XVMEoOzib2ginr3i6Sk5RBj9Xrn88ZEL6%2fOcM15m4Ix1veJ0Nkhqqip2kA%3d%3d | unknown | — | — | whitelisted |
4220 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/3aeadfbf-fadd-43ac-a5d9-c143db5f63d8?P1=1748302734&P2=404&P3=2&P4=PsqB9SKIch1KJ4Eh0j71G%2bU4Bru3XVMEoOzib2ginr3i6Sk5RBj9Xrn88ZEL6%2fOcM15m4Ix1veJ0Nkhqqip2kA%3d%3d | unknown | — | — | whitelisted |
4220 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/3aeadfbf-fadd-43ac-a5d9-c143db5f63d8?P1=1748302734&P2=404&P3=2&P4=PsqB9SKIch1KJ4Eh0j71G%2bU4Bru3XVMEoOzib2ginr3i6Sk5RBj9Xrn88ZEL6%2fOcM15m4Ix1veJ0Nkhqqip2kA%3d%3d | unknown | — | — | whitelisted |
4220 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/3aeadfbf-fadd-43ac-a5d9-c143db5f63d8?P1=1748302734&P2=404&P3=2&P4=PsqB9SKIch1KJ4Eh0j71G%2bU4Bru3XVMEoOzib2ginr3i6Sk5RBj9Xrn88ZEL6%2fOcM15m4Ix1veJ0Nkhqqip2kA%3d%3d | unknown | — | — | whitelisted |
4220 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/3aeadfbf-fadd-43ac-a5d9-c143db5f63d8?P1=1748302734&P2=404&P3=2&P4=PsqB9SKIch1KJ4Eh0j71G%2bU4Bru3XVMEoOzib2ginr3i6Sk5RBj9Xrn88ZEL6%2fOcM15m4Ix1veJ0Nkhqqip2kA%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 23.219.150.101:80 | www.microsoft.com | AKAMAI-AS | CL | whitelisted |
— | — | 40.127.240.158:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
7316 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
1276 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
7316 | msedge.exe | 140.82.121.4:443 | github.com | GITHUB | US | whitelisted |
7316 | msedge.exe | 150.171.27.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7316 | msedge.exe | 13.107.9.158:443 | business.bing.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7316 | msedge.exe | 13.107.246.53:443 | edge-mobile-static.azureedge.net | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7316 | msedge.exe | 185.199.108.133:443 | objects.githubusercontent.com | FASTLY | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
github.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
business.bing.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
objects.githubusercontent.com |
| whitelisted |
edgeservices.bing.com |
| whitelisted |
update.googleapis.com |
| whitelisted |
www.bing.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | Misc activity | ET HUNTING Telegram API Domain in DNS Lookup |
6944 | Panel.exe | Misc activity | ET HUNTING Telegram API Certificate Observed |
6944 | Panel.exe | Misc activity | ET HUNTING Observed Telegram API Domain (api .telegram .org in TLS SNI) |
2196 | svchost.exe | Misc activity | ET HUNTING Telegram API Domain in DNS Lookup |
7804 | Panel.exe | Misc activity | ET HUNTING Observed Telegram API Domain (api .telegram .org in TLS SNI) |
7804 | Panel.exe | Misc activity | ET HUNTING Telegram API Certificate Observed |