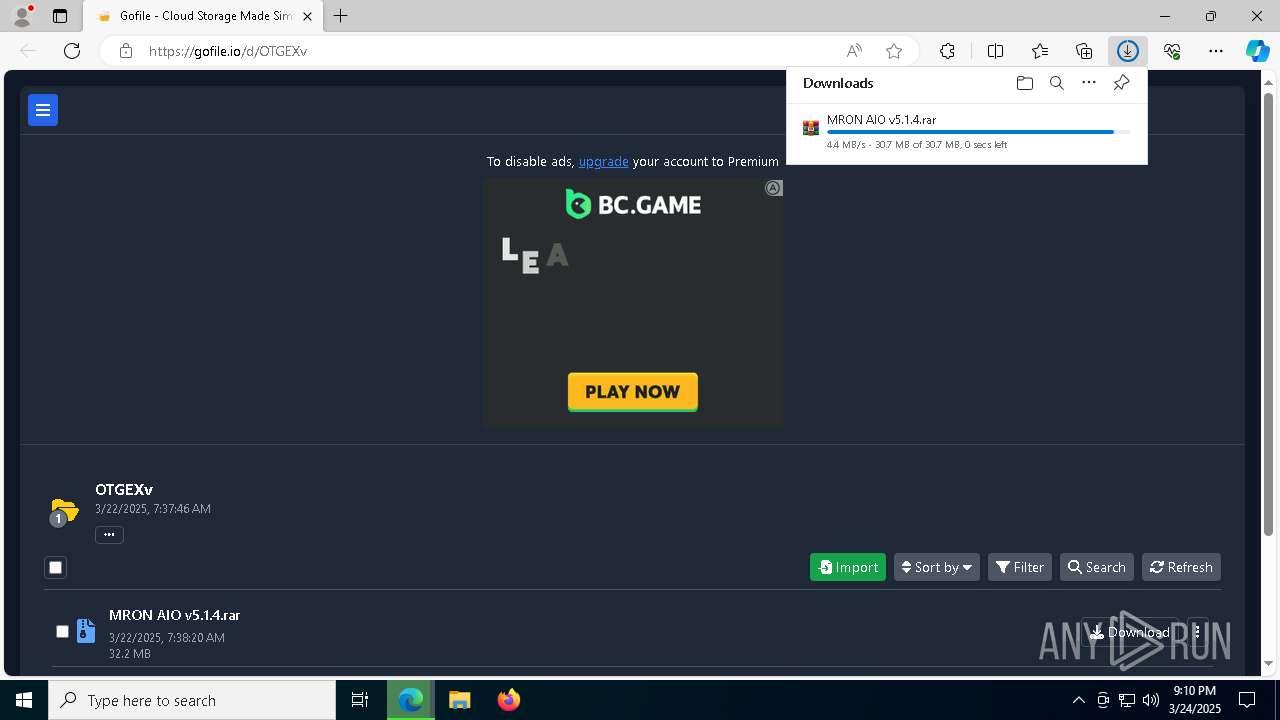
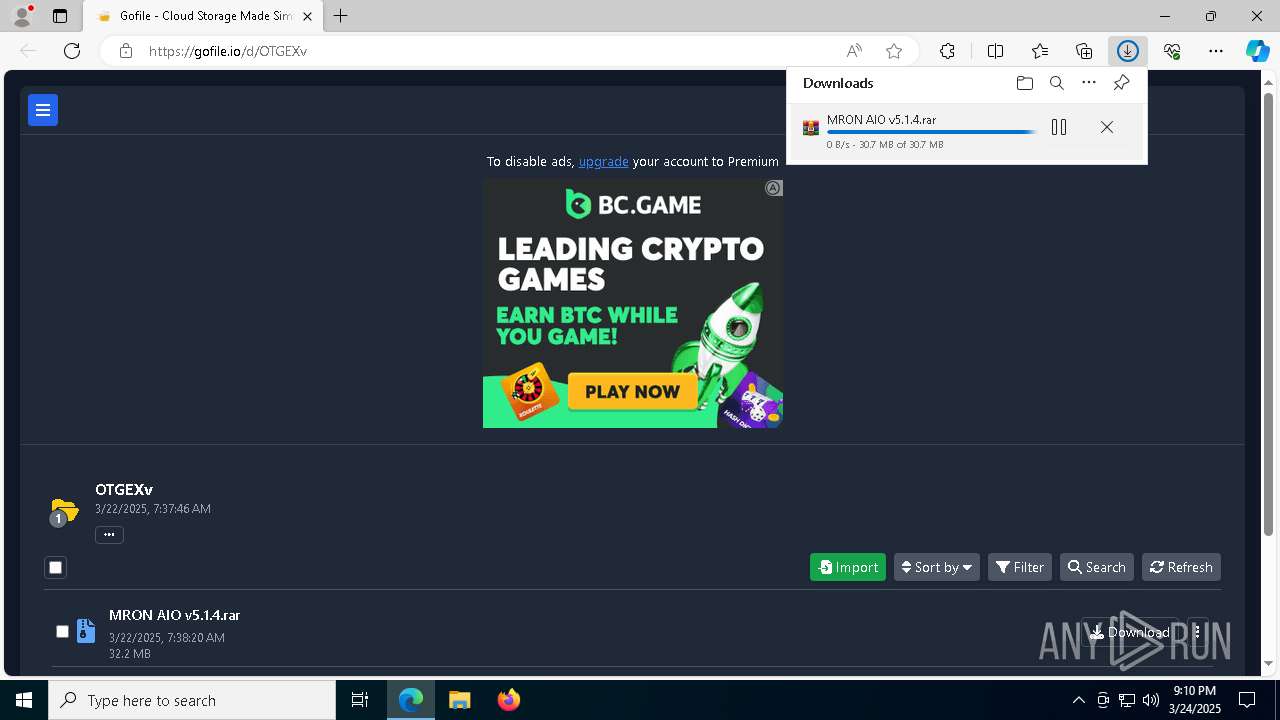
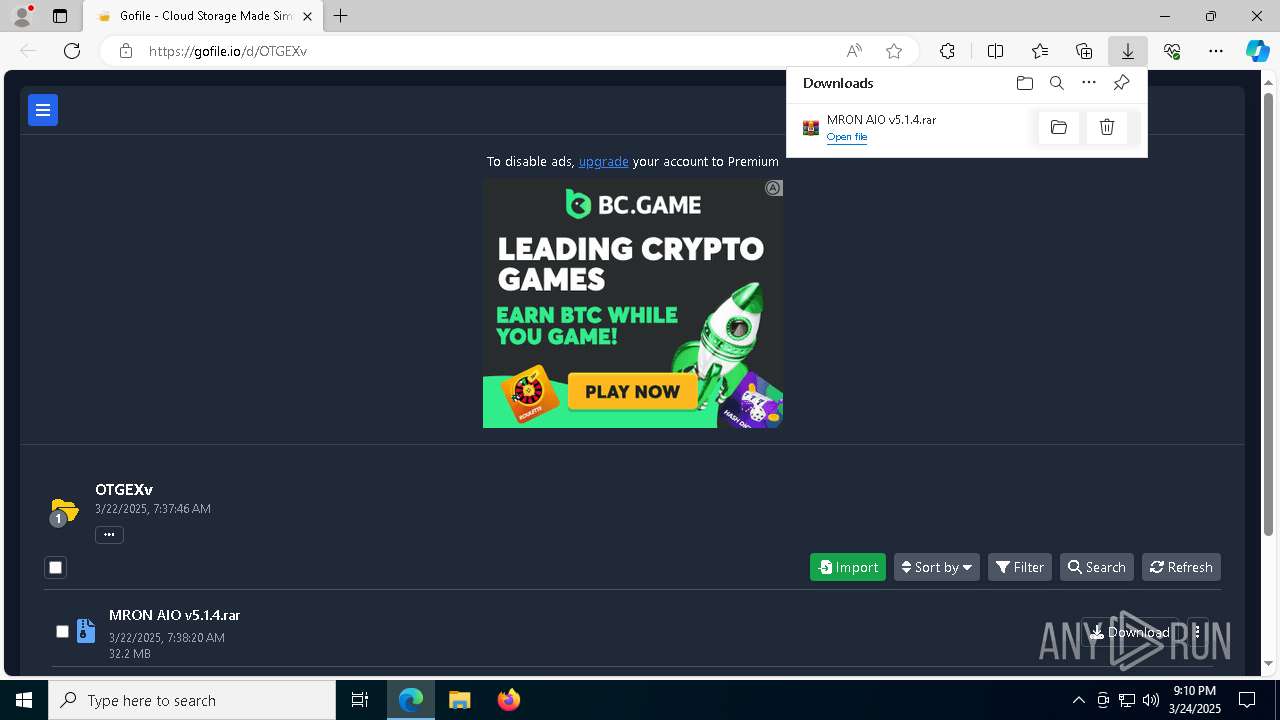
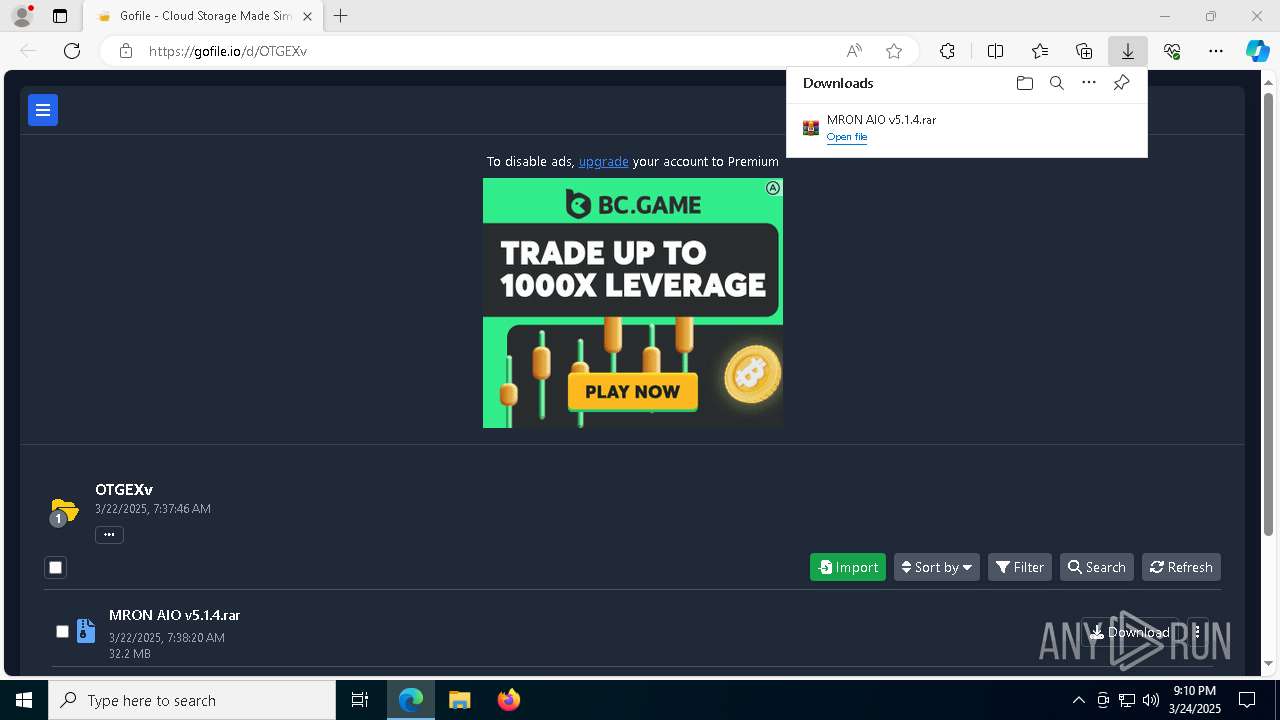
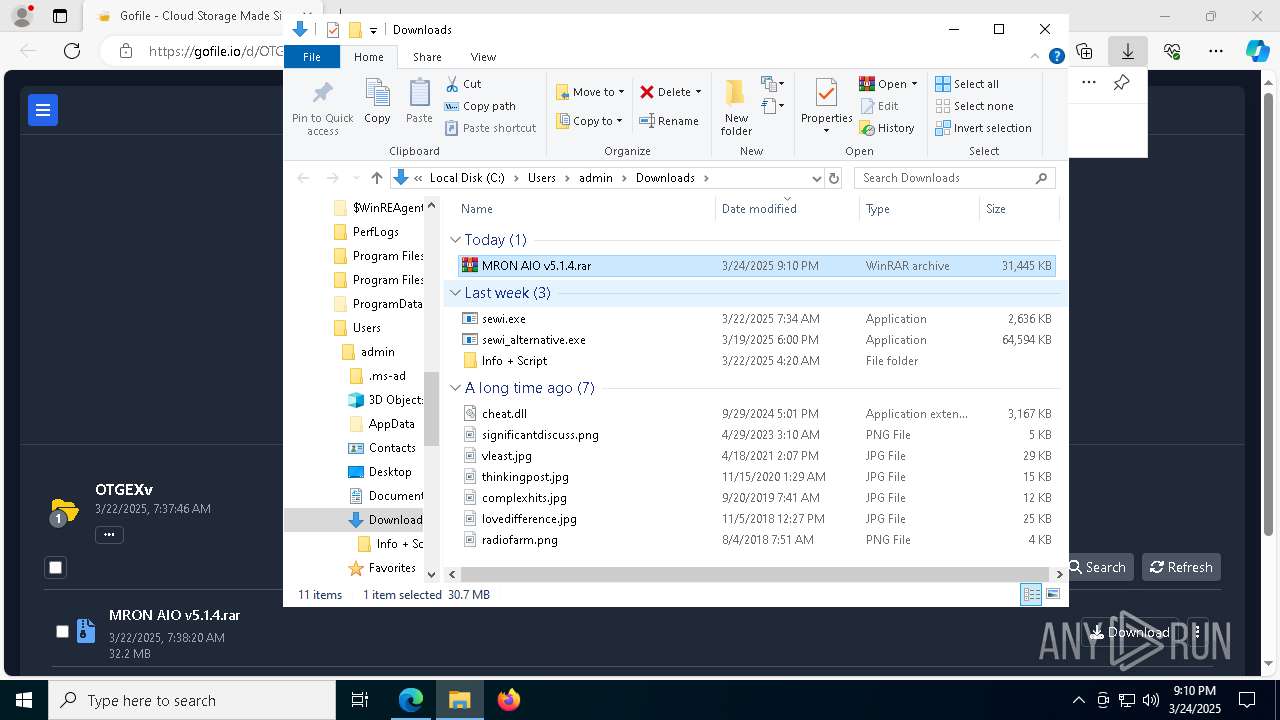
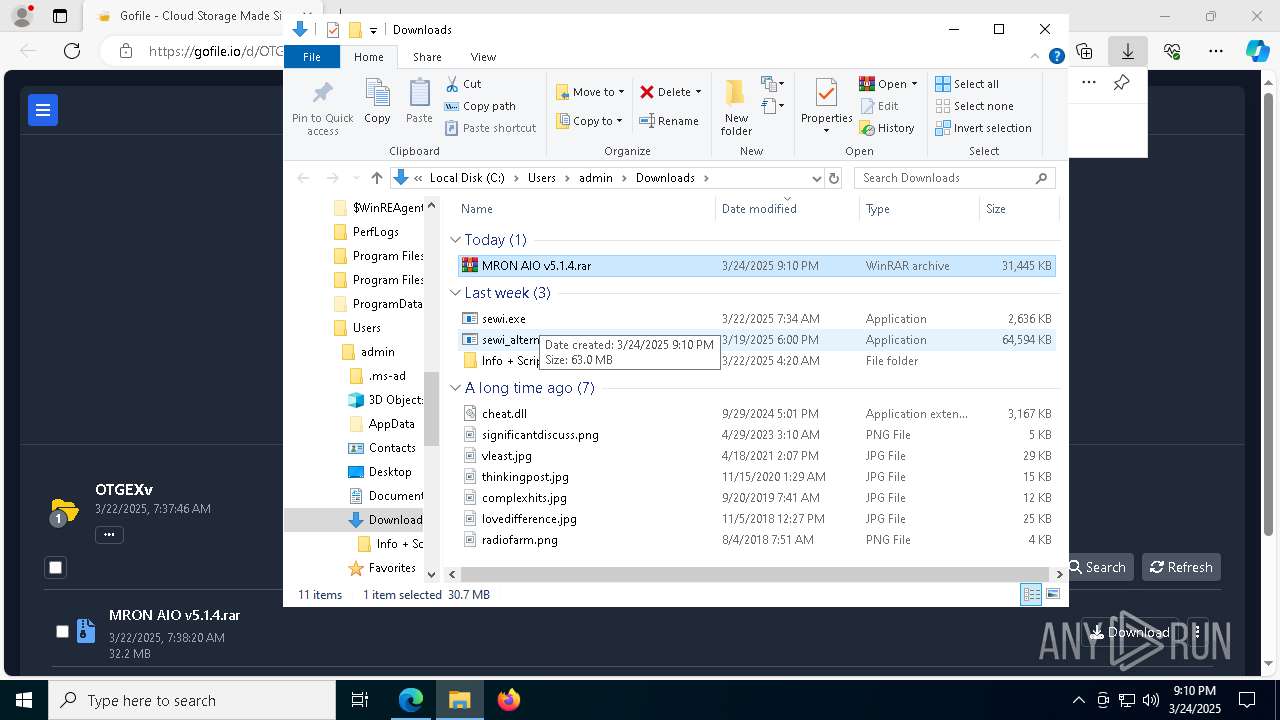
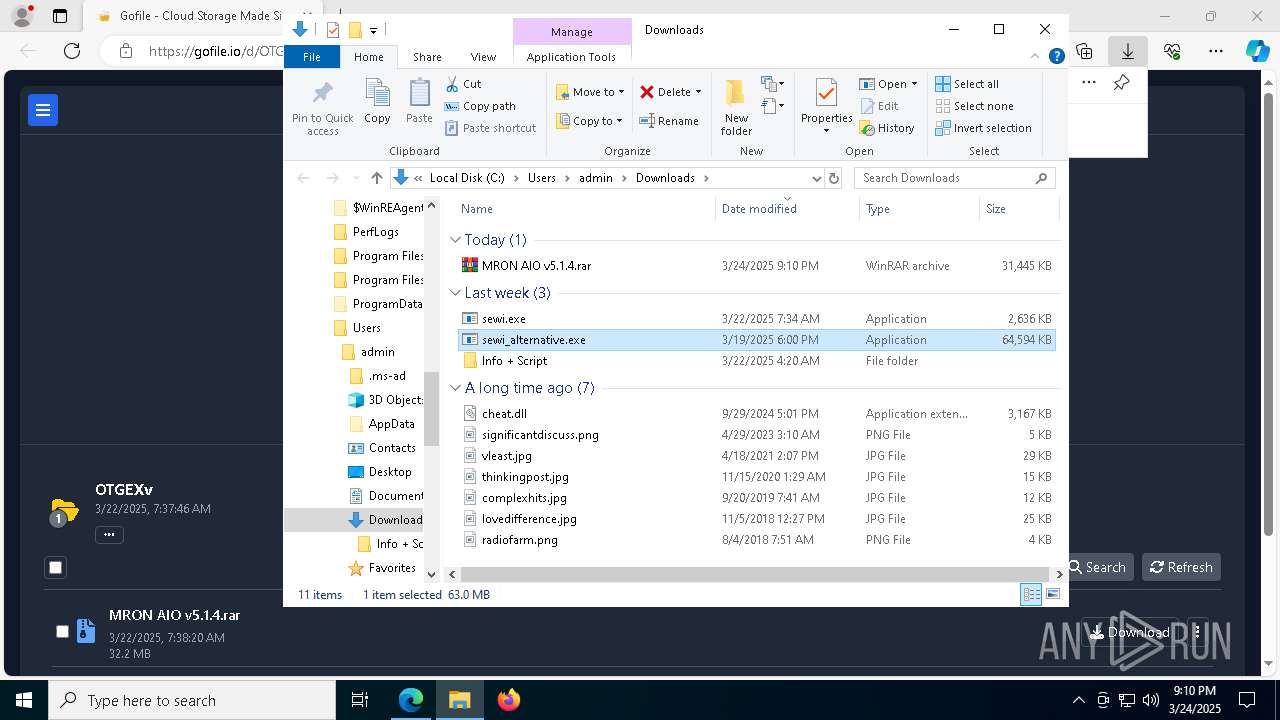
| URL: | https://gofile.io/d/OTGEXv |
| Full analysis: | https://app.any.run/tasks/4fc2cfbf-7169-4fe7-884c-4a1aeb025c44 |
| Verdict: | Malicious activity |
| Threats: | Crypto mining malware is a resource-intensive threat that infiltrates computers with the purpose of mining cryptocurrencies. This type of threat can be deployed either on an infected machine or a compromised website. In both cases the miner will utilize the computing power of the device and its network bandwidth. |
| Analysis date: | March 24, 2025, 21:10:10 |
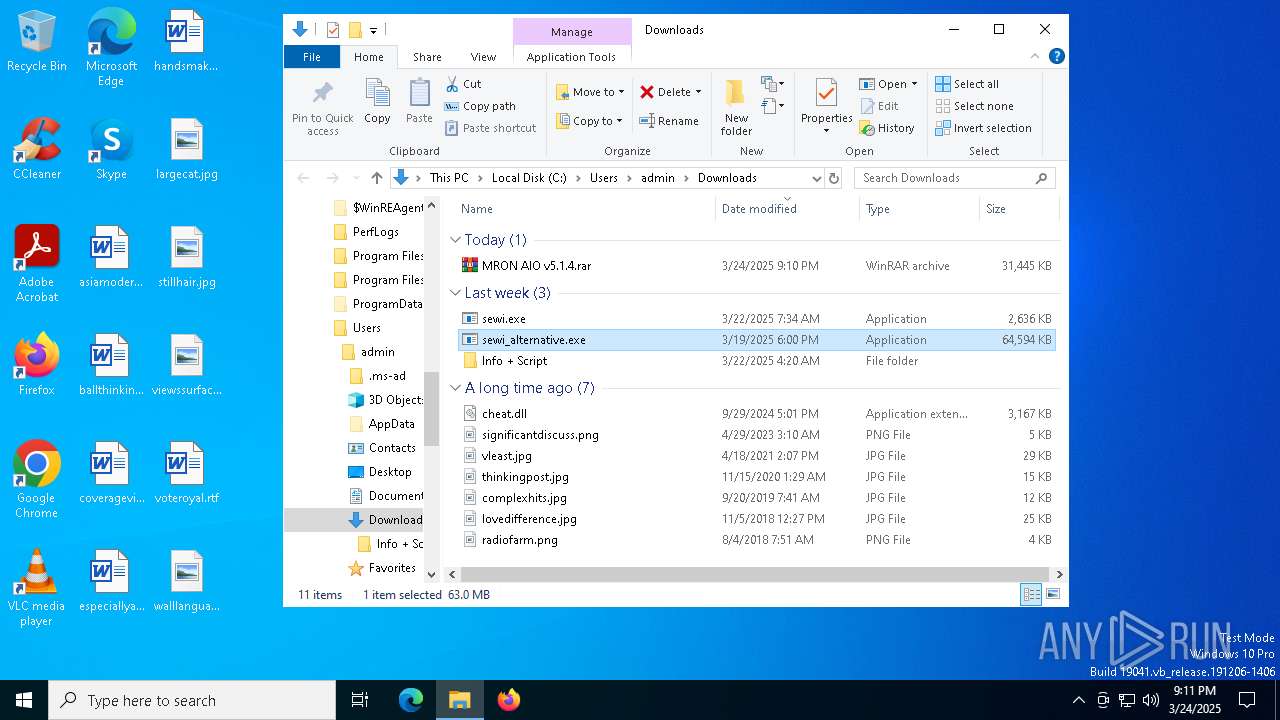
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | E970098F20E29B10A4DE91334D503516 |
| SHA1: | CE31D1468DDF24665DE5C1BC554F1989C9525429 |
| SHA256: | 7064EED5C814EDDCF482309EE7A11A73B50BDDF7DBB8AC658AC6061E3E5EACFC |
| SSDEEP: | 3:N8rxL1KF:2ZK |
MALICIOUS
Vulnerable driver has been detected
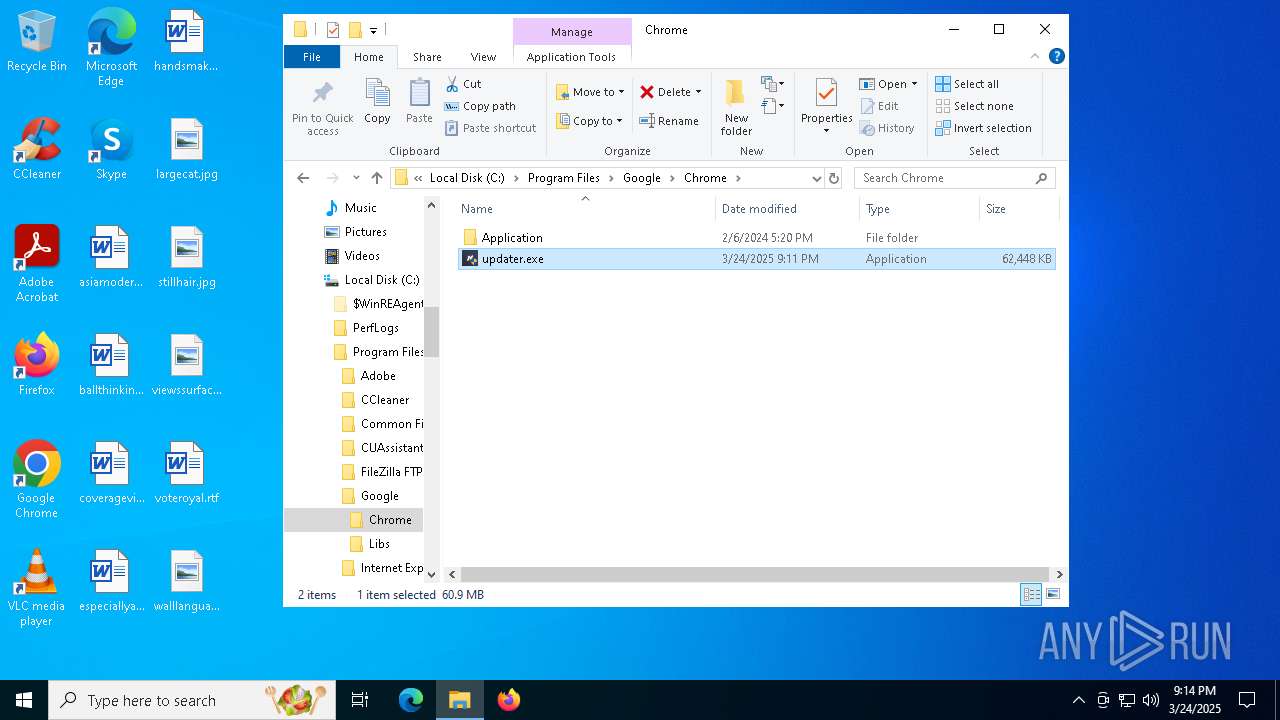
- sDQ0X.exe (PID: 5576)
- updater.exe (PID: 8392)
- updater.exe (PID: 7100)
MINER has been detected (SURICATA)
- svchost.exe (PID: 2196)
- svchost.exe (PID: 5436)
Connects to the CnC server
- svchost.exe (PID: 5436)
XMRIG has been detected (YARA)
- svchost.exe (PID: 5436)
XORed URL has been found (YARA)
- svchost.exe (PID: 5436)
SUSPICIOUS
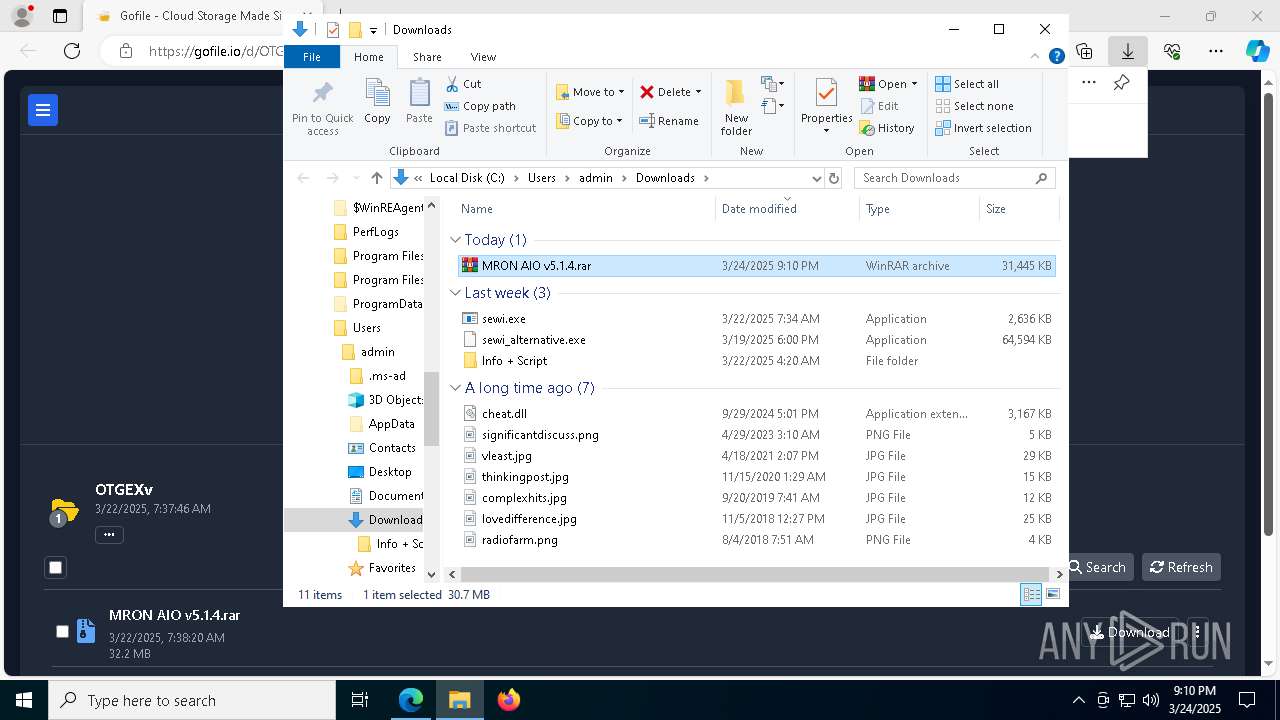
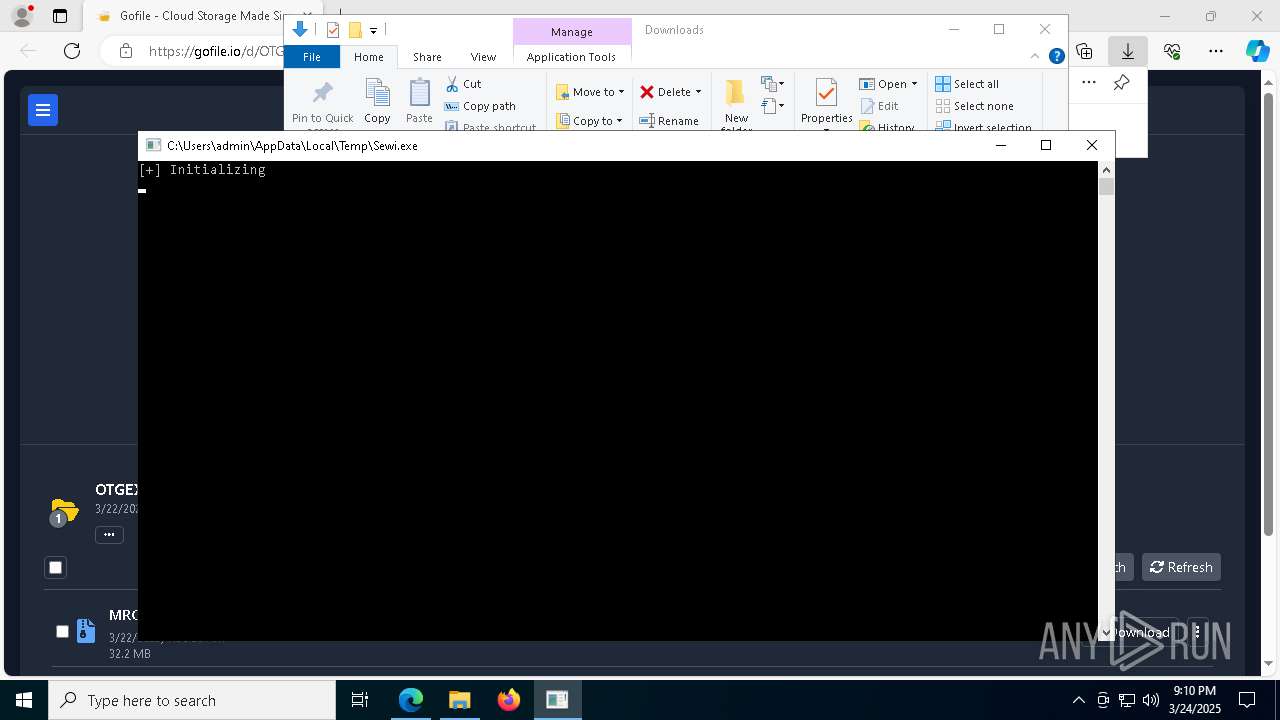
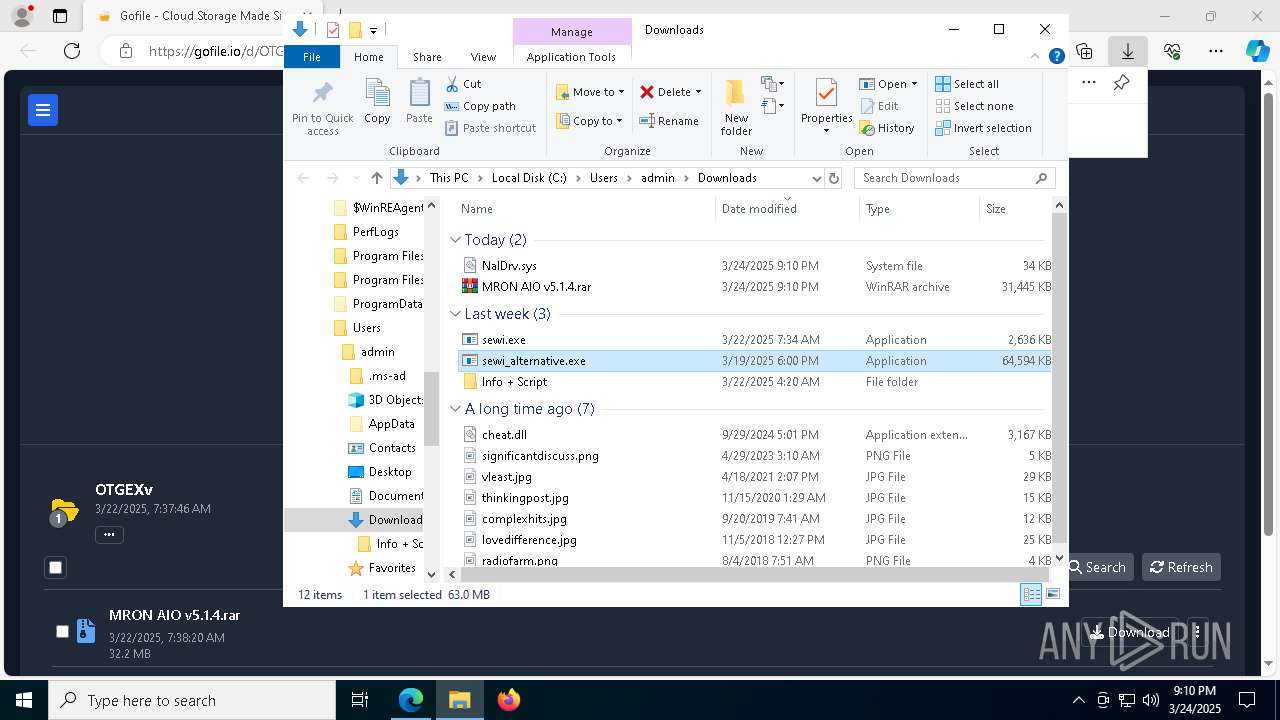
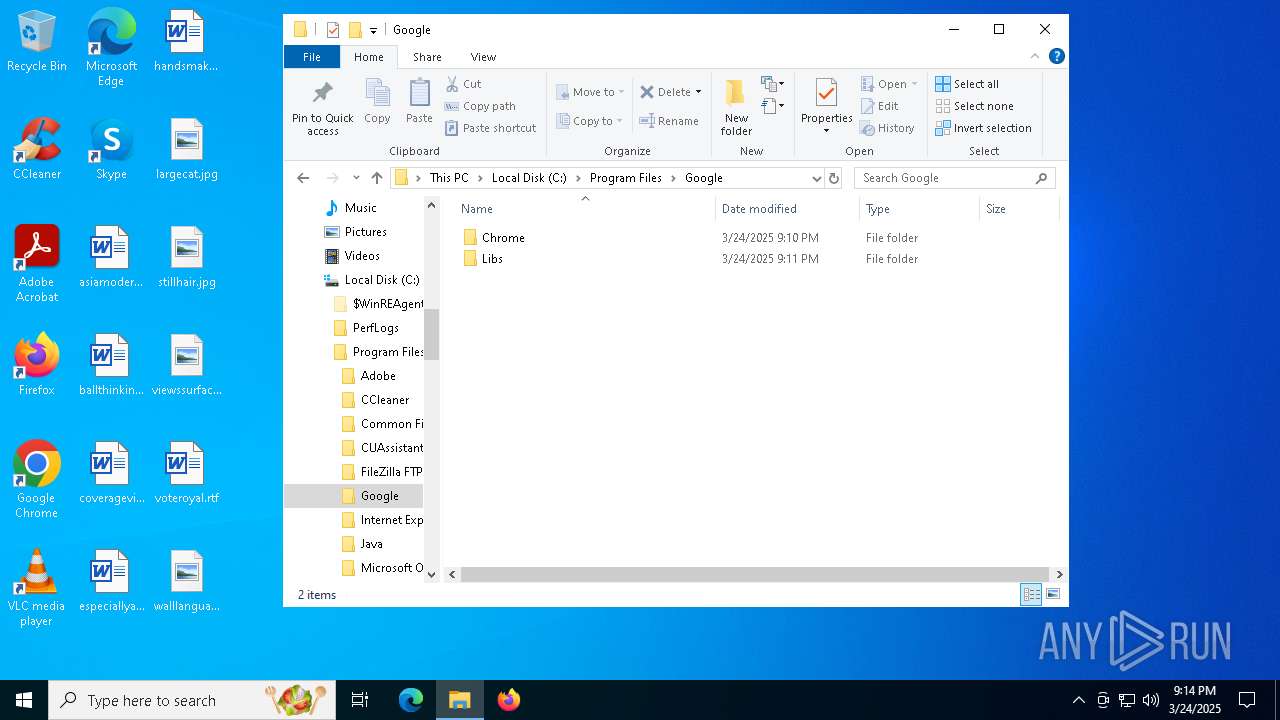
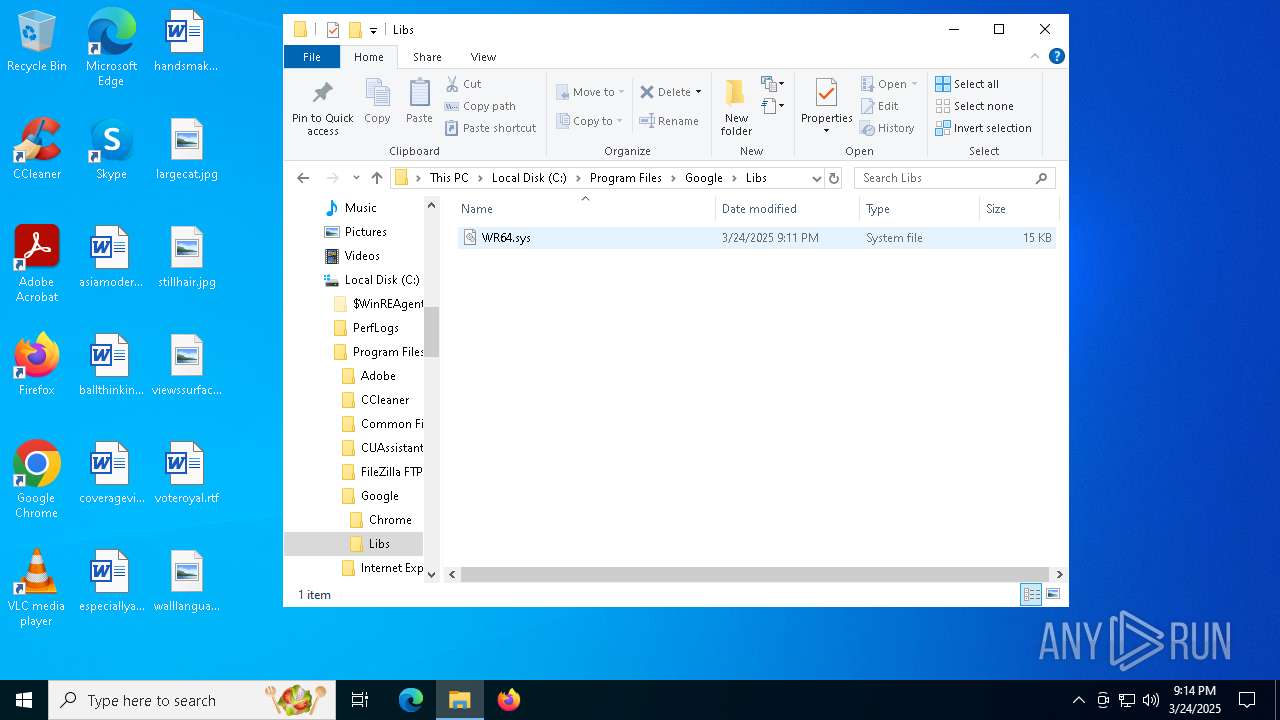
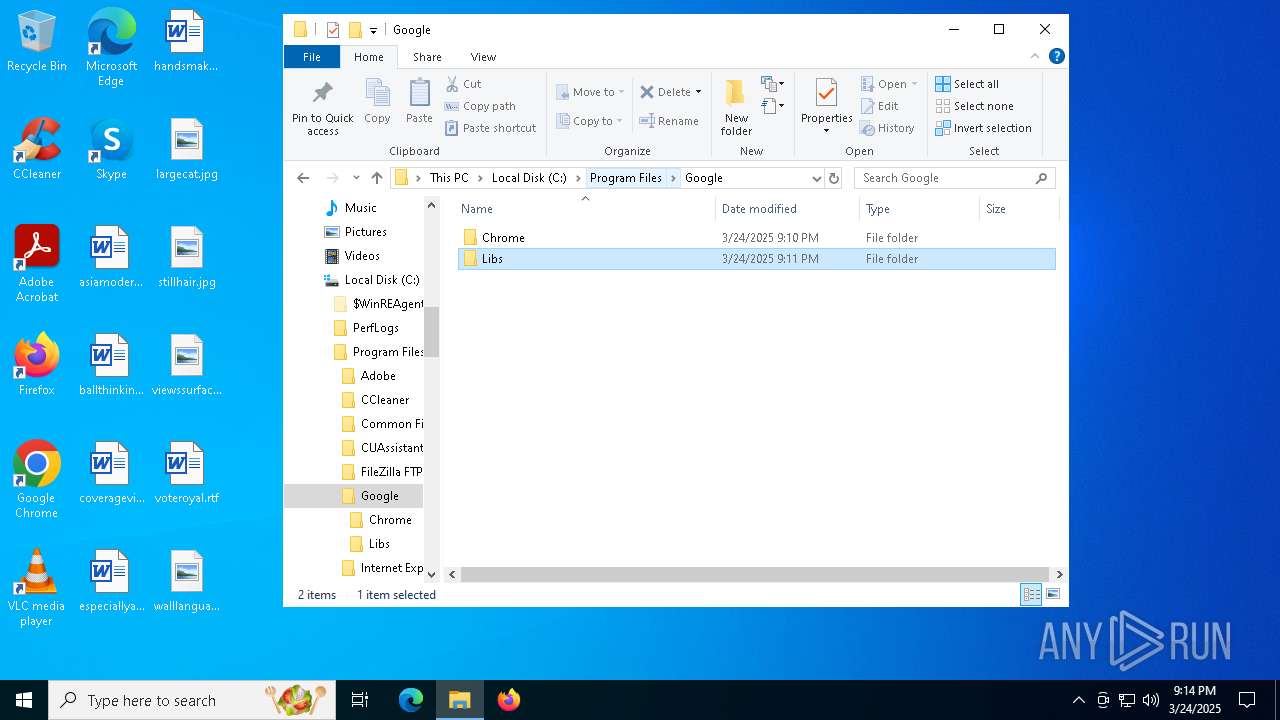
Drops a system driver (possible attempt to evade defenses)
- Sewi.exe (PID: 8340)
- sDQ0X.exe (PID: 5576)
- updater.exe (PID: 8392)
- updater.exe (PID: 7100)
Reads security settings of Internet Explorer
- Sewi.exe (PID: 8340)
- sewi_alternative.exe (PID: 6712)
Executable content was dropped or overwritten
- Sewi.exe (PID: 8340)
- sDQ0X.exe (PID: 5576)
- updater.exe (PID: 8392)
- updater.exe (PID: 7100)
Reads the date of Windows installation
- Sewi.exe (PID: 8340)
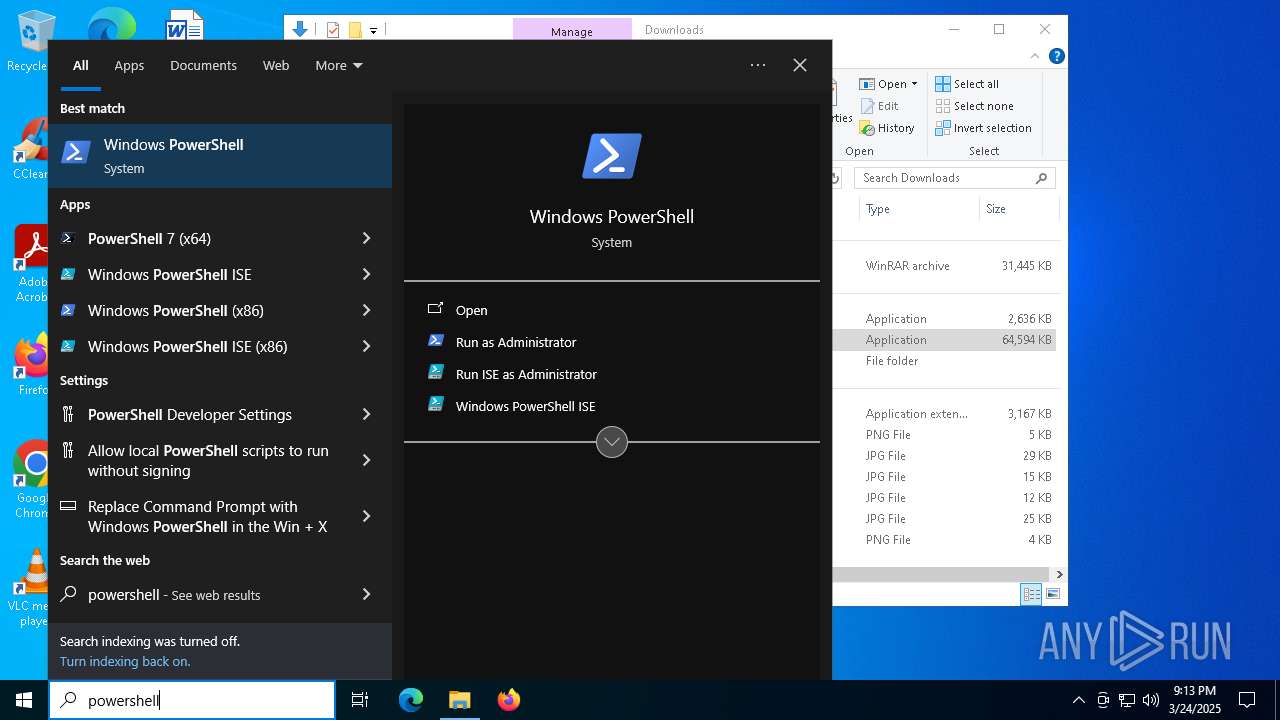
Manipulates environment variables
- powershell.exe (PID: 632)
- powershell.exe (PID: 8436)
- powershell.exe (PID: 3016)
Creates or modifies Windows services
- sDQ0X.exe (PID: 5576)
Stops a currently running service
- sc.exe (PID: 8348)
- sc.exe (PID: 8736)
- sc.exe (PID: 8272)
- sc.exe (PID: 8748)
- sc.exe (PID: 8908)
- sc.exe (PID: 6712)
- sc.exe (PID: 9144)
- sc.exe (PID: 9152)
- sc.exe (PID: 8712)
- sc.exe (PID: 7668)
- sc.exe (PID: 236)
- sc.exe (PID: 5936)
- sc.exe (PID: 232)
- sc.exe (PID: 5860)
- sc.exe (PID: 5848)
Starts SC.EXE for service management
- cmd.exe (PID: 8896)
- cmd.exe (PID: 8336)
- cmd.exe (PID: 8308)
Uses powercfg.exe to modify the power settings
- cmd.exe (PID: 8928)
- cmd.exe (PID: 6264)
- cmd.exe (PID: 9136)
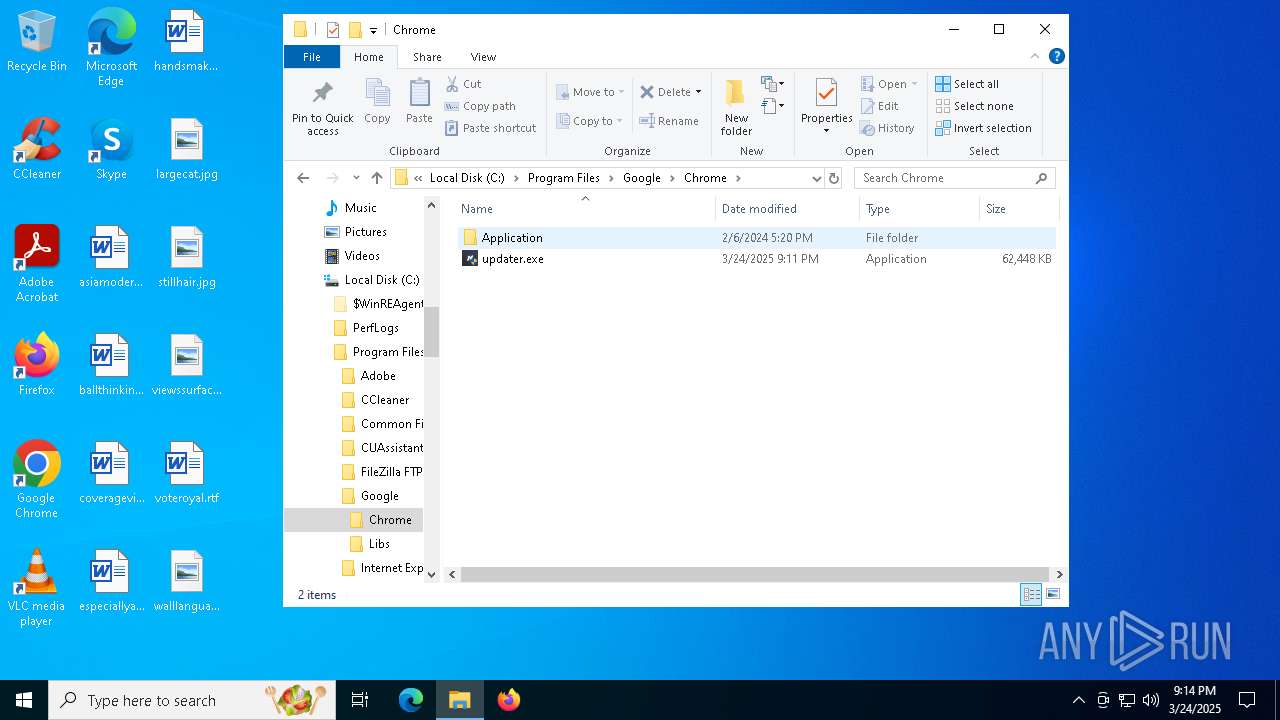
The process executes via Task Scheduler
- updater.exe (PID: 8392)
Crypto Currency Mining Activity Detected
- svchost.exe (PID: 2196)
Potential Corporate Privacy Violation
- svchost.exe (PID: 5436)
INFO
Application launched itself
- msedge.exe (PID: 4024)
- msedge.exe (PID: 8056)
Checks supported languages
- identity_helper.exe (PID: 2236)
- Sewi.exe (PID: 8340)
- sDQ0X.exe (PID: 5576)
- updater.exe (PID: 8392)
- sewi_alternative.exe (PID: 6712)
- tomas.exe (PID: 8312)
- identity_helper.exe (PID: 5596)
- updater.exe (PID: 7100)
Reads the computer name
- identity_helper.exe (PID: 2236)
- Sewi.exe (PID: 8340)
- sewi_alternative.exe (PID: 6712)
- identity_helper.exe (PID: 5596)
Reads Environment values
- identity_helper.exe (PID: 2236)
- identity_helper.exe (PID: 5596)
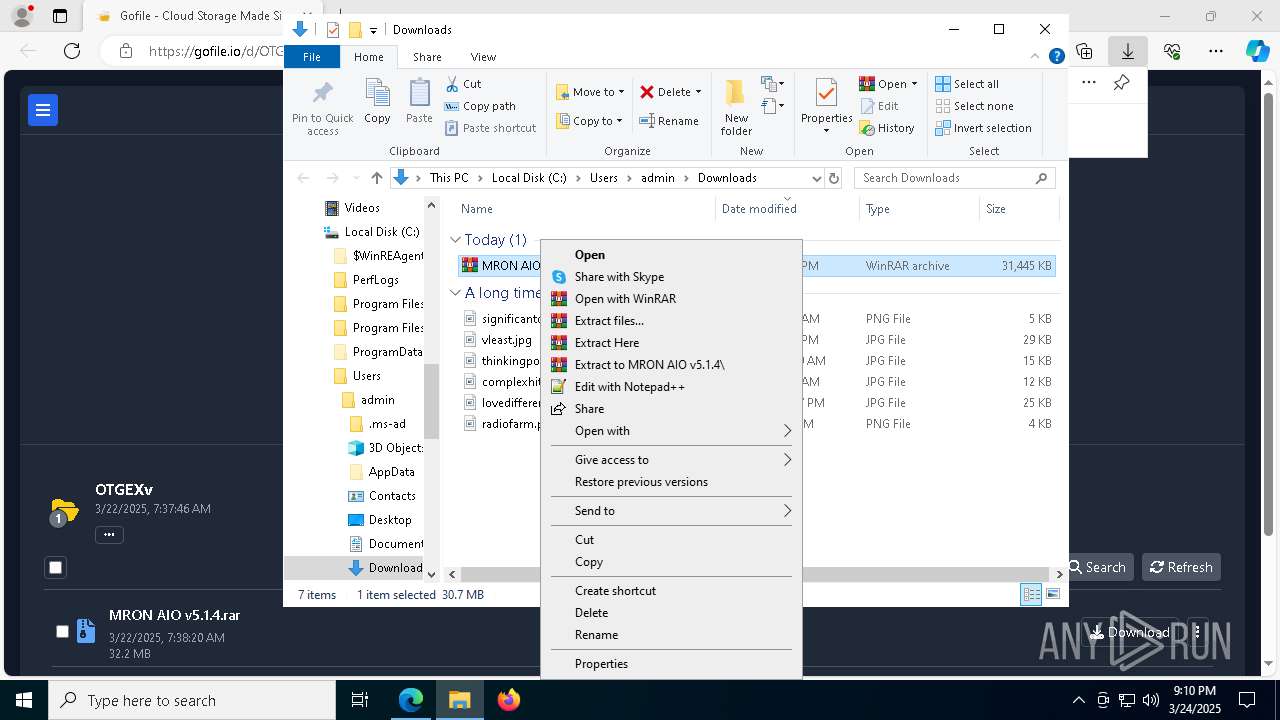
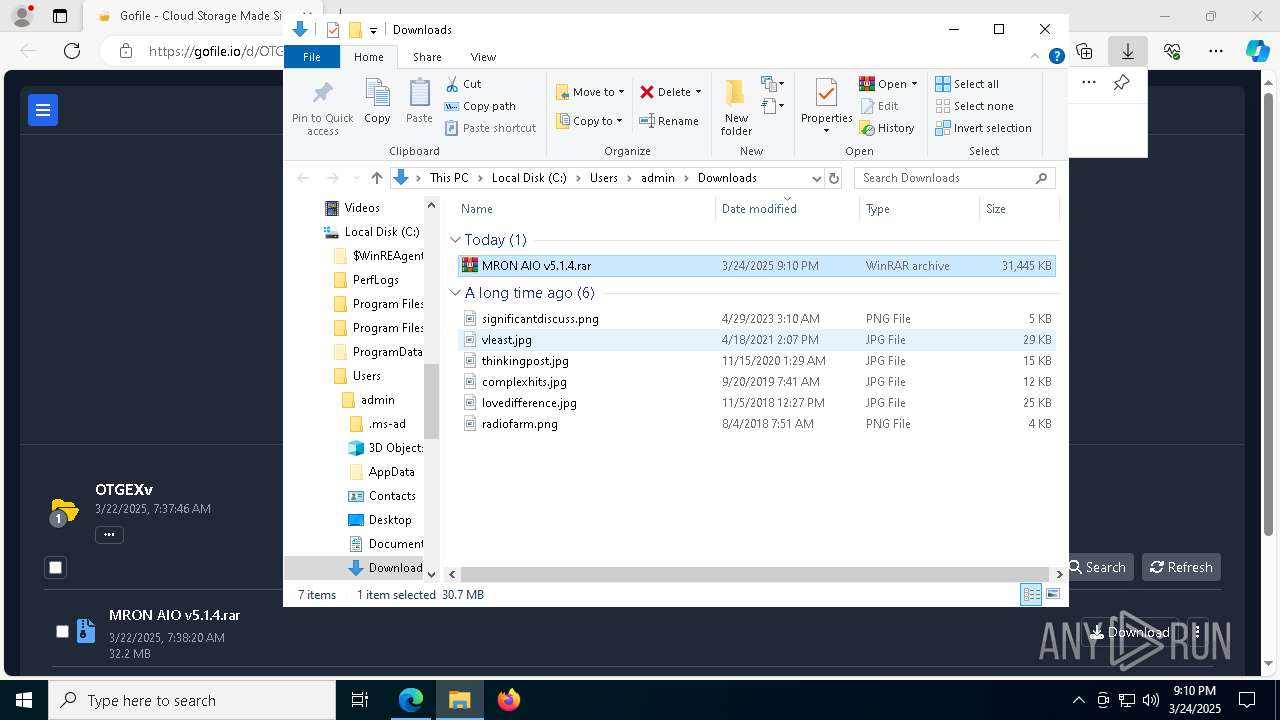
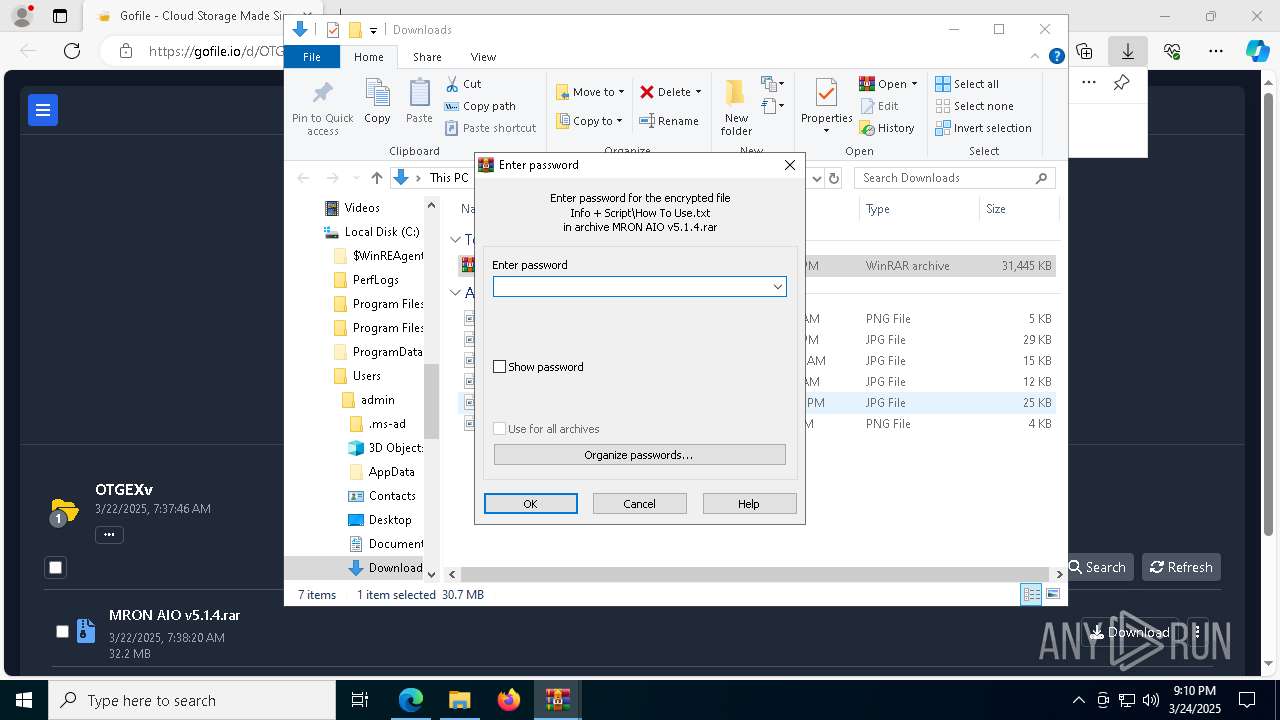
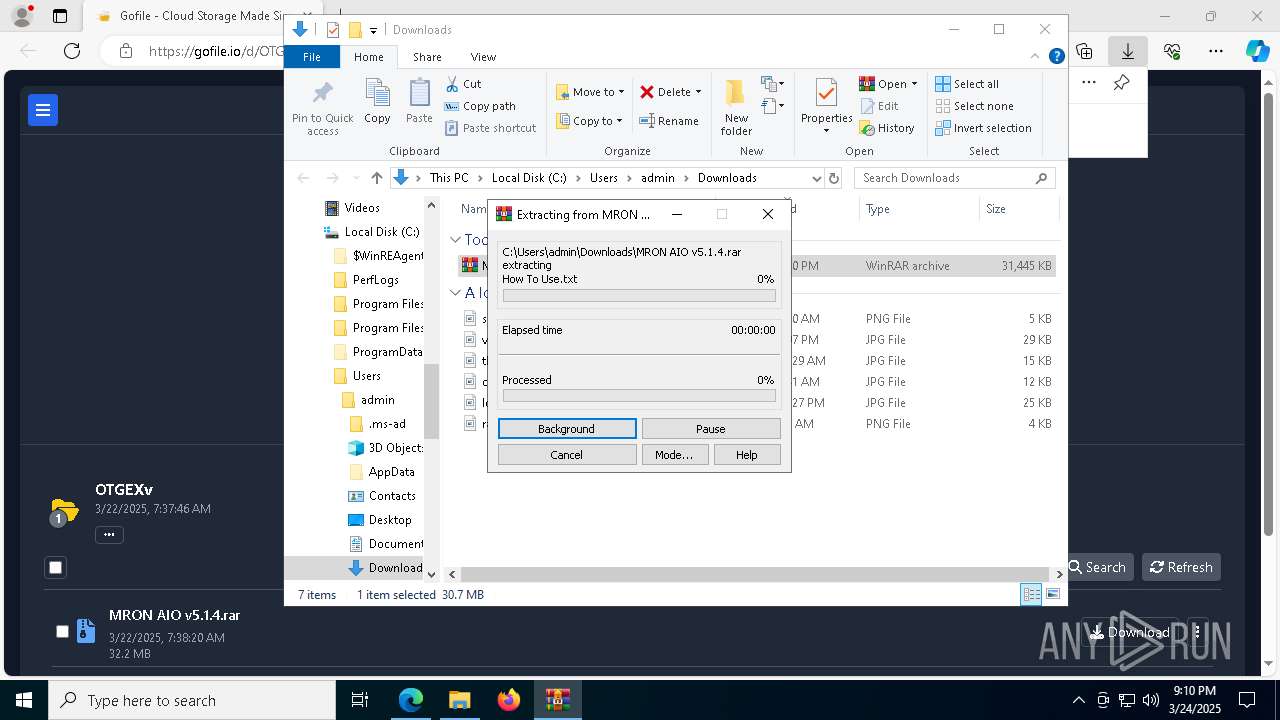
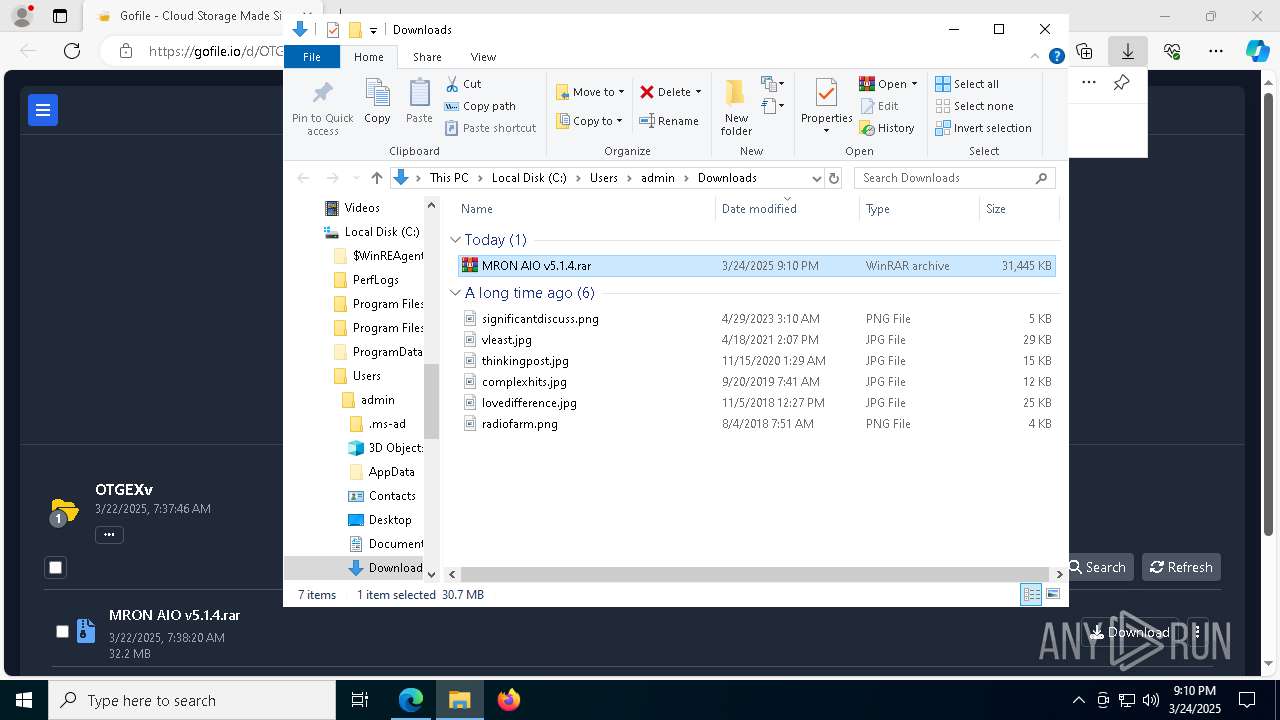
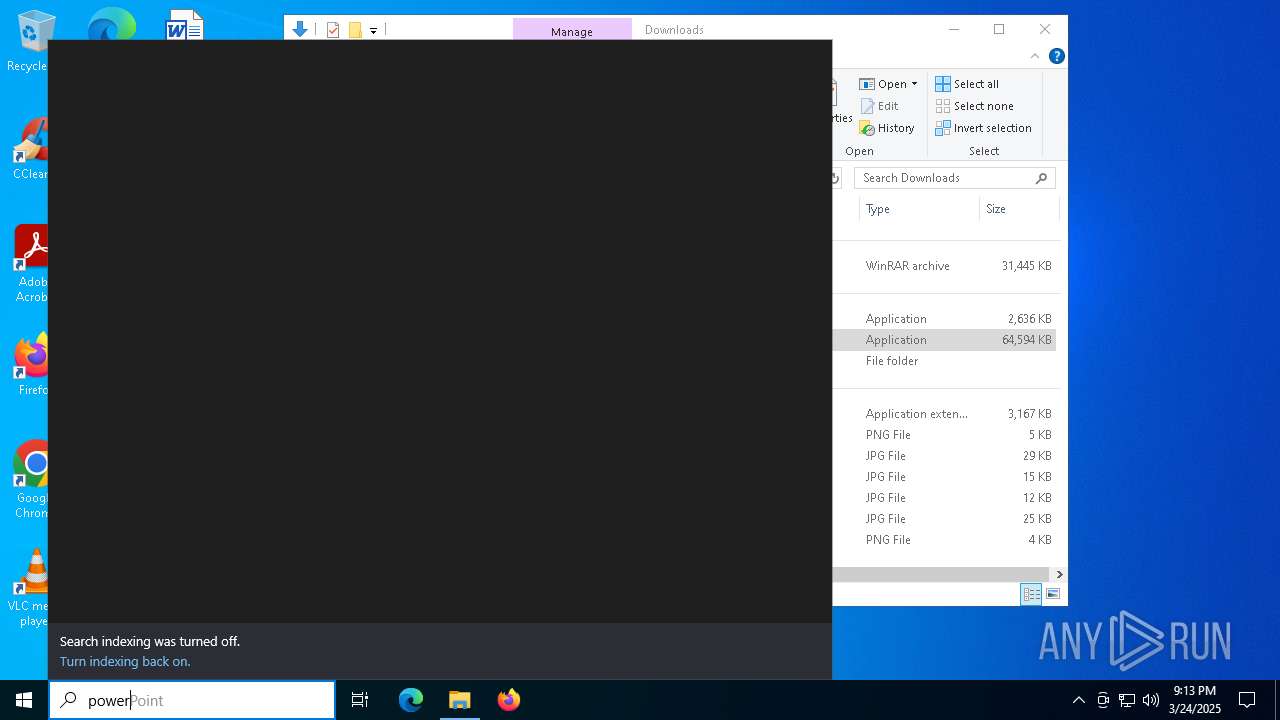
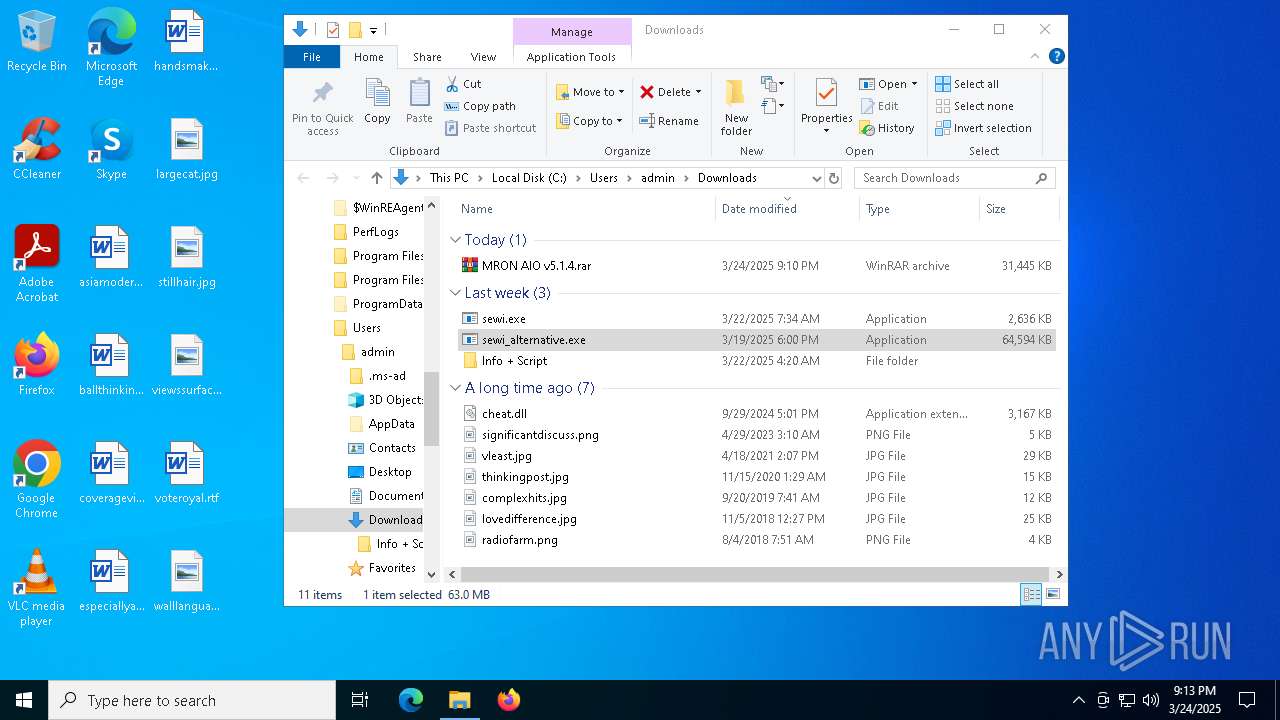
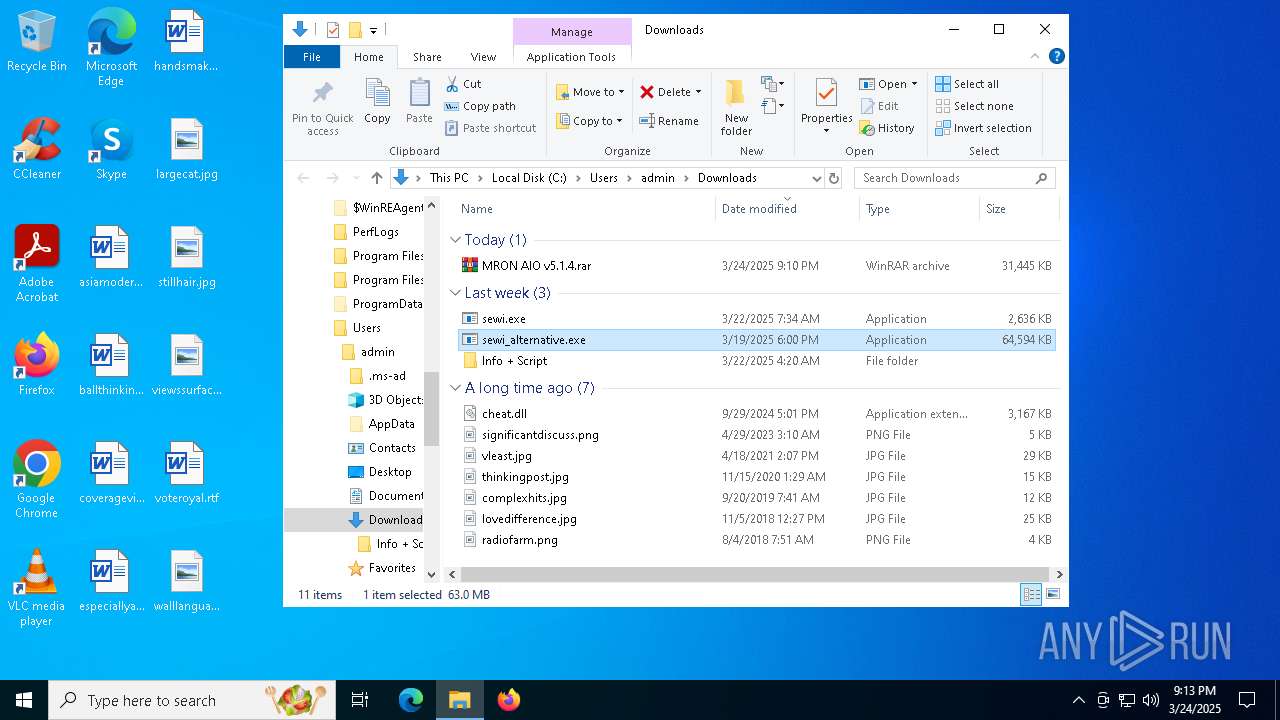
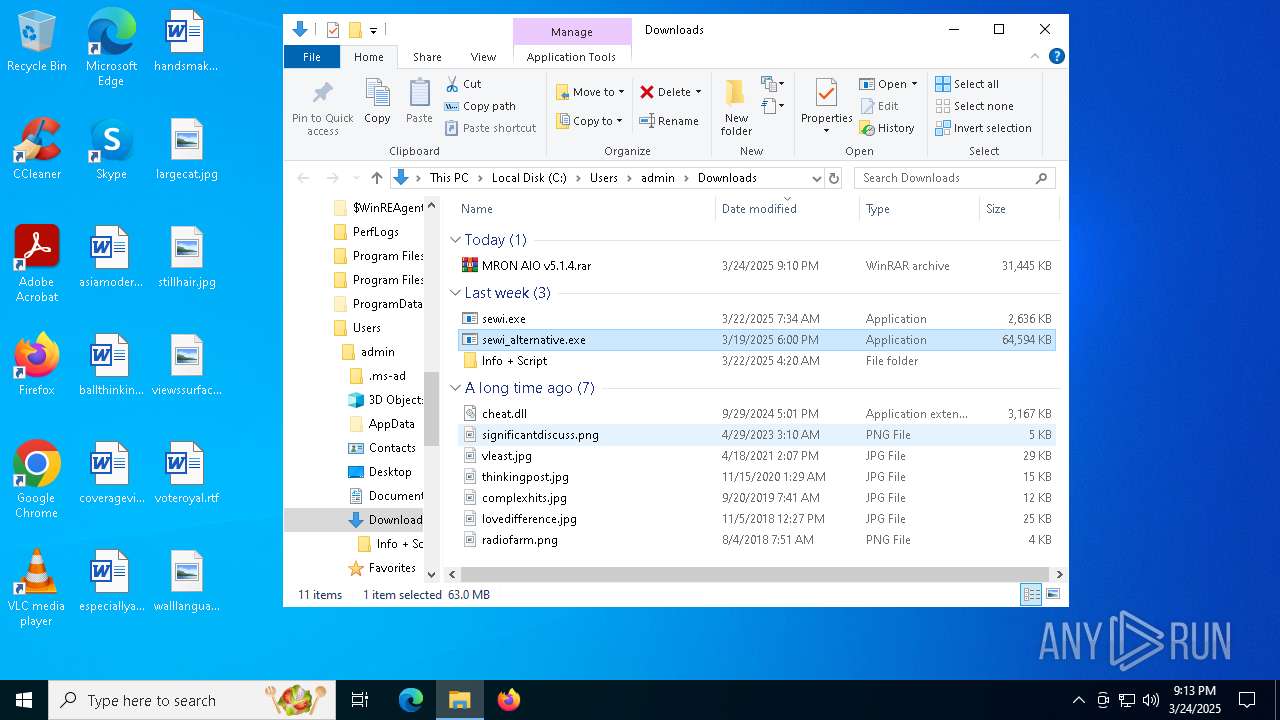
Manual execution by a user
- WinRAR.exe (PID: 9016)
- sewi_alternative.exe (PID: 6712)
- powershell.exe (PID: 632)
- cmd.exe (PID: 8896)
- cmd.exe (PID: 8928)
- powershell.exe (PID: 8952)
- schtasks.exe (PID: 7256)
- powershell.exe (PID: 8436)
- cmd.exe (PID: 8336)
- cmd.exe (PID: 6264)
- powershell.exe (PID: 3900)
- conhost.exe (PID: 5056)
- svchost.exe (PID: 5436)
- powershell.exe (PID: 7208)
- updater.exe (PID: 7100)
- updater.exe (PID: 8544)
- powershell.exe (PID: 3016)
- cmd.exe (PID: 8308)
- powershell.exe (PID: 5980)
- cmd.exe (PID: 9136)
Autorun file from Downloads
- msedge.exe (PID: 8828)
The sample compiled with english language support
- Sewi.exe (PID: 8340)
- sDQ0X.exe (PID: 5576)
- msedge.exe (PID: 8788)
Process checks computer location settings
- sewi_alternative.exe (PID: 6712)
- Sewi.exe (PID: 8340)
Reads the machine GUID from the registry
- sDQ0X.exe (PID: 5576)
Create files in a temporary directory
- sDQ0X.exe (PID: 5576)
- sewi_alternative.exe (PID: 6712)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 632)
- powershell.exe (PID: 8436)
- powershell.exe (PID: 3016)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 632)
- powershell.exe (PID: 8952)
- powershell.exe (PID: 8436)
- powershell.exe (PID: 3900)
- powershell.exe (PID: 3016)
- powershell.exe (PID: 5980)
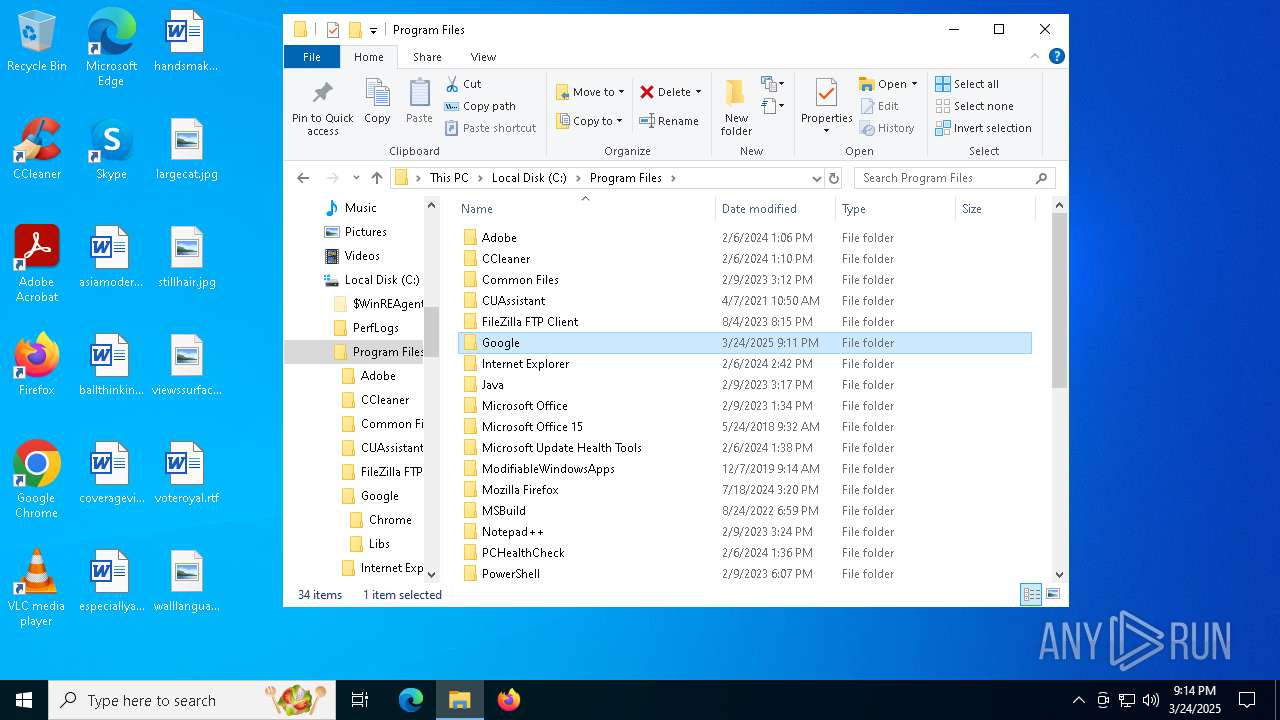
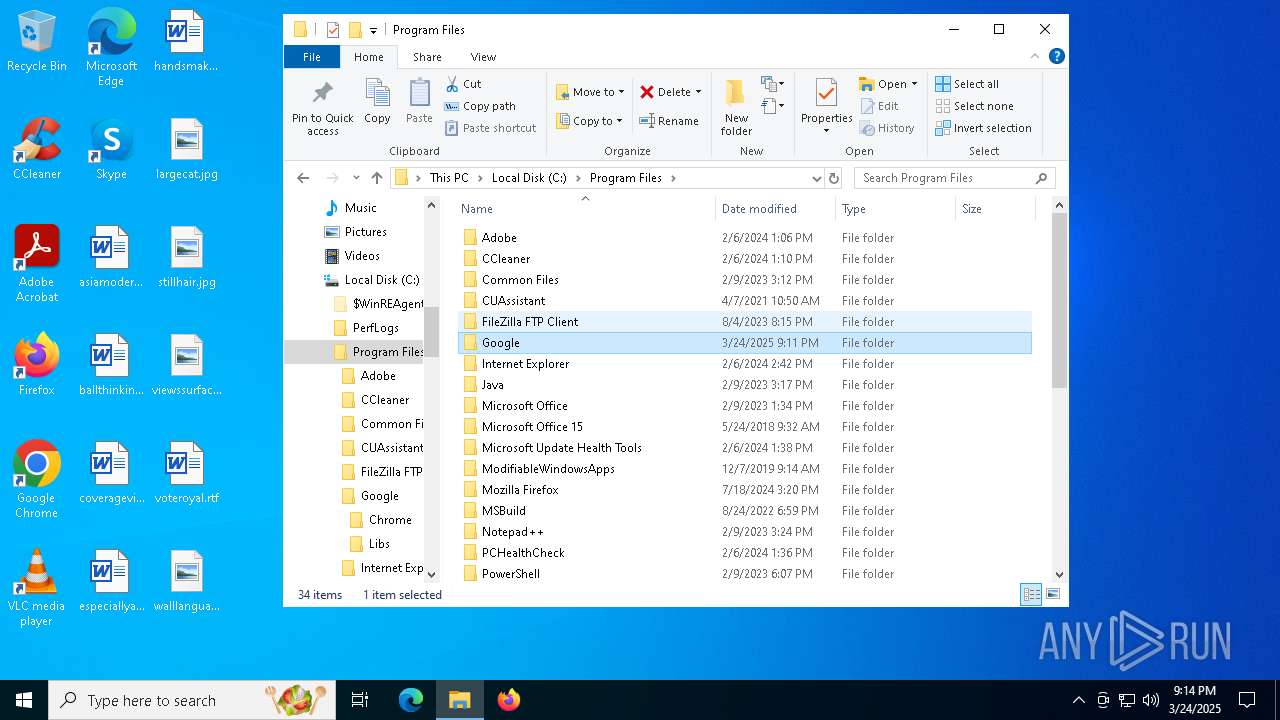
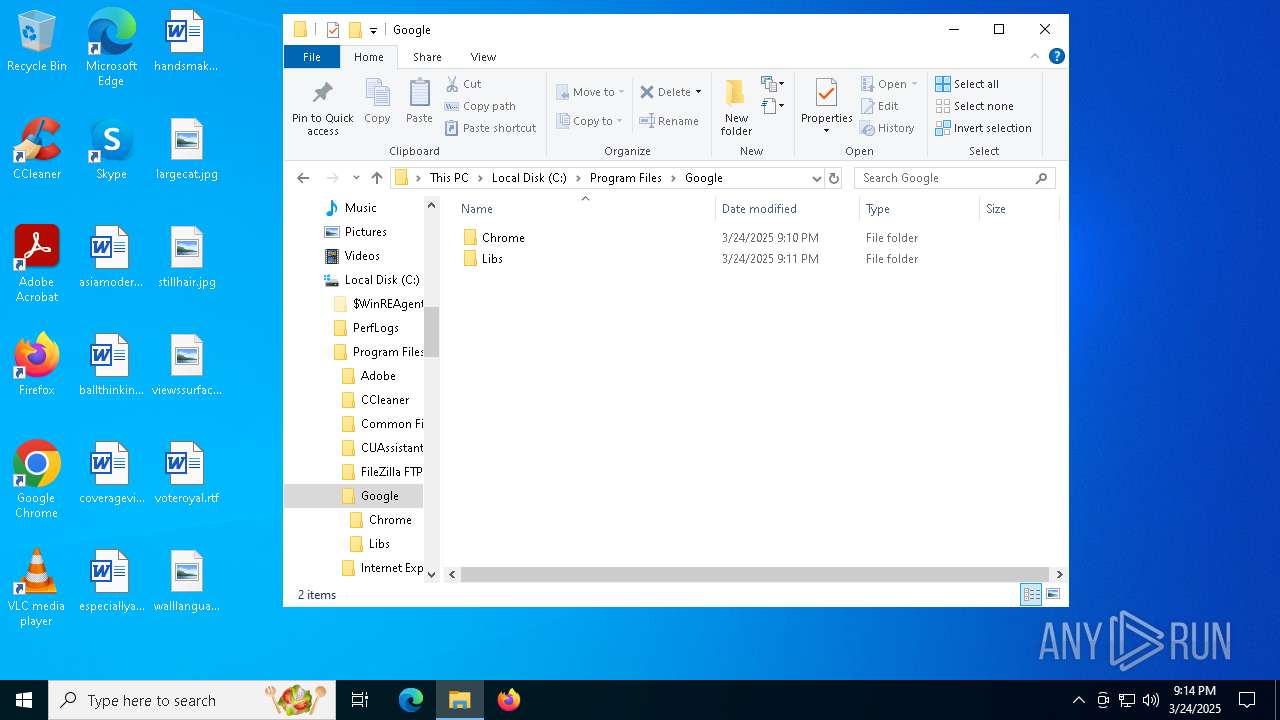
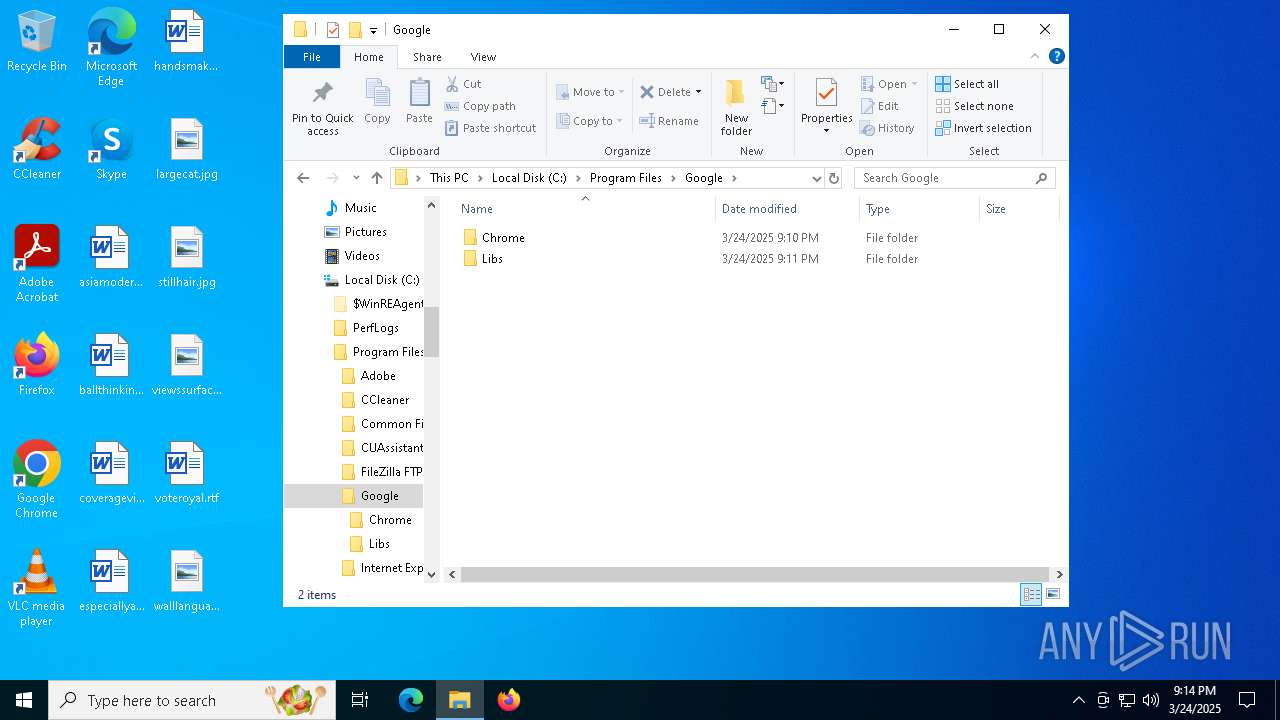
Creates files in the program directory
- tomas.exe (PID: 8312)
- updater.exe (PID: 8392)
The sample compiled with japanese language support
- updater.exe (PID: 8392)
- updater.exe (PID: 7100)
Executable content was dropped or overwritten
- msedge.exe (PID: 8788)
- WinRAR.exe (PID: 9016)
Reads the software policy settings
- slui.exe (PID: 4784)
- slui.exe (PID: 6592)
Checks proxy server information
- slui.exe (PID: 6592)
Checks current location (POWERSHELL)
- powershell.exe (PID: 7208)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
292
Monitored processes
152
Malicious processes
9
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 232 | sc stop UsoSvc | C:\Windows\System32\sc.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Service Control Manager Configuration Tool Exit code: 1062 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 236 | sc stop WaaSMedicSvc | C:\Windows\System32\sc.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Service Control Manager Configuration Tool Exit code: 1062 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 456 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=4244 --field-trial-handle=2256,i,4856407869183837205,5093574887166882233,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 516 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 632 | C:\WINDOWS\System32\WindowsPowerShell\v1.0\powershell.exe Add-MpPreference -ExclusionPath @($env:UserProfile, $env:ProgramFiles) -Force | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1012 | powercfg /x -hibernate-timeout-ac 0 | C:\Windows\System32\powercfg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Power Settings Command-Line Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1164 | "C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe" --type=utility --utility-sub-type=winrt_app_id.mojom.WinrtAppIdService --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=6160 --field-trial-handle=2256,i,4856407869183837205,5093574887166882233,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: PWA Identity Proxy Host Exit code: 3221226029 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1168 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=2508 --field-trial-handle=2352,i,7247082440950241461,6325770575896121980,262144 --variations-seed-version /prefetch:3 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | msedge.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1228 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=3516 --field-trial-handle=2352,i,7247082440950241461,6325770575896121980,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1388 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
52 639
Read events
52 591
Write events
46
Delete events
2
Modification events
| (PID) Process: | (4024) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (4024) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (4024) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (4024) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (4024) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: D39D4B50B38F2F00 | |||
| (PID) Process: | (4024) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: BBB75350B38F2F00 | |||
| (PID) Process: | (4024) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262992 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {6C5173E5-C39C-44A5-84B3-15D7CB8B6AEE} | |||
| (PID) Process: | (4024) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262992 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {D7A86D3A-D79E-4694-9210-677BAEBA46CF} | |||
| (PID) Process: | (4024) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262992 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {47839424-AC4D-4B17-83CA-9784B428B62B} | |||
| (PID) Process: | (4024) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 21B08950B38F2F00 | |||
Executable files
29
Suspicious files
463
Text files
138
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4024 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF10b344.TMP | — | |
MD5:— | SHA256:— | |||
| 4024 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4024 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF10b354.TMP | — | |
MD5:— | SHA256:— | |||
| 4024 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4024 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF10b354.TMP | — | |
MD5:— | SHA256:— | |||
| 4024 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4024 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF10b354.TMP | — | |
MD5:— | SHA256:— | |||
| 4024 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4024 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF10b354.TMP | — | |
MD5:— | SHA256:— | |||
| 4024 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
22
TCP/UDP connections
99
DNS requests
92
Threats
25
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 104.124.11.17:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
8156 | backgroundTaskHost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
7392 | msedge.exe | GET | 200 | 217.20.57.34:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/68591036-2289-4858-9f7f-9149e89c8a08?P1=1742999449&P2=404&P3=2&P4=ABw2snI6v7K7HEMIkdZrfw1rp%2fdZC9e%2bDMcjdAWWmD5lpH9U5%2bXtjm01vWv0XLakPCdMAMHoEPyCTtdees456Q%3d%3d | unknown | — | — | whitelisted |
7392 | msedge.exe | GET | 200 | 217.20.57.34:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/fb6dd03b-99d7-4cc8-a878-91c8e655c2d3?P1=1743003049&P2=404&P3=2&P4=KaHcwLFl%2fIs5JdN6ETKVkFhHrvXwTqYyZRQ%2bB6QMldY5y%2fWf6lajGKzNFQhDFGIOveJOUXhCxUuOW3C%2fdMr%2fHg%3d%3d | unknown | — | — | whitelisted |
7392 | msedge.exe | GET | 200 | 217.20.57.34:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/5cbc98ff-b69b-4fda-ad94-17ec2f9cf48b?P1=1742999450&P2=404&P3=2&P4=NhnHhqFQqNhUcXfbQLjRTE0BRpMXSAWnCOOGGvrgkpnnJtgi54tt2Z9V%2f5x%2f1%2bxxUiwqraUhgtJwlzGgJT7x9Q%3d%3d | unknown | — | — | whitelisted |
7392 | msedge.exe | GET | 200 | 217.20.57.34:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/84d3e481-77df-49da-bc37-0a994069ddb9?P1=1743114880&P2=404&P3=2&P4=FAOJFEUghqL5YeISbvZzDw%2bUAVKuxgVvJvOje%2bsDytlO39q9wFpxRfhrr55PPhCaltuqKNJQh%2fJ0bel4pbpl4Q%3d%3d | unknown | — | — | whitelisted |
7392 | msedge.exe | GET | 200 | 217.20.57.34:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/e9f25f54-9a54-4e31-91fd-7fd2ad4f4a2f?P1=1743006652&P2=404&P3=2&P4=XyTTYaJrf0aqSYD%2bsr43W3MoQJ%2frNwpS%2fBOftiGsUmqnzAFPGoPpxrzN4bfaDRRUv1I23WCiUnO2HHzrMZCi9w%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 104.124.11.17:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4024 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
7392 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7392 | msedge.exe | 51.91.7.6:443 | gofile.io | OVH SAS | FR | whitelisted |
7392 | msedge.exe | 13.107.246.45:443 | edge-mobile-static.azureedge.net | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7392 | msedge.exe | 13.107.6.158:443 | business.bing.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7392 | msedge.exe | 204.79.197.239:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
gofile.io |
| whitelisted |
edge.microsoft.com |
| whitelisted |
business.bing.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
bzib.nelreports.net |
| whitelisted |
www.bing.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7392 | msedge.exe | Potentially Bad Traffic | ET FILE_SHARING Online File Storage Domain in DNS Lookup (gofile .io) |
7392 | msedge.exe | Potentially Bad Traffic | ET FILE_SHARING Online File Storage Domain in DNS Lookup (gofile .io) |
7392 | msedge.exe | Misc activity | ET FILE_SHARING File Sharing Related Domain in TLS SNI (gofile .io) |
7392 | msedge.exe | Potentially Bad Traffic | ET FILE_SHARING Online File Storage Domain in DNS Lookup (gofile .io) |
7392 | msedge.exe | Potentially Bad Traffic | ET FILE_SHARING Online File Storage Domain in DNS Lookup (gofile .io) |
7392 | msedge.exe | Potentially Bad Traffic | ET FILE_SHARING Online File Storage Domain in DNS Lookup (gofile .io) |
7392 | msedge.exe | Misc activity | ET FILE_SHARING File Sharing Related Domain in TLS SNI (gofile .io) |
7392 | msedge.exe | Potentially Bad Traffic | ET FILE_SHARING Online File Storage Domain in DNS Lookup (gofile .io) |
7392 | msedge.exe | Misc activity | ET FILE_SHARING File Sharing Related Domain in TLS SNI (gofile .io) |
7392 | msedge.exe | Misc activity | ET FILE_SHARING File Sharing Related Domain in TLS SNI (gofile .io) |