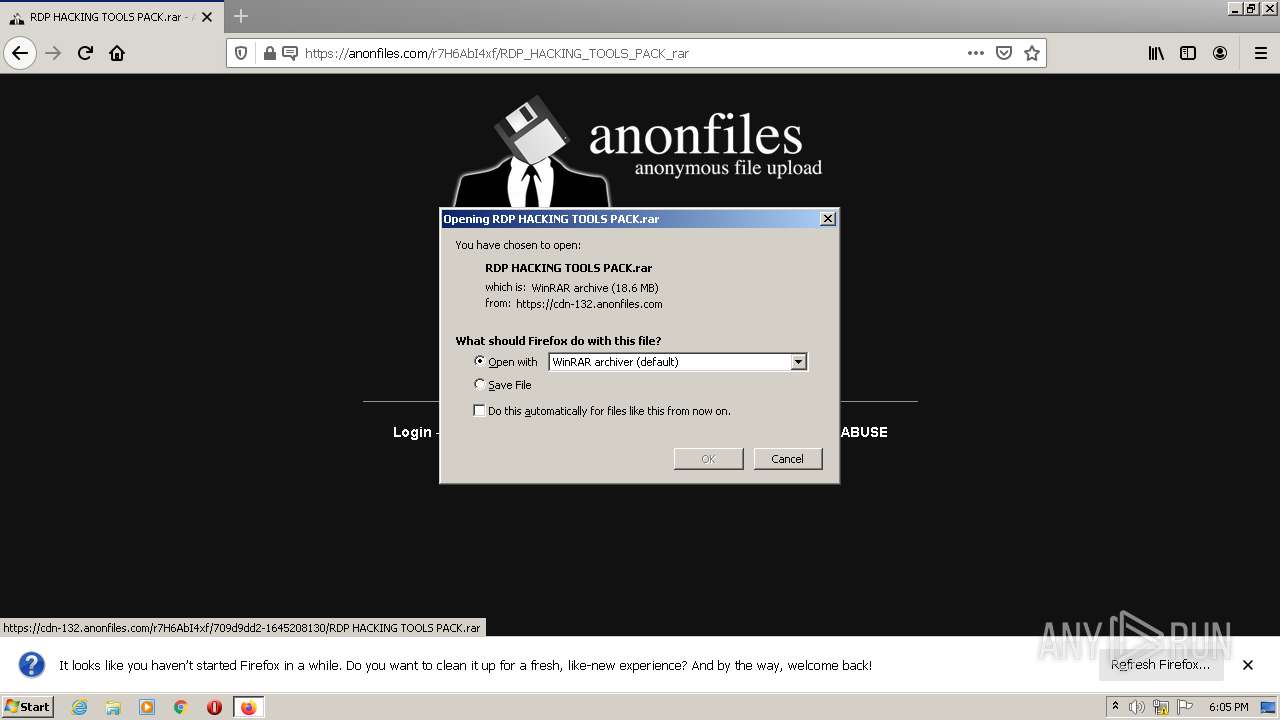
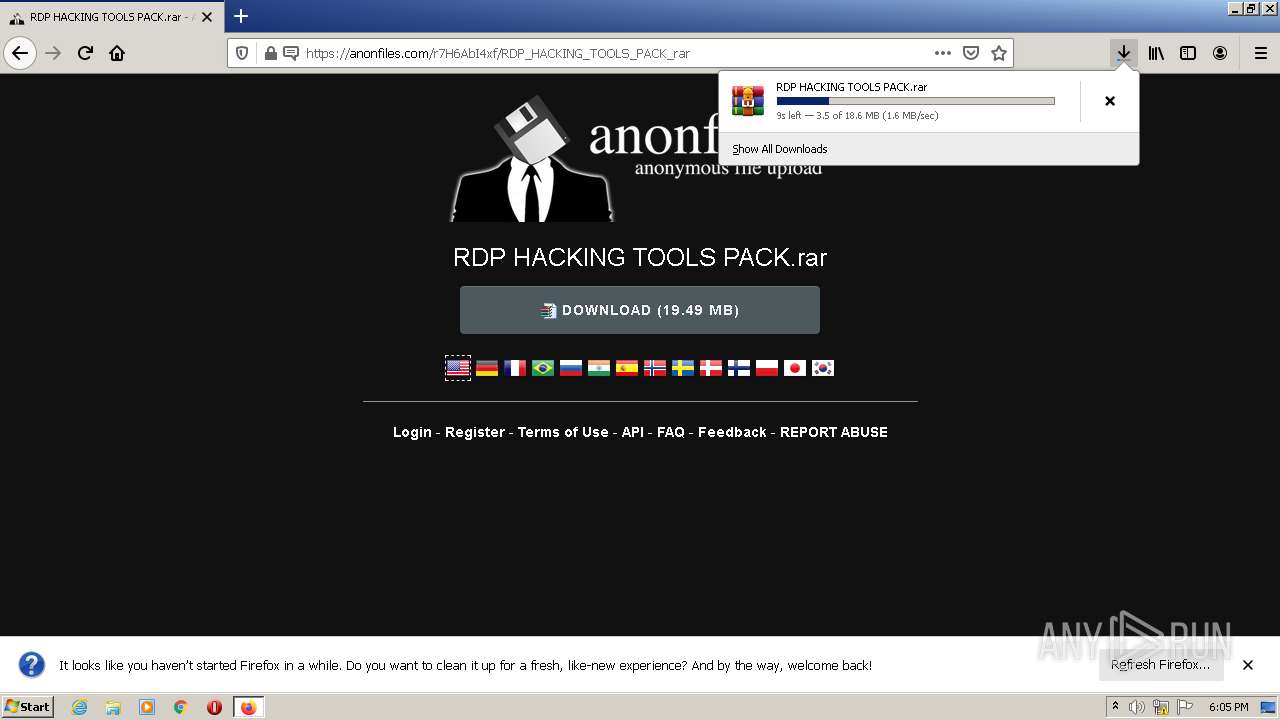
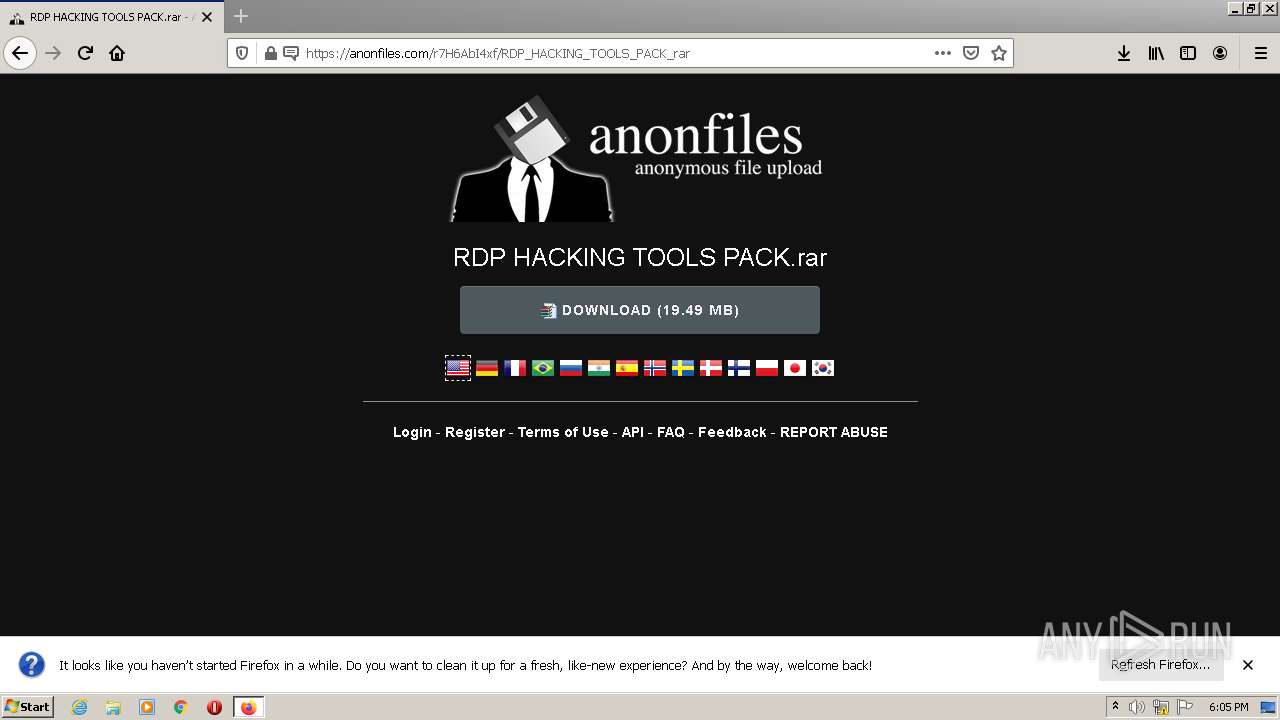
| URL: | https://anonfiles.com/r7H6AbI4xf/RDP_HACKING_TOOLS_PACK_rar |
| Full analysis: | https://app.any.run/tasks/e2ebb41f-ec18-4af4-b612-919a200eca23 |
| Verdict: | Malicious activity |
| Threats: | Orcus is a modular Remote Access Trojan with some unusual functions. This RAT enables attackers to create plugins using a custom development library and offers a robust core feature set that makes it one of the most dangerous malicious programs in its class. |
| Analysis date: | February 18, 2022, 18:05:25 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 97C3C301546A027612821271521EDE43 |
| SHA1: | 93854C22160649AFF860040B16ACD3BA0B228D99 |
| SHA256: | 7059F2E91168CDD3F9FEE781AC3FC281B7DF92E15AB52762AF7568F88C5C6561 |
| SSDEEP: | 3:N8M2MShkIDA1KuKi6LXpA:2M2ThkpKy8XpA |
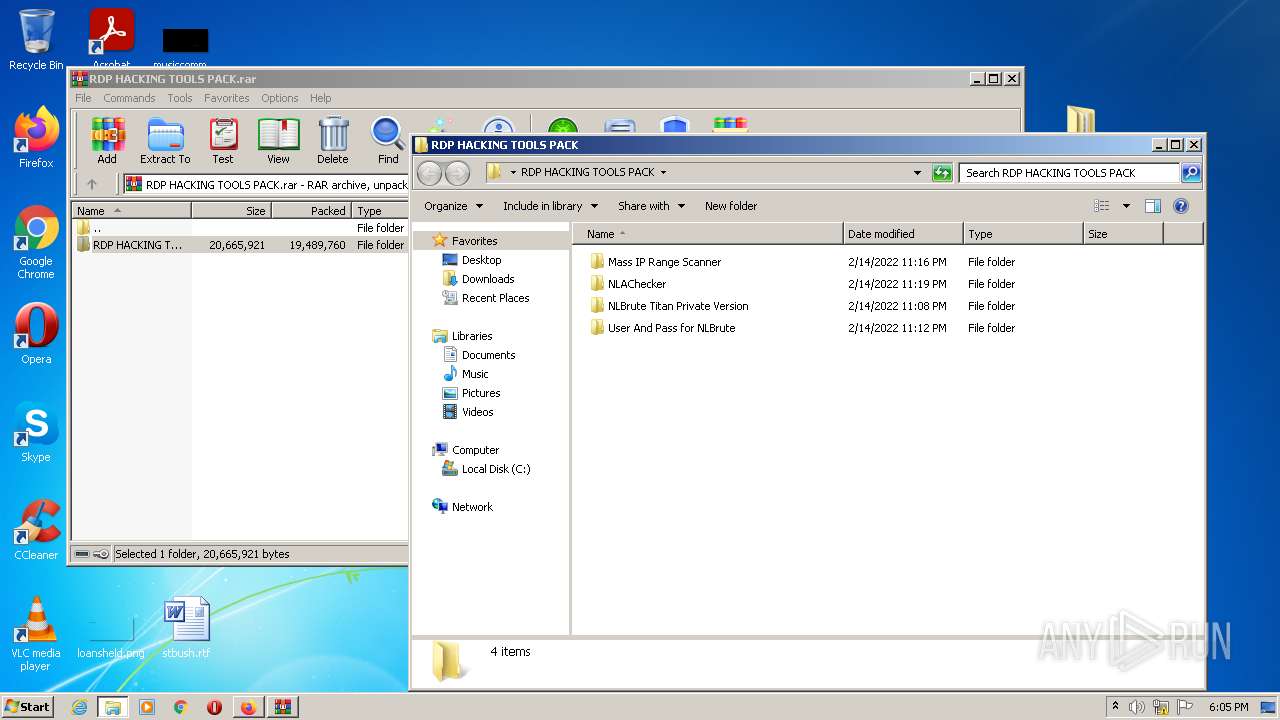
MALICIOUS
Loads dropped or rewritten executable
- SearchProtocolHost.exe (PID: 3072)
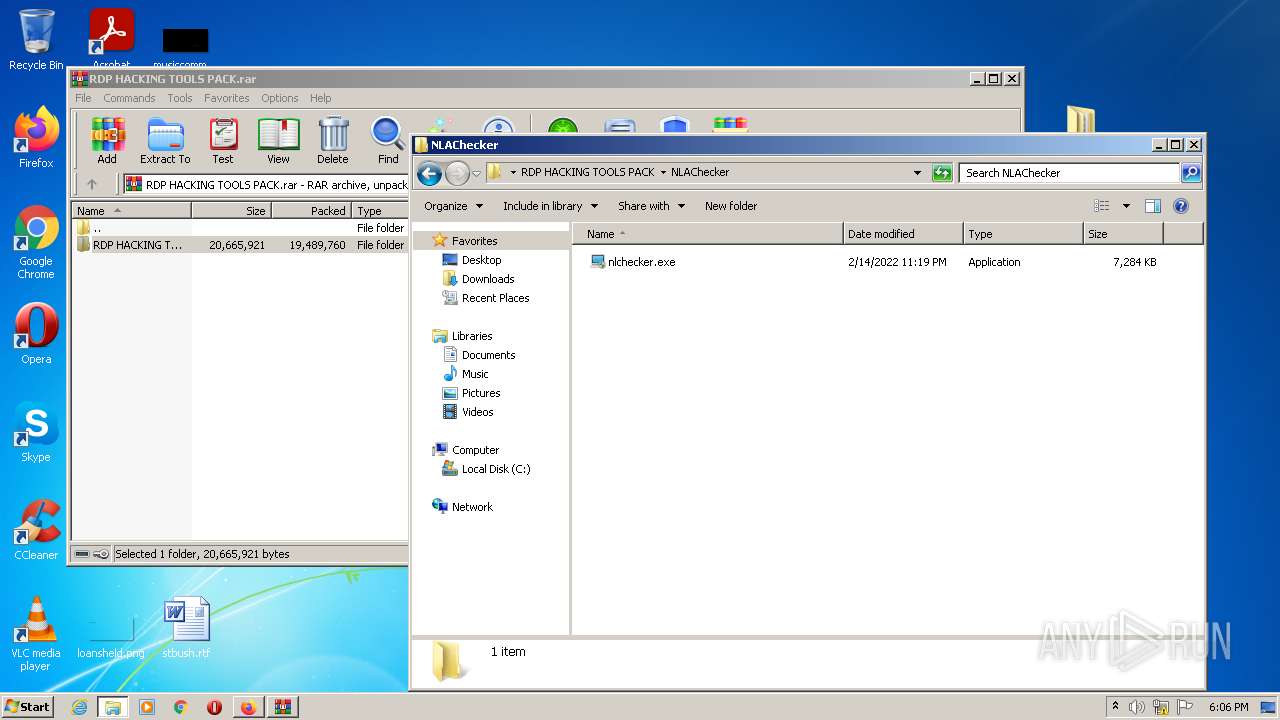
Application was dropped or rewritten from another process
- nlchecker.exe (PID: 2636)
- nlchecker.exe (PID: 3568)
- Desktop Window Manager.exe (PID: 2552)
- Desktop Window Manager.exe (PID: 3800)
Drops executable file immediately after starts
- nlchecker.exe (PID: 3568)
- Desktop Window Manager.exe (PID: 2552)
ORCUS was detected
- Desktop Window Manager.exe (PID: 2552)
- Desktop Window Manager.exe (PID: 3800)
Changes the autorun value in the registry
- Desktop Window Manager.exe (PID: 3800)
SUSPICIOUS
Checks supported languages
- WinRAR.exe (PID: 3808)
- nlchecker.exe (PID: 3568)
- Desktop Window Manager.exe (PID: 2552)
- Desktop Window Manager.exe (PID: 3800)
Drops a file that was compiled in debug mode
- WinRAR.exe (PID: 3808)
- firefox.exe (PID: 3192)
Reads the computer name
- WinRAR.exe (PID: 3808)
- nlchecker.exe (PID: 3568)
- Desktop Window Manager.exe (PID: 2552)
- Desktop Window Manager.exe (PID: 3800)
Drops a file with too old compile date
- WinRAR.exe (PID: 3808)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3808)
- nlchecker.exe (PID: 3568)
- Desktop Window Manager.exe (PID: 2552)
- firefox.exe (PID: 3192)
Drops a file with a compile date too recent
- nlchecker.exe (PID: 3568)
- Desktop Window Manager.exe (PID: 2552)
Creates files in the Windows directory
- Desktop Window Manager.exe (PID: 2552)
Starts itself from another location
- Desktop Window Manager.exe (PID: 2552)
Reads Environment values
- Desktop Window Manager.exe (PID: 3800)
INFO
Checks supported languages
- firefox.exe (PID: 3192)
- firefox.exe (PID: 2828)
- firefox.exe (PID: 1812)
- firefox.exe (PID: 1700)
- firefox.exe (PID: 2072)
- firefox.exe (PID: 3972)
- firefox.exe (PID: 3620)
Application launched itself
- firefox.exe (PID: 3192)
- firefox.exe (PID: 2828)
Reads the computer name
- firefox.exe (PID: 3972)
- firefox.exe (PID: 1700)
- firefox.exe (PID: 3192)
- firefox.exe (PID: 2072)
- firefox.exe (PID: 3620)
- firefox.exe (PID: 1812)
Reads CPU info
- firefox.exe (PID: 3192)
Creates files in the program directory
- firefox.exe (PID: 3192)
Dropped object may contain Bitcoin addresses
- firefox.exe (PID: 3192)
Checks Windows Trust Settings
- firefox.exe (PID: 3192)
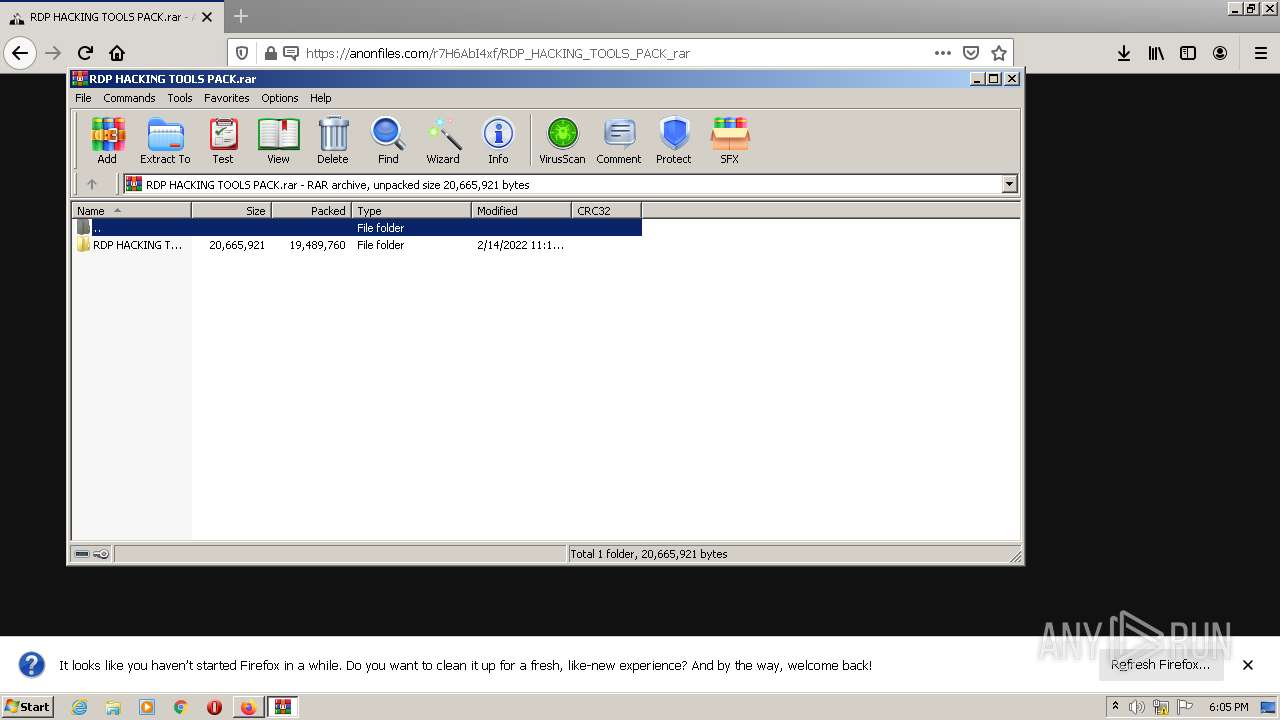
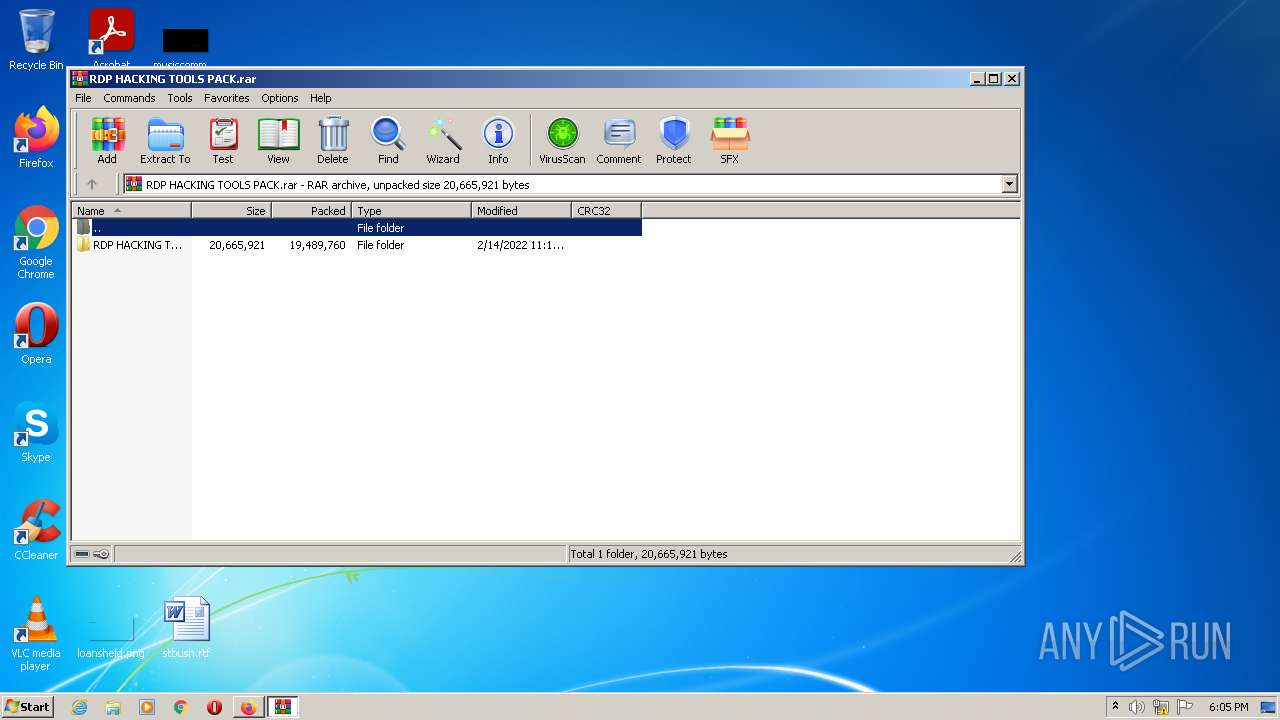
Manual execution by user
- WinRAR.exe (PID: 3808)
- nlchecker.exe (PID: 2636)
- nlchecker.exe (PID: 3568)
Creates files in the user directory
- firefox.exe (PID: 3192)
Reads settings of System Certificates
- Desktop Window Manager.exe (PID: 3800)
Reads the date of Windows installation
- firefox.exe (PID: 3192)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
51
Monitored processes
13
Malicious processes
5
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1700 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="3192.6.1031581318\226202321" -childID 1 -isForBrowser -prefsHandle 2720 -prefMapHandle 2716 -prefsLen 245 -prefMapSize 238726 -parentBuildID 20201112153044 -appdir "C:\Program Files\Mozilla Firefox\browser" - 3192 "\\.\pipe\gecko-crash-server-pipe.3192" 2732 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 83.0 Modules
| |||||||||||||||
| 1812 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="3192.27.473639664\1753255884" -childID 4 -isForBrowser -prefsHandle 7848 -prefMapHandle 7888 -prefsLen 7800 -prefMapSize 238726 -parentBuildID 20201112153044 -appdir "C:\Program Files\Mozilla Firefox\browser" - 3192 "\\.\pipe\gecko-crash-server-pipe.3192" 2588 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 83.0 Modules
| |||||||||||||||
| 2072 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="3192.13.1806907507\1777261253" -childID 2 -isForBrowser -prefsHandle 3012 -prefMapHandle 3008 -prefsLen 6644 -prefMapSize 238726 -parentBuildID 20201112153044 -appdir "C:\Program Files\Mozilla Firefox\browser" - 3192 "\\.\pipe\gecko-crash-server-pipe.3192" 3024 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 83.0 Modules
| |||||||||||||||
| 2552 | "C:\Users\admin\AppData\Local\Temp\Desktop Window Manager.exe" | C:\Users\admin\AppData\Local\Temp\Desktop Window Manager.exe | nlchecker.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Desktop Window Manager Exit code: 0 Version: 10.0.17763.0 Modules
| |||||||||||||||
| 2636 | "C:\Users\admin\Desktop\RDP HACKING TOOLS PACK\NLAChecker\nlchecker.exe" | C:\Users\admin\Desktop\RDP HACKING TOOLS PACK\NLAChecker\nlchecker.exe | — | Explorer.EXE | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 2828 | "C:\Program Files\Mozilla Firefox\firefox.exe" "https://anonfiles.com/r7H6AbI4xf/RDP_HACKING_TOOLS_PACK_rar" | C:\Program Files\Mozilla Firefox\firefox.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 83.0 Modules
| |||||||||||||||
| 3072 | "C:\Windows\system32\SearchProtocolHost.exe" Global\UsGthrFltPipeMssGthrPipe2_ Global\UsGthrCtrlFltPipeMssGthrPipe2 1 -2147483646 "Software\Microsoft\Windows Search" "Mozilla/4.0 (compatible; MSIE 6.0; Windows NT; MS Search 4.0 Robot)" "C:\ProgramData\Microsoft\Search\Data\Temp\usgthrsvc" "DownLevelDaemon" | C:\Windows\system32\SearchProtocolHost.exe | — | SearchIndexer.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Windows Search Protocol Host Exit code: 0 Version: 7.00.7601.24542 (win7sp1_ldr_escrow.191209-2211) Modules
| |||||||||||||||
| 3192 | "C:\Program Files\Mozilla Firefox\firefox.exe" https://anonfiles.com/r7H6AbI4xf/RDP_HACKING_TOOLS_PACK_rar | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 83.0 Modules
| |||||||||||||||
| 3568 | "C:\Users\admin\Desktop\RDP HACKING TOOLS PACK\NLAChecker\nlchecker.exe" | C:\Users\admin\Desktop\RDP HACKING TOOLS PACK\NLAChecker\nlchecker.exe | Explorer.EXE | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 3620 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="3192.20.1068289706\777407974" -childID 3 -isForBrowser -prefsHandle 3756 -prefMapHandle 3752 -prefsLen 7470 -prefMapSize 238726 -parentBuildID 20201112153044 -appdir "C:\Program Files\Mozilla Firefox\browser" - 3192 "\\.\pipe\gecko-crash-server-pipe.3192" 3768 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 83.0 Modules
| |||||||||||||||
Total events
17 064
Read events
16 951
Write events
113
Delete events
0
Modification events
| (PID) Process: | (2828) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Launcher |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Launcher |
Value: AF4C0A4026000000 | |||
| (PID) Process: | (3192) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Launcher |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Browser |
Value: 39550A4026000000 | |||
| (PID) Process: | (3192) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Launcher |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Telemetry |
Value: 0 | |||
| (PID) Process: | (3192) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\DllPrefetchExperiment |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe |
Value: 0 | |||
| (PID) Process: | (3192) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Default Browser Agent |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox|DisableTelemetry |
Value: 1 | |||
| (PID) Process: | (3192) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Default Browser Agent |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox|DisableDefaultBrowserAgent |
Value: 0 | |||
| (PID) Process: | (3192) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Default Browser Agent |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox|ServicesSettingsServer |
Value: https://firefox.settings.services.mozilla.com/v1 | |||
| (PID) Process: | (3192) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Default Browser Agent |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox|SecurityContentSignatureRootHash |
Value: 97:E8:BA:9C:F1:2F:B3:DE:53:CC:42:A4:E6:57:7E:D6:4D:F4:93:C2:47:B4:14:FE:A0:36:81:8D:38:23:56:0E | |||
| (PID) Process: | (3192) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3192) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 460000003B010000090000000000000000000000000000000400000000000000C0E333BBEAB1D3010000000000000000000000000100000002000000C0A80164000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
16
Suspicious files
157
Text files
51
Unknown types
31
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3192 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\startupCache\scriptCache-current.bin | — | |
MD5:— | SHA256:— | |||
| 3192 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\storage\permanent\chrome\idb\3870112724rsegmnoittet-es.sqlite | — | |
MD5:— | SHA256:— | |||
| 3192 | firefox.exe | C:\Users\admin\AppData\Local\Temp\mz_etilqs_6GfYmlgB9ELu7UQ | binary | |
MD5:— | SHA256:— | |||
| 3192 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\storage\permanent\chrome\idb\3870112724rsegmnoittet-es.sqlite-wal | binary | |
MD5:— | SHA256:— | |||
| 3192 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\startupCache\urlCache-current.bin | binary | |
MD5:994A33896BB41A278A315D0D796422B6 | SHA256:54EC50A20FFF8CC016710E49437CF6A11D3FE5EE7B28C185E4A9AAFEE2908B63 | |||
| 3192 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\places.sqlite-wal | sqlite-wal | |
MD5:— | SHA256:— | |||
| 3192 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\settings\main\ms-language-packs\asrouter.ftl | text | |
MD5:— | SHA256:— | |||
| 3192 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\storage.sqlite-journal | binary | |
MD5:— | SHA256:— | |||
| 3192 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\settings\main\ms-language-packs\asrouter.ftl.tmp | text | |
MD5:— | SHA256:— | |||
| 3192 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\sessionCheckpoints.json.tmp | binary | |
MD5:EA8B62857DFDBD3D0BE7D7E4A954EC9A | SHA256:792955295AE9C382986222C6731C5870BD0E921E7F7E34CC4615F5CD67F225DA | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
22
TCP/UDP connections
72
DNS requests
123
Threats
5
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3192 | firefox.exe | POST | 200 | 2.16.186.16:80 | http://r3.o.lencr.org/ | unknown | der | 503 b | shared |
3192 | firefox.exe | POST | — | 2.16.186.16:80 | http://e1.o.lencr.org/ | unknown | — | — | whitelisted |
3192 | firefox.exe | POST | — | 142.250.184.195:80 | http://ocsp.pki.goog/gts1c3 | US | — | — | whitelisted |
3192 | firefox.exe | POST | 200 | 142.250.184.195:80 | http://ocsp.pki.goog/gts1c3 | US | der | 471 b | whitelisted |
3192 | firefox.exe | POST | 200 | 142.250.184.195:80 | http://ocsp.pki.goog/gts1c3 | US | der | 471 b | whitelisted |
3192 | firefox.exe | POST | 200 | 142.250.184.195:80 | http://ocsp.pki.goog/gts1c3 | US | der | 472 b | whitelisted |
3192 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
3192 | firefox.exe | POST | 200 | 2.16.186.16:80 | http://r3.o.lencr.org/ | unknown | der | 503 b | shared |
3192 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
3192 | firefox.exe | POST | 200 | 2.16.186.16:80 | http://e1.o.lencr.org/ | unknown | der | 346 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3192 | firefox.exe | 35.161.134.161:443 | location.services.mozilla.com | Amazon.com, Inc. | US | unknown |
3192 | firefox.exe | 34.107.221.82:80 | detectportal.firefox.com | — | US | whitelisted |
3192 | firefox.exe | 13.32.22.10:443 | content-signature-2.cdn.mozilla.net | Amazon.com, Inc. | US | unknown |
3192 | firefox.exe | 2.16.186.16:80 | r3.o.lencr.org | Akamai International B.V. | — | whitelisted |
3192 | firefox.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3192 | firefox.exe | 65.9.58.163:443 | djv99sxoqpv11.cloudfront.net | AT&T Services, Inc. | US | unknown |
3192 | firefox.exe | 45.154.253.150:443 | anonfiles.com | — | — | suspicious |
3192 | firefox.exe | 151.101.2.217:443 | vjs.zencdn.net | Fastly | US | suspicious |
3192 | firefox.exe | 142.250.185.138:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
3192 | firefox.exe | 143.204.215.126:443 | firefox.settings.services.mozilla.com | — | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
detectportal.firefox.com |
| whitelisted |
prod.detectportal.prod.cloudops.mozgcp.net |
| whitelisted |
anonfiles.com |
| shared |
firefox.settings.services.mozilla.com |
| whitelisted |
example.org |
| whitelisted |
ipv4only.arpa |
| whitelisted |
location.services.mozilla.com |
| whitelisted |
locprod2-elb-us-west-2.prod.mozaws.net |
| whitelisted |
r3.o.lencr.org |
| shared |
a1887.dscq.akamai.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3192 | firefox.exe | Potentially Bad Traffic | ET INFO Terse Request for .txt - Likely Hostile |
3192 | firefox.exe | Potentially Bad Traffic | ET INFO Terse Request for .txt - Likely Hostile |
3192 | firefox.exe | Potentially Bad Traffic | ET INFO Terse Request for .txt - Likely Hostile |
3192 | firefox.exe | Potentially Bad Traffic | ET INFO Terse Request for .txt - Likely Hostile |
1 ETPRO signatures available at the full report