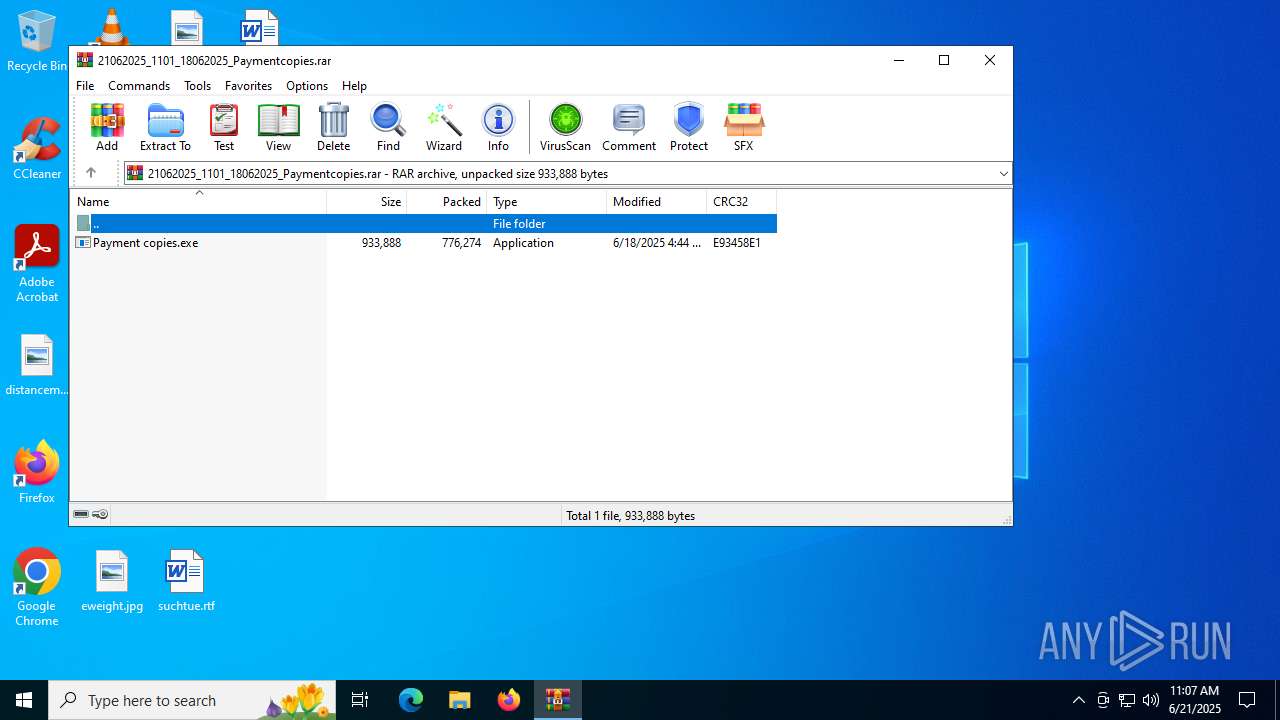
| File name: | 21062025_1101_18062025_Paymentcopies.rar |
| Full analysis: | https://app.any.run/tasks/6a20f478-e867-4a70-a31f-13de6d0bc41f |
| Verdict: | Malicious activity |
| Threats: | FormBook is a data stealer that is being distributed as a MaaS. FormBook differs from a lot of competing malware by its extreme ease of use that allows even the unexperienced threat actors to use FormBook virus. |
| Analysis date: | June 21, 2025, 11:07:11 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | 5D07ED98FFCFEE33B85C0B941CA1B78A |
| SHA1: | C2D9AC7A52608BA4534DE01D921B96AEBB326CBA |
| SHA256: | 704799079996649469EFFD0A33EE8C30583F99DBBCD928E908DD7C2407124C20 |
| SSDEEP: | 24576:fM9t2HuFx0o2QE7dP3jhiLqLDDTU2QKREUQ8moRx/hurZg3r6Ni/VnDtdsKMgzog:fM9t2HuFx0o2QE7dP3j0LqLDDTUFKR4A |
MALICIOUS
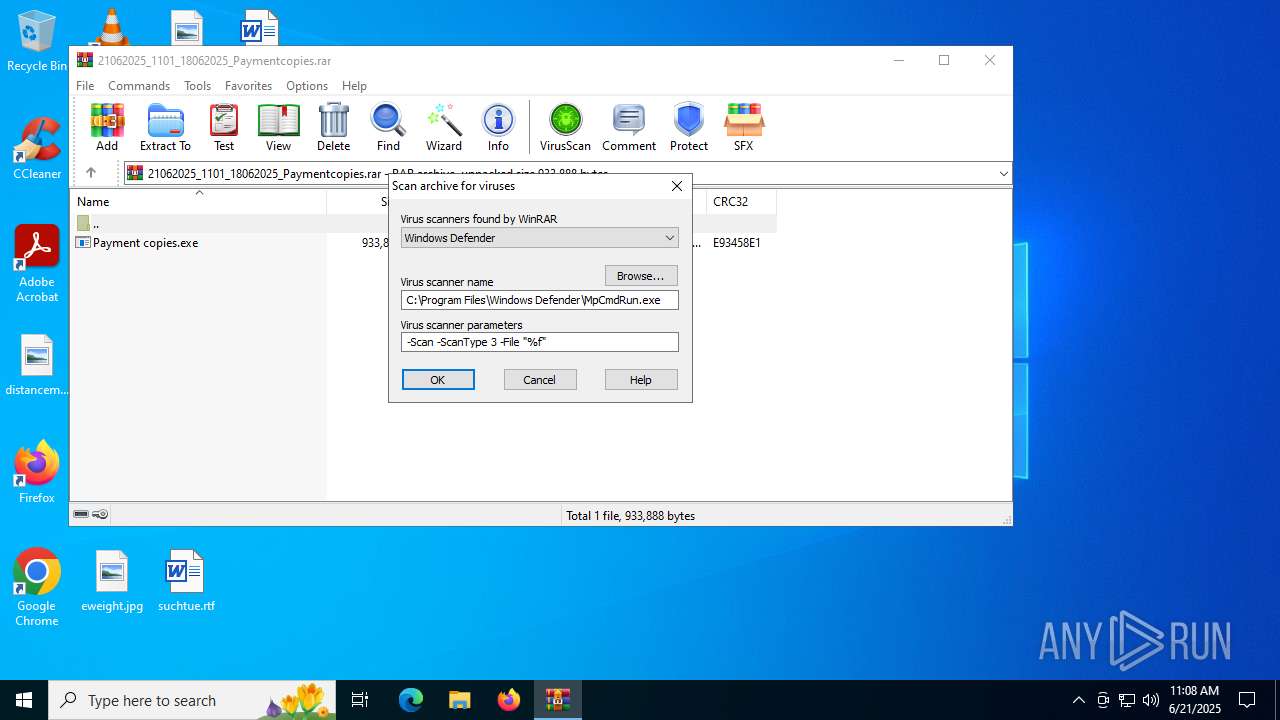
Generic archive extractor
- WinRAR.exe (PID: 6536)
Uses Task Scheduler to run other applications
- Payment copies.exe (PID: 1944)
FORMBOOK has been detected (YARA)
- w32tm.exe (PID: 1896)
Actions looks like stealing of personal data
- w32tm.exe (PID: 1896)
FORMBOOK has been detected (SURICATA)
- WinRAR.exe (PID: 6536)
SUSPICIOUS
Reads security settings of Internet Explorer
- Payment copies.exe (PID: 1944)
Executable content was dropped or overwritten
- Payment copies.exe (PID: 1944)
Query current time using 'w32tm.exe'
- WinRAR.exe (PID: 6536)
INFO
Checks supported languages
- Payment copies.exe (PID: 1944)
- RegSvcs.exe (PID: 4688)
Manual execution by a user
- Payment copies.exe (PID: 1944)
Reads the machine GUID from the registry
- Payment copies.exe (PID: 1944)
Reads the computer name
- Payment copies.exe (PID: 1944)
Creates files or folders in the user directory
- Payment copies.exe (PID: 1944)
.NET Reactor protector has been detected
- Payment copies.exe (PID: 1944)
Process checks computer location settings
- Payment copies.exe (PID: 1944)
Create files in a temporary directory
- Payment copies.exe (PID: 1944)
- w32tm.exe (PID: 1896)
Reads security settings of Internet Explorer
- w32tm.exe (PID: 1896)
Checks proxy server information
- slui.exe (PID: 3960)
Reads the software policy settings
- slui.exe (PID: 3960)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
EXIF
ZIP
| FileVersion: | RAR v5 |
|---|---|
| CompressedSize: | 776274 |
| UncompressedSize: | 933888 |
| OperatingSystem: | Win32 |
| ArchivedFileName: | Payment copies.exe |
Total processes
140
Monitored processes
8
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1896 | "C:\Windows\SysWOW64\w32tm.exe" | C:\Windows\SysWOW64\w32tm.exe | WinRAR.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Time Service Diagnostic Tool Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1944 | "C:\Users\admin\Desktop\Payment copies.exe" | C:\Users\admin\Desktop\Payment copies.exe | explorer.exe | ||||||||||||
User: admin Company: Bunnings Group Limited Integrity Level: MEDIUM Description: StIvesLib Exit code: 0 Version: 0.0.0.0 Modules
| |||||||||||||||
| 2160 | "C:\Windows\System32\schtasks.exe" /Create /TN "Updates\vERjhQ" /XML "C:\Users\admin\AppData\Local\Temp\tmpB390.tmp" | C:\Windows\SysWOW64\schtasks.exe | — | Payment copies.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Task Scheduler Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2216 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | schtasks.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2972 | "C:\Program Files\Mozilla Firefox\Firefox.exe" | C:\Program Files\Mozilla Firefox\firefox.exe | — | w32tm.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 136.0 Modules
| |||||||||||||||
| 3960 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4688 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\RegSvcs.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\RegSvcs.exe | — | Payment copies.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft .NET Services Installation Utility Exit code: 0 Version: 4.8.9037.0 built by: NET481REL1 Modules
| |||||||||||||||
| 6536 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\Desktop\21062025_1101_18062025_Paymentcopies.rar | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
Total events
8 268
Read events
8 255
Write events
13
Delete events
0
Modification events
| (PID) Process: | (6536) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (6536) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (6536) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (6536) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (6536) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (6536) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\21062025_1101_18062025_Paymentcopies.rar | |||
| (PID) Process: | (6536) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (6536) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (6536) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (6536) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
Executable files
1
Suspicious files
1
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1896 | w32tm.exe | C:\Users\admin\AppData\Local\Temp\-K9i_I-8 | binary | |
MD5:A45465CDCDC6CB30C8906F3DA4EC114C | SHA256:4412319EF944EBCCA9581CBACB1D4E1DC614C348D1DFC5D2FAAAAD863D300209 | |||
| 1944 | Payment copies.exe | C:\Users\admin\AppData\Roaming\vERjhQ.exe | executable | |
MD5:0B1CD9FDE455FDA214921DC24AA243EC | SHA256:A86E9373657EFFFF617182F3BCCD52A5E6013E635CA40357D468871F38FDAA8B | |||
| 1944 | Payment copies.exe | C:\Users\admin\AppData\Local\Temp\tmpB390.tmp | xml | |
MD5:4A9C8CE787E6C07A5C39AF1C3CB91BA1 | SHA256:23561739E8ABB5A6E4CDD0D5F8CA851D30FC2D4AA88F9508C36DC6FFB6C31C93 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
25
TCP/UDP connections
39
DNS requests
12
Threats
9
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1268 | svchost.exe | GET | 200 | 23.53.40.176:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
2028 | RUXIMICS.exe | GET | 200 | 23.53.40.176:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
2028 | RUXIMICS.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6536 | WinRAR.exe | GET | 200 | 15.197.148.33:80 | http://www.imubqtus.pro/z0ut/?BLLJ=9CDY3mpK/XIIuFSIcdQl9LhIgbmMaTDtbYDXZde3rpwVVgknw3vPW/LZMy19PbBzXsXRKzaQqlXGGn6Ca7CMOeWr2fnISUjIzMc3g3PKokDxzgCe0TXnoYcn+iqH4ncvGxkZNjI=&Ypbe=J-S8OxufC6bj | unknown | — | — | unknown |
— | — | POST | 500 | 20.83.72.98:443 | https://activation-v2.sls.microsoft.com/SLActivateProduct/SLActivateProduct.asmx?configextension=Retail | unknown | xml | 512 b | whitelisted |
6536 | WinRAR.exe | POST | — | 185.65.105.231:80 | http://www.alfaskins.vip/j0li/ | unknown | — | — | unknown |
6536 | WinRAR.exe | POST | — | 185.65.105.231:80 | http://www.alfaskins.vip/j0li/ | unknown | — | — | unknown |
6536 | WinRAR.exe | POST | — | 185.65.105.231:80 | http://www.alfaskins.vip/j0li/ | unknown | — | — | unknown |
6536 | WinRAR.exe | GET | — | 185.65.105.231:80 | http://www.alfaskins.vip/j0li/?BLLJ=IEB+jRKRgdQrgFZ/Sm6ZtNhKuySWfGgnjU02bzjcn6COUTn/enYJBiE+b6jKyK8dw0ovKD5otSVG1PHPsMGJAVRaIUf6KTM1H03NOZXQhMNCrk2XOu3Z/UyRAY27Q49prv/51wQ=&Ypbe=J-S8OxufC6bj | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | 51.124.78.146:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2028 | RUXIMICS.exe | 51.124.78.146:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1268 | svchost.exe | 51.124.78.146:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2028 | RUXIMICS.exe | 23.53.40.176:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
1268 | svchost.exe | 23.53.40.176:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
2028 | RUXIMICS.exe | 2.23.246.101:80 | www.microsoft.com | Ooredoo Q.S.C. | QA | whitelisted |
1268 | svchost.exe | 2.23.246.101:80 | www.microsoft.com | Ooredoo Q.S.C. | QA | whitelisted |
5944 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |
www.imubqtus.pro |
| unknown |
www.alfaskins.vip |
| unknown |
www.walletphilippines.shop |
| unknown |
www.slot4d.life |
| unknown |
self.events.data.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6536 | WinRAR.exe | A Network Trojan was detected | STEALER [ANY.RUN] Formbook HTTP Header |
6536 | WinRAR.exe | A Network Trojan was detected | STEALER [ANY.RUN] Formbook HTTP Header |
6536 | WinRAR.exe | A Network Trojan was detected | STEALER [ANY.RUN] Formbook HTTP Header |
6536 | WinRAR.exe | A Network Trojan was detected | STEALER [ANY.RUN] Formbook HTTP Header |
6536 | WinRAR.exe | A Network Trojan was detected | STEALER [ANY.RUN] Formbook HTTP Header |
6536 | WinRAR.exe | A Network Trojan was detected | STEALER [ANY.RUN] Formbook HTTP Header |
6536 | WinRAR.exe | A Network Trojan was detected | STEALER [ANY.RUN] Formbook HTTP Header |
6536 | WinRAR.exe | A Network Trojan was detected | STEALER [ANY.RUN] Formbook HTTP Header |
6536 | WinRAR.exe | A Network Trojan was detected | STEALER [ANY.RUN] Formbook HTTP Header |