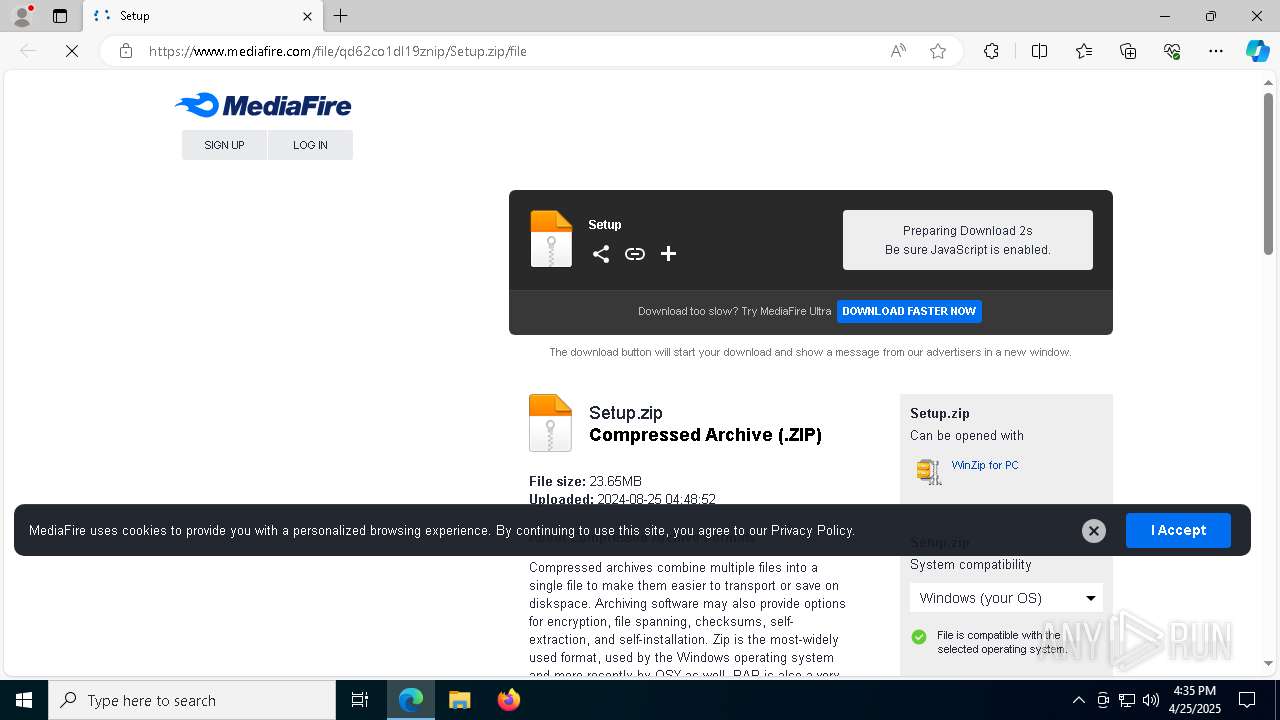
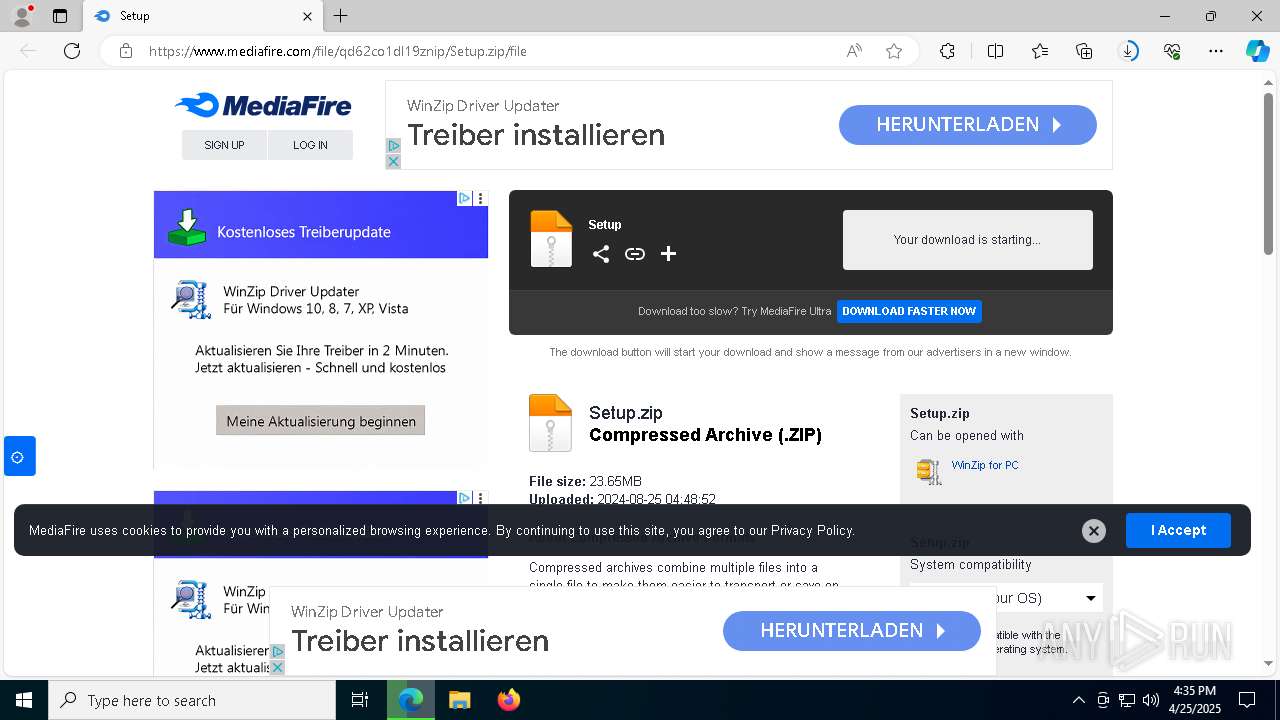
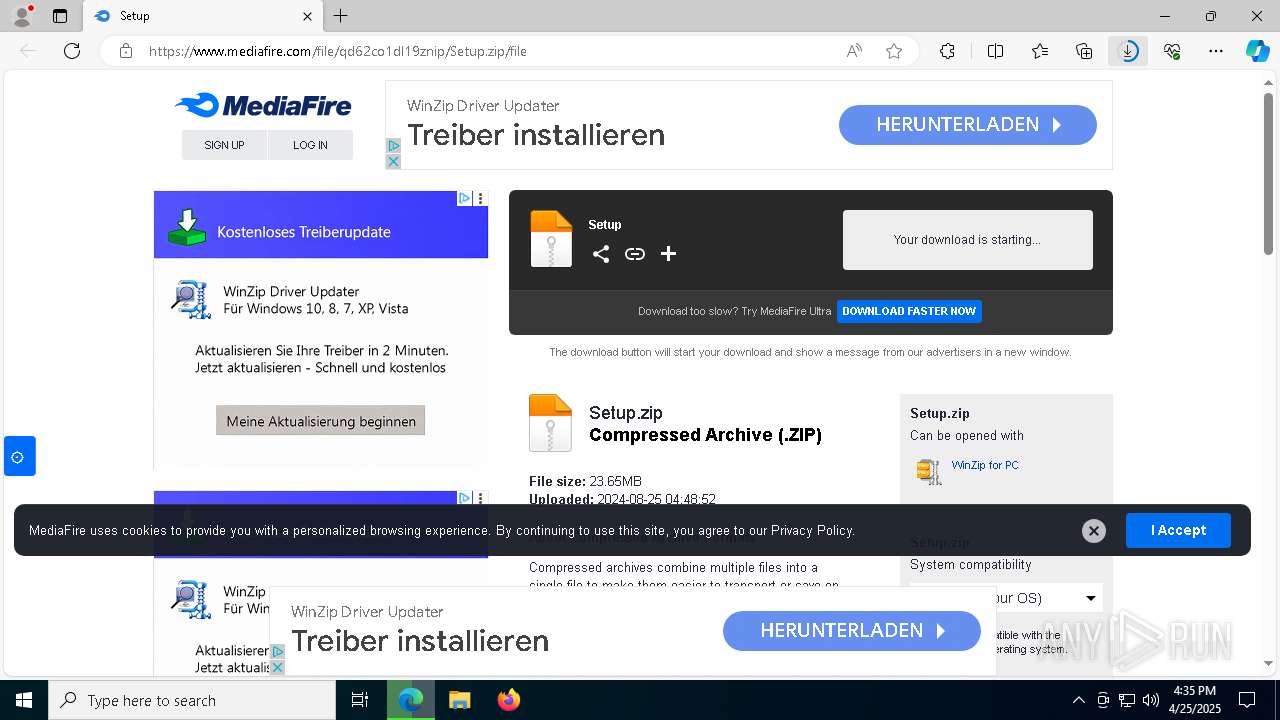
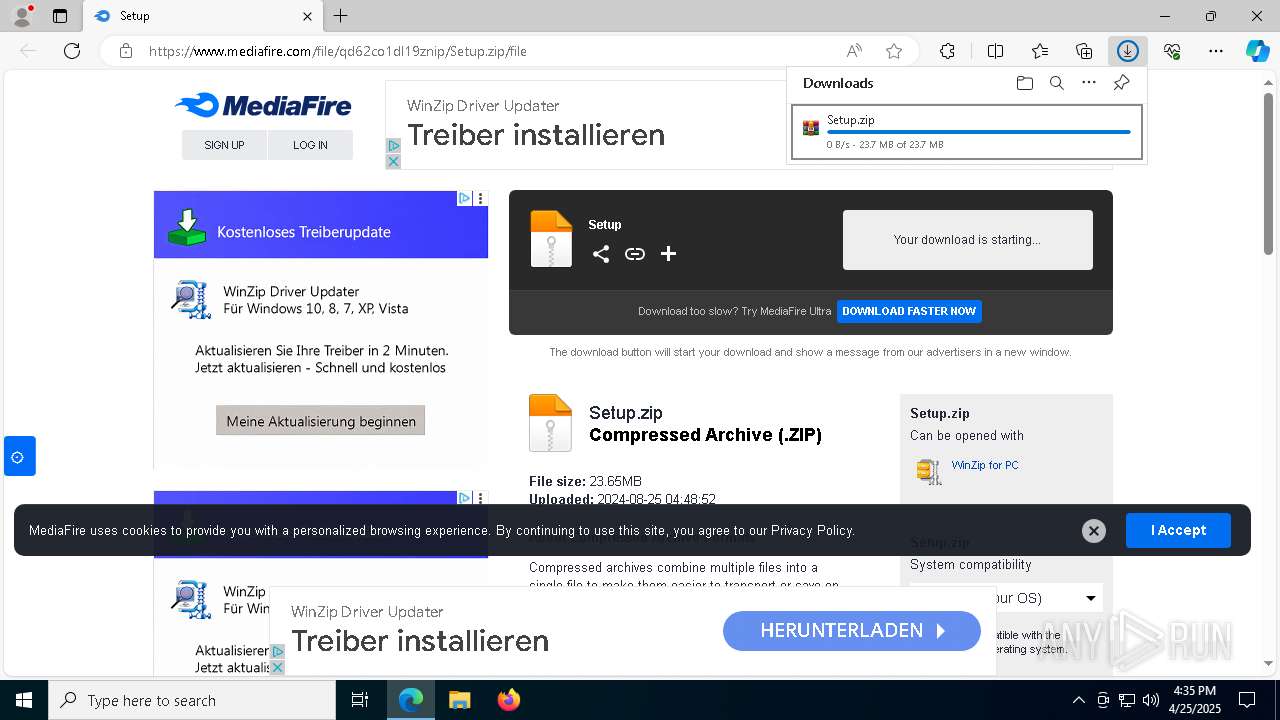
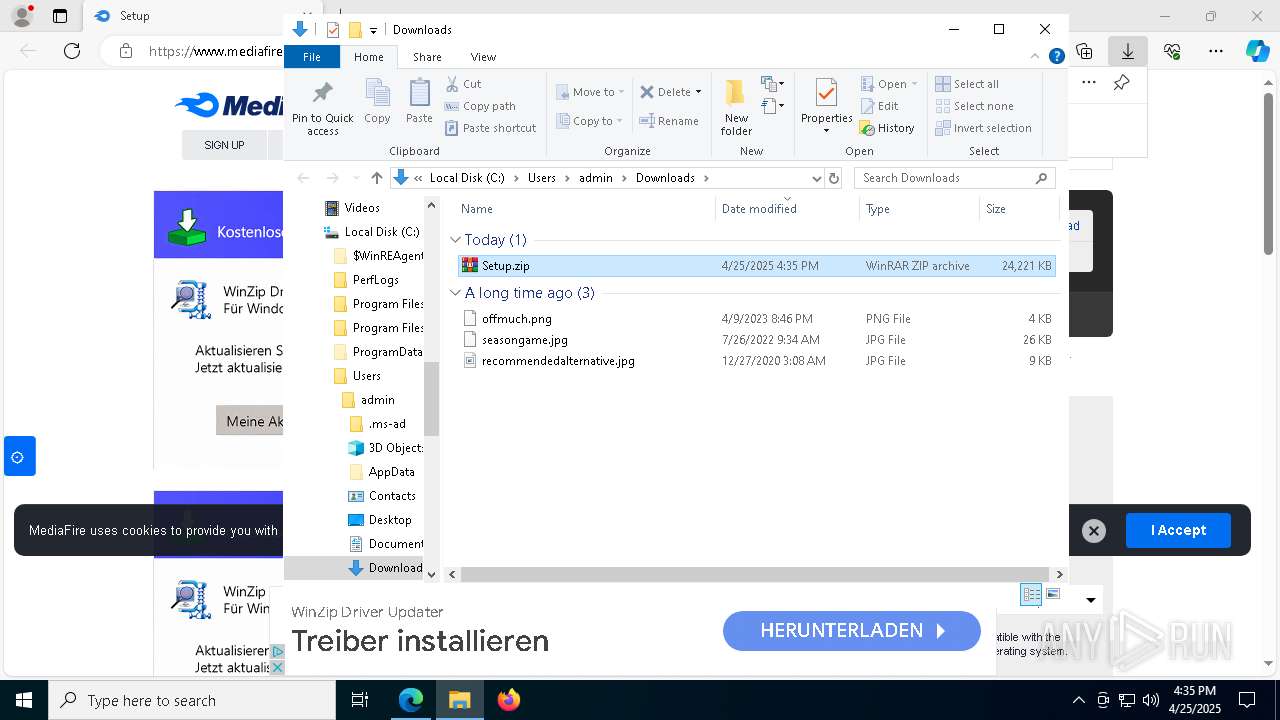
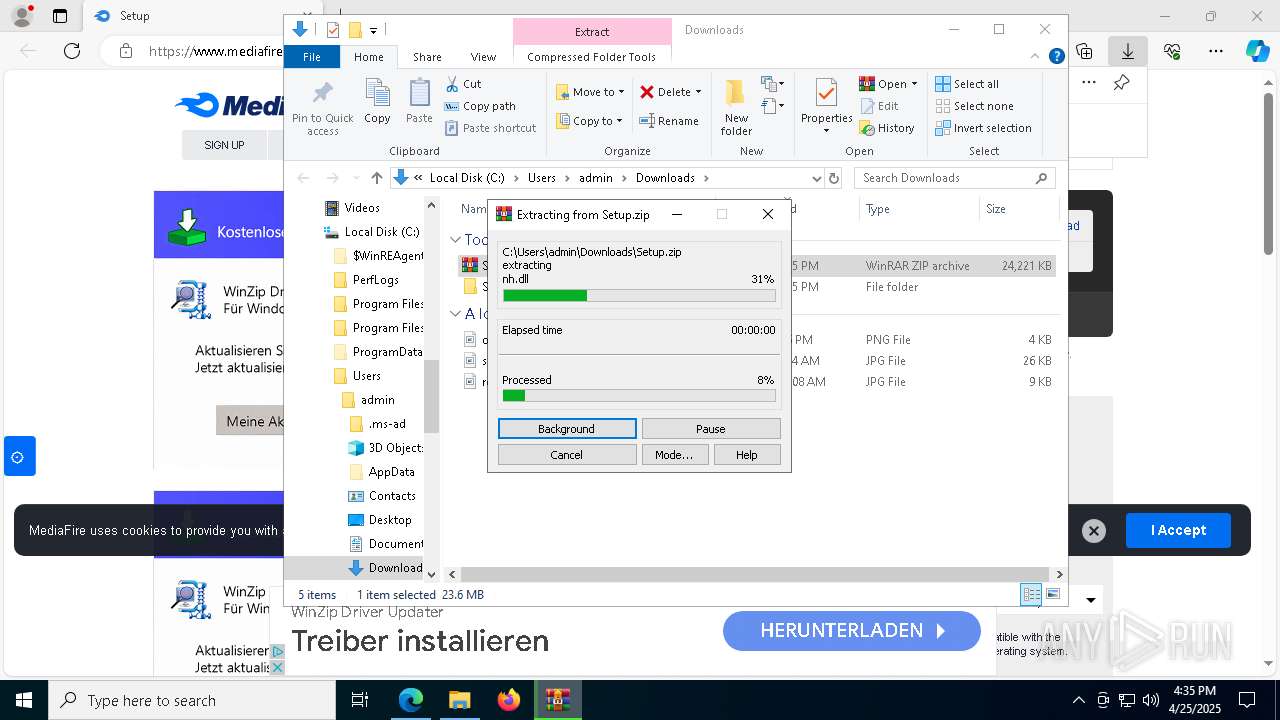
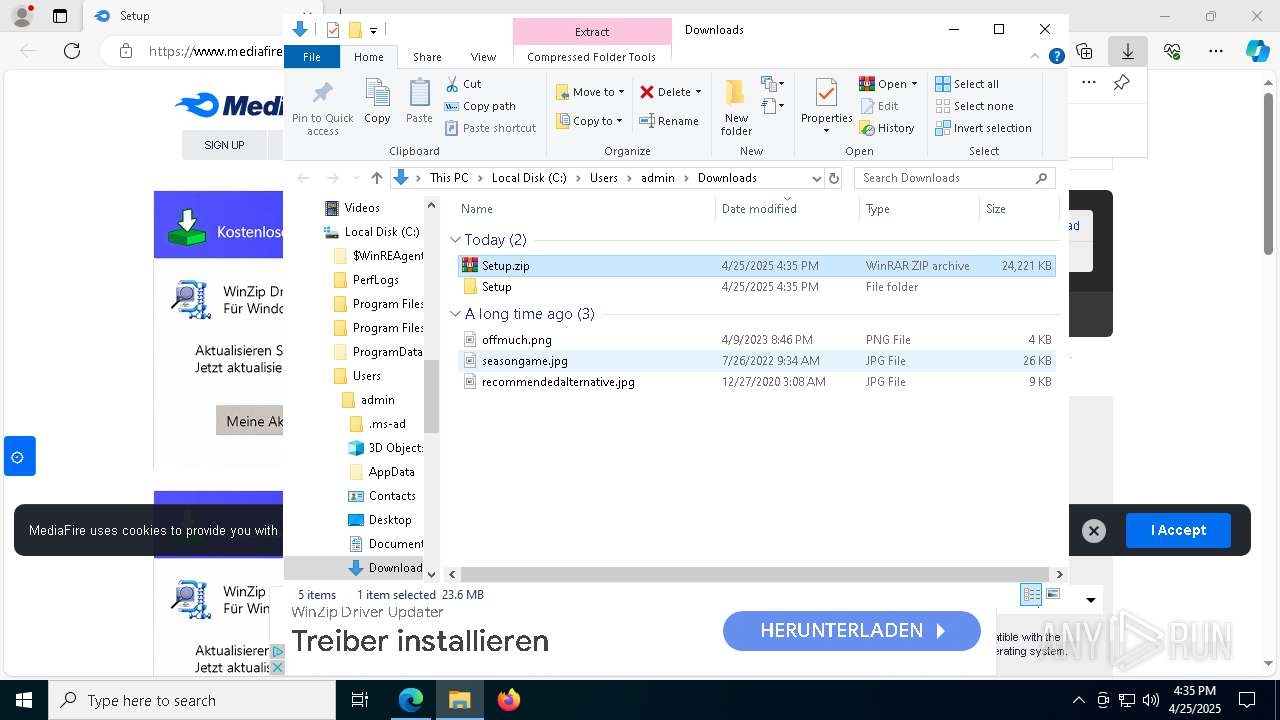
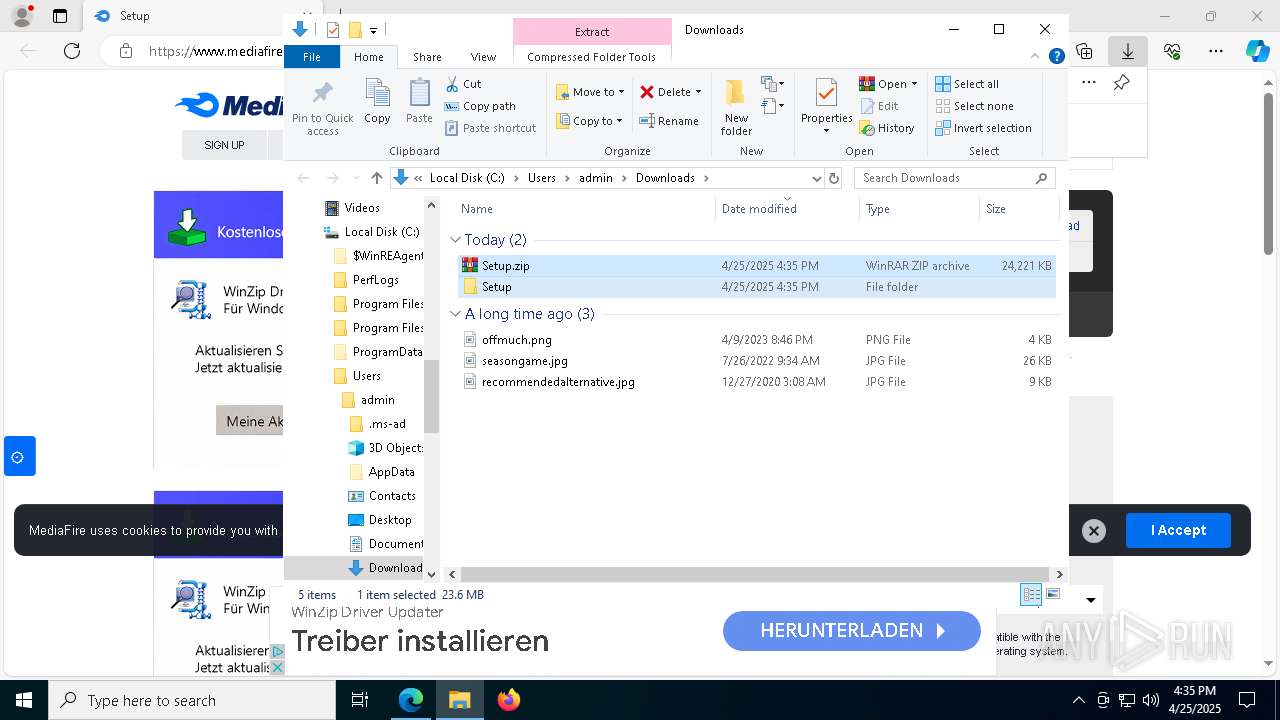
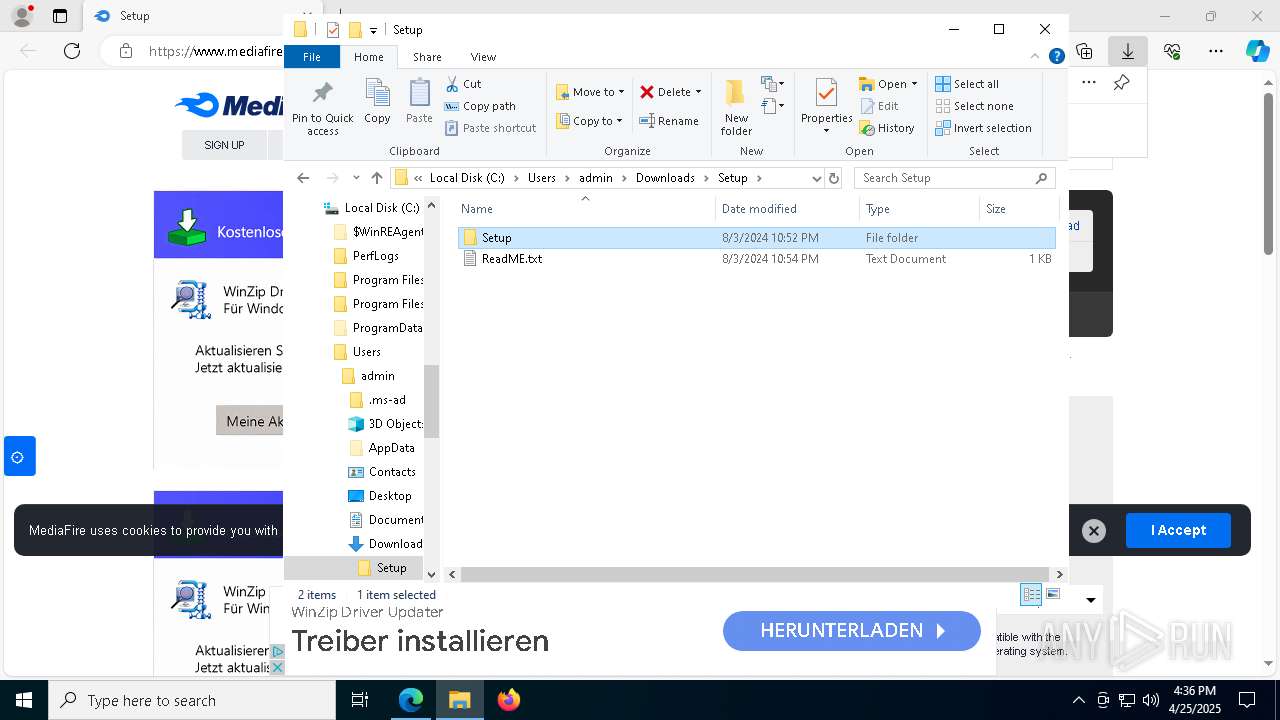
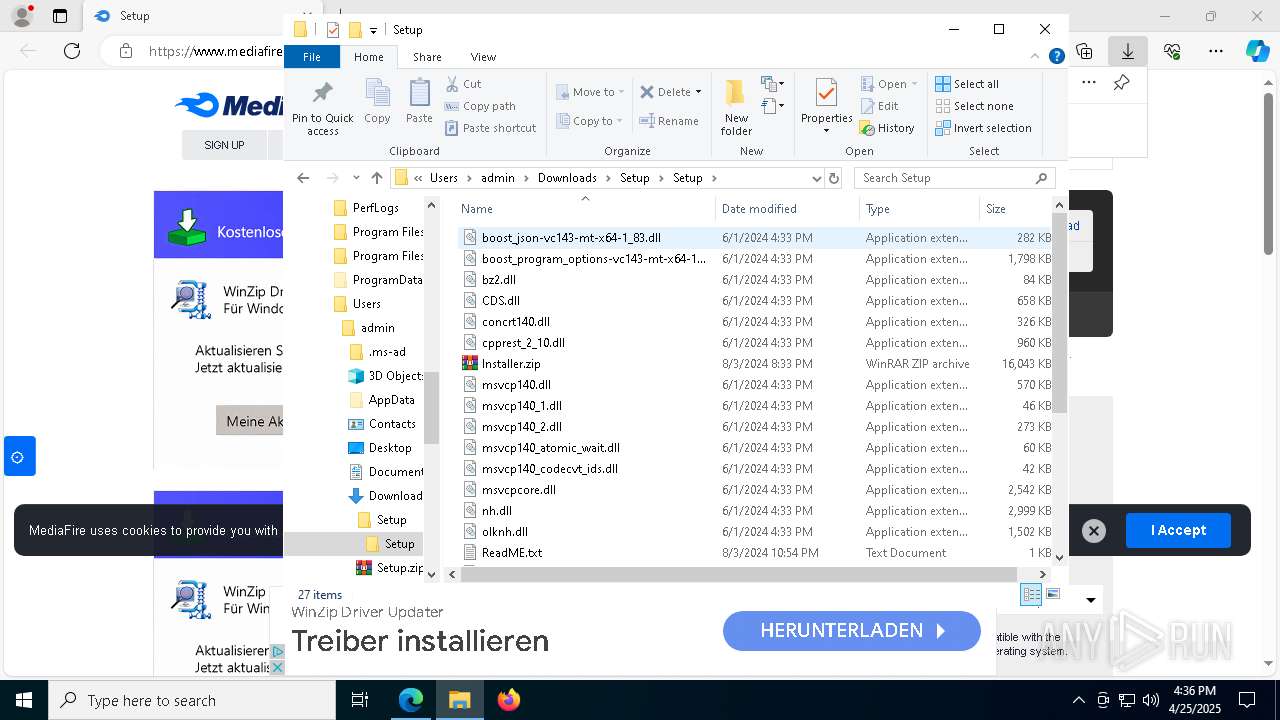
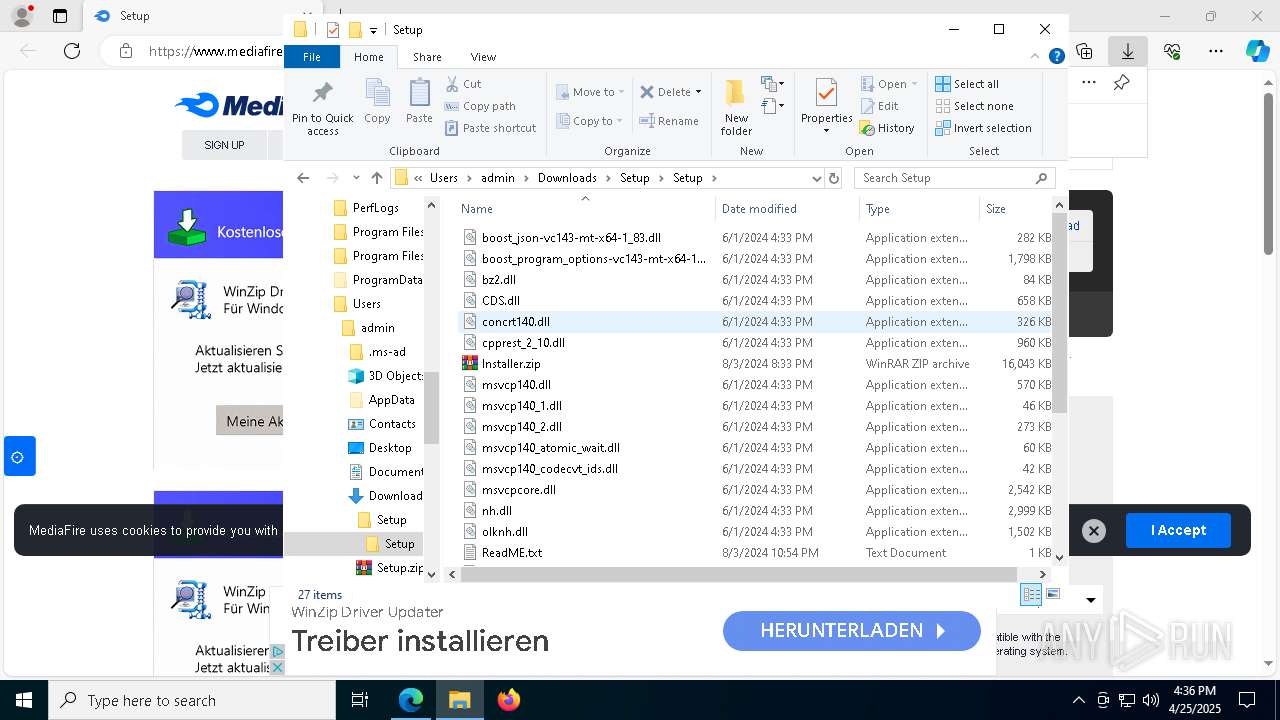
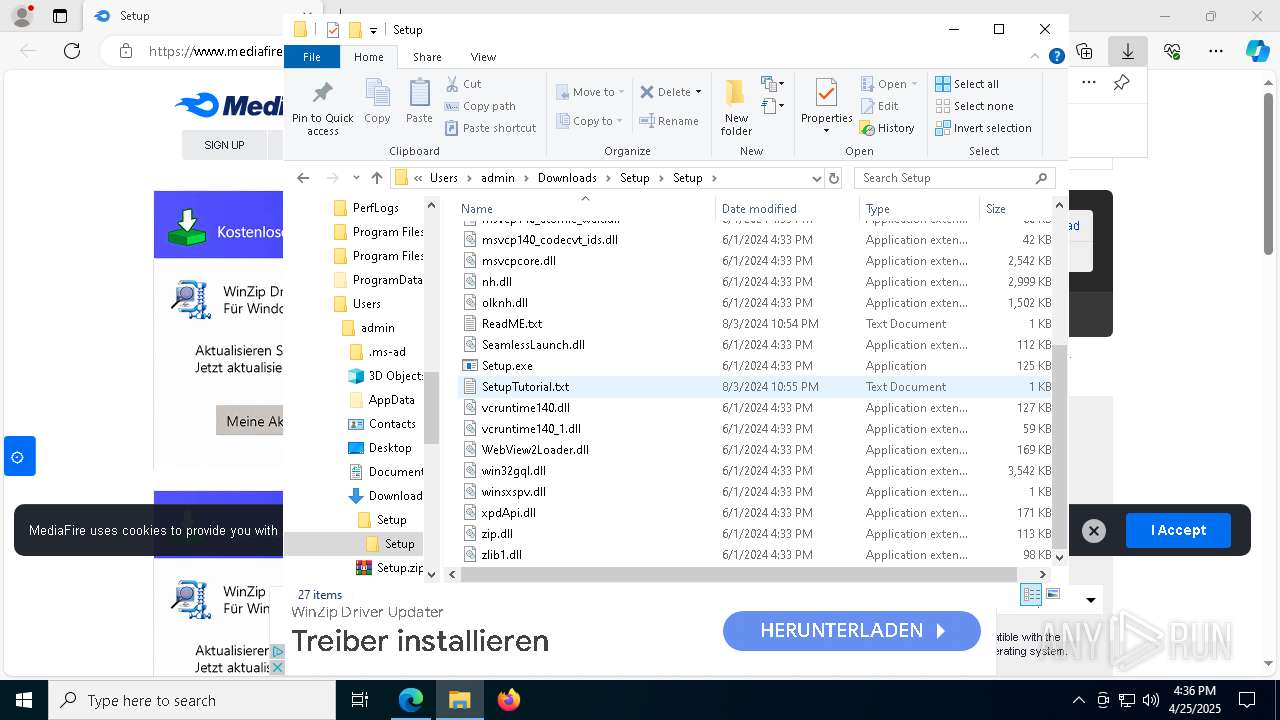
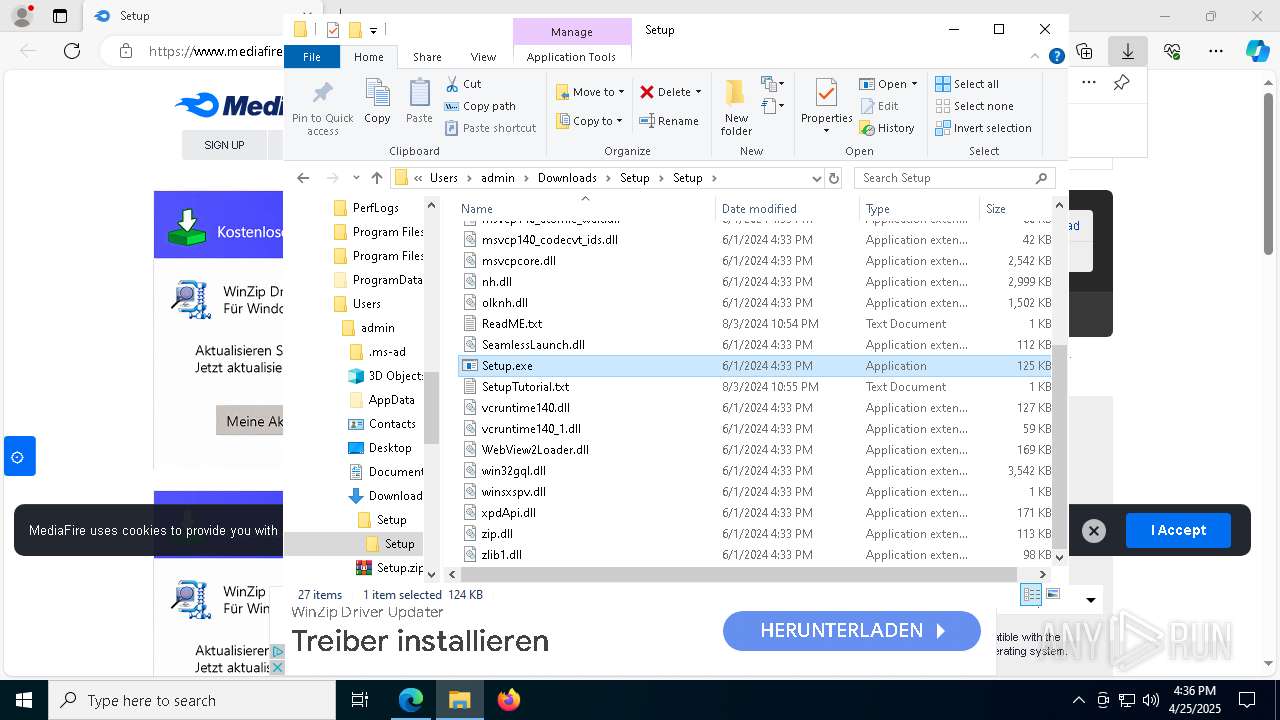
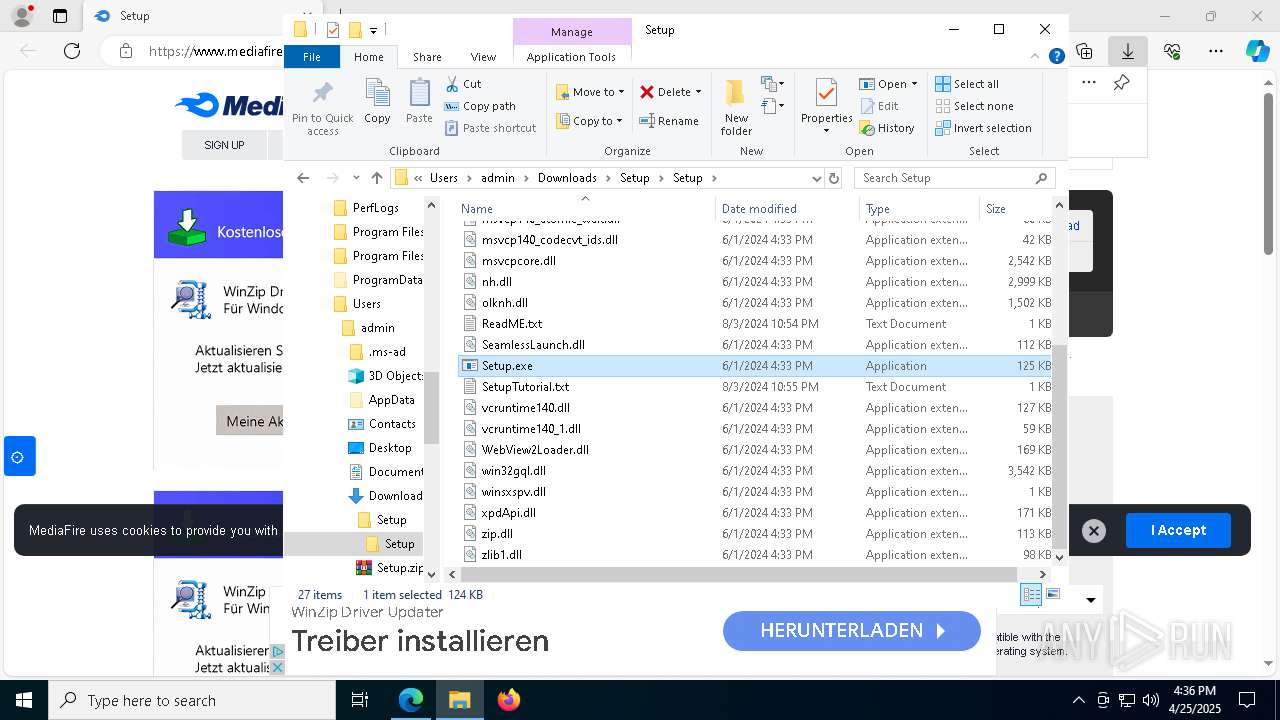
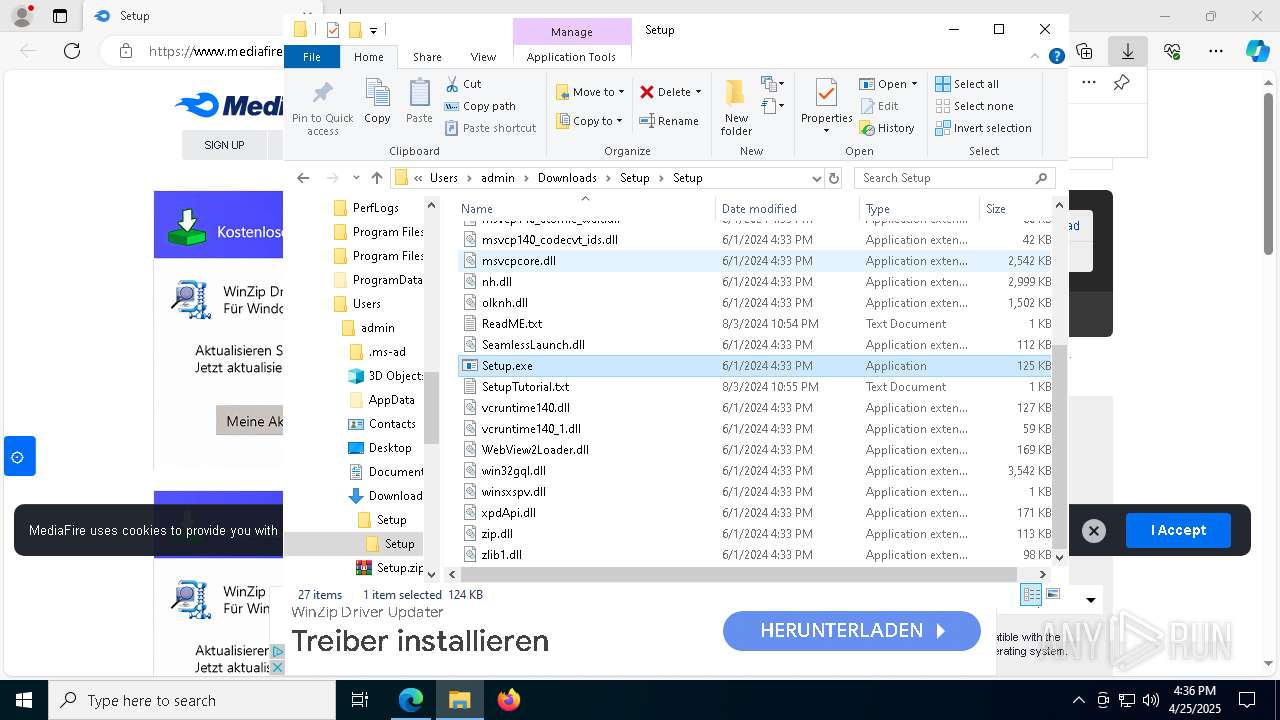
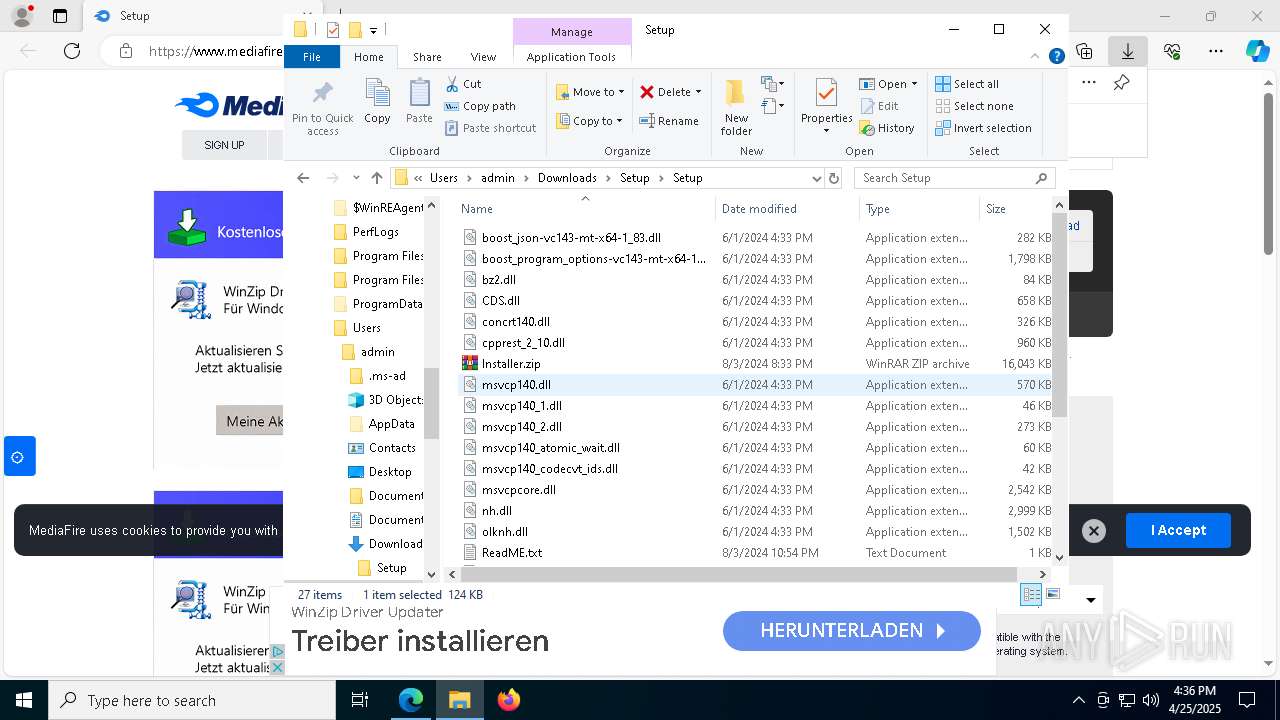
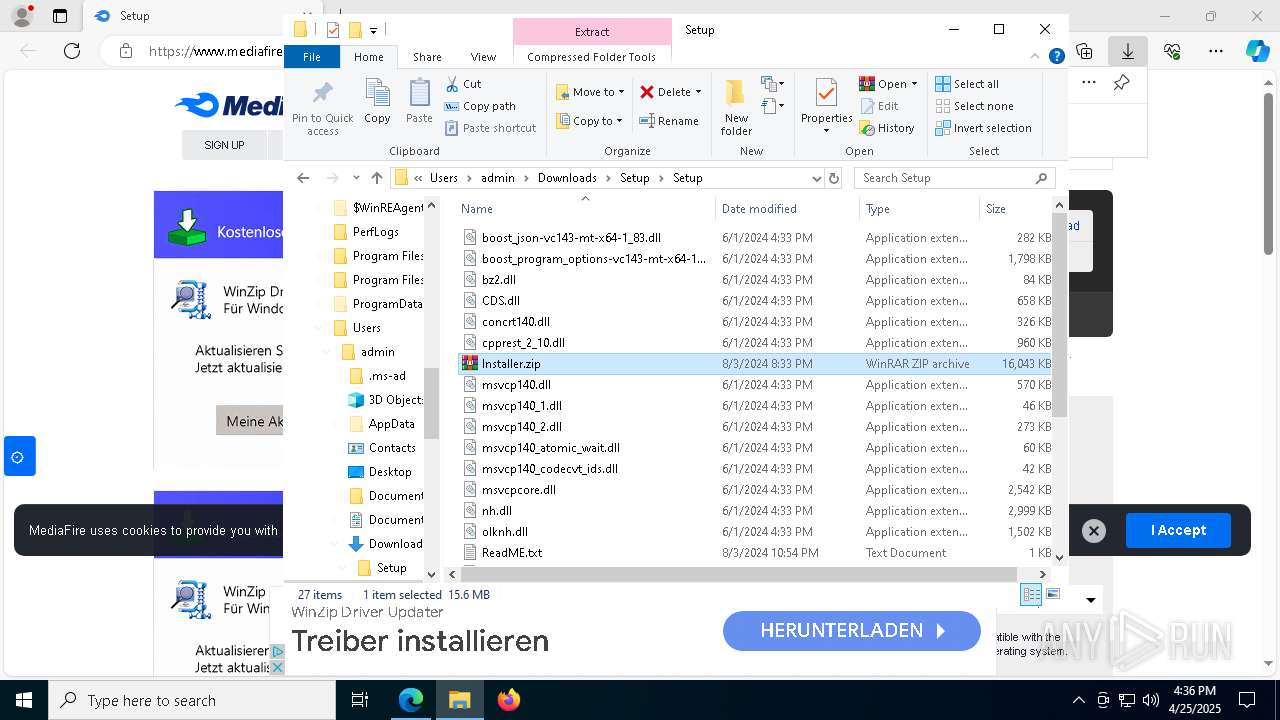
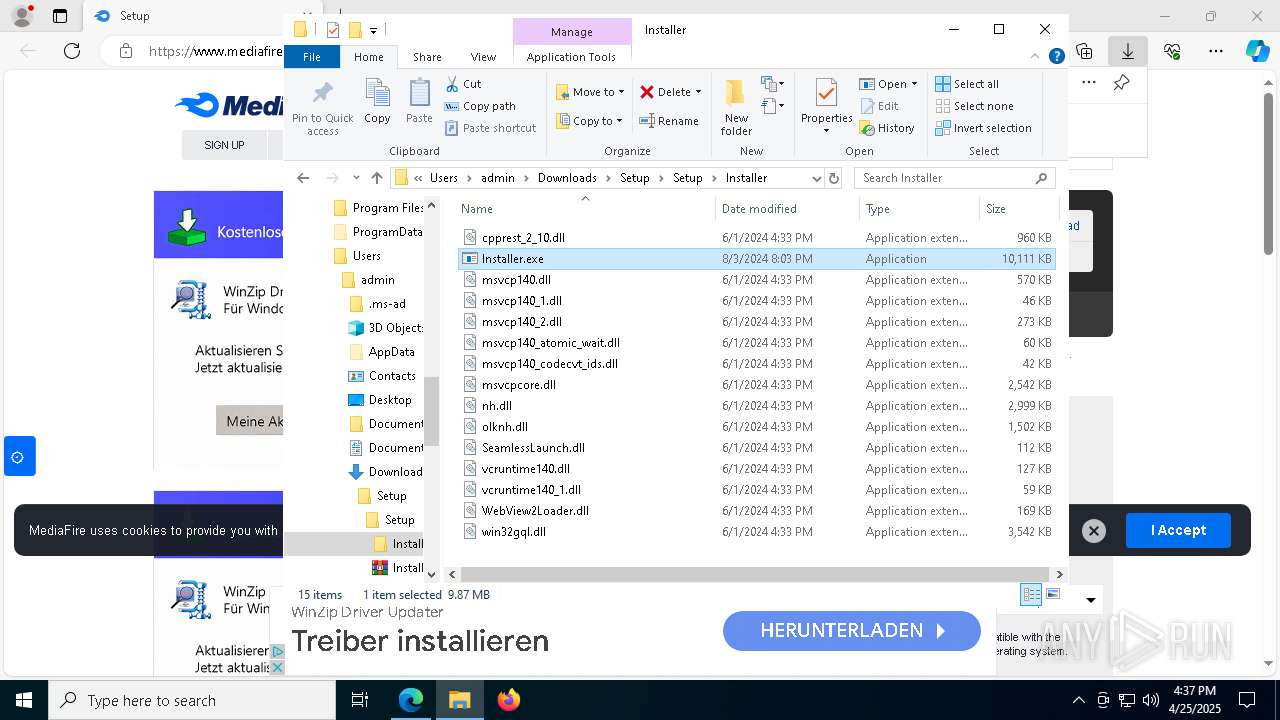
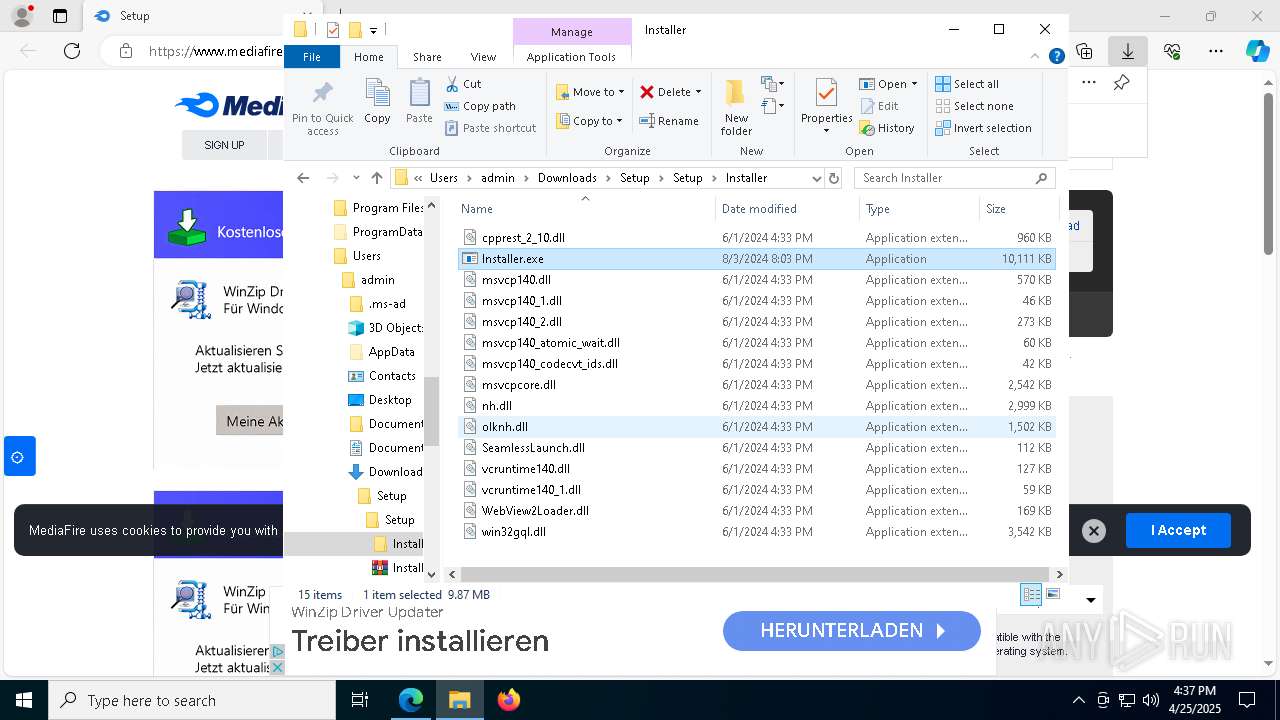
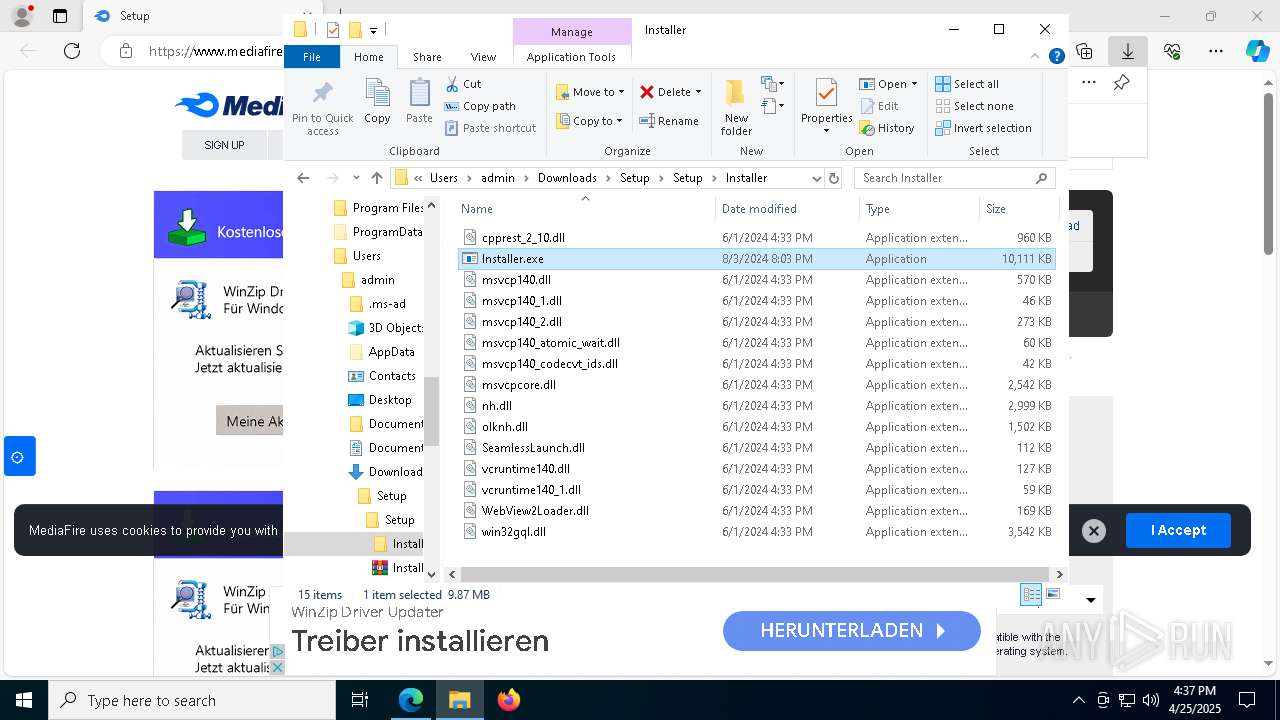
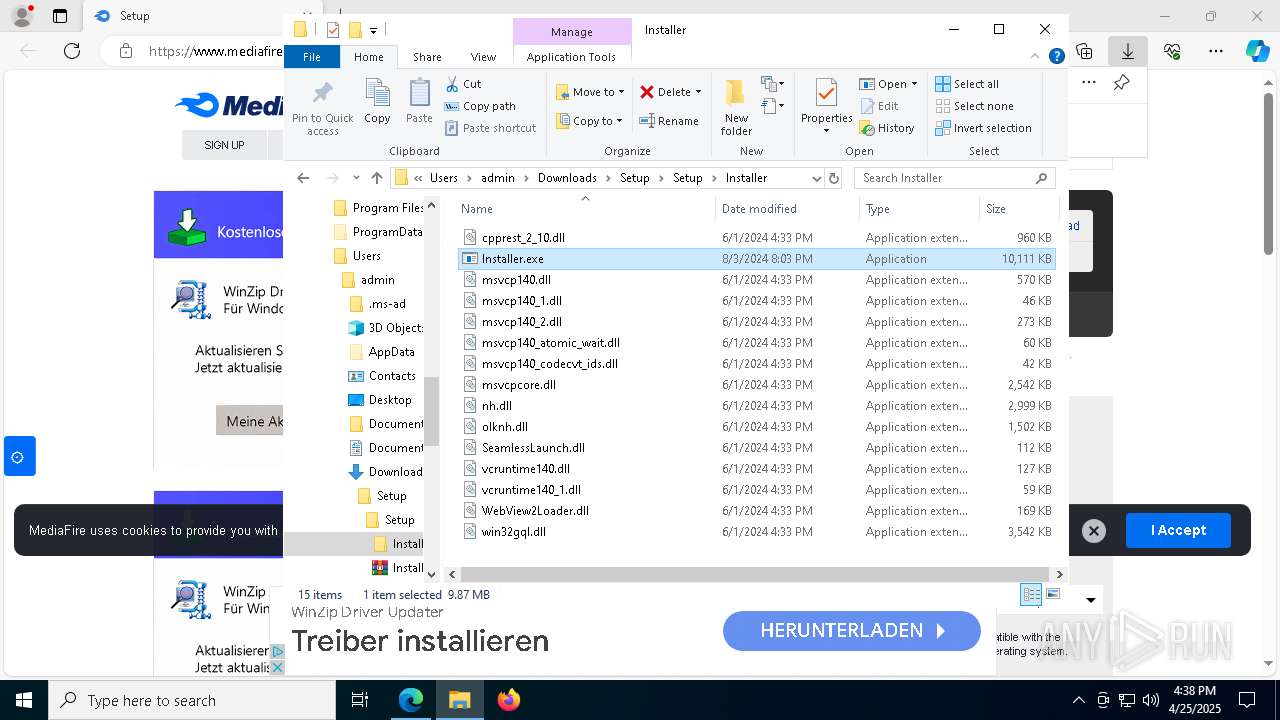
| URL: | https://www.mediafire.com/file/qd62co1dl19znip/Setup.zip/file |
| Full analysis: | https://app.any.run/tasks/65742472-4228-4f08-9f2d-d485f2c2f5c1 |
| Verdict: | Malicious activity |
| Threats: | Crypto mining malware is a resource-intensive threat that infiltrates computers with the purpose of mining cryptocurrencies. This type of threat can be deployed either on an infected machine or a compromised website. In both cases the miner will utilize the computing power of the device and its network bandwidth. |
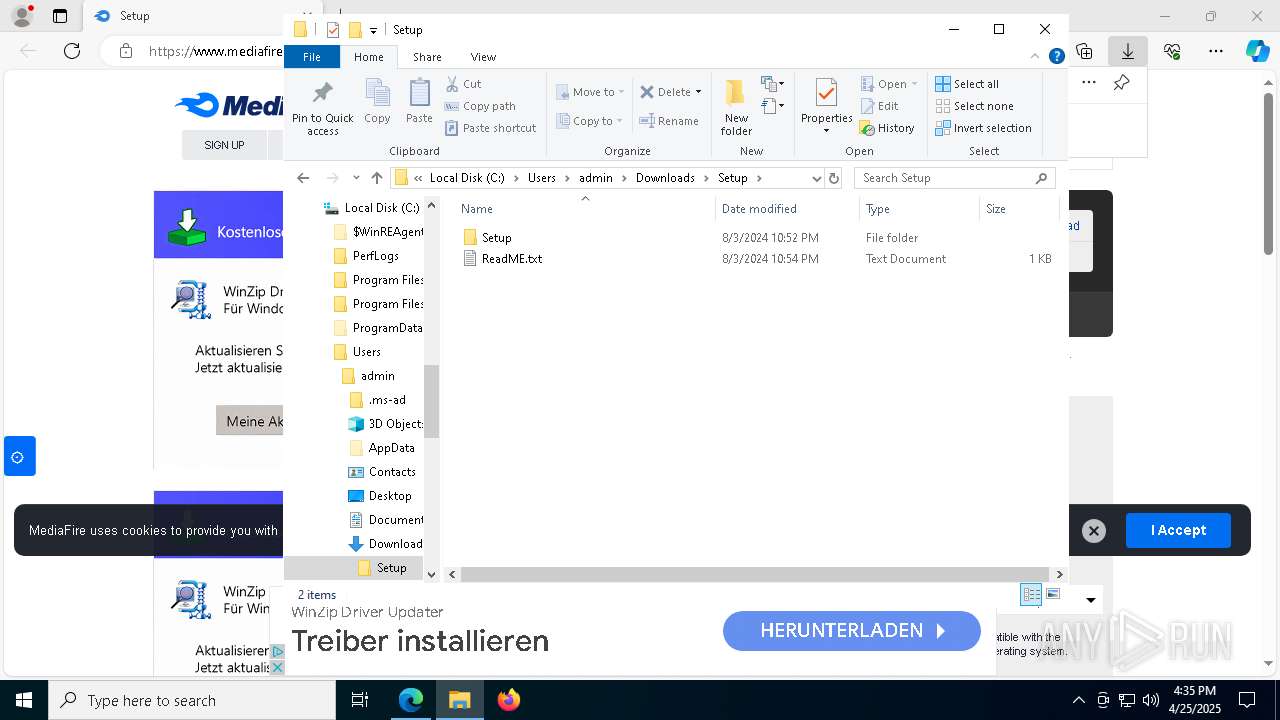
| Analysis date: | April 25, 2025, 16:35:07 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
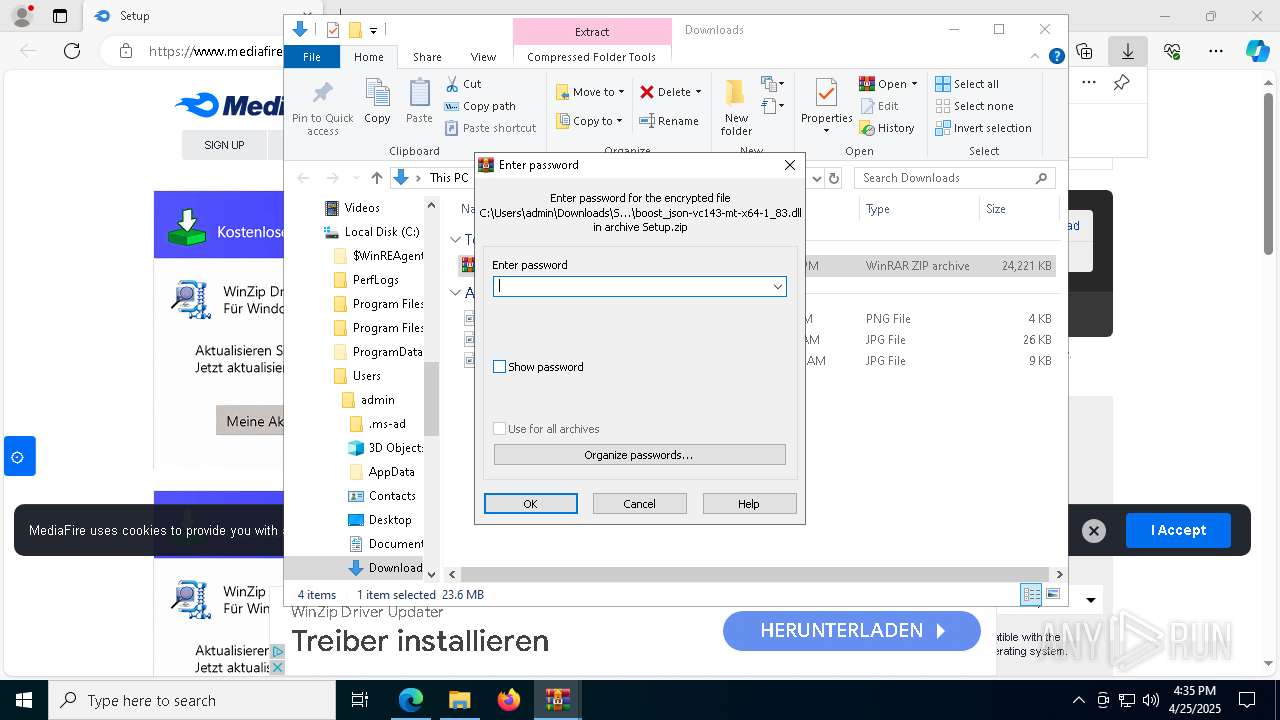
| MD5: | 4C286B28FF837D0DCA657CFAF7BF431A |
| SHA1: | 1B8A3FF0F69F6DEF8012E72CE90A369CB5F33DB7 |
| SHA256: | 703BD6971F0F383BCAE6F92FE6EBE8C33D8C68FC7D939B396D32072EFB141491 |
| SSDEEP: | 3:N8DSLw3eGUoYi5JFfLUtP9:2OLw3eG0yFj61 |
MALICIOUS
Changes the autorun value in the registry
- Setup.exe (PID: 8888)
Changes Windows Defender settings
- wmplayer.exe (PID: 6700)
Adds extension to the Windows Defender exclusion list
- wmplayer.exe (PID: 6700)
Vulnerable driver has been detected
- wmplayer.exe (PID: 6700)
MINER has been detected (SURICATA)
- svchost.exe (PID: 2196)
- conhost.exe (PID: 9076)
Connects to the CnC server
- conhost.exe (PID: 9076)
Uninstalls Malicious Software Removal Tool (MRT)
- cmd.exe (PID: 9068)
XMRIG has been detected (YARA)
- conhost.exe (PID: 9076)
REDLINE has been detected (YARA)
- playalacch.exe (PID: 6068)
SUSPICIOUS
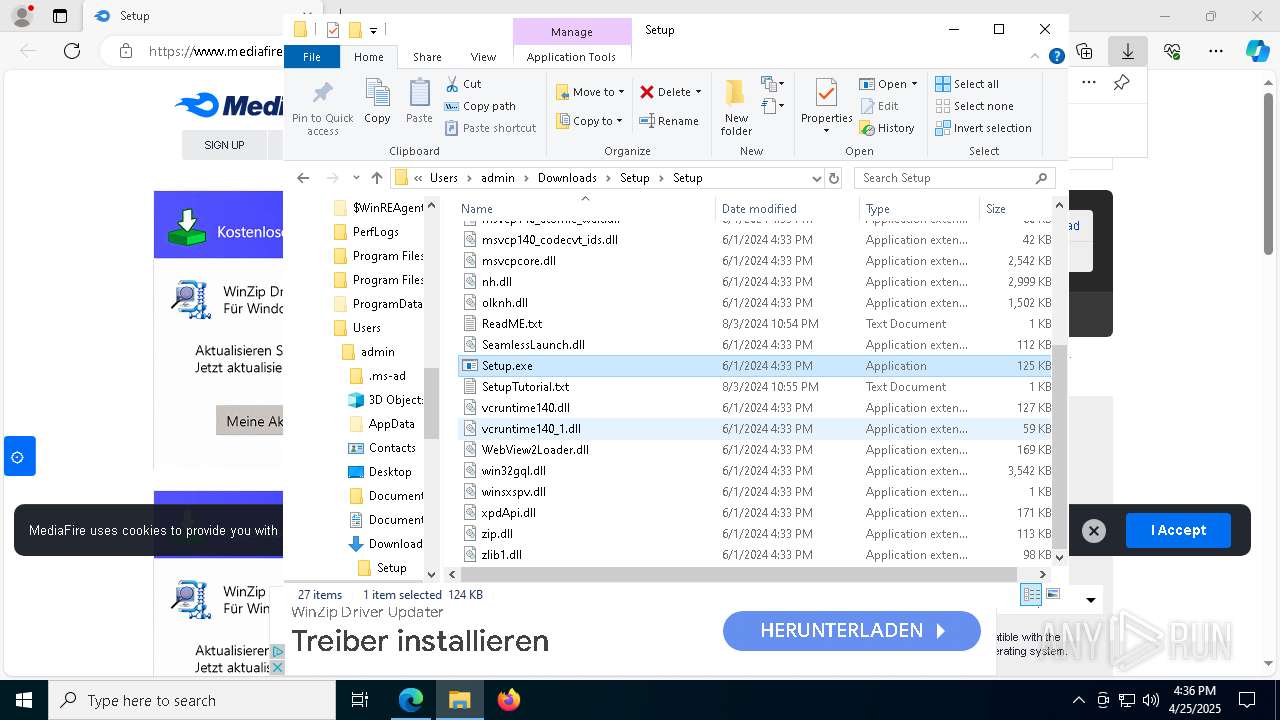
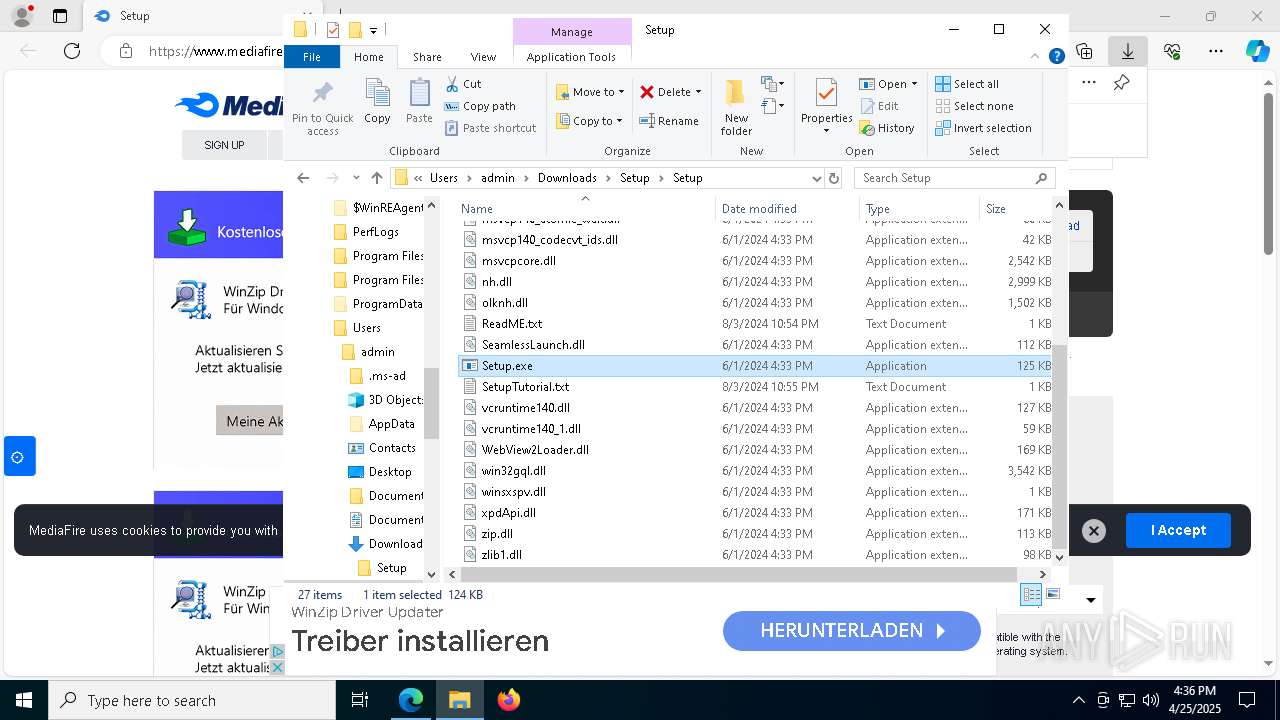
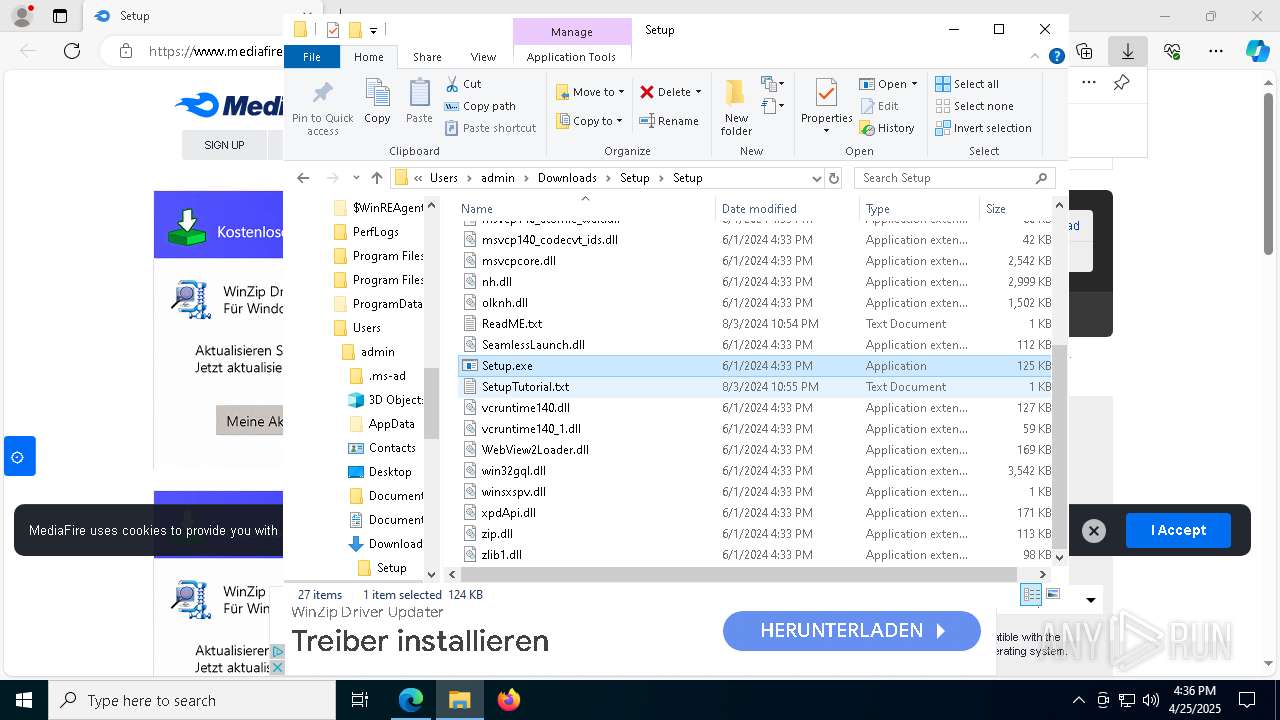
The process drops C-runtime libraries
- msedge.exe (PID: 7312)
- Setup.exe (PID: 8888)
- WinService.exe (PID: 300)
- WinService.exe (PID: 6572)
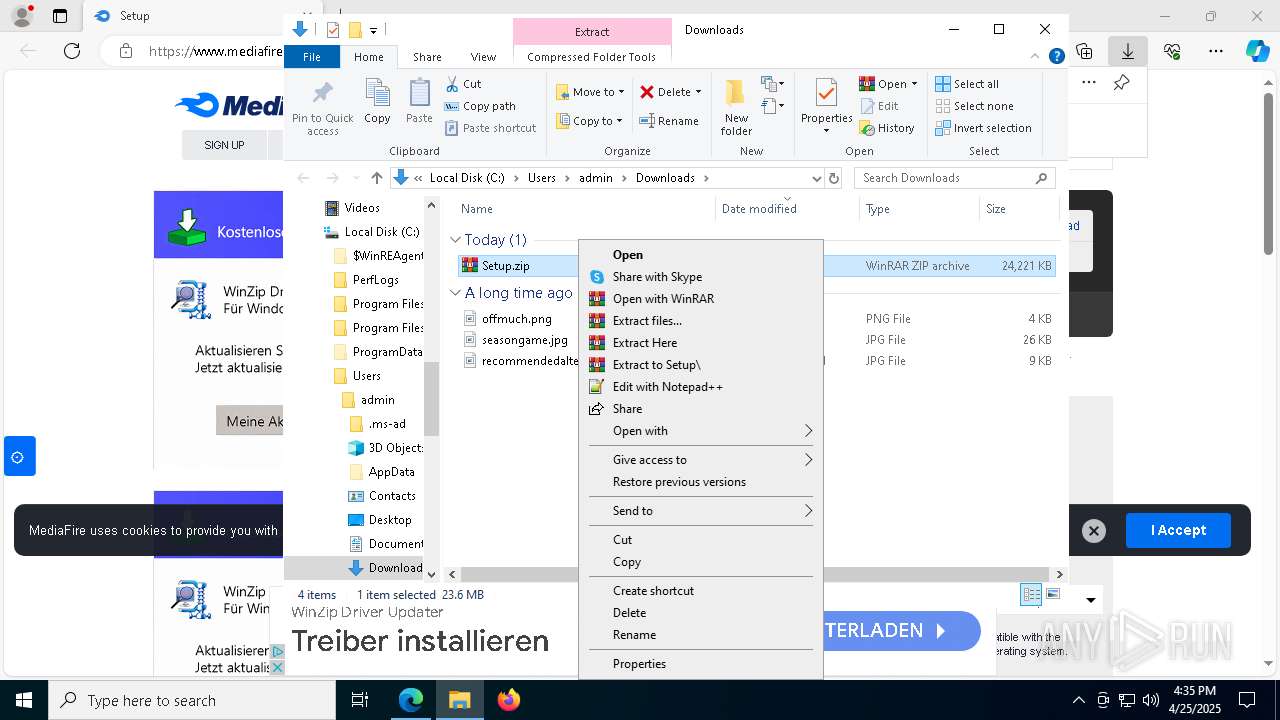
Process drops legitimate windows executable
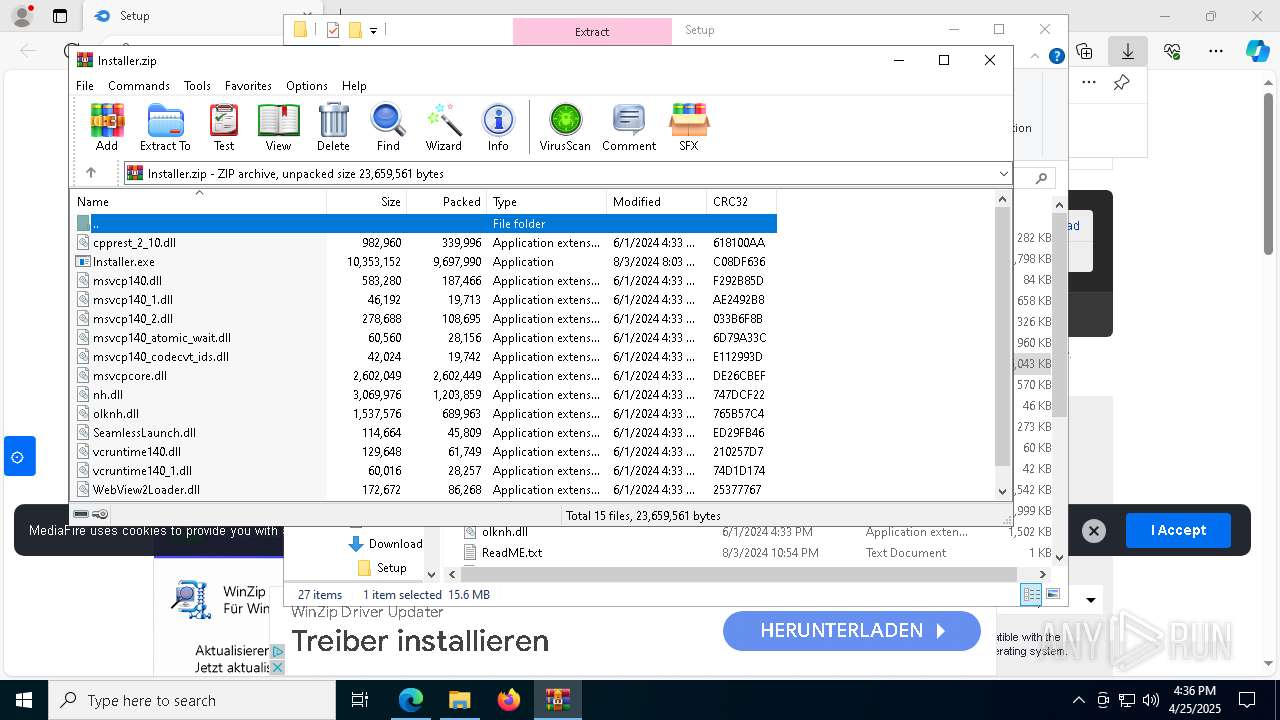
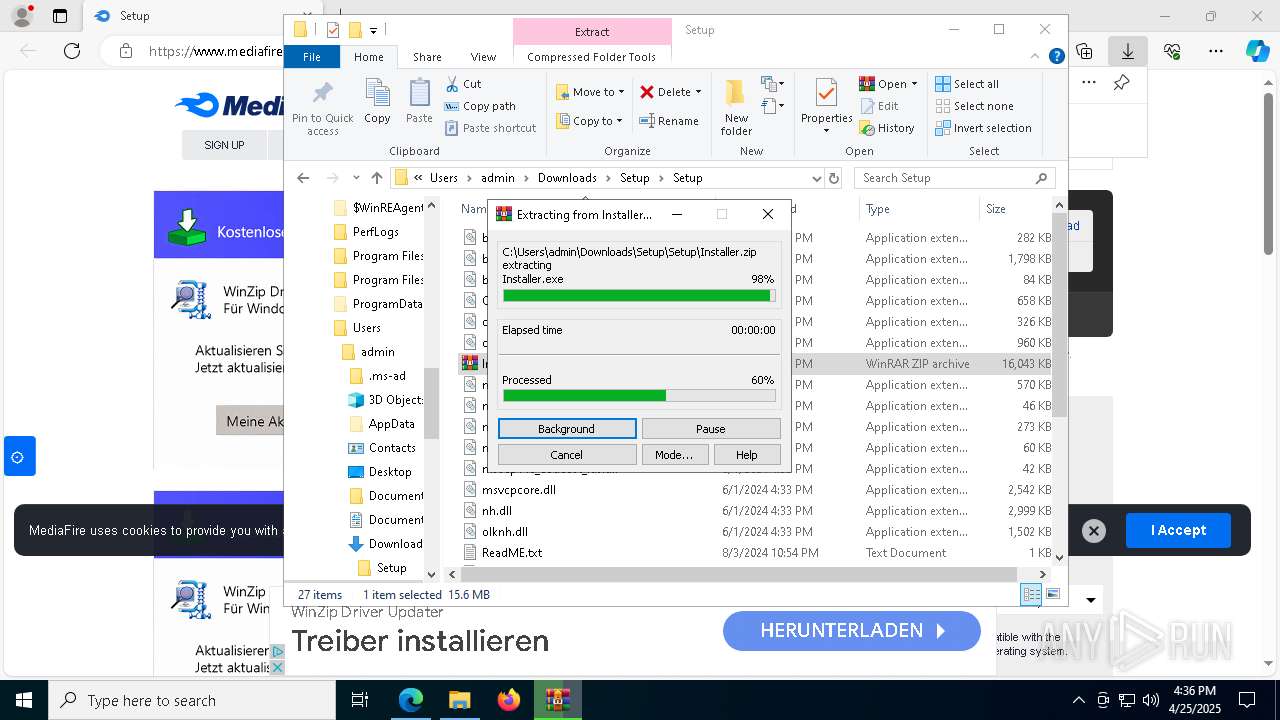
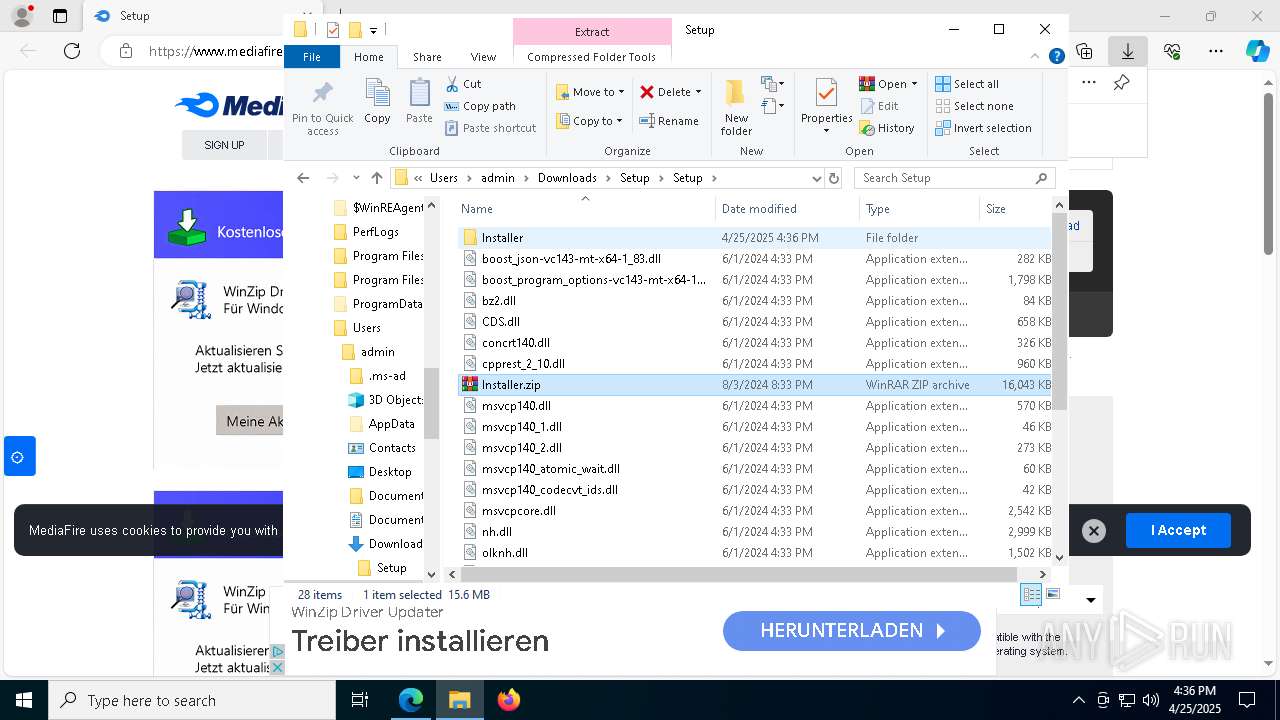
- WinRAR.exe (PID: 8408)
- msedge.exe (PID: 7312)
- Setup.exe (PID: 8888)
- WinRAR.exe (PID: 9044)
- WinService.exe (PID: 300)
- WinService.exe (PID: 6572)
Executable content was dropped or overwritten
- Setup.exe (PID: 8888)
- wmplayer.exe (PID: 6700)
- Installer.exe (PID: 8408)
- WinService.exe (PID: 300)
- WinService.exe (PID: 4776)
- WinService.exe (PID: 6572)
- sept.exe (PID: 8344)
Manipulates environment variables
- powershell.exe (PID: 6264)
Starts POWERSHELL.EXE for commands execution
- wmplayer.exe (PID: 6700)
Starts CMD.EXE for commands execution
- wmplayer.exe (PID: 6700)
- WinService.exe (PID: 4776)
Script adds exclusion path to Windows Defender
- wmplayer.exe (PID: 6700)
Process uninstalls Windows update
- wusa.exe (PID: 8068)
Drops a system driver (possible attempt to evade defenses)
- wmplayer.exe (PID: 6700)
Crypto Currency Mining Activity Detected
- svchost.exe (PID: 2196)
Potential Corporate Privacy Violation
- conhost.exe (PID: 9076)
Connects to unusual port
- conhost.exe (PID: 9076)
- playalacch.exe (PID: 6068)
Script adds exclusion extension to Windows Defender
- wmplayer.exe (PID: 6700)
Process drops python dynamic module
- WinService.exe (PID: 300)
- WinService.exe (PID: 6572)
Application launched itself
- WinService.exe (PID: 300)
- WinService.exe (PID: 6572)
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 8176)
Executing commands from a ".bat" file
- WinService.exe (PID: 4776)
The executable file from the user directory is run by the CMD process
- WinService.exe (PID: 6572)
There is functionality for taking screenshot (YARA)
- playalacch.exe (PID: 6068)
- WinService.exe (PID: 6572)
- WinService.exe (PID: 5308)
Starts itself from another location
- sept.exe (PID: 8344)
Found regular expressions for crypto-addresses (YARA)
- WinService.exe (PID: 5308)
Uses REG/REGEDIT.EXE to modify registry
- putsibdjzarh.exe (PID: 1804)
- sept.exe (PID: 8344)
INFO
Checks supported languages
- identity_helper.exe (PID: 7308)
- Setup.exe (PID: 8888)
- wmplayer.exe (PID: 6700)
Reads the computer name
- identity_helper.exe (PID: 7308)
- Setup.exe (PID: 8888)
Application launched itself
- msedge.exe (PID: 7312)
Reads Environment values
- identity_helper.exe (PID: 7308)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 8408)
- WinRAR.exe (PID: 9044)
- msedge.exe (PID: 8844)
The sample compiled with english language support
- WinRAR.exe (PID: 8408)
- msedge.exe (PID: 7312)
- Setup.exe (PID: 8888)
- WinRAR.exe (PID: 9044)
- WinService.exe (PID: 300)
- WinService.exe (PID: 6572)
- msedge.exe (PID: 8844)
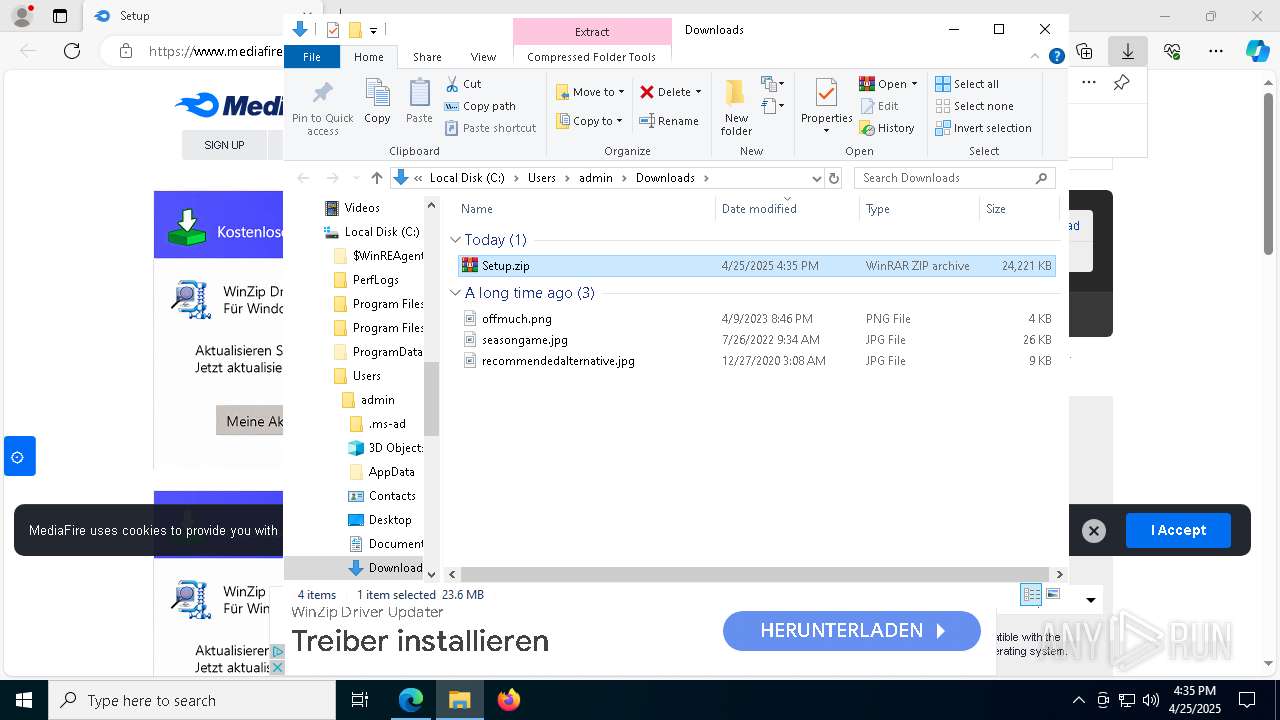
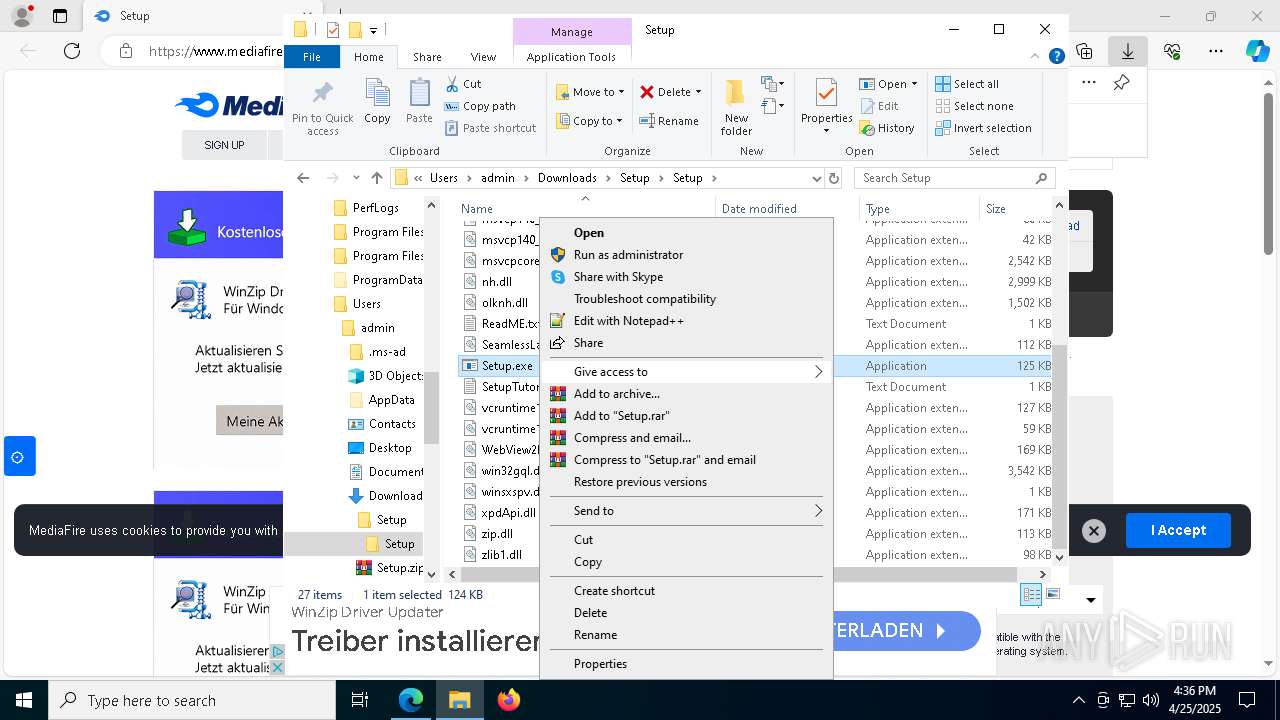
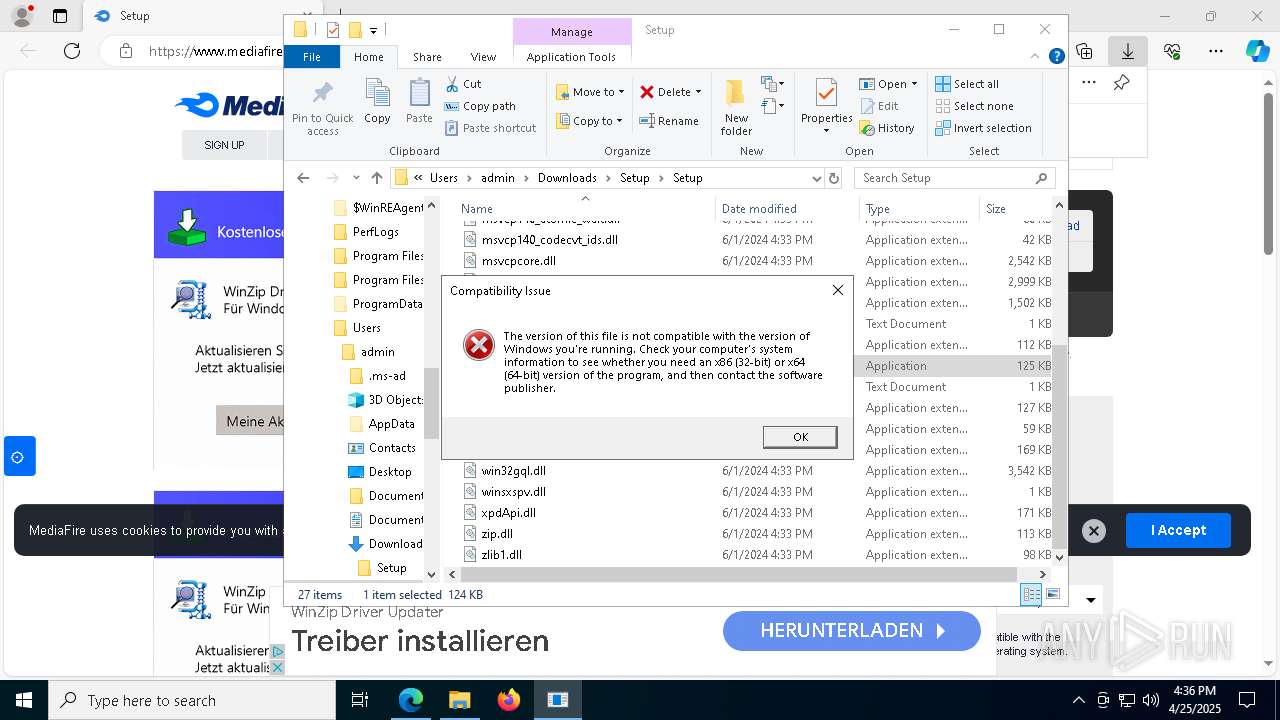
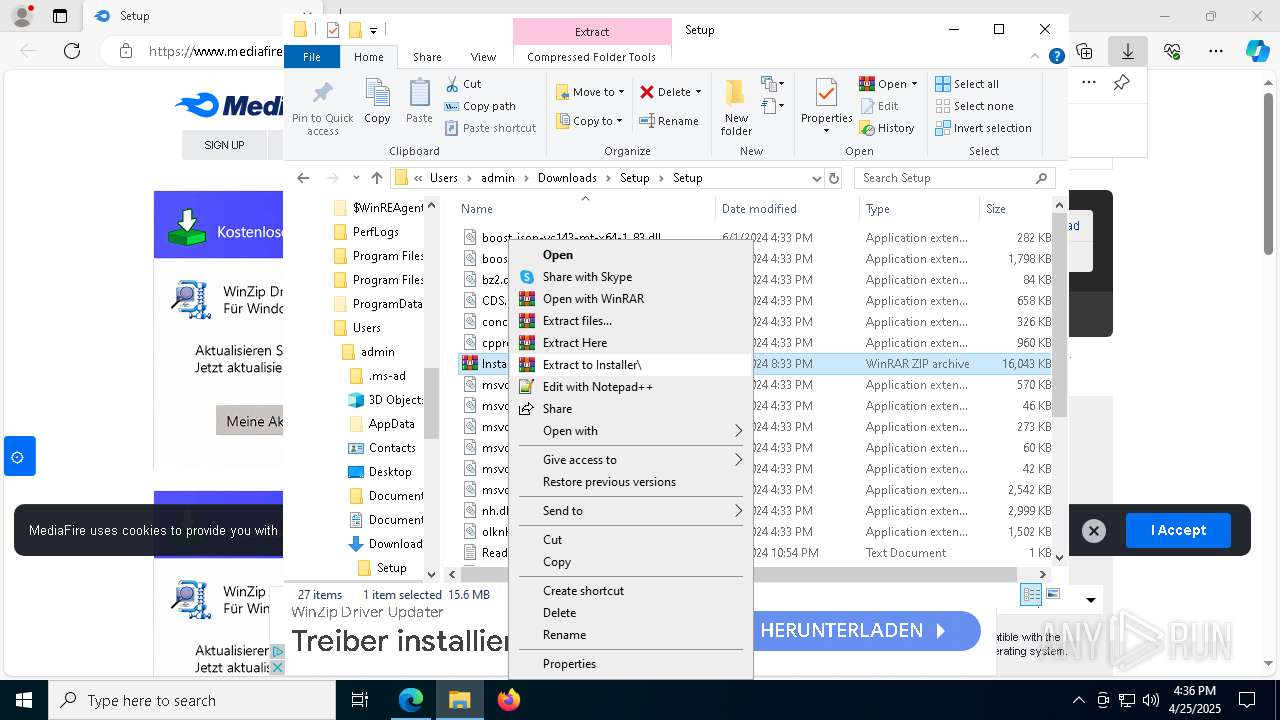
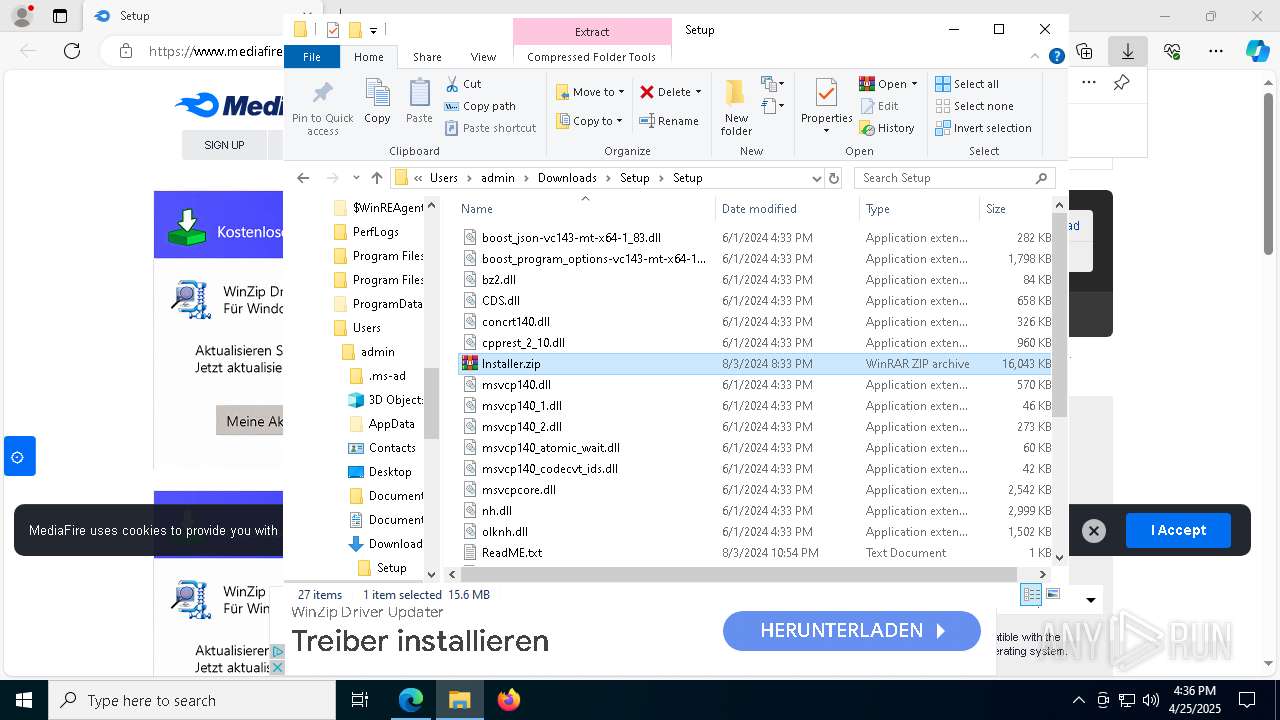
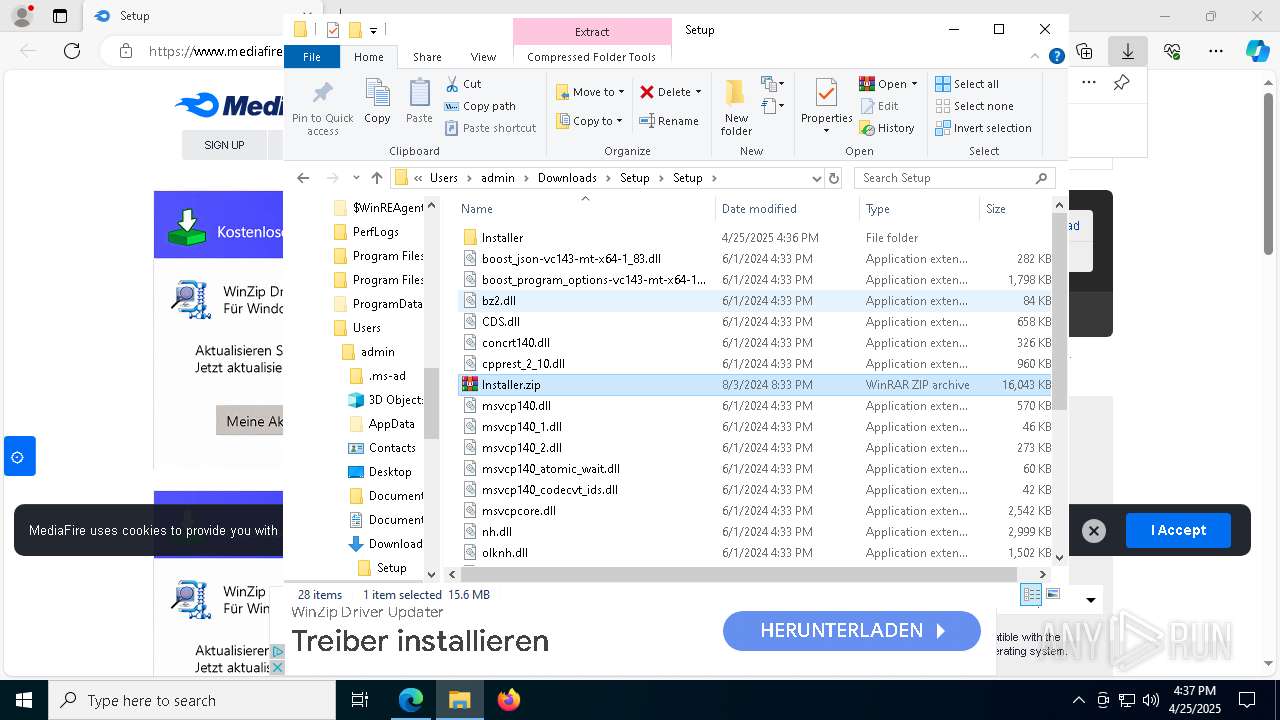
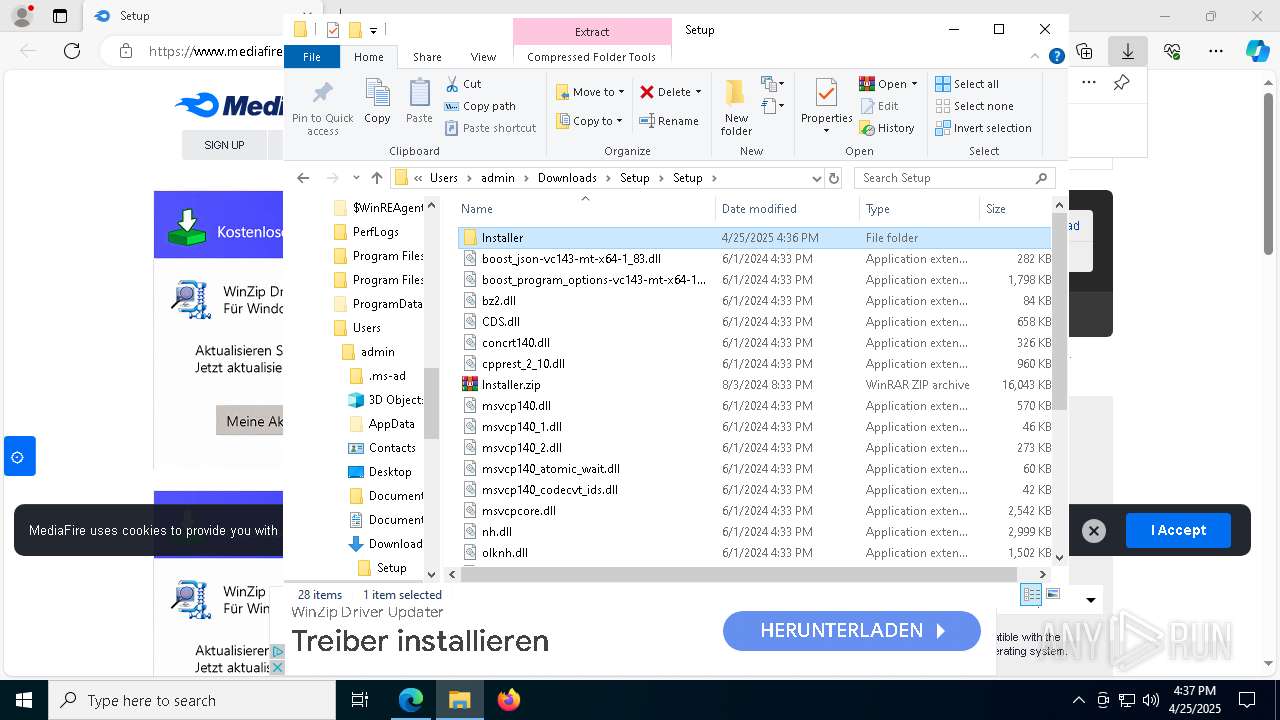
Manual execution by a user
- WinRAR.exe (PID: 8408)
- Setup.exe (PID: 8888)
- WinRAR.exe (PID: 3888)
- WinRAR.exe (PID: 9044)
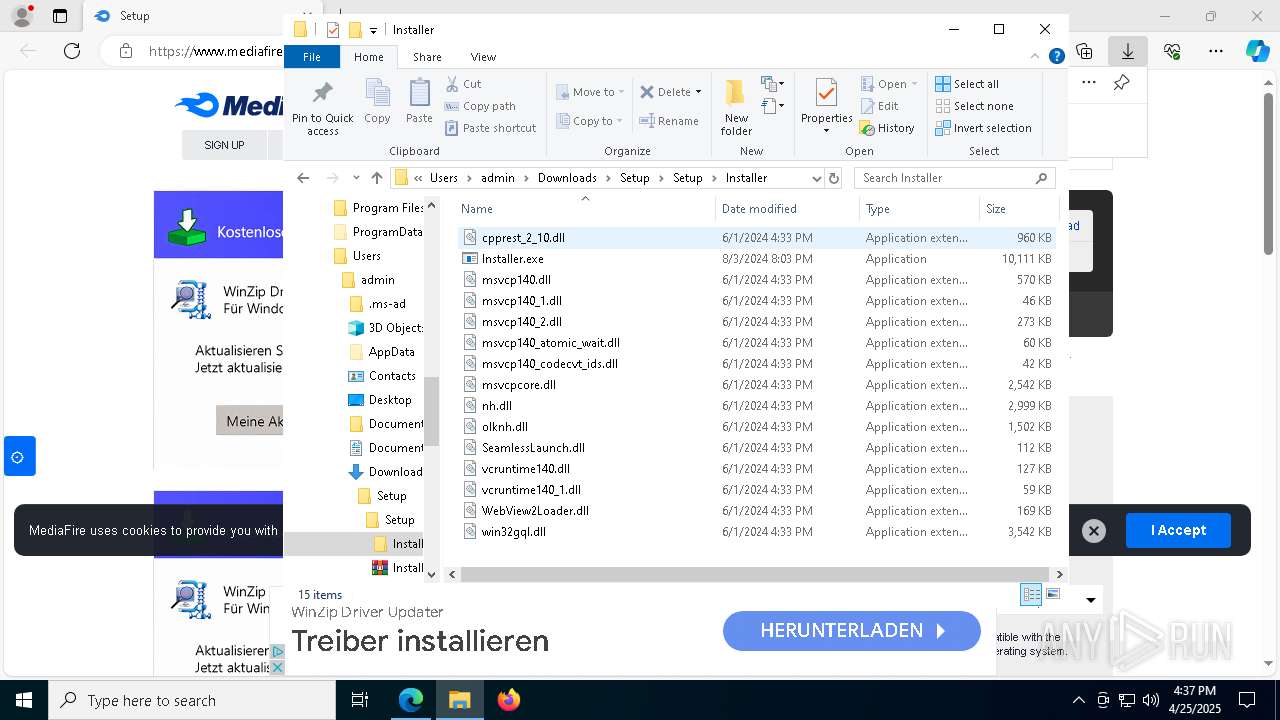
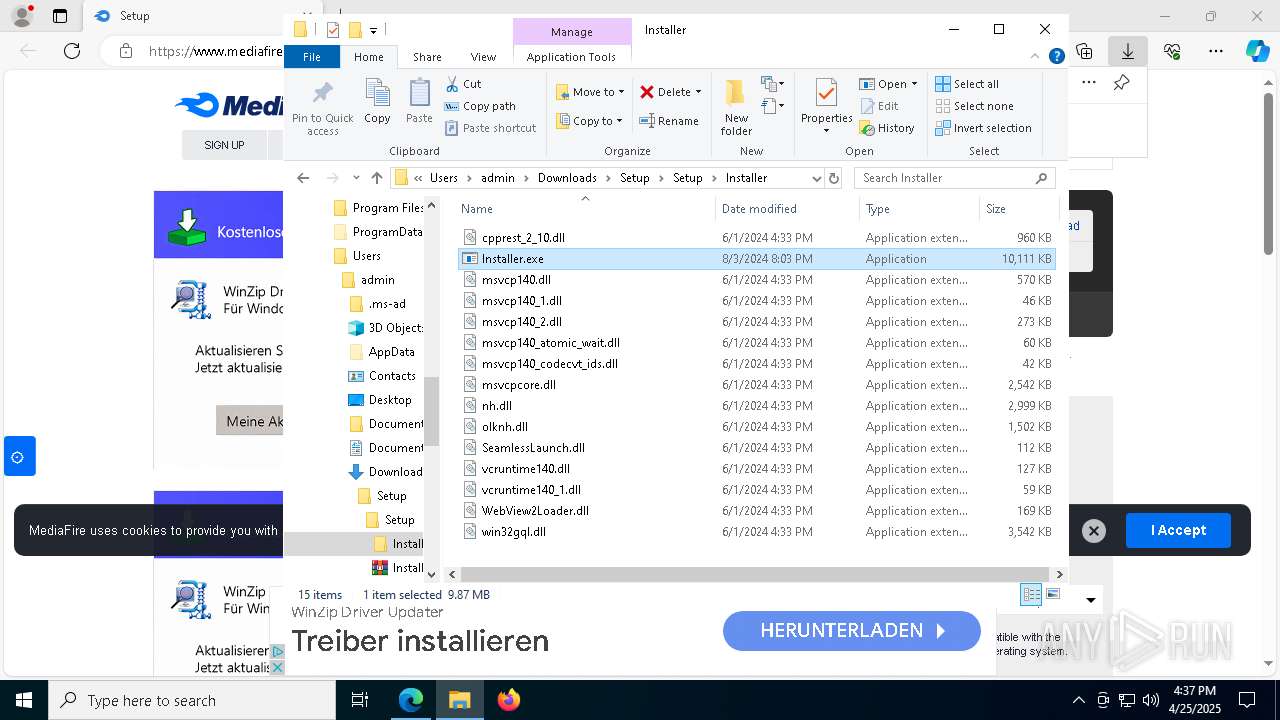
- Installer.exe (PID: 8408)
Reads the software policy settings
- slui.exe (PID: 5608)
The sample compiled with japanese language support
- wmplayer.exe (PID: 6700)
UPX packer has been detected
- conhost.exe (PID: 9076)
PyInstaller has been detected (YARA)
- WinService.exe (PID: 5308)
- WinService.exe (PID: 6572)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
RedLine
(PID) Process(6068) playalacch.exe
C2 (1)51.195.206.227:38719
BotnetTgFilecr
Options
ErrorMessage
Keys
XorRyper
Total processes
224
Monitored processes
88
Malicious processes
13
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 300 | "C:\Users\admin\AppData\Local\Temp\WinService.exe" | C:\Users\admin\AppData\Local\Temp\WinService.exe | Installer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 1 Modules
| |||||||||||||||
| 516 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5672 --field-trial-handle=2732,i,16374731680786518204,10356173785098948640,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 904 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1056 | C:\WINDOWS\system32\conhost.exe | C:\Windows\System32\conhost.exe | — | putsibdjzarh.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1168 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1228 | "C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe" --type=utility --utility-sub-type=winrt_app_id.mojom.WinrtAppIdService --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=6508 --field-trial-handle=2732,i,16374731680786518204,10356173785098948640,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: PWA Identity Proxy Host Exit code: 3221226029 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1300 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5404 --field-trial-handle=2732,i,16374731680786518204,10356173785098948640,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1804 | "C:\Users\admin\AppData\Roaming\fwrnugmlimyc\putsibdjzarh.exe" | C:\Users\admin\AppData\Roaming\fwrnugmlimyc\putsibdjzarh.exe | — | sept.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2196 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2268 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=1288 --field-trial-handle=2732,i,16374731680786518204,10356173785098948640,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
17 425
Read events
17 366
Write events
59
Delete events
0
Modification events
| (PID) Process: | (7312) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (7312) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (7312) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (7312) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (7312) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 6331A13333922F00 | |||
| (PID) Process: | (7312) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 4EEDB03333922F00 | |||
| (PID) Process: | (7312) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\197456 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {689E1119-F985-49B7-B2FE-321DB10380D4} | |||
| (PID) Process: | (7312) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\197456 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {3EAFFE2F-EA1A-4EE0-96B8-EAD8DF1E0FDA} | |||
| (PID) Process: | (7312) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\197456 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {7C632391-BBEC-479A-AE78-B23EDD1A77F5} | |||
| (PID) Process: | (7312) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\197456 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {BDE04EFD-CE60-4D58-86C9-77330A5BF17B} | |||
Executable files
108
Suspicious files
457
Text files
73
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7312 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF10baf5.TMP | — | |
MD5:— | SHA256:— | |||
| 7312 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7312 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF10baf5.TMP | — | |
MD5:— | SHA256:— | |||
| 7312 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF10baf5.TMP | — | |
MD5:— | SHA256:— | |||
| 7312 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF10baf5.TMP | — | |
MD5:— | SHA256:— | |||
| 7312 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7312 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7312 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7312 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF10bb43.TMP | — | |
MD5:— | SHA256:— | |||
| 7312 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
27
TCP/UDP connections
292
DNS requests
341
Threats
15
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.219.150.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 2.19.11.105:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5544 | svchost.exe | HEAD | 200 | 23.48.23.7:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9b9f8fb4-8a65-41e4-bda3-5416858f0aeb?P1=1746054376&P2=404&P3=2&P4=i2UWeI%2fnRwHtBdbOCk%2bVdoB%2bteAreIVtUU3GPqQyVvj%2fjysReszQ6sRowbAi6ayD%2fYOLERNCCjkeVsG7qcdgFQ%3d%3d | unknown | — | — | whitelisted |
2420 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
2420 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
5544 | svchost.exe | GET | 206 | 23.48.23.7:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9b9f8fb4-8a65-41e4-bda3-5416858f0aeb?P1=1746054376&P2=404&P3=2&P4=i2UWeI%2fnRwHtBdbOCk%2bVdoB%2bteAreIVtUU3GPqQyVvj%2fjysReszQ6sRowbAi6ayD%2fYOLERNCCjkeVsG7qcdgFQ%3d%3d | unknown | — | — | whitelisted |
5544 | svchost.exe | GET | 206 | 23.48.23.7:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9b9f8fb4-8a65-41e4-bda3-5416858f0aeb?P1=1746054376&P2=404&P3=2&P4=i2UWeI%2fnRwHtBdbOCk%2bVdoB%2bteAreIVtUU3GPqQyVvj%2fjysReszQ6sRowbAi6ayD%2fYOLERNCCjkeVsG7qcdgFQ%3d%3d | unknown | — | — | whitelisted |
5544 | svchost.exe | GET | 206 | 23.48.23.7:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9b9f8fb4-8a65-41e4-bda3-5416858f0aeb?P1=1746054376&P2=404&P3=2&P4=i2UWeI%2fnRwHtBdbOCk%2bVdoB%2bteAreIVtUU3GPqQyVvj%2fjysReszQ6sRowbAi6ayD%2fYOLERNCCjkeVsG7qcdgFQ%3d%3d | unknown | — | — | whitelisted |
5544 | svchost.exe | GET | 206 | 23.48.23.7:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9b9f8fb4-8a65-41e4-bda3-5416858f0aeb?P1=1746054376&P2=404&P3=2&P4=i2UWeI%2fnRwHtBdbOCk%2bVdoB%2bteAreIVtUU3GPqQyVvj%2fjysReszQ6sRowbAi6ayD%2fYOLERNCCjkeVsG7qcdgFQ%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | 2.19.11.105:80 | crl.microsoft.com | Elisa Oyj | NL | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.219.150.101:80 | www.microsoft.com | AKAMAI-AS | CL | whitelisted |
7612 | msedge.exe | 104.17.151.117:443 | www.mediafire.com | — | — | whitelisted |
7312 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
7612 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7612 | msedge.exe | 150.171.28.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7612 | msedge.exe | 13.107.253.45:443 | edge-mobile-static.azureedge.net | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7612 | msedge.exe | 13.107.6.158:443 | business.bing.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
www.mediafire.com |
| whitelisted |
business.bing.com |
| whitelisted |
bzib.nelreports.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7612 | msedge.exe | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain (www .mediafire .com) in DNS Lookup |
7612 | msedge.exe | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain (www .mediafire .com) in DNS Lookup |
7612 | msedge.exe | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain (www .mediafire .com) in DNS Lookup |
7612 | msedge.exe | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain (www .mediafire .com) in DNS Lookup |
7612 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |
7612 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |
7612 | msedge.exe | Potentially Bad Traffic | ET FILE_SHARING File Sharing Related Domain in DNS Lookup (download .mediafire .com) |
7612 | msedge.exe | Potentially Bad Traffic | ET FILE_SHARING File Sharing Related Domain in DNS Lookup (download .mediafire .com) |
7612 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |
7612 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |